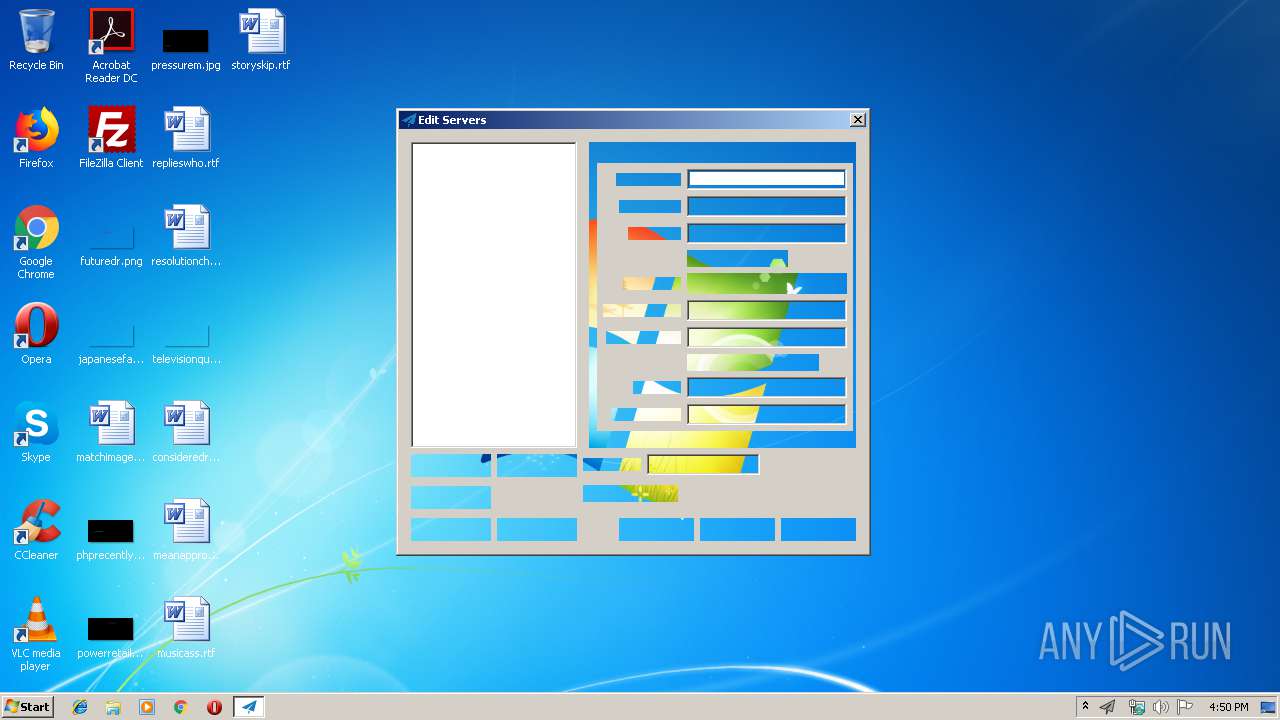
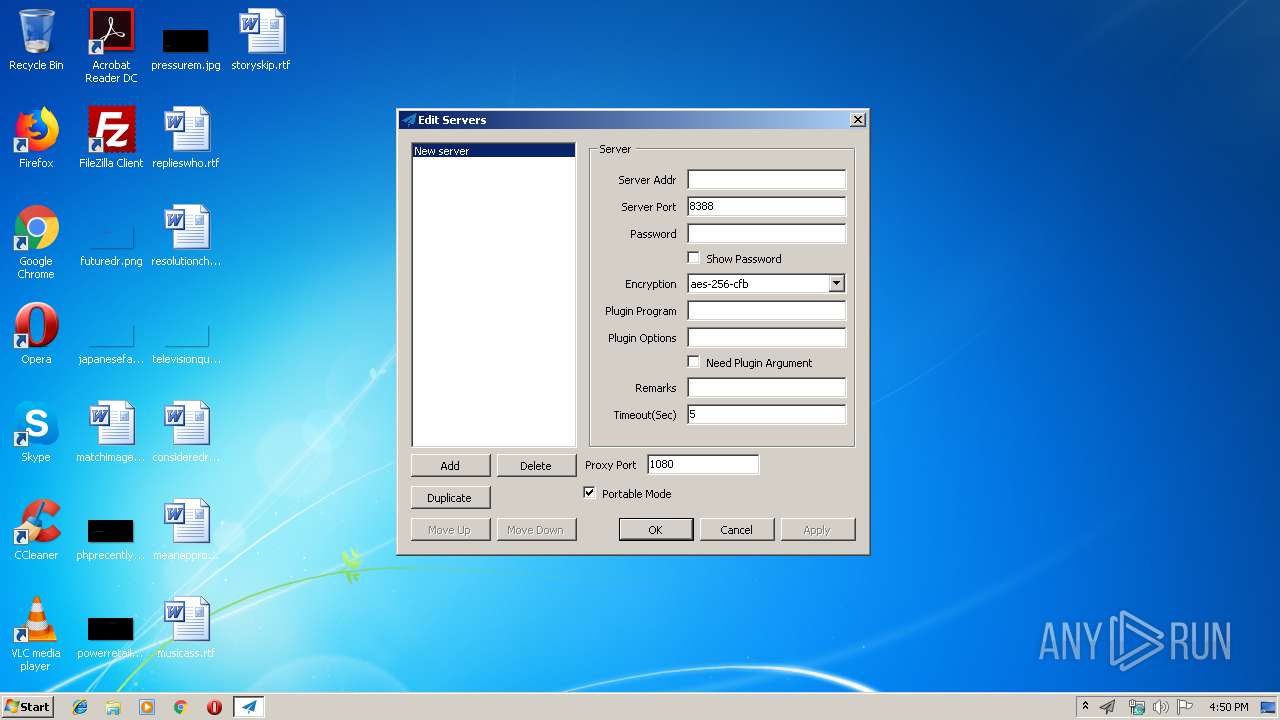
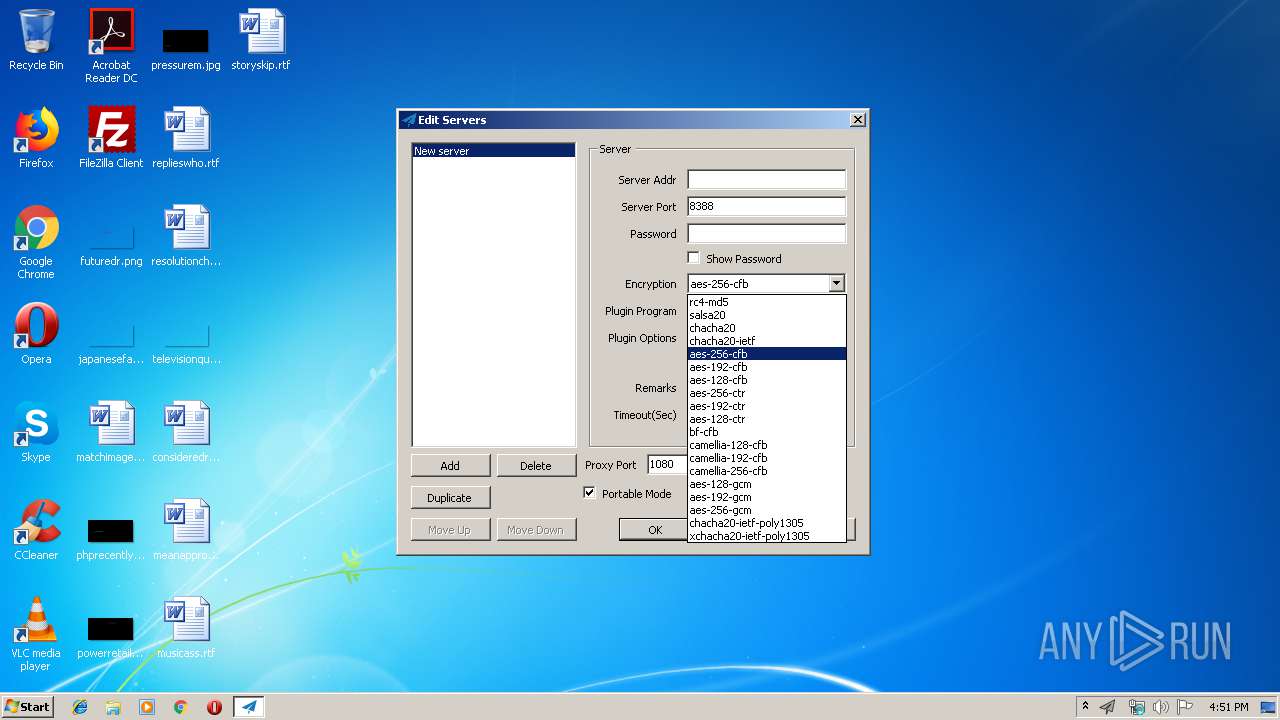
| File name: | Shadowsocks.exe |
| Full analysis: | https://app.any.run/tasks/c1aed271-4156-494f-ae99-caeaeee747e4 |
| Verdict: | Suspicious activity |
| Analysis date: | July 30, 2019, 15:50:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | DFCAA8A864C9D2E6605BB9A7C23267B2 |
| SHA1: | A4E387F0C4CFA6813937224213447575A4005886 |
| SHA256: | AFEC8DFACE828B0092E2BD068587C06C917F7E70B36CC82E57BECD14E3D9570B |
| SSDEEP: | 49152:joQC8YyoLNgbT3o9gC7qLLaOPyBOsJ4/xRWWr5unhBOLn2mVARKE:joQC8GIY9g7PaBBy/xkWrahw5E |
MALICIOUS
Application was dropped or rewritten from another process
- ss_privoxy.exe (PID: 3128)
- sysproxy.exe (PID: 3504)
- sysproxy.exe (PID: 3000)
SUSPICIOUS
Executable content was dropped or overwritten
- Shadowsocks.exe (PID: 3664)
Creates files in the user directory
- rundll32.exe (PID: 3532)
Uses RUNDLL32.EXE to load library
- sysproxy.exe (PID: 3000)
Reads Internet Cache Settings
- rundll32.exe (PID: 3532)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:14 14:07:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 2382848 |
| InitializedDataSize: | 23040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x247b8e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.7.1 |
| ProductVersionNumber: | 4.1.7.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Shadowsocks |
| FileVersion: | 4.1.7.1 |
| InternalName: | Shadowsocks.exe |
| LegalCopyright: | clowwindy & community 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | Shadowsocks.exe |
| ProductName: | Shadowsocks |
| ProductVersion: | 4.1.7.1 |
| AssemblyVersion: | 4.1.7.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jul-2019 12:07:39 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Shadowsocks |
| FileVersion: | 4.1.7.1 |
| InternalName: | Shadowsocks.exe |
| LegalCopyright: | clowwindy & community 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | Shadowsocks.exe |
| ProductName: | Shadowsocks |
| ProductVersion: | 4.1.7.1 |
| Assembly Version: | 4.1.7.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Jul-2019 12:07:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00245B94 | 0x00245C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.93611 |
.rsrc | 0x00248000 | 0x00005668 | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49646 |
.reloc | 0x0024E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16178 | 1436 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.87827 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.60699 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.6861 | 4301 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.39374 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
38
Monitored processes
5
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3000 | "C:\Users\admin\AppData\Local\Temp\ss_win_temp\sysproxy.exe" set 1 - - - | C:\Users\admin\AppData\Local\Temp\ss_win_temp\sysproxy.exe | — | Shadowsocks.exe | |||||||||||
User: admin Company: Shadowsocks.org Integrity Level: MEDIUM Description: System Proxy Agent Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3128 | "C:\Users\admin\AppData\Local\Temp\ss_win_temp\ss_privoxy.exe" privoxy_-732403044.conf | C:\Users\admin\AppData\Local\Temp\ss_win_temp\ss_privoxy.exe | — | Shadowsocks.exe | |||||||||||
User: admin Company: The Privoxy team - www.privoxy.org Integrity Level: MEDIUM Description: Privoxy Exit code: 0 Version: 3.0.28 Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\Temp\ss_win_temp\sysproxy.exe" query | C:\Users\admin\AppData\Local\Temp\ss_win_temp\sysproxy.exe | — | Shadowsocks.exe | |||||||||||
User: admin Company: Shadowsocks.org Integrity Level: MEDIUM Description: System Proxy Agent Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3532 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | sysproxy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\AppData\Local\Temp\Shadowsocks.exe" | C:\Users\admin\AppData\Local\Temp\Shadowsocks.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Shadowsocks Exit code: 0 Version: 4.1.7.1 Modules
| |||||||||||||||
Total events
476
Read events
452
Write events
24
Delete events
0
Modification events
| (PID) Process: | (3664) Shadowsocks.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Shadowsocks.exe | |||
| (PID) Process: | (3664) Shadowsocks.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3664) Shadowsocks.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | DefaultConnectionSettings |
Value: 4600000008000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3000) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
0
Text files
9
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | Shadowsocks.exe | C:\Users\admin\AppData\Local\Temp\ss_win_temp\privoxy_-732403044.conf | text | |
MD5:— | SHA256:— | |||
| 3664 | Shadowsocks.exe | C:\Users\admin\AppData\Local\Temp\ss_win_temp\ss_privoxy.exe | executable | |
MD5:BC77D427634503F3EE7603BF009D7E32 | SHA256:07DC90AE5530E49C4F2D340B56BE4942F906F2265C2FDF6559E8B31C9416DA95 | |||
| 3532 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 3664 | Shadowsocks.exe | C:\Users\admin\AppData\Local\Temp\ss_win_temp\user-wininet.json | text | |
MD5:190D9F92D3F50C2A6E49158C8EA5C987 | SHA256:FFC21B53428A6471E9EC3F58EFCE7AFB4A1A374F4620169566336C902A3AB770 | |||
| 3532 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\4YX3MTCA\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3664 | Shadowsocks.exe | C:\Users\admin\AppData\Local\Temp\ss_win_temp\sysproxy.exe | executable | |
MD5:37DDCCA40070900CD870F5E1D42F267B | SHA256:EC334E443A3362A84B5915A266BEC60E63F604FDB77B09C993898EC7A438294B | |||
| 3532 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\M6US5G1F\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3532 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\SEH3Y21C\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3532 | rundll32.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 3532 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report