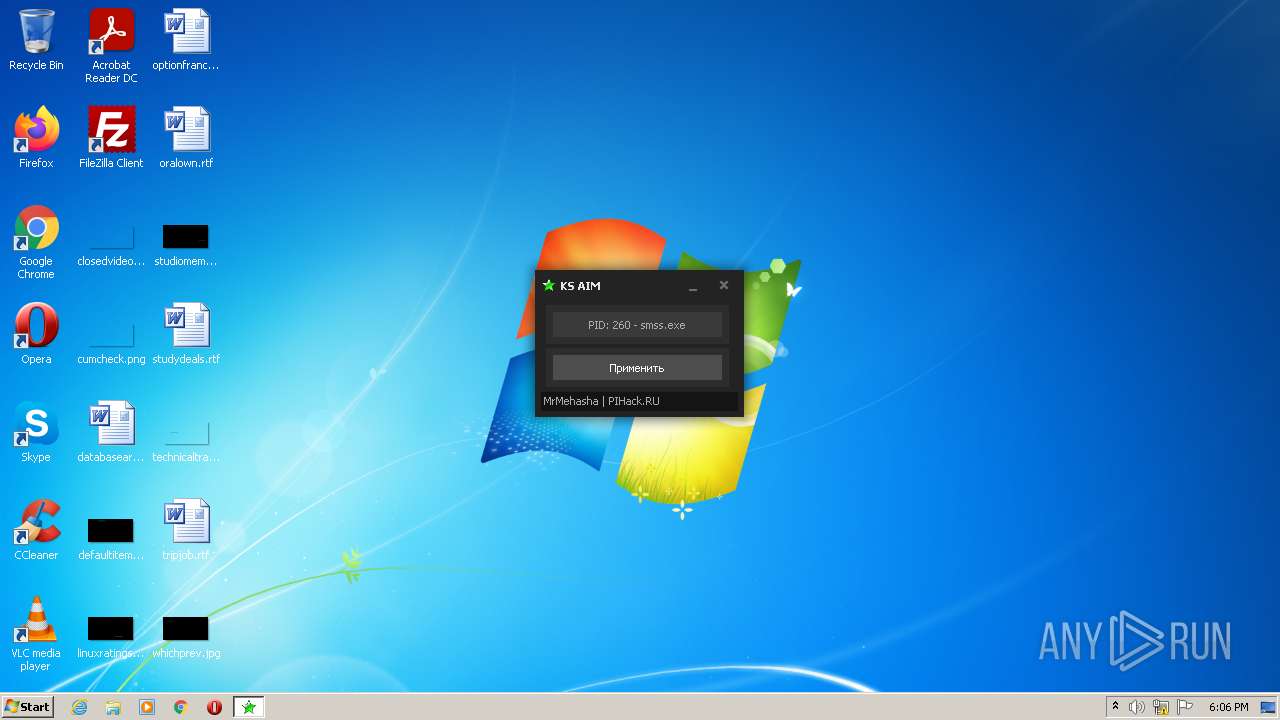
| File name: | Супер АИМ на Контра Сити.exe |
| Full analysis: | https://app.any.run/tasks/4eb004d6-88a5-4d92-bce8-e64f4e6b37d4 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 17:05:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B744F1EEBD2A5DF676F4902750AA79A3 |
| SHA1: | 4F4DF1349C4C57CF2289BD9FEEF3C7EB40D86F47 |
| SHA256: | AFE93E607F0866CFA114BFF92291ED8607E1ACA2208A9E24B4E22B9A24655F8B |
| SSDEEP: | 49152:4GTOcDBlasdzUS2GGSnmrz1kYSQwM1+EmY2xxoImYRX:4JctsCedMa+LxLmY |
MALICIOUS
Drops executable file immediately after starts
- Супер АИМ на Контра Сити.exe (PID: 3628)
SUSPICIOUS
Reads the computer name
- Супер АИМ на Контра Сити.exe (PID: 3628)
Checks supported languages
- Супер АИМ на Контра Сити.exe (PID: 3628)
Executable content was dropped or overwritten
- Супер АИМ на Контра Сити.exe (PID: 3628)
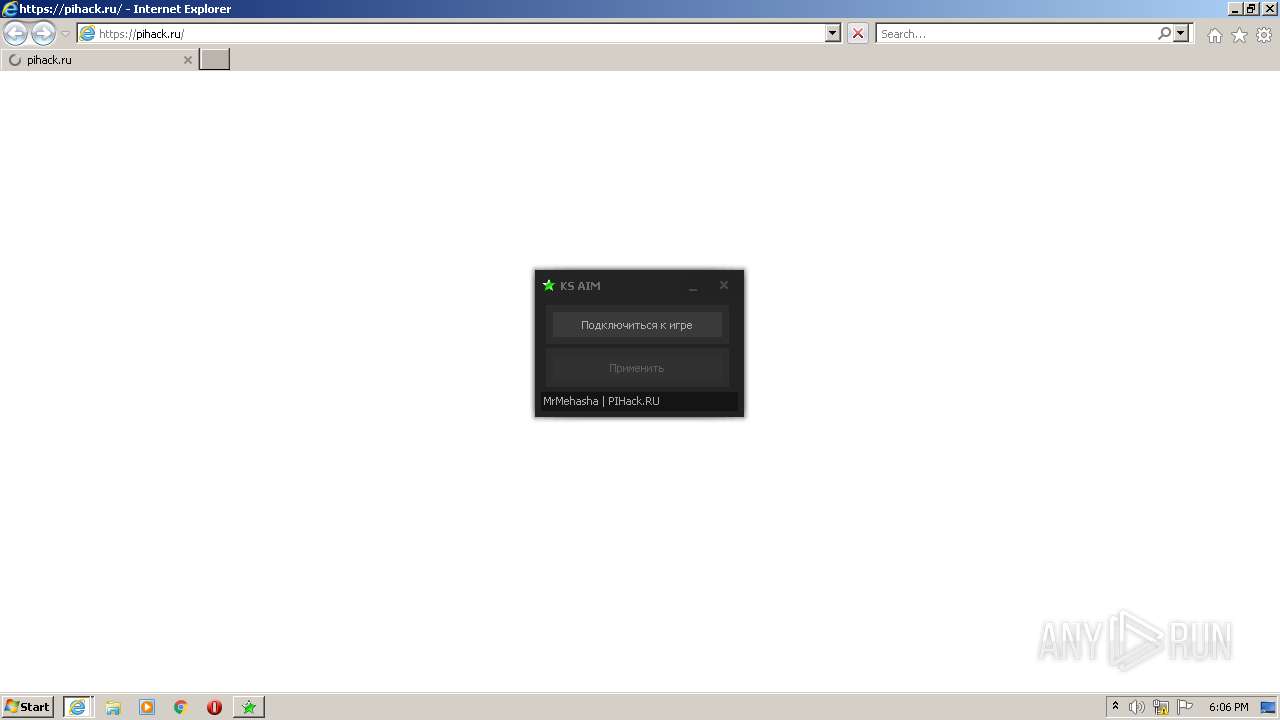
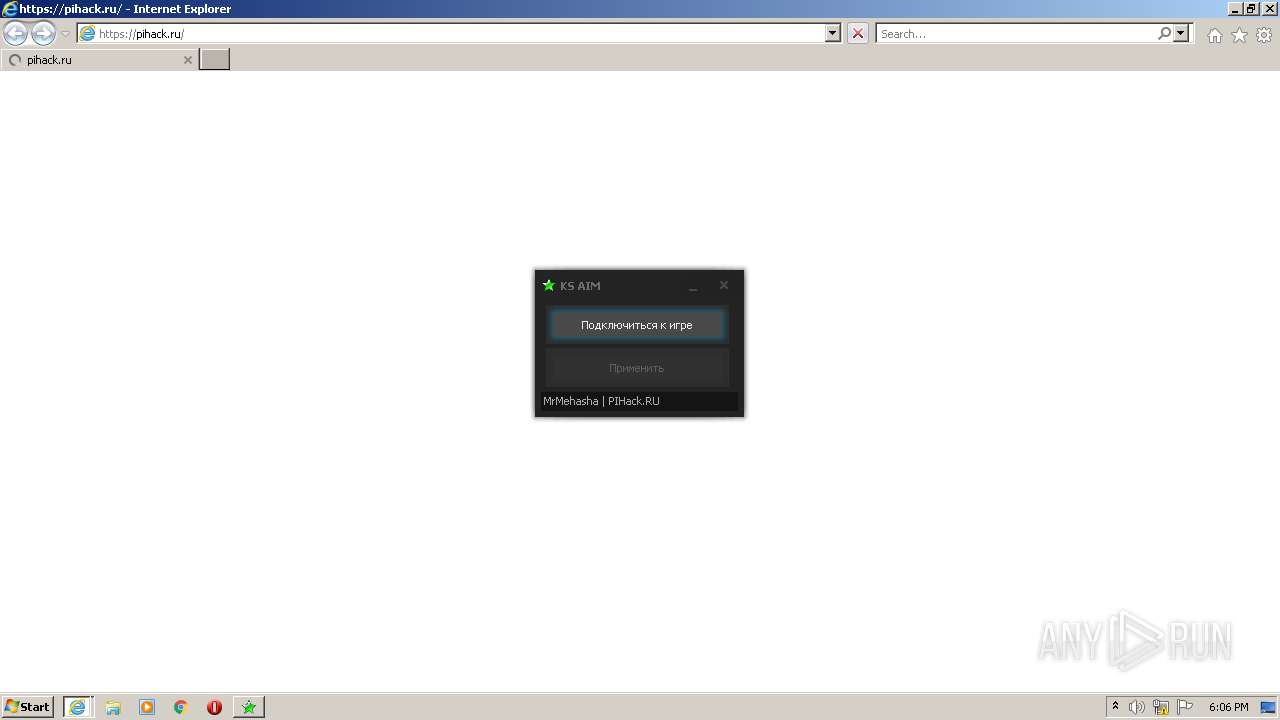
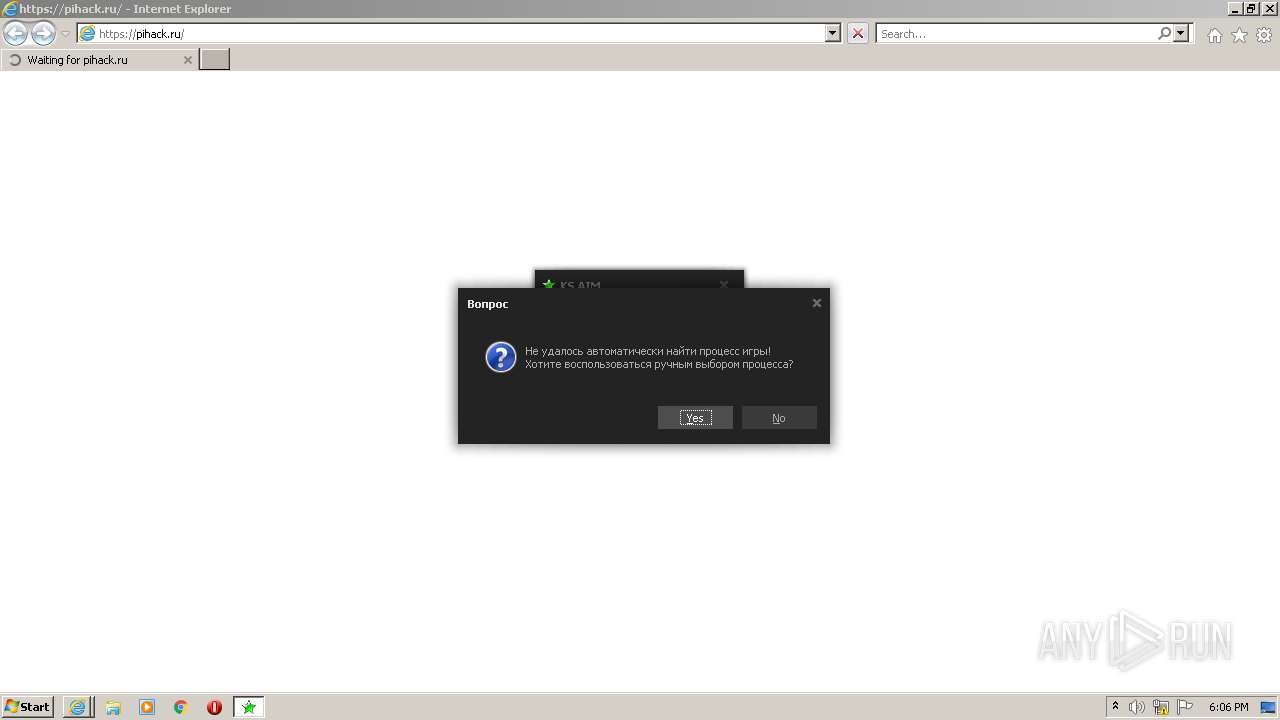
Starts Internet Explorer
- Супер АИМ на Контра Сити.exe (PID: 3628)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2476)
- iexplore.exe (PID: 2588)
Drops a file with a compile date too recent
- Супер АИМ на Контра Сити.exe (PID: 3628)
Creates files in the Windows directory
- Супер АИМ на Контра Сити.exe (PID: 3628)
INFO
Reads the computer name
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 3256)
- iexplore.exe (PID: 2588)
- iexplore.exe (PID: 2476)
Checks supported languages
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 3256)
- iexplore.exe (PID: 2588)
- iexplore.exe (PID: 2476)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2588)
- iexplore.exe (PID: 2476)
Reads settings of System Certificates
- iexplore.exe (PID: 2476)
- iexplore.exe (PID: 2588)
Changes settings of System certificates
- iexplore.exe (PID: 2588)
- iexplore.exe (PID: 2476)
Application launched itself
- iexplore.exe (PID: 3256)
- iexplore.exe (PID: 3688)
Changes internet zones settings
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 3256)
Checks Windows Trust Settings
- iexplore.exe (PID: 2588)
- iexplore.exe (PID: 2476)
Reads the date of Windows installation
- iexplore.exe (PID: 3688)
- iexplore.exe (PID: 3256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| ProductVersion: | 1.0.0.0 |
|---|---|
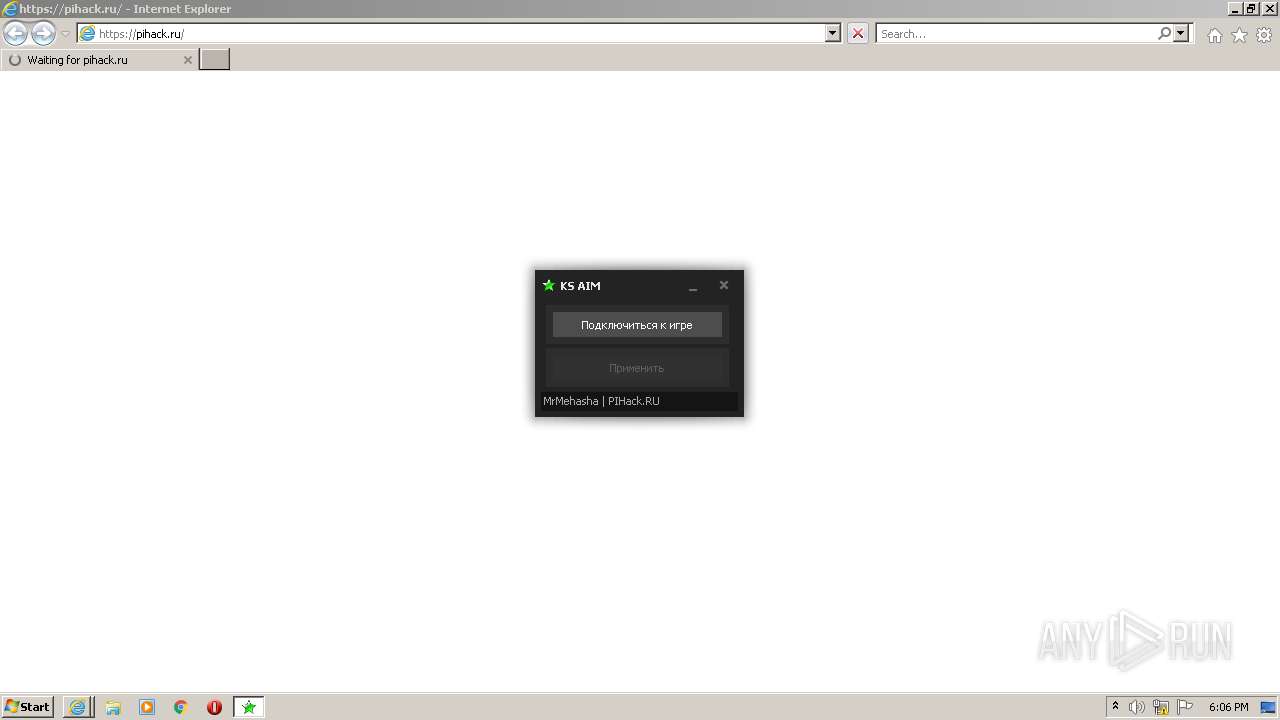
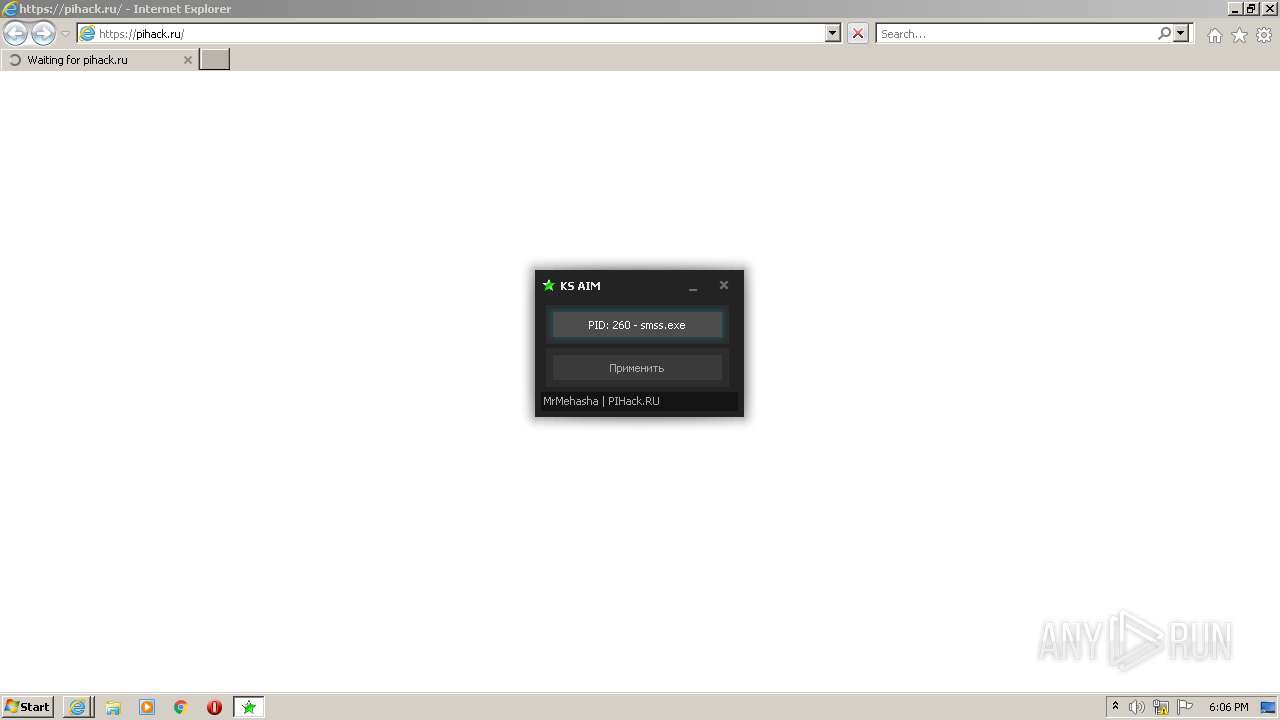
| ProductName: | KS_AIM |
| ProgramID: | com.embarcadero.KS_AIM |
| FileVersion: | 1.0.0.0 |
| FileDescription: | KS_AIM |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x6b0000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 637440 |
| CodeSize: | 3325952 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2016:12:17 17:30:23+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Dec-2016 16:30:23 |
| Detected languages: |
|
| FileDescription: | KS_AIM |
| FileVersion: | 1.0.0.0 |
| ProgramID: | com.embarcadero.KS_AIM |
| ProductName: | KS_AIM |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Dec-2016 16:30:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x00386000 | 0x00146200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9841 | |
.rsrc | 0x00387000 | 0x0004CAC0 | 0x00028C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95488 |
.idata | 0x003D4000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.04158 |
0x003D5000 | 0x00204000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.260771 | |
lrpgmryu | 0x005D9000 | 0x000D7000 | 0x000D6400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89081 |
iziphxxw | 0x006B0000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.2265 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27469 | 1697 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.23925 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 7.27629 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 7.36103 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 7.3949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 7.23774 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 7.34164 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 7.30779 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3682 | 6.01109 | 76 | Latin 1 / Western European | UNKNOWN | RT_STRING |
3683 | 6.74146 | 170 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
kernel32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x0033E5A8 |
__dbk_fcall_wrapper | 2 | 0x0001058C |
TMethodImplementationIntercept | 3 | 0x0006270C |
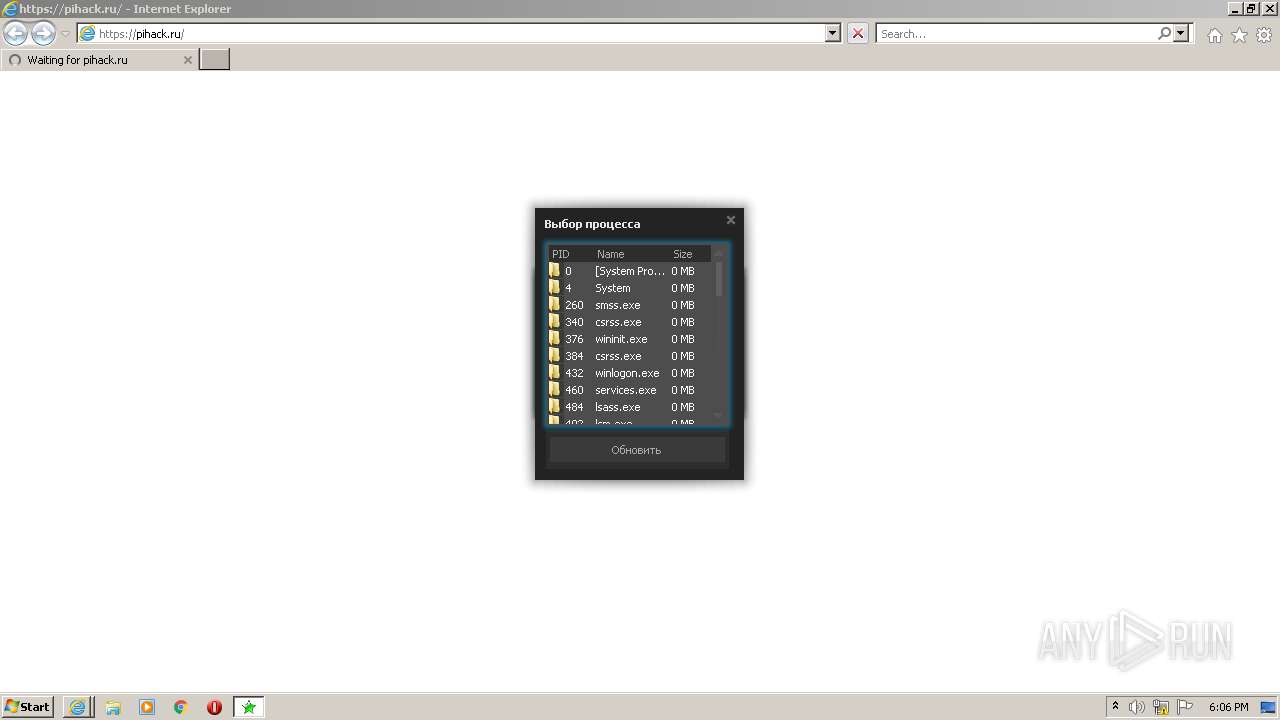
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2476 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3256 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3688 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\Супер АИМ на Контра Сити.exe" | C:\Users\admin\AppData\Local\Temp\Супер АИМ на Контра Сити.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: KS_AIM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/user/MrMehasha | C:\Program Files\Internet Explorer\iexplore.exe | Супер АИМ на Контра Сити.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
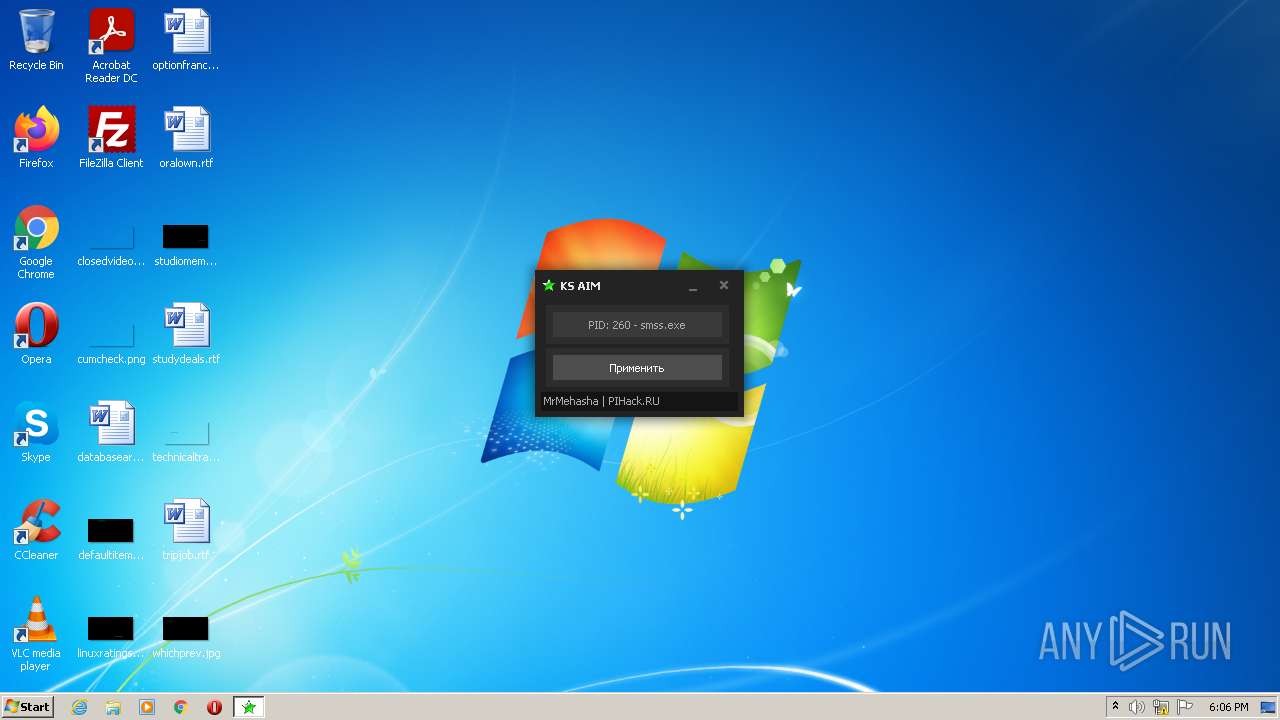
| 3628 | "C:\Users\admin\AppData\Local\Temp\Супер АИМ на Контра Сити.exe" | C:\Users\admin\AppData\Local\Temp\Супер АИМ на Контра Сити.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: KS_AIM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
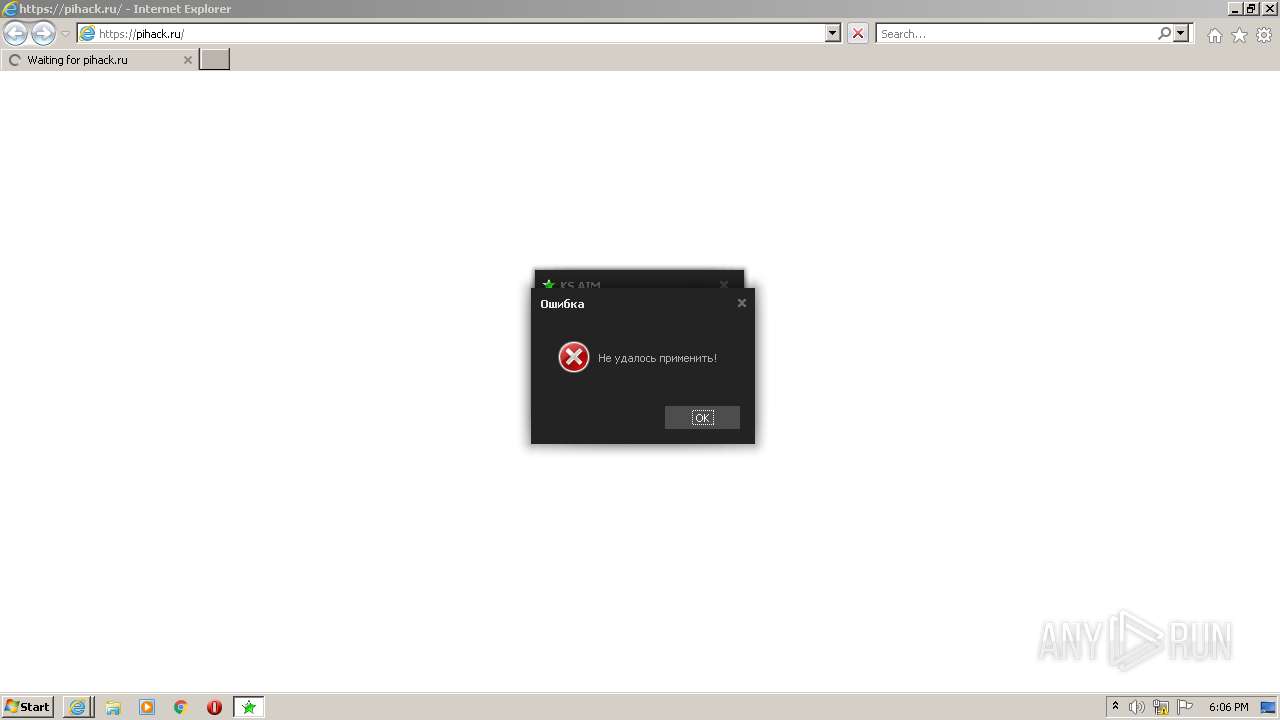
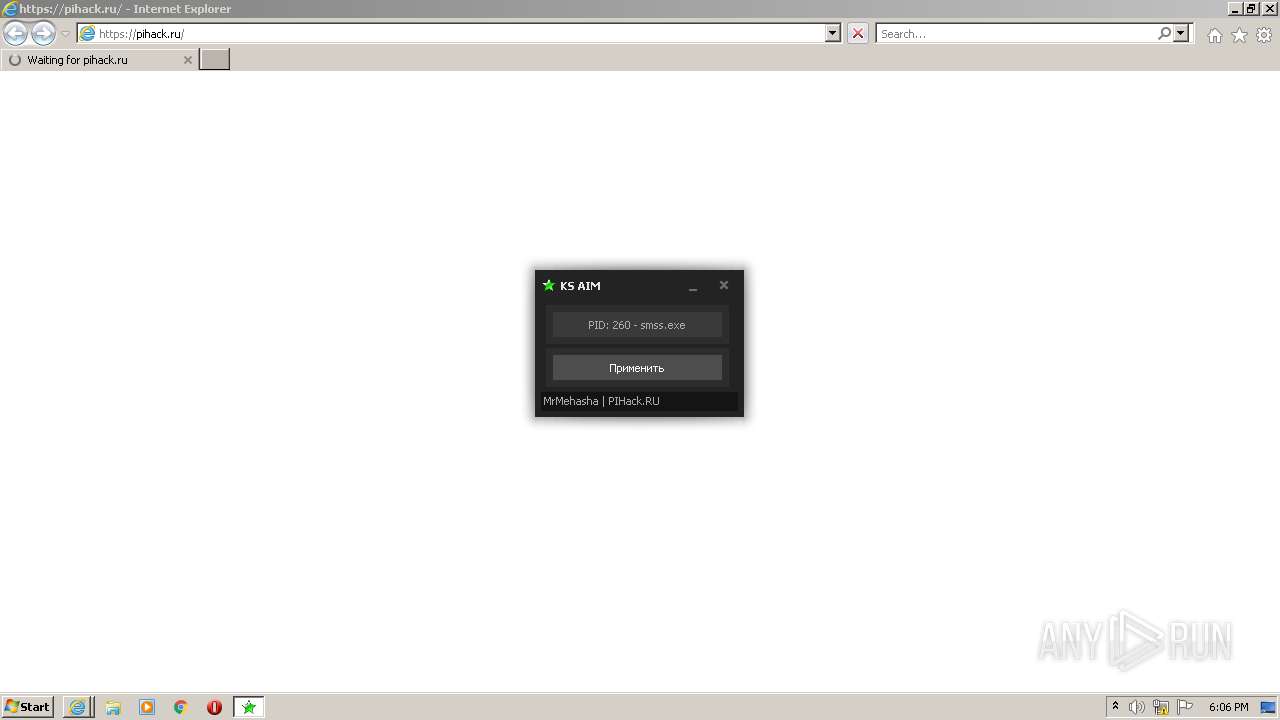
| 3688 | "C:\Program Files\Internet Explorer\iexplore.exe" https://pihack.ru/ | C:\Program Files\Internet Explorer\iexplore.exe | Супер АИМ на Контра Сити.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 748
Read events
20 509
Write events
236
Delete events
3
Modification events
| (PID) Process: | (3256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960747 | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960747 | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
2
Suspicious files
9
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3628 | Супер АИМ на Контра Сити.exe | C:\Windows\ks\System.dll | executable | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Last Active\RecoveryStore.{2A2857E4-D85F-11EC-B13F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAFE9CC93B81F2FE1.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9ABDC1064ECB12E2.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3628 | Супер АИМ на Контра Сити.exe | C:\Users\admin\AppData\Local\Temp\43959575720\KSAim.dll | executable | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9DC7A2EE69ECC348.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{21780CF3-D85F-11EC-B13F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Last Active\{2A2857E5-D85F-11EC-B13F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3256 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Last Active\{2A3B6AB4-D85F-11EC-B13F-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
17
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2588 | iexplore.exe | GET | — | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f6d808bf78d82f4a | US | — | — | whitelisted |
2588 | iexplore.exe | GET | — | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9142d926e6f1ac18 | US | — | — | whitelisted |
2588 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?969e7d0f9325e257 | US | compressed | 4.70 Kb | whitelisted |
2588 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8810623a8d743780 | US | compressed | 4.70 Kb | whitelisted |
2476 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c88ec4f211ed33e5 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | iexplore.exe | 188.114.96.10:443 | pihack.ru | Cloudflare Inc | US | malicious |
2476 | iexplore.exe | 216.58.212.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
3688 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2476 | iexplore.exe | 142.250.185.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3256 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2476 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2588 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pihack.ru |
| malicious |
www.youtube.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
Process | Message |
|---|---|
Супер АИМ на Контра Сити.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|