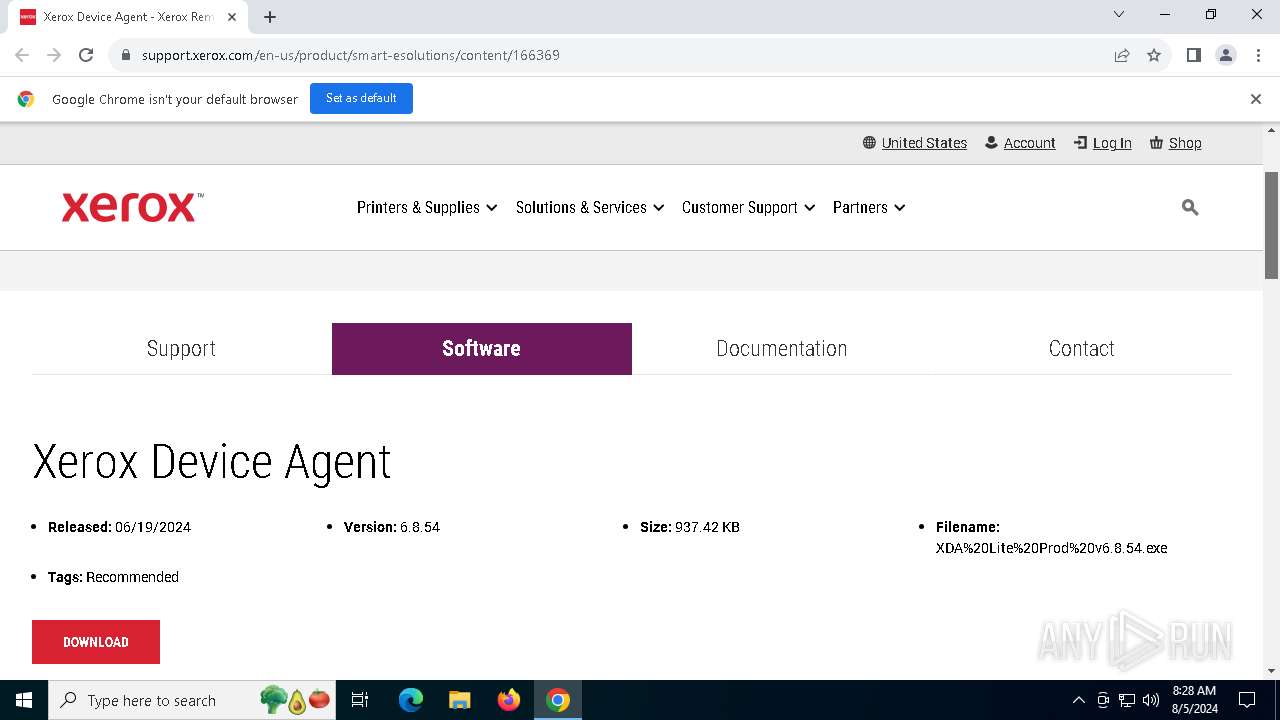
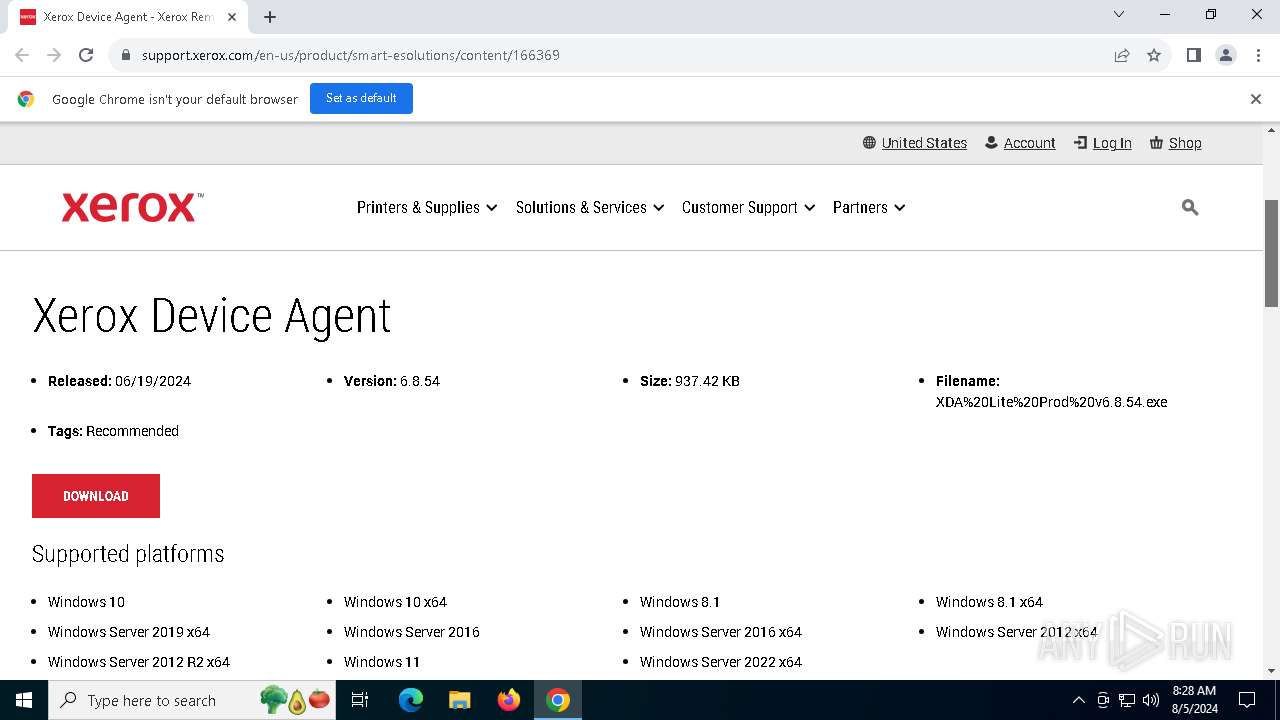
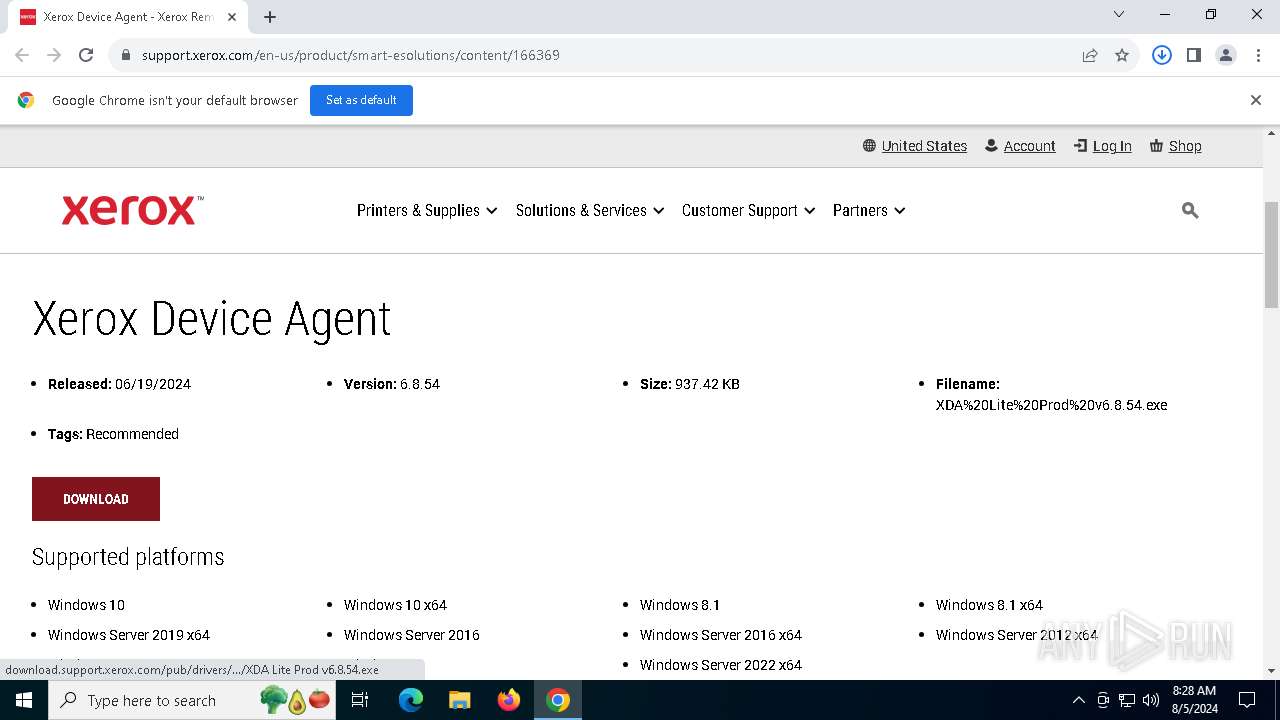
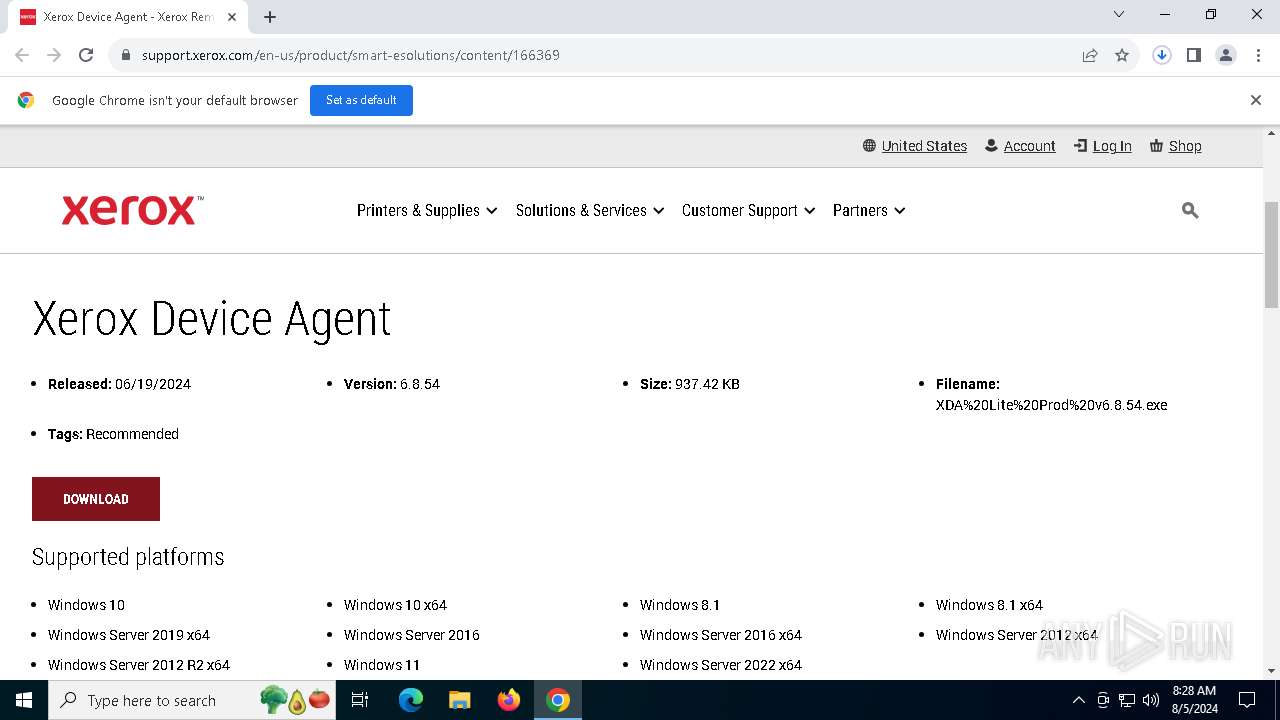
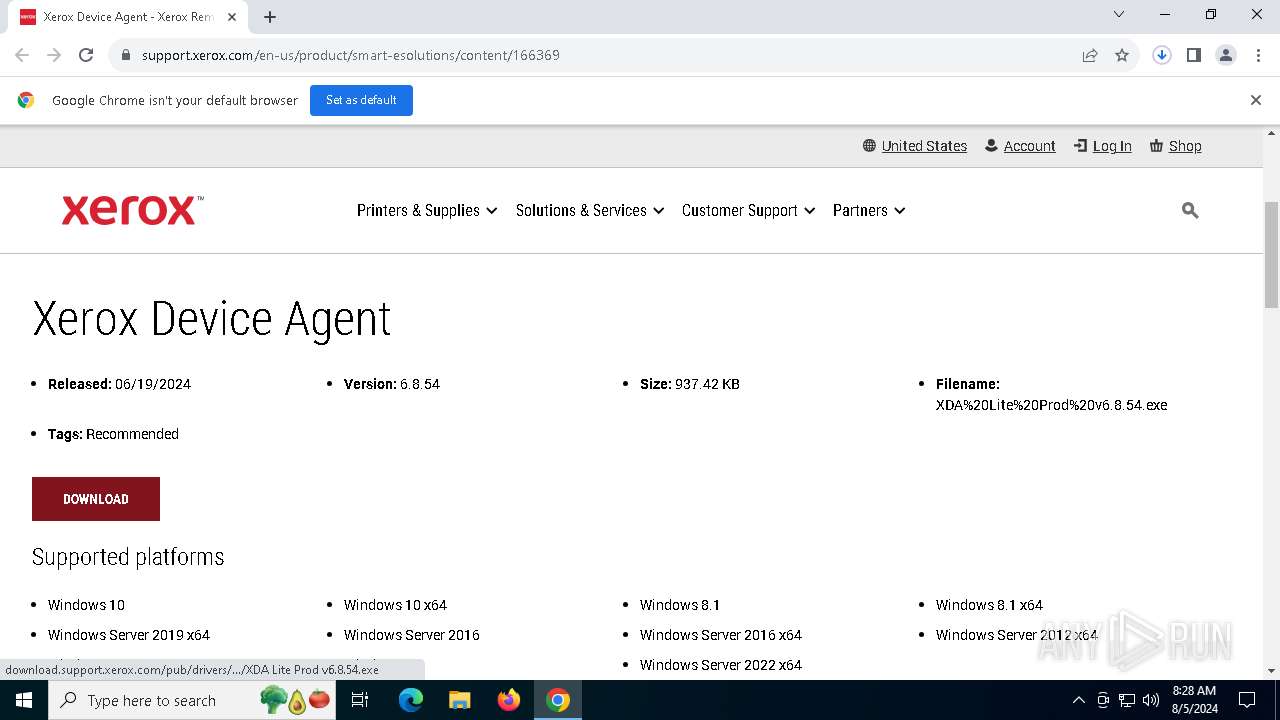
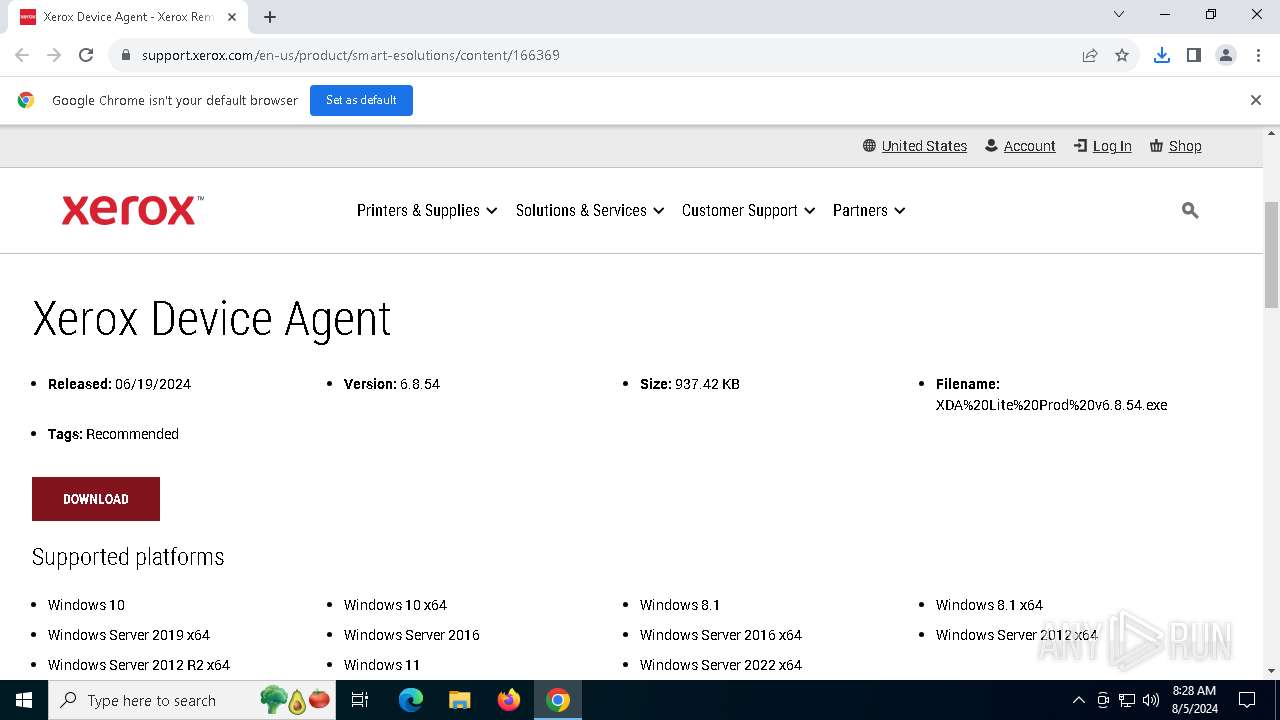
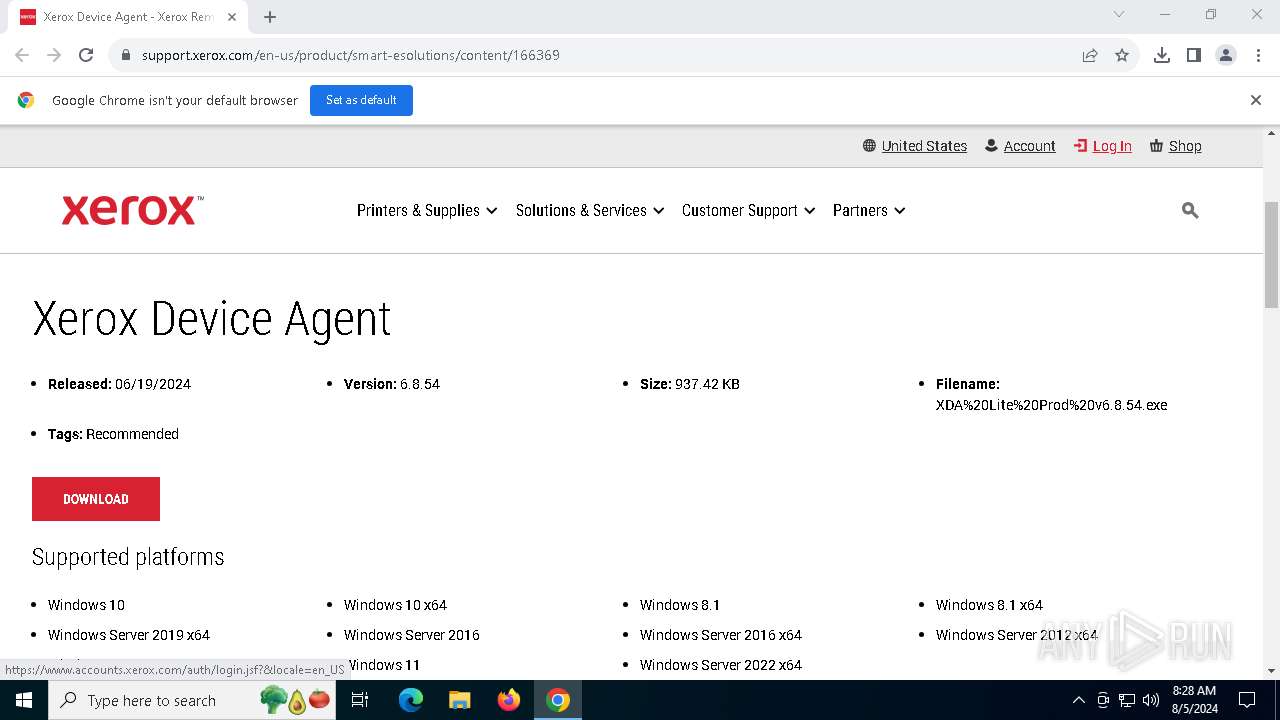
| URL: | https://www.support.xerox.com/en-us/product/smart-esolutions/content/166369 |
| Full analysis: | https://app.any.run/tasks/2c4307b8-5c87-413a-bbd3-698090f4e73d |
| Verdict: | Malicious activity |
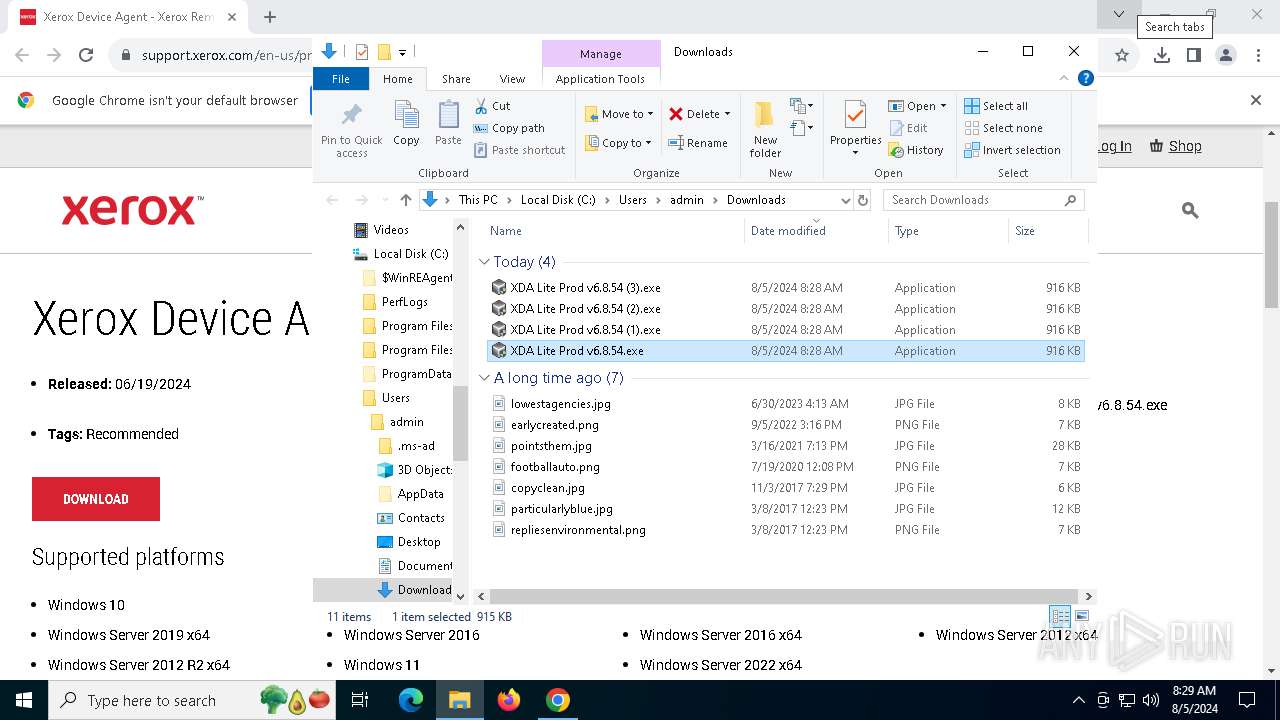
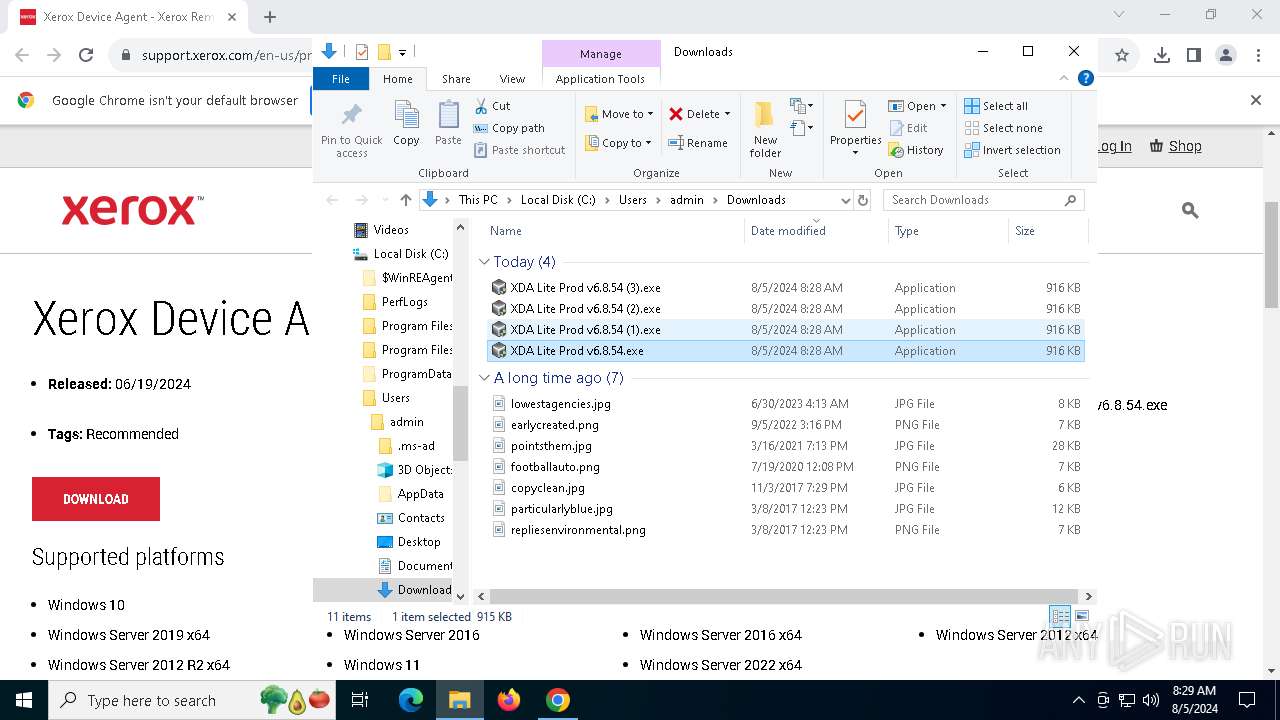
| Analysis date: | August 05, 2024, 08:27:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 6AAFD94A513A17DA2AF49F389ED6B66E |
| SHA1: | 7EC7D0F6BD208E2F0AC6348F3C8586FCF632F95E |
| SHA256: | AFE7DFFC87242BDCB6BDB8B7A82E862E9908F3DB21EA37426D7825C7A9DE5A4F |
| SSDEEP: | 3:N8DSLkRLdW8kKxRKWIE+ANJQoEALsKaQ:2OLYLc8DxRKWIHANtpj |
MALICIOUS
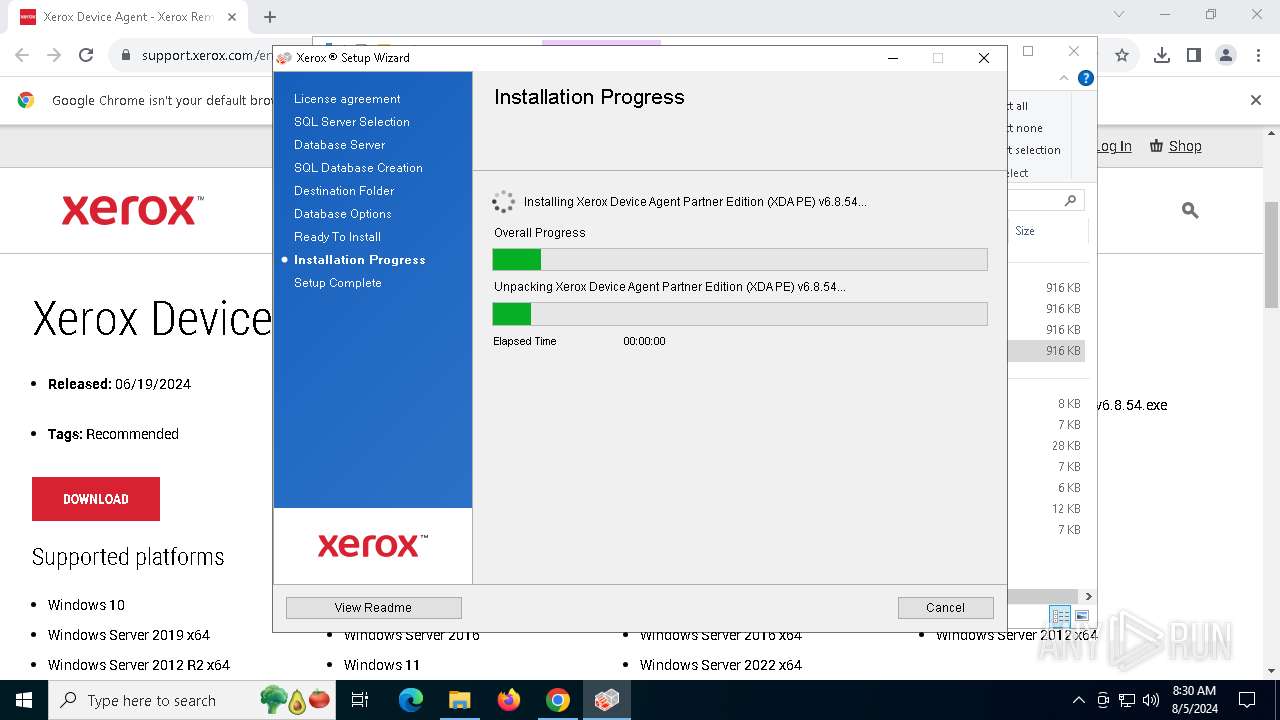
Drops the executable file immediately after the start
- Setup.exe (PID: 1132)
- msiexec.exe (PID: 4708)
- DbCreate.exe (PID: 6388)
SUSPICIOUS
Reads the date of Windows installation
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Setup.exe (PID: 1132)
- Xda.Service.exe (PID: 7508)
Reads security settings of Internet Explorer
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Setup.exe (PID: 1132)
- DbCreate.exe (PID: 6388)
- Xda.Service.exe (PID: 7508)
Executable content was dropped or overwritten
- Setup.exe (PID: 1132)
- rundll32.exe (PID: 7216)
- rundll32.exe (PID: 1748)
- rundll32.exe (PID: 8164)
- rundll32.exe (PID: 5980)
- DbCreate.exe (PID: 6388)
- rundll32.exe (PID: 3032)
The process drops C-runtime libraries
- Setup.exe (PID: 1132)
- msiexec.exe (PID: 4708)
- DbCreate.exe (PID: 6388)
Process drops legitimate windows executable
- Setup.exe (PID: 1132)
- rundll32.exe (PID: 5980)
- rundll32.exe (PID: 8164)
- rundll32.exe (PID: 1748)
- msiexec.exe (PID: 4708)
- rundll32.exe (PID: 7216)
- DbCreate.exe (PID: 6388)
- rundll32.exe (PID: 3032)
Checks Windows Trust Settings
- msiexec.exe (PID: 4708)
- DbCreate.exe (PID: 6388)
- Xda.Service.exe (PID: 7508)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4708)
The process creates files with name similar to system file names
- msiexec.exe (PID: 4708)
Executes as Windows Service
- Xda.Service.exe (PID: 7508)
- Xerox.XDAMonitorService.exe (PID: 1184)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- Xda.Service.exe (PID: 7508)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Xda.Service.exe (PID: 7508)
Executing commands from a ".bat" file
- rundll32.exe (PID: 8164)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 8164)
INFO
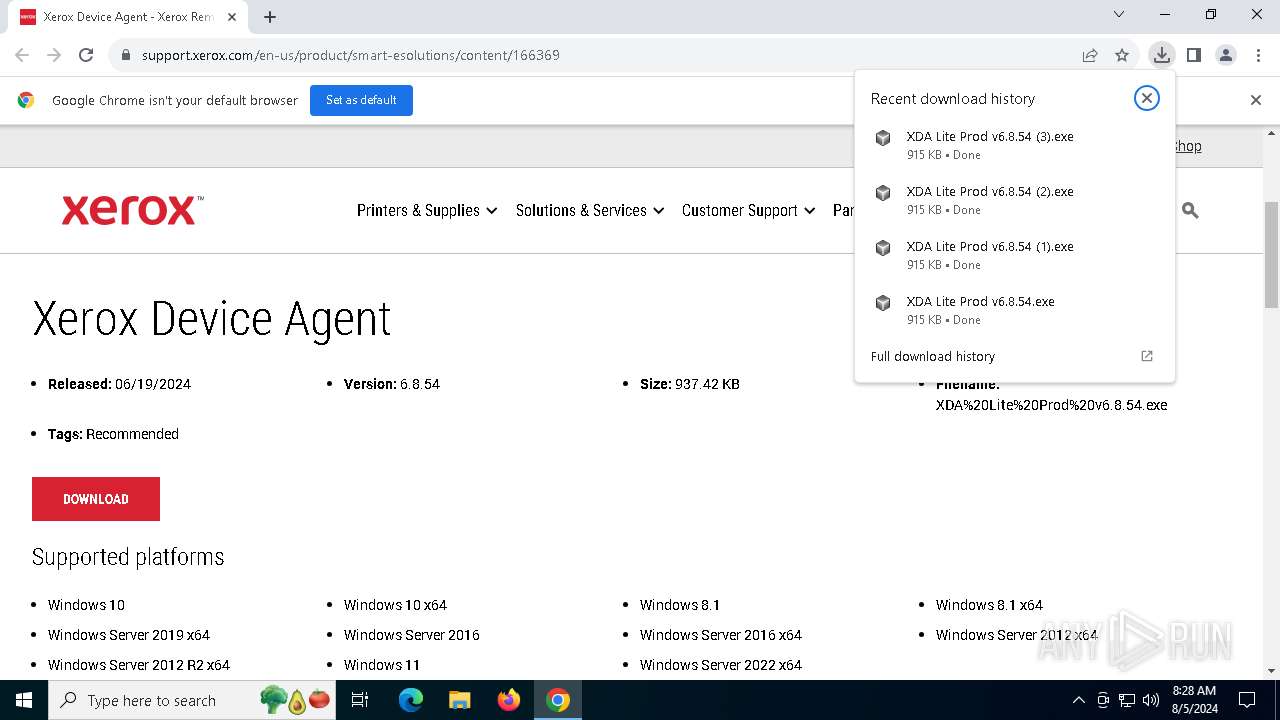
The process uses the downloaded file
- chrome.exe (PID: 7792)
- chrome.exe (PID: 6232)
- chrome.exe (PID: 5984)
- chrome.exe (PID: 8044)
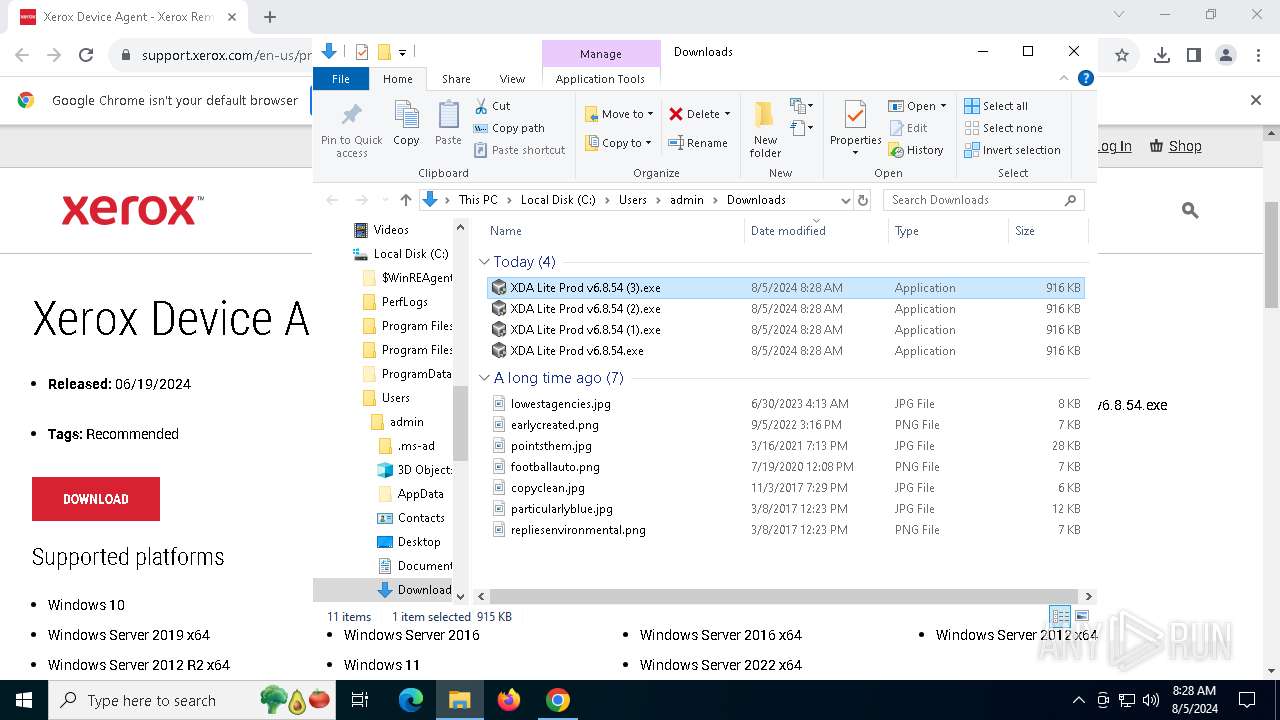
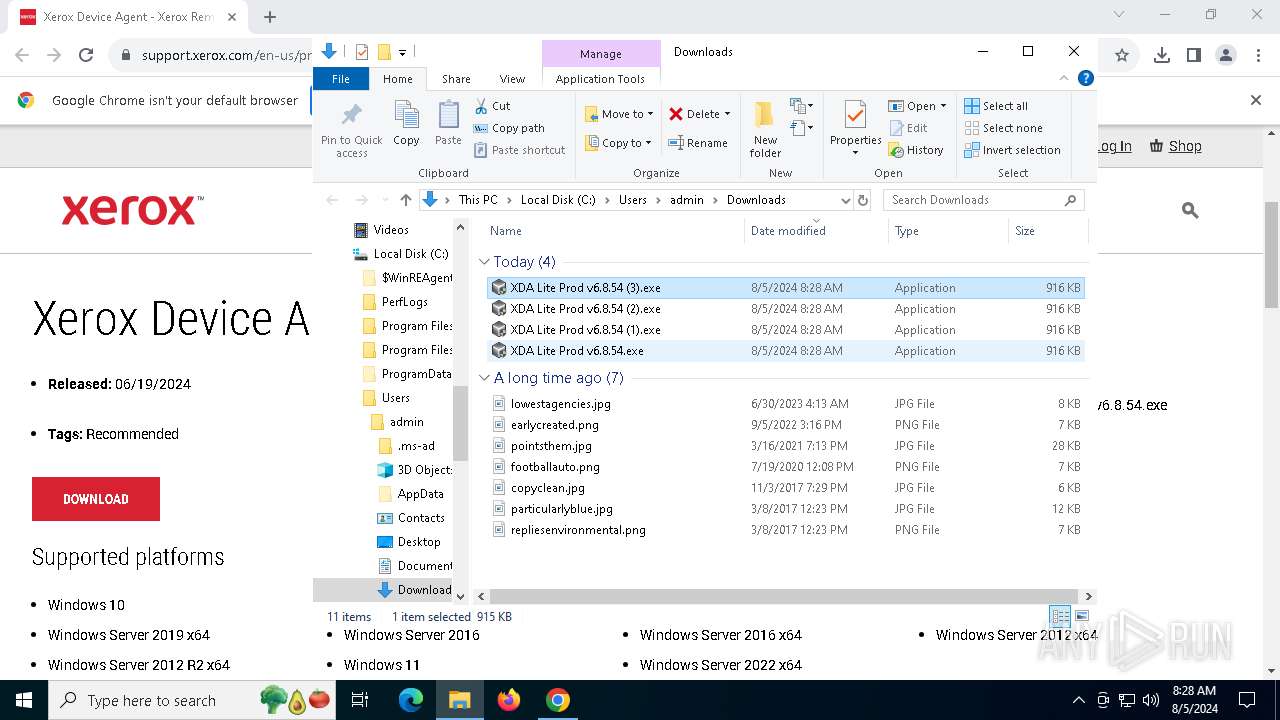
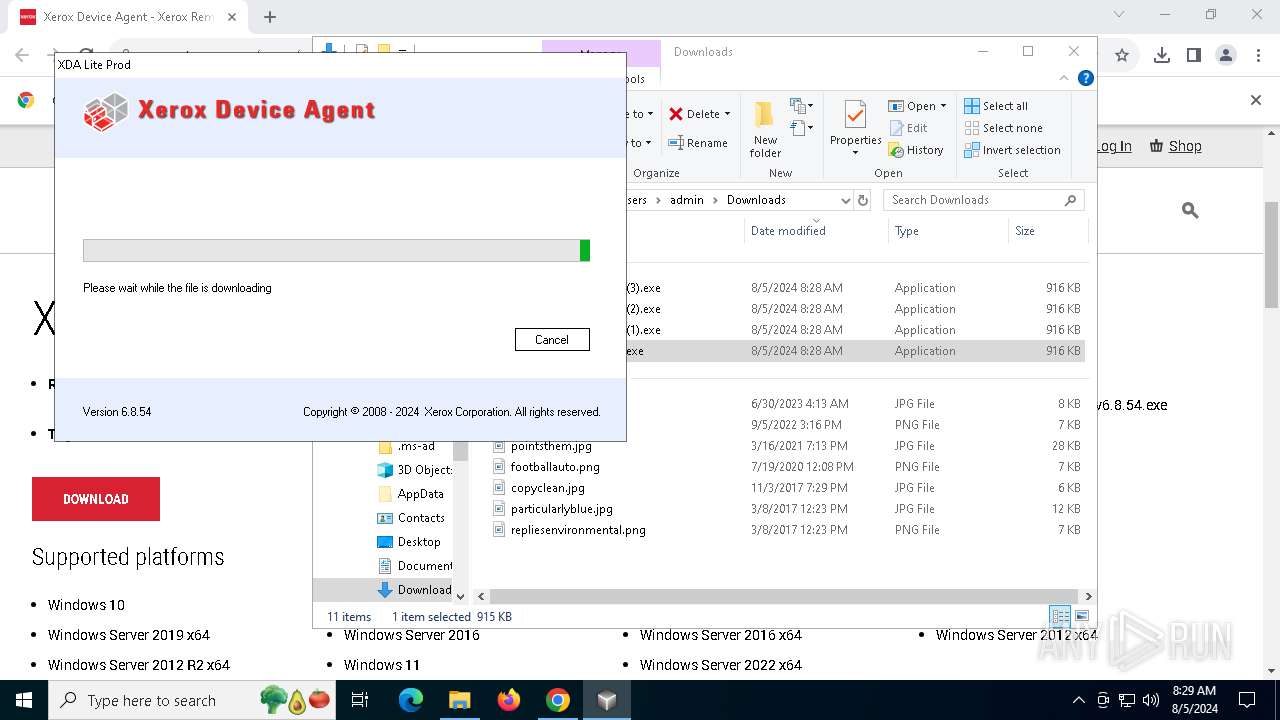
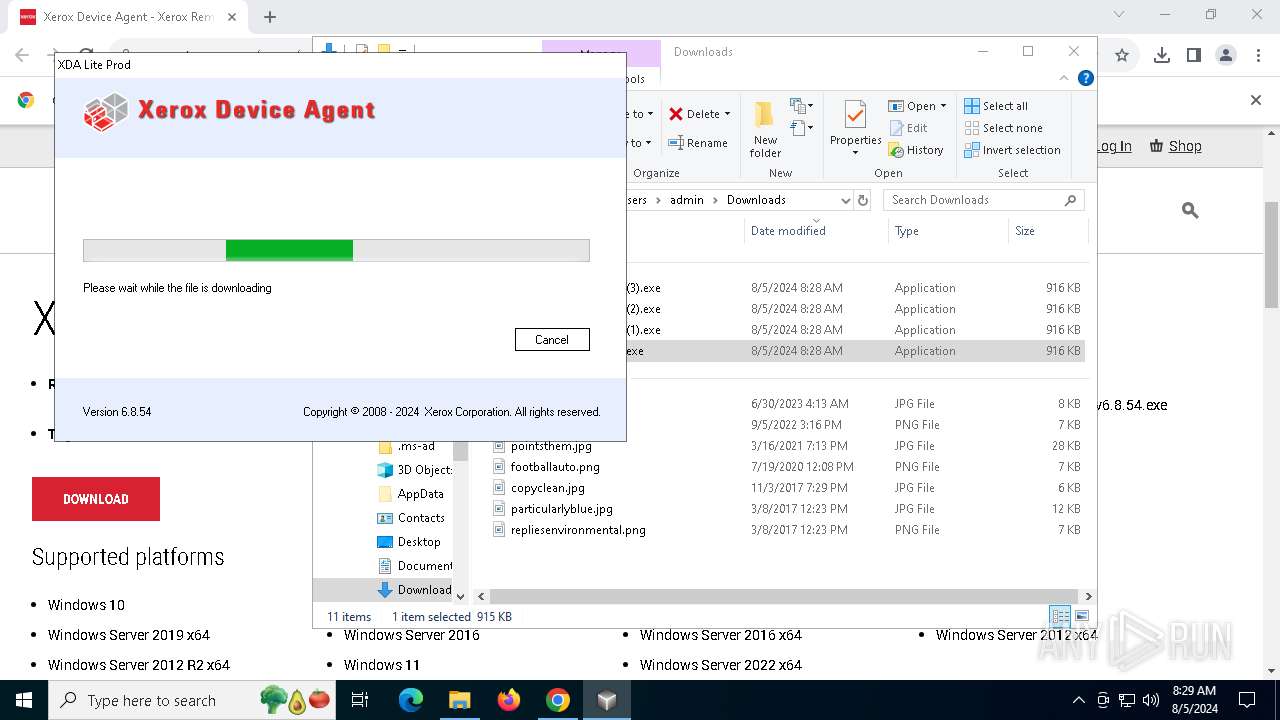
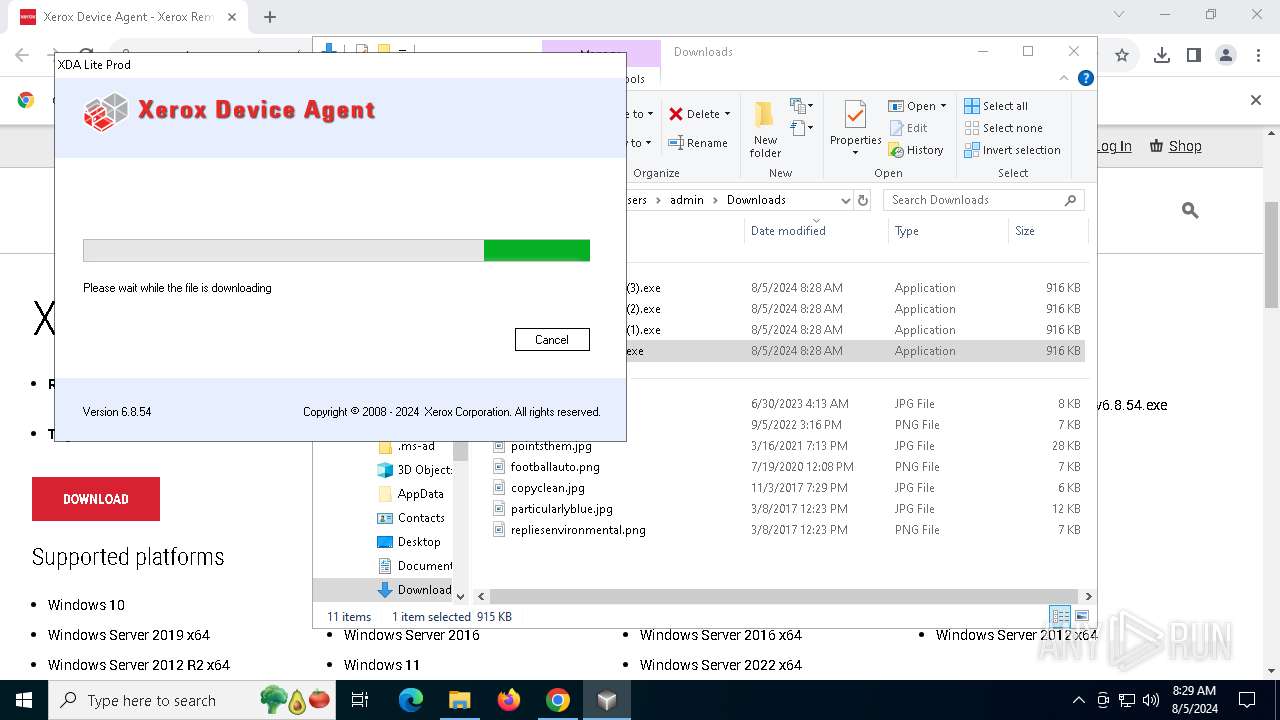
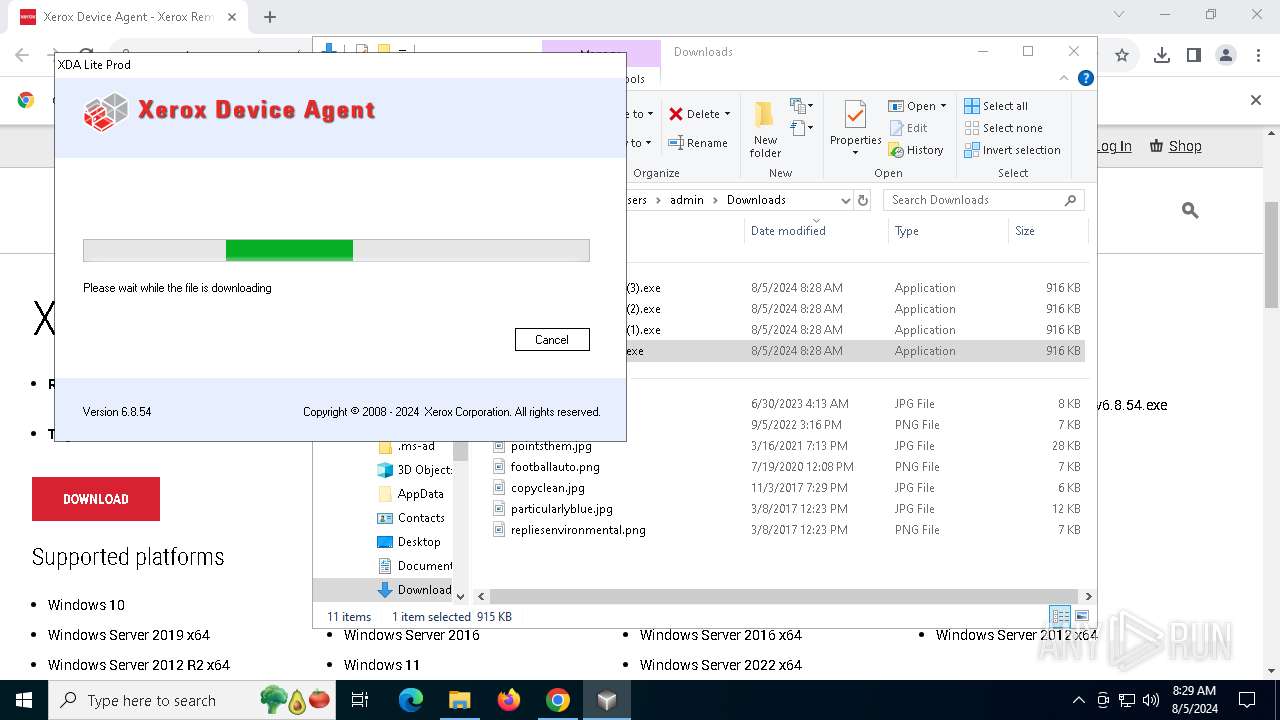
Manual execution by a user
- XDA Lite Prod v6.8.54.exe (PID: 8112)
- XDA Lite Prod v6.8.54.exe (PID: 3104)
Executable content was dropped or overwritten
- chrome.exe (PID: 6416)
- msiexec.exe (PID: 4708)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6416)
Drops the executable file immediately after the start
- chrome.exe (PID: 6416)
- rundll32.exe (PID: 5980)
- rundll32.exe (PID: 1748)
- rundll32.exe (PID: 8164)
- rundll32.exe (PID: 7216)
- rundll32.exe (PID: 3032)
Application launched itself
- chrome.exe (PID: 6416)
Reads the computer name
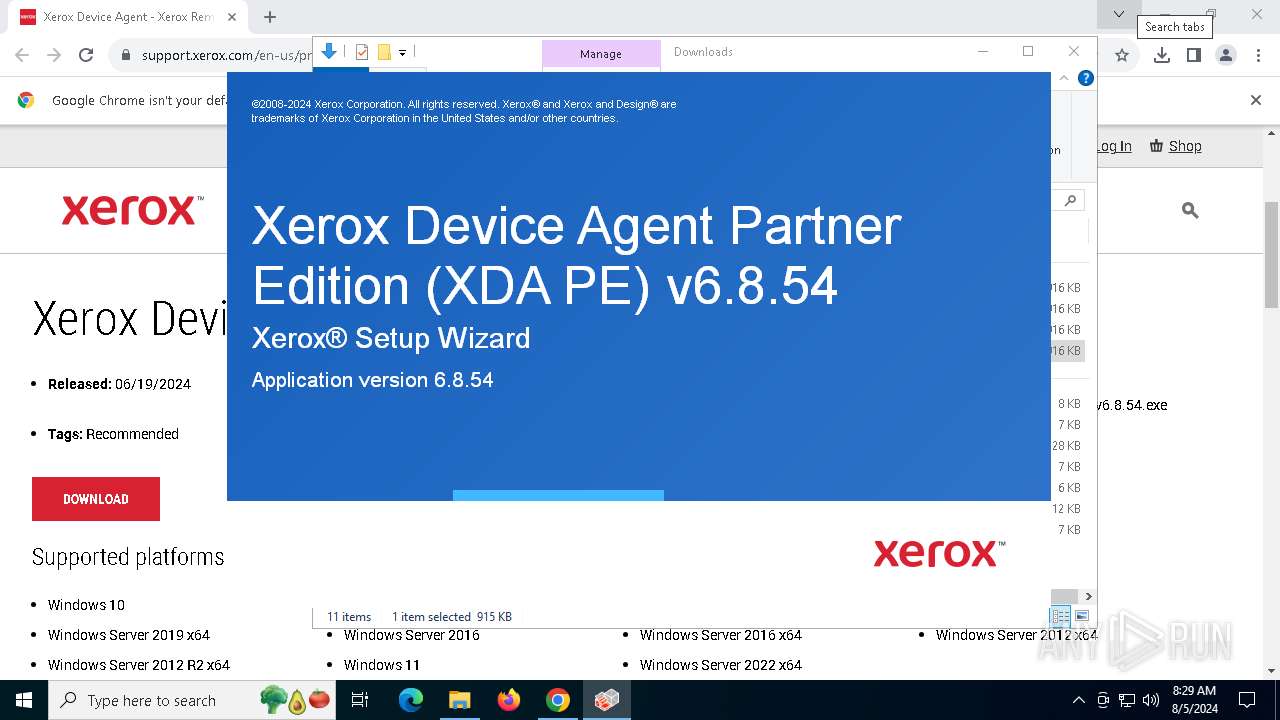
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Xerox Device Agent Partner Edition (XDA PE) v6.8.54.exe (PID: 7992)
- Setup.exe (PID: 1132)
- Setup.exe (PID: 3508)
- dbVersionDetect.exe (PID: 6156)
- msiexec.exe (PID: 4708)
- msiexec.exe (PID: 1452)
- DbCreate.exe (PID: 6388)
- BrandingTask.exe (PID: 6656)
- Xda.Service.exe (PID: 7508)
- Xerox.XDAMonitorService.exe (PID: 1184)
Reads the machine GUID from the registry
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Setup.exe (PID: 1132)
- Setup.exe (PID: 3508)
- dbVersionDetect.exe (PID: 6156)
- msiexec.exe (PID: 4708)
- DbCreate.exe (PID: 6388)
- BrandingTask.exe (PID: 6656)
- Xda.Service.exe (PID: 7508)
- Xerox.XDAMonitorService.exe (PID: 1184)
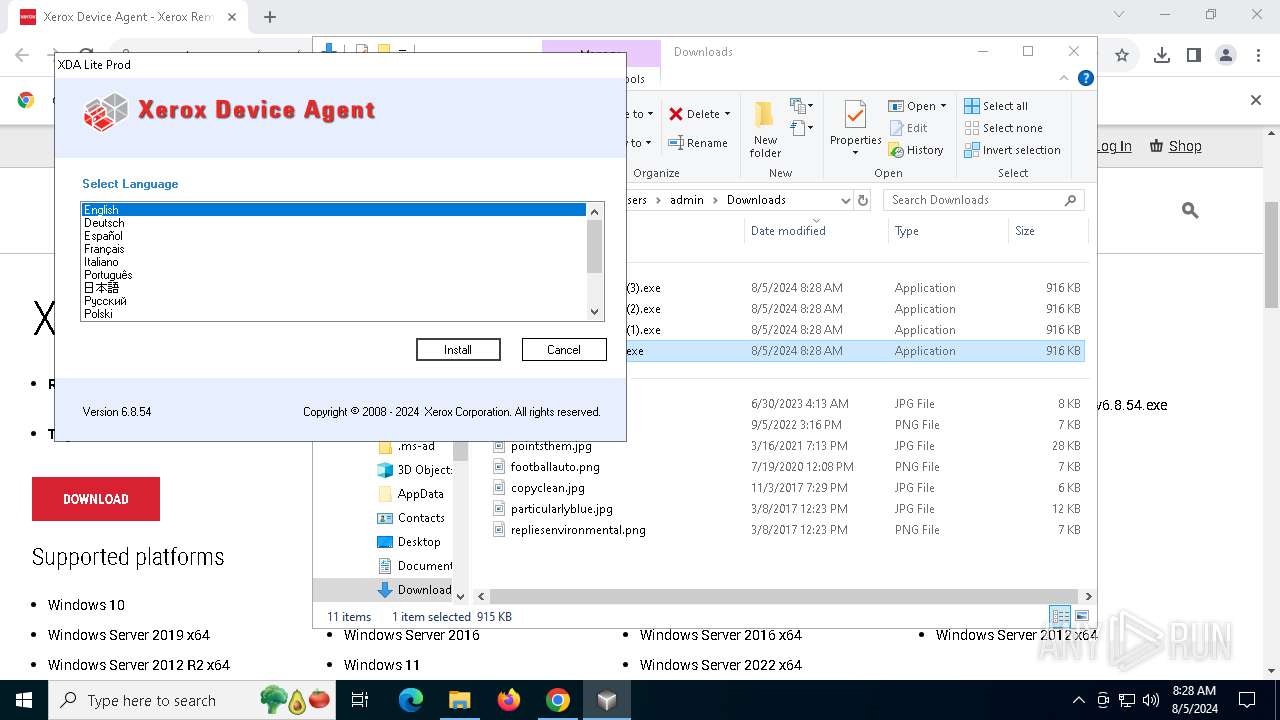
Checks supported languages
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Xerox Device Agent Partner Edition (XDA PE) v6.8.54.exe (PID: 7992)
- Setup.exe (PID: 3508)
- Setup.exe (PID: 1132)
- dbVersionDetect.exe (PID: 6156)
- msiexec.exe (PID: 4708)
- msiexec.exe (PID: 1452)
- BrandingTask.exe (PID: 6656)
- Xda.Service.exe (PID: 7508)
- DbCreate.exe (PID: 6388)
- Xerox.XDAMonitorService.exe (PID: 1184)
Reads Environment values
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Xda.Service.exe (PID: 7508)
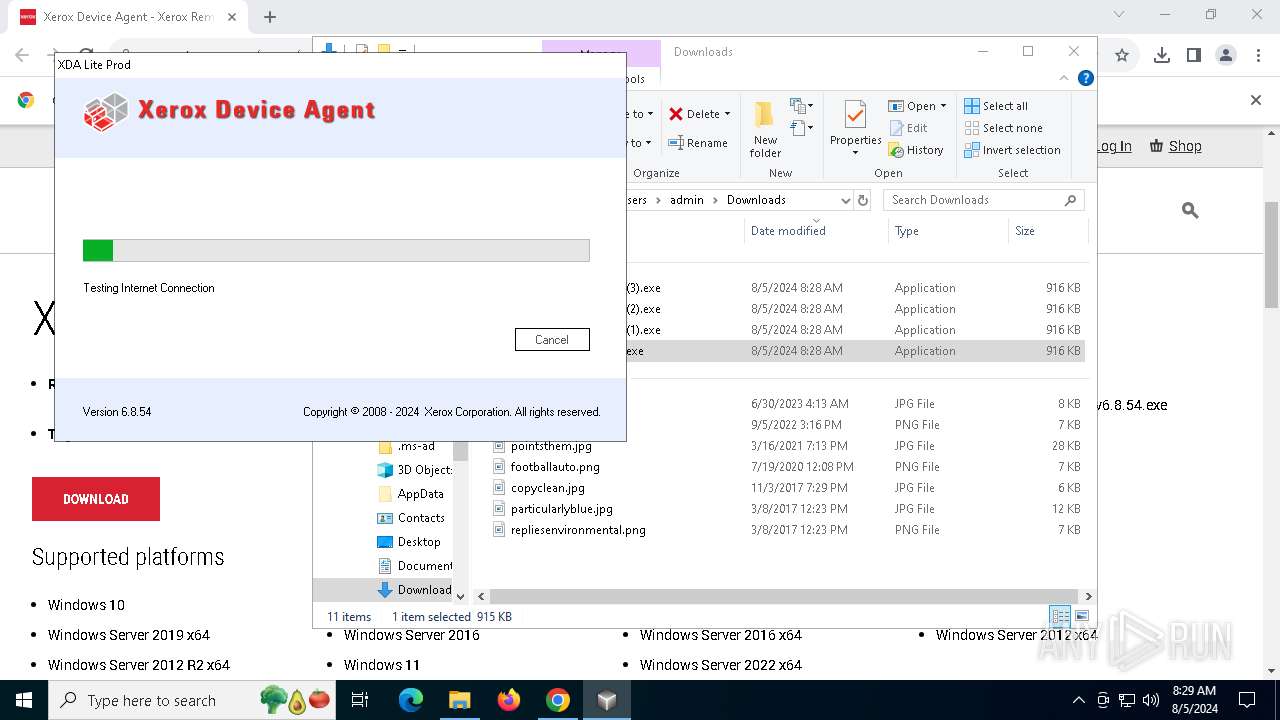
Checks proxy server information
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- DbCreate.exe (PID: 6388)
- Xda.Service.exe (PID: 7508)
Disables trace logs
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Xda.Service.exe (PID: 7508)
Reads the software policy settings
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- msiexec.exe (PID: 4708)
- DbCreate.exe (PID: 6388)
- Xda.Service.exe (PID: 7508)
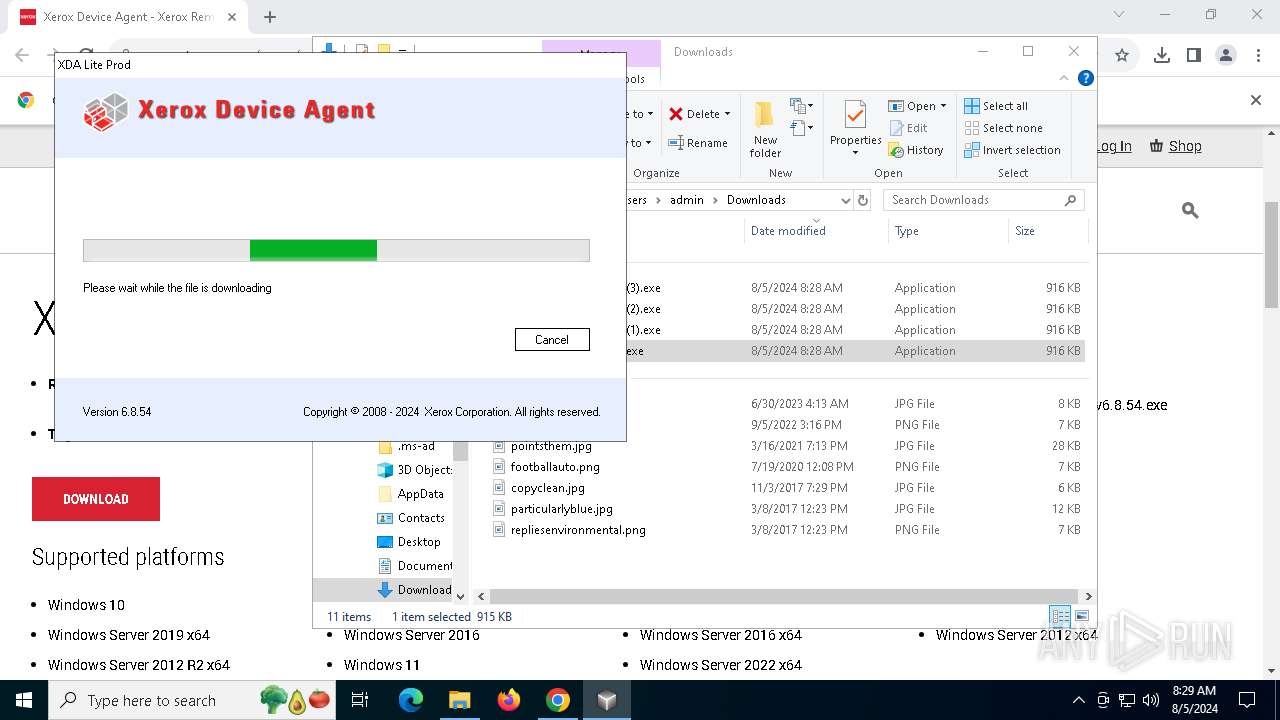
Create files in a temporary directory
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Xerox Device Agent Partner Edition (XDA PE) v6.8.54.exe (PID: 7992)
- Setup.exe (PID: 1132)
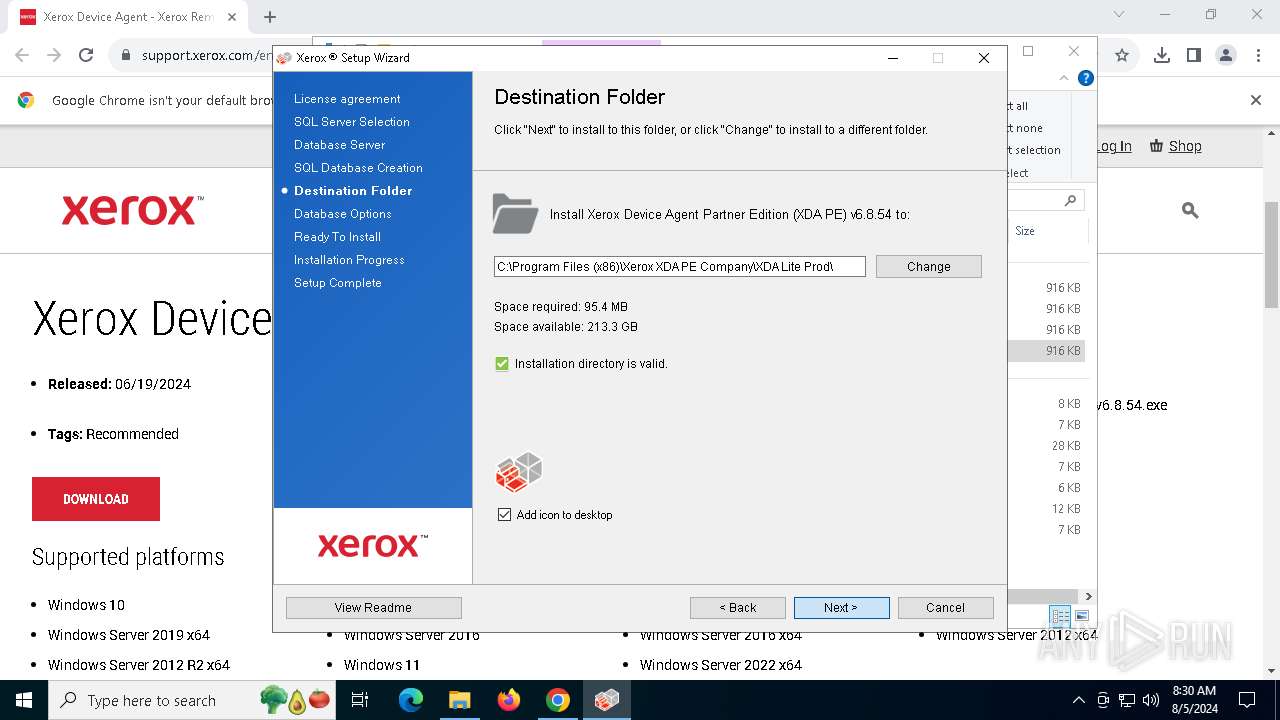
Creates files in the program directory
- Xerox Device Agent Partner Edition (XDA PE) v6.8.54.exe (PID: 7992)
- Setup.exe (PID: 1132)
- rundll32.exe (PID: 7216)
- rundll32.exe (PID: 1748)
- rundll32.exe (PID: 8164)
- DbCreate.exe (PID: 6388)
- BrandingTask.exe (PID: 6656)
- rundll32.exe (PID: 3032)
- Xda.Service.exe (PID: 7508)
Process checks computer location settings
- XDA Lite Prod v6.8.54.exe (PID: 3104)
- Setup.exe (PID: 1132)
Creates files or folders in the user directory
- msiexec.exe (PID: 4708)
- DbCreate.exe (PID: 6388)
Creates a software uninstall entry
- msiexec.exe (PID: 4708)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 8164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
197
Monitored processes
62
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=5740 --field-trial-handle=1856,i,15182412255722565825,15142150571170630518,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6088 --field-trial-handle=1856,i,15182412255722565825,15142150571170630518,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1132 | /v"XMLLocation=\"C:\Users\admin\AppData\Local\Temp\DSC\xrs.val\"" SKIPLC=true /L1033 LOG="C:\ProgramData\Xerox\InstallLogs\Xerox_XDA_6.8.54_05_08_2024_1722846578.txt" /bootstrapped | C:\Users\admin\AppData\Local\Temp\2DFC52D9-9DB5-45BC-8607-ED80F0B13881\Setup.exe | Xerox Device Agent Partner Edition (XDA PE) v6.8.54.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Controller Version: 1.0.0.0 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Xerox XDA PE Company\XDA Lite Prod\bin\Xerox.XDAMonitorService.exe" | C:\Program Files (x86)\Xerox XDA PE Company\XDA Lite Prod\bin\Xerox.XDAMonitorService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: XDAMonitorService Version: 1.0.0.0 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4824 --field-trial-handle=1856,i,15182412255722565825,15142150571170630518,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1452 | C:\Windows\syswow64\MsiExec.exe -Embedding 93E0AB3A99244386D9AAEDF40AF76EEF | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5732 --field-trial-handle=1856,i,15182412255722565825,15142150571170630518,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1748 | rundll32.exe "C:\WINDOWS\Installer\MSI454B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1066375 14 CustomAction!CustomActionsShared.ExecuteSequence.SilentExecuteValidations | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name = XDA-Service program = "C:\Program Files (x86)\Xerox XDA PE Company\XDA Lite Prod\bin\Xda.Service.exe" enable = yes profile = any dir = in action = allow protocol = UDP localport = 162 | C:\Windows\System32\netsh.exe | — | Xda.Service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
74 943
Read events
74 488
Write events
428
Delete events
27
Modification events
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
344
Suspicious files
198
Text files
158
Unknown types
286
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5530.TMP | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5540.TMP | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 6416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
119
DNS requests
92
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2636 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6644 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6856 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | — | — | whitelisted |
4208 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
6704 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
4208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
4208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
4208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1984 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 95.100.146.34:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
6416 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2636 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.support.xerox.com |
| whitelisted |
accounts.google.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
framework-assets.external.xerox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6856 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6856 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |