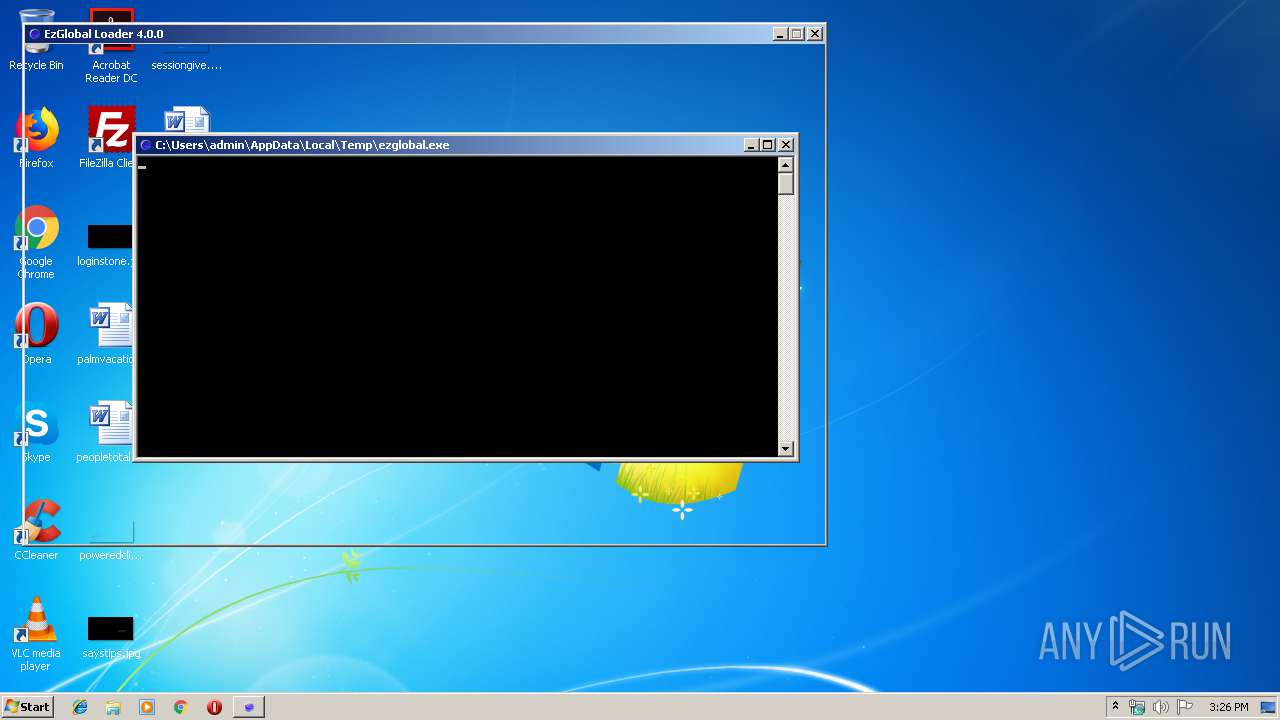
| download: | ezglobal.exe |
| Full analysis: | https://app.any.run/tasks/8e8229e8-812b-4a96-991e-60ef955a48f4 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 14:26:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 3E24F44C52D64E46D87CC5F52ADDFDD9 |
| SHA1: | 6A5BA233EE0FA5CA96014157B0F64C5DE3C96D9E |
| SHA256: | AFE7366FBD1A39E5EED38527BFC1737EC1239969B527B89C0ABE21C44E289482 |
| SSDEEP: | 393216:U6t9ywCteW6EW9VMg1Ox4EkJQlKt0syp9pm:3Yte7MqONU0sjyp9Q |
MALICIOUS
Loads dropped or rewritten executable
- ezglobal.exe (PID: 1296)
SUSPICIOUS
Executable content was dropped or overwritten
- ezglobal.exe (PID: 3756)
Loads Python modules
- ezglobal.exe (PID: 1296)
Application launched itself
- ezglobal.exe (PID: 3756)
Uses WMIC.EXE to obtain a system information
- ezglobal.exe (PID: 1296)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 1788)
- cmd.exe (PID: 392)
- cmd.exe (PID: 1972)
- cmd.exe (PID: 836)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 2468)
- cmd.exe (PID: 788)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 3300)
- cmd.exe (PID: 492)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 1992)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 1244)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 1036)
- cmd.exe (PID: 2168)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 3472)
- cmd.exe (PID: 2452)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 436)
- cmd.exe (PID: 1976)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 996)
- cmd.exe (PID: 2920)
- cmd.exe (PID: 436)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 820)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 2304)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 3048)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 1732)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 1732)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 3468)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 1528)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 3880)
- cmd.exe (PID: 532)
- cmd.exe (PID: 1404)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3012)
- cmd.exe (PID: 516)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 3128)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3308)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3308)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 324)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 3428)
- cmd.exe (PID: 2504)
- cmd.exe (PID: 3280)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 1048)
- cmd.exe (PID: 2712)
Starts CMD.EXE for commands execution
- ezglobal.exe (PID: 1296)
INFO
Dropped object may contain Bitcoin addresses
- ezglobal.exe (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:09 16:22:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 252928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x790a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jul-2019 14:22:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:22:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F3B4 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66635 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10031 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86637 |
.rsrc | 0x0003D000 | 0x000305E0 | 0x00030600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.18494 |
.reloc | 0x0006E000 | 0x000017D0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 3.03466 | 132 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.29735 | 1027 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.17504 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.83681 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.42643 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.20007 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.08165 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 2.86494 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 2.64041 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 7.97612 | 34453 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
207
Monitored processes
171
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | wmic process where "name='csgo.exe'" get Processid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | C:\Windows\system32\cmd.exe /c "wmic process where "name='csgo.exe'" get Processid" | C:\Windows\system32\cmd.exe | — | ezglobal.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 328 | wmic process where "name='csgo.exe'" get Processid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | C:\Windows\system32\cmd.exe /c "wmic process where "name='csgo.exe'" get Processid" | C:\Windows\system32\cmd.exe | — | ezglobal.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 392 | wmic process where "name='csgo.exe'" get Processid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | C:\Windows\system32\cmd.exe /c "wmic process where "name='csgo.exe'" get Processid" | C:\Windows\system32\cmd.exe | — | ezglobal.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 436 | C:\Windows\system32\cmd.exe /c "wmic process where "name='csgo.exe'" get Processid" | C:\Windows\system32\cmd.exe | — | ezglobal.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 460 | wmic process where "name='csgo.exe'" get Processid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | C:\Windows\system32\cmd.exe /c "wmic process where "name='csgo.exe'" get Processid" | C:\Windows\system32\cmd.exe | — | ezglobal.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 504 | wmic process where "name='csgo.exe'" get Processid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 812
Read events
2 812
Write events
0
Delete events
0
Modification events
Executable files
36
Suspicious files
1
Text files
921
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\PIL\_imaging.cp37-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\PIL\_imagingtk.cp37-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\PIL\_webp.cp37-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_ctypes.pyd | executable | |
MD5:9DB2D9962CBD754E91B40F91CBC49542 | SHA256:6A6DF7D77B7A5552D8443BD1B98F681AD2E6B5A8ACF7ADE542DD369BEAB7E439 | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_socket.pyd | executable | |
MD5:A4BD8E0C0597A22C3F0601FE798668AA | SHA256:96B0A3CFC16E215F0EF5D1E206F0137B4255005052720E91A58BC98CDE8C898E | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_cffi_backend.cp37-win32.pyd | executable | |
MD5:9C57FA6BD22B8DCA861E767384E428E4 | SHA256:2DBA673A4701D68FB85054F64A22C4C249C4FB8C7BA0B8CAE8383BBCC9F8D762 | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_bz2.pyd | executable | |
MD5:FF5AC8FB724EDB1635E2AD985F98EE5B | SHA256:B94F64FCB49F40682ED794FA1940A1DC0C8A28F24A1768D3BFE774CF75F59B62 | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_decimal.pyd | executable | |
MD5:E4292AD50769F592F34BC63F62A5E428 | SHA256:0240F15B44E2D3E37EBEFBB221D3D6017BE5EF99806EC4E36C3521F284CB8043 | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_lzma.pyd | executable | |
MD5:65880A33015AF2030A08987924CA737B | SHA256:A71366B95D89D1539A6EE751D48A969C1BCA1AA75116424CC5F905F32A625EEA | |||
| 3756 | ezglobal.exe | C:\Users\admin\AppData\Local\Temp\_MEI37562\_tkinter.pyd | executable | |
MD5:E46970E8EB0061DF01347A3723140E77 | SHA256:71C4545CEE713F26CF2F910A08340DD519C4713B8416479F74B0B9E2683C85D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1296 | ezglobal.exe | GET | — | 79.98.129.62:80 | http://ezglobalyazilim.com/xloader_res/lsback2.jpg | TR | — | — | malicious |
1296 | ezglobal.exe | POST | 200 | 79.98.129.62:80 | http://ezglobalyazilim.com/apiv3.php | TR | text | 8.39 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1296 | ezglobal.exe | 79.98.129.62:80 | ezglobalyazilim.com | Radore Veri Merkezi Hizmetleri A.S. | TR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ezglobalyazilim.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | ezglobal.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1296 | ezglobal.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1296 | ezglobal.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
2 ETPRO signatures available at the full report