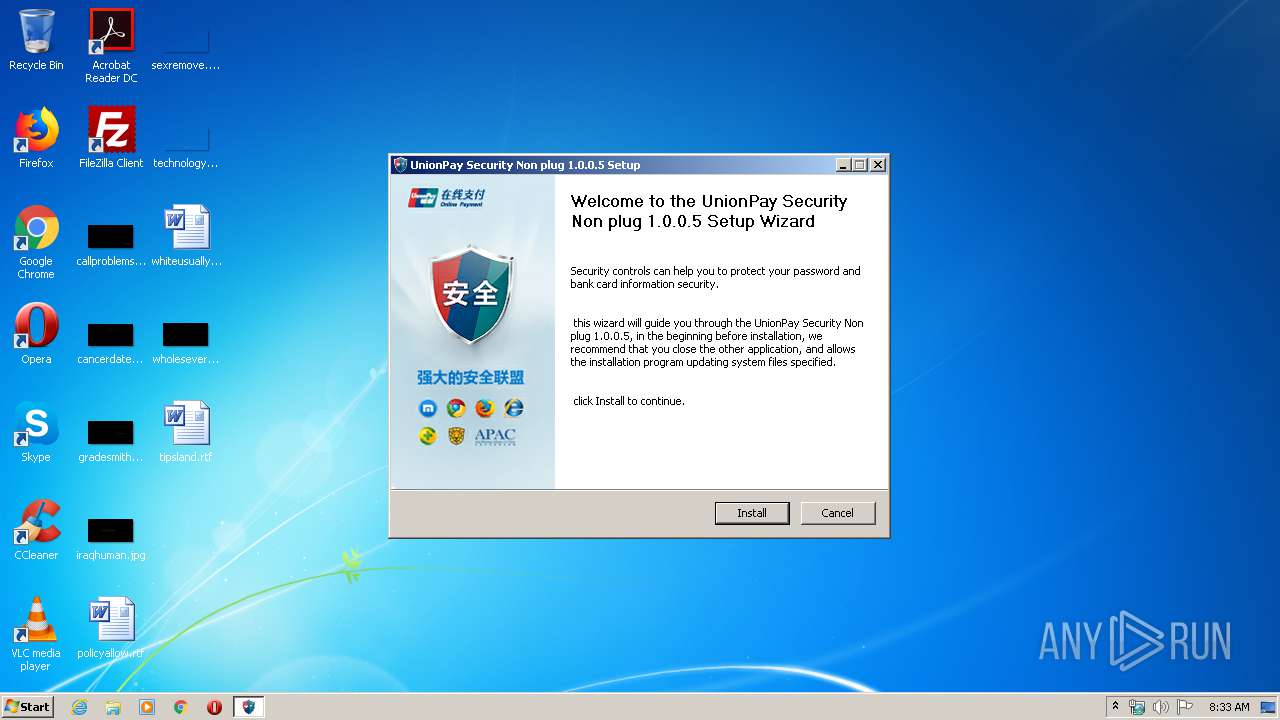
| File name: | UPEditorEdge.exe |
| Full analysis: | https://app.any.run/tasks/38c06475-bb1e-41a5-96fd-3938ce18deba |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2020, 07:32:44 |
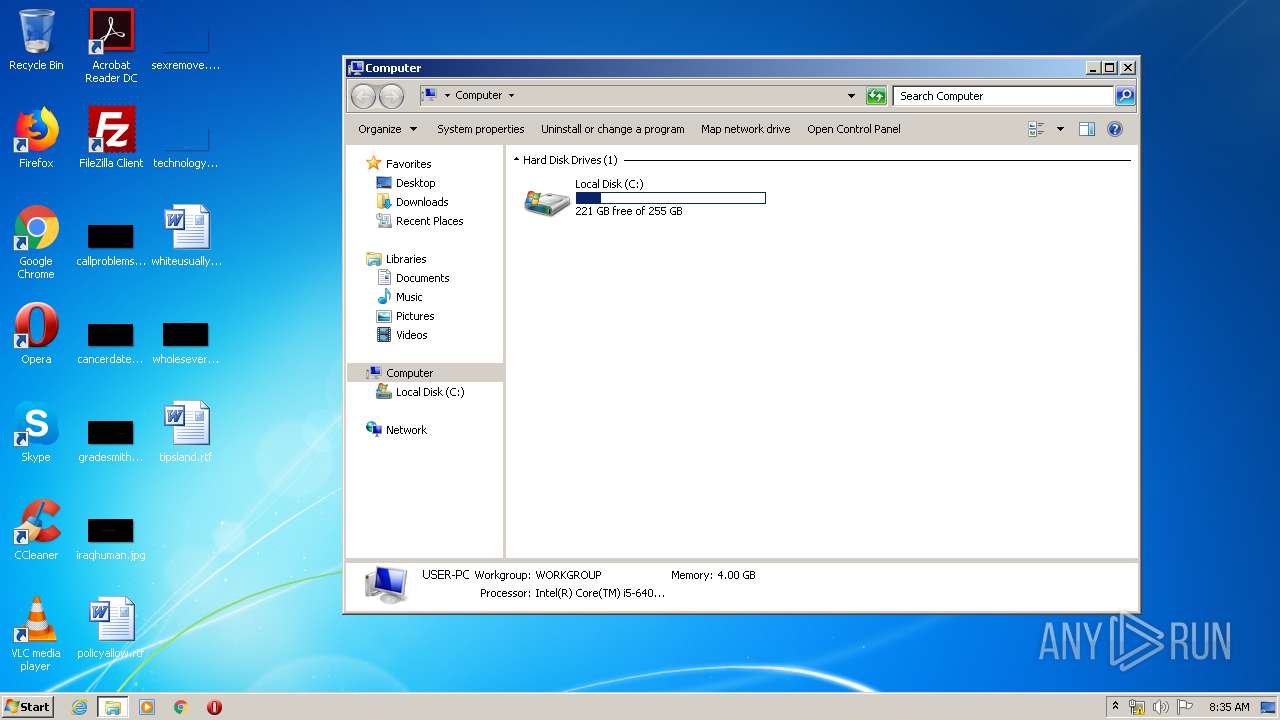
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 5421FABCB53283BF1AA2A423B131218C |
| SHA1: | 4D14B6F5ADA28D3046D7270B10E39CB634CAA0D5 |
| SHA256: | AFDDEE5824A54CFE06F00F5D11BDEB5918E3C1E713E52CF8603B2097510553E7 |
| SSDEEP: | 98304:cdlAsrmbxvcfqOcsfHN9cfDJARYwpoUPU8MAcVOux2P00qGT7Phj112oOhATR/g:o1qb1cfqOrHN9cbQToMU8Msu2P00q0PS |
MALICIOUS
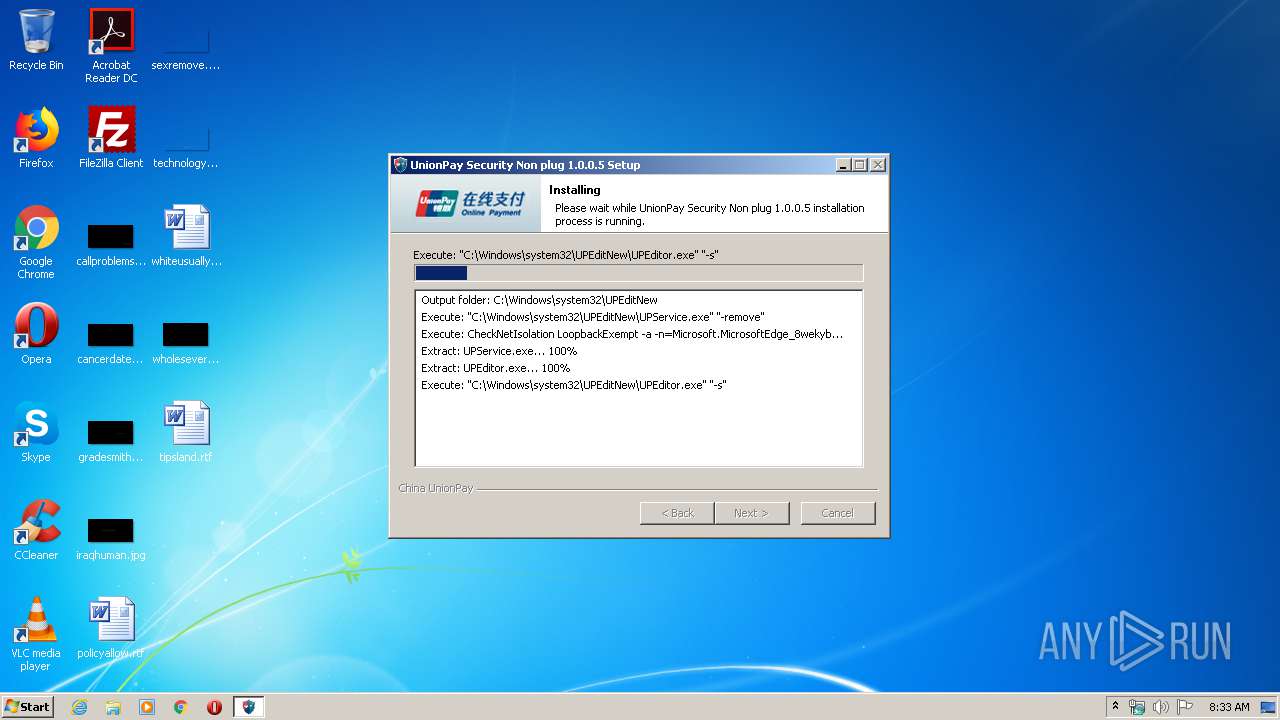
Application was dropped or rewritten from another process
- UPEditor.exe (PID: 3232)
- UPService.exe (PID: 3144)
- UPService.exe (PID: 3892)
- UPService.exe (PID: 2536)
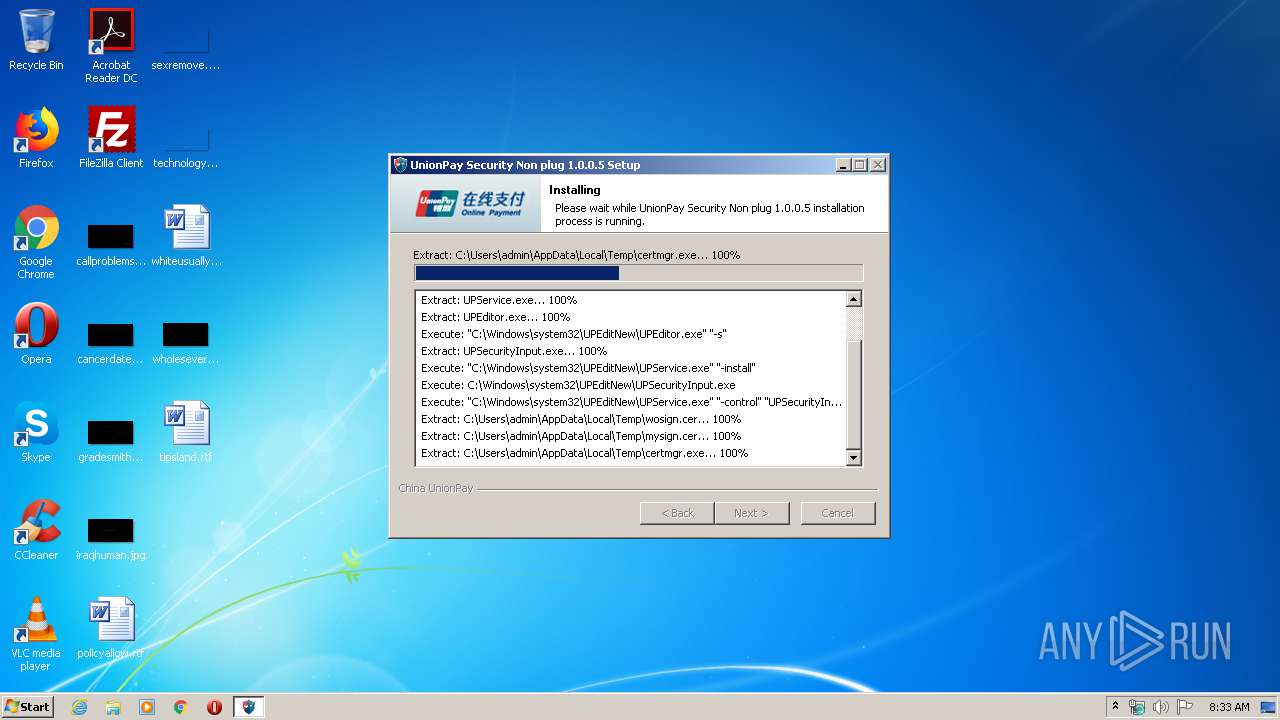
- certmgr.exe (PID: 3852)
- certmgr.exe (PID: 1352)
- UPSecurityInput.exe (PID: 3120)
- UPService.exe (PID: 4064)
Loads dropped or rewritten executable
- UPEditorEdge.exe (PID: 2344)
- Au_.exe (PID: 2248)
Changes settings of System certificates
- certmgr.exe (PID: 1352)
- certmgr.exe (PID: 3852)
Writes to the hosts file
- UPService.exe (PID: 2536)
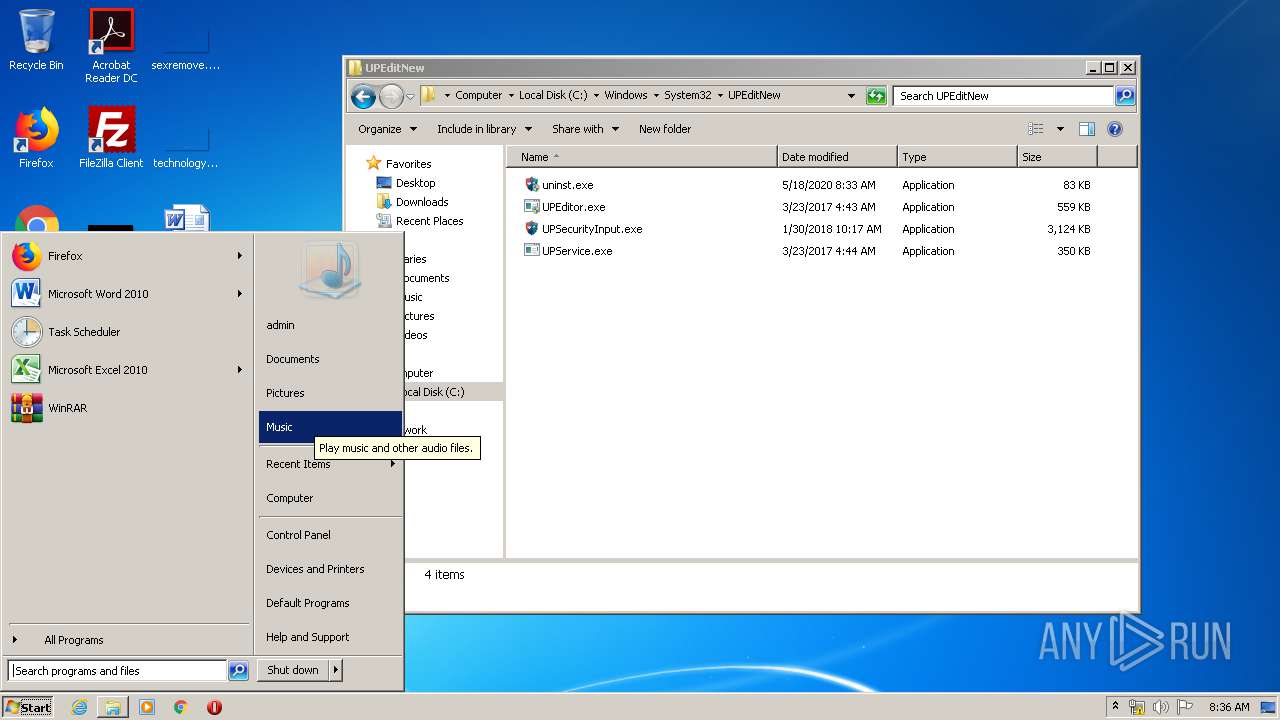
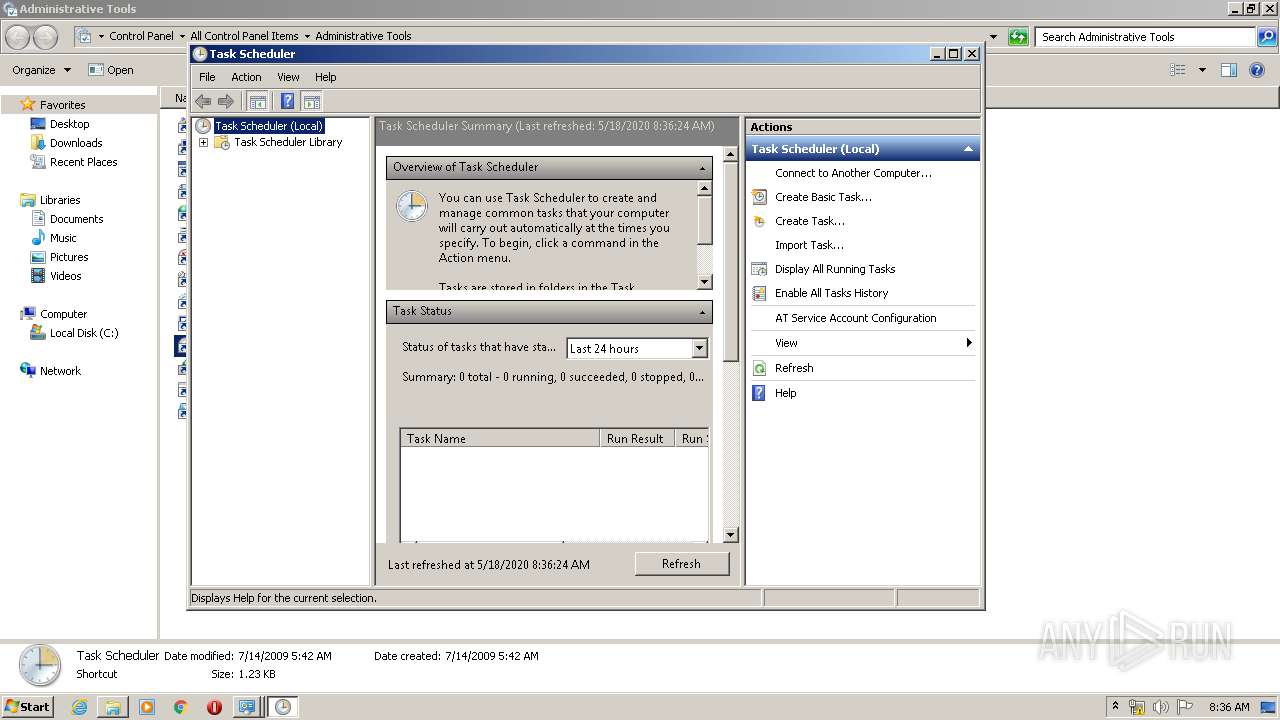
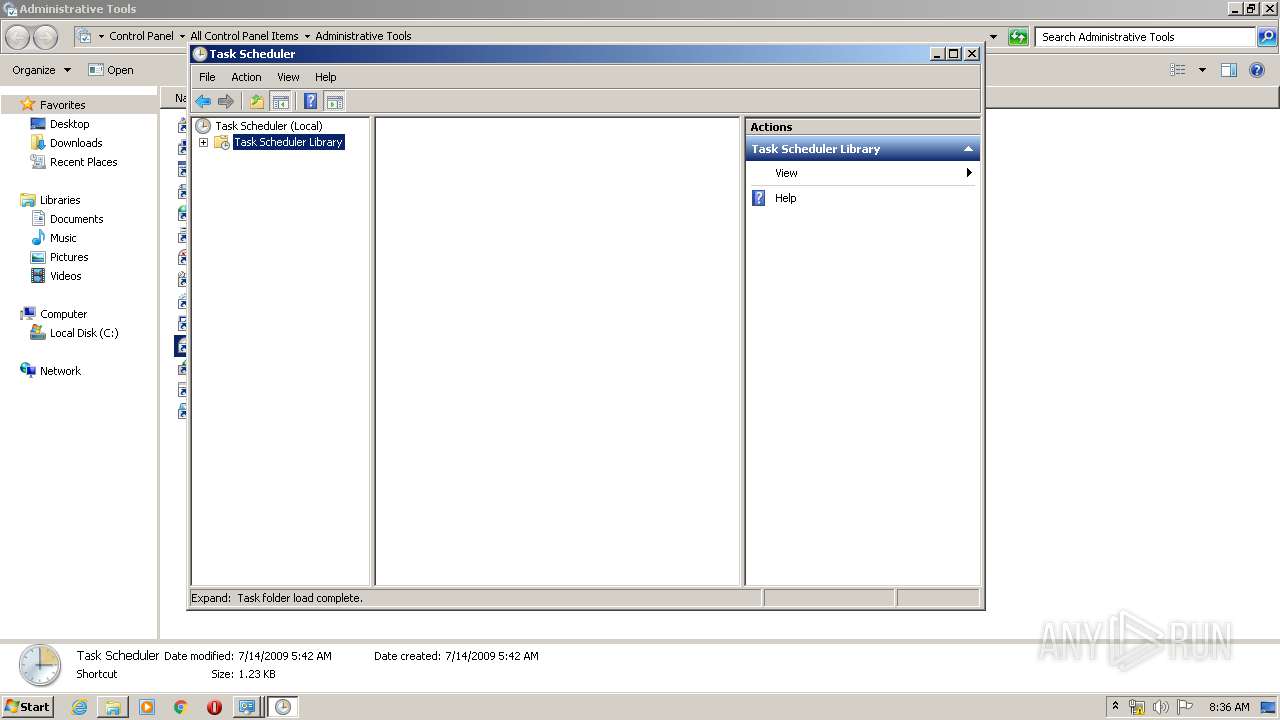
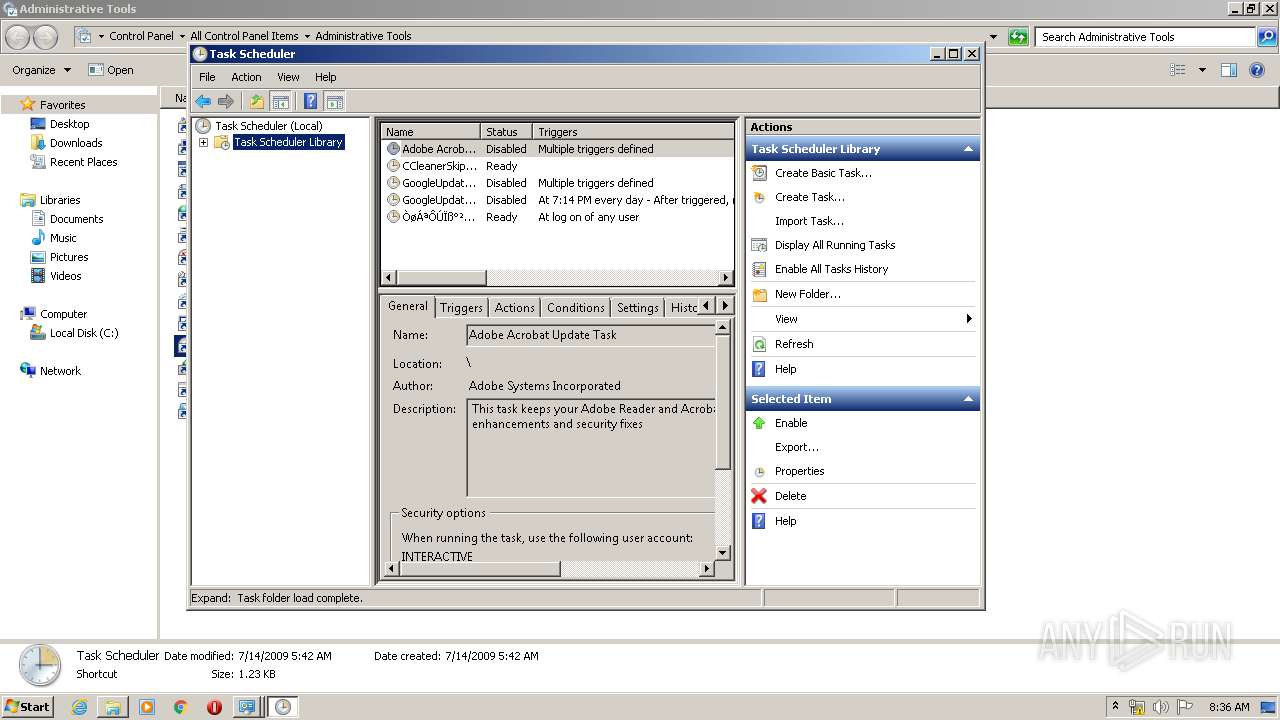
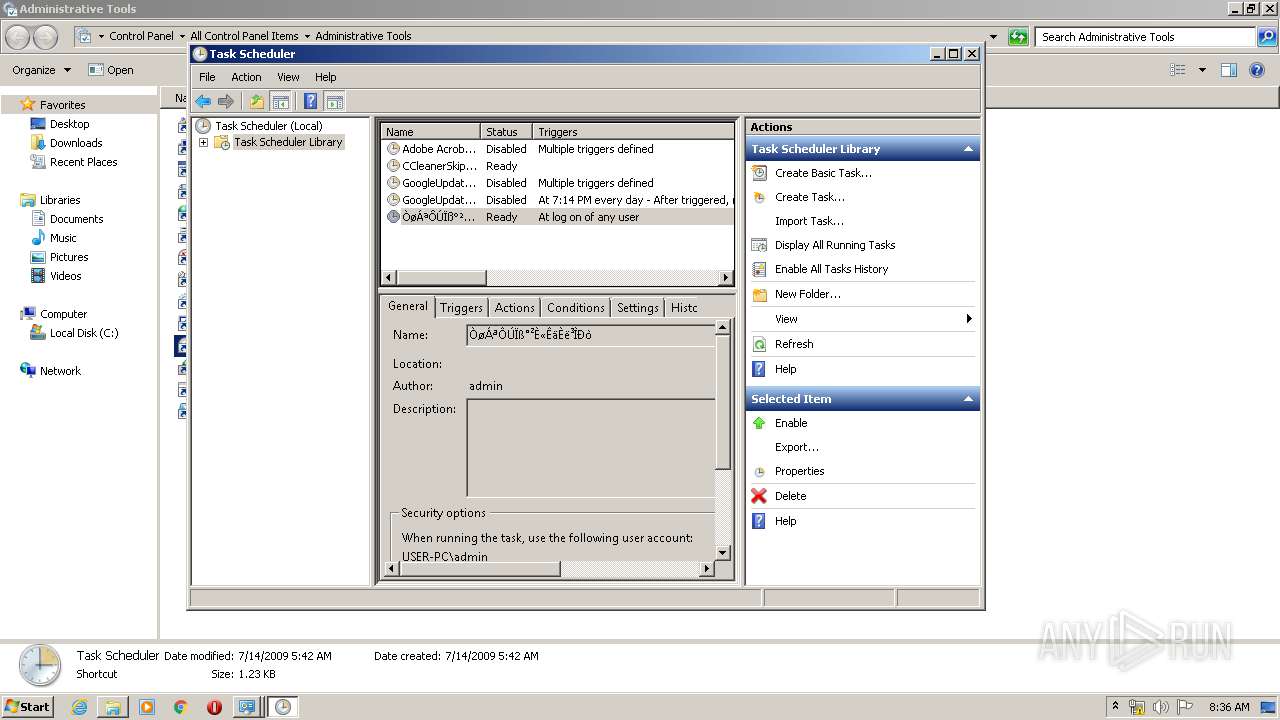
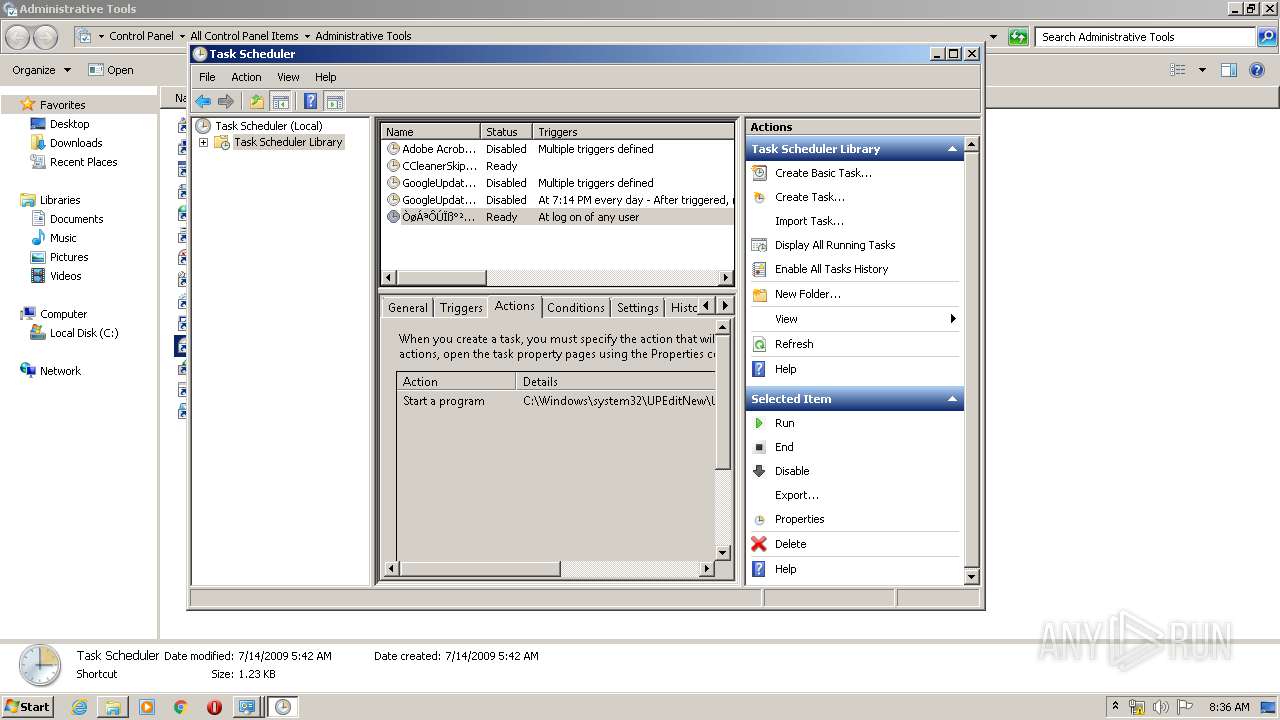
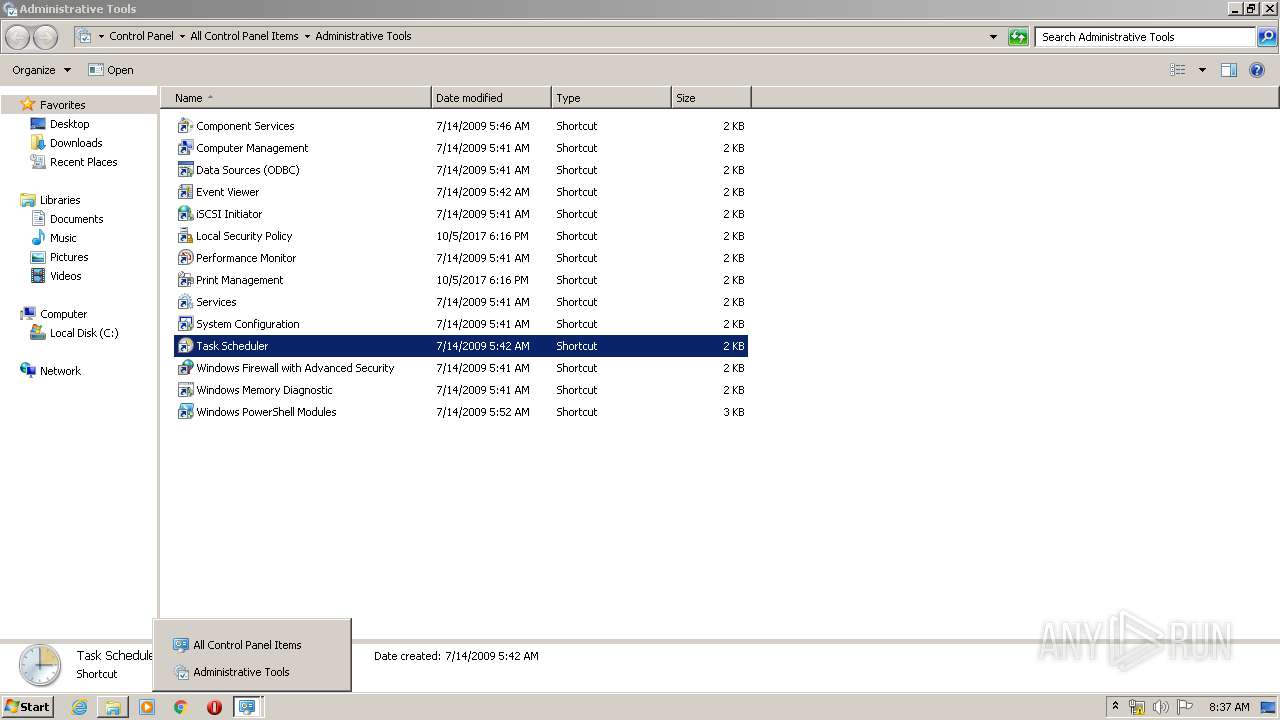
Uses Task Scheduler to run other applications
- UPSecurityInput.exe (PID: 3120)
Uses Task Scheduler to autorun other applications
- UPSecurityInput.exe (PID: 3120)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2936)
- schtasks.exe (PID: 3204)
- mmc.exe (PID: 2308)
SUSPICIOUS
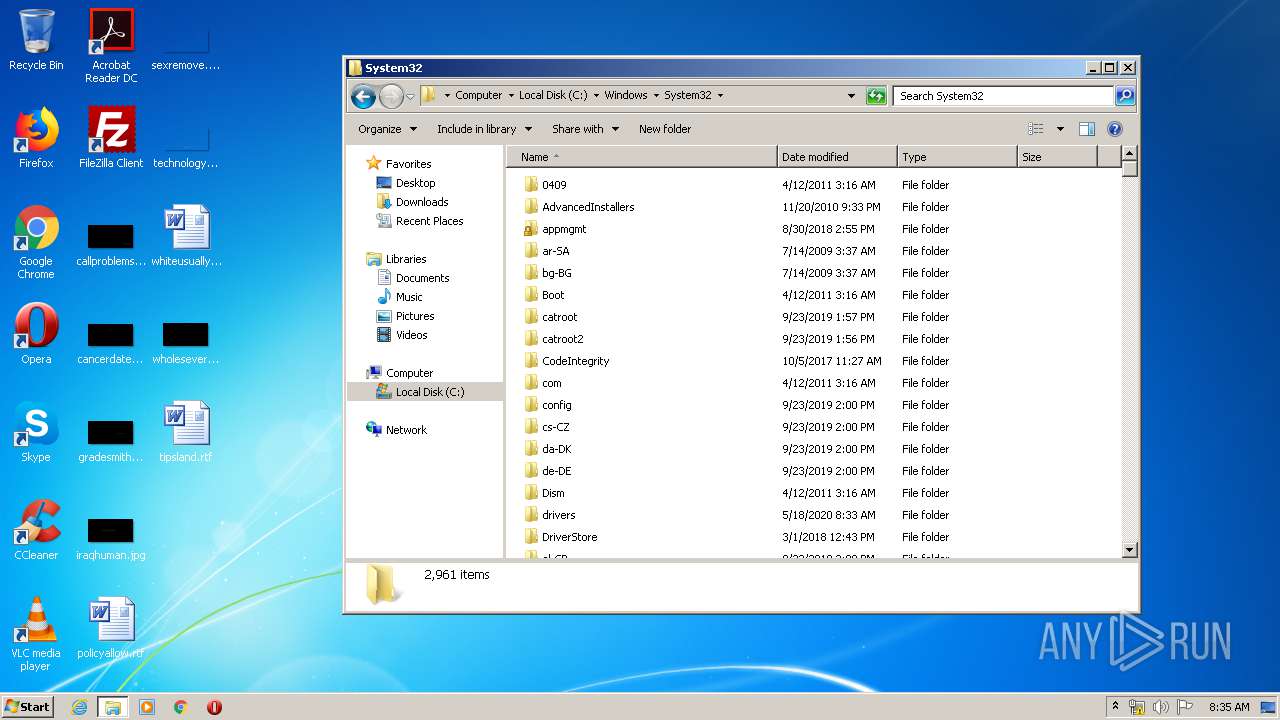
Creates files in the driver directory
- UPEditor.exe (PID: 3232)
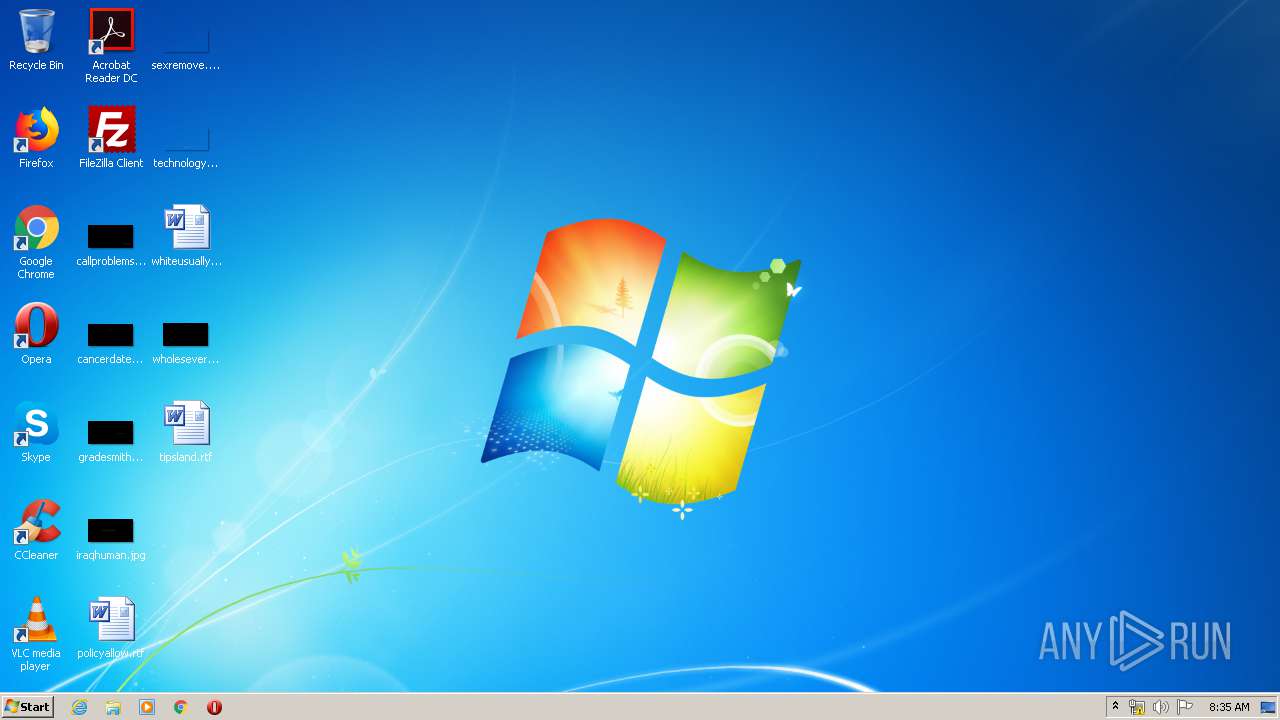
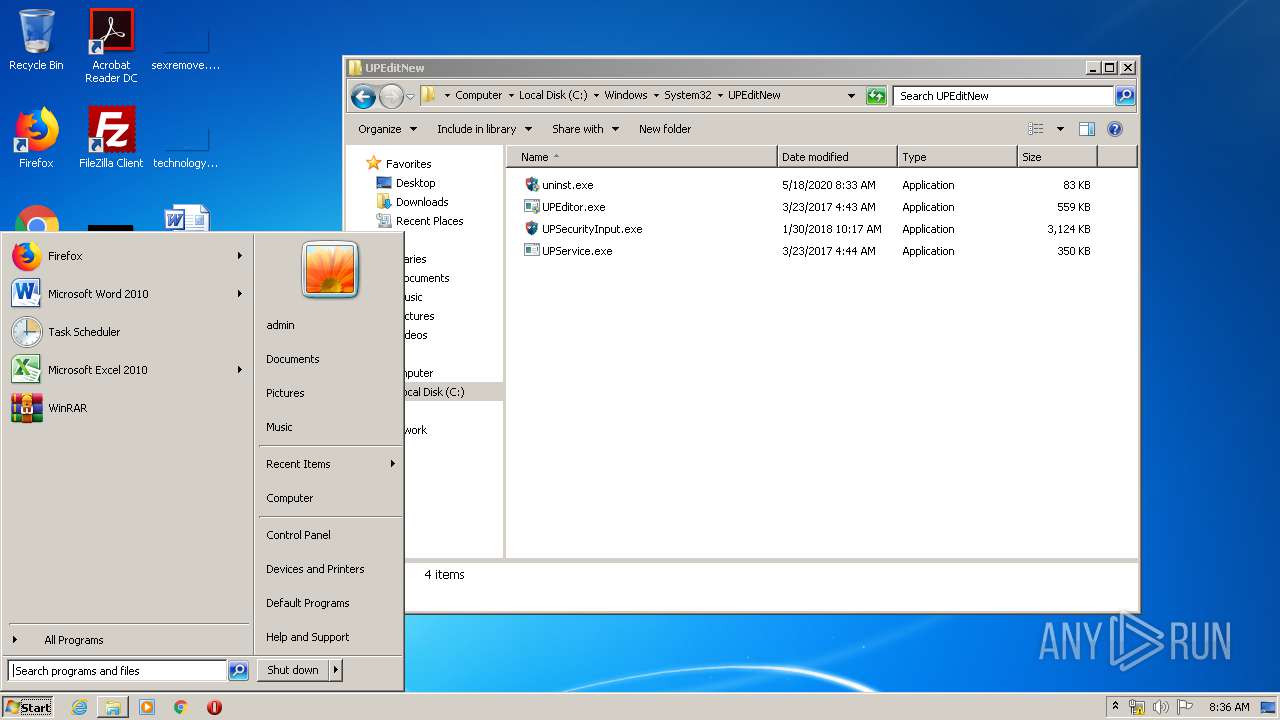
Executable content was dropped or overwritten
- UPEditor.exe (PID: 3232)
- UPEditorEdge.exe (PID: 2344)
- uninst.exe (PID: 3412)
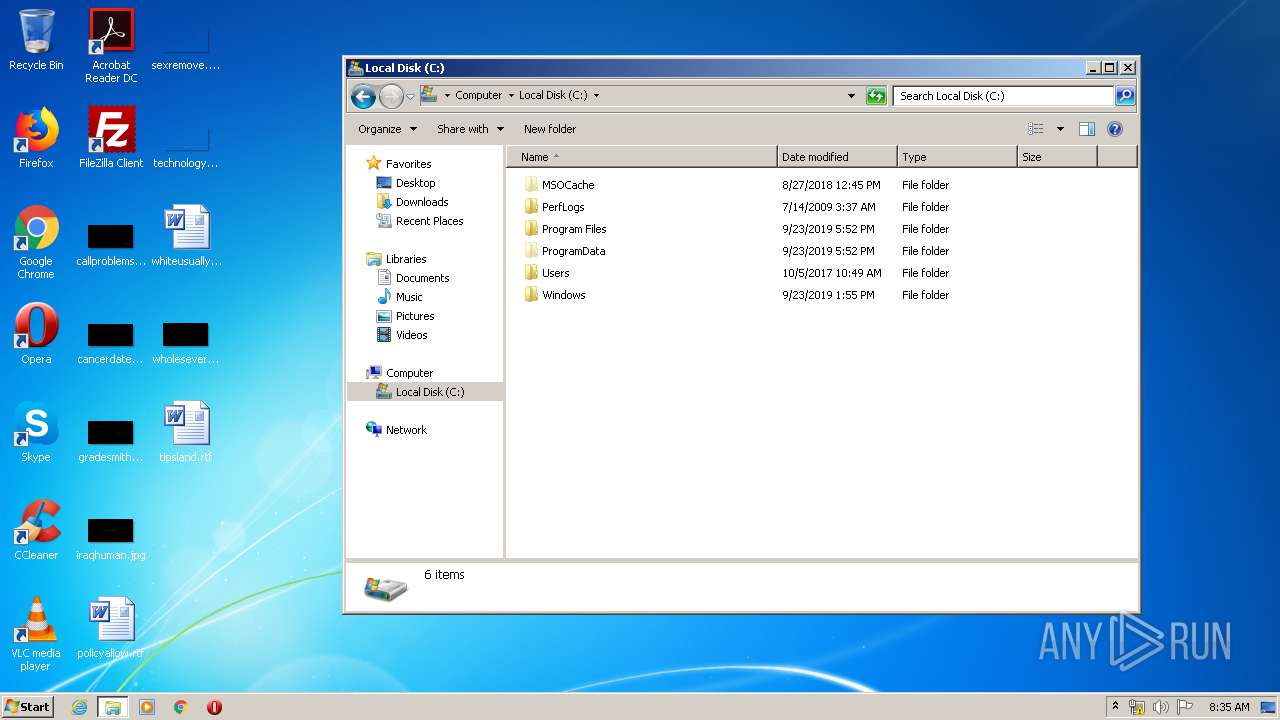
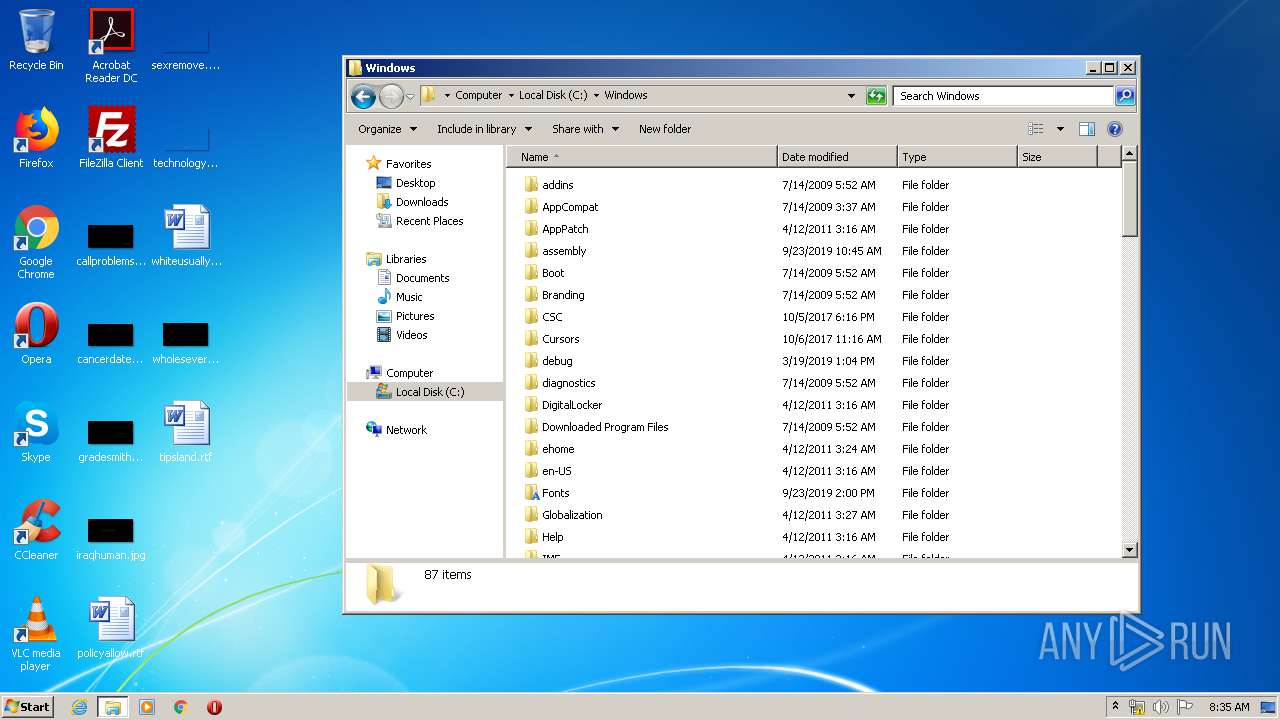
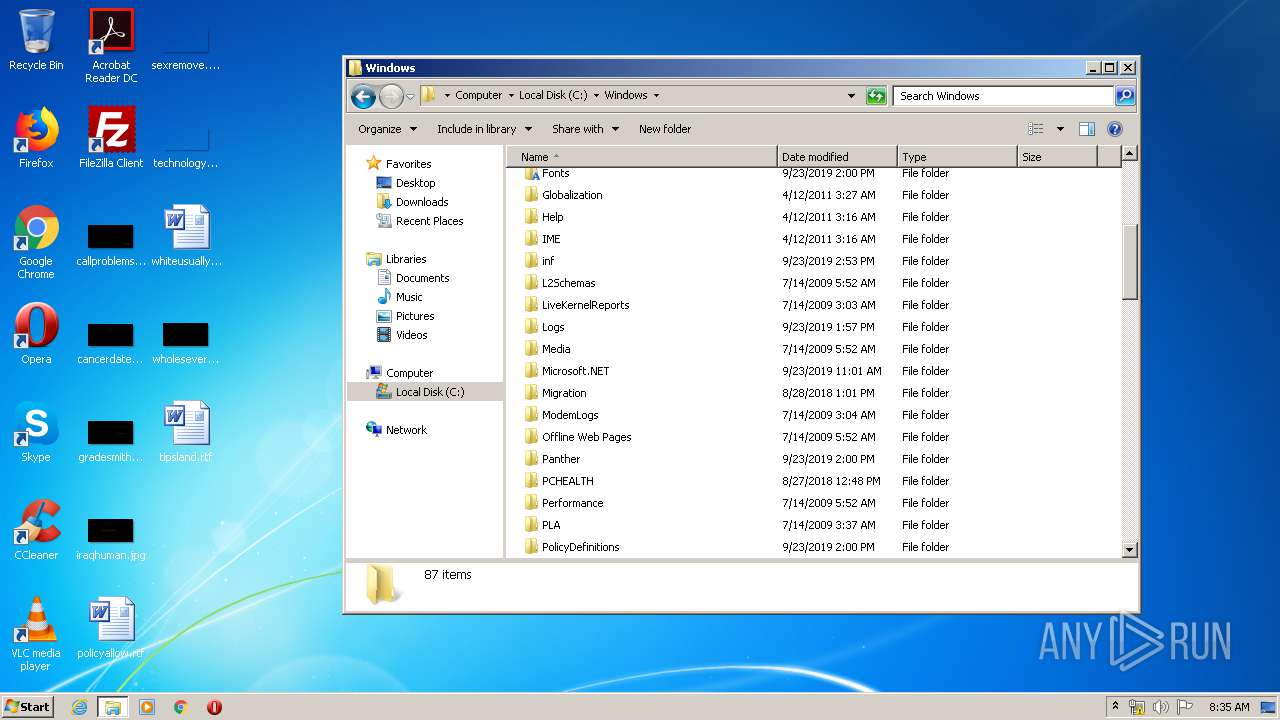
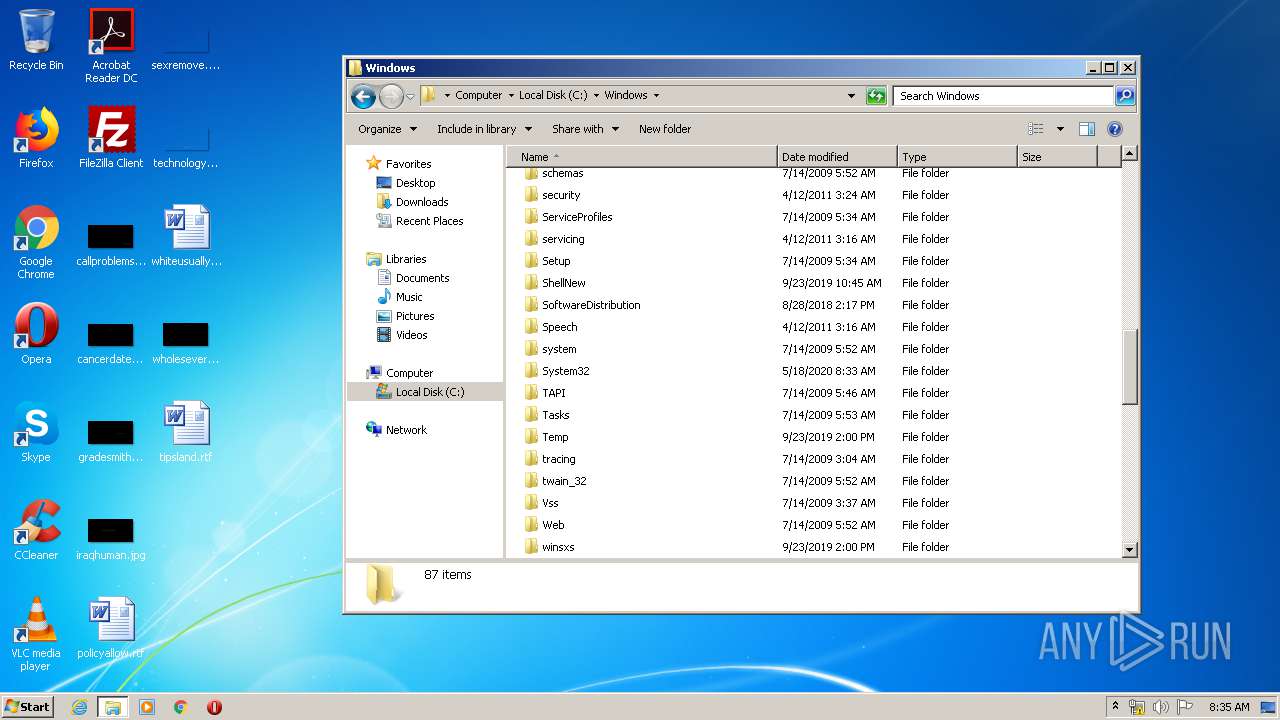
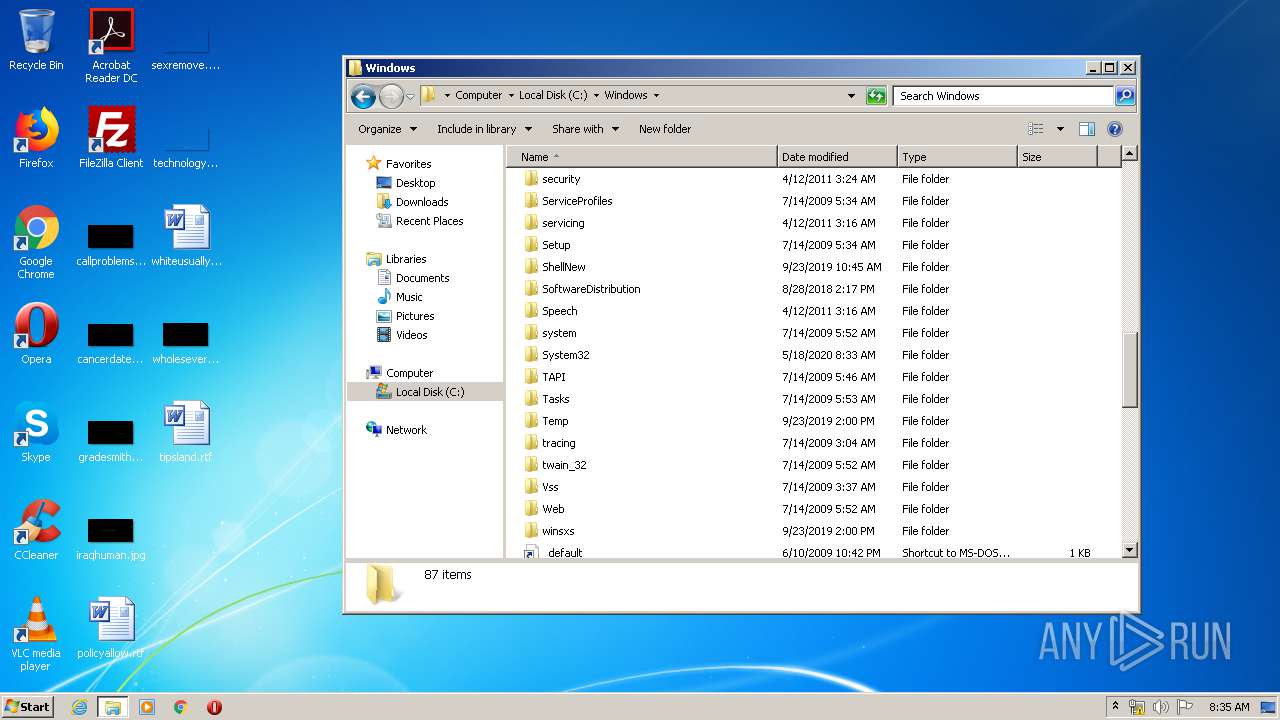
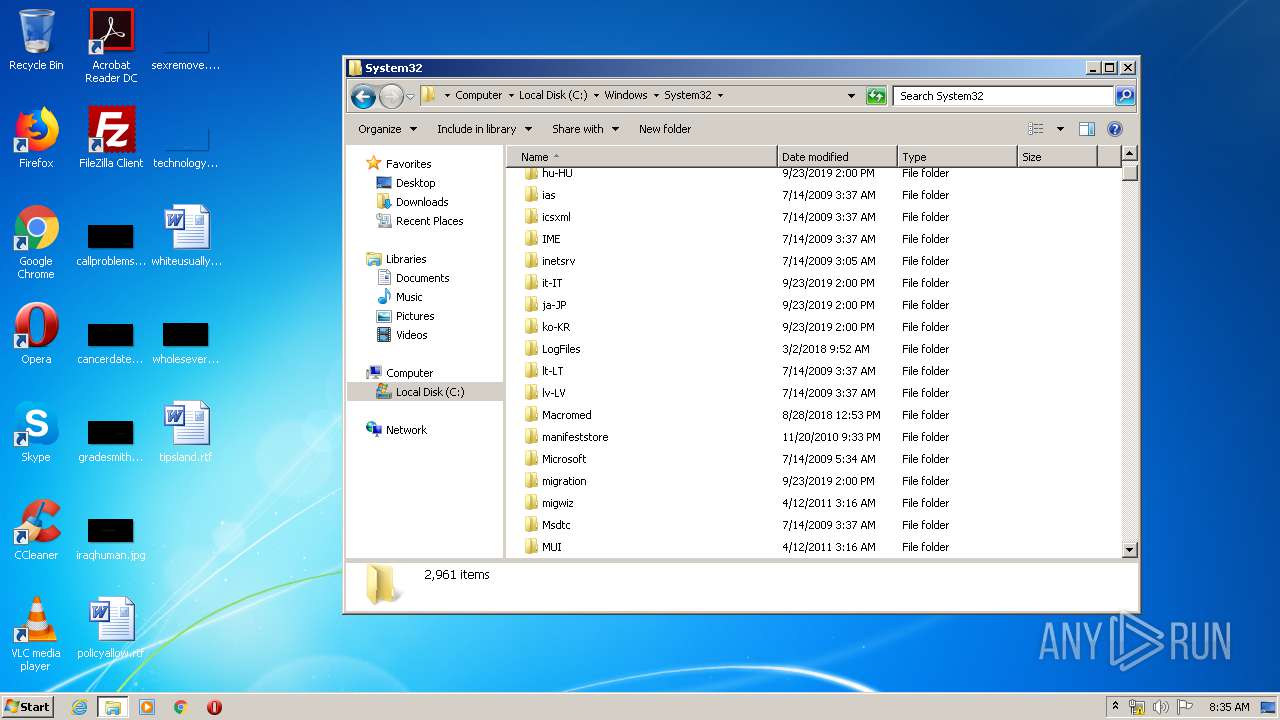
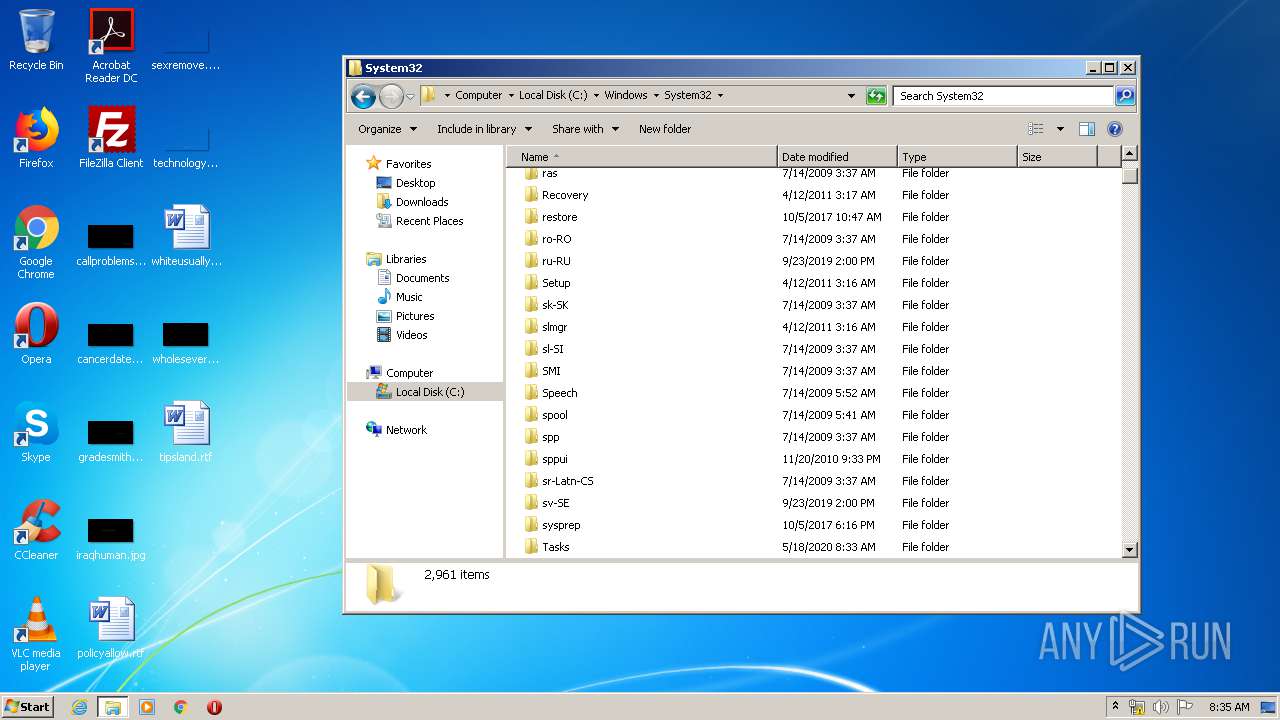
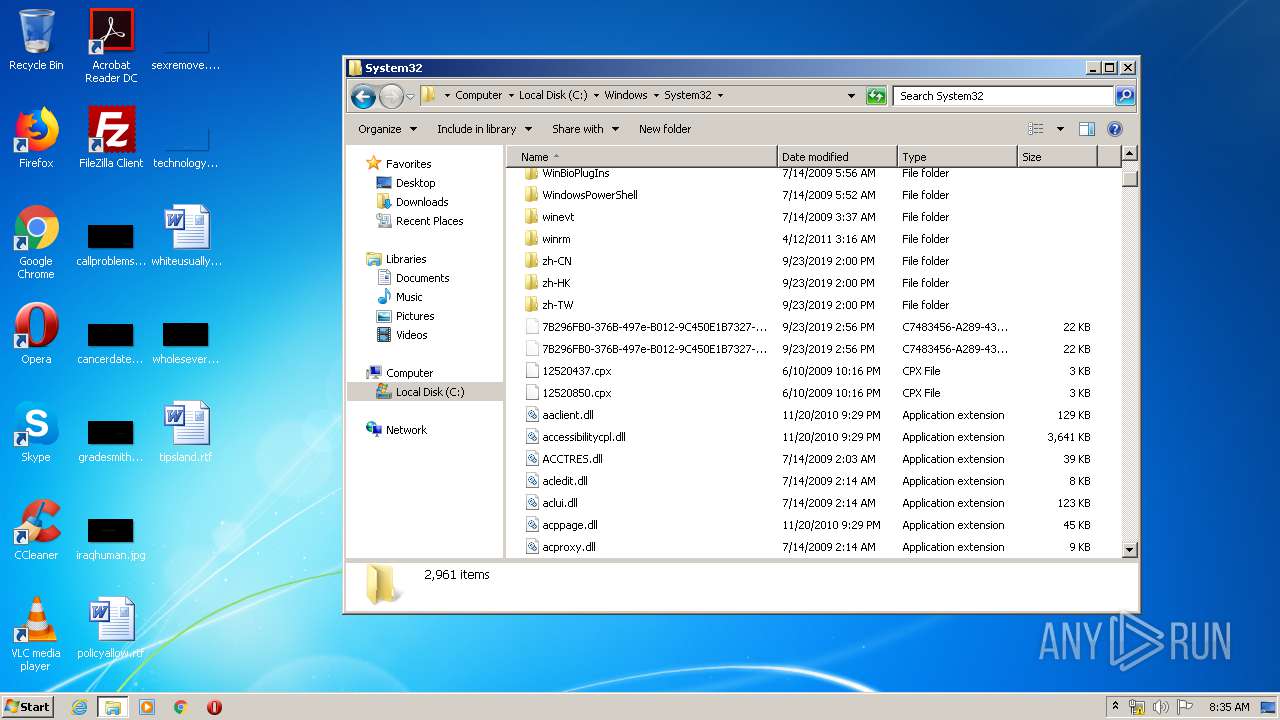
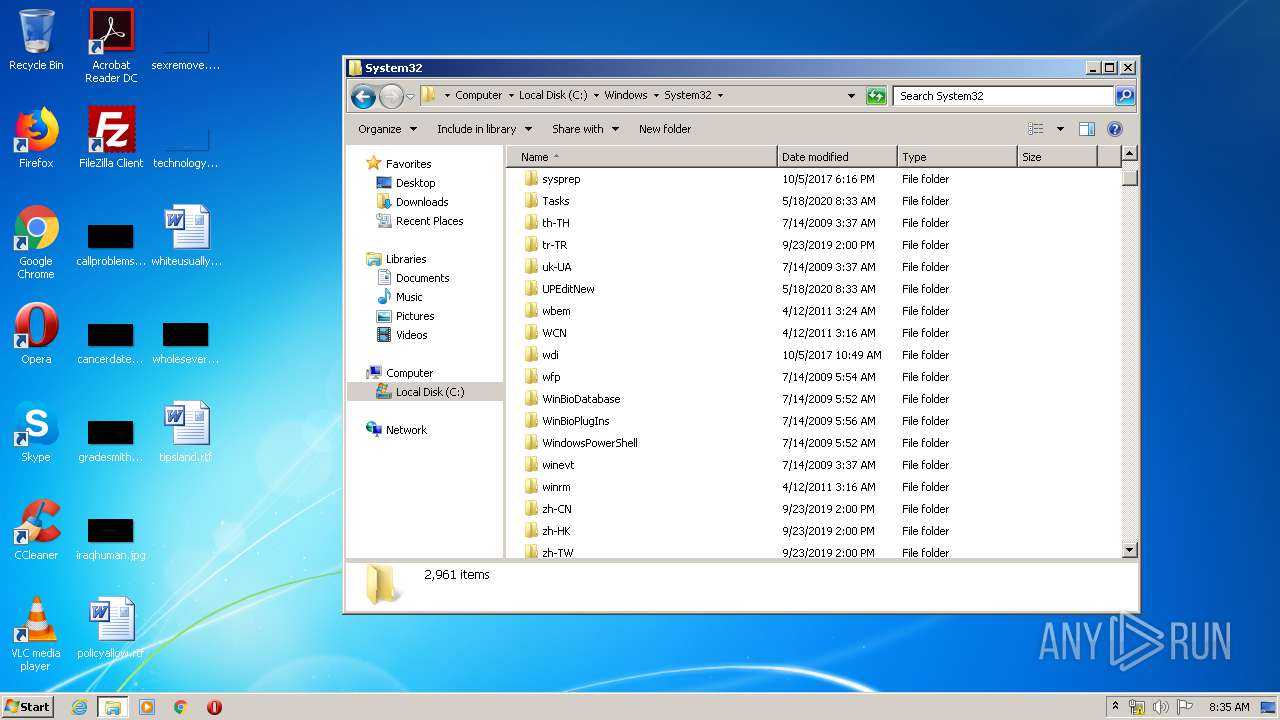
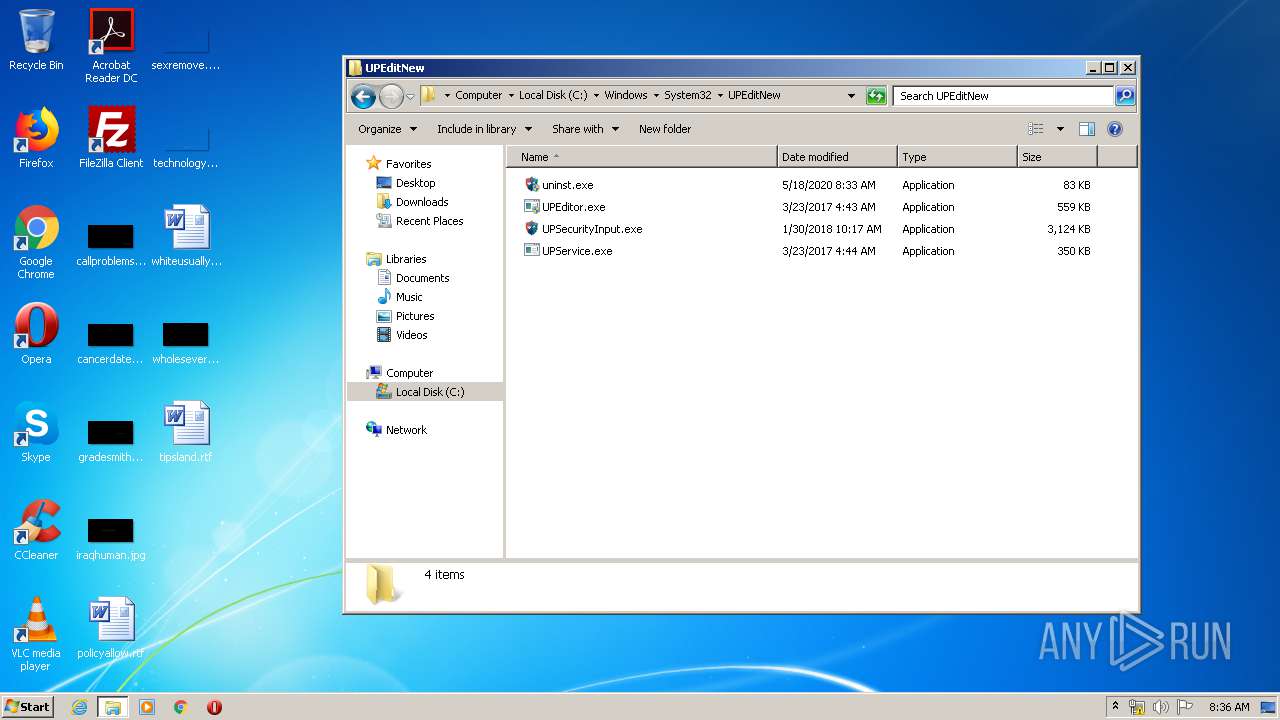
Creates files in the Windows directory
- UPEditor.exe (PID: 3232)
- UPEditorEdge.exe (PID: 2344)
Executed as Windows Service
- UPService.exe (PID: 2536)
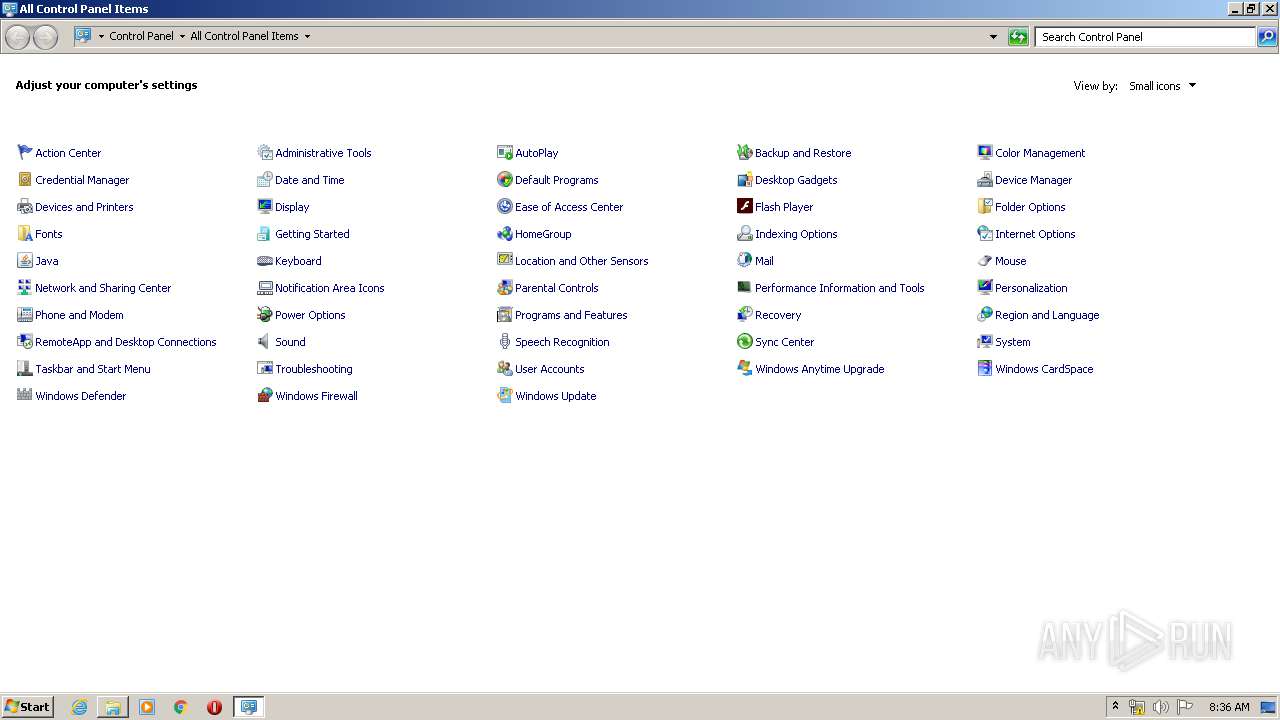
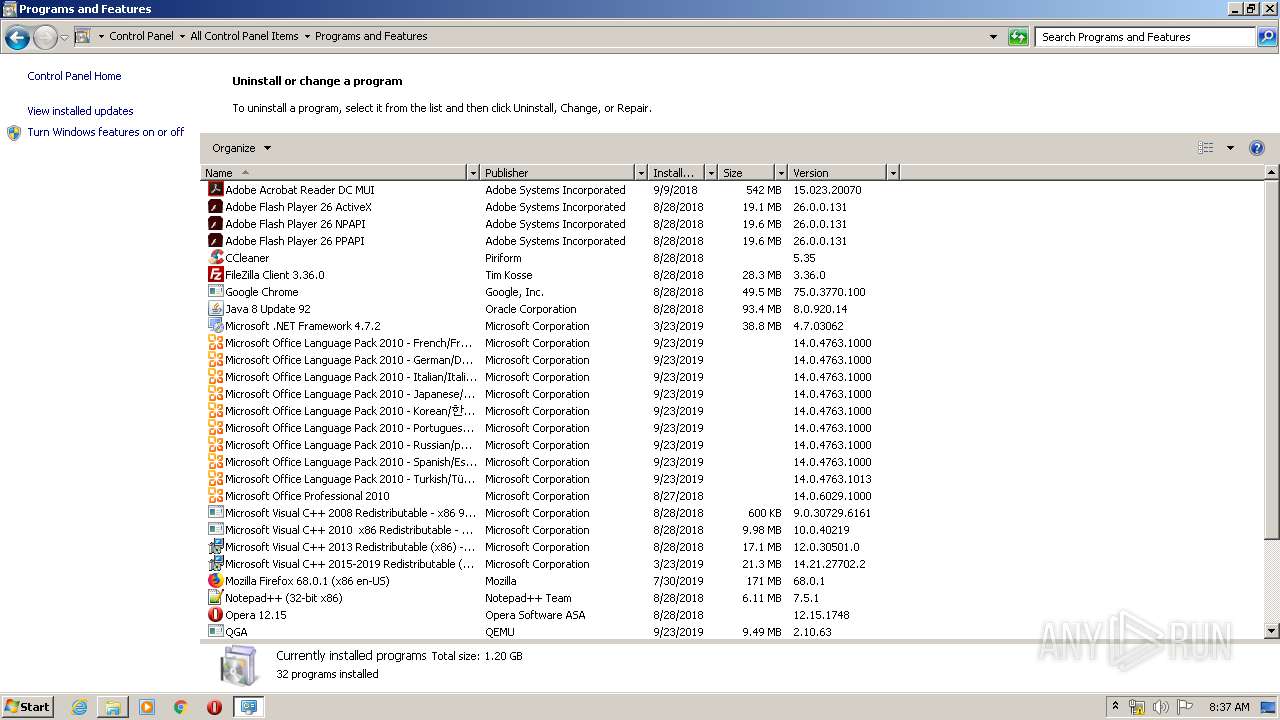
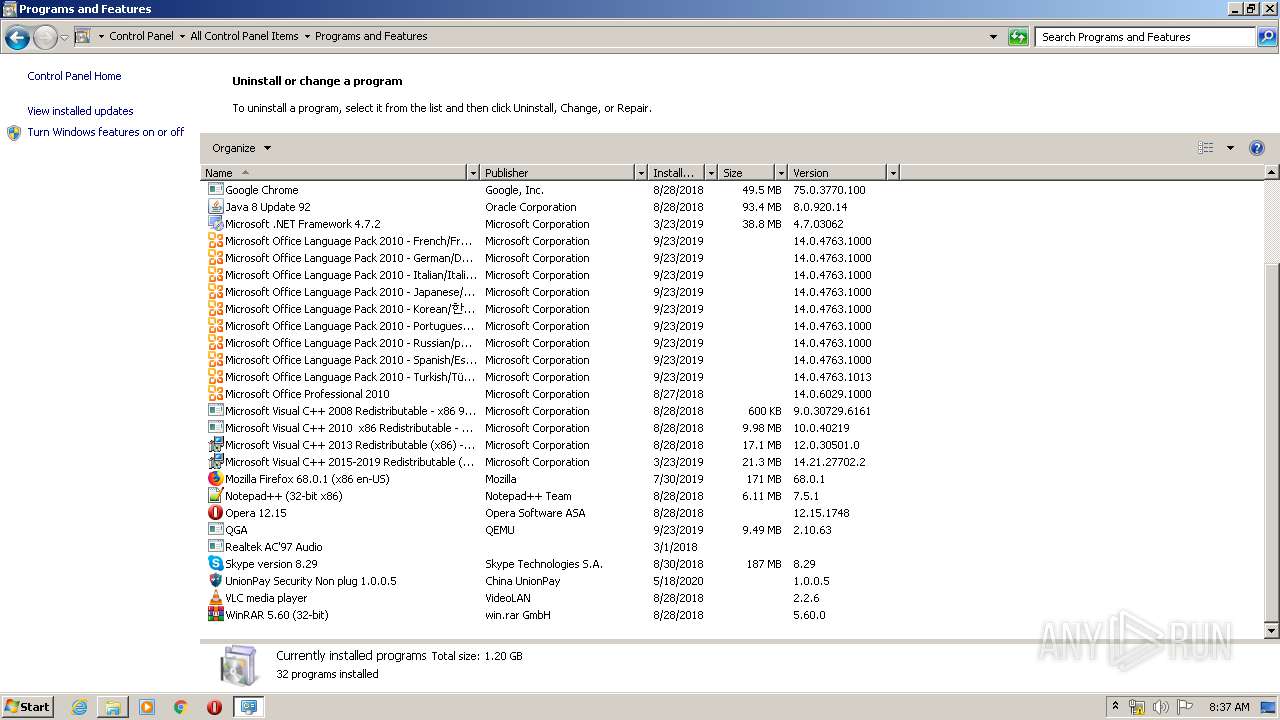
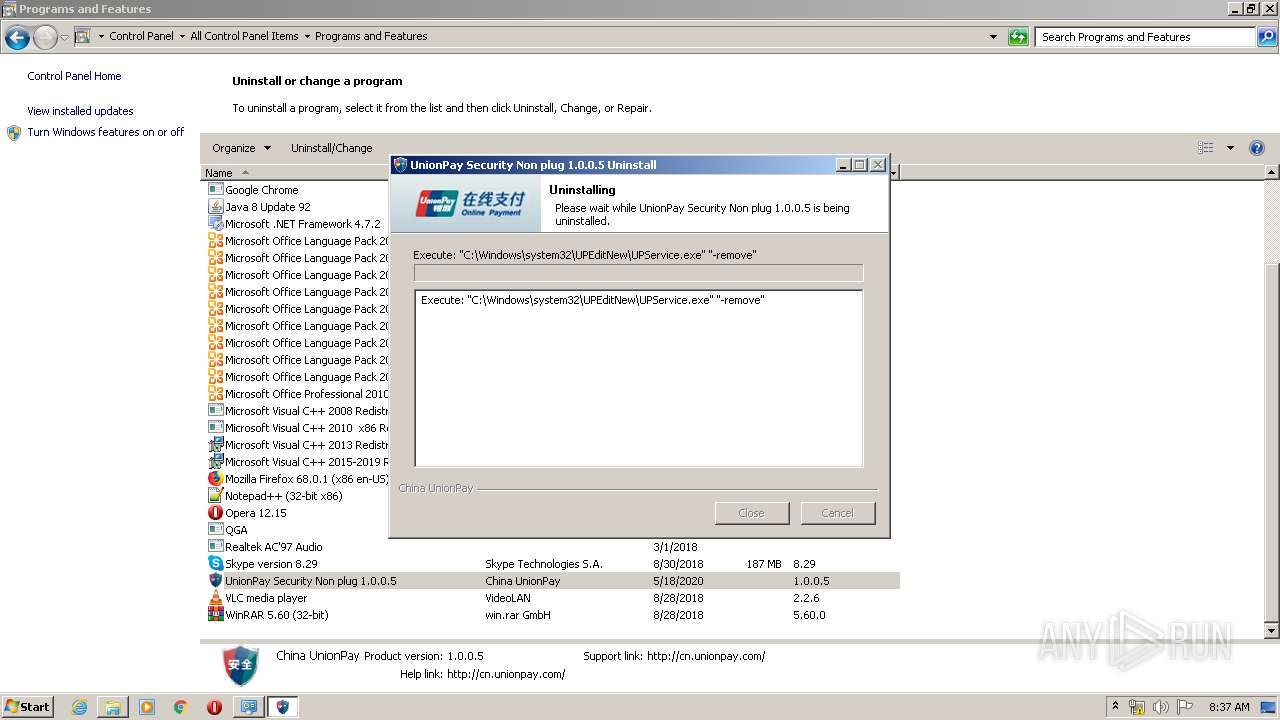
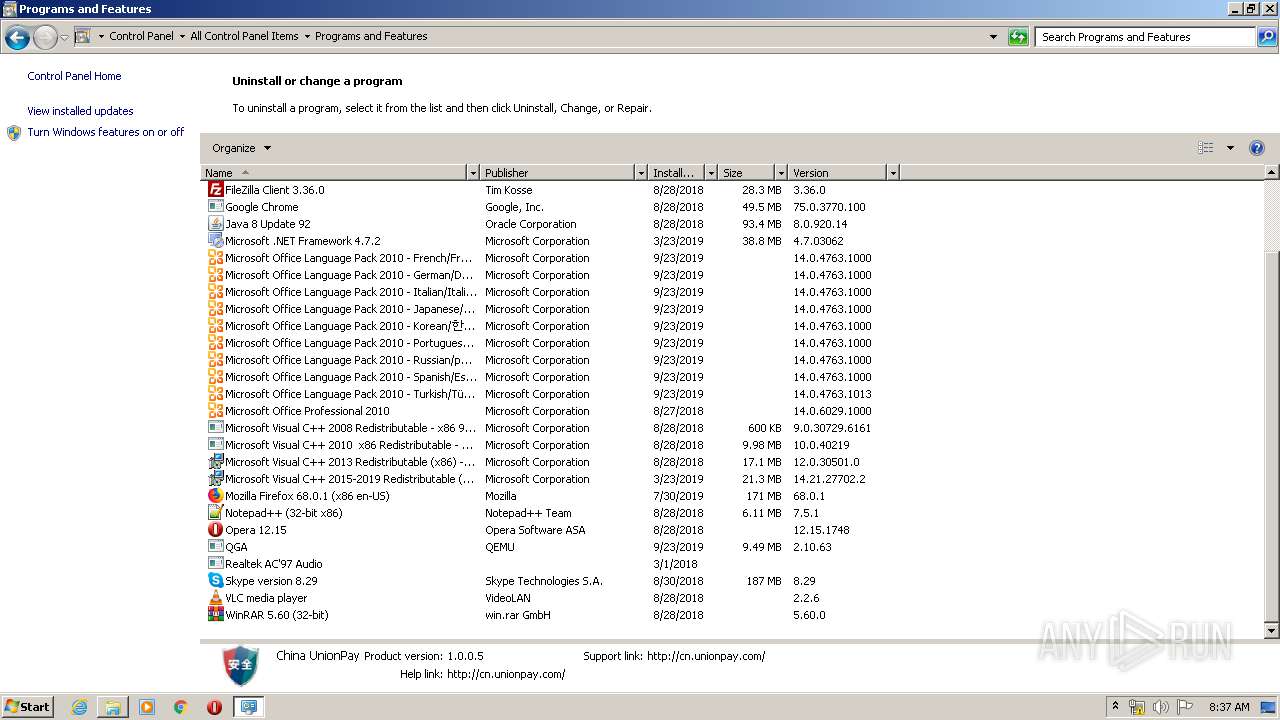
Creates a software uninstall entry
- UPEditorEdge.exe (PID: 2344)
Creates files in the user directory
- UPSecurityInput.exe (PID: 3120)
Executed via COM
- DllHost.exe (PID: 1548)
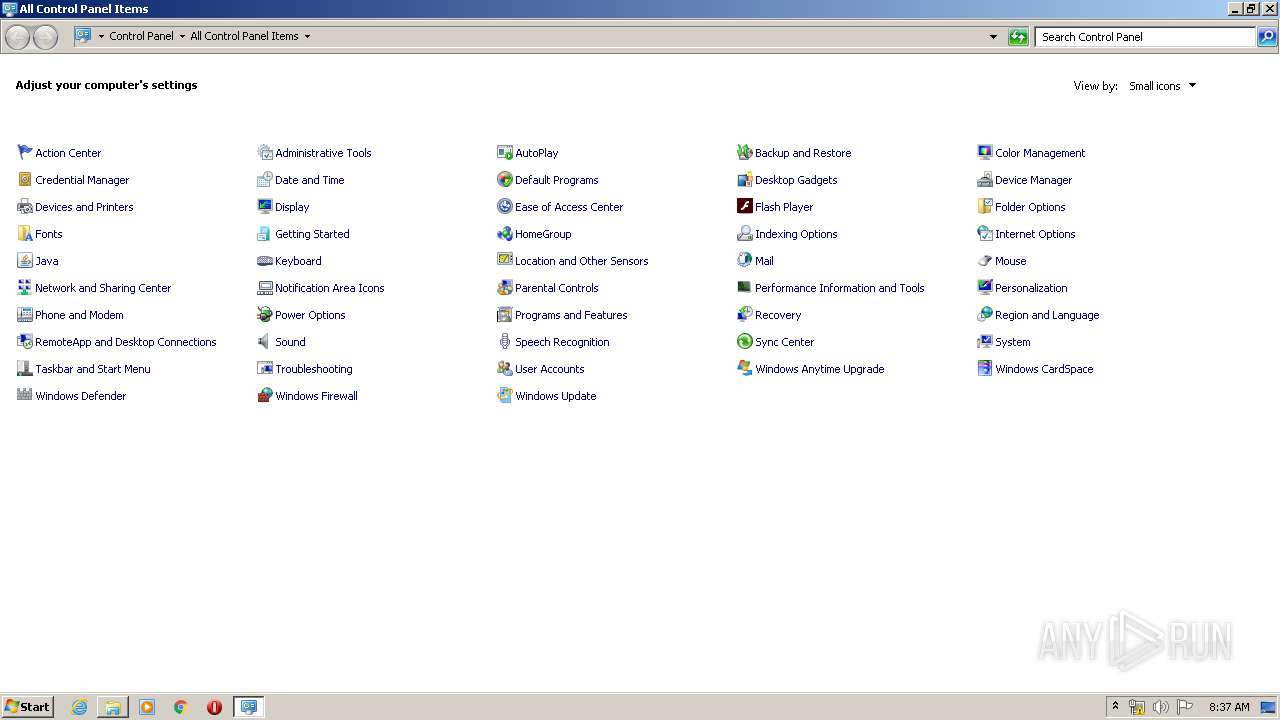
Searches for installed software
- DllHost.exe (PID: 1548)
Removes files from Windows directory
- Au_.exe (PID: 2248)
INFO
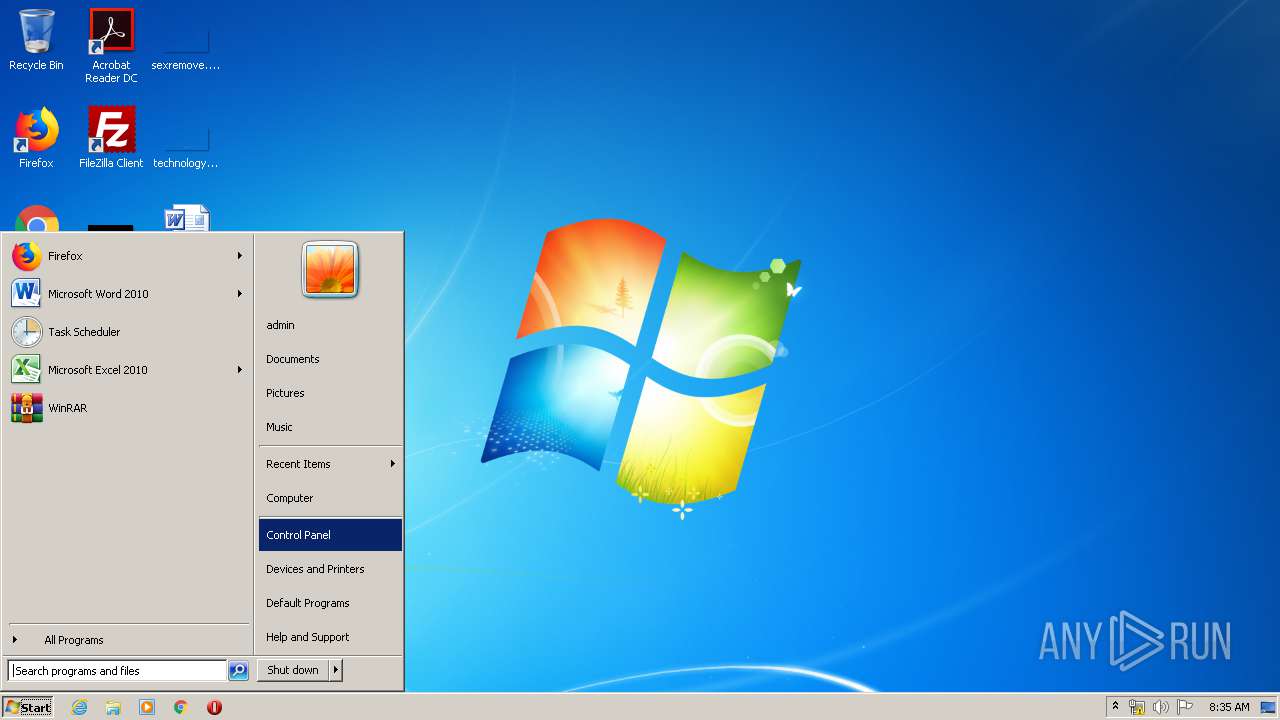
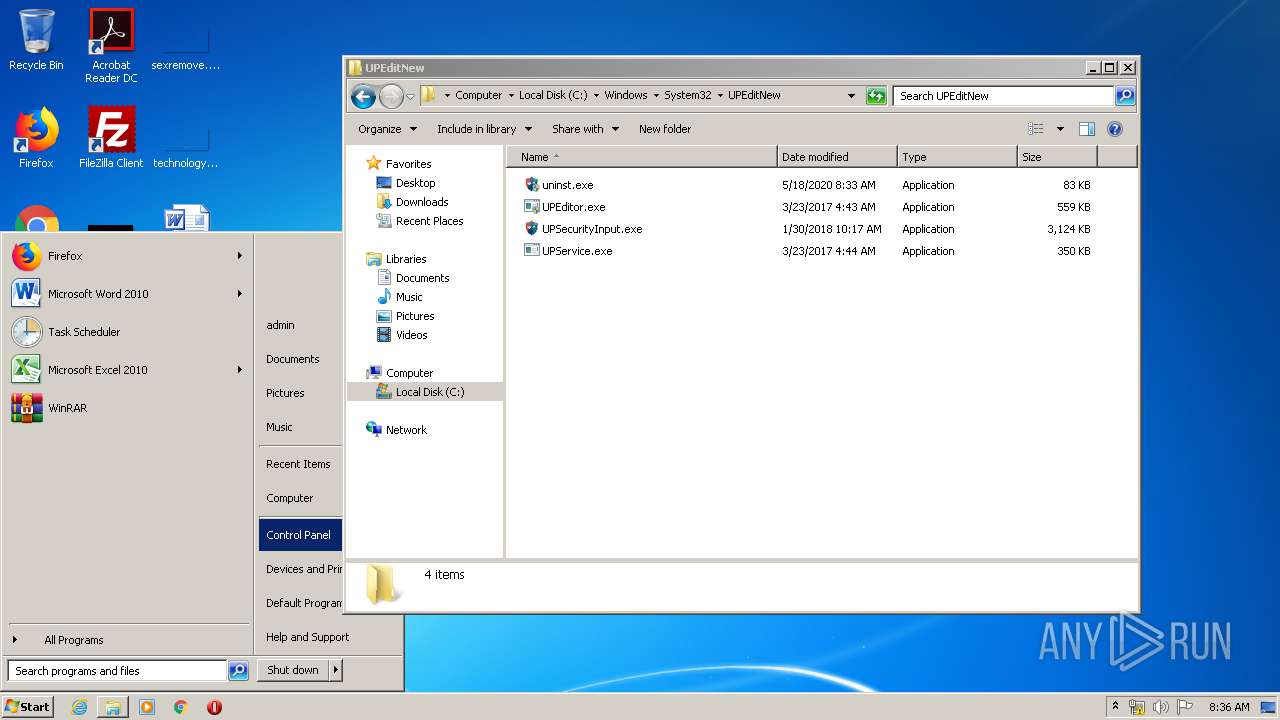
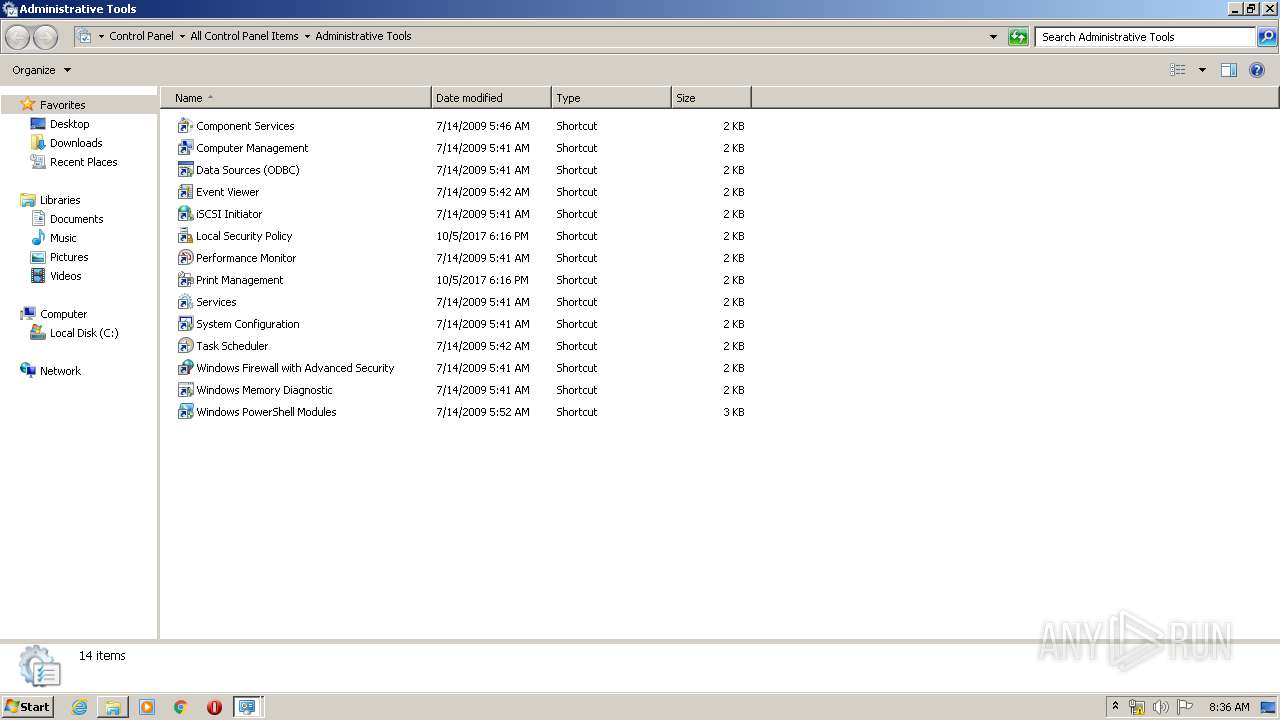
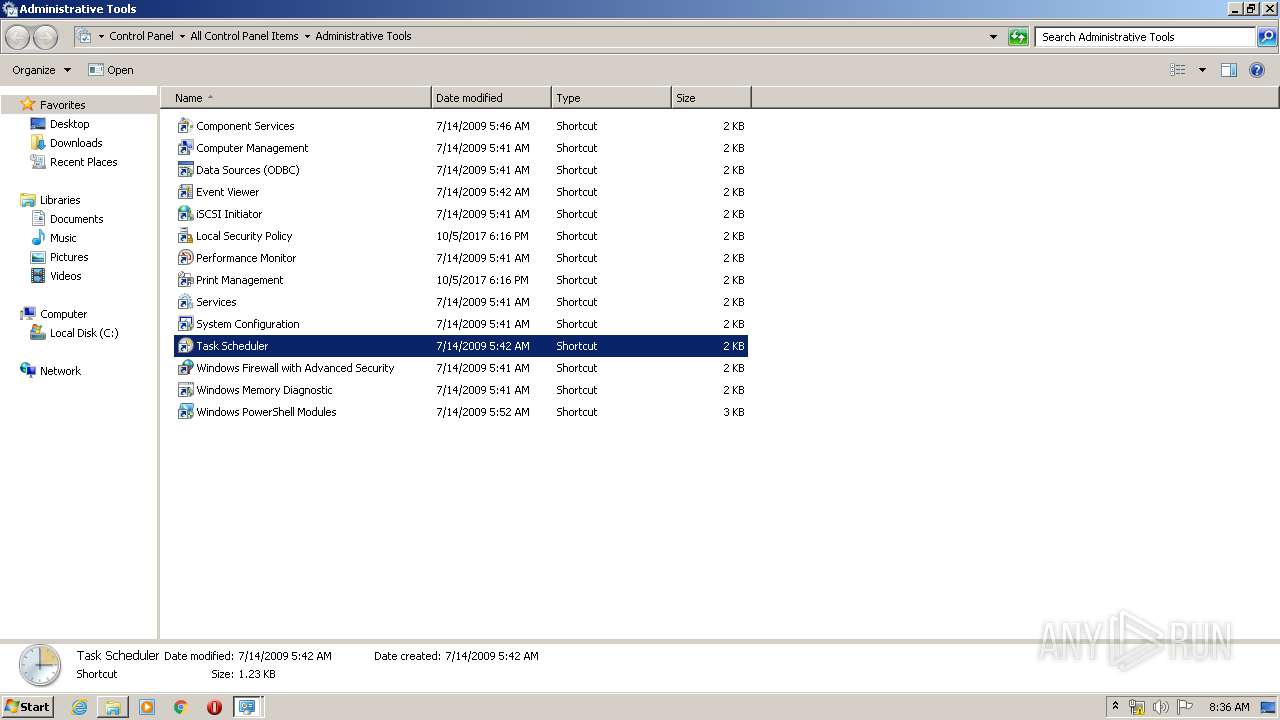
Manual execution by user
- mmc.exe (PID: 2628)
- mmc.exe (PID: 2308)
Reads the hosts file
- UPService.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:05:11 22:03:30+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 117760 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.5 |
| ProductVersionNumber: | 1.0.0.5 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Traditional) |
| CharacterSet: | Windows, Taiwan (Big5) |
| CompanyName: | China UnionPay |
| FileDescription: | UnionPay Security Control |
| FileVersion: | 1.0.0.5 |
| LegalCopyright: | (C) 2018 China UnionPay copyright reserved. |
| ProductName: | UnionPay Security Control |
| ProductVersion: | 1.0.0.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-May-2014 20:03:30 |
| Detected languages: |
|
| CompanyName: | China UnionPay |
| FileDescription: | UnionPay Security Control |
| FileVersion: | 1.0.0.5 |
| LegalCopyright: | (C) 2018 China UnionPay copyright reserved. |
| ProductName: | UnionPay Security Control |
| ProductVersion: | 1.0.0.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-May-2014 20:03:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A68 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4187 |
.rdata | 0x00007000 | 0x000011CE | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23558 |
.data | 0x00009000 | 0x0001A7B8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.87123 |
.ndata | 0x00024000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00035000 | 0x00009A60 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8058 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26024 | 1013 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.68658 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.11994 | 4264 | UNKNOWN | English - United States | RT_ICON |
103 | 2.51589 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.6156 | 492 | UNKNOWN | English - United States | RT_DIALOG |
206 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
211 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
74
Monitored processes
17
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Users\admin\AppData\Local\Temp\certmgr.exe" -add "C:\Users\admin\AppData\Local\Temp\mysign.cer" -c -s -r localMachine CA | C:\Users\admin\AppData\Local\Temp\certmgr.exe | — | UPEditorEdge.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1548 | C:\Windows\system32\DllHost.exe /Processid:{FCC74B77-EC3E-4DD8-A80B-008A702075A9} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe" _?=C:\Windows\system32\UPEditNew\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe | — | uninst.exe | |||||||||||
User: admin Company: China UnionPay Integrity Level: HIGH Description: UnionPay Security Control Exit code: 0 Version: 1.0.0.5 Modules
| |||||||||||||||
| 2308 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Local\Temp\UPEditorEdge.exe" | C:\Users\admin\AppData\Local\Temp\UPEditorEdge.exe | explorer.exe | ||||||||||||
User: admin Company: China UnionPay Integrity Level: HIGH Description: UnionPay Security Control Exit code: 0 Version: 1.0.0.5 Modules
| |||||||||||||||
| 2536 | C:\Windows\system32\UPEditNew\UPService.exe | C:\Windows\system32\UPEditNew\UPService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: 中国银联股份有限公司 Integrity Level: SYSTEM Description: UPSecurityInputService Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2628 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\AppData\Local\Temp\UPEditorEdge.exe" | C:\Users\admin\AppData\Local\Temp\UPEditorEdge.exe | — | explorer.exe | |||||||||||
User: admin Company: China UnionPay Integrity Level: MEDIUM Description: UnionPay Security Control Exit code: 3221226540 Version: 1.0.0.5 | |||||||||||||||
| 2936 | C:\Windows\system32\schtasks.exe /delete /tn "ÒøÁªÔÚÏß°²È«ÊäÈë³ÌÐò" /f | C:\Windows\system32\schtasks.exe | — | UPSecurityInput.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | C:\Windows\system32\UPEditNew\UPSecurityInput.exe | C:\Windows\system32\UPEditNew\UPSecurityInput.exe | UPEditorEdge.exe | ||||||||||||
User: admin Company: 中国银联股份有限公司 Integrity Level: HIGH Description: UPSecurityInput Exit code: 0 Version: 1.0.0.5 Modules
| |||||||||||||||
Total events
835
Read events
815
Write events
18
Delete events
2
Modification events
| (PID) Process: | (3852) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\7C2106C955C997C65E5770A3326A12D304BCBB88 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000007C2106C955C997C65E5770A3326A12D304BCBB882000000001000000FB030000308203F7308202DFA0030201020209008213409BD214E854300D06092A864886F70D01010B0500308191310B300906035504061302434E3110300E06035504080C074265694A696E673110300E06035504070C074265694A696E6731123010060355040A0C094D6963726F646F6E65310D300B060355040B0C04746563683114301206035504030C0B4D6963726F646F6E6543413125302306092A864886F70D01090116167765626D6173746572406D6963726F646F6E652E636E301E170D3138303132393037303933395A170D3338303132343037303933395A308191310B300906035504061302434E3110300E06035504080C074265694A696E673110300E06035504070C074265694A696E6731123010060355040A0C094D6963726F646F6E65310D300B060355040B0C04746563683114301206035504030C0B4D6963726F646F6E6543413125302306092A864886F70D01090116167765626D6173746572406D6963726F646F6E652E636E30820122300D06092A864886F70D01010105000382010F003082010A0282010100AE670D30F0026938C96E266D114FEB2B3B745AC04AD30FD9B1A87AFBB5A6592A292641917B18A1F9DF5CD18F56C82D07B227E1EB8BECF8CE6DF7A024F31655E69AD074C36FB7042659C3243CB76ED17E52685D0B1EDC92A943AD9B4D6B45BCC308FFC5215A0786AE87FE225DD3215DE8F434756ADC826CF244ADB69E93F60DFEC5741530C2C36FDB4CF43C87EB6C16FBE2C5AF0110C6AB2ABDFDD1E83DBBC168BA1EAE8D1DDFB0A6DC3C7DD7FFB415DCDD9EE1C6AFCBD805926F05DA20ED4BDA774A8A13F300EB1D3661A807A15FFAA178E95C65F08EB7CFDFD3DBC82B3201B30C5683C07A176D41E6EB499B6ADABC8CA87E8B8C324D7E46FDDC08A97EEEE3190203010001A350304E301D0603551D0E041604140AA0EE79A030C6168D18612B68553C00A24230BB301F0603551D230418301680140AA0EE79A030C6168D18612B68553C00A24230BB300C0603551D13040530030101FF300D06092A864886F70D01010B050003820101004FC56121FBDBE7061938954896508C14D58F1E0D226F1155E38A3F7A68CC4A99C1FD91FF45522F5BCEF0BF88549B7BE40CD663E80F47E26B0CA4FC1D77E93037A75EBE2B197C180468AC0694F3CB2ADD0C4505F35A5CCBECD0E1EBB10C440E568175F28120CC266B044F684E68A2FC646BBE19A9D2987D110B57CE91A15D9C5B754C20EDDEB9778587257C150B6586AE8922ACD4CEE10509134C22EEE09138441F186018A96267D52DF7C267AE01FD41312E00DF0A7FF9323B67CCD618B3E17DFDC2CDDE7DFA320634C1FAF88736A1AE2ED5908CF1C0B4D978F02ACF0223DD18DFCD29475C549FB11B6106DFC8C334FB7E125B560A3FDFBA70BCE1F382B08F4B | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1352) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\CA\Certificates\58729A164A555962052273F912DBBE749126F314 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000058729A164A555962052273F912DBBE749126F3142000000001000000EF030000308203EB308202D3A003020102020101300D06092A864886F70D01010B0500308191310B300906035504061302434E3110300E06035504080C074265694A696E673110300E06035504070C074265694A696E6731123010060355040A0C094D6963726F646F6E65310D300B060355040B0C04746563683114301206035504030C0B4D6963726F646F6E6543413125302306092A864886F70D01090116167765626D6173746572406D6963726F646F6E652E636E301E170D3138303132393038303432395A170D3338303132343038303432395A30818A310B300906035504061302434E3110300E06035504080C074265694A696E6731123010060355040A0C094D6963726F646F6E65310D300B060355040B0C0474656368311F301D06035504030C1677696E646F777331302E6D6963726F646F6E652E636E3125302306092A864886F70D01090116167765626D6173746572406D6963726F646F6E652E636E30820122300D06092A864886F70D01010105000382010F003082010A0282010100C568297031D56BE84BC5F695FBD2A9F7EE5E25EA6CBB8048C7F02EBEDF44A6D56B2C466A2C47CE3CADDF337931952F0FEC38FB89DE94C5D590876596D8C80EBD761A07008DF1A93D9F7CB874ABE1B29EAC28E38952103E85C2FD4179AE45DCC64FDB1A93A7D416974B51E1DC175CC02B85083DBCA77CF120A02E11B530C1E78B3DA26DDF6FB2818B7211C1D0B108A63C32AEFCAFCF9D373F06F71C33CFE70A8036E814E406B559C636801415B25D988E88FAAA0A408BF172384727808FACDC0510845AC6CDC615438036DFFA7C6359EFD5FA11307E781F2DC6DA9BC9912F1024041A366CE7D0A57C9FE075A3786EA31F3FF11E8CD2EAB787AA19273F47C973E50203010001A353305130090603551D1304023000300B0603551D0F0404030205E030370603551D110430302E821677696E646F777331302E6D6963726F646F6E652E636E820E2A2E6D6963726F646F6E652E636E87047F000001300D06092A864886F70D01010B050003820101001446BD659411843D6A4DB8C75C794EECA5B55660A1054994B978EA21155AAA95C847521F03FDDCF6F38EF78C57BF6844824FA4063B992317880D1DF546A2F6E2ADE3855E53C8A0A7040881F1B87E6256F415C2191C977B8A7F5A343161FBF9012B01DDE05E414B1A00FC3FB63F58024BB9C95A1CCCCFF89B75007630B916636244C7647CAA5E63DC02322FFC478D44AA69E44CD851BB70844BC3F65311E2653B046C97EB6077C119651C14C36E7CF4DBE7AFB296F42419A09AF905C0EA85492109B715F853915FC6C52F203A958BEA15D0163E7D7D0BCD5AC4CFD6F848277487D69BC73E6A2AA807D9DE2AB71ECFF89CF21853BD9C2F2DDE0E8E391EA06FB5CD | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\UnionPay Security Non plug |
| Operation: | write | Name: | DisplayName |
Value: UnionPay Security Non plug 1.0.0.5 | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\UnionPay Security Non plug |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Windows\system32\UPEditNew\uninst.exe | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\UnionPay Security Non plug |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\system32\UPEditNew\uninst.exe | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\UnionPay Security Non plug |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.5 | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\UnionPay Security Non plug |
| Operation: | write | Name: | URLInfoAbout |
Value: http://cn.unionpay.com/ | |||
| (PID) Process: | (2344) UPEditorEdge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\UnionPay Security Non plug |
| Operation: | write | Name: | Publisher |
Value: China UnionPay | |||
Executable files
12
Suspicious files
0
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | UPEditorEdge.exe | C:\Windows\system32\UPEditNew\UPService.exe | executable | |
MD5:— | SHA256:— | |||
| 2248 | Au_.exe | C:\Users\admin\AppData\Local\Temp\nsw7125.tmp\KillProcDLL.dll | — | |
MD5:— | SHA256:— | |||
| 2344 | UPEditorEdge.exe | C:\Windows\system32\UPEditNew\UPEditor.exe | executable | |
MD5:— | SHA256:— | |||
| 2536 | UPService.exe | C:\Windows\system32\drivers\etc\hosts | text | |
MD5:— | SHA256:— | |||
| 2344 | UPEditorEdge.exe | C:\Users\admin\AppData\Local\Temp\mysign.cer | der | |
MD5:— | SHA256:— | |||
| 2344 | UPEditorEdge.exe | C:\Users\admin\AppData\Local\Temp\nsd7ED4.tmp\modern-header.bmp | image | |
MD5:0CEC787E4C05B87939962D42D1CB8275 | SHA256:3DC4EF67950A1BD74595FE0A0040F4D55533A2571BCD0220682DF297C44C08D7 | |||
| 2344 | UPEditorEdge.exe | C:\Users\admin\AppData\Local\Temp\nsd7ED4.tmp\System.dll | executable | |
MD5:A436DB0C473A087EB61FF5C53C34BA27 | SHA256:75ED40311875312617D6711BAED0BE29FCAEE71031CA27A8D308A72B15A51E49 | |||
| 2344 | UPEditorEdge.exe | C:\Users\admin\AppData\Local\Temp\nsd7ED4.tmp\KillProcDLL.dll | executable | |
MD5:99F345CF51B6C3C317D20A81ACB11012 | SHA256:C2689BA1F66066AFCE85CA6457ECD36370BE0FE351C58422E45EFD0948655C93 | |||
| 2344 | UPEditorEdge.exe | C:\Users\admin\AppData\Local\Temp\certmgr.exe | executable | |
MD5:EC58A1586AD70953D48E3C393163348F | SHA256:A097CC322FA68E1FF500D79598F657D9C211E86E632C3C3B896E566852CEA991 | |||
| 2344 | UPEditorEdge.exe | C:\Windows\system32\UPEditNew\UPSecurityInput.exe | executable | |
MD5:53EFBA94E2F0C7AF55FFD350AF3C32E4 | SHA256:202404BD599BCA1D0D5BAB3646F9FC522B17CA5A7A37AEAB699E4279C1AA1E70 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
UPEditor.exe | ¸±°æ±¾ = 1 |
UPEditor.exe | ¸±°æ±¾ = 1 |
UPEditor.exe | buildnumber = 7601 |
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|