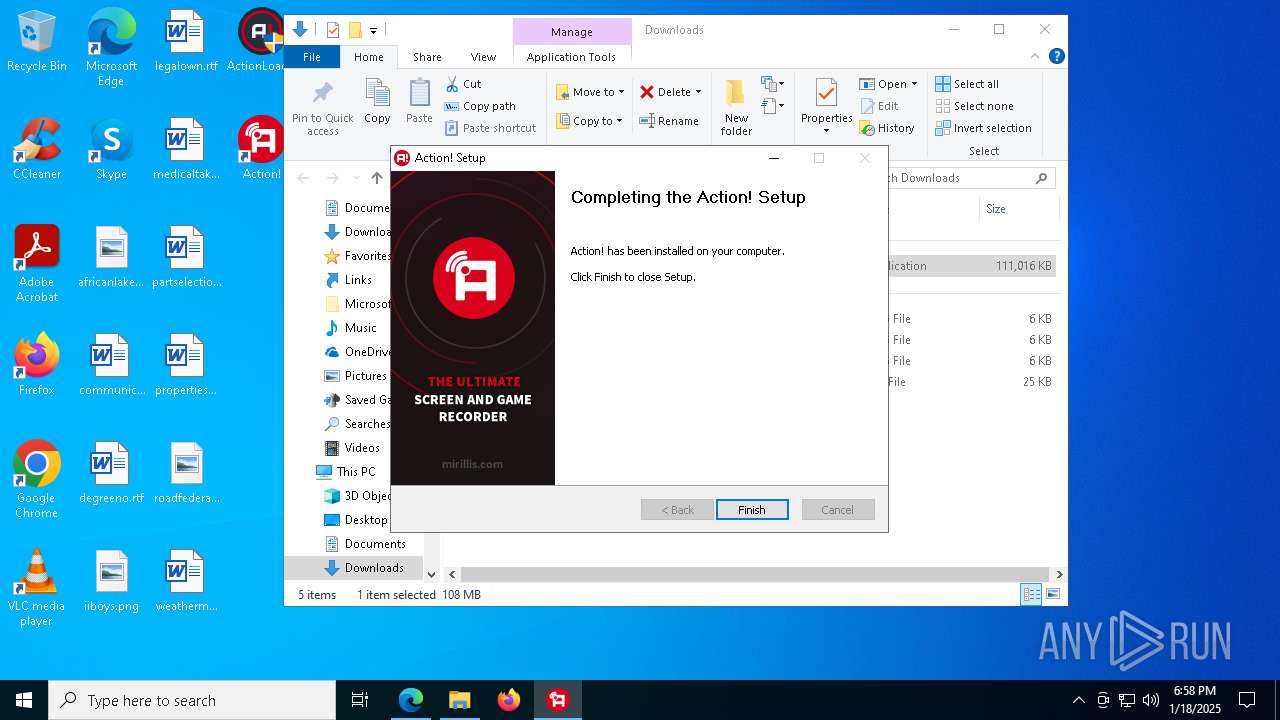
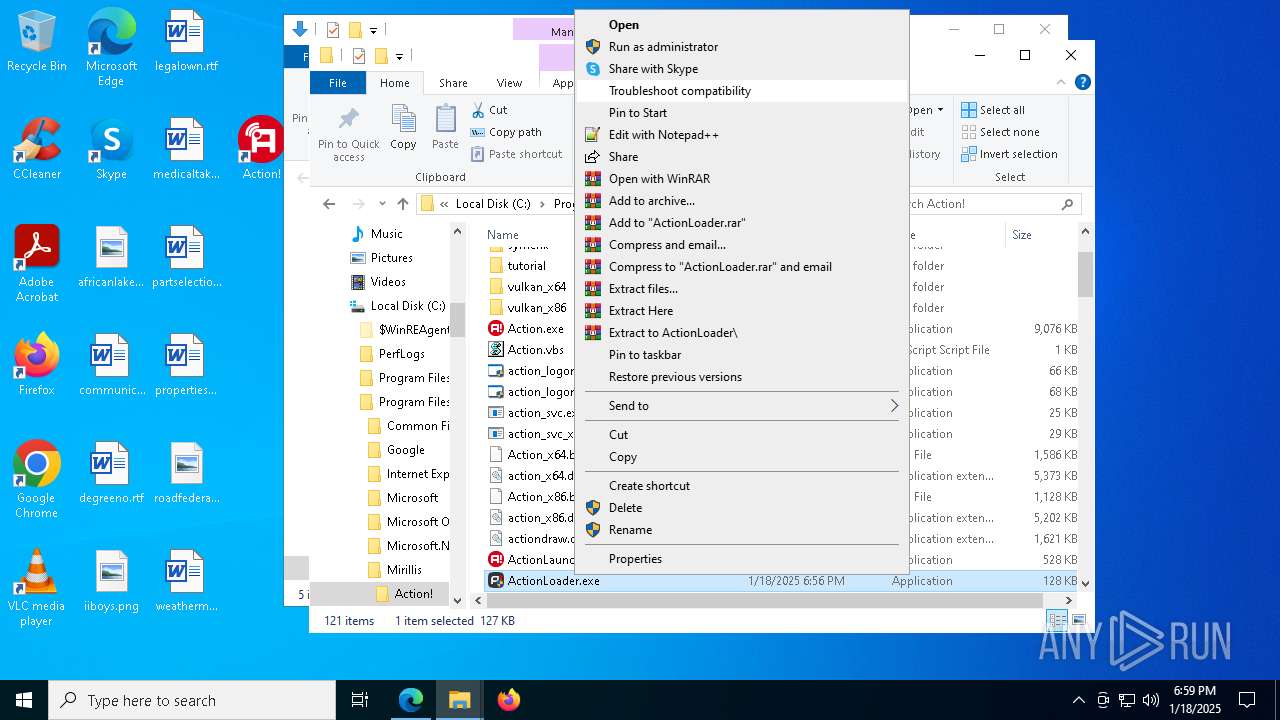
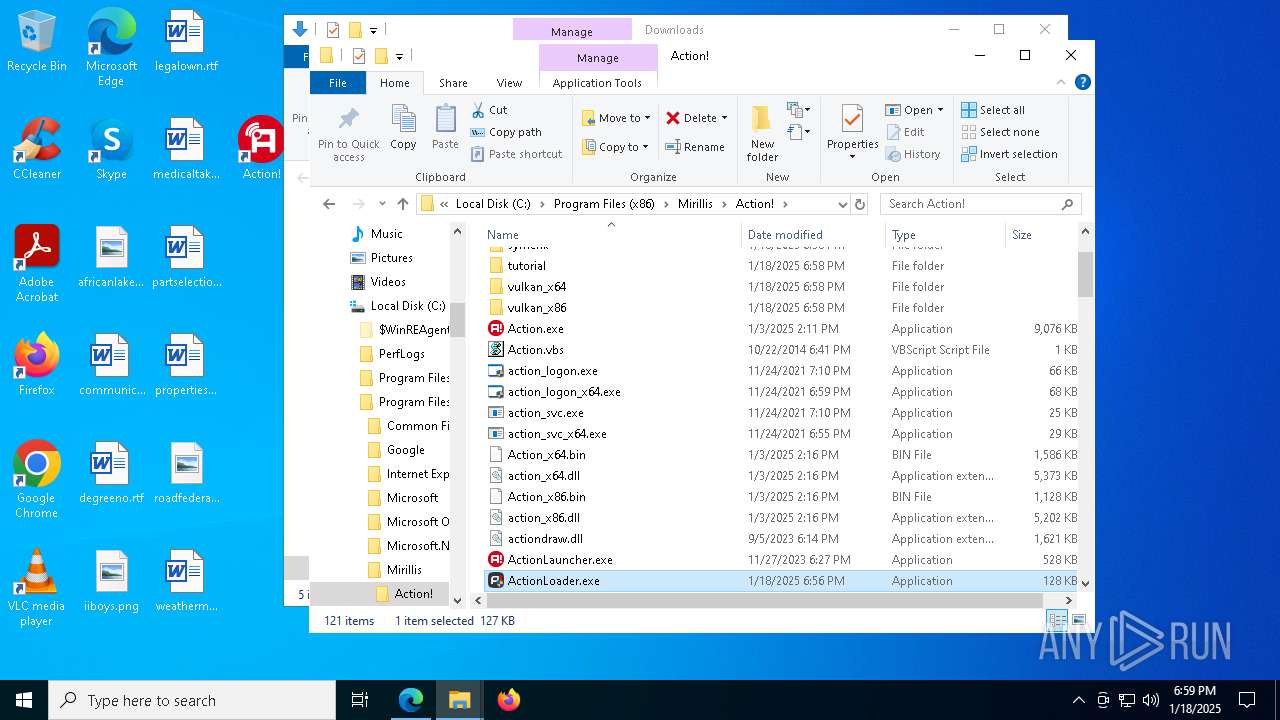
| File name: | ActionLoader.exe |
| Full analysis: | https://app.any.run/tasks/4d414cf9-c689-4c0b-9d45-b7fb54297433 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2025, 18:56:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F18A63E79C3A07FE51AE982FA705B264 |
| SHA1: | 4C25483848667606D17C0BE10E09568A34ECE303 |
| SHA256: | AFCDF863C9AC636CD7801E288E3FD3598C52078CDF9BD8AEB70FC5FFE4E80C65 |
| SSDEEP: | 1536:wNg1GaKRz5jV3uWpZJj5t5SBCBzi3i3kkpplpzEMgqnJ6Z68oACbR1RTjllb03et:wNgsaC1jV3umjQczIo/Wt7n3kXBg6 |
MALICIOUS
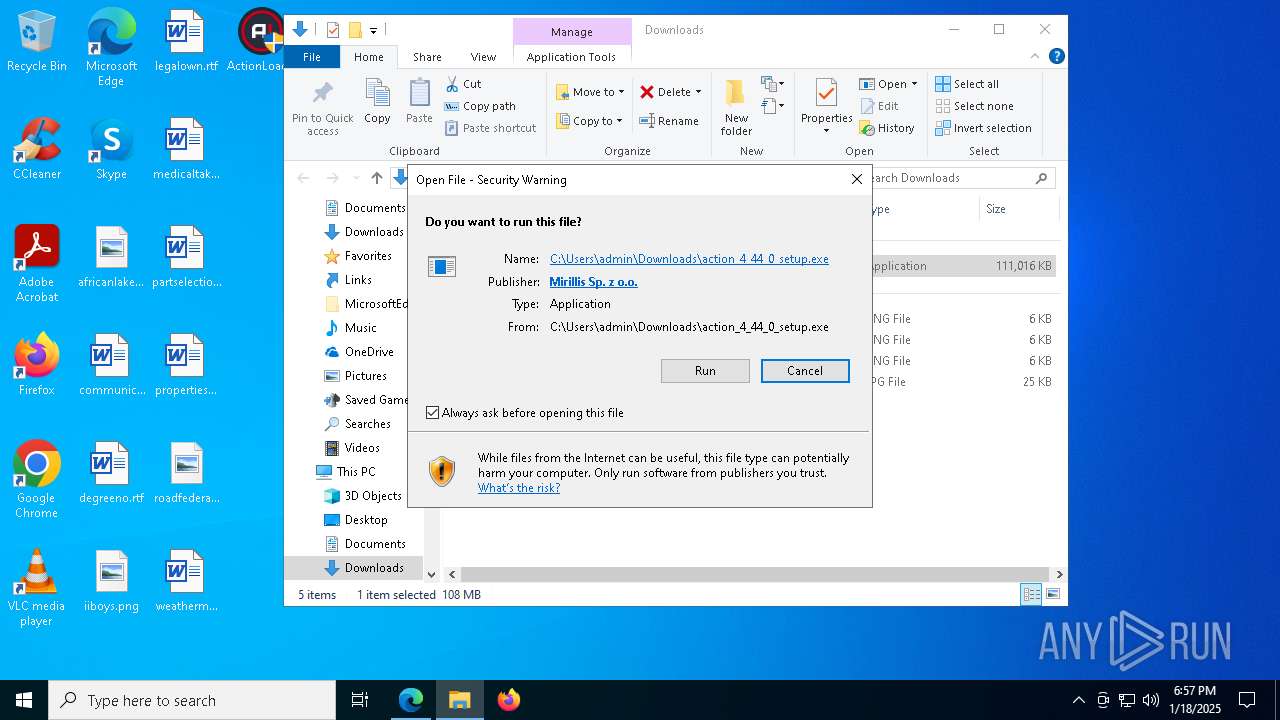
Executing a file with an untrusted certificate
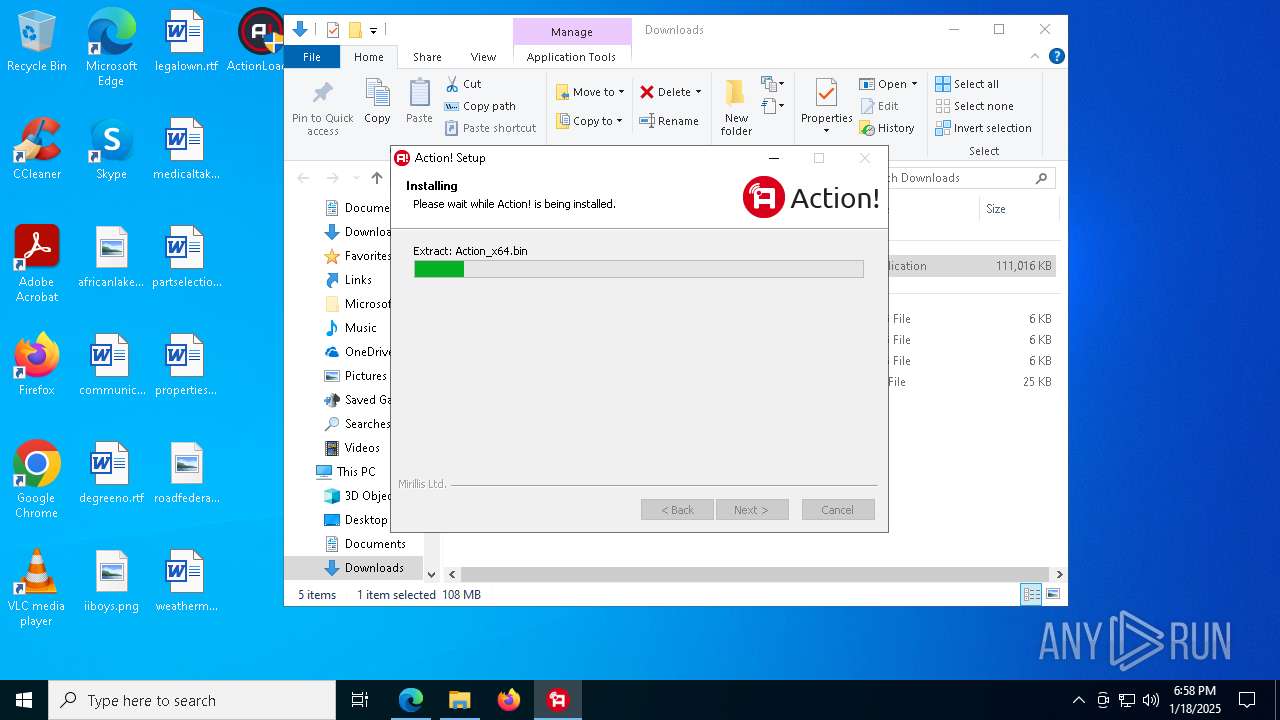
- action_setup.exe (PID: 7436)
- booter.exe (PID: 8036)
The DLL Hijacking
- symchk.exe (PID: 2152)
- symchk.exe (PID: 2012)
Runs injected code in another process
- Action_x64.bin (PID: 3820)
Application was injected by another process
- dwm.exe (PID: 912)
SUSPICIOUS
Reads security settings of Internet Explorer
- action_4_44_0_setup.exe (PID: 7336)
- action_setup.exe (PID: 7436)
- Action_x64.bin (PID: 3820)
- Action_x86.bin (PID: 2632)
- tutorial_launcher.exe (PID: 6012)
- symchk.exe (PID: 2012)
- symchk.exe (PID: 2152)
- Action.exe (PID: 4132)
The process creates files with name similar to system file names
- action_setup.exe (PID: 7436)
- ActionLoader.exe (PID: 3744)
Process drops legitimate windows executable
- action_setup.exe (PID: 7436)
Executable content was dropped or overwritten
- action_setup.exe (PID: 7436)
- dllhost.exe (PID: 5964)
- ActionLoader.exe (PID: 3744)
- Action.exe (PID: 4132)
- cmd.exe (PID: 1612)
There is functionality for taking screenshot (YARA)
- action_setup.exe (PID: 7436)
- action_4_44_0_setup.exe (PID: 7336)
- Action.exe (PID: 4132)
Malware-specific behavior (creating "System.dll" in Temp)
- action_setup.exe (PID: 7436)
The process drops C-runtime libraries
- action_setup.exe (PID: 7436)
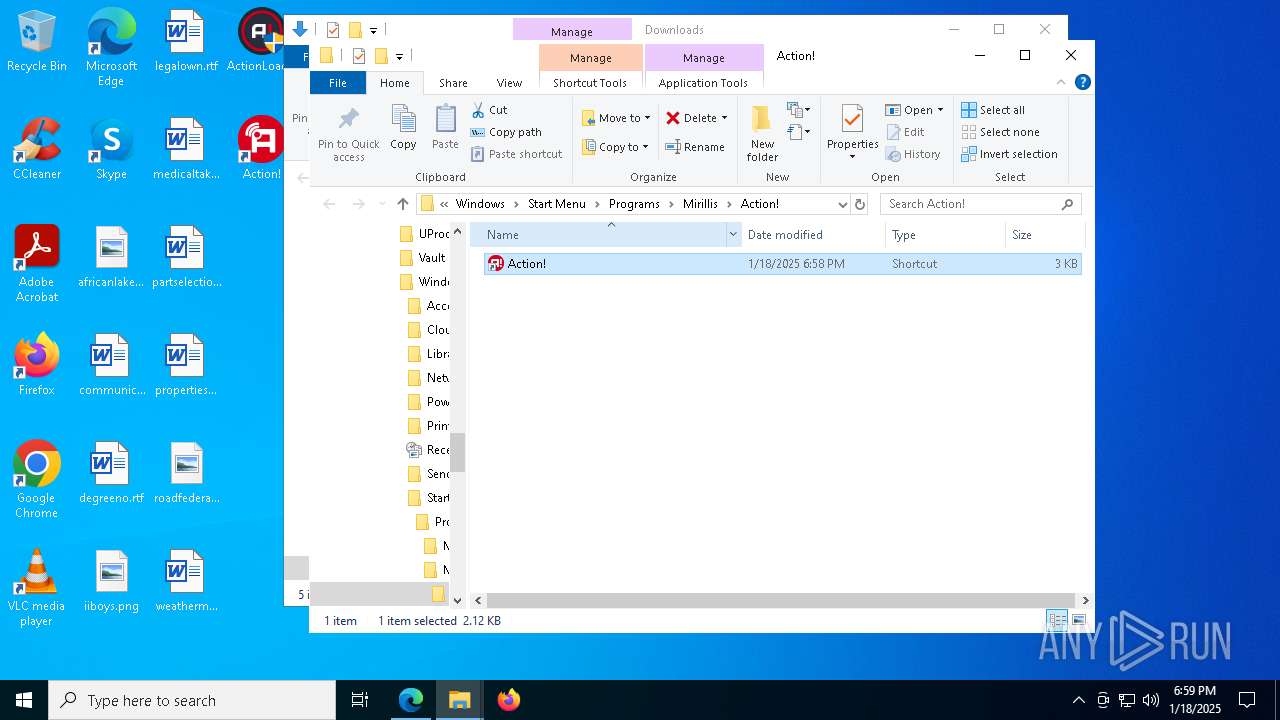
Creates a software uninstall entry
- action_setup.exe (PID: 7436)
Starts CMD.EXE for commands execution
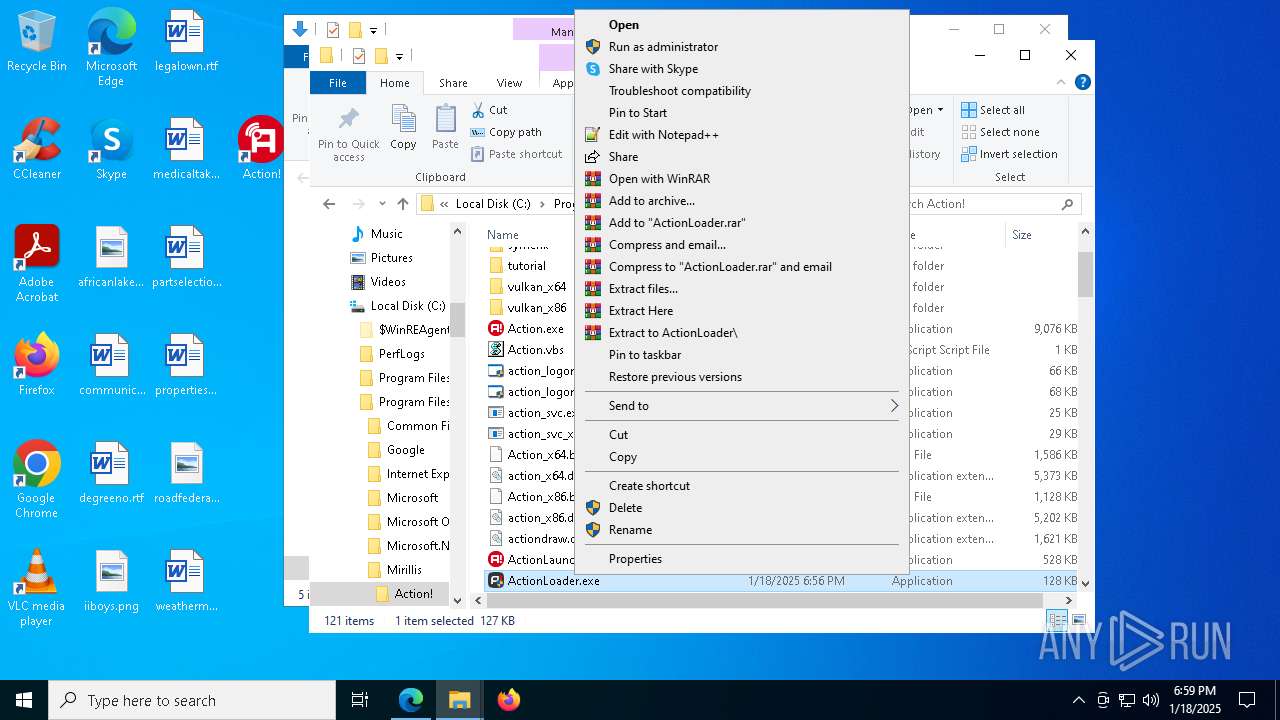
- ActionLauncher.exe (PID: 5912)
- Action_x64.bin (PID: 3820)
The process executes via Task Scheduler
- ActionLauncher.exe (PID: 7212)
Creates file in the systems drive root
- explorer.exe (PID: 4488)
Starts application with an unusual extension
- Action.exe (PID: 4132)
Reads the date of Windows installation
- Action_x64.bin (PID: 3820)
Executing commands from a ".bat" file
- Action_x64.bin (PID: 3820)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1612)
Checks Windows Trust Settings
- Action_x86.bin (PID: 2632)
- Action_x64.bin (PID: 3820)
- tutorial_launcher.exe (PID: 6012)
- symchk.exe (PID: 2152)
- symchk.exe (PID: 2012)
Reads Microsoft Outlook installation path
- tutorial_launcher.exe (PID: 6012)
Reads Internet Explorer settings
- tutorial_launcher.exe (PID: 6012)
INFO
The sample compiled with english language support
- ActionLoader.exe (PID: 6444)
- action_setup.exe (PID: 7436)
- msedge.exe (PID: 4188)
- dllhost.exe (PID: 5964)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- dllhost.exe (PID: 5964)
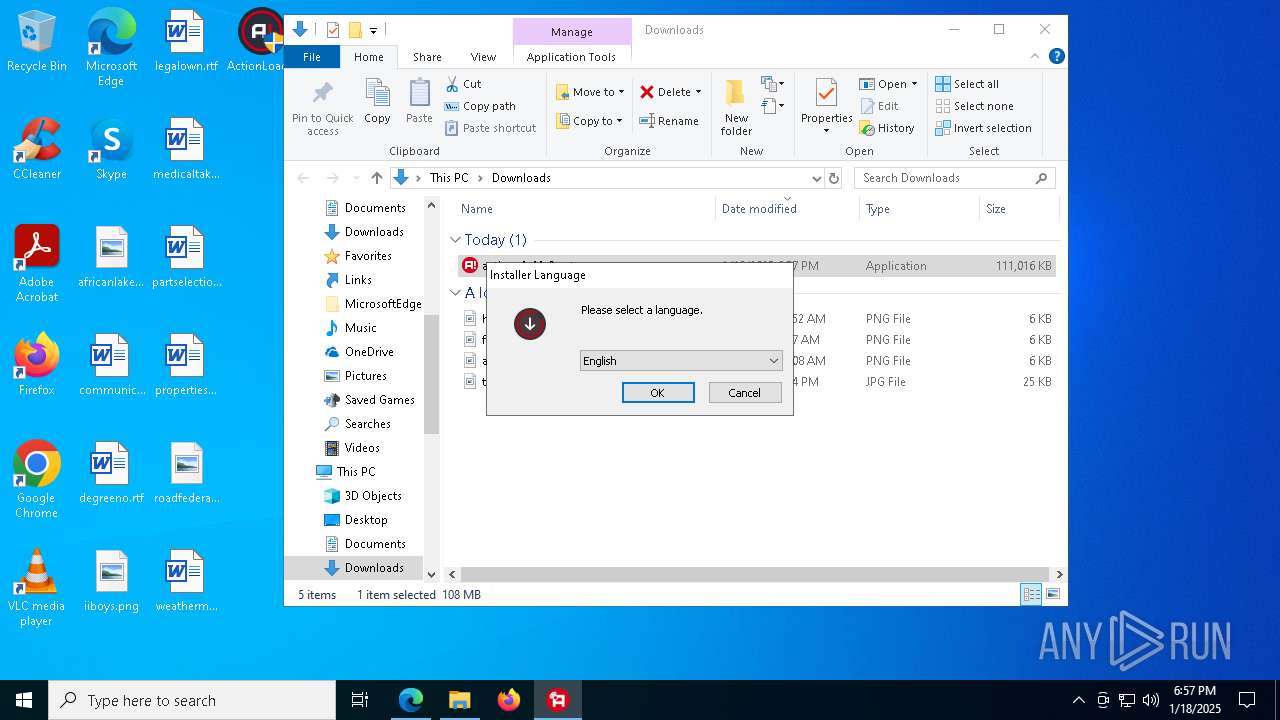
Checks supported languages
- ActionLoader.exe (PID: 6444)
- identity_helper.exe (PID: 3640)
- action_4_44_0_setup.exe (PID: 7336)
- action_setup.exe (PID: 7436)
- preinstall.exe (PID: 7544)
- ActionLauncher.exe (PID: 5912)
- booter.exe (PID: 8036)
- ActionLauncher.exe (PID: 7212)
- ActionLoader.exe (PID: 3744)
- Action.exe (PID: 4132)
- mrls_browser.bin (PID: 6912)
- mrls_browser.bin (PID: 5388)
- Action_x86.bin (PID: 2632)
- Action_x64.bin (PID: 3820)
- tscap.bin (PID: 6720)
- tutorial_launcher.exe (PID: 6012)
- AGHelper_x86.exe (PID: 2424)
- AGHelper_x64.exe (PID: 1076)
- symchk.exe (PID: 2012)
- symchk.exe (PID: 2152)
- vlc.exe (PID: 8108)
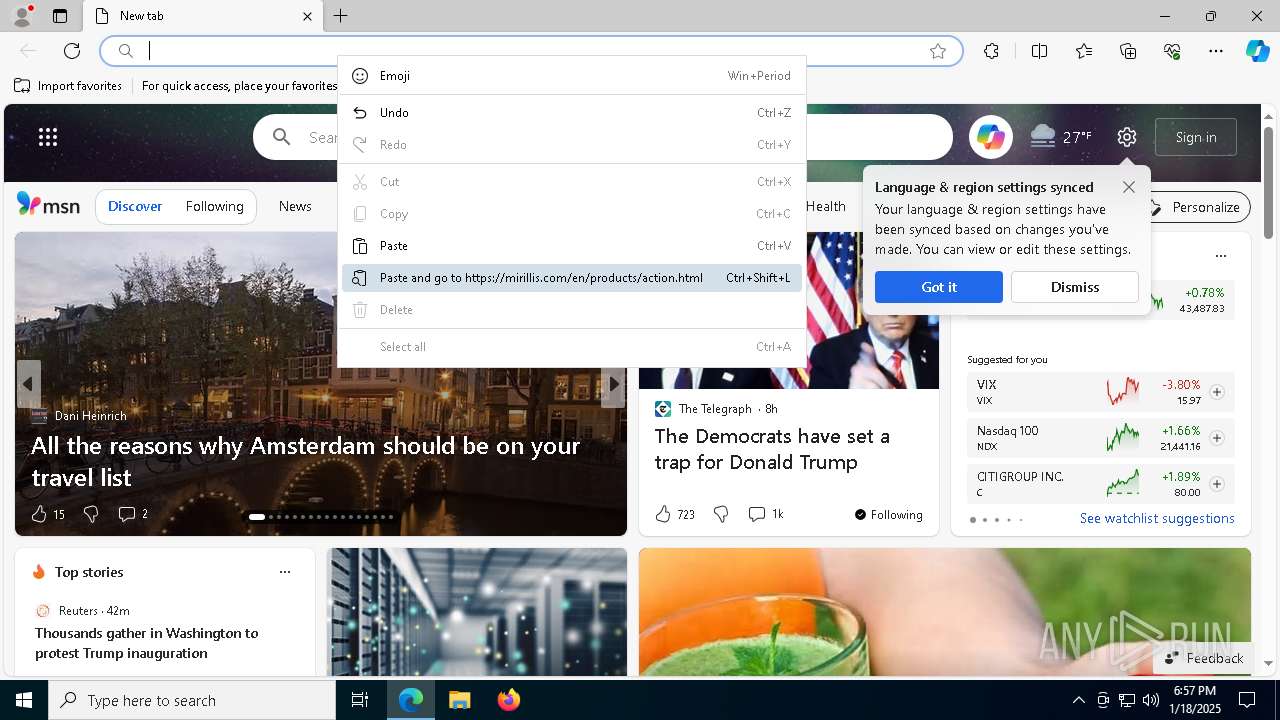
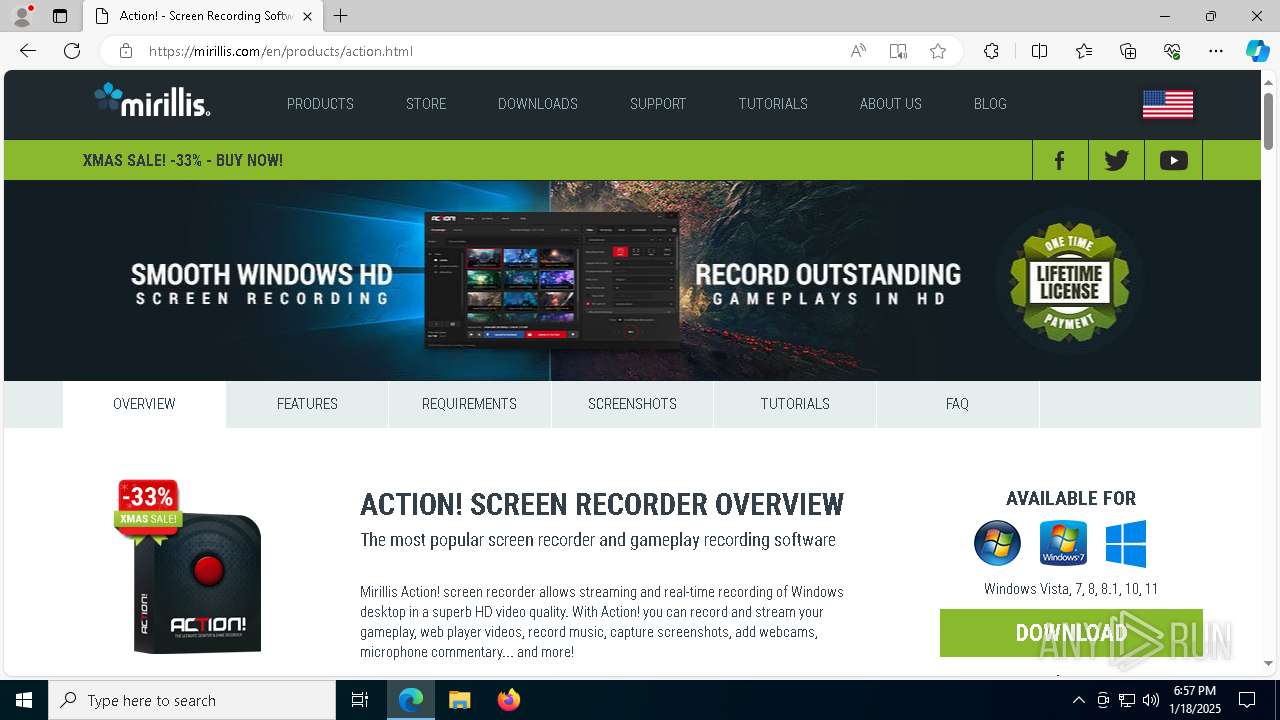
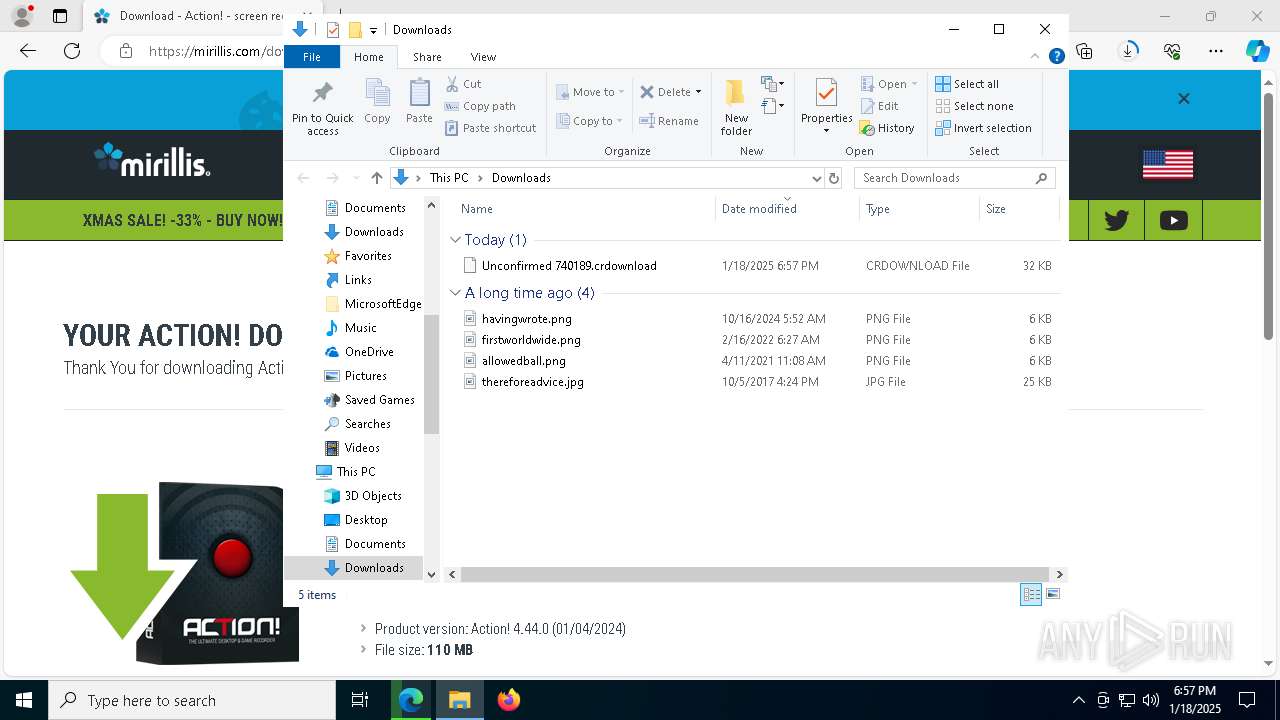
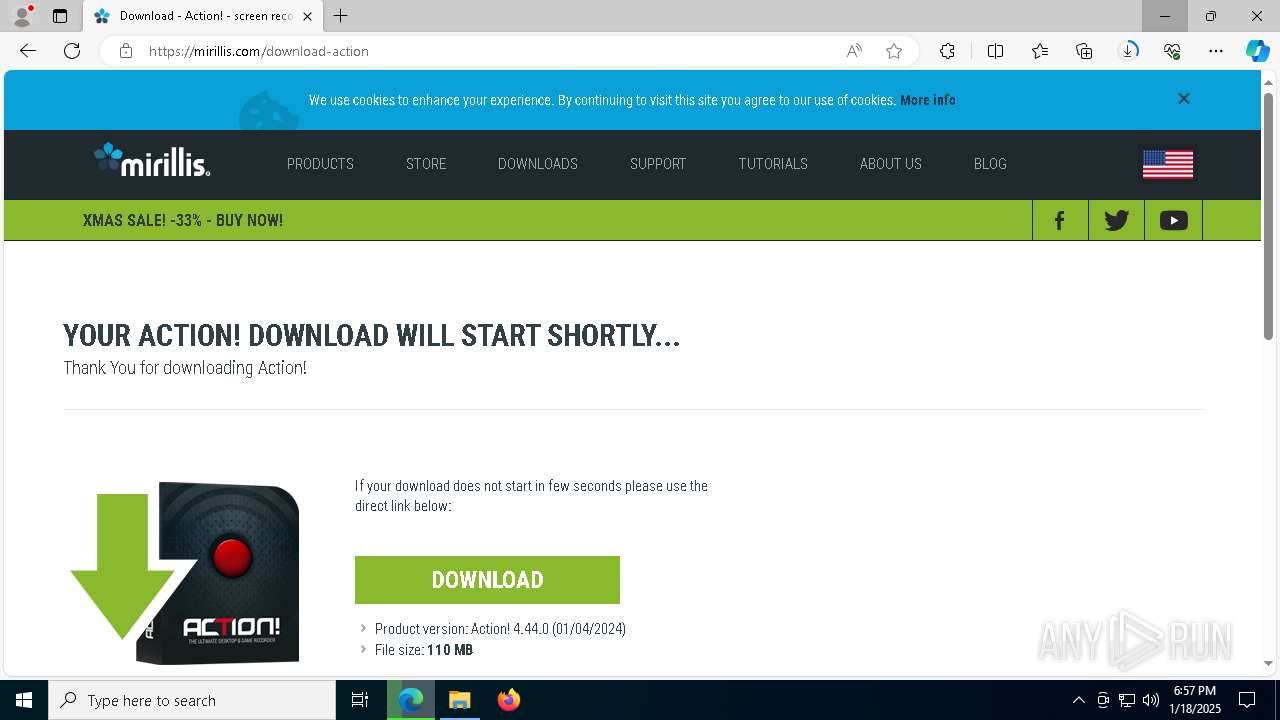
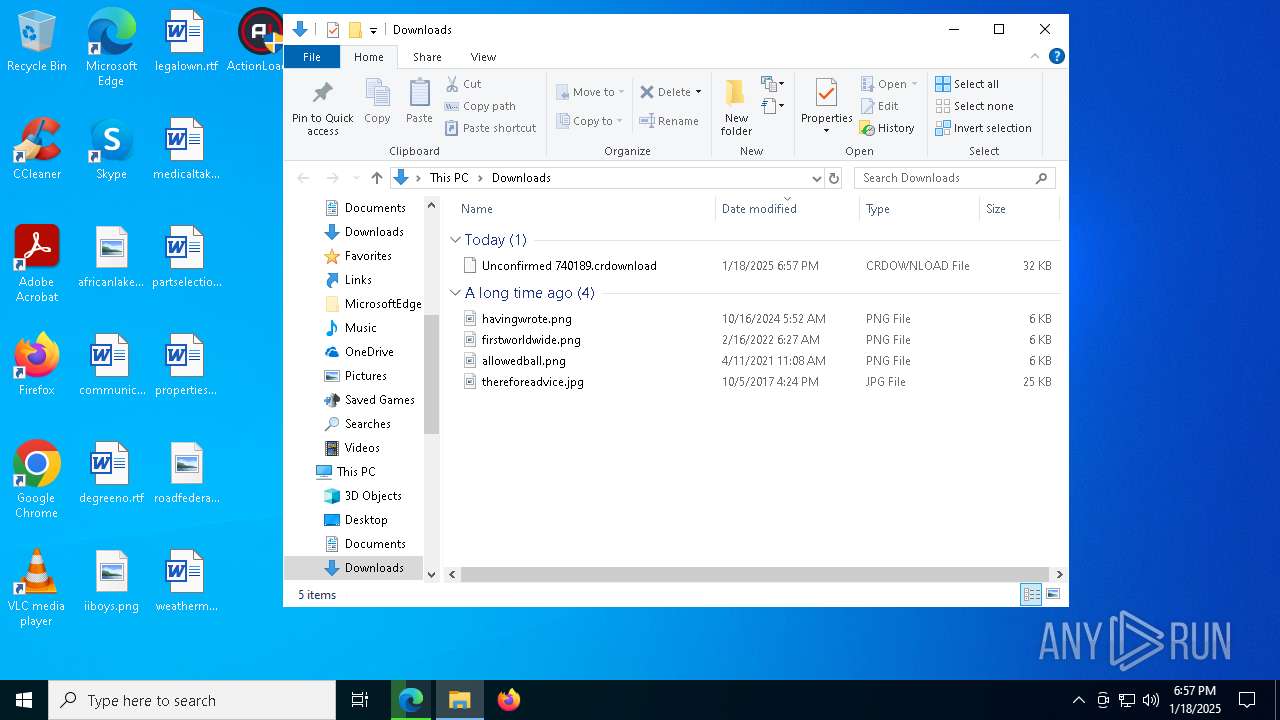
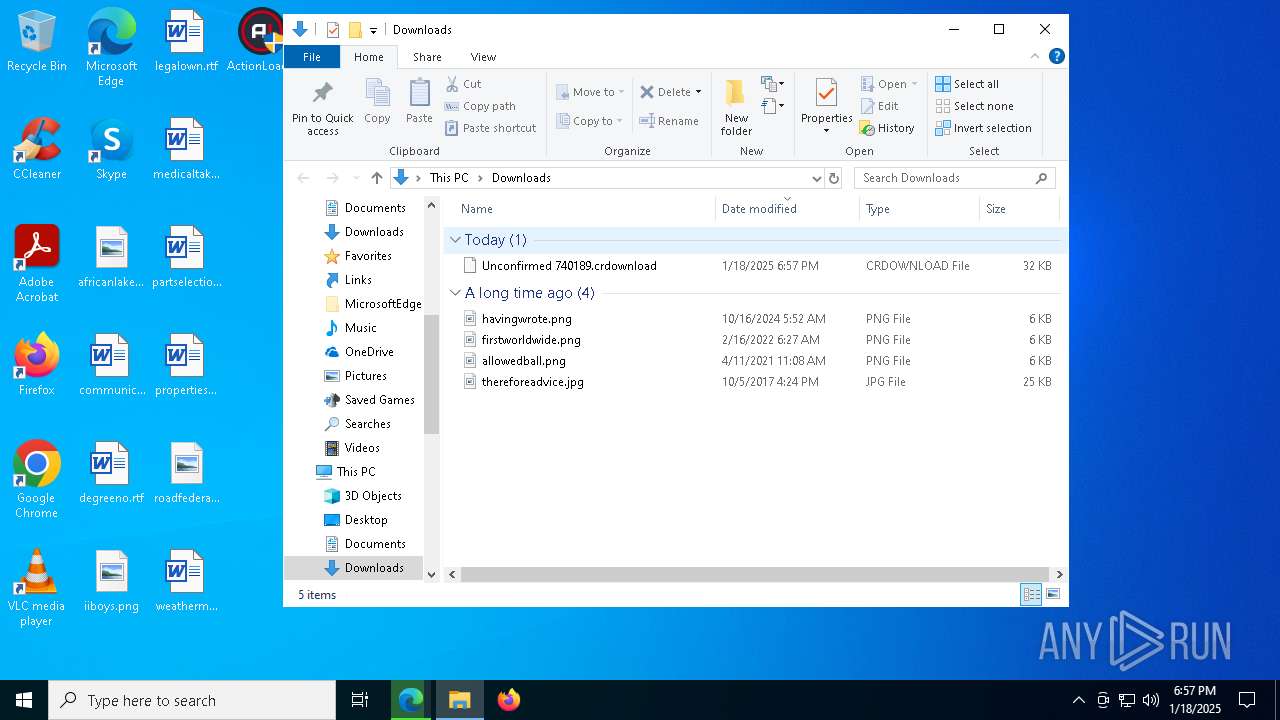
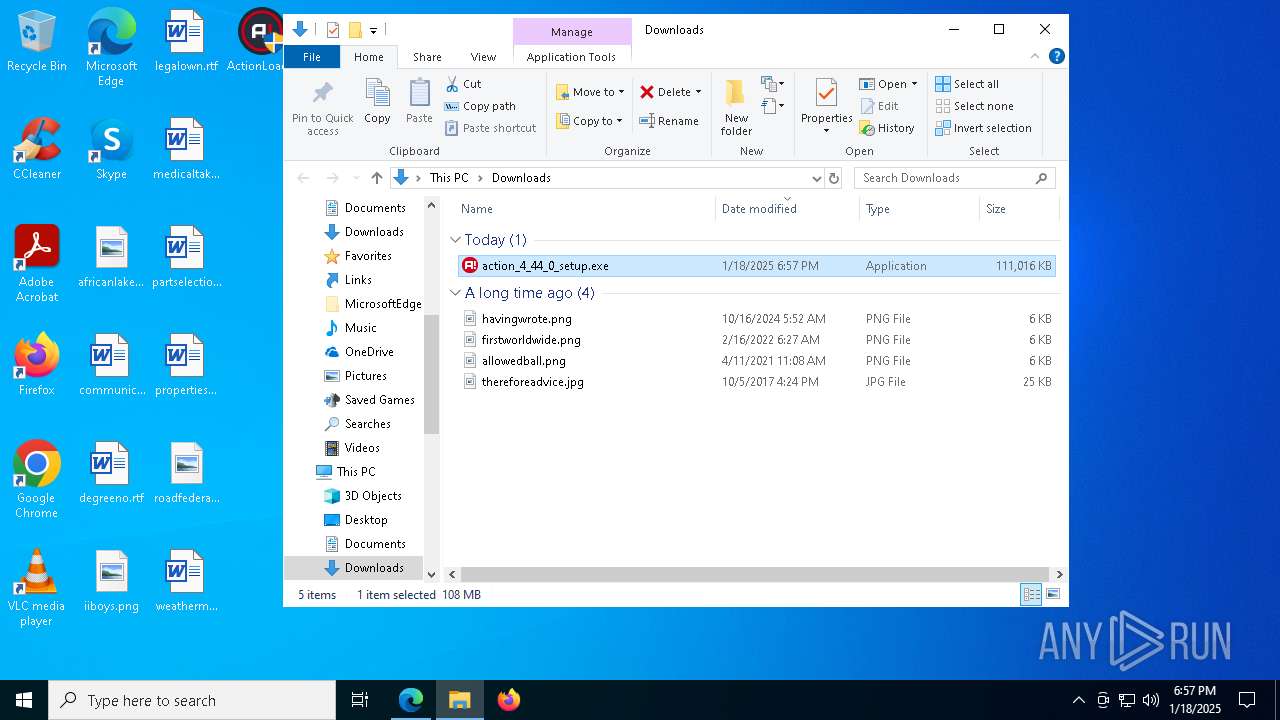
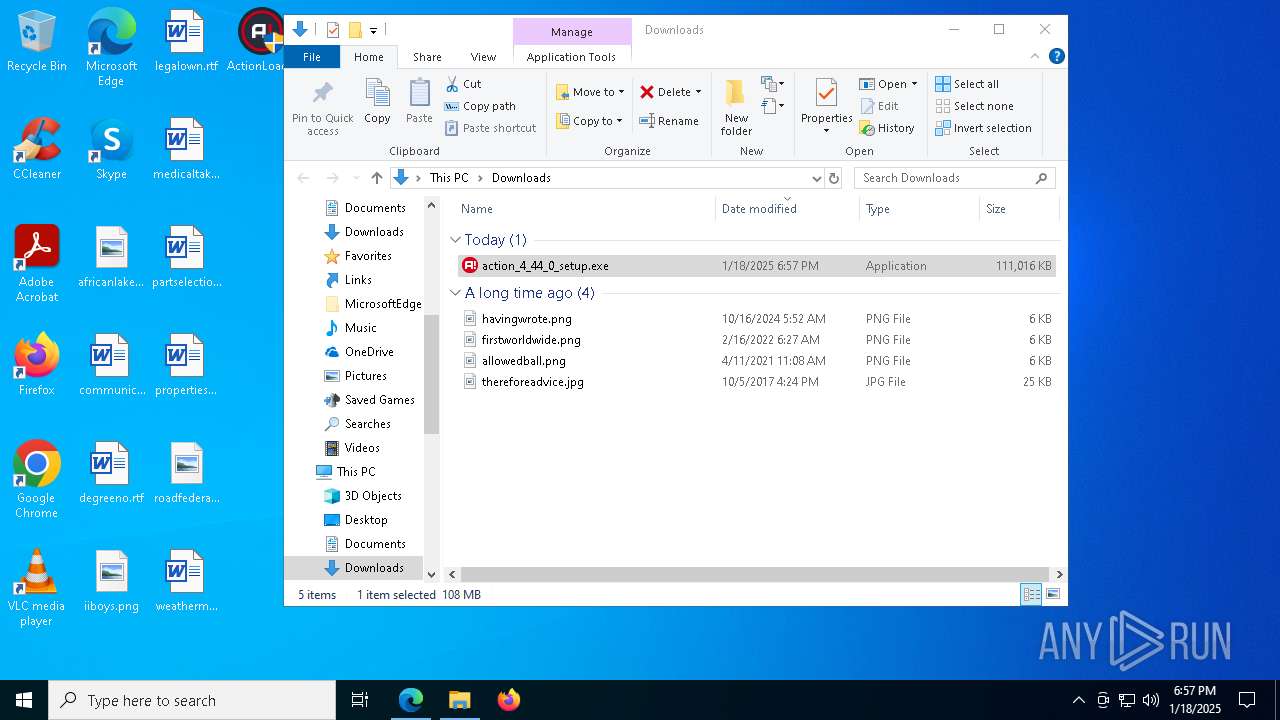
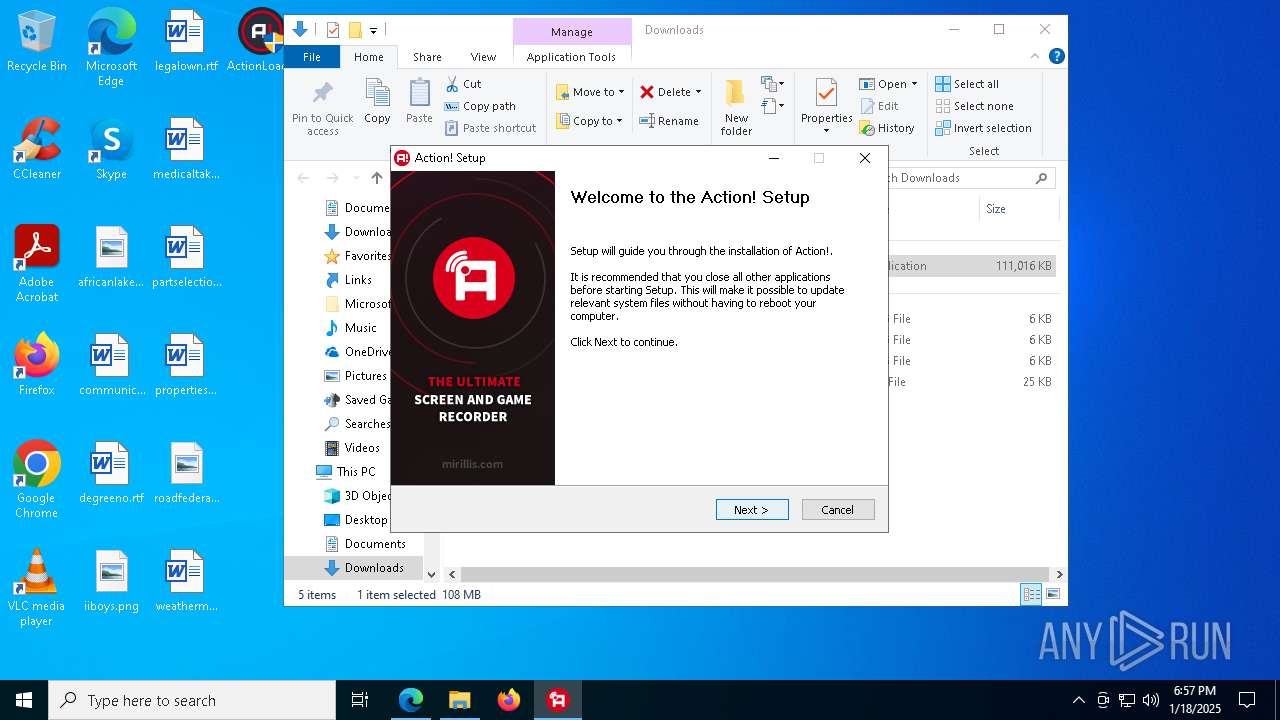
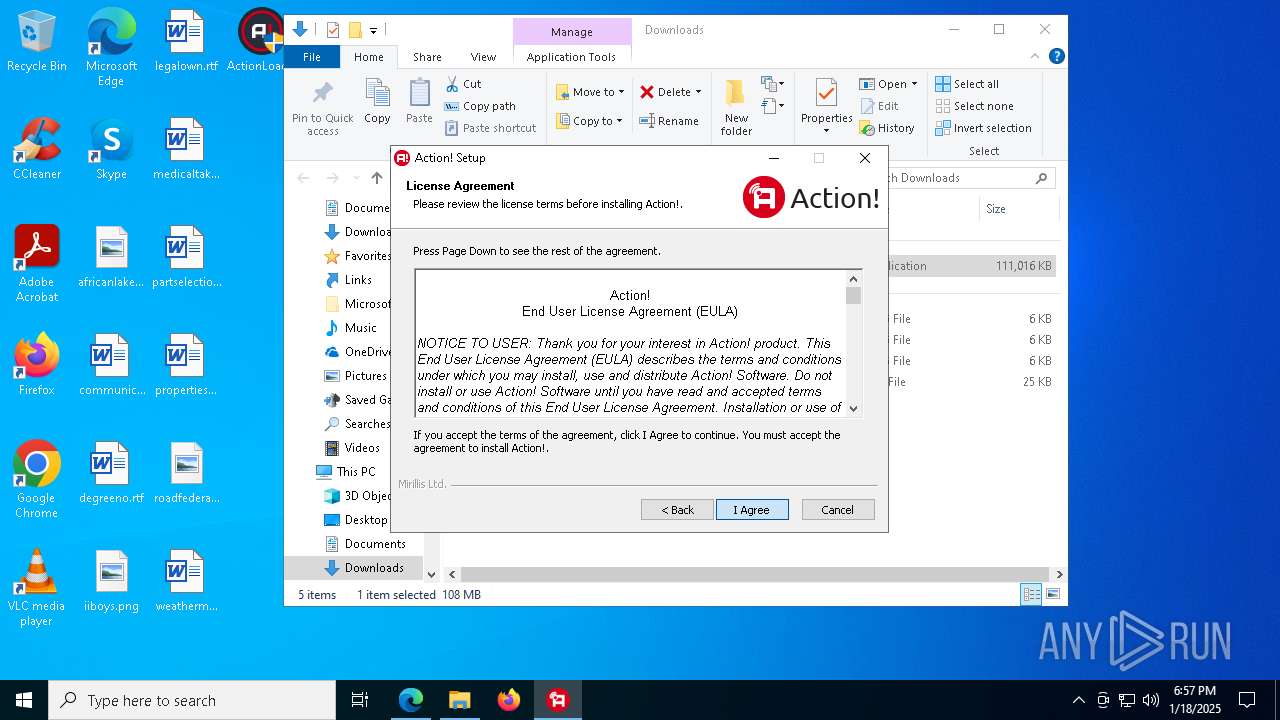
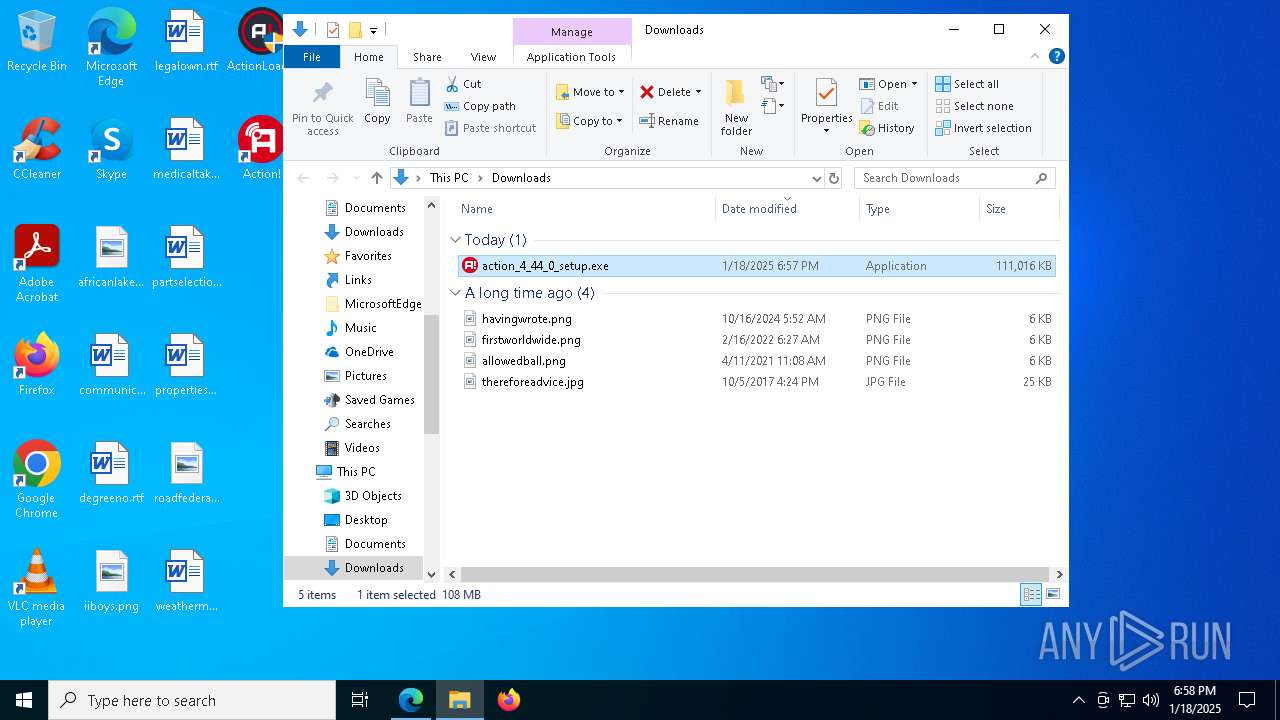
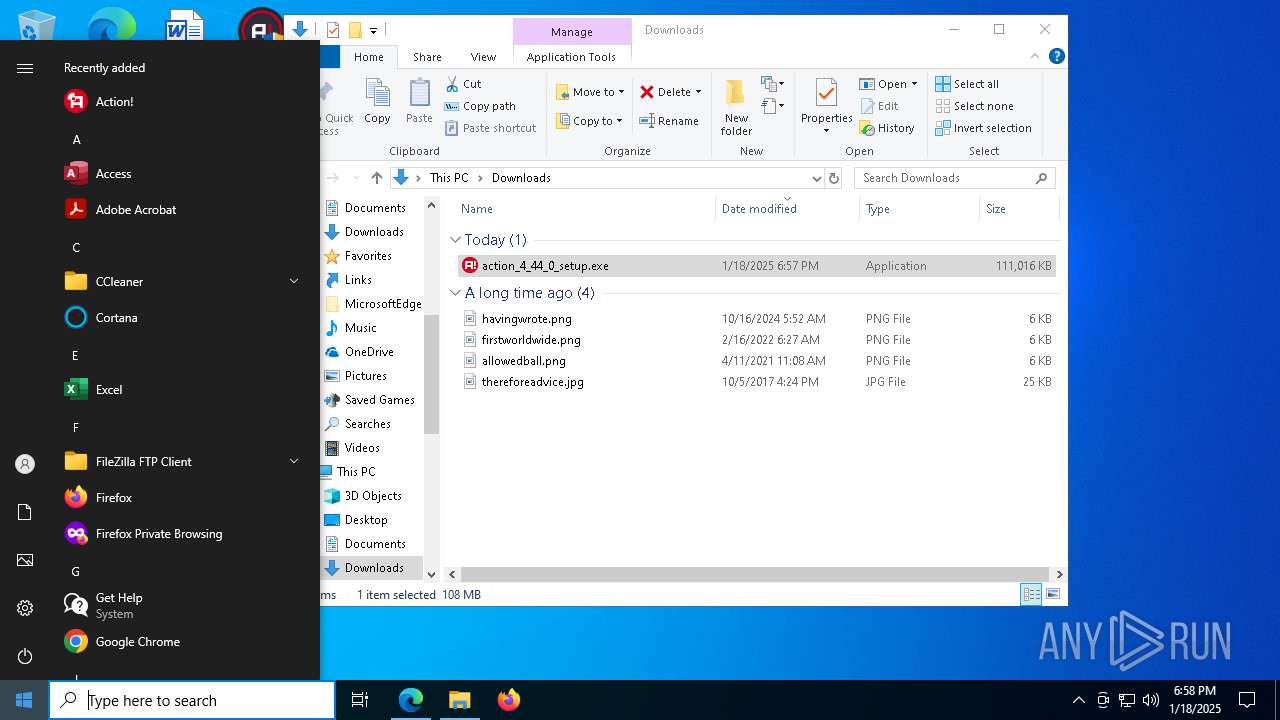
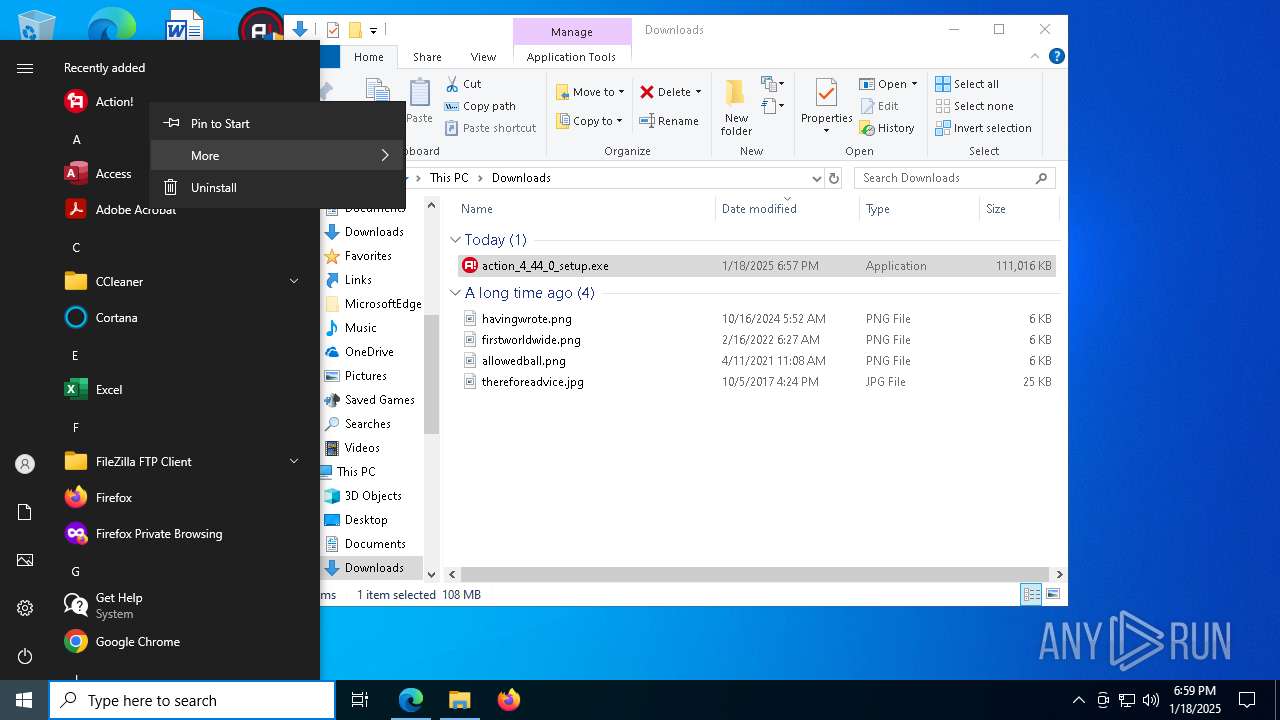
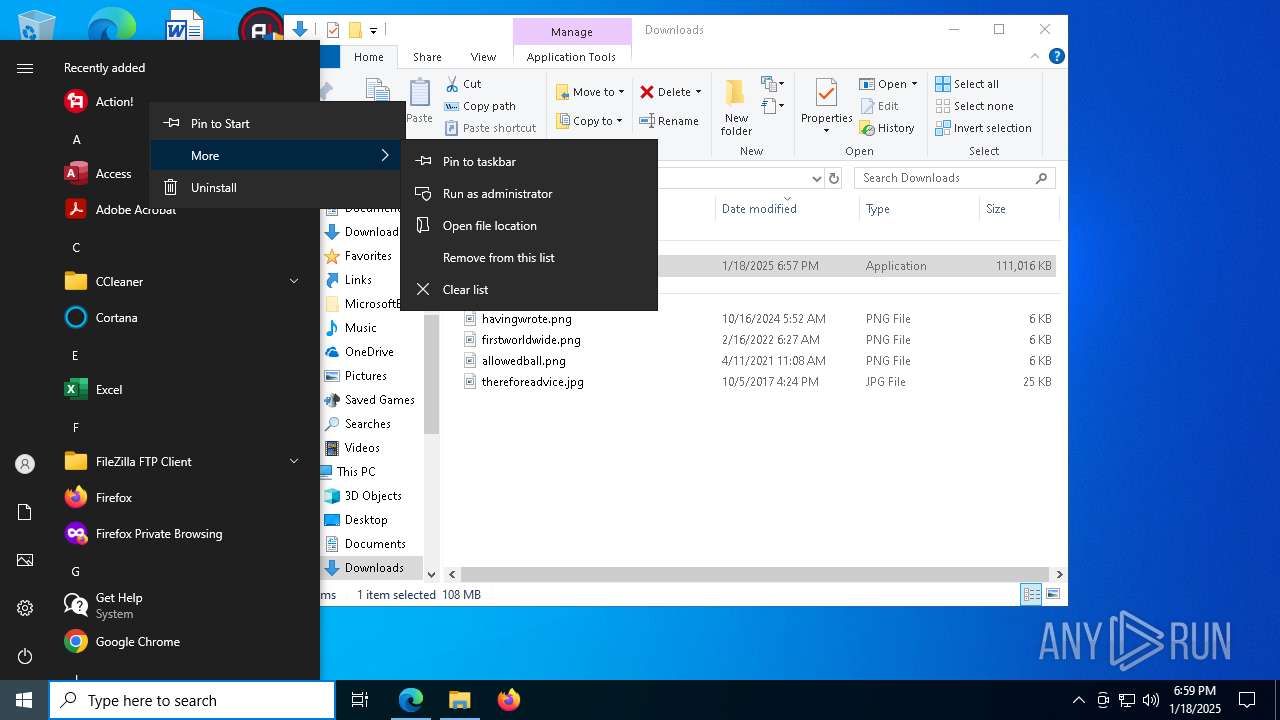
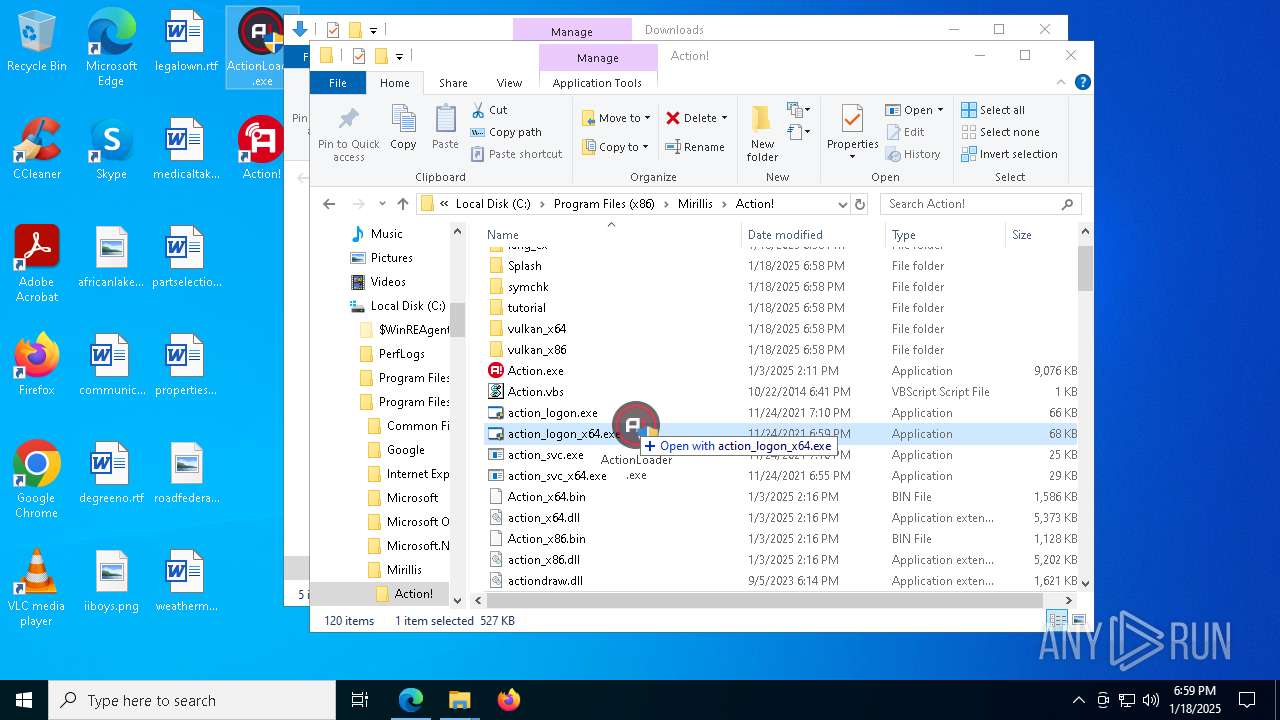
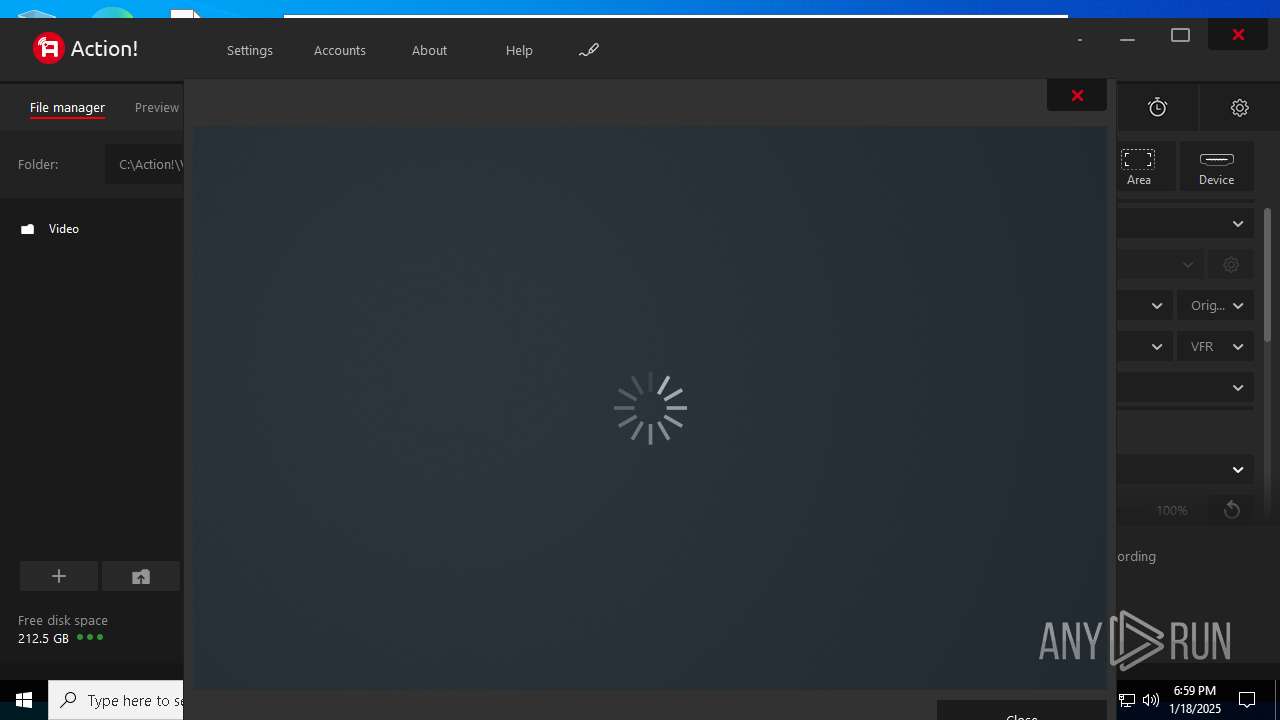
Manual execution by a user
- msedge.exe (PID: 6944)
The process uses the downloaded file
- explorer.exe (PID: 4488)
- msedge.exe (PID: 7260)
- action_4_44_0_setup.exe (PID: 7336)
- Action_x64.bin (PID: 3820)
- Action.exe (PID: 4132)
Executable content was dropped or overwritten
- msedge.exe (PID: 6944)
- msedge.exe (PID: 4188)
Checks proxy server information
- explorer.exe (PID: 4488)
- Action.exe (PID: 4132)
- Action_x64.bin (PID: 3820)
- Action_x86.bin (PID: 2632)
- symchk.exe (PID: 2152)
- symchk.exe (PID: 2012)
- tutorial_launcher.exe (PID: 6012)
Reads the computer name
- ActionLoader.exe (PID: 6444)
- identity_helper.exe (PID: 3640)
- action_4_44_0_setup.exe (PID: 7336)
- action_setup.exe (PID: 7436)
- preinstall.exe (PID: 7544)
- ActionLauncher.exe (PID: 5912)
- Action.exe (PID: 4132)
- mrls_browser.bin (PID: 6912)
- mrls_browser.bin (PID: 5388)
- Action_x86.bin (PID: 2632)
- Action_x64.bin (PID: 3820)
- ActionLauncher.exe (PID: 7212)
- tutorial_launcher.exe (PID: 6012)
- symchk.exe (PID: 2012)
- symchk.exe (PID: 2152)
- AGHelper_x64.exe (PID: 1076)
- AGHelper_x86.exe (PID: 2424)
- vlc.exe (PID: 8108)
Application launched itself
- msedge.exe (PID: 6944)
Reads the software policy settings
- explorer.exe (PID: 4488)
- Action_x86.bin (PID: 2632)
- symchk.exe (PID: 2012)
- symchk.exe (PID: 2152)
- tutorial_launcher.exe (PID: 6012)
- dwm.exe (PID: 912)
- Action.exe (PID: 4132)
- Action_x64.bin (PID: 3820)
Reads Environment values
- identity_helper.exe (PID: 3640)
- Action_x64.bin (PID: 3820)
Create files in a temporary directory
- action_4_44_0_setup.exe (PID: 7336)
- action_setup.exe (PID: 7436)
- ActionLoader.exe (PID: 3744)
Process checks computer location settings
- action_4_44_0_setup.exe (PID: 7336)
- Action_x64.bin (PID: 3820)
- Action.exe (PID: 4132)
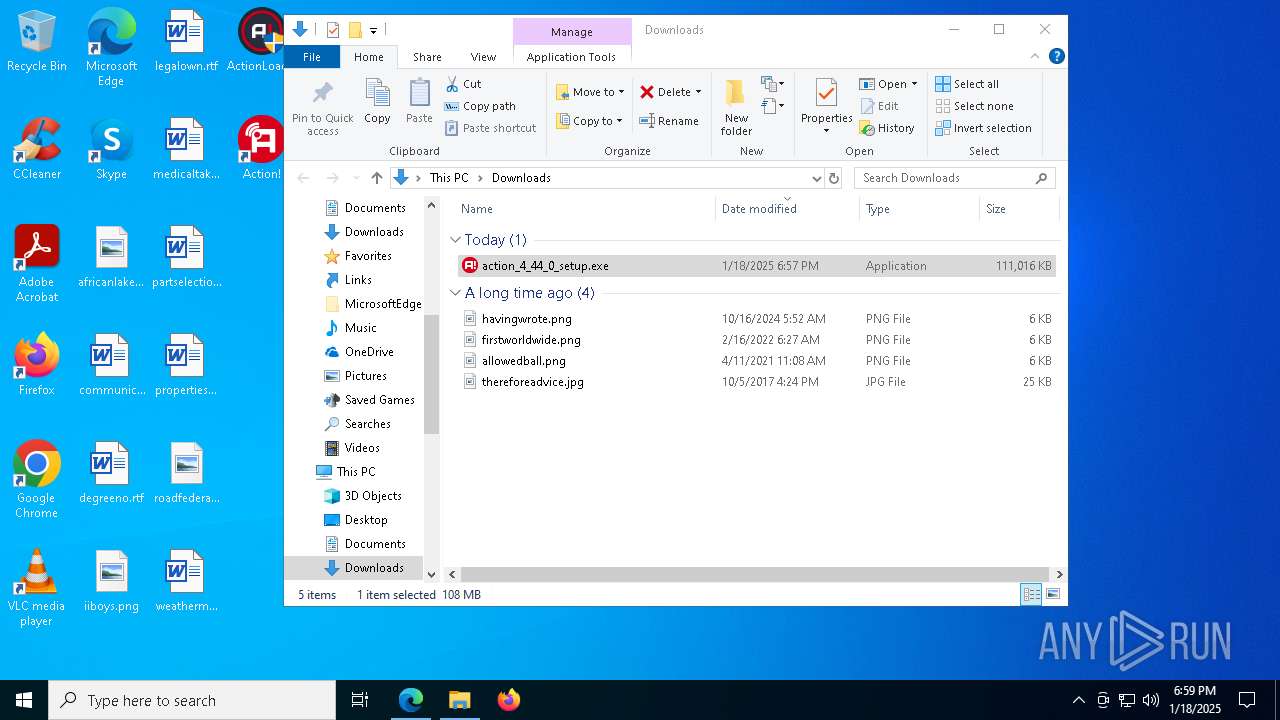
Creates files or folders in the user directory
- action_setup.exe (PID: 7436)
- explorer.exe (PID: 4488)
- Action_x64.bin (PID: 3820)
- Action.exe (PID: 4132)
- Action_x86.bin (PID: 2632)
- symchk.exe (PID: 2012)
- symchk.exe (PID: 2152)
- tutorial_launcher.exe (PID: 6012)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 4488)
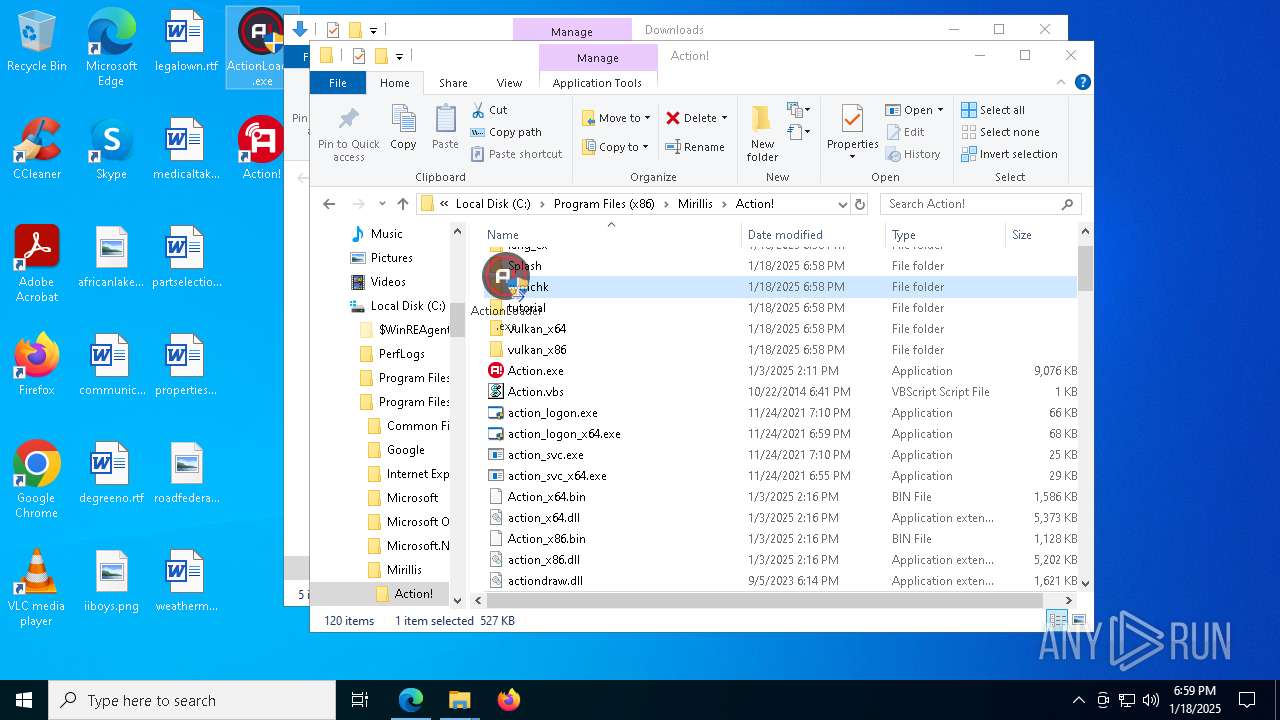
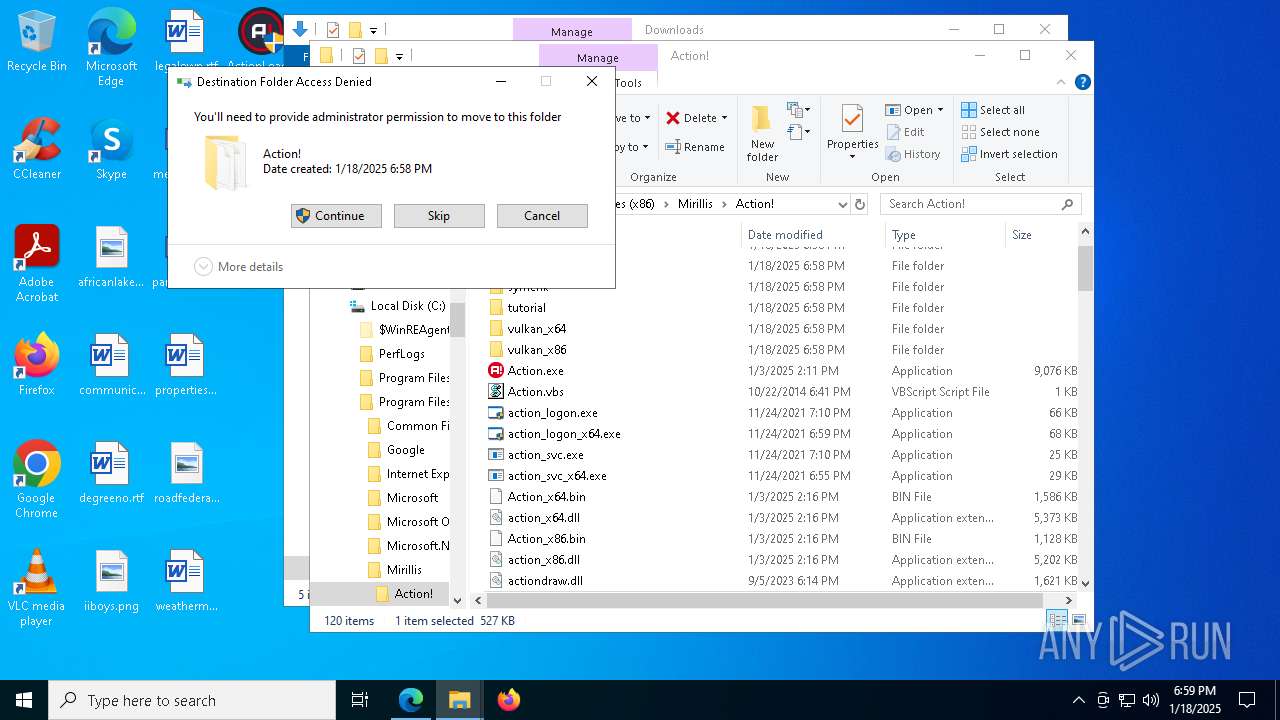
Creates files in the program directory
- action_setup.exe (PID: 7436)
- ActionLoader.exe (PID: 3744)
- Action.exe (PID: 4132)
- symchk.exe (PID: 2152)
- symchk.exe (PID: 2012)
Sends debugging messages
- Action.exe (PID: 4132)
- AGHelper_x86.exe (PID: 2424)
- AGHelper_x64.exe (PID: 1076)
- vlc.exe (PID: 8108)
Reads the machine GUID from the registry
- Action.exe (PID: 4132)
- Action_x64.bin (PID: 3820)
- Action_x86.bin (PID: 2632)
- tutorial_launcher.exe (PID: 6012)
- symchk.exe (PID: 2152)
- symchk.exe (PID: 2012)
The process uses Lua
- Action.exe (PID: 4132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 00:33:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x333d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | CheshireCat |
| FileDescription: | Action! Loader |
| FileVersion: | 4.0.0.0 |
| LegalCopyright: | © CheshireCat |
| ProductName: | Action! Loader |
| ProductVersion: | 4.0.0.0 |
Total processes
239
Monitored processes
99
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | symchk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | symchk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 912 | "dwm.exe" | C:\Windows\System32\dwm.exe | winlogon.exe | ||||||||||||
User: DWM-1 Company: Microsoft Corporation Integrity Level: SYSTEM Description: Desktop Window Manager Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
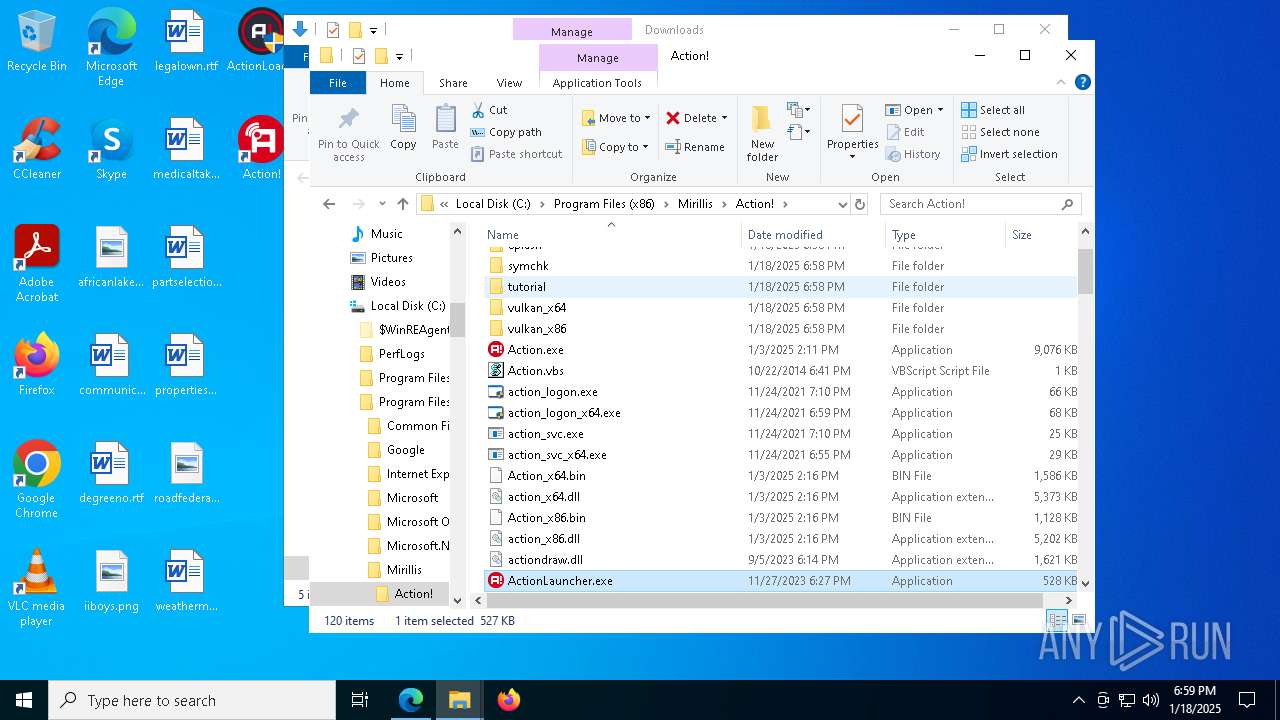
| 1076 | AGHelper_x64.exe | C:\Program Files (x86)\Mirillis\Action!\AGHelper_x64.exe | Action.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1220 | /c C:\WINDOWS\system32\schtasks.exe /End /TN "ActionLauncher_admin" | C:\Windows\SysWOW64\cmd.exe | — | ActionLauncher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5544 --field-trial-handle=2392,i,8073035278091590424,15550490229278083030,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1612 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files (x86)\Mirillis\Action!\register_ficv_codec.bat" " | C:\Windows\System32\cmd.exe | Action_x64.bin | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5672 --field-trial-handle=2392,i,8073035278091590424,15550490229278083030,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1688 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6496 --field-trial-handle=2392,i,8073035278091590424,15550490229278083030,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
79 349
Read events
79 054
Write events
277
Delete events
18
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000000000009089180C | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000006035A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 76F98B6700000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010013000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C00000013000000000000006100660072006900630061006E006C0061006B0065002E0070006E0067003E002000200000001F0000000000000063006F006D006D0075006E00690063006100740069006F006E007300630075007200720065006E0074006C0079002E007200740066003E0020002000000010000000000000006400650067007200650065006E006F002E007200740066003E002000200000000E000000000000006900690062006F00790073002E0070006E0067003E0020002000000010000000000000006C006500670061006C006F0077006E002E007200740066003E0020002000000014000000000000006D00650064006900630061006C00740061006B00650073002E007200740066003E0020002000000015000000000000007000610072007400730065006C0065006300740069006F006E002E007200740066003E002000200000001A00000000000000700072006F0070006500720074006900650073007100750065007300740069006F006E002E007200740066003E00200020000000130000000000000072006F00610064006600650064006500720061006C002E006A00700067003E00200020000000190000000000000077006500610074006800650072006D0061006E006100670065006D0065006E0074002E007200740066003E00200020000000140000000000000041006300740069006F006E004C006F0061006400650072002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001300000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A0401100000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000004040000000001200 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisible |
Value: 1 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisibleOnAnyMonitor |
Value: 1 | |||
| (PID) Process: | (6444) ActionLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | C:\Users\admin\Desktop\ActionLoader.exe |
Value: | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000006035A |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppLaunch |
| Operation: | write | Name: | MSEdge |
Value: 12 | |||
Executable files
263
Suspicious files
1 081
Text files
321
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF139108.TMP | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF139108.TMP | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF139137.TMP | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF139137.TMP | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF139108.TMP | — | |
MD5:— | SHA256:— | |||
| 6944 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
78
TCP/UDP connections
156
DNS requests
158
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7696 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7696 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 2.21.65.130:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQC78My1t7gx%2FSGuMneK5AyJ | unknown | — | — | whitelisted |
2216 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1737529402&P2=404&P3=2&P4=EpgLFmzWrX68X5WNfFqiUldQds%2fPoPaSm6q9HcZZC%2btPZnGNoPKuhfh0q7ZZA0DqqV%2bEnFh6aIU19fjDoHNAqA%3d%3d | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 95.100.110.12:80 | http://cevcsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR2rKuShFxBxX%2BVZ%2F8jiOwbsyptXQQUrFfKCBbcP8UxHApN2%2Fvx3pknLTQCEDrnzkqfP7Ac8GV%2FItcVHnw%3D | unknown | — | — | unknown |
2216 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1737529402&P2=404&P3=2&P4=EpgLFmzWrX68X5WNfFqiUldQds%2fPoPaSm6q9HcZZC%2btPZnGNoPKuhfh0q7ZZA0DqqV%2bEnFh6aIU19fjDoHNAqA%3d%3d | unknown | — | — | whitelisted |
2216 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1737529402&P2=404&P3=2&P4=EpgLFmzWrX68X5WNfFqiUldQds%2fPoPaSm6q9HcZZC%2btPZnGNoPKuhfh0q7ZZA0DqqV%2bEnFh6aIU19fjDoHNAqA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1468 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1076 | svchost.exe | 2.23.242.9:443 | go.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
Process | Message |
|---|---|
Action.exe | 2025-01-18 18:59:28.256 C14 [AMFEncoderVCE] Error: ..\..\..\..\..\impl\components\EncoderVCE\EncoderVCEImpl.cpp(901):AMF_ERROR 36 : AMF_ENCODER_NOT_PRESENT: InitAveService() Failed to create AVE Service. AVE error = 0x80000000
|
Action.exe | 2025-01-18 18:59:28.256 C14 [AMFEncoderVCE] Error: ..\..\..\..\..\impl\components\EncoderVCE\EncoderVCEImpl.cpp(569):AMF_ERROR 36 : AMF_ENCODER_NOT_PRESENT: Prepare() - Failed to init the AVE service
|
AGHelper_x64.exe | DBGHELP: audioses - public symbols
C:\Program Files (x86)\Mirillis\Action!\symchk\symbols\audioses.pdb\EFC9FBF8150FC0304755B84EE78792BB1\audioses.pdb
|
AGHelper_x86.exe | DBGHELP: audioses - private symbols
C:\Program Files (x86)\Mirillis\Action!\symchk\symbols\audioses.pdb\84E2FB31AD769EE663C832DF7A7DB19F1\audioses.pdb
|
AGHelper_x64.exe | DBGHELP: |
AGHelper_x86.exe | DBGHELP: |
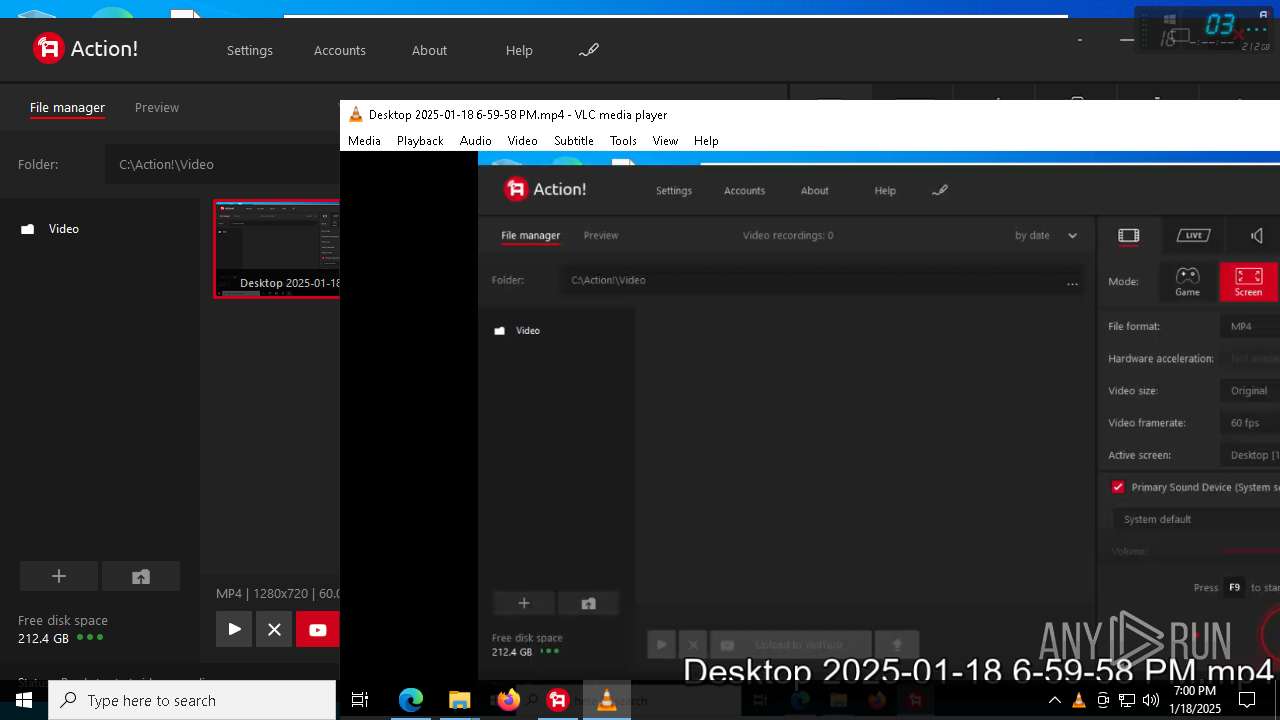
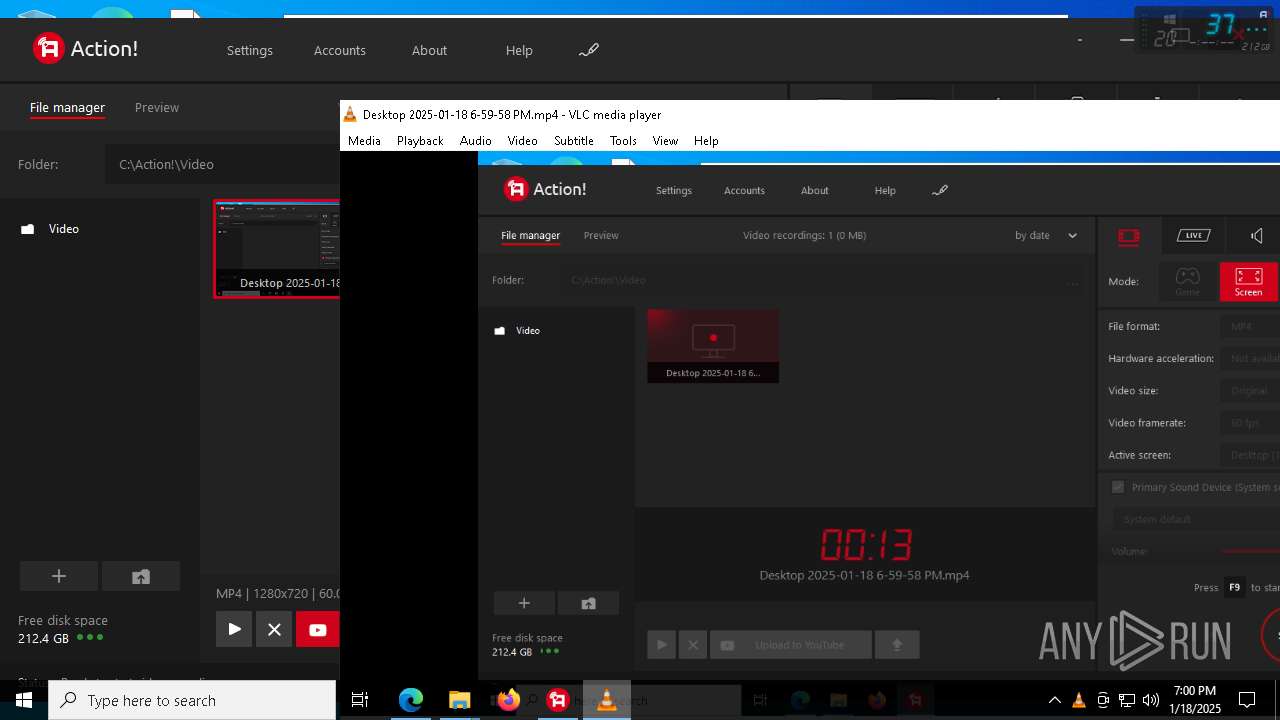
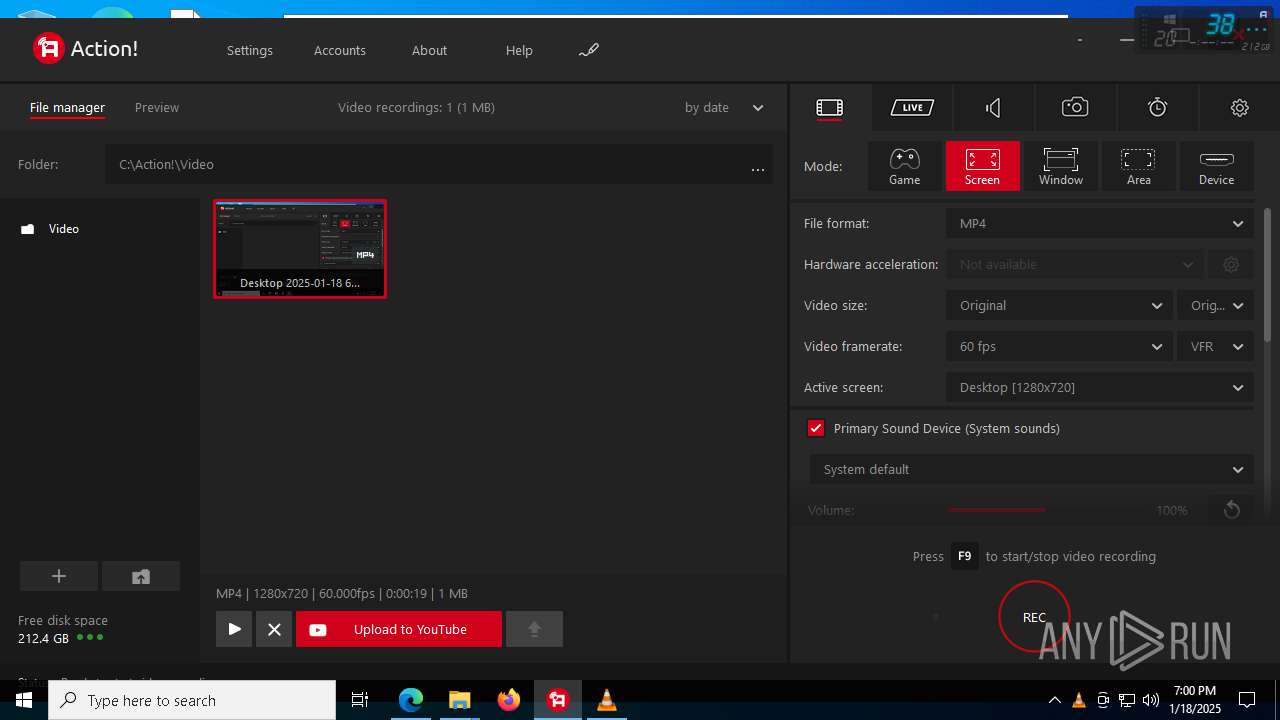
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|