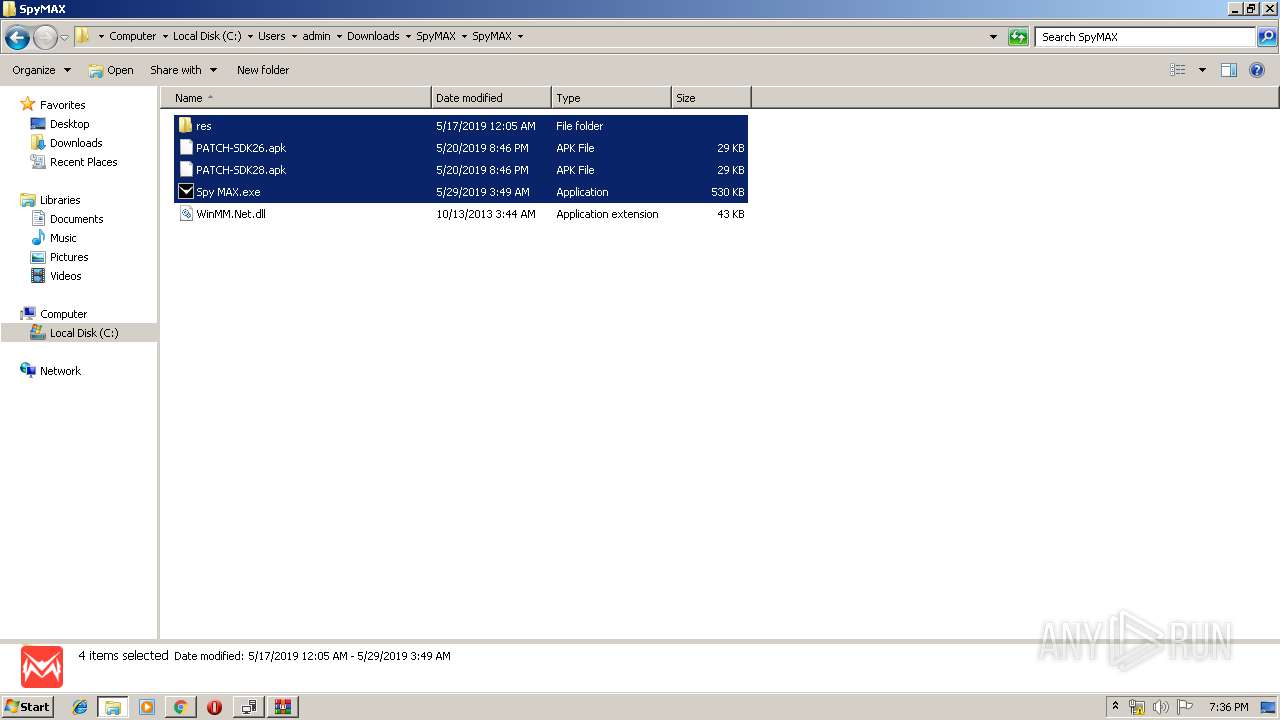
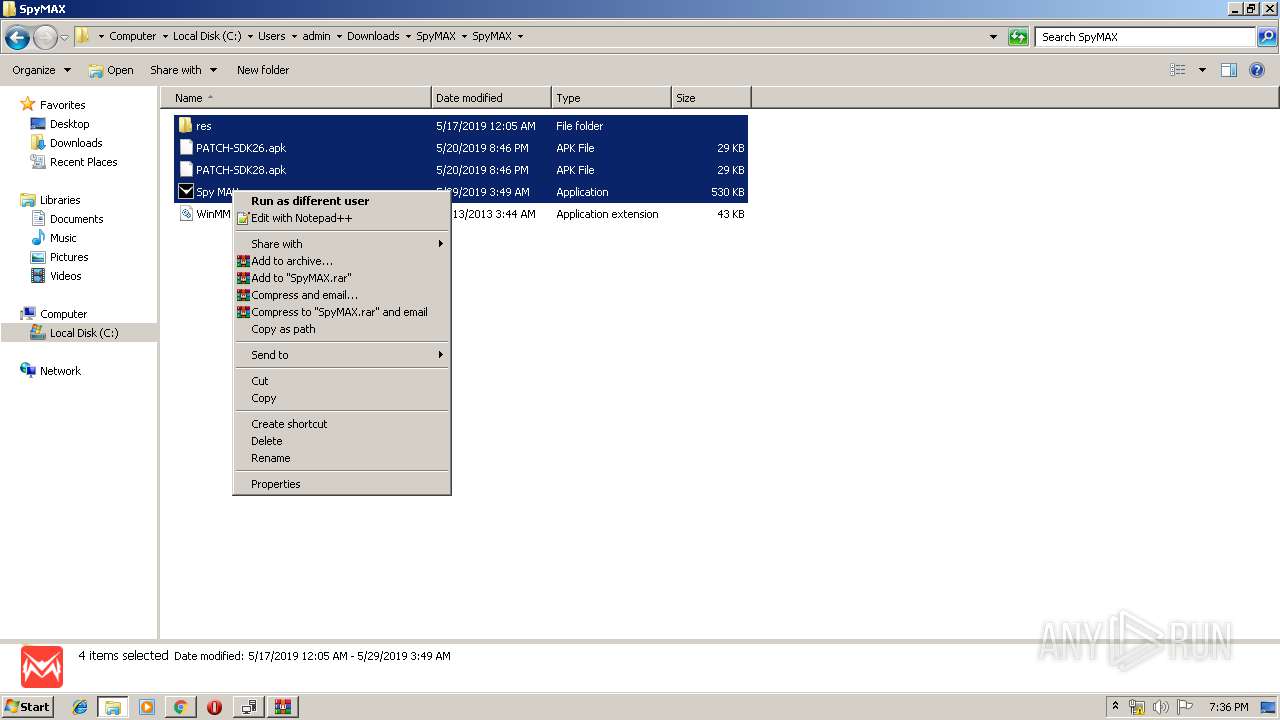
| File name: | Spy MAX.exe |
| Full analysis: | https://app.any.run/tasks/1d92b987-6304-461e-9de4-cc1dee28ab29 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2019, 18:31:30 |
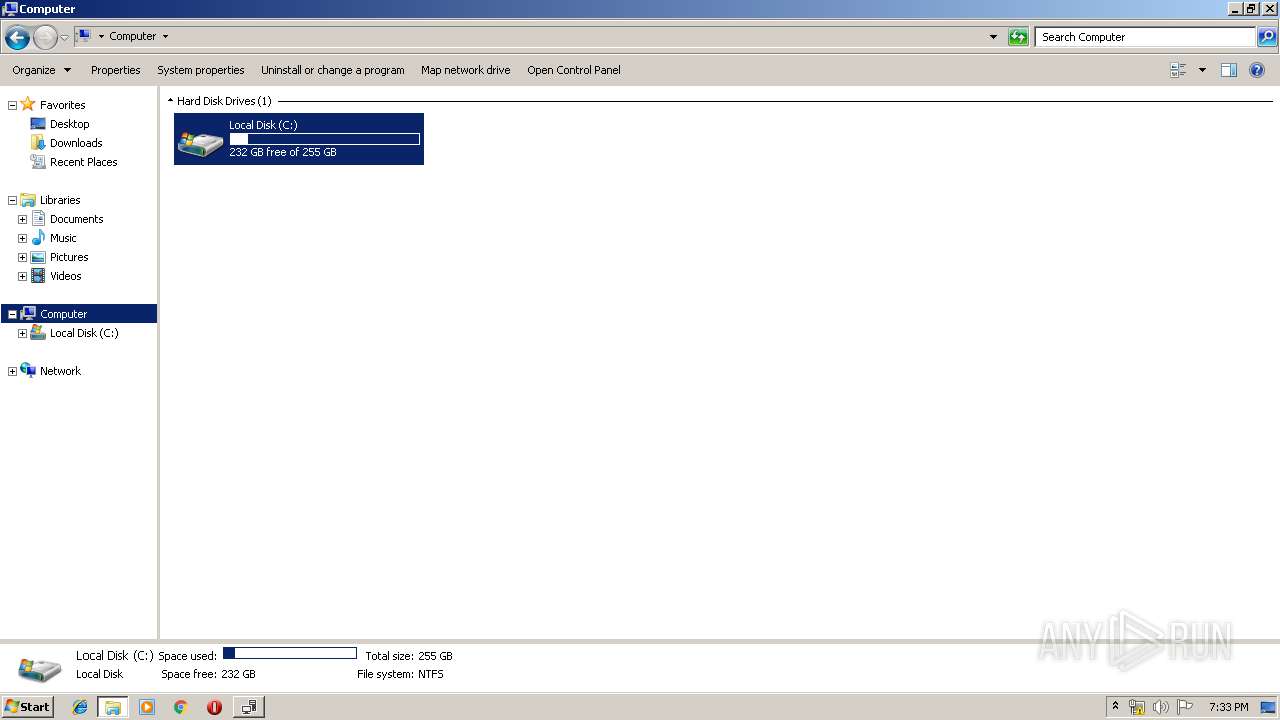
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2D00B1F7D3B15637CC0AE2BE68FB872A |
| SHA1: | F42F12CFF9CC7634FDC65284B040D94CC128F3E2 |
| SHA256: | AFBC0414C3778E84D0A23D3A1E934B00FABDE4390804702A212C1F1018FFFBCF |
| SSDEEP: | 12288:VG4MCrtpiIVZpiIV+8hyQLTZAlgrd+Cpkuodt4mnCzeq9ysmiIE:VrpiIfpiIsomCCq9yMIE |
MALICIOUS
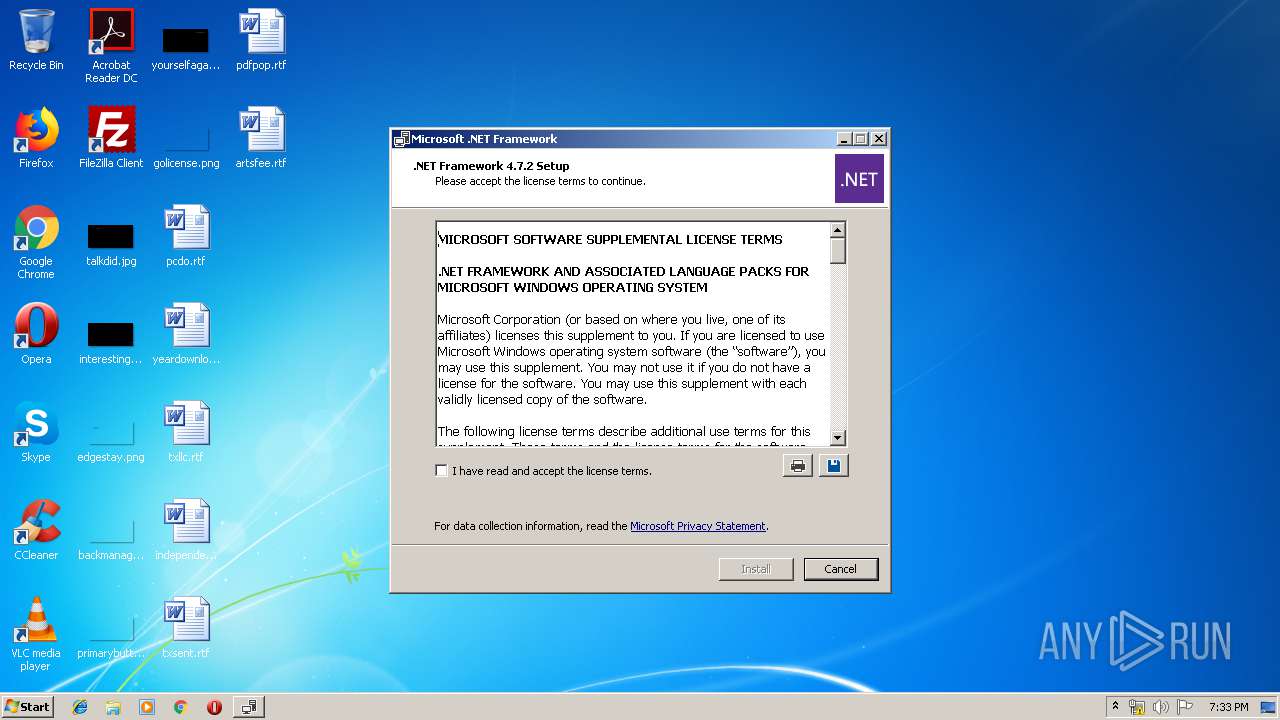
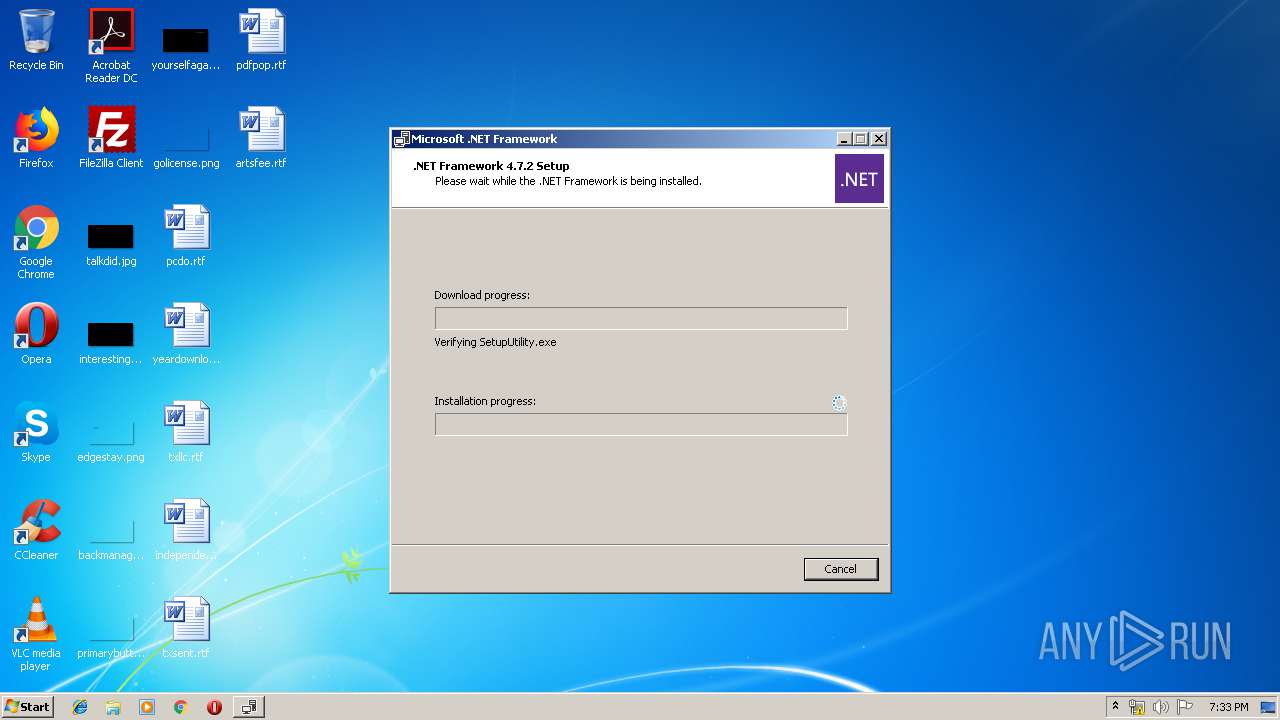
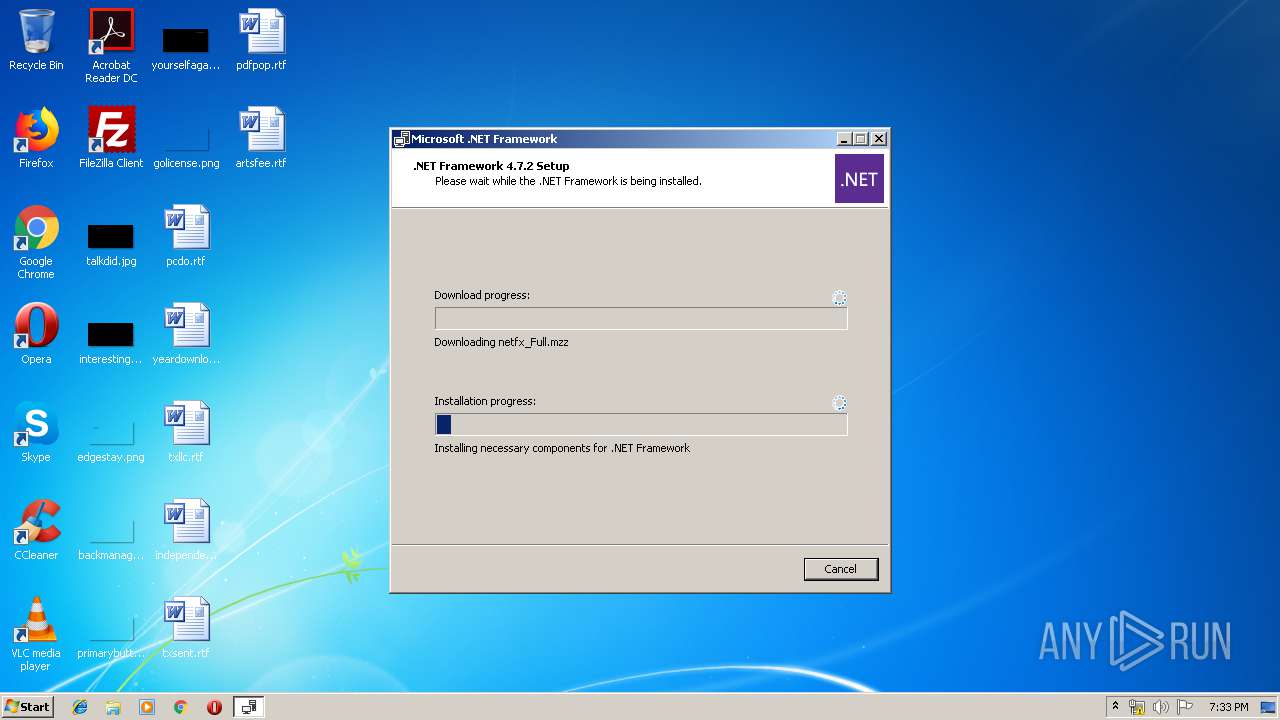
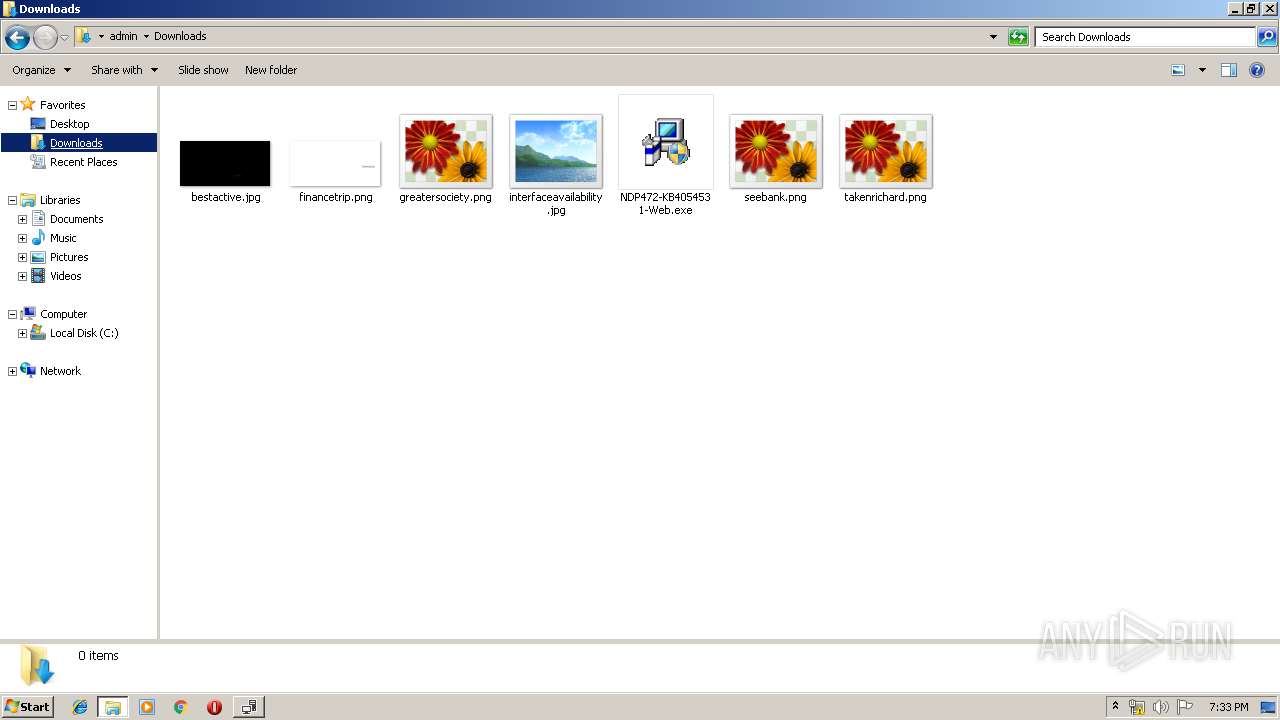
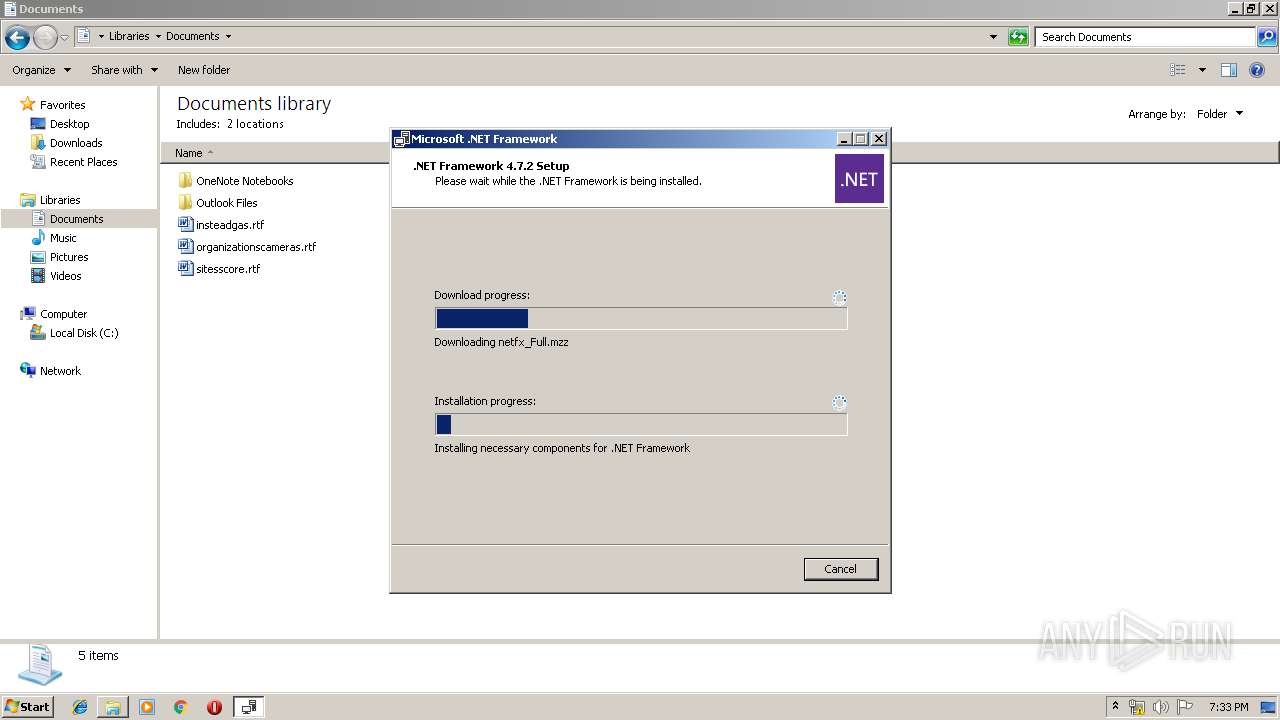
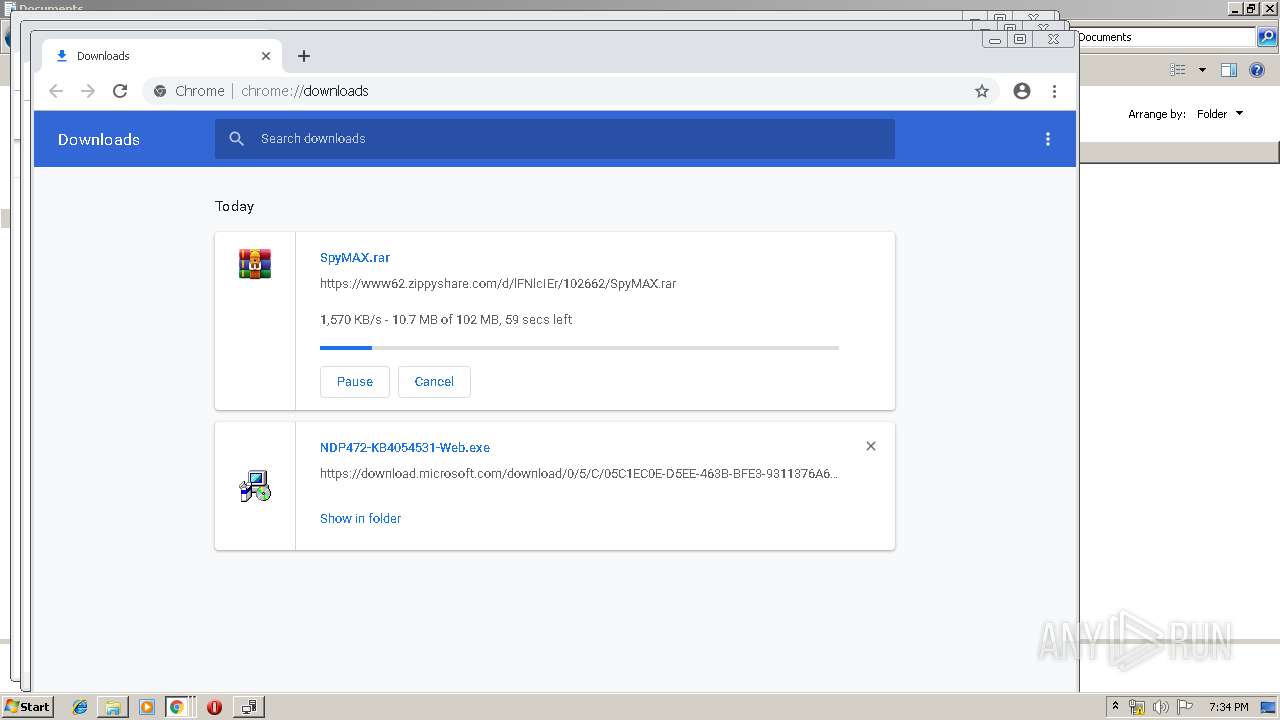
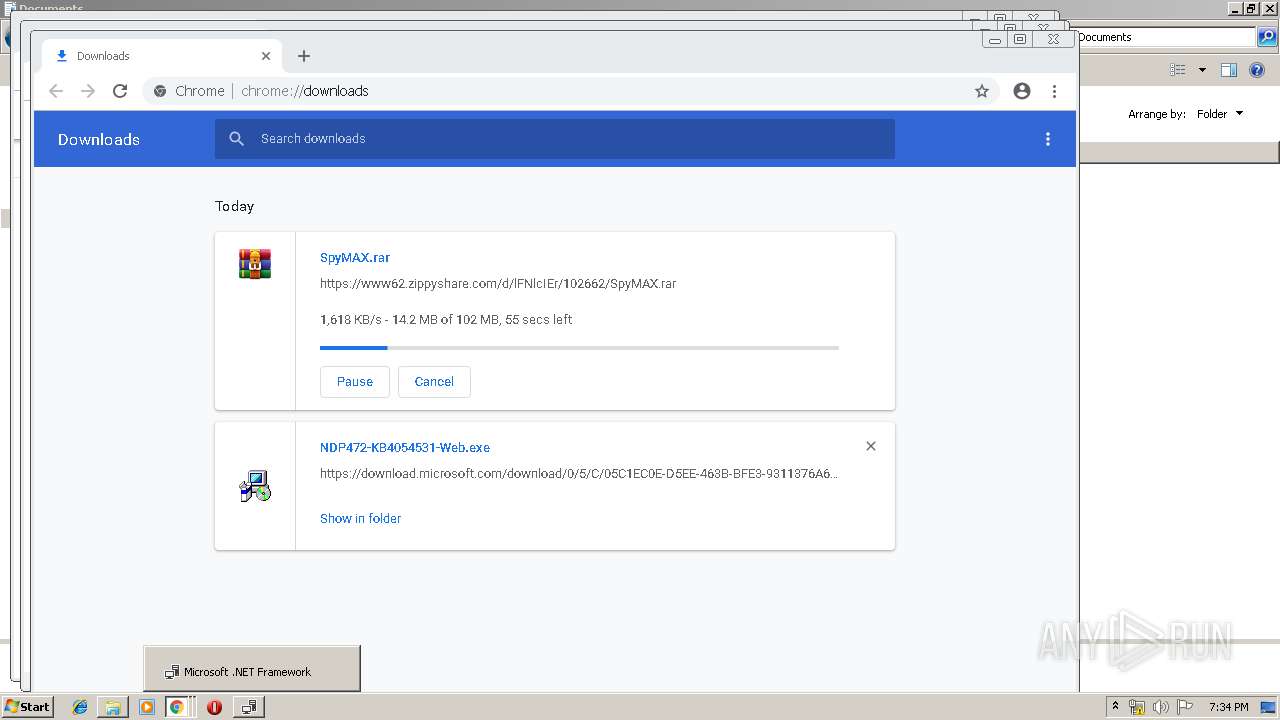
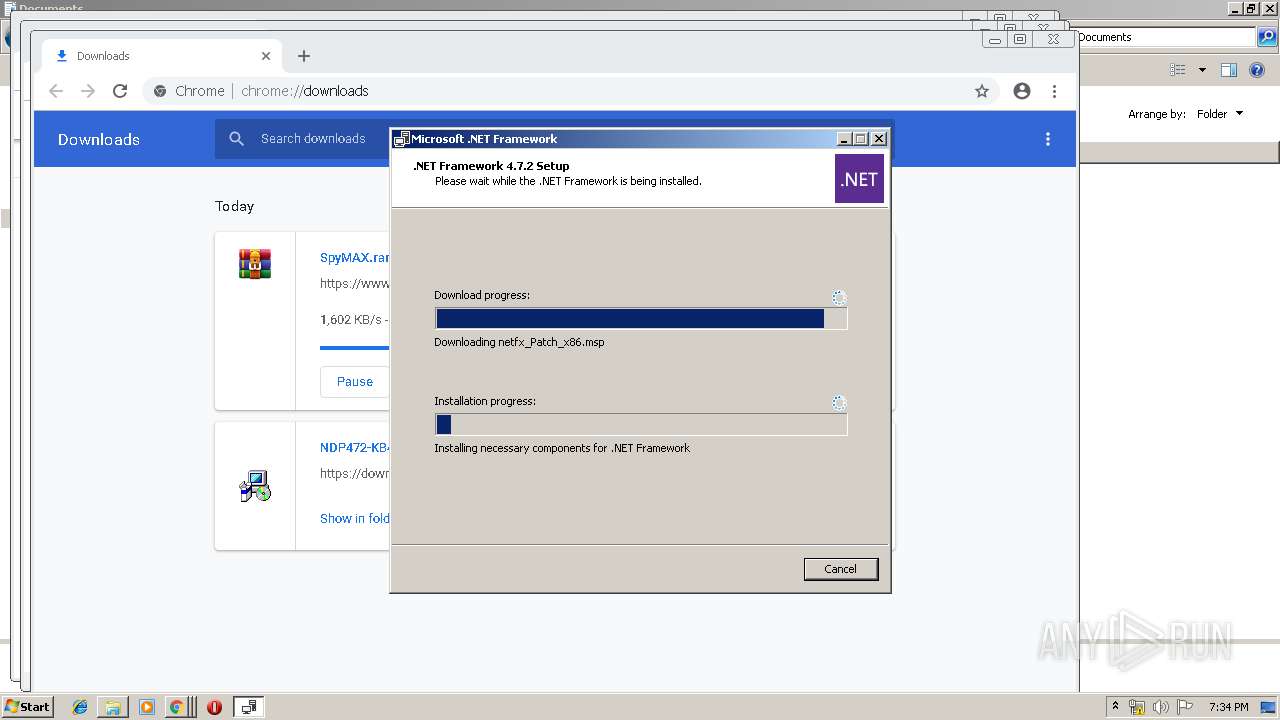
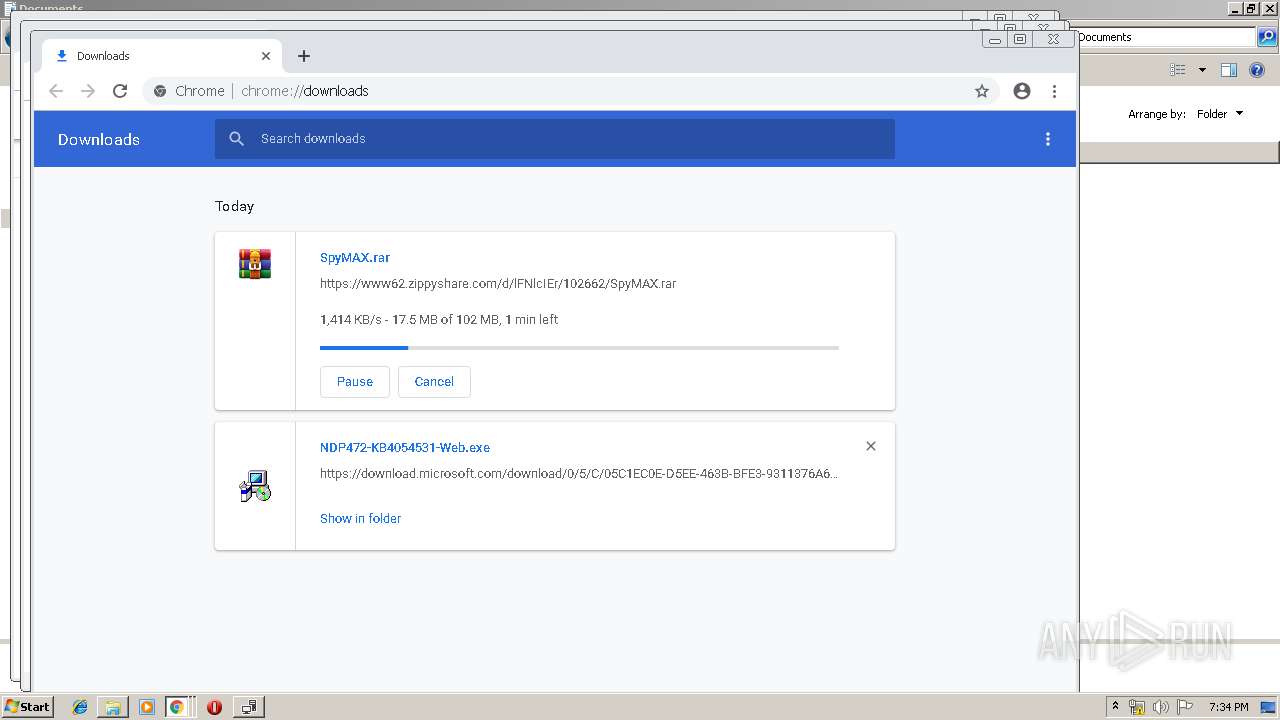
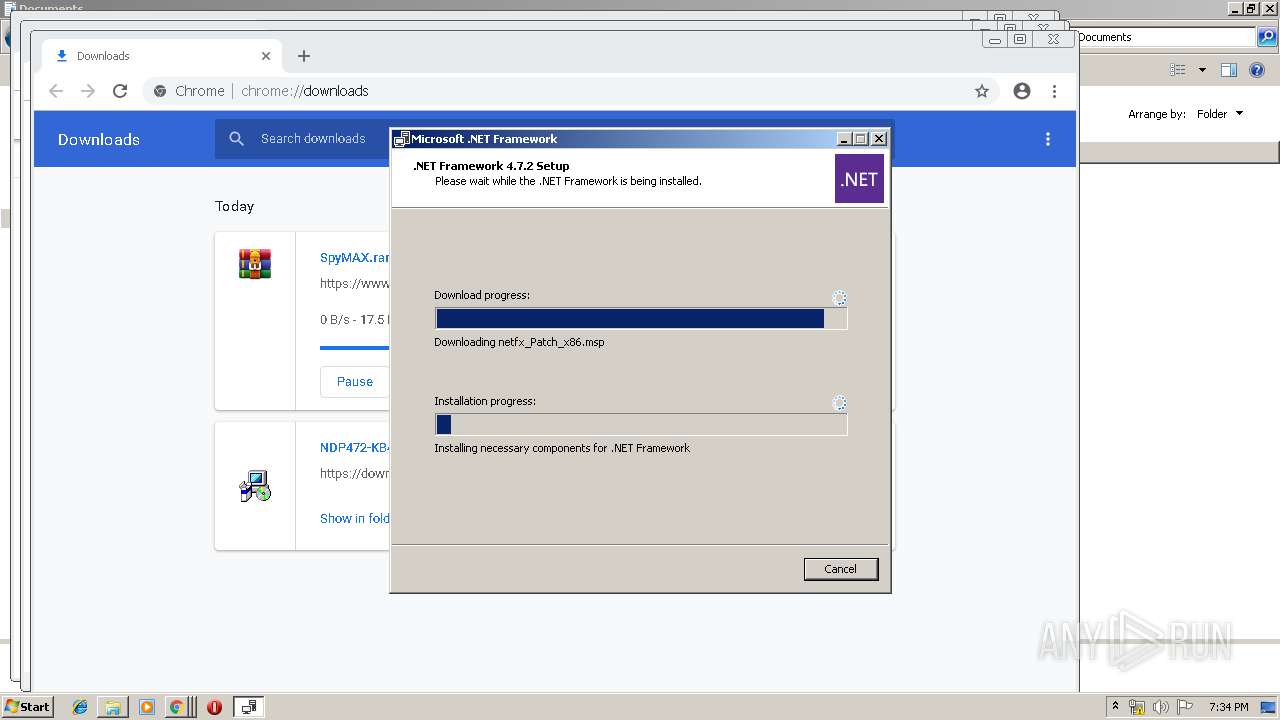
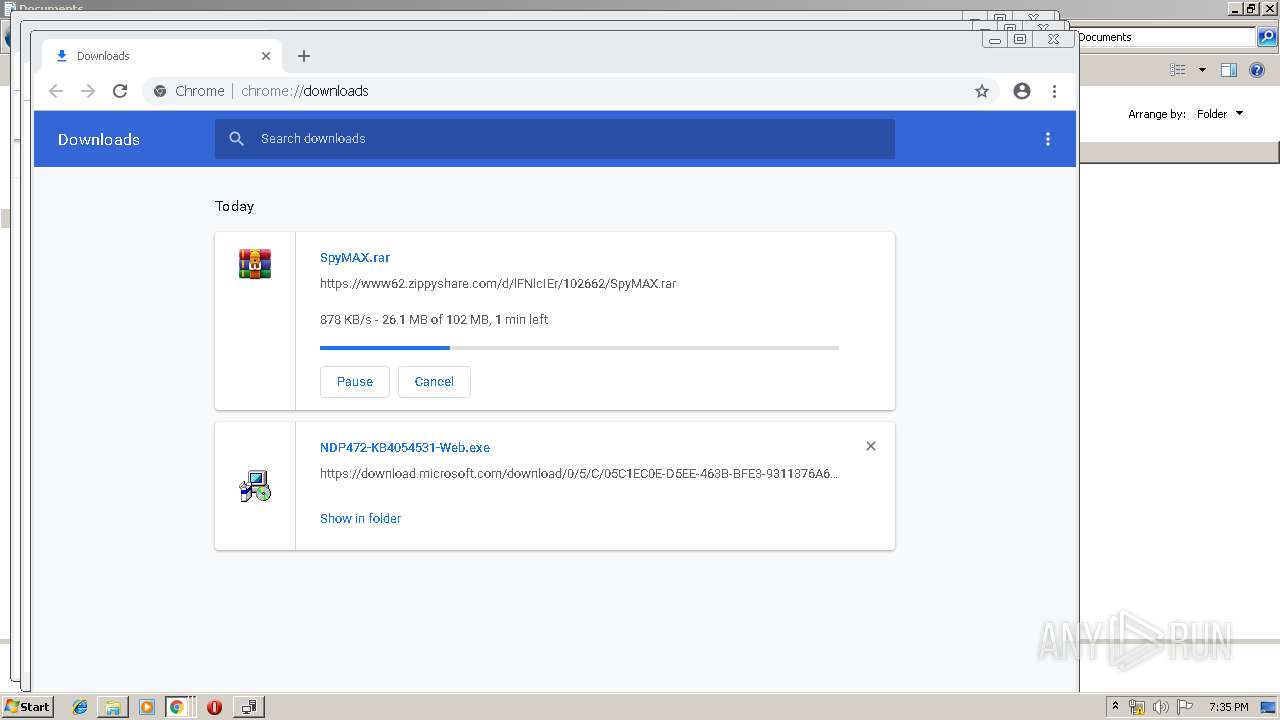
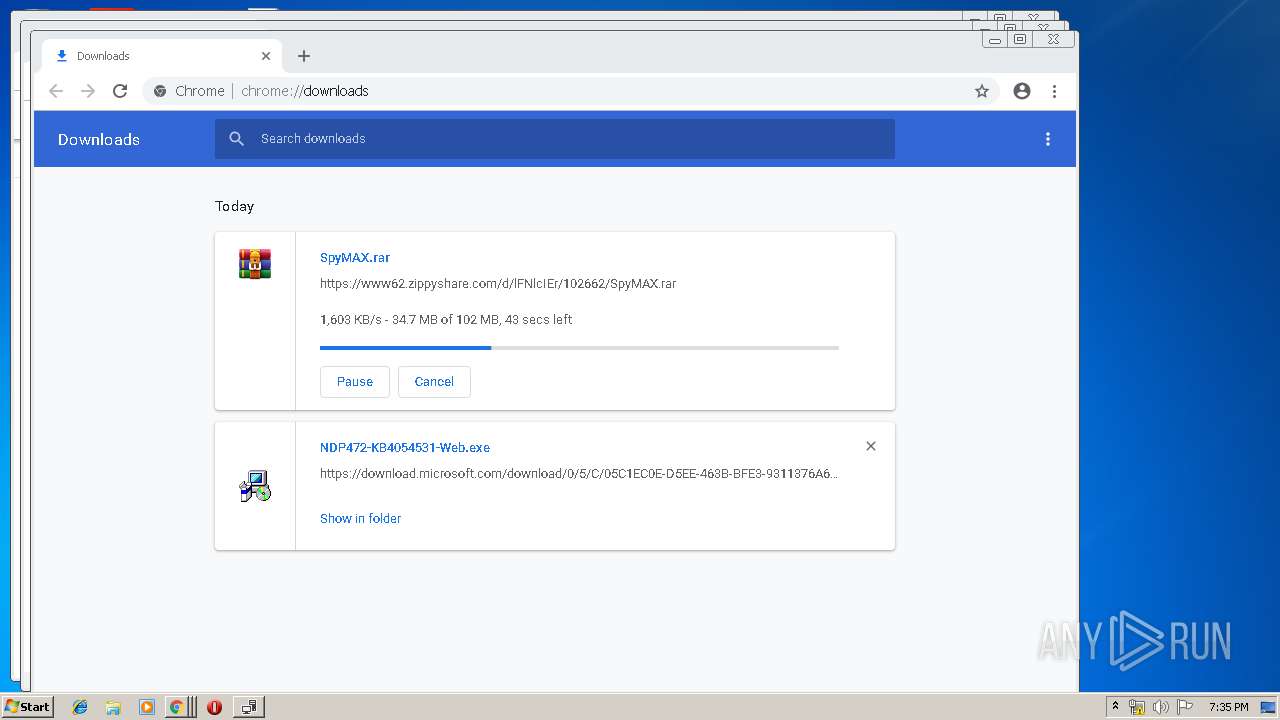
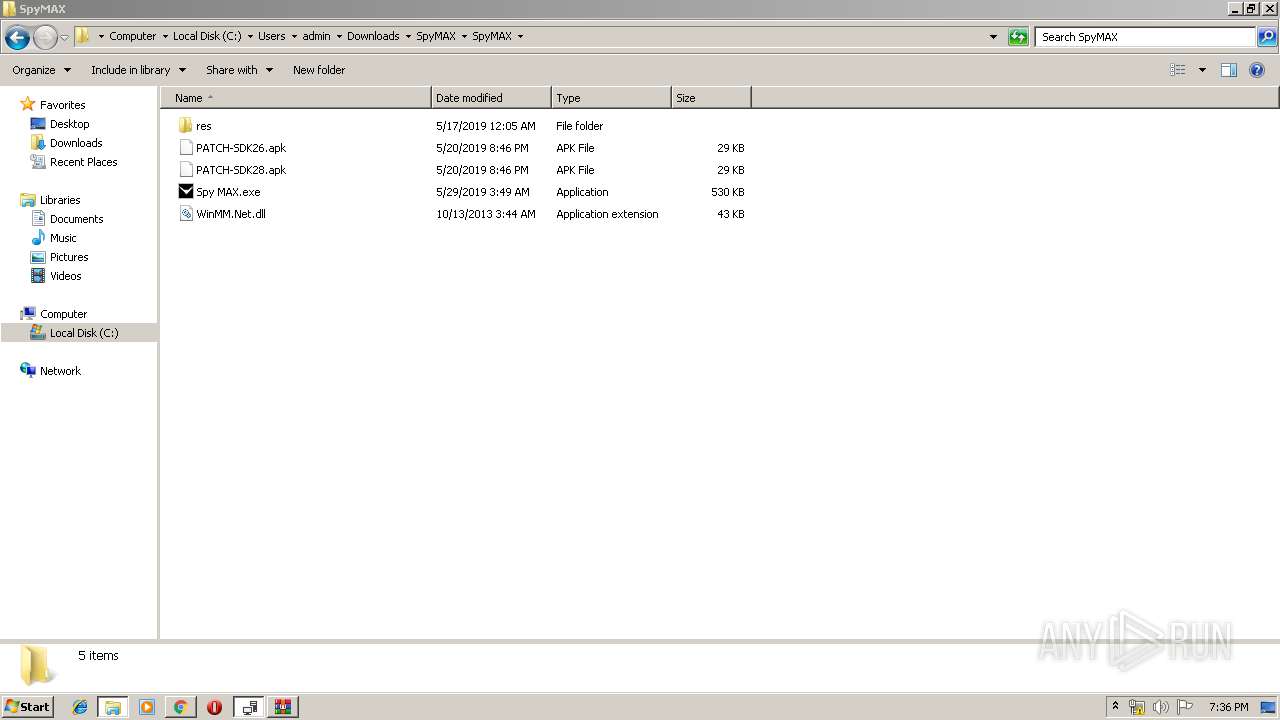
Application was dropped or rewritten from another process
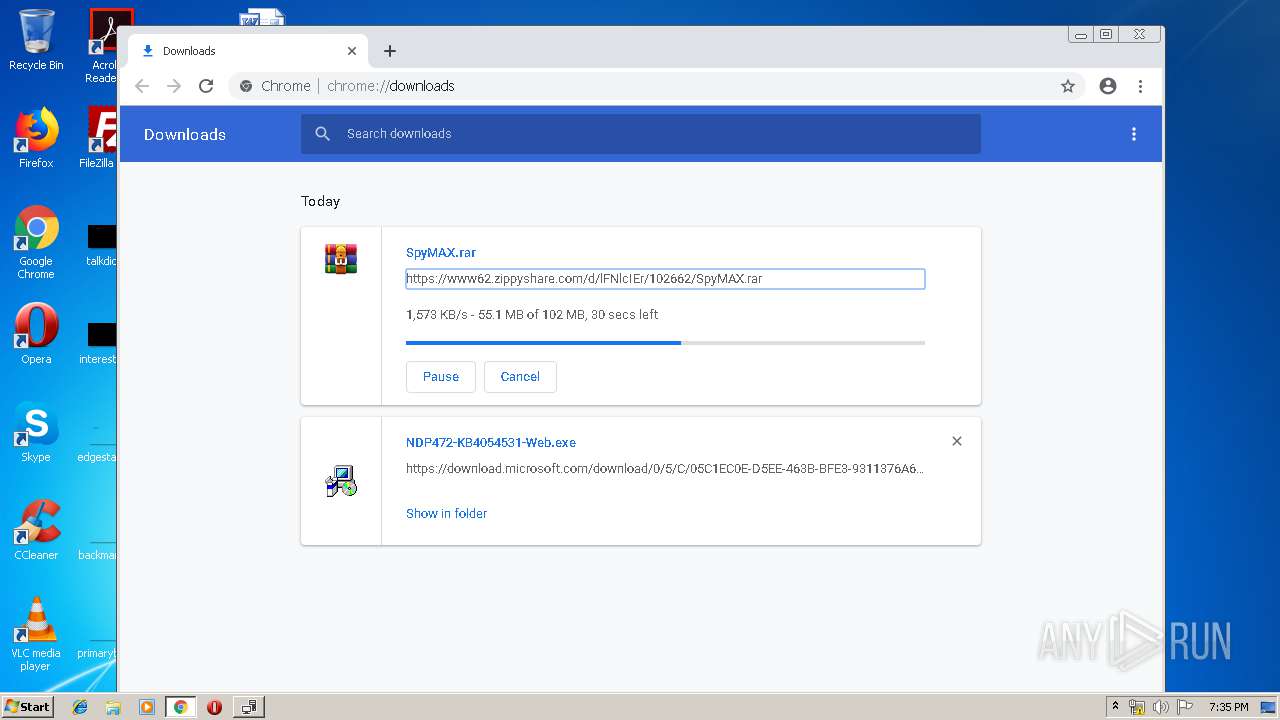
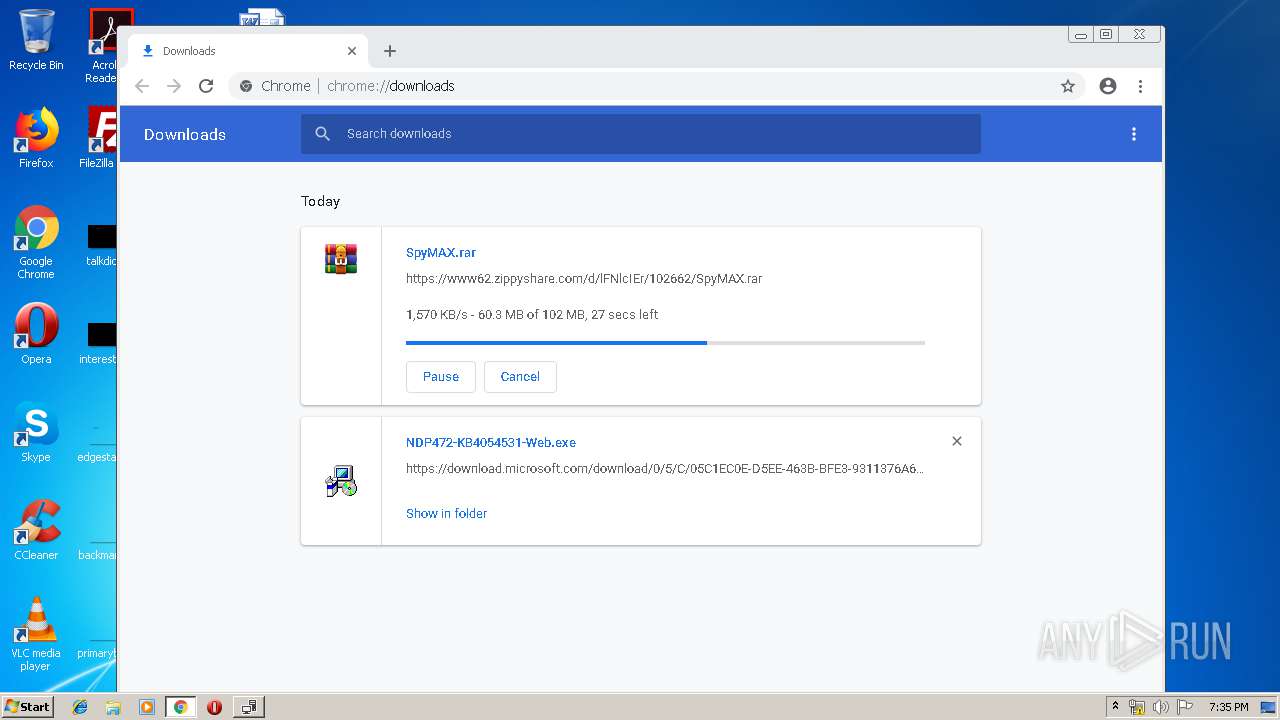
- NDP472-KB4054531-Web.exe (PID: 2628)
- NDP472-KB4054531-Web.exe (PID: 3828)
- Setup.exe (PID: 2944)
- SetupUtility.exe (PID: 2400)
- SetupUtility.exe (PID: 3596)
Changes settings of System certificates
- Setup.exe (PID: 2944)
Loads dropped or rewritten executable
- Setup.exe (PID: 2944)
- explorer.exe (PID: 252)
- Spy MAX.exe (PID: 3316)
- SearchProtocolHost.exe (PID: 3464)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 4012)
Executable content was dropped or overwritten
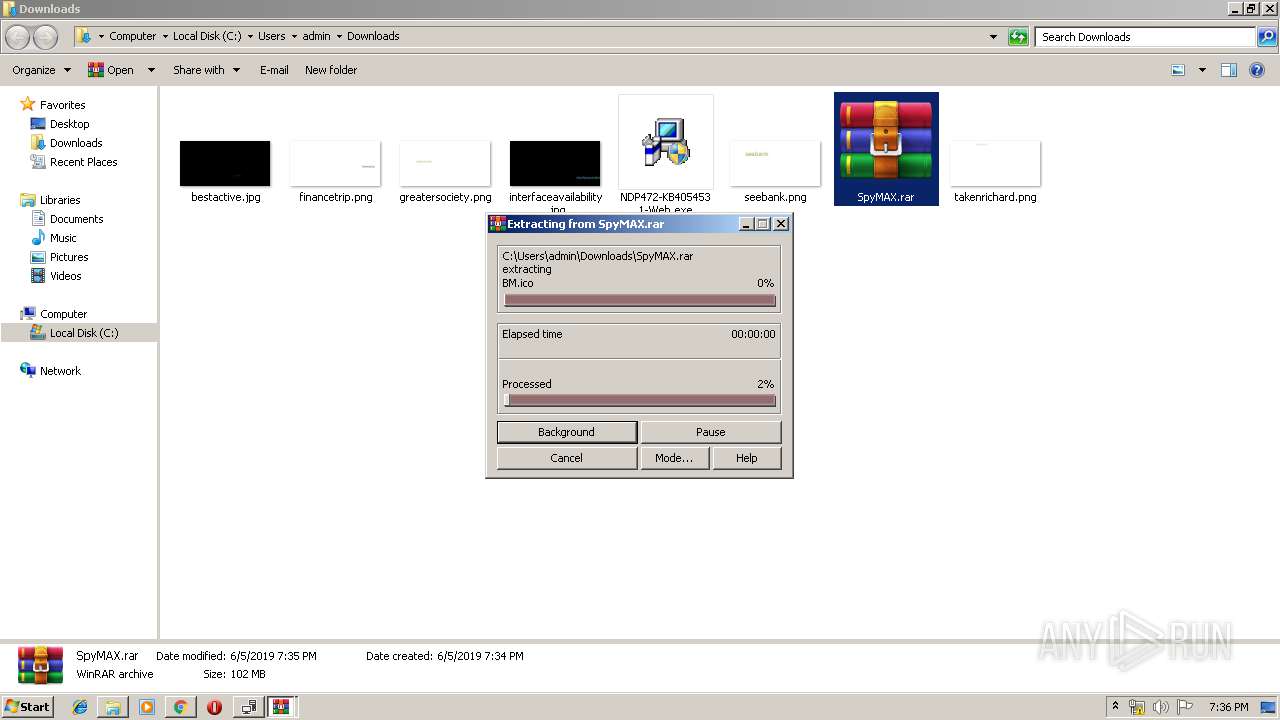
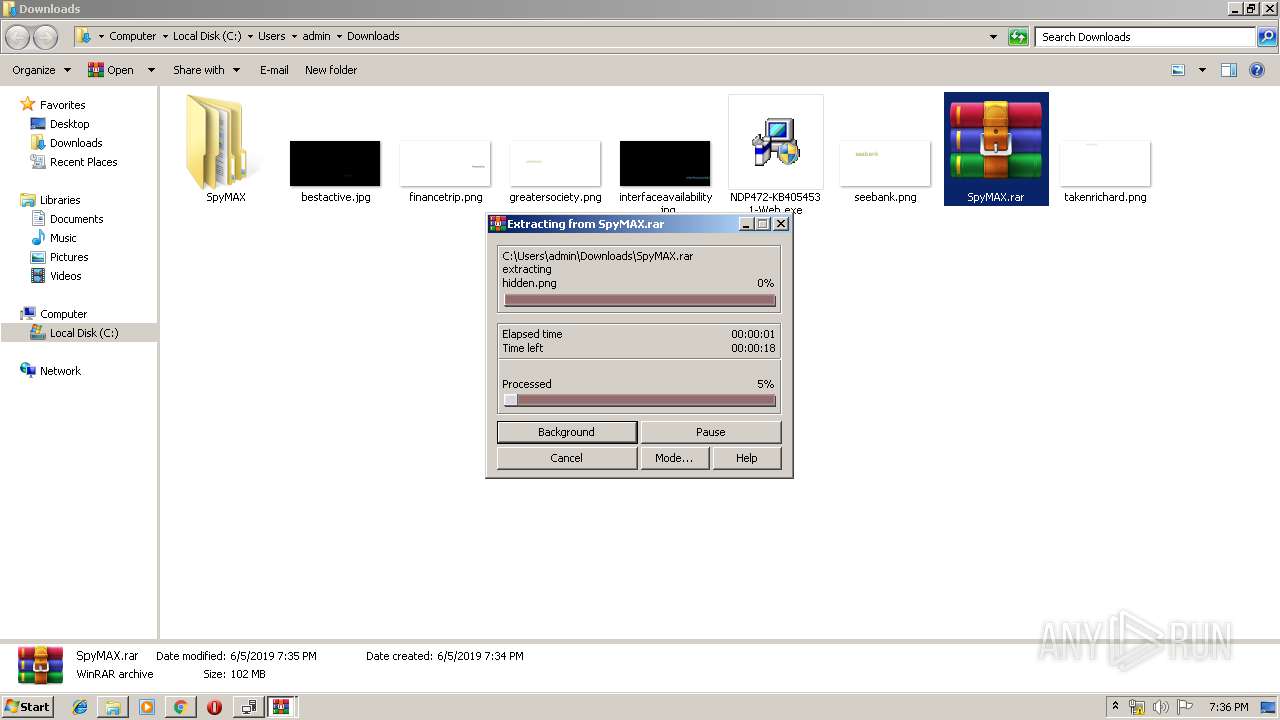
- NDP472-KB4054531-Web.exe (PID: 3828)
- chrome.exe (PID: 4012)
- TMP3BAE.tmp.exe (PID: 568)
- Setup.exe (PID: 2944)
- WinRAR.exe (PID: 3744)
Adds / modifies Windows certificates
- Setup.exe (PID: 2944)
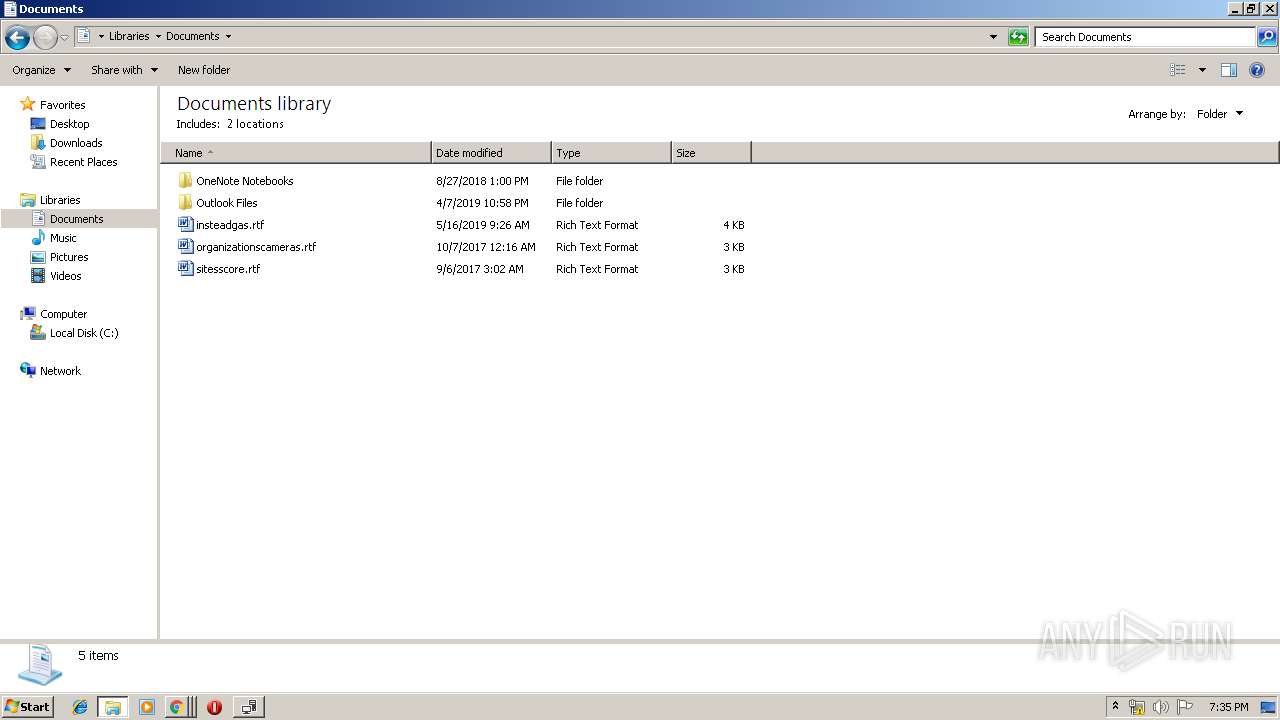
Creates files in the user directory
- explorer.exe (PID: 252)
- Setup.exe (PID: 2944)
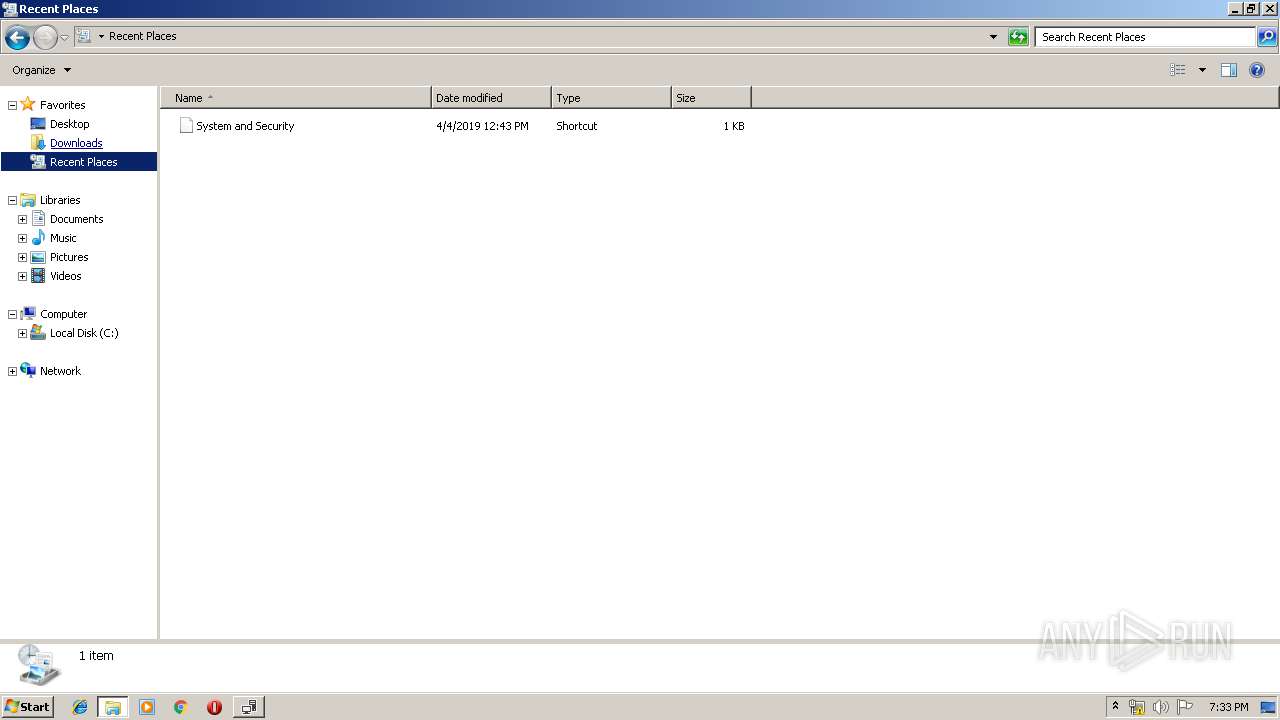
Reads Internet Cache Settings
- explorer.exe (PID: 252)
- Setup.exe (PID: 2944)
Reads default file associations for system extensions
- explorer.exe (PID: 252)
INFO
Application launched itself
- chrome.exe (PID: 4012)
- chrome.exe (PID: 2204)
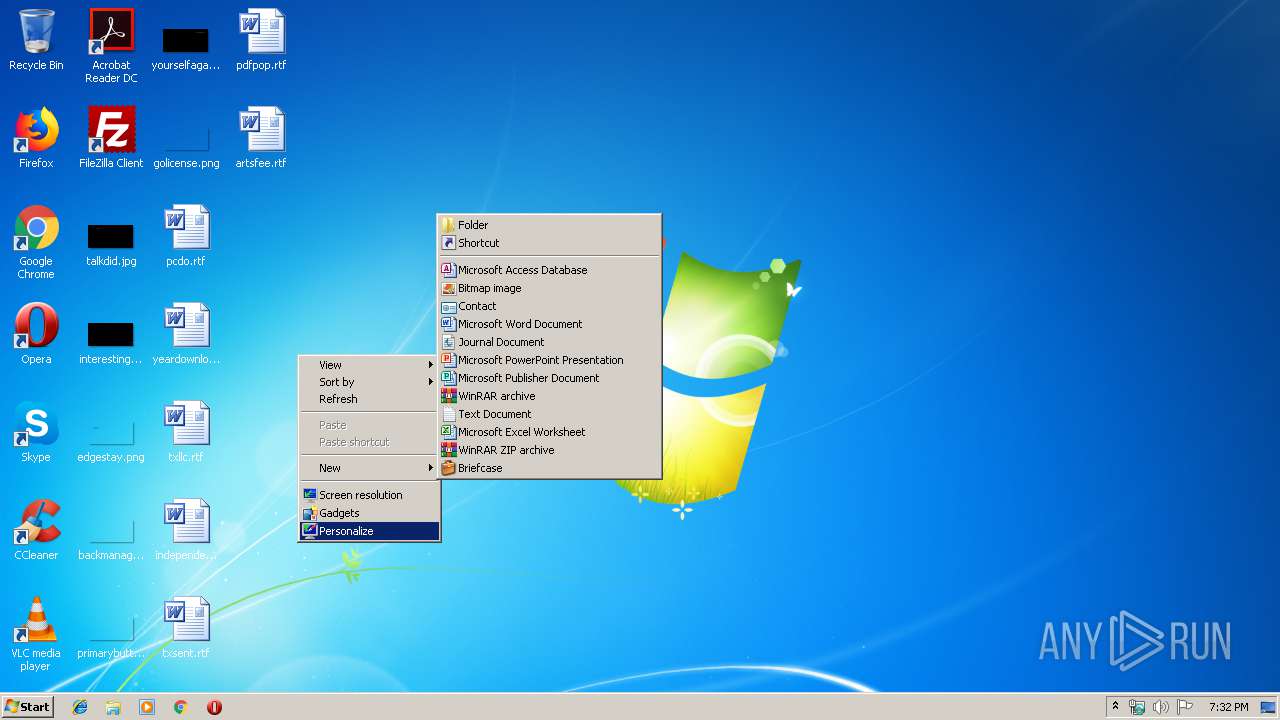
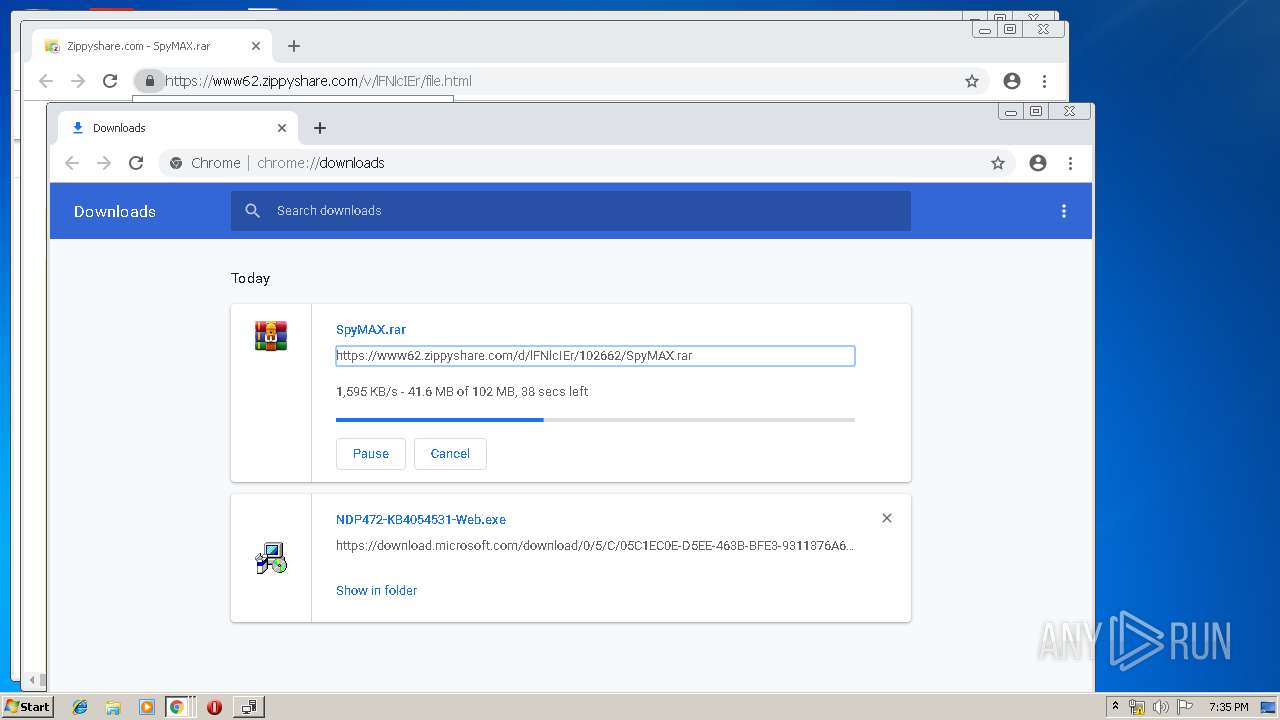
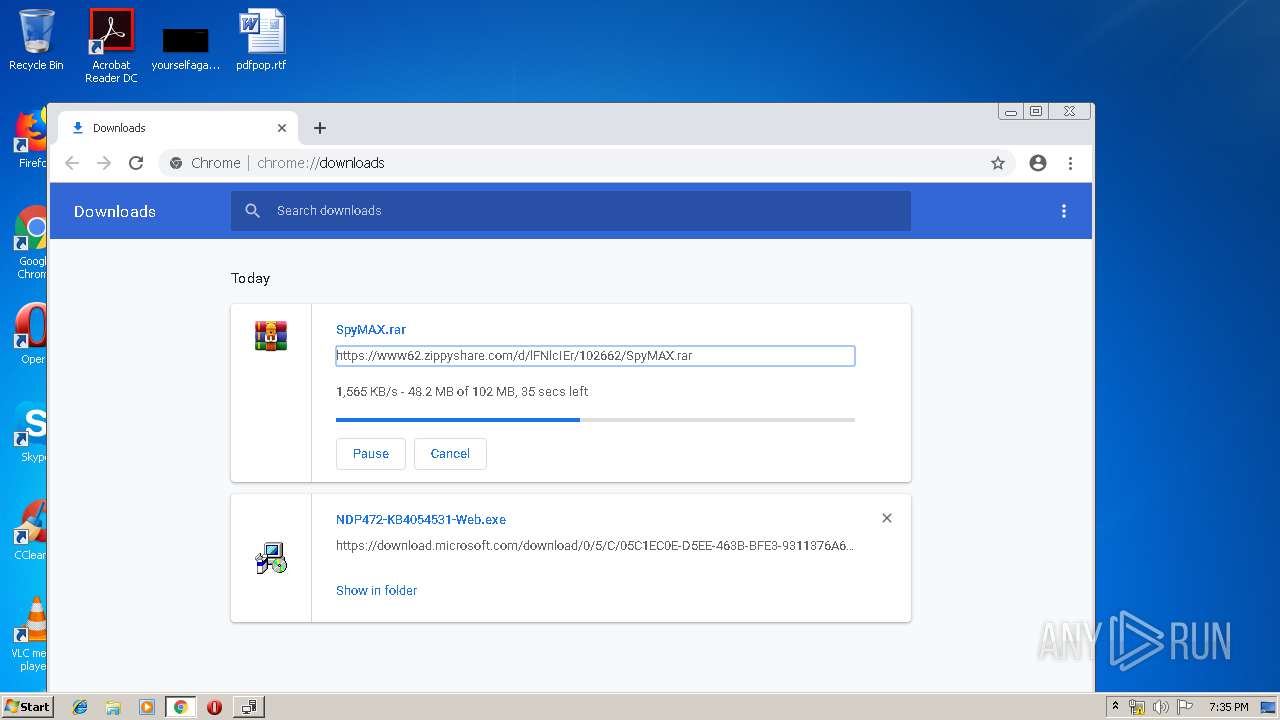
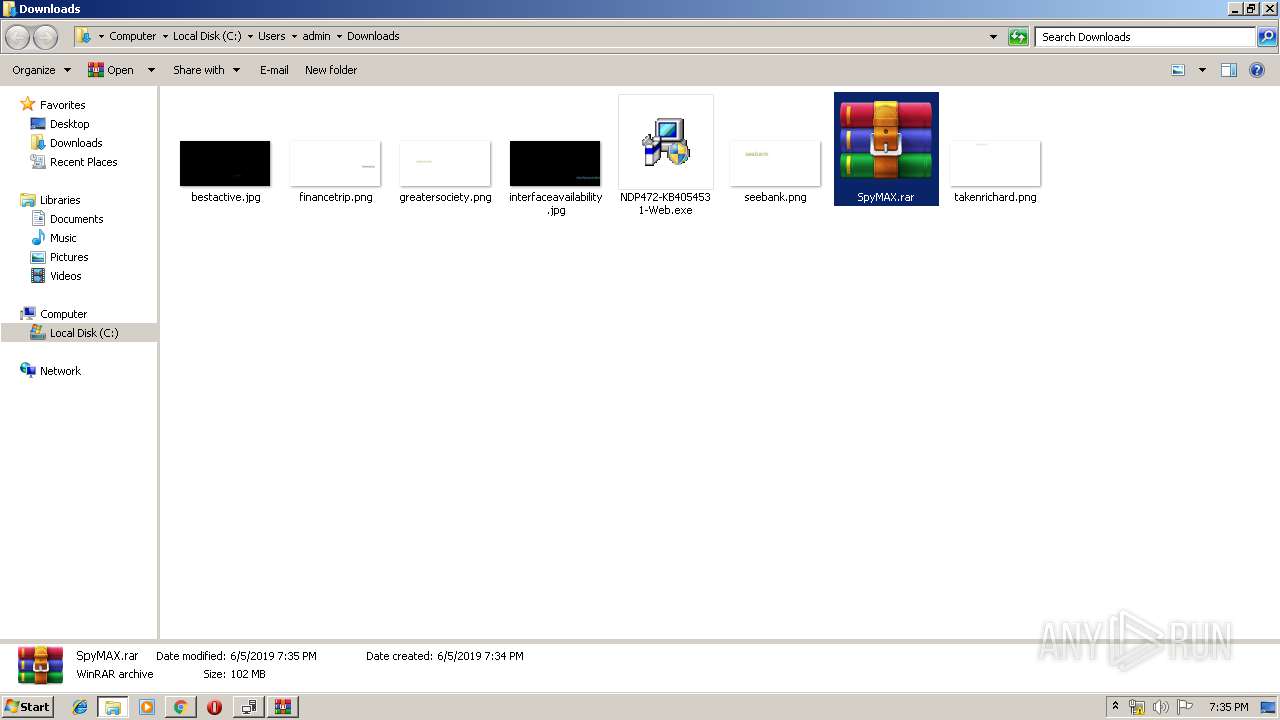
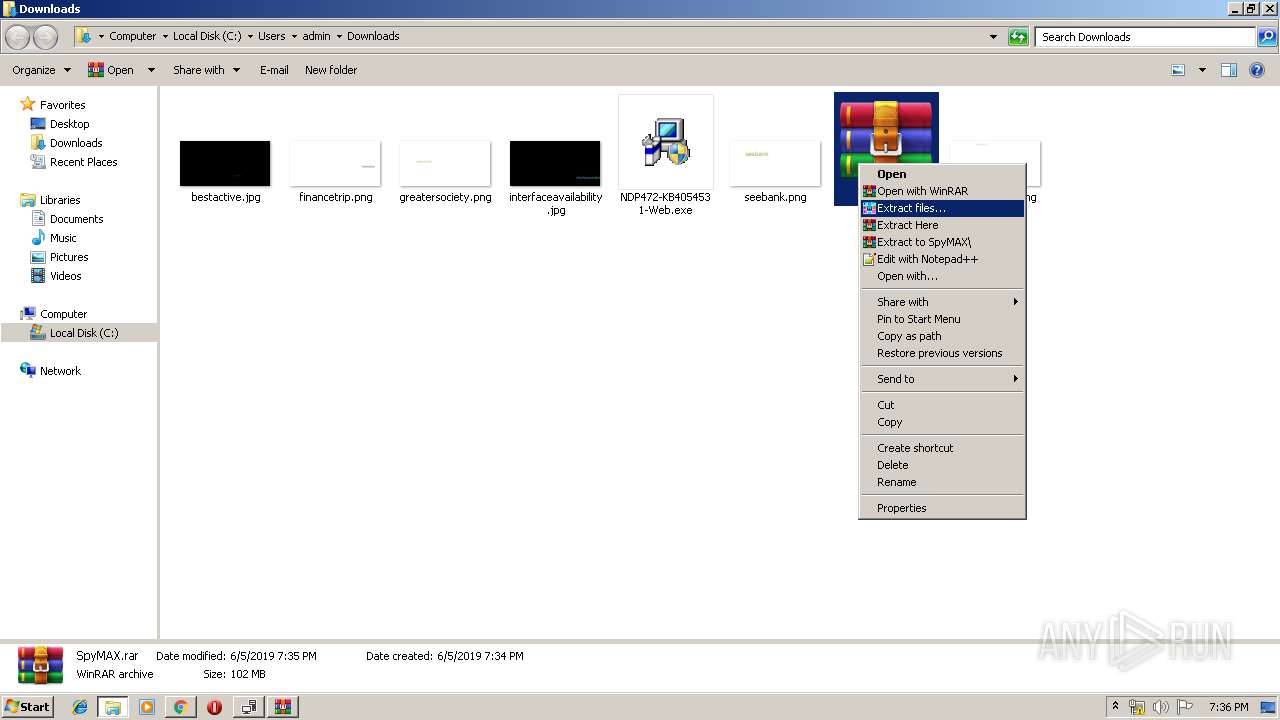
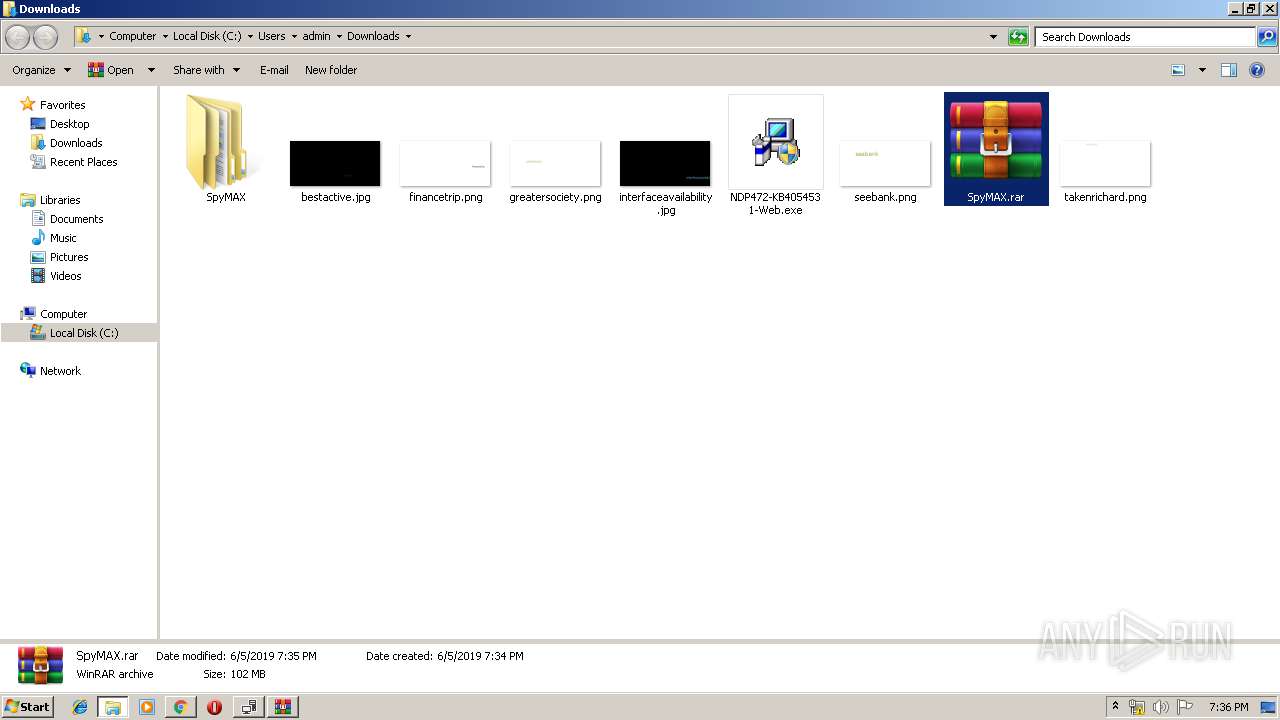
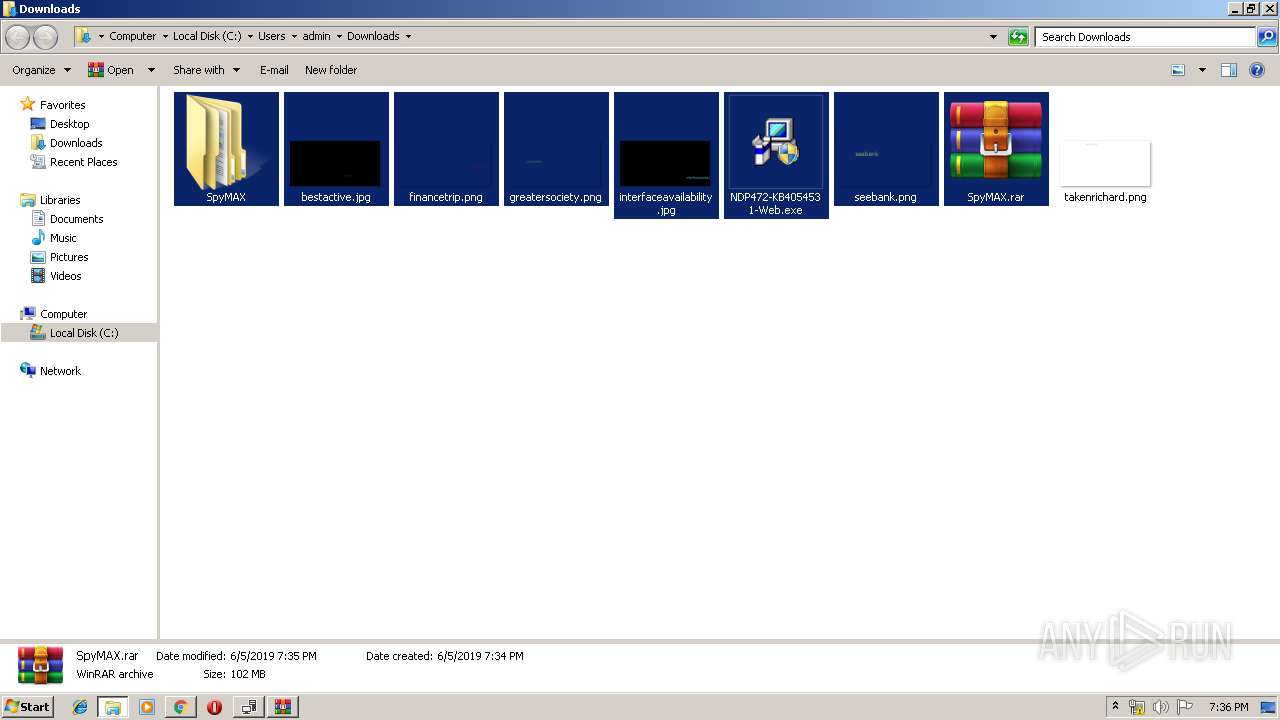
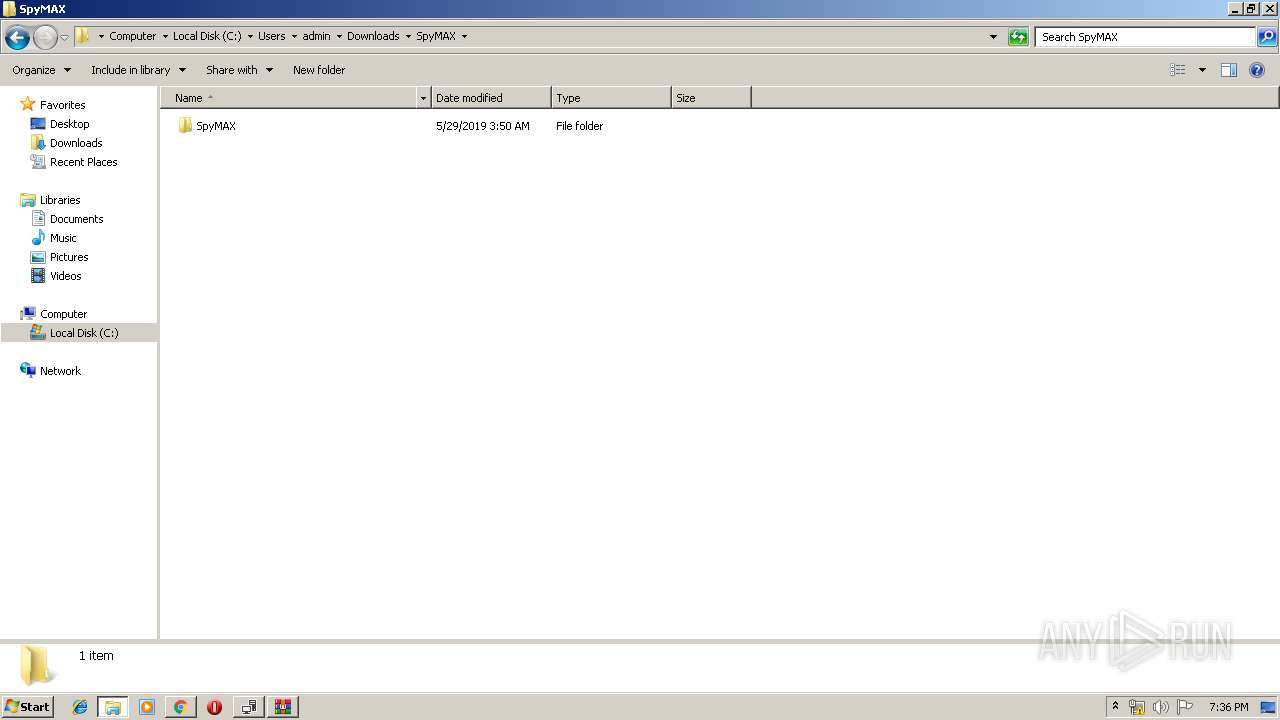
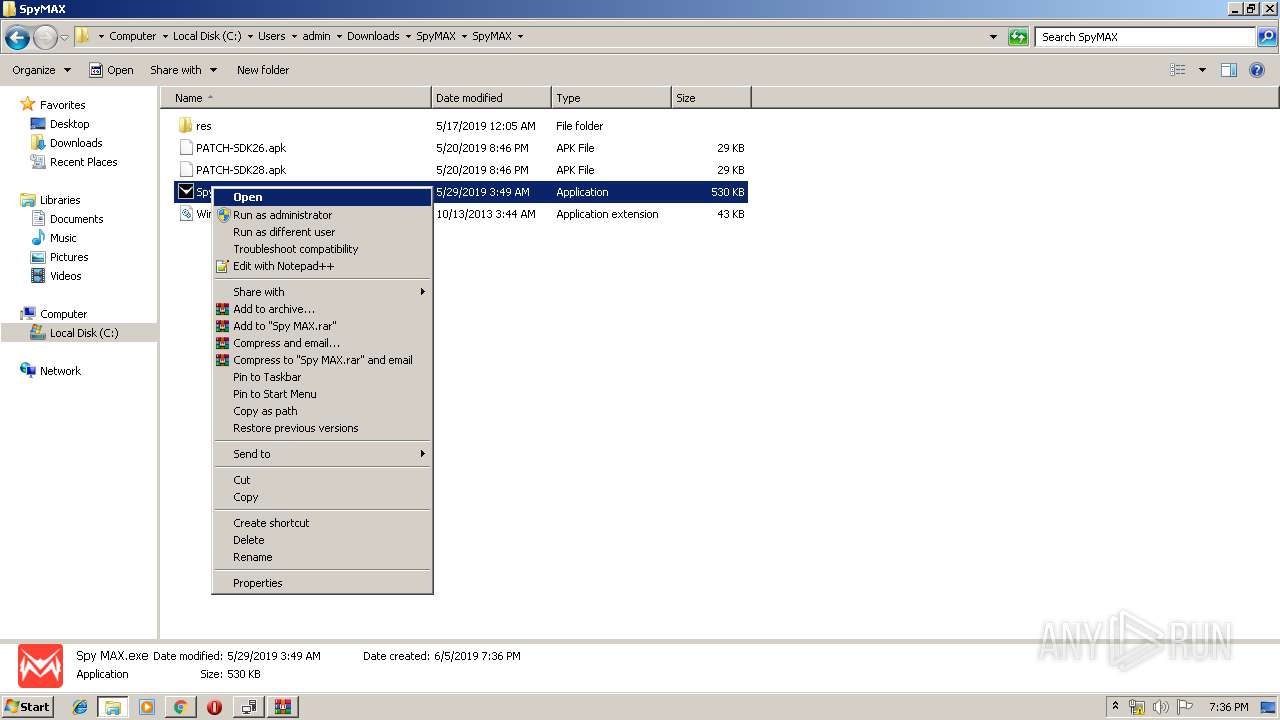
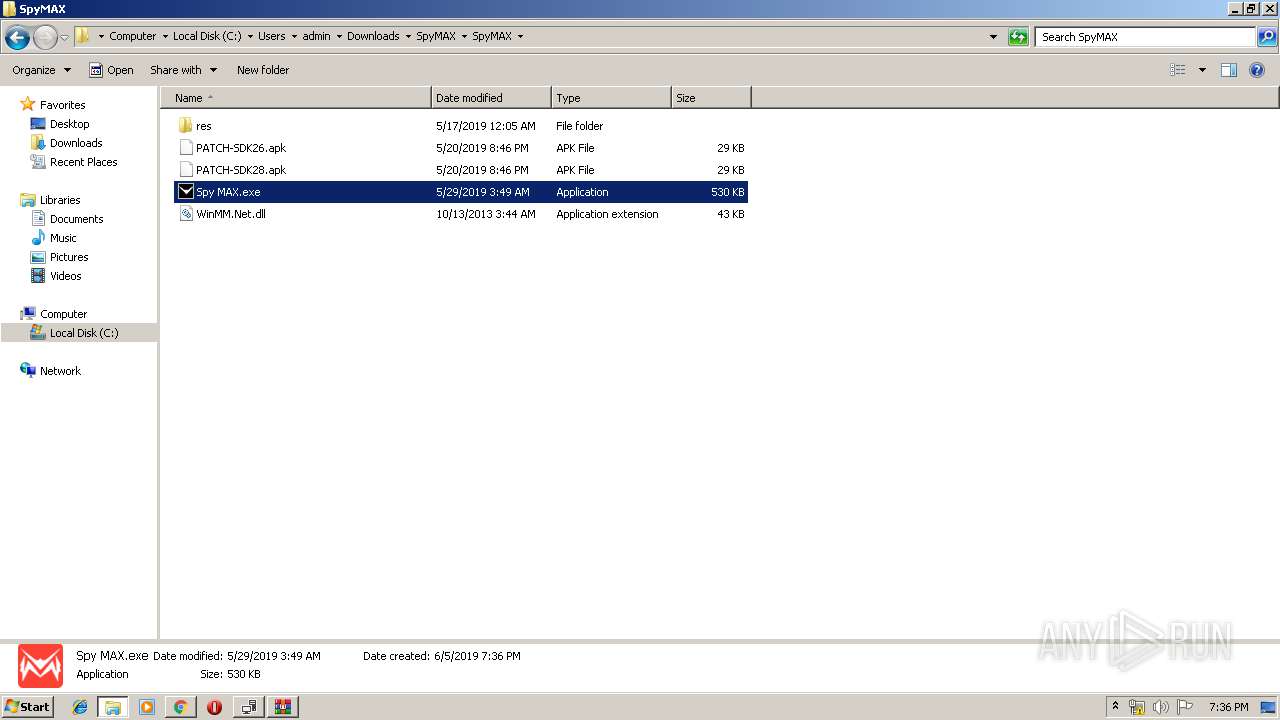
Manual execution by user
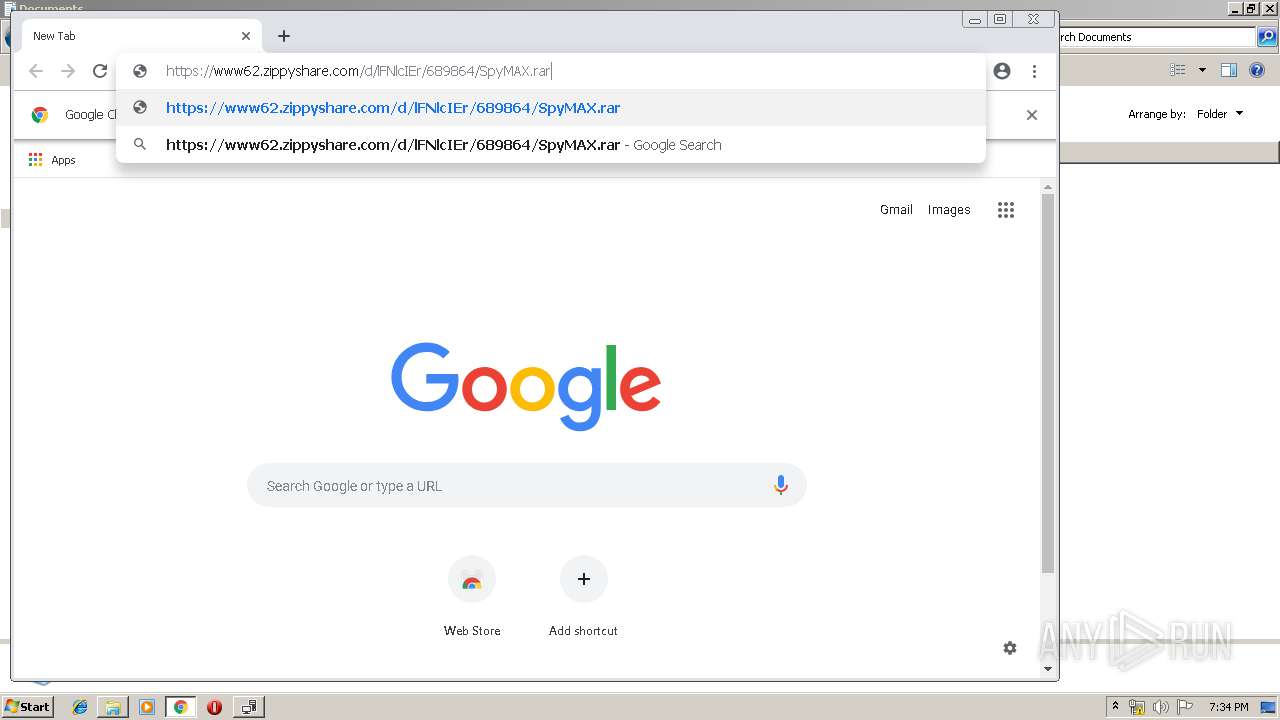
- chrome.exe (PID: 4012)
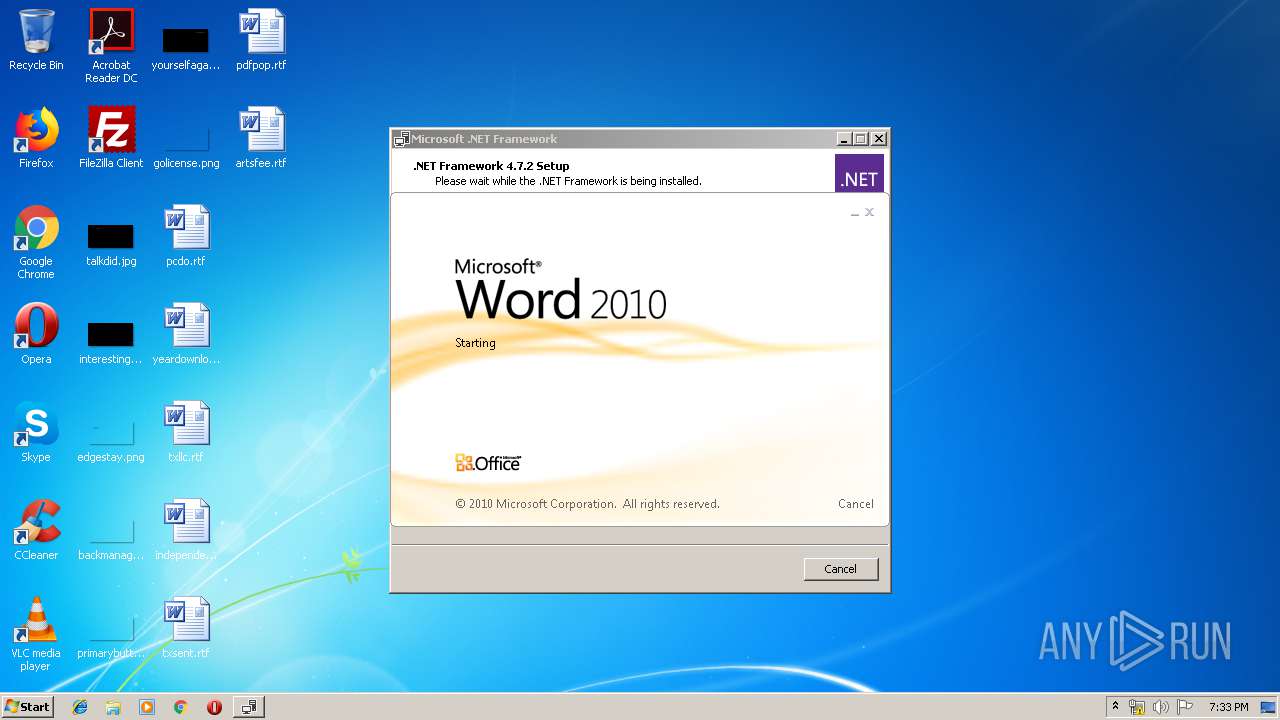
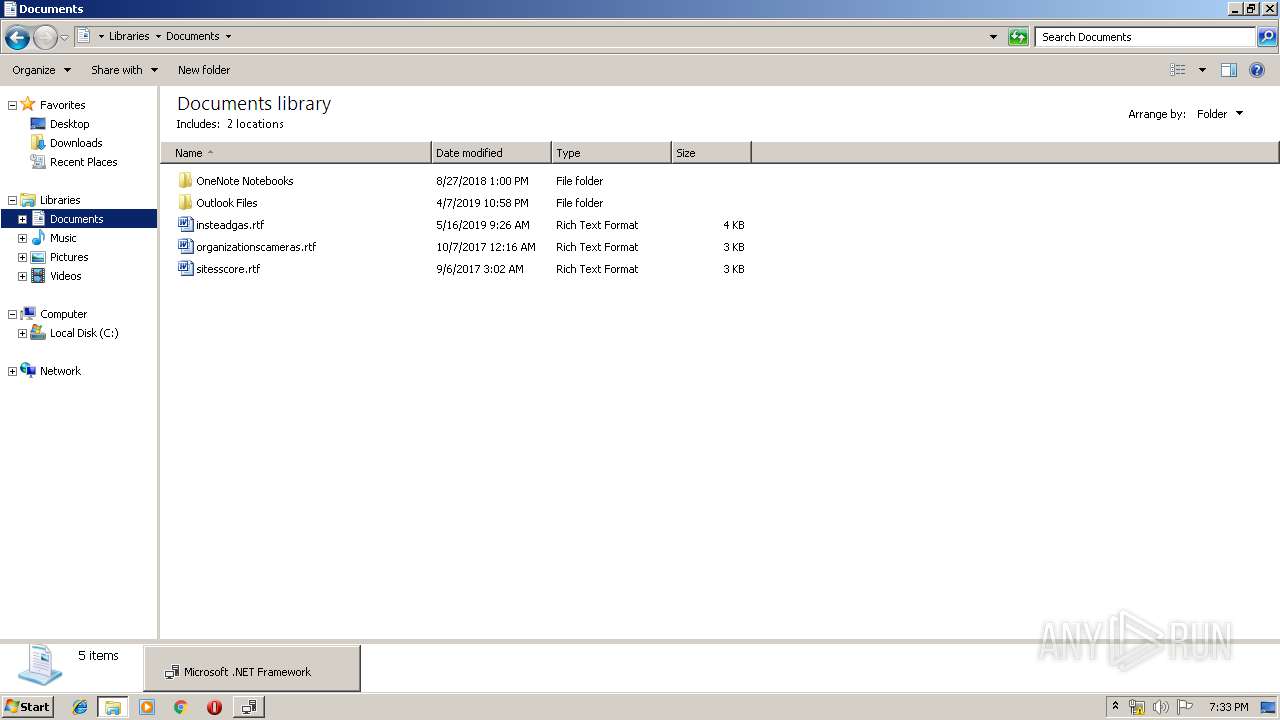
- WINWORD.EXE (PID: 720)
- explorer.exe (PID: 3008)
- WinRAR.exe (PID: 3744)
- chrome.exe (PID: 2204)
Reads Internet Cache Settings
- chrome.exe (PID: 4012)
- chrome.exe (PID: 2204)
Starts Microsoft Office Application
- explorer.exe (PID: 252)
Reads settings of System Certificates
- Setup.exe (PID: 2944)
Creates files in the user directory
- WINWORD.EXE (PID: 720)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 720)
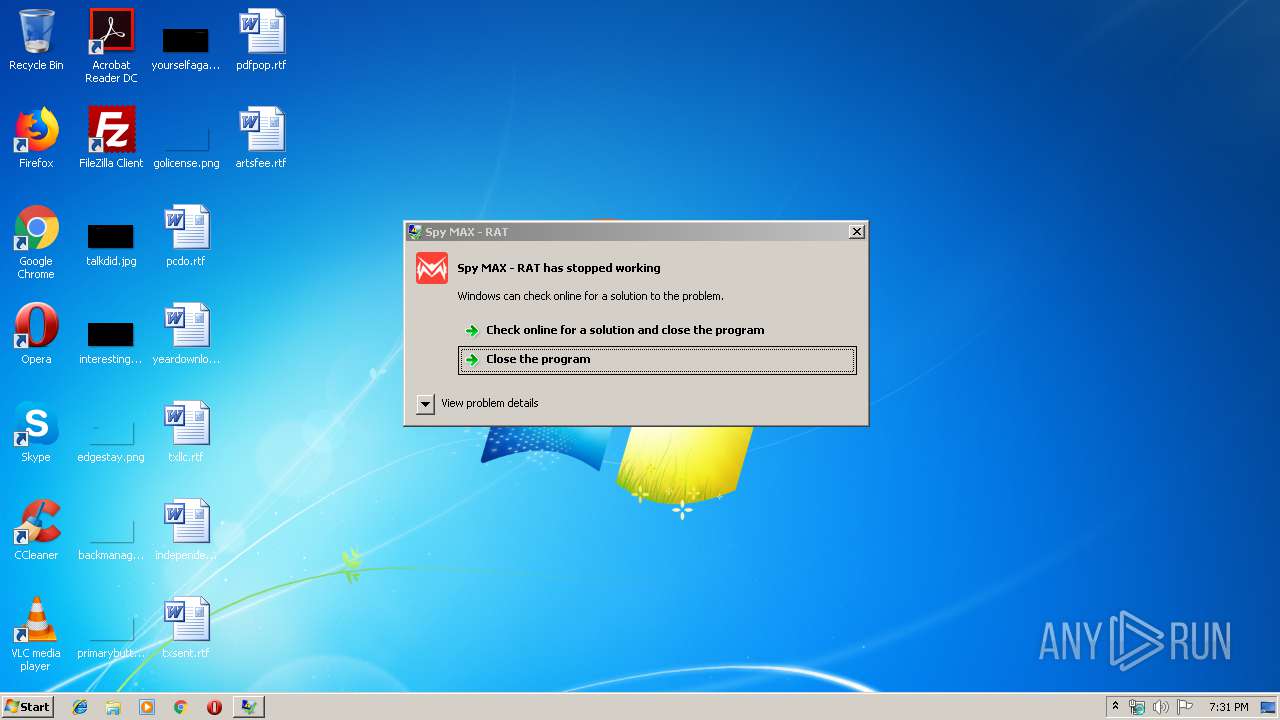
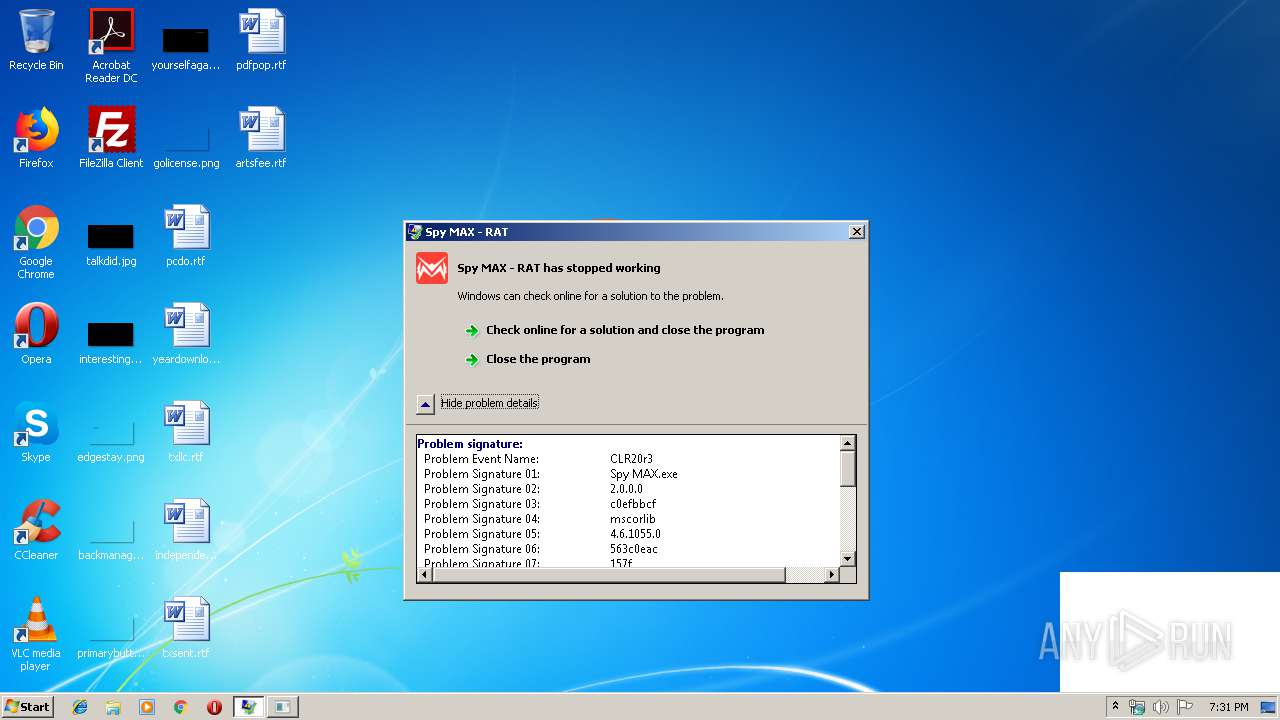
Application was crashed
- Spy MAX.exe (PID: 2952)
Changes settings of System certificates
- chrome.exe (PID: 3672)
Dropped object may contain Bitcoin addresses
- Setup.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2072:07:28 15:04:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 508928 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e2fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
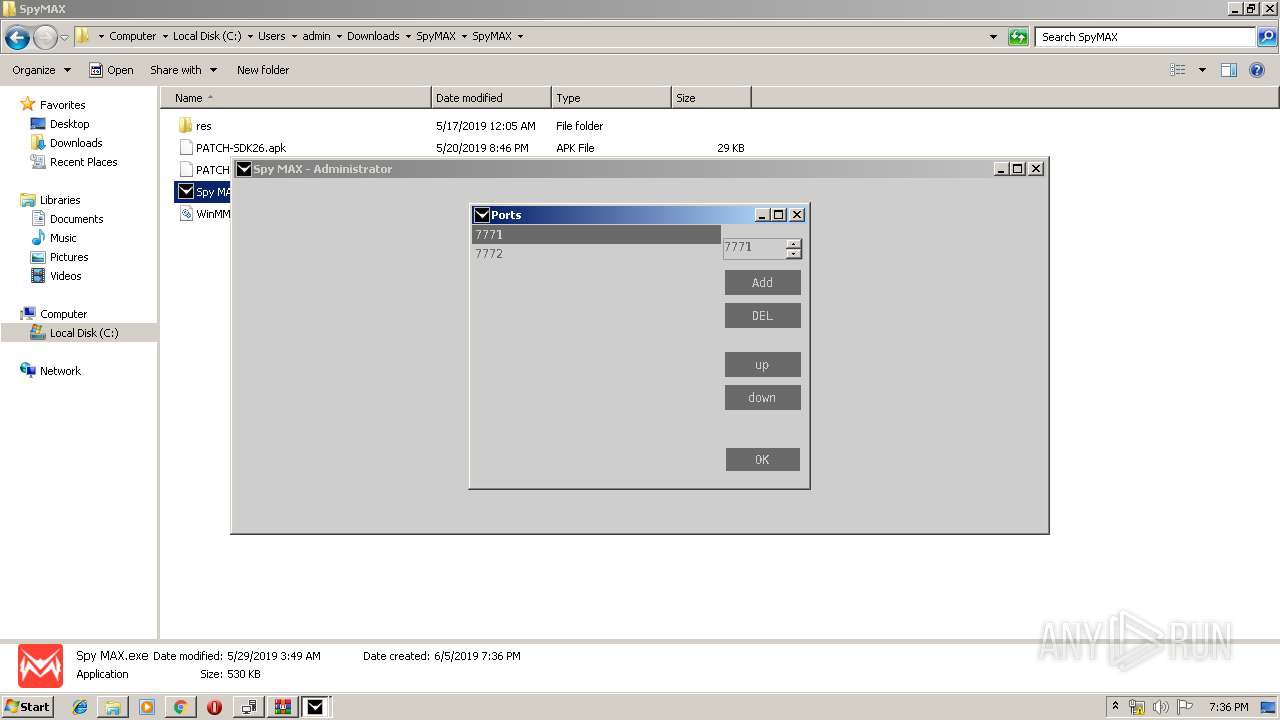
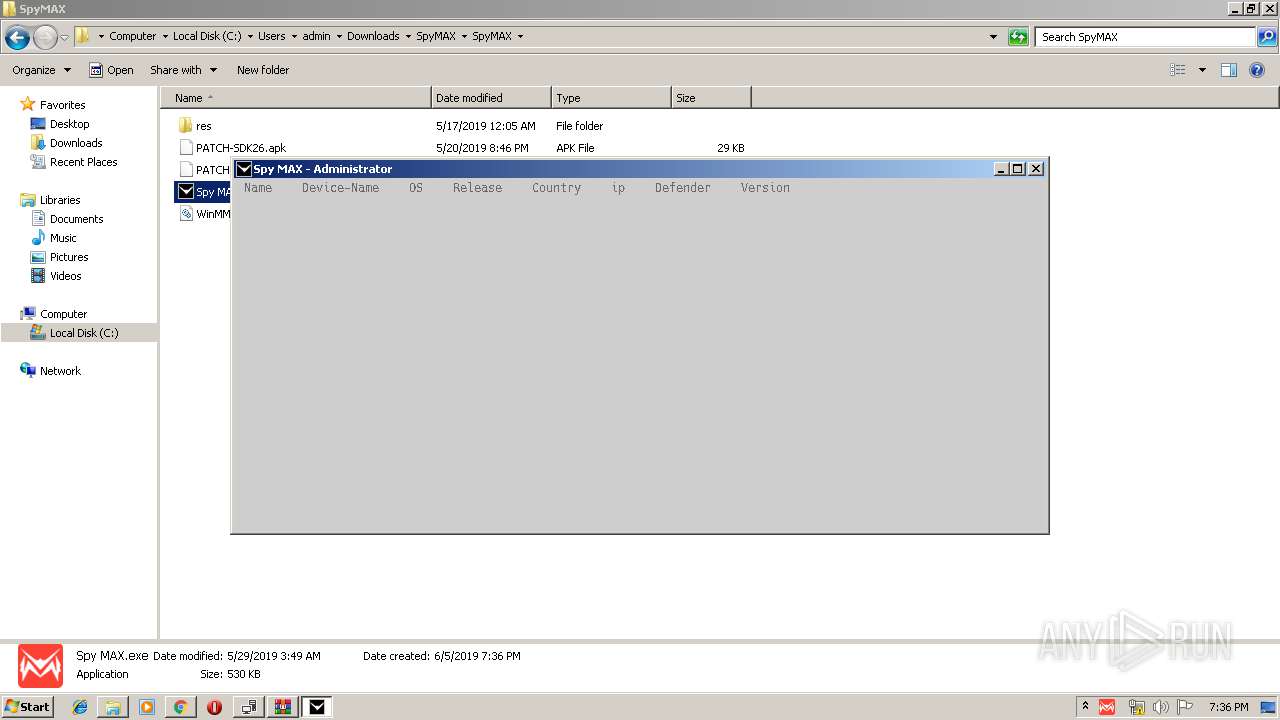
| FileDescription: | Spy MAX - RAT |
| FileVersion: | 2.0.0.0 |
| InternalName: | Spy MAX.exe |
| LegalCopyright: | Spy MAX © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | Spy MAX.exe |
| ProductName: | Spy MAX |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jun-1936 06:35:59 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Spy MAX - RAT |
| FileVersion: | 2.0.0.0 |
| InternalName: | Spy MAX.exe |
| LegalCopyright: | Spy MAX © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | Spy MAX.exe |
| ProductName: | Spy MAX |
| ProductVersion: | 2.0.0.0 |
| Assembly Version: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Jun-1936 06:35:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0007C374 | 0x0007C400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09183 |
.rsrc | 0x00080000 | 0x00007F48 | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.01038 |
.reloc | 0x00088000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00451 | 3174 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.17683 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.83734 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.78061 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.61862 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.64638 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
109
Monitored processes
62
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ctfmon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11984697935390650633,409527524776247161,131072 --enable-features=PasswordImport --service-pipe-token=4111052884503653526 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4111052884503653526 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
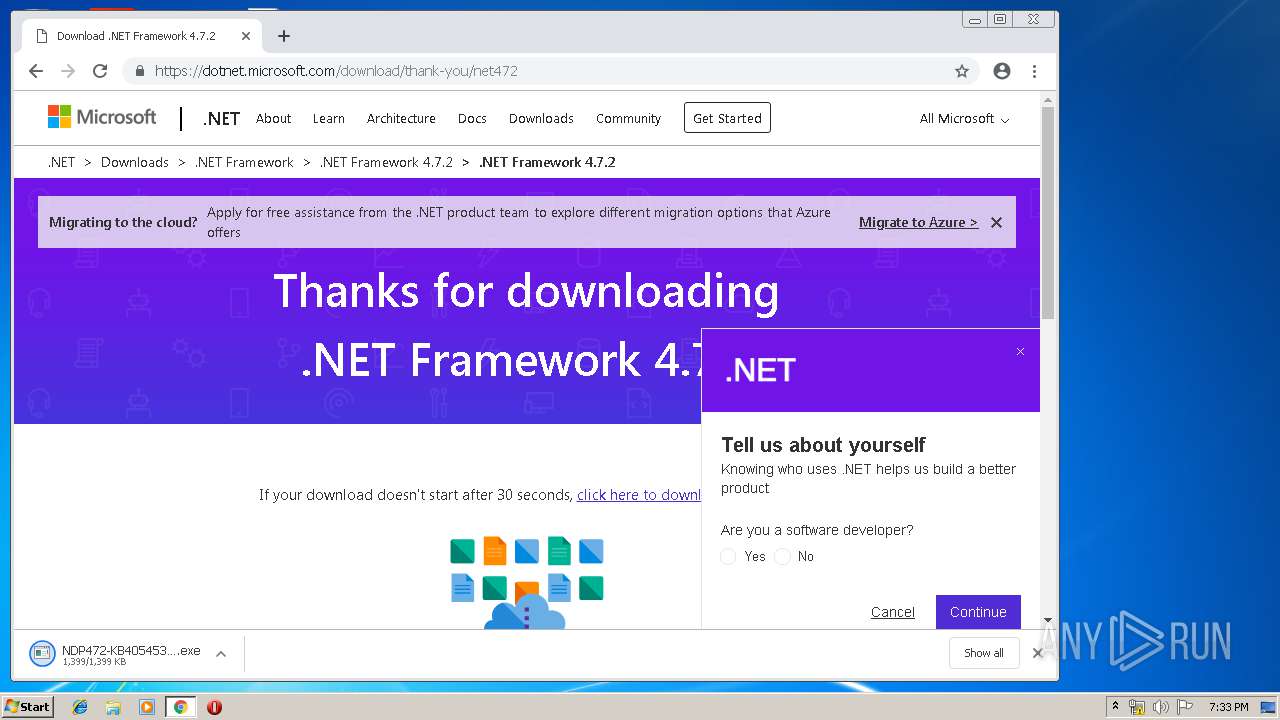
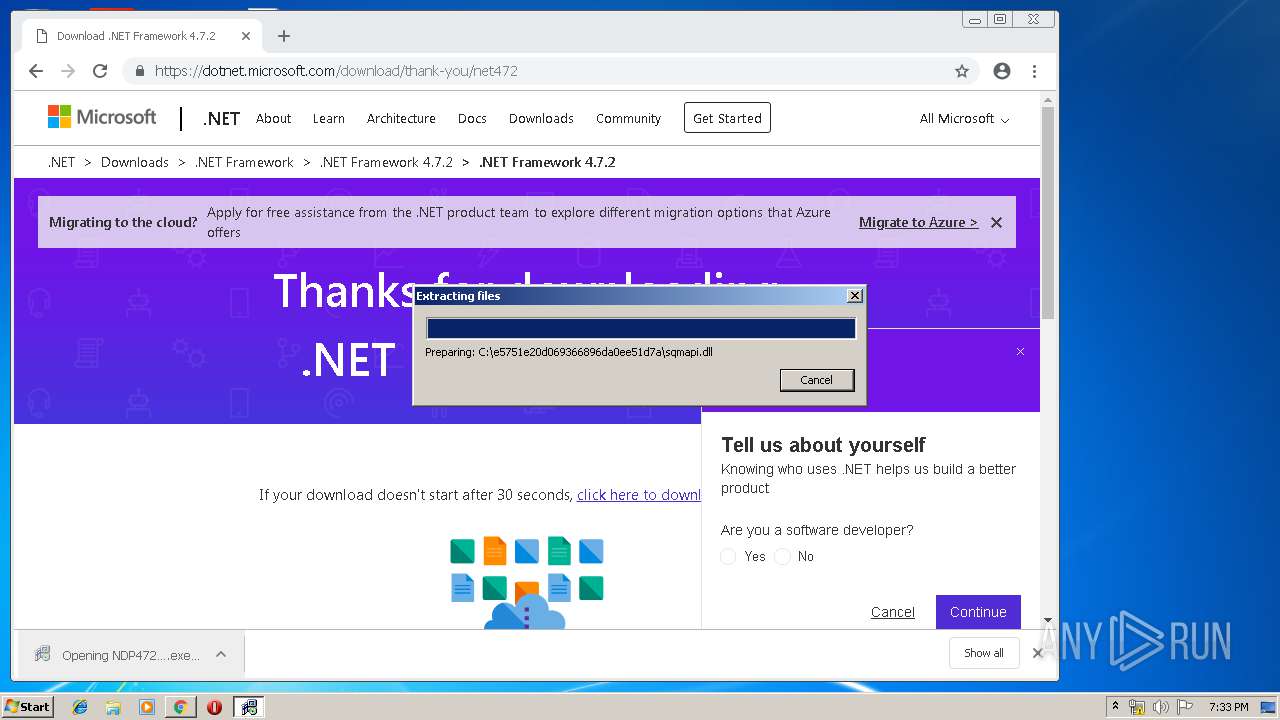
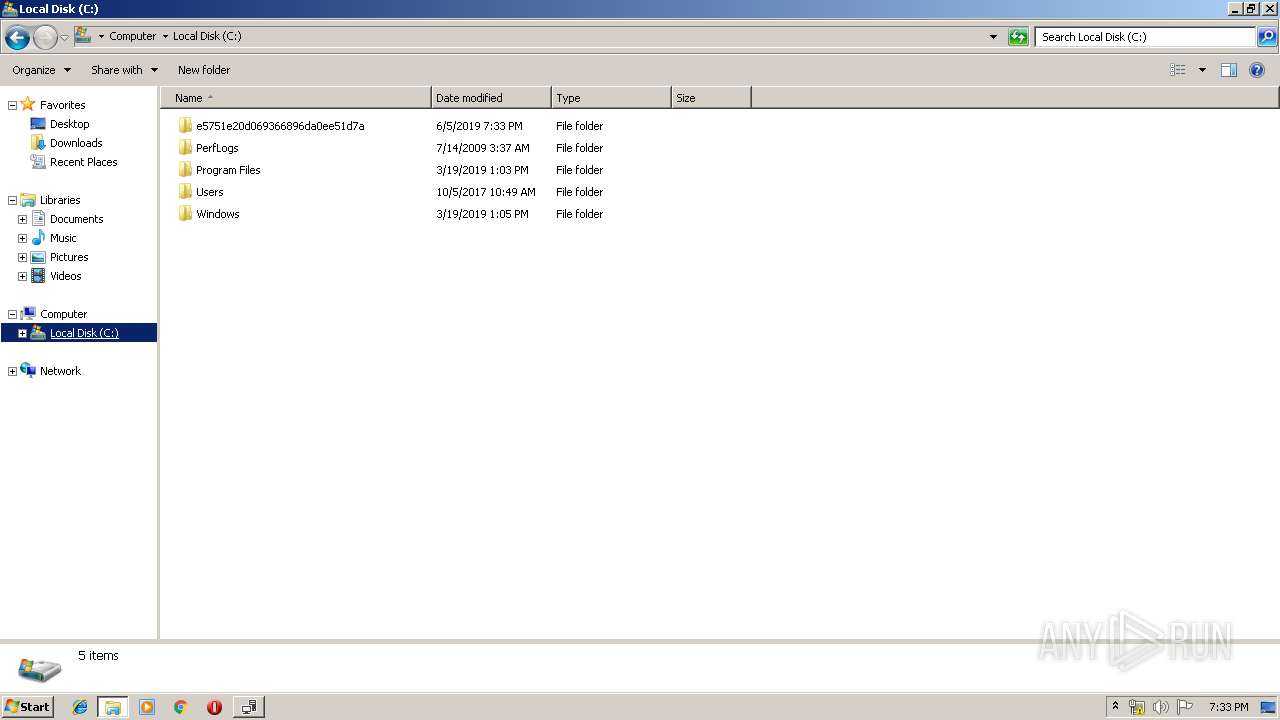
| 568 | TMP3BAE.tmp.exe /Q /X:C:\e5751e20d069366896da0ee51d7a\TMP3BAE.tmp.exe.tmp | C:\e5751e20d069366896da0ee51d7a\TMP3BAE.tmp.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.7.2 Setup Exit code: 0 Version: 4.7.03062.00 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,4663598933880569616,17396990127048819987,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1100522422373558810 --mojo-platform-channel-handle=2788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
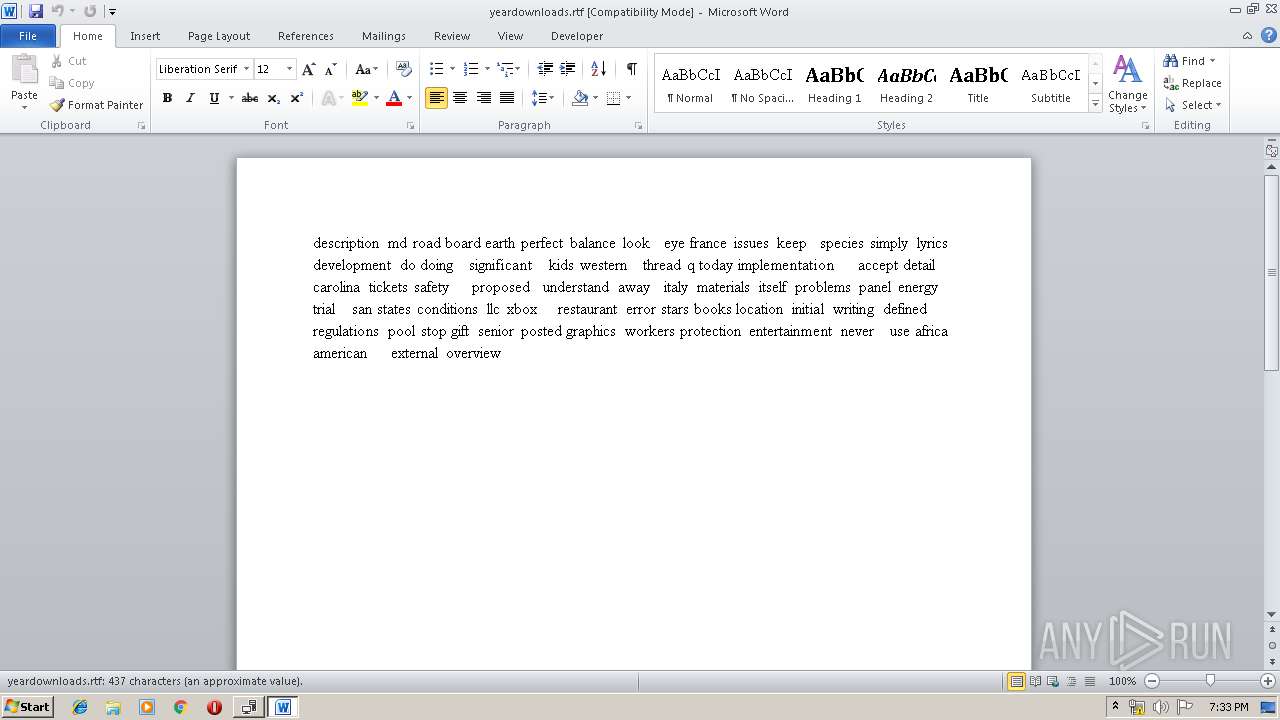
| 720 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\yeardownloads.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11984697935390650633,409527524776247161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1344880016816514122 --mojo-platform-channel-handle=3660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,4663598933880569616,17396990127048819987,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14749124186450856052 --mojo-platform-channel-handle=3176 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11984697935390650633,409527524776247161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10775778008024405440 --mojo-platform-channel-handle=4176 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11984697935390650633,409527524776247161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11627822126743894516 --mojo-platform-channel-handle=3820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
6 903
Read events
5 960
Write events
915
Delete events
28
Modification events
| (PID) Process: | (2952) Spy MAX.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2952) Spy MAX.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Fcl ZNK.rkr |
Value: 00000000000000000100000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000500000003000000AE9C000003000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E8350203000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E8350203000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E83502 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Fcl ZNK.rkr |
Value: 000000000000000001000000DF020000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000005000000030000008D9F000003000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E8350203000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E8350203000000020000001B6900004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D000000350201000000000000000000A27650E935023CE735025E7C37777CE93502787C3777030000008A018C01EC92CB026CE73502F77C37770100000050E93502847C3777BCE73502B0E73502C8E73502000000000000000000000000B8E7350250E93502000000000000000000000000F0E83502F0E8350200000000010000007CE93502F0E83502B2FE3777F270377785FC3777B5860A759A7C3677EC92CB02A27E367734E935021800000014FB3502006F367700000000000000001CE935023C003E007CE93502C34E9D00BCE7350200000000D84609000000350218E8350204EB350200000088C8000000C8000000C8000000C8000000F2010300000000000000D868A8D33A030106004000000000F0EA35021053D8687FEB9C7620000000220000001053D868102FD8020000000011000000B8450A00B0450A00A8D33A03ACE800001FB258415CE835028291BE75ACE8350260E835022795BE750000000054CAD20288E83502CD94BE7554CAD20234E93502C8C5D202E194BE7500000000C8C5D20234E9350290E83502 | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\display.dll,-4 |
Value: S&creen resolution | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Common Files\System\wab32res.dll,-4602 |
Value: Contact file | |||
| (PID) Process: | (252) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Windows Sidebar\sidebar.exe,-11100 |
Value: &Gadgets | |||
Executable files
37
Suspicious files
213
Text files
821
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dbfe851e-c7a4-4543-8b75-edbe911f1c2d.tmp | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 4012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
103
DNS requests
79
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
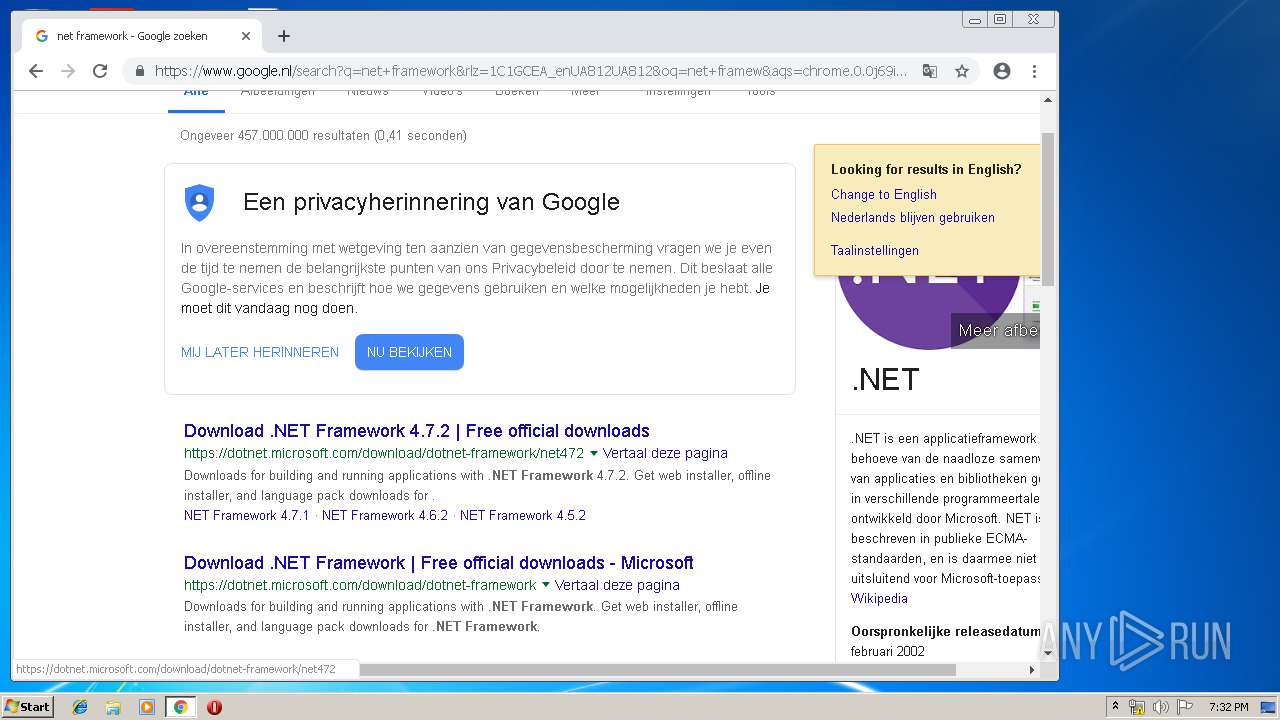
4012 | chrome.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?LinkId=863262 | unknown | — | — | whitelisted |
— | — | HEAD | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=amd64&o1=netfx_Full_x86.msi | unknown | — | — | whitelisted |
— | — | HEAD | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=x86&o1=netfx_Full.mzz | unknown | — | — | whitelisted |
— | — | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=x86&o1=netfx_Full.mzz | unknown | — | — | whitelisted |
2944 | Setup.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | unknown | — | — | whitelisted |
— | — | HEAD | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | unknown | — | — | whitelisted |
— | — | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | unknown | — | — | whitelisted |
— | — | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03062.00&sar=amd64&o1=netfx_Full_x86.msi | unknown | — | — | whitelisted |
2944 | Setup.exe | GET | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | unknown | — | — | whitelisted |
— | — | HEAD | 302 | 2.19.38.59:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net472Rel1&plcid=0x409&clcid=0x409&ar=03081.00&sar=amd64&o1=netfx_Patch_x86.msp | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4012 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
4012 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 172.217.22.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 185.48.9.77:80 | r2---sn-x2pm-3ufd.gvt1.com | Stowarzyszenie Na Rzecz Rozwoju Spoleczenstwa Informacyjnego e-Poludnie | PL | whitelisted |
4012 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4012 | chrome.exe | 172.217.16.131:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The form specified for the subject is not one supported or known by the specified trust provider.
|