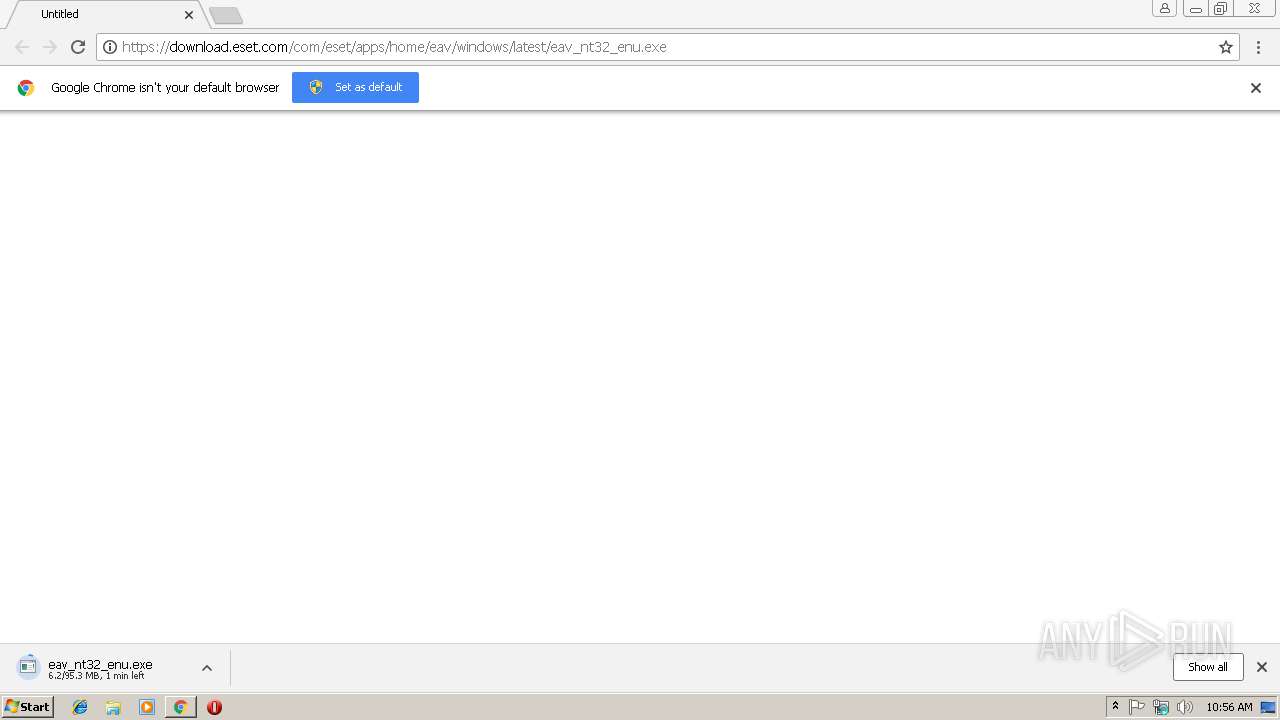
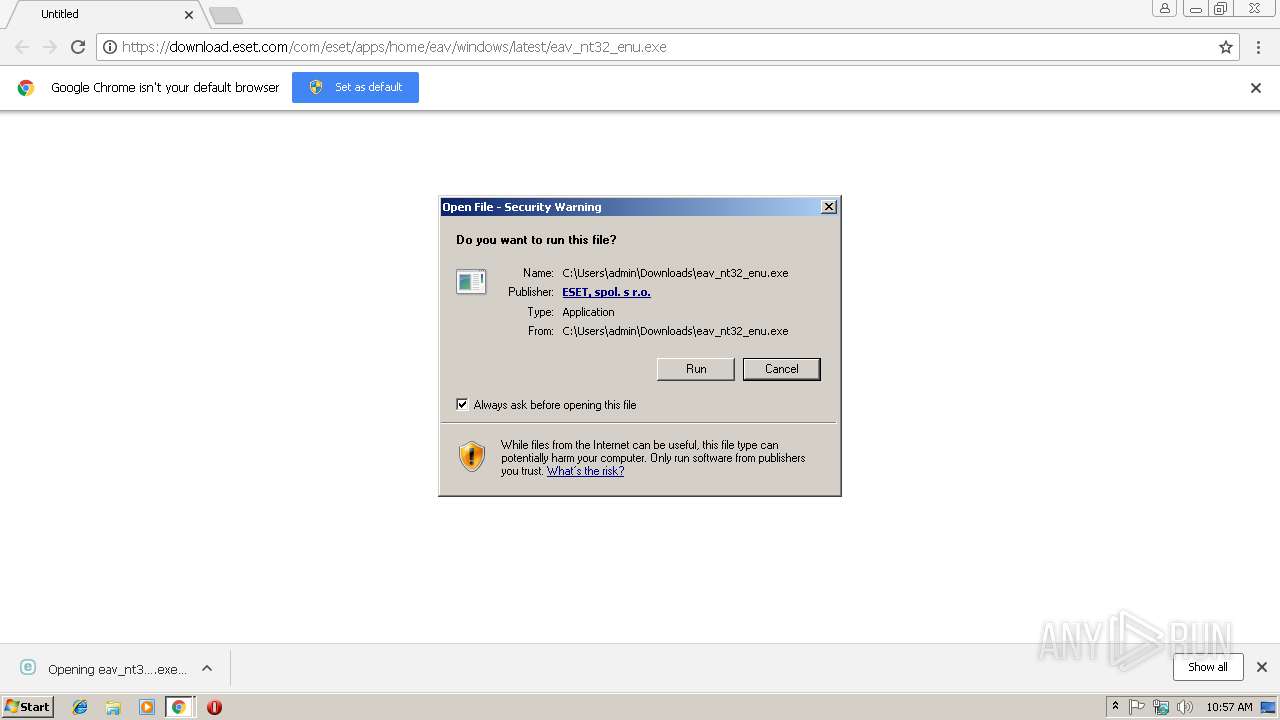
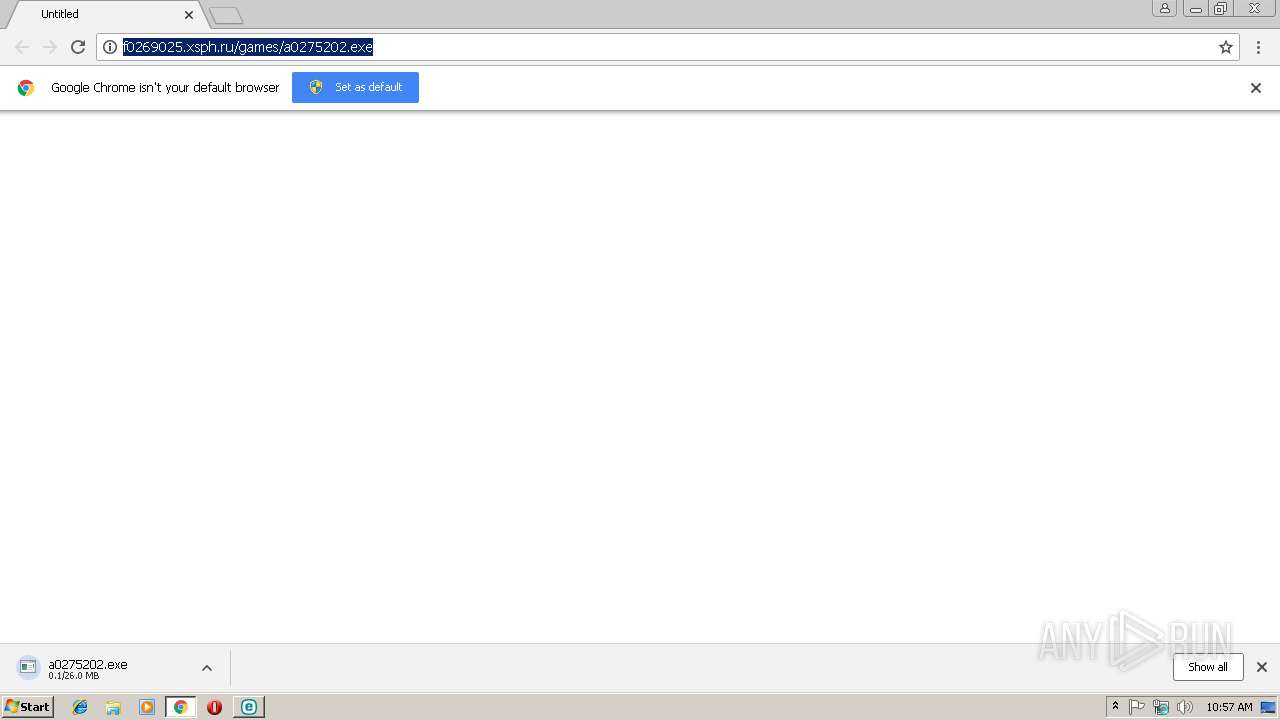
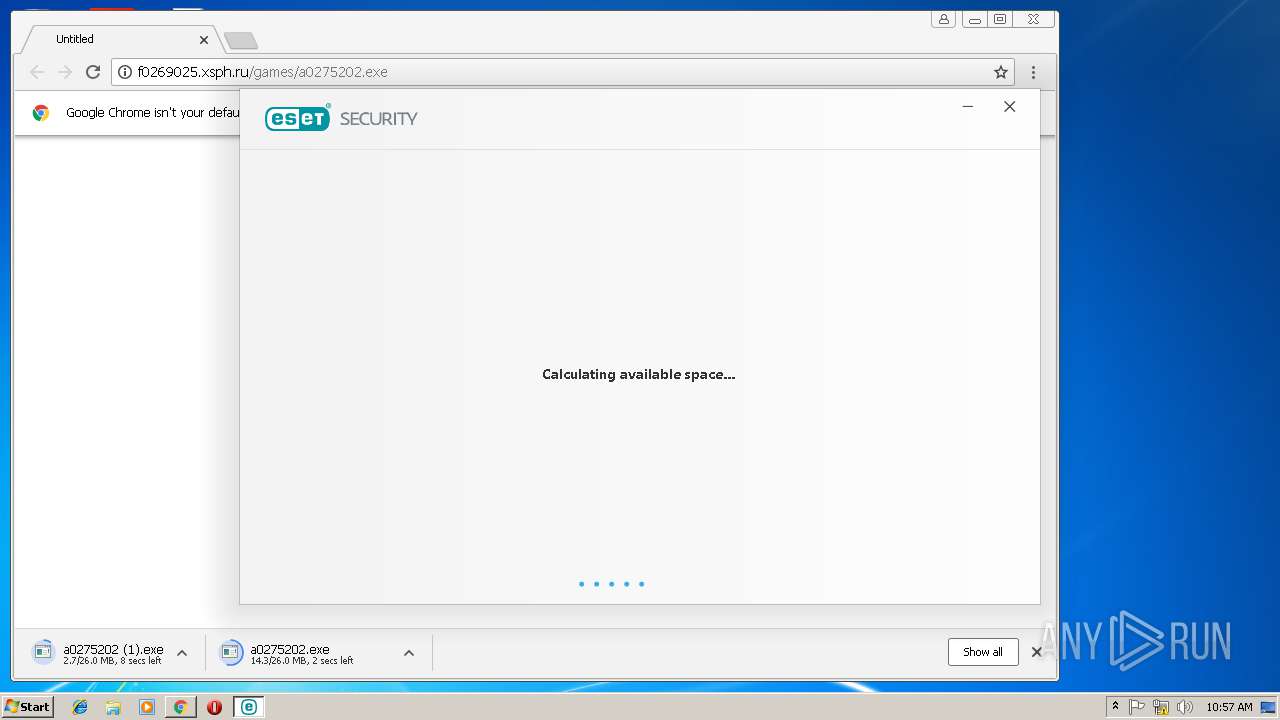
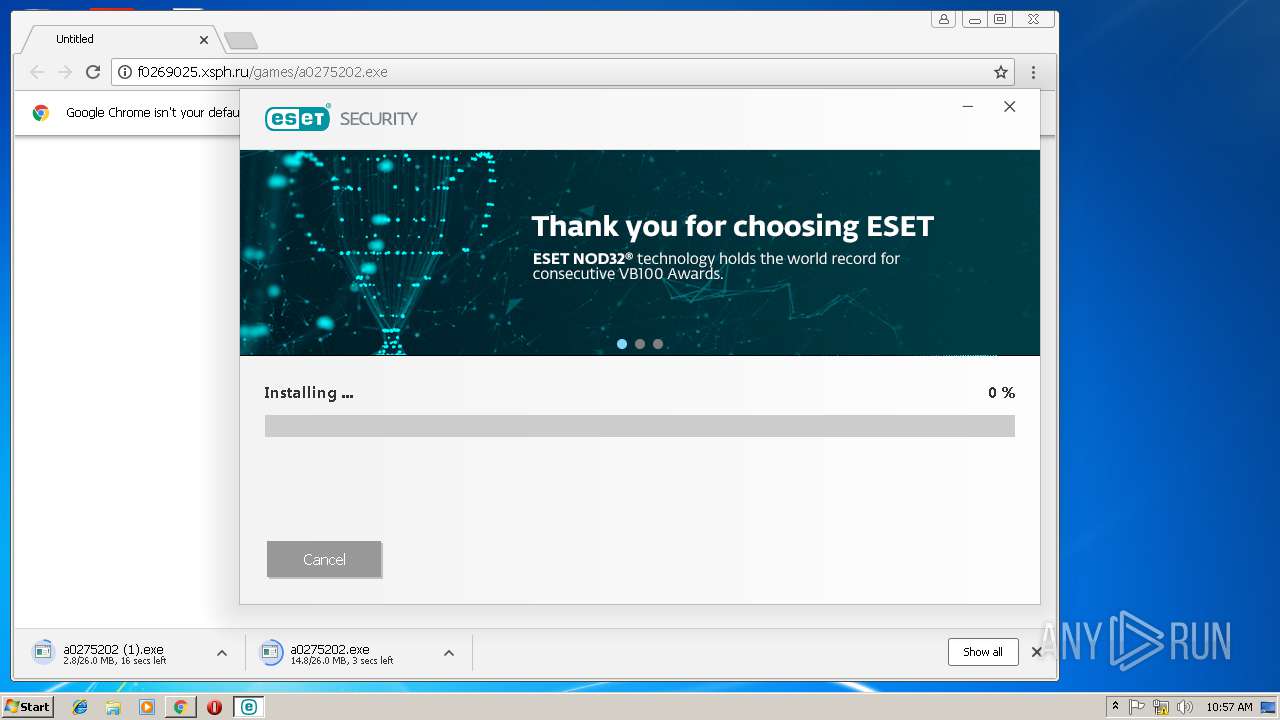
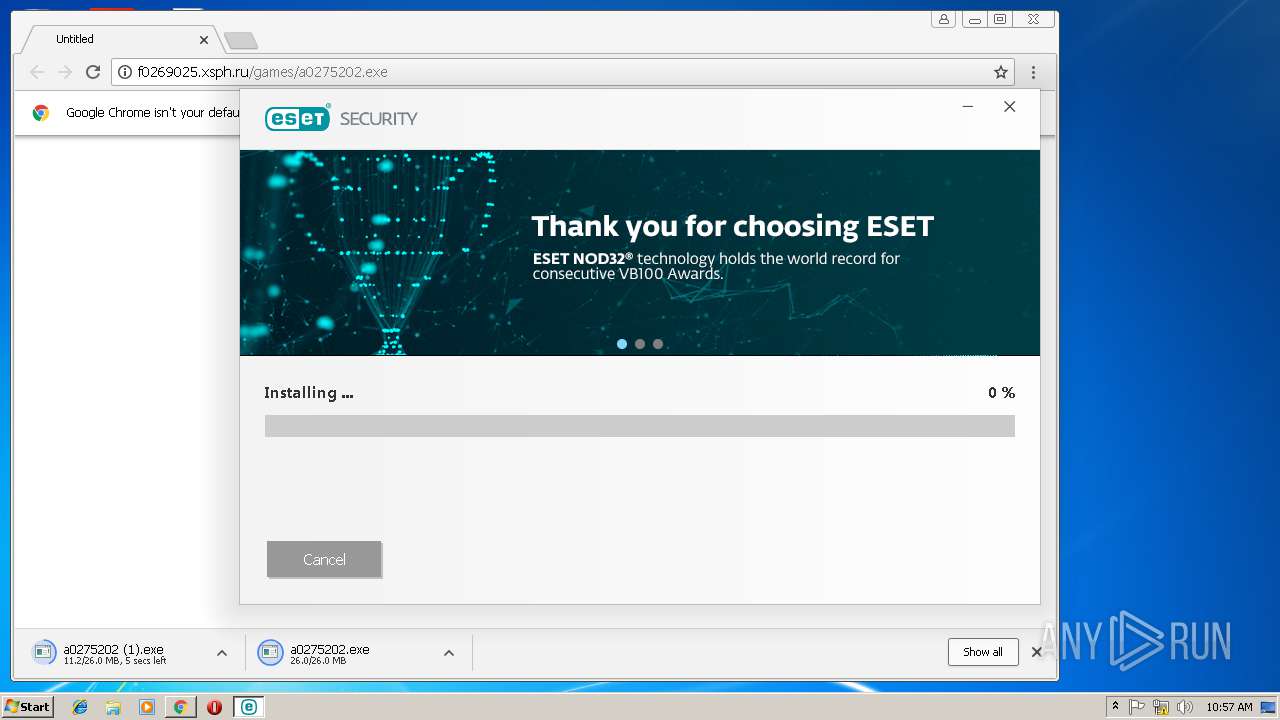
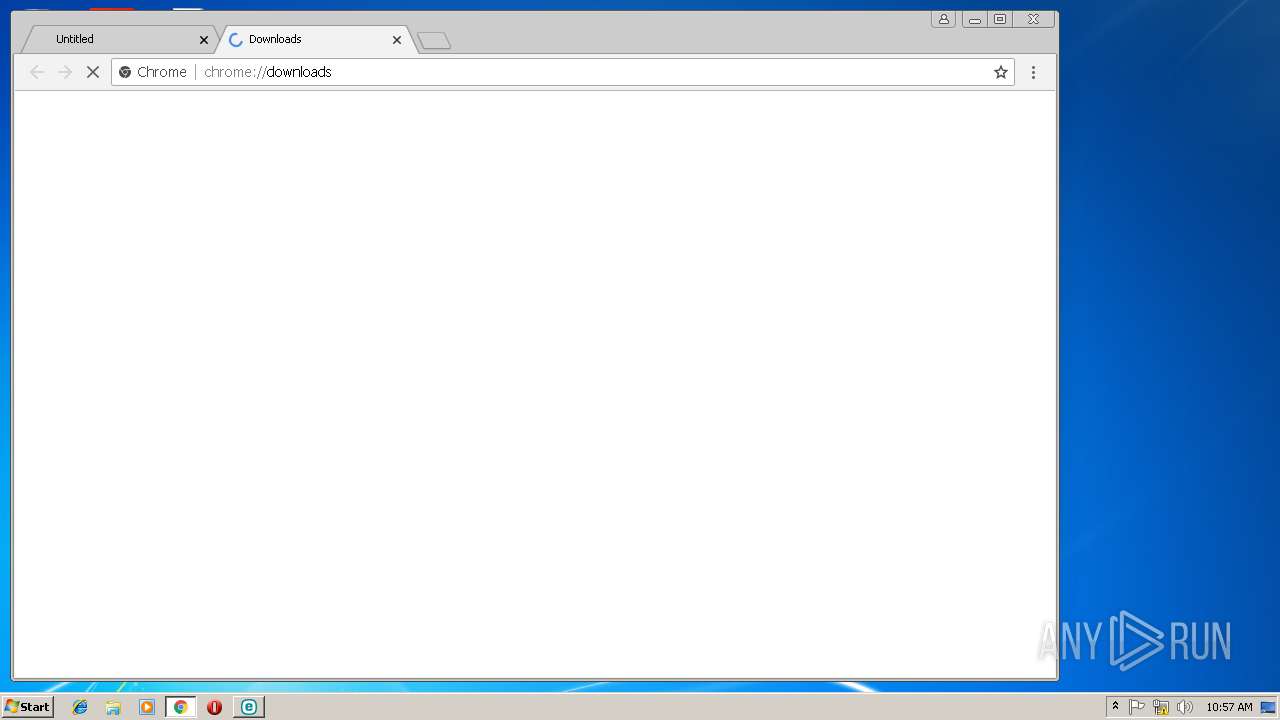
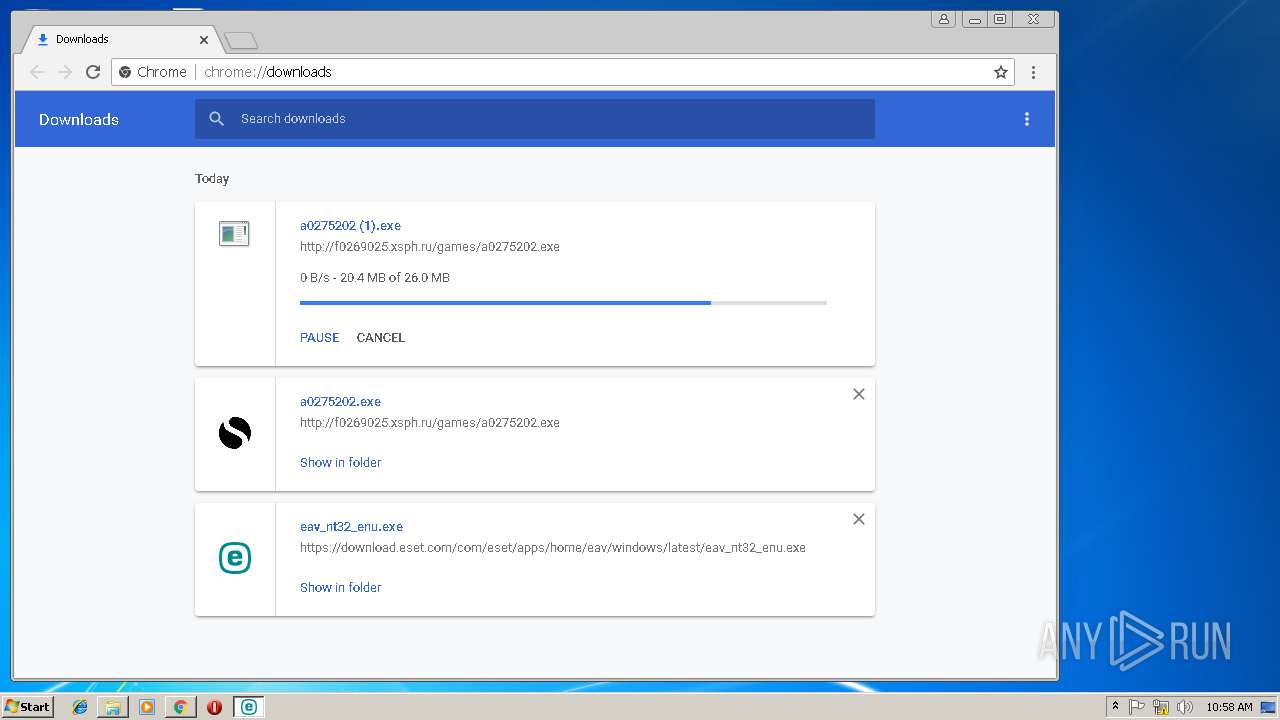
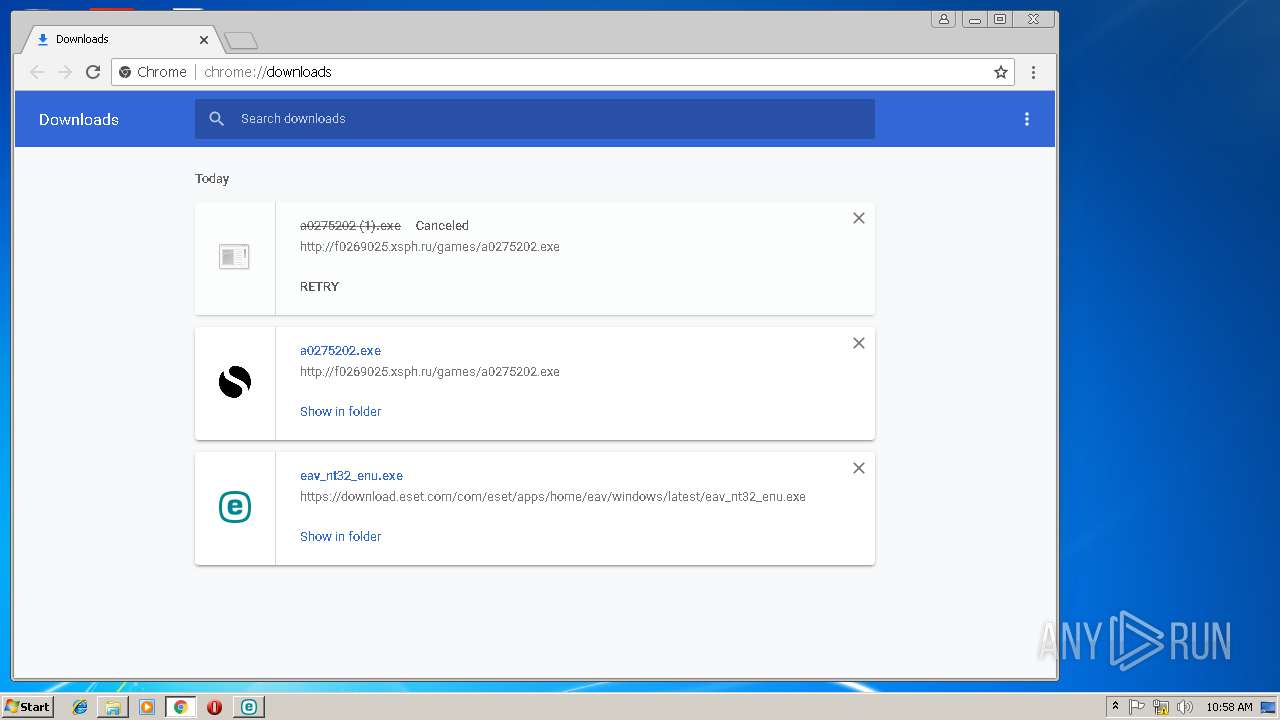
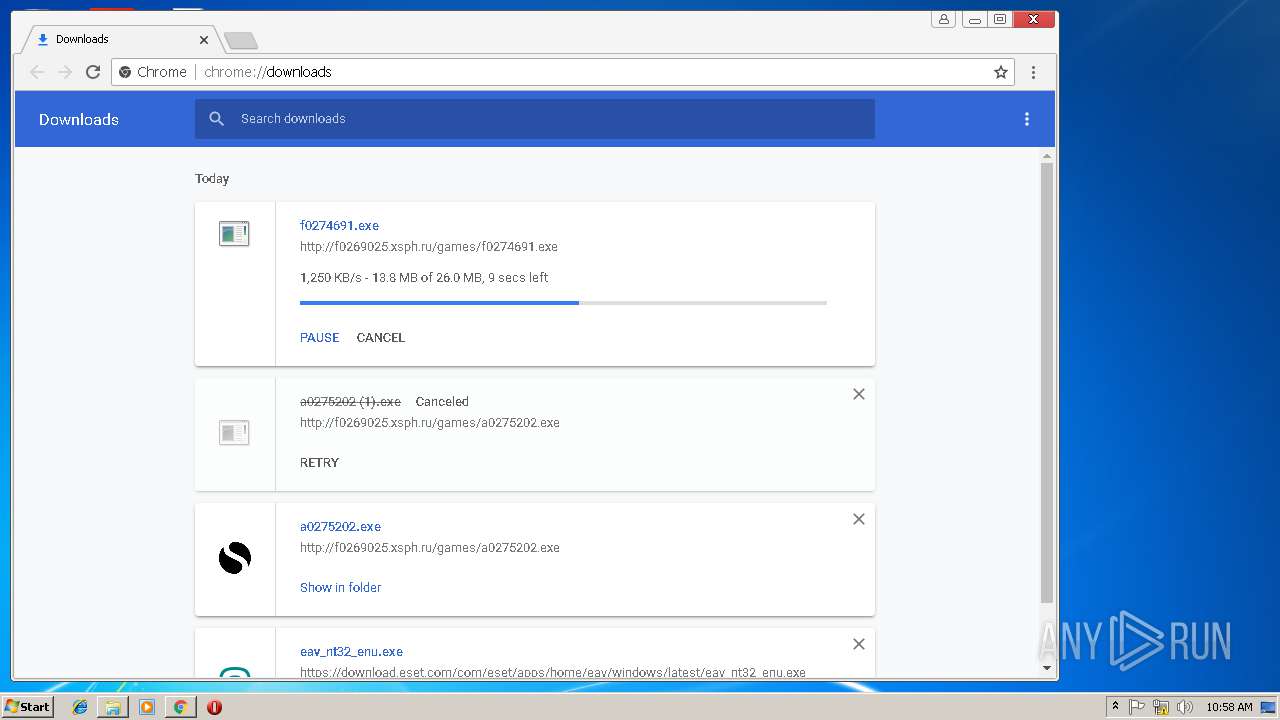
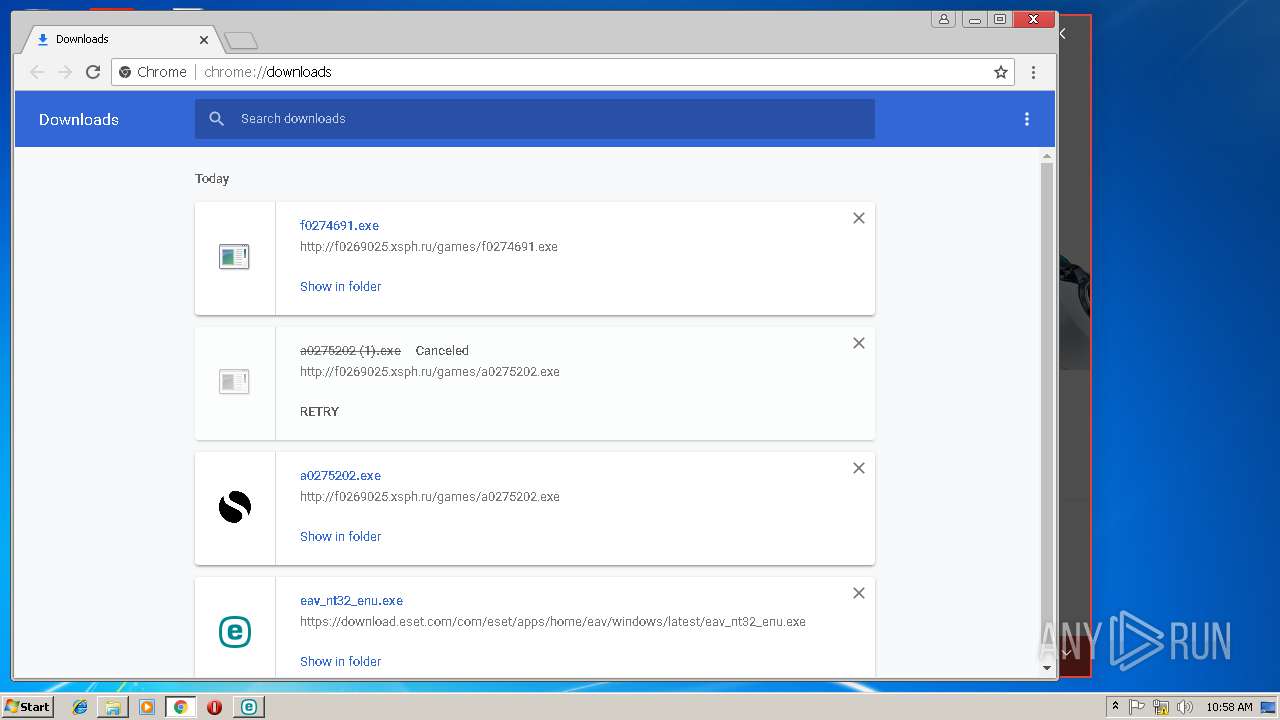
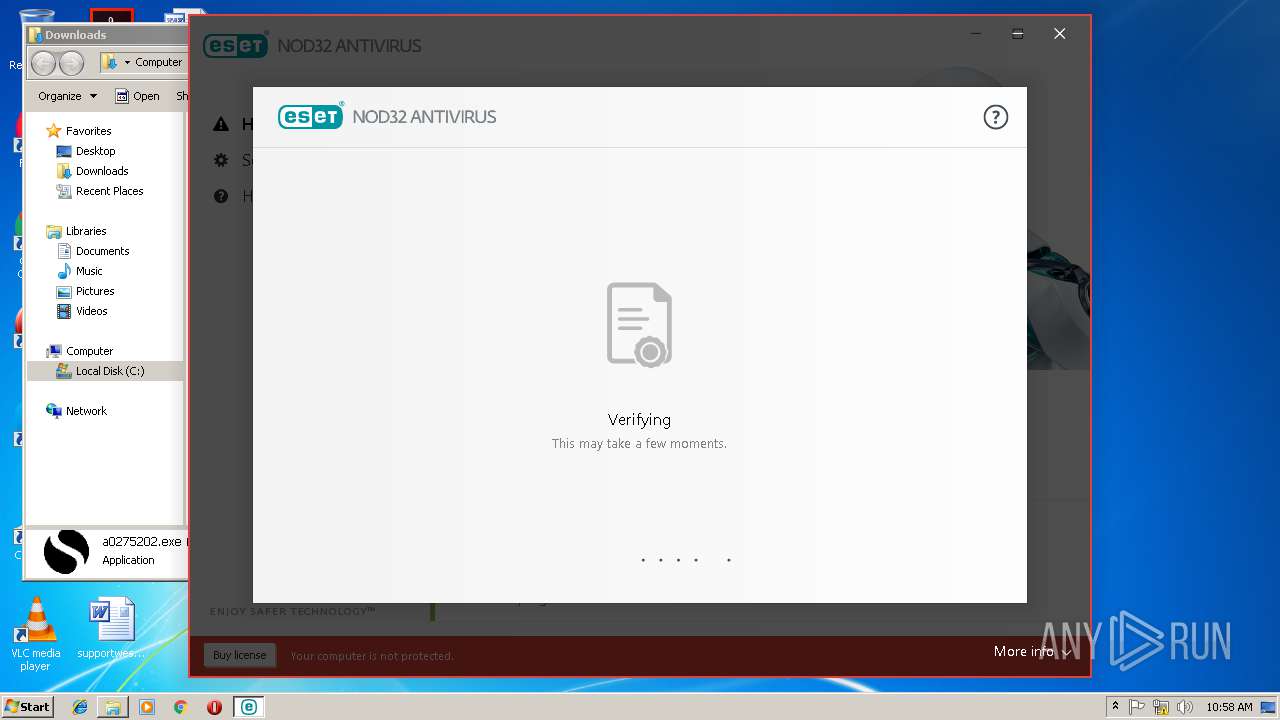
| URL: | https://download.eset.com/com/eset/apps/home/eav/windows/latest/eav_nt32_enu.exe |
| Full analysis: | https://app.any.run/tasks/d2806eaa-d013-4ddc-82d1-9ec490527b45 |
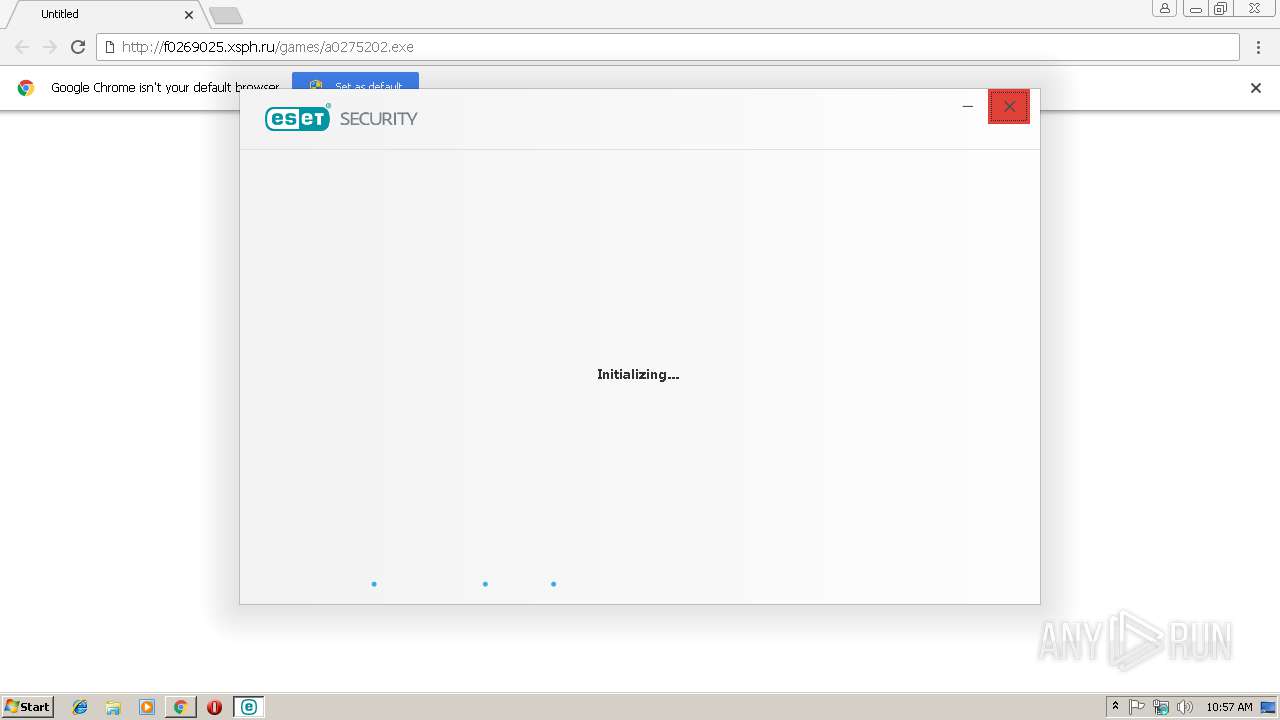
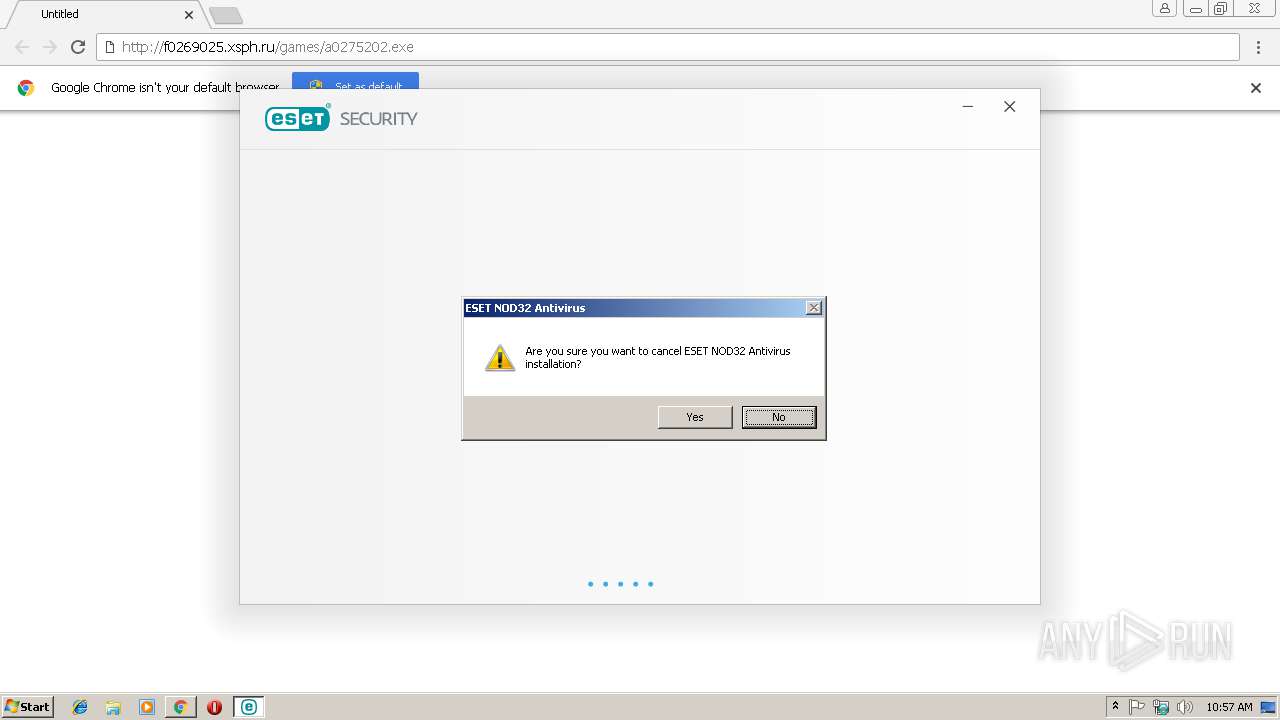
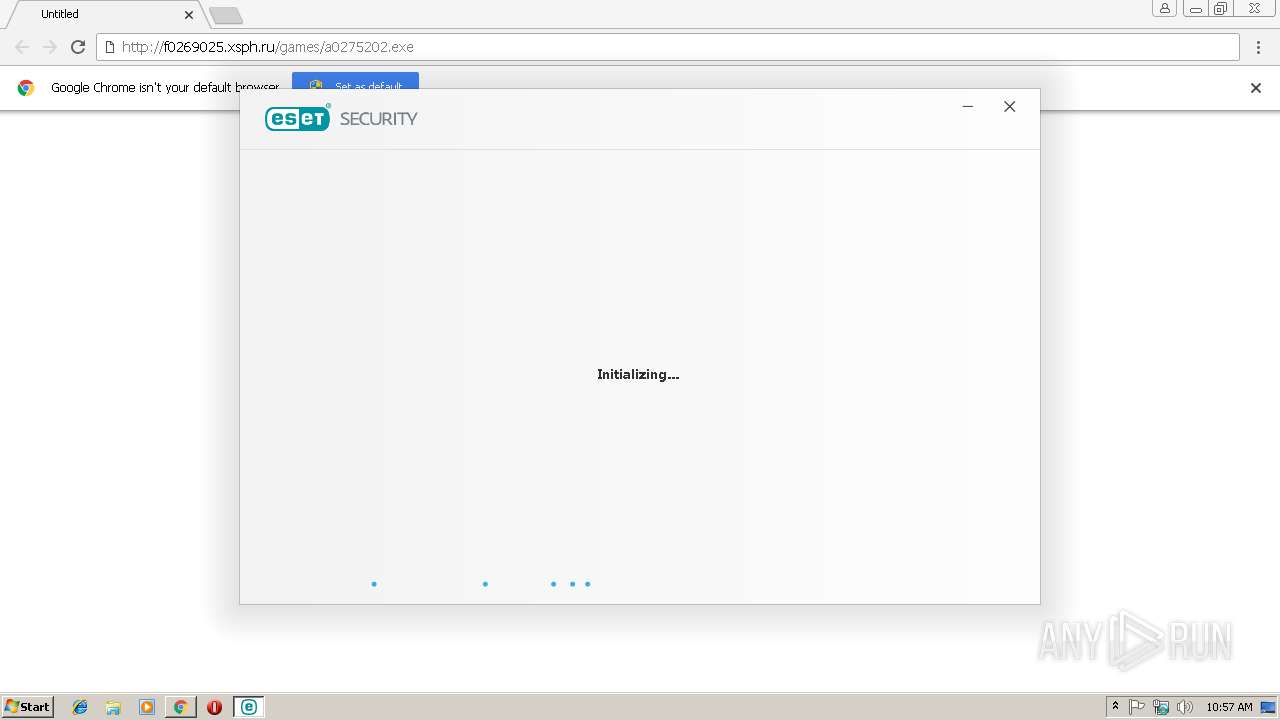
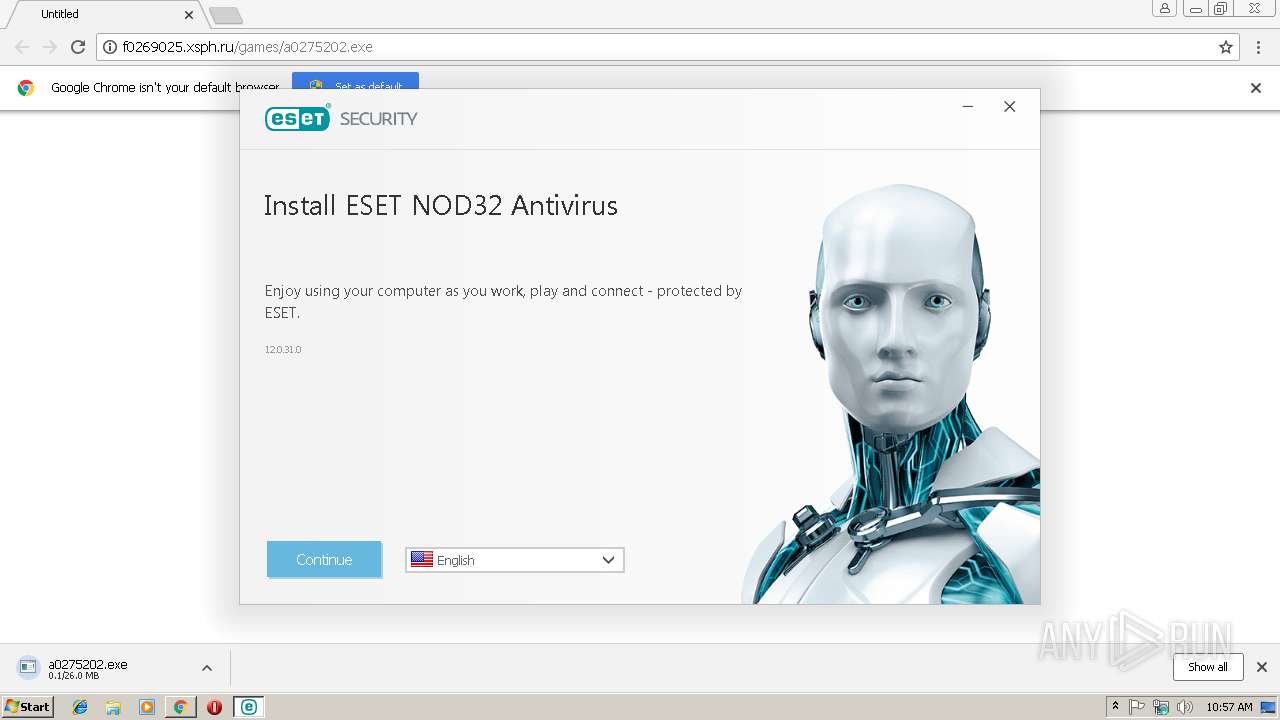
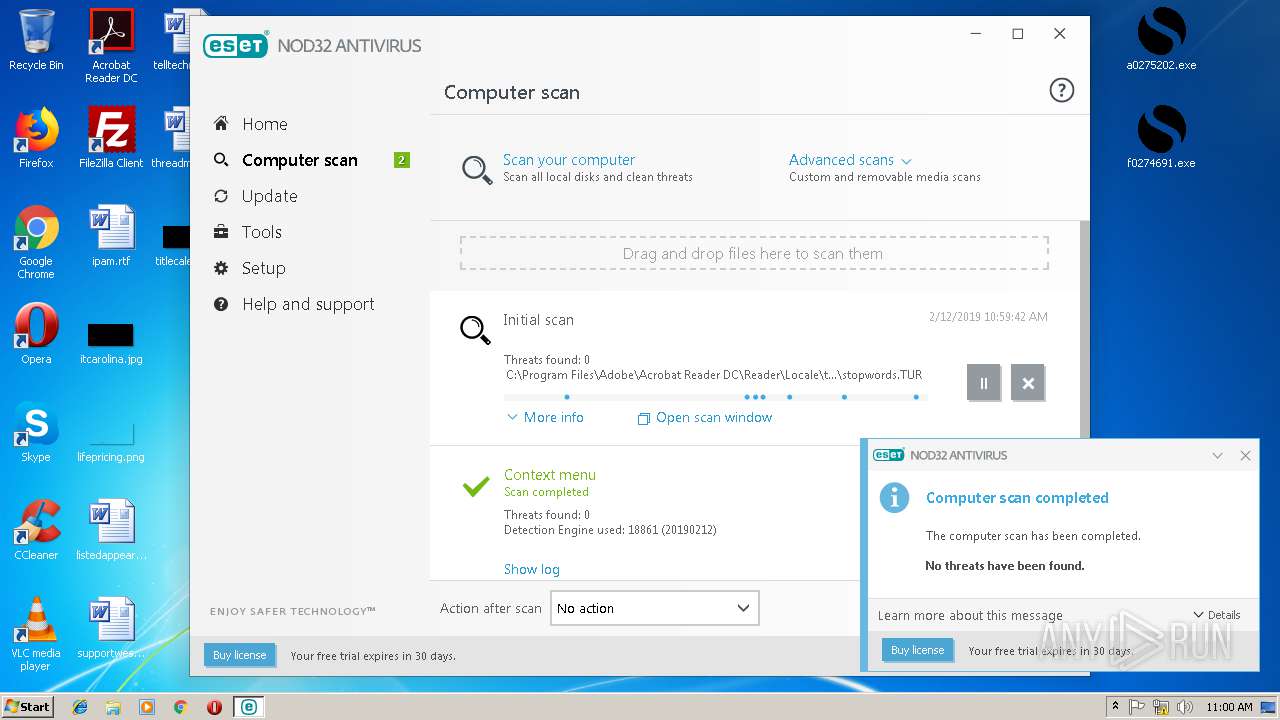
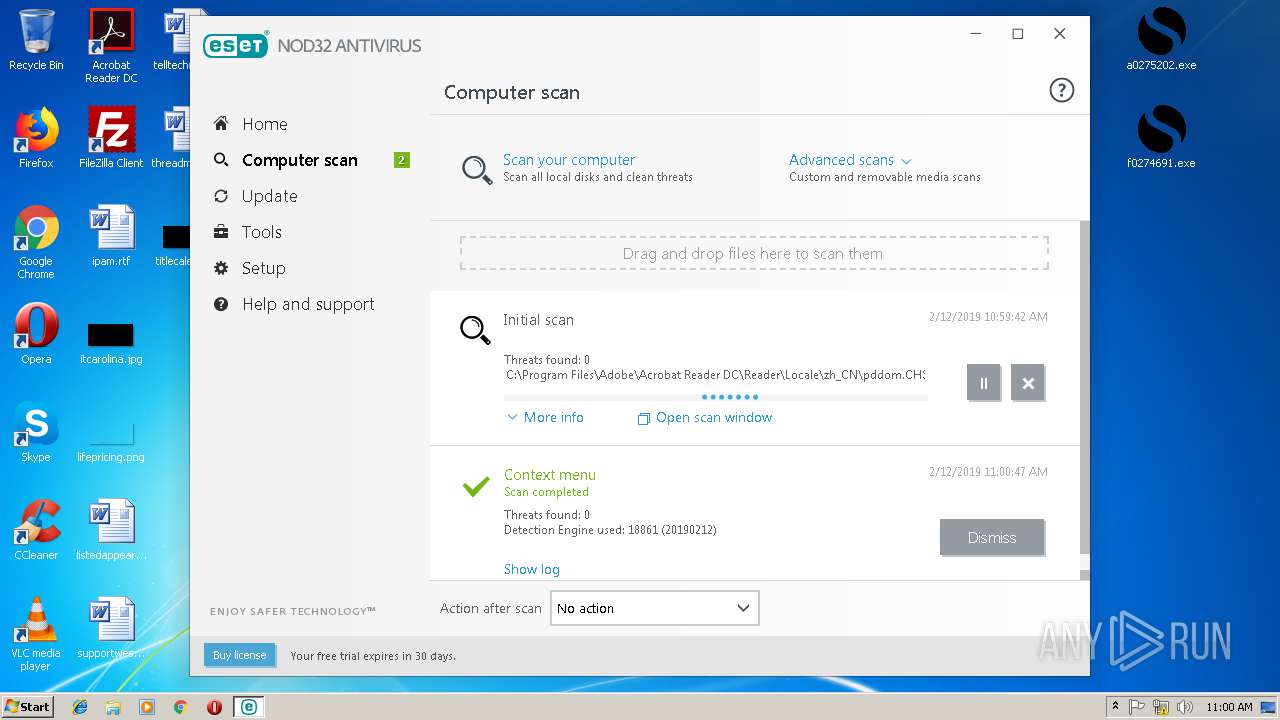
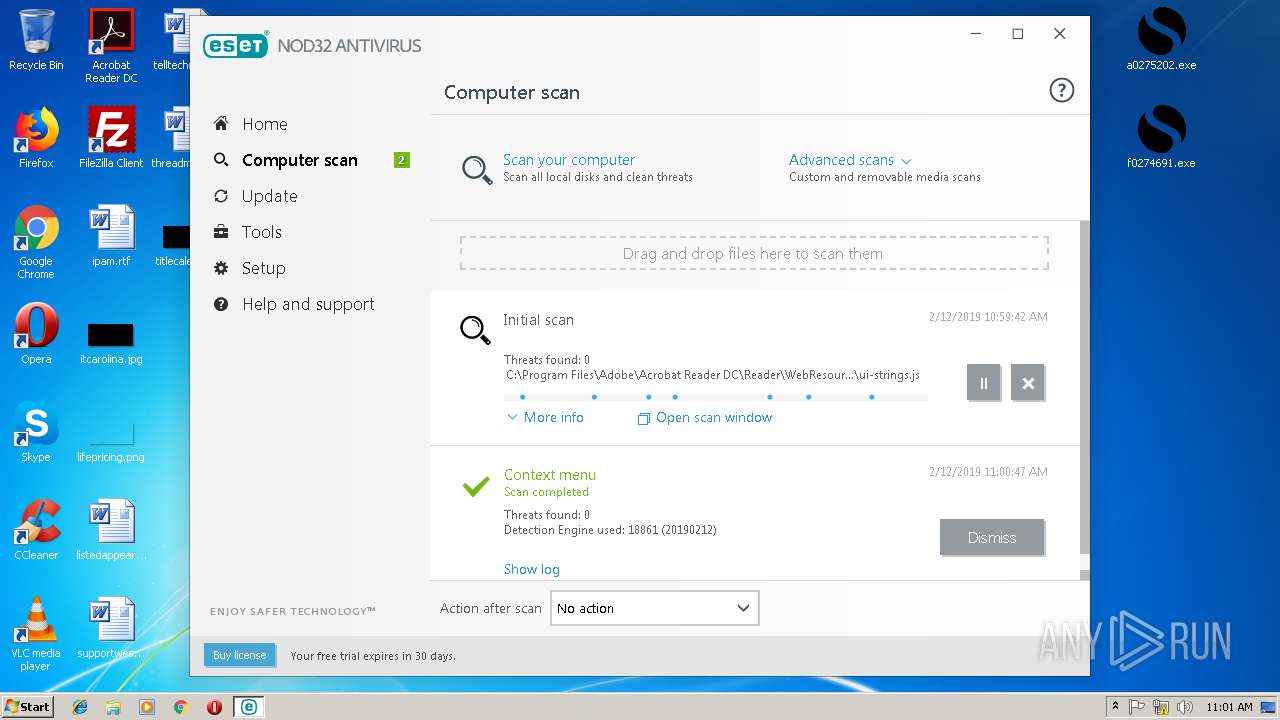
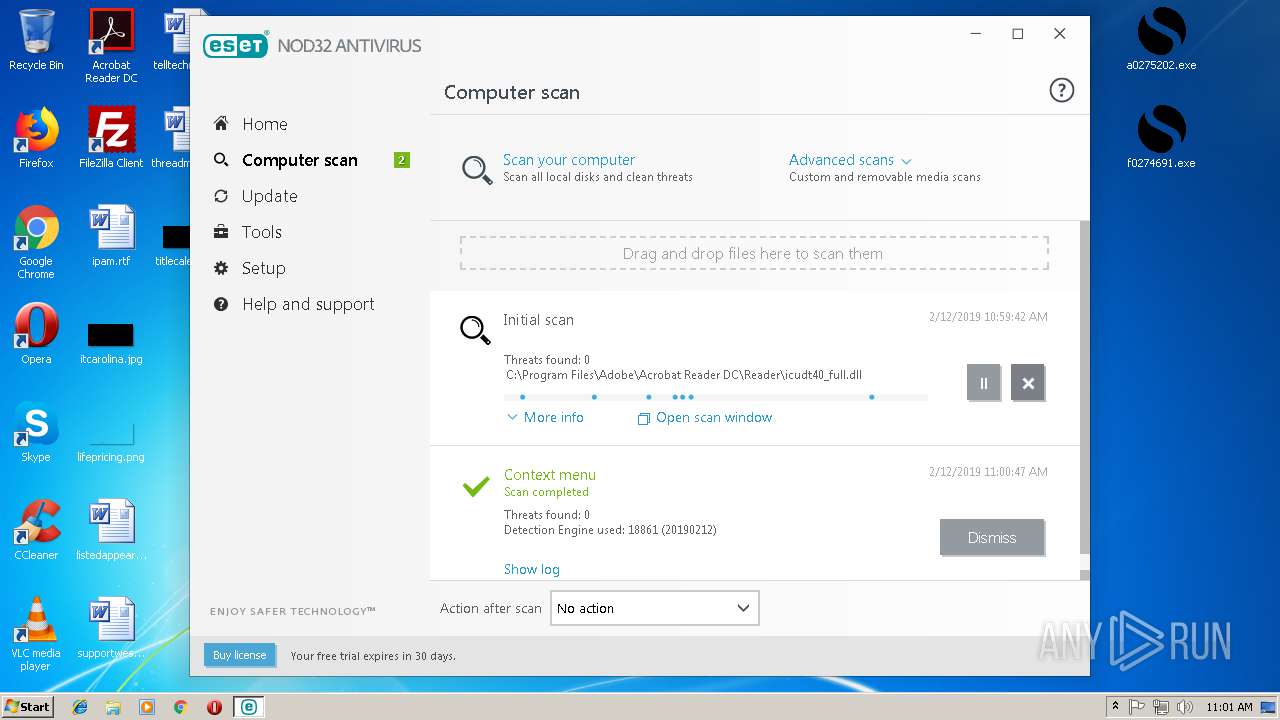
| Verdict: | Malicious activity |
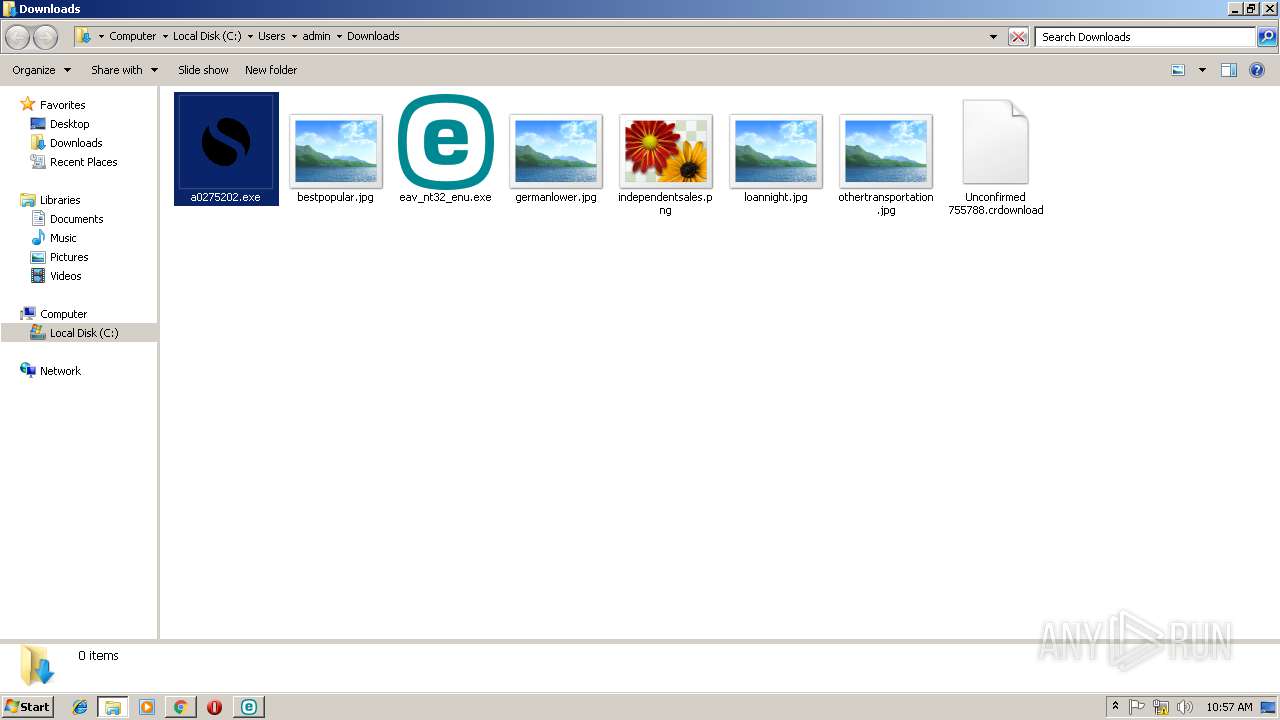
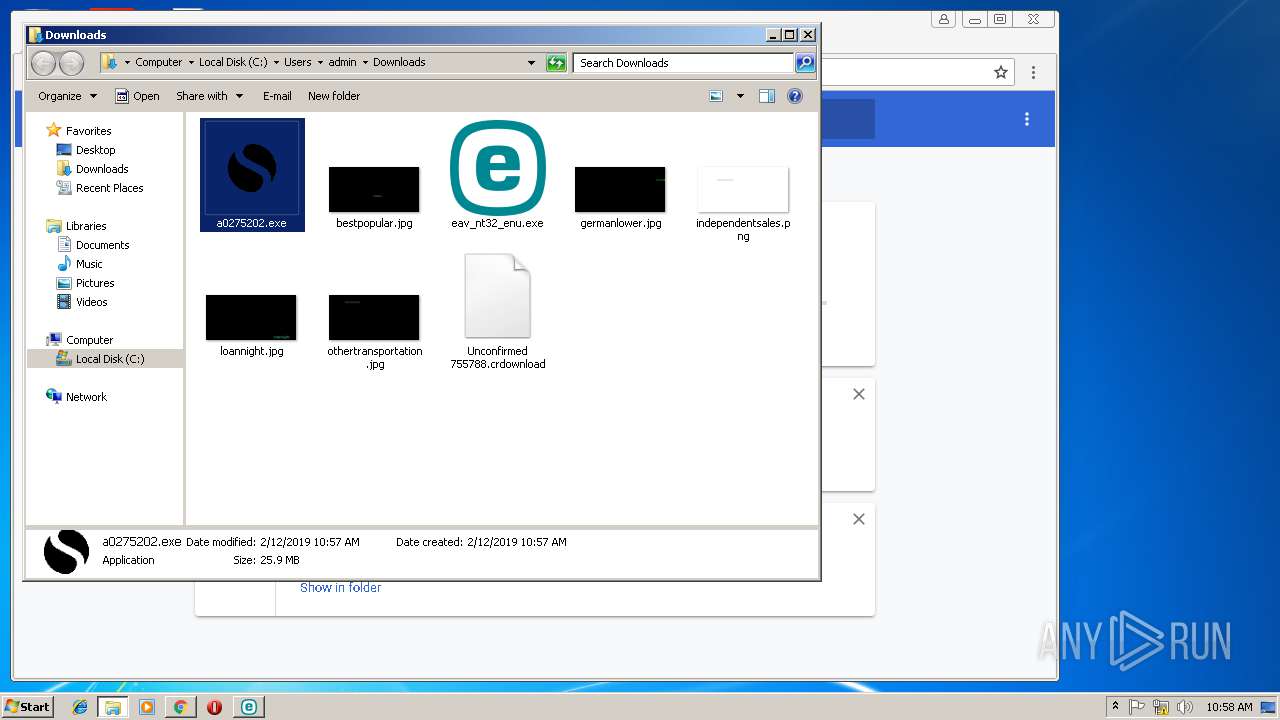
| Analysis date: | February 12, 2019, 10:56:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 138845DD114E66AF62BAB6553DC0DD03 |
| SHA1: | 7ADBCD317C087C9E38A8E2832A66C99930B912A6 |
| SHA256: | AFB80F8ECD46CD539ACF24FFEB8EF7344C43E9B357B4FFF07772DFFCE6FB05EA |
| SSDEEP: | 3:N8SElsRLKIIyAsSAbhdJERAW/Mque4An:2SKstKKSAbhdKRQP1An |
MALICIOUS
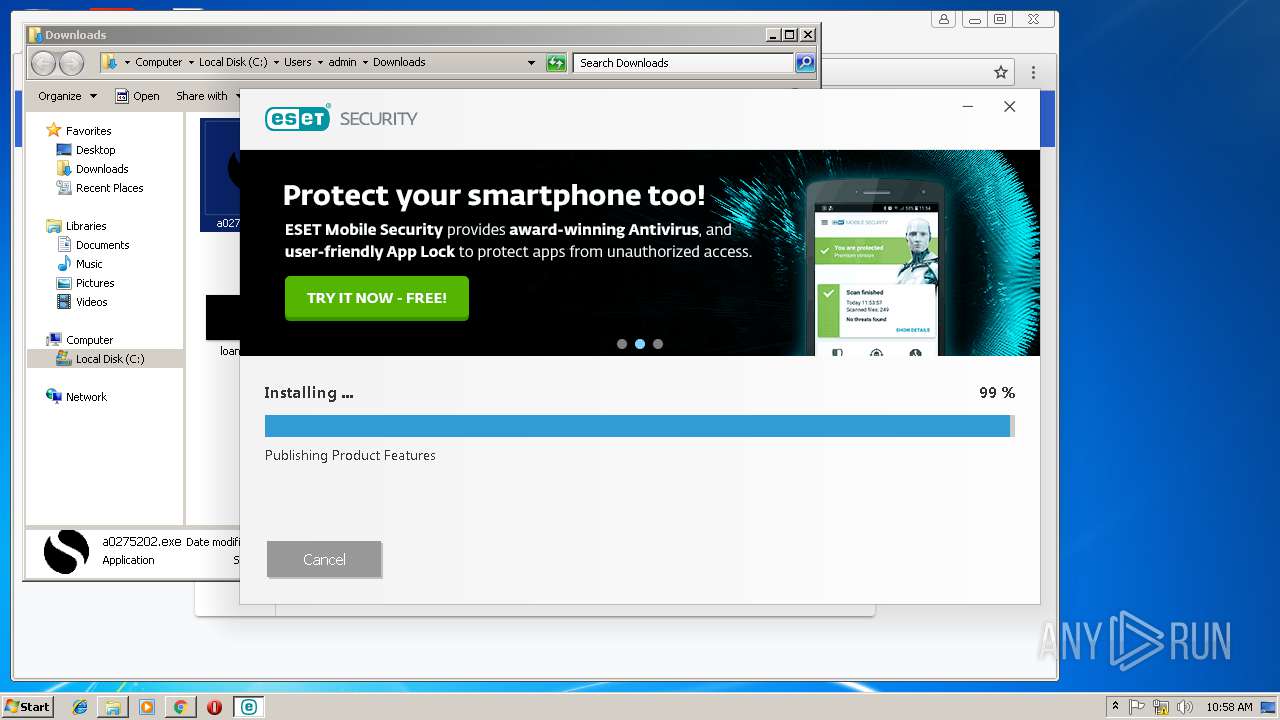
Application was dropped or rewritten from another process
- BootHelper.exe (PID: 3404)
- eav_nt32_enu.exe (PID: 2224)
- eav_nt32_enu.exe (PID: 3560)
- InstHelper.exe (PID: 3088)
- ekrn.exe (PID: 1008)
- egui.exe (PID: 2208)
- eeclnt.exe (PID: 2528)
- CertImporter-1504.exe (PID: 3280)
- CertImporter-1504.exe (PID: 2592)
Loads dropped or rewritten executable
- eav_nt32_enu.exe (PID: 2224)
- egui.exe (PID: 2208)
- InstHelper.exe (PID: 3088)
- explorer.exe (PID: 2028)
- svchost.exe (PID: 844)
- iexplore.exe (PID: 2820)
- ekrn.exe (PID: 1008)
Changes settings of System certificates
- ekrn.exe (PID: 1008)
- svchost.exe (PID: 844)
Loads the Task Scheduler COM API
- ekrn.exe (PID: 1008)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- MsiExec.exe (PID: 2416)
Cleans NTFS data-stream (Zone Identifier)
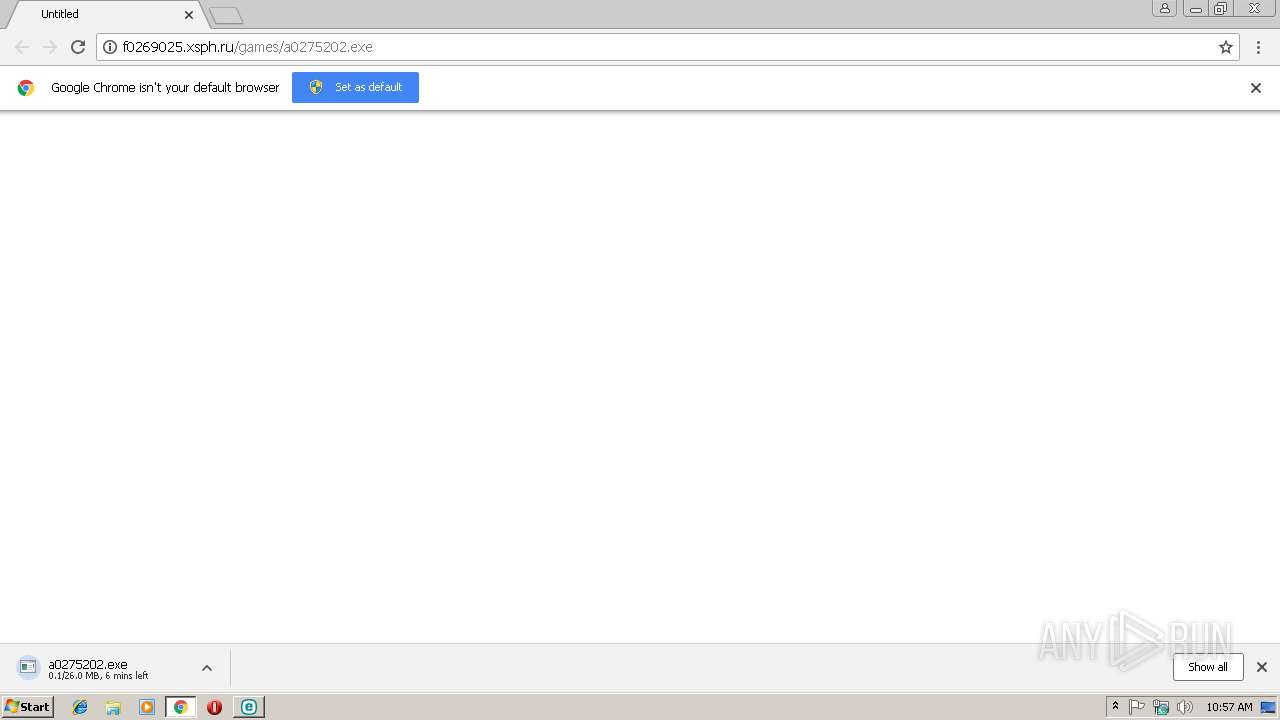
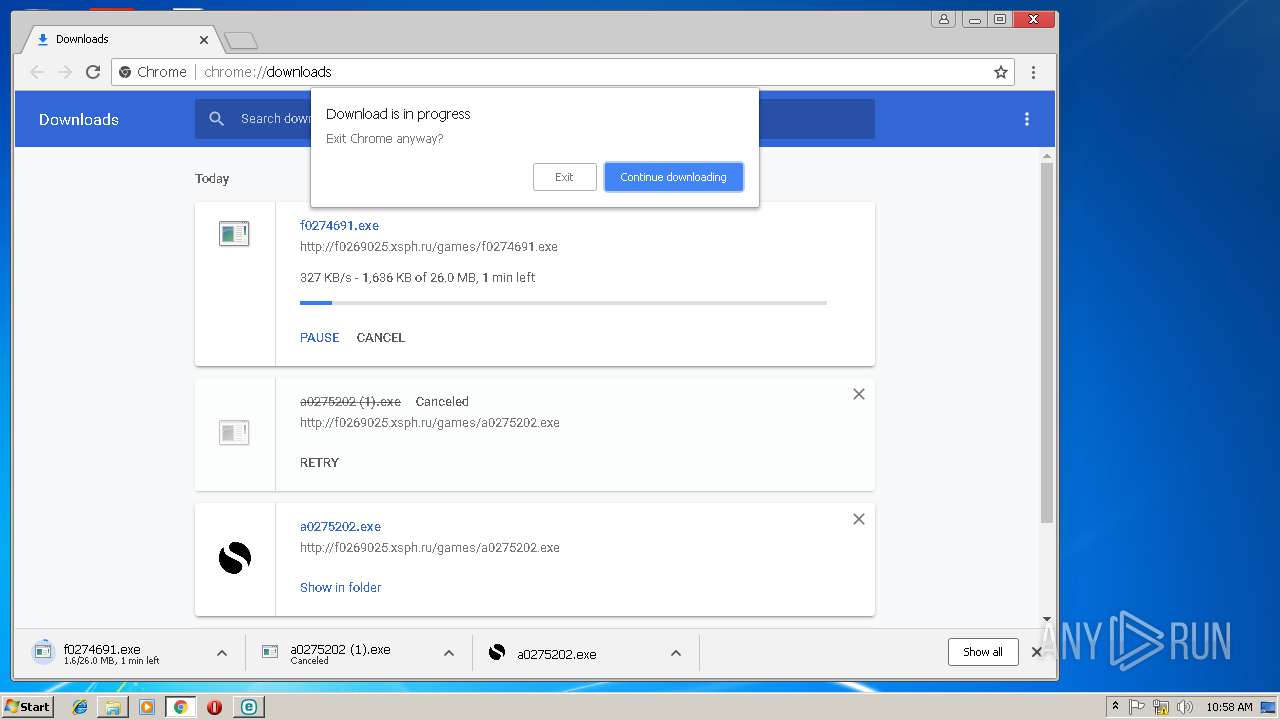
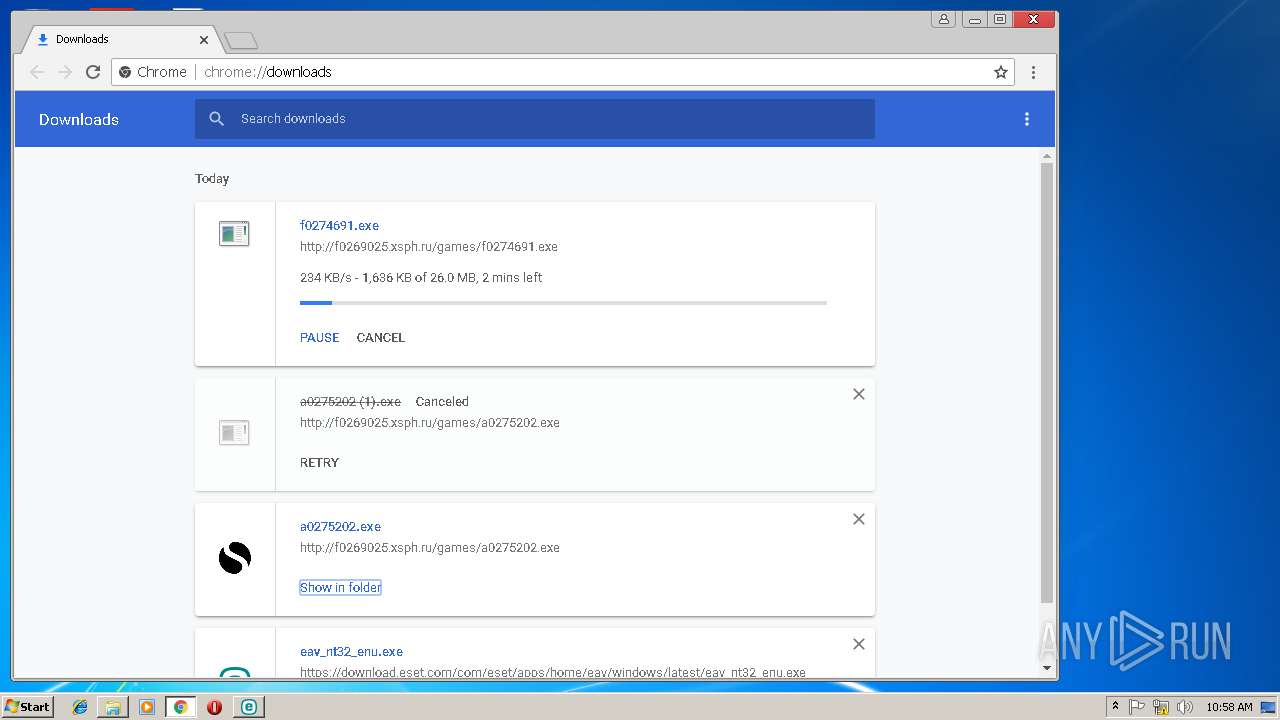
- chrome.exe (PID: 2848)
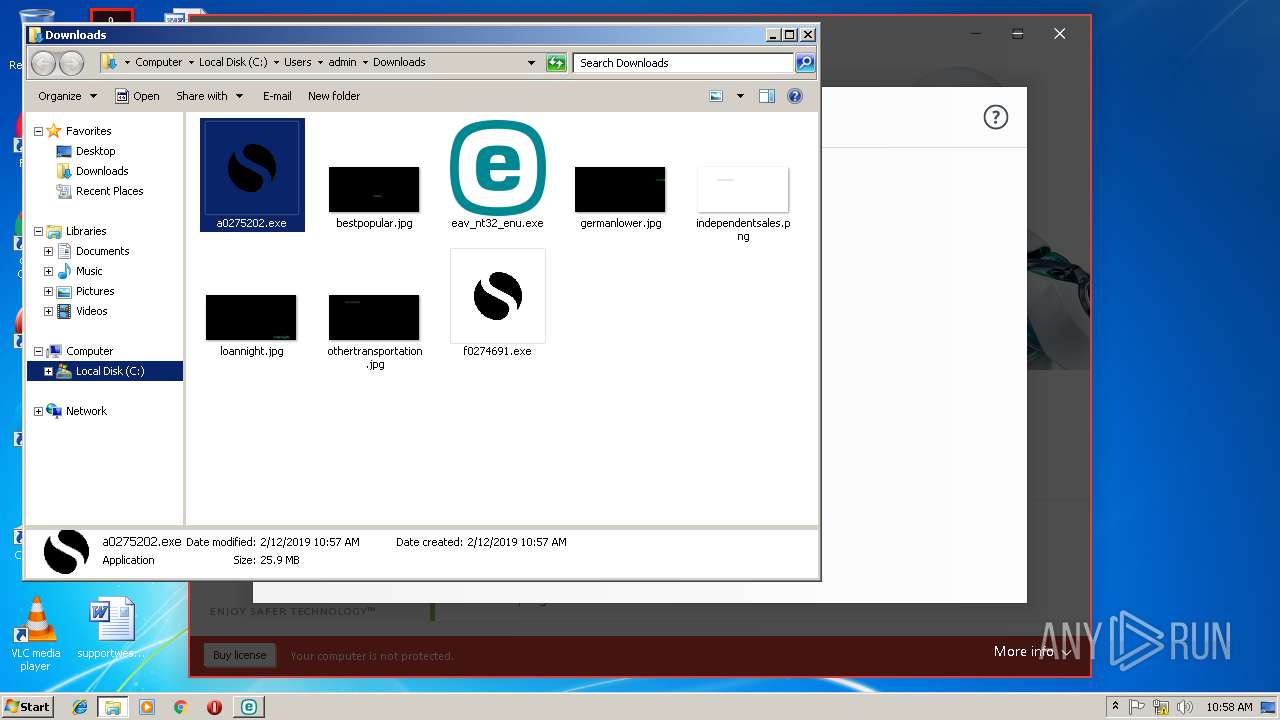
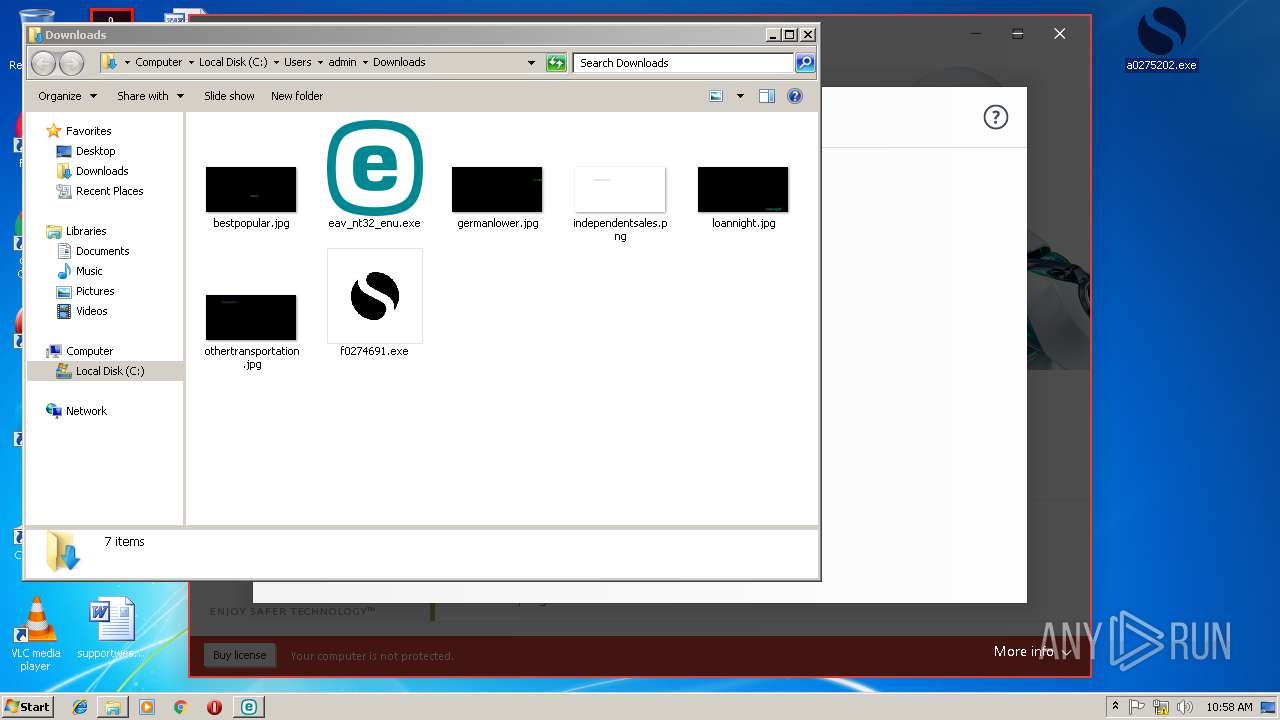
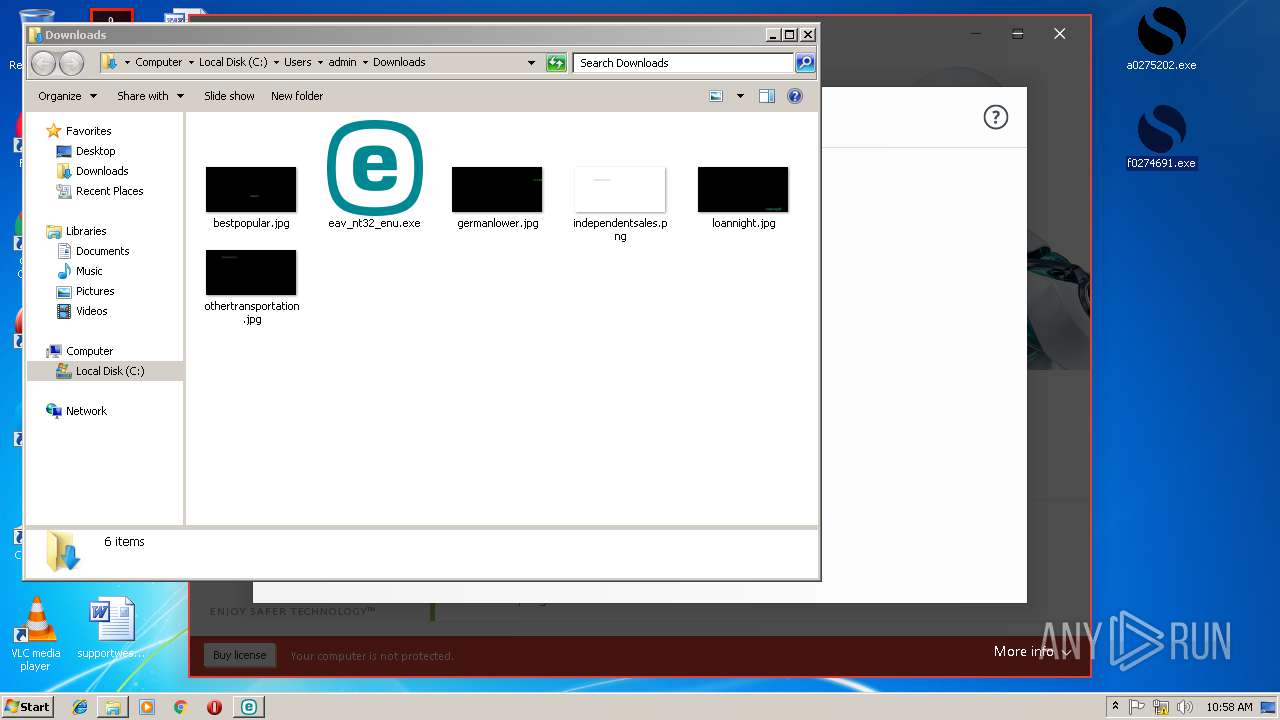
Executable content was dropped or overwritten
- chrome.exe (PID: 2848)
- eav_nt32_enu.exe (PID: 3560)
- MsiExec.exe (PID: 3312)
- eav_nt32_enu.exe (PID: 2224)
- msiexec.exe (PID: 2344)
- MsiExec.exe (PID: 2416)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 608)
- ekrn.exe (PID: 1008)
Creates COM task schedule object
- MsiExec.exe (PID: 3312)
- MsiExec.exe (PID: 2416)
Changes the autorun value in the registry
- msiexec.exe (PID: 2344)
Creates files in the driver directory
- ekrn.exe (PID: 1008)
- DrvInst.exe (PID: 2916)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 608)
Removes files from Windows directory
- DrvInst.exe (PID: 2916)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 608)
- ekrn.exe (PID: 1008)
- svchost.exe (PID: 844)
Creates files in the Windows directory
- DrvInst.exe (PID: 2916)
- DrvInst.exe (PID: 3972)
- DrvInst.exe (PID: 608)
- ekrn.exe (PID: 1008)
- svchost.exe (PID: 844)
Creates or modifies windows services
- ekrn.exe (PID: 1008)
Creates files in the program directory
- ekrn.exe (PID: 1008)
Searches for installed software
- CertImporter-1504.exe (PID: 3280)
- CertImporter-1504.exe (PID: 2592)
- ekrn.exe (PID: 1008)
Creates files in the user directory
- CertImporter-1504.exe (PID: 3280)
Loads DLL from Mozilla Firefox
- CertImporter-1504.exe (PID: 3280)
Writes to a desktop.ini file (may be used to cloak folders)
- ekrn.exe (PID: 1008)
Low-level read access rights to disk partition
- ekrn.exe (PID: 1008)
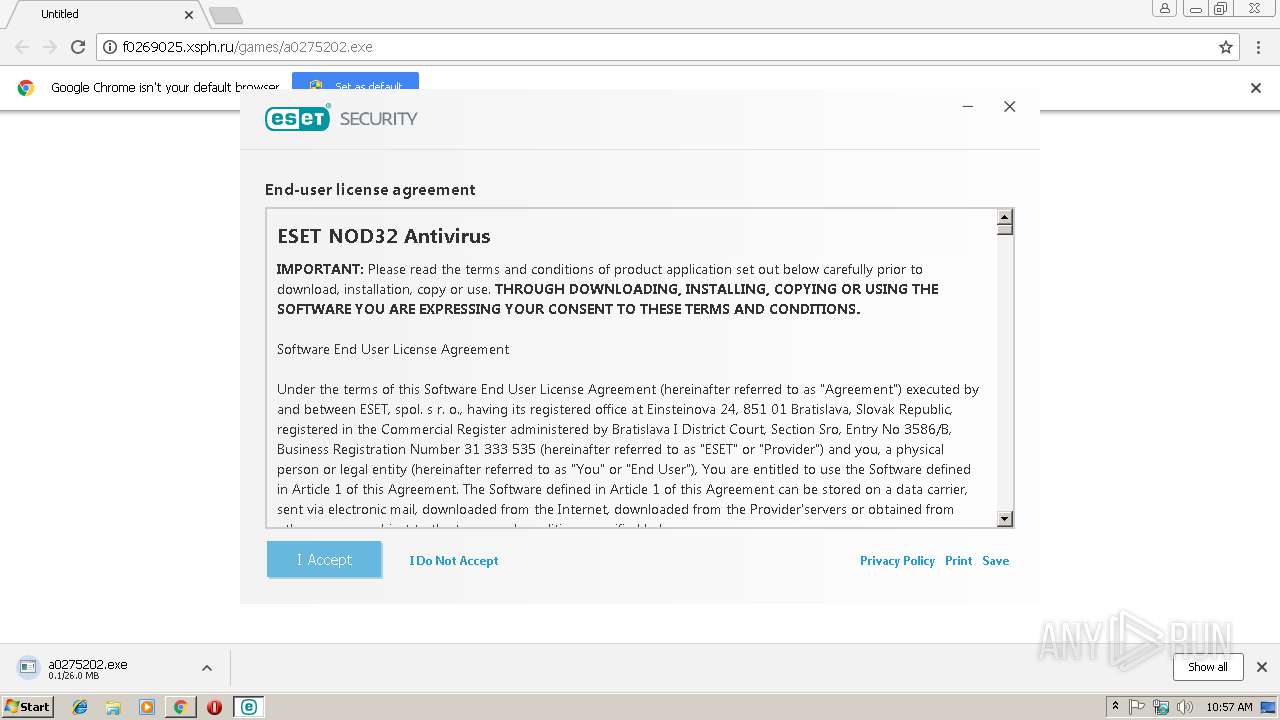
Adds / modifies Windows certificates
- ekrn.exe (PID: 1008)
Starts Internet Explorer
- explorer.exe (PID: 2028)
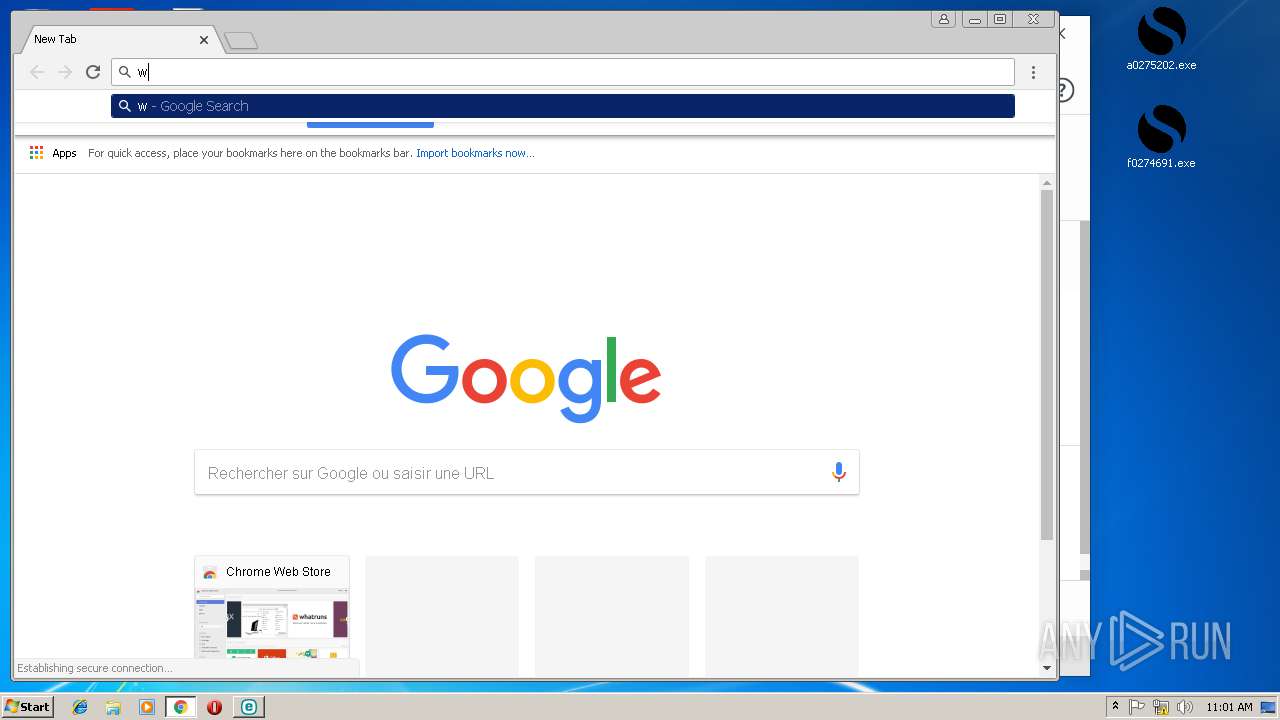
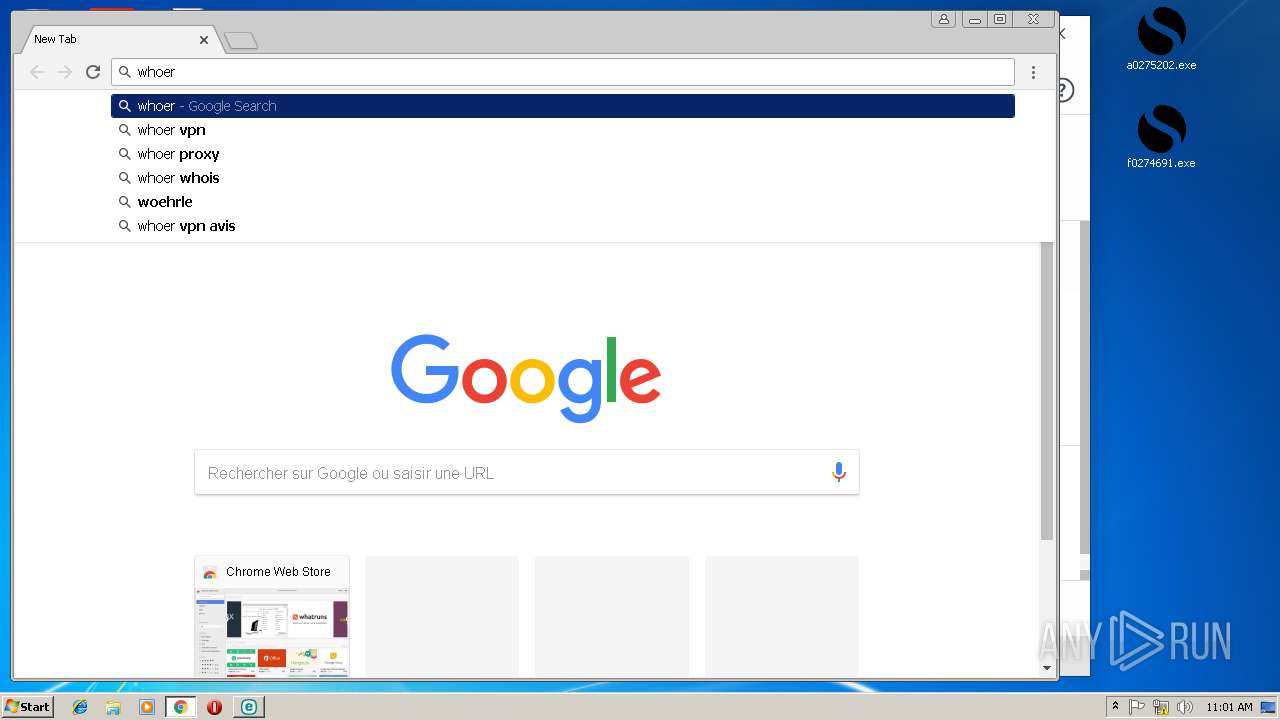
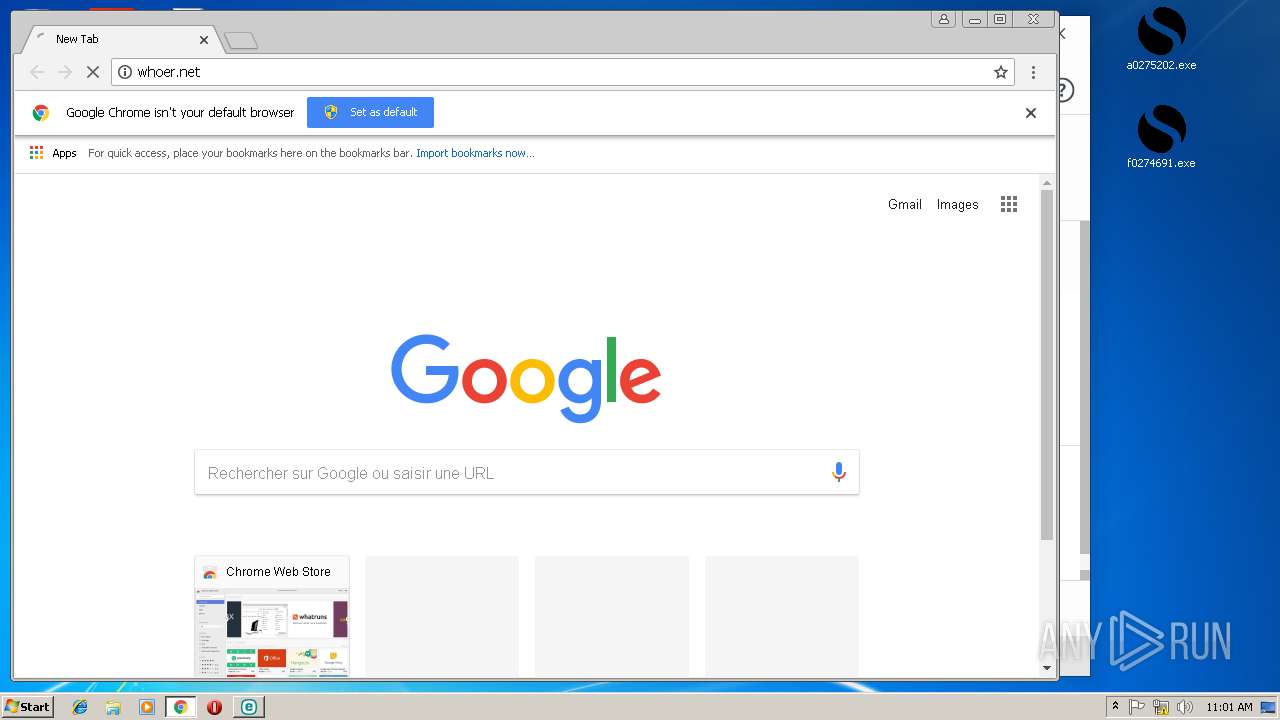
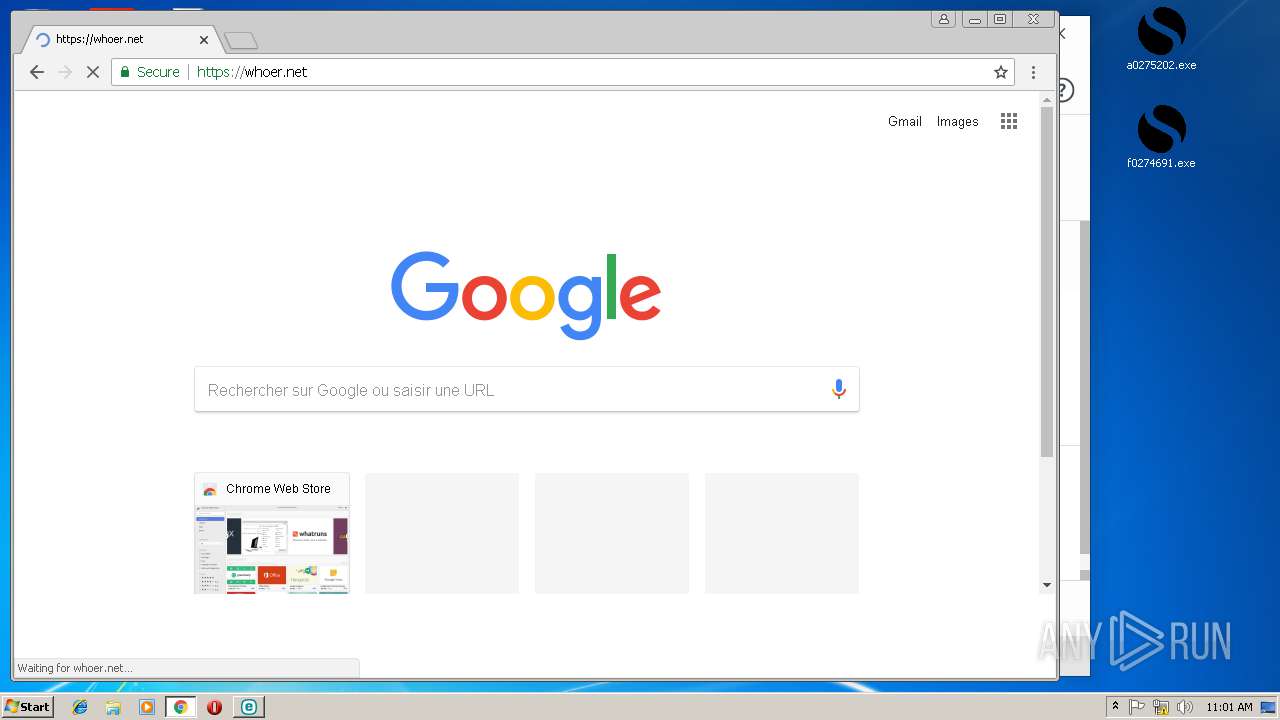
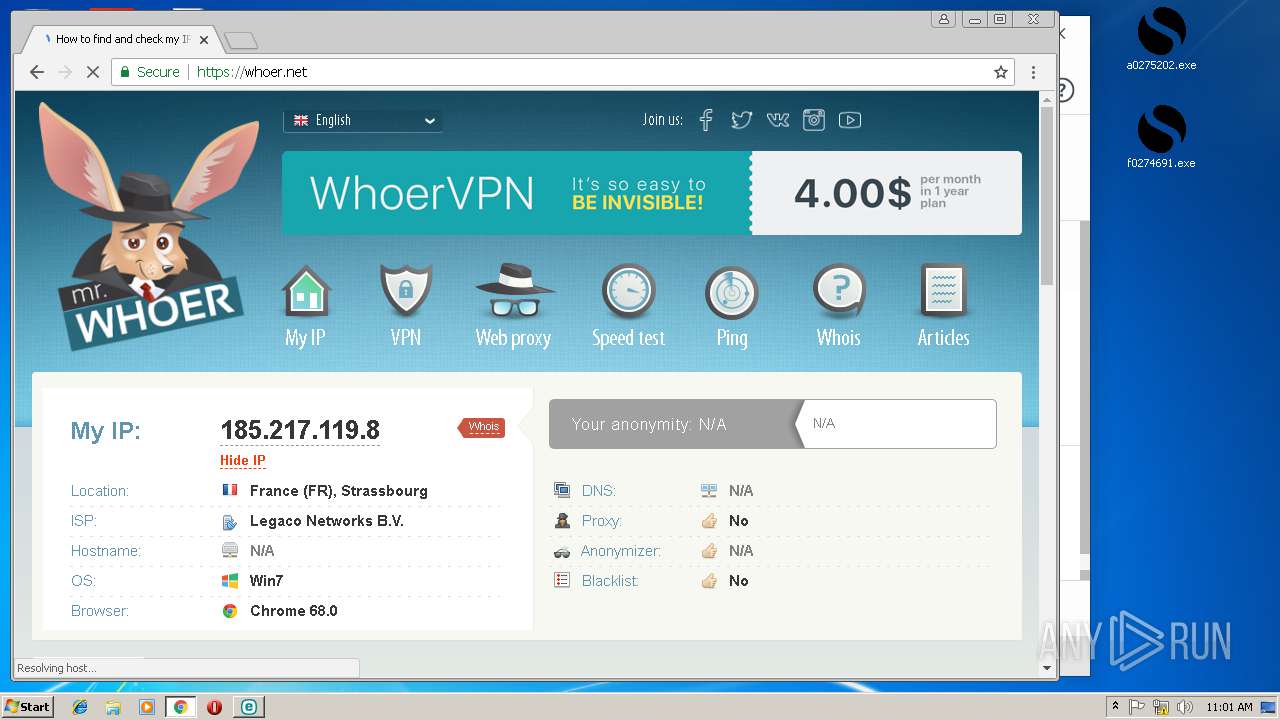
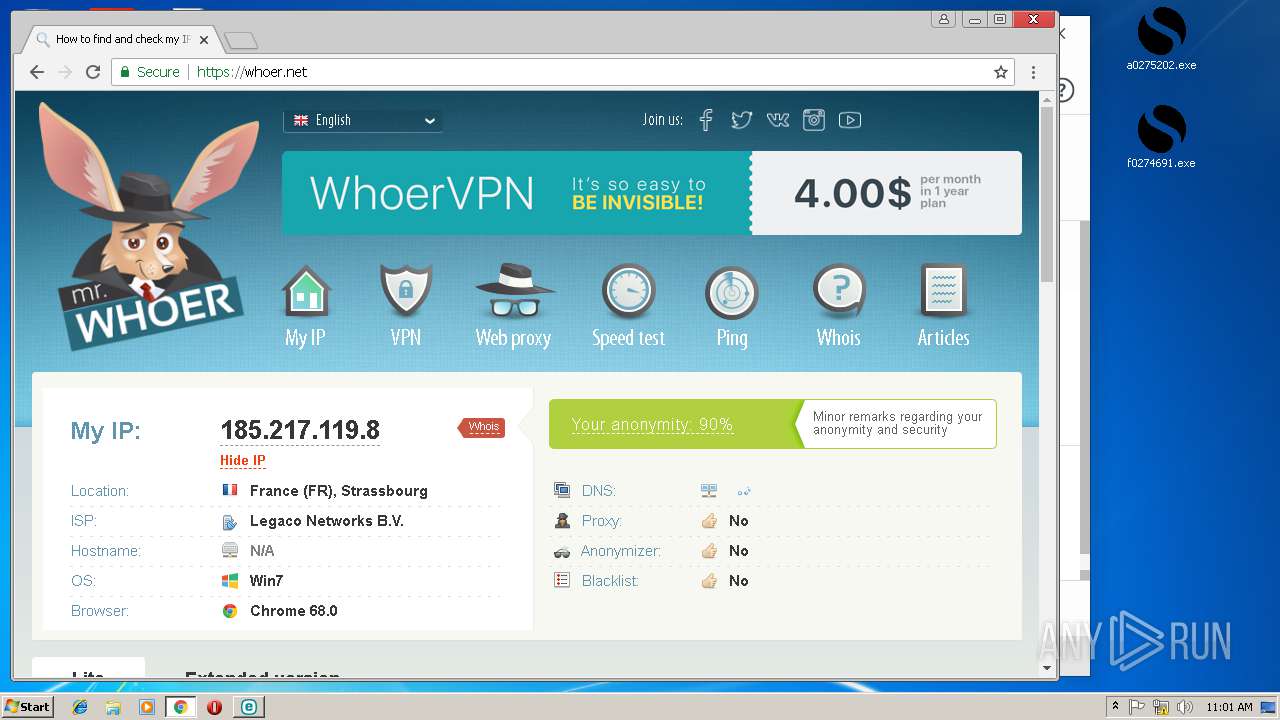
Checks for external IP
- chrome.exe (PID: 3328)
Reads the cookies of Google Chrome
- ekrn.exe (PID: 1008)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2848)
- iexplore.exe (PID: 2820)
Reads settings of System Certificates
- chrome.exe (PID: 2848)
- eav_nt32_enu.exe (PID: 2224)
- svchost.exe (PID: 844)
- ekrn.exe (PID: 1008)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3312)
- MsiExec.exe (PID: 1496)
- MsiExec.exe (PID: 2416)
Application launched itself
- chrome.exe (PID: 2848)
- msiexec.exe (PID: 2344)
- iexplore.exe (PID: 3036)
- chrome.exe (PID: 3328)
Creates files in the user directory
- chrome.exe (PID: 2848)
Reads Microsoft Office registry keys
- ekrn.exe (PID: 1008)
Creates a software uninstall entry
- msiexec.exe (PID: 2344)
- MsiExec.exe (PID: 2416)
Creates files in the program directory
- msiexec.exe (PID: 2344)
- MsiExec.exe (PID: 3312)
- MsiExec.exe (PID: 2416)
Changes internet zones settings
- iexplore.exe (PID: 3036)
Reads internet explorer settings
- iexplore.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
45
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,17432334430952045474,4071488276537974279,131072 --enable-features=PasswordImport --service-pipe-token=A9551D0438340B8BE7814898A785D5FF --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A9551D0438340B8BE7814898A785D5FF --renderer-client-id=5 --mojo-platform-channel-handle=1868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 608 | DrvInst.exe "4" "8" "C:\Windows\TEMP\{649d3e88-9170-0fa3-03e6-ec0d39c12743}\eamonm.inf" "0" "6d14d0413" "000005C8" "WinSta0\Default" "000003F0" "208" "C:\Program Files\ESET\ESET Security\Drivers\eamonm" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,17432334430952045474,4071488276537974279,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=73B5ACF8EB035832A365A5B7CB2A6A53 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=73B5ACF8EB035832A365A5B7CB2A6A53 --renderer-client-id=7 --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Program Files\ESET\ESET Security\ekrn.exe" | C:\Program Files\ESET\ESET Security\ekrn.exe | services.exe | ||||||||||||
User: SYSTEM Company: ESET Integrity Level: SYSTEM Description: ESET Service Exit code: 0 Version: 10.6.209.0 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2184 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=856,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=E8E65589C0329EDF840B17443E132653 --mojo-platform-channel-handle=1144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1496 | C:\Windows\system32\MsiExec.exe -Embedding A10EC1DC475F89C01B52CFA734328586 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=876,17432334430952045474,4071488276537974279,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=BBE3CB933D3DC45E21A4BF25F7F13A9B --mojo-platform-channel-handle=896 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2028 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12 033
Read events
10 401
Write events
1 593
Delete events
39
Modification events
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2848-13194442597980250 |
Value: 259 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
256
Suspicious files
289
Text files
469
Unknown types
78
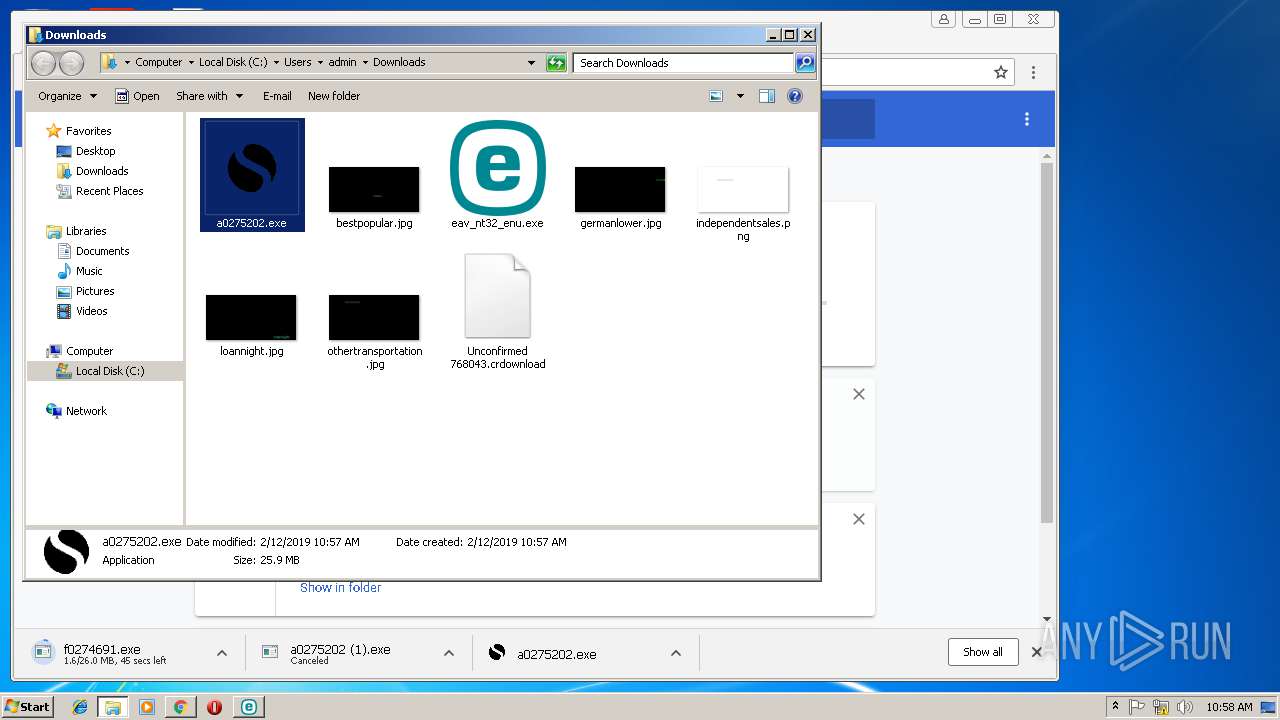
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\303e44fd-469f-44df-8e76-0a6566c14902.tmp | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\06045be2-a478-4a00-93ee-bdb65b308549.tmp | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6e4b50db-08f7-45fa-9287-1d3cb69bc863.tmp | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246ce3.TMP | text | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246cb5.TMP | text | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF246f93.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
25
DNS requests
15
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2224 | eav_nt32_enu.exe | GET | 200 | 91.228.167.110:80 | http://download.eset.com:80/com/eset/tools/installers/av_detector/v1/1.86.0.0/detectavdb_windefend.dat | SK | binary | 181 Kb | suspicious |
2224 | eav_nt32_enu.exe | GET | 200 | 91.228.165.81:80 | http://iploc.eset.com:80/ip_locate_iso2 | SK | xml | 246 b | whitelisted |
2224 | eav_nt32_enu.exe | GET | 302 | 91.228.167.134:80 | http://go.eset.eu:80/banner-v2?lng=1033&product=eav&version=12&type=li | SK | html | 268 b | suspicious |
2224 | eav_nt32_enu.exe | GET | 200 | 91.228.167.30:80 | http://banner.eset.com:80/banner-v2/?product=eav&version=12&type=li&lng=1033 | SK | text | 497 b | whitelisted |
2848 | chrome.exe | GET | 200 | 67.27.235.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2224 | eav_nt32_enu.exe | GET | 200 | 91.228.166.23:80 | http://repositorynocdn.eset.com:80/v1/com/eset/apps/home/security/windows/metadata3.default | SK | binary | 177 Kb | suspicious |
2224 | eav_nt32_enu.exe | GET | 302 | 91.228.167.134:80 | http://go.eset.eu:80/detectav?product=ehs | SK | html | 238 b | suspicious |
2224 | eav_nt32_enu.exe | GET | 200 | 91.228.167.30:80 | http://banner.eset.com:80/banner-v2/data/images/li/eav/v12/1033/Banner.png | SK | image | 142 Kb | whitelisted |
2224 | eav_nt32_enu.exe | GET | 302 | 91.228.166.23:80 | http://repository.eset.com:80/v1/com/eset/apps/home/security/windows/metadata3 | SK | text | 88 b | suspicious |
2224 | eav_nt32_enu.exe | GET | 200 | 91.228.167.110:80 | http://download.eset.com:80/special/detectav/detectav.xml | SK | xml | 503 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 91.228.167.110:443 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
2848 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 67.27.235.126:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2224 | eav_nt32_enu.exe | 91.228.166.23:80 | repository.eset.com | ESET, spol. s r.o. | SK | suspicious |
2848 | chrome.exe | 216.58.207.67:443 | www.google.fr | Google Inc. | US | whitelisted |
2224 | eav_nt32_enu.exe | 91.228.165.81:80 | iploc.eset.com | ESET, spol. s r.o. | SK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
download.eset.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
repository.eset.com |
| malicious |
repositorynocdn.eset.com |
| suspicious |
www.google.fr |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2848 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2848 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1008 | ekrn.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3328 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup whoer.net |