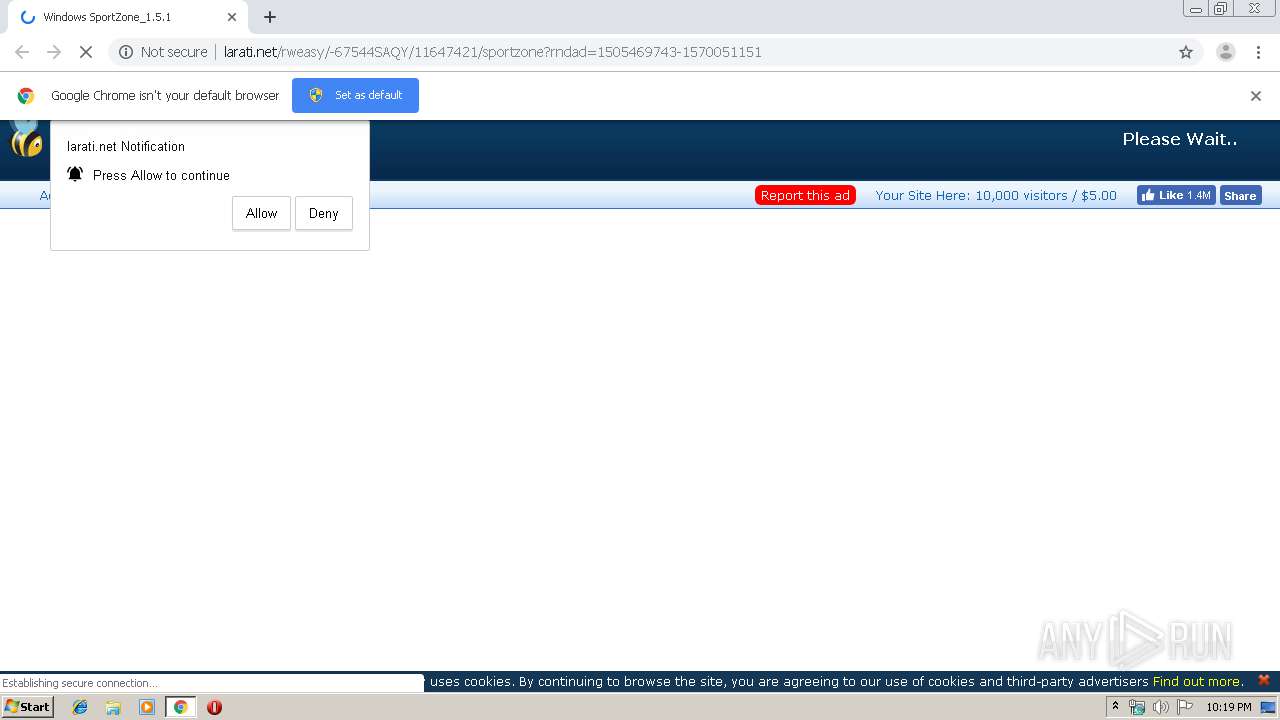
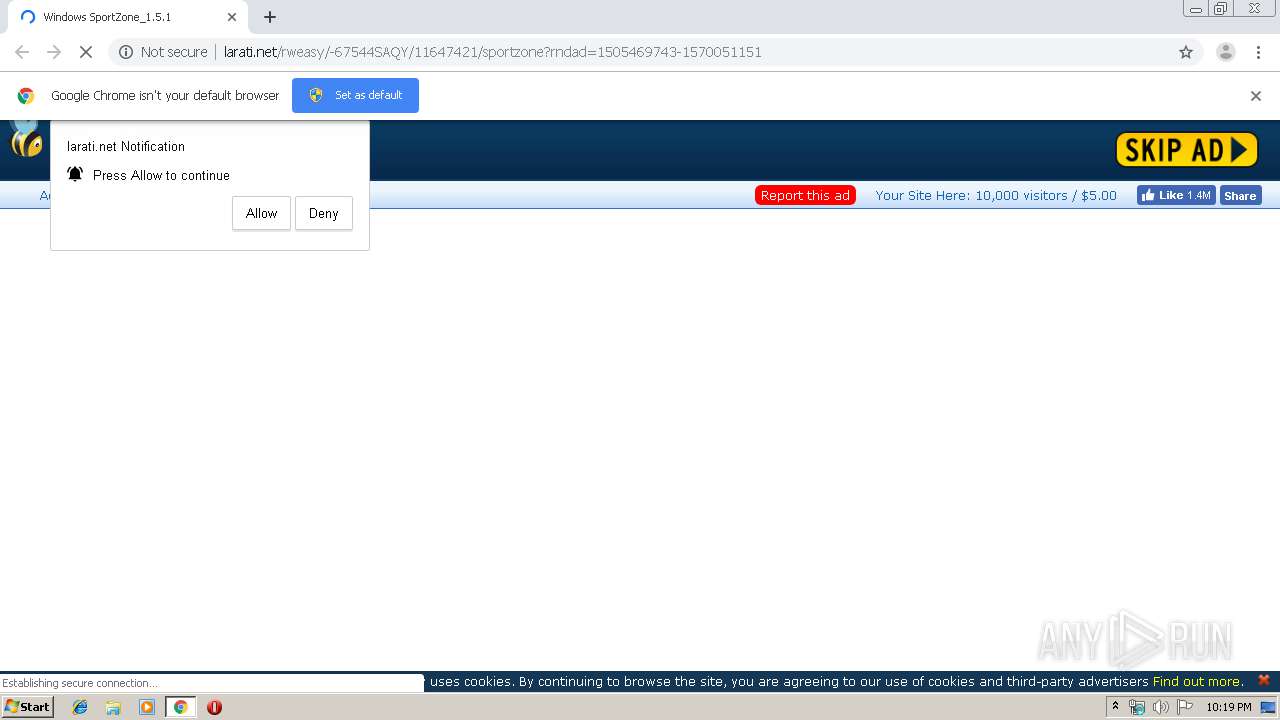
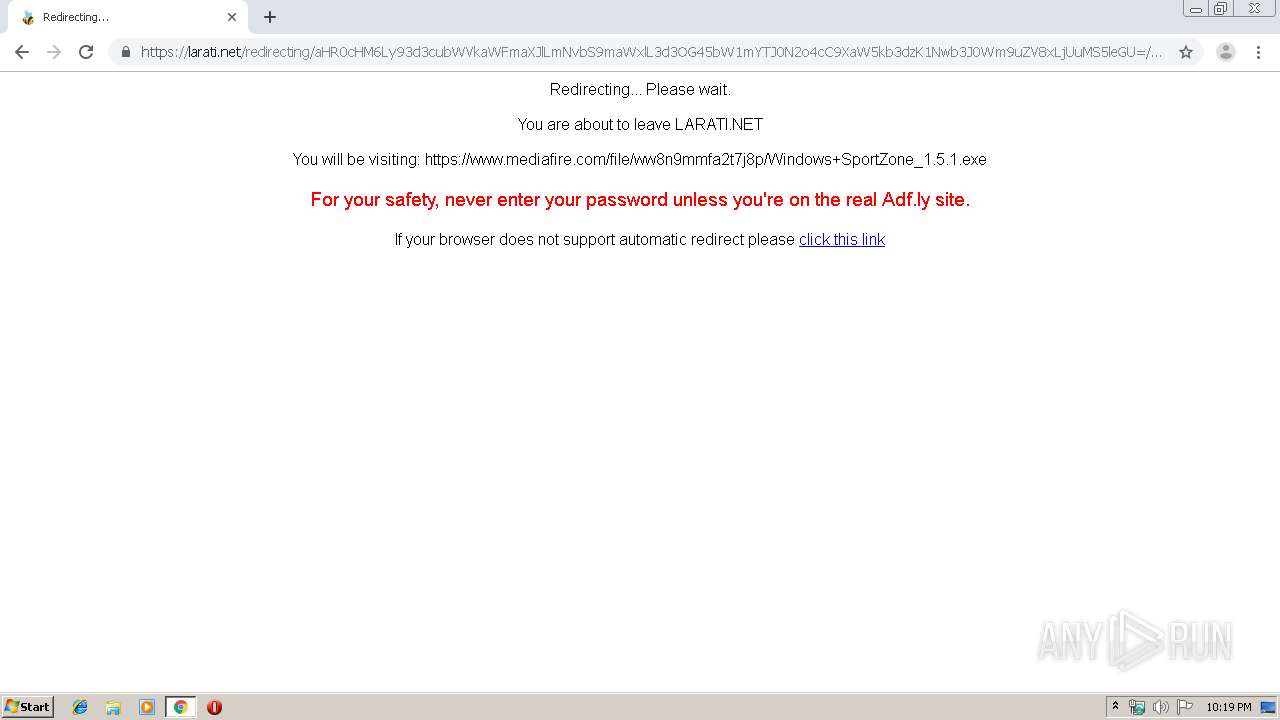
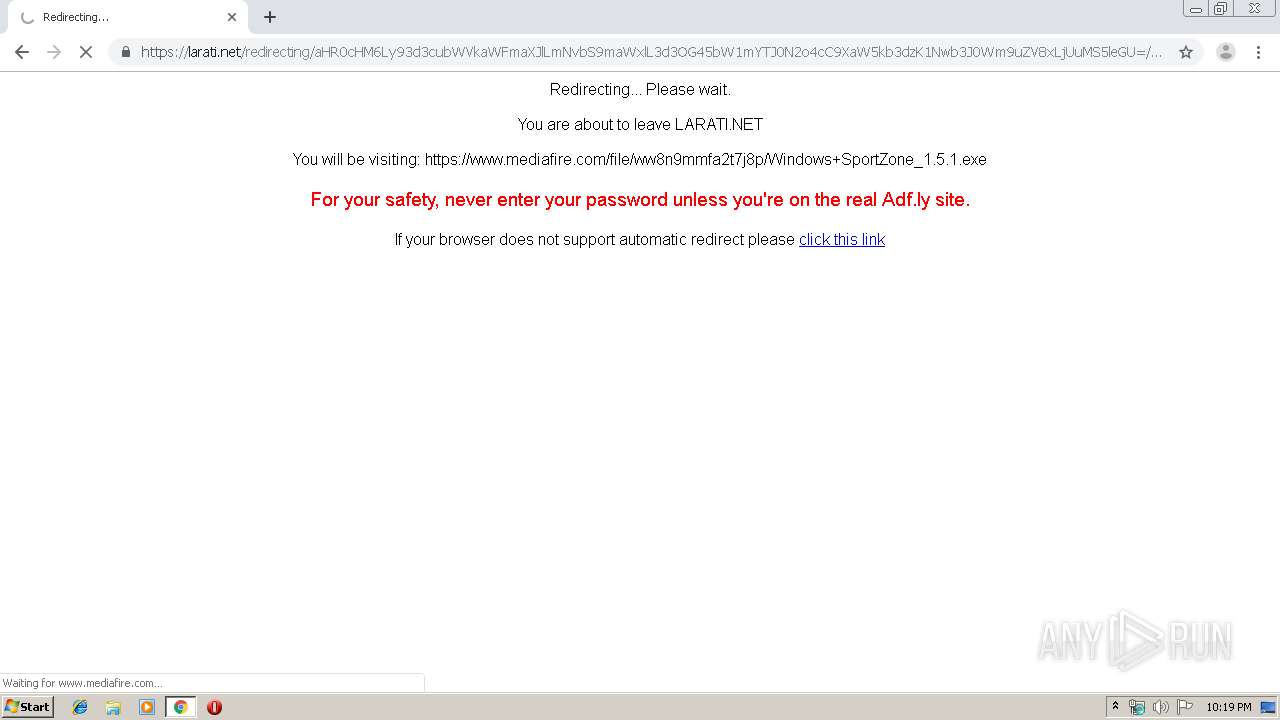
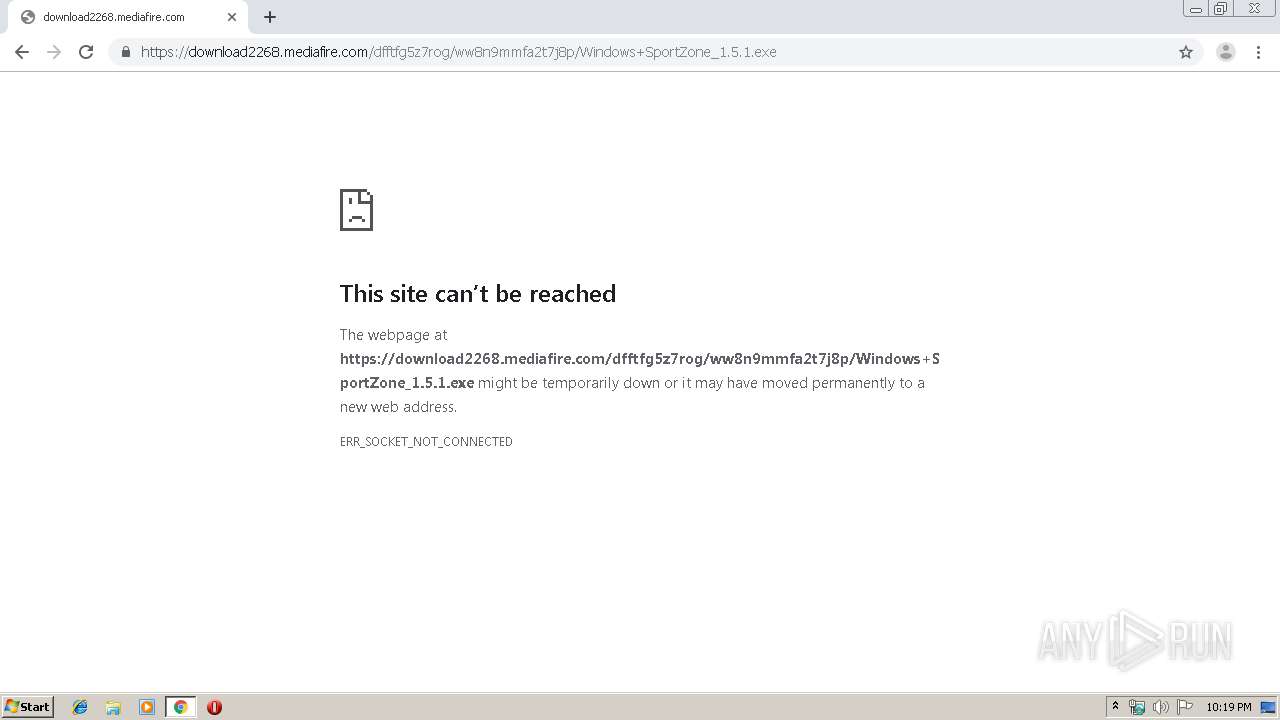
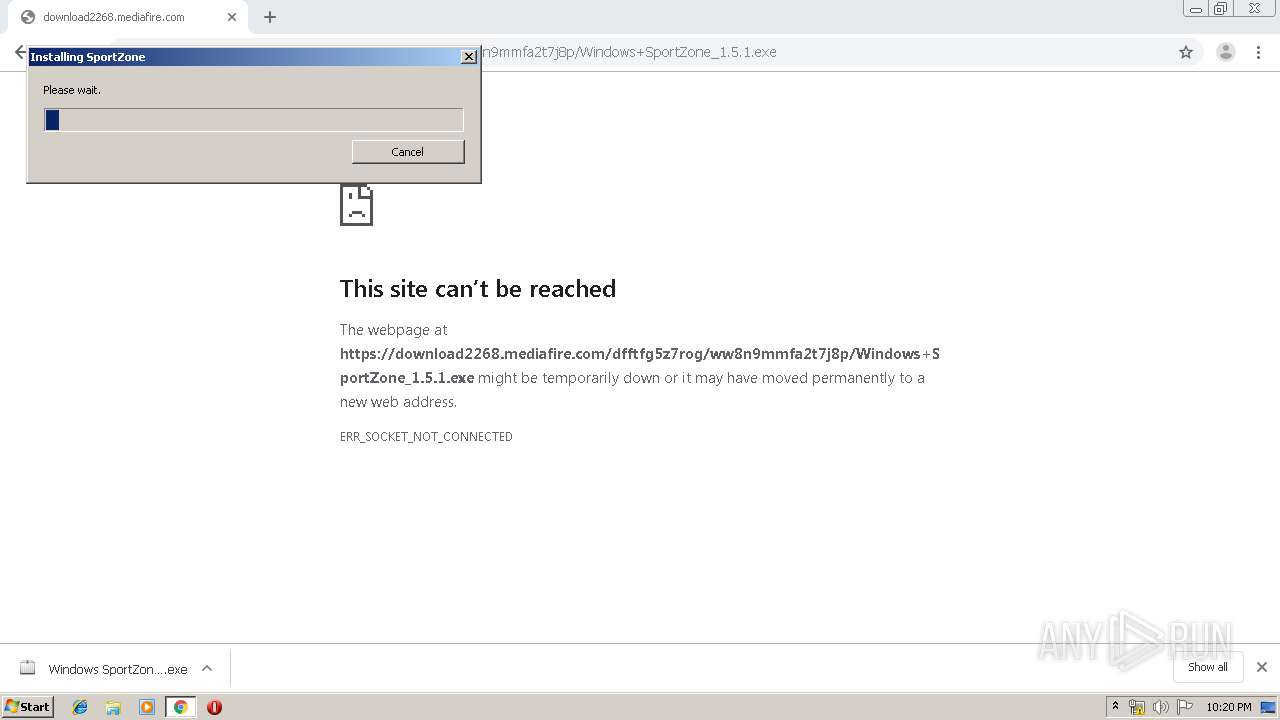
| URL: | http://vaugette.com/11647421/sportzone |
| Full analysis: | https://app.any.run/tasks/21a96fc9-db1b-4c84-b000-6583751c5c96 |
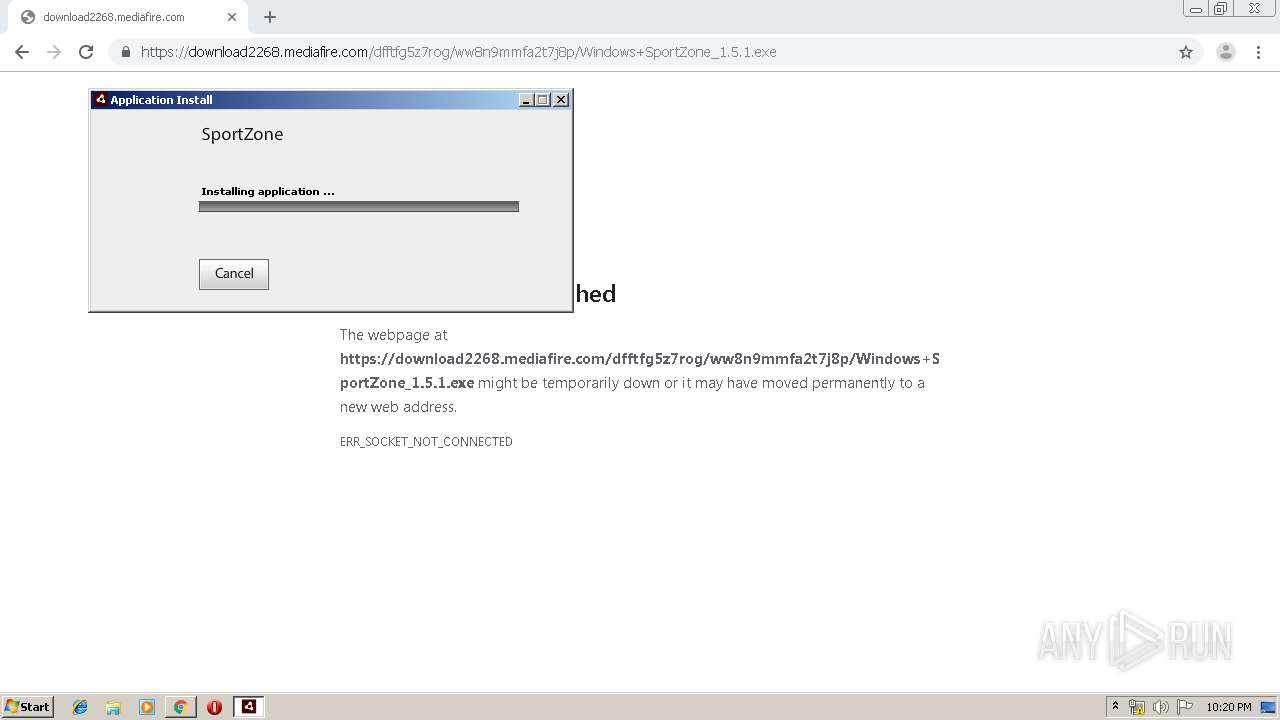
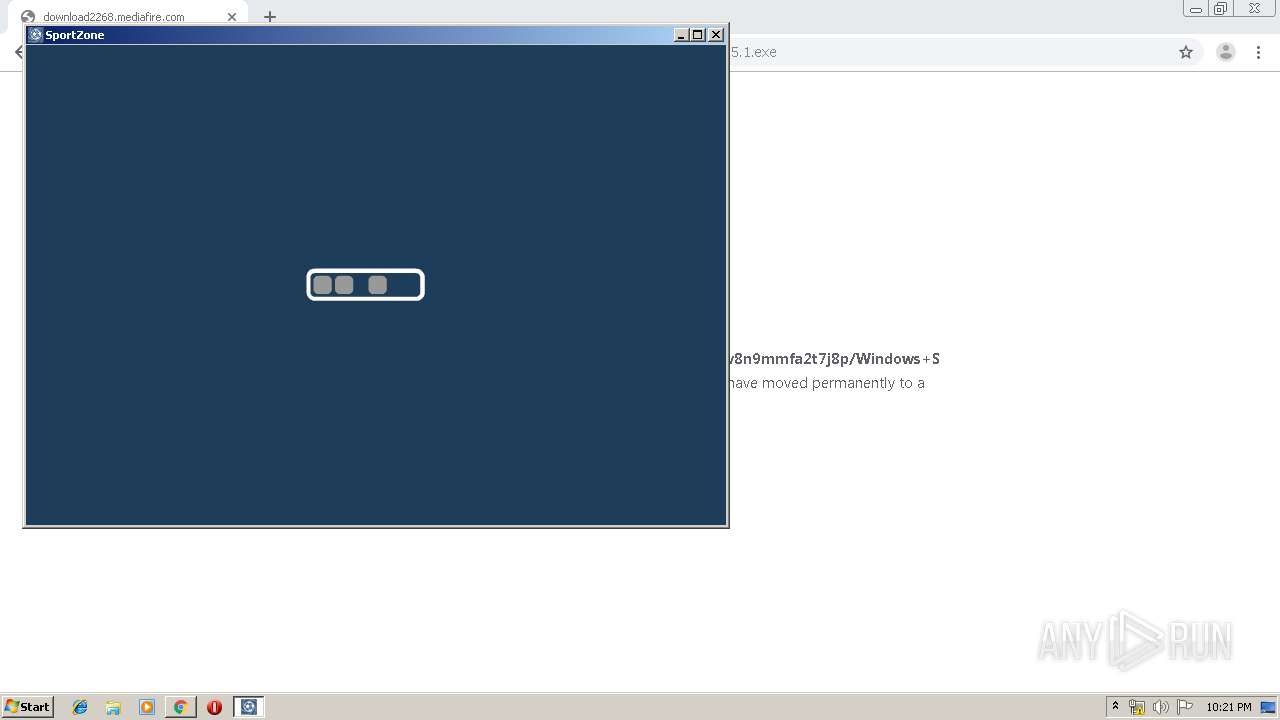
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2019, 21:18:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E23975015A6C0C4A68BF4C9E29D0079E |
| SHA1: | BBCC14A0E789EEC3819849C7F3EA2739AE1DC750 |
| SHA256: | AFB7AAB1AFCEB2A0FF3AA1061894B713590F2DC8B6BDEDED6DC9D5C3A82BFB1B |
| SSDEEP: | 3:N1KIcAwjTR0eR0:CIcdvKm0 |
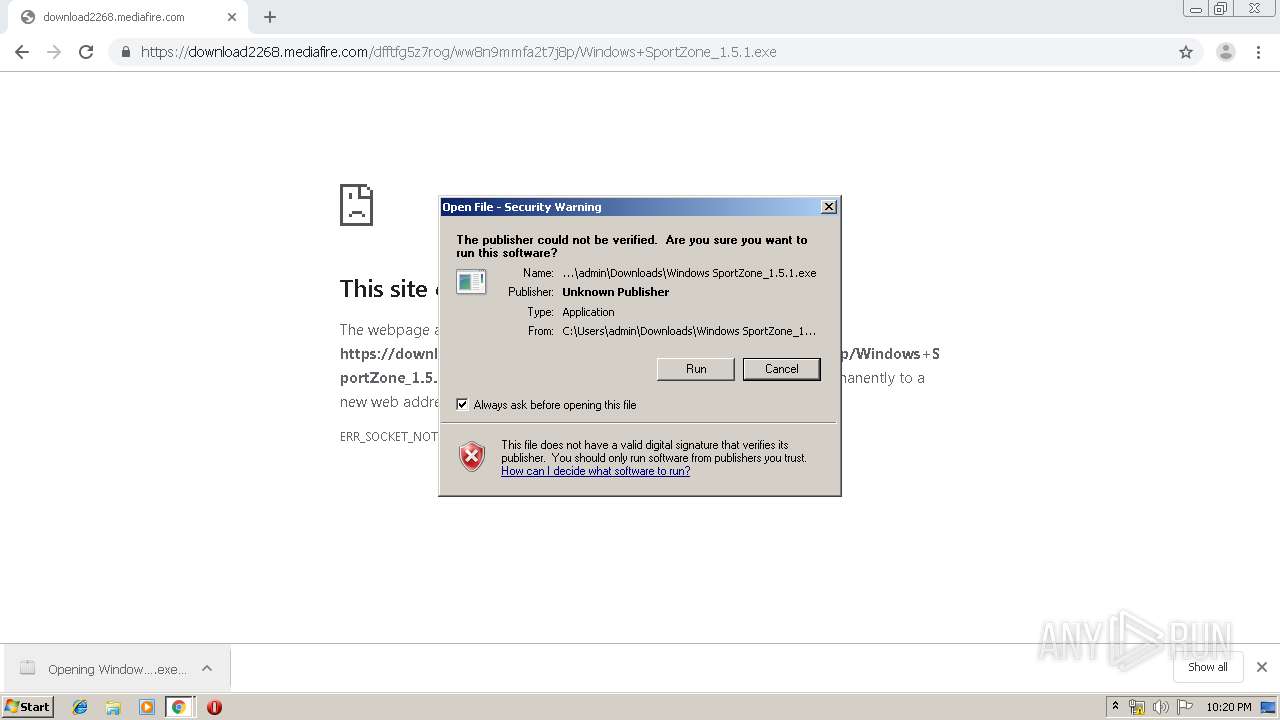
MALICIOUS
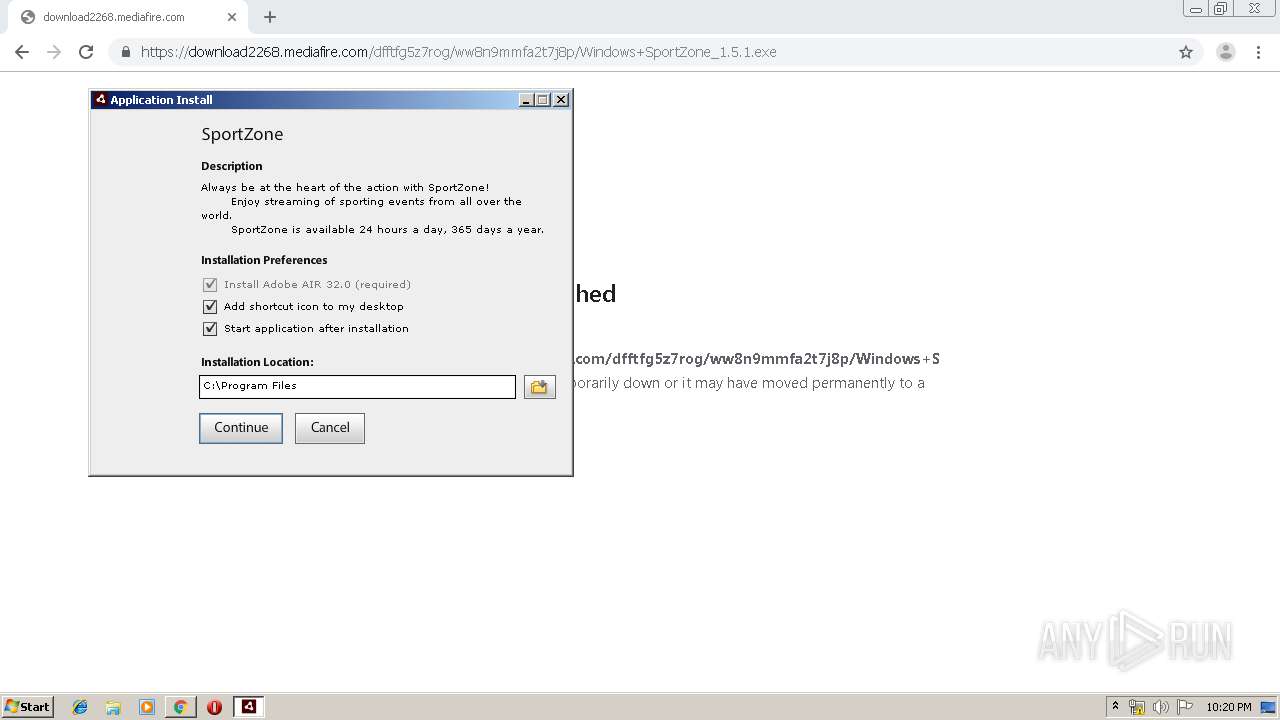
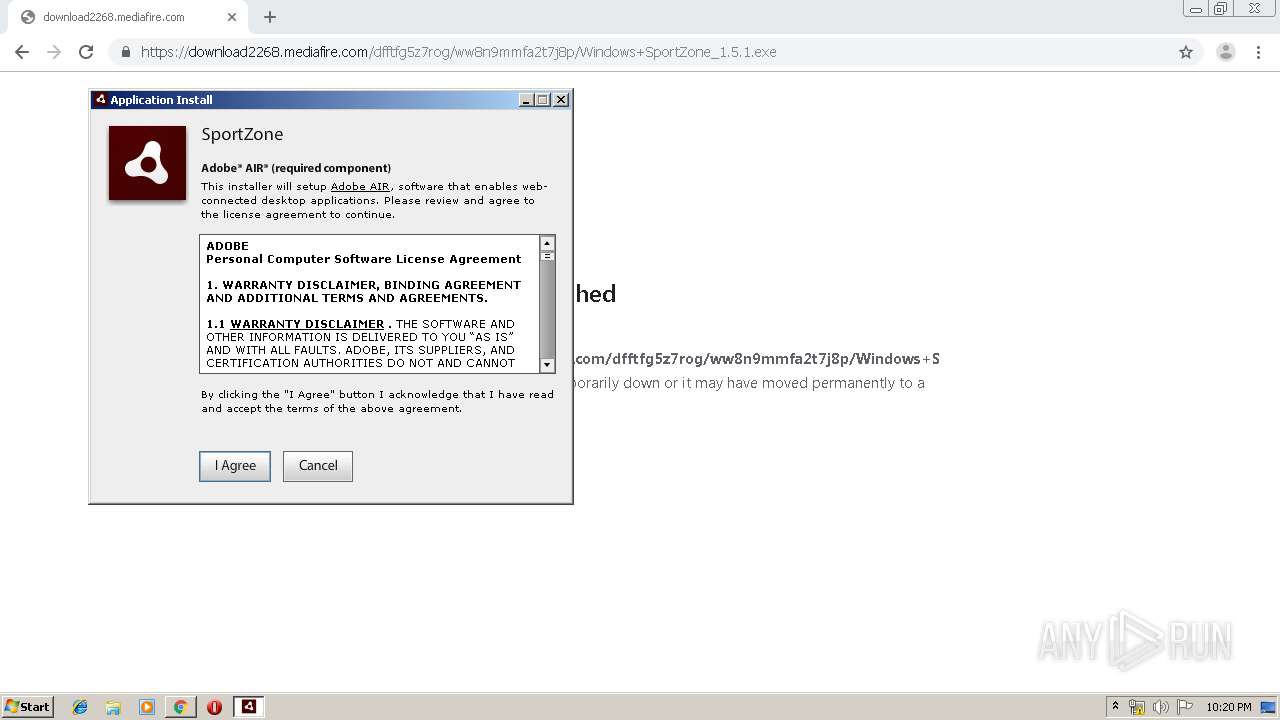
Loads dropped or rewritten executable
- Adobe AIR Installer.exe (PID: 2728)
- Adobe AIR Application Installer.exe (PID: 3476)
- Adobe AIR Application Installer.exe (PID: 2740)
- SportZone.exe (PID: 3820)
- Adobe AIR Updater.exe (PID: 3380)
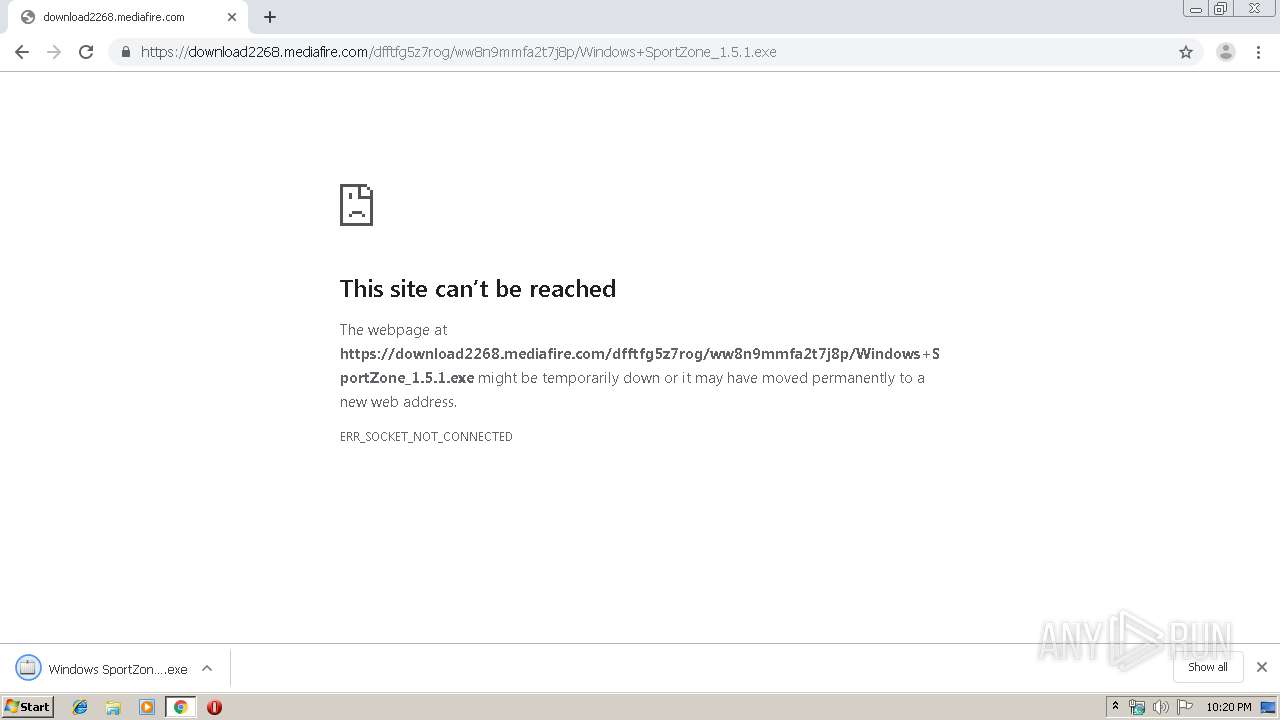
Application was dropped or rewritten from another process
- AIRRuntimeInstaller.exe (PID: 3300)
- Adobe AIR Installer.exe (PID: 2728)
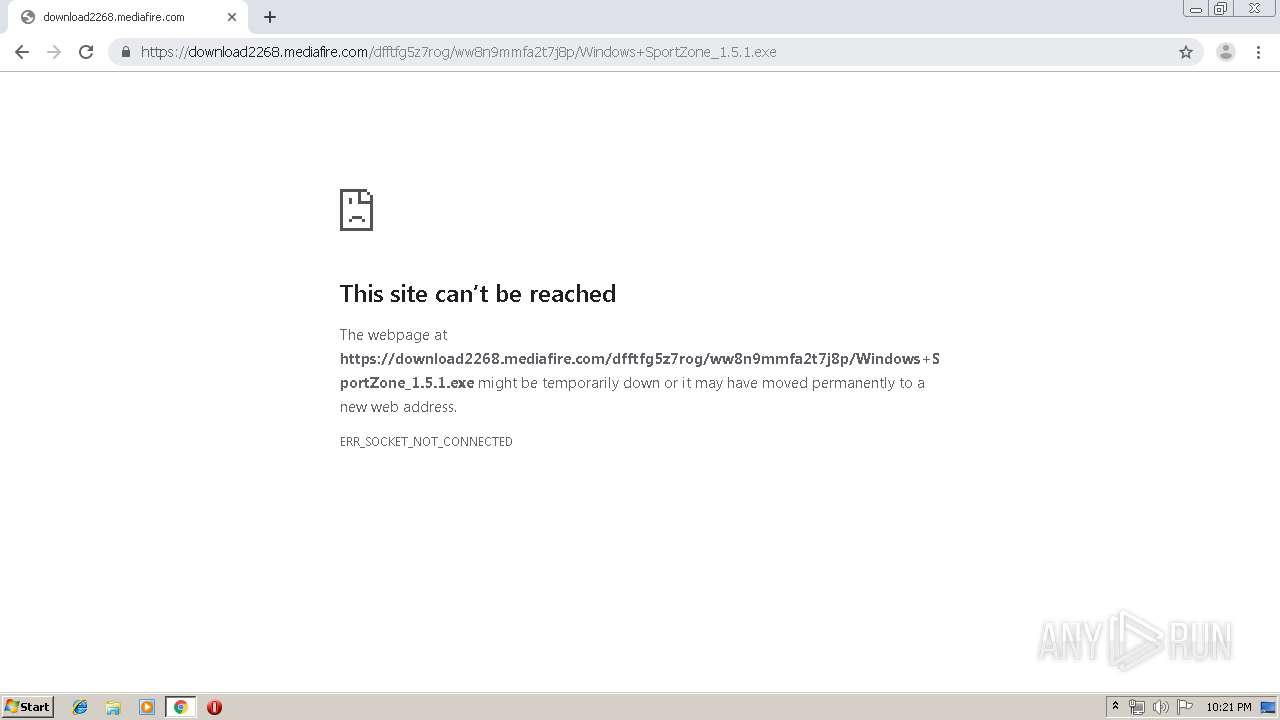
- Windows SportZone_1.5.1.exe (PID: 3524)
- Adobe AIR Application Installer.exe (PID: 2740)
- SportZone.exe (PID: 3820)
- Adobe AIR Updater.exe (PID: 3380)
- Install SportZone.exe (PID: 3764)
- Adobe AIR Application Installer.exe (PID: 3476)
Changes settings of System certificates
- msiexec.exe (PID: 2896)
SUSPICIOUS
Reads Internet Cache Settings
- Adobe AIR Application Installer.exe (PID: 3476)
- Adobe AIR Updater.exe (PID: 3380)
Creates files in the user directory
- Adobe AIR Application Installer.exe (PID: 3476)
- Adobe AIR Updater.exe (PID: 3380)
- SportZone.exe (PID: 3820)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2812)
Executable content was dropped or overwritten
- chrome.exe (PID: 2812)
- msiexec.exe (PID: 2896)
- Adobe AIR Application Installer.exe (PID: 3476)
- Adobe AIR Application Installer.exe (PID: 2740)
- Windows SportZone_1.5.1.exe (PID: 3524)
- Install SportZone.exe (PID: 3764)
- AIRRuntimeInstaller.exe (PID: 3300)
Application launched itself
- Adobe AIR Application Installer.exe (PID: 3476)
Creates files in the program directory
- Adobe AIR Application Installer.exe (PID: 2740)
Adds / modifies Windows certificates
- msiexec.exe (PID: 2896)
Modifies the open verb of a shell class
- msiexec.exe (PID: 2896)
INFO
Reads the hosts file
- chrome.exe (PID: 2812)
- chrome.exe (PID: 2224)
Changes settings of System certificates
- chrome.exe (PID: 2224)
Application launched itself
- chrome.exe (PID: 2812)
Reads Internet Cache Settings
- chrome.exe (PID: 2812)
Creates a software uninstall entry
- msiexec.exe (PID: 2896)
Creates files in the program directory
- msiexec.exe (PID: 2896)
Reads settings of System Certificates
- chrome.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
40
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9178907261940242811 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17277232797513219096 --mojo-platform-channel-handle=2560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2258893971147724726 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1872808934701247205 --mojo-platform-channel-handle=2544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6307959912984969592 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=19780528249234844 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8176835885950363007 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=773634791641093407 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11727797510518299738 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,6608501789949888850,18436390482390691623,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3218279102266042872 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 873
Read events
2 427
Write events
419
Delete events
27
Modification events
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2812-13214524749110375 |
Value: 259 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
35
Suspicious files
58
Text files
259
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b3dd5c7d-aeea-4260-bba6-1e800b1b99b0.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF114f55.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF114fa4.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF114ff2.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
79
DNS requests
44
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2224 | chrome.exe | GET | 204 | 52.85.182.236:80 | http://d1nmxiiewlx627.cloudfront.net/?ixmnd=709056 | US | — | — | whitelisted |
2224 | chrome.exe | GET | 204 | 3.225.70.173:80 | http://thetreuntalle.pro/ZU1WQkxKcjUxcTR/PisYHwcvGh0jfwAKBgcbLykNAQs5ByoSByxkOAwpa3R8UX5gdmoVJDJ/fUM+IiM4ED5rc2oMIzAtcUM7a3NiVnl4c3xLfHA2PAQqa3NqFTkiLnFUeGFyfFB8Z3d1VH9l | US | — | — | suspicious |
2224 | chrome.exe | GET | 204 | 3.225.70.173:80 | http://thetreuntalle.pro/SUtDc3pmdCAARy15GSYZERkEJgAtAgYYIB8SERcyHXoNHiscGQtVDiAvfkRKcHt2RVw5IidOSHBtMAcbPT4wTktvIi0VFXRtNU5LZ3ttQUxne2UHCigsfkJcOT83H0d4fnRDSnx6ckZDeHh1 | US | — | — | suspicious |
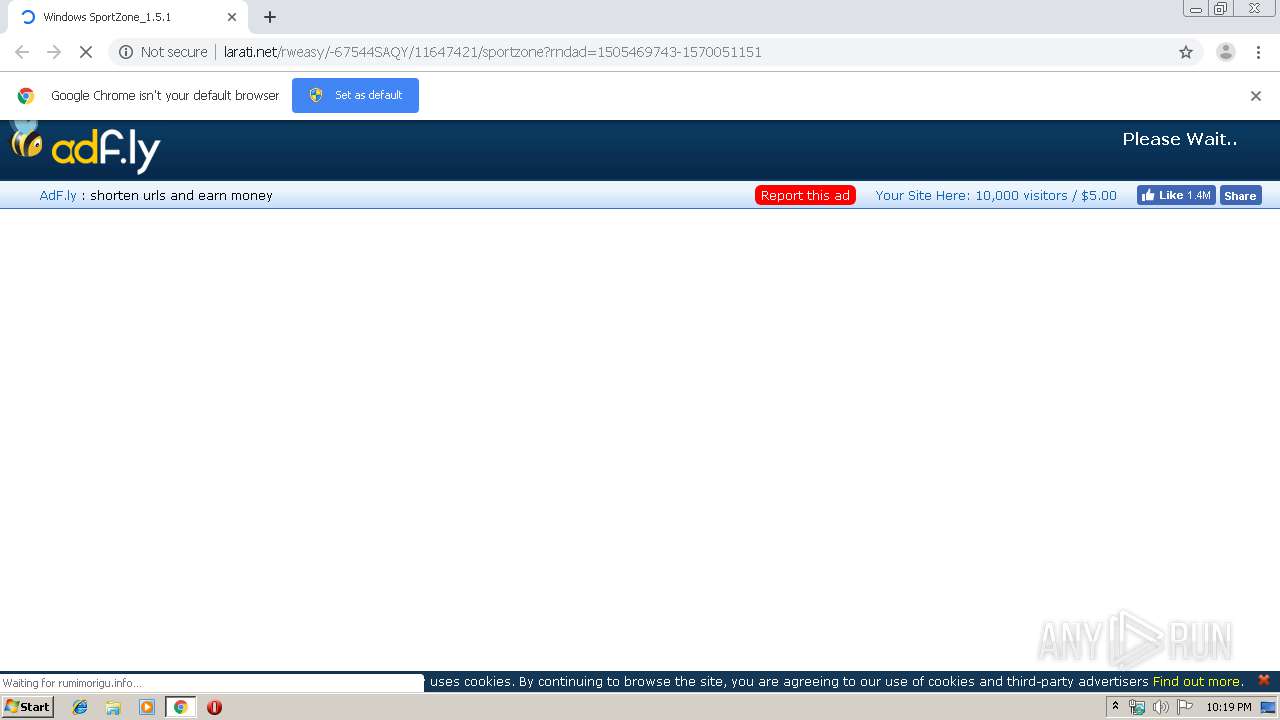
2224 | chrome.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/plugins/like.php?href=https%3A%2F%2Fwww.facebook.com%2Fx19ltd.adfly&width=150&fb_source=unshorten&layout=button_count&action=like&show_faces=false&share=true&height=21&appId=399141353502152 | IE | — | — | whitelisted |
2224 | chrome.exe | GET | 200 | 172.64.111.15:80 | http://cdn.larati.net/static/css/adfly_7.css | US | text | 869 b | malicious |
2224 | chrome.exe | GET | 200 | 172.64.111.15:80 | http://cdn.larati.net/static/js/view105c2.js | US | text | 27.2 Kb | malicious |
2224 | chrome.exe | GET | 200 | 172.64.111.15:80 | http://cdn.larati.net/static/js/b64.js | US | text | 1.08 Kb | malicious |
2224 | chrome.exe | GET | 200 | 172.64.111.15:80 | http://cdn.larati.net/static/js/amvn.js | US | text | 87.0 Kb | malicious |
2224 | chrome.exe | GET | 200 | 172.64.111.15:80 | http://cdn.larati.net/static/js/main.js | US | text | 667 b | malicious |
2224 | chrome.exe | GET | 200 | 172.64.111.15:80 | http://cdn.larati.net/static/image/logo_fb2.png | US | image | 6.14 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2224 | chrome.exe | 104.27.168.15:80 | vaugette.com | Cloudflare Inc | US | shared |
2224 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 172.64.110.15:80 | larati.net | Cloudflare Inc | US | shared |
2224 | chrome.exe | 172.217.22.78:443 | clients4.google.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.64.111.15:80 | larati.net | Cloudflare Inc | US | shared |
2224 | chrome.exe | 34.237.66.209:80 | rumimorigu.info | Amazon.com, Inc. | US | unknown |
2224 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2224 | chrome.exe | 3.225.70.173:80 | thetreuntalle.pro | — | US | unknown |
2224 | chrome.exe | 143.204.101.61:80 | trillianu.info | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vaugette.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
larati.net |
| malicious |
clients4.google.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
cdn.larati.net |
| malicious |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
rumimorigu.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3476 | Adobe AIR Application Installer.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |