| URL: | https://https.secure-links.bloemlight.com/XYWtocFMyUTVWRWd2TWpkbkwxVkdRMjlNUVdOSlVUQjZiazlGUVdvd05UTkRSVUpGVEVKd1FucHVVRlV3T0VOMVUzTjRaR05YU0hSVVoyRlBZVkp6VkhnNVdVbEZMMnBFUlVwek5GcGpRa3hLZDBsU1ExVlhlV3h6YURCU1pWQTFhbXQwTTJvck5tNW9iR1k0U1ZSTmFHUndUV3M1TjNCTU1ETnhOeXRhT0hoVVkwczRWWEozVHpFMmFWZDRhelk0ZWpaS1dXVTBSWGhXU1hneE5FRjRiMllyVGpGeFdVWlVNblJqUFMwdFIxcHJaQ3RvWmpaTVNXOWlNamxIYUV3clJuVnJkejA5LS1kZjUwYTdlM2Y4ZDc4ZDhiM2Y1ODJiNjZiMDE2MzM1MGViMDcwYzFh?cid=863404604 |
| Full analysis: | https://app.any.run/tasks/e86dce9d-45c7-4b62-bf39-4e22c357c541 |
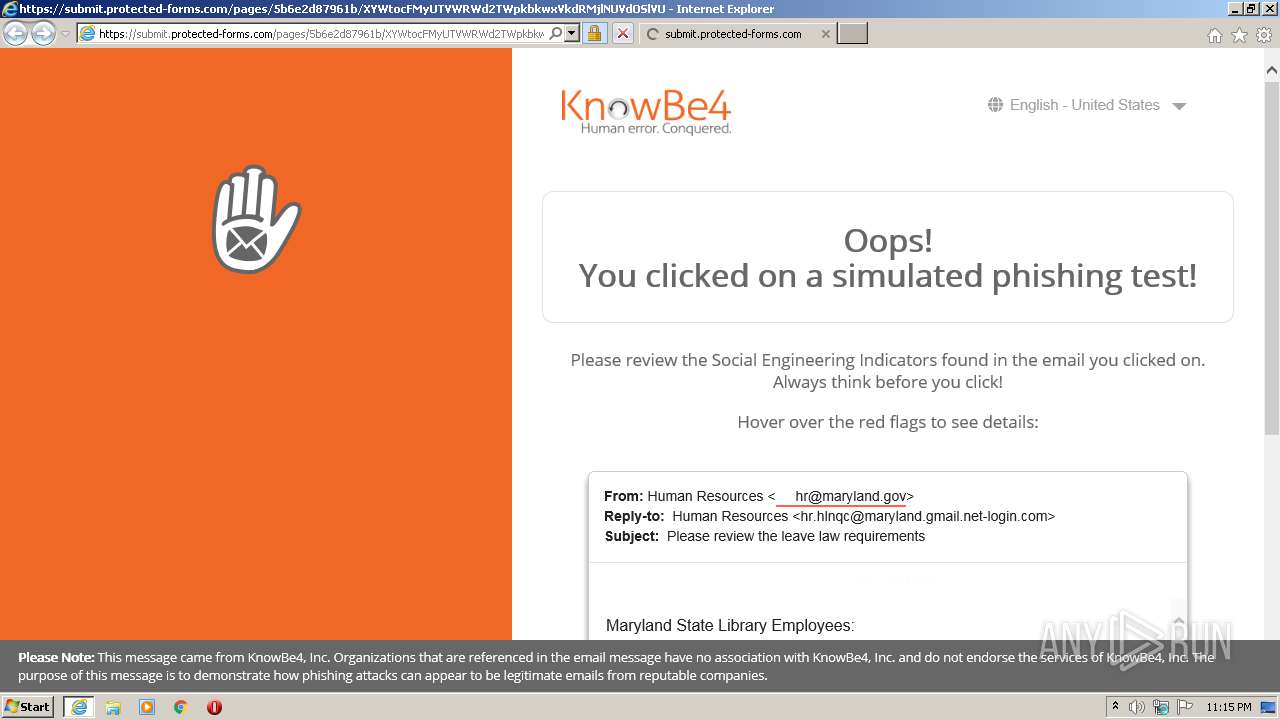
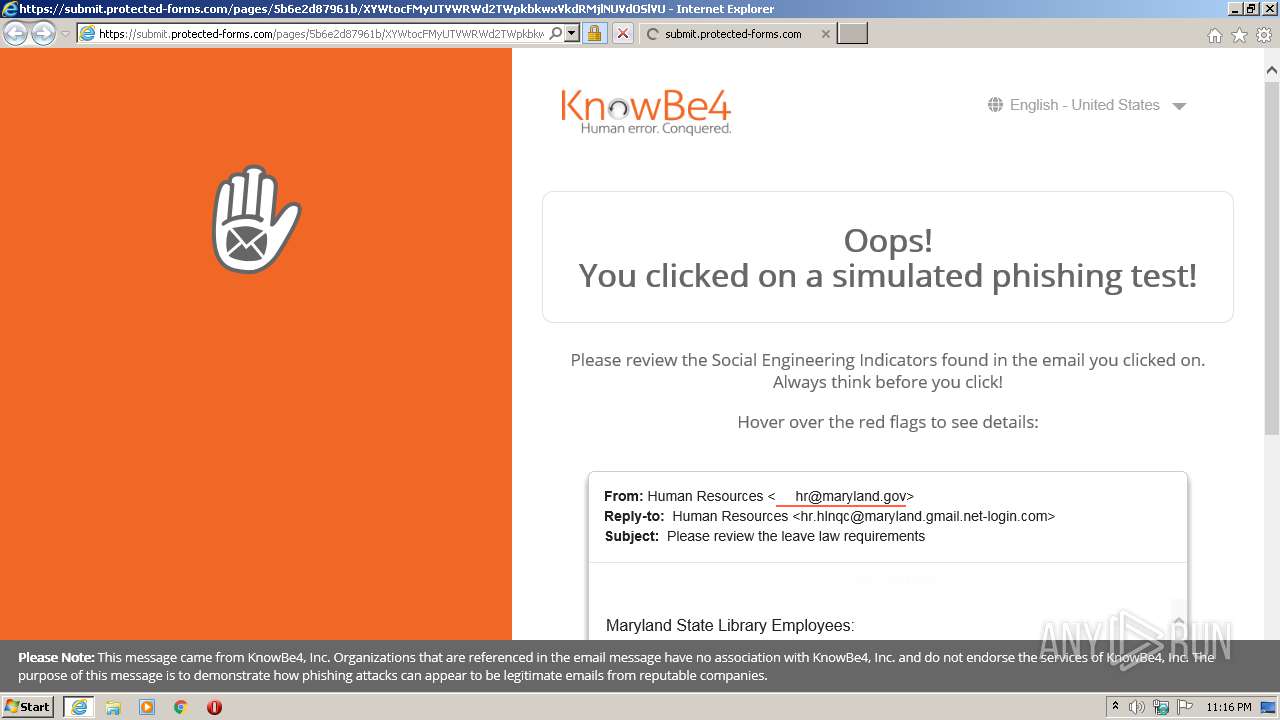
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2021, 22:15:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E99E56F90D9150D8D32852B730980D2C |
| SHA1: | 7AC19EFC21D0591FD8BB23446677428C3E131105 |
| SHA256: | AFB7878D0E170F7D27E8B197C43F8E19BCA568803E789AD5AF504C37B00795F1 |
| SSDEEP: | 12:2jyR6fHCrTnjuha1DbDnkR4CuvL7tbjhMvW/pYgRkn/MwZV5:2GRGHaTyhalbGu3xCoY2kNr |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2592)
Changes internet zones settings
- iexplore.exe (PID: 2592)
Reads internet explorer settings
- iexplore.exe (PID: 1176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1176 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2592 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://https.secure-links.bloemlight.com/XYWtocFMyUTVWRWd2TWpkbkwxVkdRMjlNUVdOSlVUQjZiazlGUVdvd05UTkRSVUpGVEVKd1FucHVVRlV3T0VOMVUzTjRaR05YU0hSVVoyRlBZVkp6VkhnNVdVbEZMMnBFUlVwek5GcGpRa3hLZDBsU1ExVlhlV3h6YURCU1pWQTFhbXQwTTJvck5tNW9iR1k0U1ZSTmFHUndUV3M1TjNCTU1ETnhOeXRhT0hoVVkwczRWWEozVHpFMmFWZDRhelk0ZWpaS1dXVTBSWGhXU1hneE5FRjRiMllyVGpGeFdVWlVNblJqUFMwdFIxcHJaQ3RvWmpaTVNXOWlNamxIYUV3clJuVnJkejA5LS1kZjUwYTdlM2Y4ZDc4ZDhiM2Y1ODJiNjZiMDE2MzM1MGViMDcwYzFh?cid=863404604" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
306
Read events
242
Write events
64
Delete events
0
Modification events
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2980693710 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30887365 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2592) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
40
Text files
19
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1176 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab941B.tmp | — | |
MD5:— | SHA256:— | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar941C.tmp | — | |
MD5:— | SHA256:— | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:D07A6B1F0BAA27489F370D87A2781D22 | SHA256:20BB7B12285437E21A31683C926EC58346A39CC03AB1D06653CE788FD2CCA168 | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:5CFBE81DCD90C84C9FD5A52F160BDA70 | SHA256:C1861AFE438052C9F477B17A3A3B202F834EA651DB4204F2D9A029129AF4DF04 | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FC5A820A001B41D68902E051F36A5282_1F04940D44B997E44F87A1C77844ABA8 | binary | |
MD5:8D83AEDEBC6634341CEF35A8E6A35992 | SHA256:EACEA3A7DE82B2CAD7163A68185E0C23E2F8D4C17AC455C1766297215AD3C47F | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\338V03WS.htm | html | |
MD5:41868AC06566F544942209B7DEC902D7 | SHA256:77C10D4620DD275DA20FC18AFCBB707DE281CC60460FF6080BC7A6CD3FFEC3CE | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:6AA344BDFF63DBE39003F245B99DE06B | SHA256:30C79D03AD055E2F61C205AC31A6062782B0880A2AB17B6283901A8389A6A47D | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\landing-watermark-8487e36eef1bec74f06631f19fea0aa171c208e2976373cda5bd0a4b9e230903[1].css | text | |
MD5:15E89F9684B18EC43EE51F8D62A787C3 | SHA256:16F13E16A7EF02FB6F94250AA1931DED83DBEE5D9FAD278E33DD5792D085194F | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:8CC55FA670A7F461764B67604533F7CE | SHA256:07FE00F2F840C062FD13D10AFAA640487B0D6762CC52A87C1A433F76786781EF | |||
| 1176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\8TV29DFG.htm | html | |
MD5:B18AC9B5BFCAC6CCEECA021E22026EDE | SHA256:38093D4B28EA8518BCE6503D7008A8F08E7D006652485CAA4A84E23AA4A4E5F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
34
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | iexplore.exe | GET | 200 | 143.204.101.190:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
1176 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
1176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEA1kUGtF8wzjWmwt3ywYtDc%3D | US | der | 471 b | whitelisted |
1176 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEA1kUGtF8wzjWmwt3ywYtDc%3D | US | der | 471 b | whitelisted |
1176 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1176 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCw80IEZ3xvjQUAAAAAh8vC | US | der | 472 b | whitelisted |
1176 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1176 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCw80IEZ3xvjQUAAAAAh8vC | US | der | 472 b | whitelisted |
1176 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCyLOF%2BWIn0QAMAAAAAzA6w | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1176 | iexplore.exe | 143.204.101.177:80 | o.ss2.us | — | US | suspicious |
1176 | iexplore.exe | 143.204.101.190:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
1176 | iexplore.exe | 143.204.101.42:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2592 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1176 | iexplore.exe | 54.165.45.250:443 | https.secure-links.bloemlight.com | Amazon.com, Inc. | US | unknown |
1176 | iexplore.exe | 143.204.101.143:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
1176 | iexplore.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1176 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1176 | iexplore.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
1176 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
https.secure-links.bloemlight.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.sca1b.amazontrust.com |
| whitelisted |
submit.protected-forms.com |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |