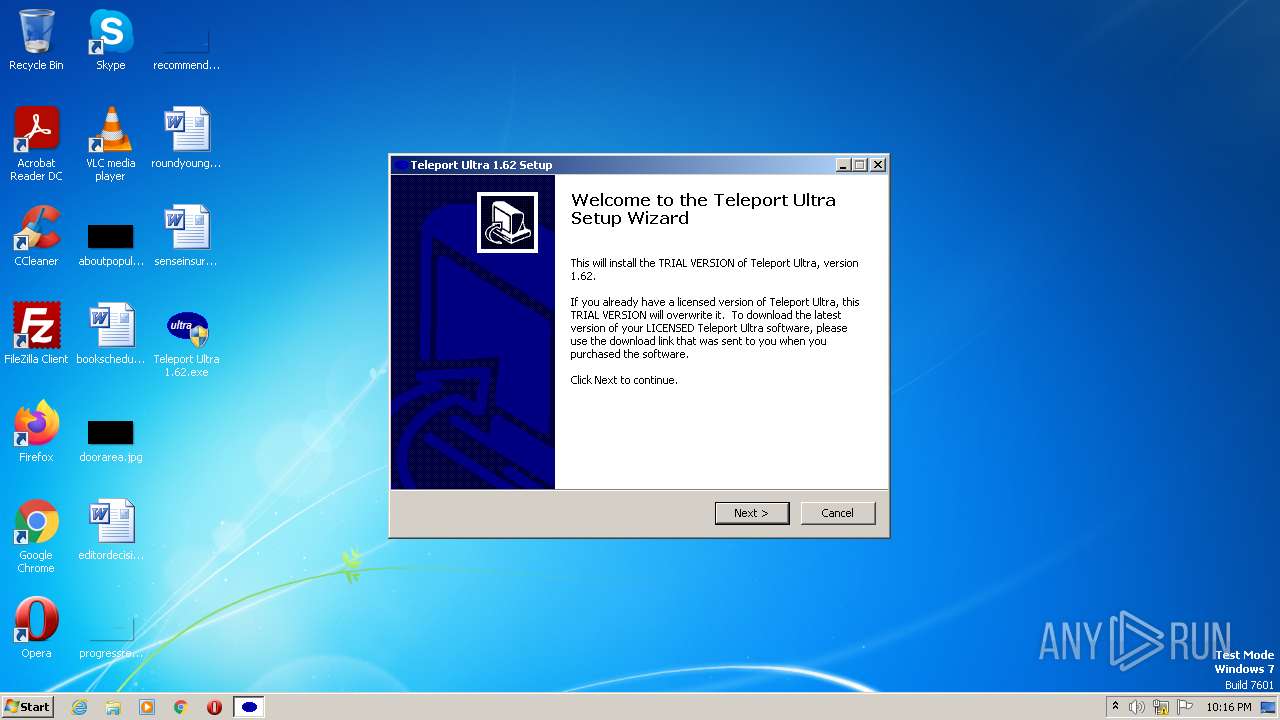
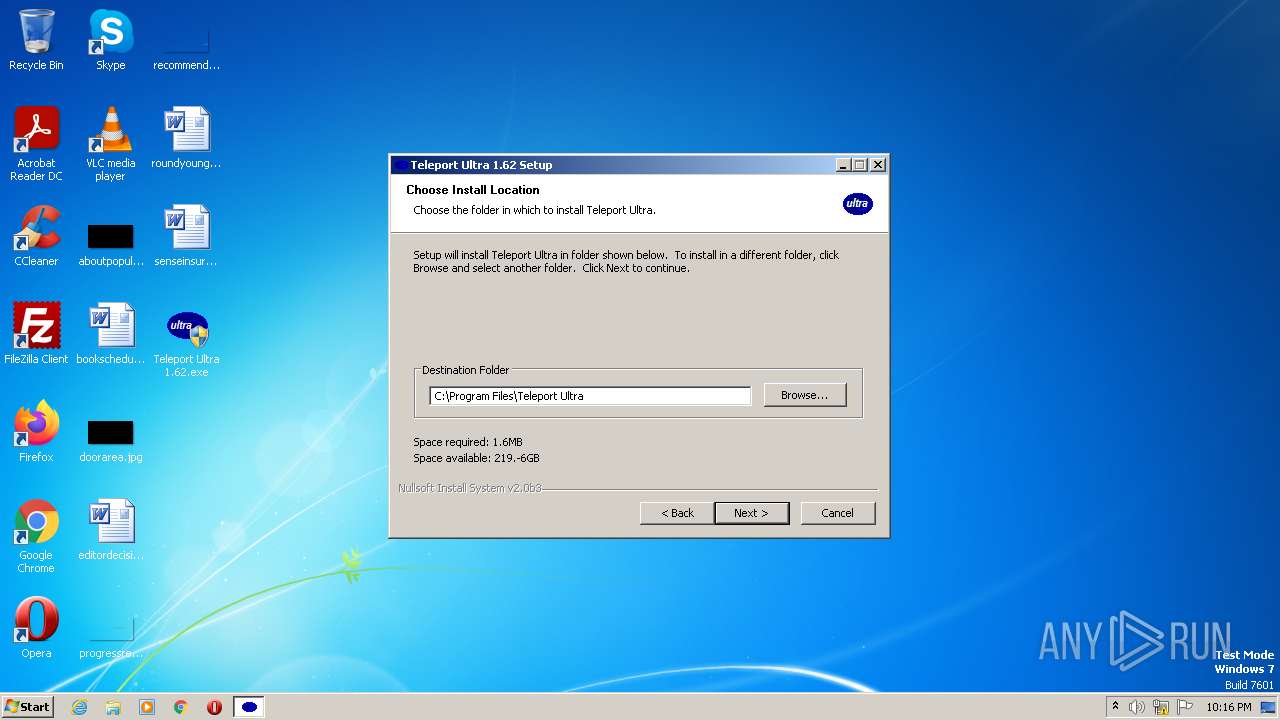
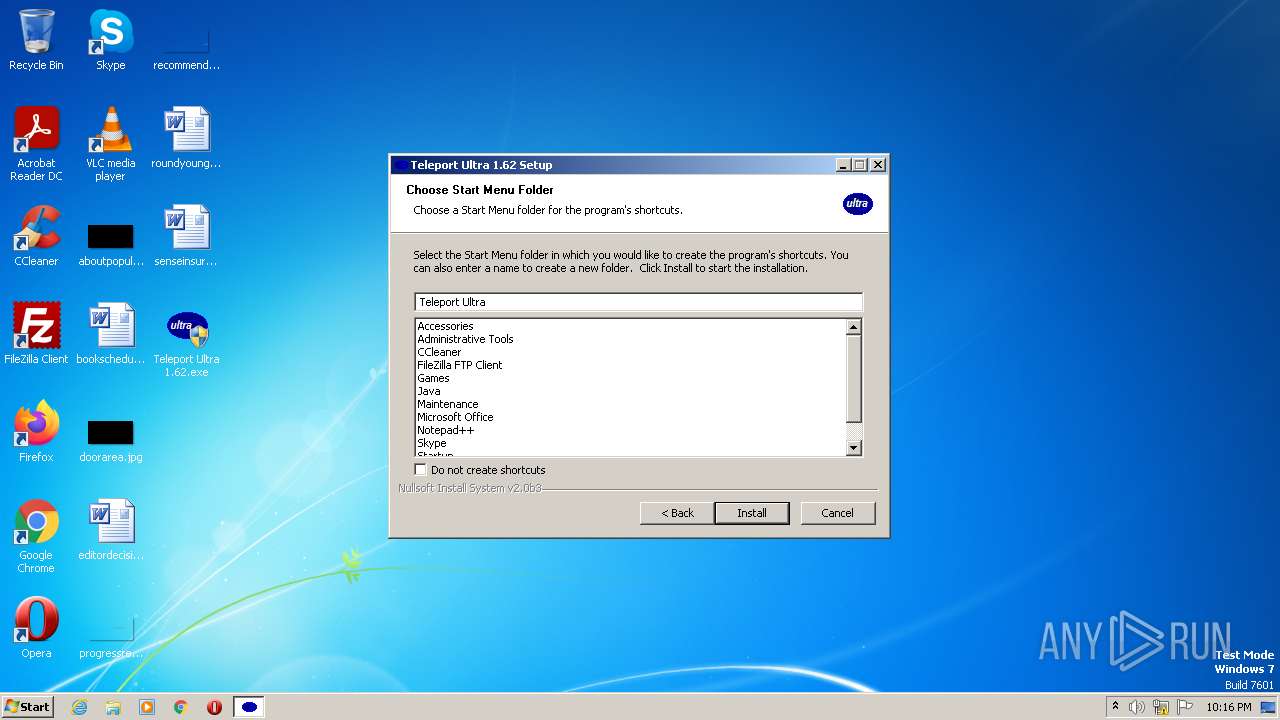
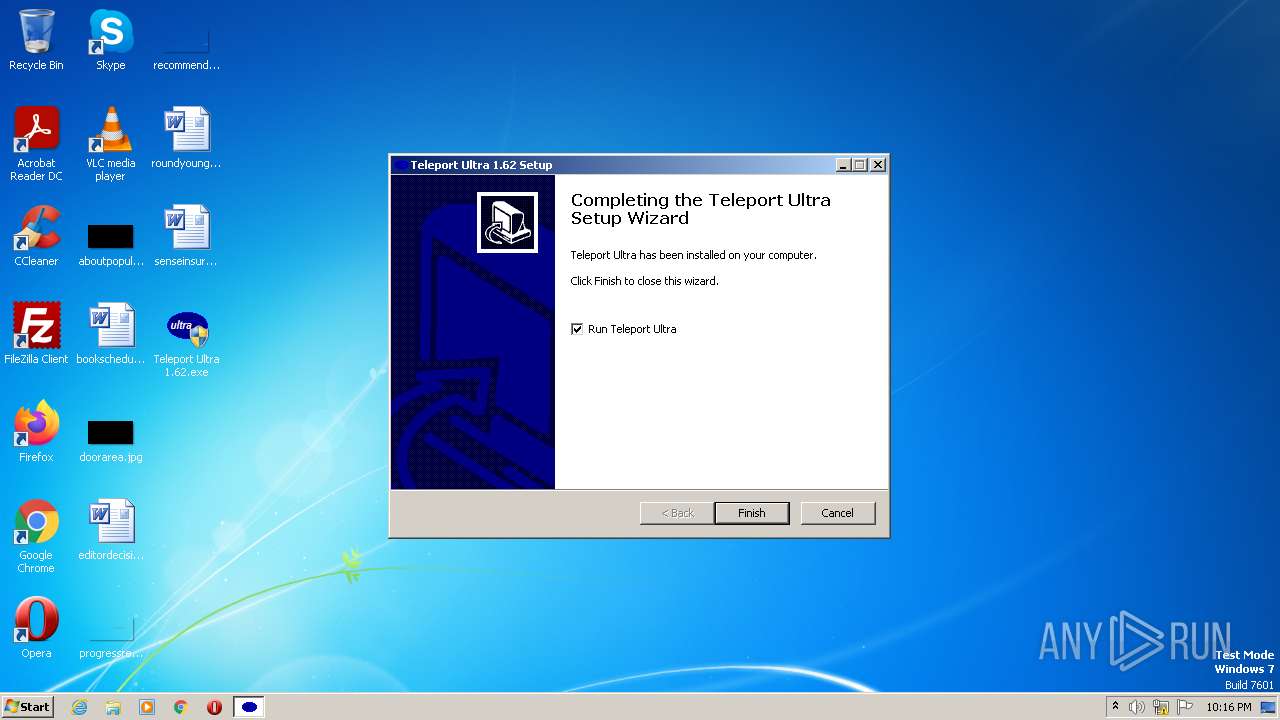
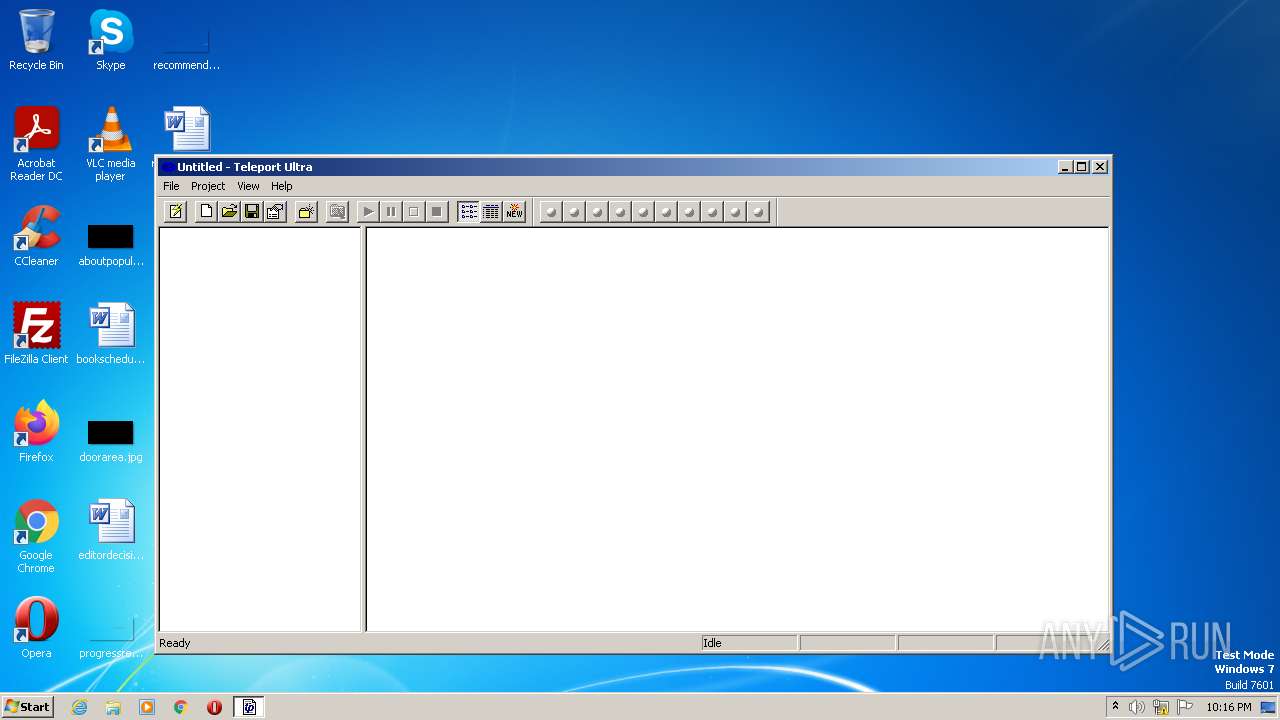
| File name: | Teleport Ultra 1.62.exe |
| Full analysis: | https://app.any.run/tasks/894d8eb2-c1d3-4218-898b-ecbf7be028e4 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2023, 22:16:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 673E2C6BC2B0484F158D708BC28D0990 |
| SHA1: | 85E2BCF8102BB05848BE7ED3F9DA2C1E1347C983 |
| SHA256: | AFA44A32662A396C036217771B65803EC94EAC7DFE58C4DD1CC30DEE011CAE5E |
| SSDEEP: | 24576:2lwHn946feOHbUMT3hF/lJiThoLqdjF42qShm:2lwHnC6feOPBJfSjRqkm |
MALICIOUS
Application was dropped or rewritten from another process
- ultra.exe (PID: 1164)
SUSPICIOUS
Executable content was dropped or overwritten
- Teleport Ultra 1.62.exe (PID: 3388)
INFO
Create files in a temporary directory
- Teleport Ultra 1.62.exe (PID: 3388)
Reads the computer name
- Teleport Ultra 1.62.exe (PID: 3388)
- ultra.exe (PID: 1164)
Checks supported languages
- Teleport Ultra 1.62.exe (PID: 3388)
- ultra.exe (PID: 1164)
The process checks LSA protection
- Teleport Ultra 1.62.exe (PID: 3388)
- ultra.exe (PID: 1164)
Creates files in the program directory
- ultra.exe (PID: 1164)
- Teleport Ultra 1.62.exe (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x40a1 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 155136 |
| CodeSize: | 24576 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2003:07:30 19:36:16+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jul-2003 19:36:16 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 30-Jul-2003 19:36:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E8A | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42359 |
.rdata | 0x00007000 | 0x000011D4 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23003 |
.data | 0x00009000 | 0x00023BFC | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0051 |
.rsrc | 0x0002D000 | 0x00002000 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.00615 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10531 | 534 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.41902 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 3.15029 | 3752 | UNKNOWN | English - United States | RT_ICON |
103 | 2.21754 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73432 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.9204 | 312 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.49109 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.87634 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
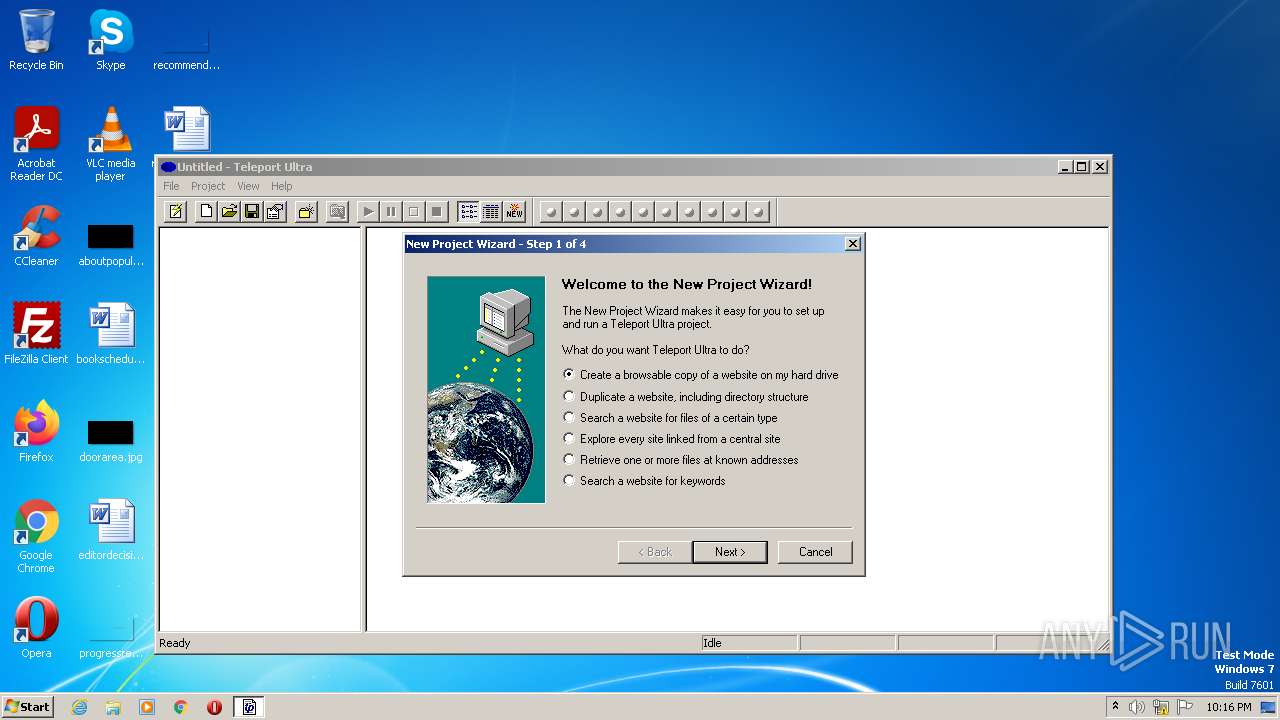
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | "C:\Program Files\Teleport Ultra\ultra.exe" | C:\Program Files\Teleport Ultra\ultra.exe | — | Teleport Ultra 1.62.exe | |||||||||||
User: admin Company: Tennyson Maxwell Information Systems, Inc. Integrity Level: HIGH Description: Teleport Ultra Exit code: 0 Version: 1.62 Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\Desktop\Teleport Ultra 1.62.exe" | C:\Users\admin\Desktop\Teleport Ultra 1.62.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\Desktop\Teleport Ultra 1.62.exe" | C:\Users\admin\Desktop\Teleport Ultra 1.62.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 188
Read events
1 184
Write events
0
Delete events
4
Modification events
| (PID) Process: | (1164) ultra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\MenuExt\Add to &Teleport |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1164) ultra.exe | Key: | HKEY_CURRENT_USER\Software\Tennyson Maxwell\Teleport Ultra\Recent File List |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
10
Suspicious files
2
Text files
6
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | Teleport Ultra 1.62.exe | C:\Program Files\Teleport Ultra\Projects\LA Opera.tpu | tpp | |
MD5:8A6D8A1F94B77856528F657E4AE14FEB | SHA256:490037FD6C2F85C720FA16F5B951C2DC01682D3EF24E6ED15C4610188D15291A | |||
| 3388 | Teleport Ultra 1.62.exe | C:\Program Files\Teleport Ultra\Projects\Museums.tpu | tpp | |
MD5:F2E98B7D939CD6A44135AB56198DF95D | SHA256:27F5547193B99E76B1E7D0F3644B5DD24BBC4B0D3E478CCD3E905A3D35ABE6ED | |||
| 3388 | Teleport Ultra 1.62.exe | C:\Program Files\Teleport Ultra\Projects\Hitchhiker's Guide.tpu | tpp | |
MD5:9AD05098719A2079F03B8E7431313B12 | SHA256:77972126F7ED01F7E4BB01EB932945C55CB9C5630F2A3E8F5B9B3D49FE21F7D8 | |||
| 3388 | Teleport Ultra 1.62.exe | C:\Users\admin\AppData\Local\Temp\nstF211.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3388 | Teleport Ultra 1.62.exe | C:\Program Files\Teleport Ultra\ultra.exe | executable | |
MD5:9FF29E4D8E5942BDA10C8A42D067C590 | SHA256:25689F382E5FF007454C7CAAFB1C5490CAF24ABBA33355A647E08745CB6EFC63 | |||
| 3388 | Teleport Ultra 1.62.exe | C:\Program Files\Teleport Ultra\manual.pdf | ||
MD5:E6C6CBEFD07D40E4F827DC2FDCE4C537 | SHA256:A8D179FFD82CB5554E95CE9647C937517E524499BEB843D40198F86D79624100 | |||
| 3388 | Teleport Ultra 1.62.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Teleport Ultra\Scheduler.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3388 | Teleport Ultra 1.62.exe | C:\Program Files\Teleport Ultra\scheduler.exe | executable | |
MD5:886B390FCC2578E9F68C987D145D8516 | SHA256:4CC1D94AB7EAE85264501DE09F596D603905EA714D9EE5A6E087EFB3DEAE5105 | |||
| 3388 | Teleport Ultra 1.62.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Teleport Ultra\Teleport Ultra.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3388 | Teleport Ultra 1.62.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Teleport Ultra\Help.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report