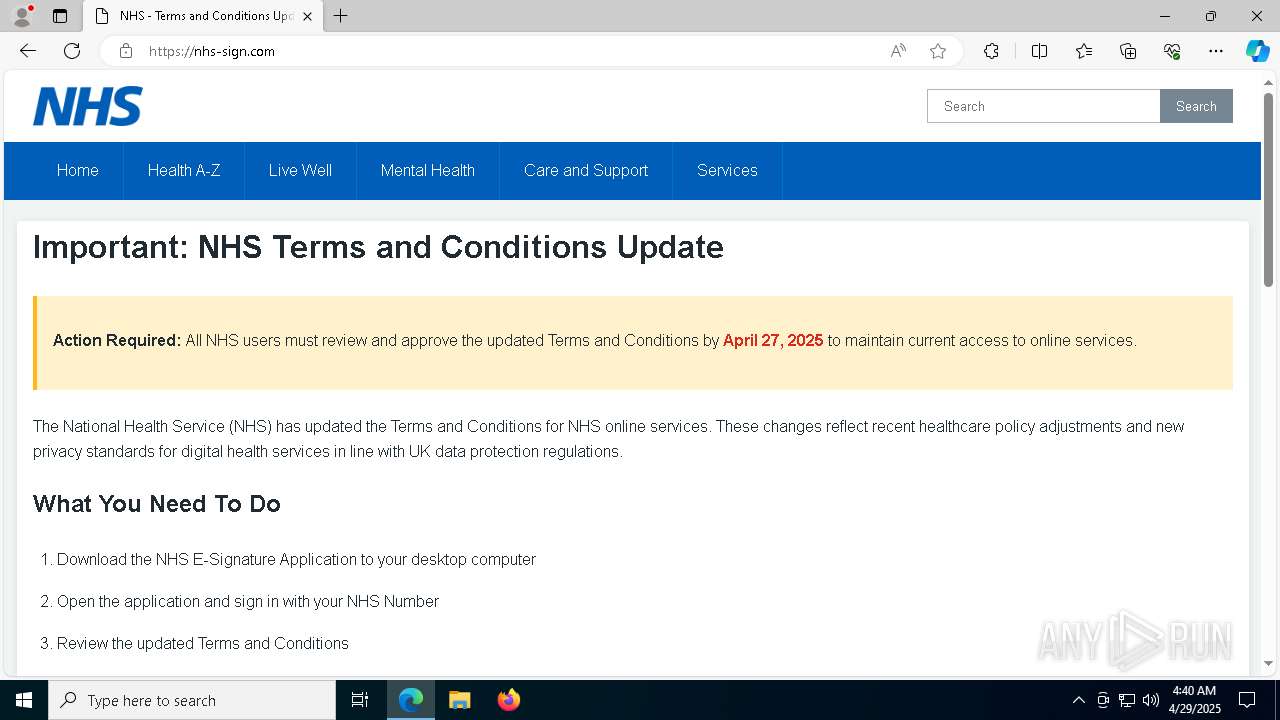
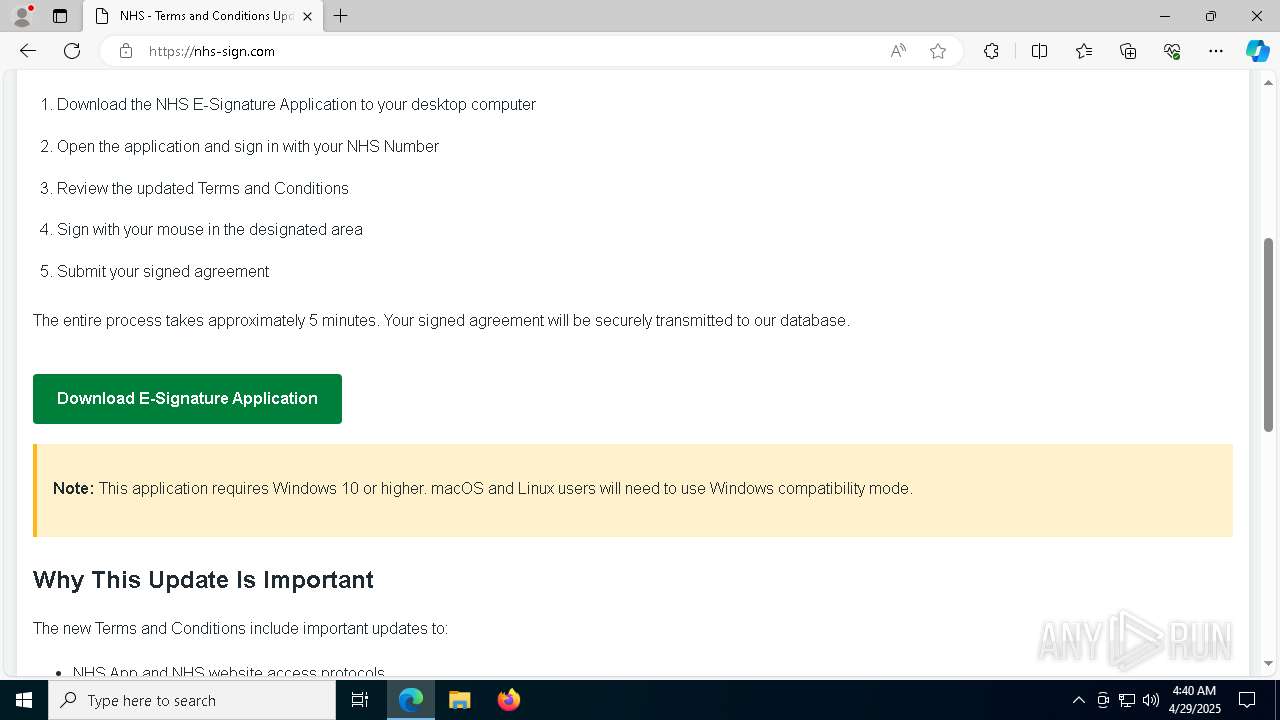
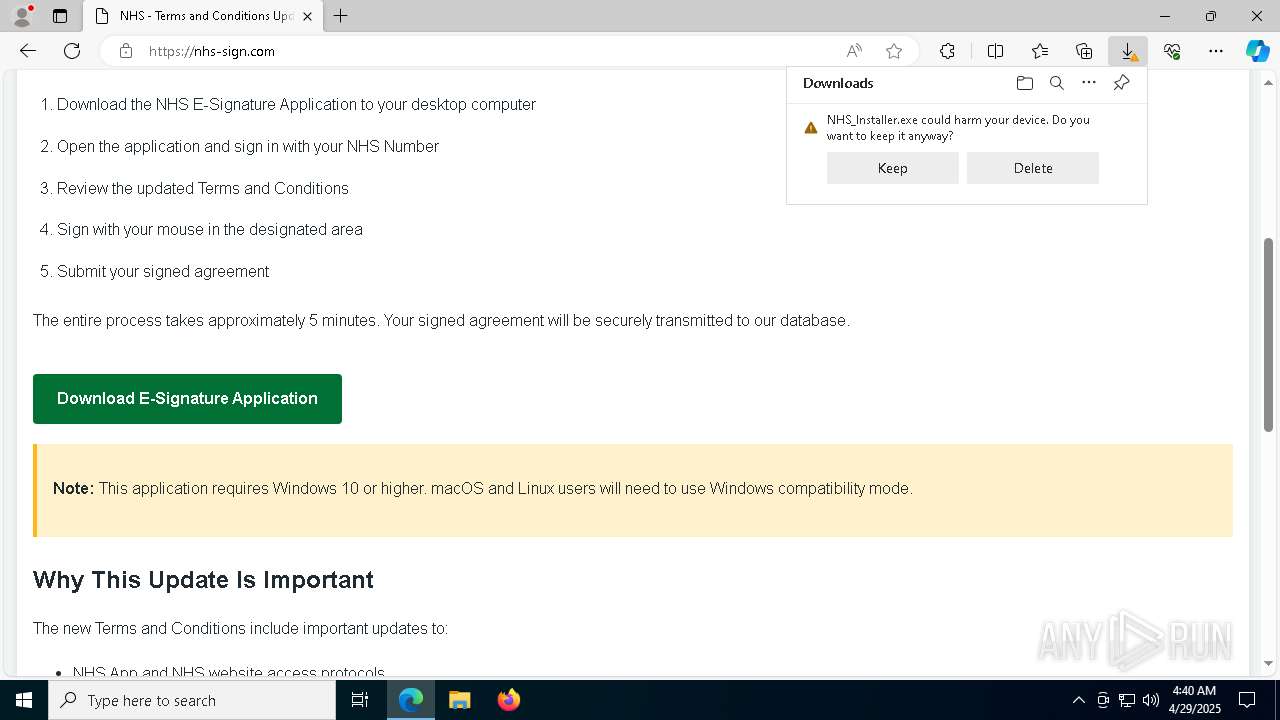
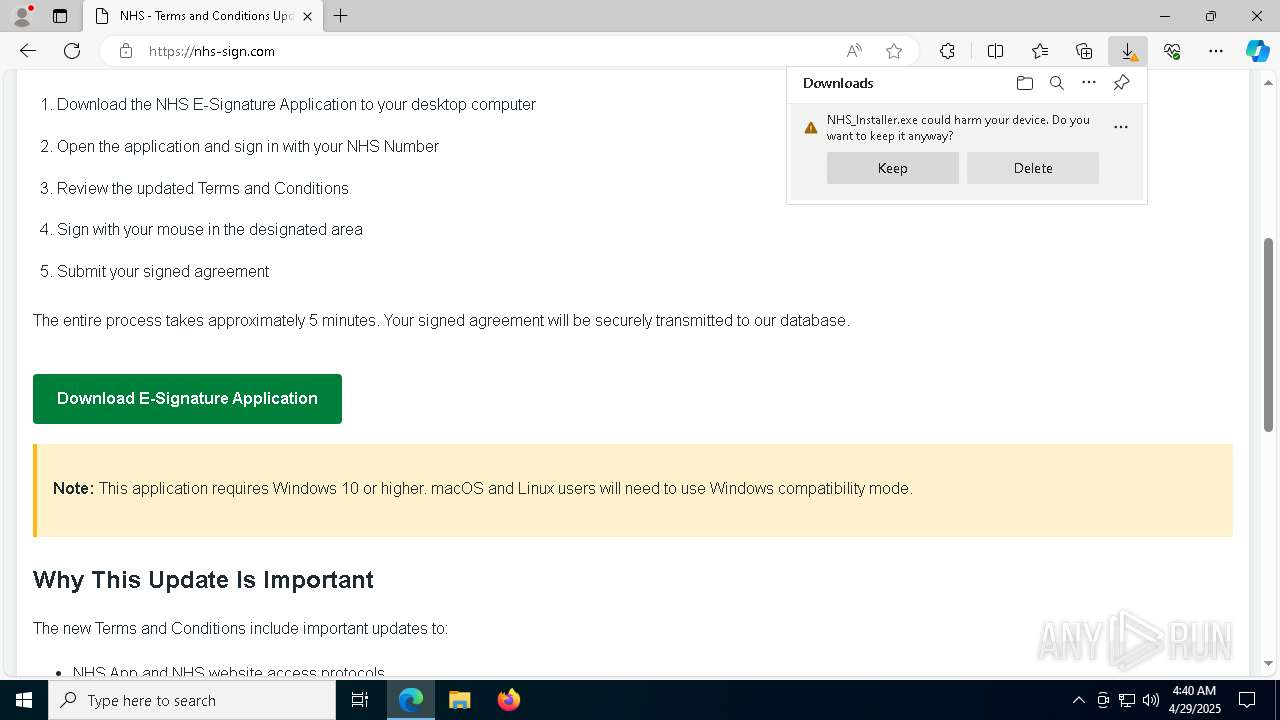
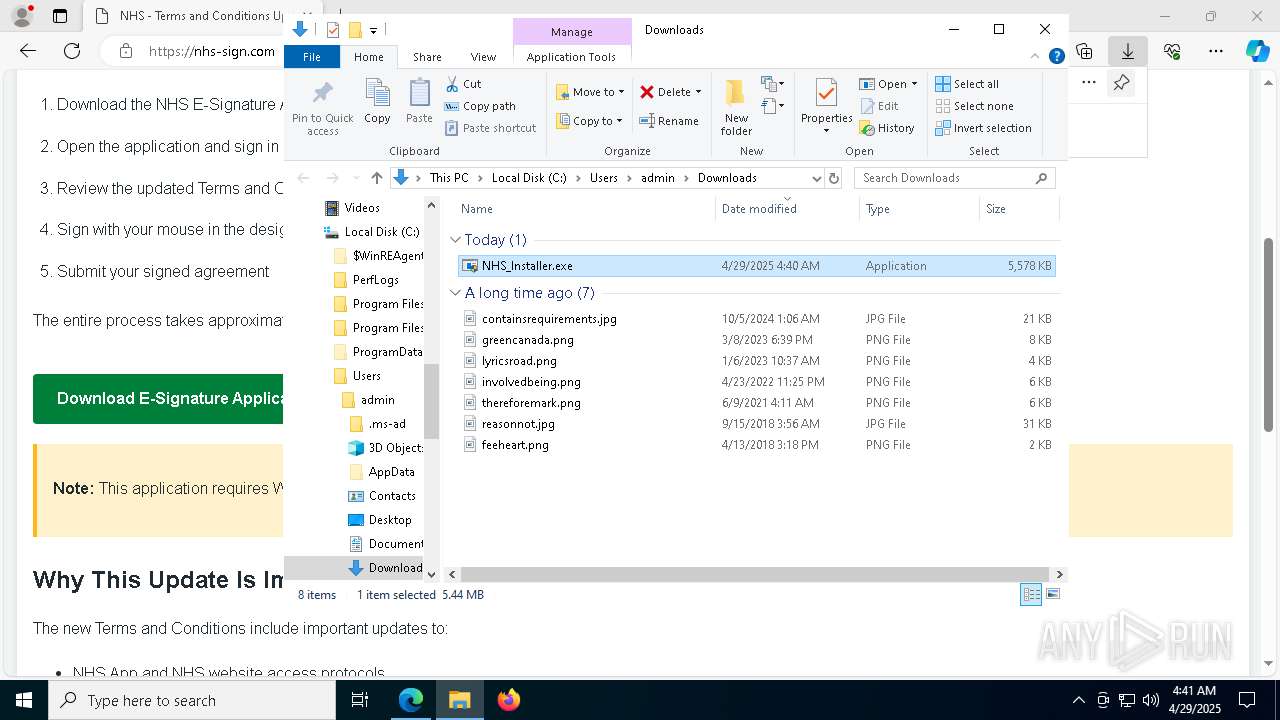
| URL: | https://nhs-sign.com |
| Full analysis: | https://app.any.run/tasks/29b32aa0-c29e-4783-be23-ca985e9d85de |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 04:39:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DFE398652BB3A5C52989AF7AAD75D26F |
| SHA1: | CE9A9D8B4277238C4098BEF4B8FF360095D6E037 |
| SHA256: | AF968187647793D504301412E6C32AA452D6BE1D86075EA39E42B546CC7F9D96 |
| SSDEEP: | 3:N8zCLZI:2zCLZI |
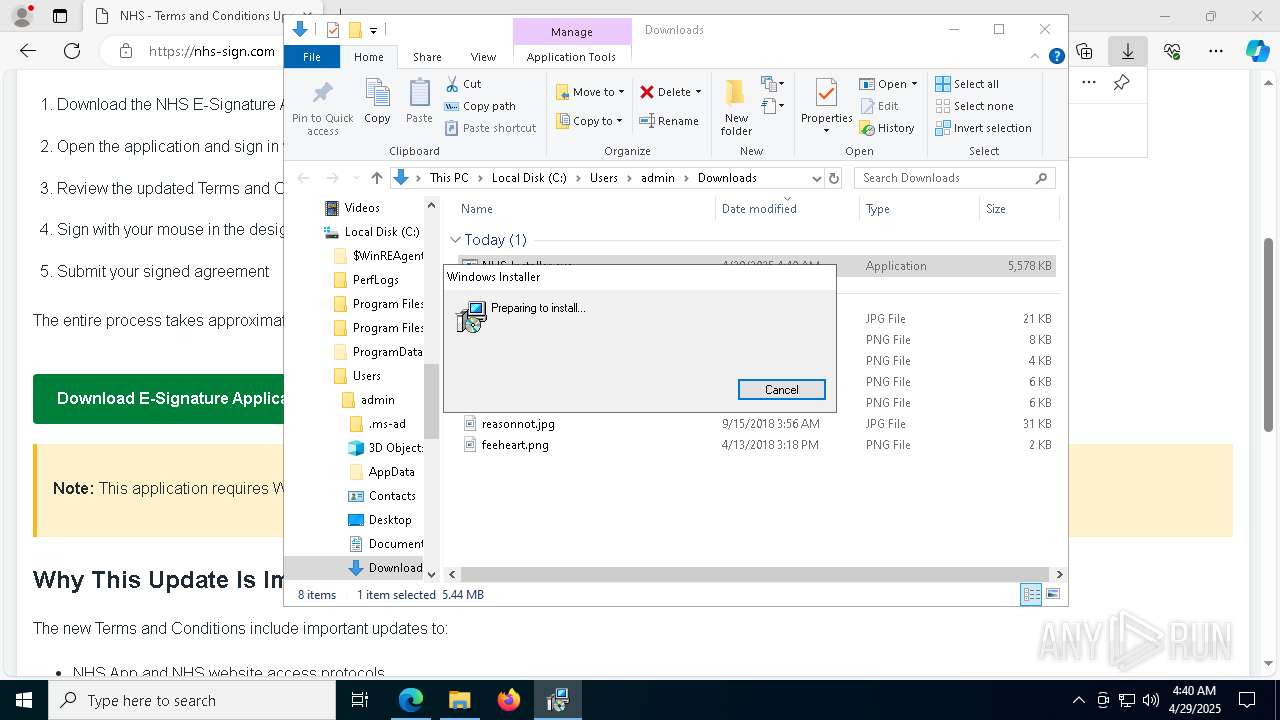
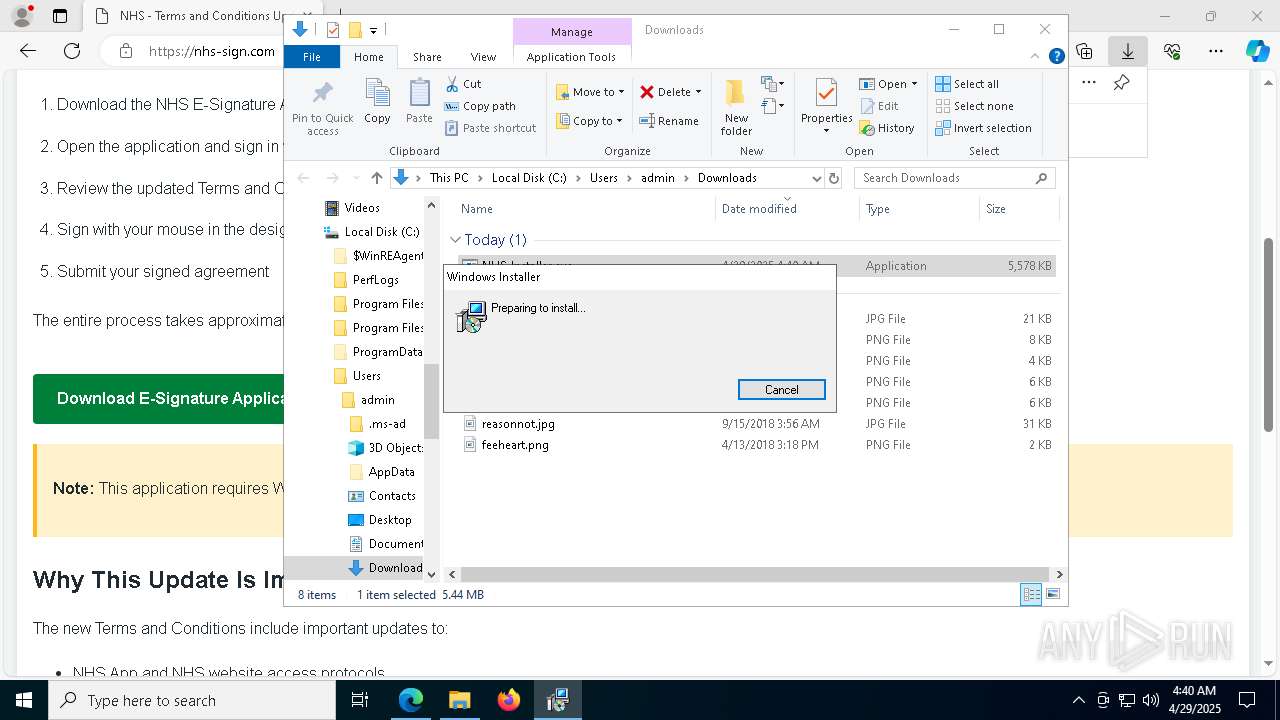
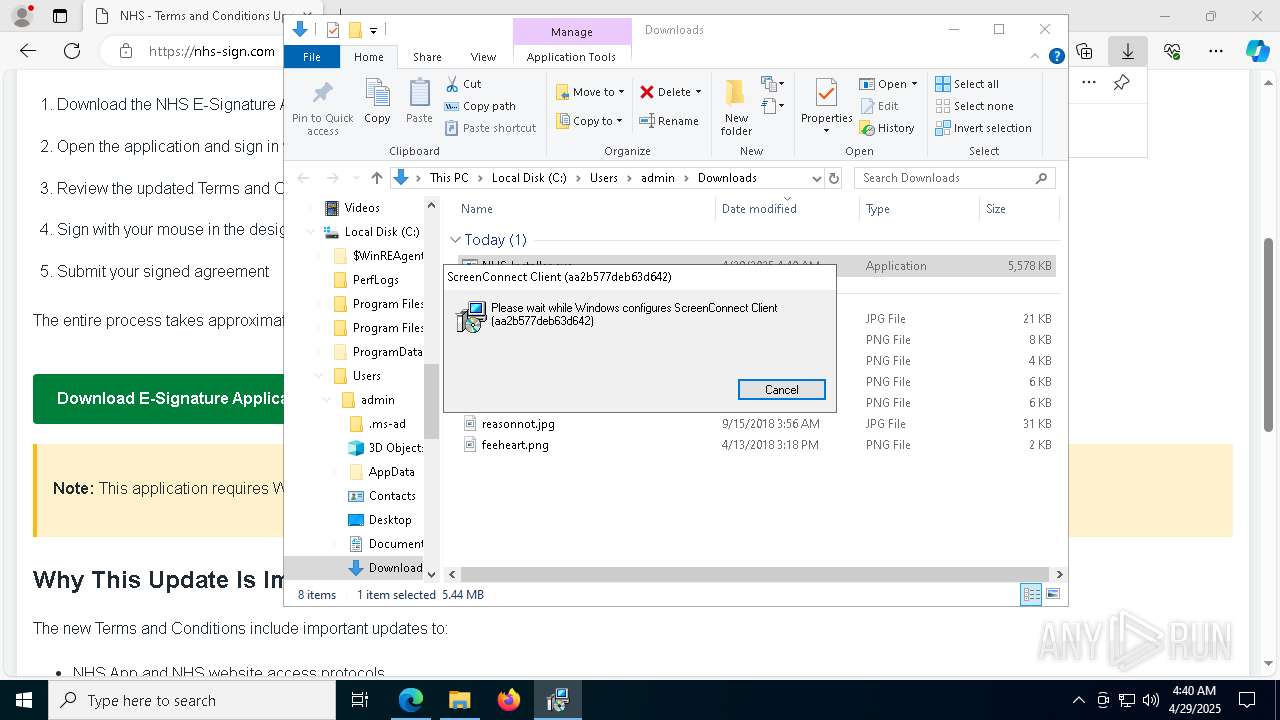
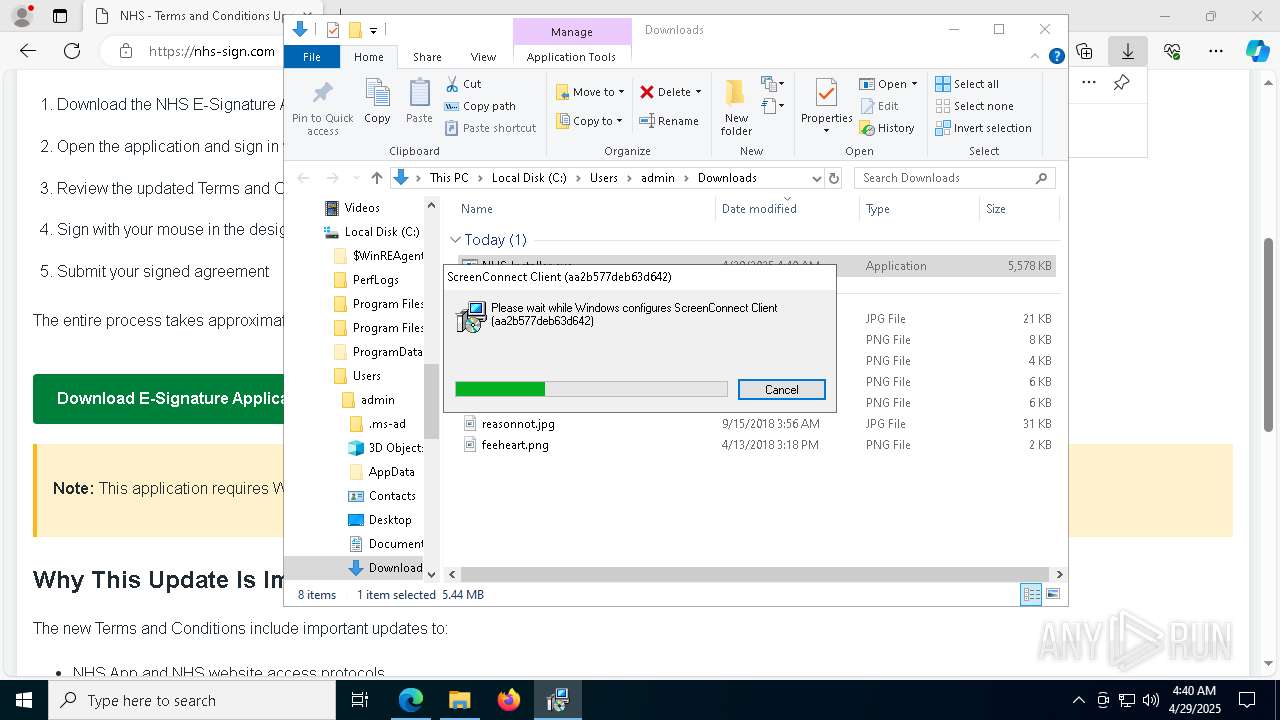
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 1804)
SUSPICIOUS
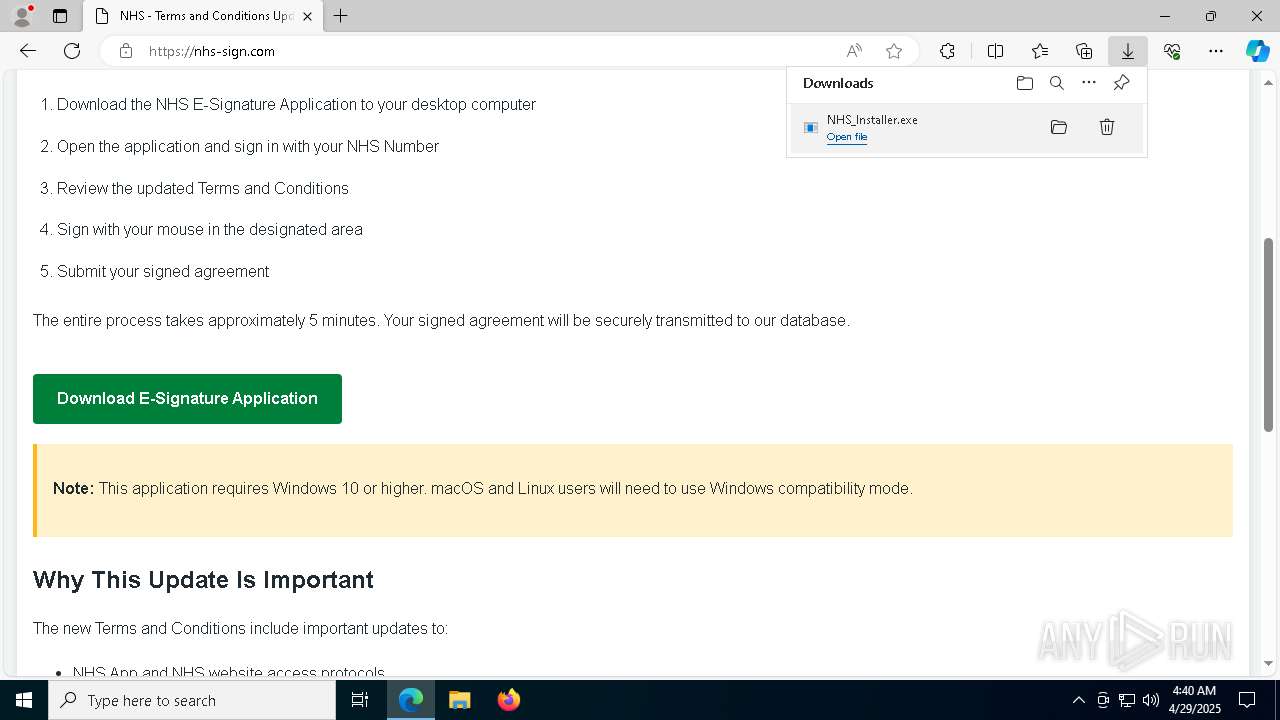
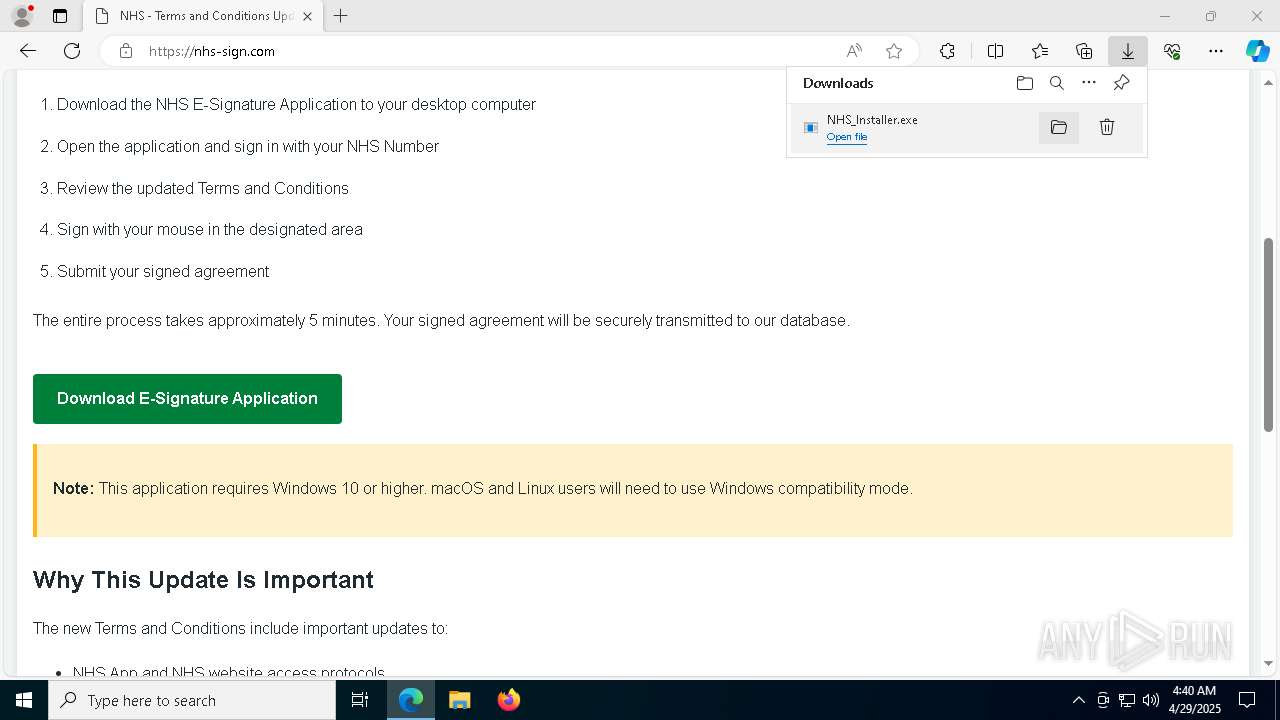
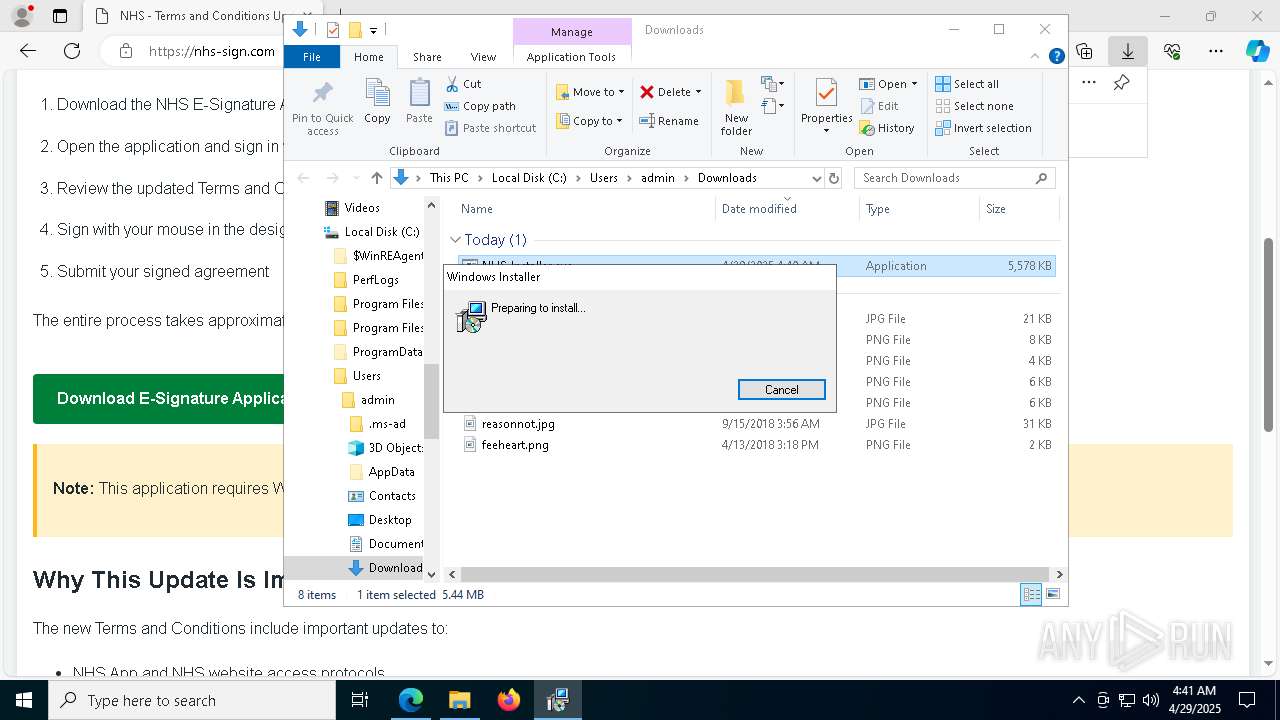
Executes application which crashes
- NHS_Installer.exe (PID: 2560)
- NHS_Installer.exe (PID: 7704)
- NHS_Installer.exe (PID: 1040)
Reads security settings of Internet Explorer
- NHS_Installer.exe (PID: 6392)
Executes as Windows Service
- VSSVC.exe (PID: 7780)
- ScreenConnect.ClientService.exe (PID: 1804)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 1804)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 1804)
Executable content was dropped or overwritten
- rundll32.exe (PID: 1188)
- rundll32.exe (PID: 2596)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 1804)
INFO
Reads Environment values
- identity_helper.exe (PID: 4608)
Reads the computer name
- identity_helper.exe (PID: 4608)
- NHS_Installer.exe (PID: 6392)
- NHS_Installer.exe (PID: 2560)
- NHS_Installer.exe (PID: 7704)
- NHS_Installer.exe (PID: 1040)
- msiexec.exe (PID: 3024)
- msiexec.exe (PID: 5776)
Application launched itself
- msedge.exe (PID: 660)
Checks supported languages
- identity_helper.exe (PID: 4608)
- NHS_Installer.exe (PID: 2560)
- NHS_Installer.exe (PID: 6392)
- msiexec.exe (PID: 3024)
- NHS_Installer.exe (PID: 7704)
- NHS_Installer.exe (PID: 1040)
- msiexec.exe (PID: 5776)
Executable content was dropped or overwritten
- msedge.exe (PID: 660)
- msedge.exe (PID: 7236)
- msiexec.exe (PID: 3024)
- msiexec.exe (PID: 5972)
- msedge.exe (PID: 3992)
- msiexec.exe (PID: 2100)
Reads the machine GUID from the registry
- NHS_Installer.exe (PID: 6392)
- NHS_Installer.exe (PID: 2560)
- NHS_Installer.exe (PID: 7704)
- NHS_Installer.exe (PID: 1040)
Process checks computer location settings
- NHS_Installer.exe (PID: 6392)
SCREENCONNECT has been detected
- NHS_Installer.exe (PID: 2560)
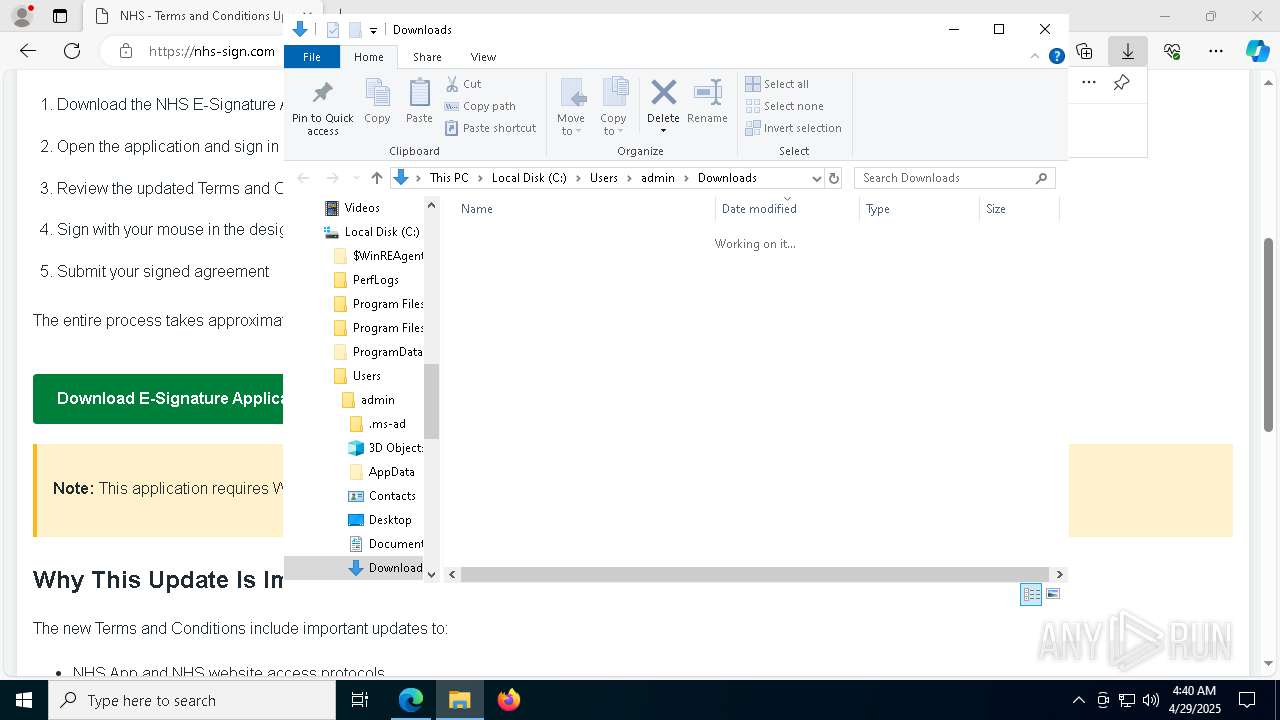
Create files in a temporary directory
- NHS_Installer.exe (PID: 6392)
- rundll32.exe (PID: 1188)
CONNECTWISE has been detected
- msiexec.exe (PID: 5972)
Manages system restore points
- SrTasks.exe (PID: 7920)
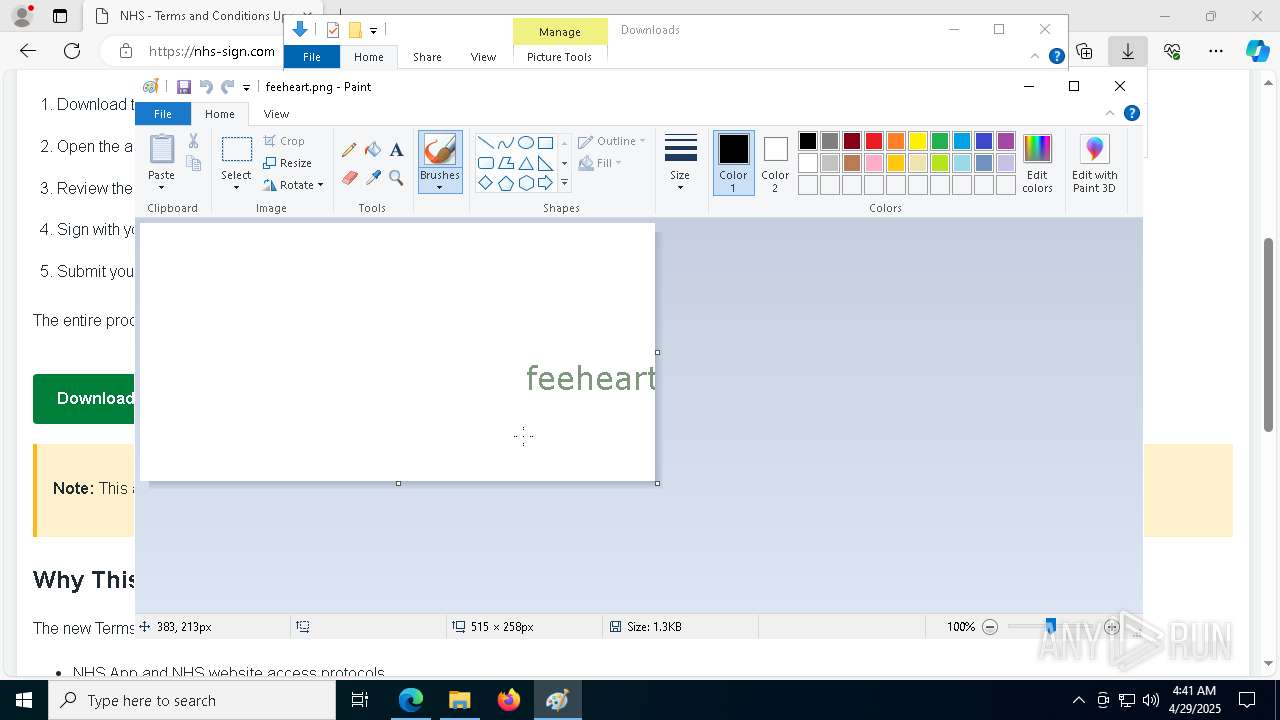
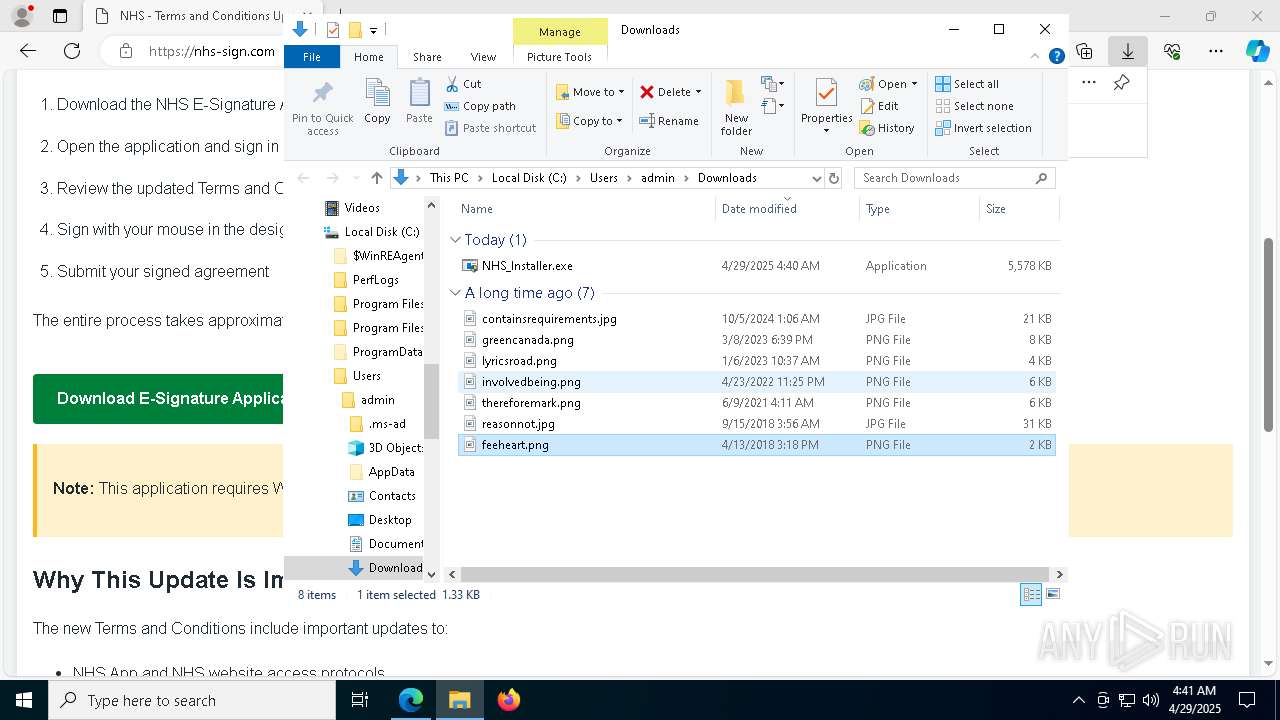
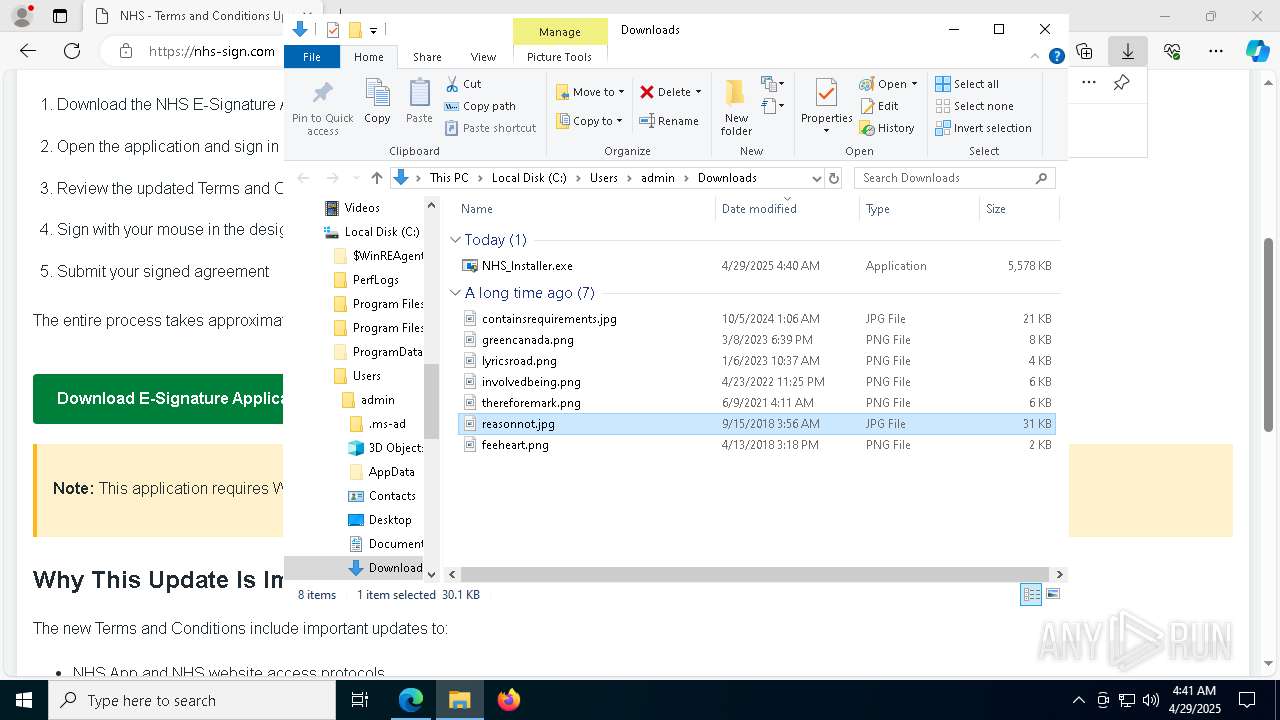
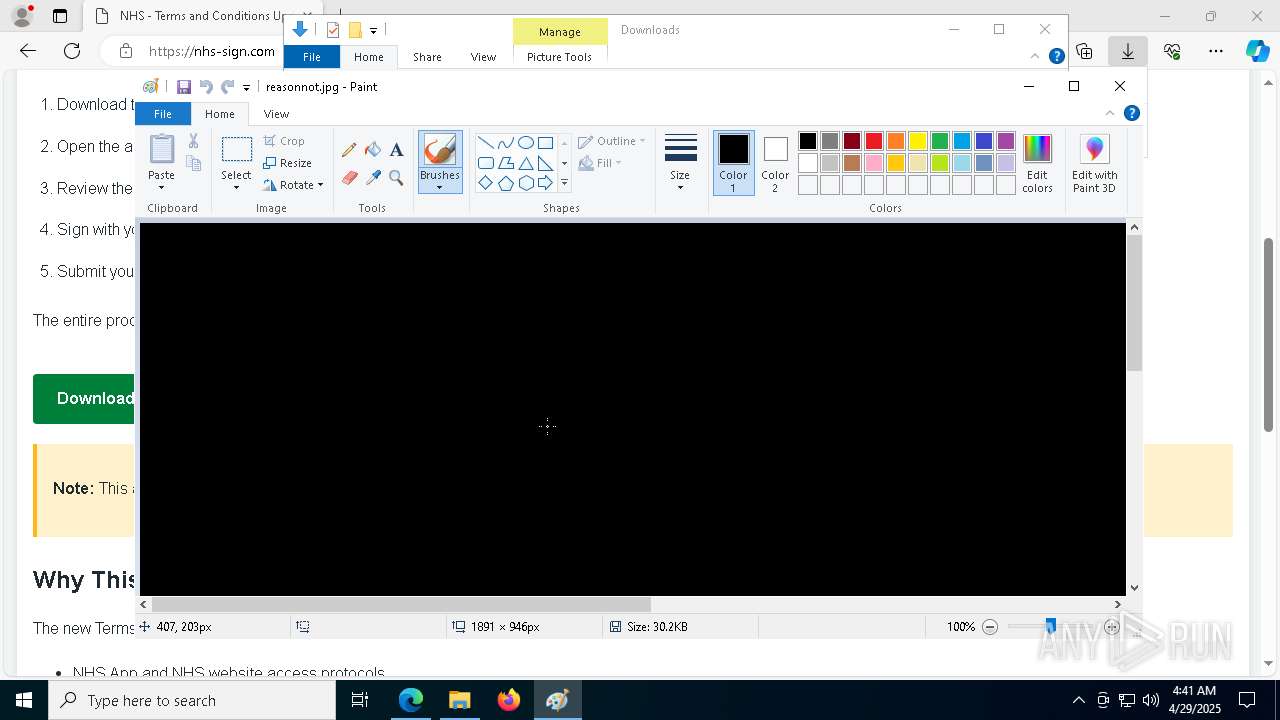
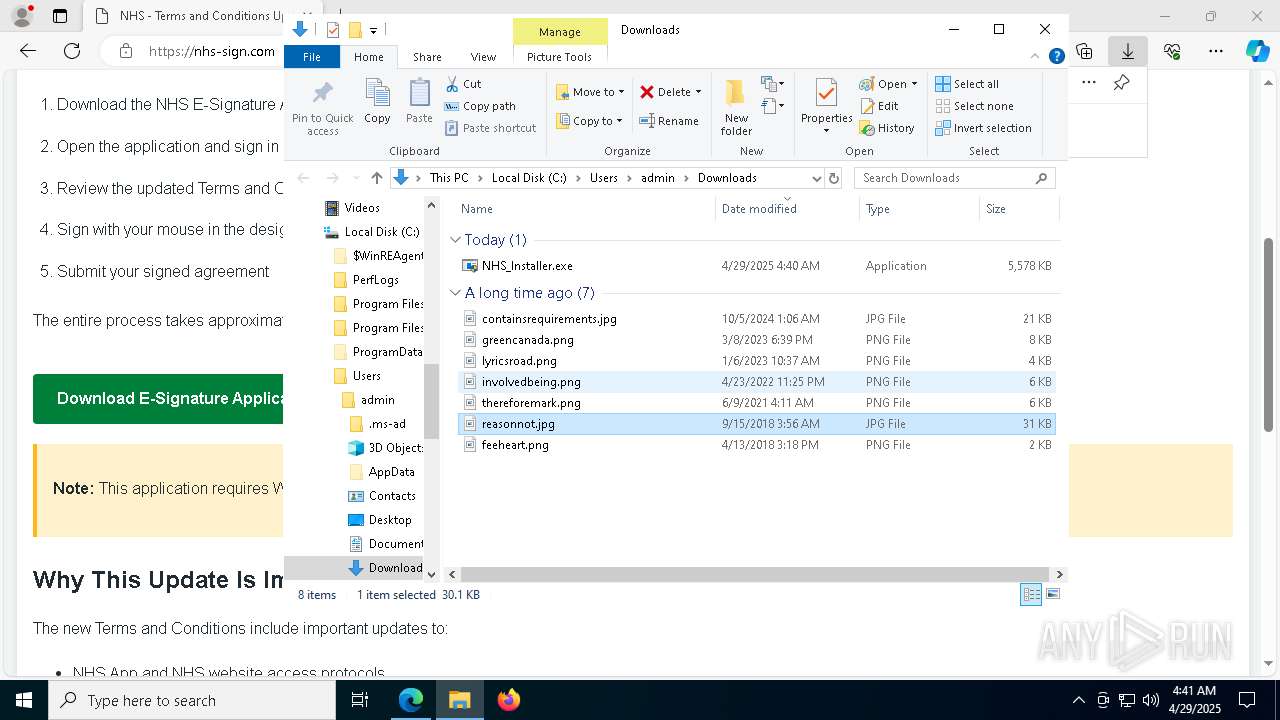
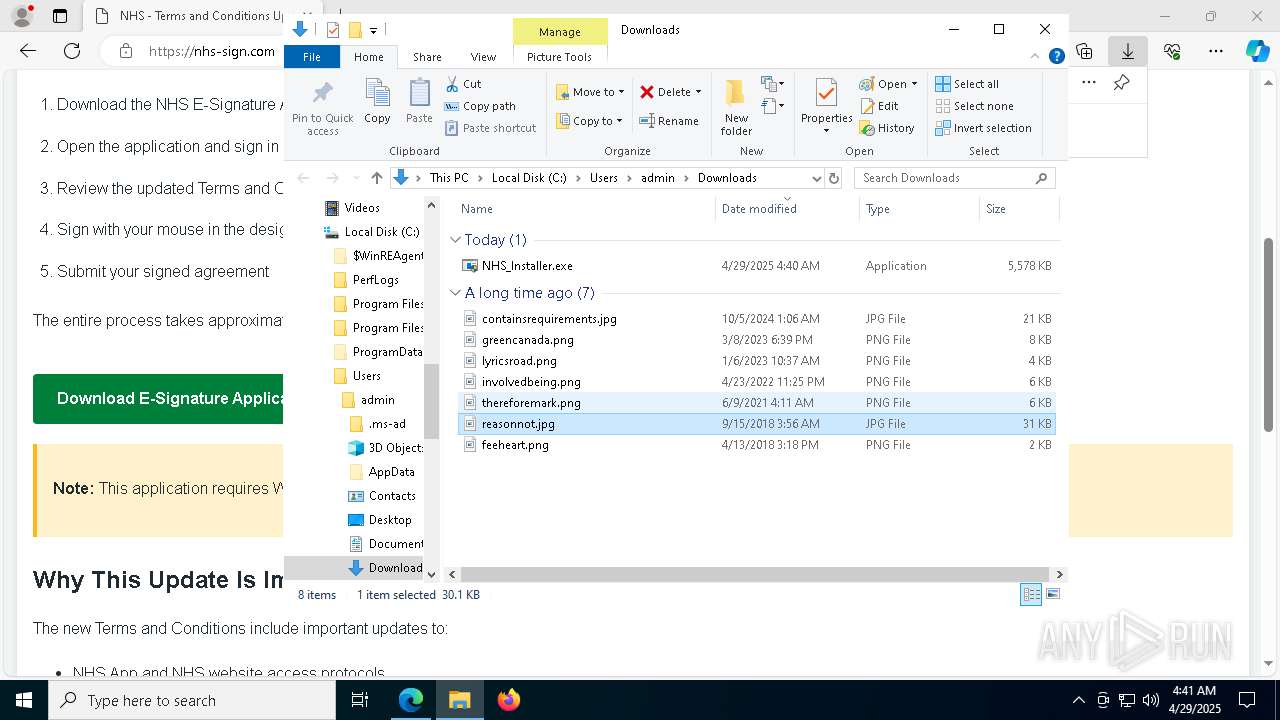
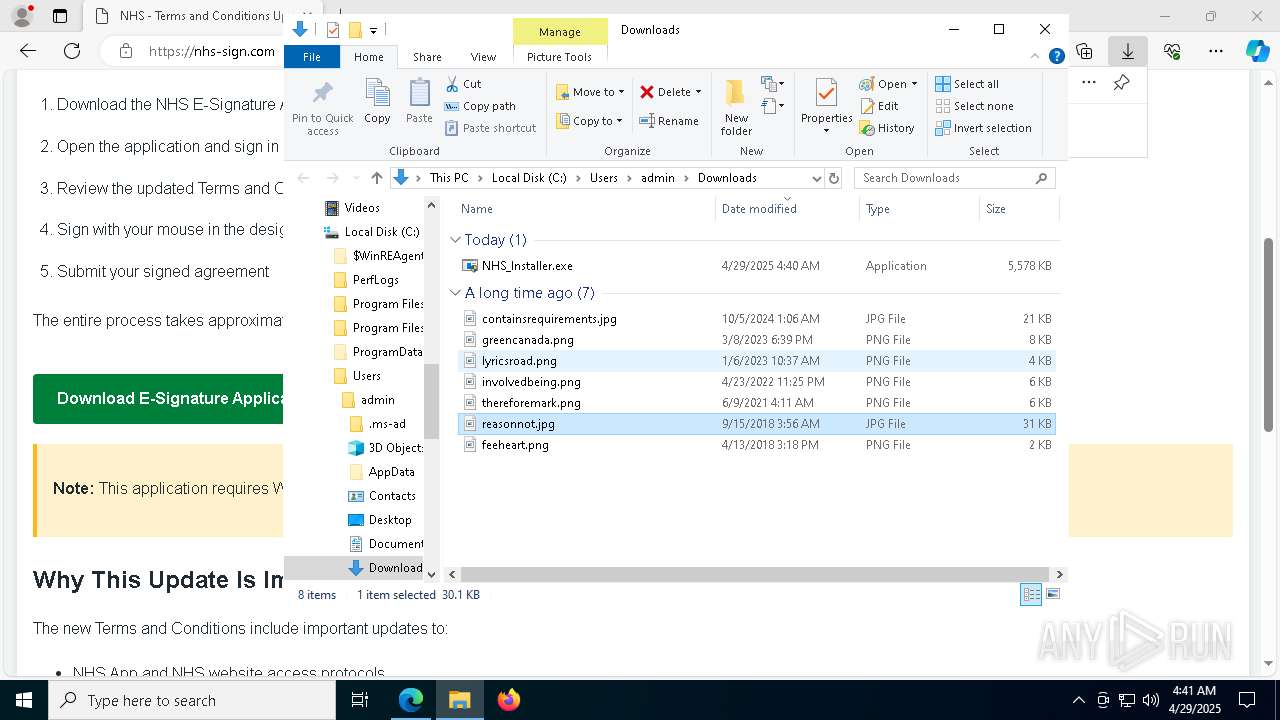
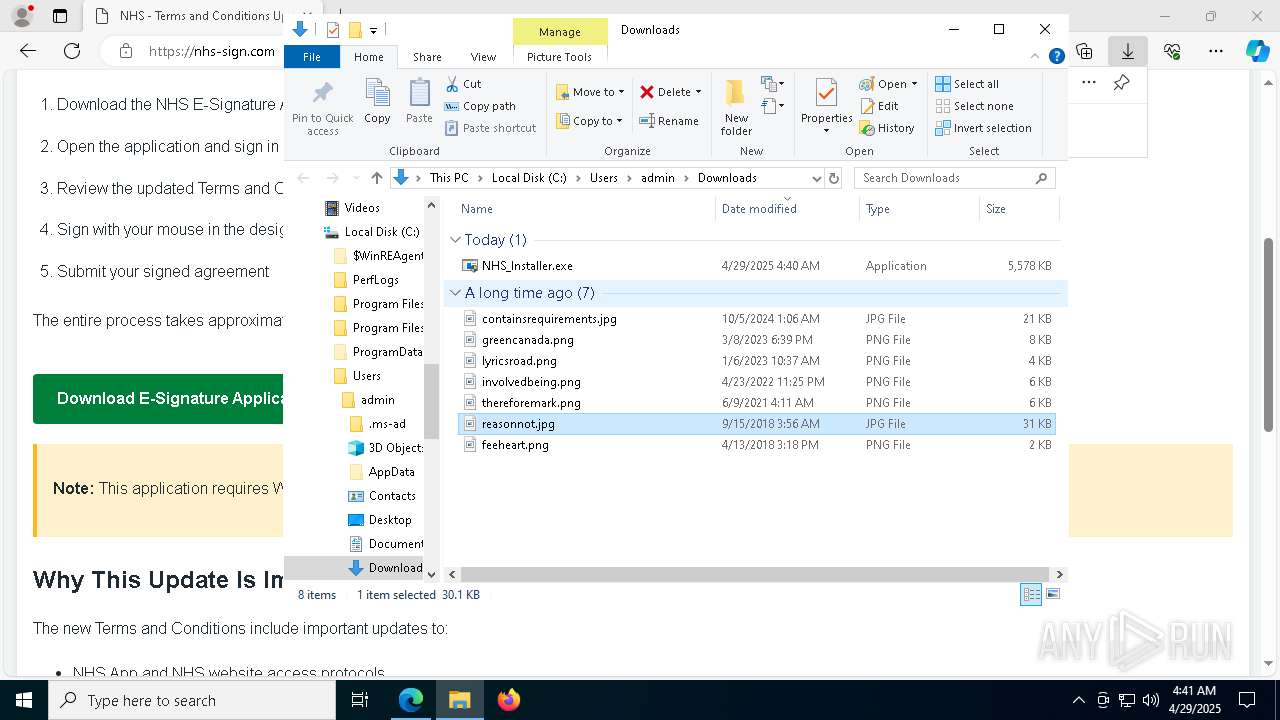
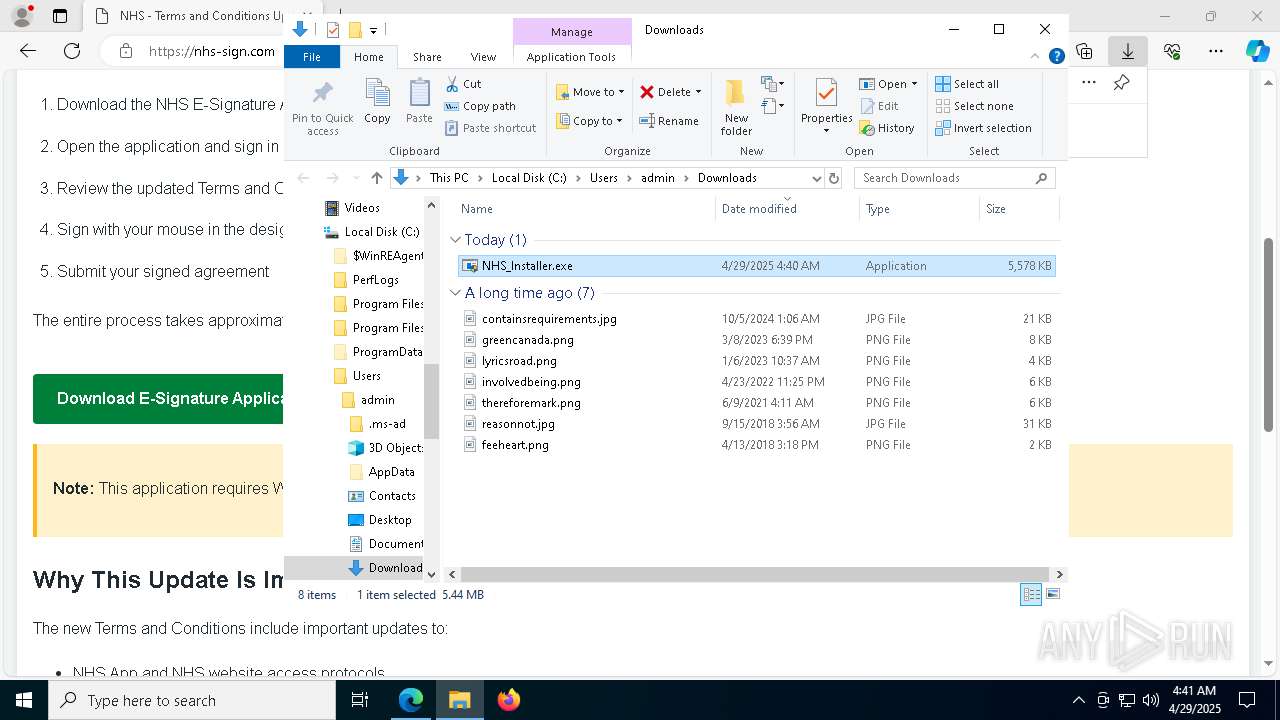
Manual execution by a user
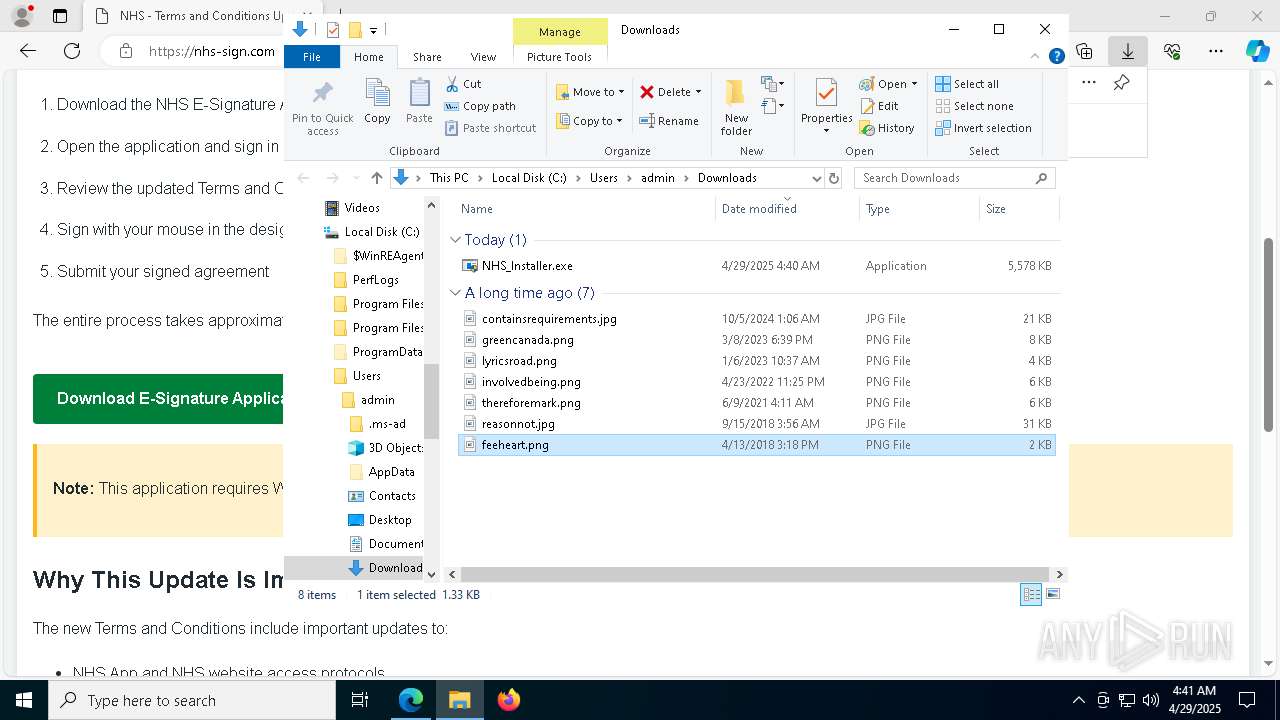
- mspaint.exe (PID: 4012)
- mspaint.exe (PID: 8024)
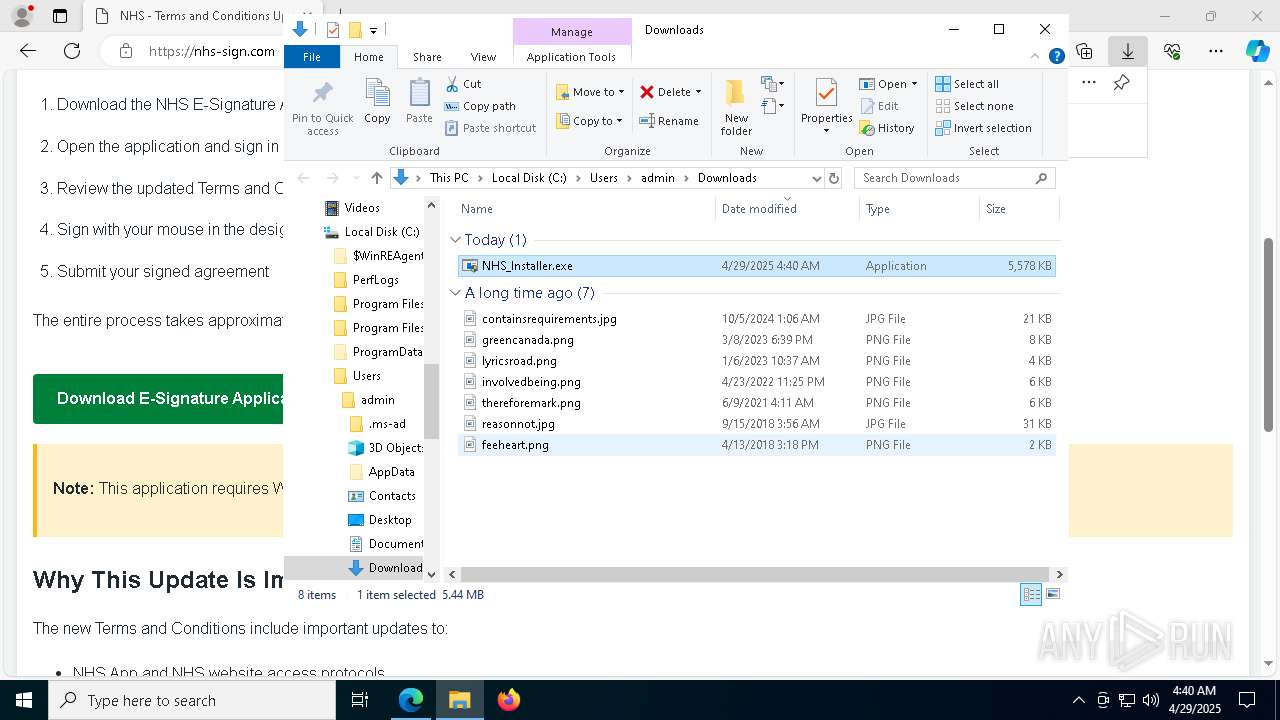
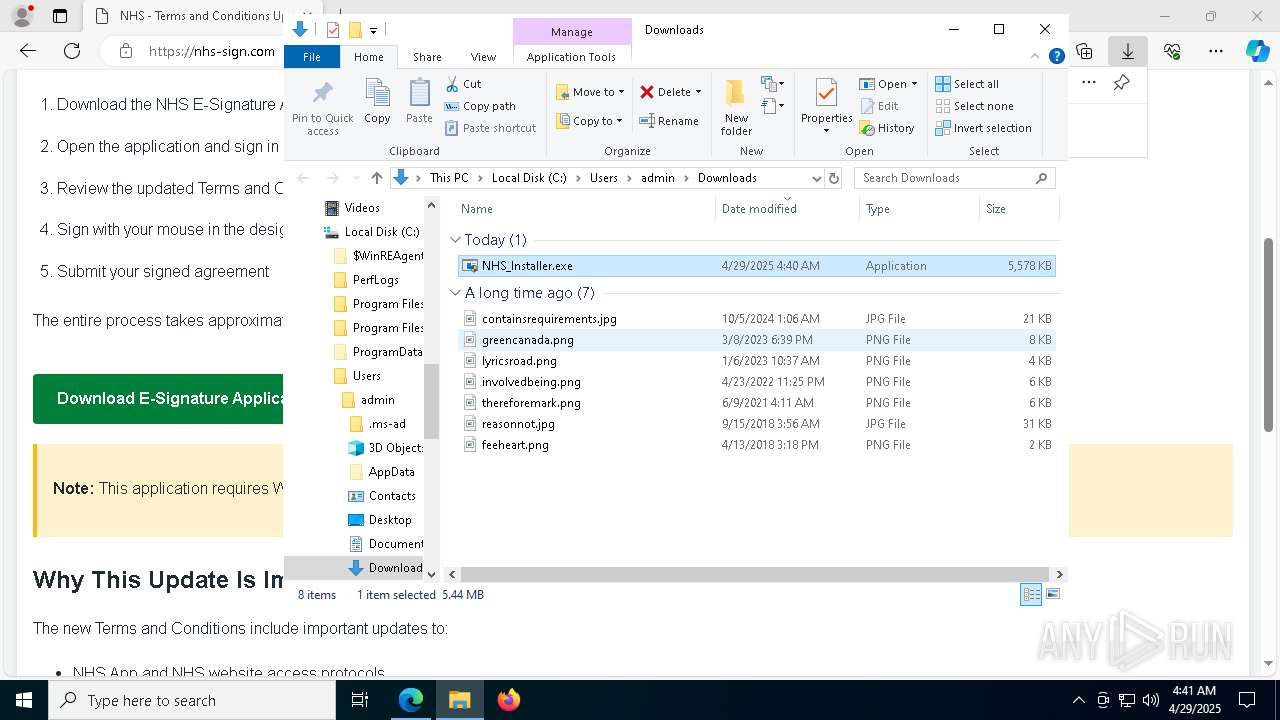
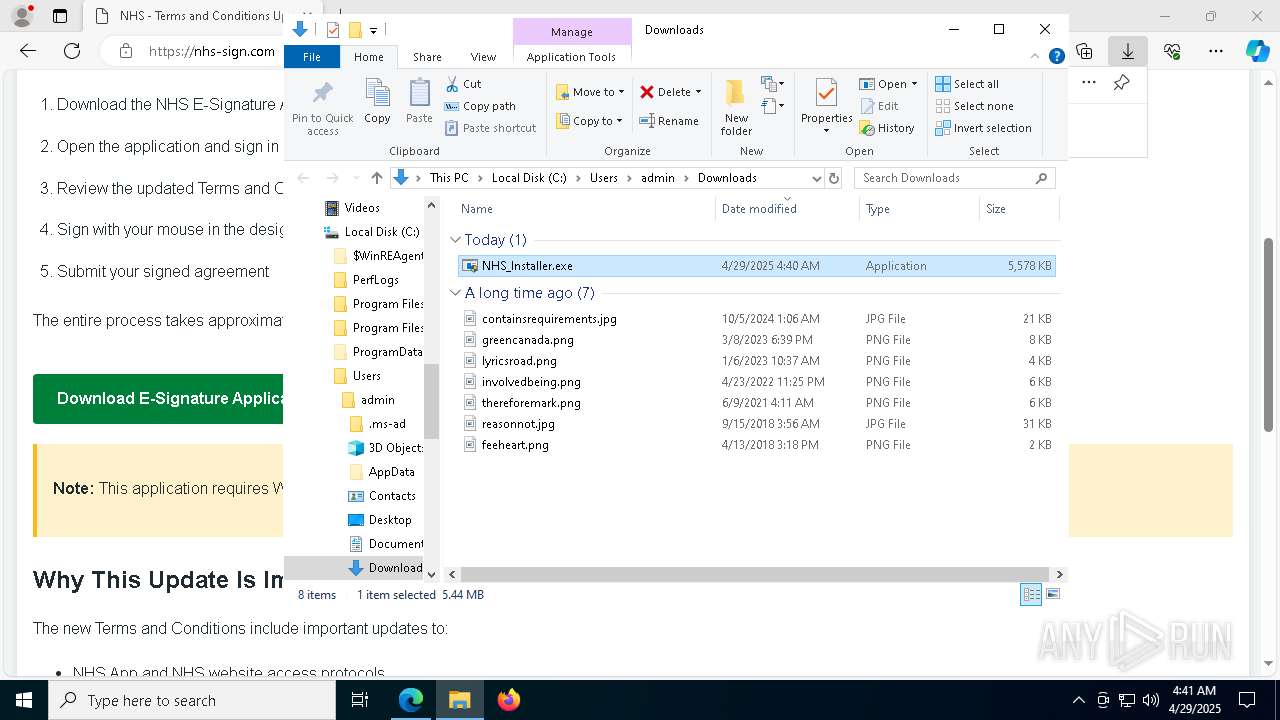
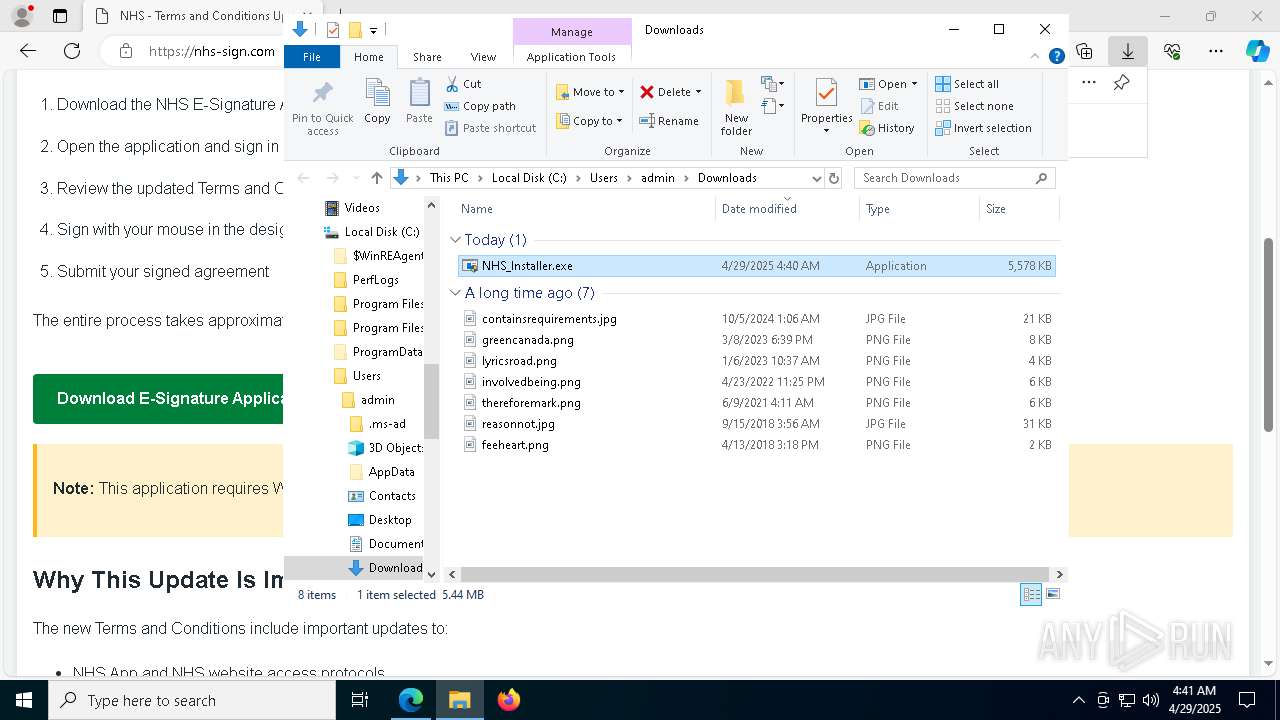
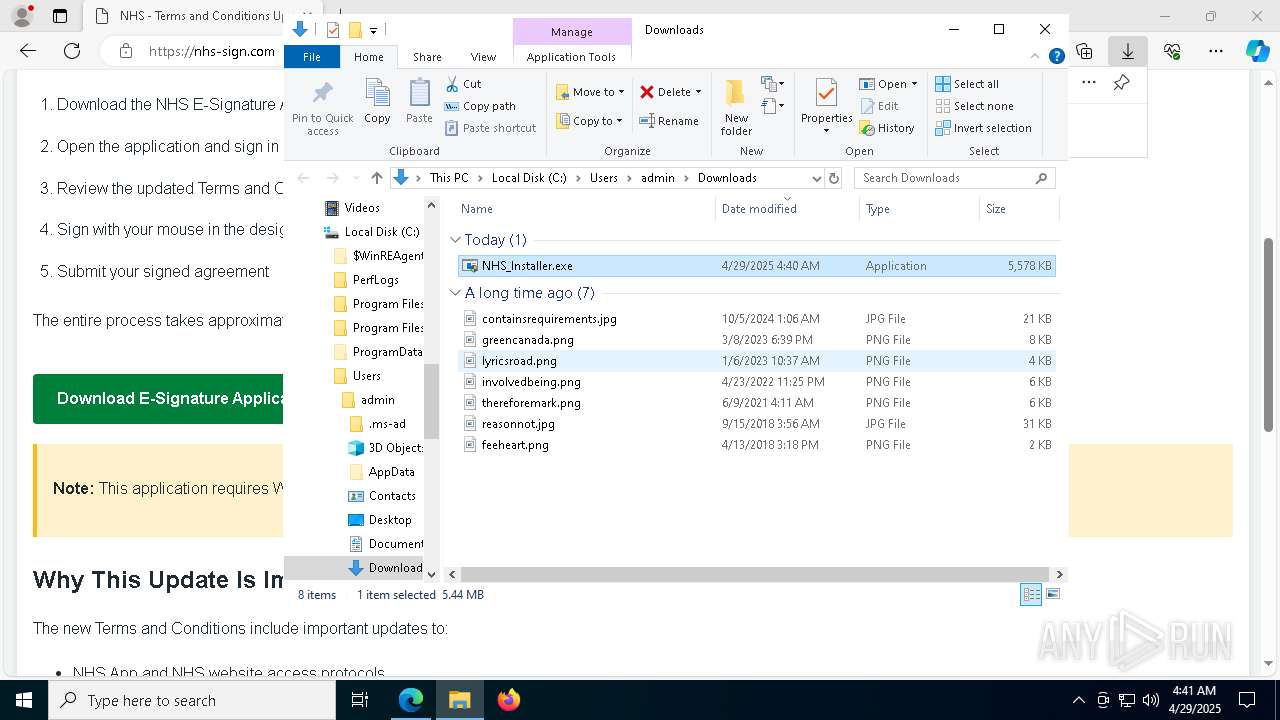
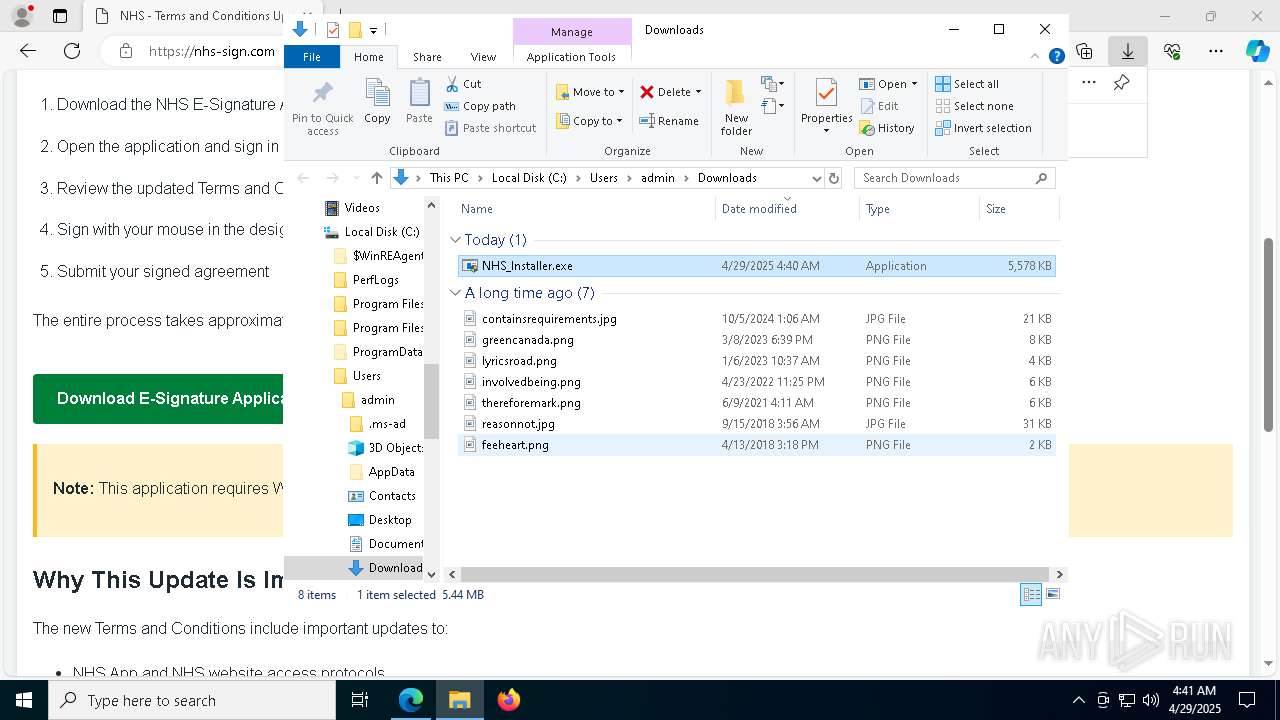
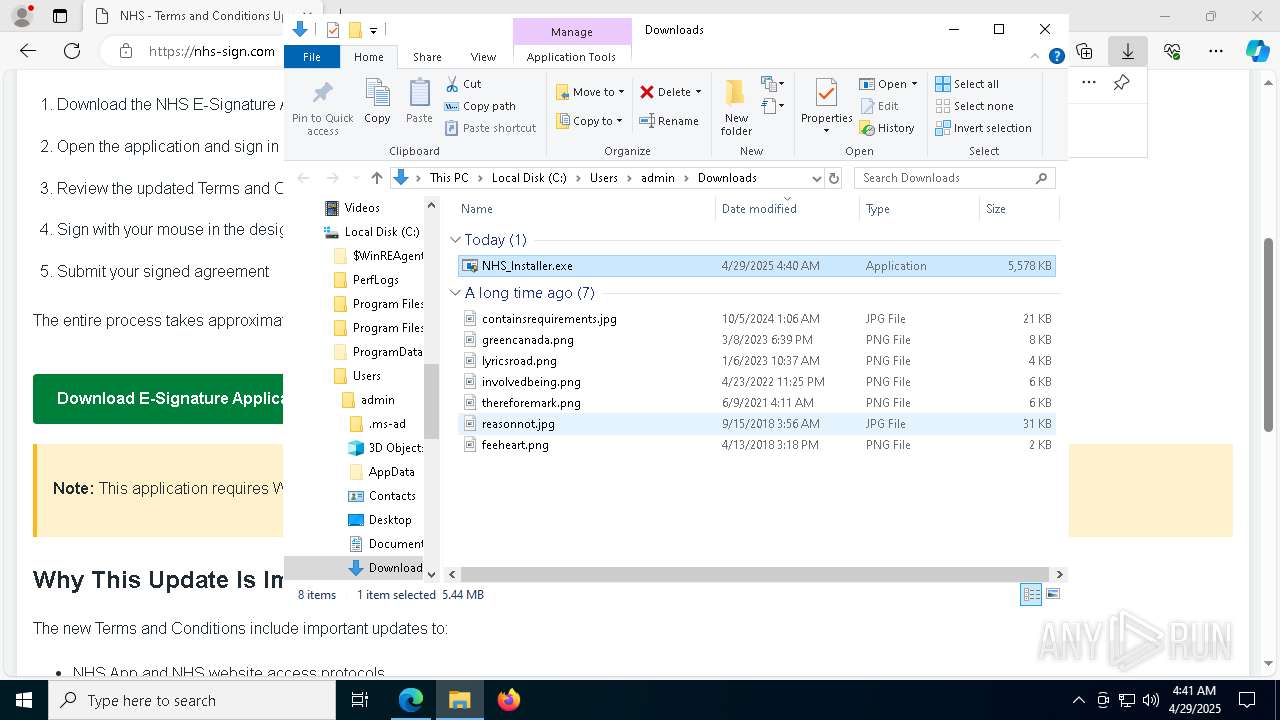
- NHS_Installer.exe (PID: 1328)
- NHS_Installer.exe (PID: 240)
The sample compiled with english language support
- msedge.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
84
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Users\admin\Downloads\NHS_Installer.exe" | C:\Users\admin\Downloads\NHS_Installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://nhs-sign.com" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6700 --field-trial-handle=2384,i,4071811372531940722,1301473478225480709,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\Downloads\NHS_Installer.exe" | C:\Users\admin\Downloads\NHS_Installer.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3762504530 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6628 --field-trial-handle=2384,i,4071811372531940722,1301473478225480709,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI8356.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1148031 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | C:\Windows\syswow64\MsiExec.exe -Embedding 0BDD78467E3E1F18385C39731239A567 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\Downloads\NHS_Installer.exe" | C:\Users\admin\Downloads\NHS_Installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6652 --field-trial-handle=2384,i,4071811372531940722,1301473478225480709,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 876
Read events
20 446
Write events
391
Delete events
39
Modification events
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DA646BAC79922F00 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A33A83AC79922F00 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197384 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E112EA6F-9A98-444D-8456-FEB40E96F4B8} | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197384 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9E6F86FA-EEB3-47A0-885E-D0A8AB93D1D9} | |||
| (PID) Process: | (660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197384 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {571B16D8-0FBD-4FA0-85C6-D04A894221E6} | |||
Executable files
45
Suspicious files
354
Text files
61
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b9eb.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b9eb.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b9fb.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ba0b.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba0b.TMP | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
72
DNS requests
75
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8028 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746054376&P2=404&P3=2&P4=KrDkfzGnfmG6q24BAt6DO87hhYXGOlSgS3ZvY9JQP9pPTLvbeUygU%2fRXHCz2VgWEVleQI3ldPCBuAlZyCDdYLQ%3d%3d | unknown | — | — | whitelisted |
5800 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8028 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746054376&P2=404&P3=2&P4=KrDkfzGnfmG6q24BAt6DO87hhYXGOlSgS3ZvY9JQP9pPTLvbeUygU%2fRXHCz2VgWEVleQI3ldPCBuAlZyCDdYLQ%3d%3d | unknown | — | — | whitelisted |
5800 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8028 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1746054377&P2=404&P3=2&P4=g9Z2ugGbUvvN2yjLNaSua9rTNw6ab9ZAjuMKqpxrPxROSfVFOg6NYaDe%2bgYCKFqUvpGcDbTqZ17Nag7iULsqoQ%3d%3d | unknown | — | — | whitelisted |
8028 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746054376&P2=404&P3=2&P4=KrDkfzGnfmG6q24BAt6DO87hhYXGOlSgS3ZvY9JQP9pPTLvbeUygU%2fRXHCz2VgWEVleQI3ldPCBuAlZyCDdYLQ%3d%3d | unknown | — | — | whitelisted |
8028 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1746054377&P2=404&P3=2&P4=g9Z2ugGbUvvN2yjLNaSua9rTNw6ab9ZAjuMKqpxrPxROSfVFOg6NYaDe%2bgYCKFqUvpGcDbTqZ17Nag7iULsqoQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
660 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7236 | msedge.exe | 35.190.80.1:443 | a.nel.cloudflare.com | — | — | whitelisted |
7236 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7236 | msedge.exe | 172.67.73.236:443 | nhs-sign.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
nhs-sign.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7236 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7236 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7236 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7236 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
1804 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |