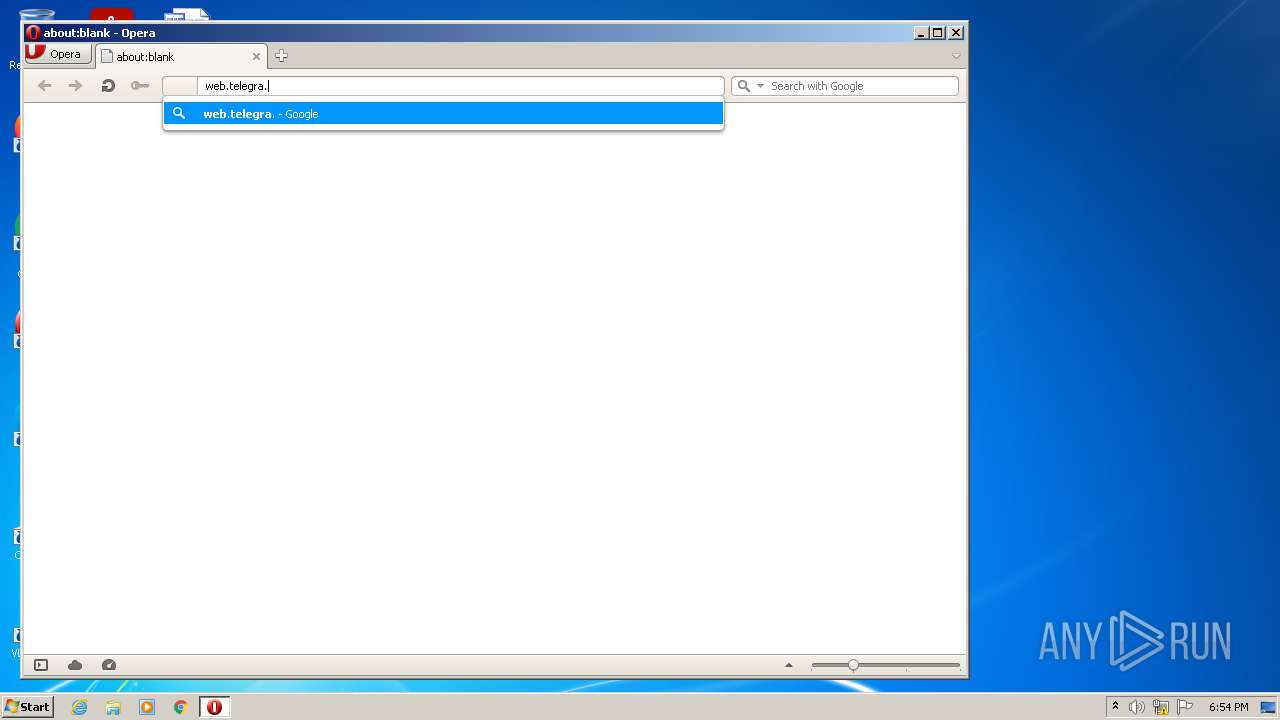
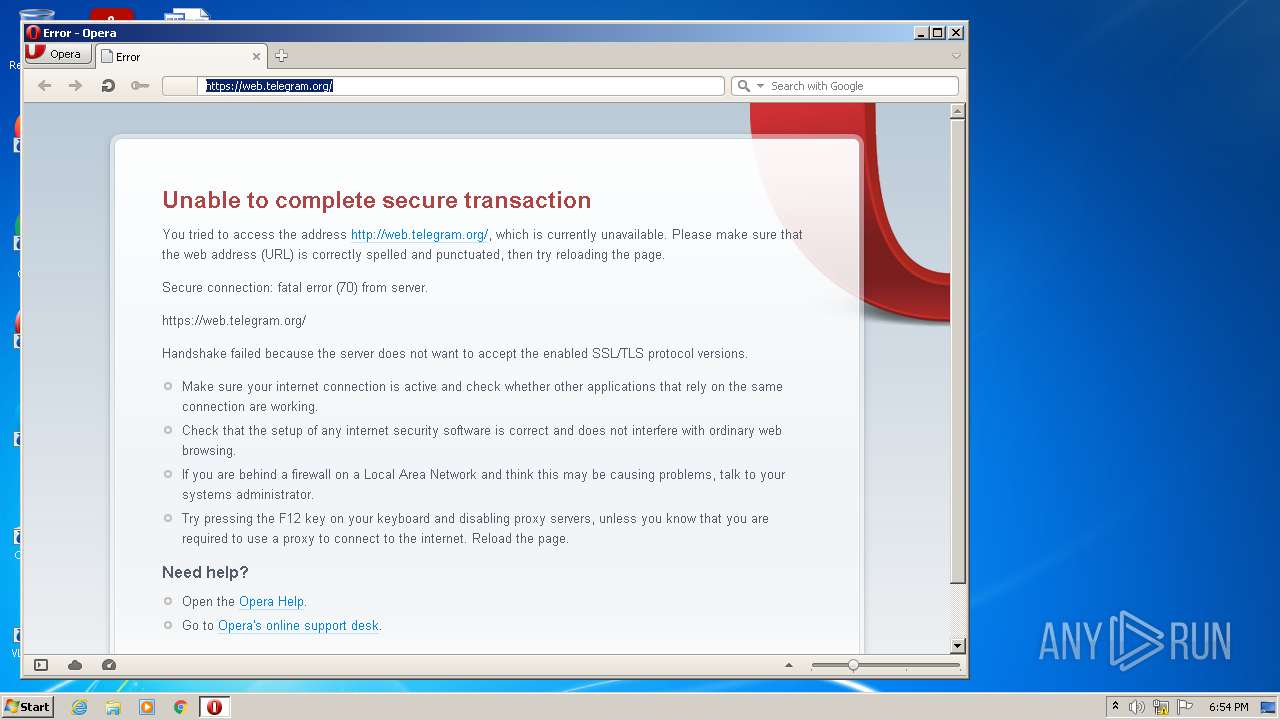
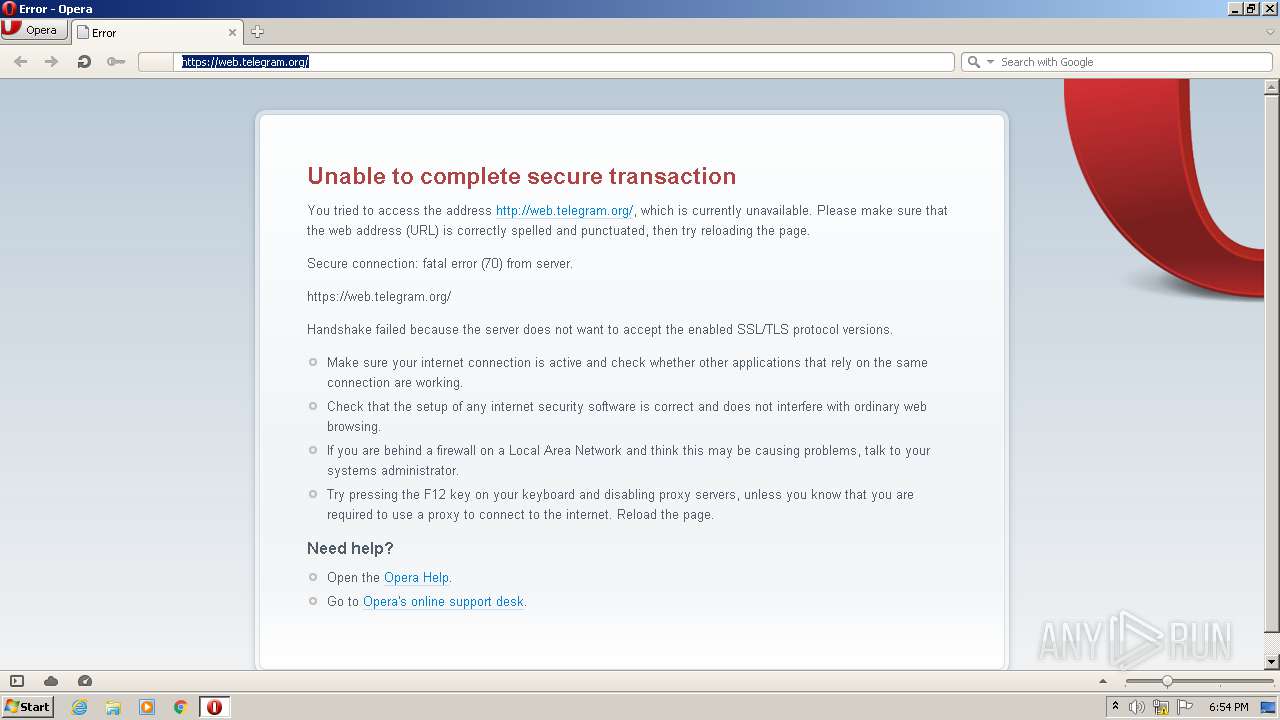
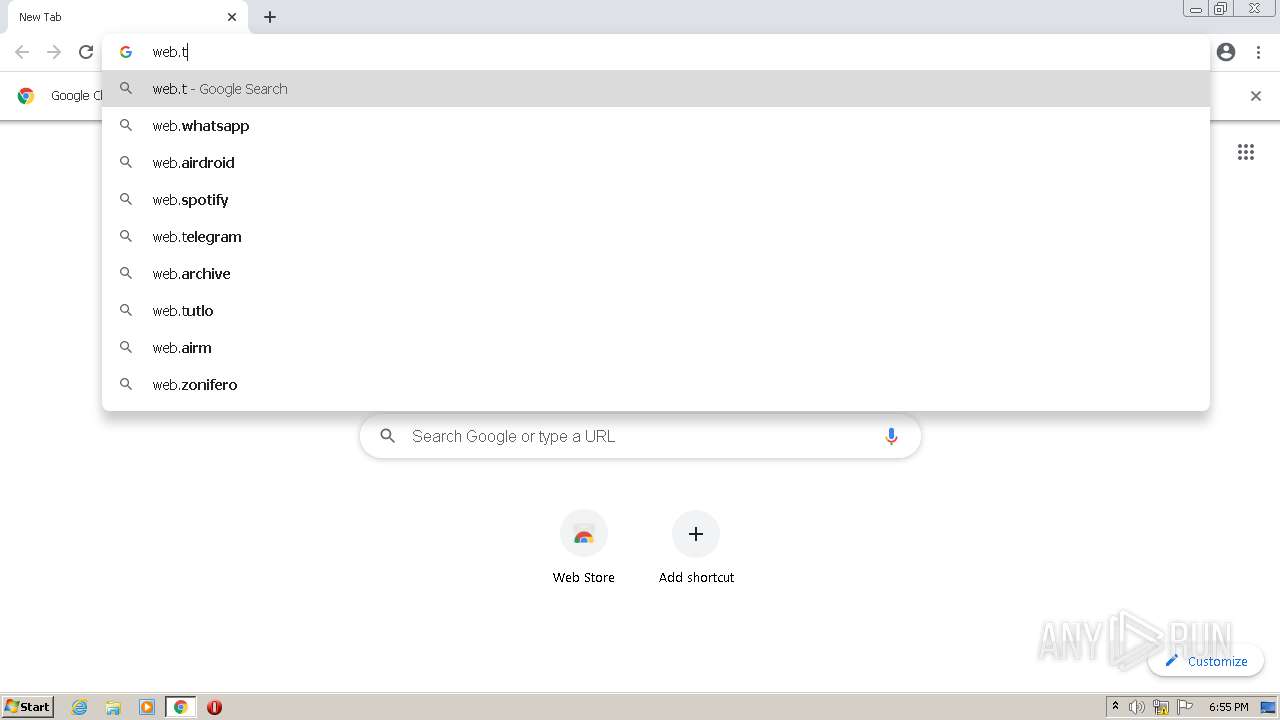
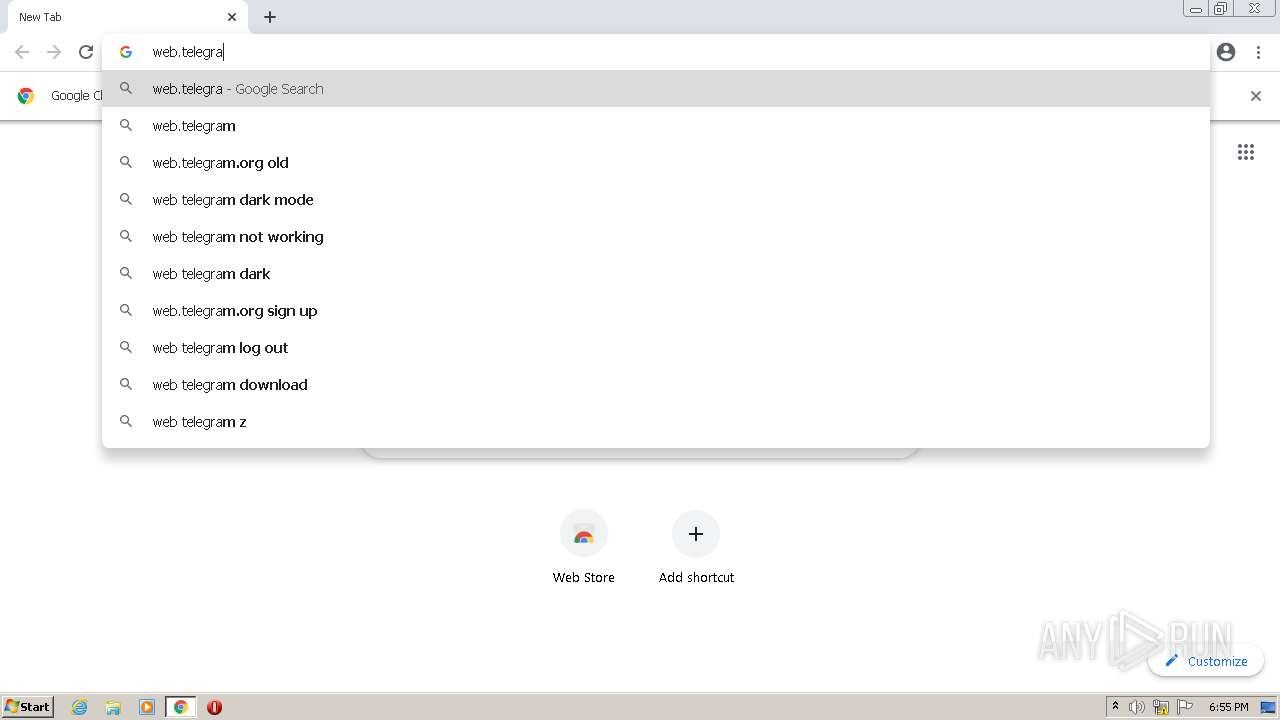
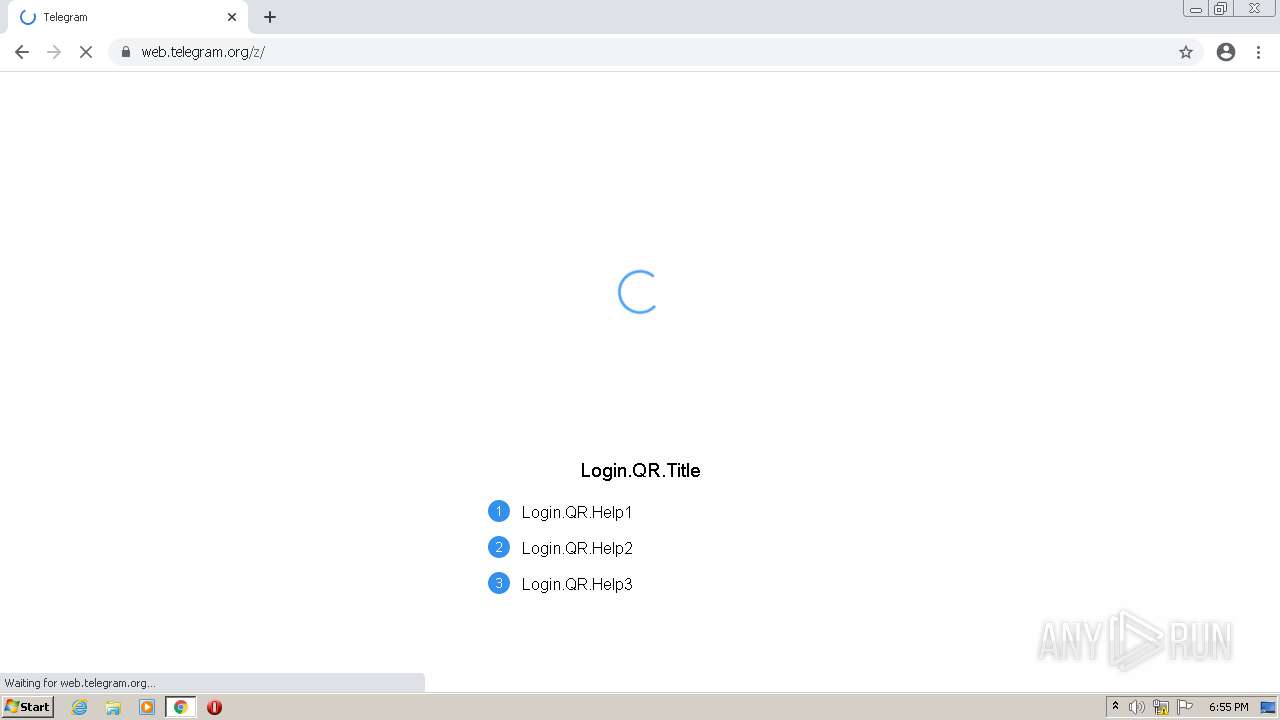
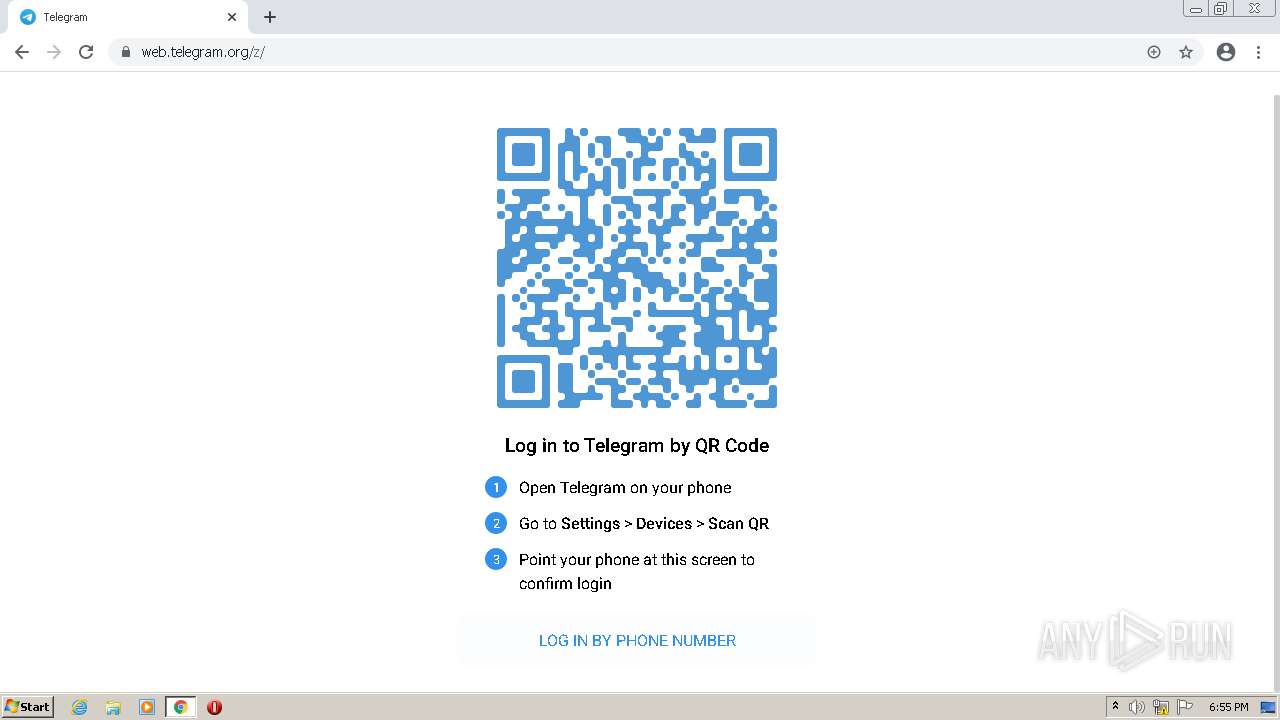
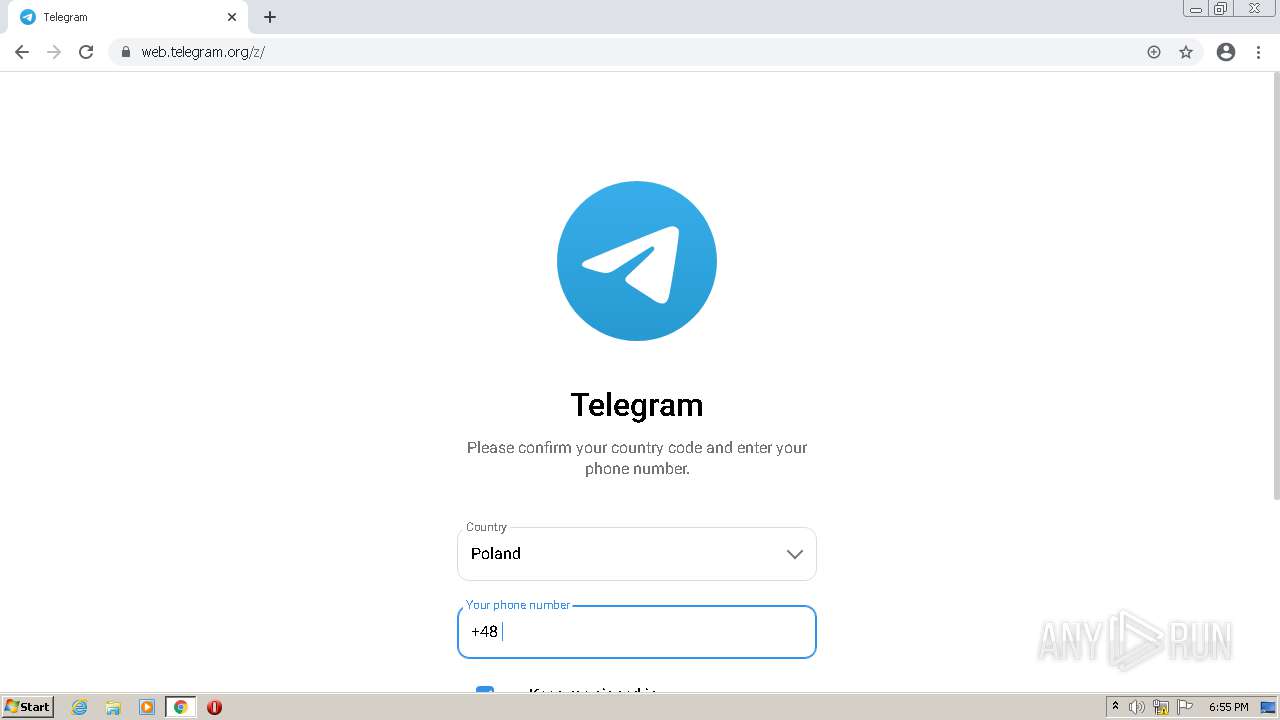
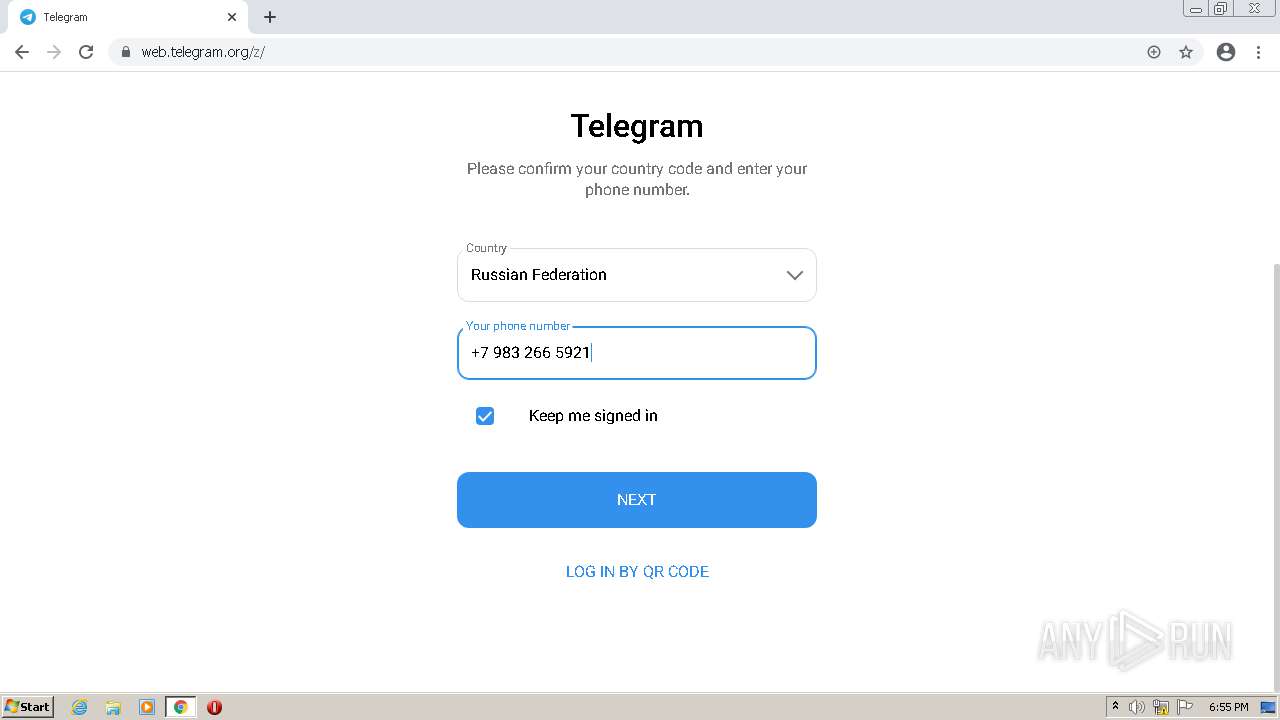
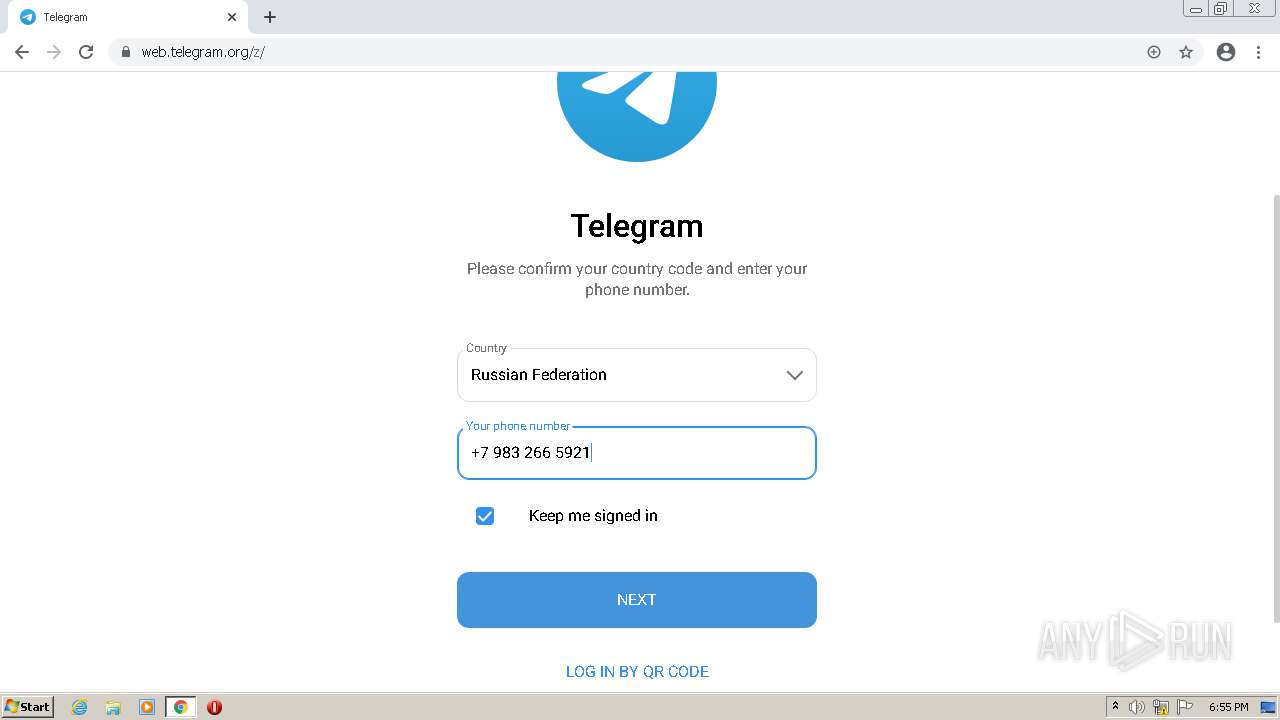
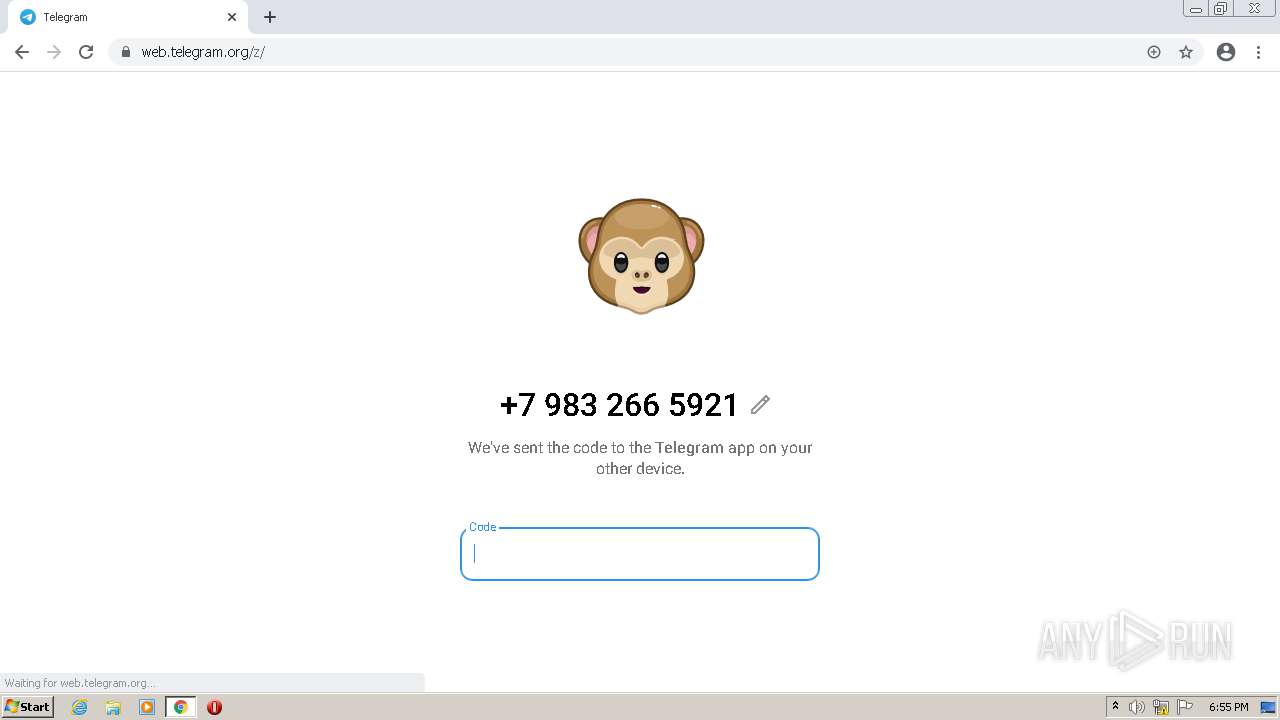
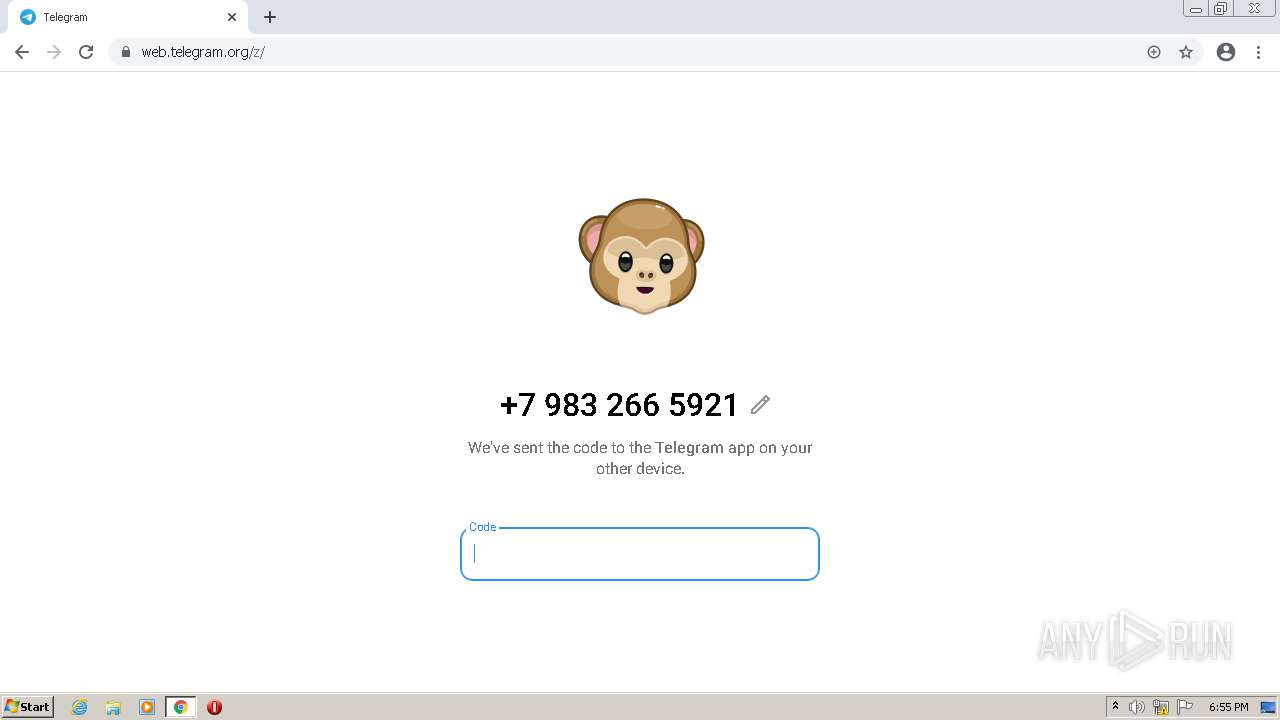
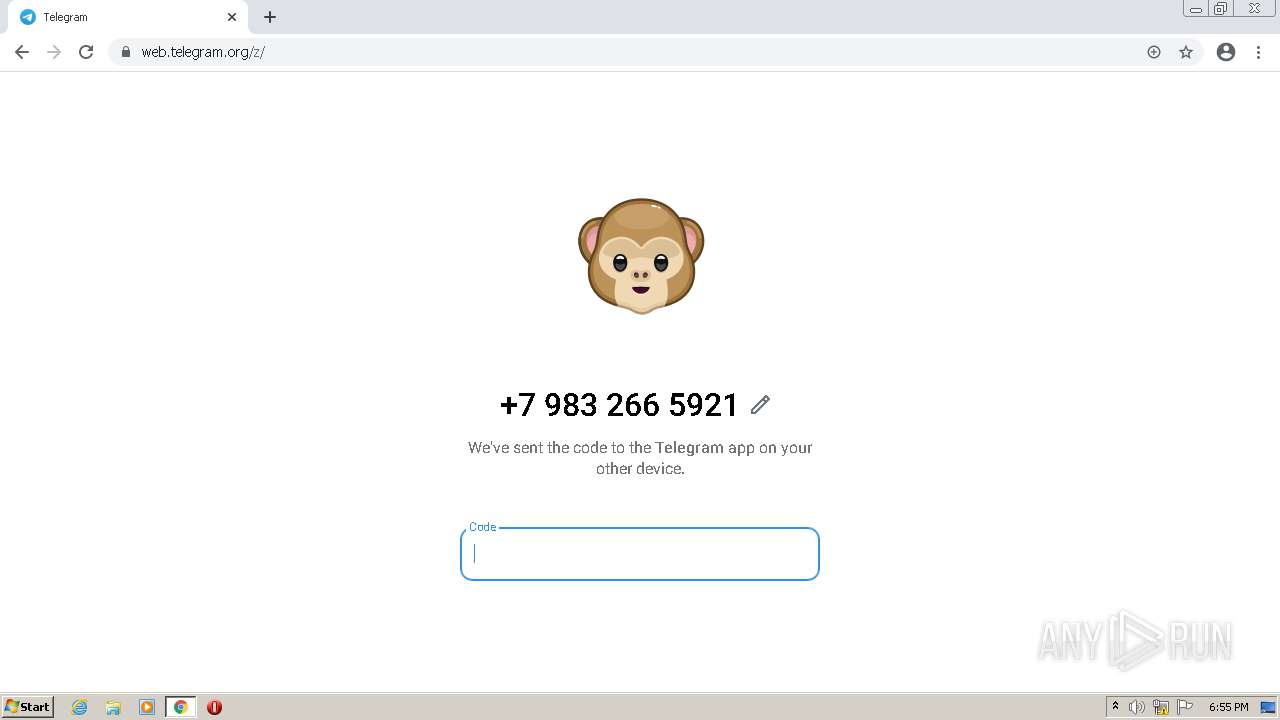
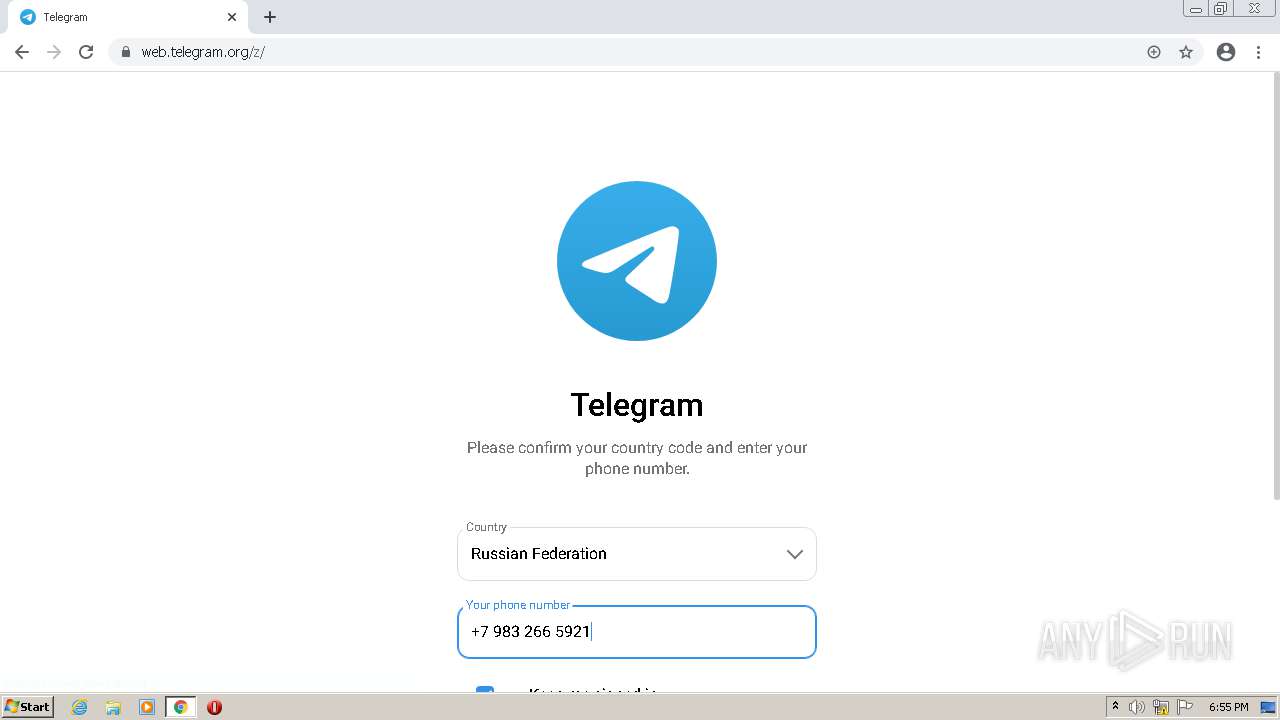
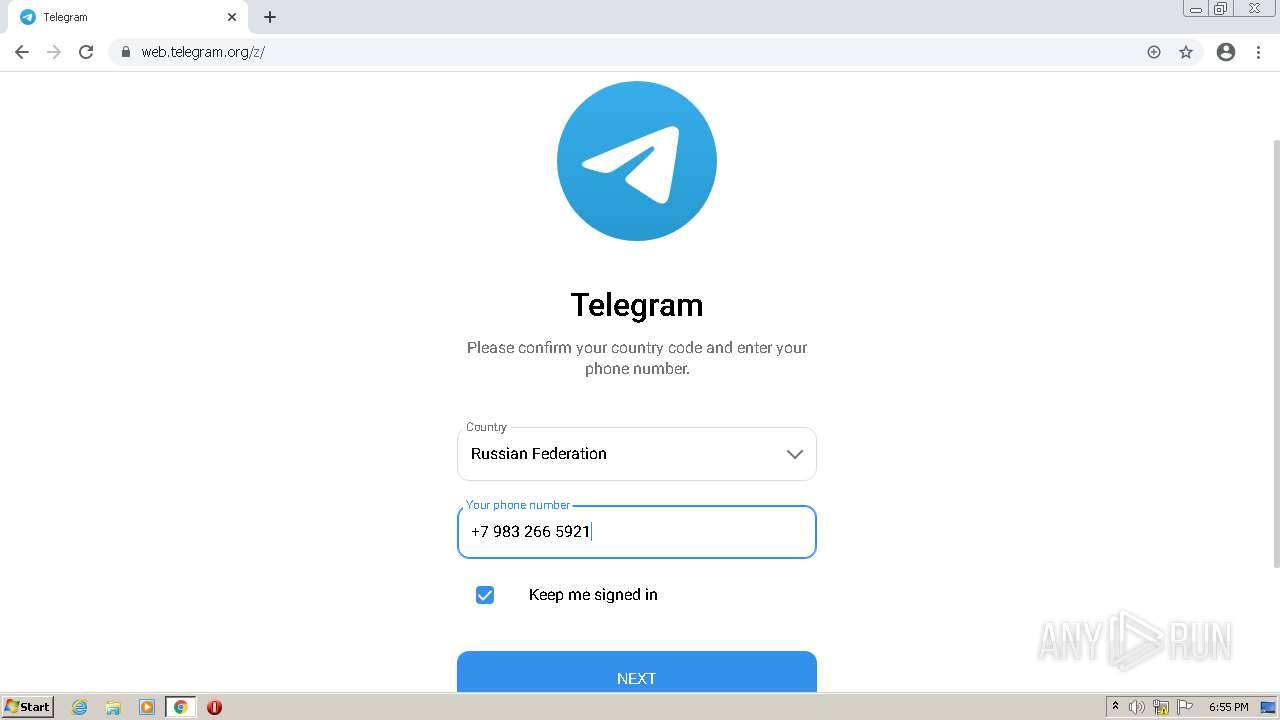
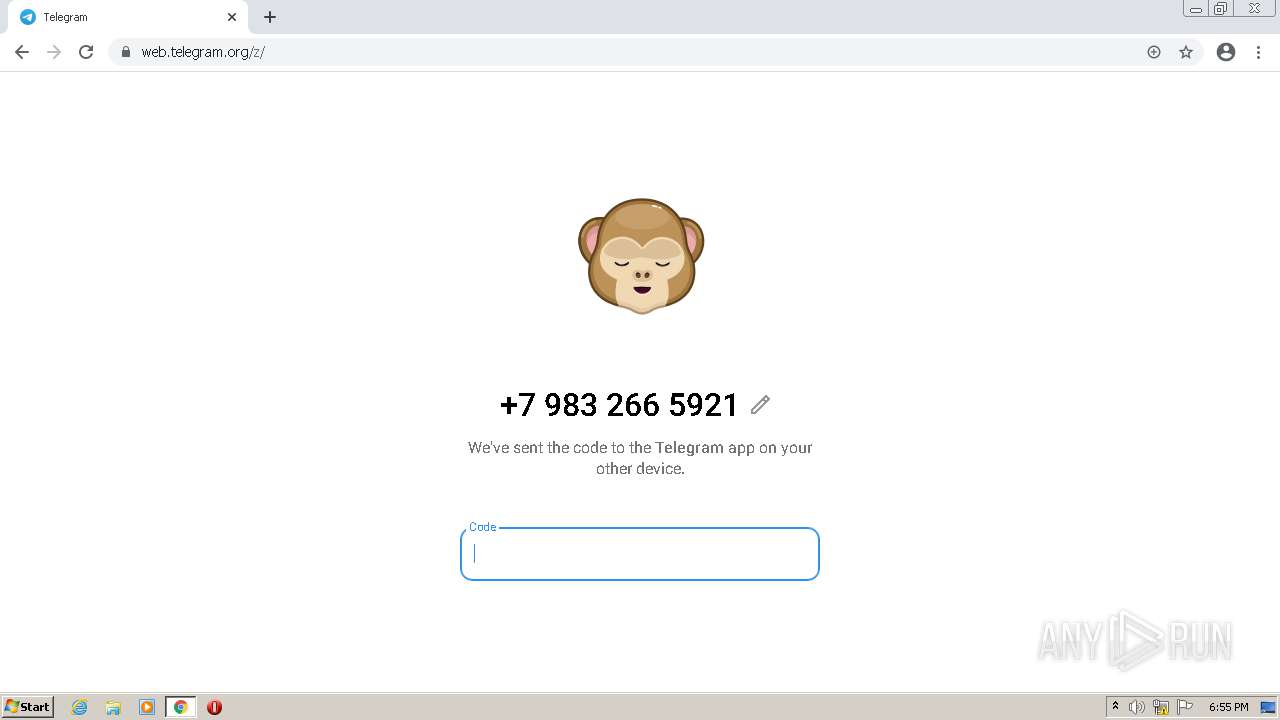
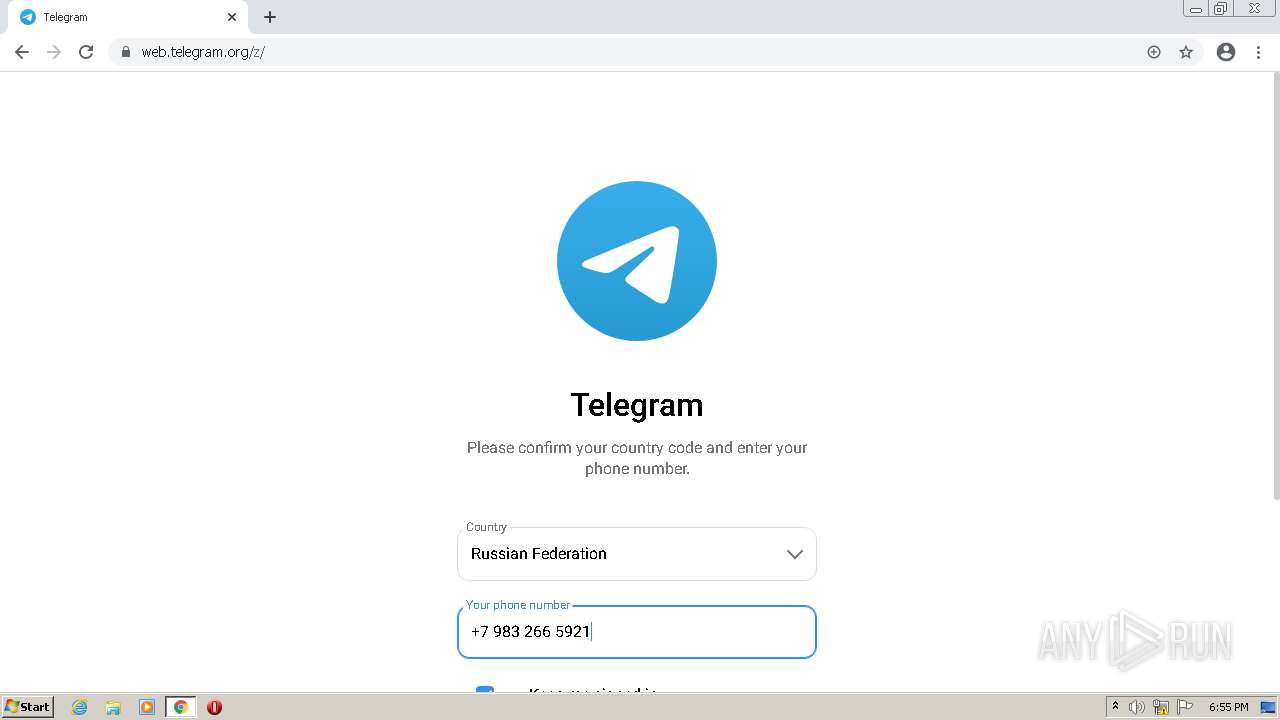
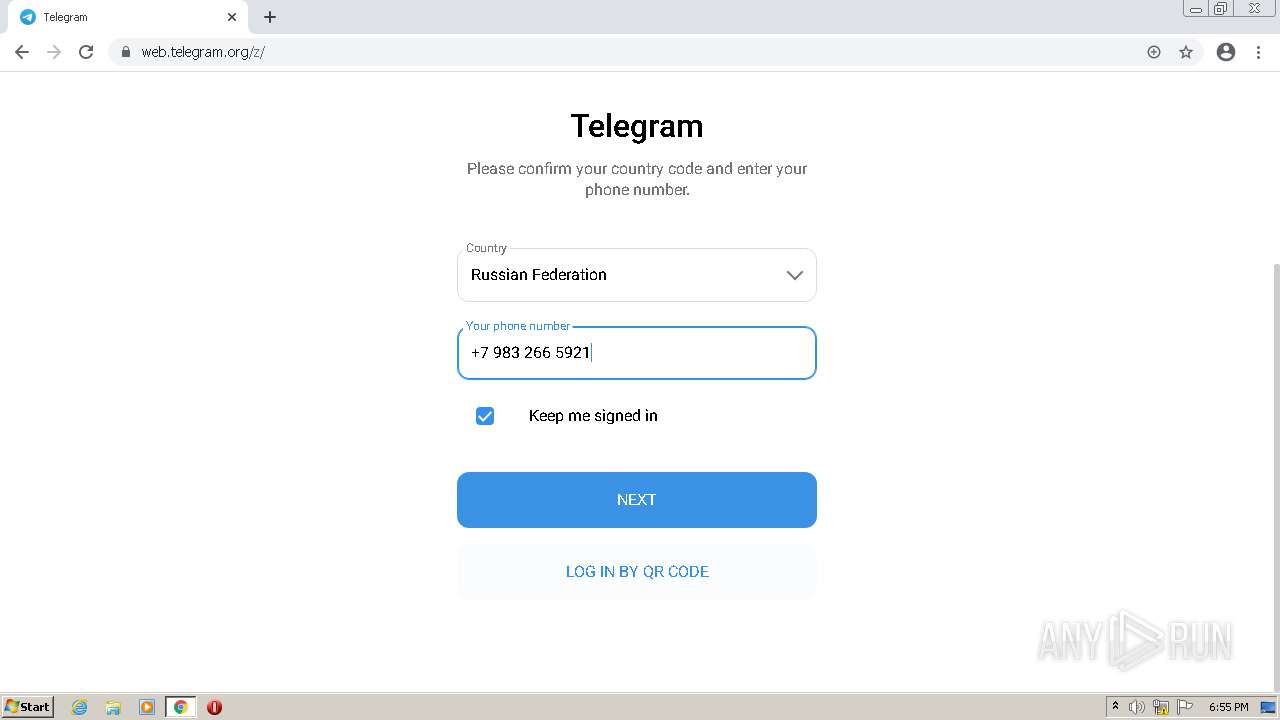
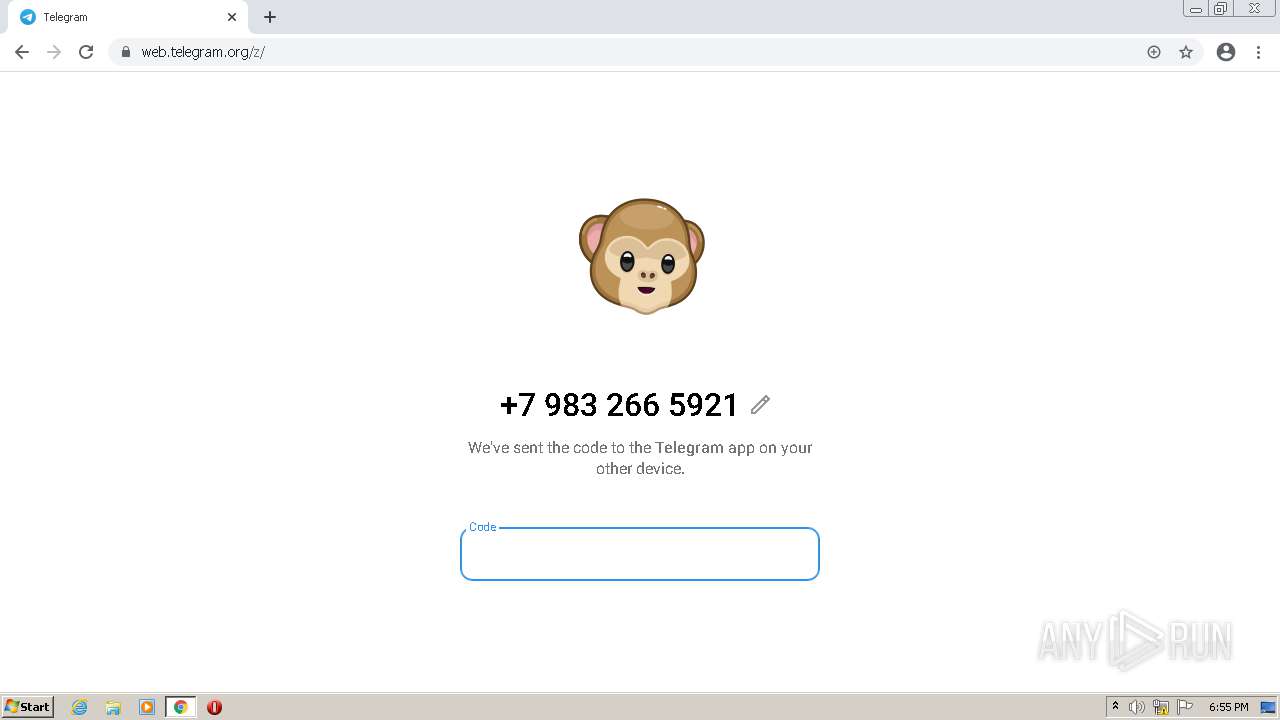
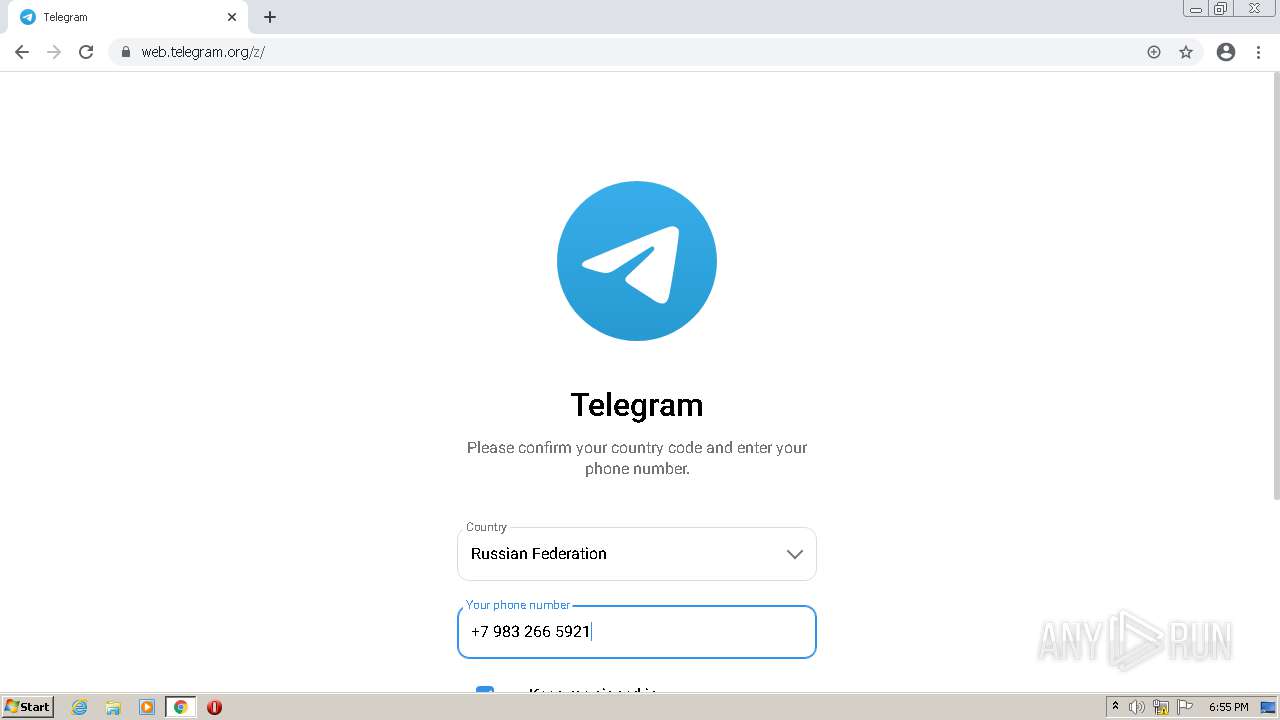
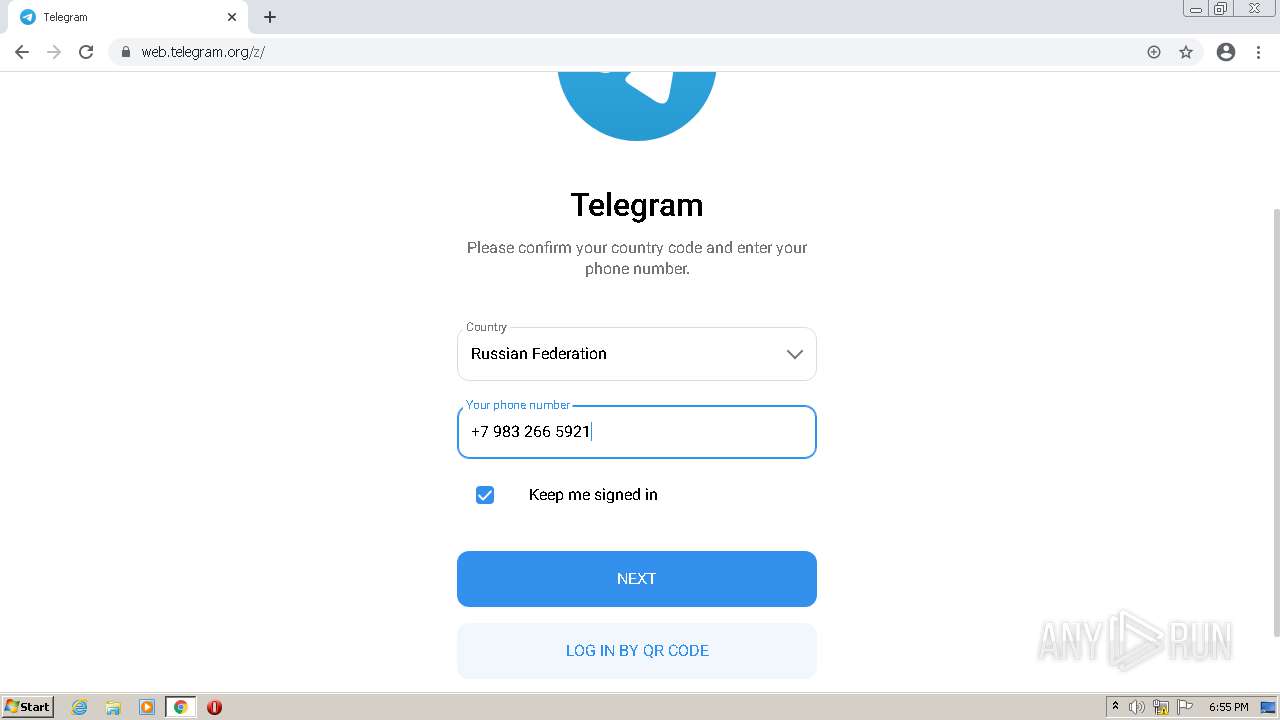
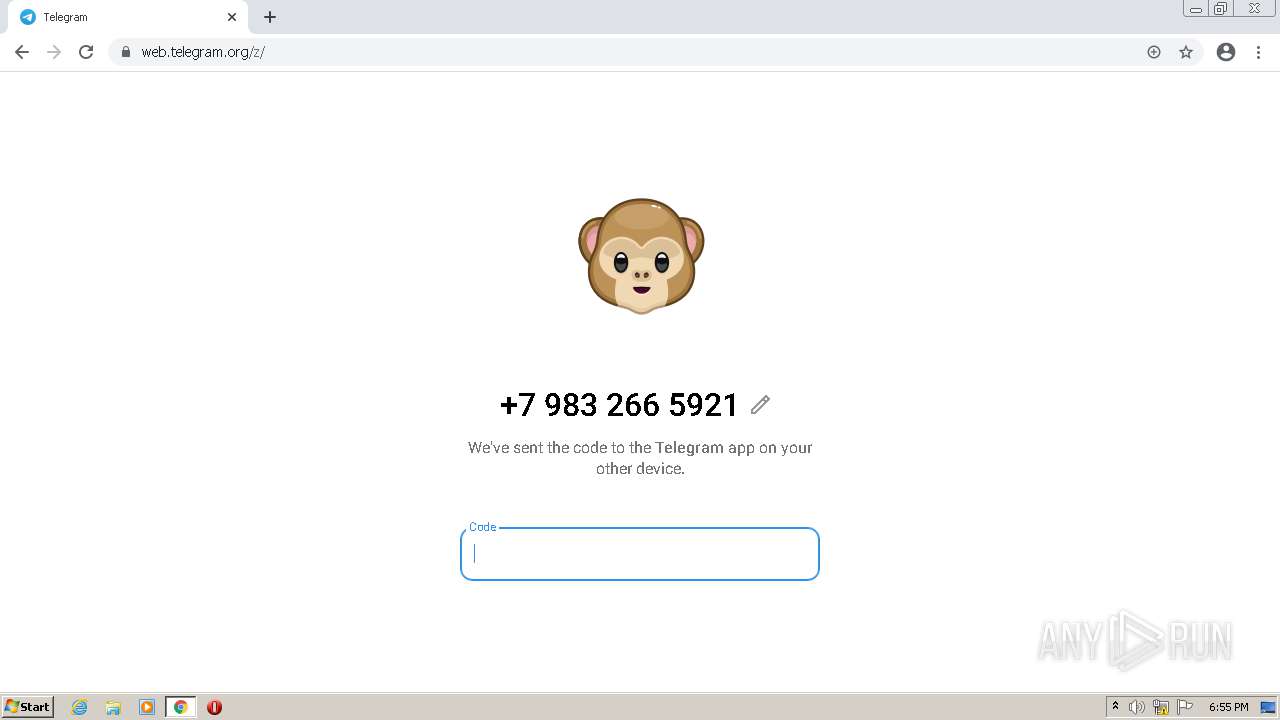
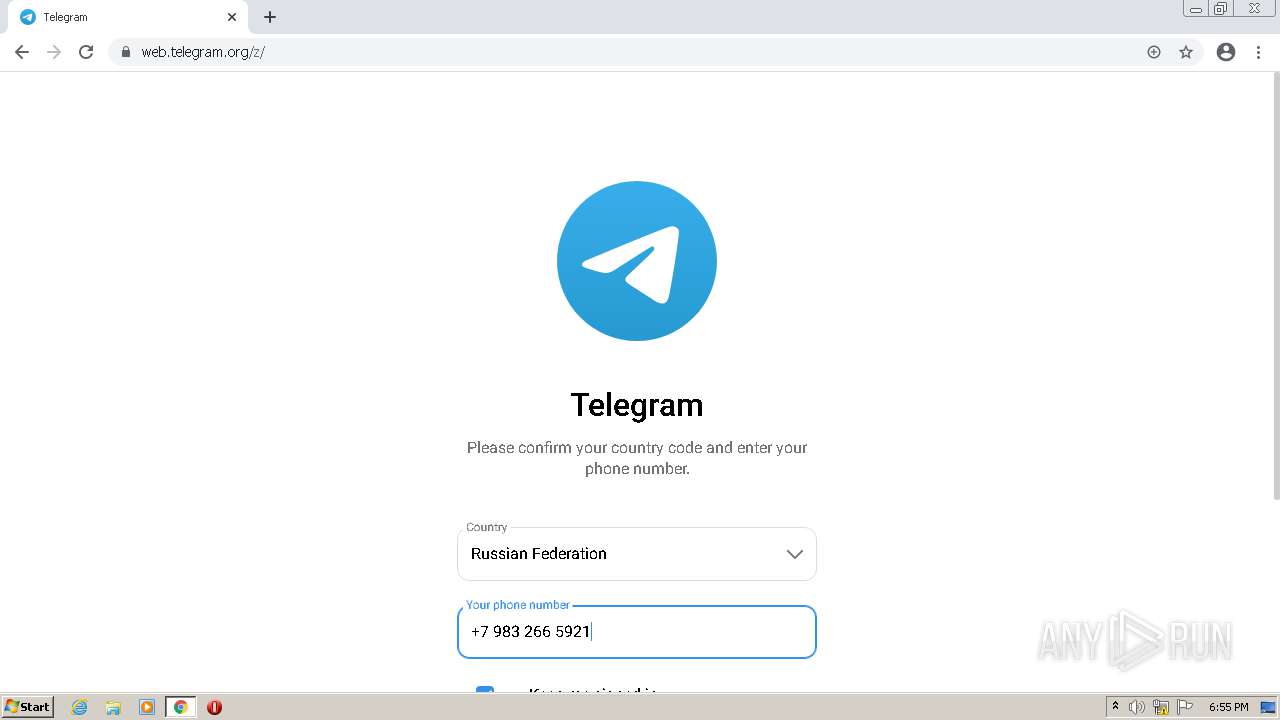
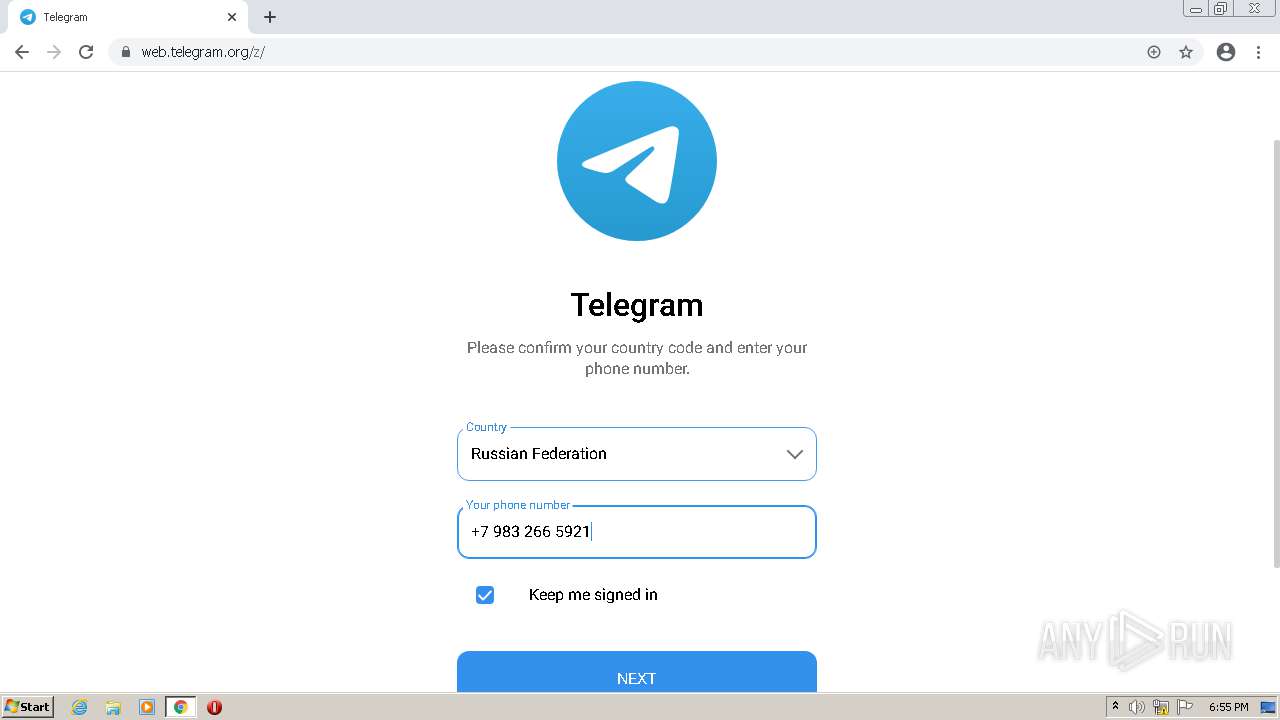
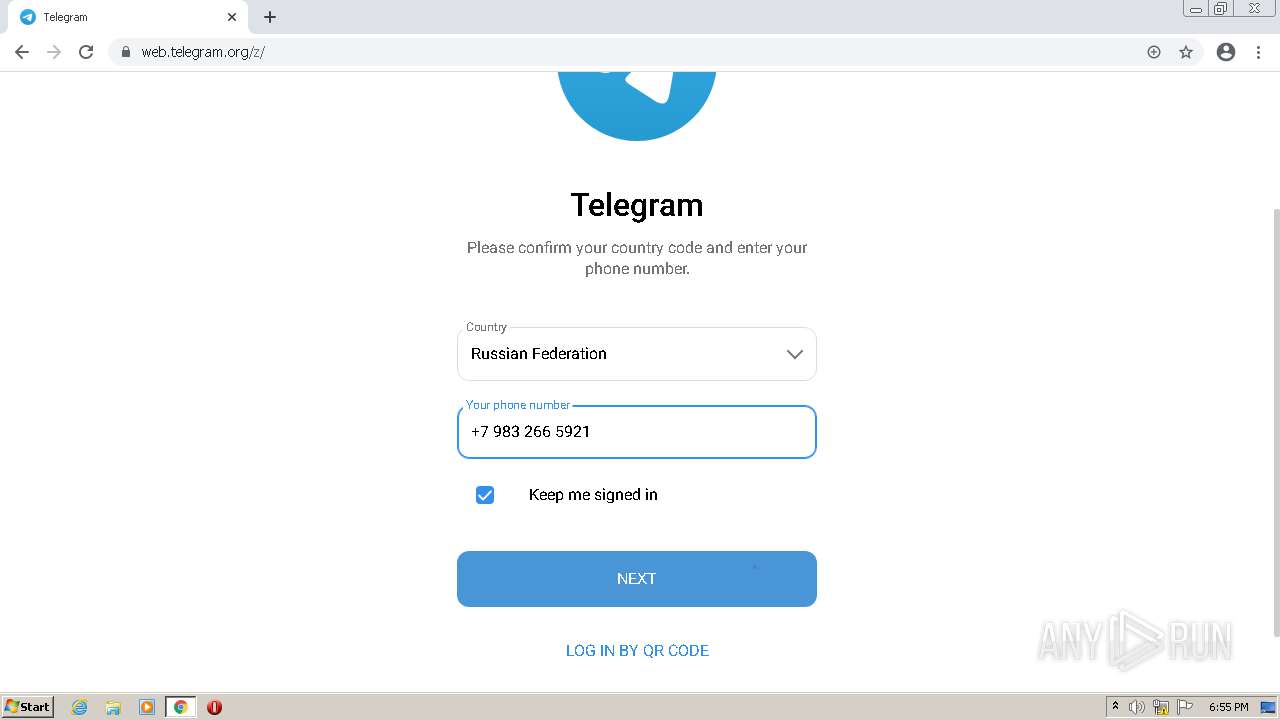
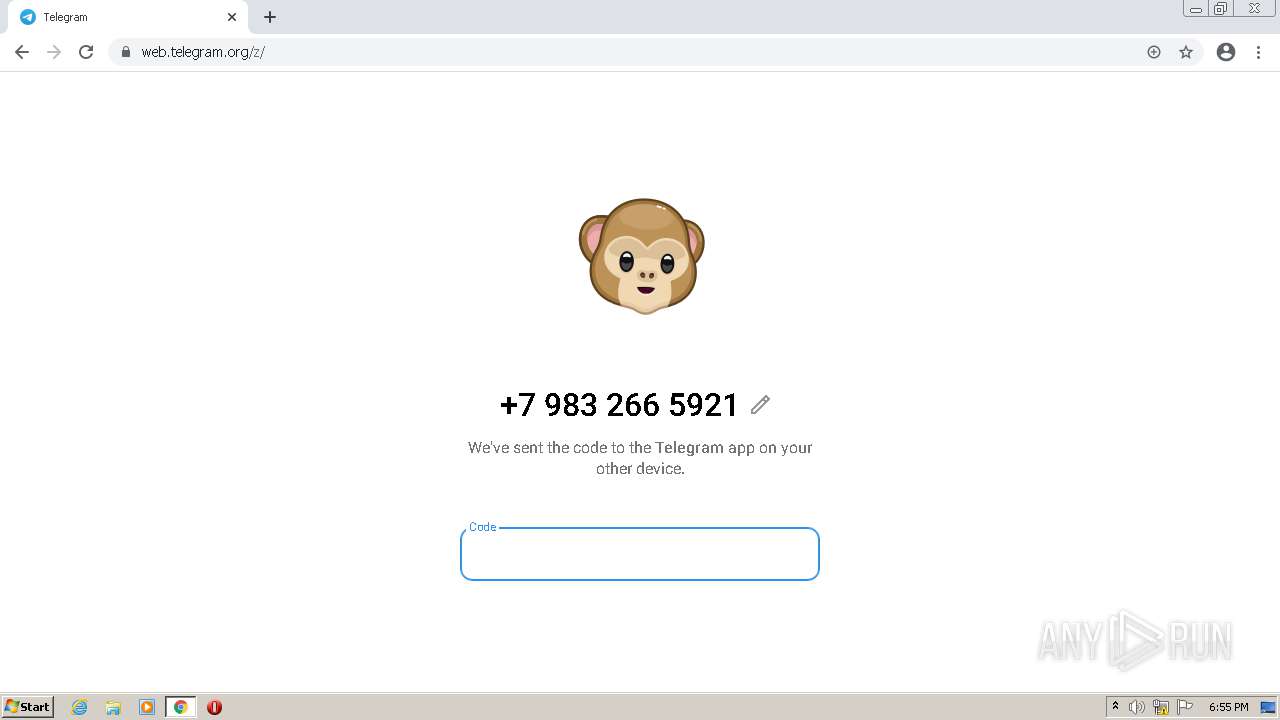
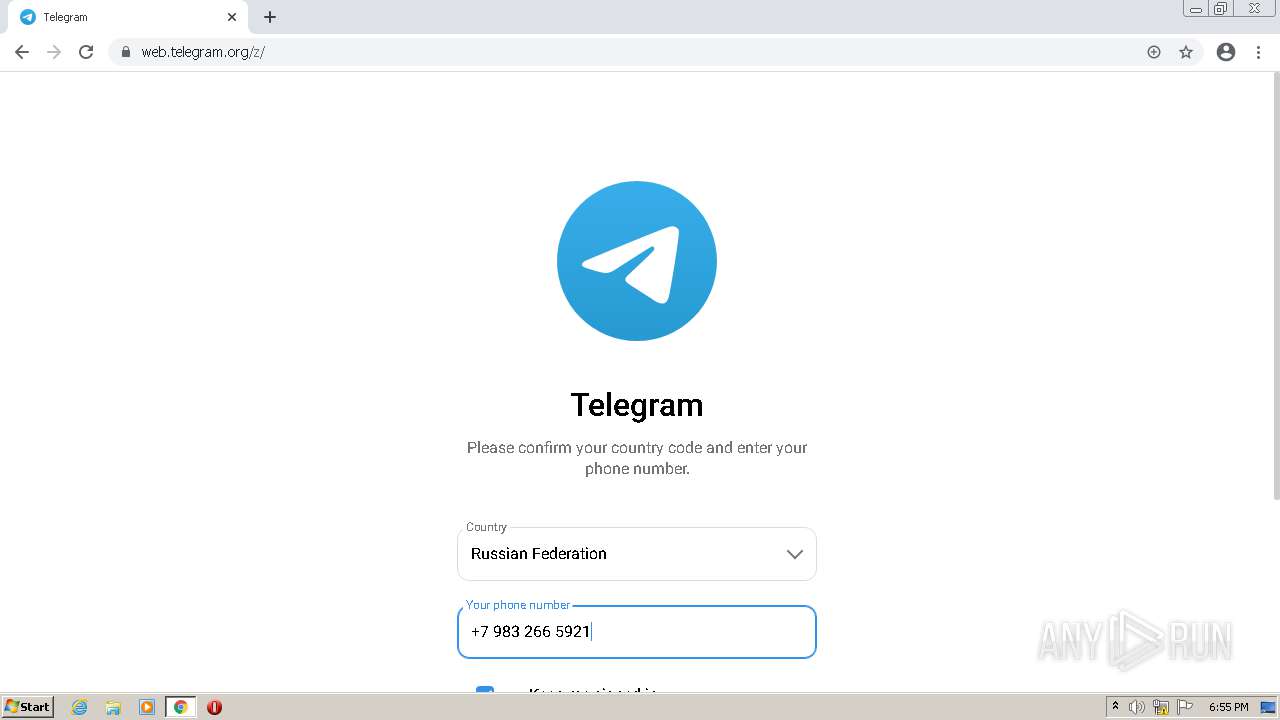
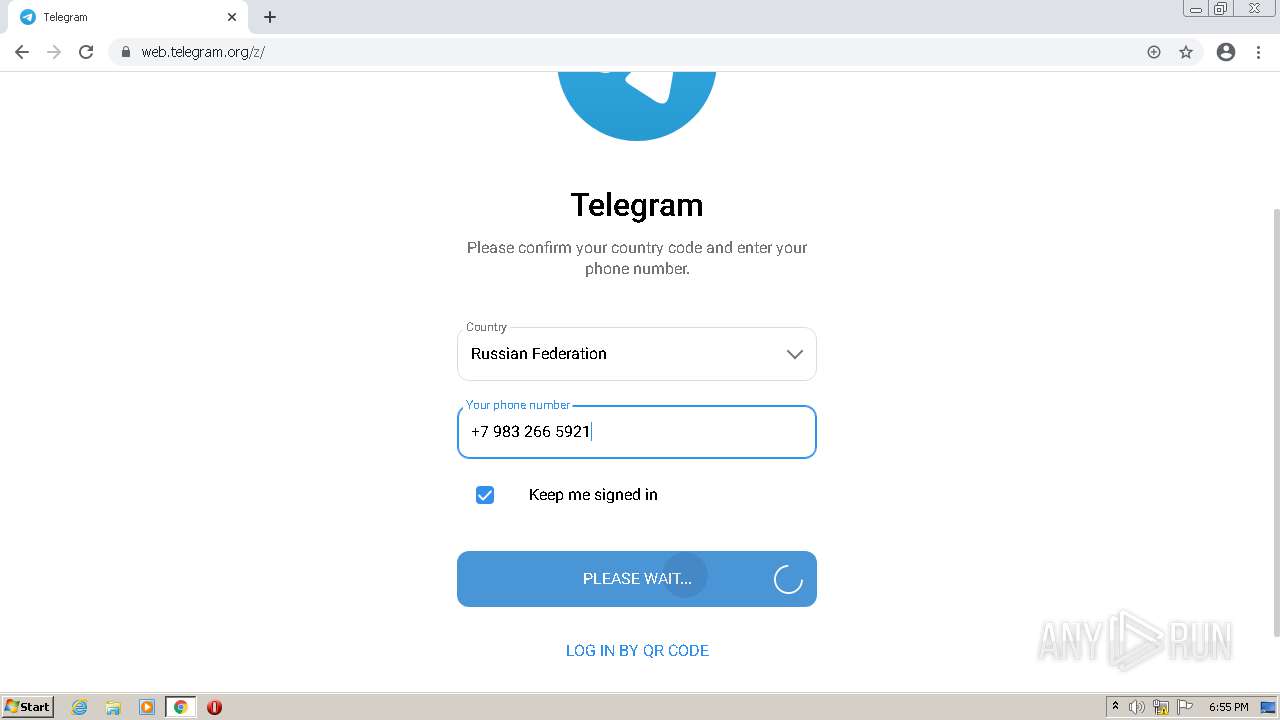
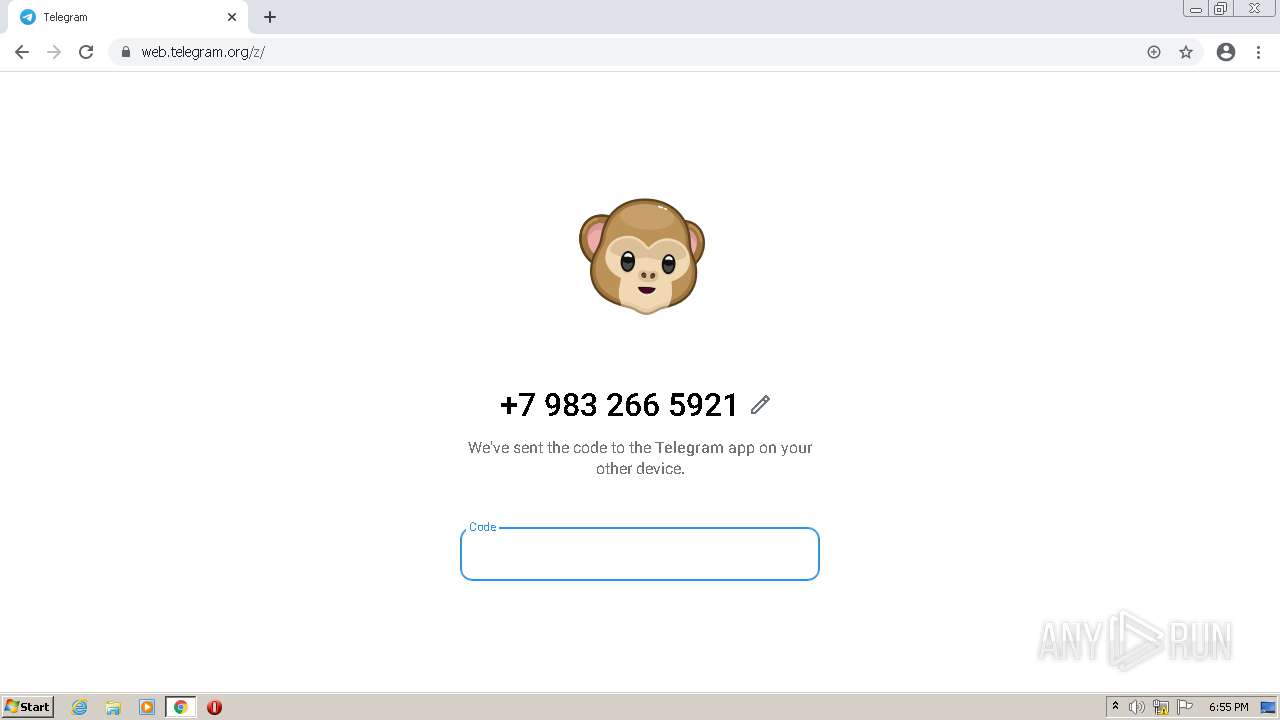
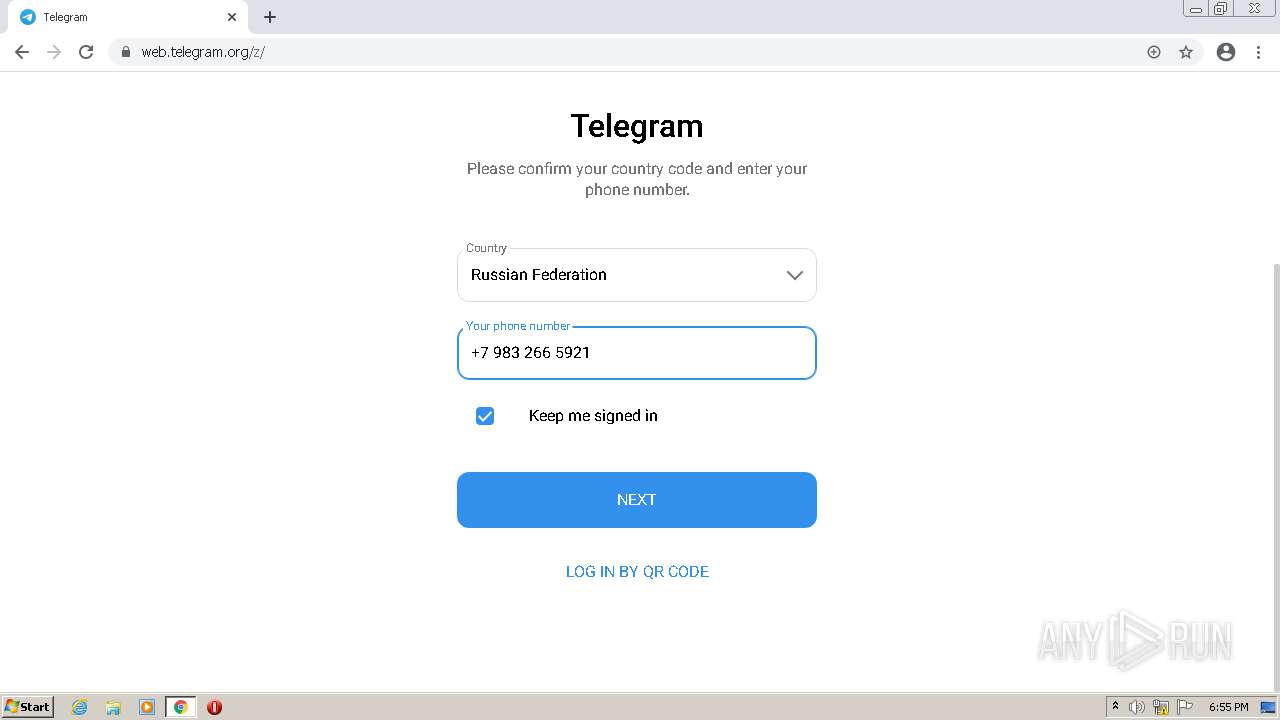
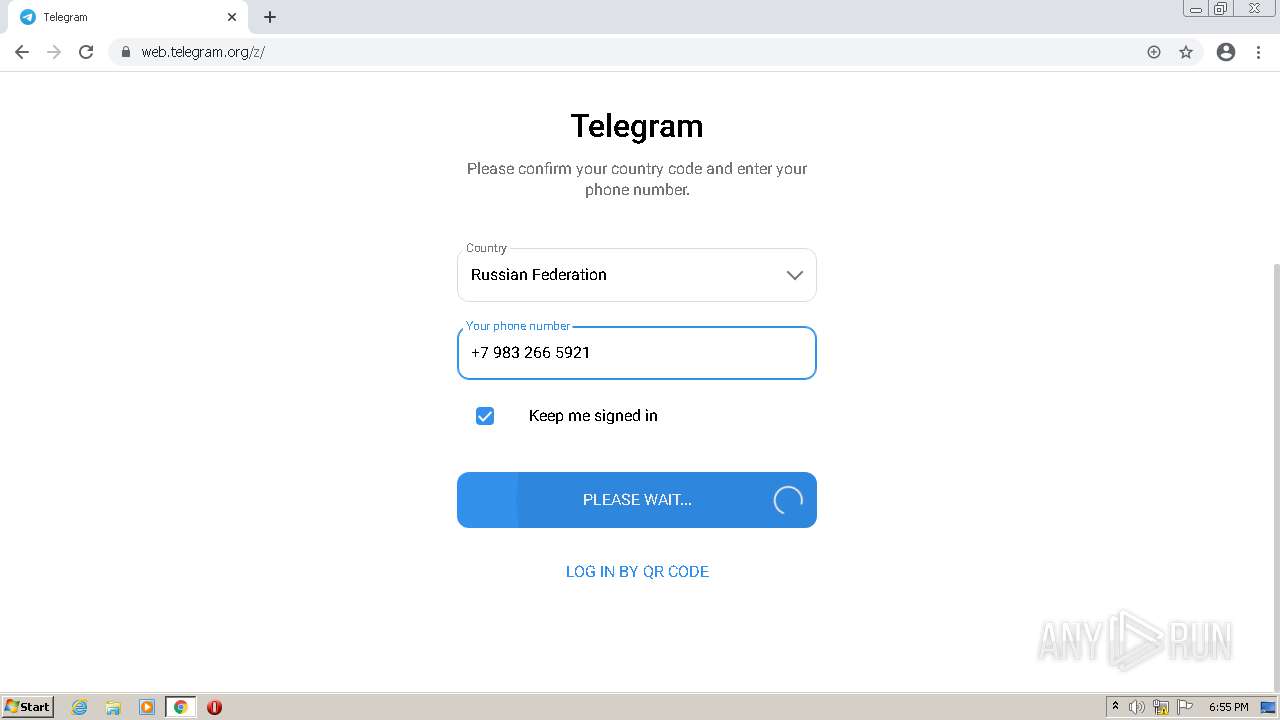
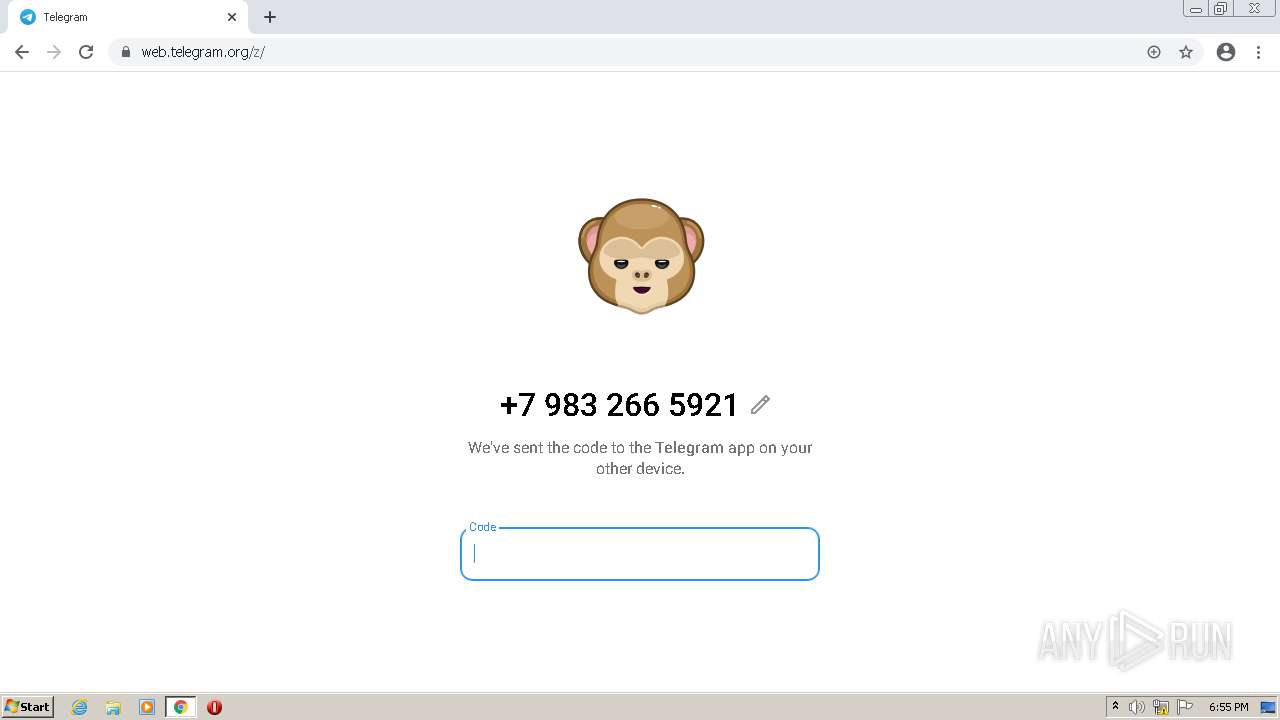
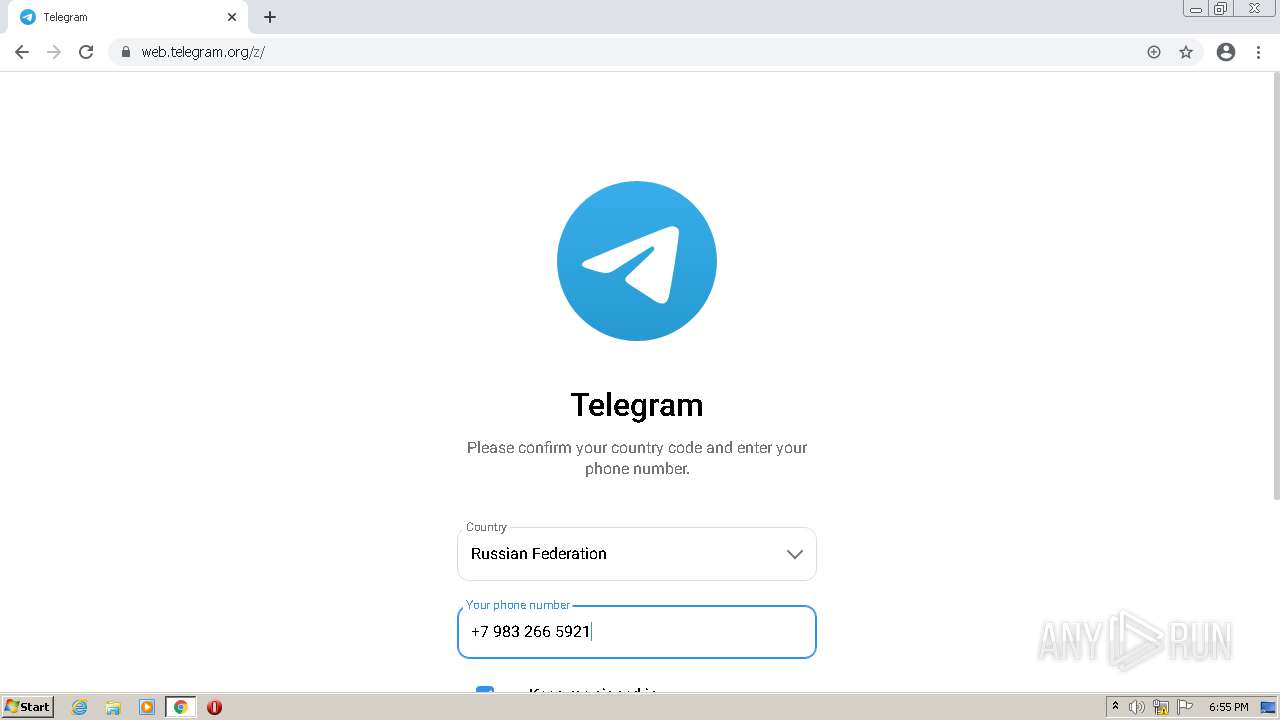
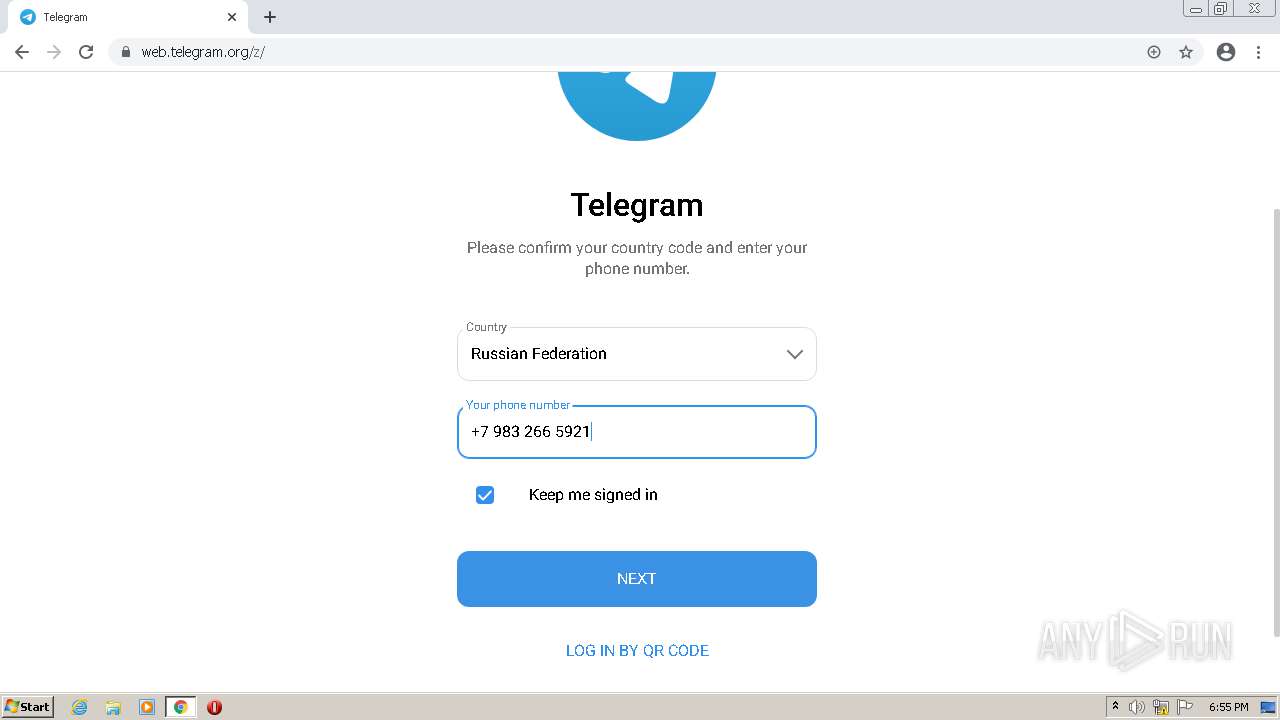
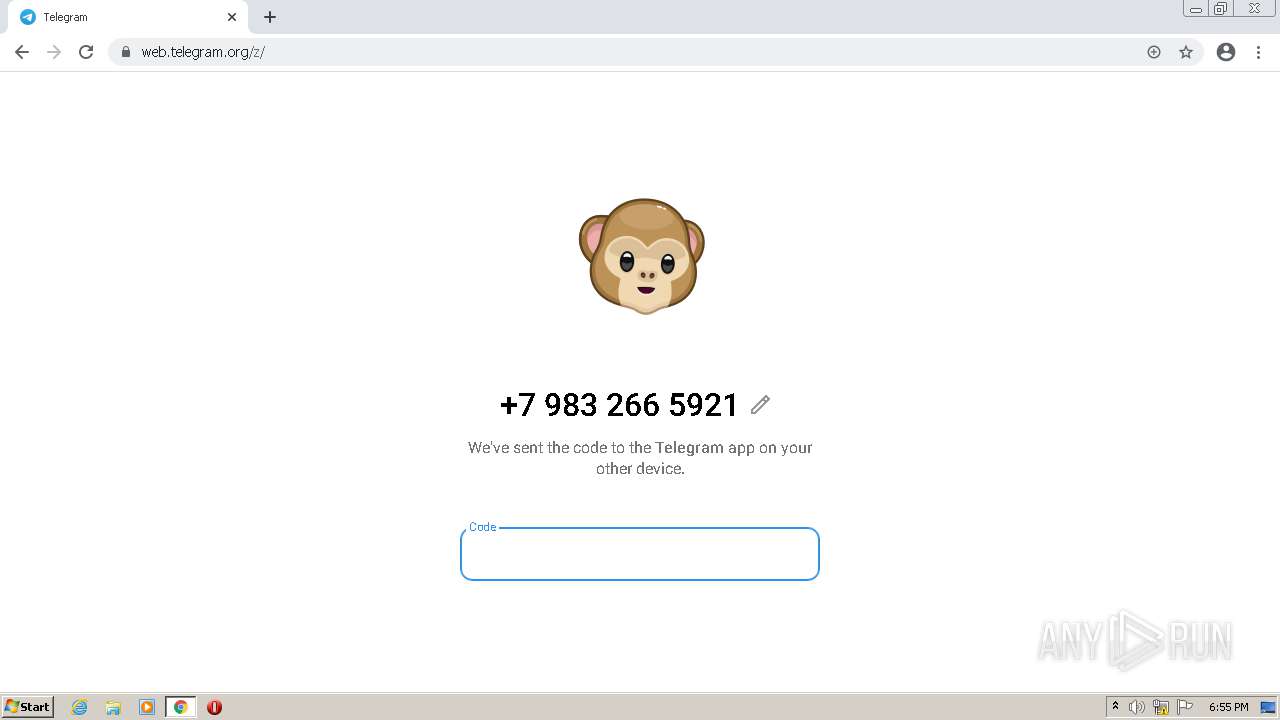
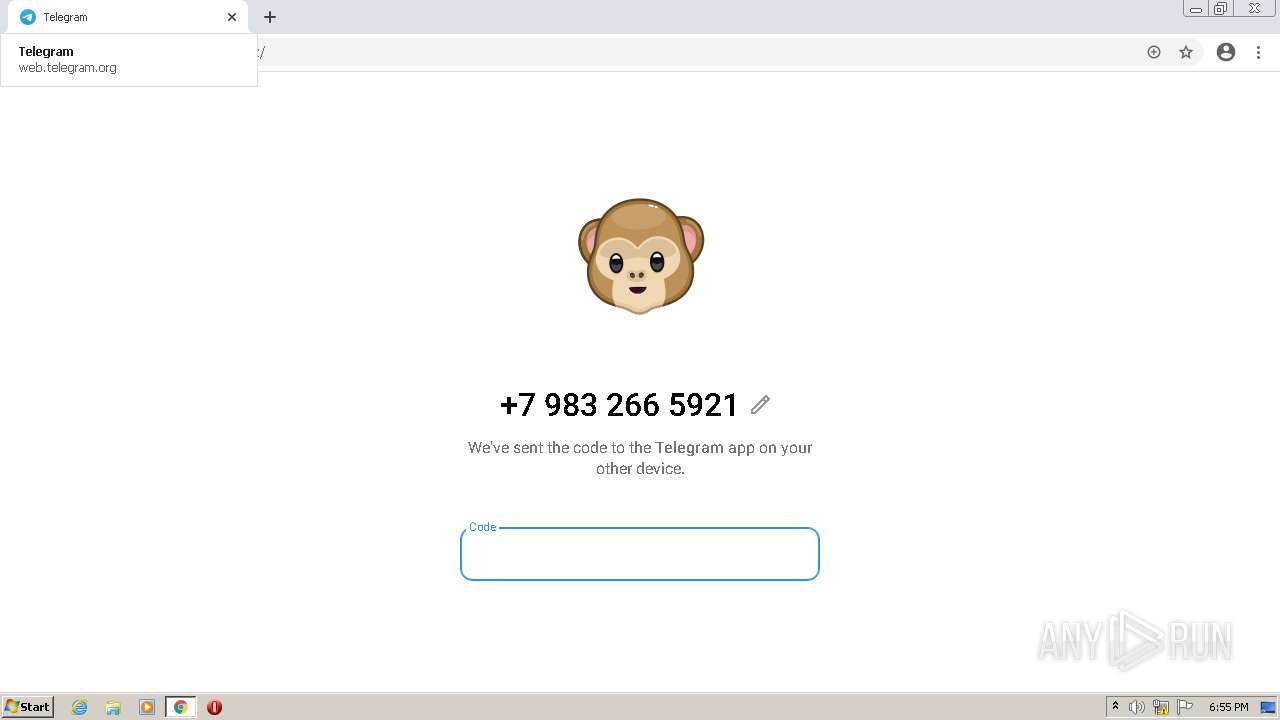
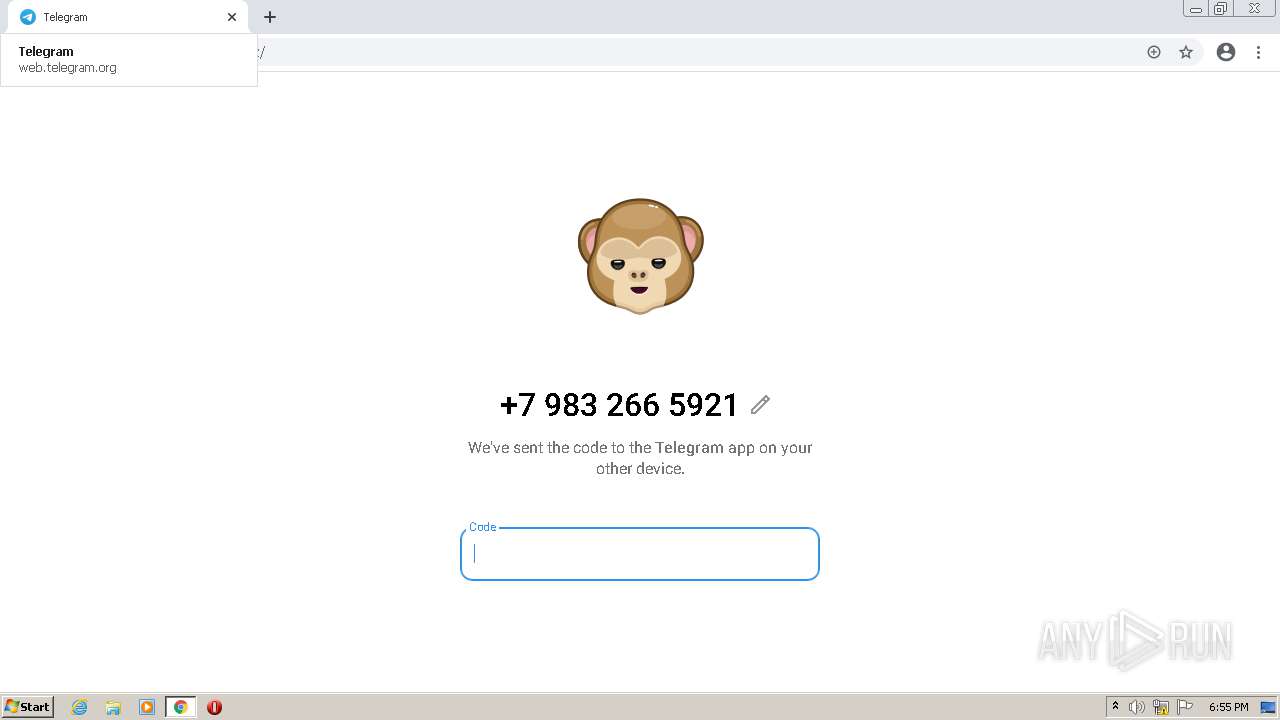
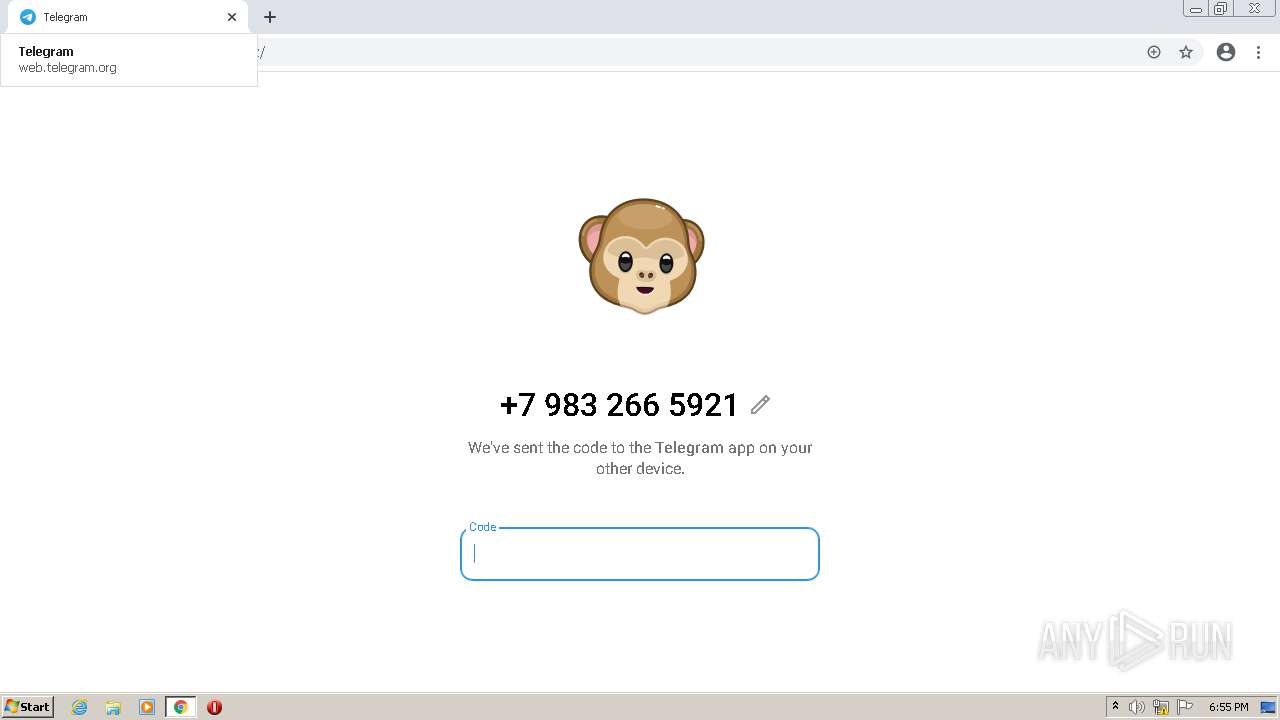
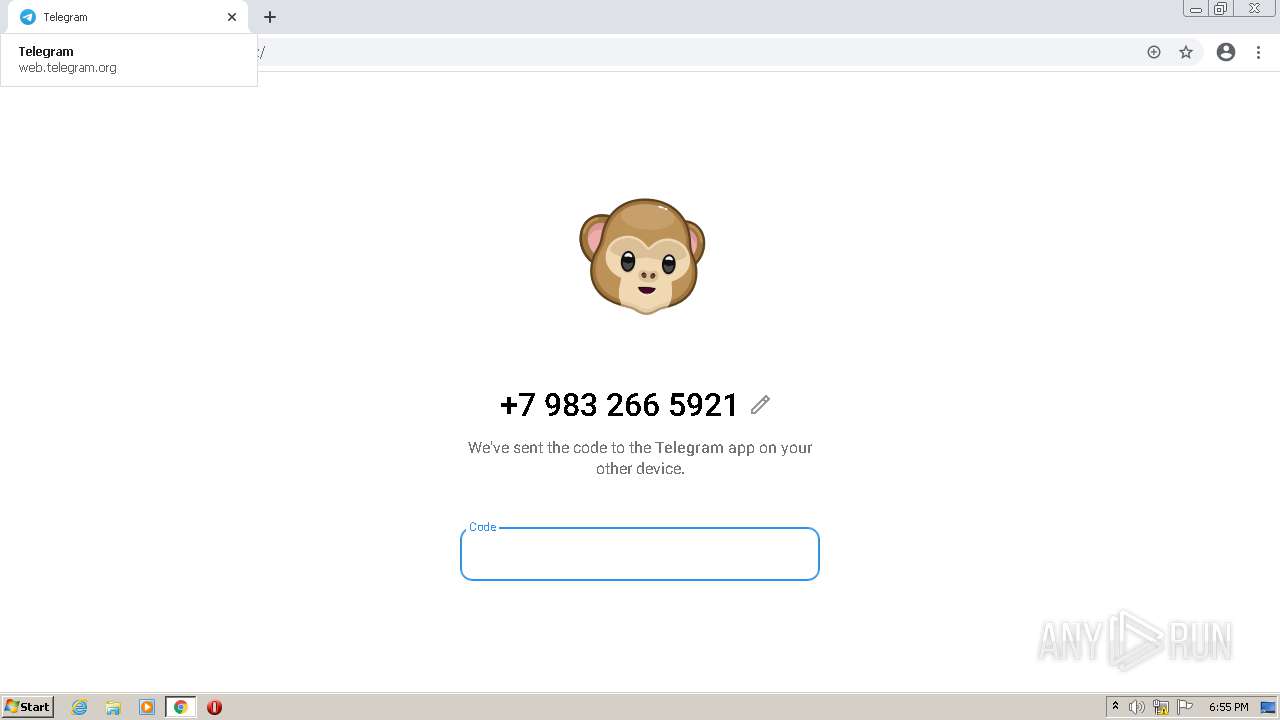
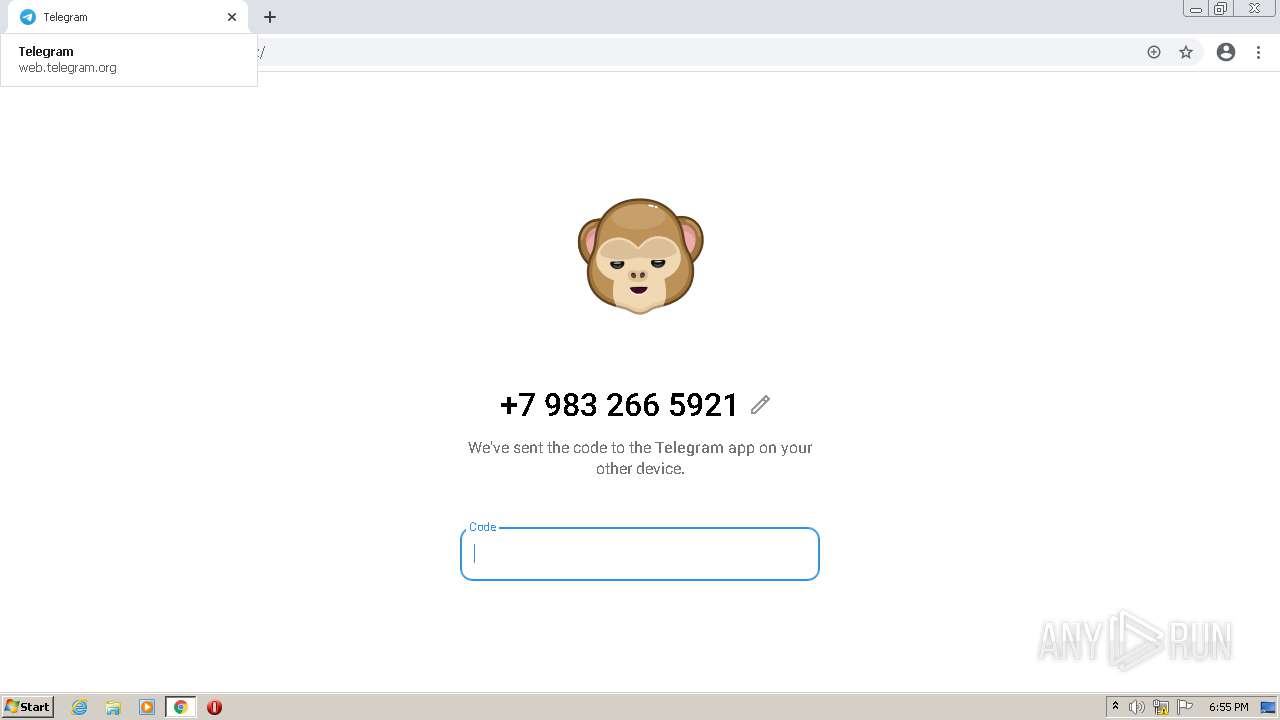
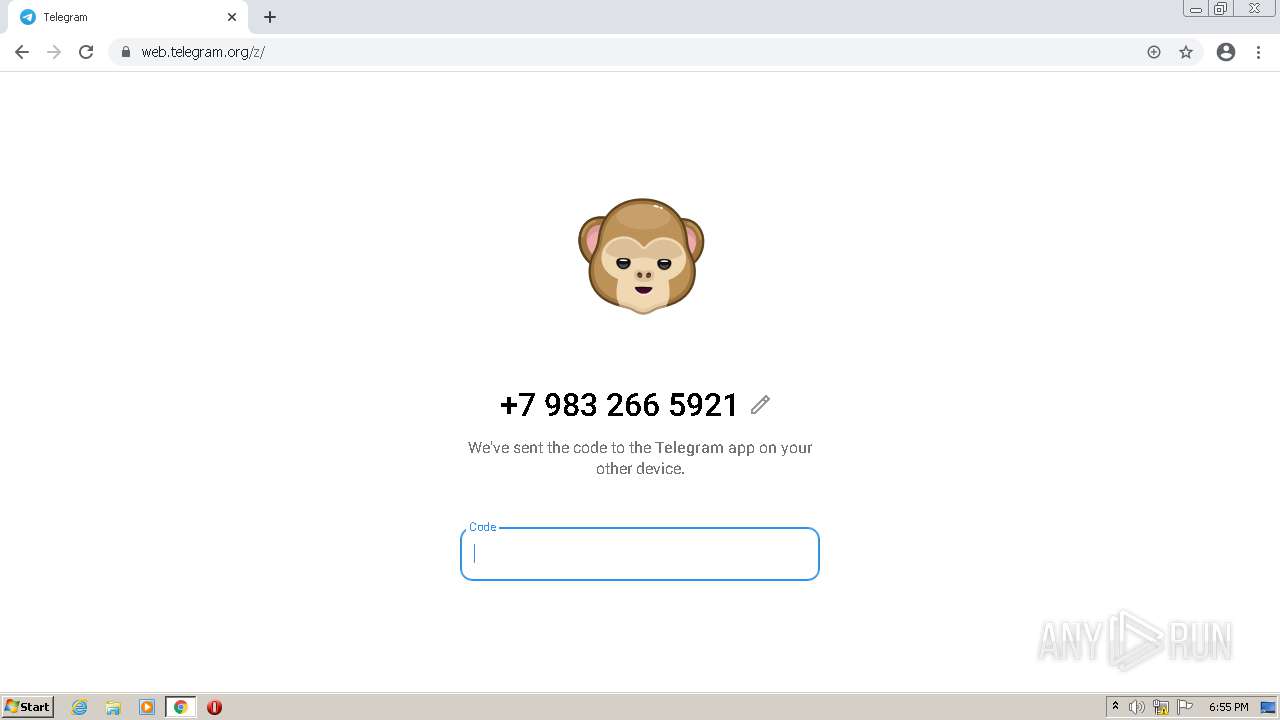
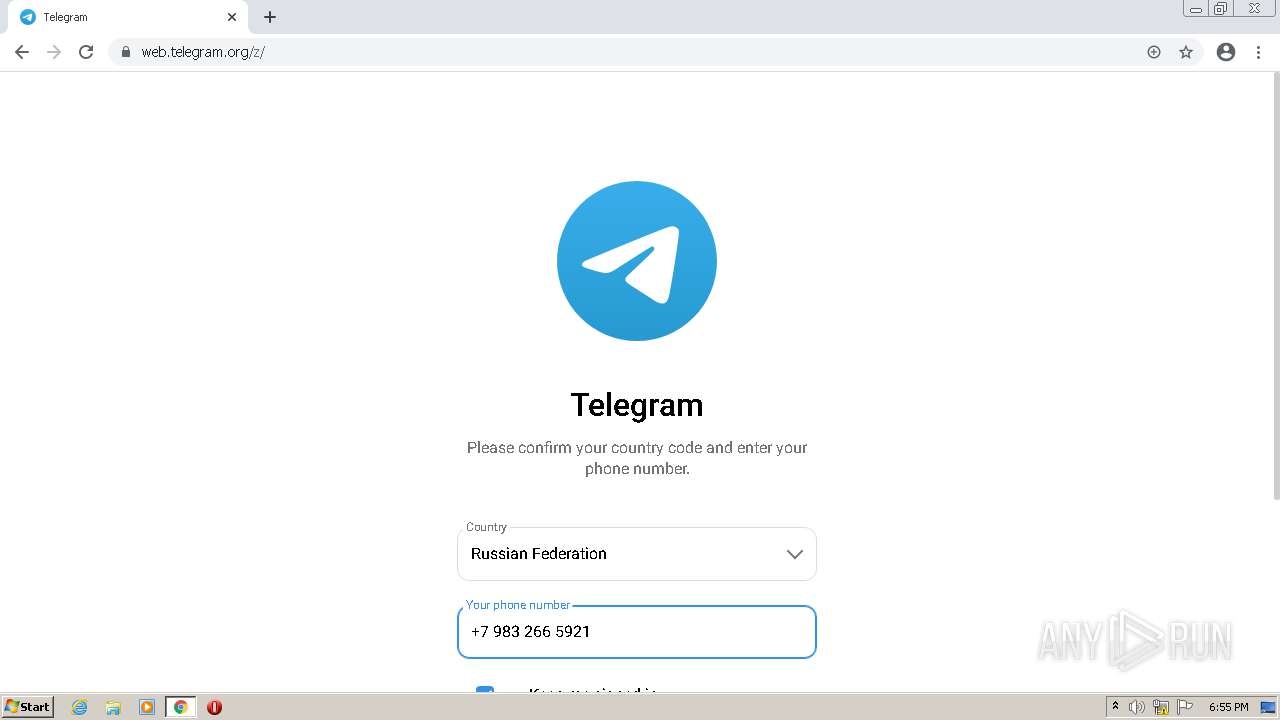
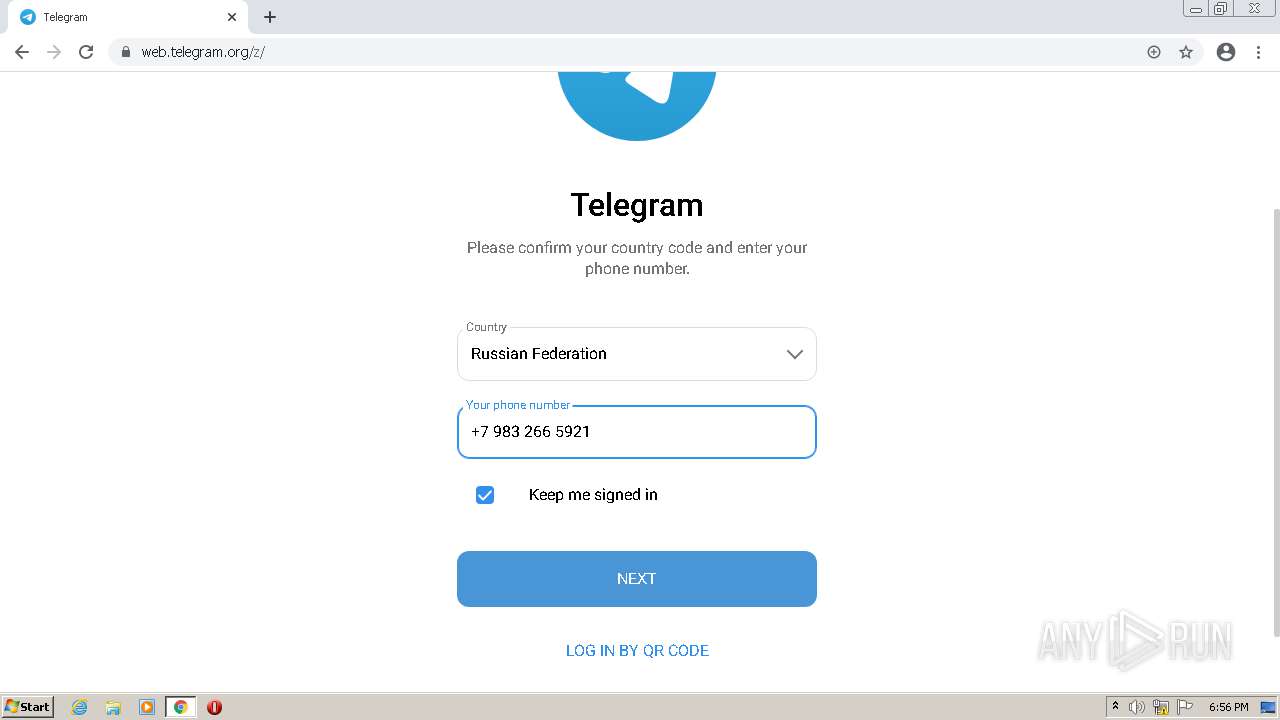
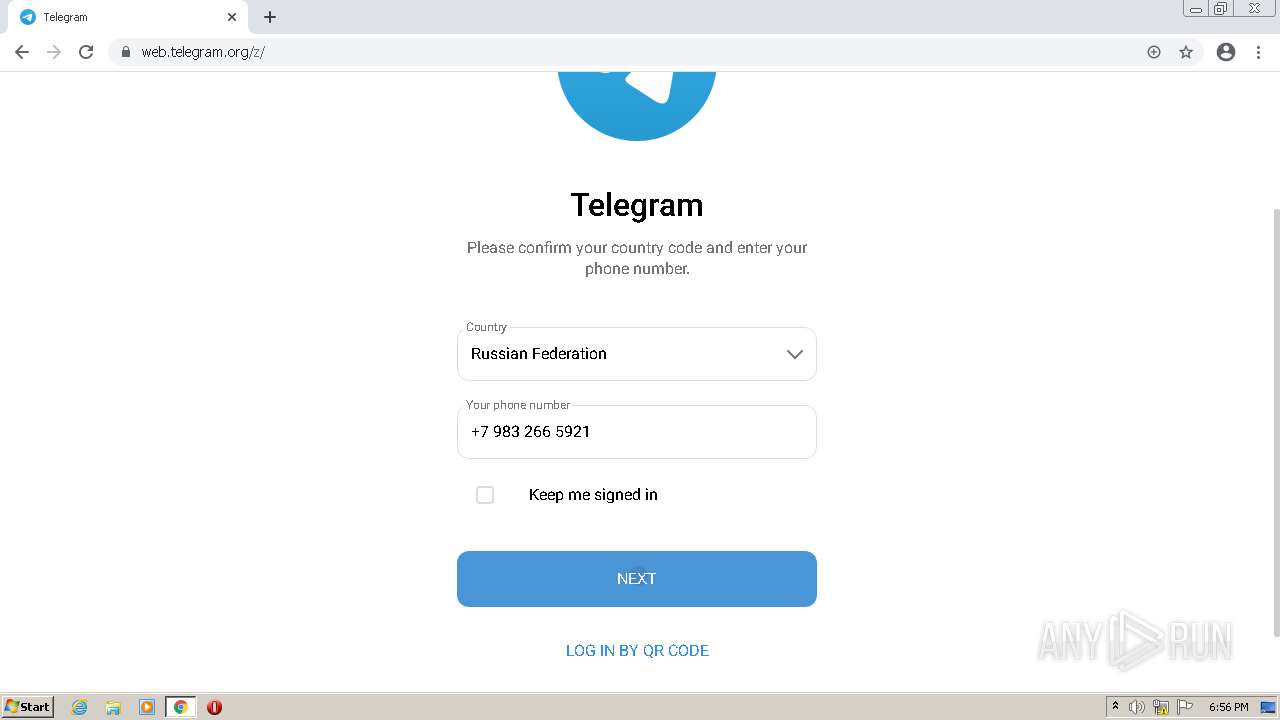
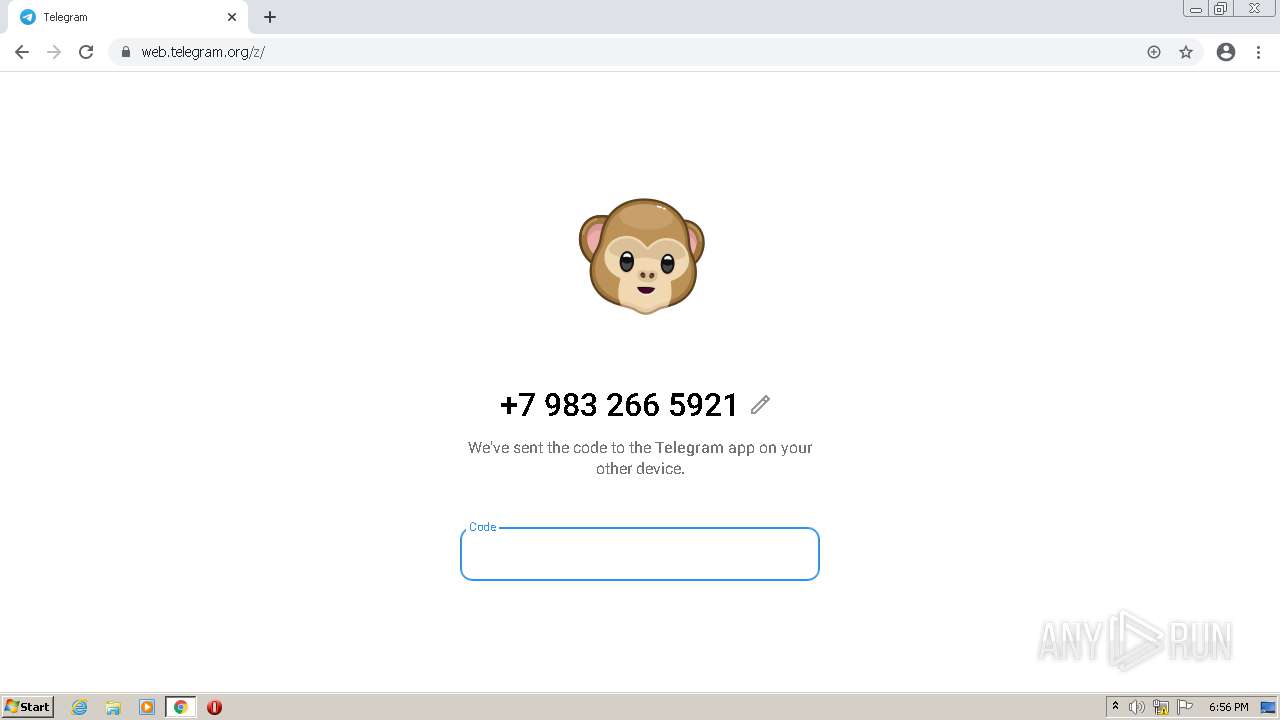
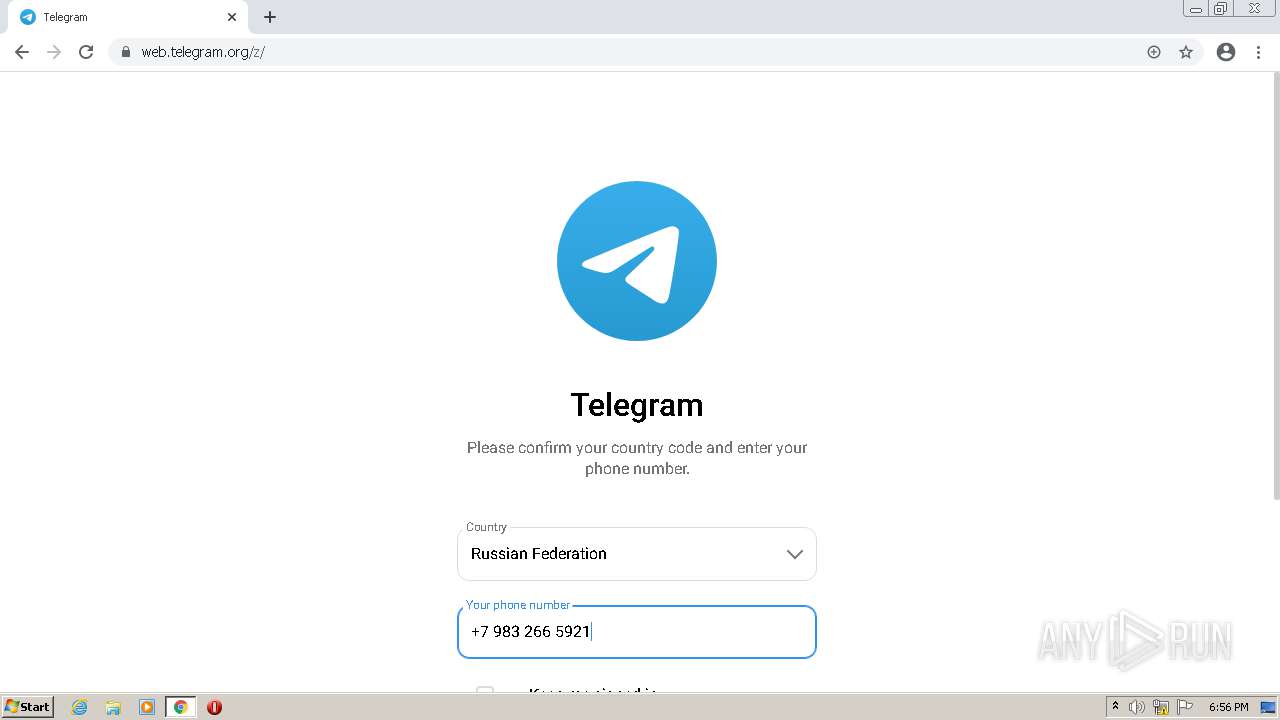
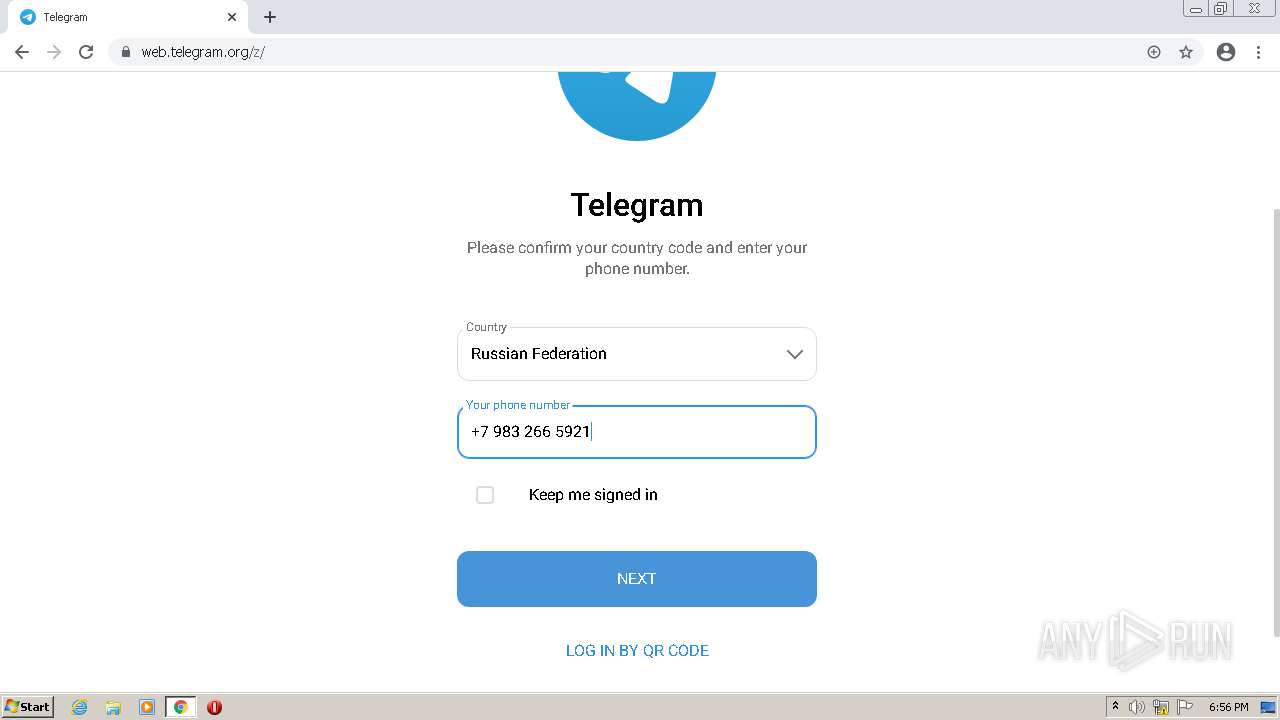
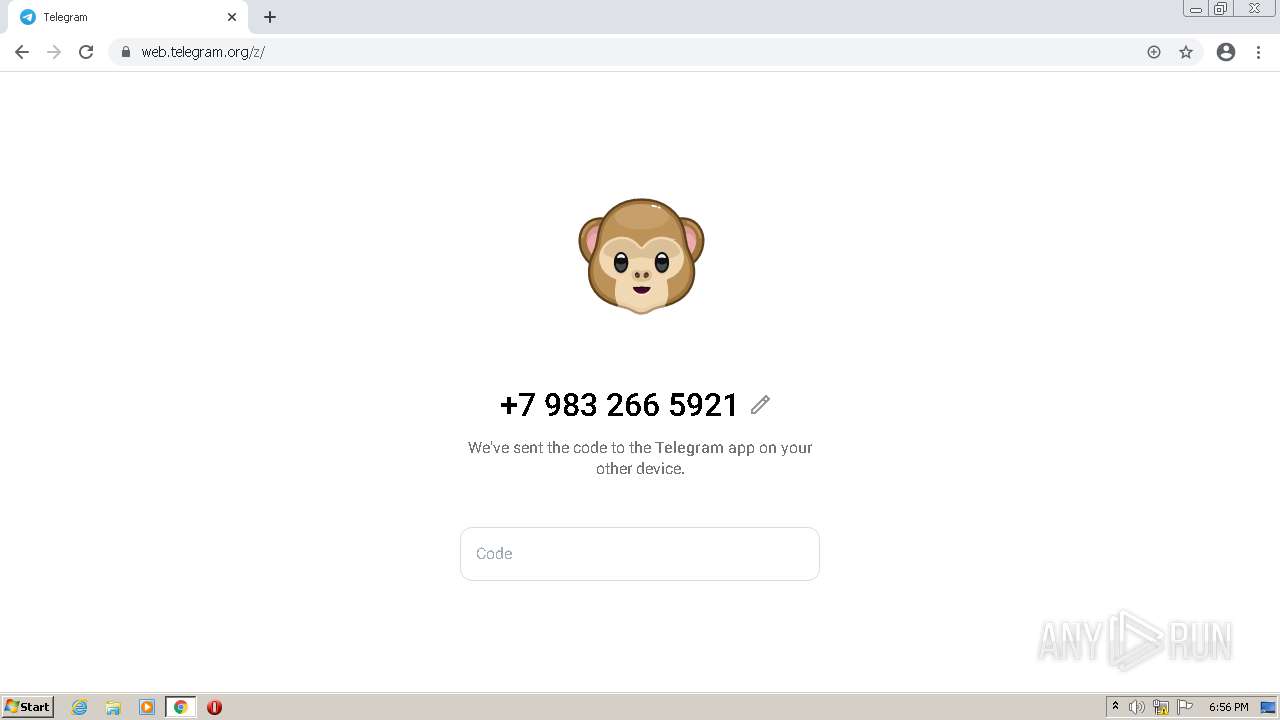
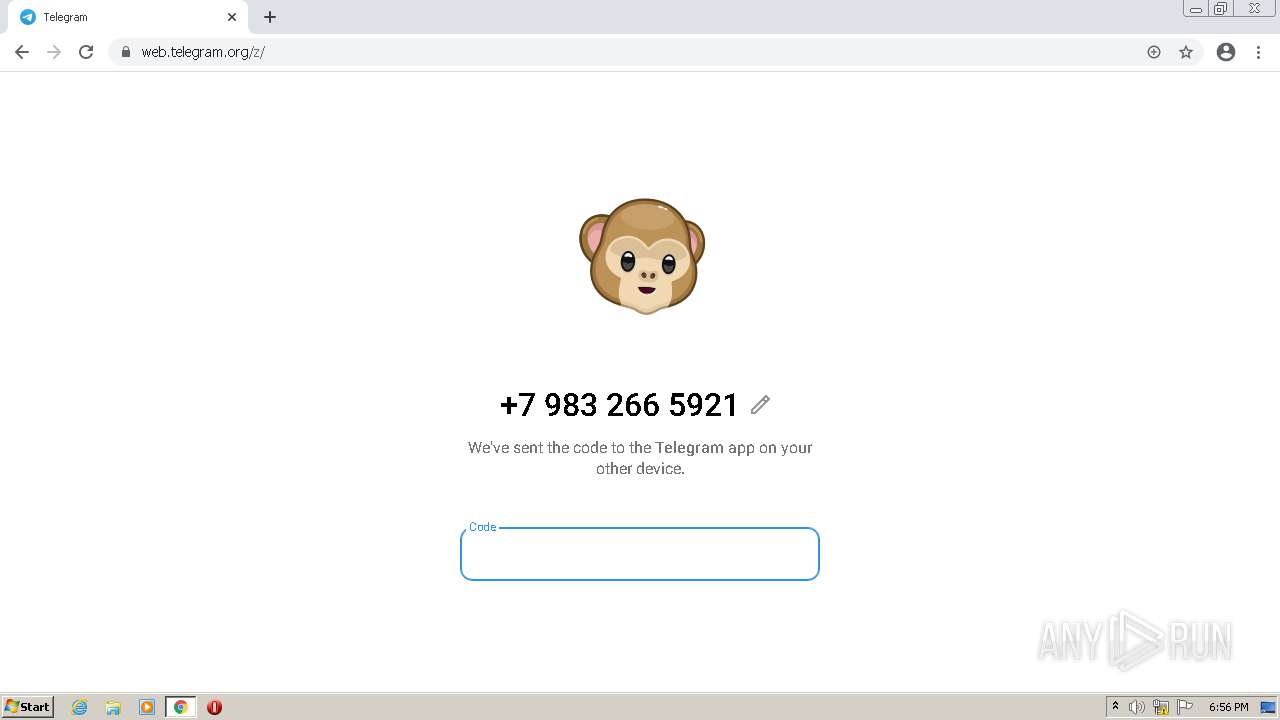
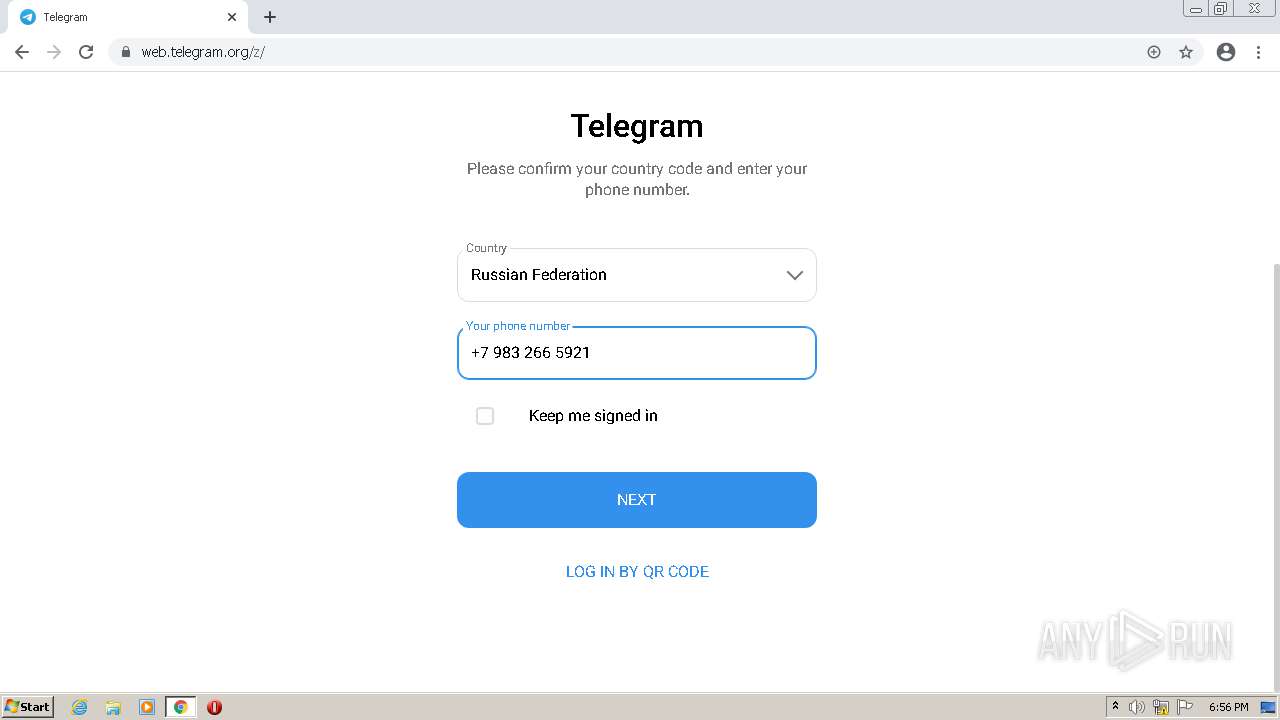
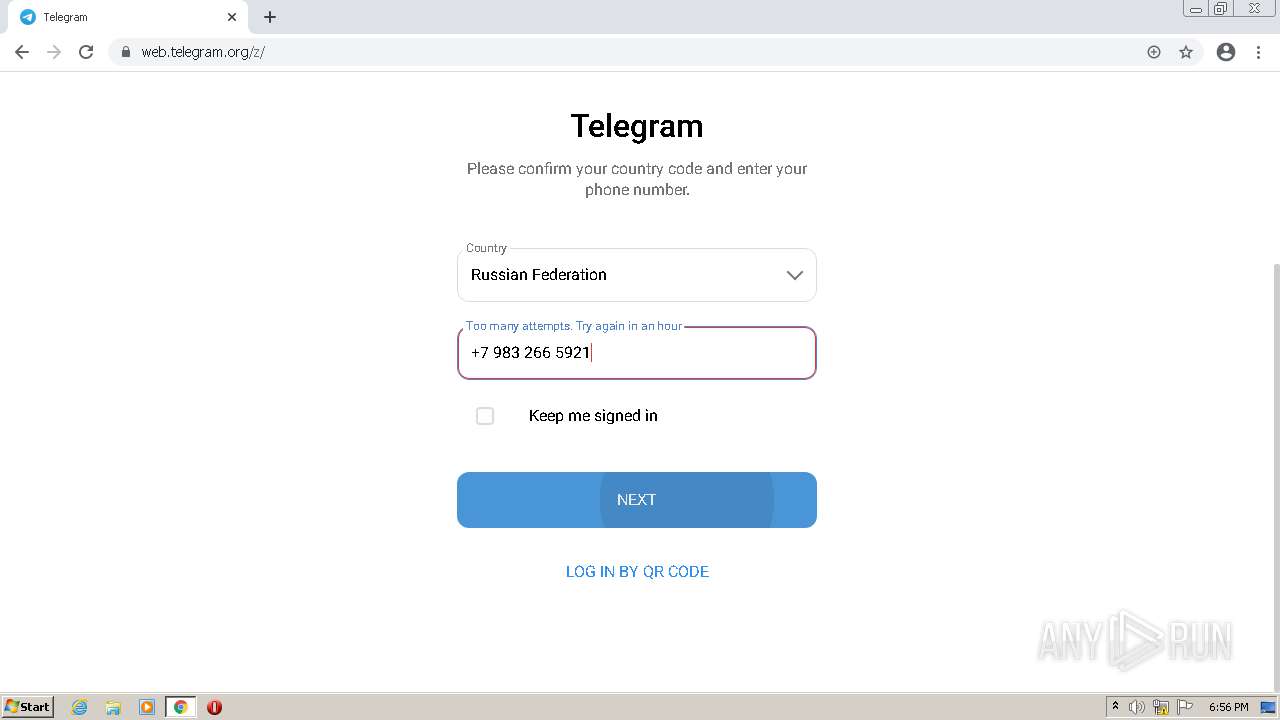
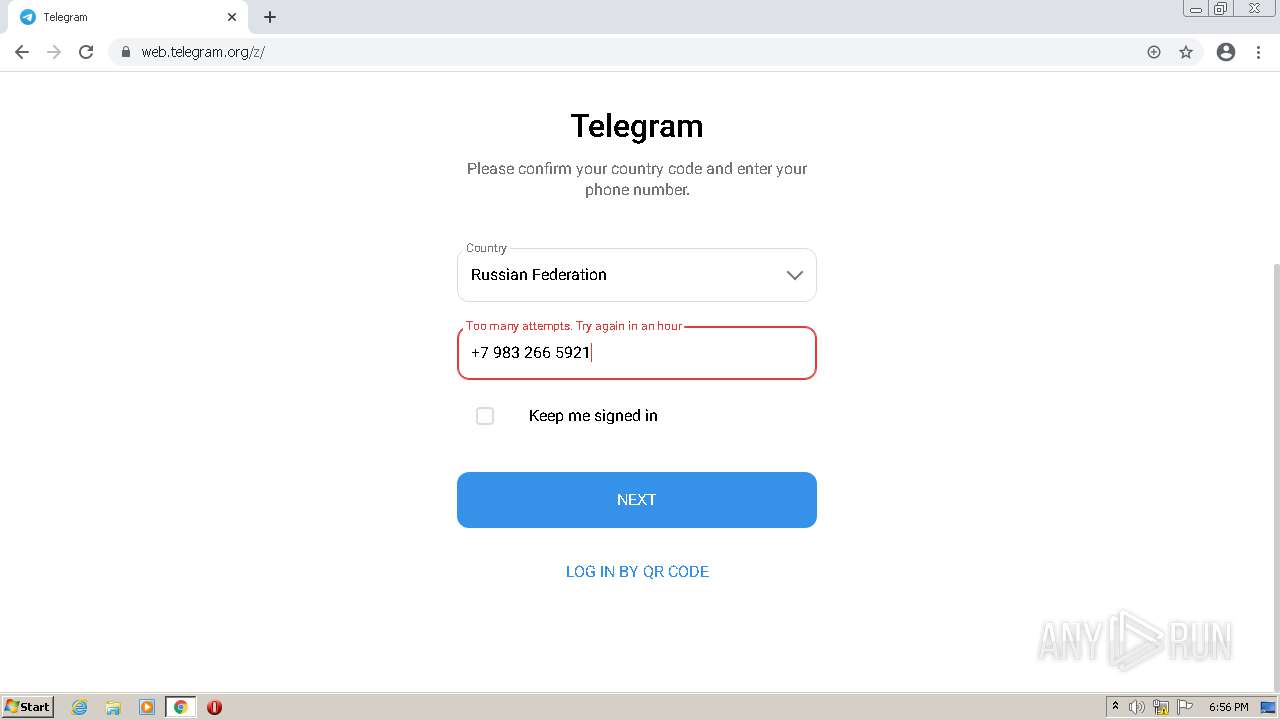
| URL: | https://web.telegram.org/ |
| Full analysis: | https://app.any.run/tasks/67f123c8-b1d3-4876-b55a-70c5da3d7ca6 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2021, 18:53:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 98C27C36ED2A83C6EA41B1E27E4CB6DA |
| SHA1: | 78977F7AEC98D1C072A768B6A366B8D99CDE8DF4 |
| SHA256: | AF7EFCA26DFA871700E8C8D6A705C8641DCEB448C70DE86CA0E07D8D7AA7F2AC |
| SSDEEP: | 3:N8RFsJK:2X |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 500)
- iexplore.exe (PID: 492)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2128)
INFO
Application launched itself
- iexplore.exe (PID: 492)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2128)
Checks supported languages
- iexplore.exe (PID: 492)
- iexplore.exe (PID: 500)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 3844)
- opera.exe (PID: 1344)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 736)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 624)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 596)
- chrome.exe (PID: 352)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 1644)
Reads the computer name
- iexplore.exe (PID: 500)
- iexplore.exe (PID: 492)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2972)
- opera.exe (PID: 1344)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3412)
Changes internet zones settings
- iexplore.exe (PID: 492)
Checks Windows Trust Settings
- iexplore.exe (PID: 492)
- iexplore.exe (PID: 500)
Reads settings of System Certificates
- iexplore.exe (PID: 492)
- iexplore.exe (PID: 500)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 2128)
Reads internet explorer settings
- iexplore.exe (PID: 500)
Manual execution by user
- chrome.exe (PID: 3180)
- opera.exe (PID: 1344)
- chrome.exe (PID: 2128)
Reads the hosts file
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 1512)
Creates files in the user directory
- opera.exe (PID: 1344)
- iexplore.exe (PID: 492)
Reads the date of Windows installation
- iexplore.exe (PID: 492)
- opera.exe (PID: 1344)
- chrome.exe (PID: 1644)
Check for Java to be installed
- opera.exe (PID: 1344)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 1344)
- chrome.exe (PID: 2128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,1750830194911368902,4640083602304959767,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3664 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://web.telegram.org/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 500 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:492 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1750830194911368902,4640083602304959767,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,1750830194911368902,4640083602304959767,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4048 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1750830194911368902,4640083602304959767,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1016,1750830194911368902,4640083602304959767,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6401834294695627990,2171862121992361035,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,1750830194911368902,4640083602304959767,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 300
Read events
29 913
Write events
384
Delete events
3
Modification events
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30925558 | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30925558 | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
1 271
Text files
194
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E9F5BE56845D3BEEA3D65CC577DA0CE5_E57AD3883ED05819987532B8A3097280 | binary | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E9F5BE56845D3BEEA3D65CC577DA0CE5_E57AD3883ED05819987532B8A3097280 | der | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\app[1].js | binary | |
MD5:— | SHA256:— | |||
| 492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 500 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
78
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 200 | 194.9.24.81:80 | http://r6---sn-5uh5o-f5f6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=188.212.135.7&mm=28&mn=sn-5uh5o-f5f6&ms=nvh&mt=1637952504&mv=m&mvi=6&pl=24&rmhost=r3---sn-5uh5o-f5f6.gvt1.com&shardbypass=yes&smhost=r3---sn-5uh5o-f5fs.gvt1.com | PL | — | — | whitelisted |
492 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
500 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
500 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1344 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
500 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCYyjQx%2Bggm1w%3D%3D | US | der | 1.74 Kb | whitelisted |
500 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQC%2BvXkdgXs5aw%3D%3D | US | der | 1.74 Kb | whitelisted |
1344 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
492 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
492 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
492 | iexplore.exe | 23.32.238.208:80 | ctldl.windowsupdate.com | XO Communications | US | unknown |
492 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
500 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
500 | iexplore.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
492 | iexplore.exe | 149.154.167.99:443 | web.telegram.org | Telegram Messenger LLP | GB | malicious |
492 | iexplore.exe | 23.32.238.226:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1708 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
492 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1708 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web.telegram.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
telegram.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |