| download: | index.html |
| Full analysis: | https://app.any.run/tasks/bcae1473-069c-418a-a714-023264a35802 |
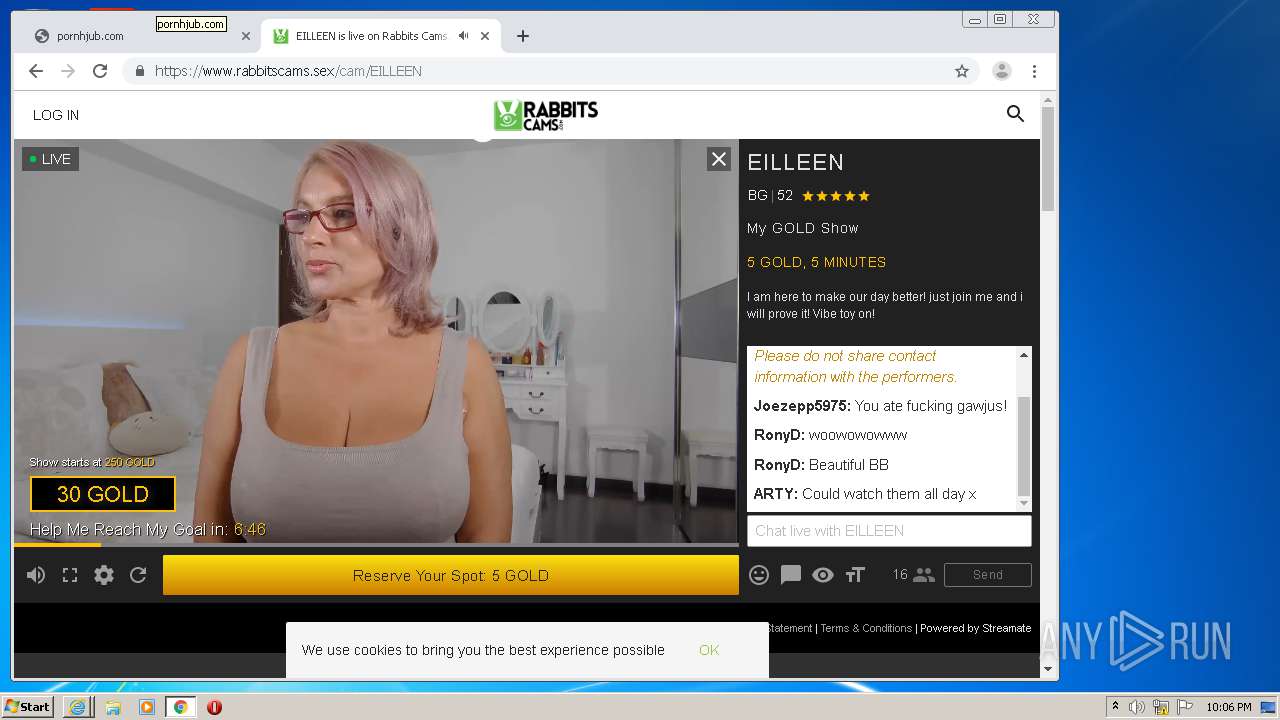
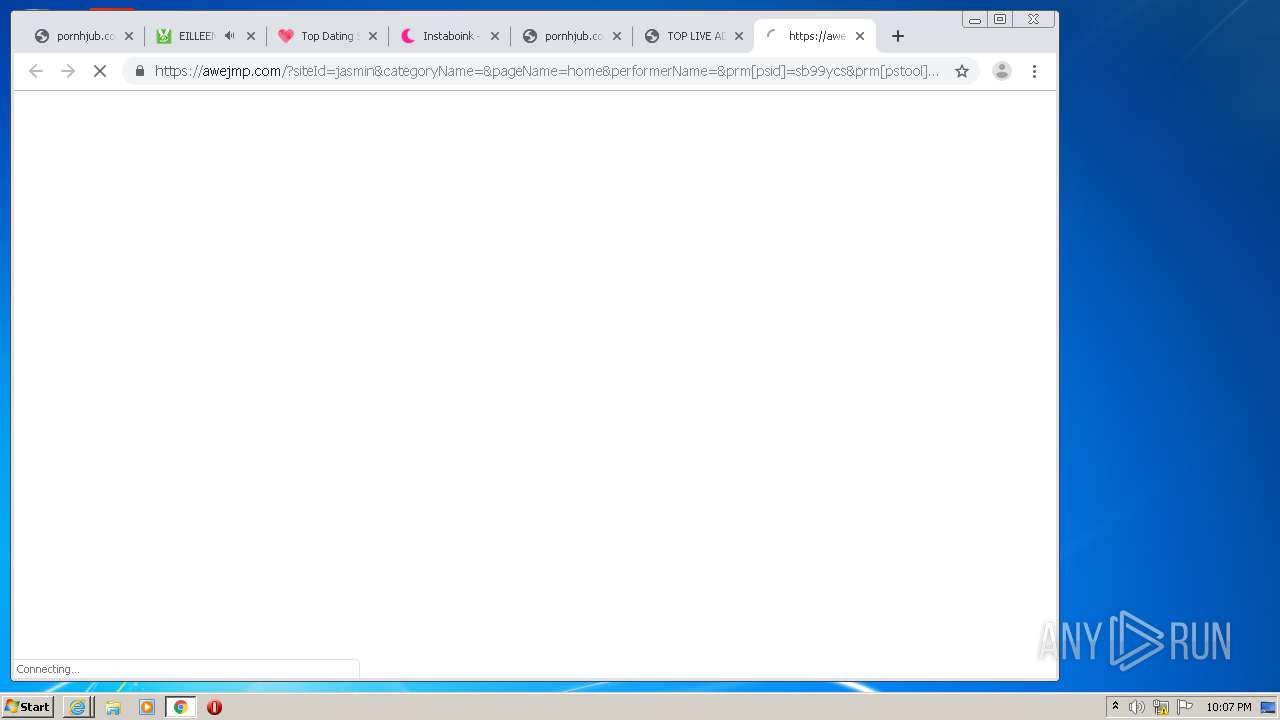
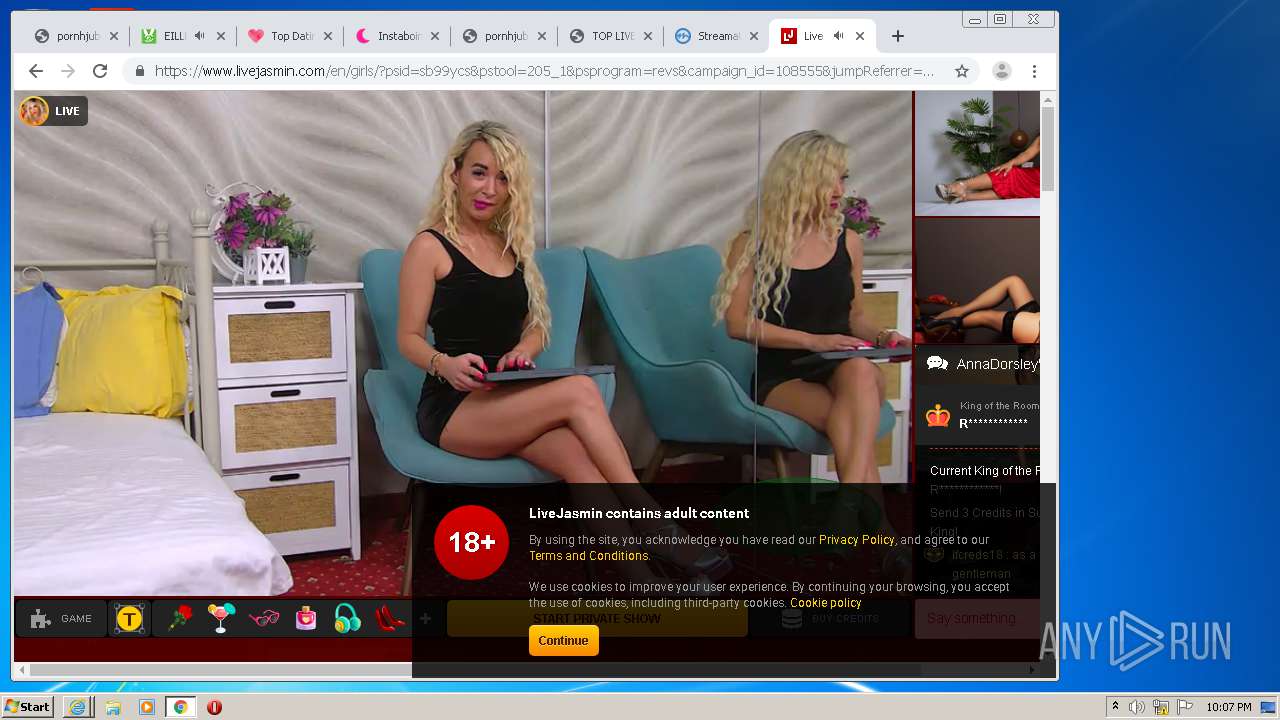
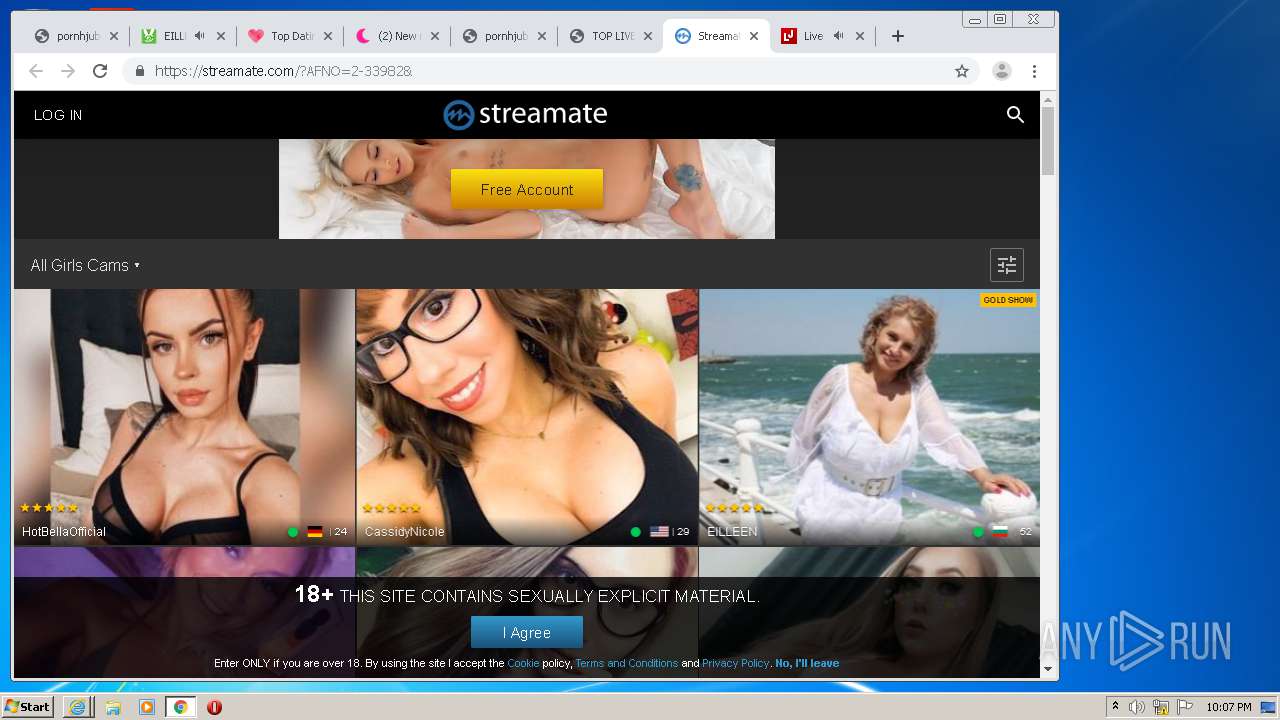
| Verdict: | Malicious activity |
| Analysis date: | September 20, 2020, 21:05:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | E69165E7C63F3DF7C9CF755CE790D789 |
| SHA1: | BFEF58F8EB413A2950F4ADC1068CD7870EA5B099 |
| SHA256: | AF7E23261E6706B49E96F871A6CE668C1346C7BEB4315E574194988F0542B1E1 |
| SSDEEP: | 384:tnVjkfG6+ITx1q6g8Y9QU9WRhBdcQG/FnMbToQZOo/YwI6EvMxjpgWsvSGlHzR:9UGQU9WjcQGCZ/FIXANgWsvSmHzR |
MALICIOUS
No malicious indicators.SUSPICIOUS
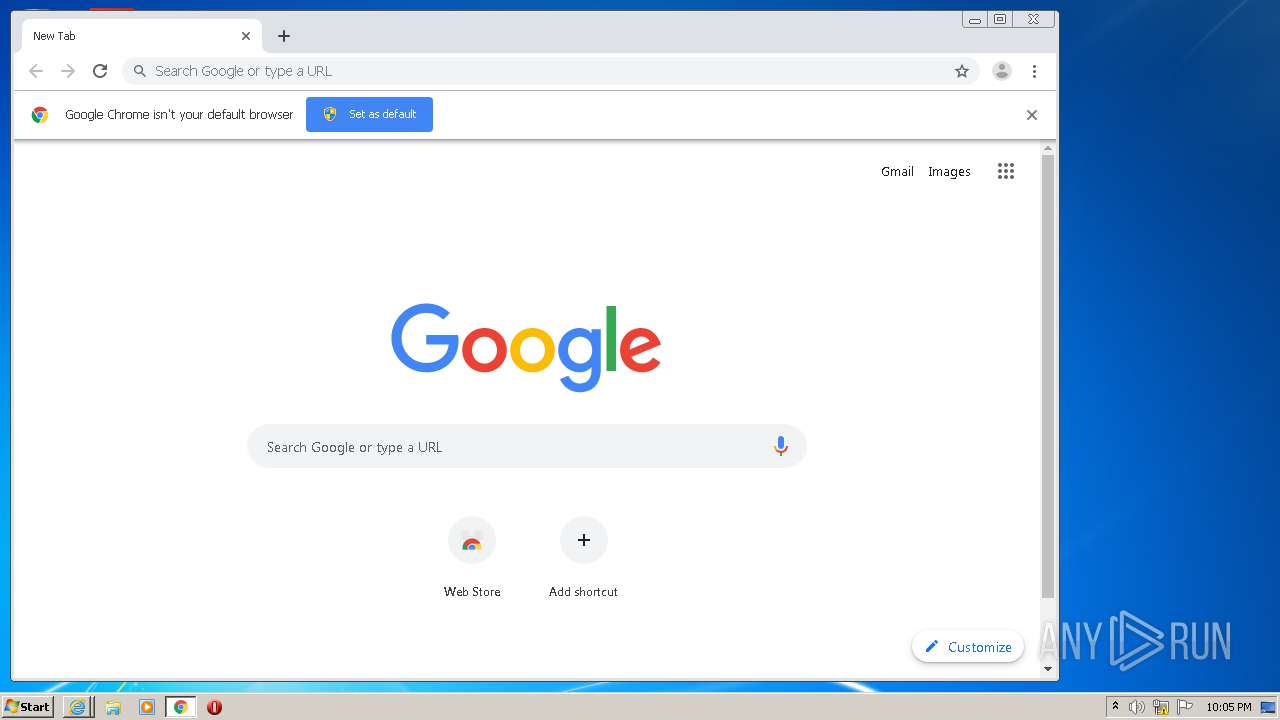
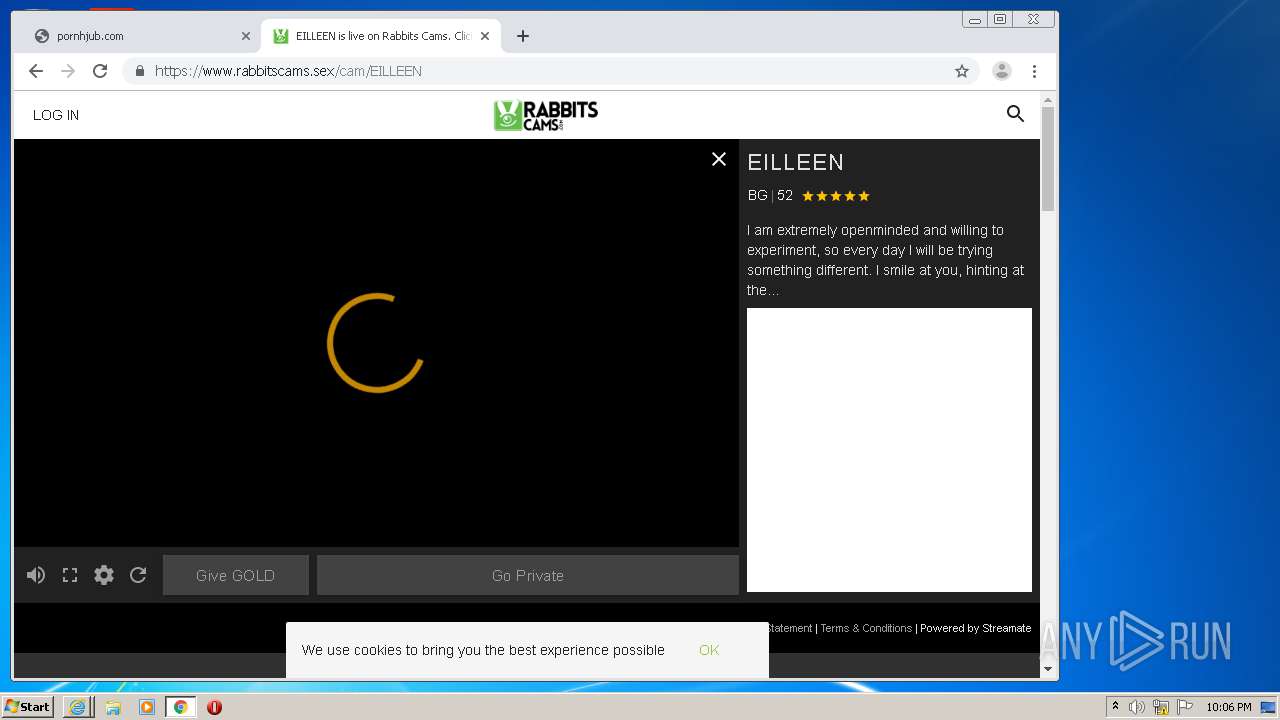
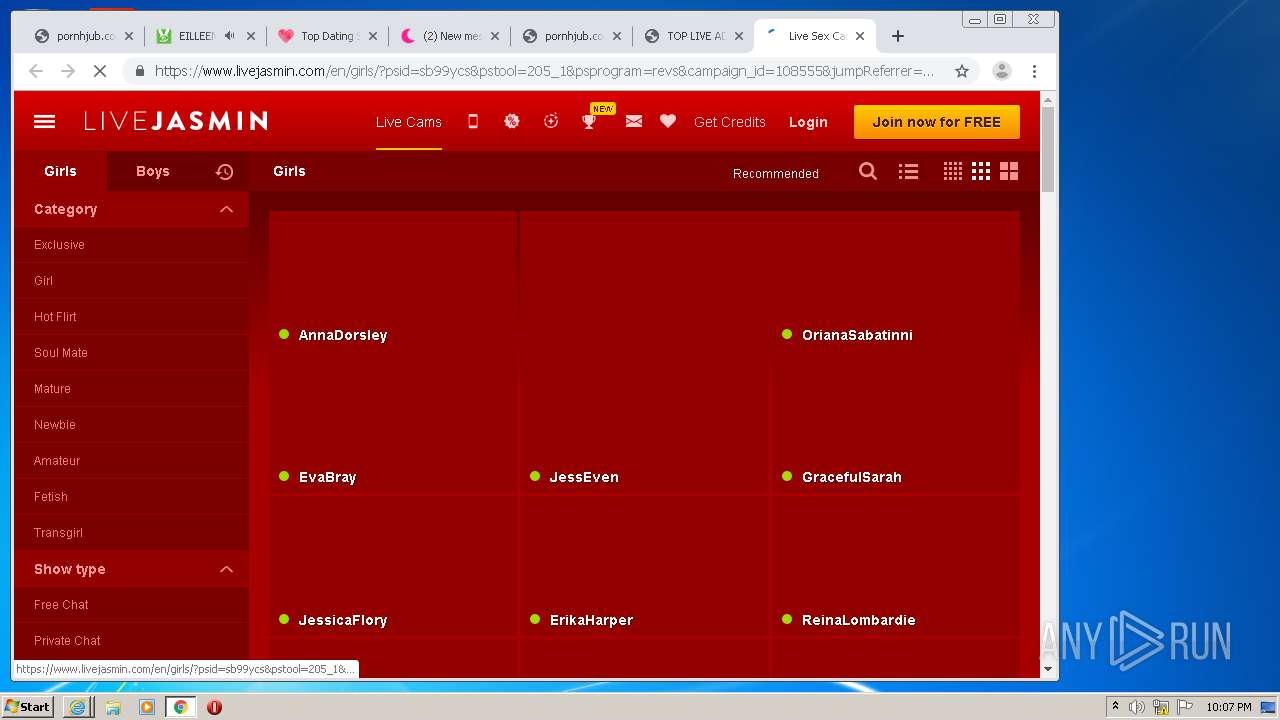
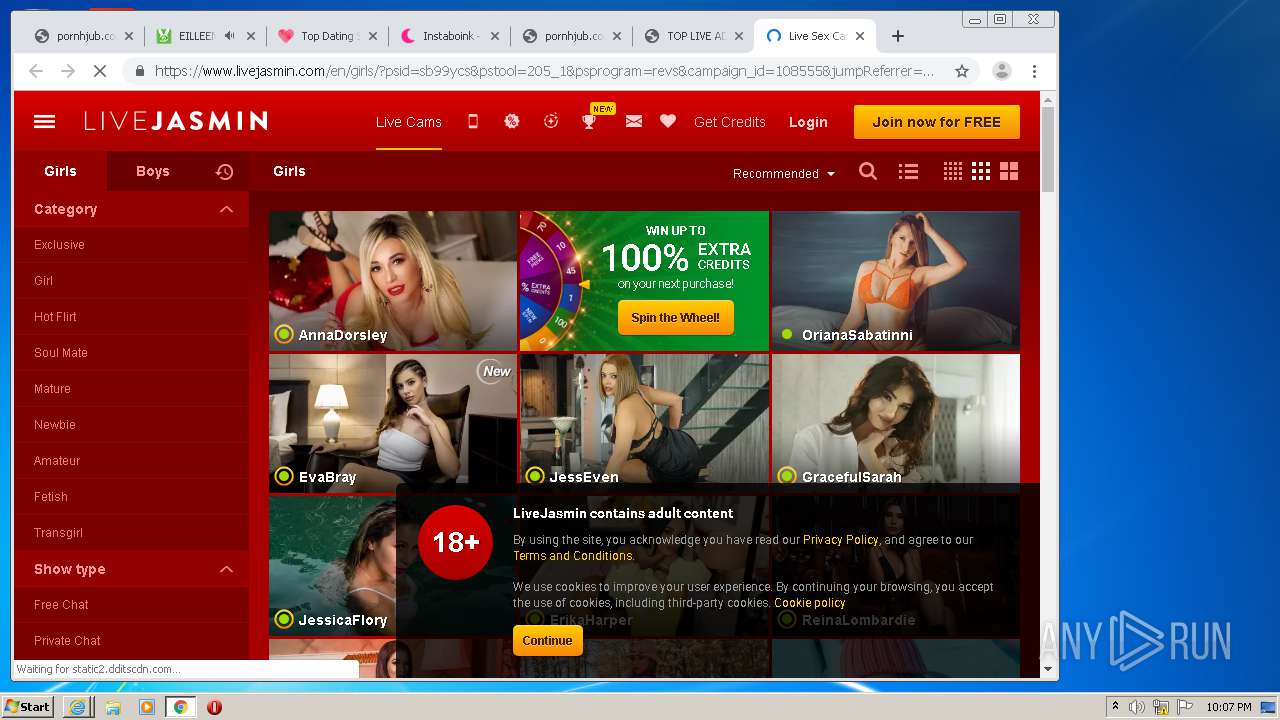
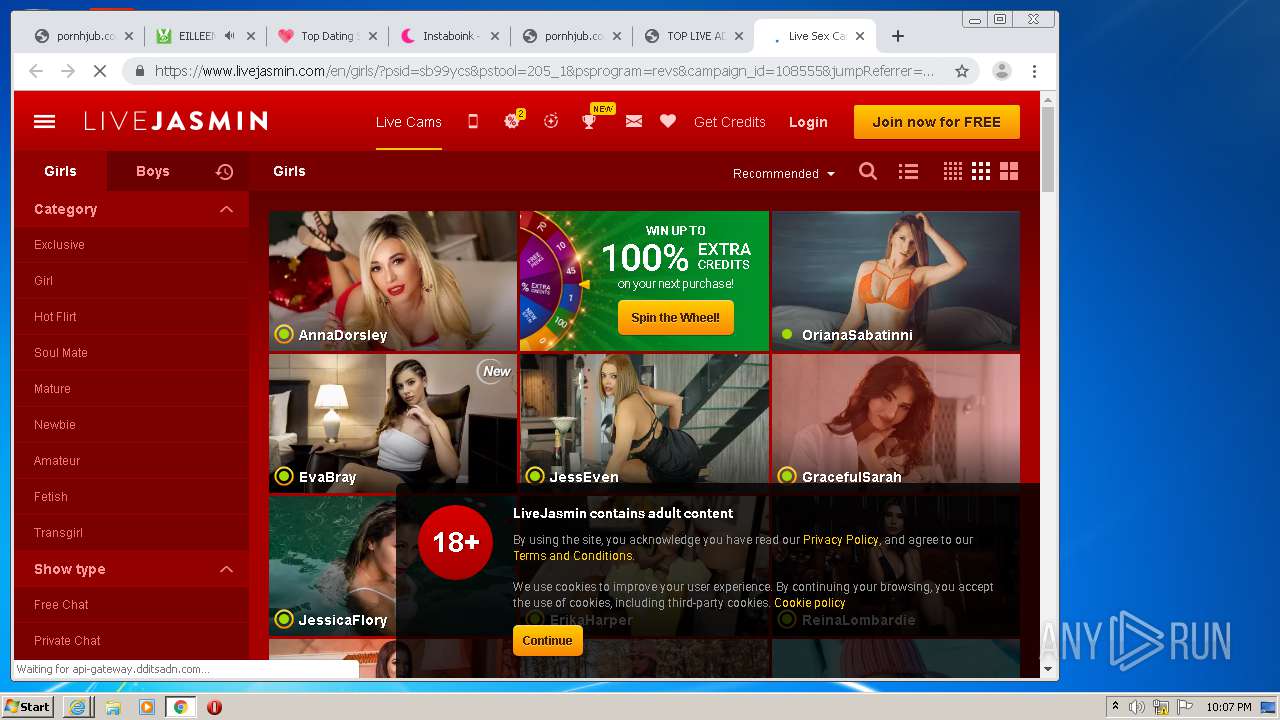
Modifies files in Chrome extension folder
- chrome.exe (PID: 2588)
INFO
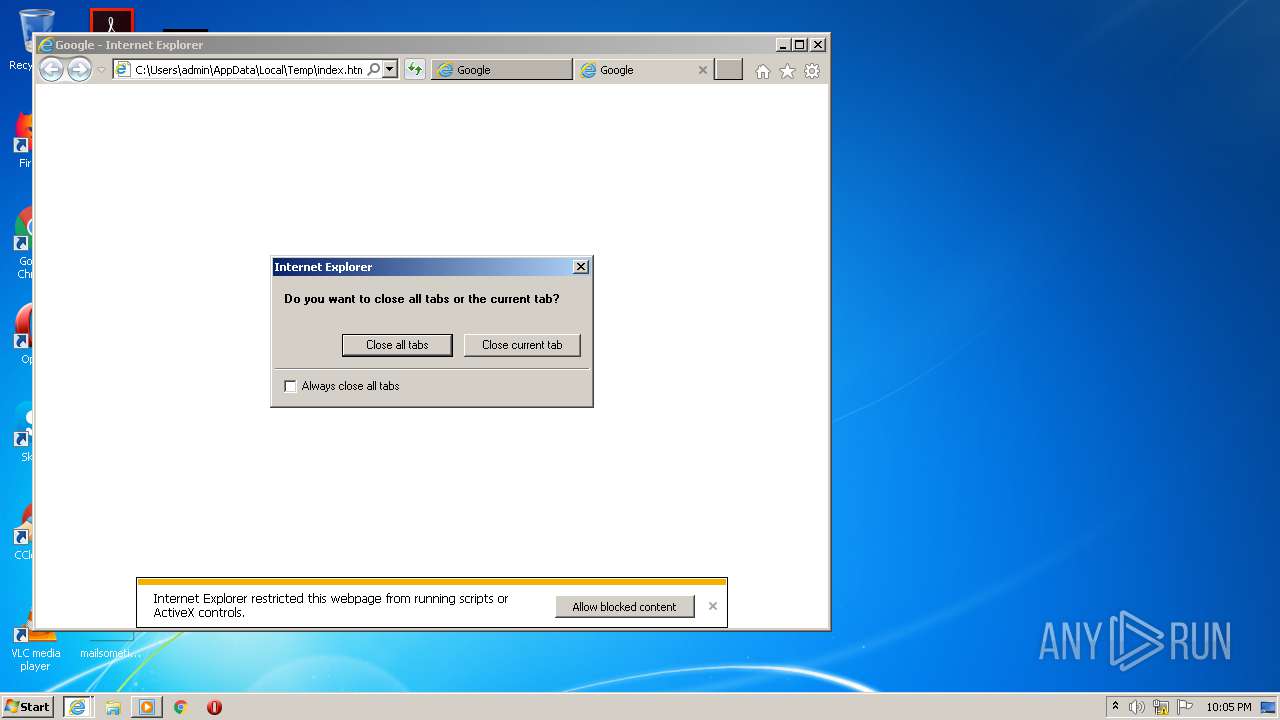
Application launched itself
- iexplore.exe (PID: 840)
- chrome.exe (PID: 2588)
- iexplore.exe (PID: 1084)
Adds / modifies Windows certificates
- iexplore.exe (PID: 840)
- iexplore.exe (PID: 1084)
Creates files in the user directory
- chrome.exe (PID: 2588)
- iexplore.exe (PID: 840)
Reads the hosts file
- chrome.exe (PID: 2588)
- chrome.exe (PID: 2412)
Changes settings of System certificates
- iexplore.exe (PID: 840)
- iexplore.exe (PID: 1084)
Reads settings of System Certificates
- iexplore.exe (PID: 840)
- iexplore.exe (PID: 1084)
Reads Internet Cache Settings
- iexplore.exe (PID: 840)
- iexplore.exe (PID: 3312)
Changes internet zones settings
- iexplore.exe (PID: 840)
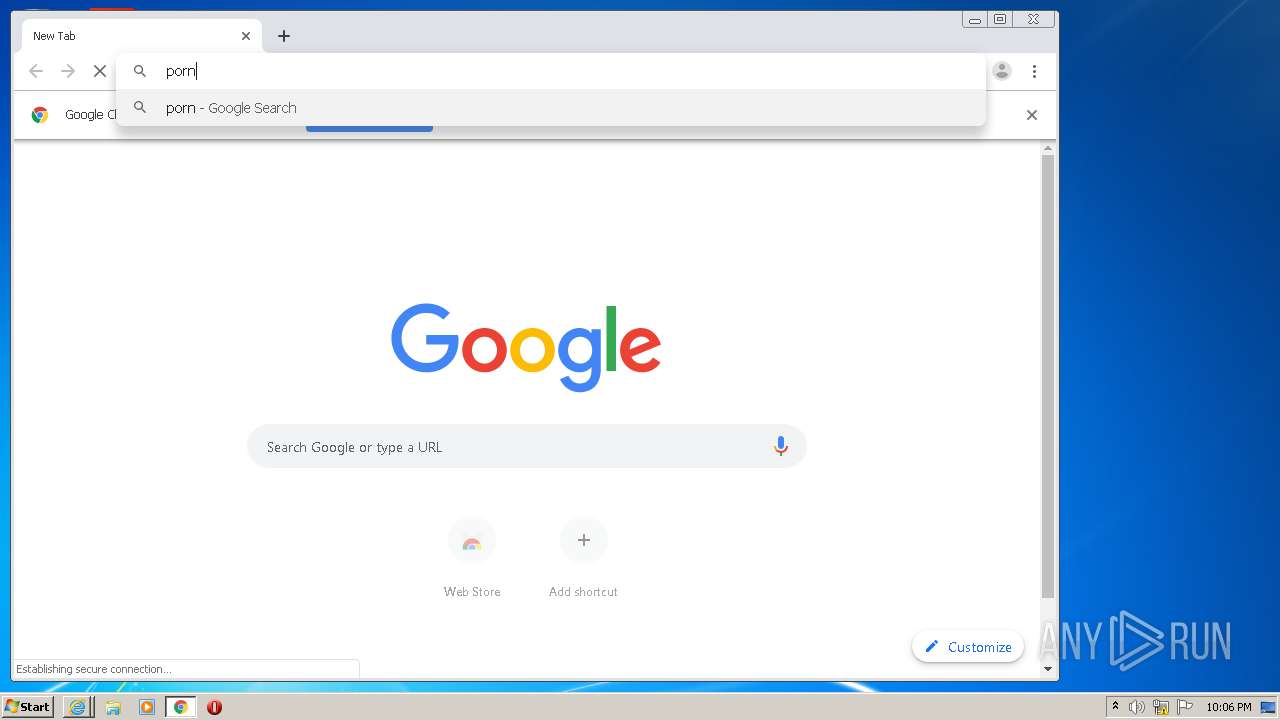
Manual execution by user
- chrome.exe (PID: 2588)
Reads internet explorer settings
- iexplore.exe (PID: 1084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
88
Monitored processes
52
Malicious processes
0
Suspicious processes
0
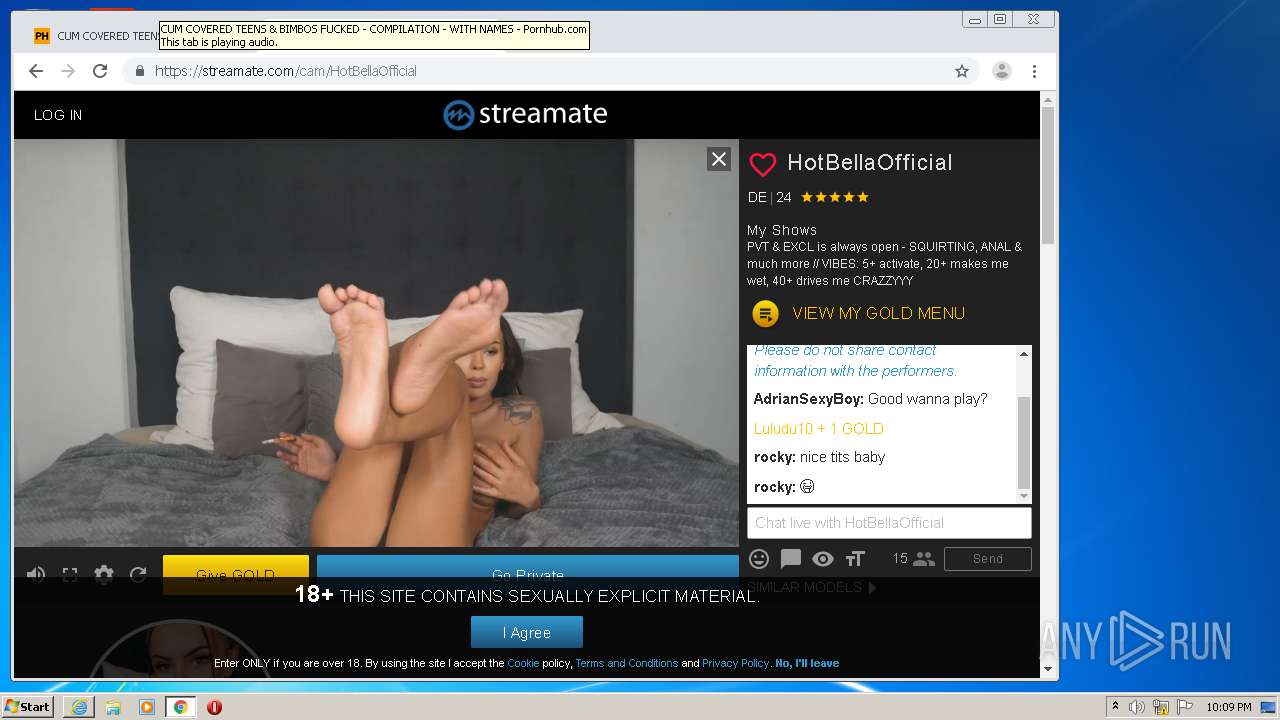
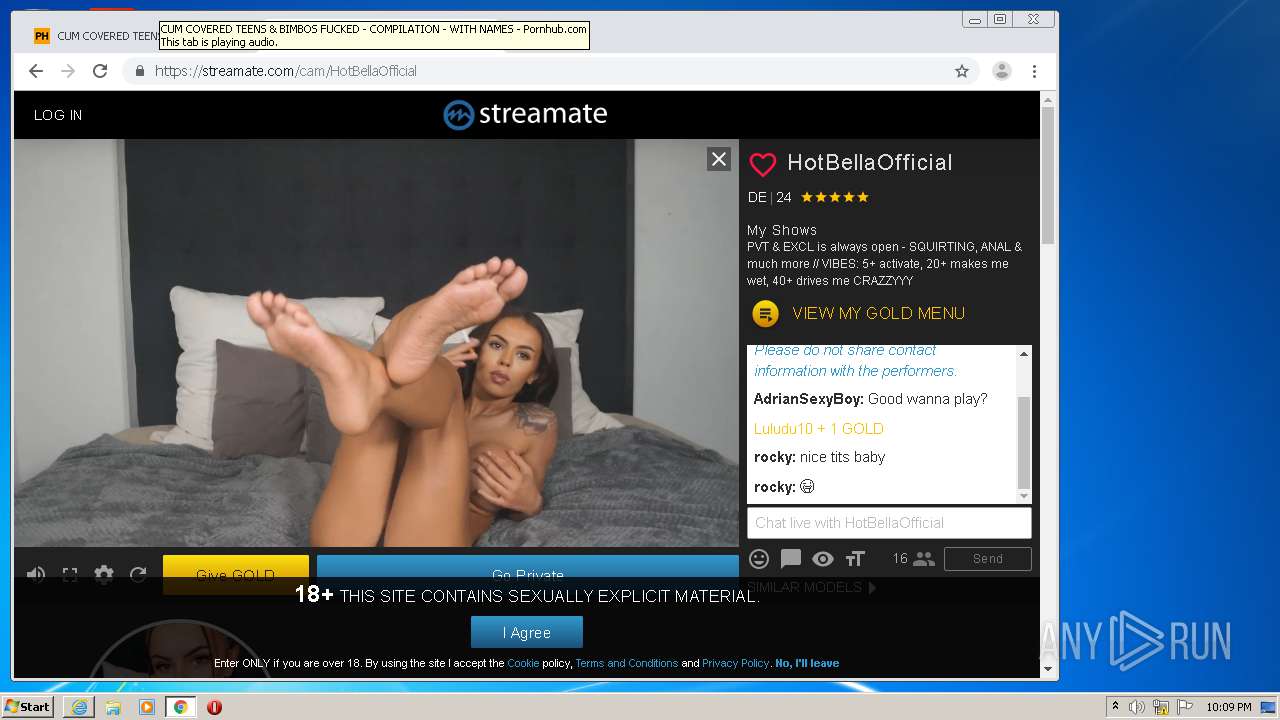
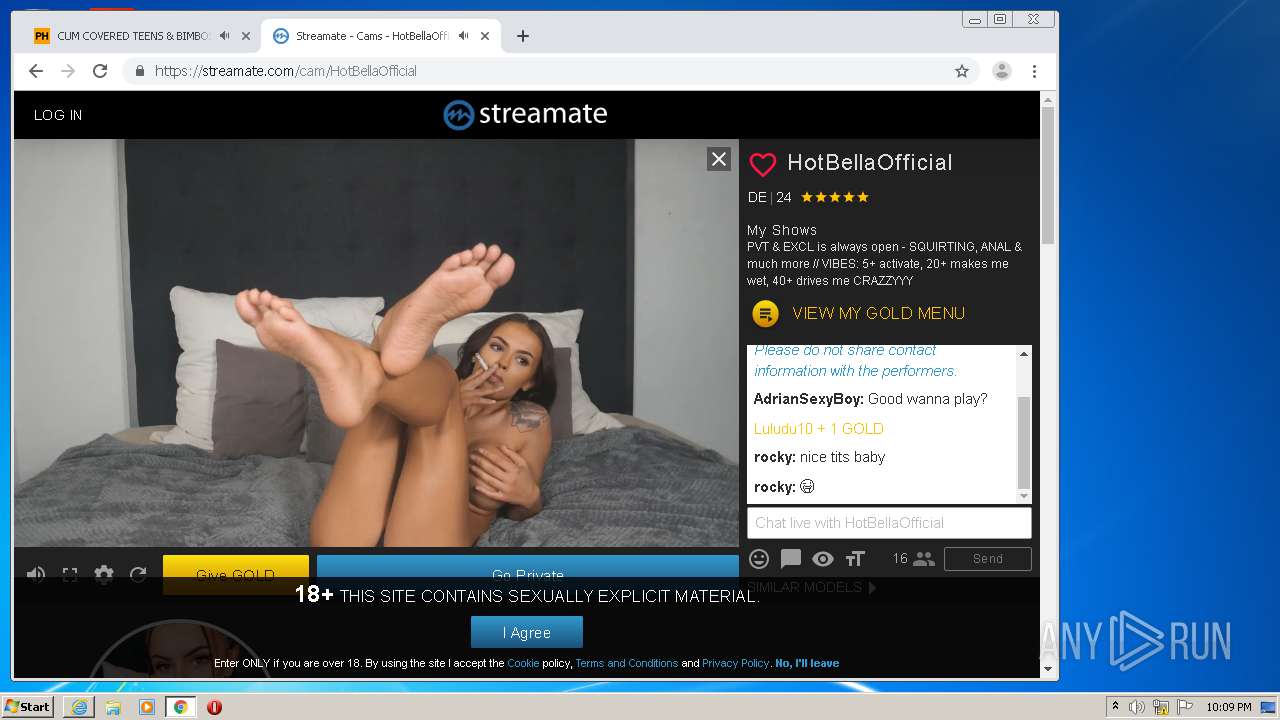
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16748415308282261181 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
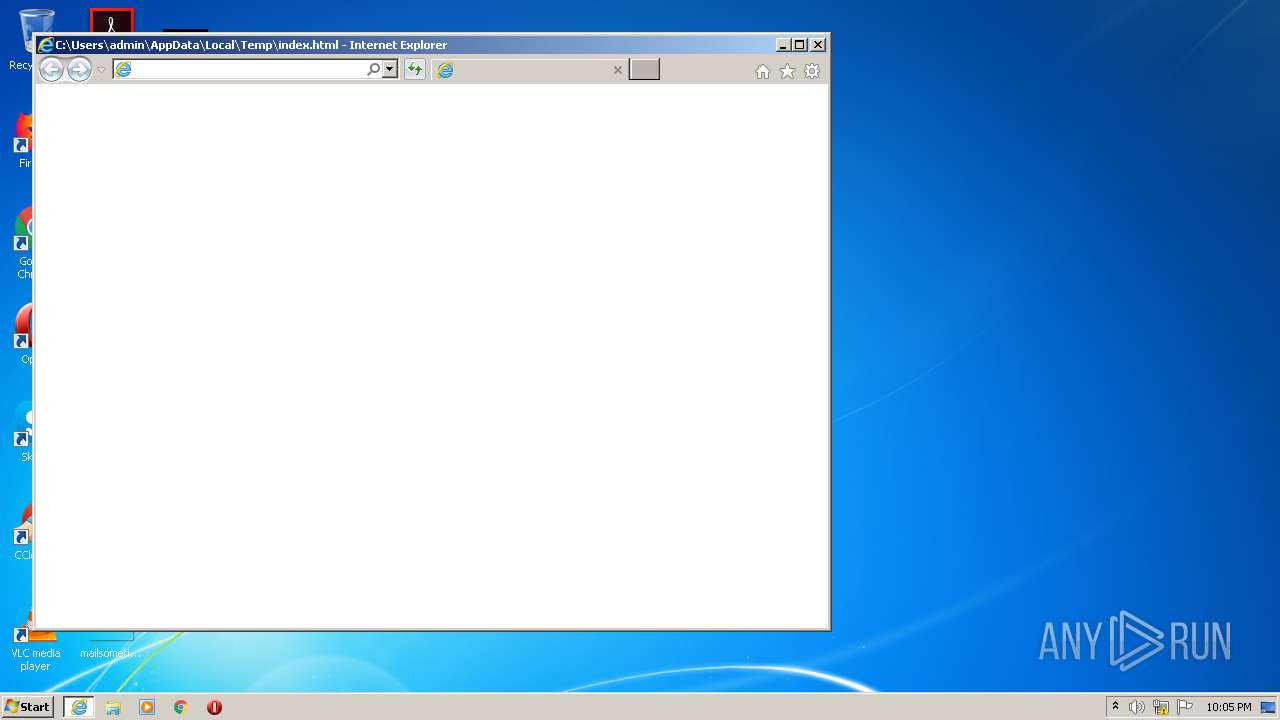
| 840 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2067981066436623624 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11274911010593975971 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8663444364350532966 --mojo-platform-channel-handle=4028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:840 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14881633628949950556 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16258601706341091391 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8461940859785944545 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16376422824298416400,14123202014622390295,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11047211638928086589 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 798
Read events
1 574
Write events
215
Delete events
9
Modification events
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3809705542 | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30838673 | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
336
Text files
365
Unknown types
232
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabE805.tmp | — | |
MD5:— | SHA256:— | |||
| 1084 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarE806.tmp | — | |
MD5:— | SHA256:— | |||
| 840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fd0466e4-4102-4307-8ef4-c489f8880e6c.tmp | — | |
MD5:— | SHA256:— | |||
| 2588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 1084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 1084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_7A97AA4A9353D3BAC496995B4E415D5E | der | |
MD5:— | SHA256:— | |||
| 1084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_7A97AA4A9353D3BAC496995B4E415D5E | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
269
DNS requests
151
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1084 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2412 | chrome.exe | GET | 200 | 74.125.173.25:80 | http://r3---sn-4g5e6nld.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=185.128.27.151&mm=28&mn=sn-4g5e6nld&ms=nvh&mt=1600635853&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
1084 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBnDSwYD0b%2FmAgAAAAB5ZF4%3D | US | der | 471 b | whitelisted |
2412 | chrome.exe | GET | 200 | 143.204.208.65:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/cleanPeppermint_7a82f1f3/style.css | US | text | 571 b | shared |
2412 | chrome.exe | GET | 200 | 143.204.208.65:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/assets/style.css | US | text | 343 b | shared |
1084 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
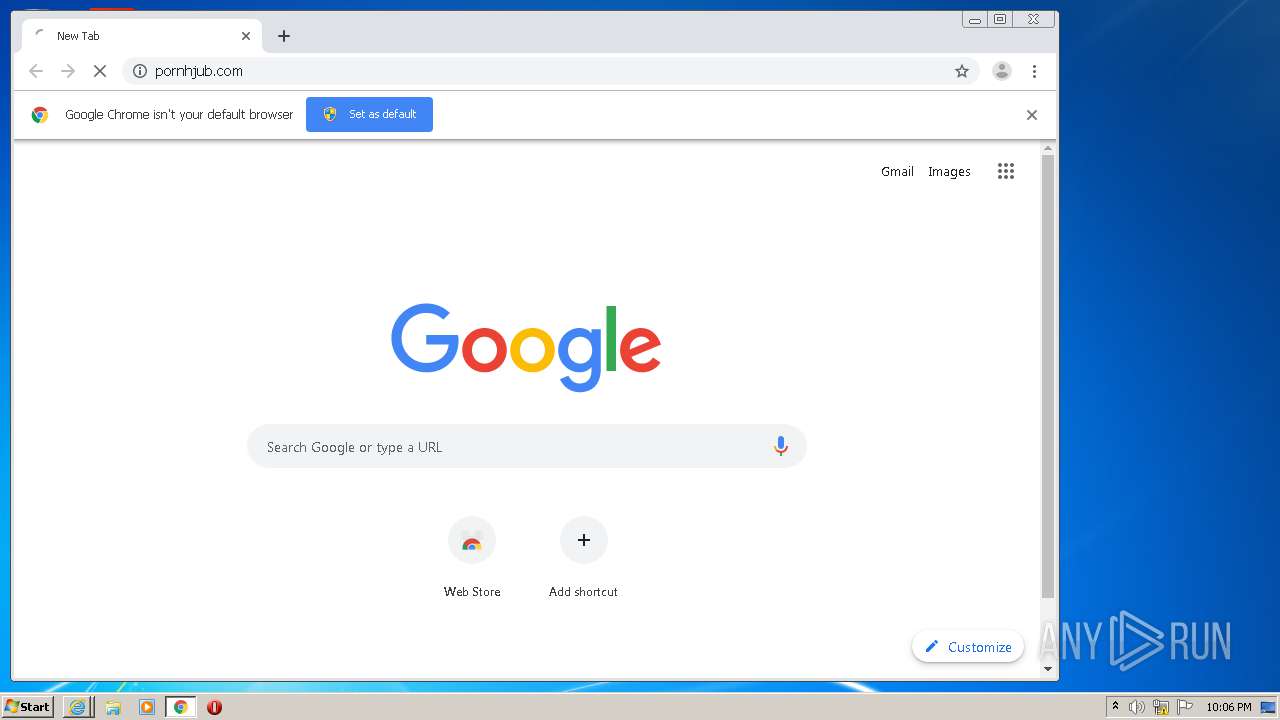
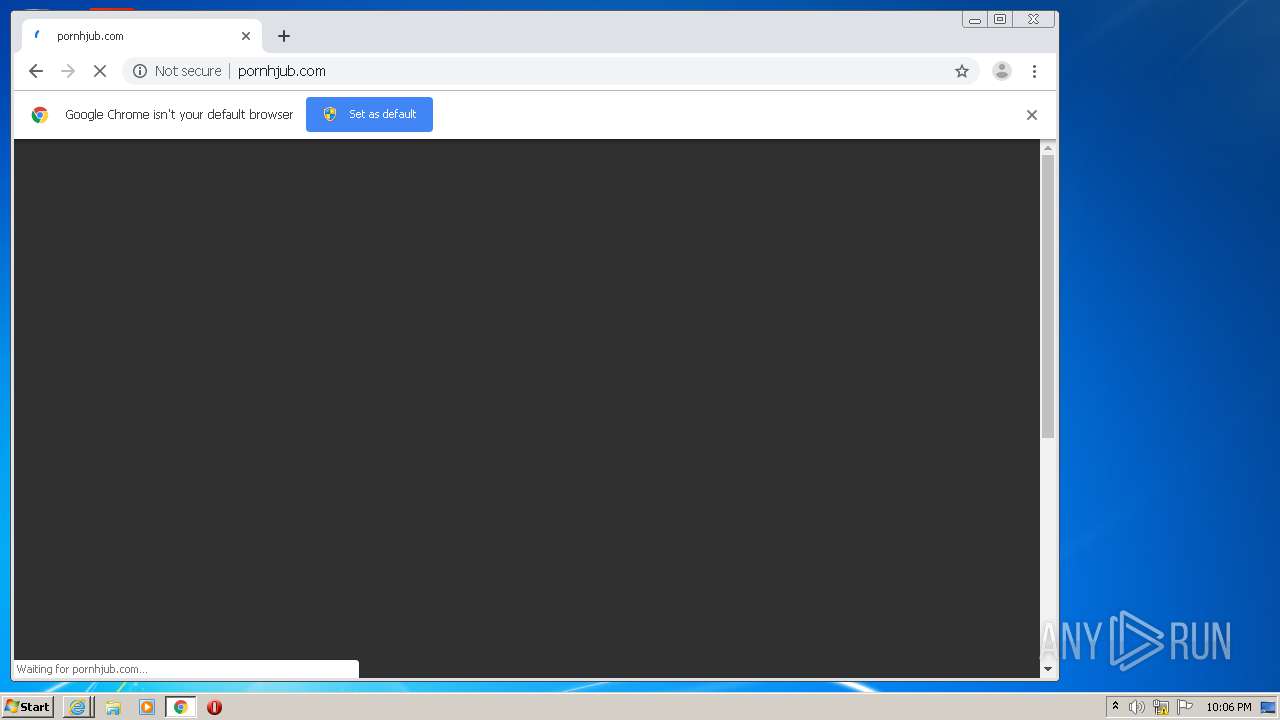
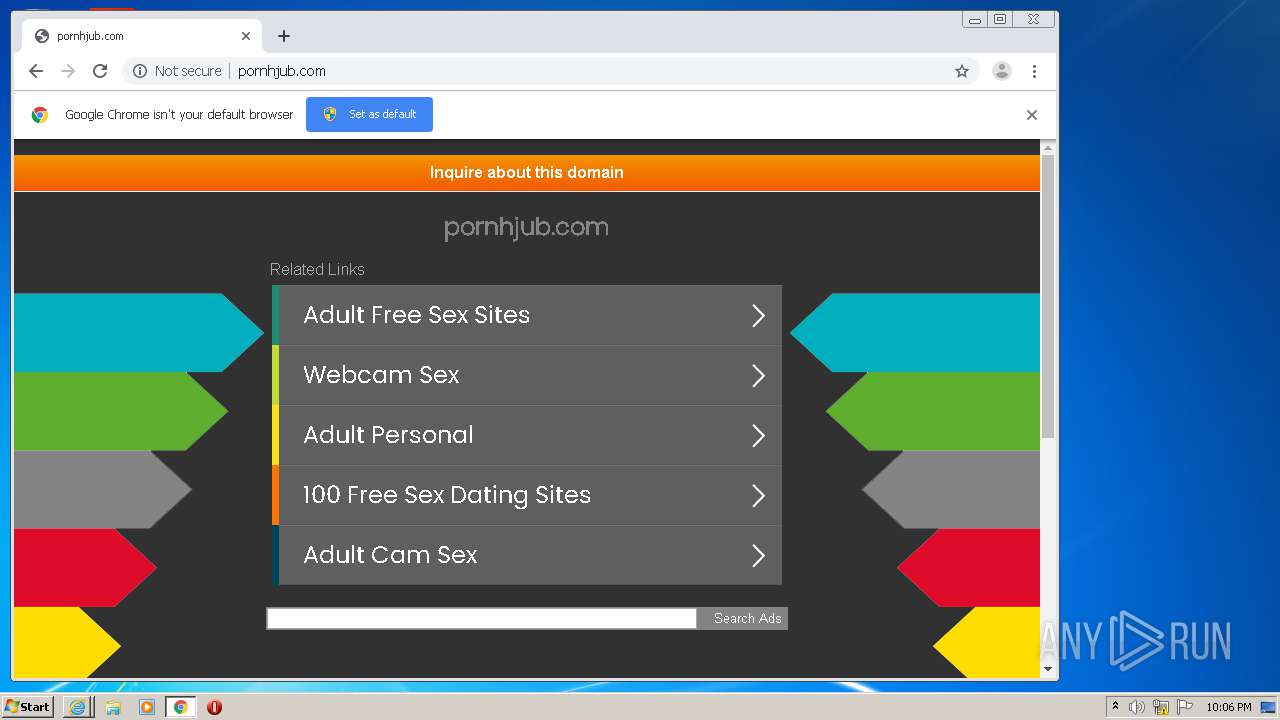
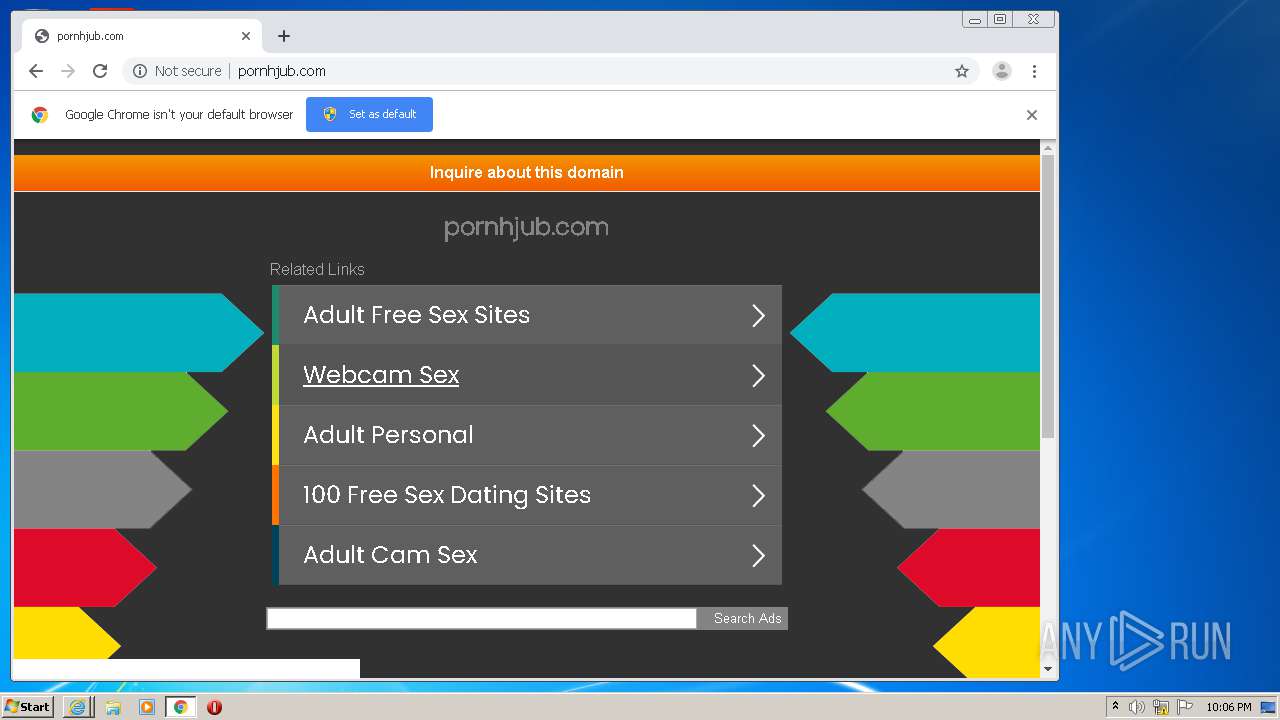
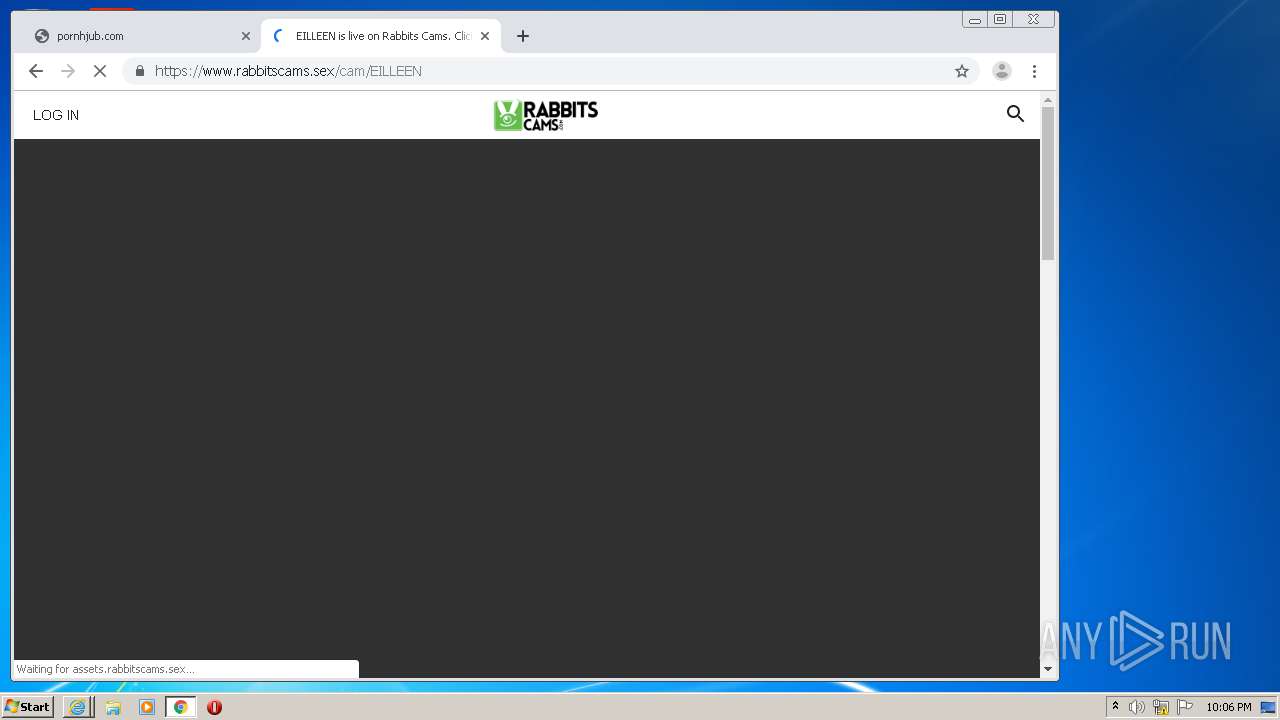
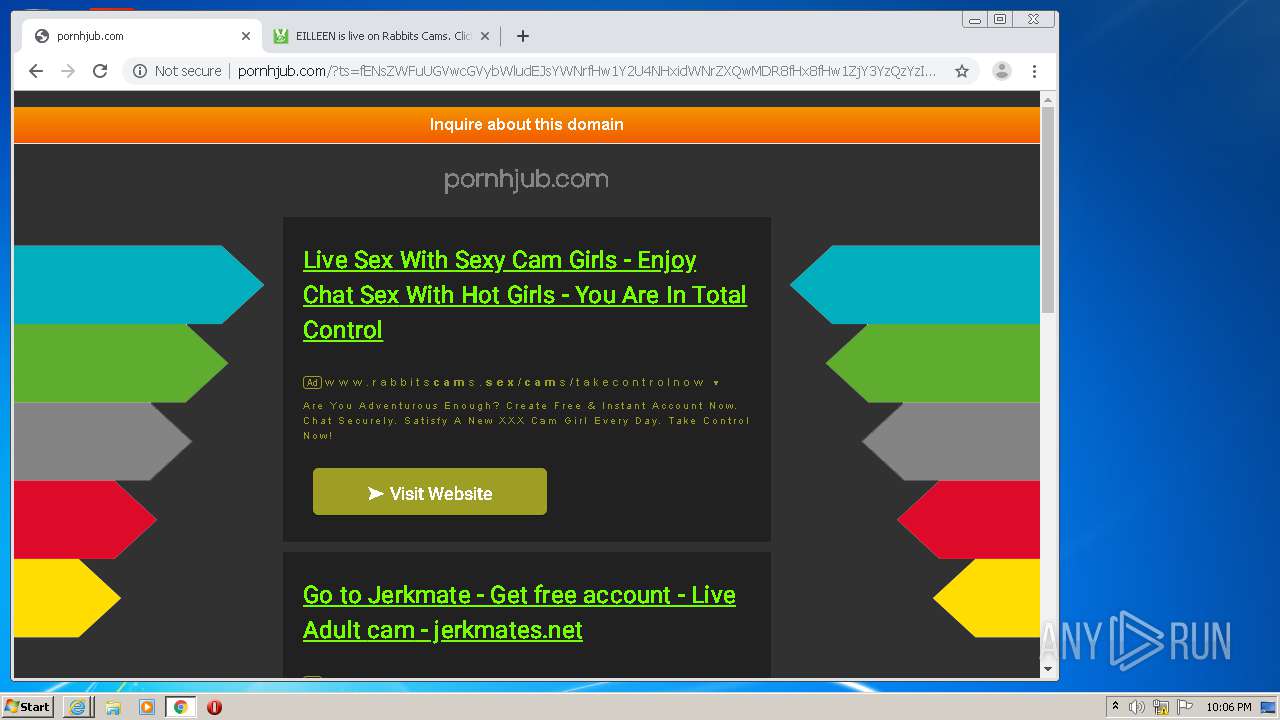
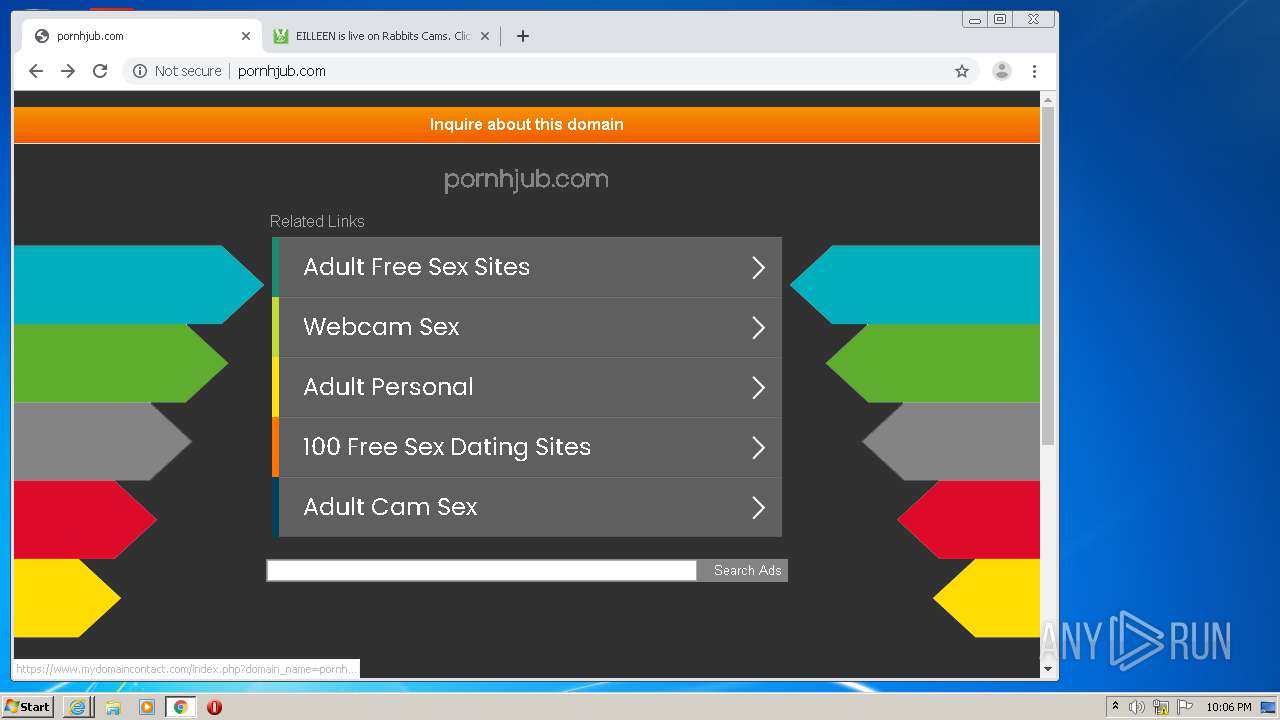
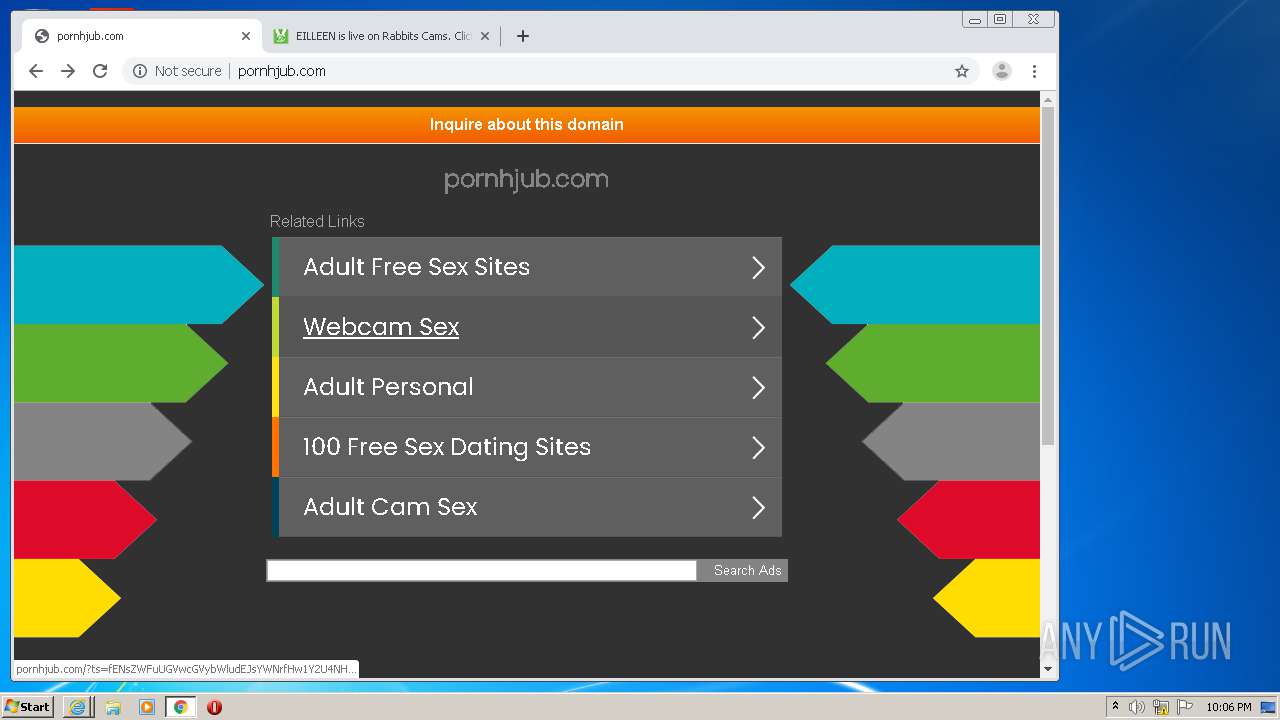
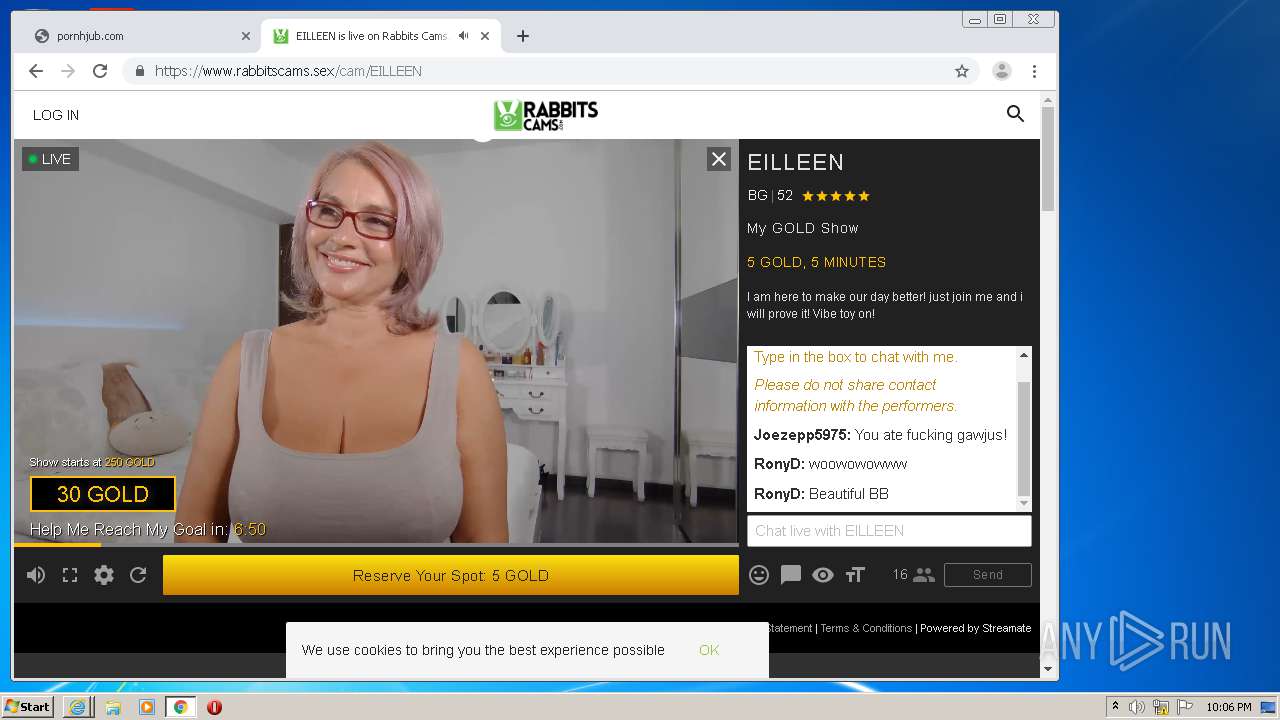
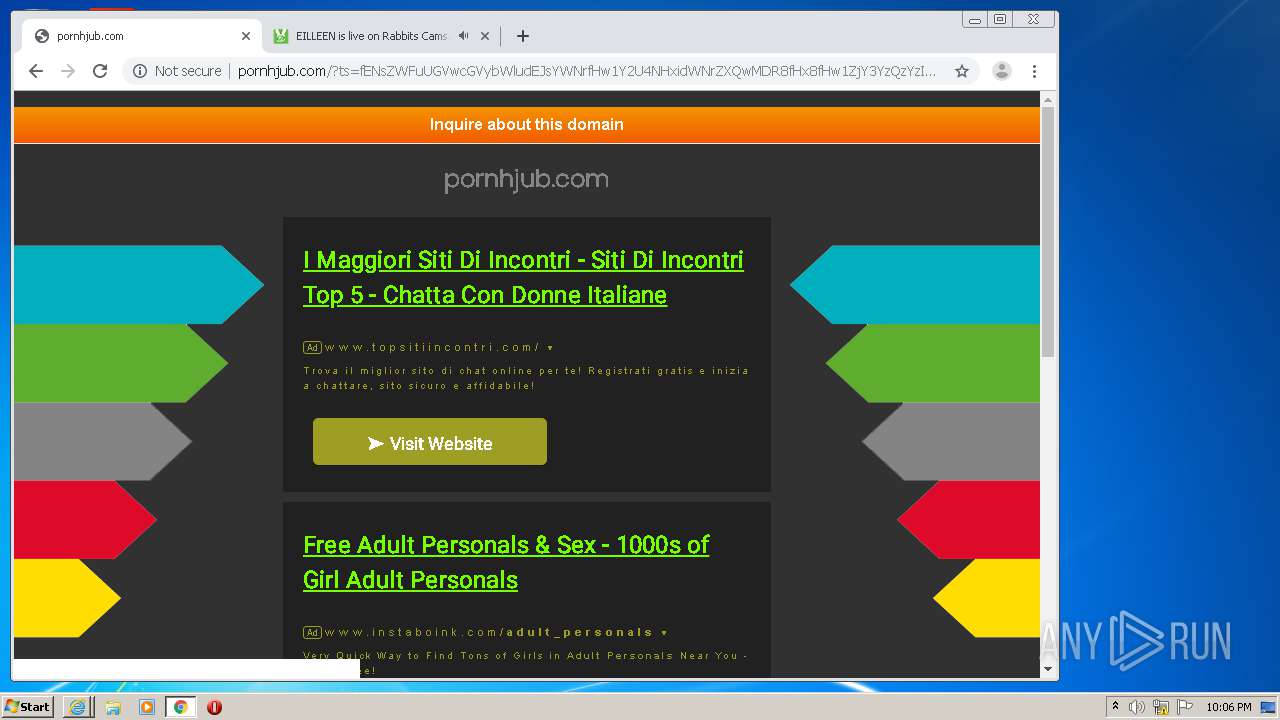
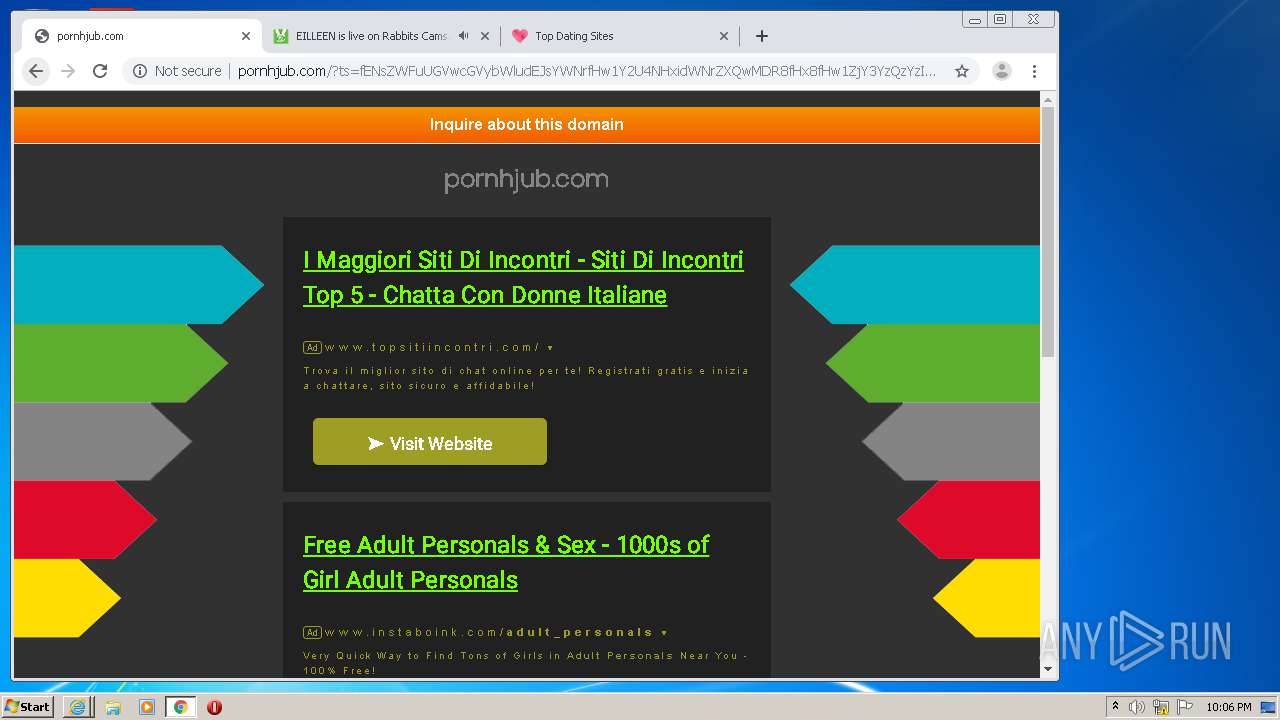
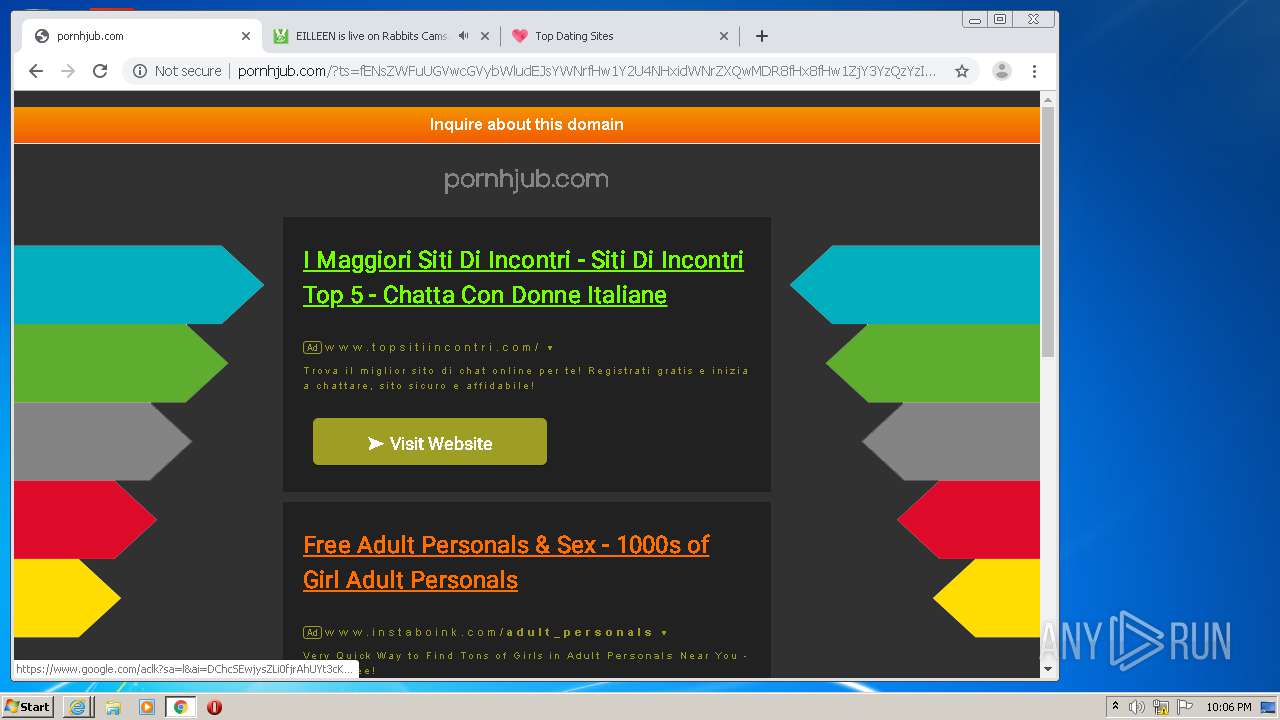
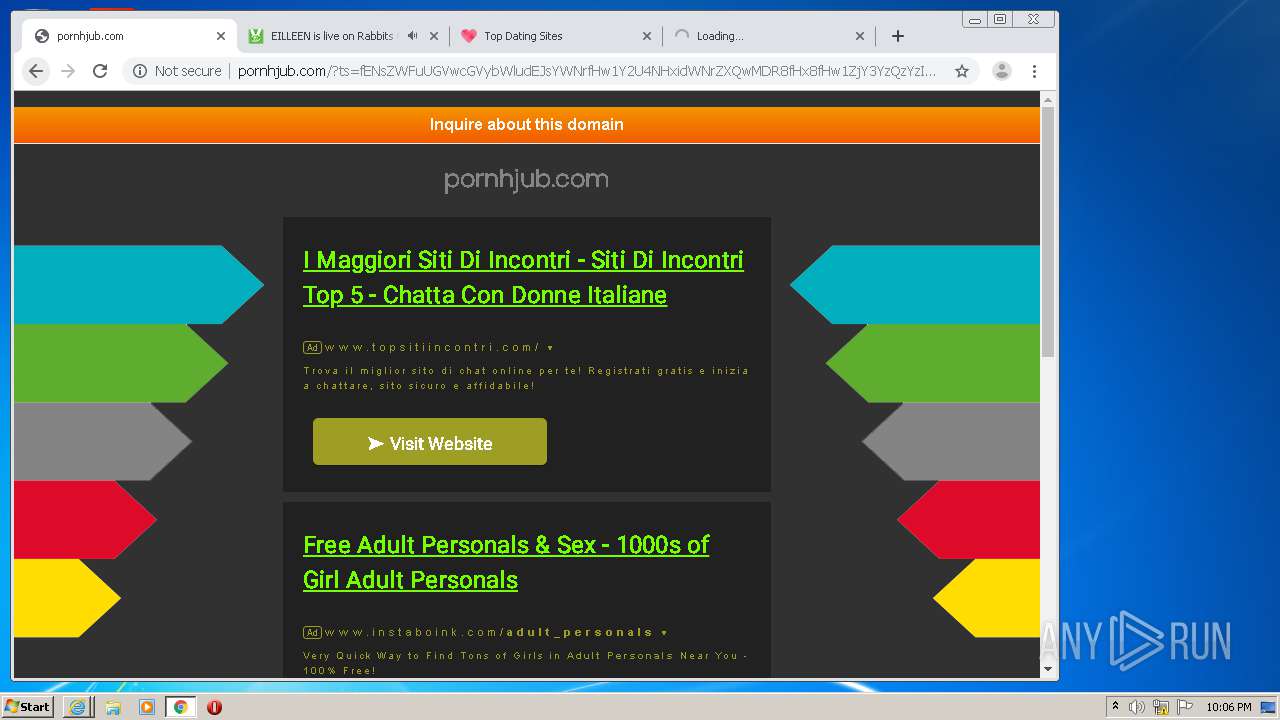
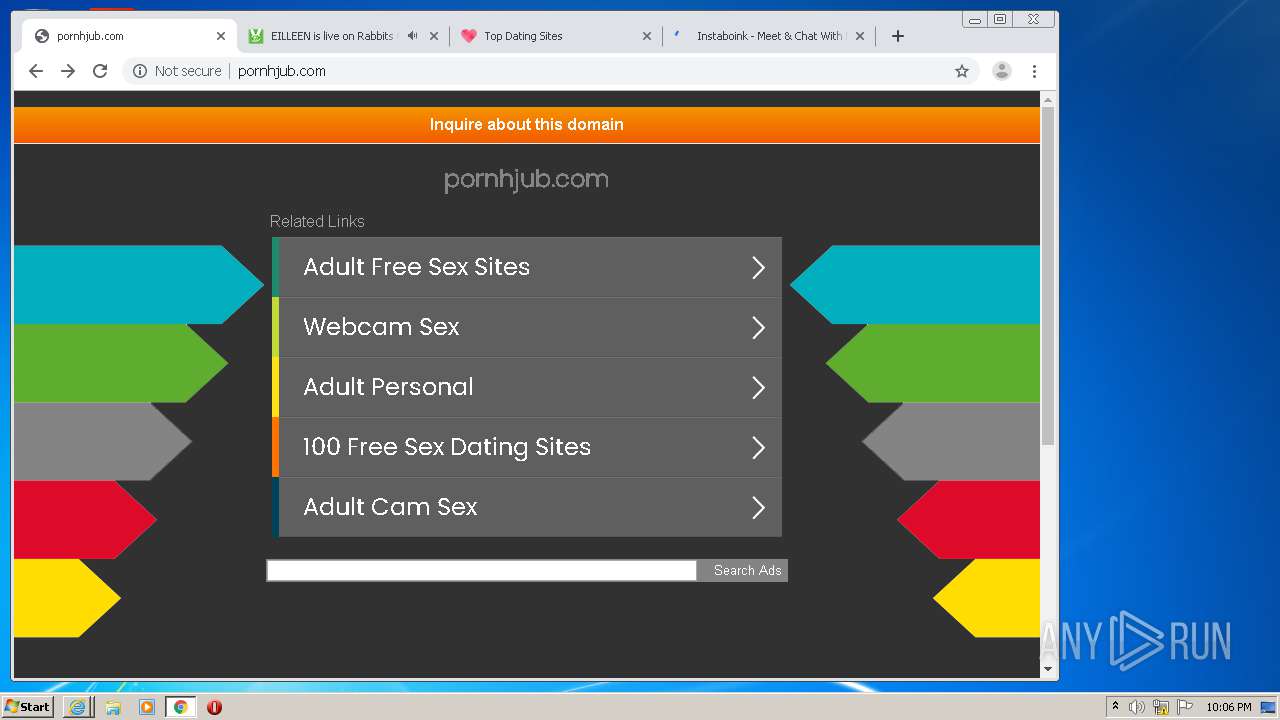
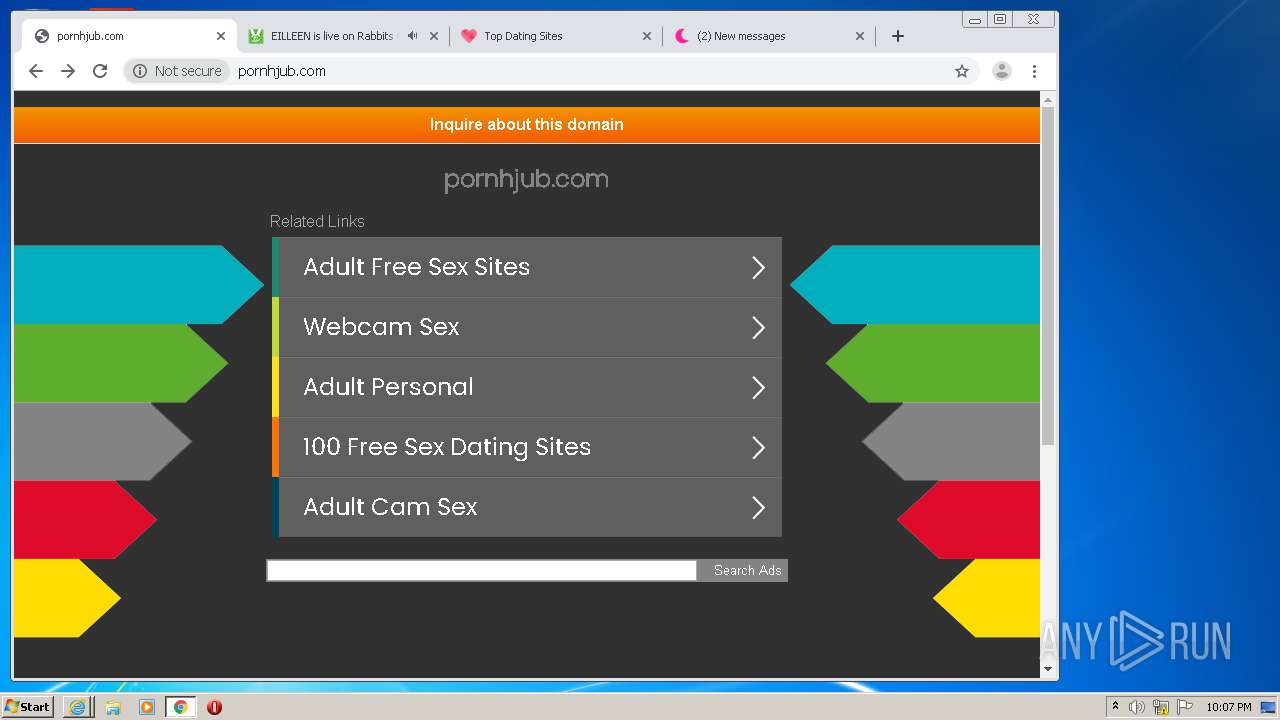
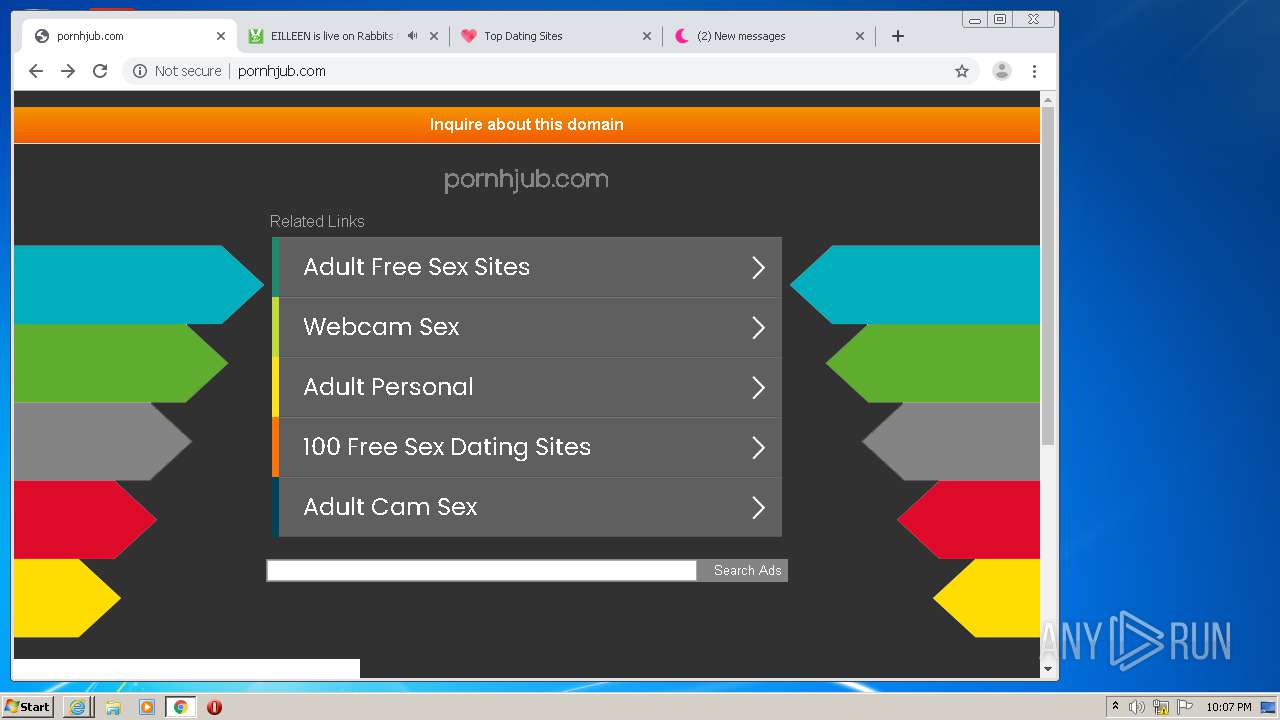
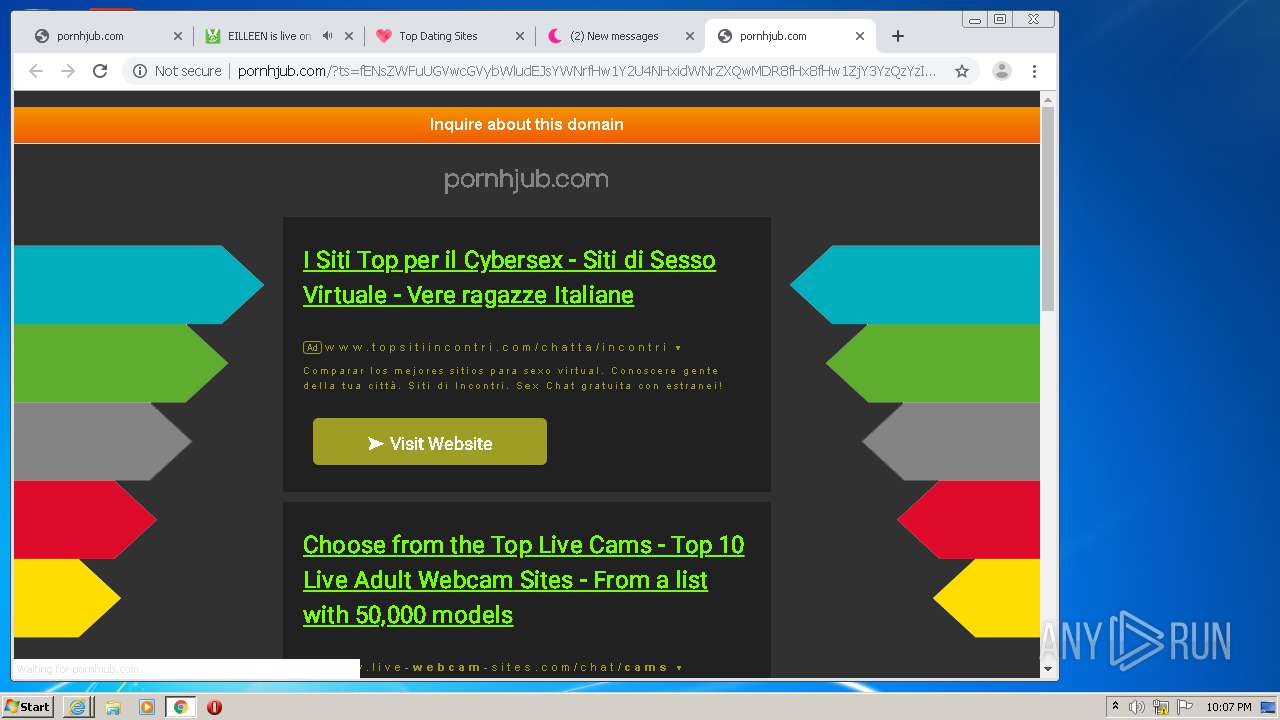
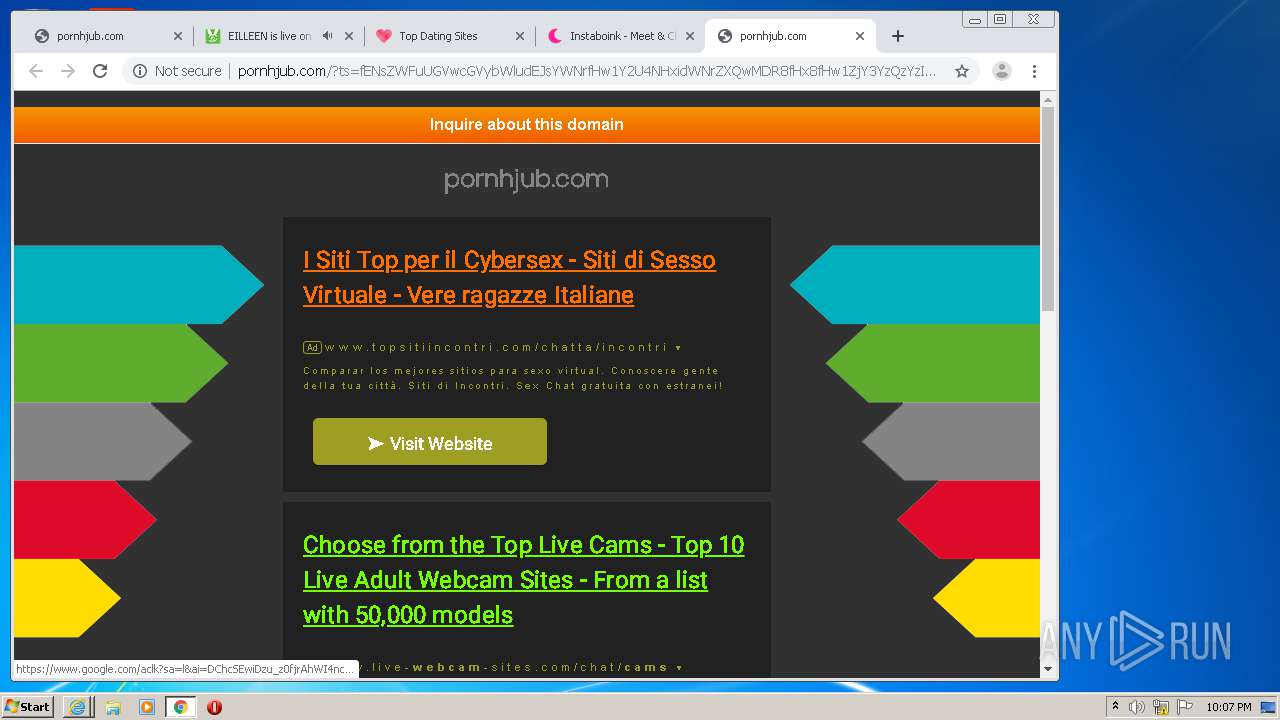
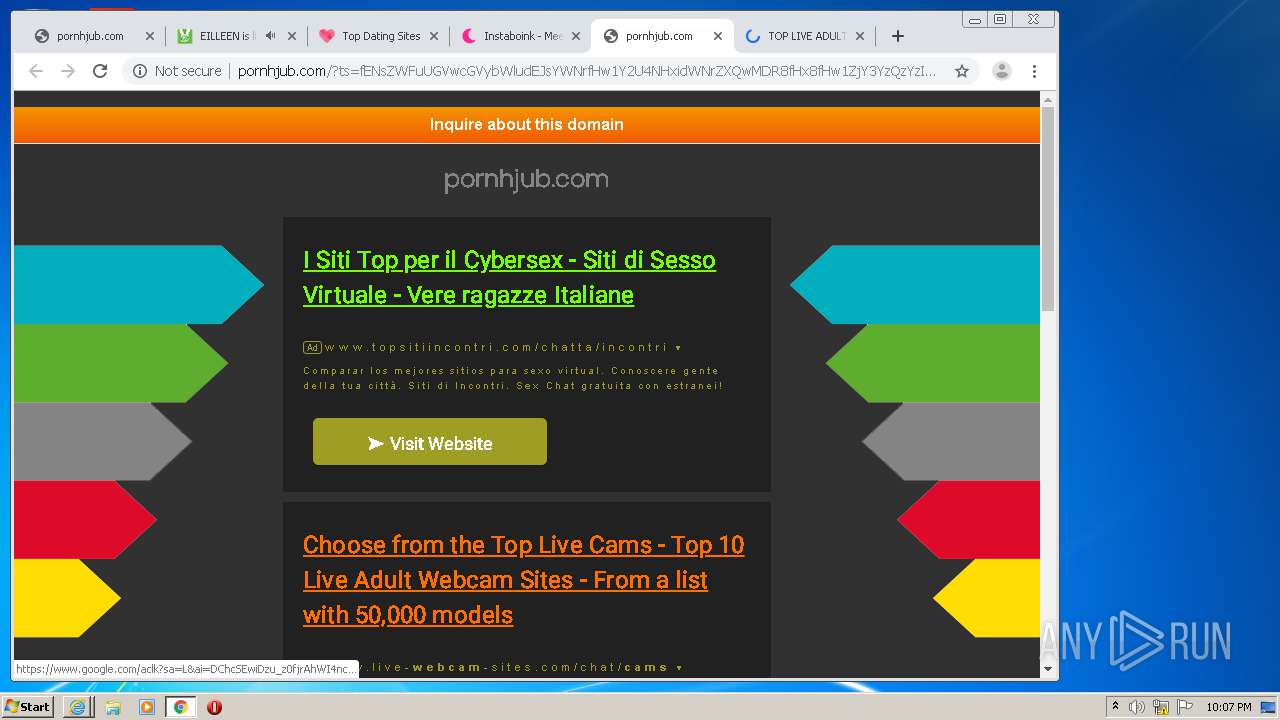
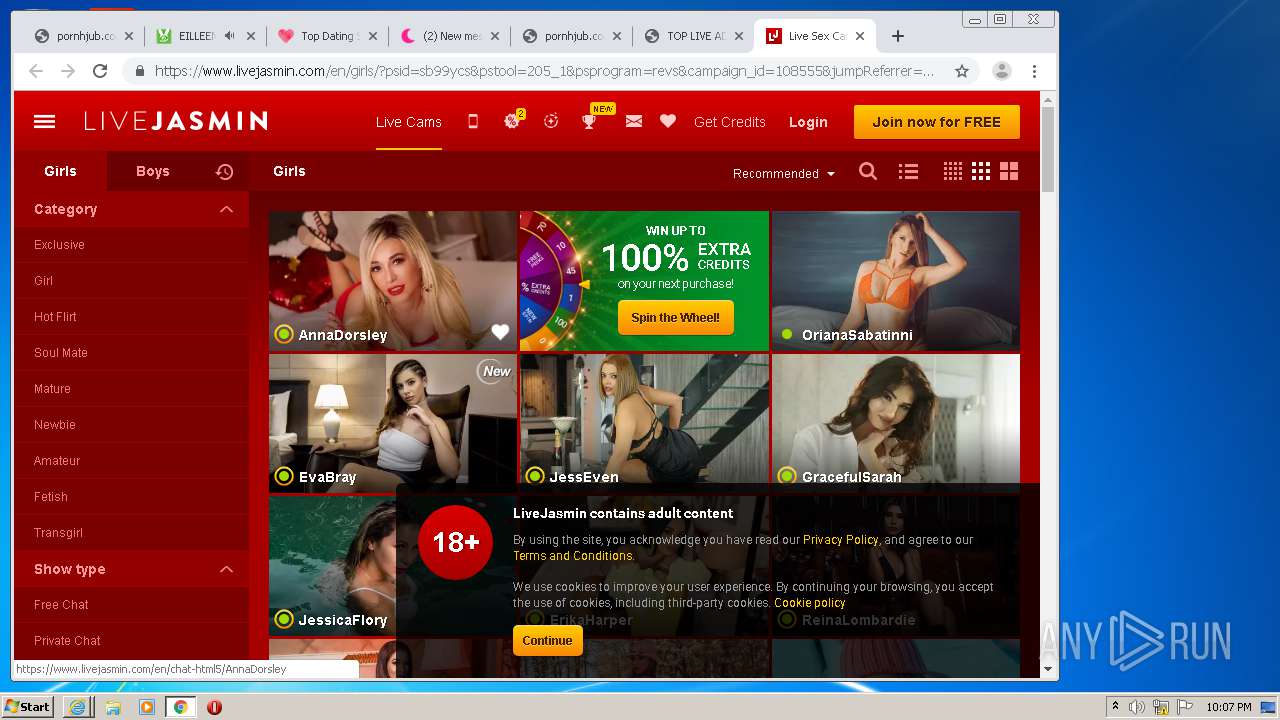
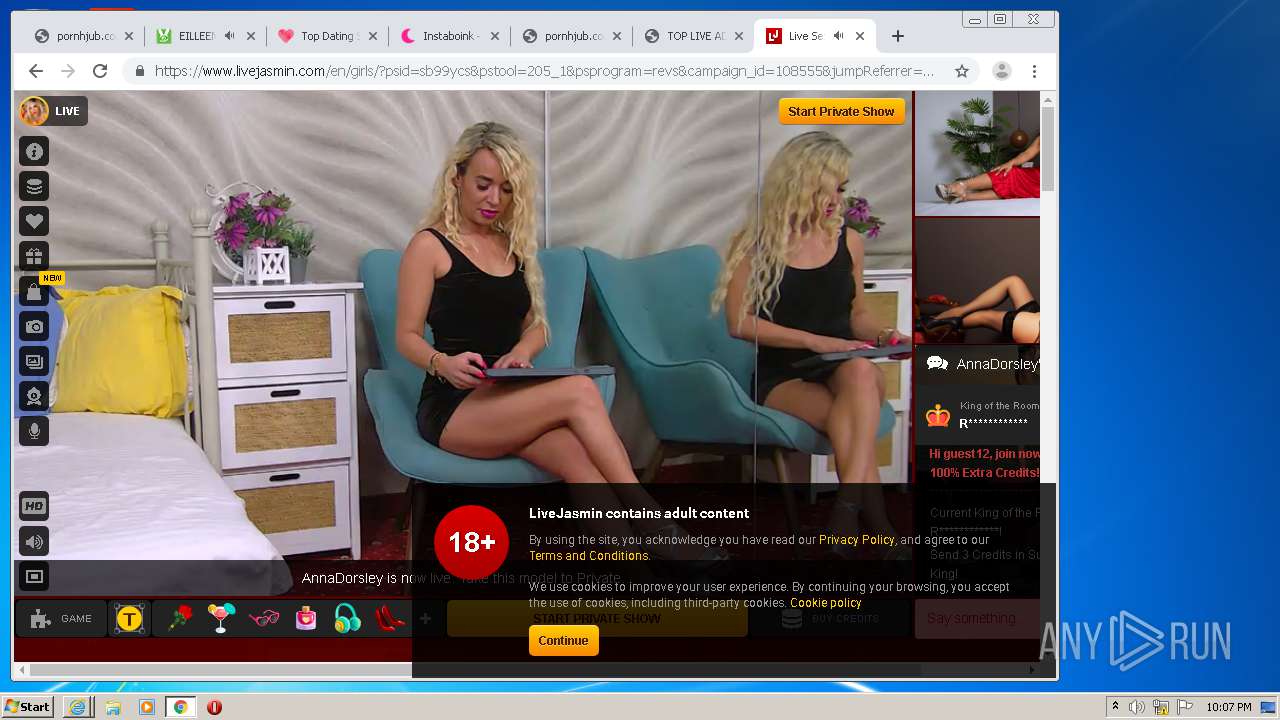
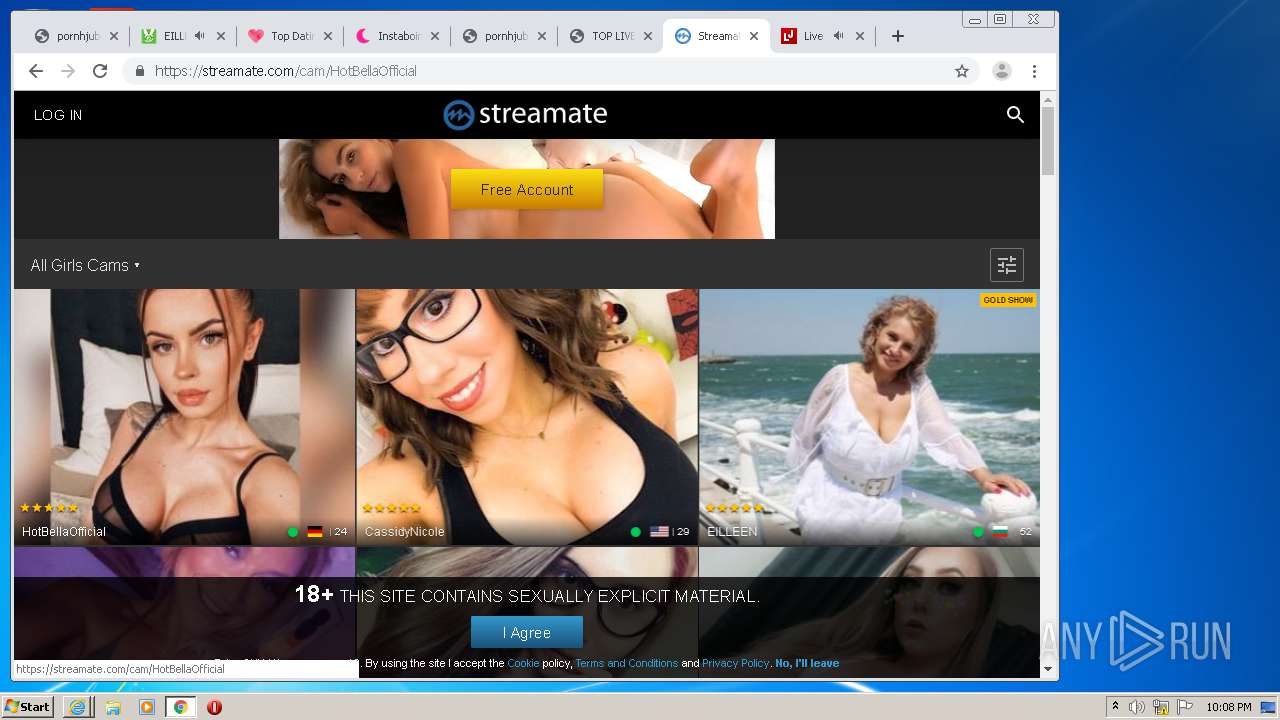
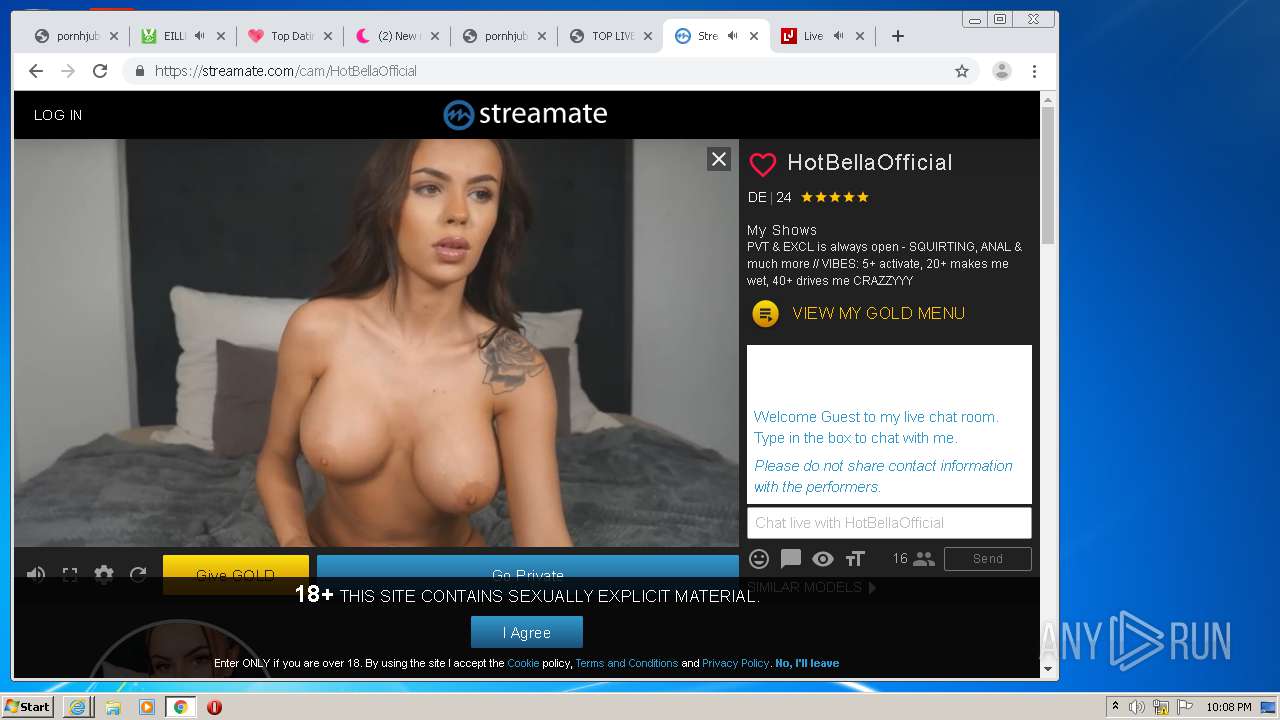
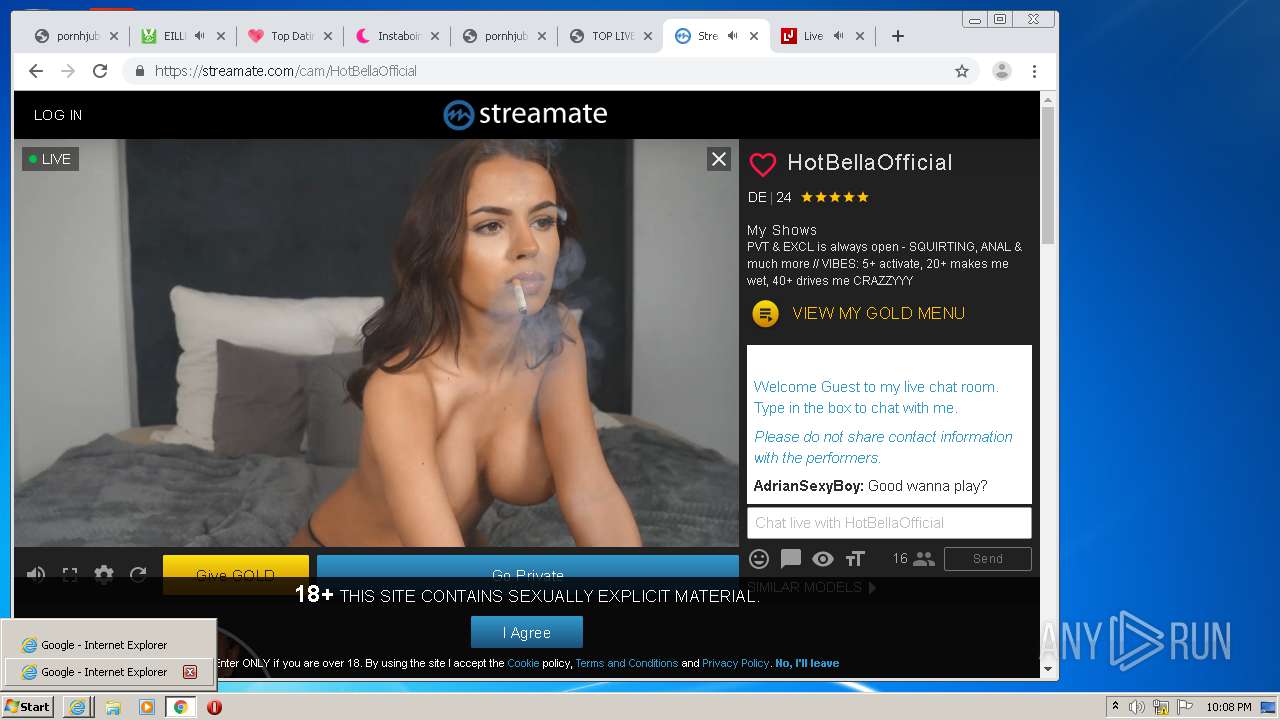
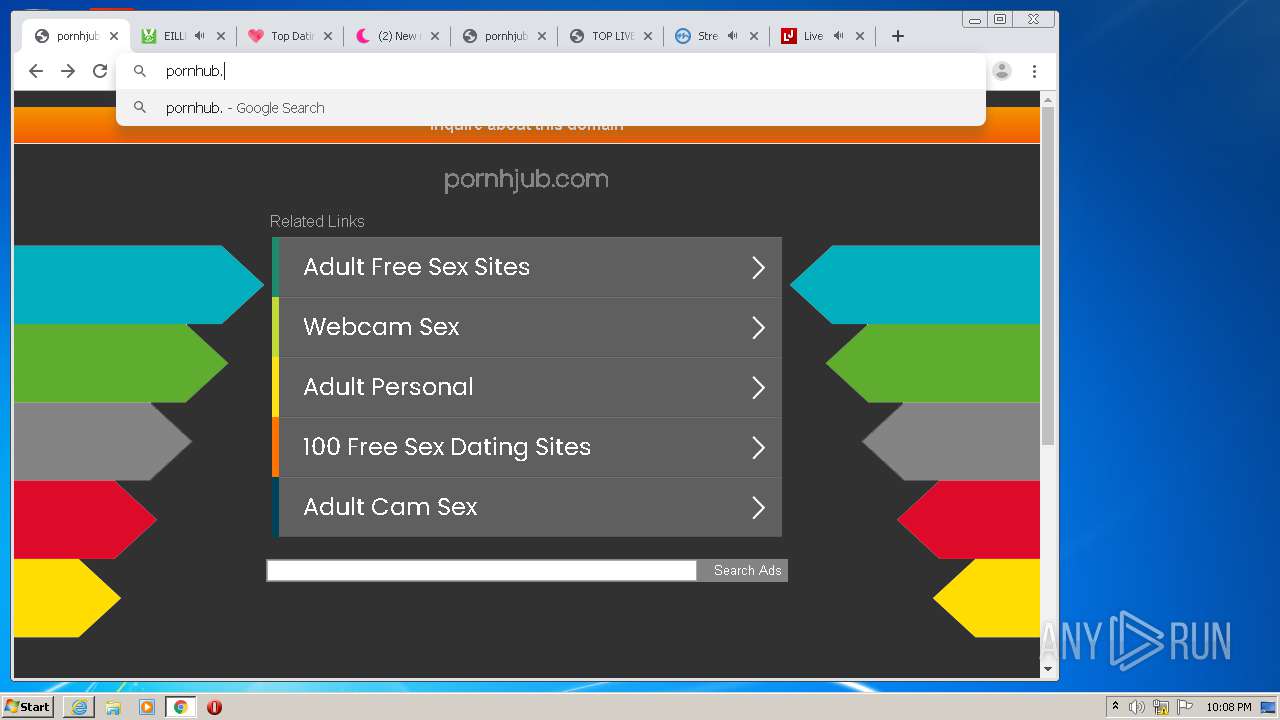
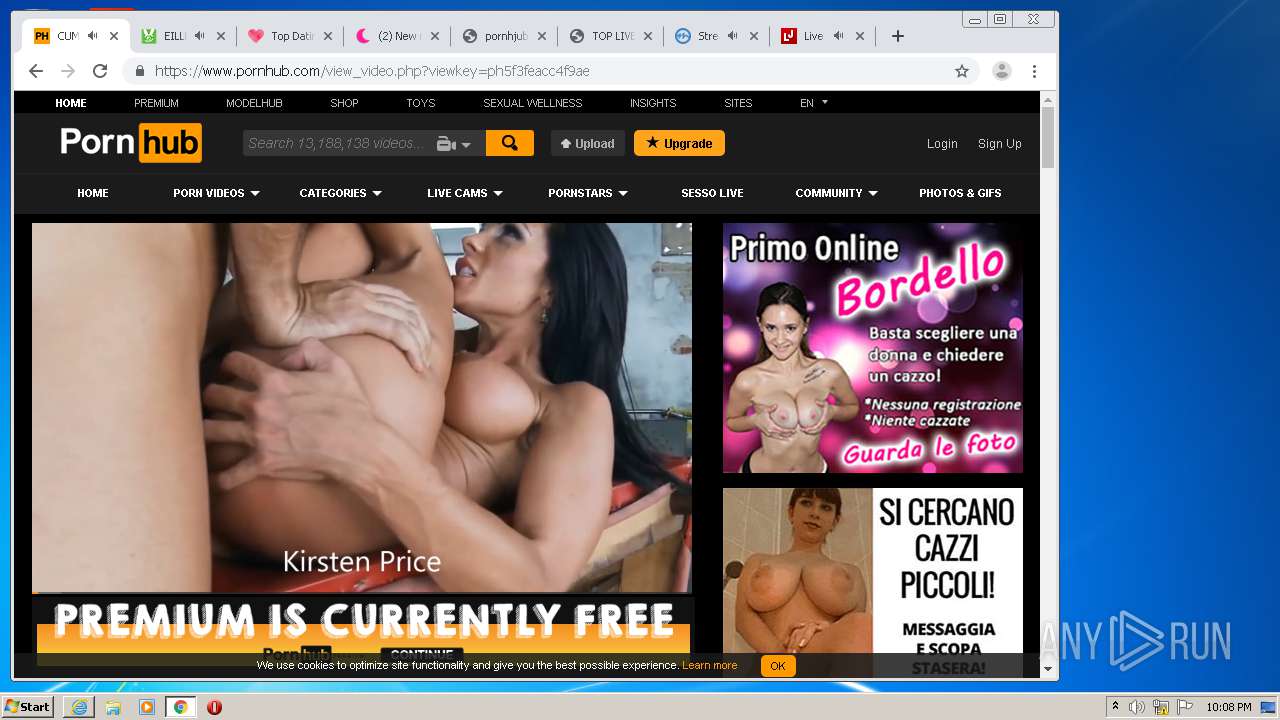
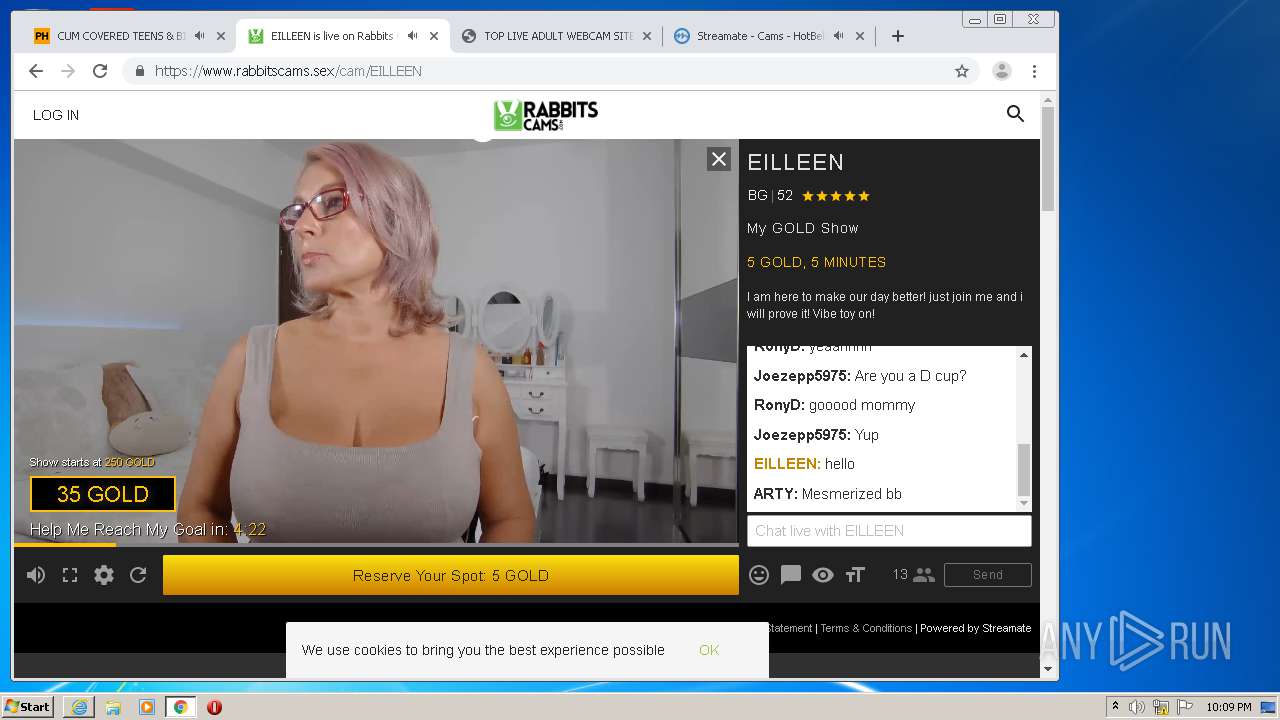
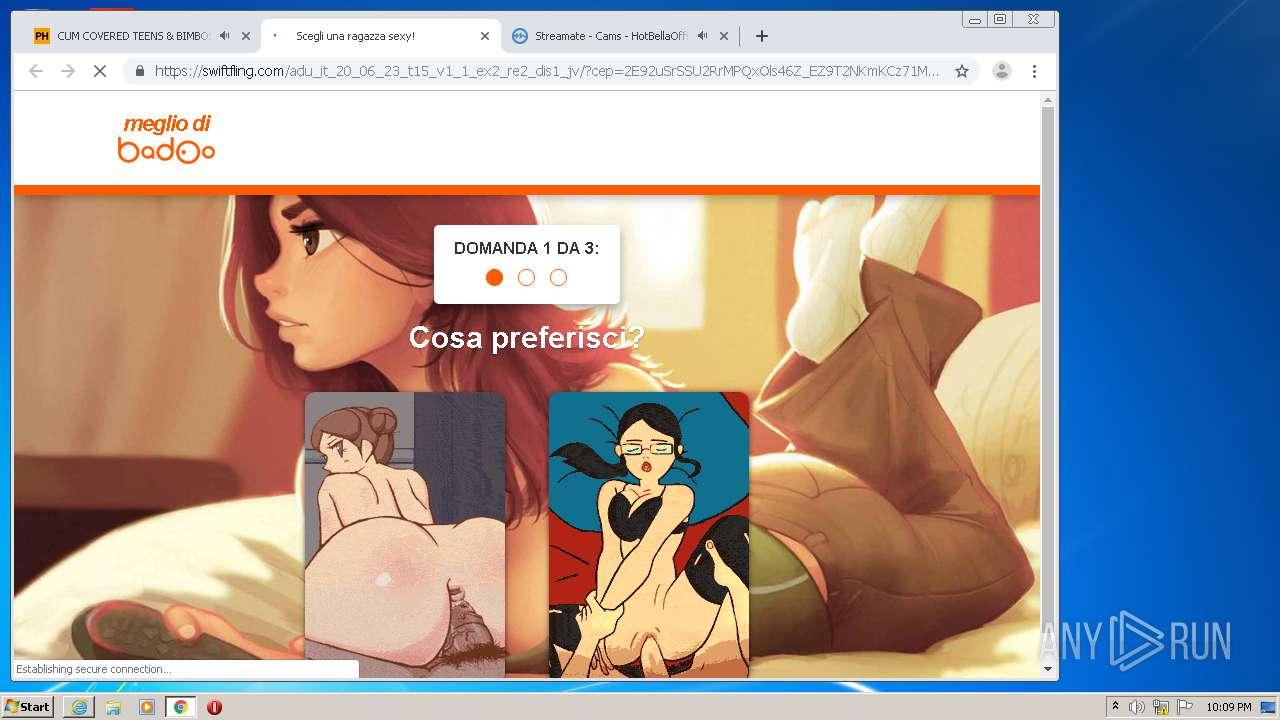
2412 | chrome.exe | GET | 200 | 104.247.81.132:80 | http://pornhjub.com/ | CA | html | 4.96 Kb | unknown |
2412 | chrome.exe | GET | 200 | 143.204.208.65:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/saledefault.css | US | text | 1.48 Kb | shared |
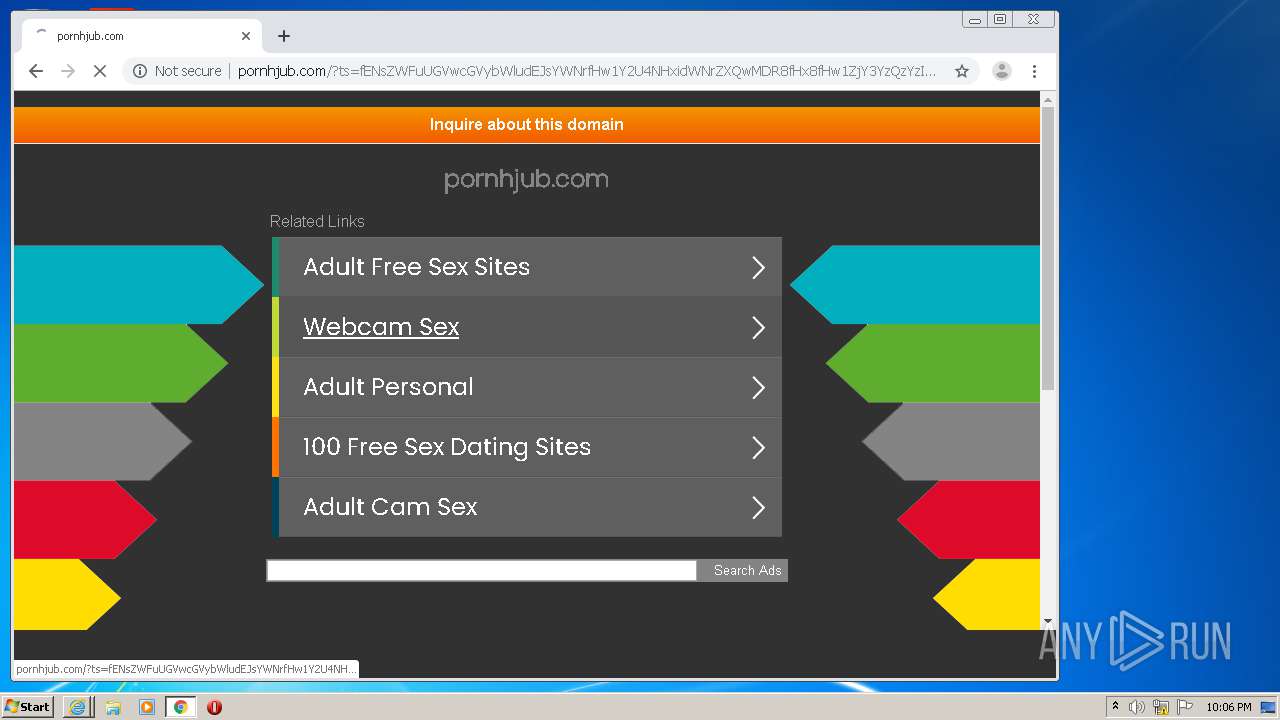
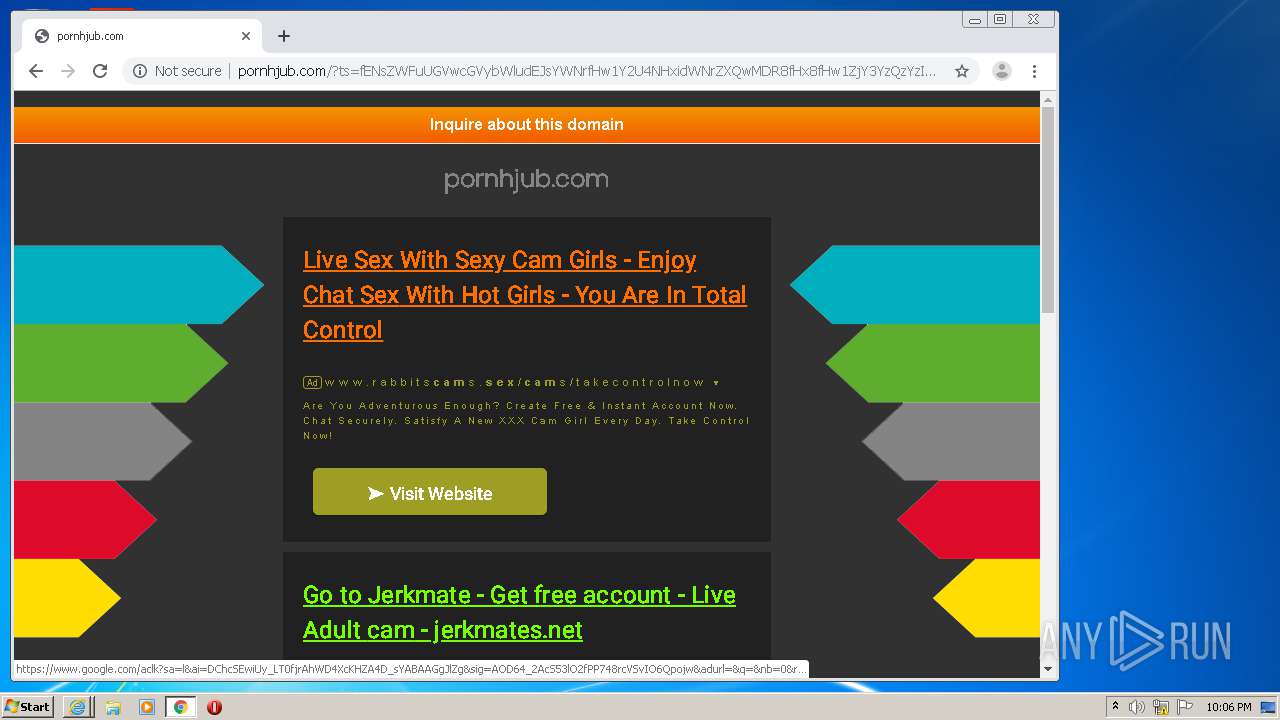
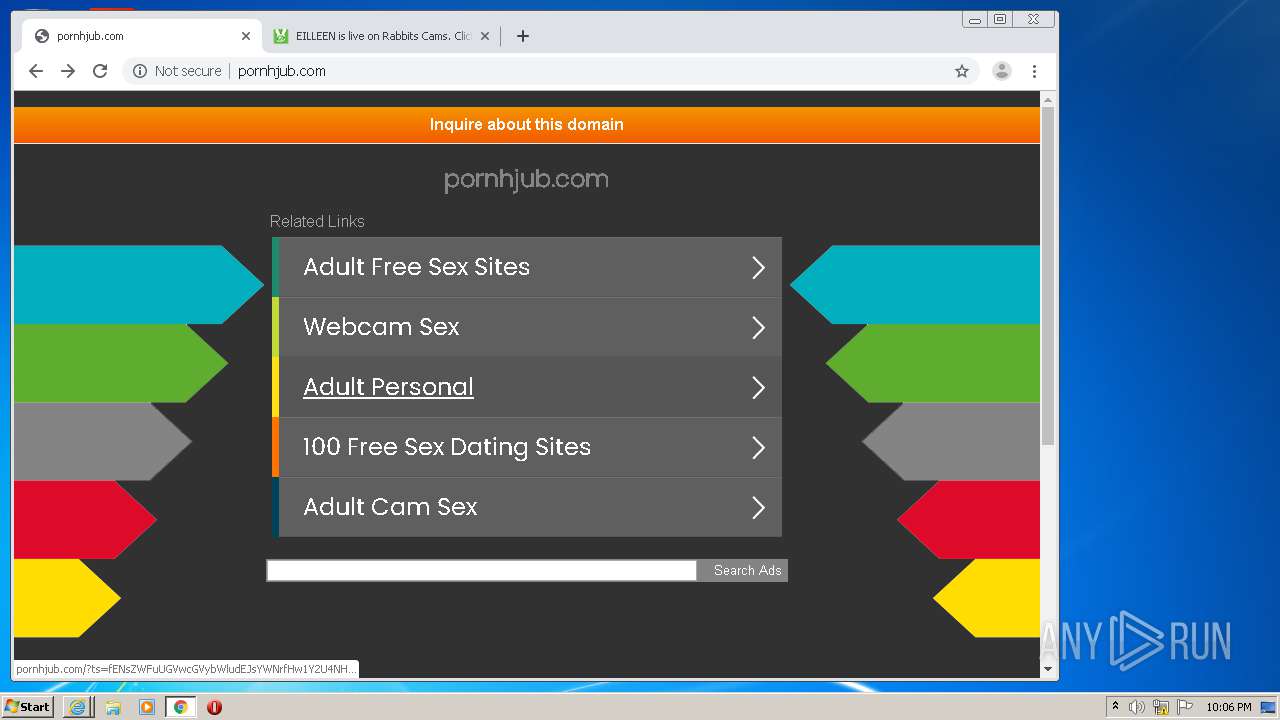
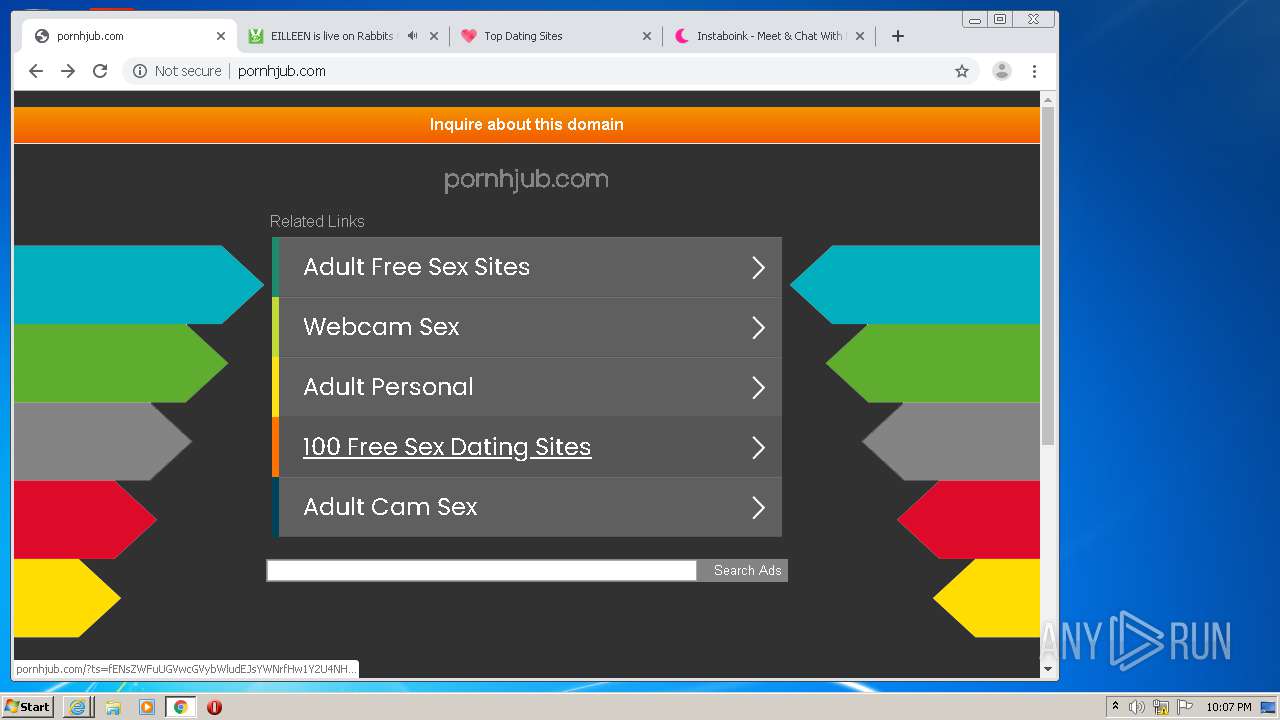
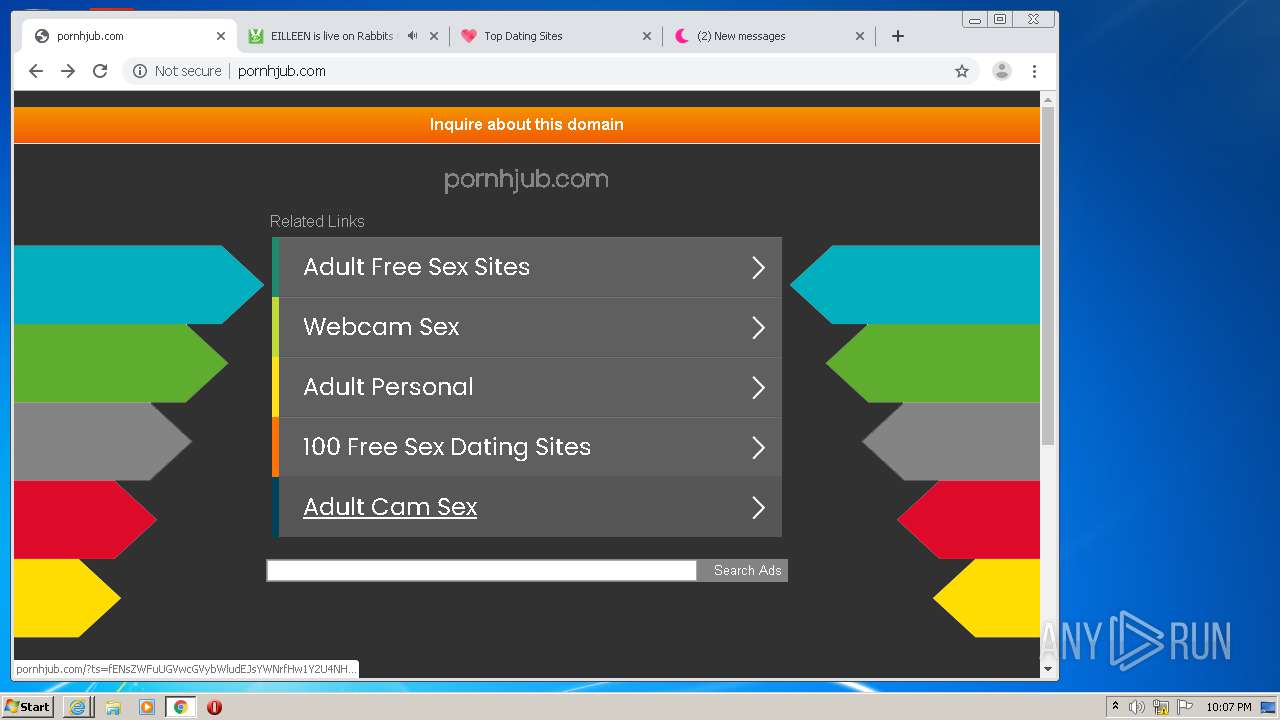
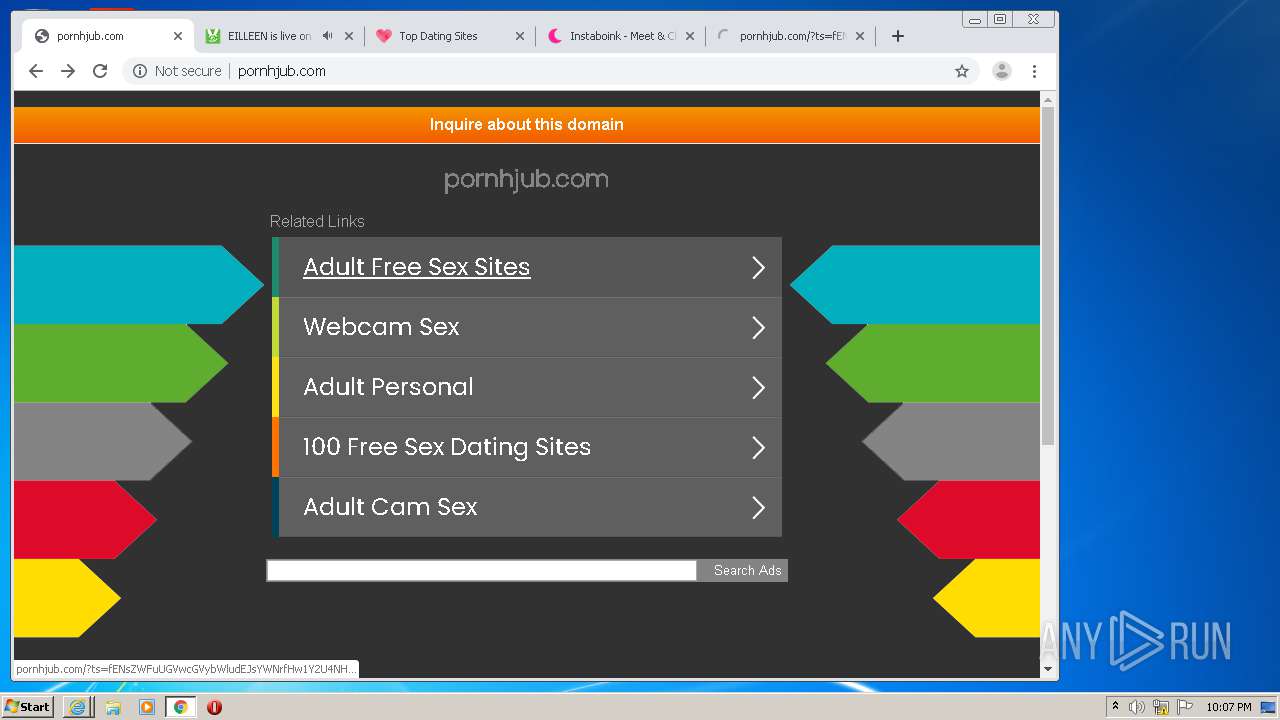
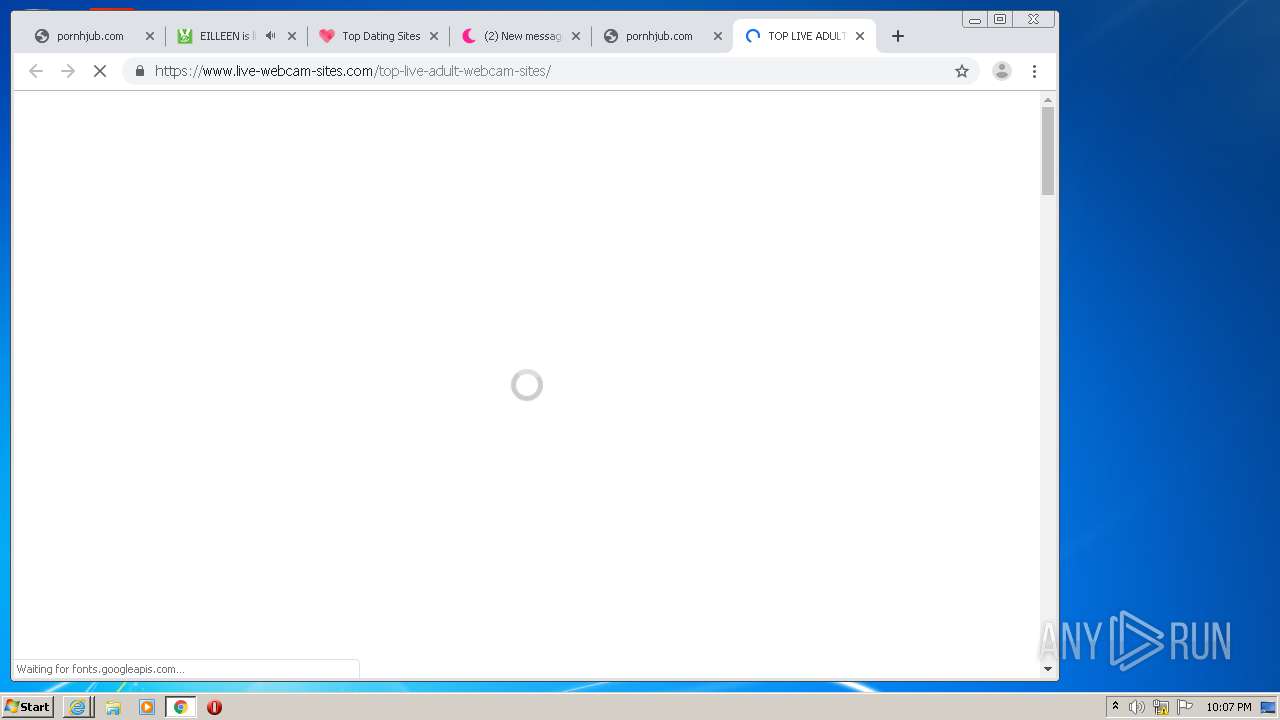
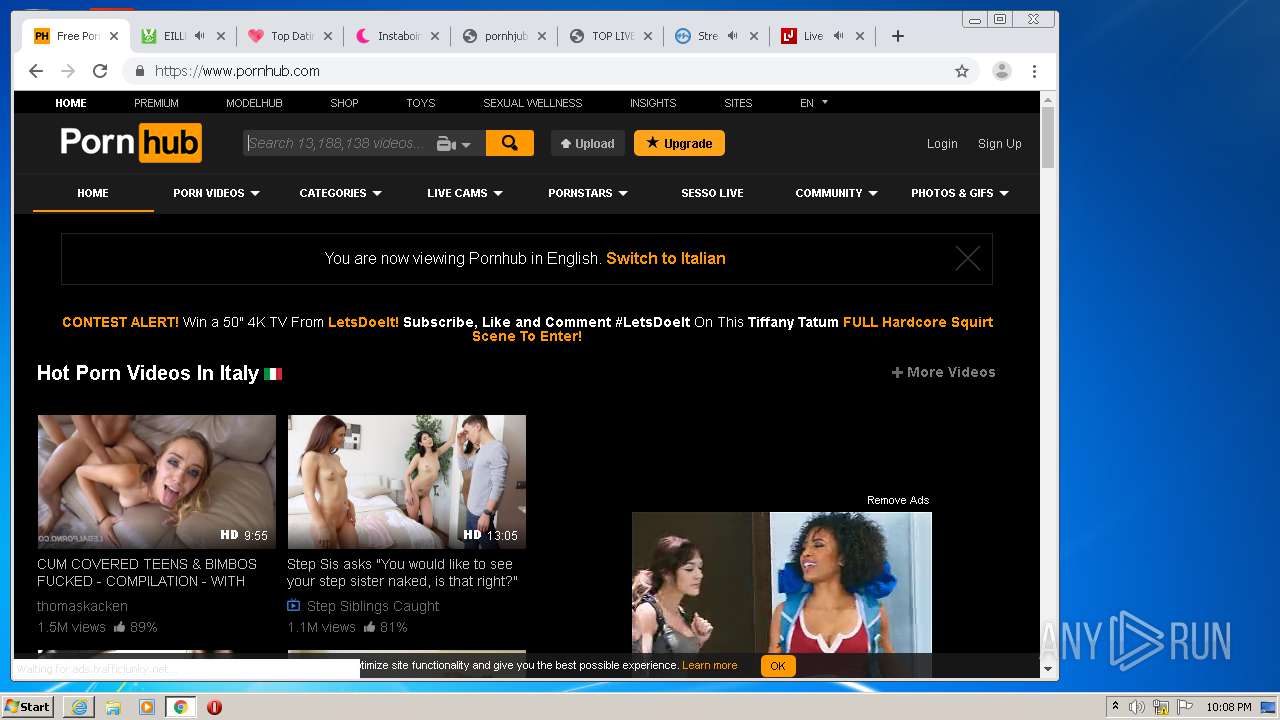
2412 | chrome.exe | GET | 200 | 104.247.81.132:80 | http://pornhjub.com/?ts=fENsZWFuUGVwcGVybWludEJsYWNrfHw1Y2U4NHxidWNrZXQwMDR8fHx8fHw1ZjY3YzQzYzI0OGQ4fHx8MTYwMDYzNTk2NC4xNjk1fDIyNzk0NDg4MTYxOWRkYjZhYWJkNTE2MjJjMmFiMDJmMDlmYTFlZDh8fHx8fDF8fHwwfHx8fDF8fHx8fDB8MHx8fHx8fHx8fHwwfDF8fDB8MHwxfDB8MHxXMTA9fHwxfFcxMD18ZTA4YWY1OWJkODE0Mzg3ZWZkMzViN2I1MjM2ZDhlM2ZjMjk4MDBhOQ%3D%3D&query=Webcam%20Sex&afdToken=3B1gu2myILOA5jdD0fXXvjjByqF1zIADrFhb0GhPNugzZfH3TKcBV4KQvCh7L2l1HmXv340D8qjz1dsnqtlYPiOCwnIFU9zXEdVunIiEUG8&pcsa=false | CA | html | 5.32 Kb | unknown |
2412 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2412 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2412 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1084 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
840 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1084 | iexplore.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2412 | chrome.exe | 142.250.74.195:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2412 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2412 | chrome.exe | 104.247.81.132:80 | pornhjub.com | Team Internet AG | CA | unknown |
2412 | chrome.exe | 172.217.18.174:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2412 | chrome.exe | 216.58.210.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssl.gstatic.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
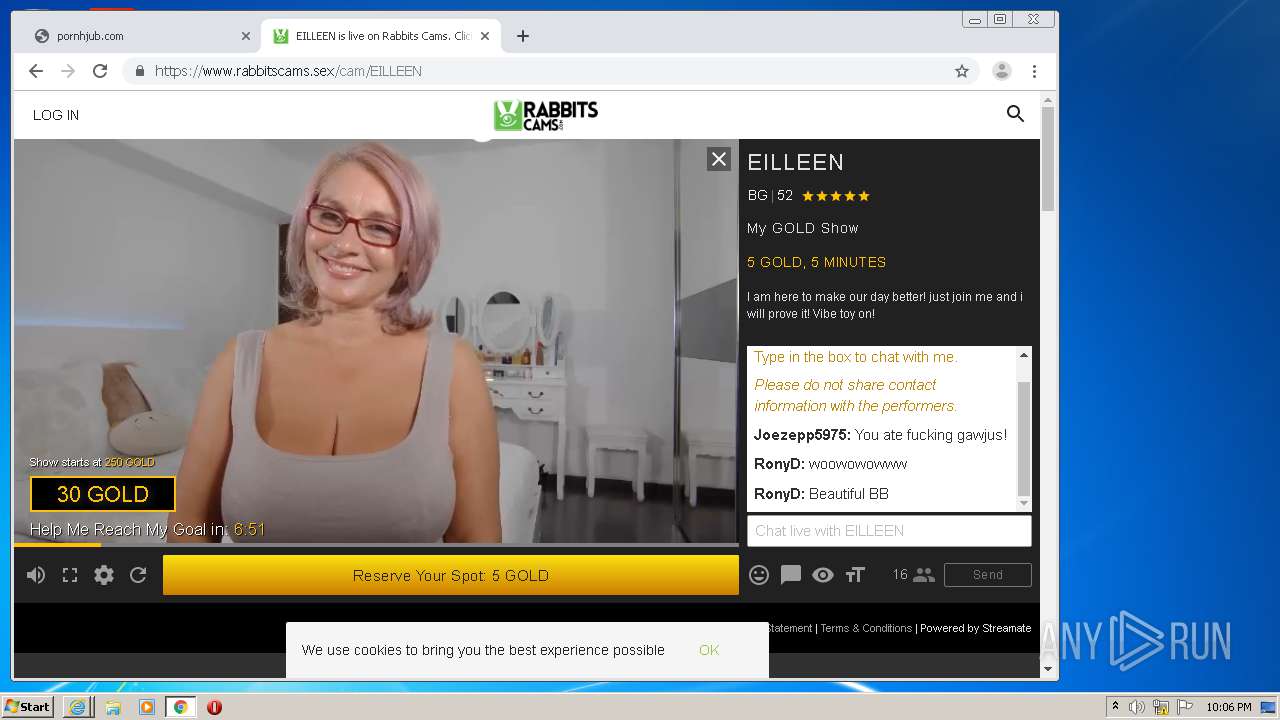
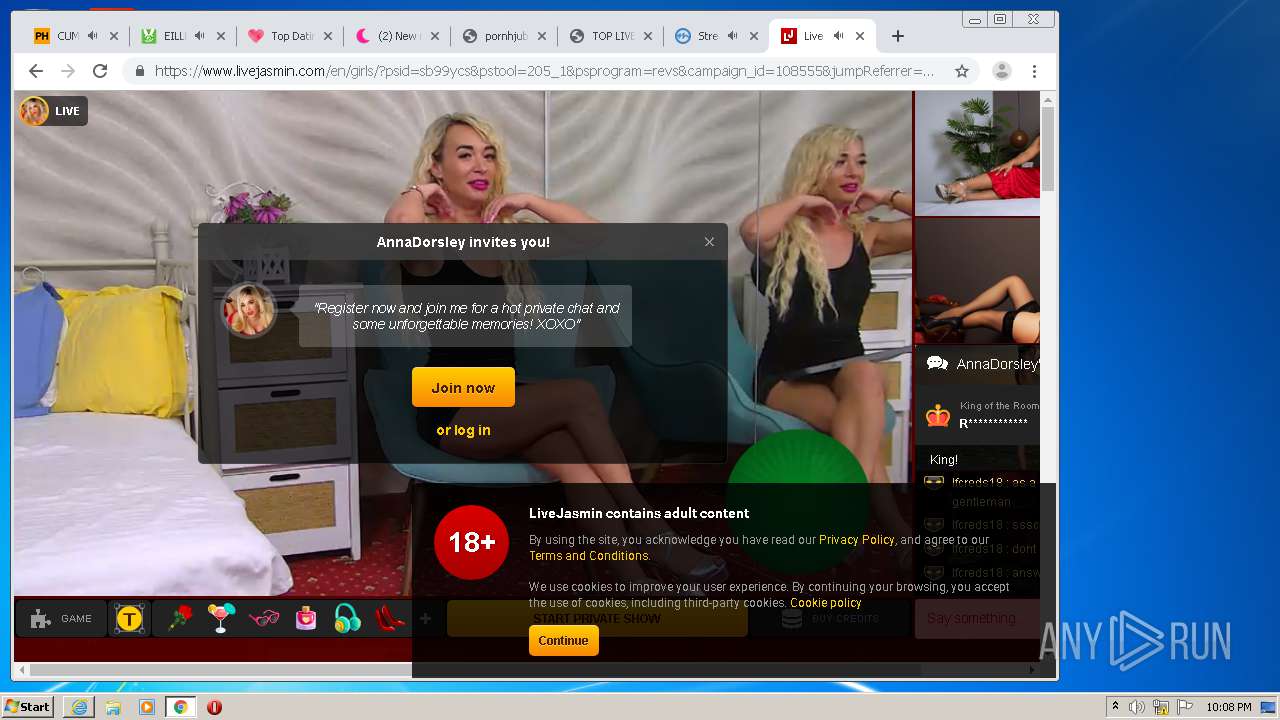
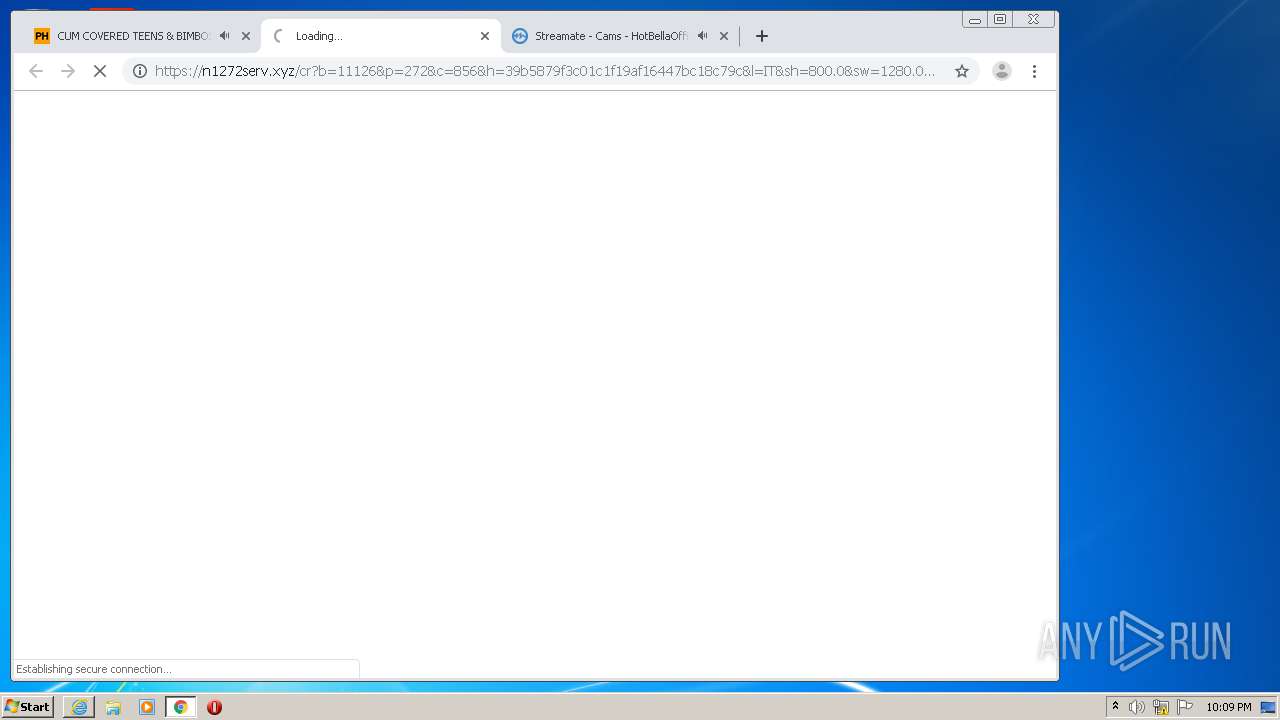
2412 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2412 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2412 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2412 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
2412 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |