| File name: | xiomired.exe |
| Full analysis: | https://app.any.run/tasks/ebf6176a-53f2-4a0d-a70e-33bdf833230a |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2023, 16:14:44 |
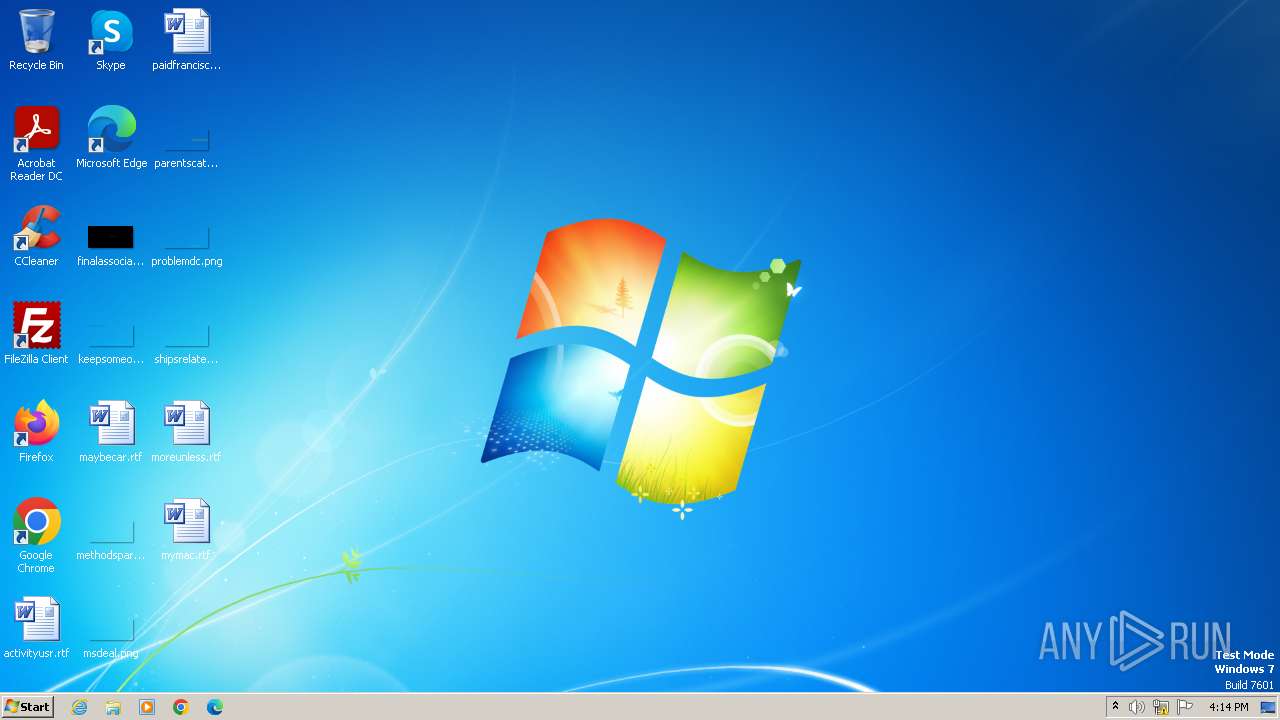
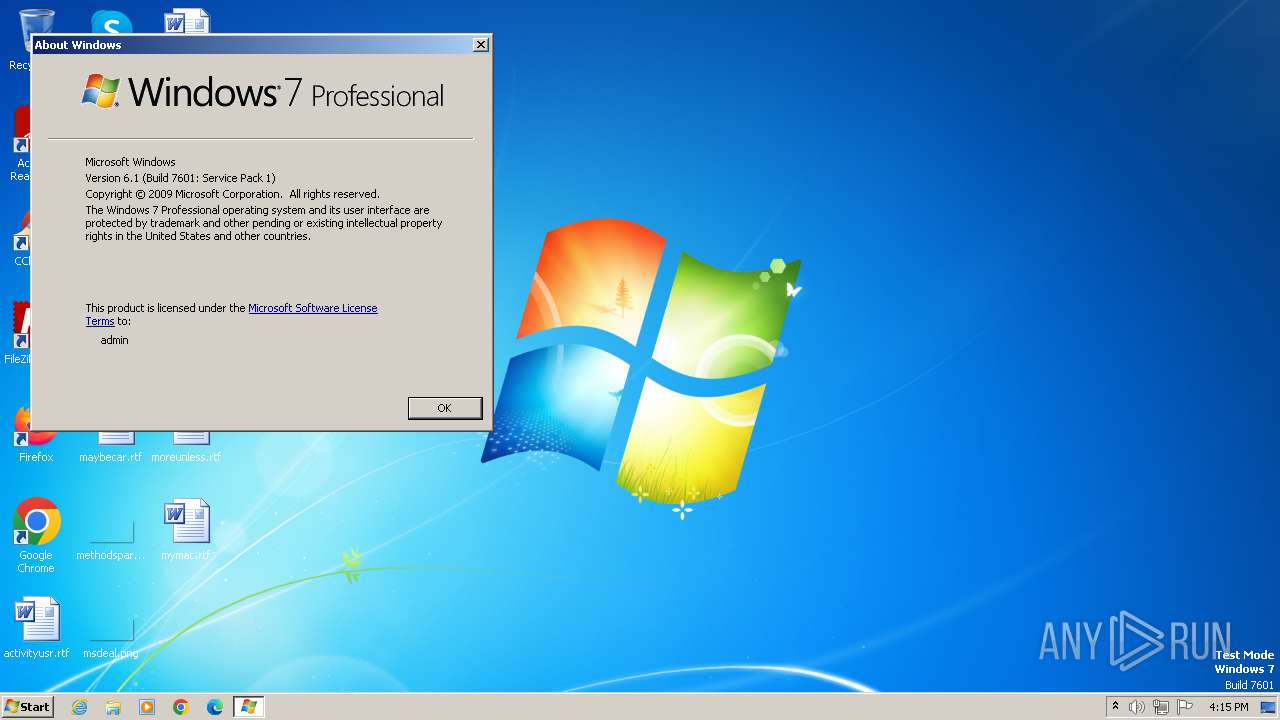
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 9905CB61E8AAD5461C942BC9C65C1F55 |
| SHA1: | 593B4D69049C053567ECD45FD0B588120DE0F796 |
| SHA256: | AF7E1E926F4130A99D02891F8538FDACBE9C917B5497887BB1E3E8AC6AE2DAB3 |
| SSDEEP: | 98304:2Rf/3gB7Y7WWrualerUvBGAD8cqpngkxR/r3CIdIq2s5yFfUuSUOe4ELKpZNS1xf:a6DEitwTd+8ydiZ+HAlM9gTeo8pxk |
MALICIOUS
Drops the executable file immediately after the start
- xiomired.exe (PID: 3504)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4032)
SUSPICIOUS
The process creates files with name similar to system file names
- xiomired.exe (PID: 3504)
Reads the Internet Settings
- xiomired.exe (PID: 3504)
Malware-specific behavior (creating "System.dll" in Temp)
- xiomired.exe (PID: 3504)
Executes as Windows Service
- ClasSvc.exe (PID: 3580)
Reads the Windows owner or organization settings
- ClasSvc.exe (PID: 3580)
Connects to unusual port
- ClasSvc.exe (PID: 3580)
Starts application with an unusual extension
- xiomired.exe (PID: 3504)
Starts CMD.EXE for commands execution
- nsB0D8.tmp (PID: 4064)
- nsC4DE.tmp (PID: 3684)
Starts SC.EXE for service management
- cmd.exe (PID: 4060)
The process executes via Task Scheduler
- ClasSvc.exe (PID: 1756)
Application launched itself
- ClasSvc.exe (PID: 3580)
INFO
Creates files in the program directory
- xiomired.exe (PID: 3504)
- ClasSvc.exe (PID: 3564)
Create files in a temporary directory
- xiomired.exe (PID: 3504)
Checks supported languages
- xiomired.exe (PID: 3504)
- ClasSvc.exe (PID: 3564)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3756)
- ClassicSvc.exe (PID: 3852)
- wmpnscfg.exe (PID: 3724)
- ClasSvc.exe (PID: 3548)
- nsB0D8.tmp (PID: 4064)
- nsC4DE.tmp (PID: 3684)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 1344)
- ClasSvc.exe (PID: 3424)
Reads the computer name
- xiomired.exe (PID: 3504)
- ClasSvc.exe (PID: 3564)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3852)
- ClassicSvc.exe (PID: 3756)
- wmpnscfg.exe (PID: 3724)
- ClasSvc.exe (PID: 3548)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 1344)
- ClasSvc.exe (PID: 3424)
Reads Environment values
- xiomired.exe (PID: 3504)
- ClasSvc.exe (PID: 3564)
- ClasSvc.exe (PID: 3424)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3852)
- ClassicSvc.exe (PID: 3756)
- ClasSvc.exe (PID: 3548)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 1344)
Process checks computer location settings
- ClasSvc.exe (PID: 3564)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3852)
- ClassicSvc.exe (PID: 3756)
- ClasSvc.exe (PID: 3548)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 1344)
- ClasSvc.exe (PID: 3424)
Reads product name
- ClasSvc.exe (PID: 3564)
- ClasSvc.exe (PID: 3424)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3852)
- ClassicSvc.exe (PID: 3756)
- ClasSvc.exe (PID: 3548)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 1344)
Reads Windows Product ID
- ClasSvc.exe (PID: 3564)
- ClasSvc.exe (PID: 3424)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3852)
- ClassicSvc.exe (PID: 3756)
- ClasSvc.exe (PID: 3548)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 1344)
Reads the machine GUID from the registry
- ClasSvc.exe (PID: 3424)
- ClasSvc.exe (PID: 3580)
- ClassicSvc.exe (PID: 3852)
- ClassicSvc.exe (PID: 3756)
- wmpnscfg.exe (PID: 3724)
- ClasSvc.exe (PID: 3548)
- ClasSvc.exe (PID: 1344)
- ClasSvc.exe (PID: 1756)
- ClasSvc.exe (PID: 3564)
Reads CPU info
- ClasSvc.exe (PID: 3580)
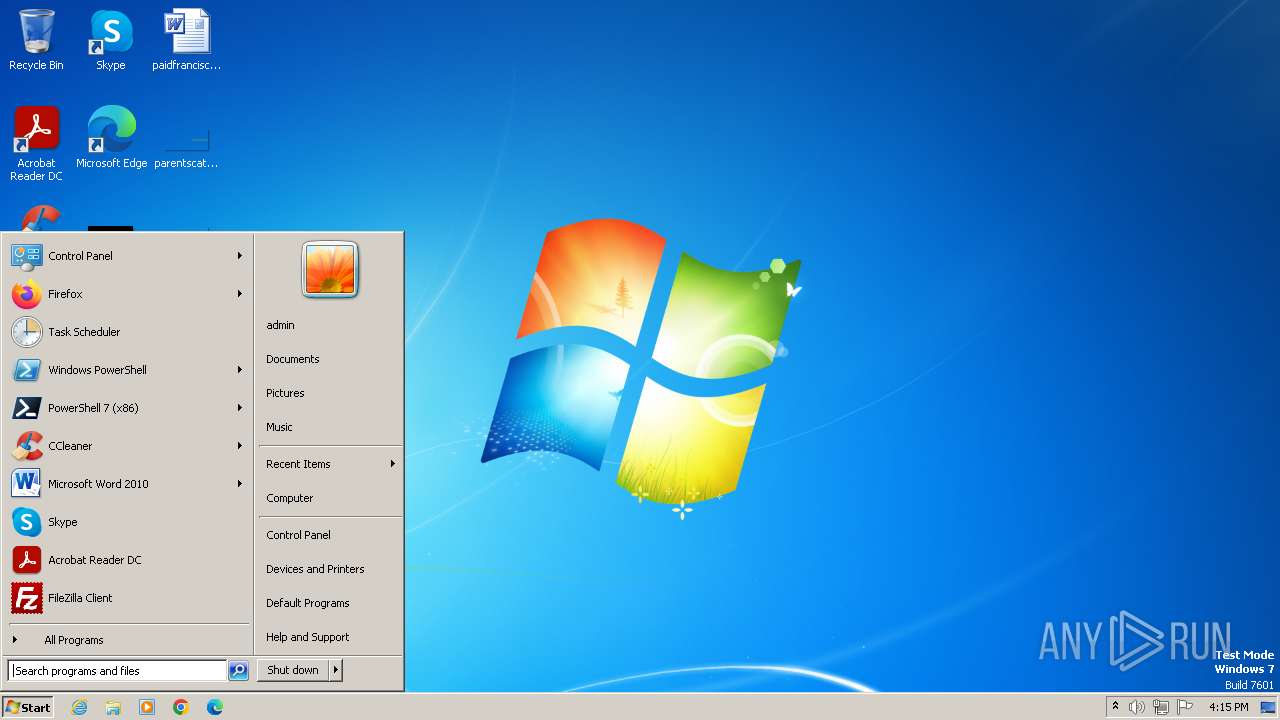
Manual execution by a user
- wmpnscfg.exe (PID: 3724)
- winver.exe (PID: 1208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:01 04:50:14+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 4092416 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x34a2 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.9.0.1 |
| ProductVersionNumber: | 5.9.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Classic Shell Red |
| CompanyName: | IvoSoft |
| FileDescription: | Classic Shell |
| FileVersion: | 5.9.0.1 |
| LegalCopyright: | Copyright 2020 IvoSoft Company |
| LegalTrademarks: | Copyright 2020 IvoSoft Company |
| OriginalFileName: | ClasSvc.exe |
| ProductName: | Classic Shell Red |
Total processes
59
Monitored processes
20
Malicious processes
2
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Windows\system32\winver.exe" | C:\Windows\System32\winver.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Version Reporter Applet Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Classic Shell\ClasSvc.exe" -firewall | C:\Program Files\Classic Shell\ClasSvc.exe | — | ClasSvc.exe | |||||||||||
User: SYSTEM Company: IvoSoft LLC Integrity Level: SYSTEM Description: Classic Shell Exit code: 0 Version: 5.9.0.1 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Classic Shell\ClasSvc.exe" /start | C:\Program Files\Classic Shell\ClasSvc.exe | — | taskeng.exe | |||||||||||
User: admin Company: IvoSoft LLC Integrity Level: HIGH Description: Classic Shell Exit code: 0 Version: 5.9.0.1 Modules
| |||||||||||||||
| 2064 | sc failure ClassicSSvc reset= 0 actions= restart/500/restart/500/restart/500 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | schtasks /Change /TN \microsoft\windows\defrag\scheduleddefrag /ENABLE | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3128 | "C:\Users\admin\AppData\Local\Temp\xiomired.exe" | C:\Users\admin\AppData\Local\Temp\xiomired.exe | — | explorer.exe | |||||||||||
User: admin Company: IvoSoft Integrity Level: MEDIUM Description: Classic Shell Exit code: 3221226540 Version: 5.9.0.1 Modules
| |||||||||||||||
| 3236 | schtasks /run /TN \microsoft\windows\defrag\scheduleddefrag | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Classic Shell\ClasSvc.exe" /start | C:\Program Files\Classic Shell\ClasSvc.exe | — | xiomired.exe | |||||||||||
User: admin Company: IvoSoft LLC Integrity Level: HIGH Description: Classic Shell Exit code: 0 Version: 5.9.0.1 Modules
| |||||||||||||||
| 3504 | "C:\Users\admin\AppData\Local\Temp\xiomired.exe" | C:\Users\admin\AppData\Local\Temp\xiomired.exe | explorer.exe | ||||||||||||
User: admin Company: IvoSoft Integrity Level: HIGH Description: Classic Shell Exit code: 2 Version: 5.9.0.1 Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Classic Shell\ClasSvc.exe" -run_agent -second | C:\Program Files\Classic Shell\ClasSvc.exe | — | xiomired.exe | |||||||||||
User: admin Company: IvoSoft LLC Integrity Level: HIGH Description: Classic Shell Exit code: 0 Version: 5.9.0.1 Modules
| |||||||||||||||
Total events
2 331
Read events
2 304
Write events
23
Delete events
4
Modification events
| (PID) Process: | (3504) xiomired.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Unpretentiously schlong\Host\Host\Parameters |
| Operation: | delete value | Name: | 1807 |
Value: 1 | |||
| (PID) Process: | (3504) xiomired.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3504) xiomired.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3504) xiomired.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3504) xiomired.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3580) ClasSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Unpretentiously schlong\Host\Host\Parameters |
| Operation: | write | Name: | General |
Value: 3C3F786D6C2076657273696F6E3D22312E302220656E636F64696E673D225554462D38223F3E3C67656E6572616C5F73657474696E67732076657273696F6E3D223639313130223E3C706F72743E353635303C2F706F72743E3C686964655F747261795F69636F6E5F706F7075705F6D656E753E747275653C2F686964655F747261795F69636F6E5F706F7075705F6D656E753E3C747261795F6D656E755F686964655F73746F703E747275653C2F747261795F6D656E755F686964655F73746F703E3C6C616E67756167653E5275737369616E3C2F6C616E67756167653E3C63616C6C6261636B5F6175746F5F636F6E6E6563743E747275653C2F63616C6C6261636B5F6175746F5F636F6E6E6563743E3C63616C6C6261636B5F636F6E6E6563745F696E74657276616C3E36303C2F63616C6C6261636B5F636F6E6E6563745F696E74657276616C3E3C70617373776F72645F646174613E3C2F70617373776F72645F646174613E3C70726F746563745F63616C6C6261636B5F73657474696E67733E66616C73653C2F70726F746563745F63616C6C6261636B5F73657474696E67733E3C70726F746563745F696E65745F69645F73657474696E67733E66616C73653C2F70726F746563745F696E65745F69645F73657474696E67733E3C7573655F6C65676163795F636170747572653E747275653C2F7573655F6C65676163795F636170747572653E3C646F5F6E6F745F636170747572655F7264703E66616C73653C2F646F5F6E6F745F636170747572655F7264703E3C7573655F69705F765F363E747275653C2F7573655F69705F765F363E3C6C6F675F7573653E66616C73653C2F6C6F675F7573653E3C636861745F636C69656E745F73657474696E67733E3C2F636861745F636C69656E745F73657474696E67733E3C617574685F6B65795F737472696E673E3C2F617574685F6B65795F737472696E673E3C7369645F69643E3C2F7369645F69643E3C6E6F746966795F73686F775F70616E656C3E66616C73653C2F6E6F746966795F73686F775F70616E656C3E3C6E6F746966795F6368616E67655F747261795F69636F6E3E747275653C2F6E6F746966795F6368616E67655F747261795F69636F6E3E3C6E6F746966795F62616C6C6F6E5F68696E743E66616C73653C2F6E6F746966795F62616C6C6F6E5F68696E743E3C6E6F746966795F706C61795F736F756E643E66616C73653C2F6E6F746966795F706C61795F736F756E643E3C6E6F746966795F70616E656C5F783E2D313C2F6E6F746966795F70616E656C5F783E3C6E6F746966795F70616E656C5F793E2D313C2F6E6F746966795F70616E656C5F793E3C70726F78795F73657474696E67733E3737752F3737752F5044393462577767646D567963326C76626A30694D5334774969426C626D4E765A476C755A7A3069565652474C546769507A343863484A7665486C666332563064476C755A334D67646D567963326C76626A30694E6A6B784D544169506A78316332566663484A7665486B2B5A6D4673633255384C33567A5A563977636D39346554343863484A7665486C6664486C775A54347750433977636D3934655639306558426C506A786F62334E30506A77766147397A6444343863473979644434384C334276636E512B5047356C5A575266595856306144356D5957787A5A547776626D566C5A4639686458526F506A787564473173583246316447672B5A6D4673633255384C32353062577866595856306144343864584E6C636D35686257552B5043393163325679626D46745A5434386347467A63336476636D512B5043397759584E7A643239795A4434385A47397459576C75506A77765A47397459576C75506A777663484A7665486C666332563064476C755A334D2B3C2F70726F78795F73657474696E67733E3C6164646974696F6E616C3E3C2F6164646974696F6E616C3E3C64697361626C655F696E7465726E65745F69643E66616C73653C2F64697361626C655F696E7465726E65745F69643E3C736166655F6D6F64655F7365743E66616C73653C2F736166655F6D6F64655F7365743E3C73686F775F69645F6E6F74696669636174696F6E3E66616C73653C2F73686F775F69645F6E6F74696669636174696F6E3E3C73686F775F69645F6E6F74696669636174696F6E5F726571756573743E66616C73653C2F73686F775F69645F6E6F74696669636174696F6E5F726571756573743E3C696E746567726174655F6669726577616C6C5F61745F737461727475703E747275653C2F696E746567726174655F6669726577616C6C5F61745F737461727475703E3C2F67656E6572616C5F73657474696E67733E | |||
| (PID) Process: | (3580) ClasSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Unpretentiously schlong\Host\Host\Parameters |
| Operation: | write | Name: | InternetId |
Value: 3C3F786D6C2076657273696F6E3D22312E302220656E636F64696E673D225554462D38223F3E3C726D735F696E7465726E65745F69645F73657474696E67732076657273696F6E3D223639313130223E3C696E7465726E65745F69643E3833332D3133332D3537372D3835353C2F696E7465726E65745F69643E3C7573655F696E65745F636F6E6E656374696F6E3E747275653C2F7573655F696E65745F636F6E6E656374696F6E3E3C696E65745F7365727665723E3C2F696E65745F7365727665723E3C7573655F637573746F6D5F696E65745F7365727665723E66616C73653C2F7573655F637573746F6D5F696E65745F7365727665723E3C696E65745F69645F706F72743E353635353C2F696E65745F69645F706F72743E3C7573655F696E65745F69645F697076363E747275653C2F7573655F696E65745F69645F697076363E3C696E65745F69645F7573655F70696E3E66616C73653C2F696E65745F69645F7573655F70696E3E3C696E65745F69645F70696E3E3C2F696E65745F69645F70696E3E3C2F726D735F696E7465726E65745F69645F73657474696E67733E | |||
| (PID) Process: | (3580) ClasSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Unpretentiously schlong\Host\Host\Parameters |
| Operation: | write | Name: | Security |
Value: EFBBBF3C3F786D6C2076657273696F6E3D22312E302220656E636F64696E673D225554462D38223F3E3C73656375726974795F73657474696E67732076657273696F6E3D223639313130223E3C77696E646F77735F73656375726974793E3C2F77696E646F77735F73656375726974793E3C73696E676C655F70617373776F72645F686173683E3C2F73696E676C655F70617373776F72645F686173683E3C6D795F757365725F6163636573735F6C6973743E3C757365725F6163636573735F6C6973743E3C757365725F6163636573733E3C7369643E7B45314336424331392D393233382D344635372D423346352D3436353538344139453146457D3C2F7369643E3C757365725F6E616D653E7777773C2F757365725F6E616D653E3C70617373776F72643E31413244323930353546334442423346313734373942343734413234464536424246433344373935343133303043434345313936413343454645343032353338353138374630393741424434443739364144323833443136343637393731424430463933353342464343303734333937384145373730343745423843353841353C2F70617373776F72643E3C6163636573735F6D61736B3E3935393C2F6163636573735F6D61736B3E3C6163746976653E747275653C2F6163746976653E3C757365725F7065726D697373696F6E735F61736B3E66616C73653C2F757365725F7065726D697373696F6E735F61736B3E3C757365725F7065726D697373696F6E735F696E74657276616C3E31303030303C2F757365725F7065726D697373696F6E735F696E74657276616C3E3C757365725F7065726D697373696F6E735F616C6C6F775F64656661756C743E66616C73653C2F757365725F7065726D697373696F6E735F616C6C6F775F64656661756C743E3C757365725F7065726D697373696F6E735F6F6E6C795F69665F757365725F6C6F676765645F6F6E3E66616C73653C2F757365725F7065726D697373696F6E735F6F6E6C795F69665F757365725F6C6F676765645F6F6E3E3C2F757365725F6163636573733E3C2F757365725F6163636573735F6C6973743E3C2F6D795F757365725F6163636573735F6C6973743E3C69705F66696C7465725F747970653E323C2F69705F66696C7465725F747970653E3C69705F626C61636B5F6C6973743E3C2F69705F626C61636B5F6C6973743E3C69705F77686974655F6C6973743E3C2F69705F77686974655F6C6973743E3C617574685F6B696E643E323C2F617574685F6B696E643E3C6F74705F656E61626C653E66616C73653C2F6F74705F656E61626C653E3C6F74705F707269766174655F6B65793E3C2F6F74705F707269766174655F6B65793E3C6F74705F71725F7365637265743E3C2F6F74705F71725F7365637265743E3C757365725F7065726D697373696F6E735F61736B3E66616C73653C2F757365725F7065726D697373696F6E735F61736B3E3C757365725F7065726D697373696F6E735F696E74657276616C3E31303030303C2F757365725F7065726D697373696F6E735F696E74657276616C3E3C757365725F7065726D697373696F6E735F616C6C6F775F64656661756C743E66616C73653C2F757365725F7065726D697373696F6E735F616C6C6F775F64656661756C743E3C757365725F7065726D697373696F6E735F6F6E6C795F69665F757365725F6C6F676765645F6F6E3E66616C73653C2F757365725F7065726D697373696F6E735F6F6E6C795F69665F757365725F6C6F676765645F6F6E3E3C64697361626C655F72656D6F74655F636F6E74726F6C3E66616C73653C2F64697361626C655F72656D6F74655F636F6E74726F6C3E3C64697361626C655F72656D6F74655F73637265656E3E66616C73653C2F64697361626C655F72656D6F74655F73637265656E3E3C64697361626C655F66696C655F7472616E736665723E66616C73653C2F64697361626C655F66696C655F7472616E736665723E3C64697361626C655F72656469726563743E66616C73653C2F64697361626C655F72656469726563743E3C64697361626C655F74656C6E65743E66616C73653C2F64697361626C655F74656C6E65743E3C64697361626C655F72656D6F74655F657865637574653E66616C73653C2F64697361626C655F72656D6F74655F657865637574653E3C64697361626C655F7461736B5F6D616E616765723E66616C73653C2F64697361626C655F7461736B5F6D616E616765723E3C64697361626C655F73687574646F776E3E66616C73653C2F64697361626C655F73687574646F776E3E3C64697361626C655F72656D6F74655F757067726164653E66616C73653C2F64697361626C655F72656D6F74655F757067726164653E3C64697361626C655F707265766965775F636170747572653E66616C73653C2F64697361626C655F707265766965775F636170747572653E3C64697361626C655F6465766963655F6D616E616765723E66616C73653C2F64697361626C655F6465766963655F6D616E616765723E3C64697361626C655F636861743E66616C73653C2F64697361626C655F636861743E3C64697361626C655F73637265656E5F7265636F72643E66616C73653C2F64697361626C655F73637265656E5F7265636F72643E3C64697361626C655F61765F636170747572653E66616C73653C2F64697361626C655F61765F636170747572653E3C64697361626C655F73656E645F6D6573736167653E66616C73653C2F64697361626C655F73656E645F6D6573736167653E3C64697361626C655F72656769737472793E66616C73653C2F64697361626C655F72656769737472793E3C64697361626C655F61765F636861743E66616C73653C2F64697361626C655F61765F636861743E3C64697361626C655F72656D6F74655F73657474696E67733E66616C73653C2F64697361626C655F72656D6F74655F73657474696E67733E3C64697361626C655F72656D6F74655F7072696E74696E673E66616C73653C2F64697361626C655F72656D6F74655F7072696E74696E673E3C64697361626C655F7264703E66616C73653C2F64697361626C655F7264703E3C637573746F6D5F7365727665725F6C6973743E3737752F5044393462577767646D567963326C76626A30694D5334774969426C626D4E765A476C755A7A3069565652474C546769507A344E436A787A5A584A325A584A6659323975626D566A6446396A623235305A58683049485A6C636E4E7062323439496A59354D544577496A3438636D317A58334E6C636E5A6C636E4D76506A777663325679646D567958324E76626D356C5933526659323975644756346444344E43673D3D3C2F637573746F6D5F7365727665725F6C6973743E3C73656C65637465645F637573746F6D5F7365727665725F69643E3C2F73656C65637465645F637573746F6D5F7365727665725F69643E3C637573746F6D5F7365727665725F6163636573733E3737752F5044393462577767646D567963326C76626A30694D5334774969426C626D4E765A476C755A7A3069565652474C546769507A344E436A787962584E6659574E7349485A6C636E4E7062323439496A59354D544577496A3438636D317A5832466A5A584D76506A786C626D4669624756666157356F5A584A7064443530636E566C5043396C626D4669624756666157356F5A584A70644434384C334A74633139685932772B44516F3D3C2F637573746F6D5F7365727665725F6163636573733E3C2F73656375726974795F73657474696E67733E | |||
| (PID) Process: | (3580) ClasSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Unpretentiously schlong\Host\Host\Parameters |
| Operation: | write | Name: | General |
Value: EFBBBF3C3F786D6C2076657273696F6E3D22312E302220656E636F64696E673D225554462D38223F3E0D0A3C67656E6572616C5F73657474696E67732076657273696F6E3D223730303031223E3C706F72743E353635303C2F706F72743E3C686964655F747261795F69636F6E5F706F7075705F6D656E753E747275653C2F686964655F747261795F69636F6E5F706F7075705F6D656E753E3C747261795F6D656E755F686964655F73746F703E747275653C2F747261795F6D656E755F686964655F73746F703E3C6C616E67756167653E5275737369616E3C2F6C616E67756167653E3C63616C6C6261636B5F6175746F5F636F6E6E6563743E747275653C2F63616C6C6261636B5F6175746F5F636F6E6E6563743E3C63616C6C6261636B5F636F6E6E6563745F696E74657276616C3E36303C2F63616C6C6261636B5F636F6E6E6563745F696E74657276616C3E3C70617373776F72645F646174613E3C2F70617373776F72645F646174613E3C70726F746563745F63616C6C6261636B5F73657474696E67733E66616C73653C2F70726F746563745F63616C6C6261636B5F73657474696E67733E3C70726F746563745F696E65745F69645F73657474696E67733E66616C73653C2F70726F746563745F696E65745F69645F73657474696E67733E3C7573655F6C65676163795F636170747572653E747275653C2F7573655F6C65676163795F636170747572653E3C646F5F6E6F745F636170747572655F7264703E66616C73653C2F646F5F6E6F745F636170747572655F7264703E3C7573655F69705F765F363E747275653C2F7573655F69705F765F363E3C6C6F675F7573653E66616C73653C2F6C6F675F7573653E3C6C6F675F7573655F77696E646F77733E66616C73653C2F6C6F675F7573655F77696E646F77733E3C636861745F636C69656E745F73657474696E67733E3C2F636861745F636C69656E745F73657474696E67733E3C617574685F6B65795F737472696E673E3C2F617574685F6B65795F737472696E673E3C7369645F69643E34353235312E363737313539333238373C2F7369645F69643E3C6E6F746966795F73686F775F70616E656C3E66616C73653C2F6E6F746966795F73686F775F70616E656C3E3C6E6F746966795F6368616E67655F747261795F69636F6E3E747275653C2F6E6F746966795F6368616E67655F747261795F69636F6E3E3C6E6F746966795F62616C6C6F6E5F68696E743E66616C73653C2F6E6F746966795F62616C6C6F6E5F68696E743E3C6E6F746966795F706C61795F736F756E643E66616C73653C2F6E6F746966795F706C61795F736F756E643E3C6E6F746966795F70616E656C5F783E2D313C2F6E6F746966795F70616E656C5F783E3C6E6F746966795F70616E656C5F793E2D313C2F6E6F746966795F70616E656C5F793E3C70726F78795F73657474696E67733E3737752F3737752F5044393462577767646D567963326C76626A30694D5334774969426C626D4E765A476C755A7A3069565652474C546769507A343863484A7665486C666332563064476C755A334D67646D567963326C76626A30694E6A6B784D544169506A78316332566663484A7665486B2B5A6D4673633255384C33567A5A563977636D39346554343863484A7665486C6664486C775A54347750433977636D3934655639306558426C506A786F62334E30506A77766147397A6444343863473979644434384C334276636E512B5047356C5A575266595856306144356D5957787A5A547776626D566C5A4639686458526F506A787564473173583246316447672B5A6D4673633255384C32353062577866595856306144343864584E6C636D35686257552B5043393163325679626D46745A5434386347467A63336476636D512B5043397759584E7A643239795A4434385A47397459576C75506A77765A47397459576C75506A777663484A7665486C666332563064476C755A334D2B3C2F70726F78795F73657474696E67733E3C6164646974696F6E616C3E3C2F6164646974696F6E616C3E3C64697361626C655F696E7465726E65745F69643E66616C73653C2F64697361626C655F696E7465726E65745F69643E3C736166655F6D6F64655F7365743E66616C73653C2F736166655F6D6F64655F7365743E3C73686F775F69645F6E6F74696669636174696F6E3E66616C73653C2F73686F775F69645F6E6F74696669636174696F6E3E3C73686F775F69645F6E6F74696669636174696F6E5F726571756573743E66616C73653C2F73686F775F69645F6E6F74696669636174696F6E5F726571756573743E3C696E746567726174655F6669726577616C6C5F61745F737461727475703E747275653C2F696E746567726174655F6669726577616C6C5F61745F737461727475703E3C636C6970626F6172645F7472616E736665725F6D6F64653E303C2F636C6970626F6172645F7472616E736665725F6D6F64653E3C636C6F73655F73657373696F6E5F69646C653E66616C73653C2F636C6F73655F73657373696F6E5F69646C653E3C636C6F73655F73657373696F6E5F69646C655F696E74657276616C3E36303C2F636C6F73655F73657373696F6E5F69646C655F696E74657276616C3E3C2F67656E6572616C5F73657474696E67733E0D0A | |||
| (PID) Process: | (3580) ClasSvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Unpretentiously schlong\Host\Host\Parameters |
| Operation: | write | Name: | InternetId |
Value: EFBBBF3C3F786D6C2076657273696F6E3D22312E302220656E636F64696E673D225554462D38223F3E0D0A3C726D735F696E7465726E65745F69645F73657474696E67732076657273696F6E3D223730303031223E3C696E7465726E65745F69643E3833332D3133332D3537372D3835353C2F696E7465726E65745F69643E3C7573655F696E65745F636F6E6E656374696F6E3E747275653C2F7573655F696E65745F636F6E6E656374696F6E3E3C696E65745F7365727665723E3C2F696E65745F7365727665723E3C7573655F637573746F6D5F696E65745F7365727665723E66616C73653C2F7573655F637573746F6D5F696E65745F7365727665723E3C696E65745F69645F706F72743E353635353C2F696E65745F69645F706F72743E3C7573655F696E65745F69645F697076363E747275653C2F7573655F696E65745F69645F697076363E3C696E65745F69645F7573655F70696E3E66616C73653C2F696E65745F69645F7573655F70696E3E3C696E65745F69645F70696E3E3C2F696E65745F69645F70696E3E3C2F726D735F696E7465726E65745F69645F73657474696E67733E0D0A | |||
Executable files
10
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | xiomired.exe | C:\Users\admin\AppData\Local\Temp\nsh7B60.tmp\System.dll | executable | |
MD5:8CF2AC271D7679B1D68EEFC1AE0C5618 | SHA256:6950991102462D84FDC0E3B0AE30C95AF8C192F77CE3D78E8D54E6B22F7C09BA | |||
| 3504 | xiomired.exe | C:\Program Files\Classic Shell\ssleay32.dll | executable | |
MD5:197DA919E4C91125656BF905877C9B5A | SHA256:303C78ABA3B776472C245F17020F9AA5A53F09A6F6C1E4F34B8E18E33906B5EE | |||
| 3504 | xiomired.exe | C:\Program Files\Classic Shell\libeay32.dll | executable | |
MD5:0D51927274281007657C7F3E0DF7BECB | SHA256:DFC847405BE60C29E86E3E3222E7F63C1FF584727D87D3C35C25C4893E19FDA0 | |||
| 3504 | xiomired.exe | C:\Users\admin\AppData\Local\Temp\nsh7B60.tmp\registry.dll | executable | |
MD5:2B7007ED0262CA02EF69D8990815CBEB | SHA256:0B25B20F26DE5D5BD795F934C70447112B4981343FCB2DFAB3374A4018D28C2D | |||
| 3504 | xiomired.exe | C:\Program Files\Classic Shell\ClasSvc.exe | executable | |
MD5:305E71EC353A718B055EA9ACAA6598A3 | SHA256:031F9345C33543366E9C66447F4F3FB085A2E04F3C2F98F562F191DE6A413DD0 | |||
| 3504 | xiomired.exe | C:\Program Files\Classic Shell\inst353.7z | compressed | |
MD5:8E10F5D61AF188F5E365FBB68A2D3FA4 | SHA256:1E80F5FA9B456D6D50E69DA1C2063AF3DEF635AA92CDC91CDA5A5CEBE3F2DC13 | |||
| 3504 | xiomired.exe | C:\Users\admin\AppData\Local\Temp\Log922.xml | xml | |
MD5:6A7D2833BE9BF77842C9B56F23DBB0E7 | SHA256:50D4FE0CD2BCEA2ACDCFF6ED67E7BB61FBE7D8BB93C0891C5F4F5DEF17CEA858 | |||
| 3504 | xiomired.exe | C:\Users\admin\AppData\Local\Temp\nsh7B60.tmp\NSISList.dll | executable | |
MD5:49BB98396DC0187146319F8C130C363C | SHA256:517A328BFED8935773D94A40812763CCDF08881AD5D71A83A629EAFA62B41CF2 | |||
| 3504 | xiomired.exe | C:\Program Files\Classic Shell\ClassicSvc.exe | executable | |
MD5:385CA557571FF7C65D25B15426F9A8B6 | SHA256:7FDBE1E9F540292F53D41452663B1B117077F9DB5D5DD68947005C8DC3DB9896 | |||
| 3504 | xiomired.exe | C:\Users\admin\AppData\Local\Temp\nsh7B60.tmp\nsC4DE.tmp | executable | |
MD5:F27689C513E7D12C7C974D5F8EF710D6 | SHA256:1F18F4126124B0551F3DBCD0FEC7F34026F930CA509F04435657CEDC32AE8C47 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3580 | ClasSvc.exe | 64.20.61.146:5655 | id70.remoteutilities.com | IS-AS-1 | US | unknown |
3580 | ClasSvc.exe | 66.23.226.254:5655 | — | IS-AS-1 | US | unknown |
3580 | ClasSvc.exe | 66.23.226.254:443 | — | IS-AS-1 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
id70.remoteutilities.com |
| unknown |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
ClasSvc.exe | TMainService.Start |
ClassicSvc.exe | 21-11-2023_16:15:13:503#T:Error #19 @2 |