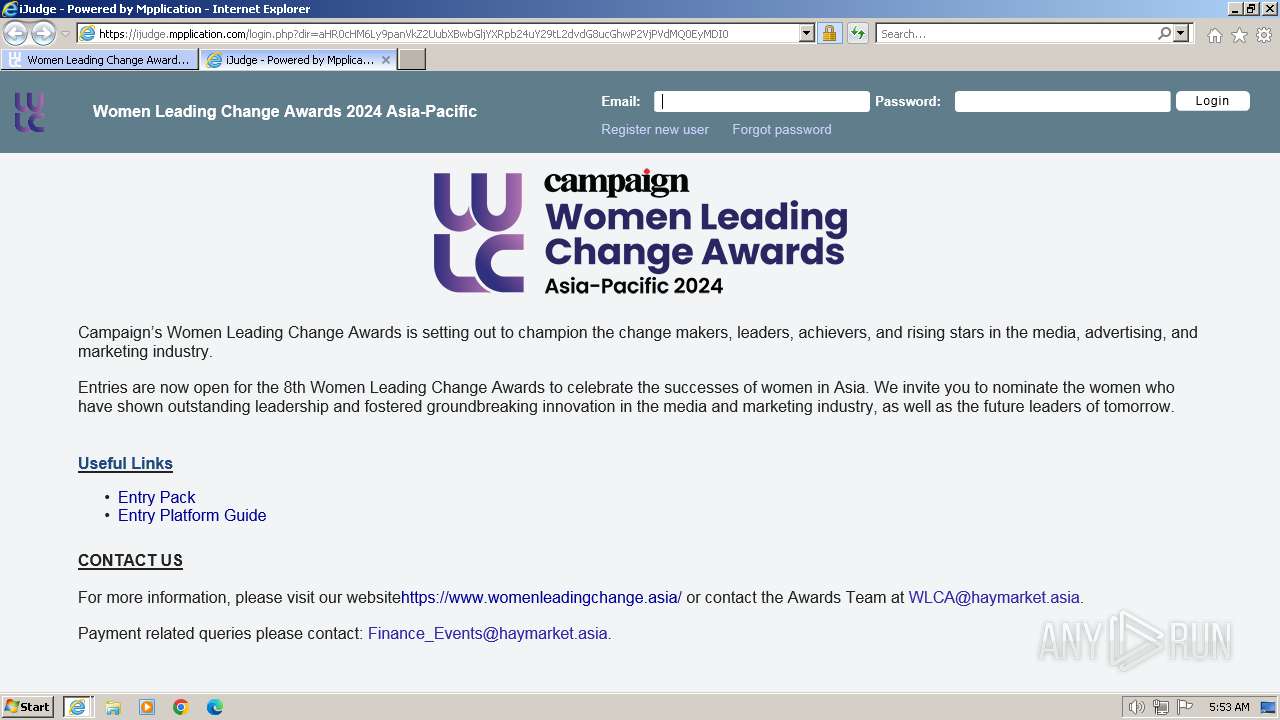
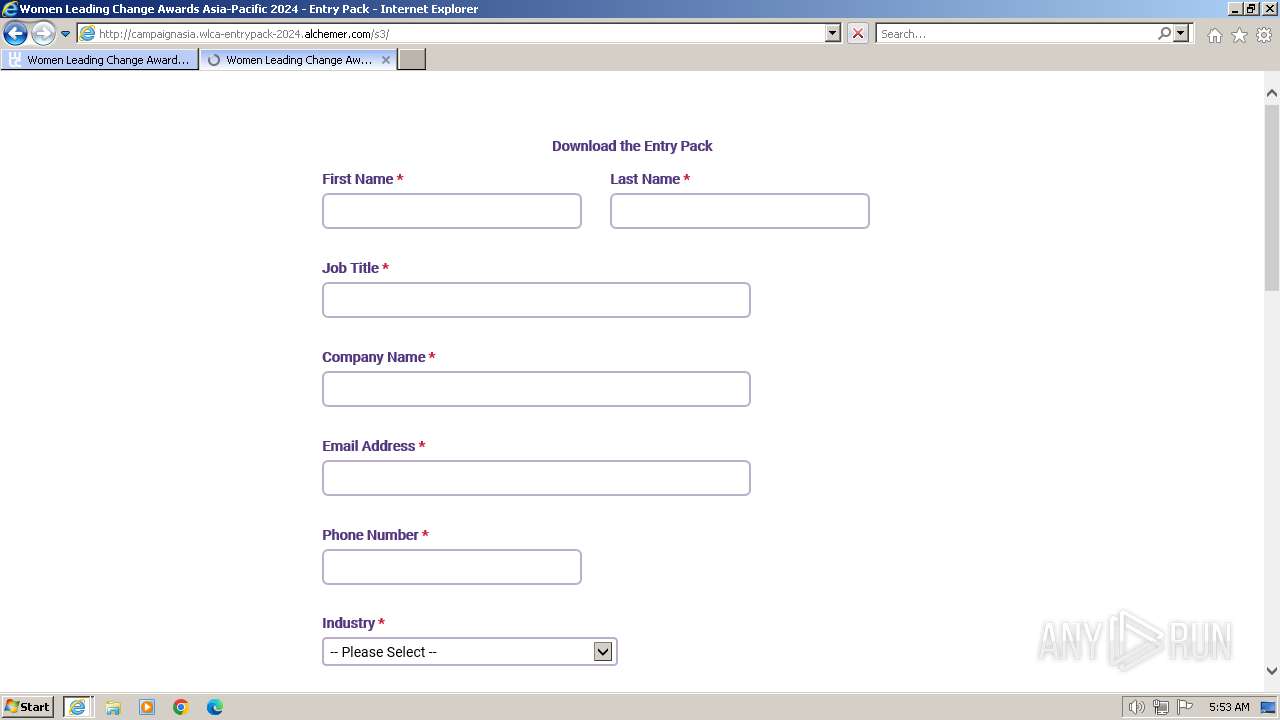
| URL: | https://haymarket.us20.list-manage.com/track/click?u=75812e9e0ad463237414a7749&id=39ab54bc3e&e=373842fcc7 |
| Full analysis: | https://app.any.run/tasks/8da031e2-8dd2-4a23-a0c3-deaeb6314cc0 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2024, 05:53:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CEB6401FCEA45254404E9F9C6B330036 |
| SHA1: | 1A2F829037782F4FB3632BF6A350035491357619 |
| SHA256: | AF600A34904E3B07CF721899044807D8DC3FAFC950A31DBAF1AB4AE3462480A1 |
| SSDEEP: | 3:N845EeKPXRkULGGRXEGcJMkNCXyr58QB+RHBoWSaC:245xKPBkULEGcJMDXyrj+RHRHC |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1384 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://haymarket.us20.list-manage.com/track/click?u=75812e9e0ad463237414a7749&id=39ab54bc3e&e=373842fcc7" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1384 CREDAT:3478796 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3536 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1384 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
32 929
Read events
32 784
Write events
101
Delete events
44
Modification events
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31089399 | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31089399 | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1384) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
40
Text files
116
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3536 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SRZUCU66.txt | text | |
MD5:E3851BCD961CCA9A7C0CFE00CF769FED | SHA256:612AEFC818B8035A7C164E37F720DD5BB7115BDD0EAC19DC96B93F037B670062 | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VEEDYNZT.txt | text | |
MD5:984B9EBE9EC7D913366C9B1B1E72E59B | SHA256:B7E341BC7A389ABECF5B8118BD011C53D2F87190C48F732C901E9DD2E381D6D0 | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:CF01AB691B9FD38601584494D613F12A | SHA256:76040CA2351F7946382A3C420CE1755DE1C7B3A8E7CD5ADD65838BA2A699F715 | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF4E0.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF4DF.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:02C0000B7F420EFDFDEEA3F8BDB2FC0F | SHA256:FC93E6A73FBDAB86871CCC62E398AFA0EA51360016682A92BEF257BA357344BB | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\15YRVNEA.htm | html | |
MD5:17EF158B602B449EAB1457D21DE8A5DC | SHA256:9F21C90D39E8A5B4CC359F73719C69C170CDABE6E2A0D3806452A93D1954C1FE | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:9C73C5F52713589CABBFC7331F81AEF4 | SHA256:53C607FF60826470E64FF58F823ED150F94436CC68B5BD97C0E0859B6F881EBA | |||
| 3536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F36C11AE96545FE7C5A9052C7AD3D5ED | binary | |
MD5:07F4D8FA39CA36786839D595F5D02475 | SHA256:FA71EF8B83268553E25779FAD8E6A8D7E5C732EB9A114B55332CF0645CB546C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
83
DNS requests
30
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3536 | iexplore.exe | GET | 304 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a08f35fbea17b647 | unknown | — | — | unknown |
3536 | iexplore.exe | GET | 304 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
3536 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
3536 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?86b4b67e50f1d6bf | unknown | compressed | 65.2 Kb | unknown |
3536 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?46a3771404230298 | unknown | compressed | 65.2 Kb | unknown |
3536 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2c64f22eaf0ba1e1 | unknown | compressed | 65.2 Kb | unknown |
3536 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3536 | iexplore.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgP%2BFe3uU5xfipmxnEpx5V6PbA%3D%3D | unknown | binary | 503 b | unknown |
3536 | iexplore.exe | GET | 301 | 34.120.190.48:80 | http://womenleadingchange.asia/wp-content/uploads/2024/02/Abhinav-Sharma-e1707896741954.jpeg | unknown | text | 24 b | unknown |
3536 | iexplore.exe | GET | 301 | 34.120.190.48:80 | http://womenleadingchange.asia/wp-content/uploads/2024/02/Aleli-Arcilla-scaled-e1707896799664.jpeg | unknown | text | 24 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3536 | iexplore.exe | 23.212.219.180:443 | haymarket.us20.list-manage.com | AKAMAI-AS | AU | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3536 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3536 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
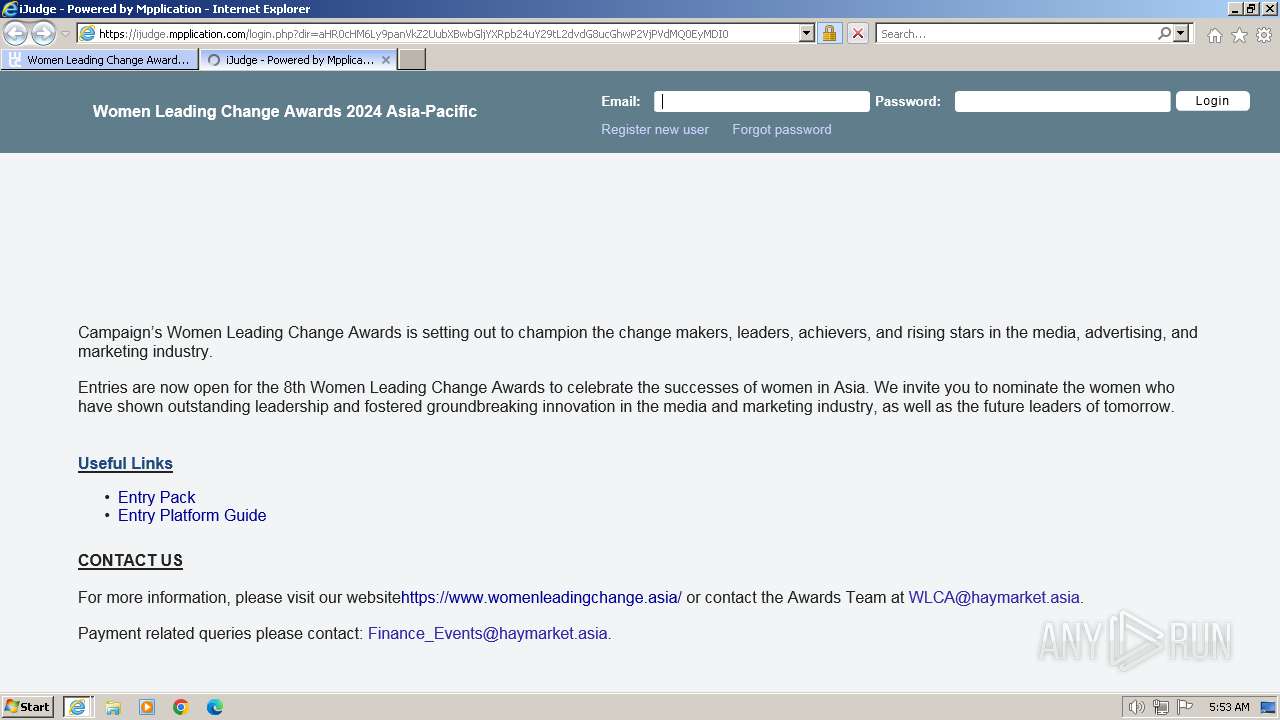
3536 | iexplore.exe | 34.120.190.48:443 | womenleadingchange.asia | GOOGLE-CLOUD-PLATFORM | US | unknown |
3536 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
3536 | iexplore.exe | 184.24.77.48:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3536 | iexplore.exe | 142.250.181.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
haymarket.us20.list-manage.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
womenleadingchange.asia |
| unknown |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
3536 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |