| File name: | en-us_windows_server_2025_updated_may_2025_x64_dvd_9c776dbb.iso.cmd |
| Full analysis: | https://app.any.run/tasks/f3f4d36b-93fb-408f-91fe-ba72524df2f1 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 04:17:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text |
| MD5: | 4BFB21324383406182E42813CBA3EFA2 |
| SHA1: | 6B3B78F61EF5115133A7267B072D2135351A8C1D |
| SHA256: | AF50D055949892808AD95E588CF12A68FA846D42AAF274E56D396BC3B82A1B92 |
| SSDEEP: | 48:z/sW+w+fC0Uymve1bIJOepRSY0y1Wg7rwekEny3fRvbuLL8Ui:z7+w+fpukleSY06Xwe/yvluLIUi |
MALICIOUS
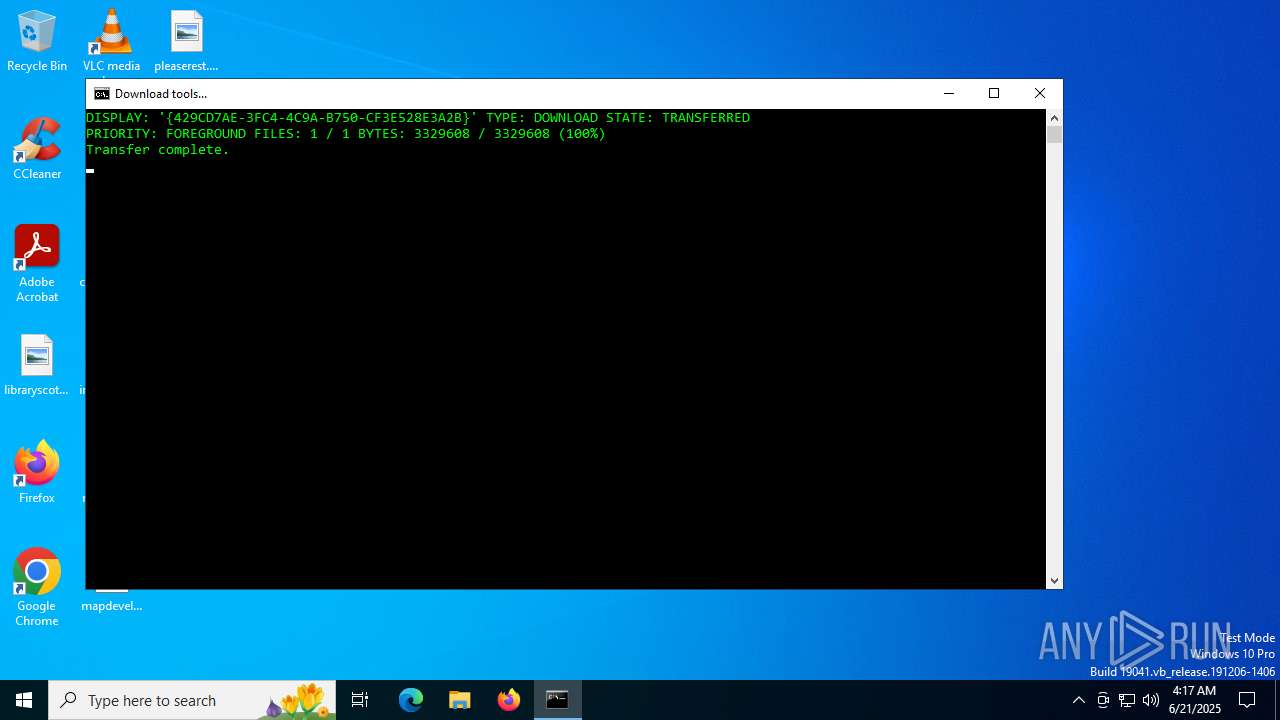
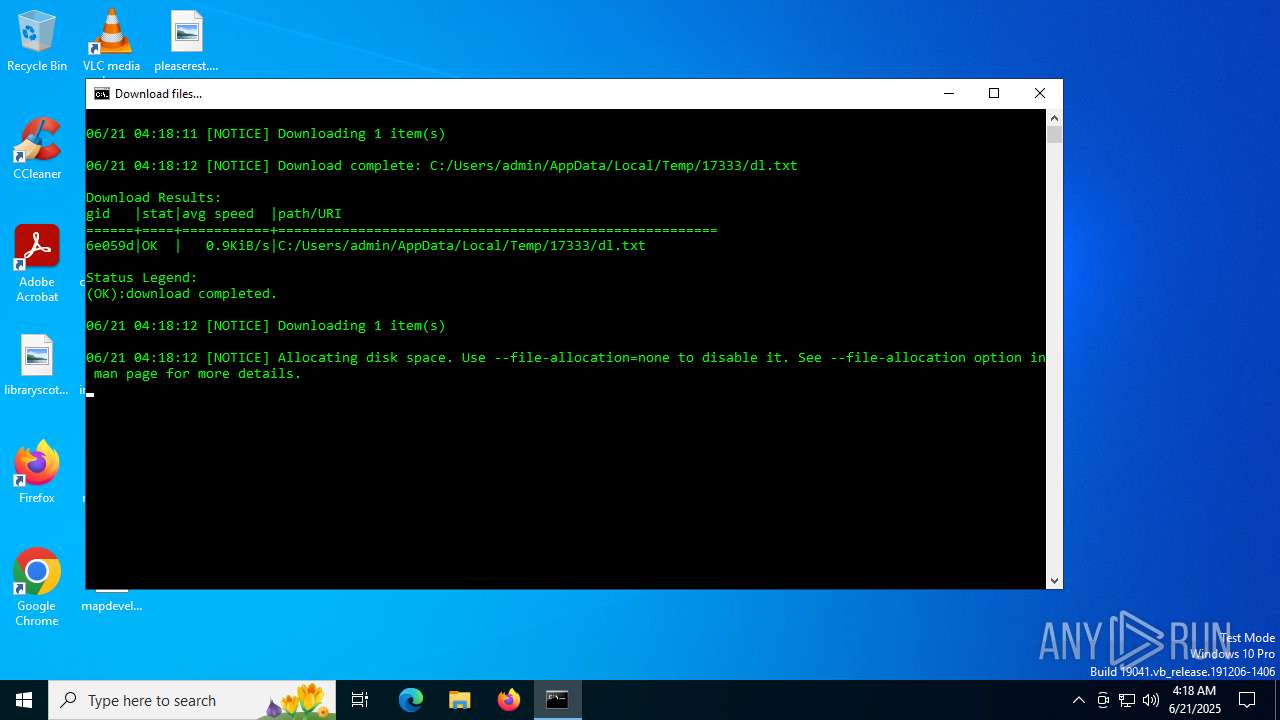
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 5400)
SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1520)
Executable content was dropped or overwritten
- expand.exe (PID: 3840)
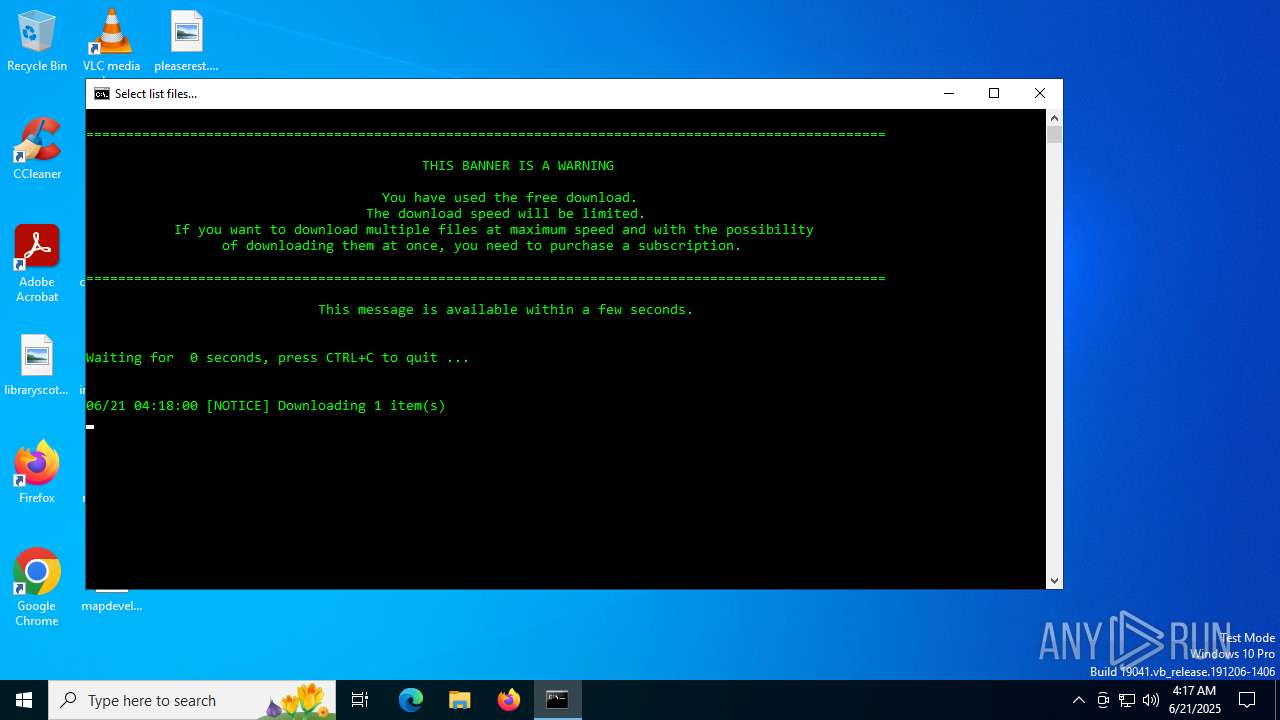
The executable file from the user directory is run by the CMD process
- aria2c.exe (PID: 4236)
- aria2c.exe (PID: 760)
- aria2c.exe (PID: 6360)
Drops 7-zip archiver for unpacking
- expand.exe (PID: 3840)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5400)
Application launched itself
- cmd.exe (PID: 5400)
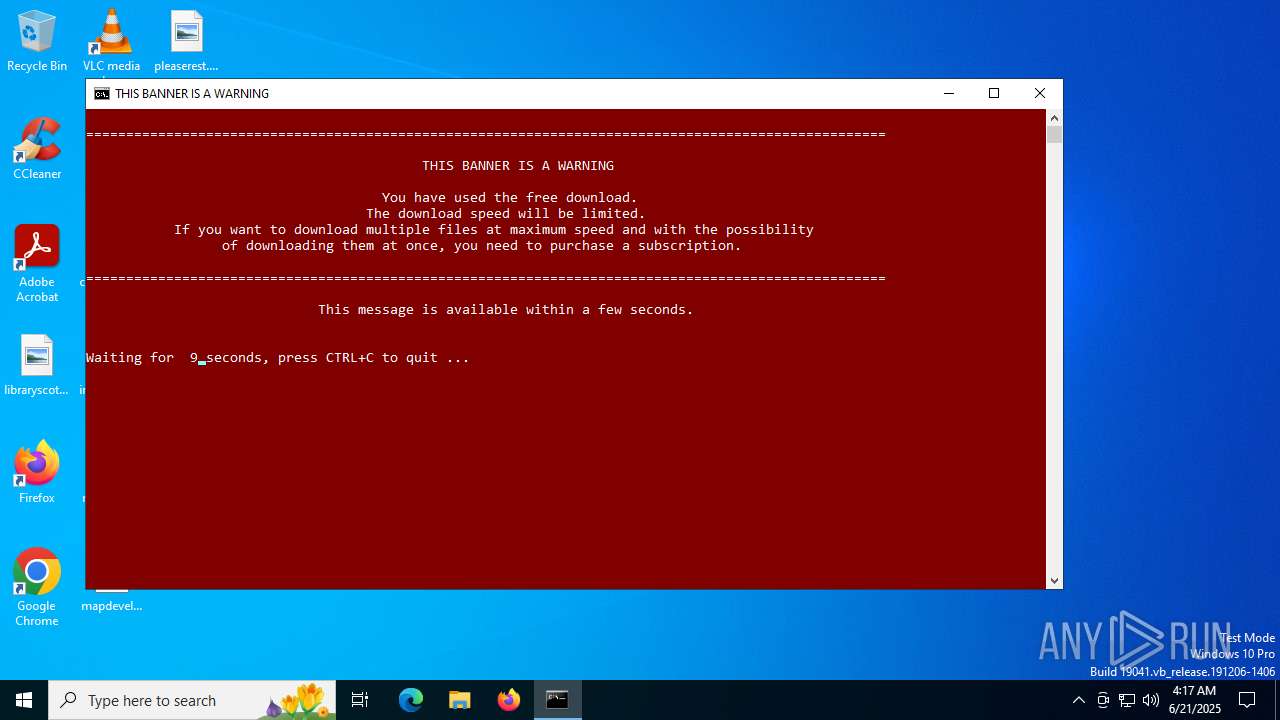
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5400)
INFO
Uses BITSADMIN.EXE
- cmd.exe (PID: 1520)
Checks supported languages
- expand.exe (PID: 3840)
- aria2c.exe (PID: 4236)
- aria2c.exe (PID: 760)
- aria2c.exe (PID: 6360)
Reads the machine GUID from the registry
- expand.exe (PID: 3840)
- aria2c.exe (PID: 760)
- aria2c.exe (PID: 6360)
- aria2c.exe (PID: 4236)
Create files in a temporary directory
- expand.exe (PID: 3840)
- aria2c.exe (PID: 6360)
- aria2c.exe (PID: 760)
- aria2c.exe (PID: 4236)
The sample compiled with english language support
- expand.exe (PID: 3840)
Reads the computer name
- aria2c.exe (PID: 6360)
- aria2c.exe (PID: 760)
- aria2c.exe (PID: 4236)
Checks operating system version
- cmd.exe (PID: 5400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
151
Monitored processes
16
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | "C:\Users\admin\AppData\Local\Temp\bin\aria2c.exe" -x1 -s1 -d"C:\Users\admin\AppData\Local\Temp\17333" -o"list.txt" "https://files.rg-adguard.net/file/81503de4-c83e-3184-4063-10343712728c/list" --disable-ipv6 | C:\Users\admin\AppData\Local\Temp\bin\aria2c.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\cmd.exe /c type "C:\Users\admin\AppData\Local\Temp\17333\list.txt" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | C:\WINDOWS\system32\cmd.exe /c bitsadmin.exe /CREATE /DOWNLOAD "Download Tools" | findstr "Created job" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1720 | findstr "Created job" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | CHOICE /c fs /n /m "Save all or just the requested file?" | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | bitsadmin /transfer {429CD7AE-3FC4-4C9A-B750-CF3E528E3A2B} /download /priority foreground https://files.rg-adguard.net/tools "C:\Users\admin\AppData\Local\Temp\tools.cab" | C:\Windows\System32\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.8.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | C:\WINDOWS\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3800 | timeout /t 10 /NOBREAK | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | expand "tools.cab" -f:* .\ | C:\Windows\System32\expand.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 153
Read events
1 153
Write events
0
Delete events
0
Modification events
Executable files
7
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | expand.exe | C:\Users\admin\AppData\Local\Temp\bin\7z.cmd | text | |
MD5:5DD57ED7AFC26FFC598AF730B224CF52 | SHA256:25C5A15960D922036F863879914C891A93830E773630F6E7EA4FCE35398AA440 | |||
| 3840 | expand.exe | C:\Users\admin\AppData\Local\Temp\bin\aria2c.exe | executable | |
MD5:8C71B86BF407C05BAF11E8D296B9C8B8 | SHA256:BE2099C214F63A3CB4954B09A0BECD6E2E34660B886D4C898D260FEBFE9D70C2 | |||
| 3840 | expand.exe | C:\Users\admin\AppData\Local\Temp\bin\smv.cmd | text | |
MD5:4DD25E07C4506DB89FE59962235E5CD4 | SHA256:732B5B32C38AB6BADDAB060B2DF2BF21A75F97E8B9F7055DCDB245D10FE74A90 | |||
| 3840 | expand.exe | C:\Users\admin\AppData\Local\Temp\bin\7z.exe | executable | |
MD5:9A1DD1D96481D61934DCC2D568971D06 | SHA256:8CEBB25E240DB3B6986FCAED6BC0B900FA09DAD763A56FB71273529266C5C525 | |||
| 3840 | expand.exe | C:\Users\admin\AppData\Local\Temp\bin\7z.dll | executable | |
MD5:4E35A902CA8ED1C3D4551B1A470C4655 | SHA256:77222E81CB7004E8C3E077AADA02B555A3D38FB05B50C64AFD36CA230A8FD5B9 | |||
| 3840 | expand.exe | C:\Users\admin\AppData\Local\Temp\bin\smv.exe | executable | |
MD5:F3C45AE821B803E521B9E14B4B87EB1A | SHA256:93FBA2D50921565BCF283075BB3B8195F2B9B10719EC5123FBF06EA596A782B4 | |||
| 4236 | aria2c.exe | C:\Users\admin\AppData\Local\Temp\tmp\81503de4-c83e-3184-4063-10343712728c.7z.aria2 | binary | |
MD5:A07AB05DCA4A1B6C9BF92C6892E0158A | SHA256:4185E79256833FFEEAA4A3C1858A4DD3A5EE5E04C64096F97CDE338FC8CDD3EF | |||
| 6360 | aria2c.exe | C:\Users\admin\AppData\Local\Temp\17333\dl.txt | text | |
MD5:7A24DE9E0FC97ACD05A0DF2A06B22807 | SHA256:A607C8738E553CC341953459C0414DA0FC87F0701B0CCAD96E9952D15E453802 | |||
| 4236 | aria2c.exe | C:\Users\admin\AppData\Local\Temp\tmp\81503de4-c83e-3184-4063-10343712728c.7z.aria2__temp | binary | |
MD5:A07AB05DCA4A1B6C9BF92C6892E0158A | SHA256:4185E79256833FFEEAA4A3C1858A4DD3A5EE5E04C64096F97CDE338FC8CDD3EF | |||
| 760 | aria2c.exe | C:\Users\admin\AppData\Local\Temp\17333\list.txt | text | |
MD5:E998DDF86F27940CB22D2F0C1BF7C7CF | SHA256:777D58D2675DCE7A4DF7564E731672A9275DCB9D184B7EC4A0B1E31327D31245 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 184.25.50.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
3740 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3740 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6160 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2028 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4140 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 184.25.50.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2136 | svchost.exe | 104.21.48.1:443 | files.rg-adguard.net | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
files.rg-adguard.net |
| whitelisted |
c.pki.goog |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
c8kcmvb5.rg-adguard.net |
| whitelisted |
login.live.com |
| whitelisted |