| File name: | RedLine_V3.0-BobTheFrog.zip |
| Full analysis: | https://app.any.run/tasks/9bb21343-9d14-4ece-bcbf-06d40f1dc092 |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2019, 06:40:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | EE040E2178686C83C5BBFD41F6E770DF |
| SHA1: | 7B7AF40712D215BDACC544447259A6A521FD904F |
| SHA256: | AF4F9F5F964CB6E0F140E52FC7B304A868C3D54F768F824F23918B0C3982F383 |
| SSDEEP: | 12288:8FUzctzeU3HSzimPx6NjQVMXkucjPuA/uCuH+OmKIQP8YMYcLkn4kEG6yZzBh4kZ:8FUgtj3HSXPxejQVMXCj1uCuHx9PAQ4q |
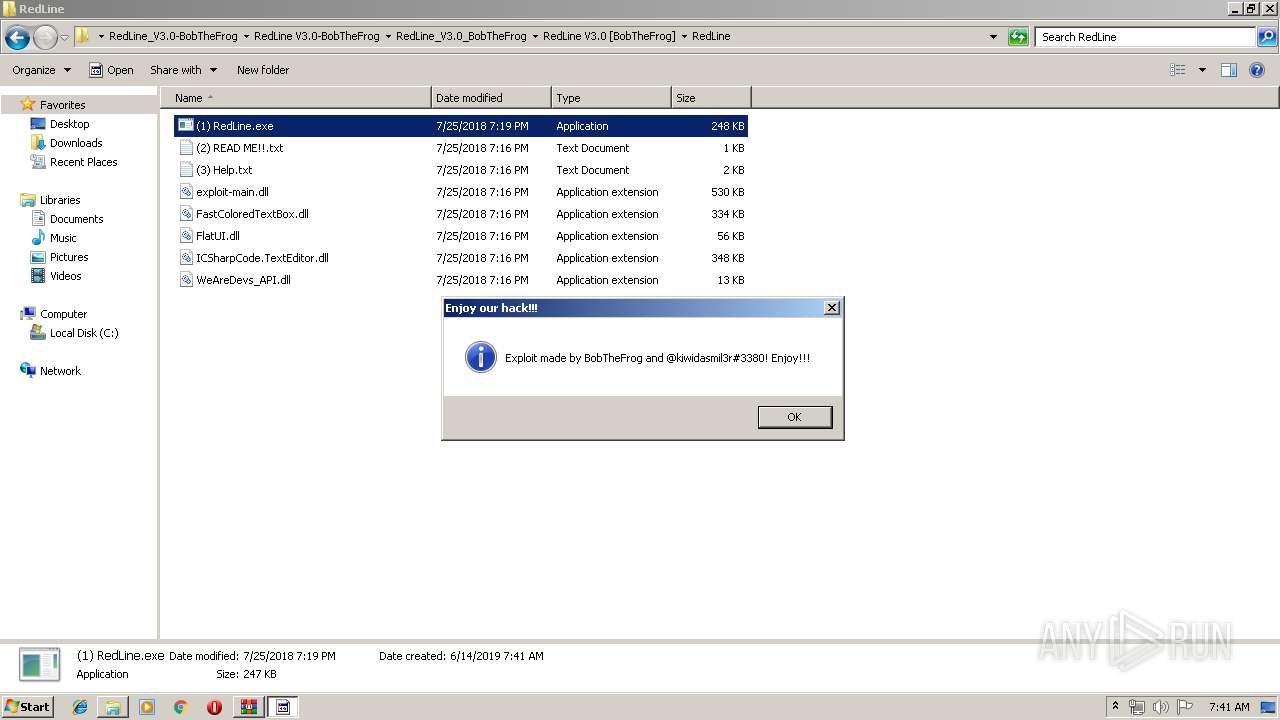
MALICIOUS
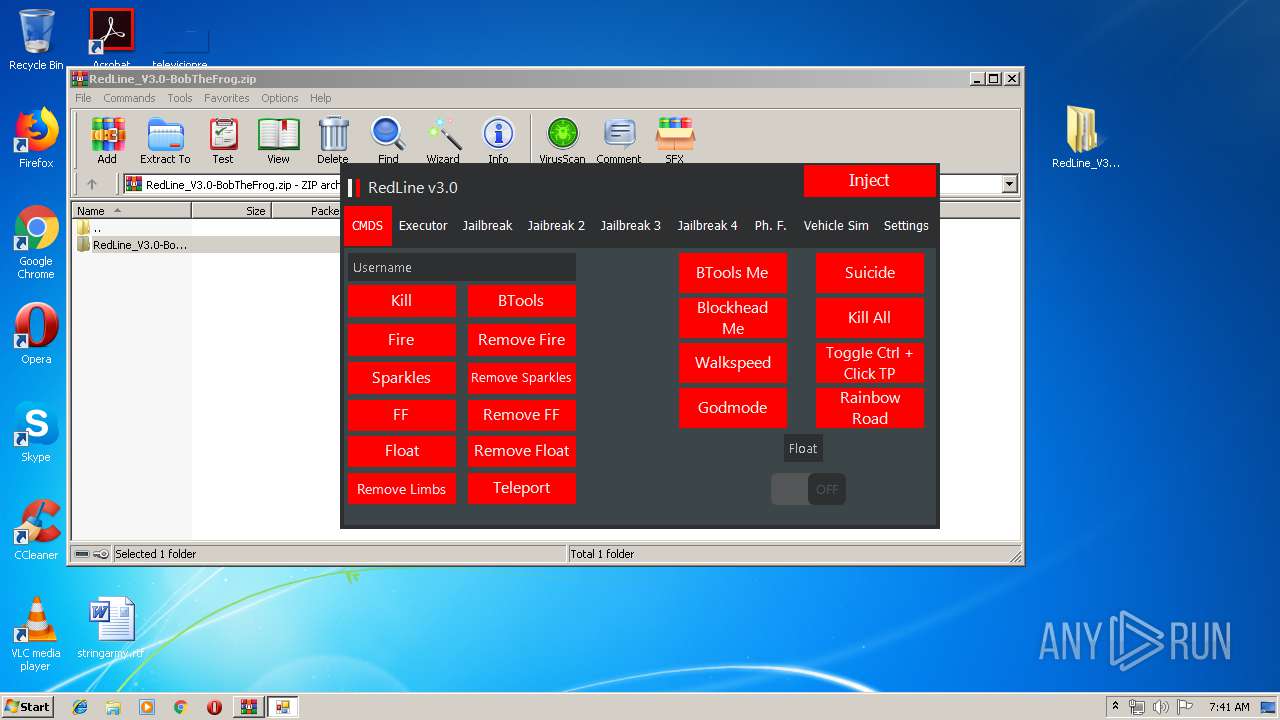
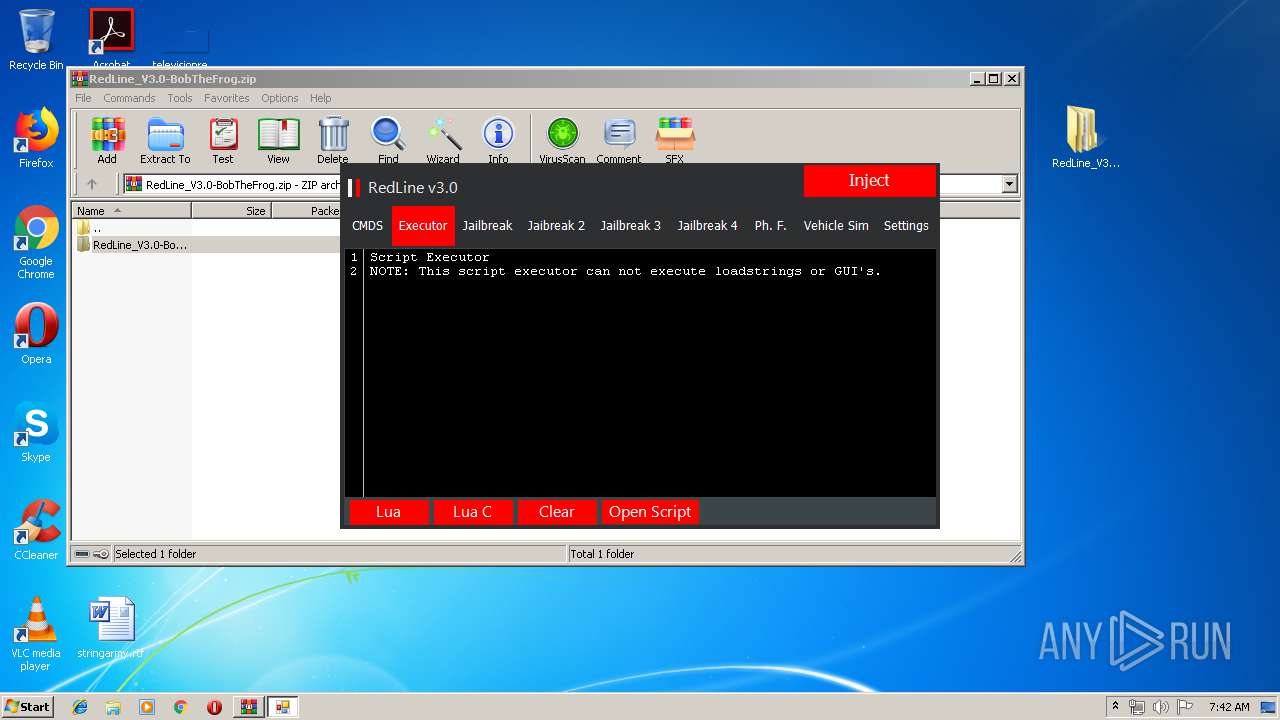
Loads dropped or rewritten executable
- (1) RedLine.exe (PID: 2304)
- SearchProtocolHost.exe (PID: 2920)
Application was dropped or rewritten from another process
- (1) RedLine.exe (PID: 2304)
SUSPICIOUS
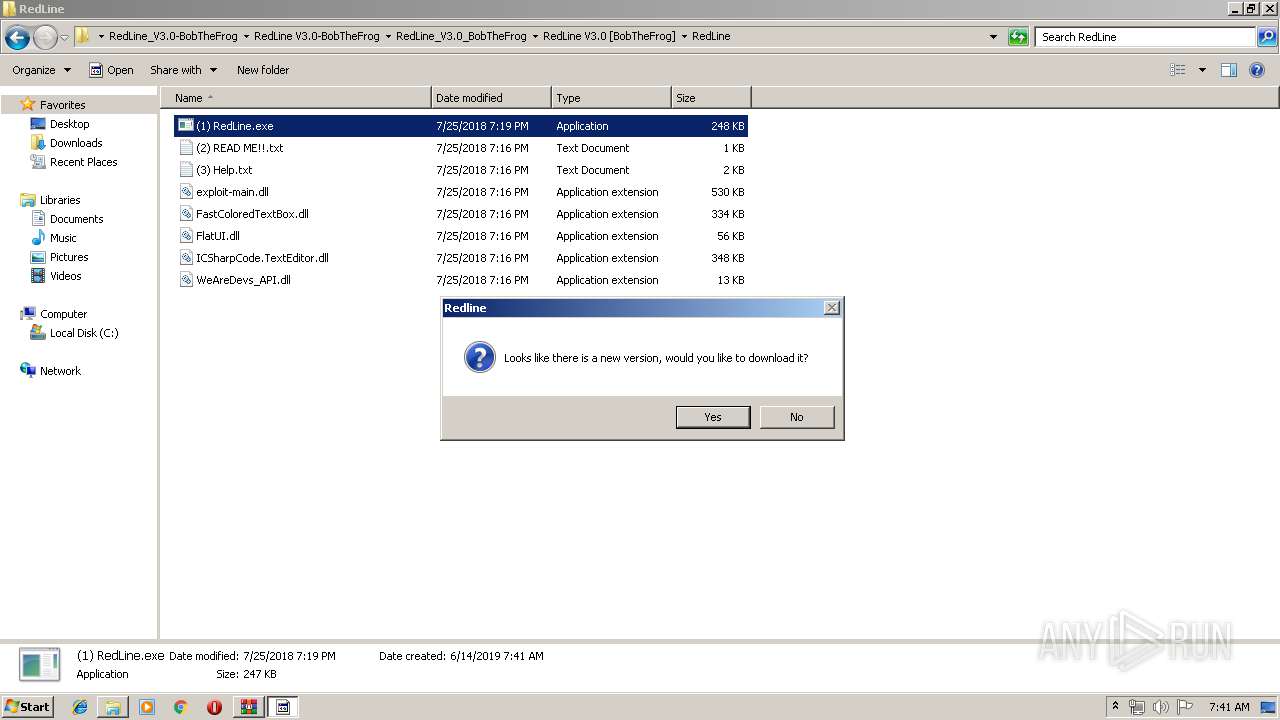
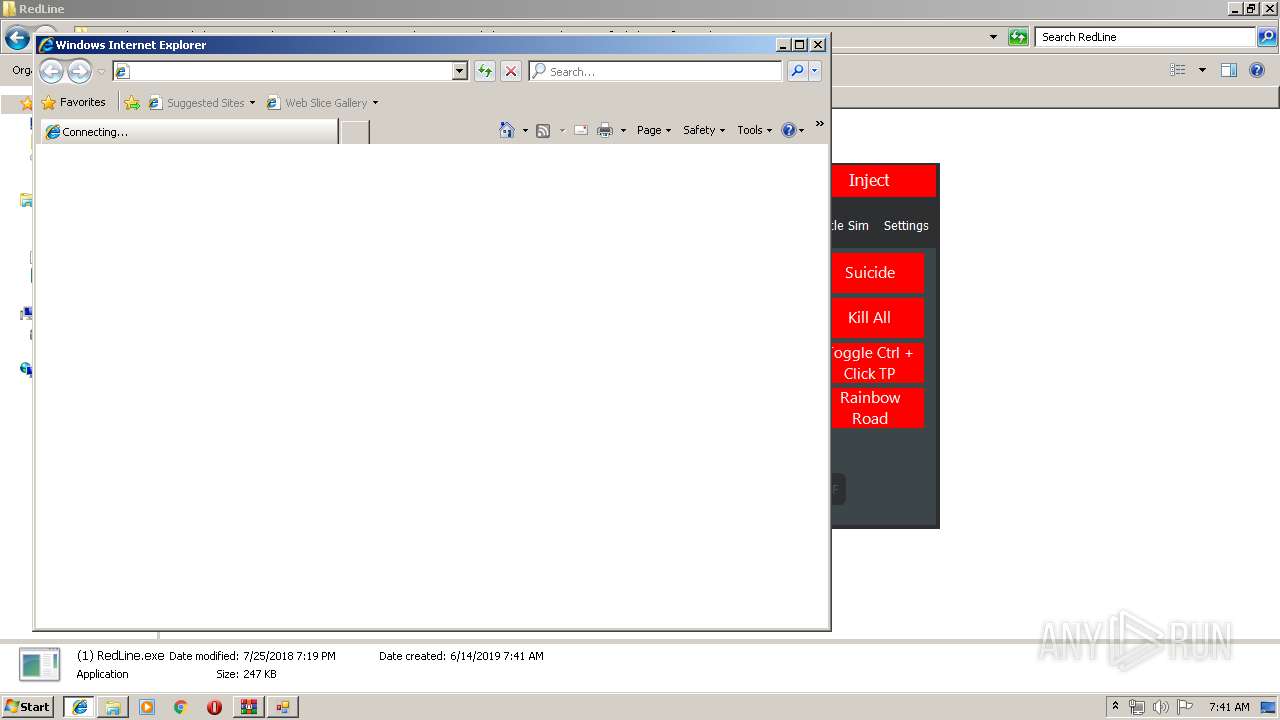
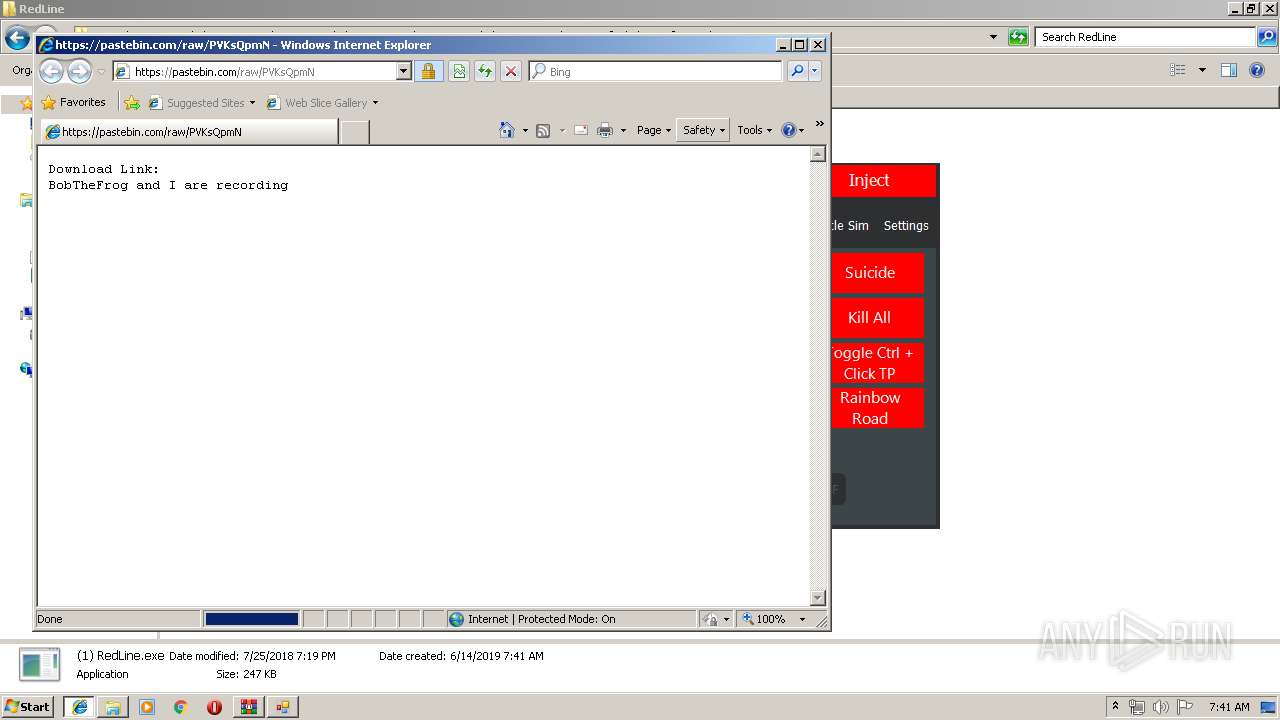
Starts Internet Explorer
- (1) RedLine.exe (PID: 2304)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 284)
Reads Environment values
- (1) RedLine.exe (PID: 2304)
INFO
Manual execution by user
- (1) RedLine.exe (PID: 2304)
Application launched itself
- iexplore.exe (PID: 3952)
Changes internet zones settings
- iexplore.exe (PID: 3952)
Creates files in the user directory
- iexplore.exe (PID: 116)
- iexplore.exe (PID: 3952)
Reads internet explorer settings
- iexplore.exe (PID: 116)
Reads Internet Cache Settings
- iexplore.exe (PID: 3952)
- iexplore.exe (PID: 116)
Reads settings of System Certificates
- iexplore.exe (PID: 3952)
Changes settings of System certificates
- iexplore.exe (PID: 3952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:07:25 19:16:01 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
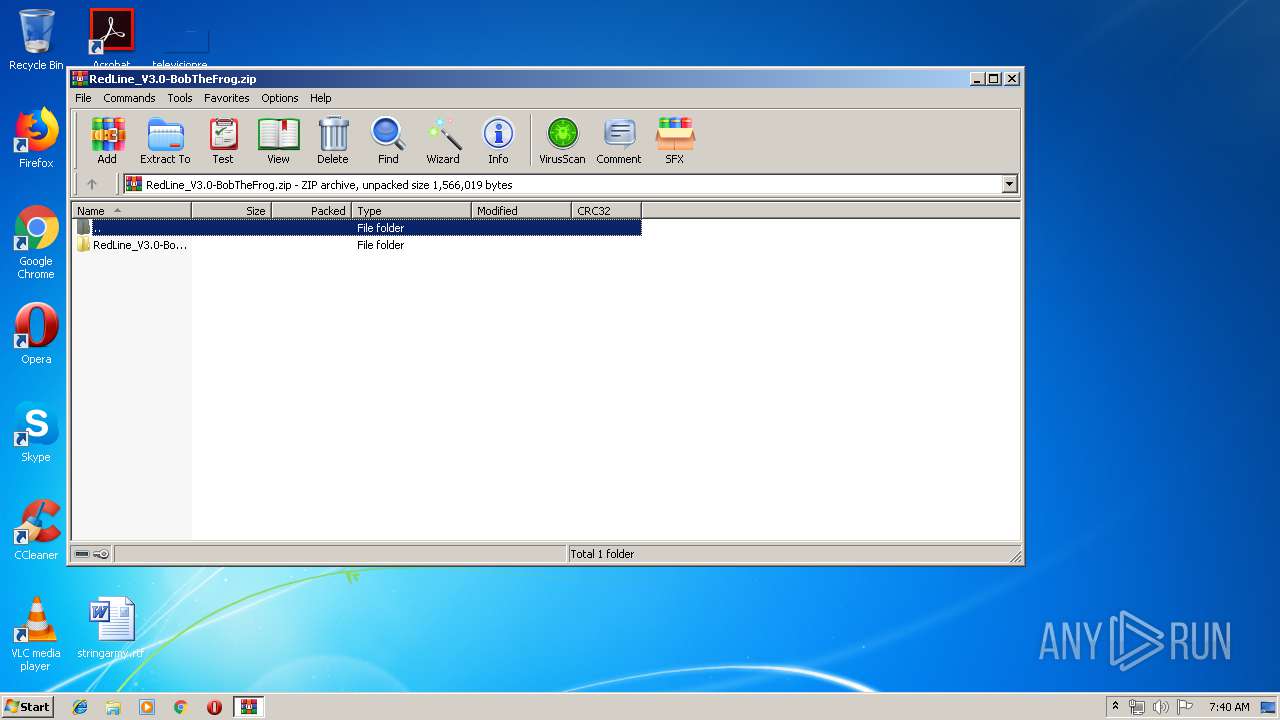
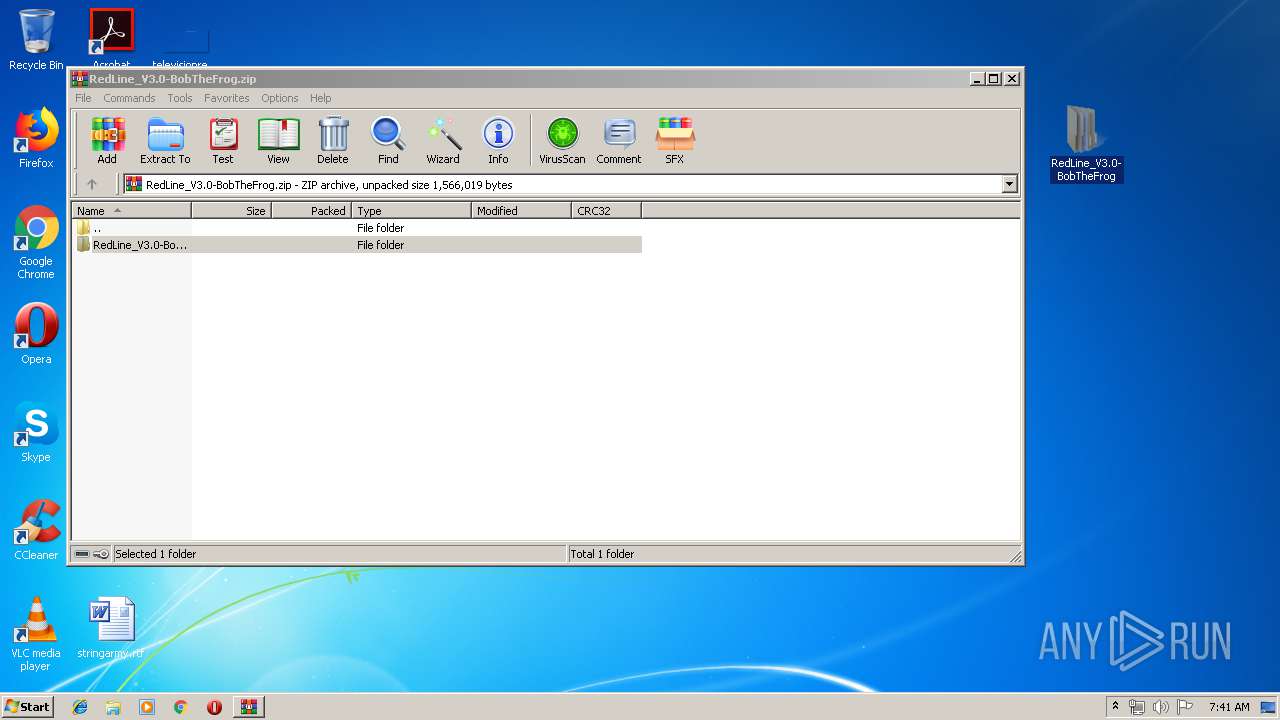
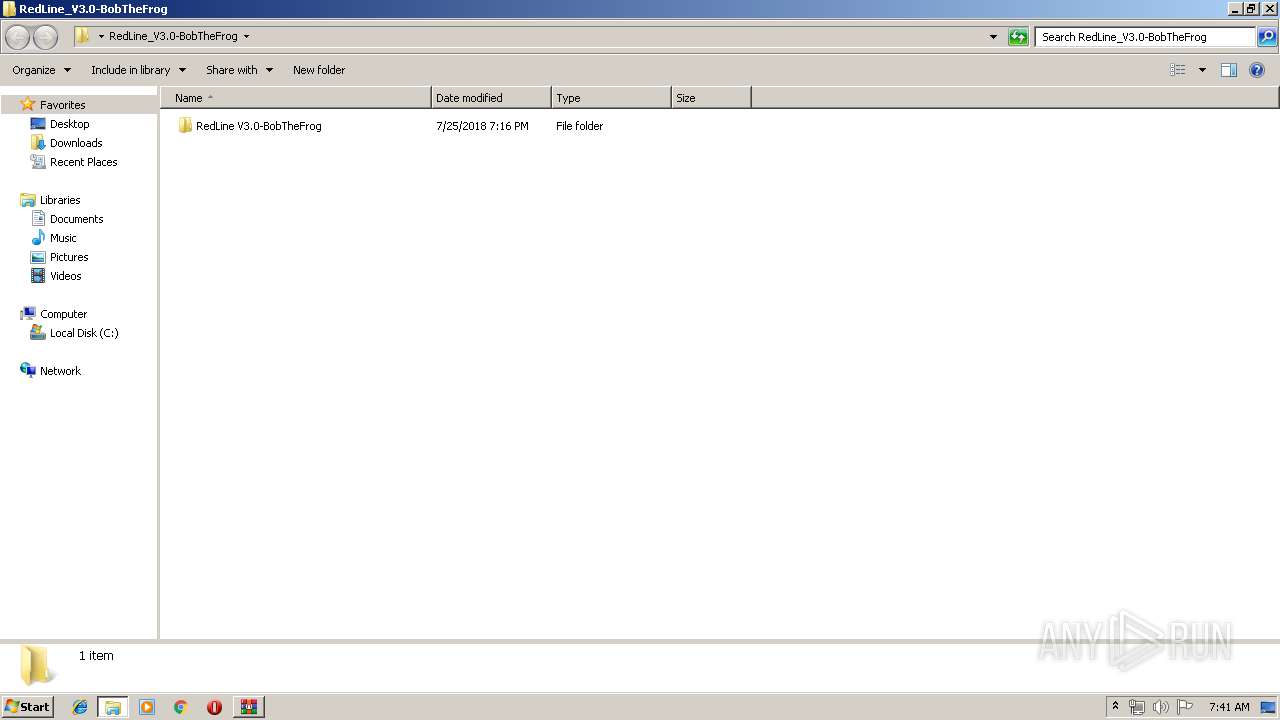
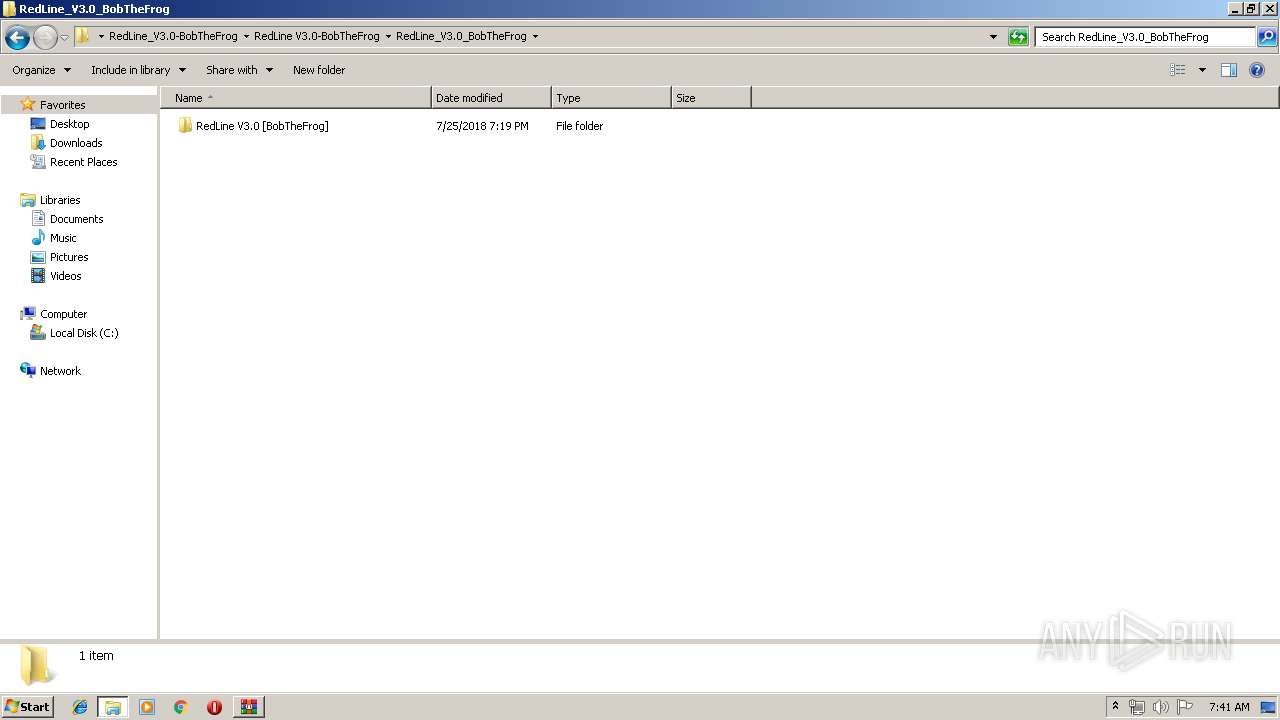
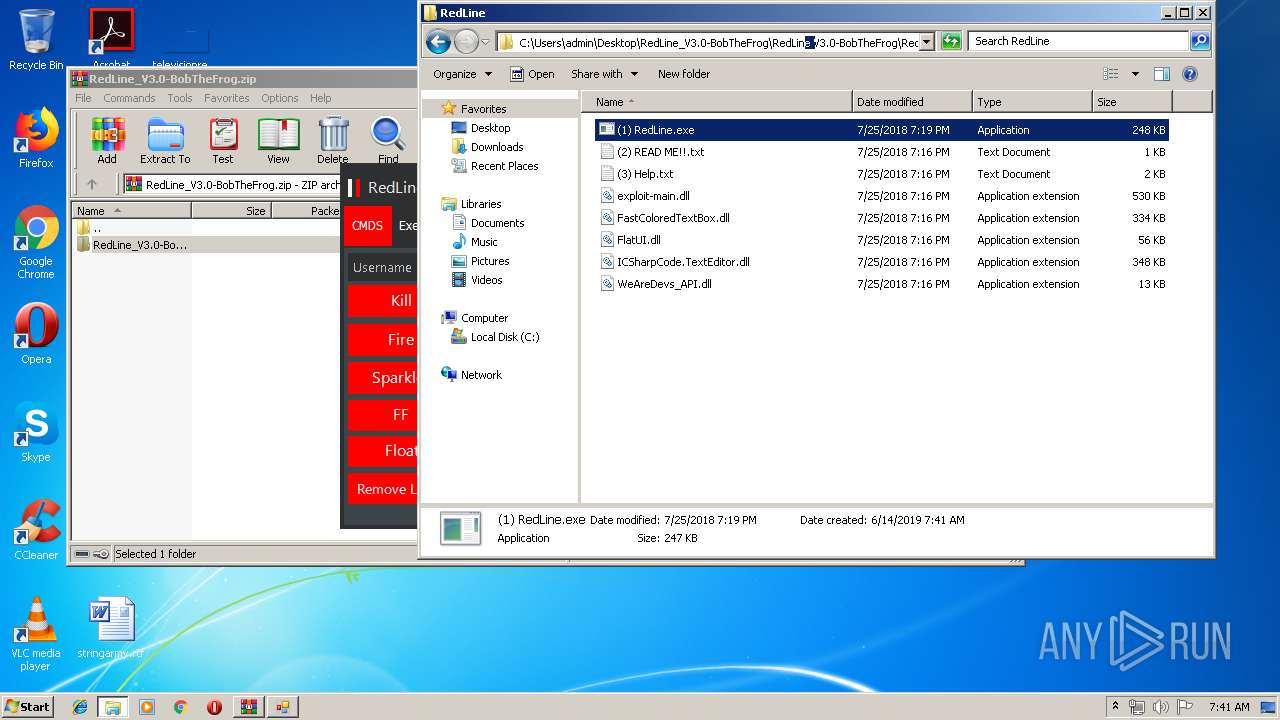
| ZipFileName: | RedLine_V3.0-BobTheFrog/RedLine V3.0-BobTheFrog/ |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3952 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\RedLine_V3.0-BobTheFrog.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
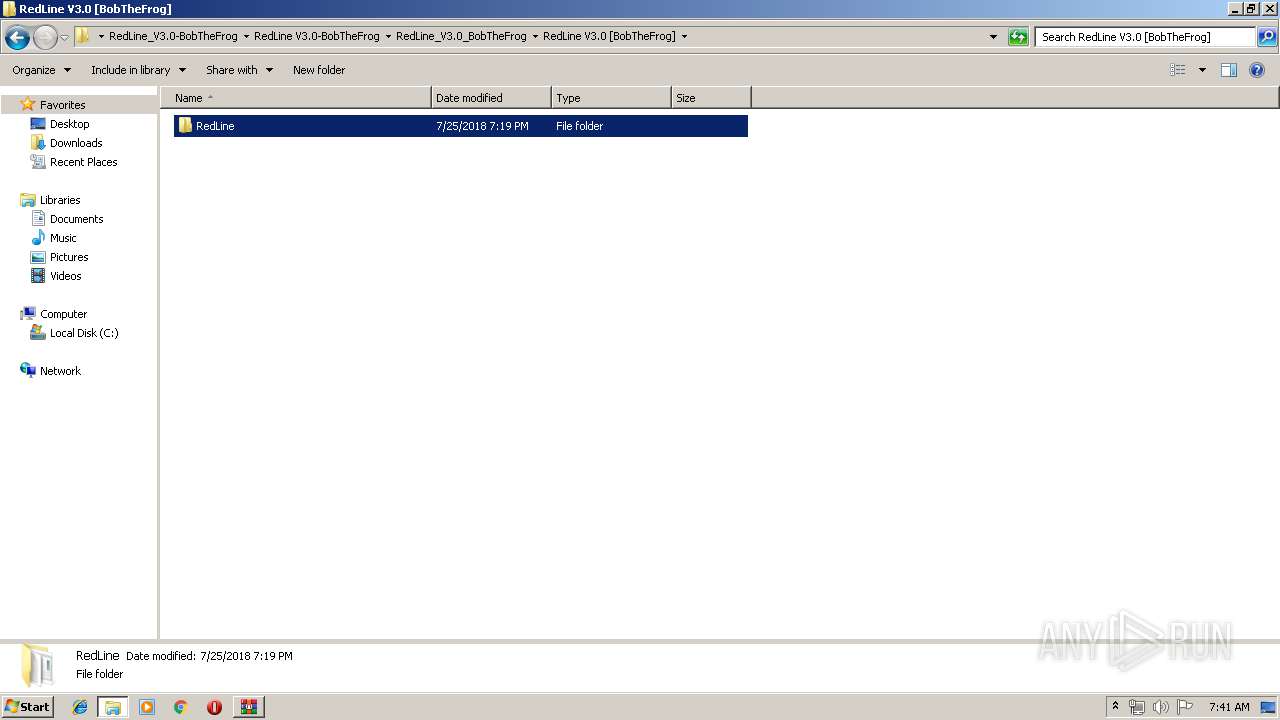
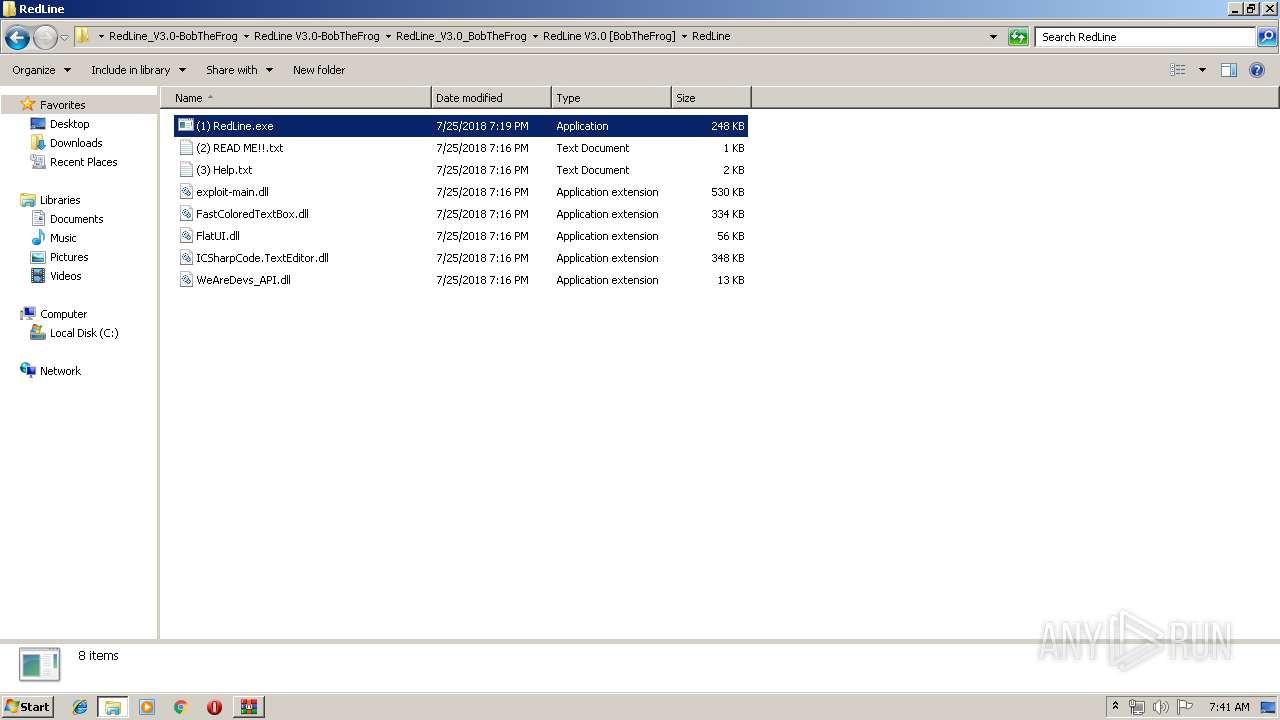
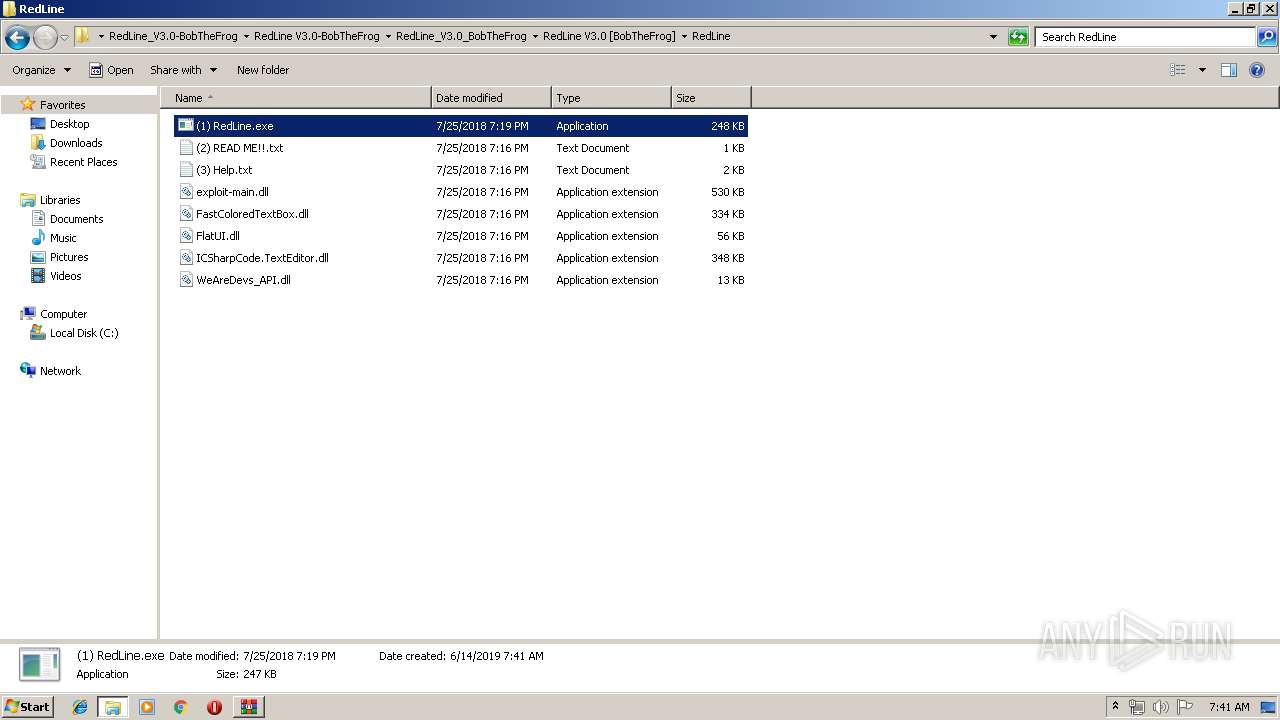
| 2304 | "C:\Users\admin\Desktop\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\(1) RedLine.exe" | C:\Users\admin\Desktop\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\(1) RedLine.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Blank_Space v1.1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2920 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3952 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | (1) RedLine.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 253
Read events
1 141
Write events
107
Delete events
5
Modification events
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RedLine_V3.0-BobTheFrog.zip | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2920) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2920) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
6
Suspicious files
3
Text files
15
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa284.47680\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\exploit-main.dll | executable | |
MD5:— | SHA256:— | |||
| 284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa284.47680\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\(3) Help.txt | text | |
MD5:— | SHA256:— | |||
| 284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa284.47680\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\(2) READ ME!!.txt | text | |
MD5:— | SHA256:— | |||
| 284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa284.47680\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\FastColoredTextBox.dll | executable | |
MD5:B746707265772B362C0BA18D8D630061 | SHA256:3701B19CCDAC79B880B197756A972027E2AC609EBED36753BD989367EA4EF519 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RPSNZPPU\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Feeds Cache\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0A48791E64D6B813.TMP | — | |
MD5:— | SHA256:— | |||
| 284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa284.47680\RedLine_V3.0-BobTheFrog\RedLine V3.0-BobTheFrog\RedLine_V3.0_BobTheFrog\RedLine V3.0 [BobTheFrog]\RedLine\WeAreDevs_API.dll | executable | |
MD5:286B3F23F10C9D11101132E6E80515E9 | SHA256:9AD9B337FBEC7D9F2A0592C3D2384F09E64CFB033EB602AD1FD732E72C20338E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2304 | (1) RedLine.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
116 | iexplore.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
3952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3952 | iexplore.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.bing.com |
| whitelisted |