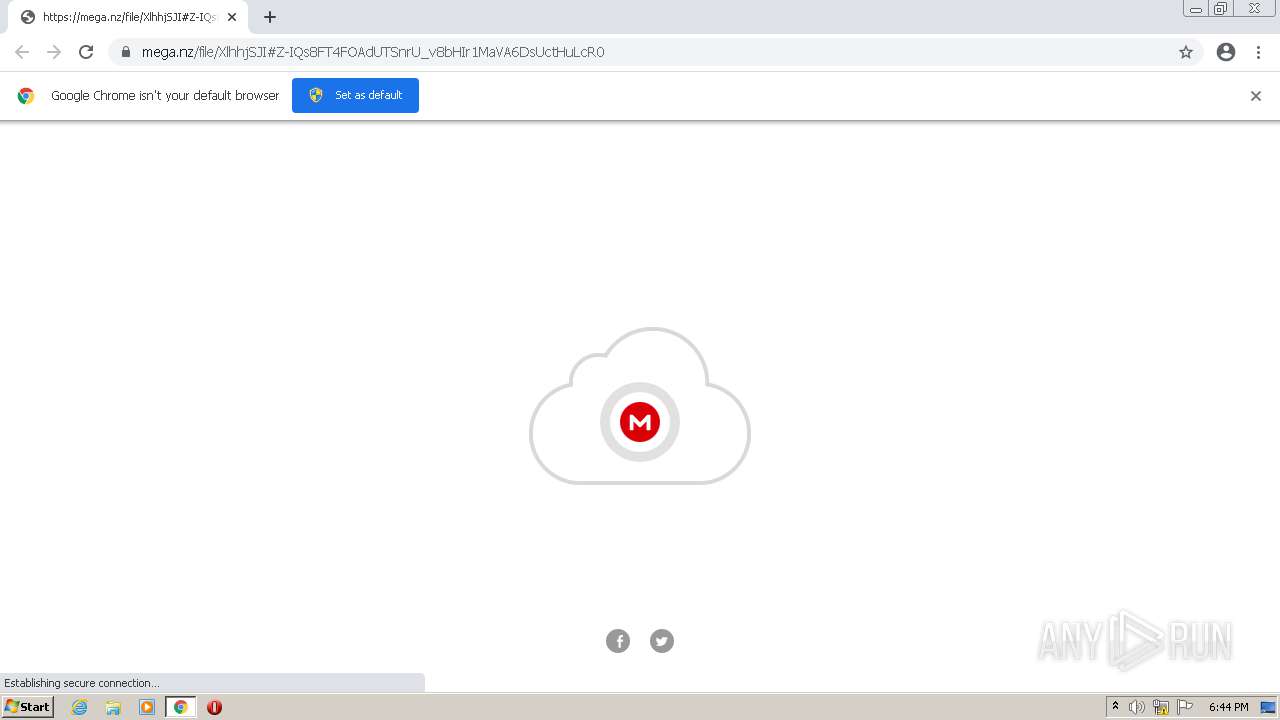
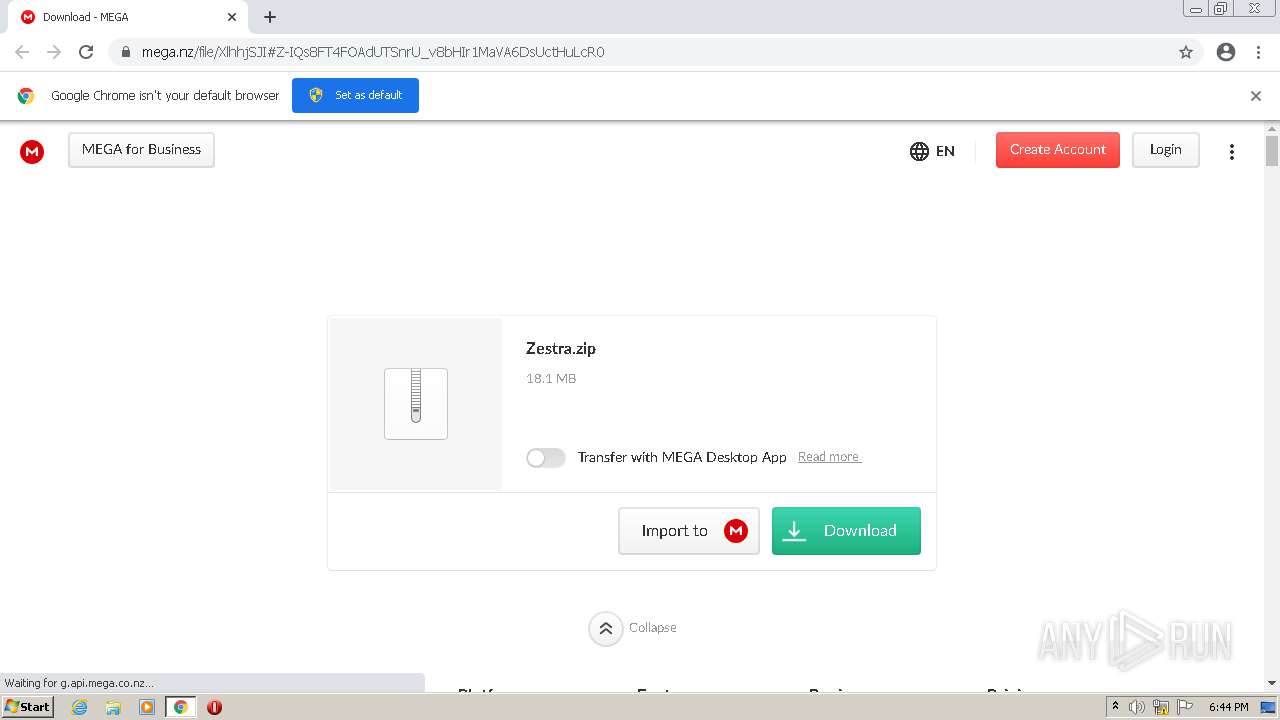
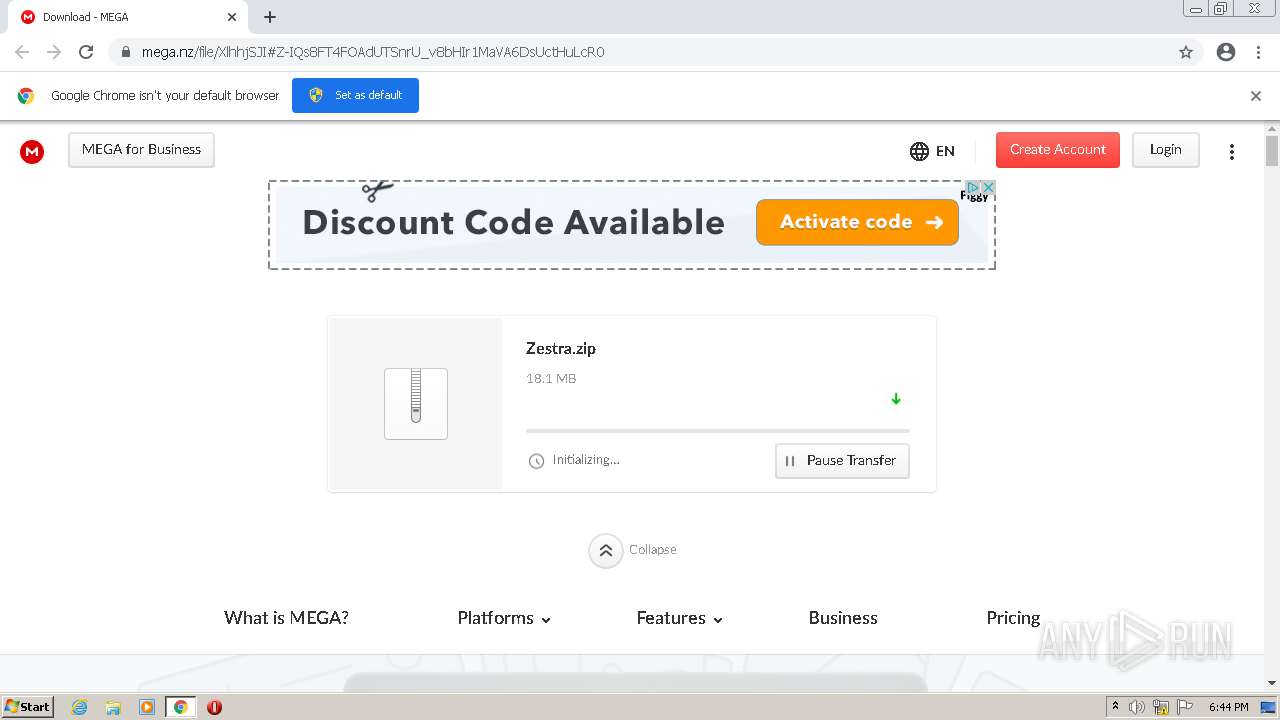
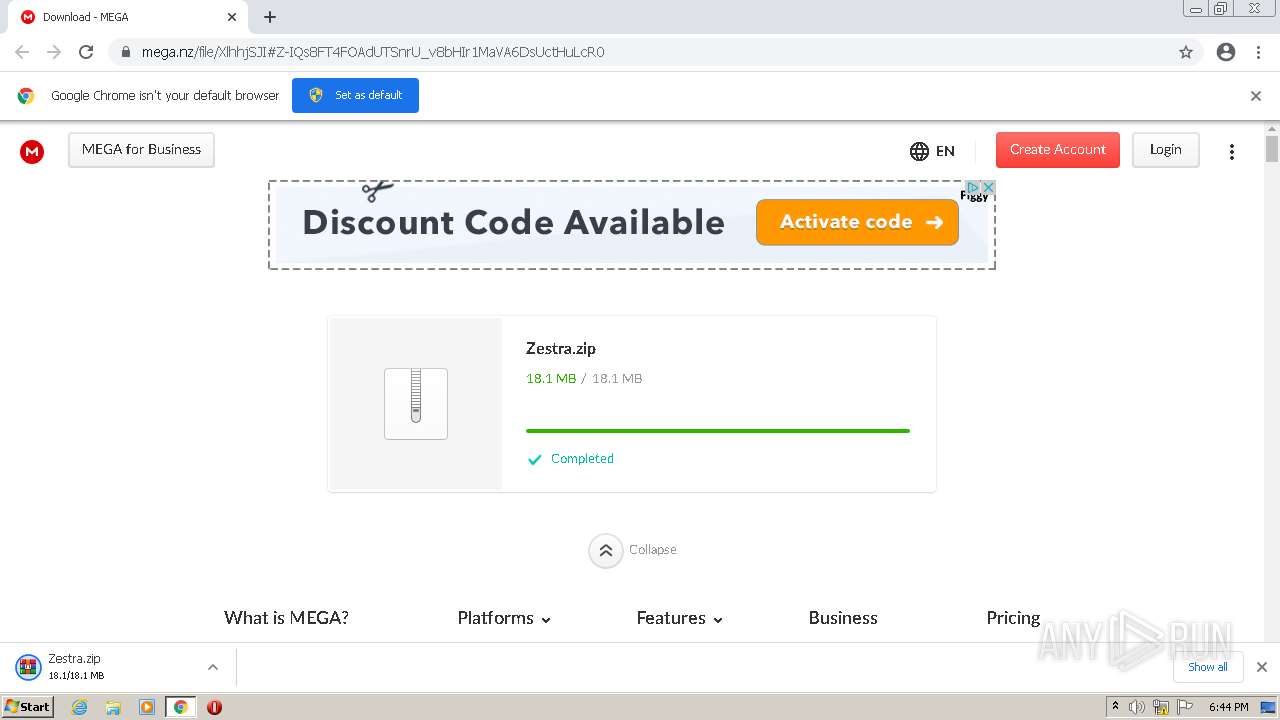
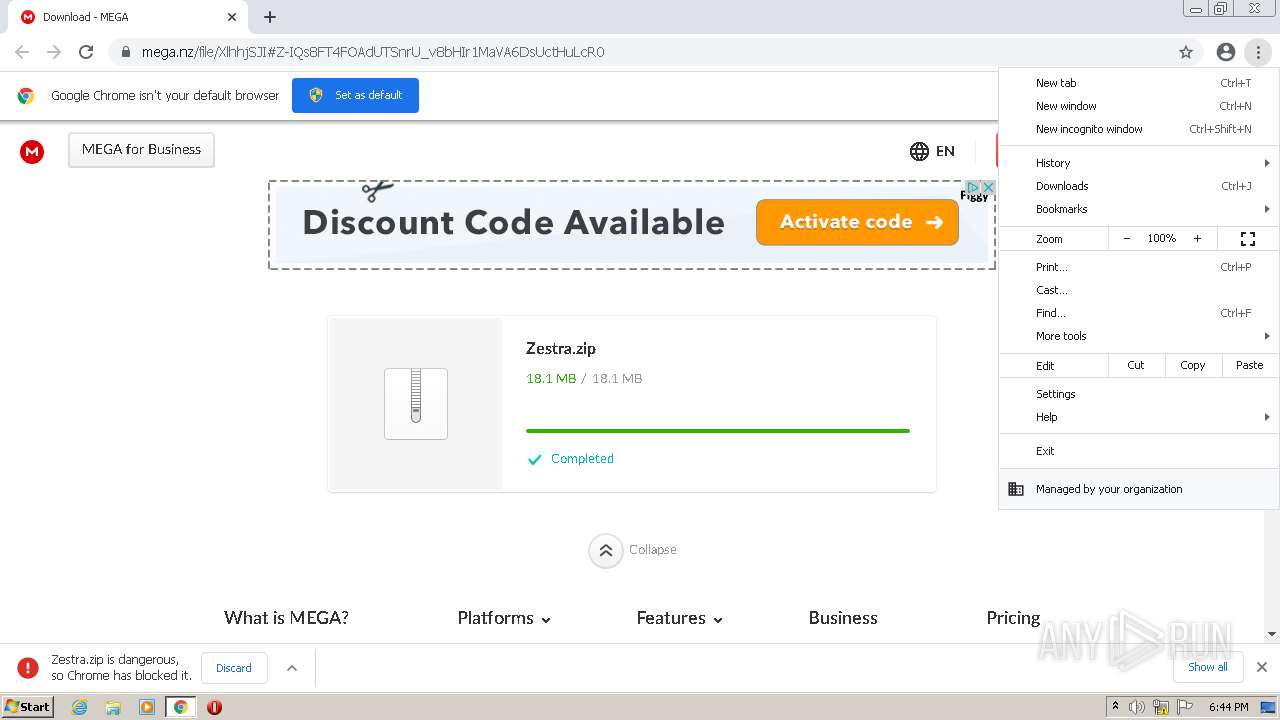
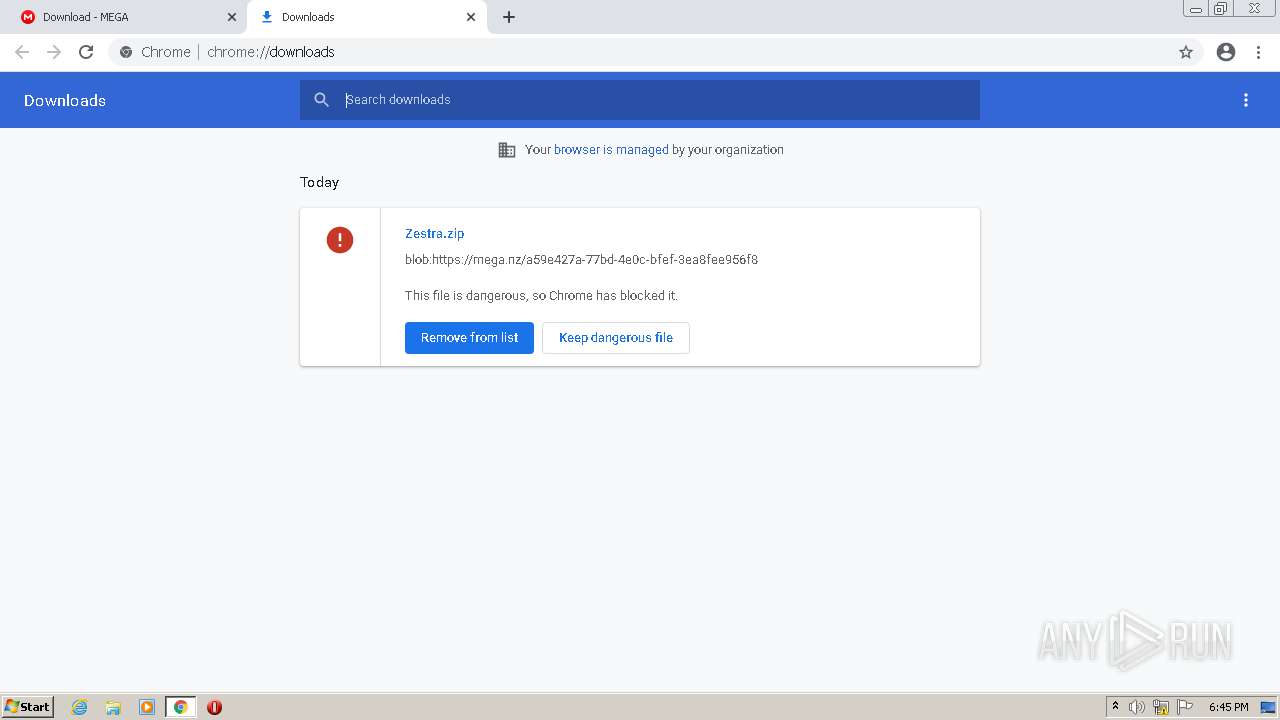
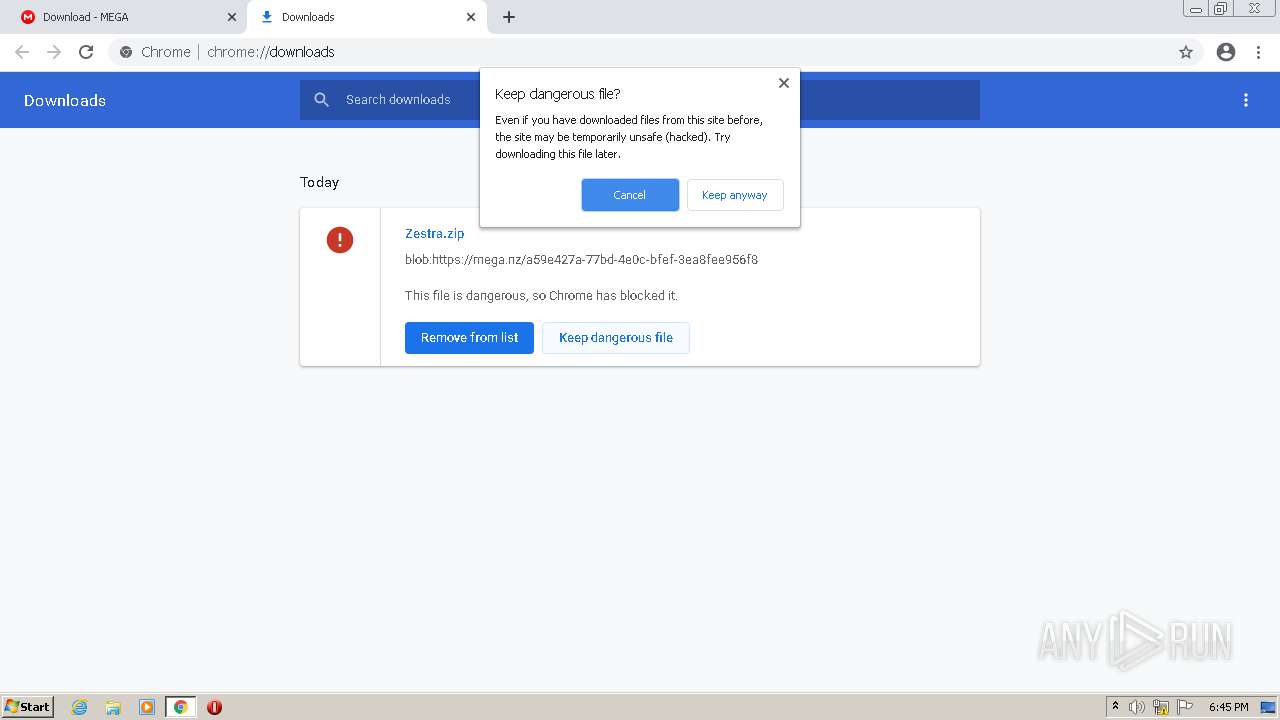
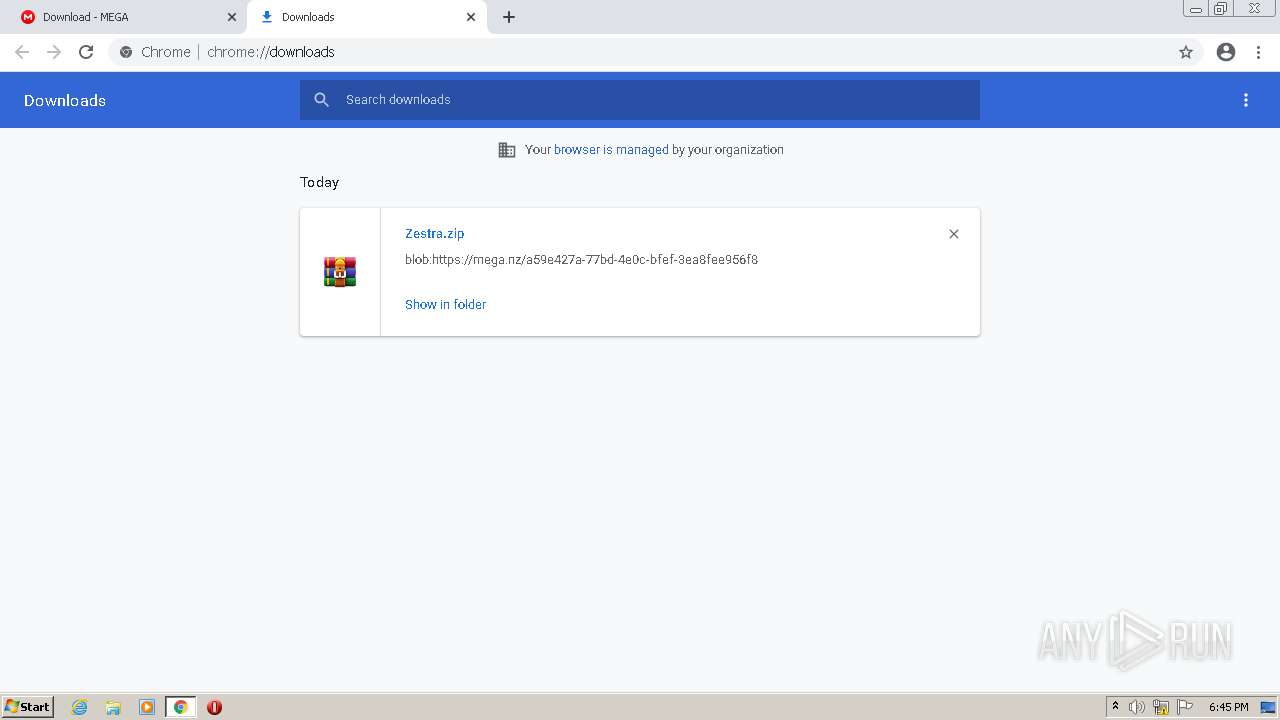
| URL: | https://mega.nz/file/XlhhjSJI#Z-IQs8FT4FOAdUTSnrU_v8bHIr1MaVA6DsUctHuLcR0 |
| Full analysis: | https://app.any.run/tasks/b7d51824-658a-408f-ae37-d6239cd3b241 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2021, 17:44:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AEC338057BF1523187528A3038ADCFE6 |
| SHA1: | C17E32482BA6983B7691CFE7A5D029F208489DE5 |
| SHA256: | AF4726C7A3CCB21662A6FC02D3567BB645248FFD7891DBD119ECF34FD5487B7A |
| SSDEEP: | 3:N8X/iYNiZCxXQHttztwGDl:2picQHtBtzB |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2864)
Application was dropped or rewritten from another process
- Zestra.exe (PID: 696)
- Zestra.exe (PID: 2188)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2092)
- Zestra.exe (PID: 696)
- Zestra.exe (PID: 2188)
SUSPICIOUS
Reads Microsoft Outlook installation path
- chrome.exe (PID: 2432)
Reads the computer name
- WinRAR.exe (PID: 2864)
- Zestra.exe (PID: 696)
- Zestra.exe (PID: 2188)
Checks supported languages
- WinRAR.exe (PID: 2864)
- Zestra.exe (PID: 696)
- Zestra.exe (PID: 2188)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2864)
Drops a file with too old compile date
- WinRAR.exe (PID: 2864)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2864)
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 2864)
INFO
Checks supported languages
- chrome.exe (PID: 872)
- chrome.exe (PID: 504)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 732)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 768)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 276)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3076)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 2432)
- WISPTIS.EXE (PID: 2592)
Application launched itself
- chrome.exe (PID: 872)
Reads the hosts file
- chrome.exe (PID: 2908)
- chrome.exe (PID: 872)
Reads the computer name
- chrome.exe (PID: 872)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3180)
- WISPTIS.EXE (PID: 2592)
Reads settings of System Certificates
- chrome.exe (PID: 2908)
Reads the date of Windows installation
- chrome.exe (PID: 3744)
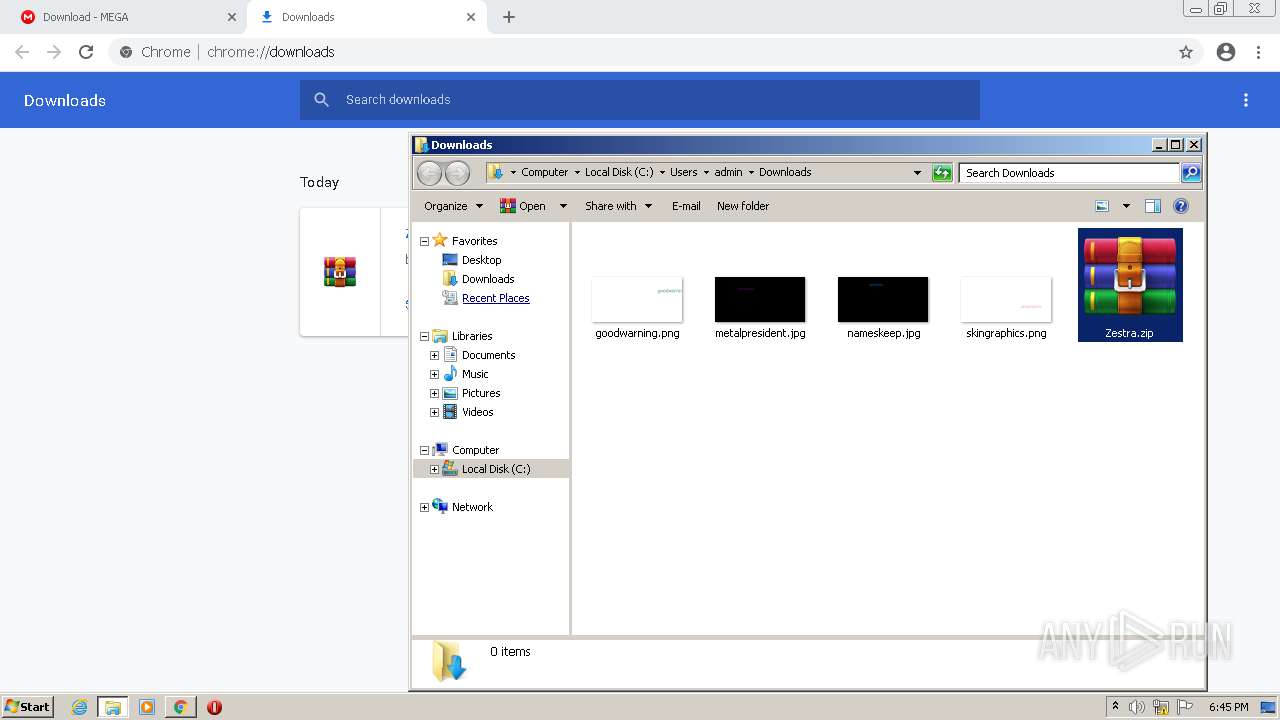
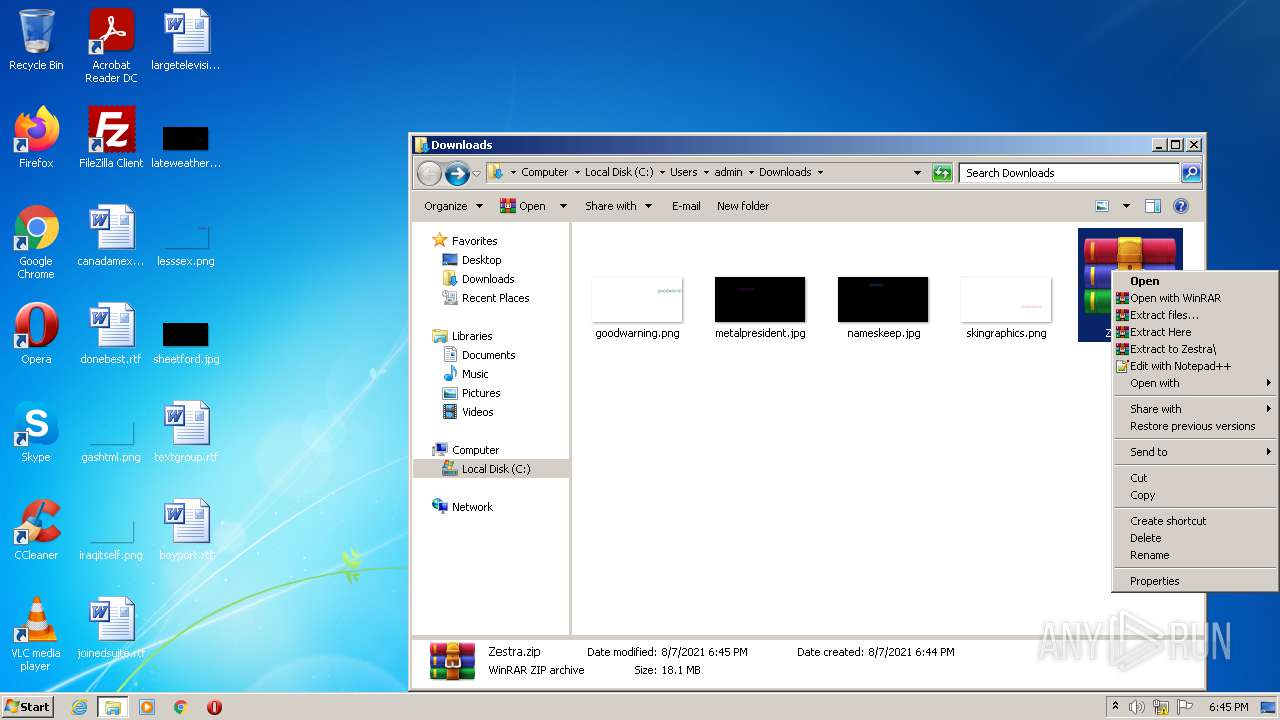
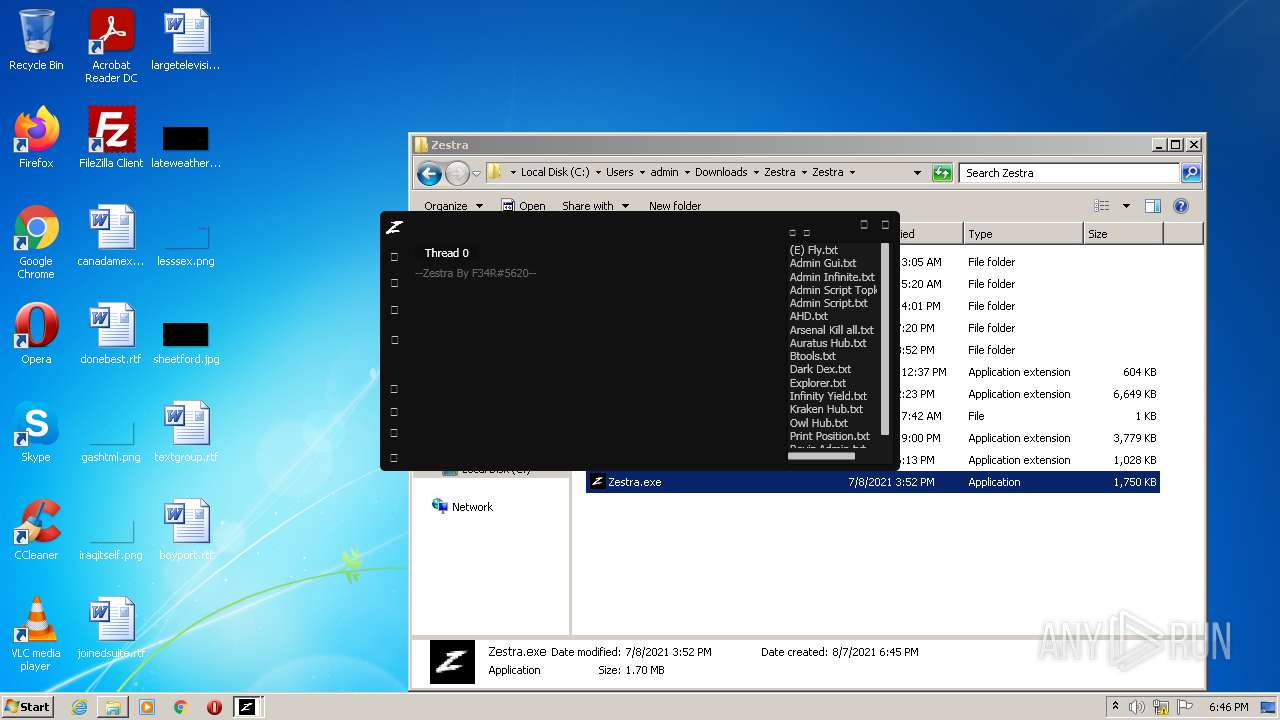
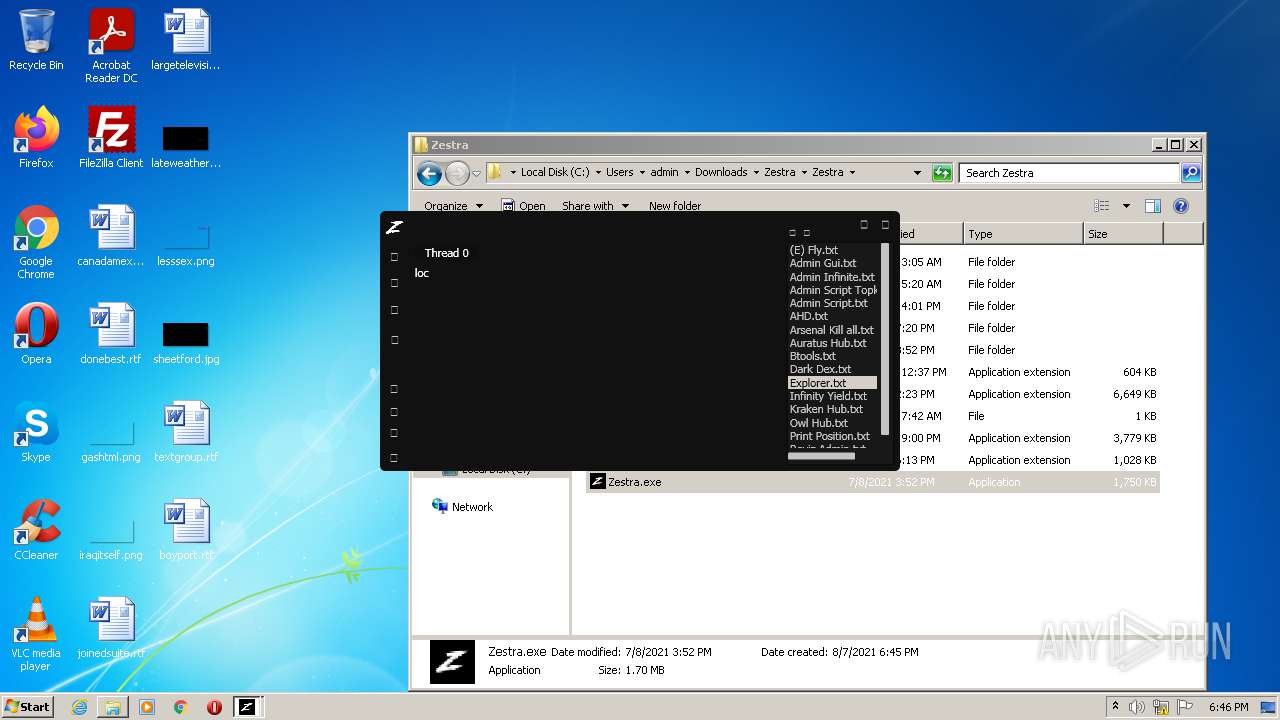
Manual execution by user
- WinRAR.exe (PID: 2864)
- Zestra.exe (PID: 696)
- Zestra.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
26
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10643042782615571270,9021389450930089958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f12d988,0x6f12d998,0x6f12d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10643042782615571270,9021389450930089958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
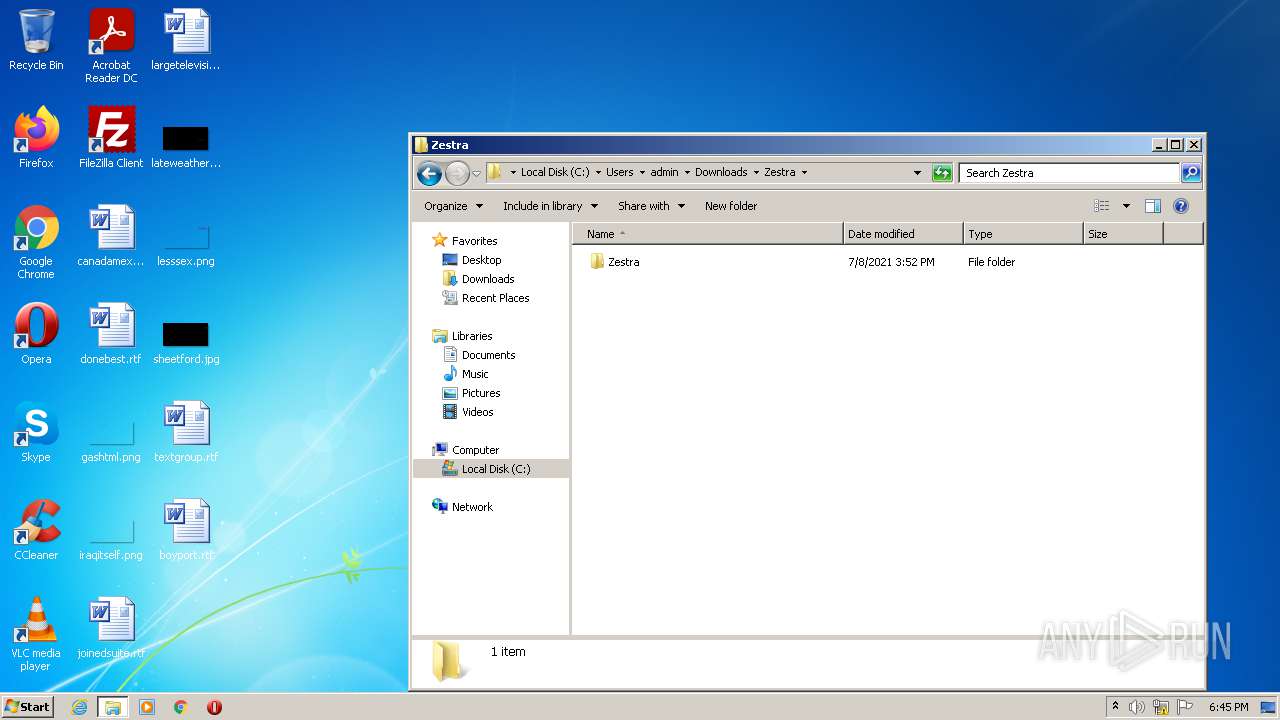
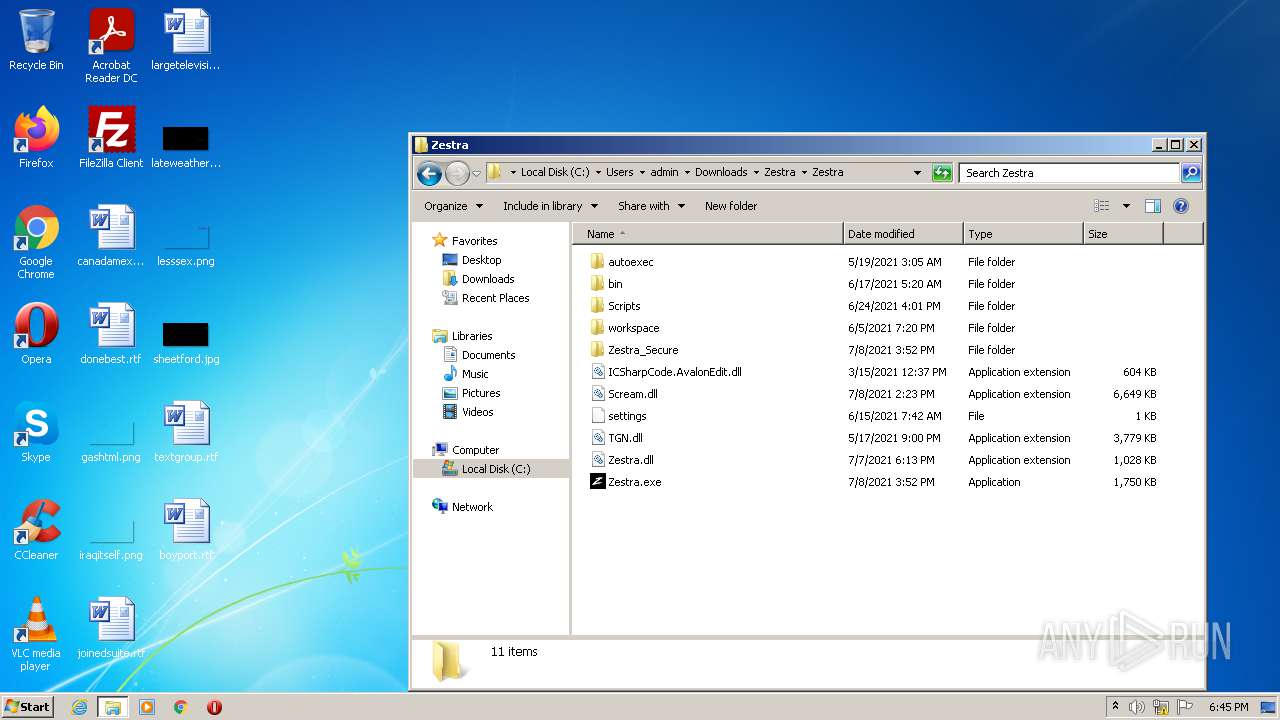
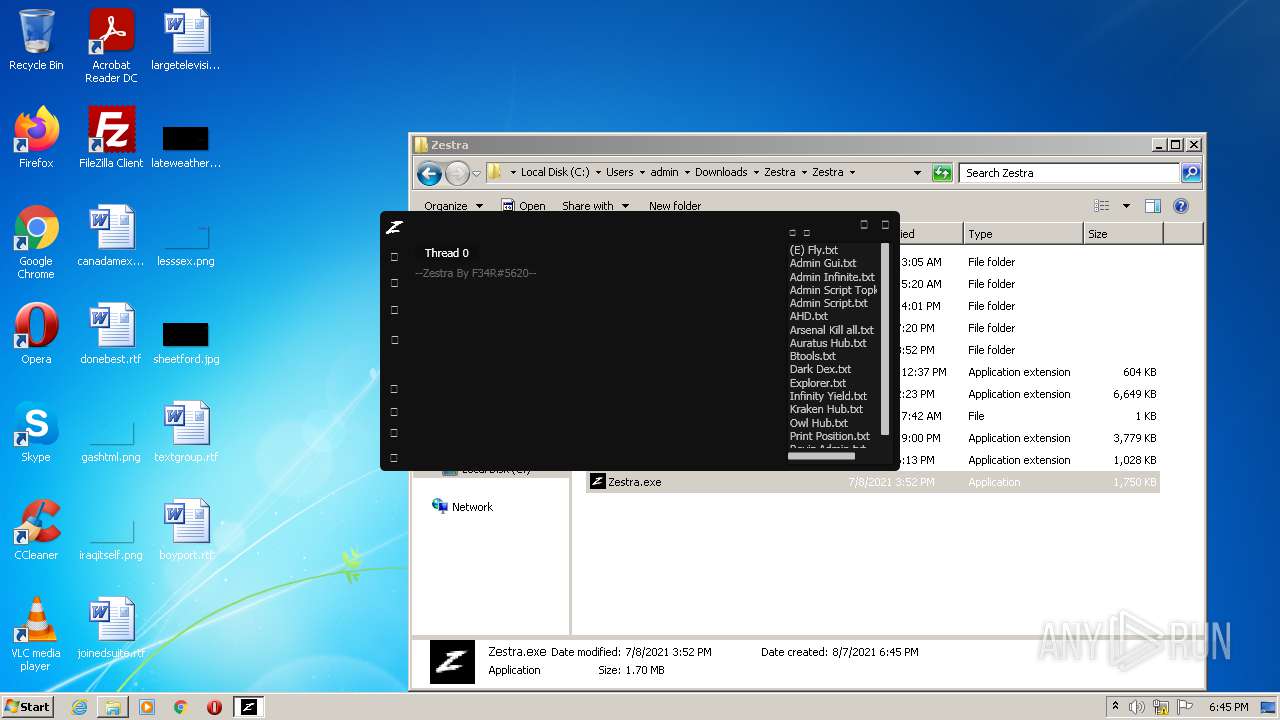
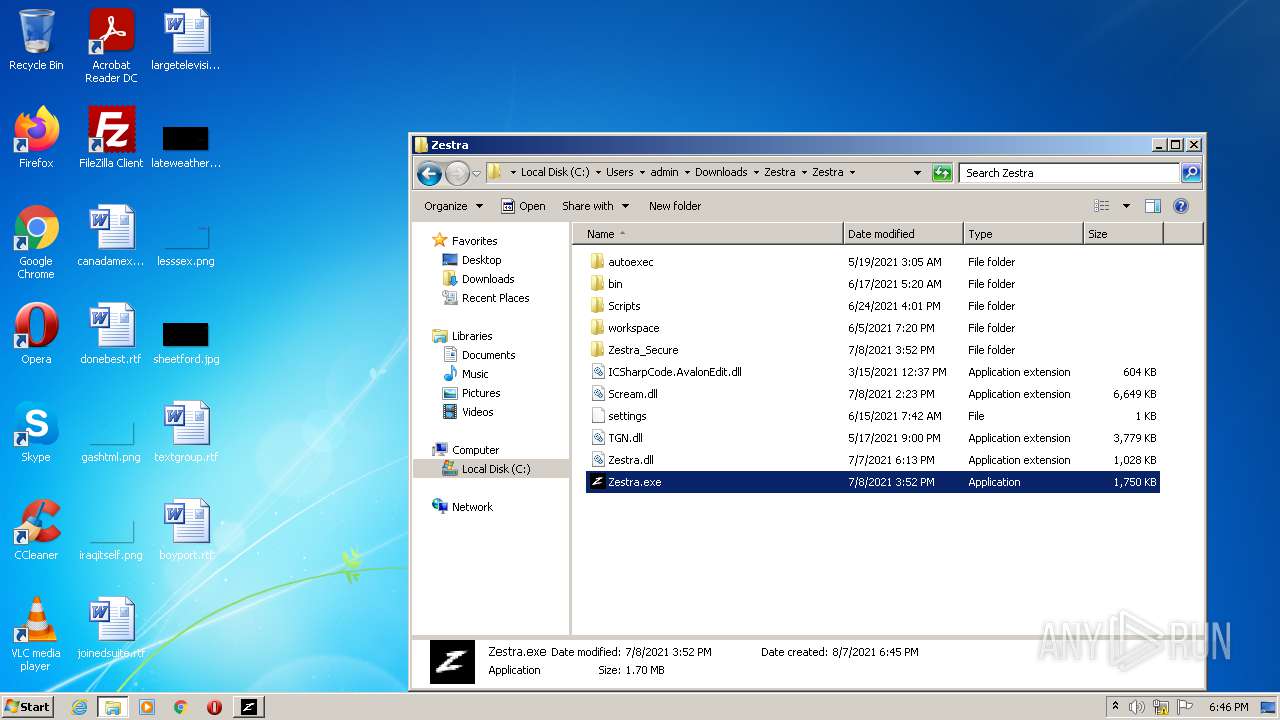
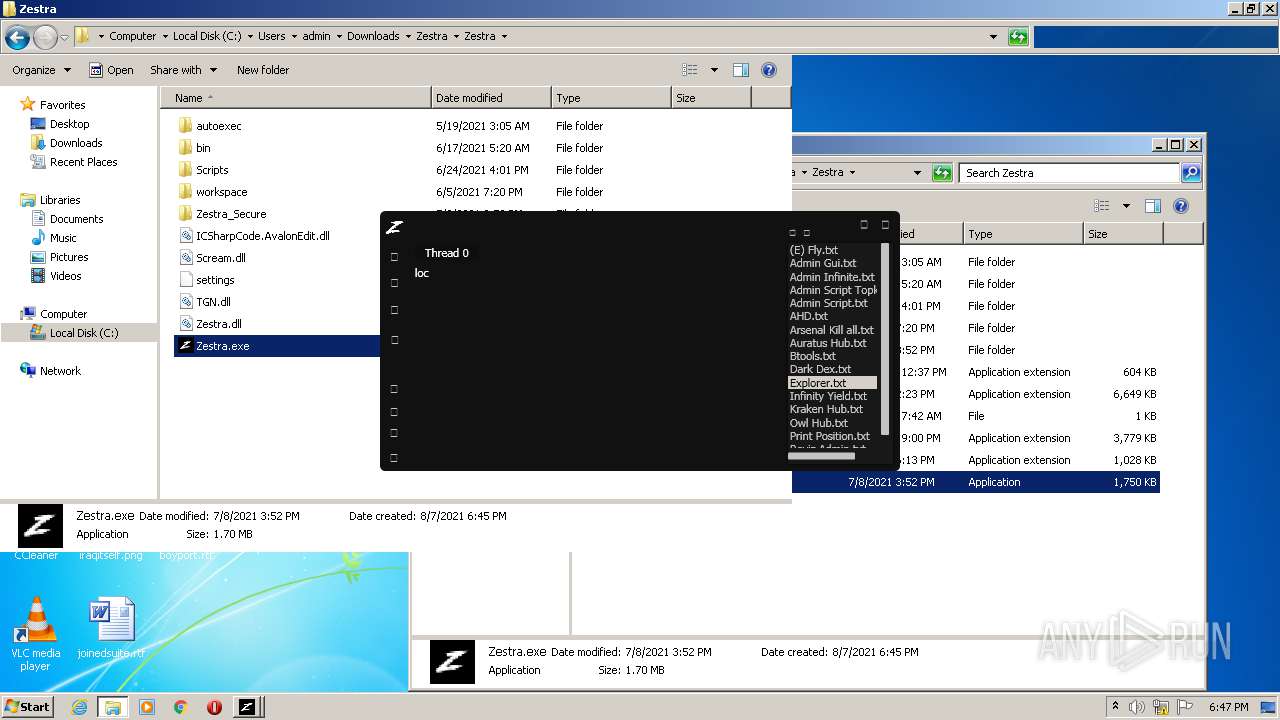
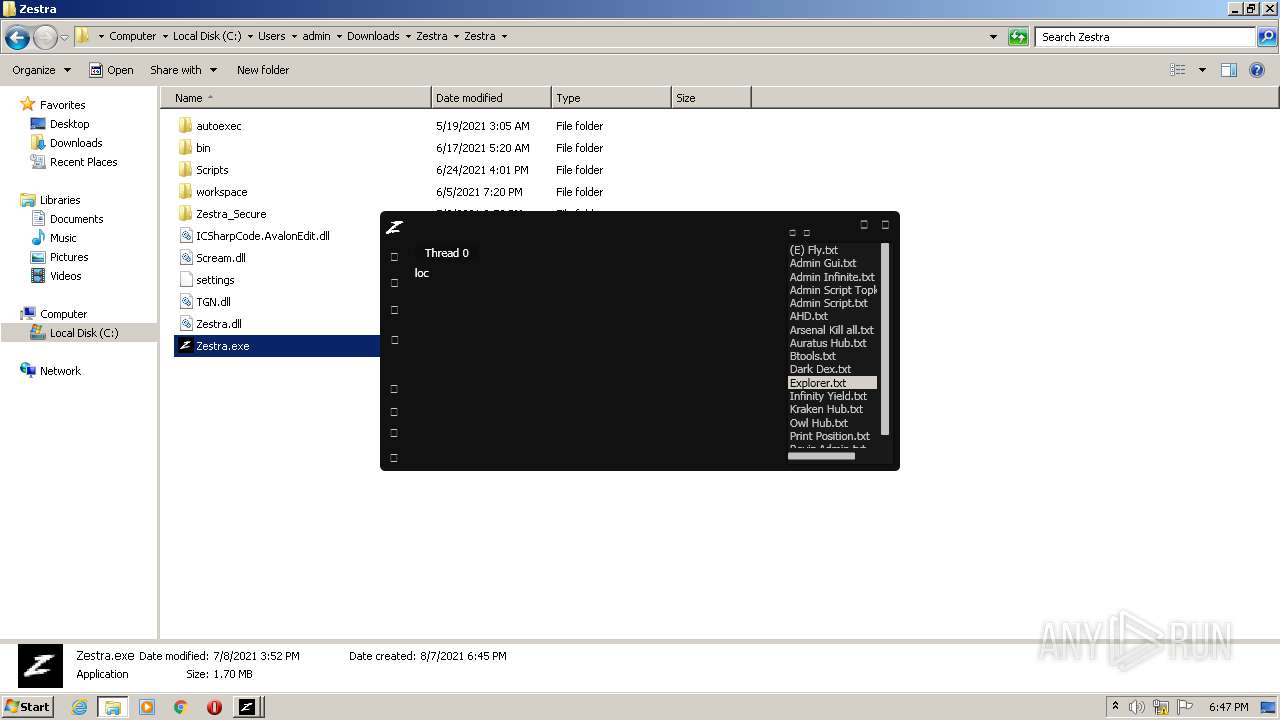
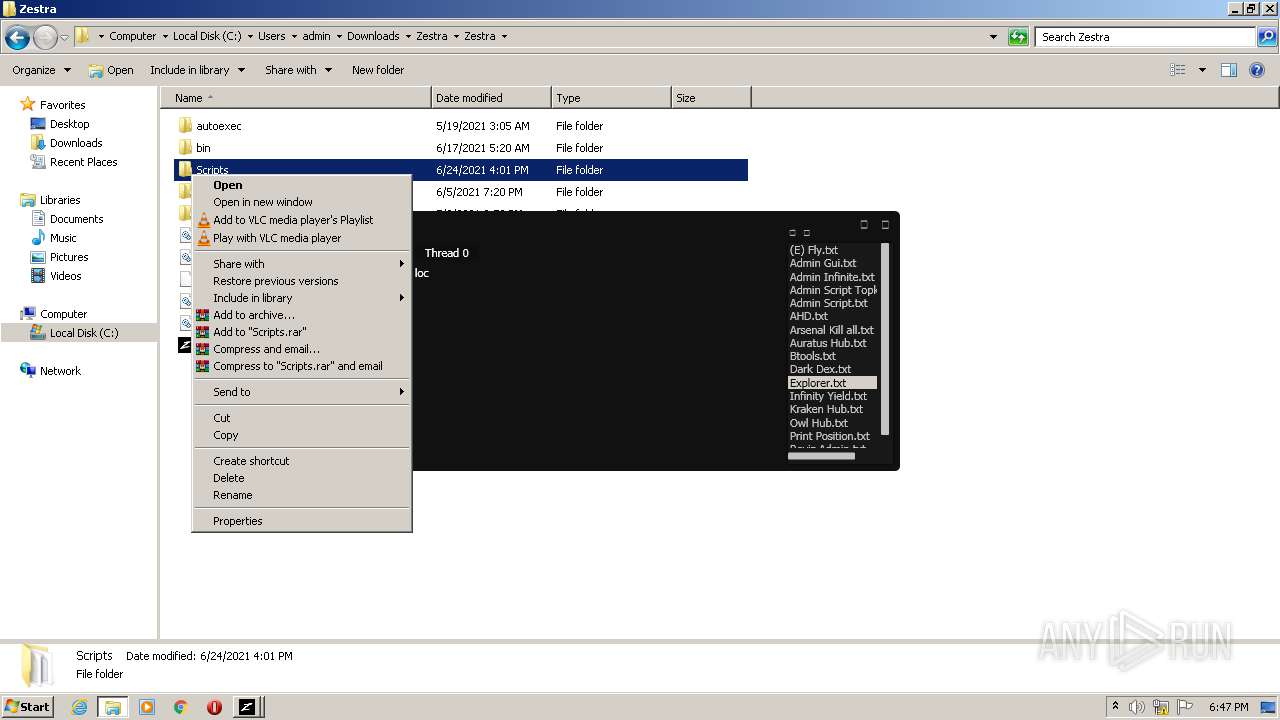
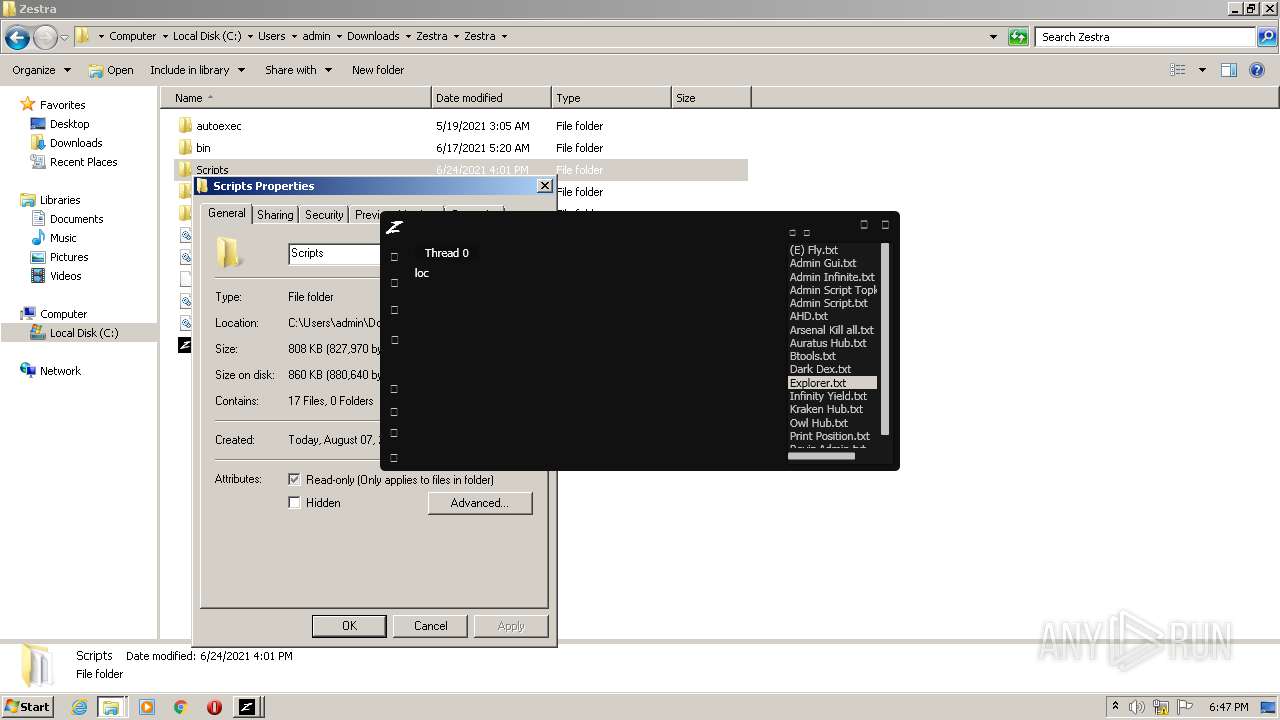
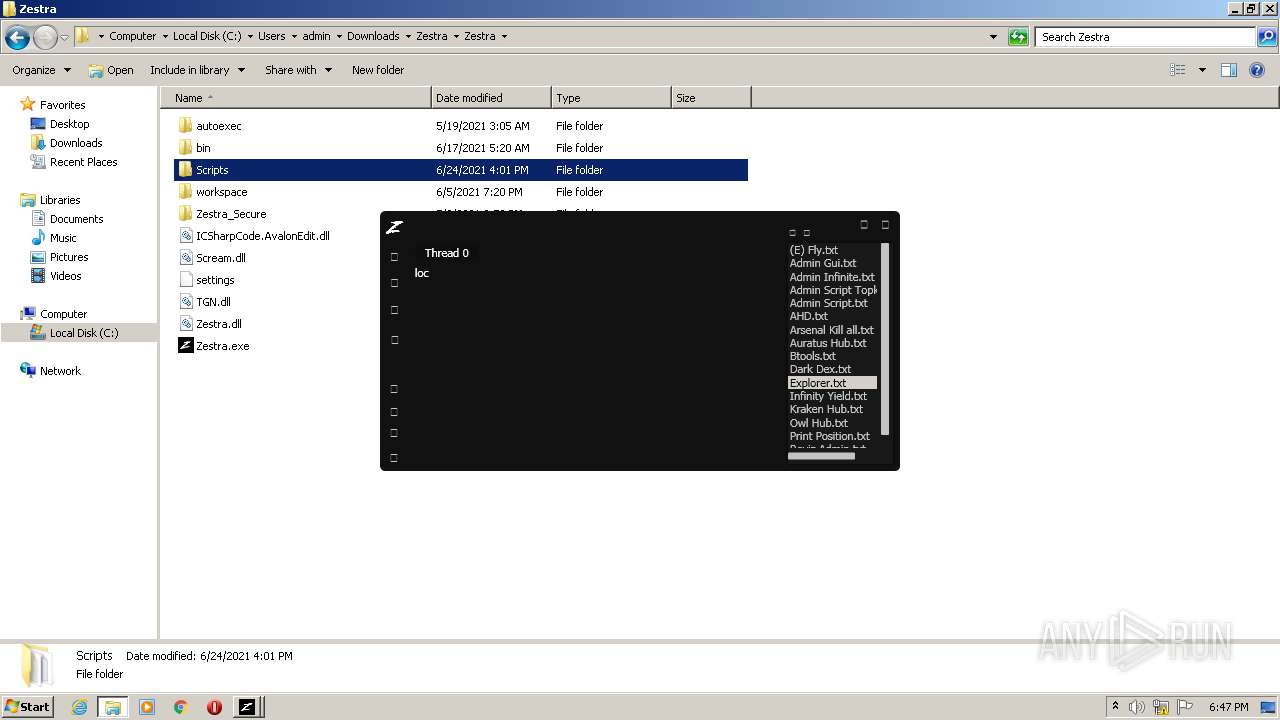
| 696 | "C:\Users\admin\Downloads\Zestra\Zestra\Zestra.exe" | C:\Users\admin\Downloads\Zestra\Zestra\Zestra.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Zestra Integrity Level: MEDIUM Description: Zestra Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10643042782615571270,9021389450930089958,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,10643042782615571270,9021389450930089958,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://mega.nz/file/XlhhjSJI#Z-IQs8FT4FOAdUTSnrU_v8bHIr1MaVA6DsUctHuLcR0" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2092 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\Downloads\Zestra\Zestra\Zestra.exe" | C:\Users\admin\Downloads\Zestra\Zestra\Zestra.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Zestra Integrity Level: MEDIUM Description: Zestra Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1020,10643042782615571270,9021389450930089958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 401
Read events
13 234
Write events
167
Delete events
0
Modification events
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
7
Suspicious files
47
Text files
128
Unknown types
8
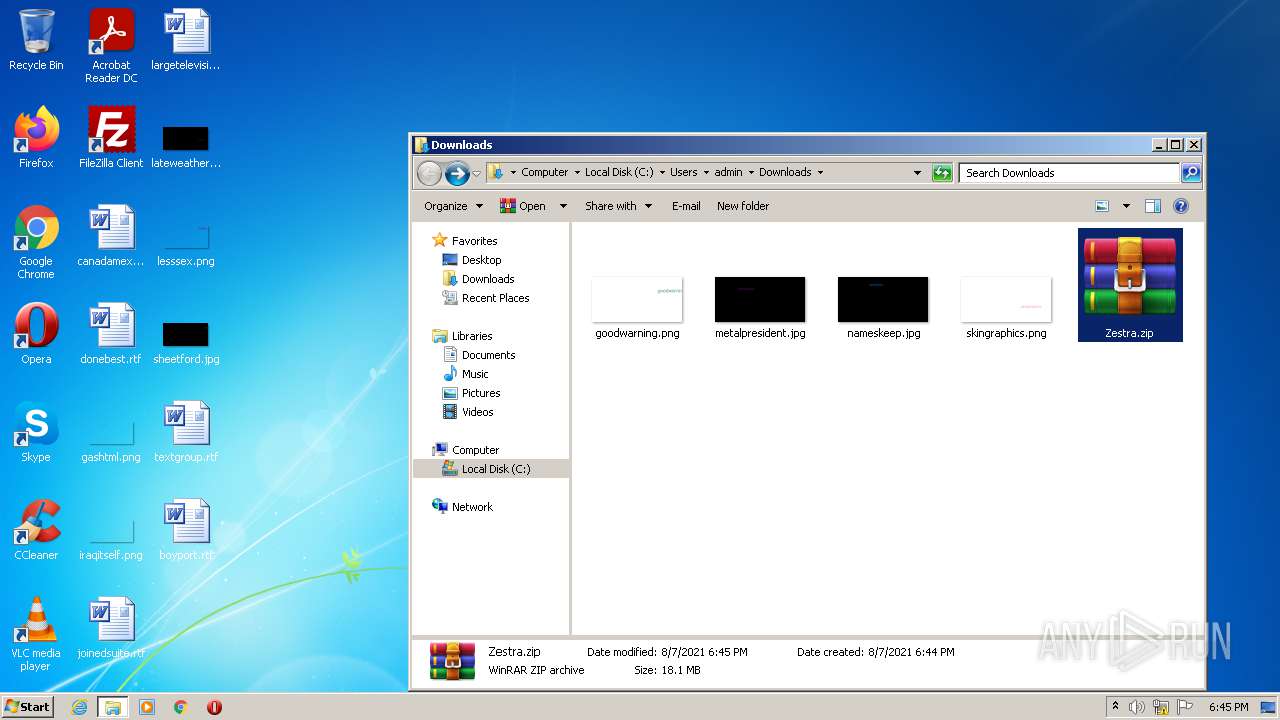
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-610EC674-368.pma | — | |
MD5:— | SHA256:— | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:98010592CF37F664ABF4E6590654C0C6 | SHA256:32BBC5D7B1C4D417CF3DB929EF8D1342AF0020C21E23FF4B4E8F3684CCDB40B0 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\290a4b3e-329e-424c-b18e-6adf71044866.tmp | text | |
MD5:98010592CF37F664ABF4E6590654C0C6 | SHA256:32BBC5D7B1C4D417CF3DB929EF8D1342AF0020C21E23FF4B4E8F3684CCDB40B0 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10c035.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF10c797.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF10c3de.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 872 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF10c1db.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
45
DNS requests
22
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2908 | chrome.exe | 66.203.127.18:443 | mega.nz | RealNetworks, Inc. | US | suspicious |
2908 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2908 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2908 | chrome.exe | 142.250.186.42:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
2908 | chrome.exe | 66.203.127.11:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
2908 | chrome.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2908 | chrome.exe | 66.203.127.13:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
2908 | chrome.exe | 142.250.184.194:443 | securepubads.g.doubleclick.net | Google Inc. | US | suspicious |
2908 | chrome.exe | 66.203.125.15:443 | g.api.mega.co.nz | RealNetworks, Inc. | US | unknown |
2908 | chrome.exe | 142.250.186.66:443 | adservice.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
eu.megaad.nz |
| suspicious |
securepubads.g.doubleclick.net |
| whitelisted |
adservice.google.nl |
| whitelisted |