| File name: | OpenBullet.1.2.1.1.zip |
| Full analysis: | https://app.any.run/tasks/1ee90167-eb3d-4216-b4bd-e45dbaa4db03 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2019, 22:10:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 41E32CB1F01AEC55974411FB61DDBDB7 |
| SHA1: | C4813E5A661217719014FBB04C7B8E3ED077D4D4 |
| SHA256: | AF3690A4D3AB8A2AE5A22B426C7D1460B24000CC6CB5D0D5EC348E514FC6406D |
| SSDEEP: | 393216:H4/xL8XurZu858EnaHMsVGQOyEKV83HN+QJ9/Fvx8:H4/xL8XaOEnaHMNQOzlUes |
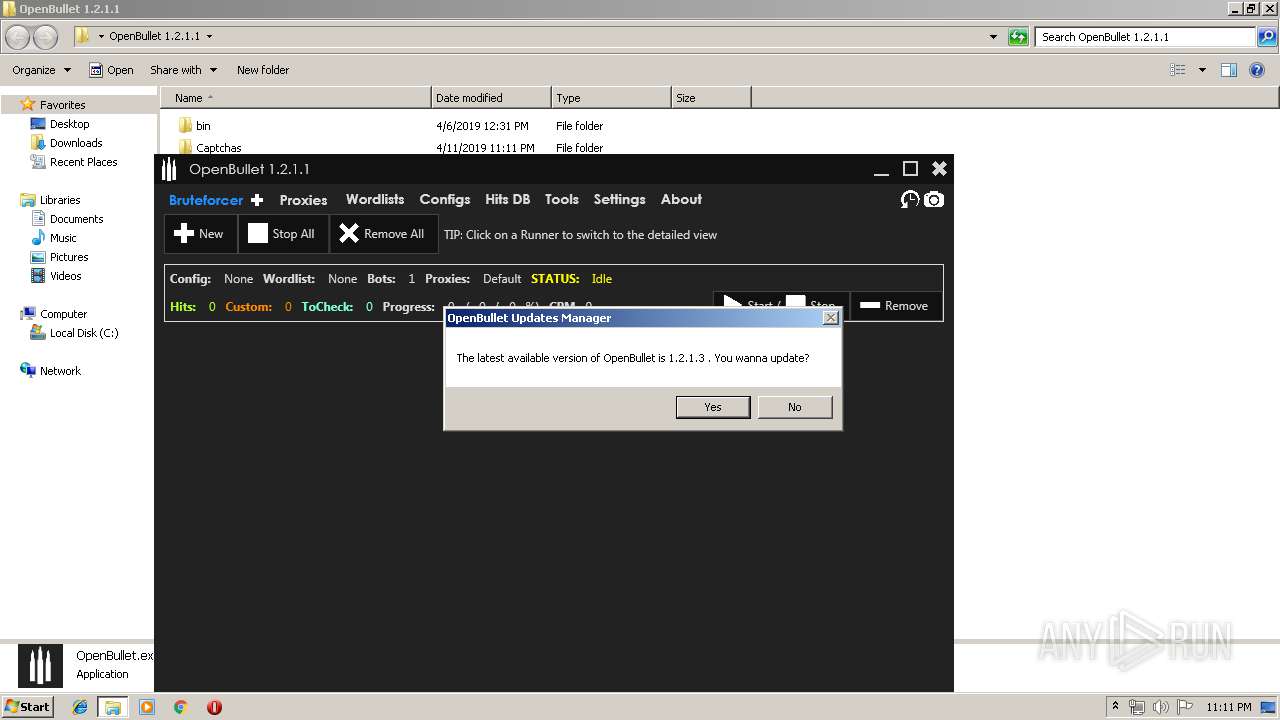
MALICIOUS
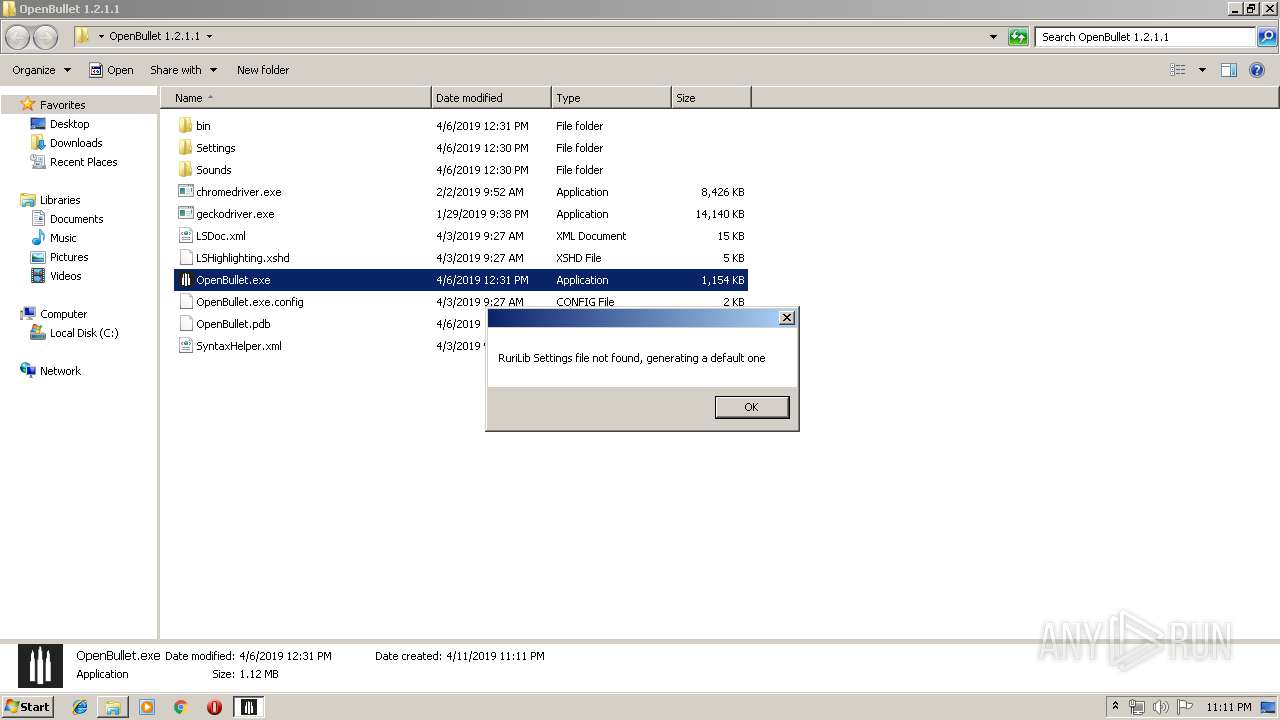
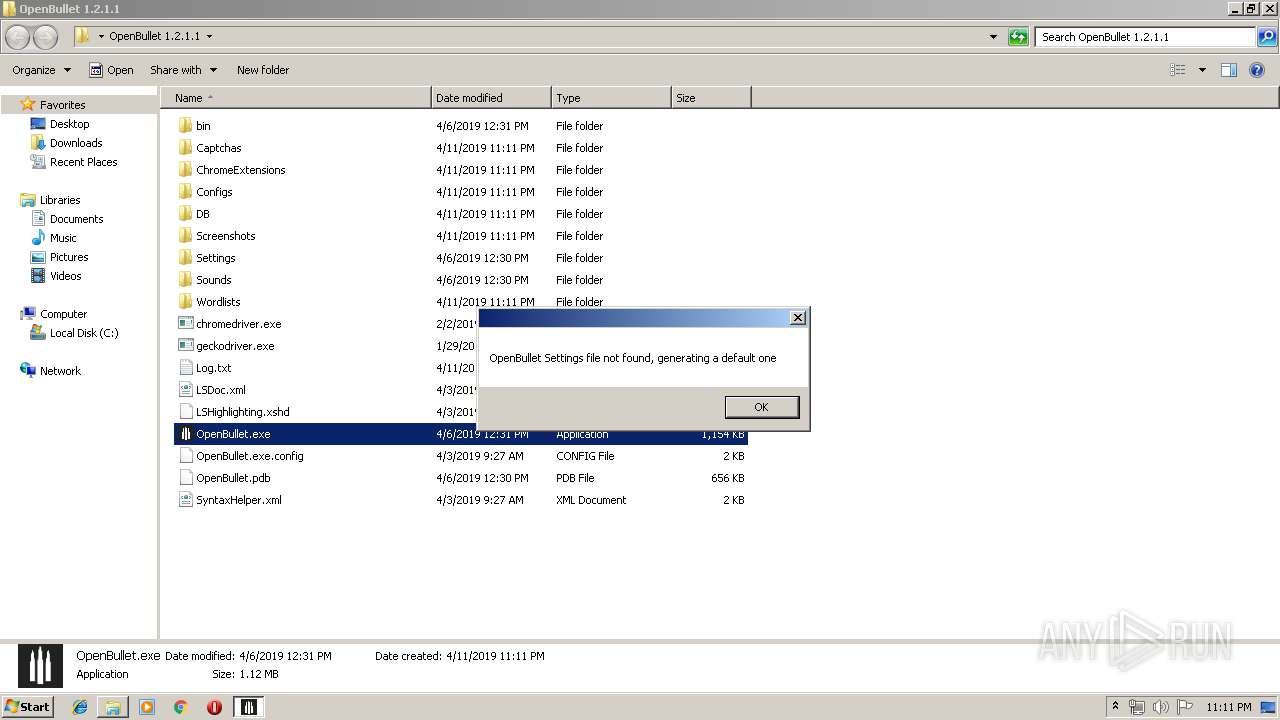
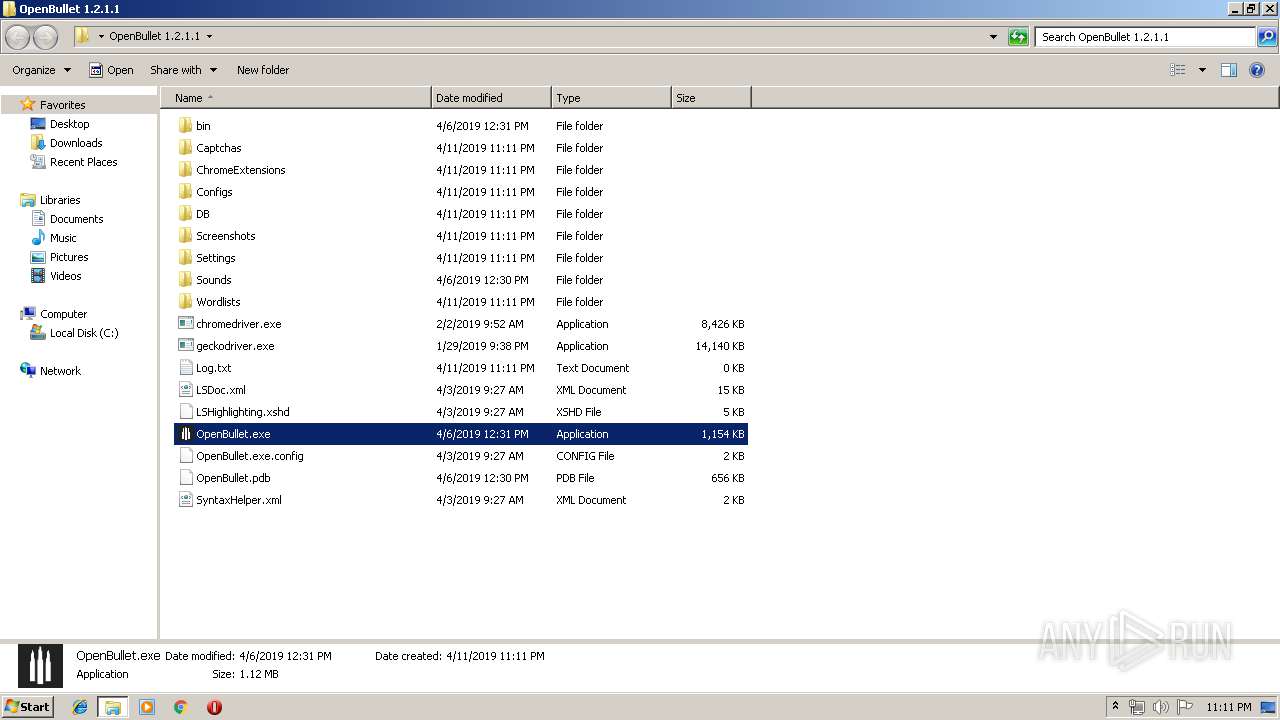
Loads dropped or rewritten executable
- OpenBullet.exe (PID: 2992)
- SearchProtocolHost.exe (PID: 3884)
Application was dropped or rewritten from another process
- OpenBullet.exe (PID: 2992)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2864)
Starts Internet Explorer
- OpenBullet.exe (PID: 2992)
Reads Environment values
- OpenBullet.exe (PID: 2992)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3028)
Creates files in the user directory
- iexplore.exe (PID: 1076)
Reads internet explorer settings
- iexplore.exe (PID: 1076)
Reads Internet Cache Settings
- iexplore.exe (PID: 1076)
Application launched itself
- iexplore.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:04:06 11:30:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
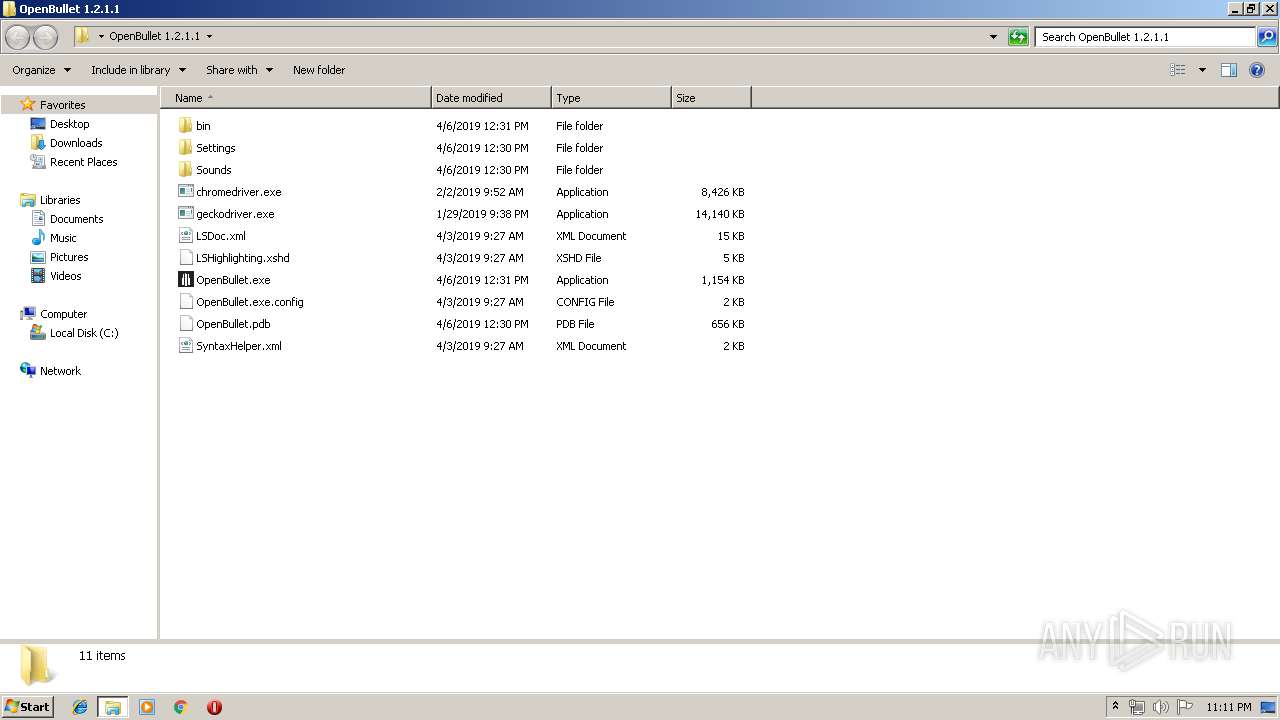
| ZipFileName: | OpenBullet 1.2.1.1/ |
Total processes
35
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3028 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
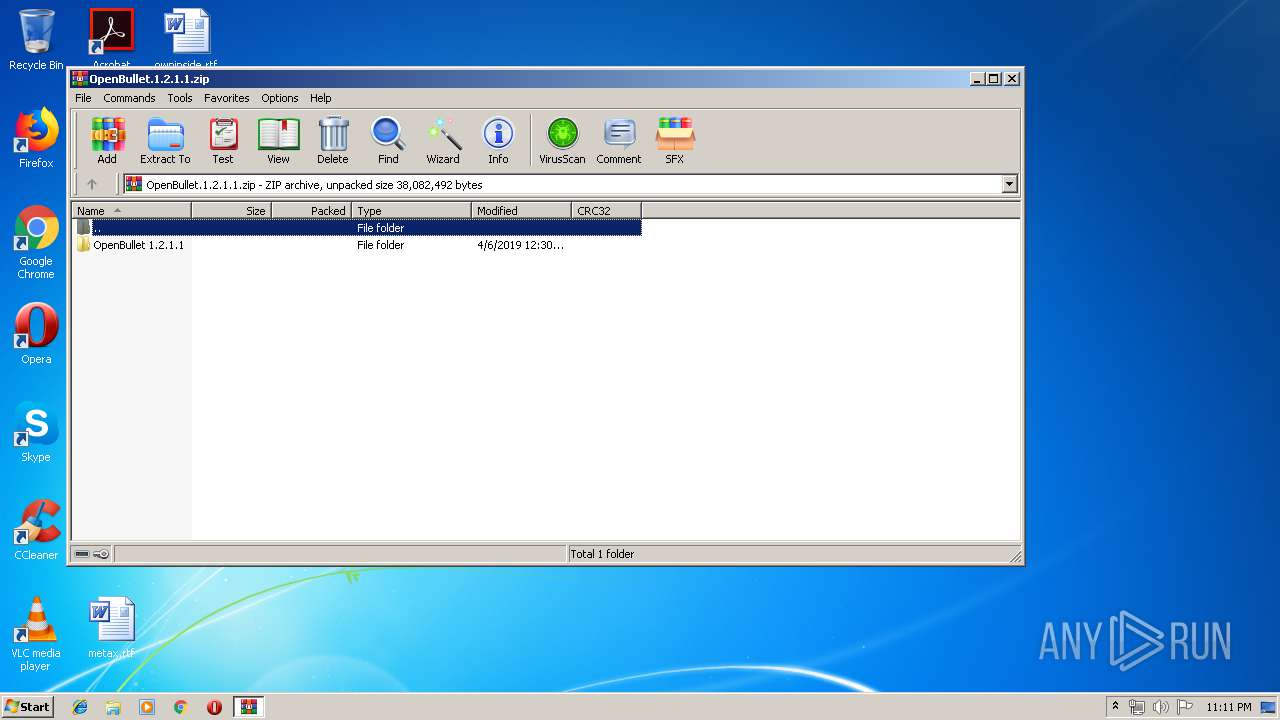
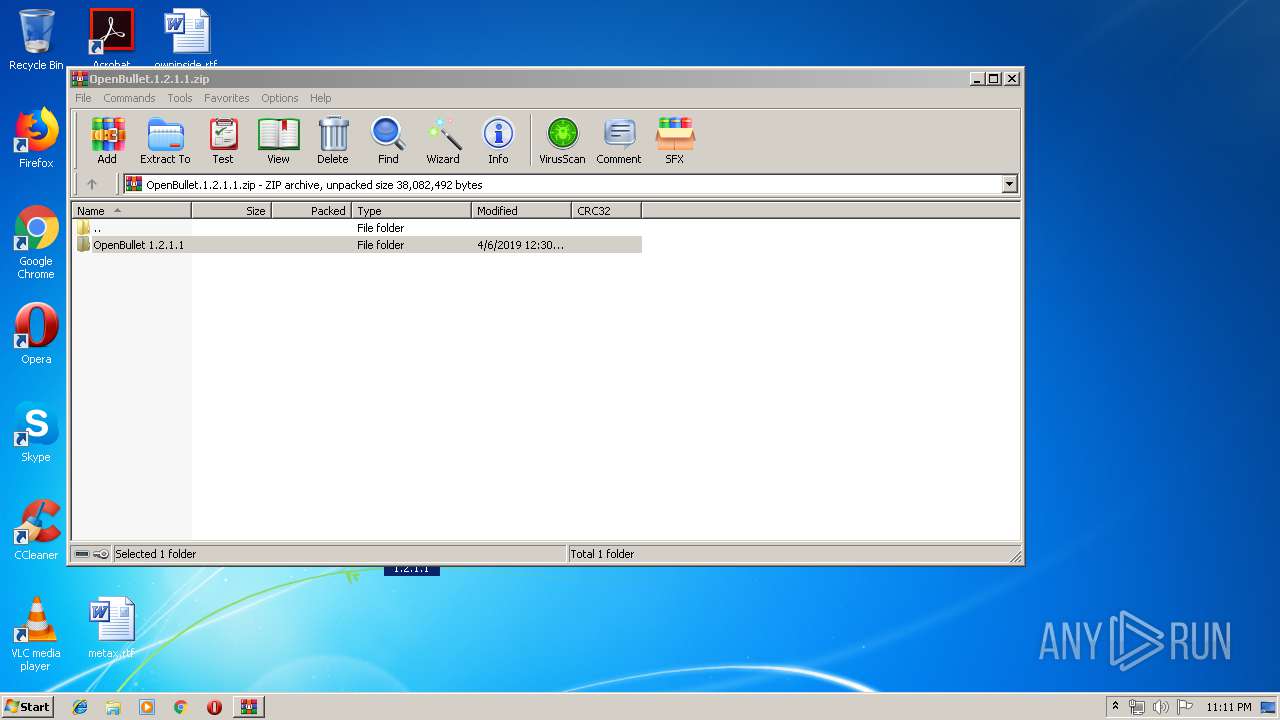
| 2864 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\OpenBullet.1.2.1.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\Desktop\OpenBullet 1.2.1.1\OpenBullet.exe" | C:\Users\admin\Desktop\OpenBullet 1.2.1.1\OpenBullet.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OpenBullet Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | OpenBullet.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3884 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 195
Read events
1 104
Write events
91
Delete events
0
Modification events
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\OpenBullet.1.2.1.1.zip | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
34
Suspicious files
0
Text files
24
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\Leaf.xNet.dll | executable | |
MD5:— | SHA256:— | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\Extreme.Net.dll | executable | |
MD5:— | SHA256:— | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\AngleSharp.dll | executable | |
MD5:BF331AB2E9BB06D900929DE29C659AE8 | SHA256:0B6D37C6113914DECB8AE2142DEE7CF476206036806821AC6DC63D69269F827B | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\IronPython.dll | executable | |
MD5:9A39A51E6DCB22B80DB481FBFBCD7826 | SHA256:61B809B97DC878F42E85EE2C5D8471853527754E4F53B17C0507334C57E19E04 | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\ICSharpCode.AvalonEdit.dll | executable | |
MD5:B4D5D46E50006E87B30E7D514E95173C | SHA256:058F38F33F3F99F904AB9588447A234346C859718404B4E8A523673ED19CDBE7 | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\IronPython.Wpf.dll | executable | |
MD5:F1E1A1058A95C27CC453F8559E4AB3ED | SHA256:4061499B5E66C9309352A660A457AC95C8FA98229A8BBCCC648DEB85F5FF7CC7 | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\LiteDB.dll | executable | |
MD5:25B242D00C6C32E1F437EB2064EA2E29 | SHA256:E72ACDDF47586BC0999D598E3BD125A254BB6F4AE151C076993304F6E31FBBED | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\Microsoft.Dynamic.dll | executable | |
MD5:ABA389A299BEB16CC04337EC76C8A965 | SHA256:4F7425CB08CC9BCA6FCA4BFC08D22B6D9716C507F306F40AE7134B878D909A21 | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\RuriLib.dll | executable | |
MD5:— | SHA256:— | |||
| 2864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2864.19035\OpenBullet 1.2.1.1\bin\Jint.dll | executable | |
MD5:734C5CE8F9B104D8AD3C7B494E96F9B9 | SHA256:ED618668AE9E7C02C7C2B7332DD09079168CCA96432A051044683C996337001C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
3
Threats
0
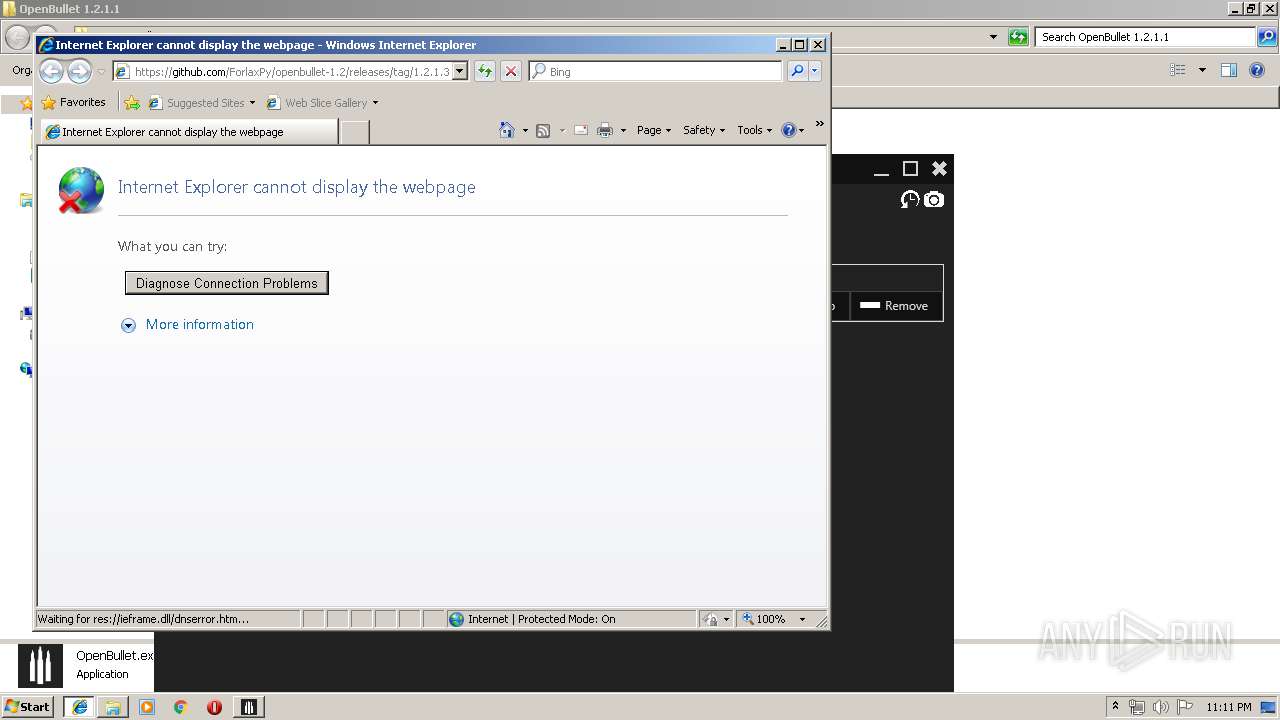
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | OpenBullet.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
3028 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1076 | iexplore.exe | 140.82.118.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
www.bing.com |
| whitelisted |
github.com |
| malicious |