| File name: | IDM_6.4x_Crack_v19.3.exe |
| Full analysis: | https://app.any.run/tasks/4a8aa1d8-182e-47f8-a185-76367efc7fd0 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2024, 14:48:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F149E4A106B1A6941F6FB1B3B8AB87AE |
| SHA1: | BDD04100E82F8406DBF7EC3074B572B635CEE1B4 |
| SHA256: | AF26D2A5315BBE1D8F772CA82FFCB55131E84FADBC3869B6BD5C36729A610399 |
| SSDEEP: | 768:G5qROJM8eV4DqXbt46DL92gUwO9saFBxG5DpbIogHTIG+Xo9oIzMkk+LPjJ3AF:G5qRPFfQgUwU1xG5t0IGbdzBAF |
MALICIOUS
Drops the executable file immediately after the start
- IDM_6.4x_Crack_v19.3.exe (PID: 3004)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3156)
Unusual connection from system programs
- wscript.exe (PID: 3156)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3156)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3156)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3156)
Deletes a file (SCRIPT)
- wscript.exe (PID: 3156)
SUSPICIOUS
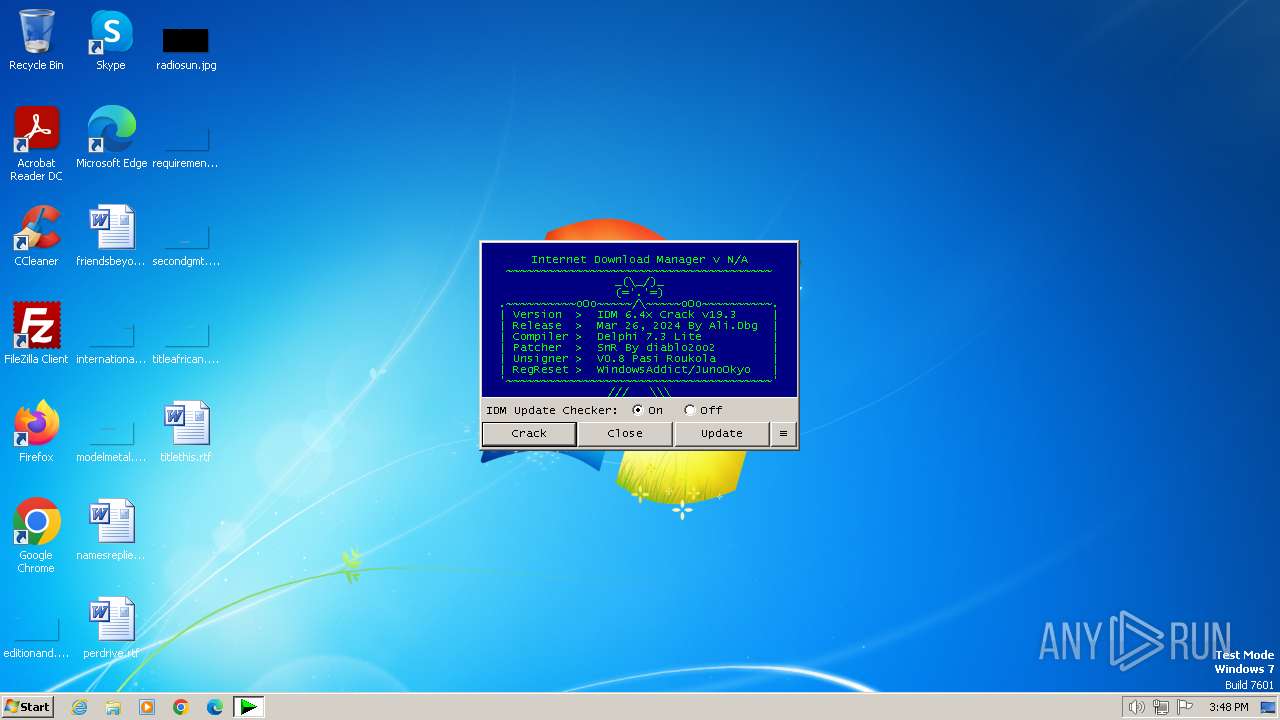
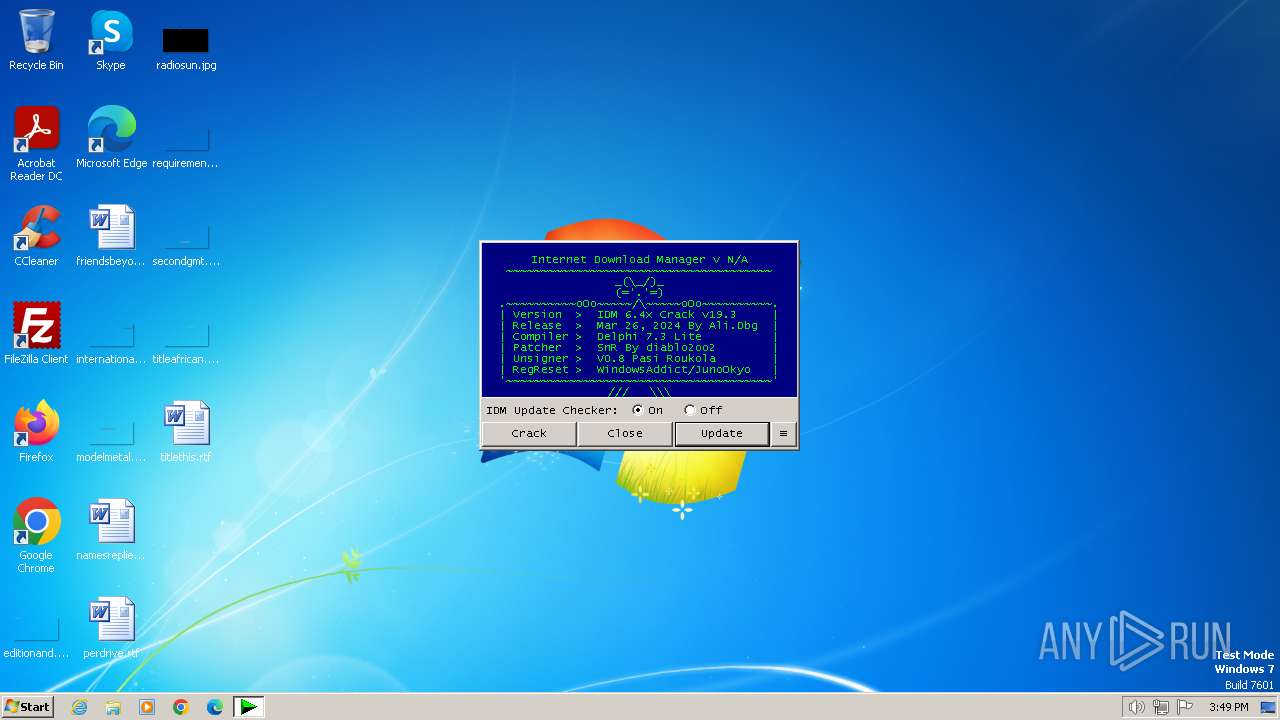
The process executes VB scripts
- IDM_6.4x_Crack_v19.3.exe (PID: 3004)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3156)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3156)
Reads the Internet Settings
- wscript.exe (PID: 3156)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3156)
INFO
Checks supported languages
- IDM_6.4x_Crack_v19.3.exe (PID: 3004)
Reads the computer name
- IDM_6.4x_Crack_v19.3.exe (PID: 3004)
Create files in a temporary directory
- IDM_6.4x_Crack_v19.3.exe (PID: 3004)
The process uses the downloaded file
- chrome.exe (PID: 1740)
Creates files in the program directory
- chrome.exe (PID: 696)
Application launched itself
- chrome.exe (PID: 696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 49152 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 163840 |
| EntryPoint: | 0x33ec0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
57
Monitored processes
19
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.3.exe" | C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
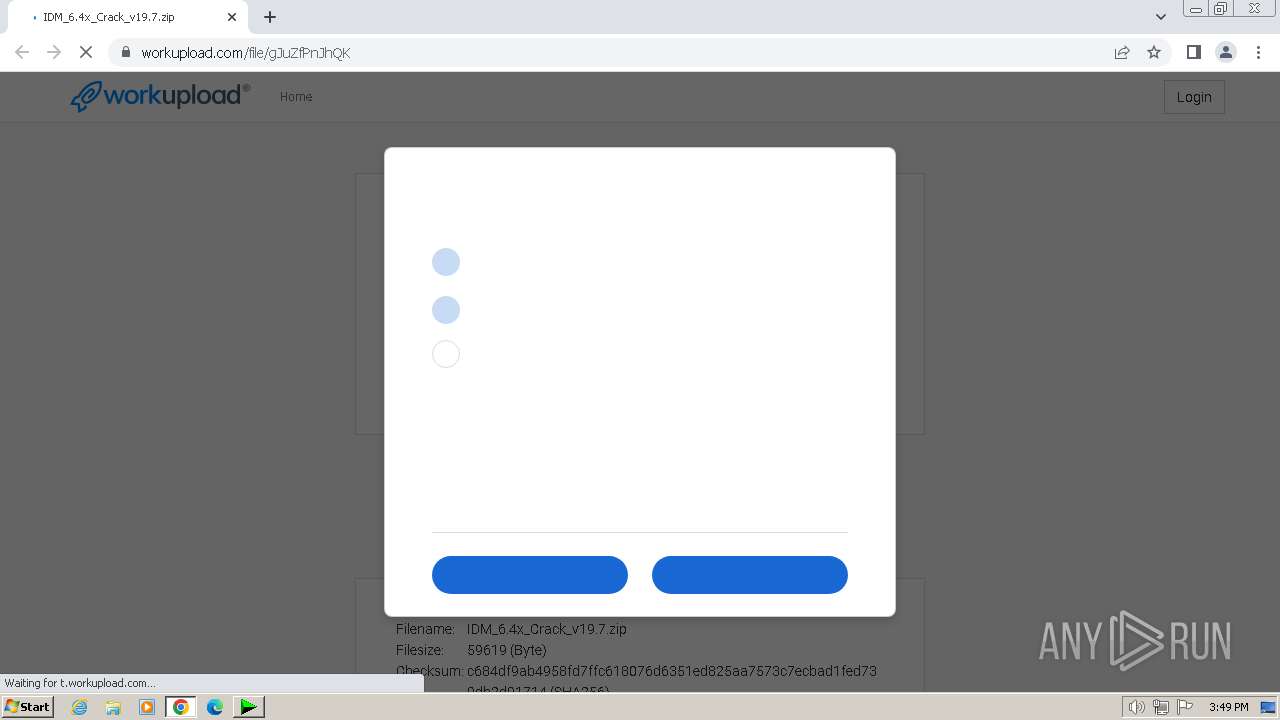
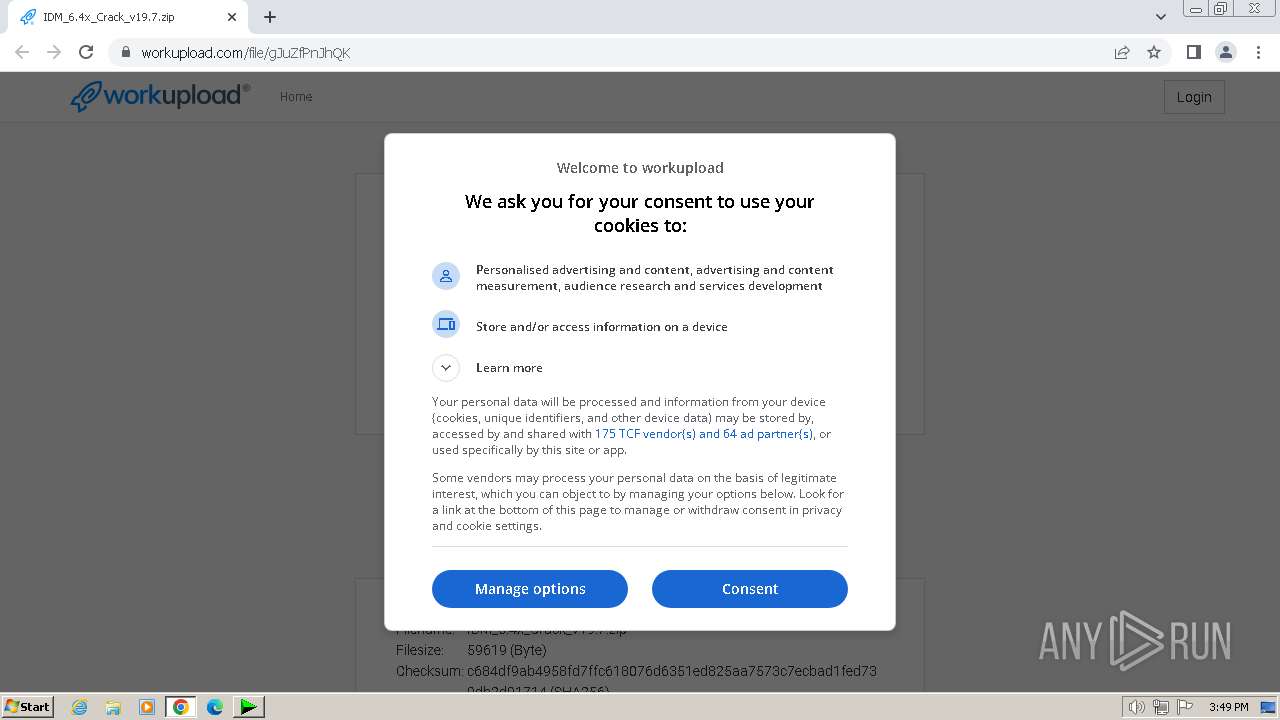
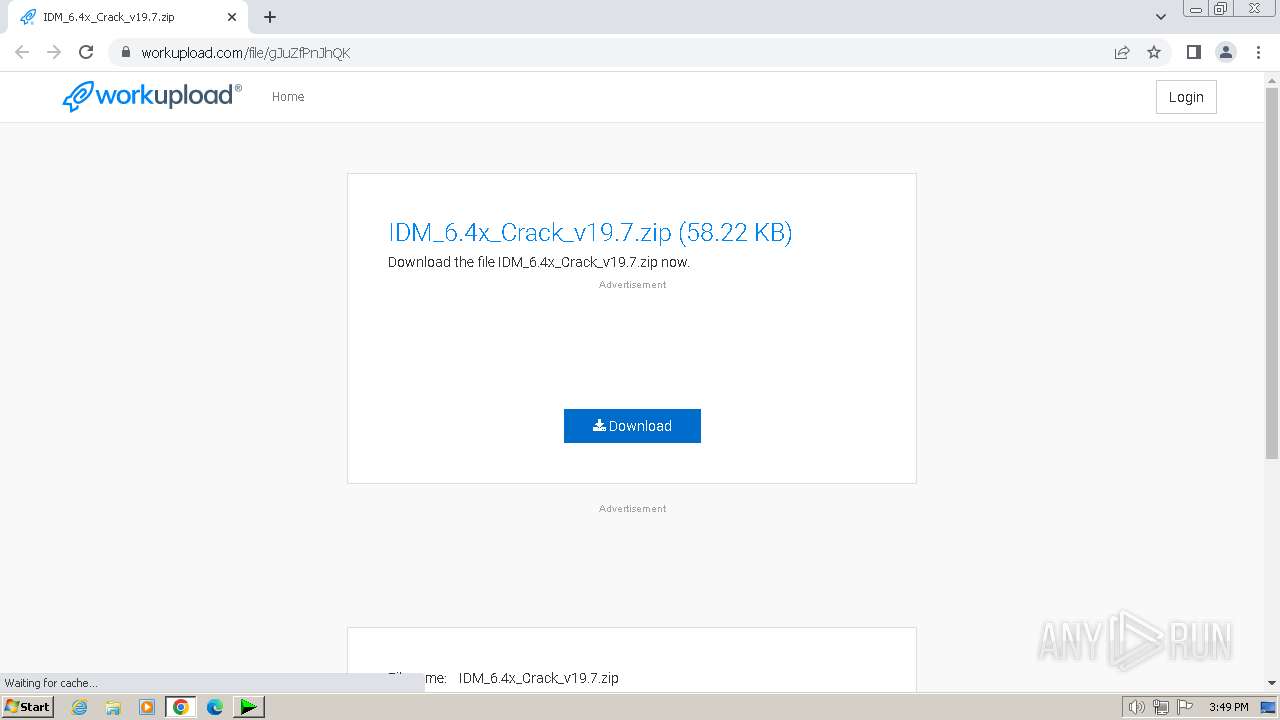
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://workupload.com/file/gJuZfPnJhQK | C:\Program Files\Google\Chrome\Application\chrome.exe | wscript.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3428 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4232 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1564 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1344 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ba18b38,0x6ba18b48,0x6ba18b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1064 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2092 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4228 --field-trial-handle=1136,i,11292557552287114450,1320689928121242637,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
10 109
Read events
9 994
Write events
106
Delete events
9
Modification events
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (3004) IDM_6.4x_Crack_v19.3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
Executable files
0
Suspicious files
56
Text files
22
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1c4c91.TMP | — | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1c4e85.TMP | — | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3004 | IDM_6.4x_Crack_v19.3.exe | C:\Users\admin\AppData\Local\Temp\UPDT.vbs | text | |
MD5:7B18A872D4BE22EECF2F95CE5E63CE15 | SHA256:E64D9B855B8F02B15626C7E932C0451C07AF8E8EBB53BB17626C66E117F50CBA | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1c4ca1.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1c4c91.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
64
DNS requests
61
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3156 | wscript.exe | 188.114.97.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
696 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2016 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2016 | chrome.exe | 144.76.176.119:443 | workupload.com | Hetzner Online GmbH | DE | unknown |
2016 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
2016 | chrome.exe | 216.58.206.34:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idm.0dy.ir |
| unknown |
clientservices.googleapis.com |
| whitelisted |
workupload.com |
| whitelisted |
accounts.google.com |
| shared |
fundingchoicesmessages.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
t.workupload.com |
| unknown |
securepubads.g.doubleclick.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |