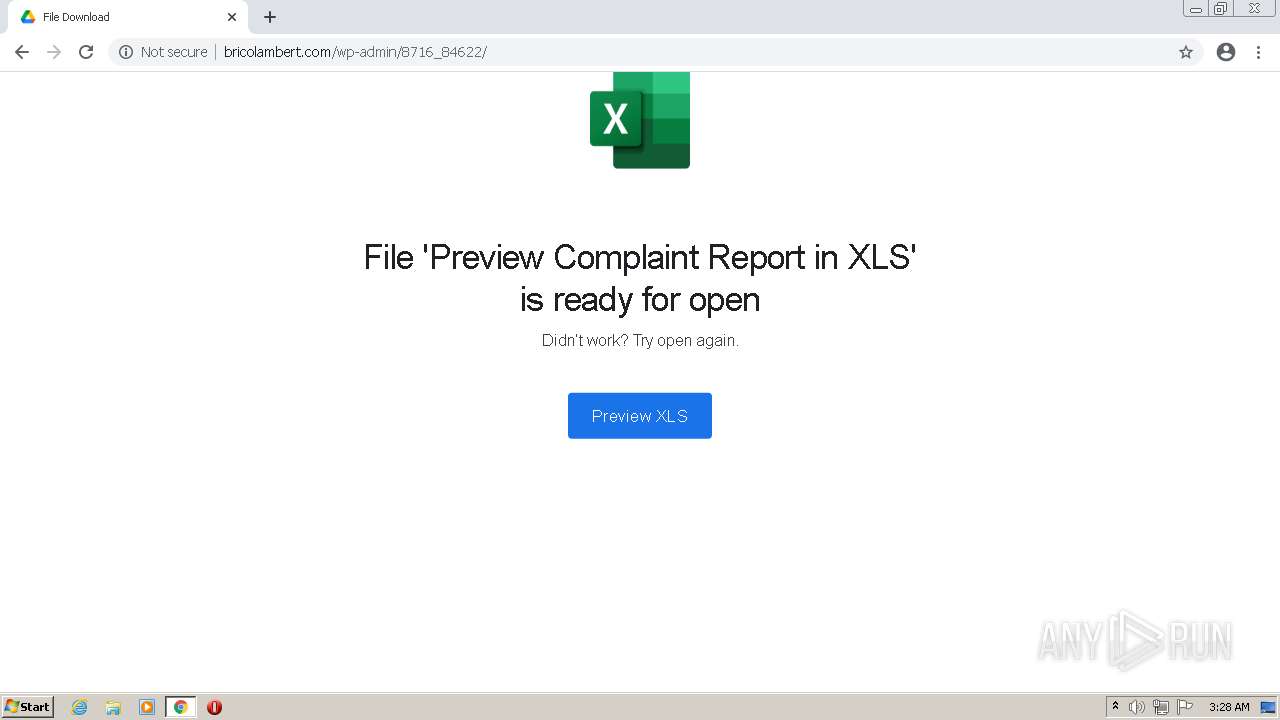
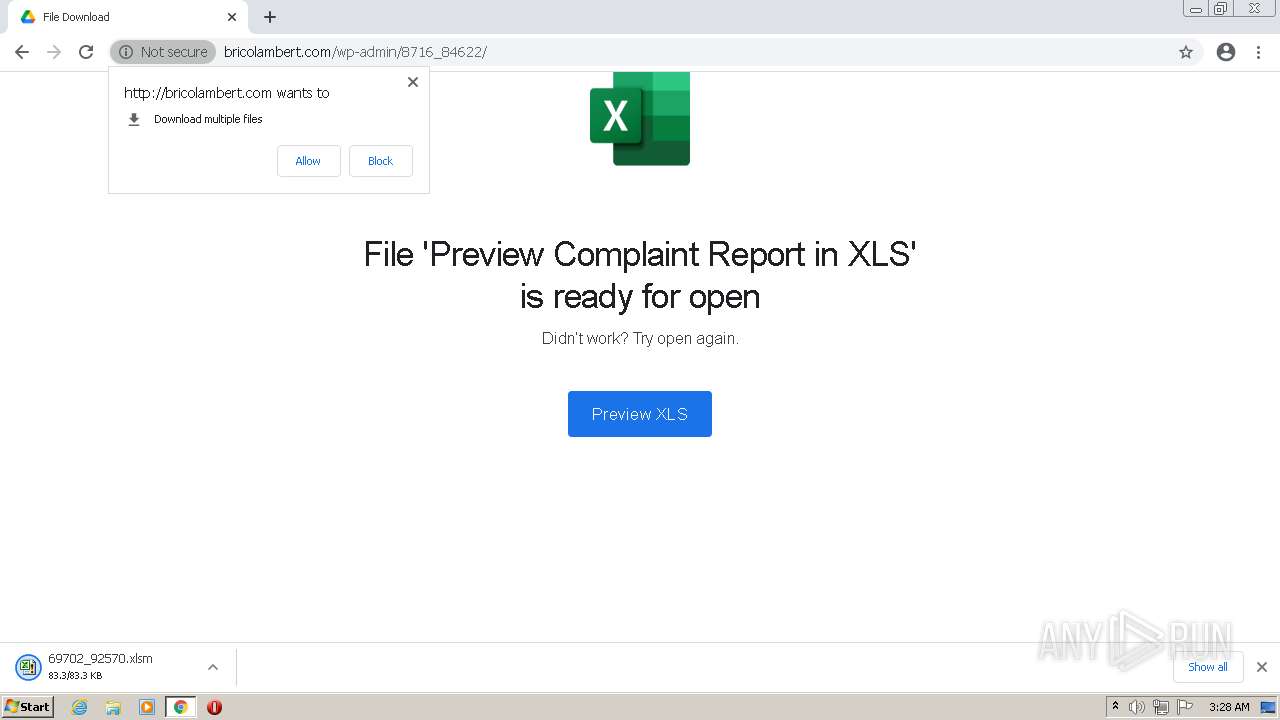
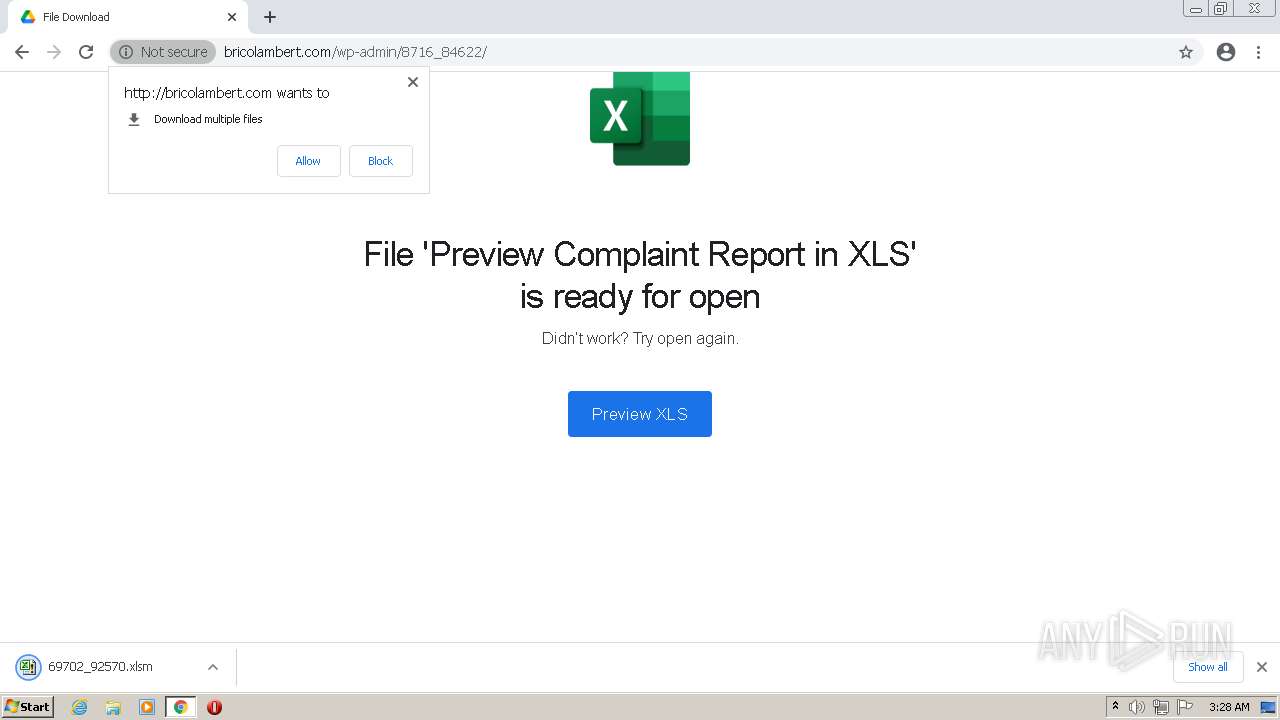
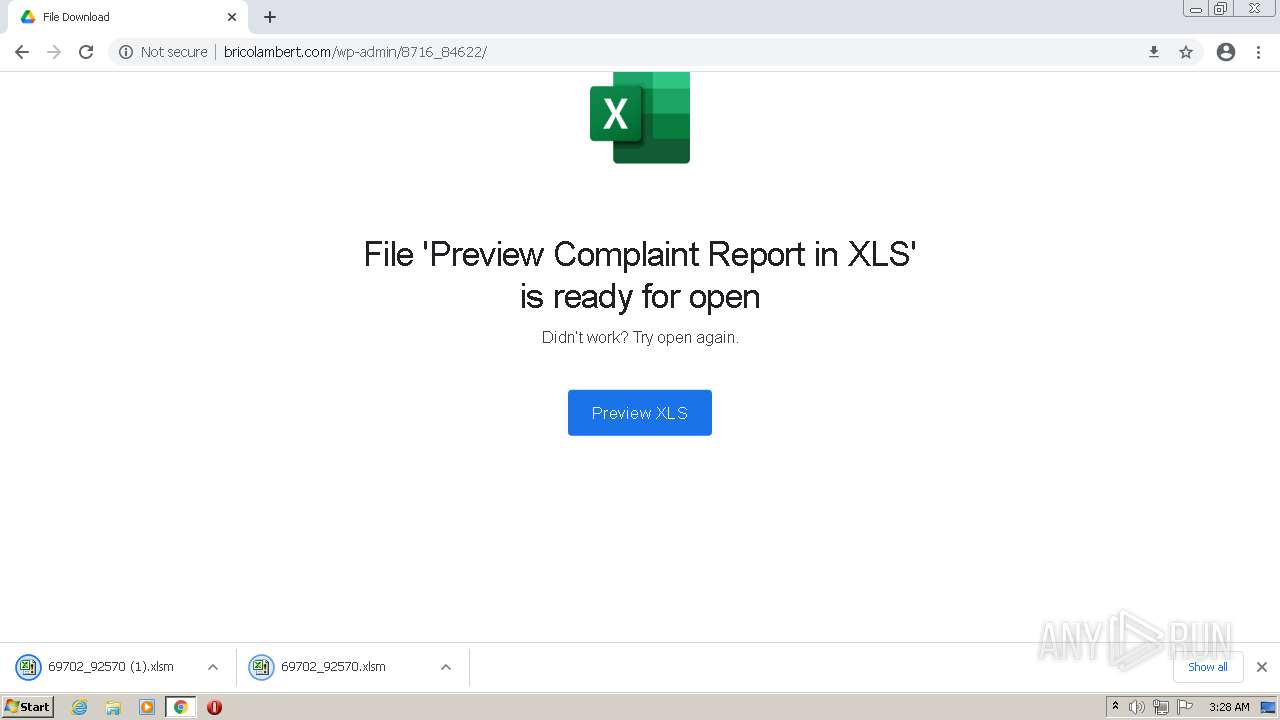
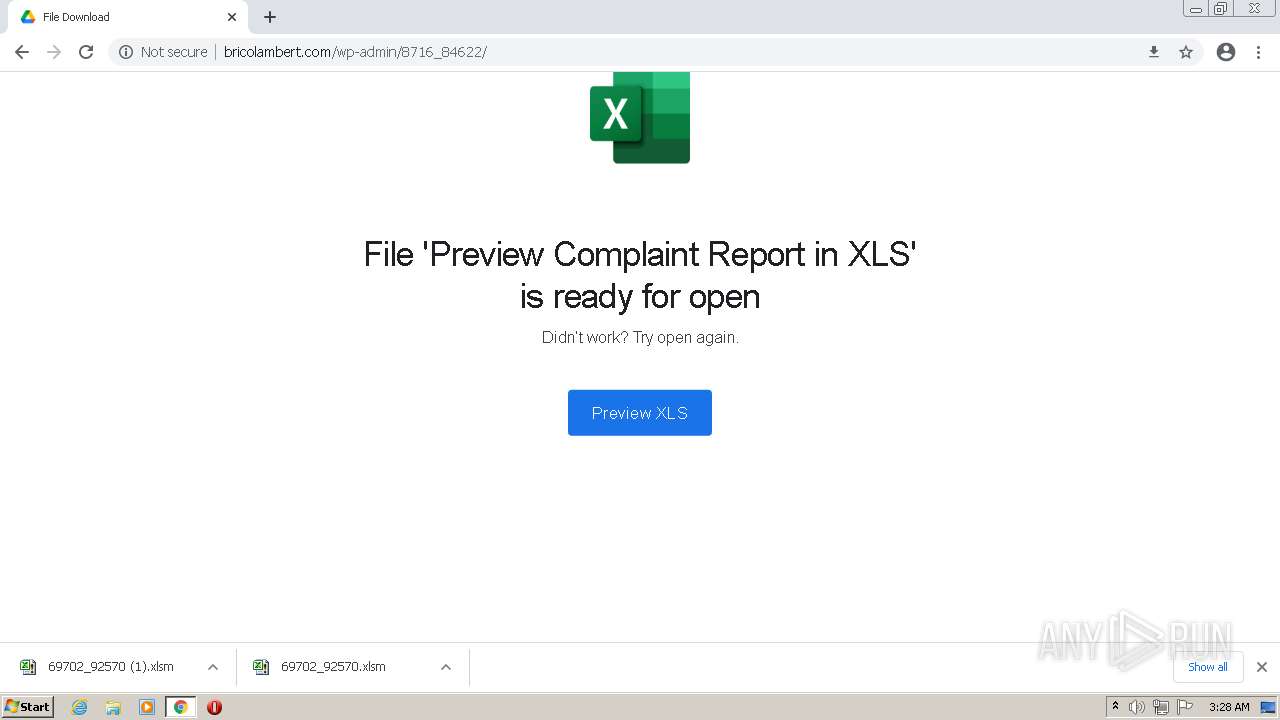
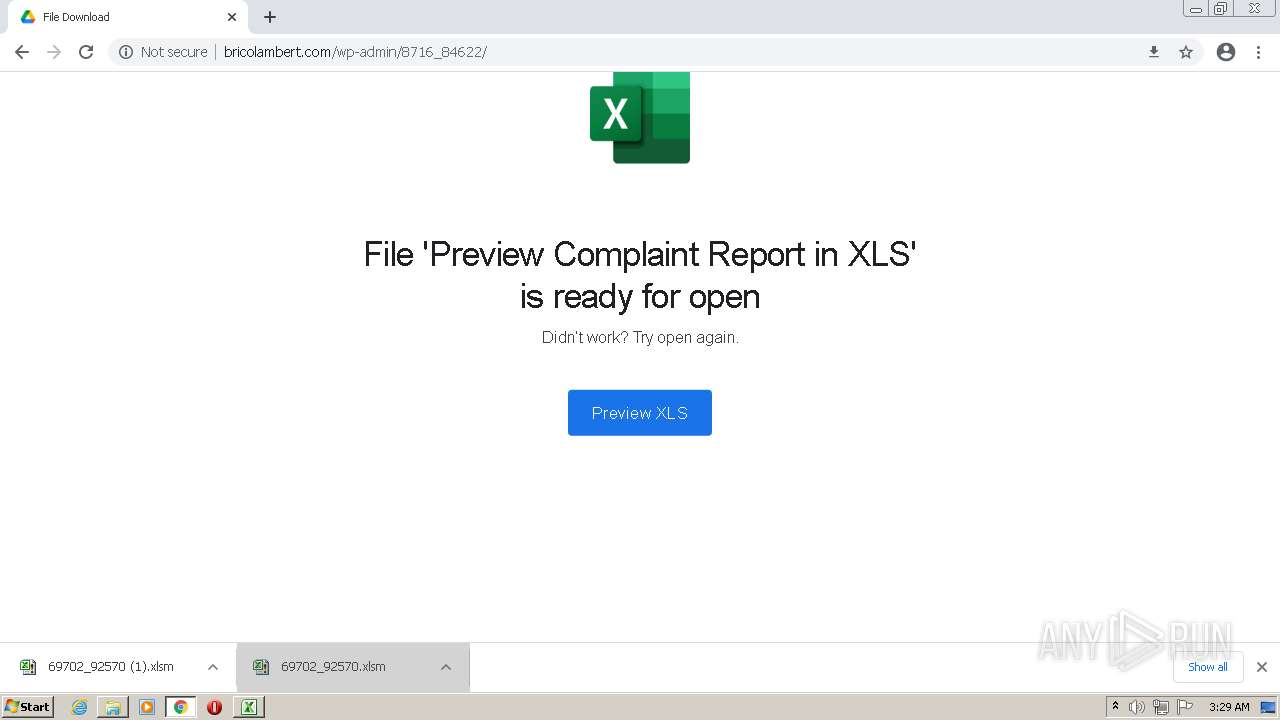
| URL: | http://bricolambert.com |
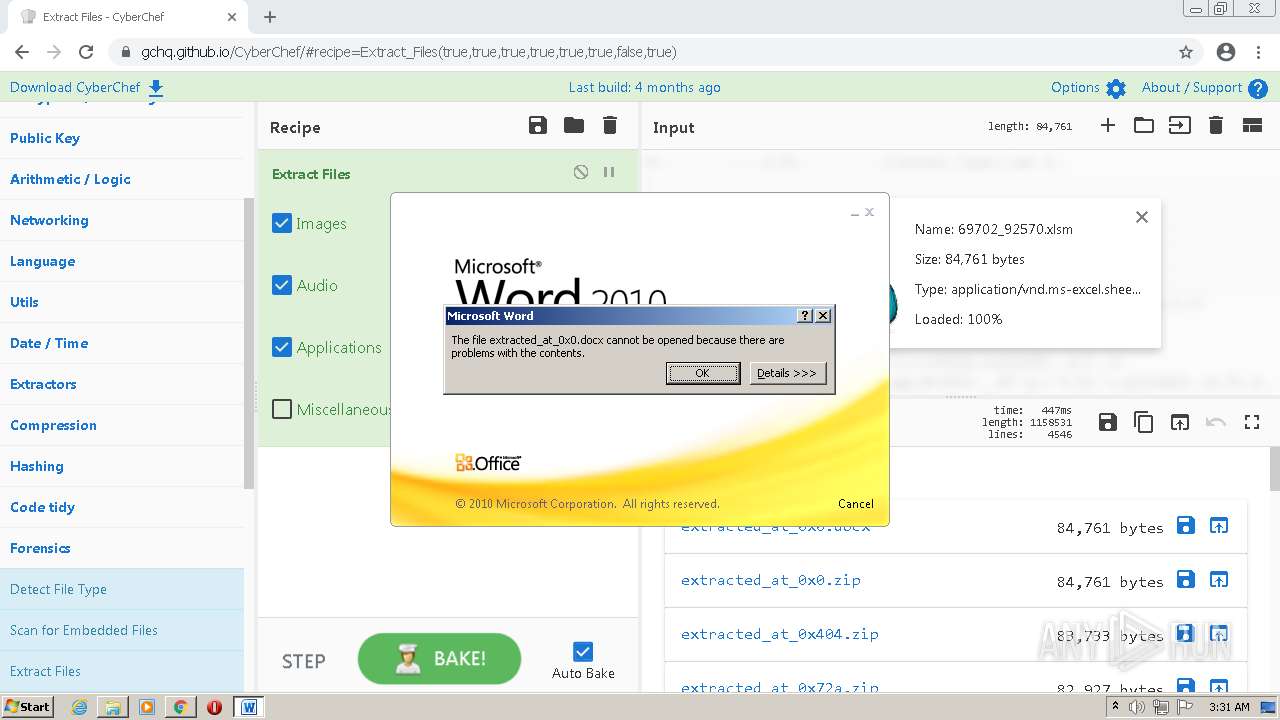
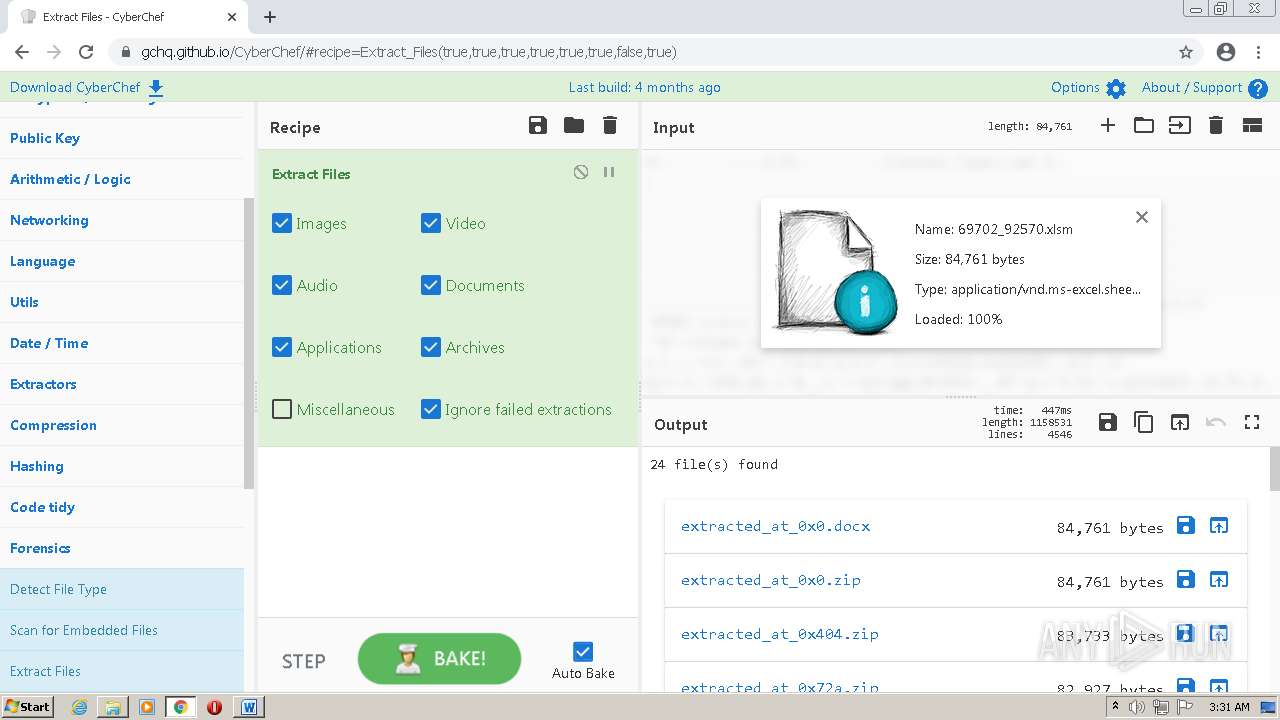
| Full analysis: | https://app.any.run/tasks/203ca02d-dc36-4dab-a74c-d1885961b72d |
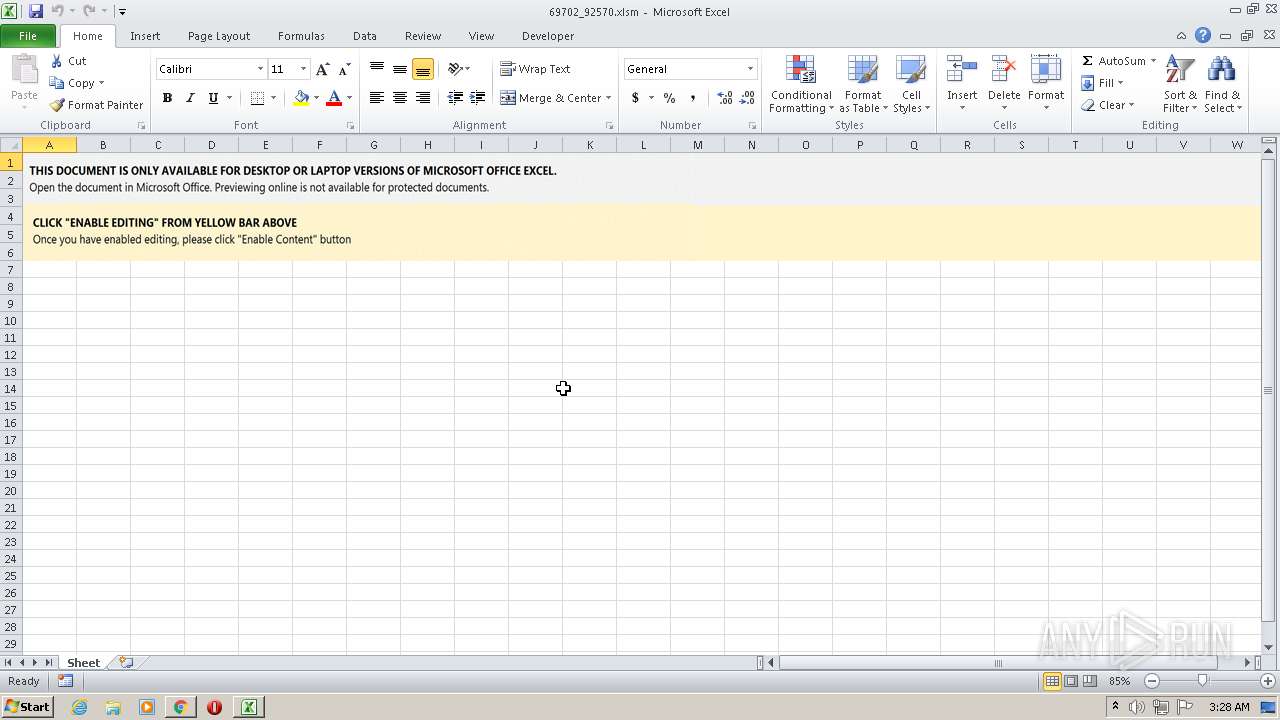
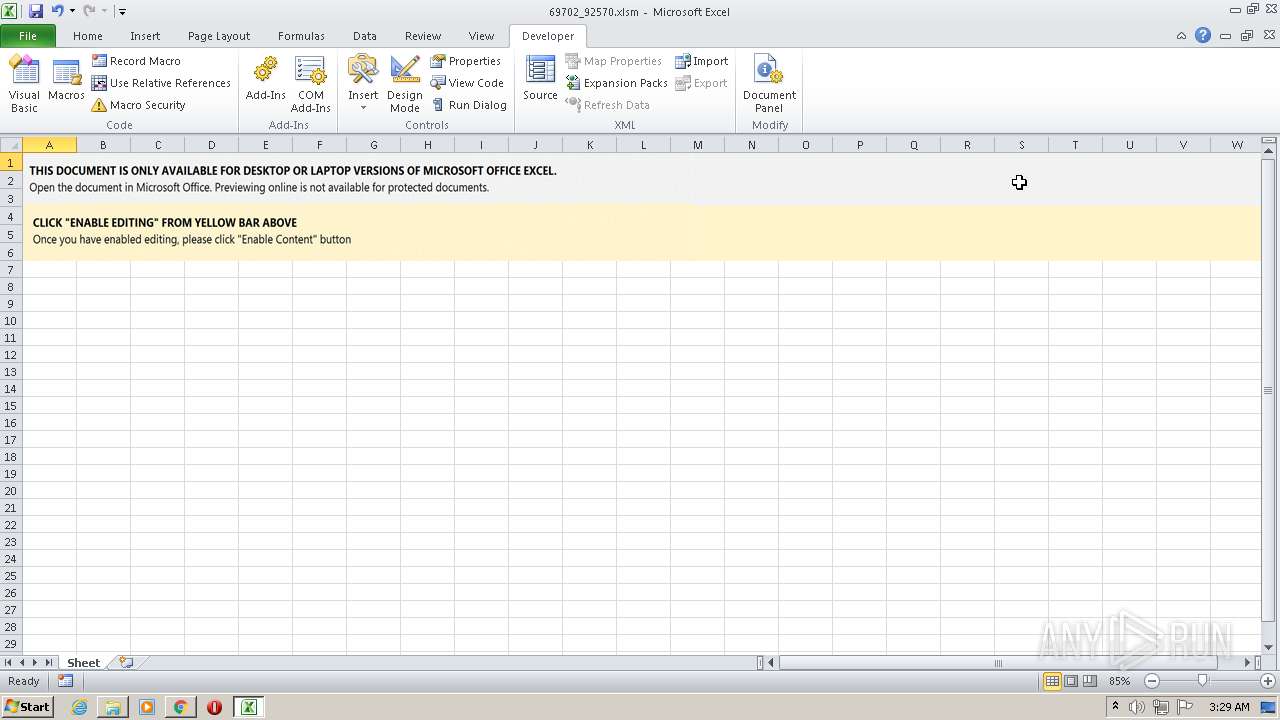
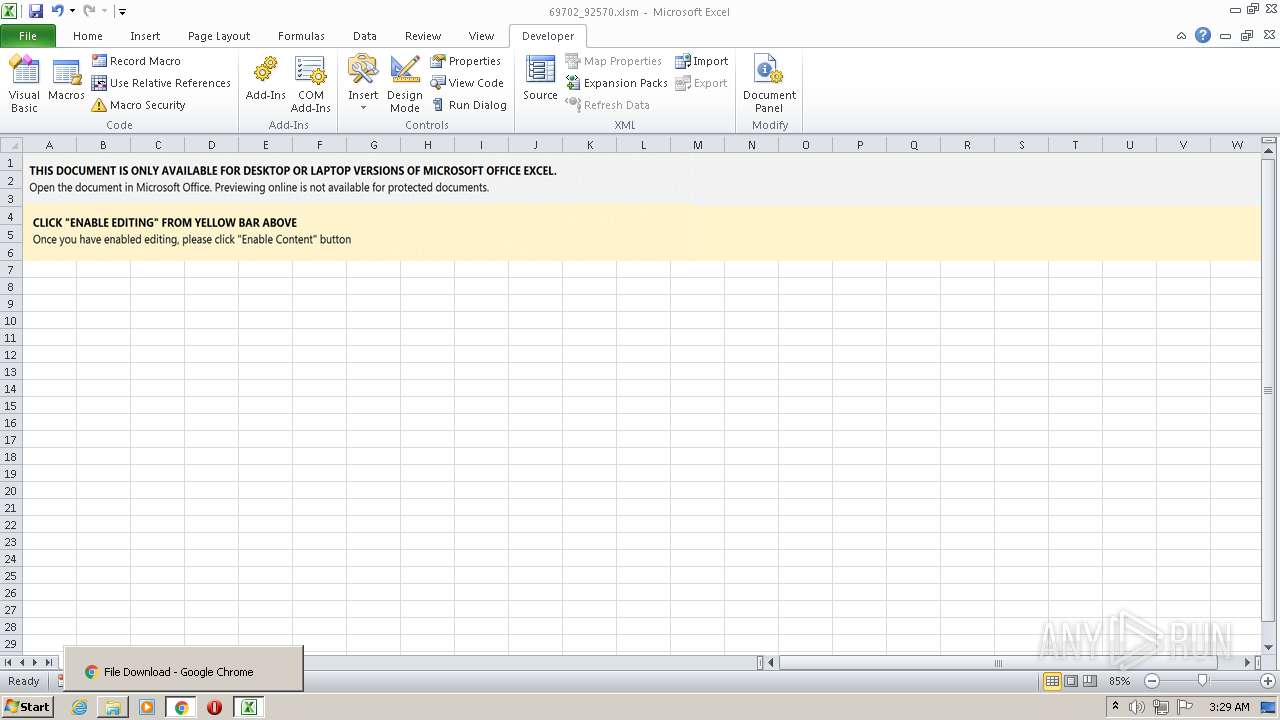
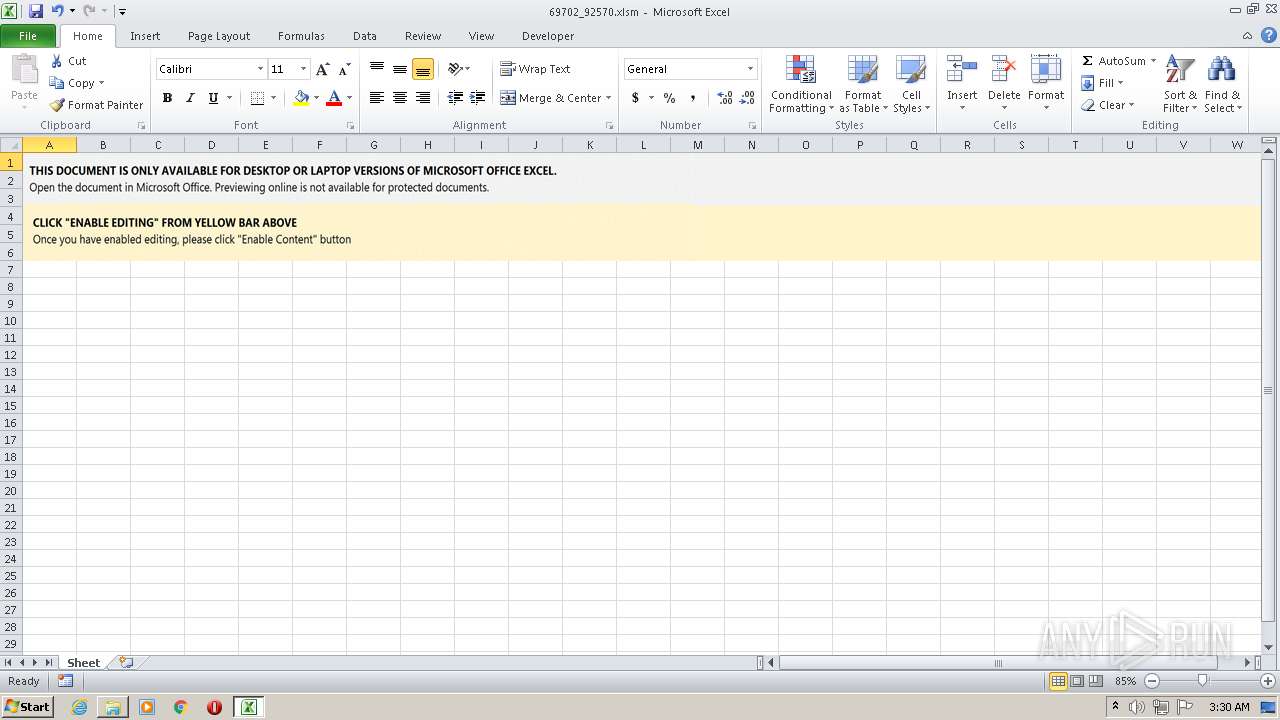
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 15, 2022, 03:26:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
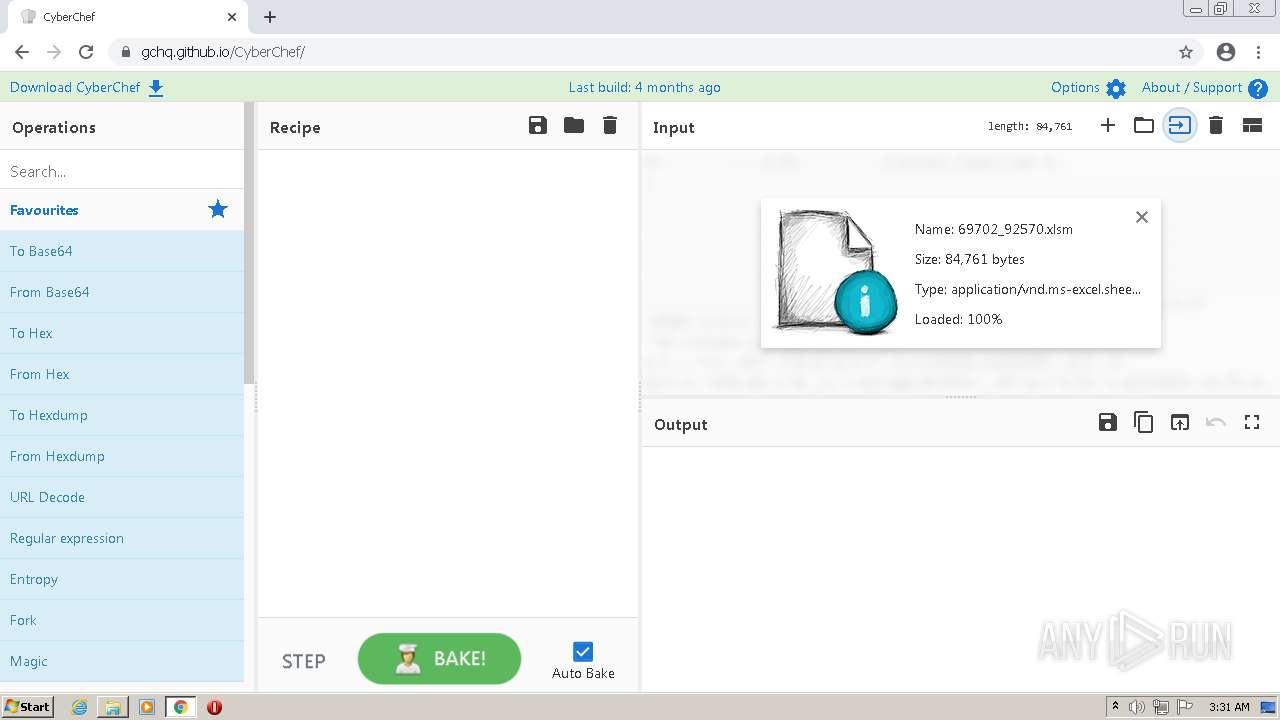
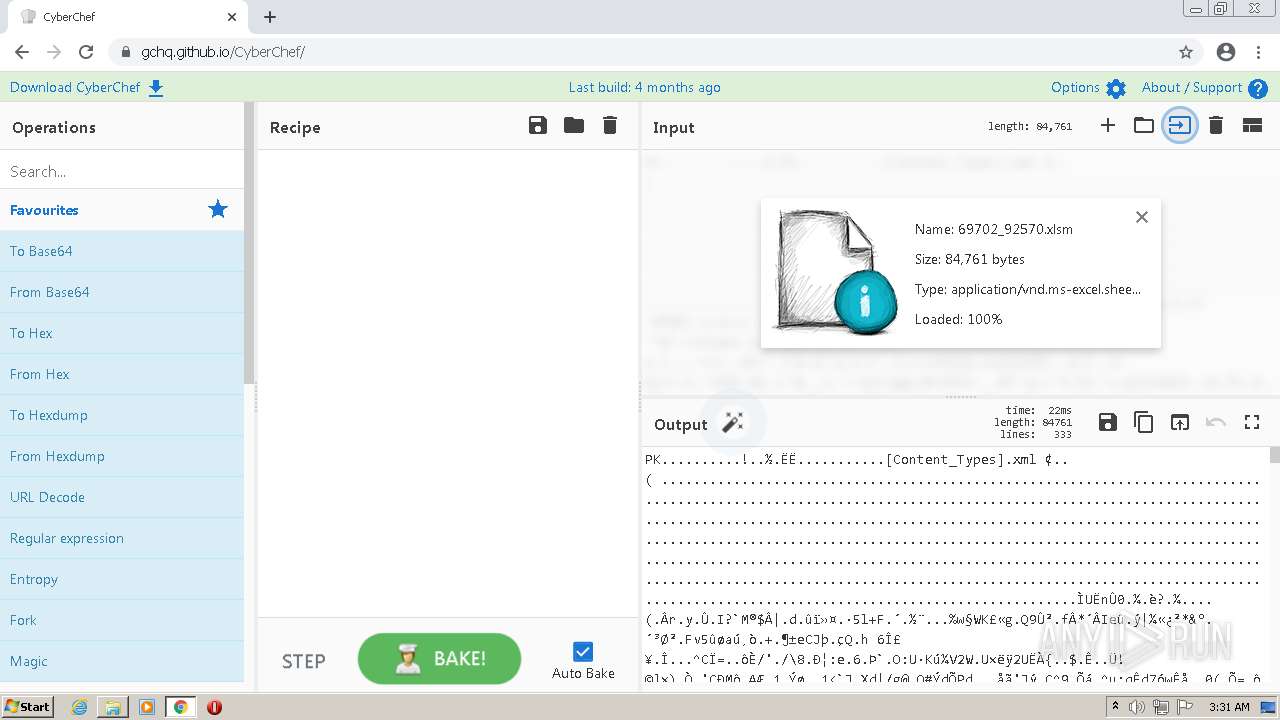
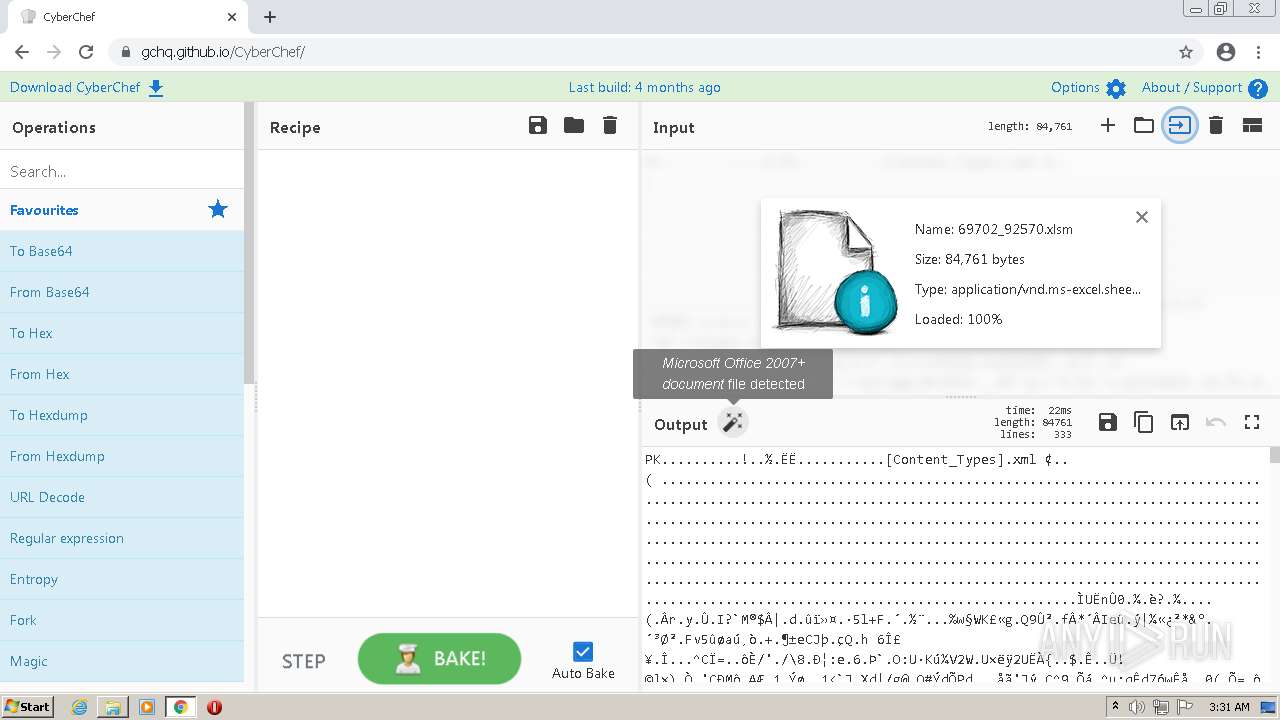
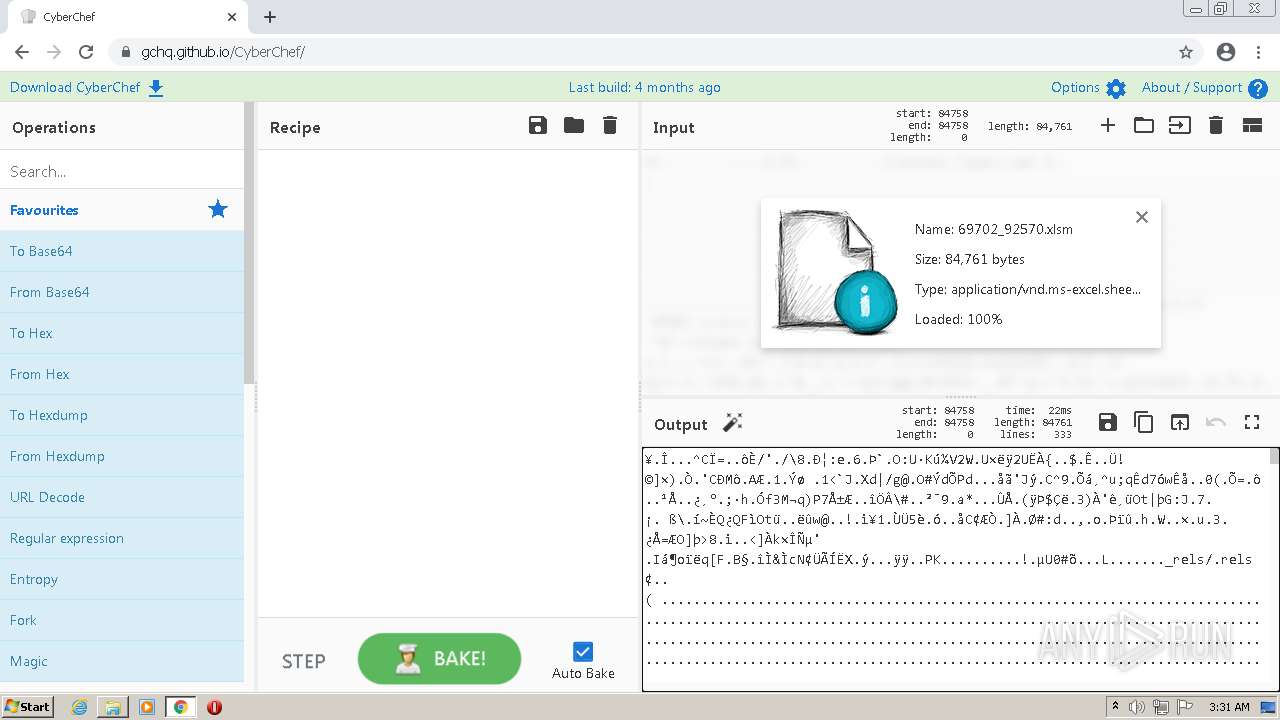
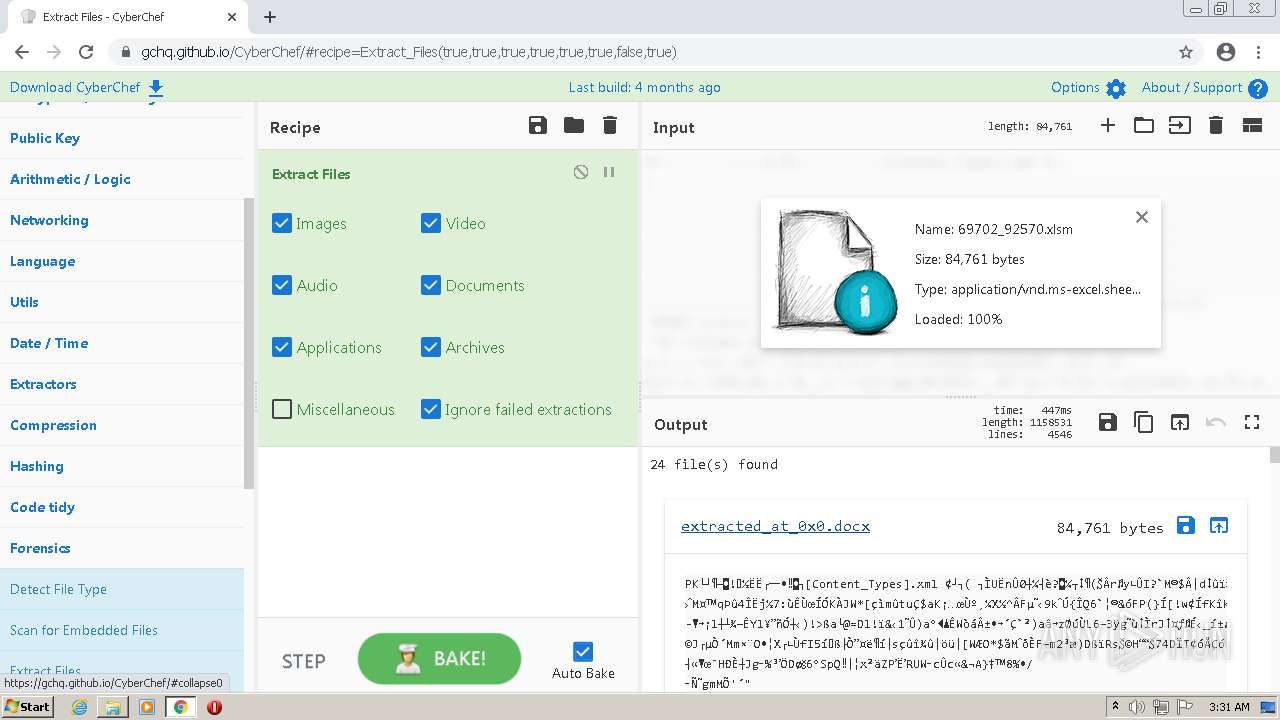
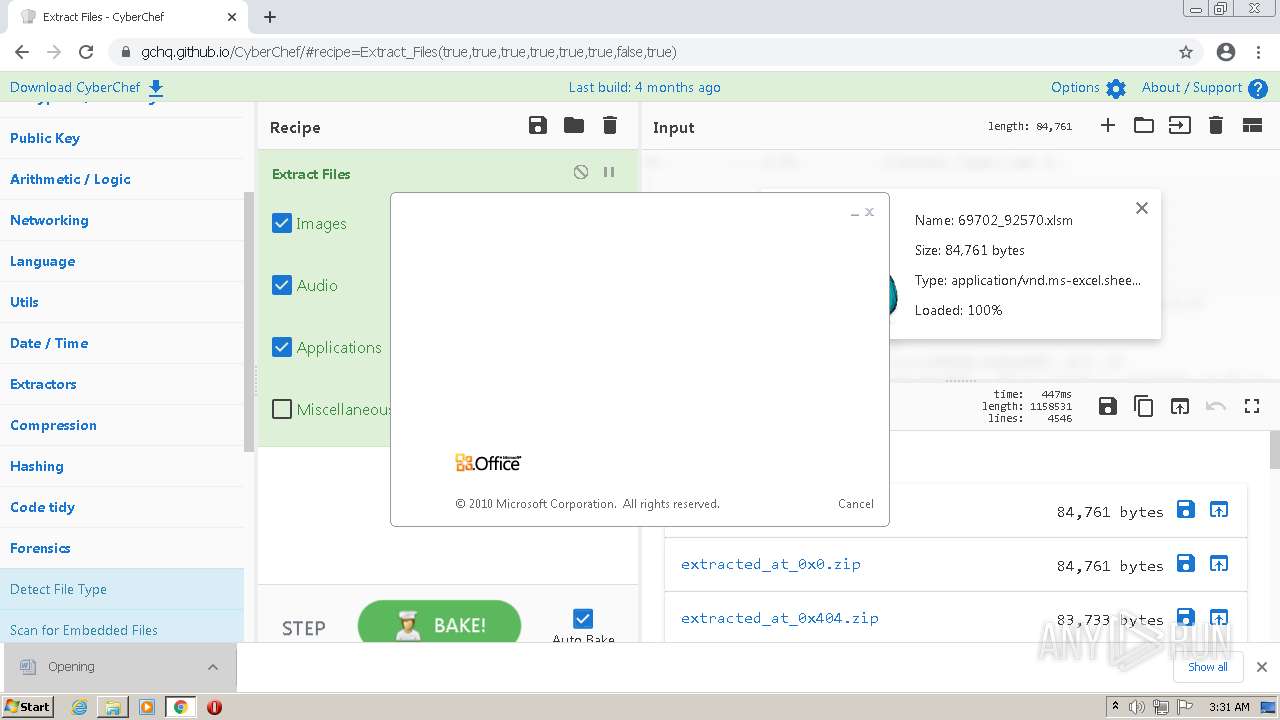
| MD5: | 27CAB4888E2CCBADCAEEFFAD7E402B55 |
| SHA1: | 9754A775DB066ED3065158D3B5405B5E5E472C38 |
| SHA256: | AF1E9382D1B031664A543429BEAC51C2B1E4359A7AFDA63977DF1DE72B0850FC |
| SSDEEP: | 3:N1Kc6TiLK:Cc6e2 |
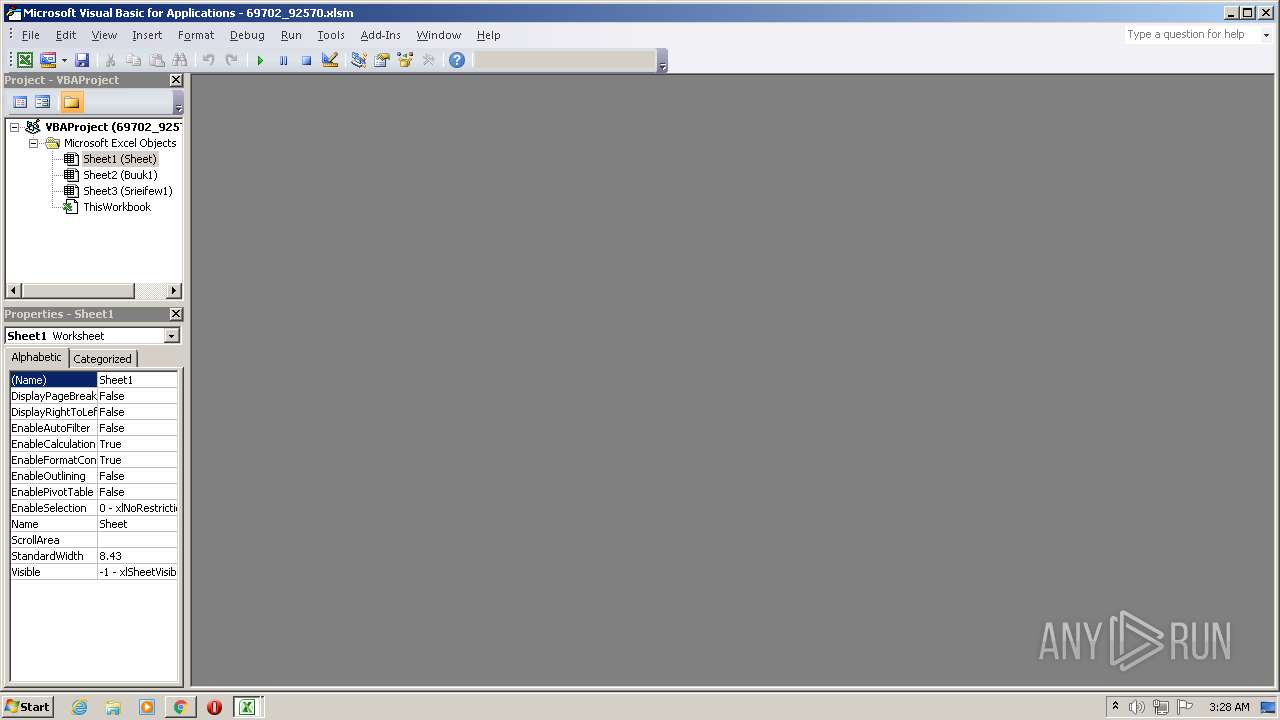
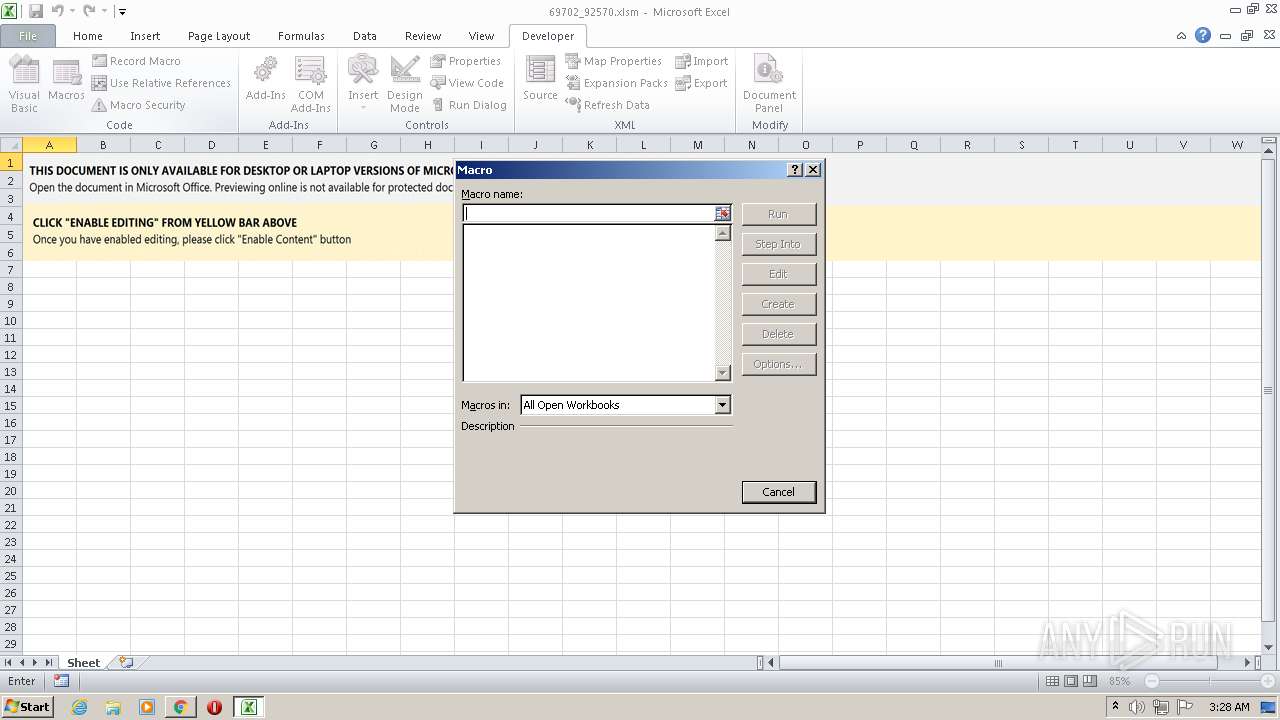
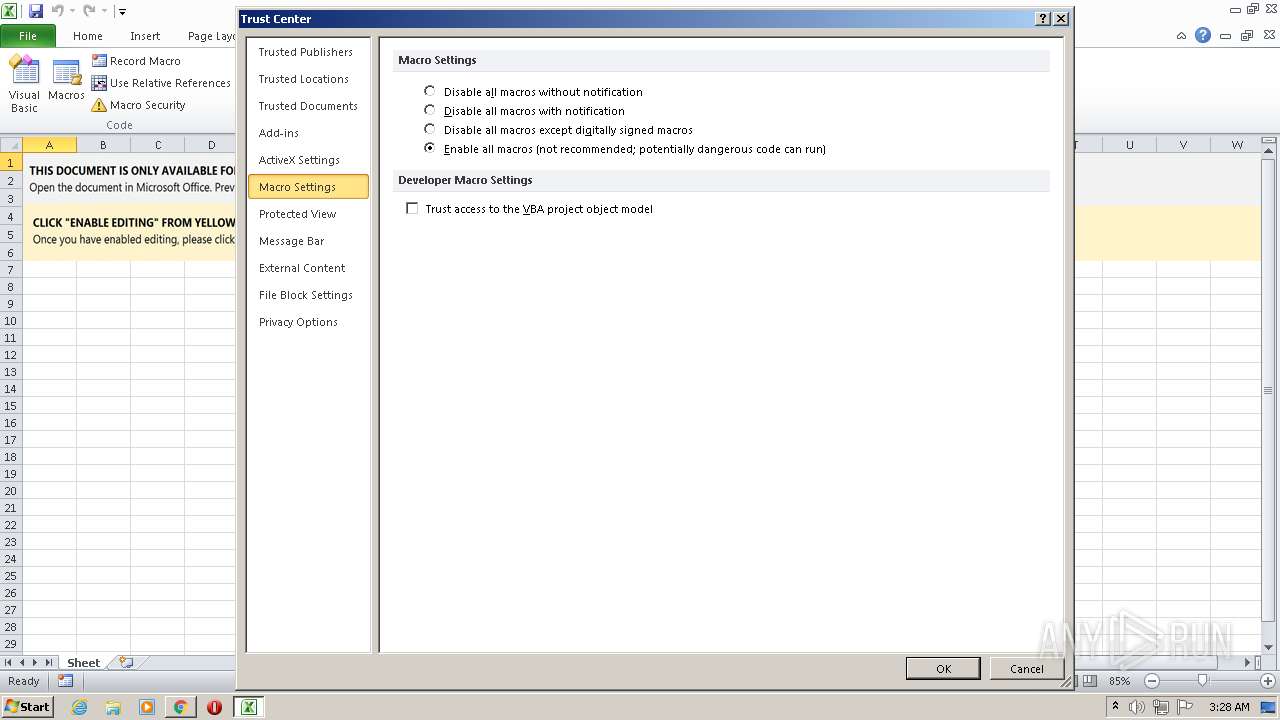
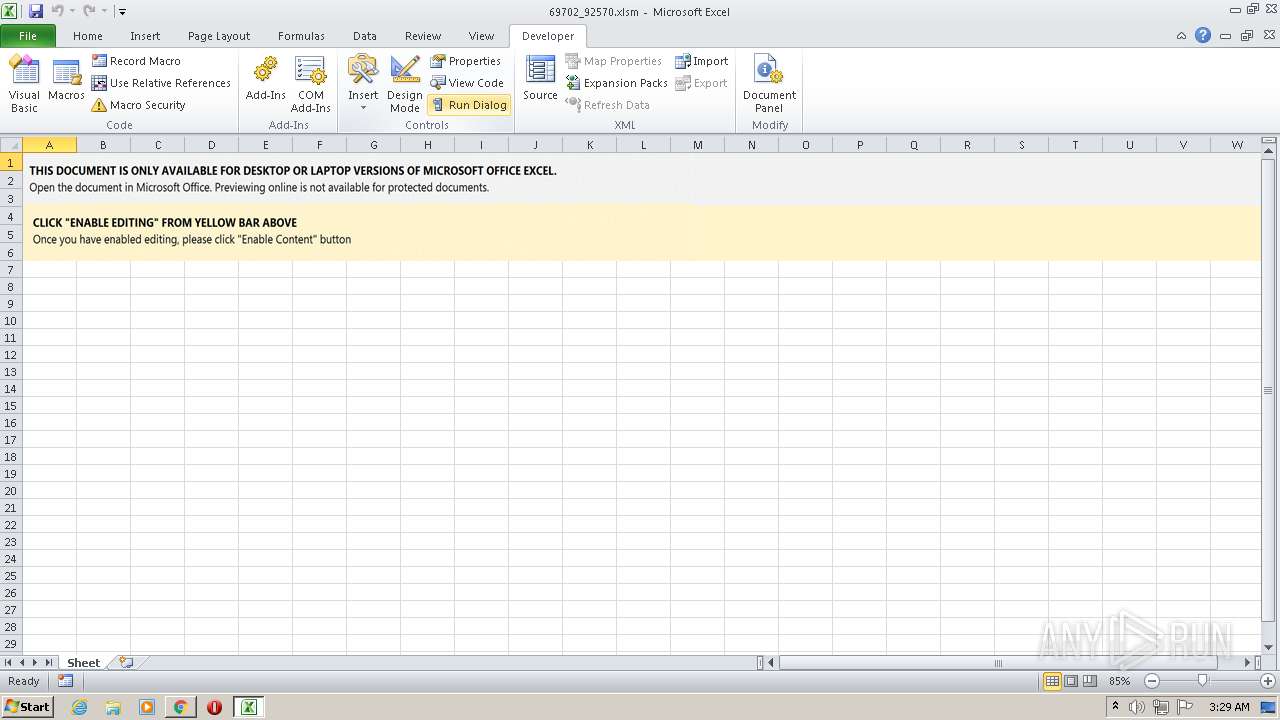
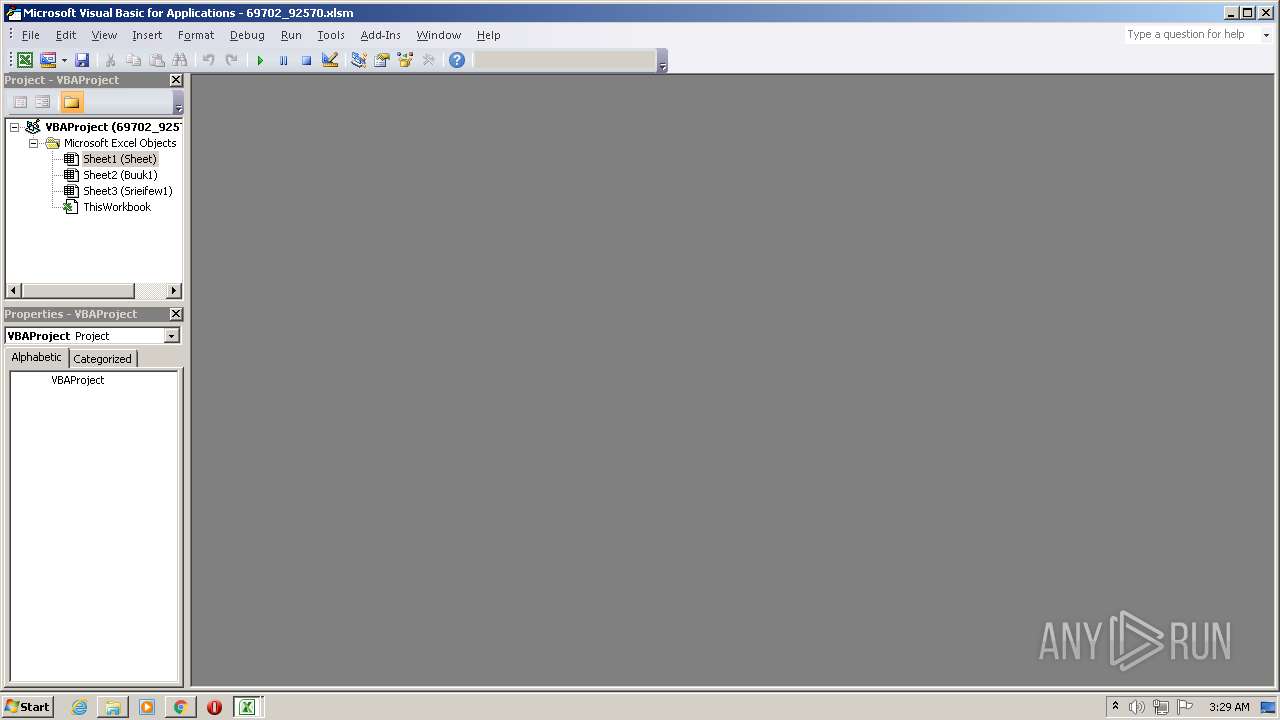
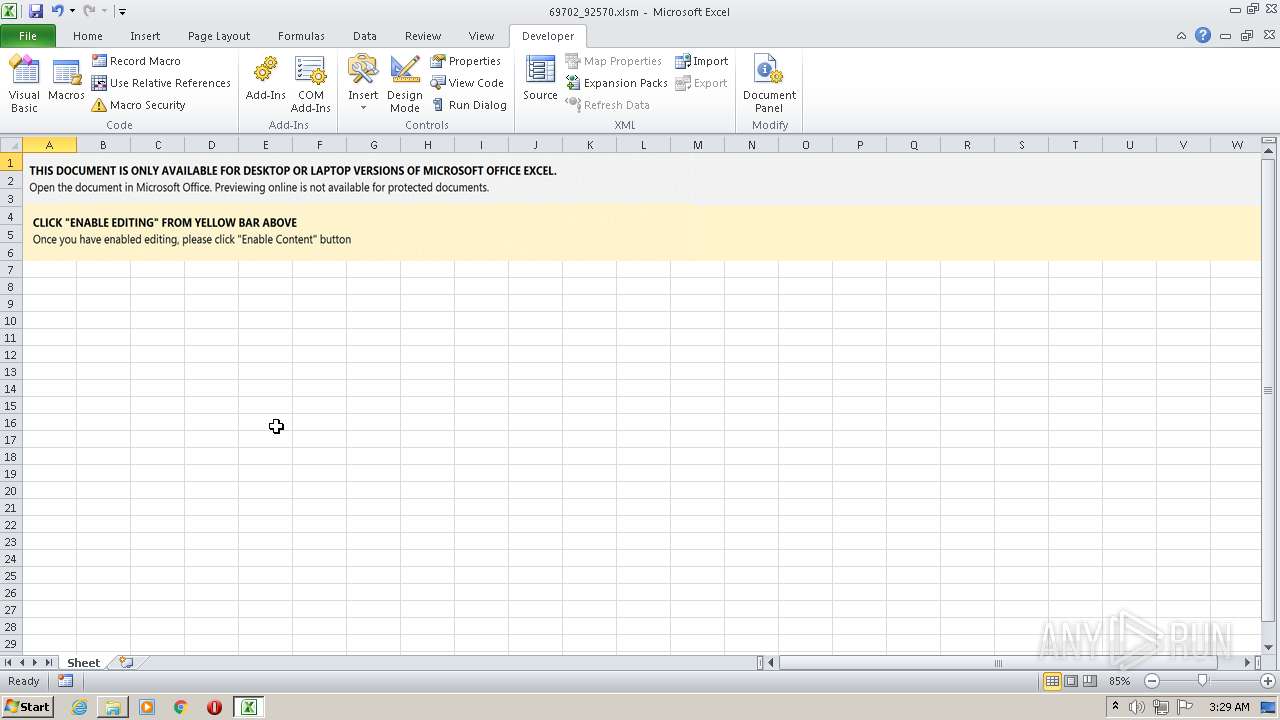
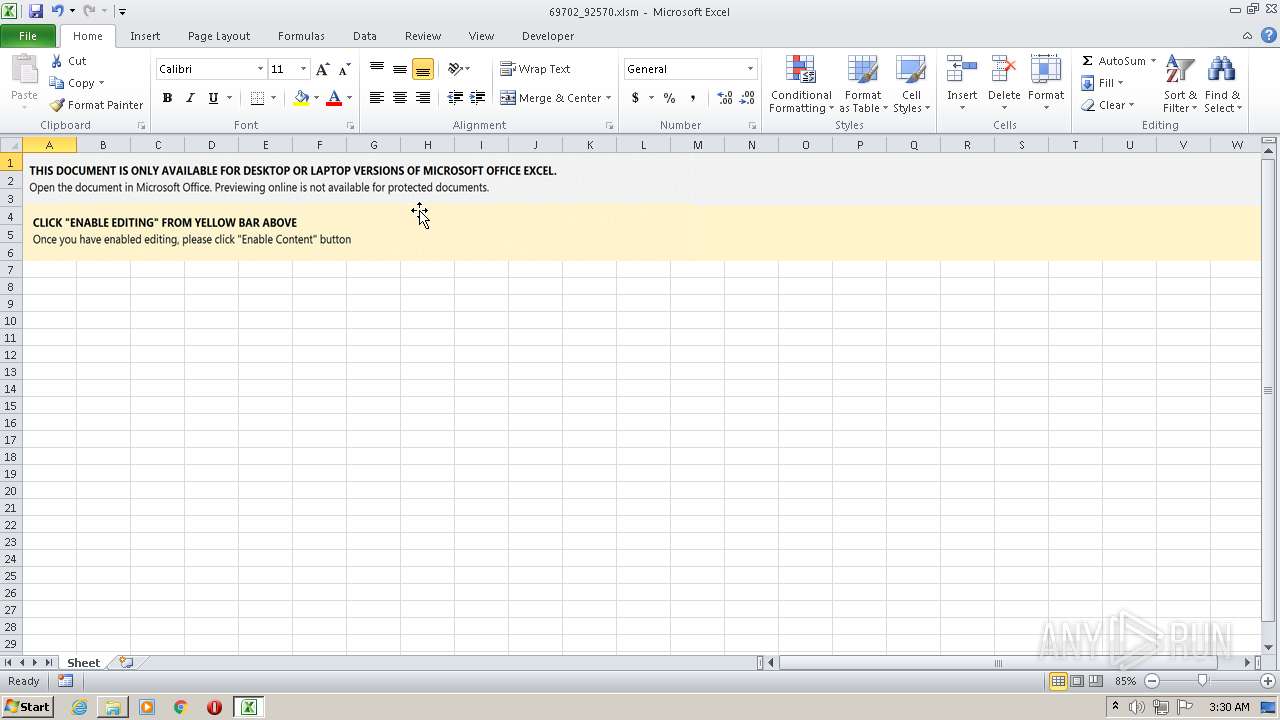
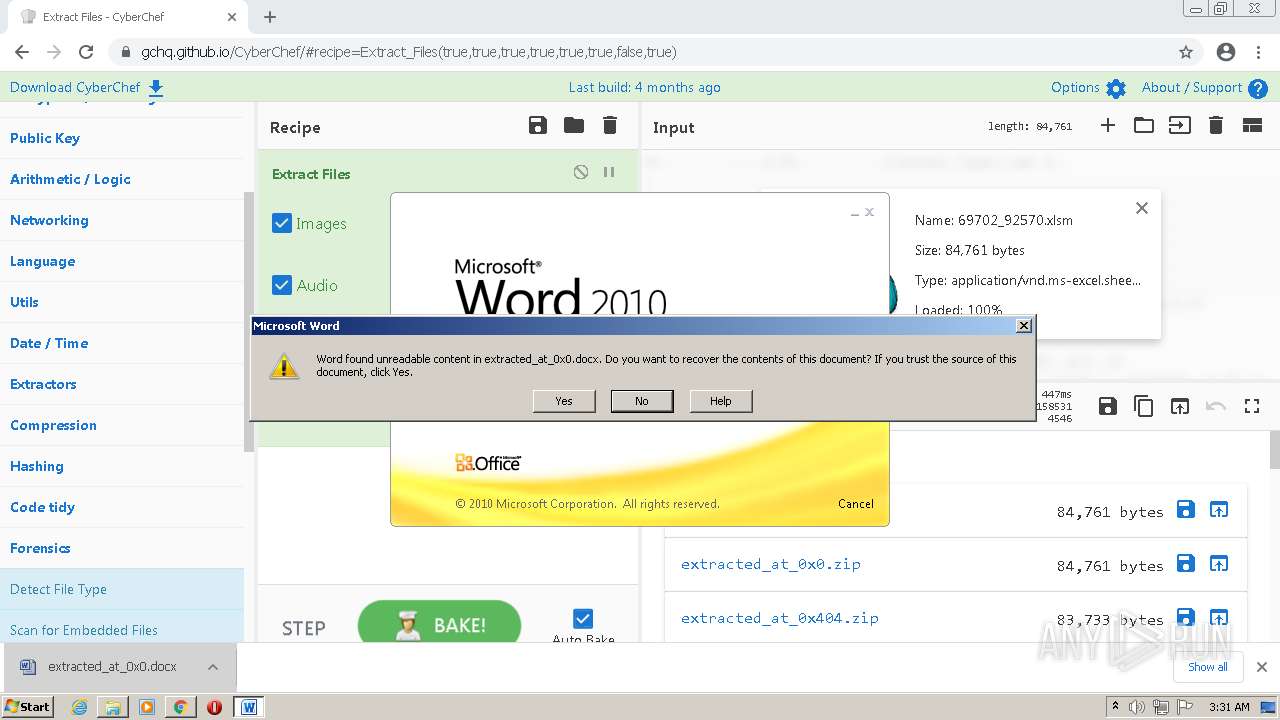
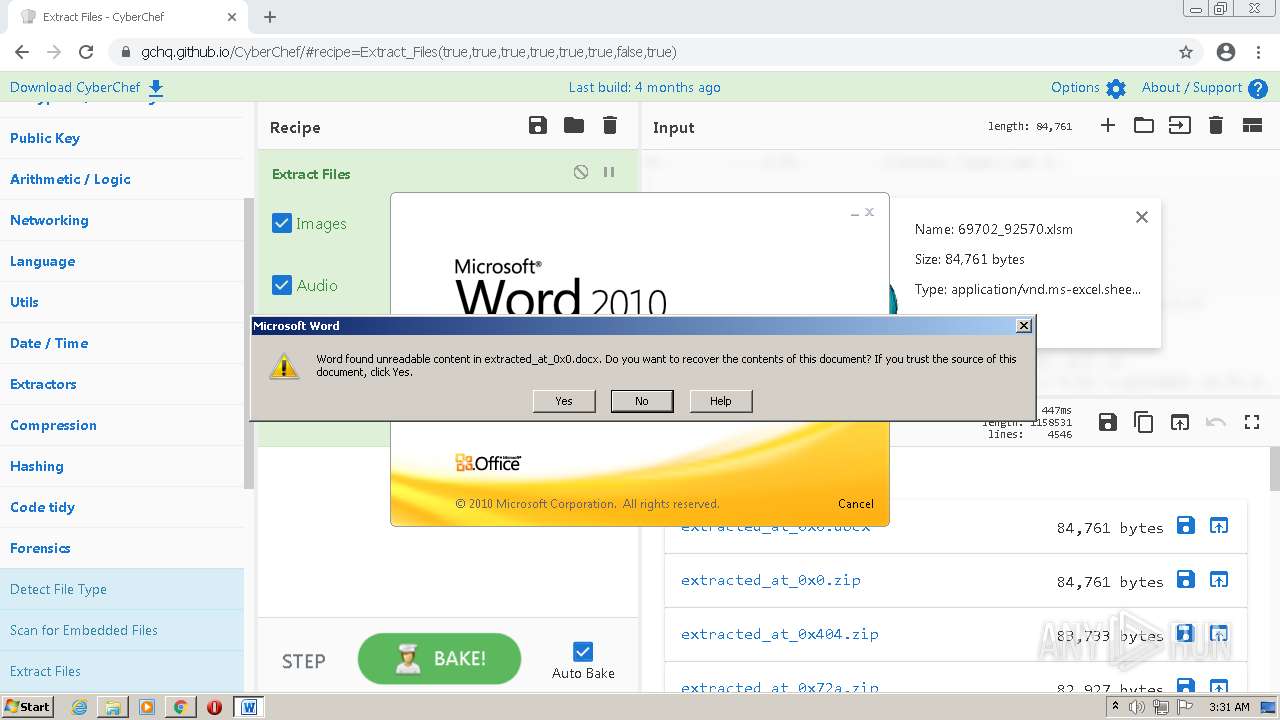
MALICIOUS
EMOTET was detected
- chrome.exe (PID: 4020)
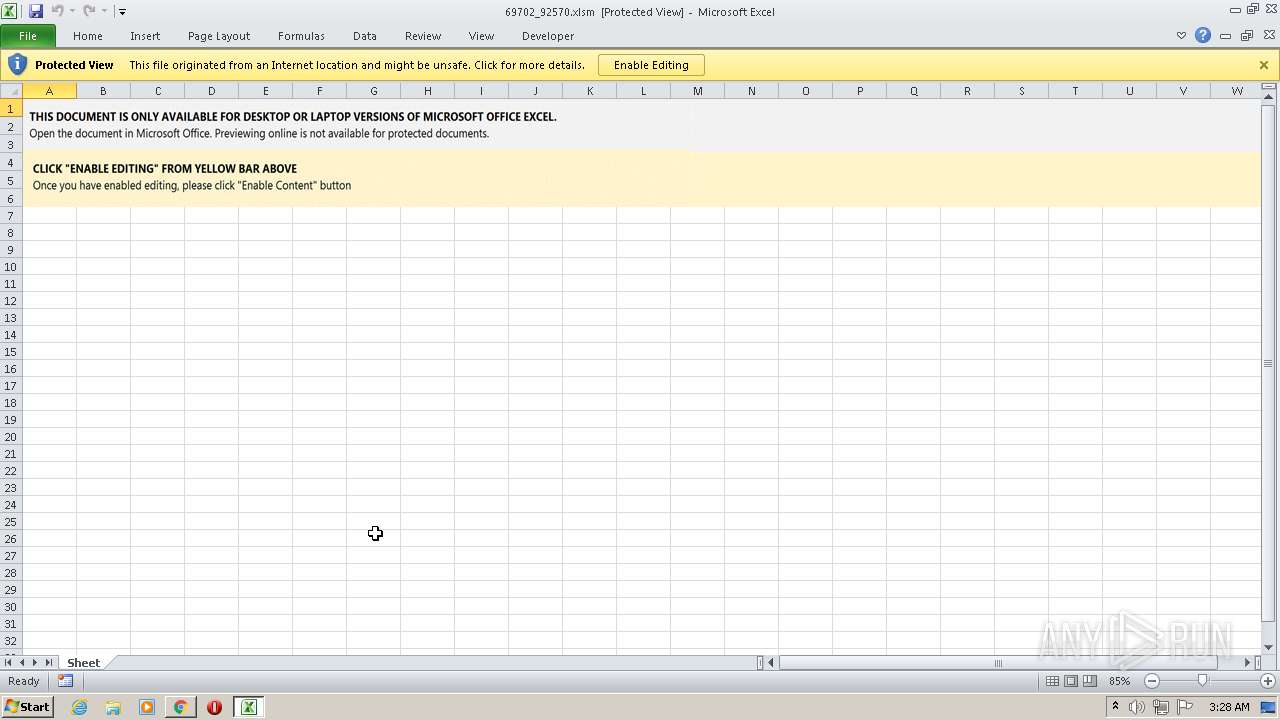
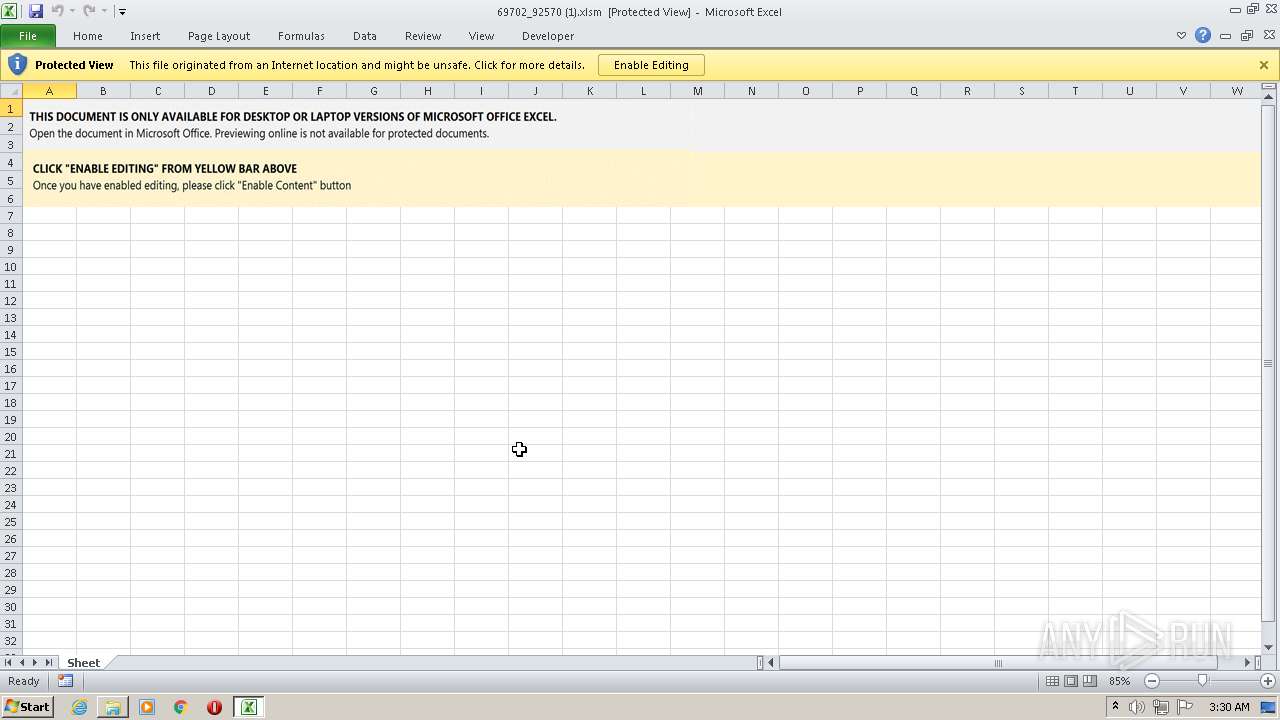
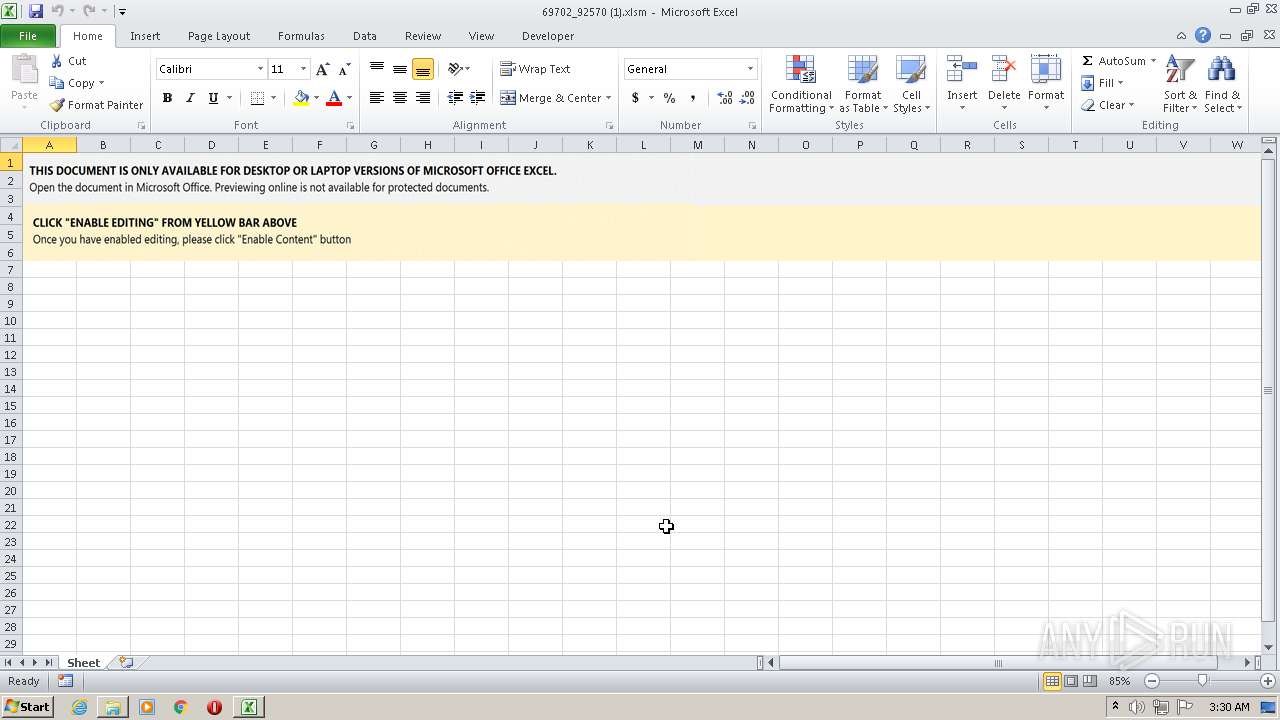
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1648)
- EXCEL.EXE (PID: 3992)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1648)
- EXCEL.EXE (PID: 3992)
Loads dropped or rewritten executable
- rundll32.exe (PID: 1512)
- SearchProtocolHost.exe (PID: 1820)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 2312)
- rundll32.exe (PID: 2740)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 3532)
- rundll32.exe (PID: 684)
- rundll32.exe (PID: 3548)
Changes the autorun value in the registry
- rundll32.exe (PID: 2740)
- rundll32.exe (PID: 3548)
Connects to CnC server
- rundll32.exe (PID: 2740)
SUSPICIOUS
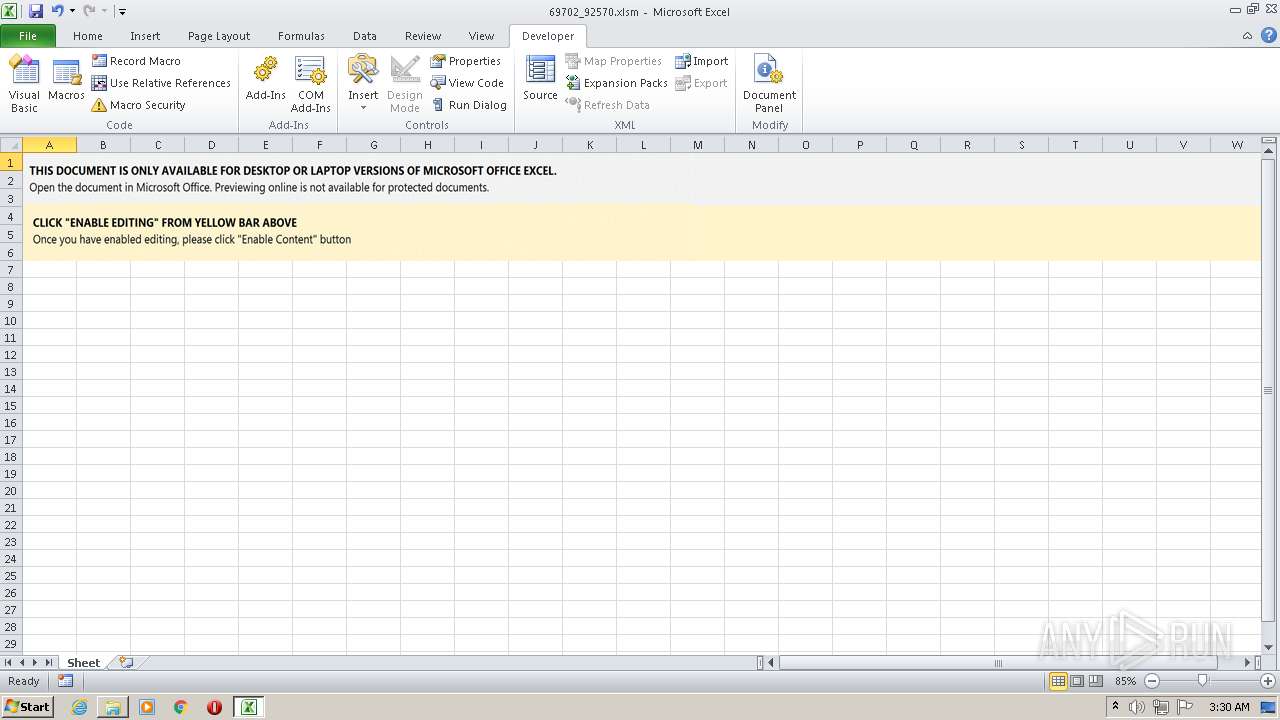
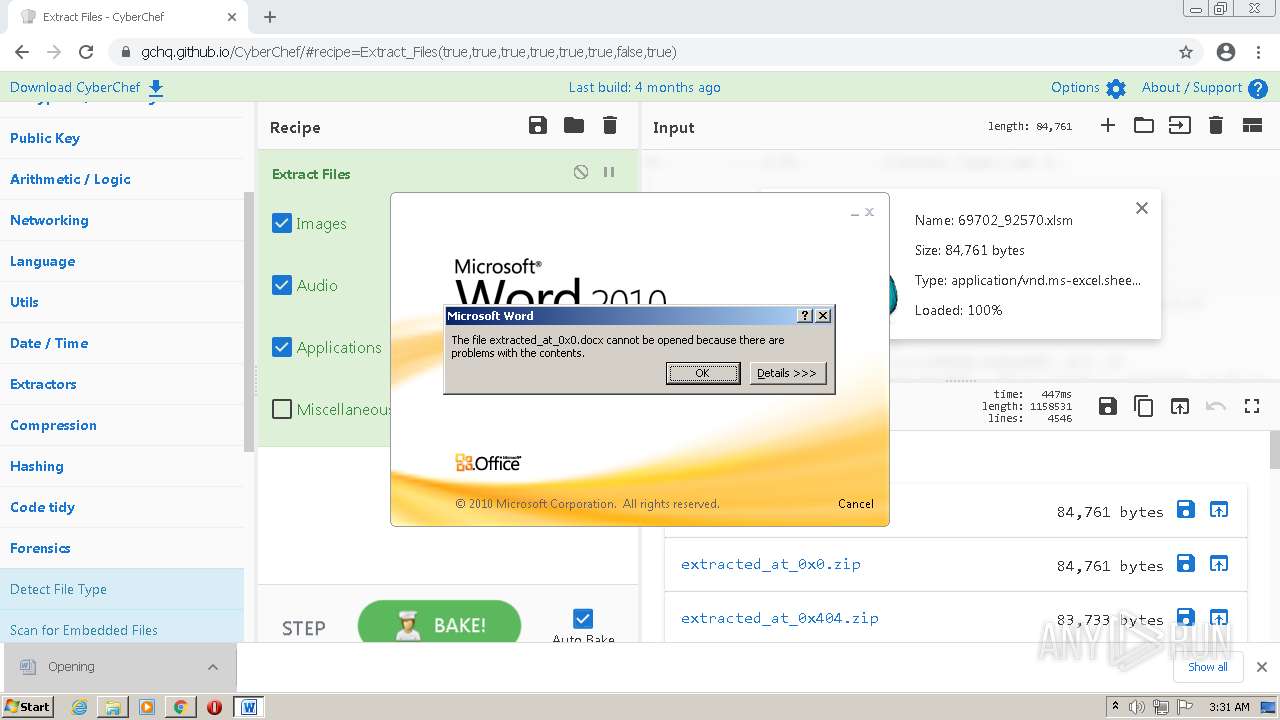
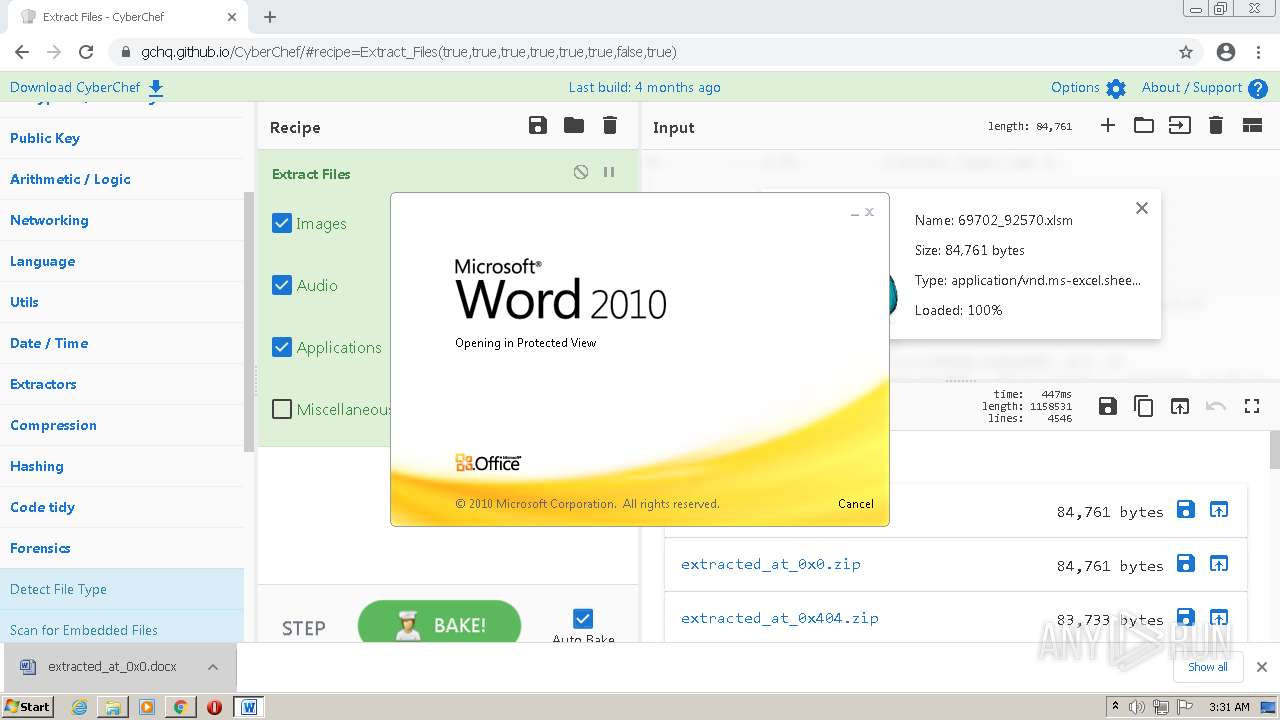
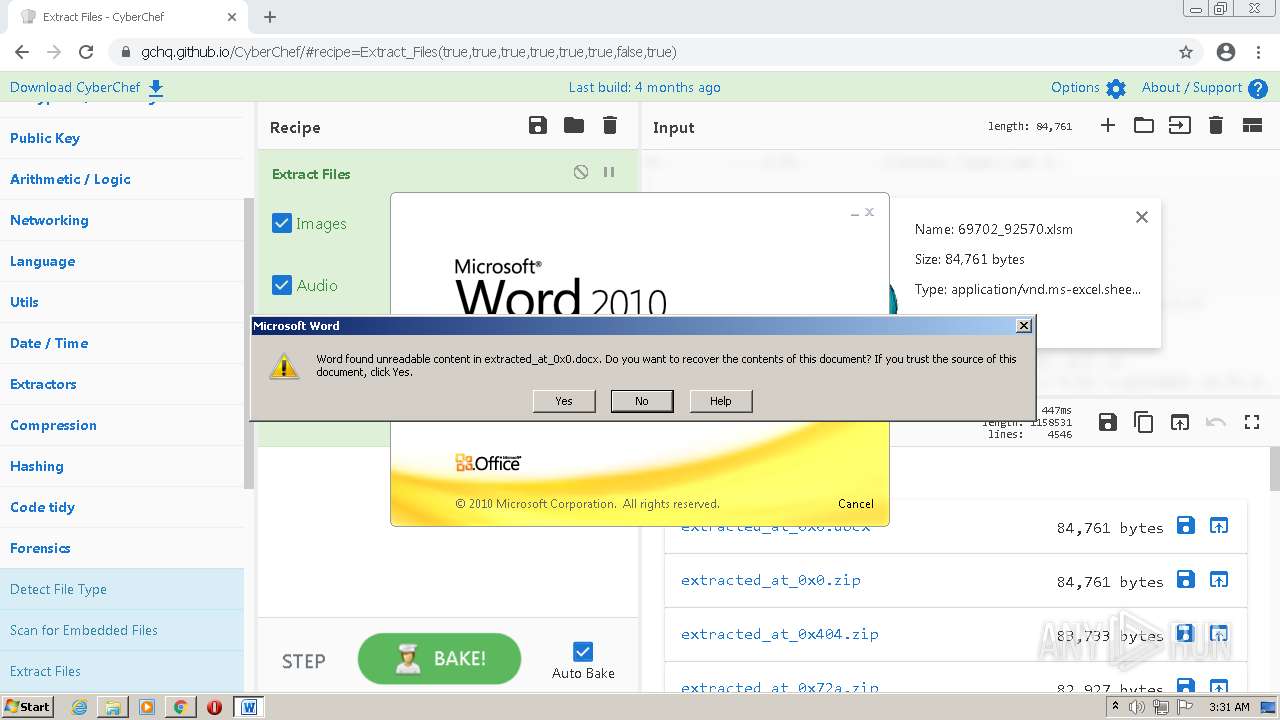
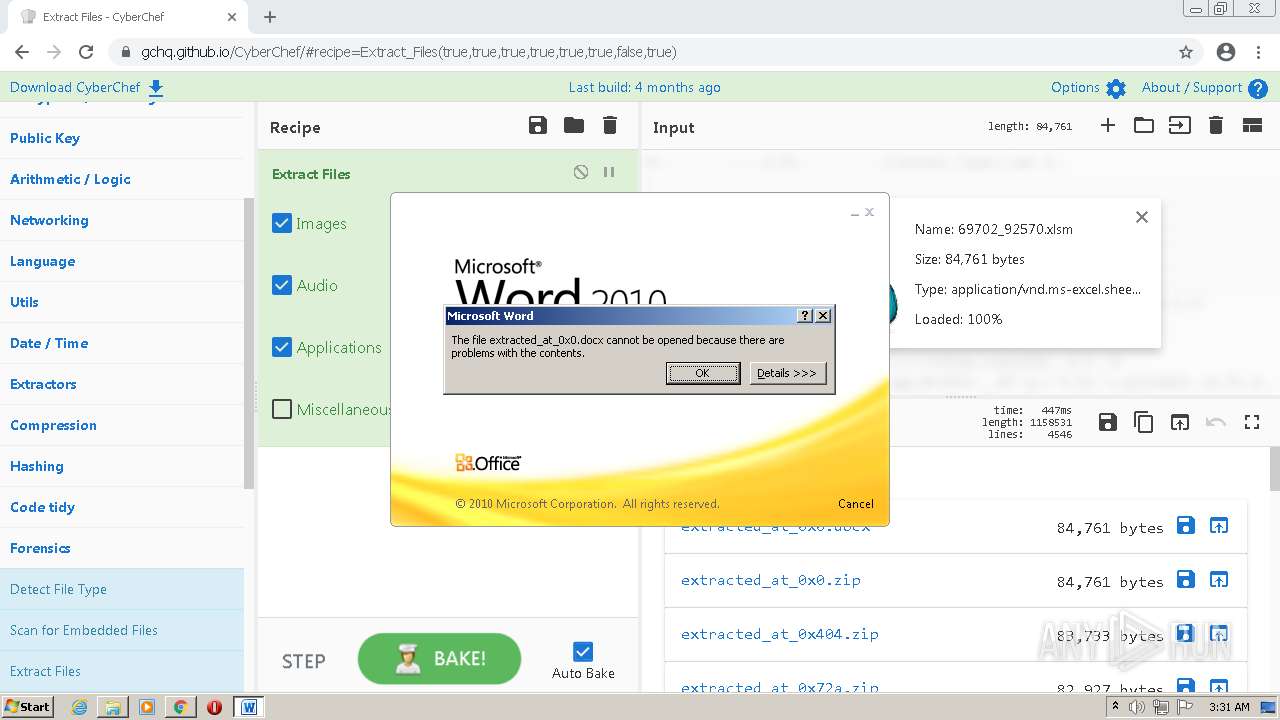
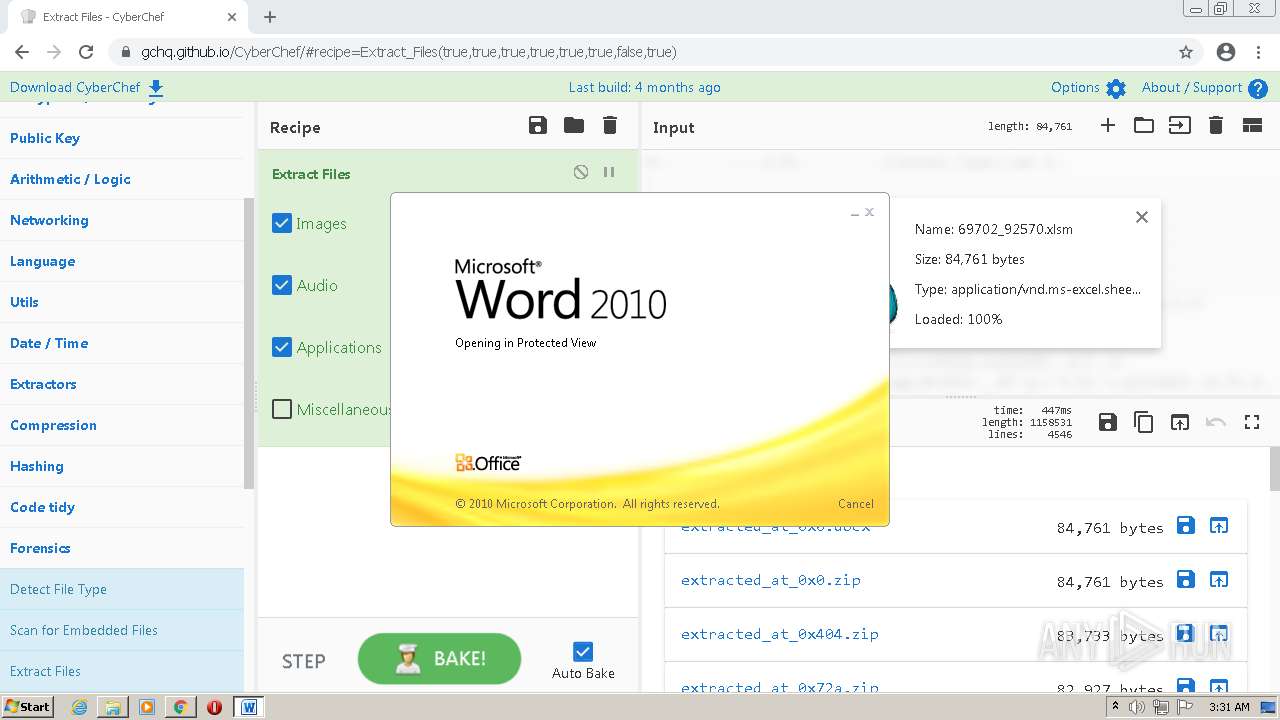
Starts Microsoft Office Application
- chrome.exe (PID: 2204)
- EXCEL.EXE (PID: 1648)
- EXCEL.EXE (PID: 3500)
- chrome.exe (PID: 1076)
- WINWORD.EXE (PID: 3844)
Application launched itself
- EXCEL.EXE (PID: 1648)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 2312)
- EXCEL.EXE (PID: 3500)
- rundll32.exe (PID: 3532)
- rundll32.exe (PID: 684)
- WINWORD.EXE (PID: 3844)
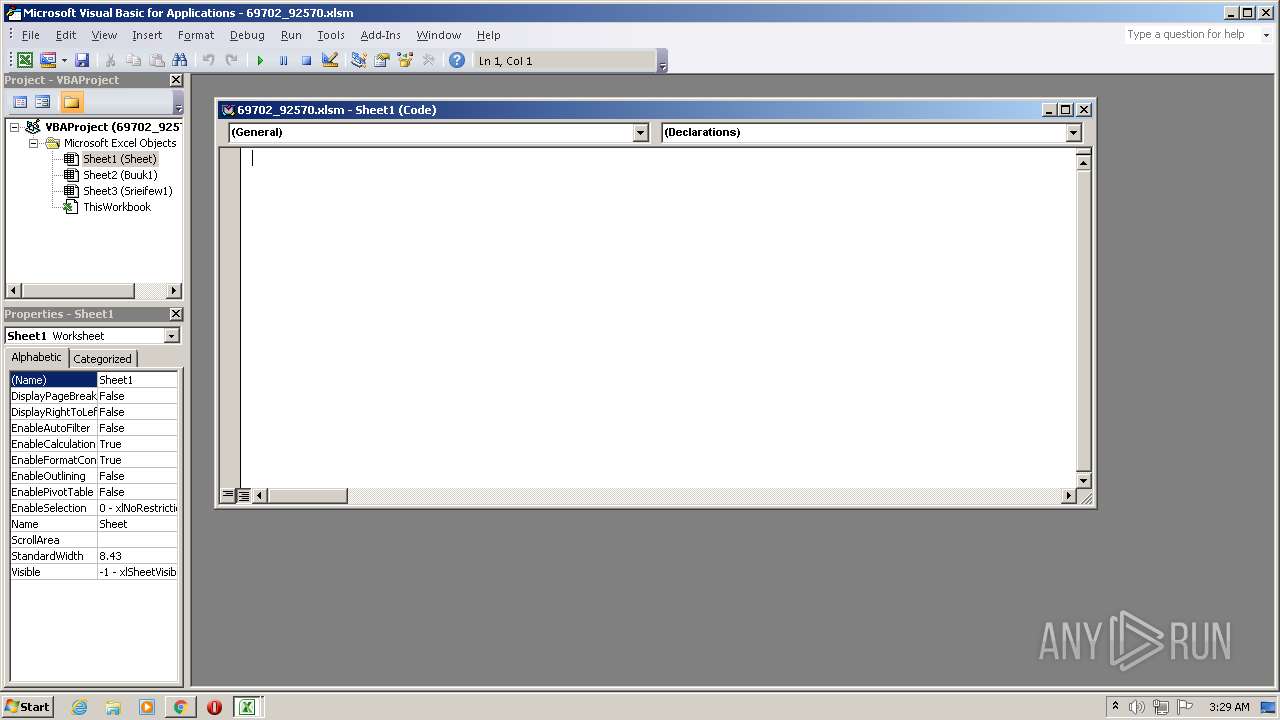
Uses RUNDLL32.EXE to load library
- EXCEL.EXE (PID: 1648)
- rundll32.exe (PID: 1512)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 2312)
- rundll32.exe (PID: 3532)
- rundll32.exe (PID: 3360)
- EXCEL.EXE (PID: 3992)
- rundll32.exe (PID: 684)
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 1820)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 3532)
- chrome.exe (PID: 1564)
Starts itself from another location
- rundll32.exe (PID: 1512)
- rundll32.exe (PID: 3360)
Drops a file with a compile date too recent
- EXCEL.EXE (PID: 1648)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 3532)
- EXCEL.EXE (PID: 3992)
Executable content was dropped or overwritten
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 3532)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 2368)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1076)
INFO
Application launched itself
- chrome.exe (PID: 2204)
- chrome.exe (PID: 1076)
Reads the computer name
- chrome.exe (PID: 2204)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2396)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 452)
- chrome.exe (PID: 348)
- chrome.exe (PID: 3220)
- SearchProtocolHost.exe (PID: 1820)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 3072)
- EXCEL.EXE (PID: 3336)
- EXCEL.EXE (PID: 1648)
- explorer.exe (PID: 2532)
- chrome.exe (PID: 2484)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 2740)
- EXCEL.EXE (PID: 2964)
- EXCEL.EXE (PID: 3500)
- EXCEL.EXE (PID: 3992)
- rundll32.exe (PID: 3532)
- rundll32.exe (PID: 3548)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 1564)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2820)
- WINWORD.EXE (PID: 3844)
- WINWORD.EXE (PID: 908)
Checks supported languages
- chrome.exe (PID: 4020)
- chrome.exe (PID: 1028)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2396)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 452)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 348)
- SearchProtocolHost.exe (PID: 1820)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2484)
- EXCEL.EXE (PID: 1648)
- EXCEL.EXE (PID: 3336)
- chrome.exe (PID: 2816)
- explorer.exe (PID: 2532)
- rundll32.exe (PID: 3360)
- rundll32.exe (PID: 2312)
- rundll32.exe (PID: 1512)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2376)
- EXCEL.EXE (PID: 3500)
- rundll32.exe (PID: 2740)
- EXCEL.EXE (PID: 2964)
- rundll32.exe (PID: 3532)
- rundll32.exe (PID: 3360)
- EXCEL.EXE (PID: 3992)
- rundll32.exe (PID: 3548)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 1584)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 1124)
- rundll32.exe (PID: 684)
- chrome.exe (PID: 2492)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 656)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 1564)
- WINWORD.EXE (PID: 3844)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 2368)
- WINWORD.EXE (PID: 908)
- chrome.exe (PID: 2160)
Reads the hosts file
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 3532)
Reads settings of System Certificates
- chrome.exe (PID: 4020)
- EXCEL.EXE (PID: 1648)
- rundll32.exe (PID: 2740)
- rundll32.exe (PID: 3548)
- chrome.exe (PID: 3532)
Reads the date of Windows installation
- chrome.exe (PID: 348)
- chrome.exe (PID: 2820)
Checks Windows Trust Settings
- chrome.exe (PID: 2204)
- EXCEL.EXE (PID: 1648)
- rundll32.exe (PID: 2740)
- rundll32.exe (PID: 3548)
- chrome.exe (PID: 1076)
Reads Microsoft Office registry keys
- chrome.exe (PID: 2204)
- EXCEL.EXE (PID: 3336)
- EXCEL.EXE (PID: 2964)
- EXCEL.EXE (PID: 3500)
- EXCEL.EXE (PID: 3992)
- chrome.exe (PID: 1076)
- WINWORD.EXE (PID: 908)
- WINWORD.EXE (PID: 3844)
- EXCEL.EXE (PID: 1648)
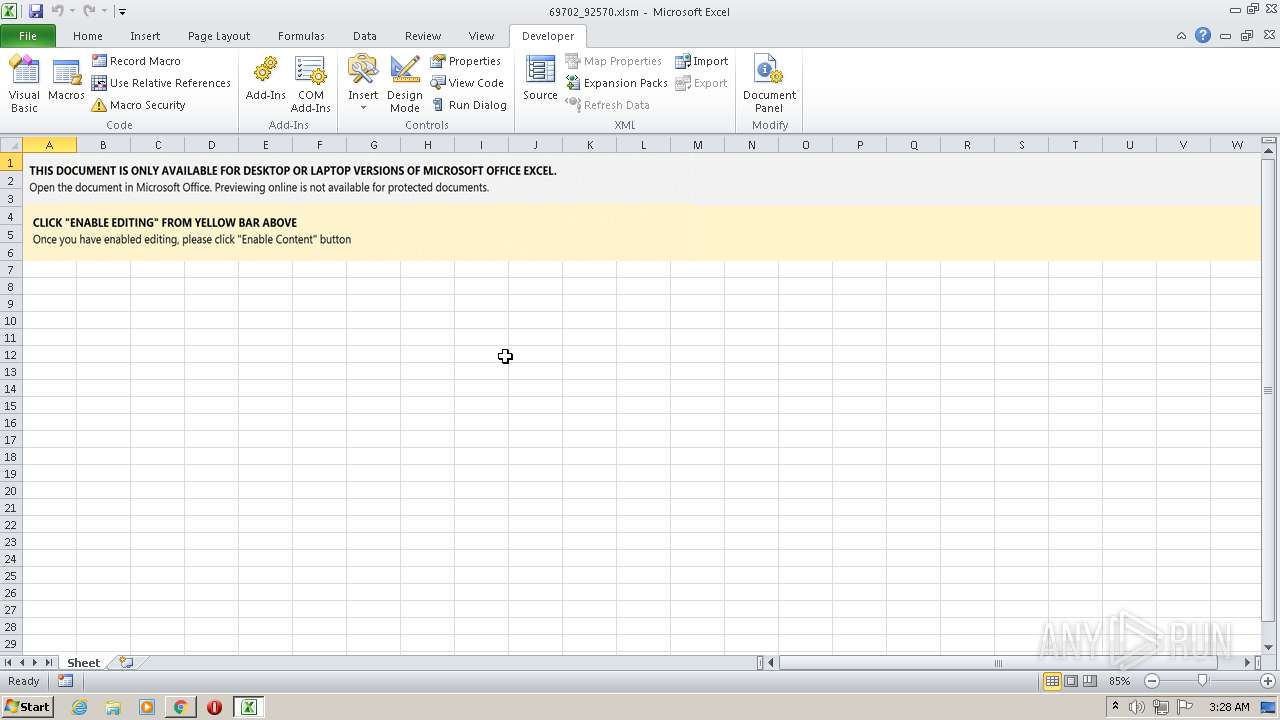
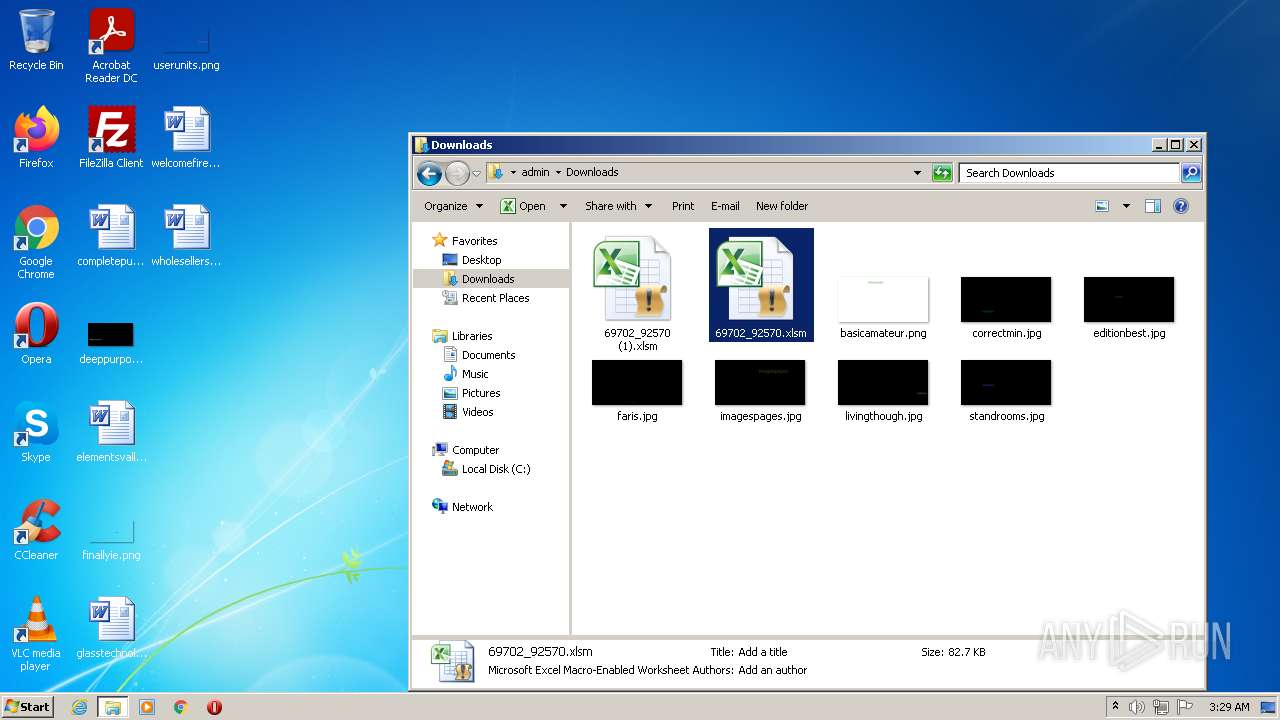
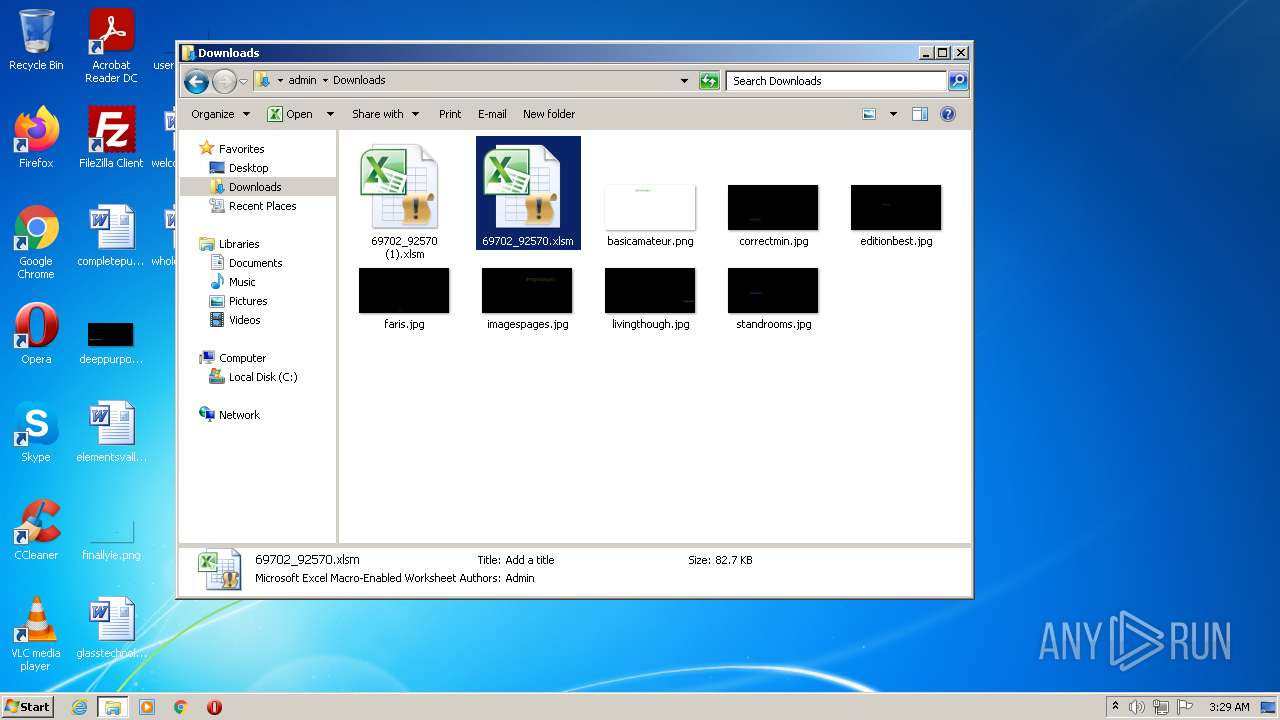
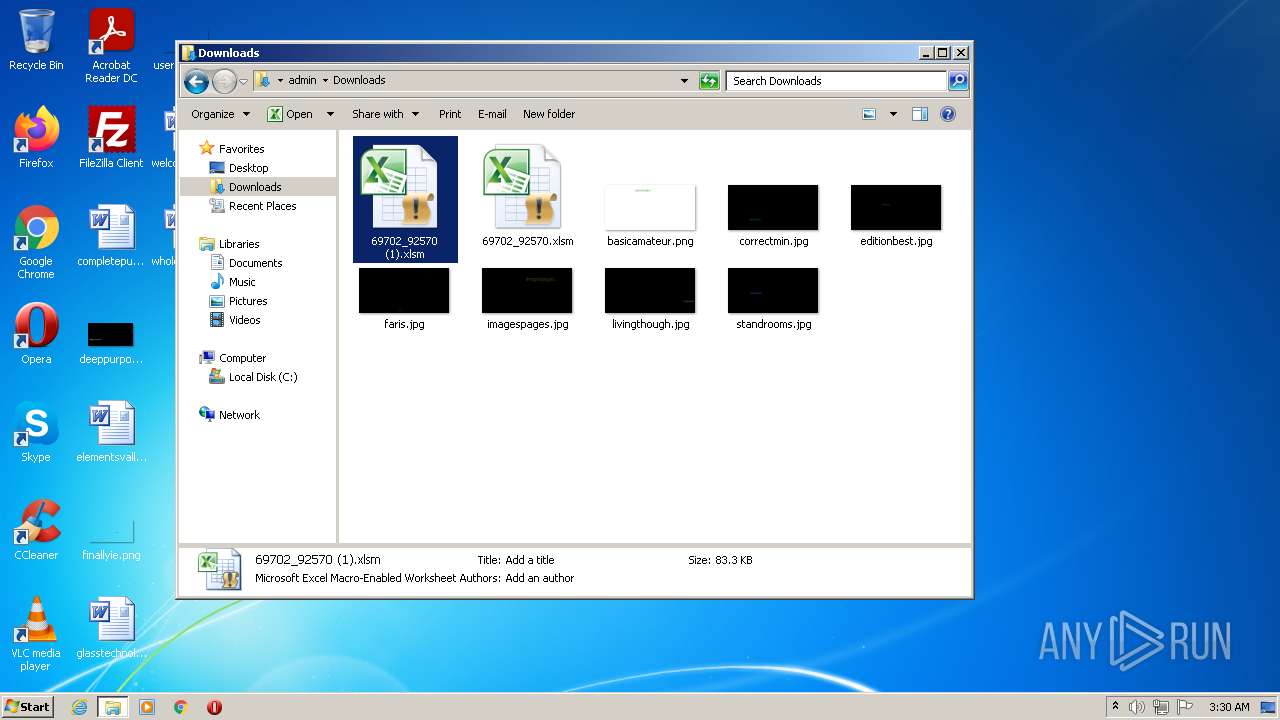
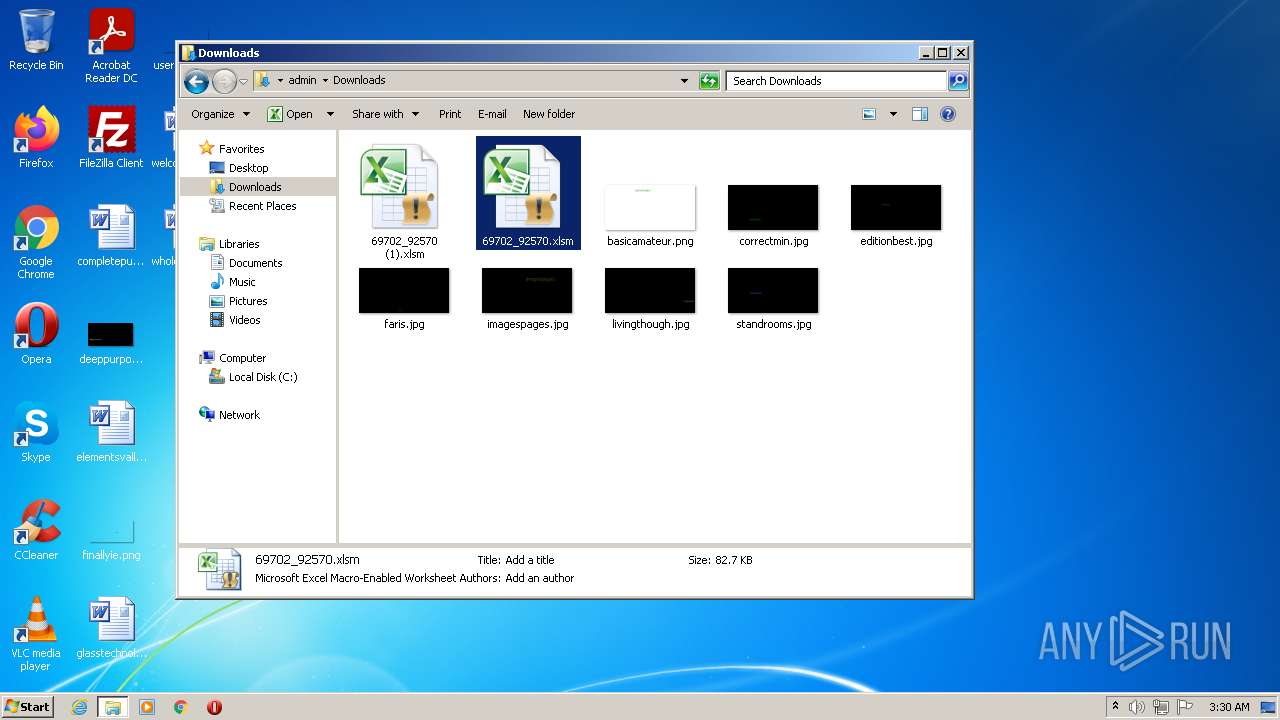
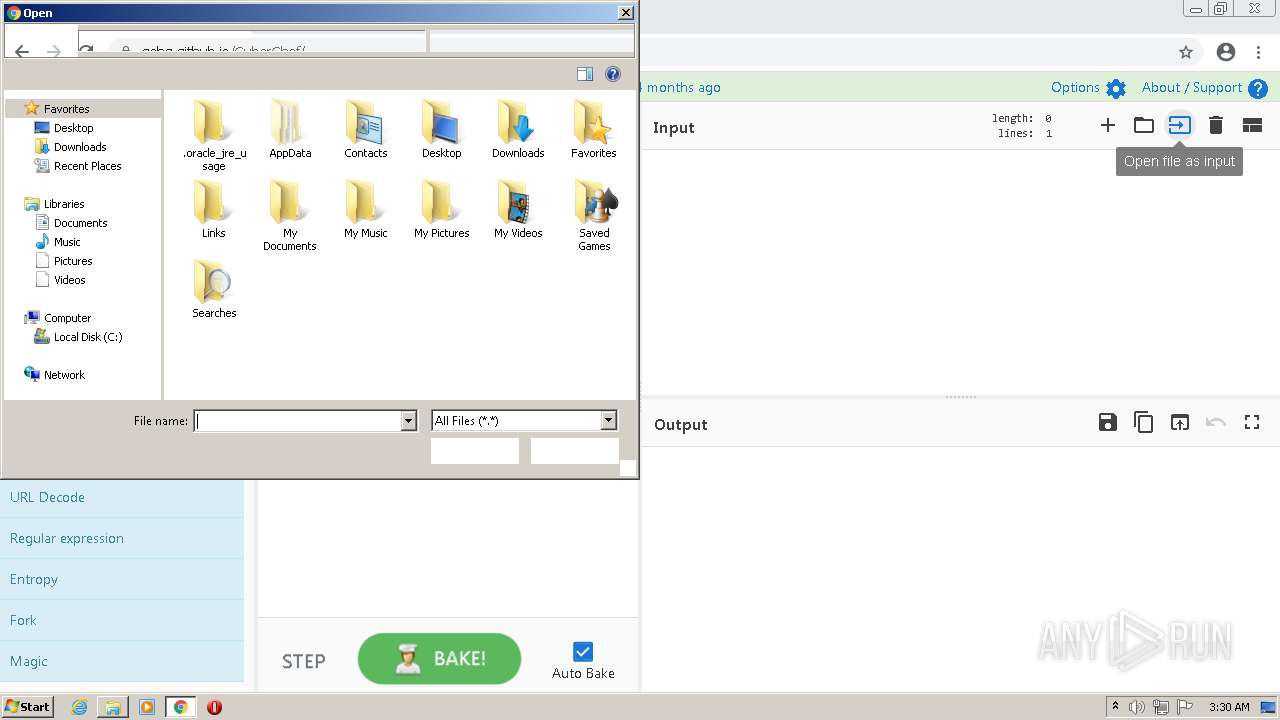
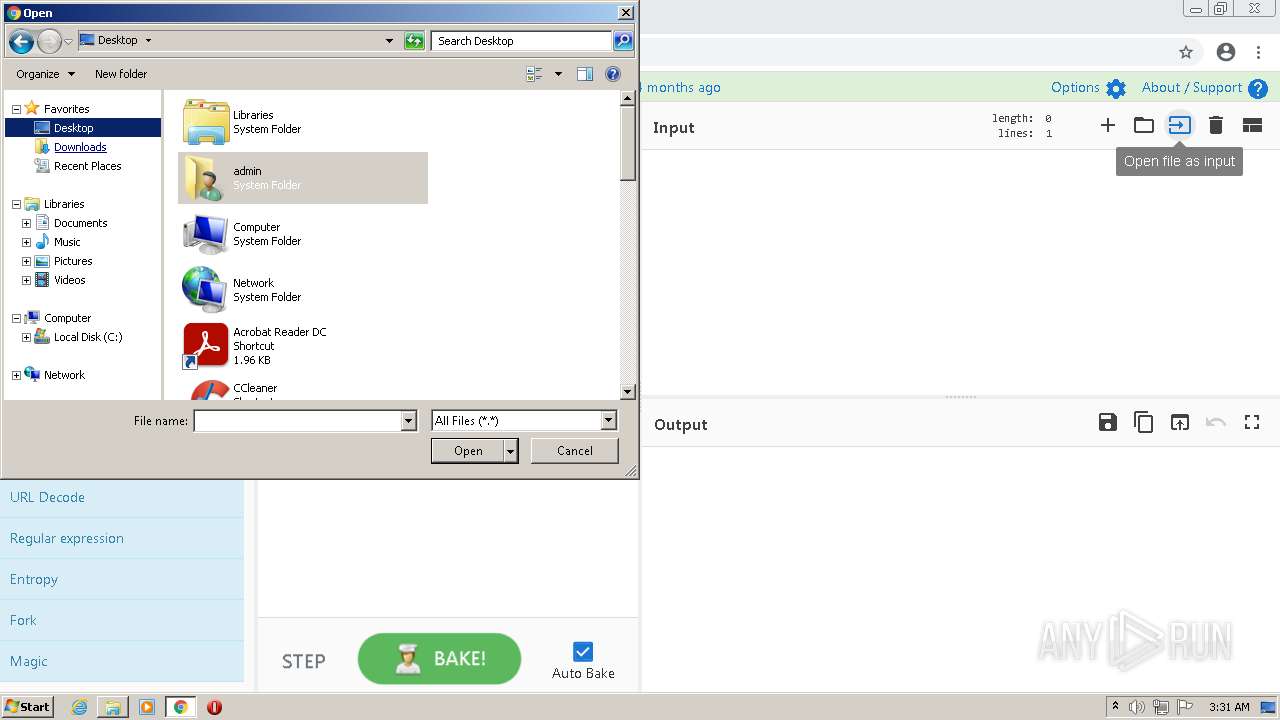
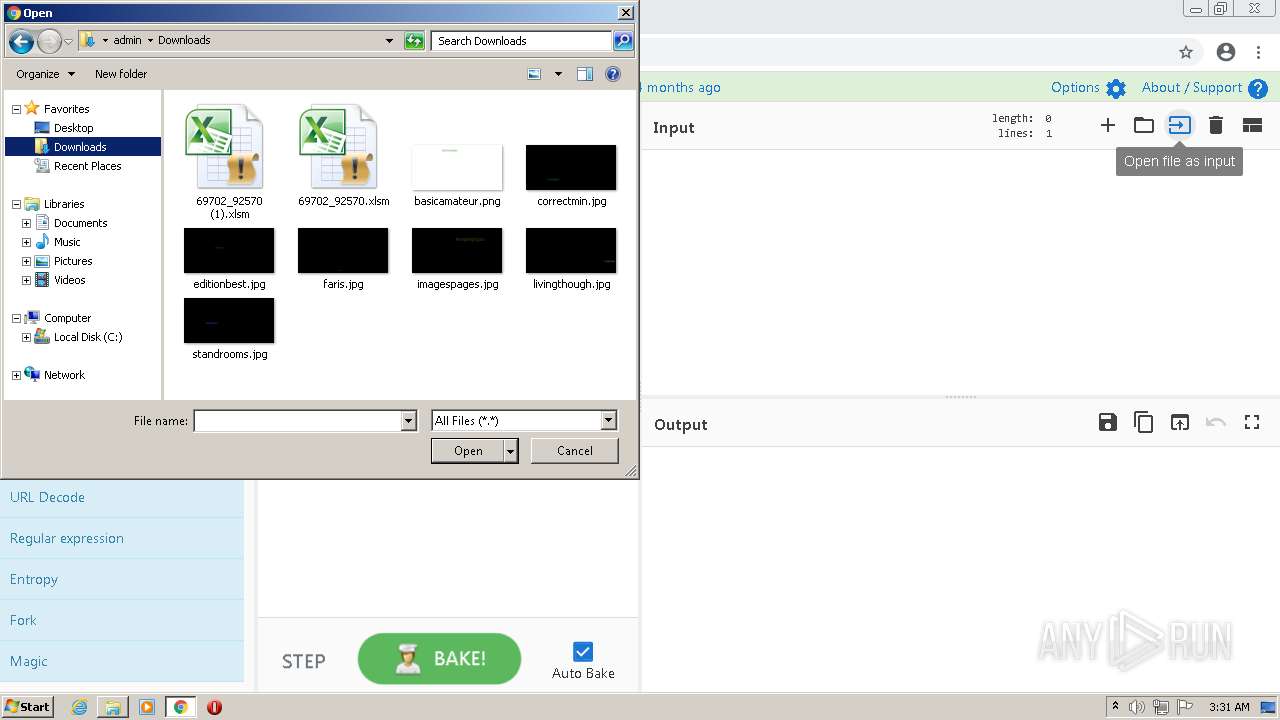
Manual execution by user
- explorer.exe (PID: 2532)
- EXCEL.EXE (PID: 3500)
- EXCEL.EXE (PID: 3992)
- chrome.exe (PID: 1076)
Creates files in the user directory
- EXCEL.EXE (PID: 1648)
- EXCEL.EXE (PID: 3500)
- EXCEL.EXE (PID: 3992)
- WINWORD.EXE (PID: 3844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
62
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1024,8126062584457211974,14228918914290004490,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3492 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 684 | C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Local\Rfauchgynabbpc\ogltsxvun.wgg",blWpfSPOLTZ | C:\Windows\system32\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e7ed988,0x6e7ed998,0x6e7ed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,8126062584457211974,14228918914290004490,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1512 | C:\Windows\SysWow64\rundll32.exe ..\erum.ocx,D"&"l"&"lR"&"egister"&"Serve"&"r | C:\Windows\SysWow64\rundll32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1024,8126062584457211974,14228918914290004490,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
75 381
Read events
64 076
Write events
10 948
Delete events
357
Modification events
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
6
Suspicious files
217
Text files
249
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E23EFA-89C.pma | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\aa142227-b1b1-4ad5-8018-29e6c7916af7.tmp | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF112e60.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF112d27.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF112d37.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF112e21.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
66
DNS requests
44
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 74.125.105.106:80 | http://r5---sn-aigl6nsk.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigl6nsk&ms=nvh&mt=1642217060&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigl6nsk.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6n76.gvt1.com | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.105.106:80 | http://r5---sn-aigl6nsk.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigl6nsk&ms=nvh&mt=1642216830&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigl6nsk.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6n76.gvt1.com | US | binary | 5.63 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.105.106:80 | http://r5---sn-aigl6nsk.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigl6nsk&ms=nvh&mt=1642216830&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigl6nsk.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6n76.gvt1.com | US | binary | 9.45 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.105.106:80 | http://r5---sn-aigl6nsk.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigl6nsk&ms=nvh&mt=1642216830&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigl6nsk.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6n76.gvt1.com | US | binary | 9.44 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.105.106:80 | http://r5---sn-aigl6nsk.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigl6nsk&ms=nvh&mt=1642216830&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigl6nsk.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6n76.gvt1.com | US | binary | 9.44 Kb | whitelisted |
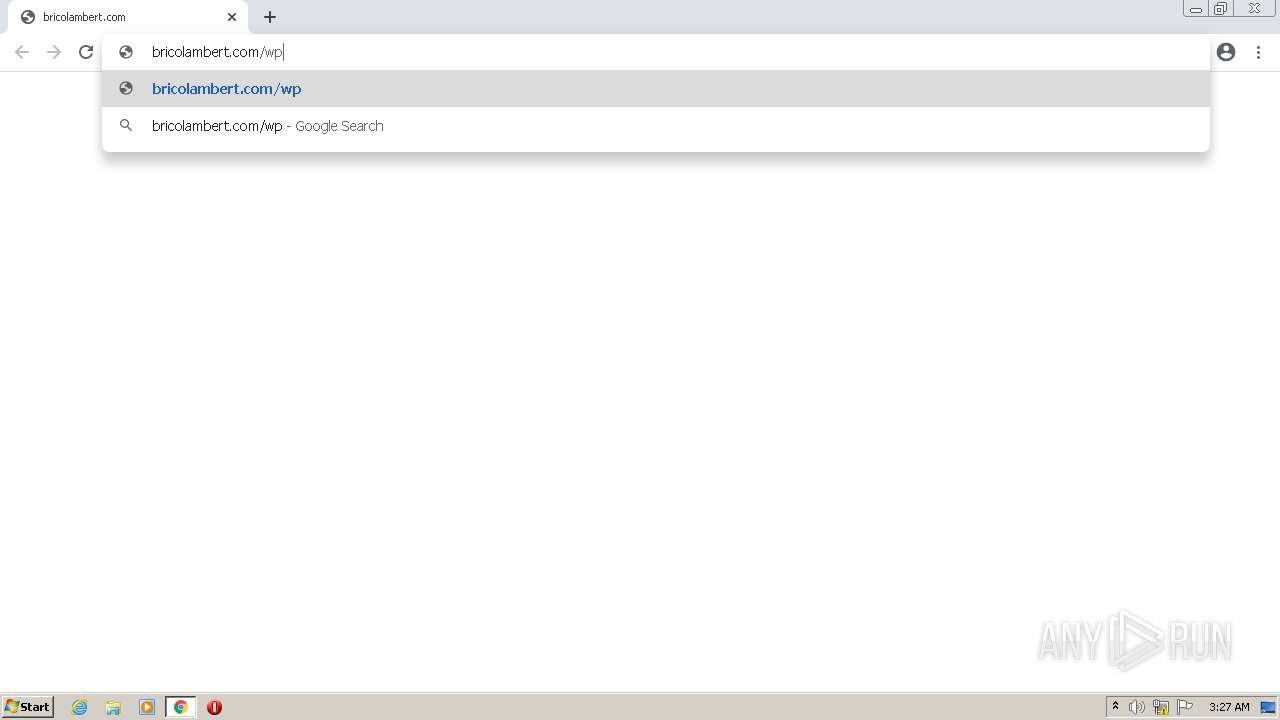
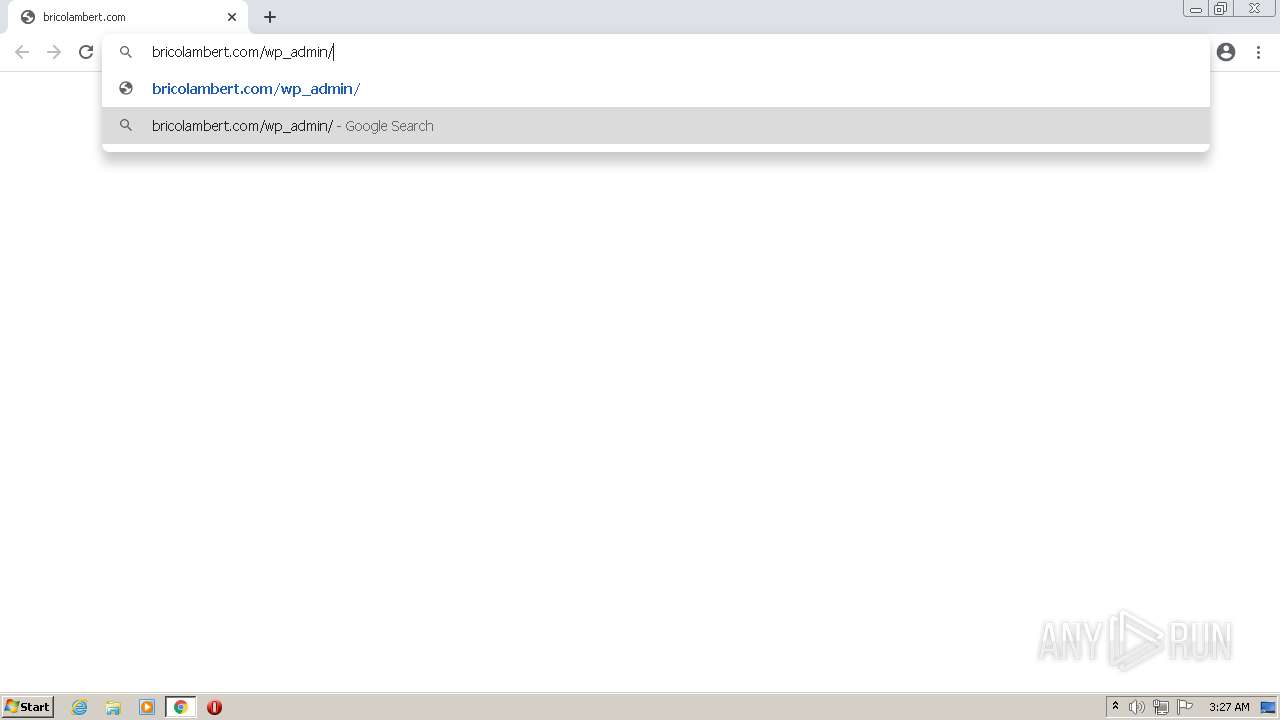
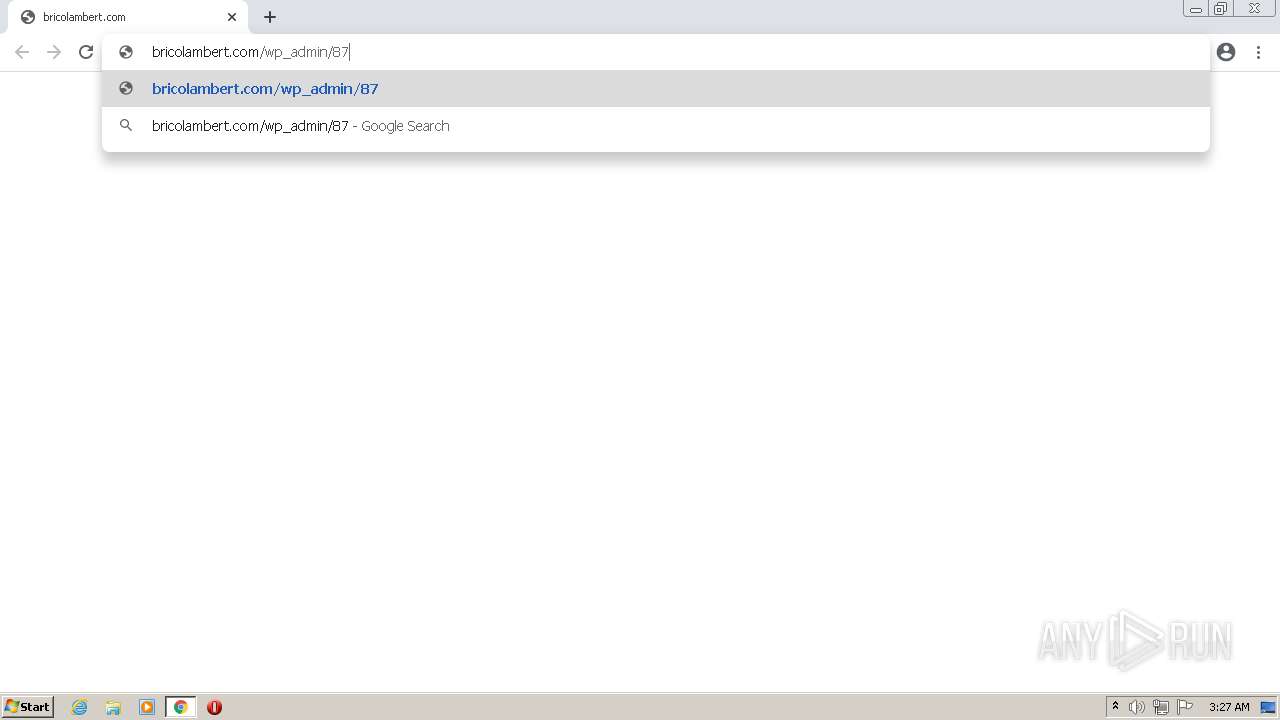
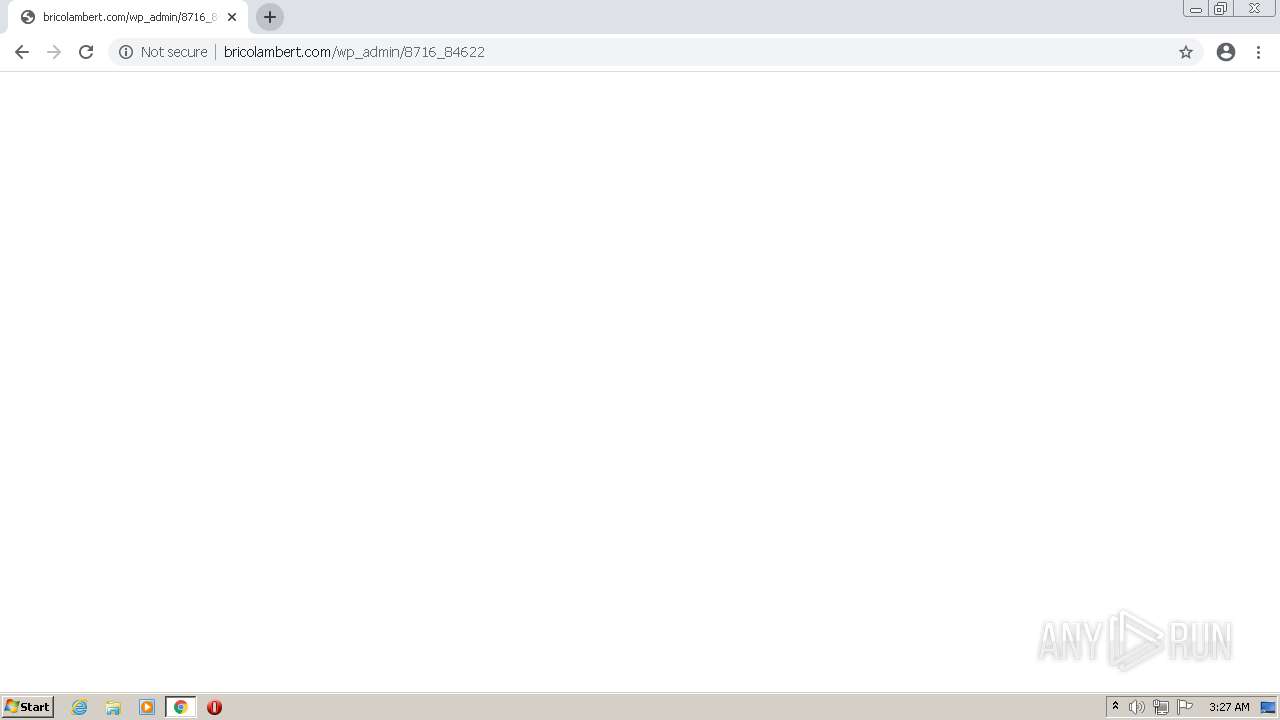
4020 | chrome.exe | GET | 200 | 217.160.0.236:80 | http://bricolambert.com/wp-admin/8716_84622/ | DE | html | 45.9 Kb | malicious |
860 | svchost.exe | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
4020 | chrome.exe | GET | 301 | 217.160.0.236:80 | http://bricolambert.com/wp-admin/8716_84622 | DE | html | 252 b | malicious |
860 | svchost.exe | GET | 302 | 142.250.184.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1648 | EXCEL.EXE | 157.7.107.100:80 | recont.com | GMO Internet,Inc | JP | suspicious |
860 | svchost.exe | 173.194.5.231:80 | r2---sn-aigzrn7l.gvt1.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 217.160.0.236:80 | bricolambert.com | 1&1 Internet SE | DE | malicious |
4020 | chrome.exe | 142.250.184.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 142.250.185.68:443 | www.google.com | Google Inc. | US | whitelisted |
860 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
860 | svchost.exe | 142.250.184.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
860 | svchost.exe | 74.125.105.106:80 | r5---sn-aigl6nsk.gvt1.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 142.250.186.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
4020 | chrome.exe | 142.250.181.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
bricolambert.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-aigl6nsk.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4020 | chrome.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet HTML Template Response |
1648 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1648 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
1648 | EXCEL.EXE | Misc activity | ET INFO EXE - Served Attached HTTP |
2740 | rundll32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
2740 | rundll32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
3992 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3992 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3992 | EXCEL.EXE | Misc activity | ET INFO EXE - Served Attached HTTP |
4 ETPRO signatures available at the full report