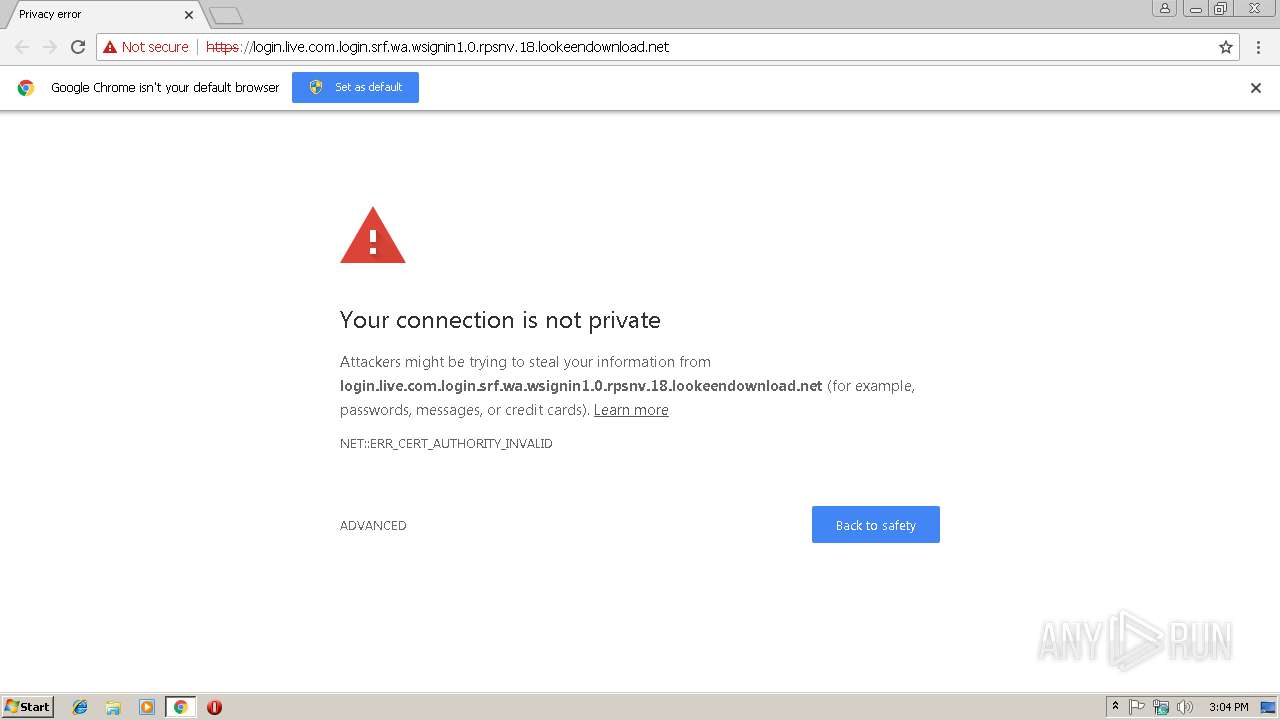
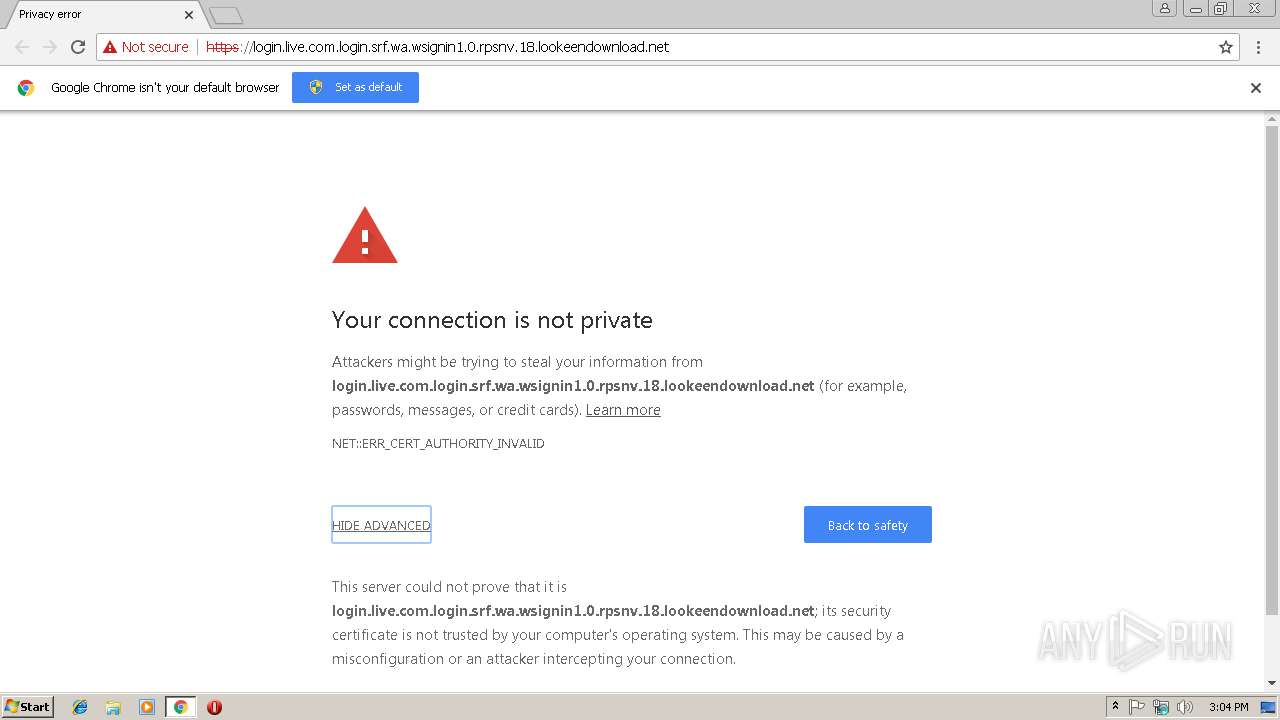
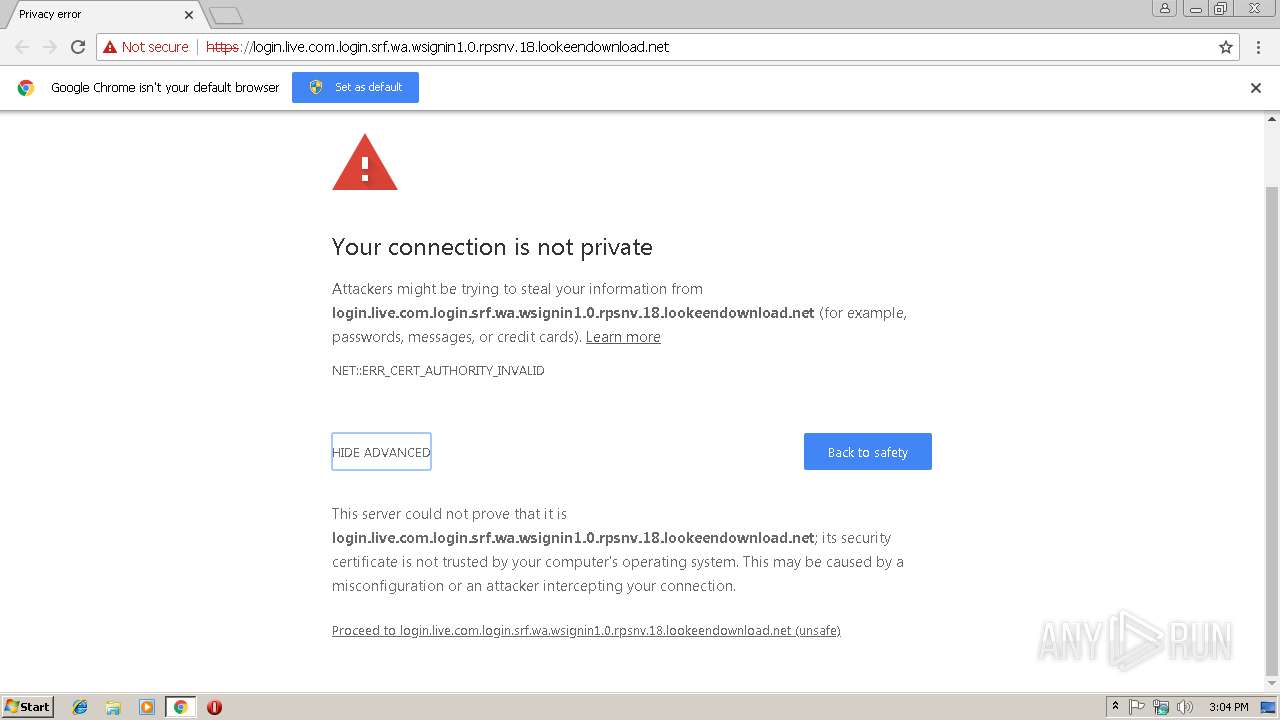
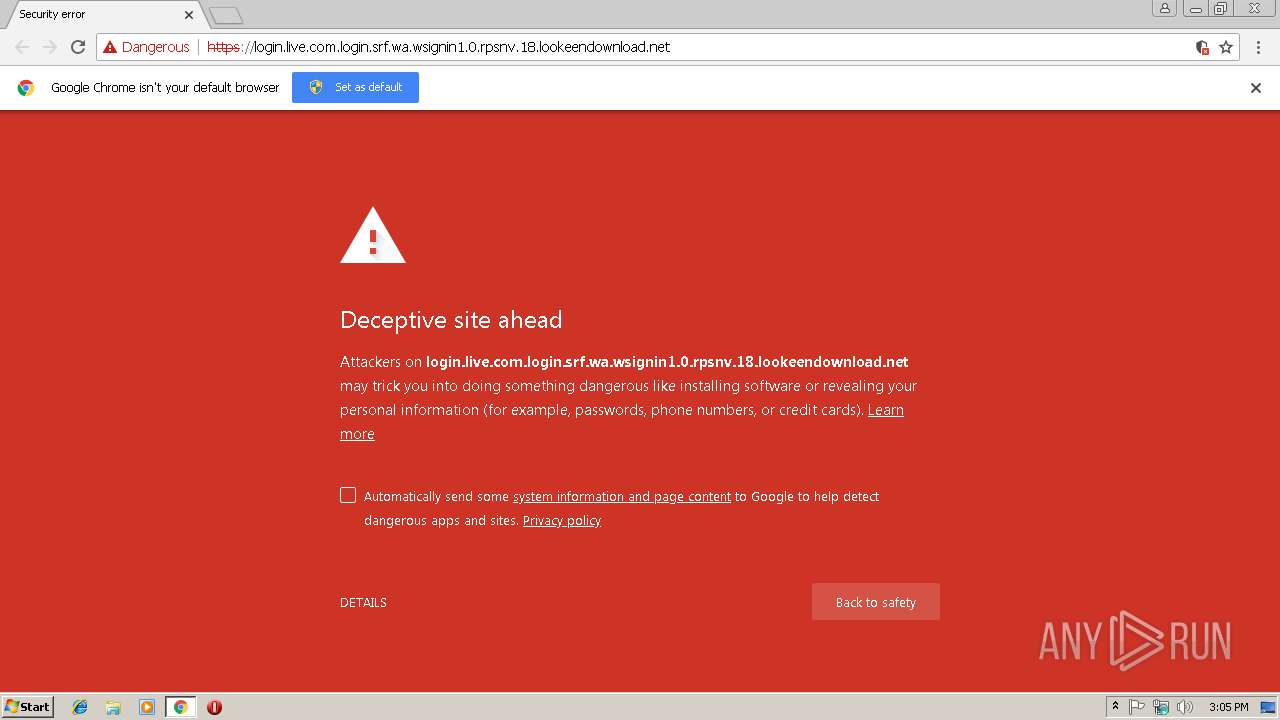
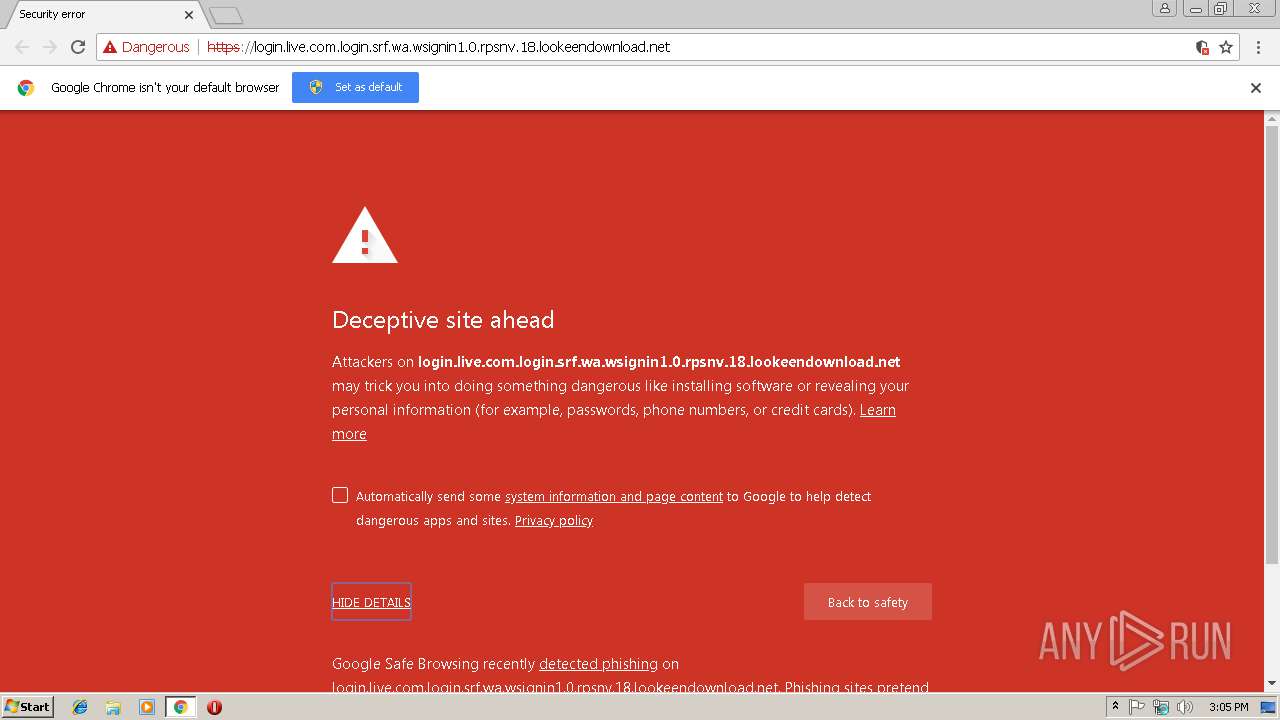
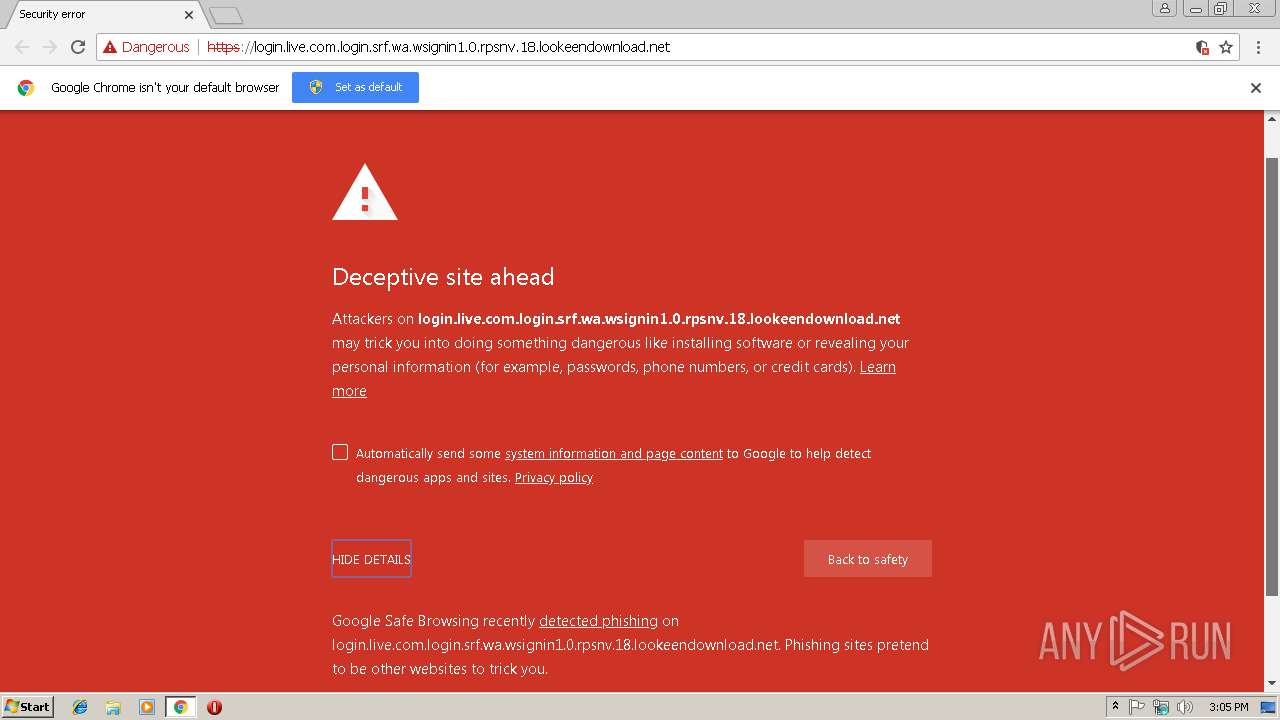
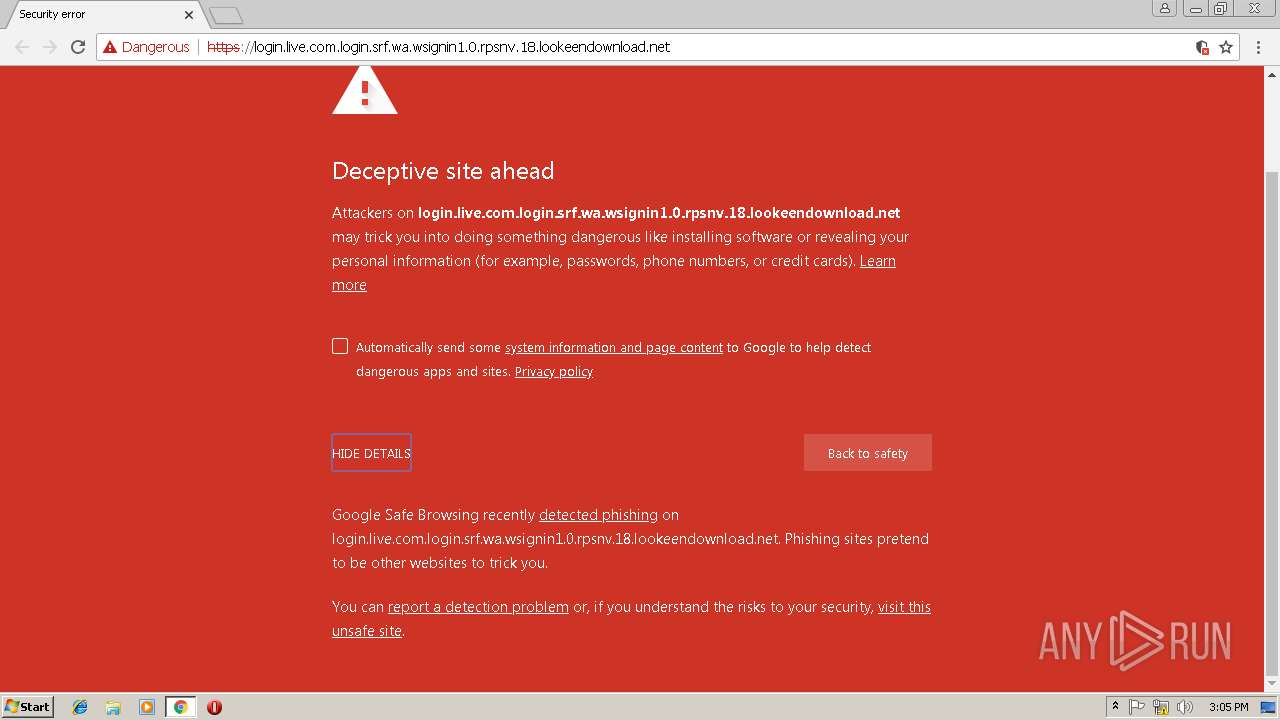
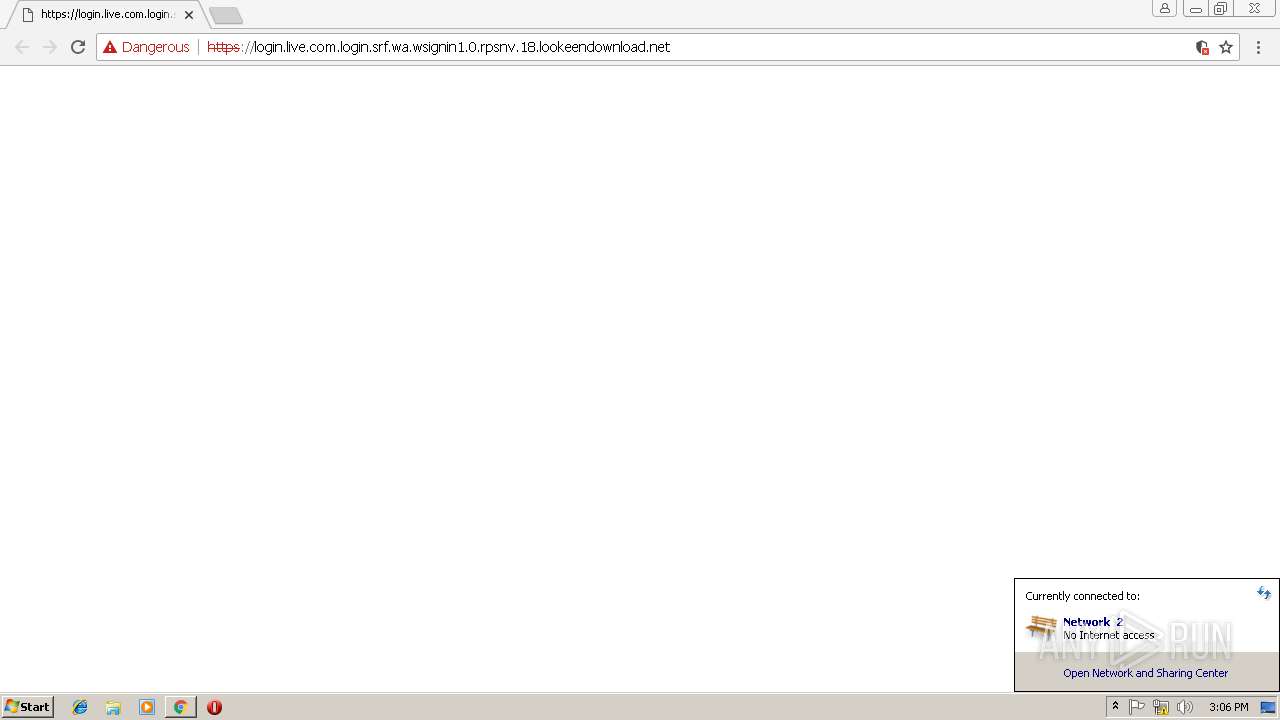
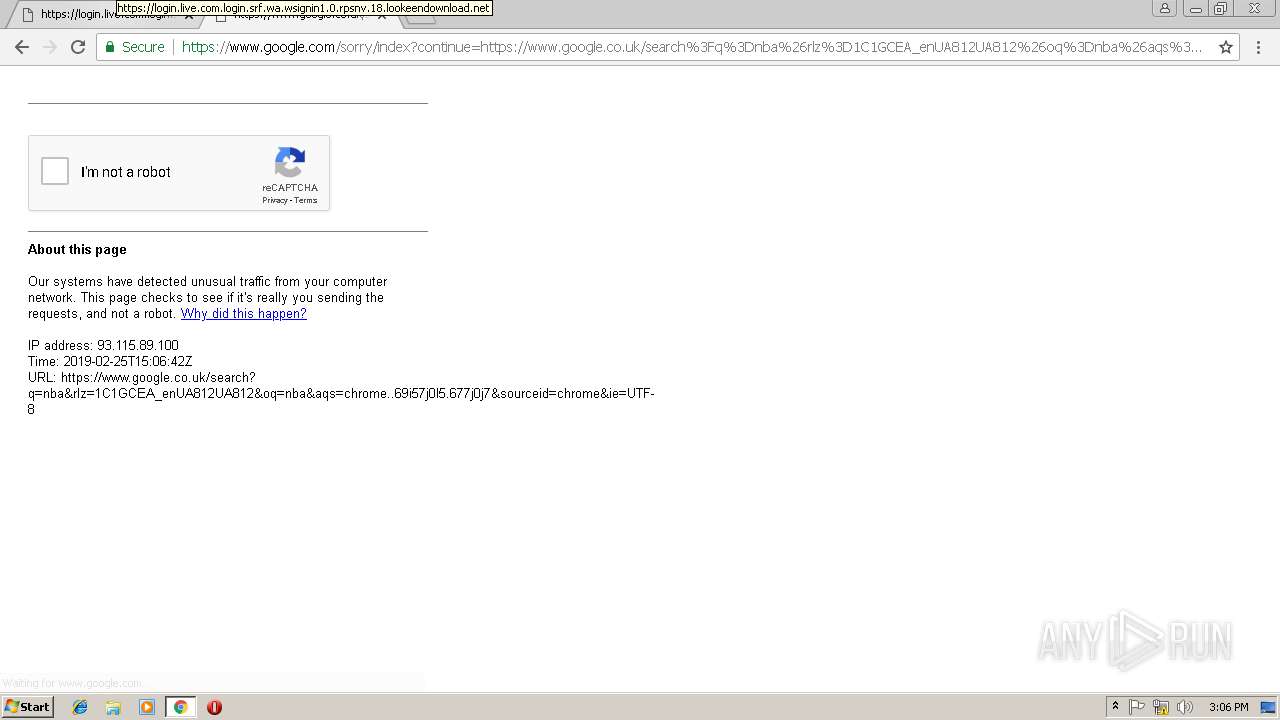
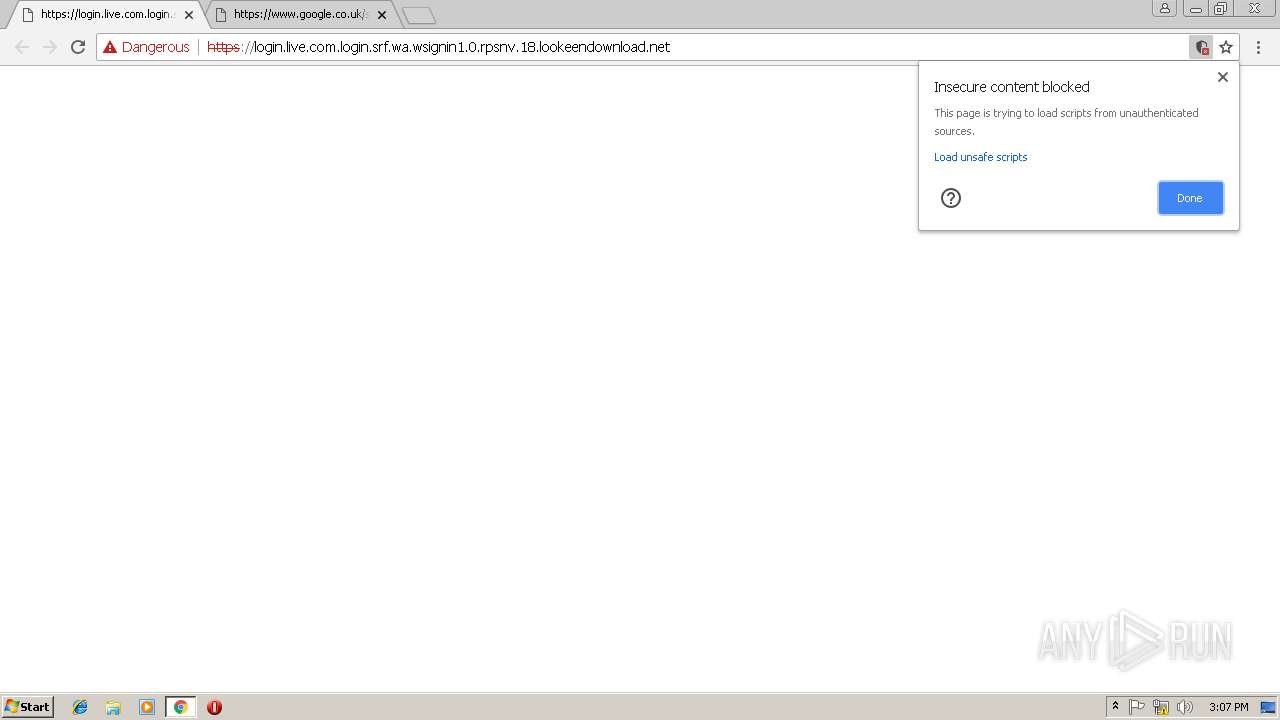
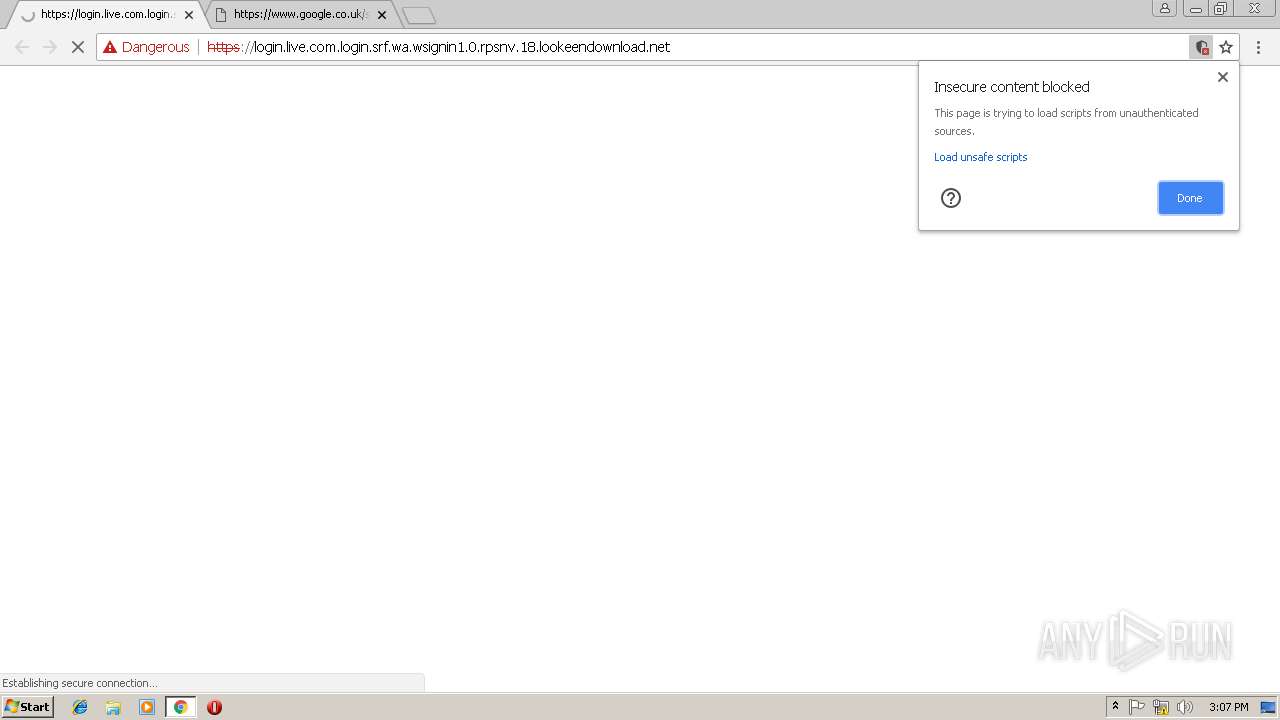
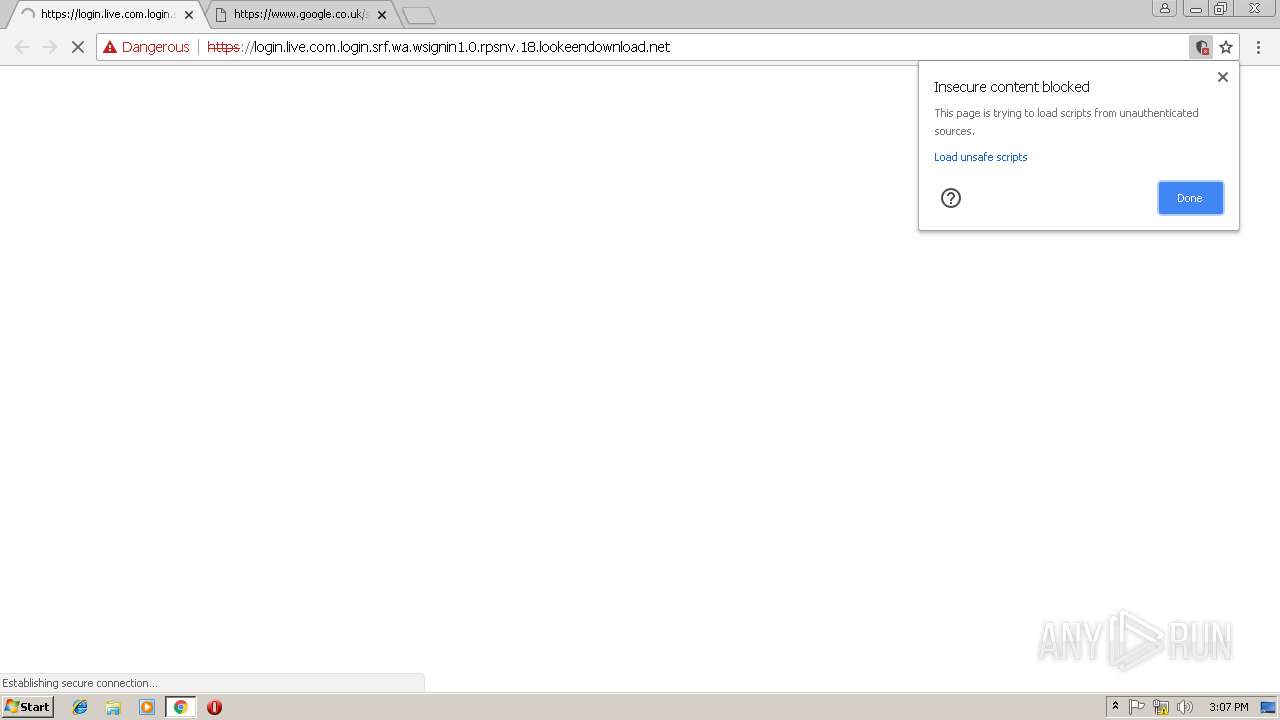
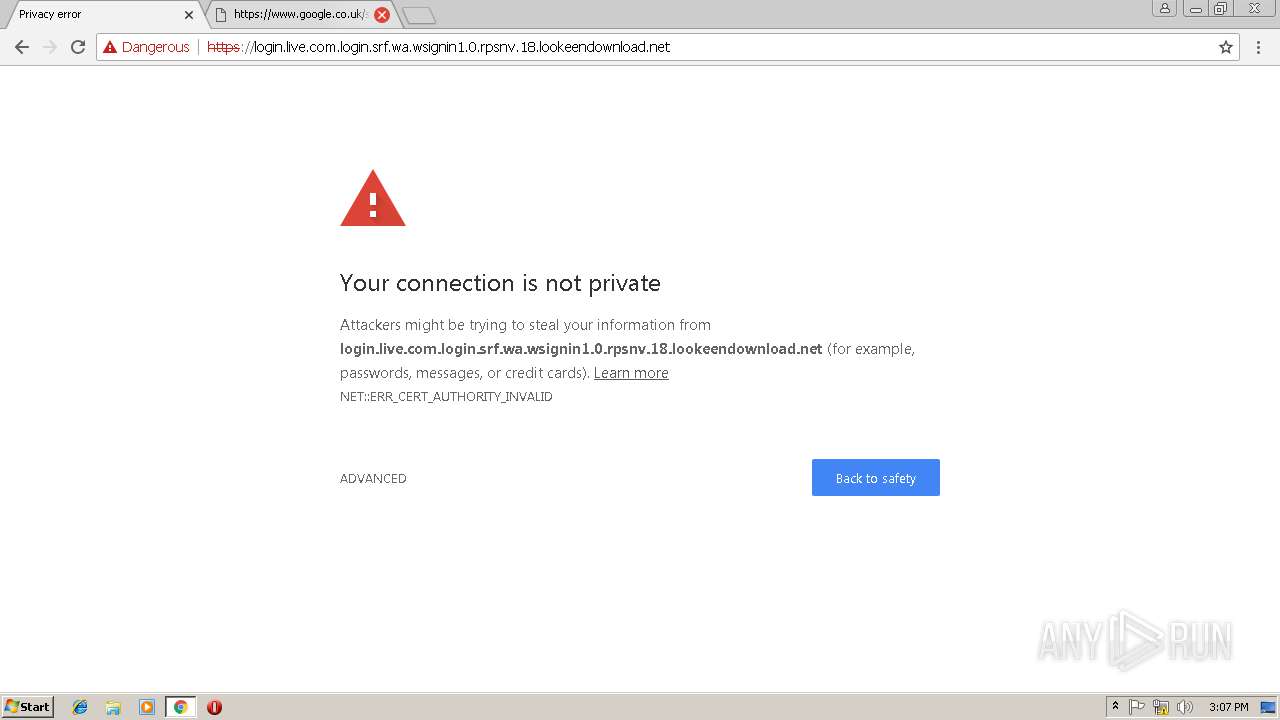
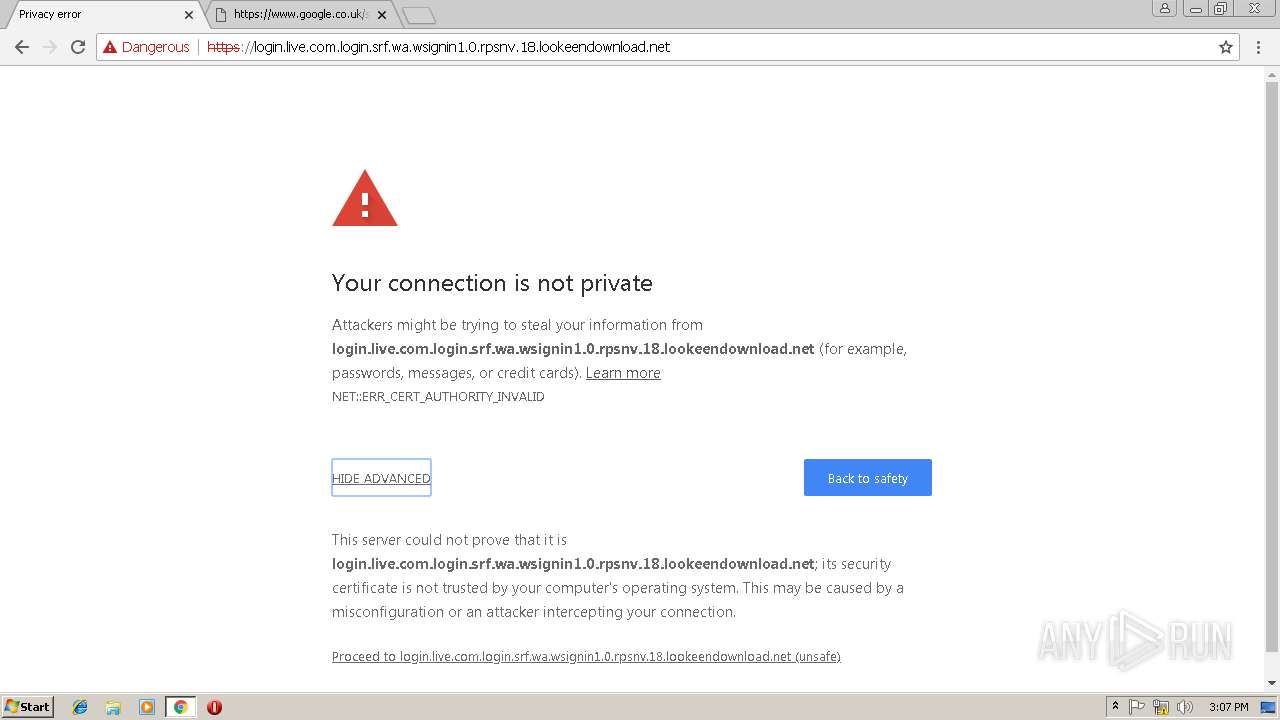
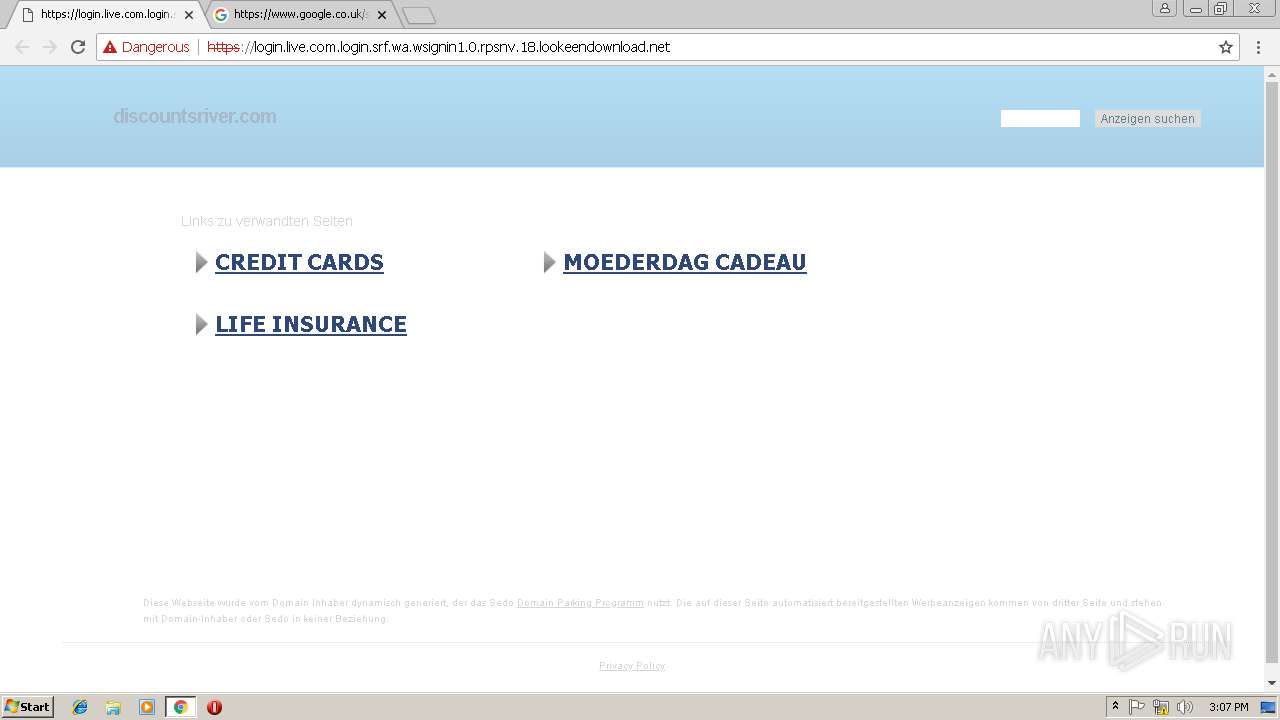
| URL: | https://login.live.com.login.srf.wa.wsignin1.0.rpsnv.18.lookeendownload.net |
| Full analysis: | https://app.any.run/tasks/163a9dd0-acec-4a6a-a2c8-4586f583347e |
| Verdict: | No threats detected |
| Analysis date: | February 25, 2019, 15:04:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F51A597EA3EE9271503C383620C3AE9B |
| SHA1: | F74E5A1A3D845C5C4F35187DA1783769982EE773 |
| SHA256: | AF1A825D3252AFFF69903D589EF30798E348133FE5B7C4B5297E8FE3F9179F9A |
| SSDEEP: | 3:N8KP6BM/Q6CGGYLEoKtK0Rn:2KPYM/9NxxKtKo |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6C3818E4C20E26A2334973E780919ED7 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6C3818E4C20E26A2334973E780919ED7 --renderer-client-id=14 --mojo-platform-channel-handle=4032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C07459F841FA612FB6FDADBA13006A13 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C07459F841FA612FB6FDADBA13006A13 --renderer-client-id=11 --mojo-platform-channel-handle=3124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=FC9D74C754E1F982CAEABAE0CB640C7C --mojo-platform-channel-handle=3076 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=79B45216AE97A5F5A97B725AD575E778 --mojo-platform-channel-handle=916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=40925AAA7E8472C3EC6A0EBF12A74306 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=40925AAA7E8472C3EC6A0EBF12A74306 --renderer-client-id=16 --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --renderer-client-id=4 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=A7420CE55A93B29AE445B4B5B3F29BAA --mojo-platform-channel-handle=3640 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=FE59E9E87EB0FC9A59B9EB20A5FF93B8 --mojo-platform-channel-handle=3864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=8FC767577AF1E7C24CB24E9688133455 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8FC767577AF1E7C24CB24E9688133455 --renderer-client-id=3 --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
547
Read events
474
Write events
69
Delete events
4
Modification events
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2988-13195580681370875 |
Value: 259 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2988-13195580681370875 |
Value: 259 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
47
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b6d89c3f-64e3-4100-a6fe-82248c9983ef.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\95d90732-8f29-42a4-9d86-3c39e0c33022.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF199495.TMP | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
49
DNS requests
26
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | chrome.exe | GET | 204 | 172.217.21.227:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2988 | chrome.exe | GET | 204 | 172.217.21.227:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
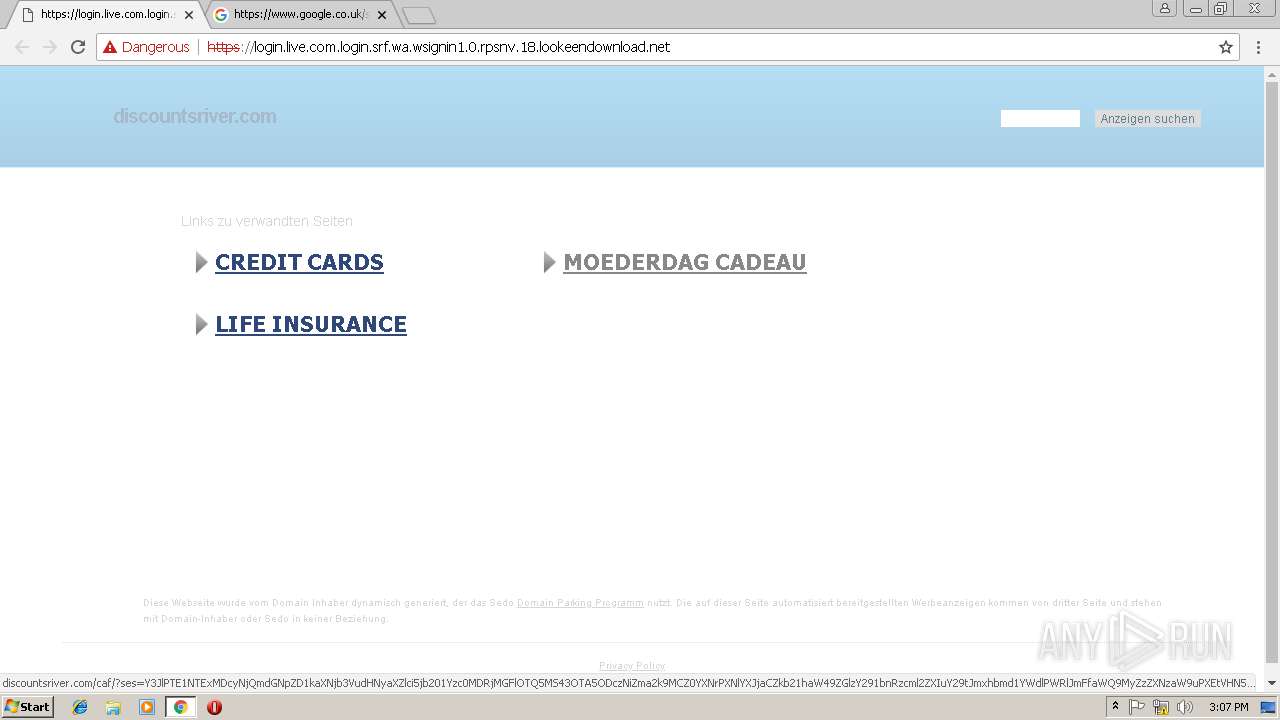
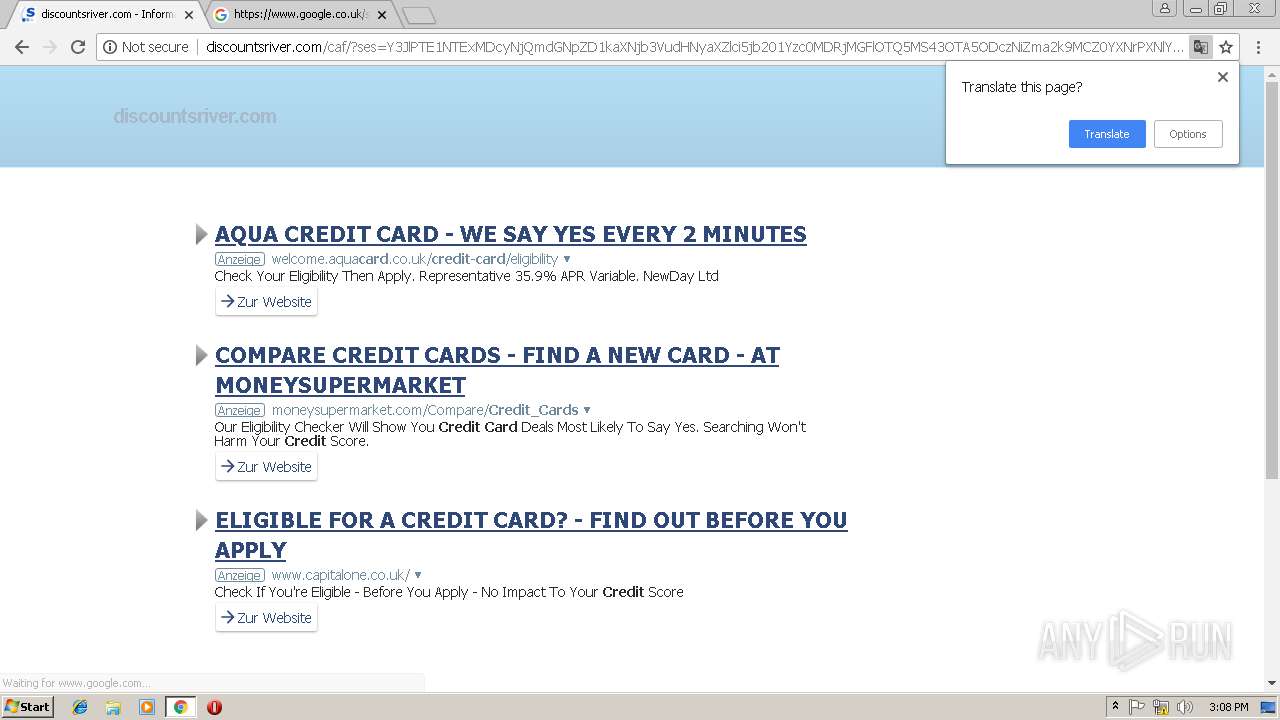
2988 | chrome.exe | GET | 302 | 23.253.22.100:80 | http://friend-deals.xyz/?Z289MSZzMT0zNzI2NDYmczI9MCZzMz1GUg== | US | — | — | suspicious |
2988 | chrome.exe | GET | 302 | 91.215.100.40:80 | http://de.ioam.de/tx.io?st=sedo&cp=322&sv=in&pt=CP&ps=lin&er=N22&rf=&r2=&ur=discountsriver.com&xy=1280x720x24&lo=DE%2FBayern&cb=000a&i2=000abacfe6b4e8ead5c7404c0&ep=1572215760&vr=412&id=1q0p57&i3=nocookie&n1=1&dntt=0<=1551107264243&ev=&cs=dhguzf&mo=1 | DE | — | — | whitelisted |
2988 | chrome.exe | GET | 200 | 91.195.240.94:80 | http://discountsriver.com/search/tsc.php?200=MzIxMDE2NzE3&21=OTMuMTE1Ljg5LjEwMA==&681=MTU1MTEwNzI2NDQ0MzA0MDY2ZTlmMGExOGRlZDFlZTFiMDBlNDViYTgz&crc=13edca86dc918bd56594c5b5f1be6aea891f7edf&cv=1 | DE | — | — | malicious |
2988 | chrome.exe | GET | 200 | 91.215.100.40:80 | http://de.ioam.de/tx.io?st=sedo&cp=322&sv=in&pt=CP&ps=lin&er=N22&rf=www.google.com&r2=https%3A%2F%2Fwww.google.com%2F&ur=discountsriver.com&xy=1280x720x24&lo=DE%2FBayern&cb=000a&i2=000abacfe6b4e8ead5c7404c0&ep=1572215760&vr=412&id=1q0p57&i3=nocookie&n1=1&dntt=0<=1551107296696&ev=&cs=5fm32g&mo=1 | DE | — | — | whitelisted |
2988 | chrome.exe | GET | 200 | 91.195.240.94:80 | http://discountsriver.com/ | DE | html | 19.5 Kb | malicious |
2988 | chrome.exe | GET | 200 | 193.46.63.75:80 | http://irqs.ioam.de/identitystatus?offerIdentifier=sedo&siteIdentifier=322&sampleType=in&pixelType=CP&isFadeoutFlash=true&isFadeoutFrame=true&isFadeoutForm=true&positionTop=10&positionLeft=100&zIndex=1100000&c=0.38992393215531096 | DE | text | 25 b | whitelisted |
2988 | chrome.exe | GET | 200 | 91.195.240.94:80 | http://discountsriver.com/search/tsc.php?200=MzIxMDE2NzE3&21=OTMuMTE1Ljg5LjEwMA==&681=MTU1MTEwNzI5N2NiNjNkZjNmYjljNWM0YzA5ZDE2MWVjZGM4ZjIzYzIw&crc=b33f5b9514c3a3d2f688e3c5b995ca421e95f601&cv=1 | DE | compressed | 19.5 Kb | malicious |
2988 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/js/jquery-1.11.3.custom.min.js | US | text | 24.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 23.253.22.100:443 | login.live.com.login.srf.wa.wsignin1.0.rpsnv.18.lookeendownload.net | Rackspace Ltd. | US | suspicious |
2988 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.21.227:80 | www.gstatic.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.21.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.18.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com.login.srf.wa.wsignin1.0.rpsnv.18.lookeendownload.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2988 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Self Signed SSL Certificate (SomeOrganizationalUnit) |
2988 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Self Signed SSL Certificate (SomeOrganizationalUnit) |
2988 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Self Signed SSL Certificate (SomeOrganizationalUnit) |