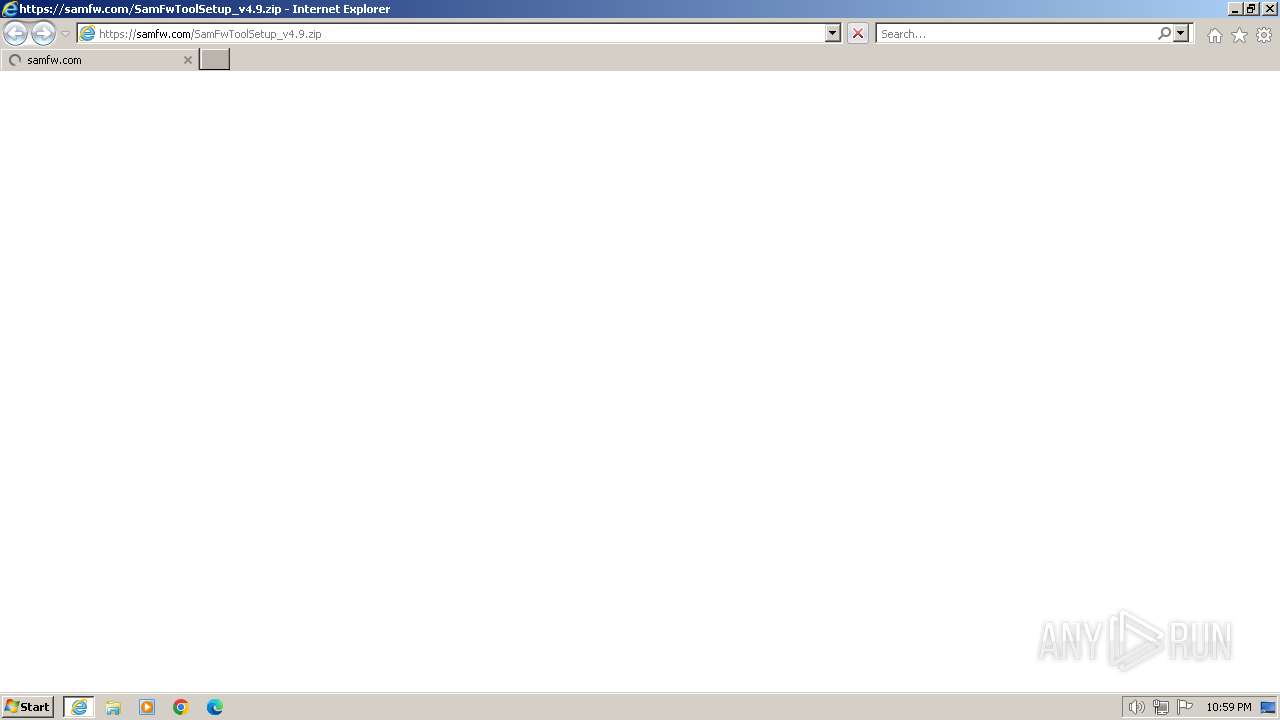
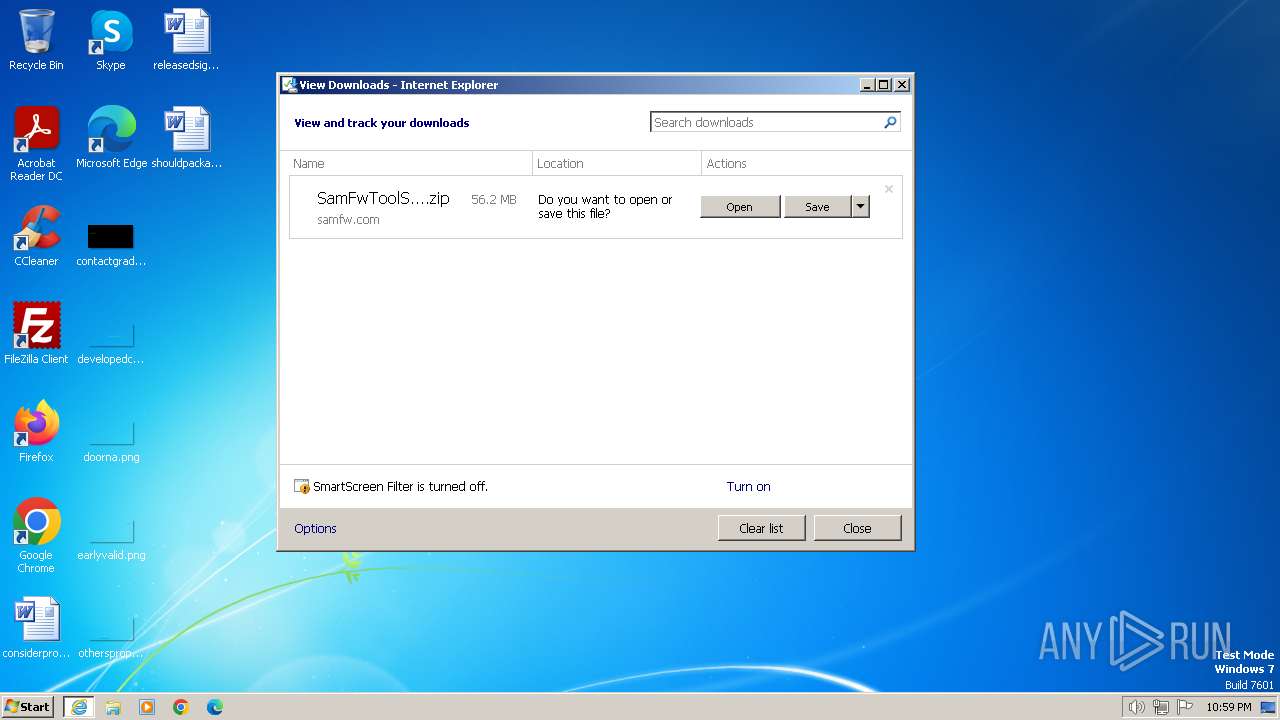
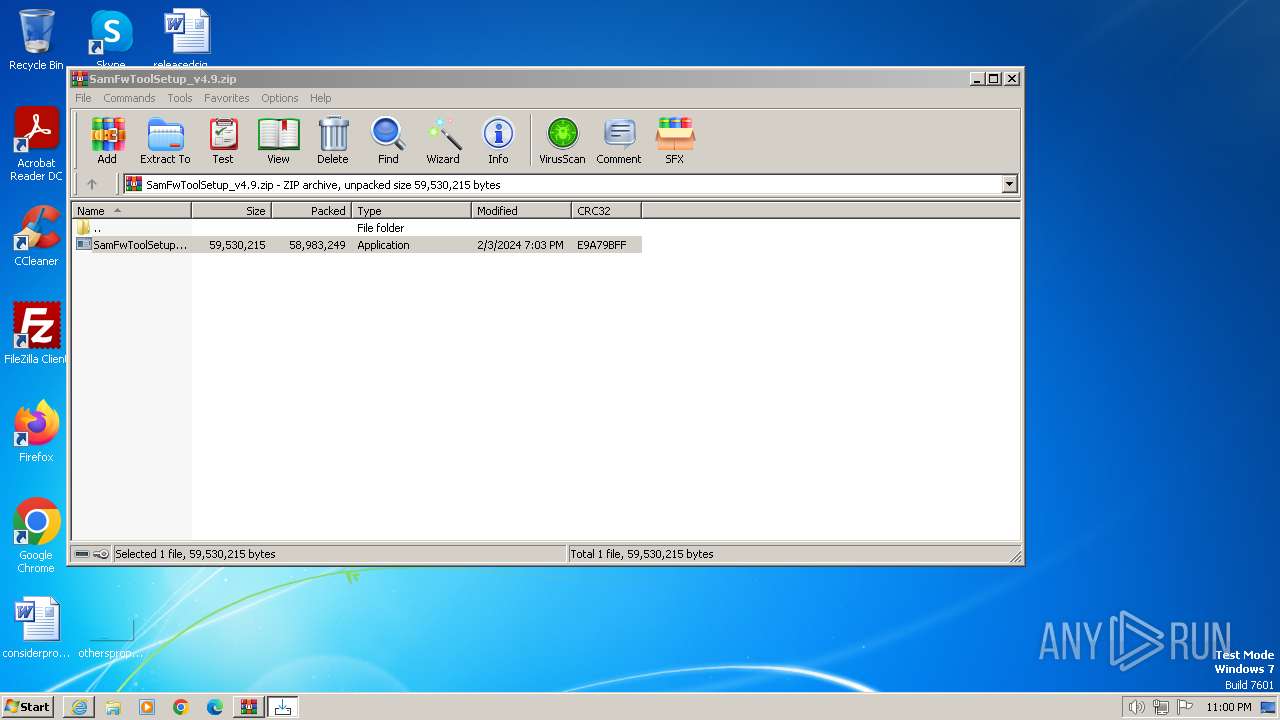
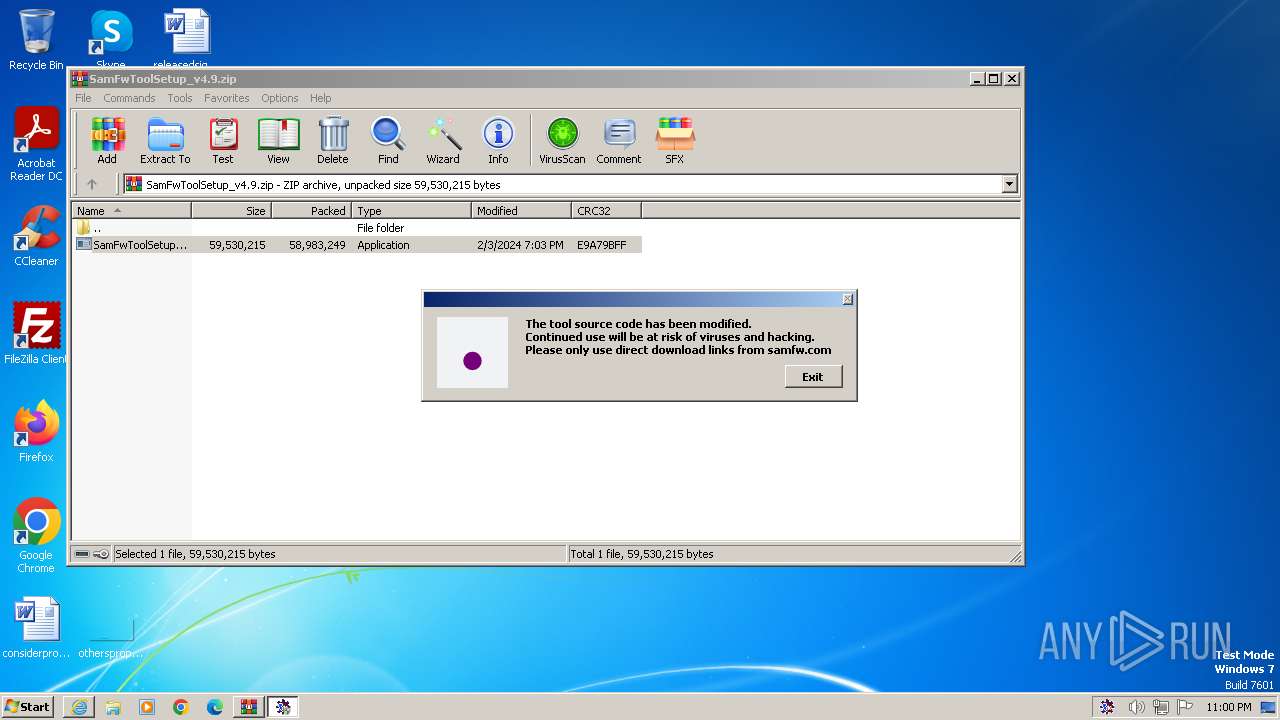
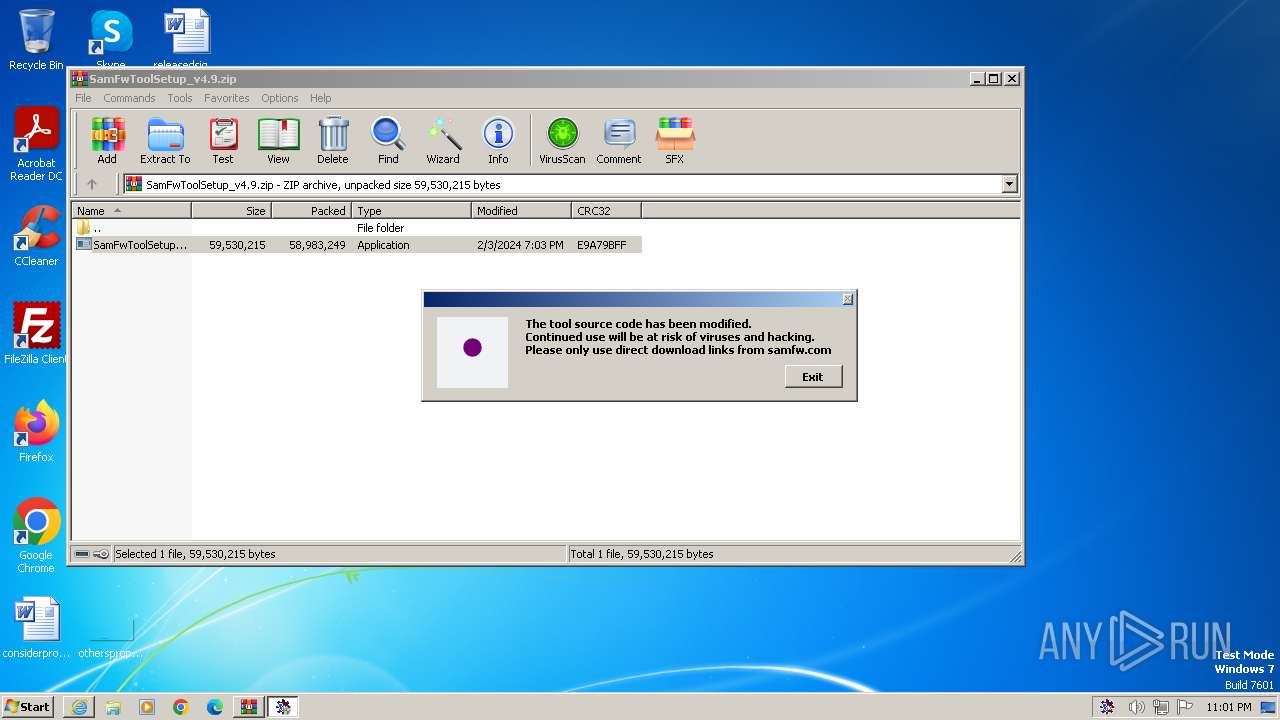
| URL: | https://samfw.com/SamFwToolSetup_v4.9.zip |
| Full analysis: | https://app.any.run/tasks/974b7a07-190a-4e1b-bd61-1db360a47692 |
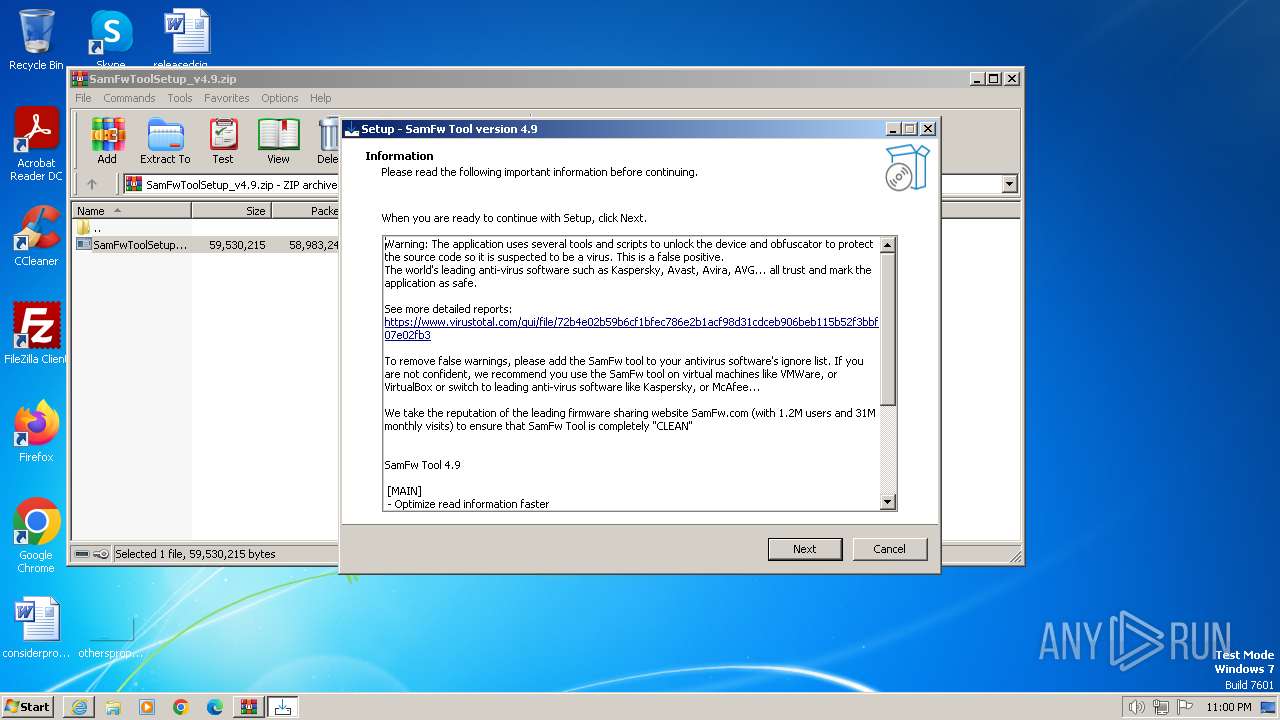
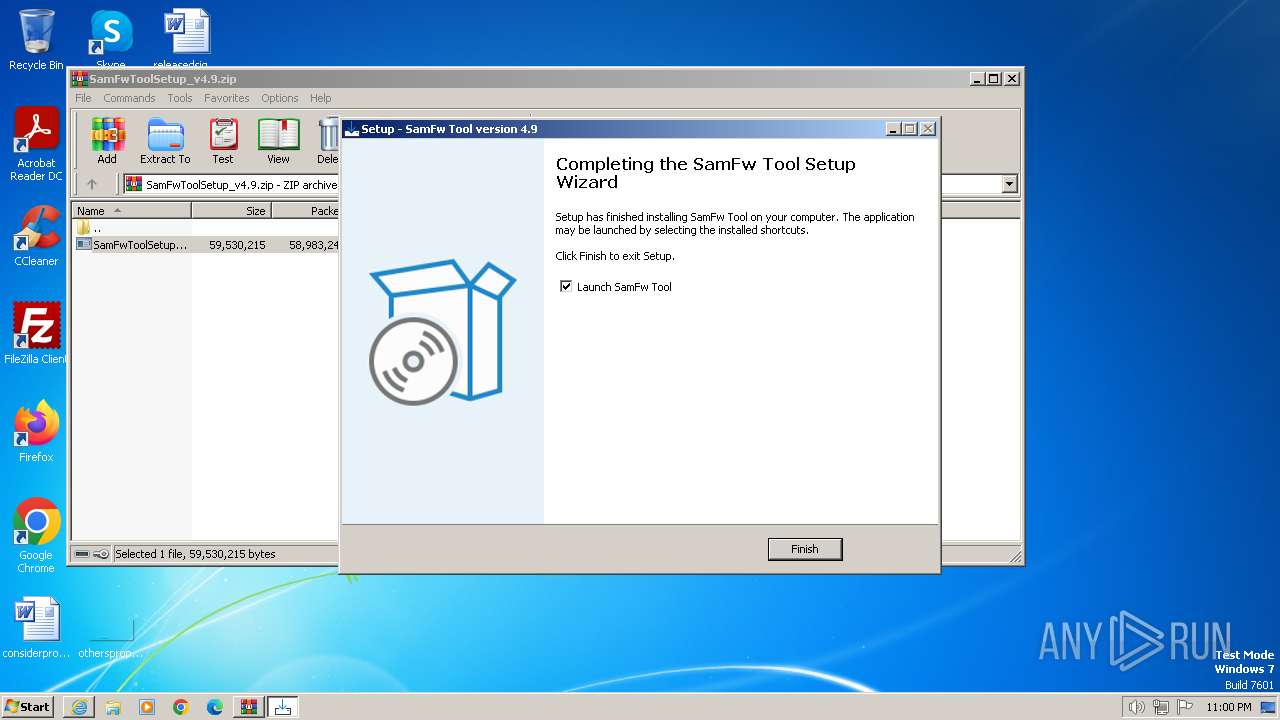
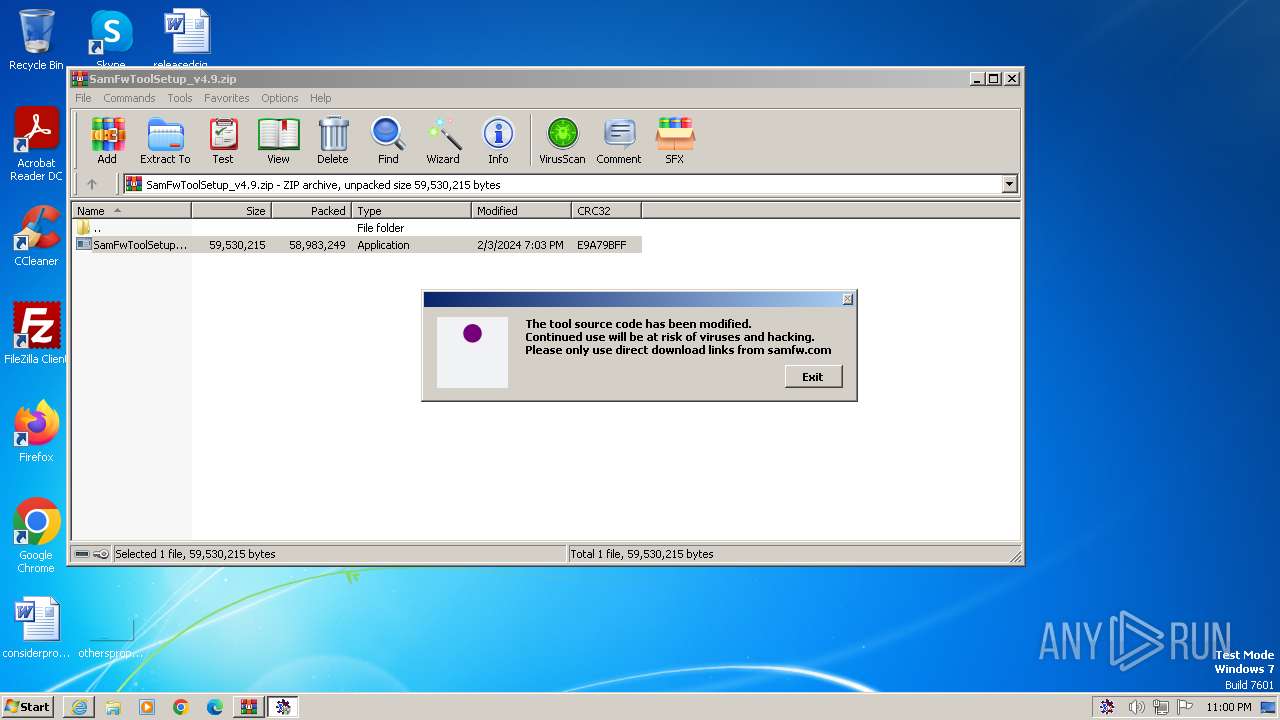
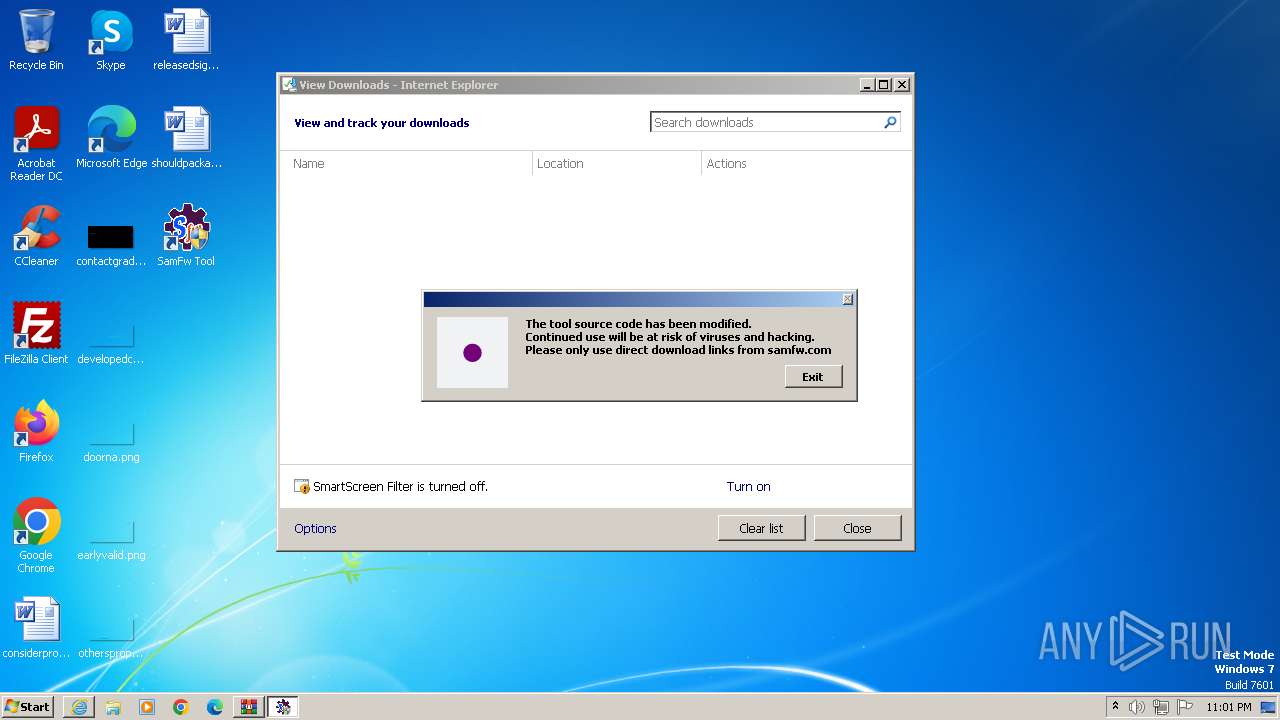
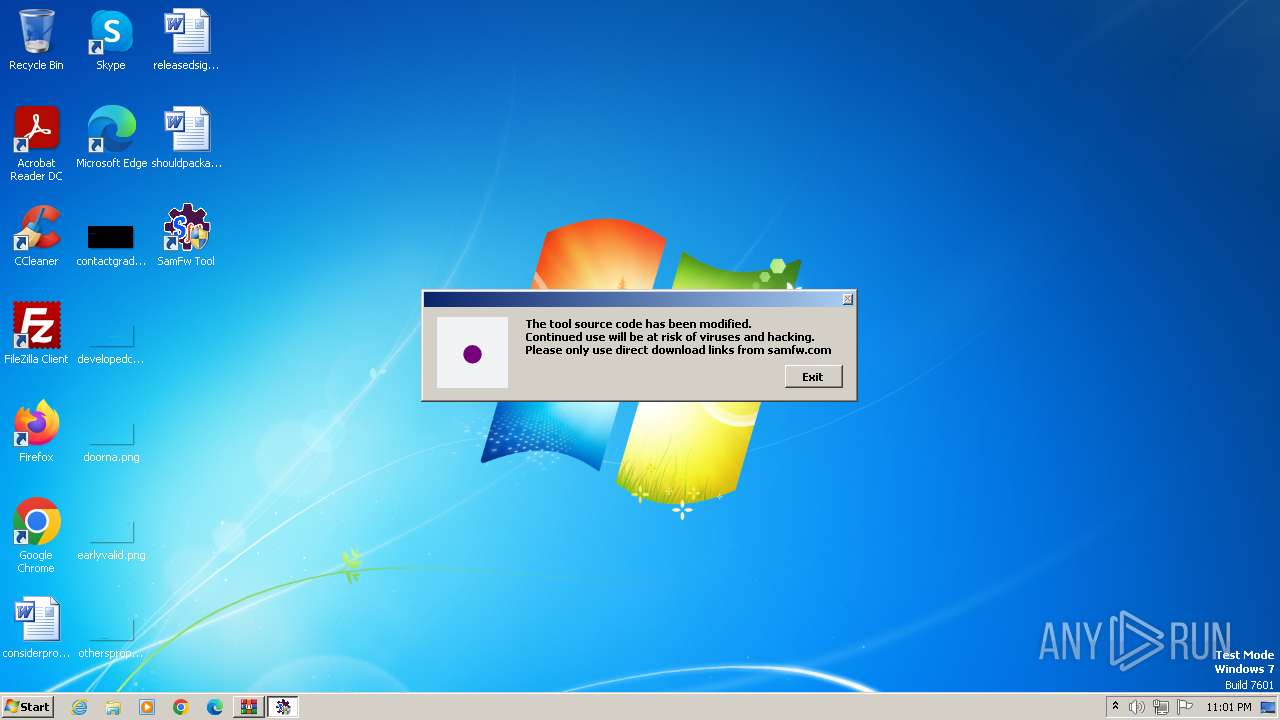
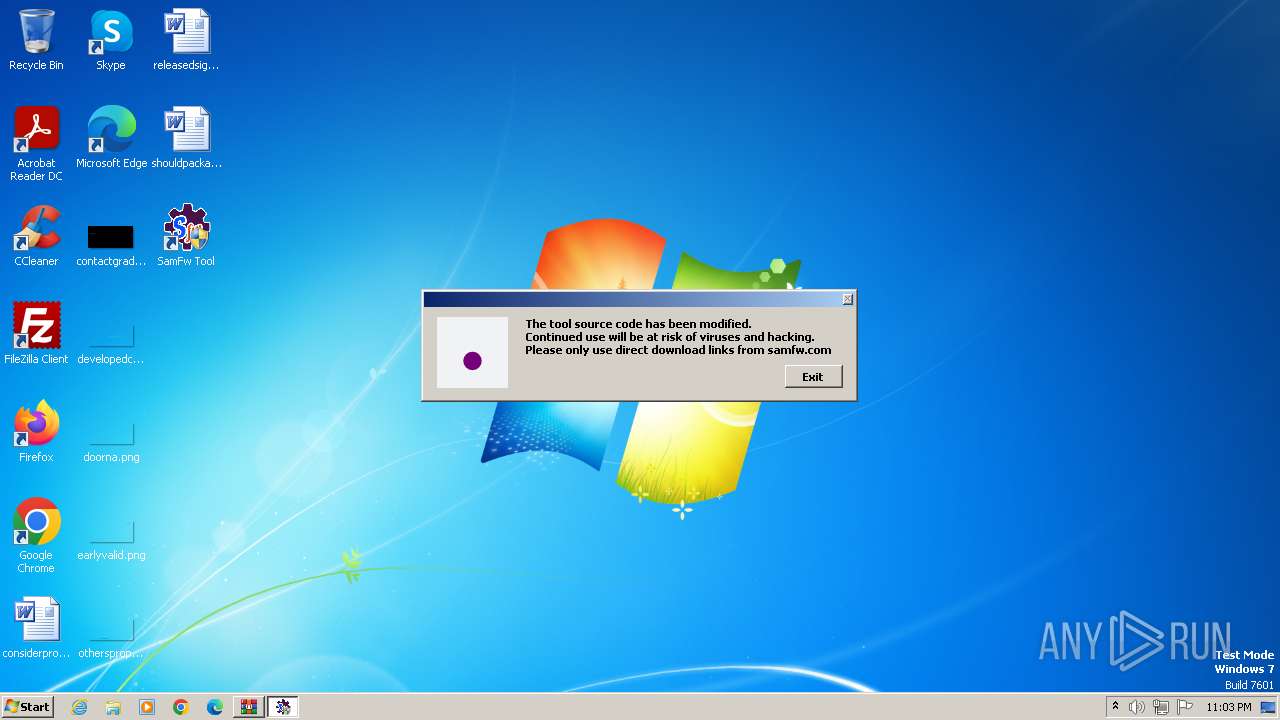
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2024, 21:59:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6322AE3A9FDA92458EAD62DA57A6E724 |
| SHA1: | DEB677078D91D6F7AF207188E1122BBF521FFBAD |
| SHA256: | AF0E4E6C8684BCBCBA91BA46433F50DA396E9B63D3ACE7543AEC1FEAF69BD8CF |
| SSDEEP: | 3:N8JtyKG1zpGRL0MV:2LE1zpGB |
MALICIOUS
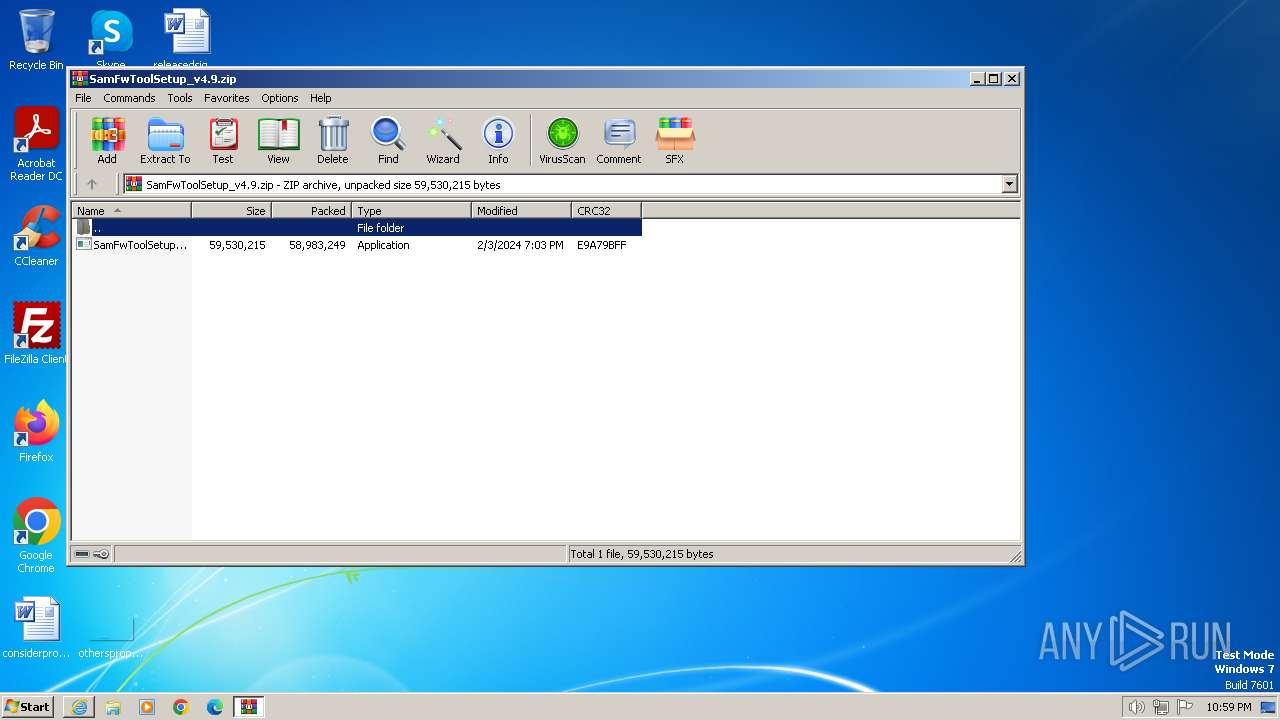
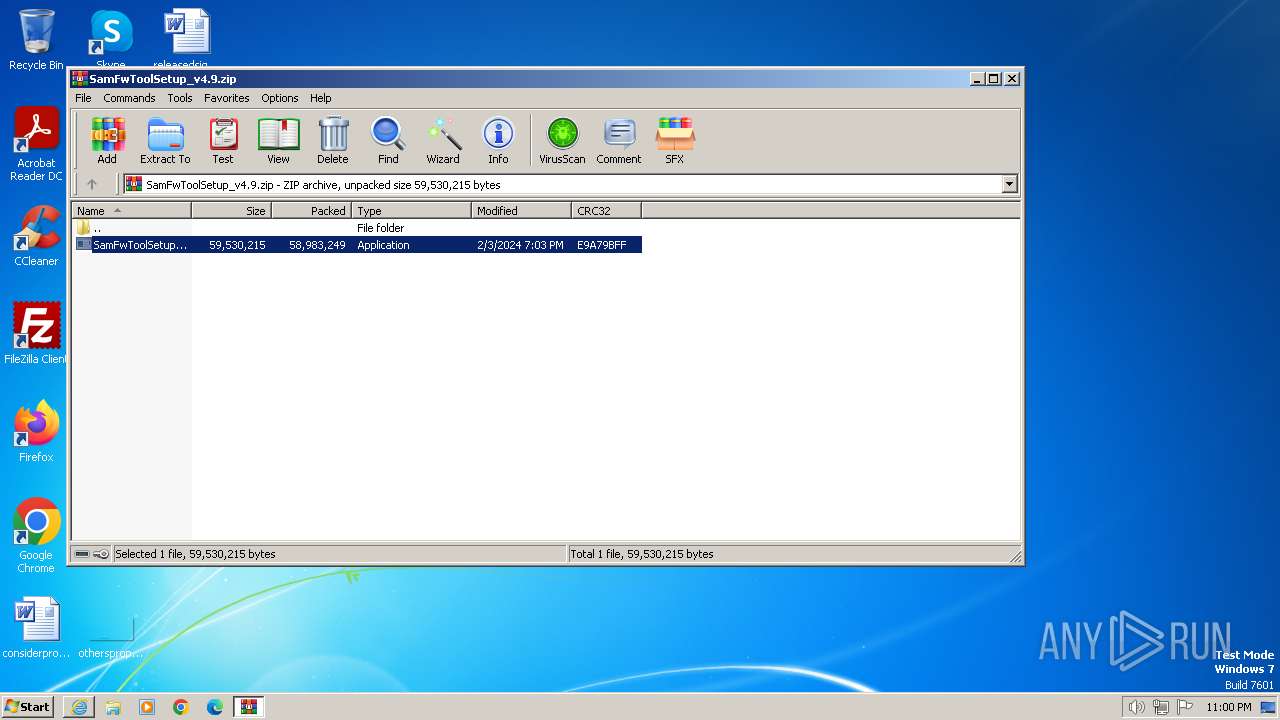
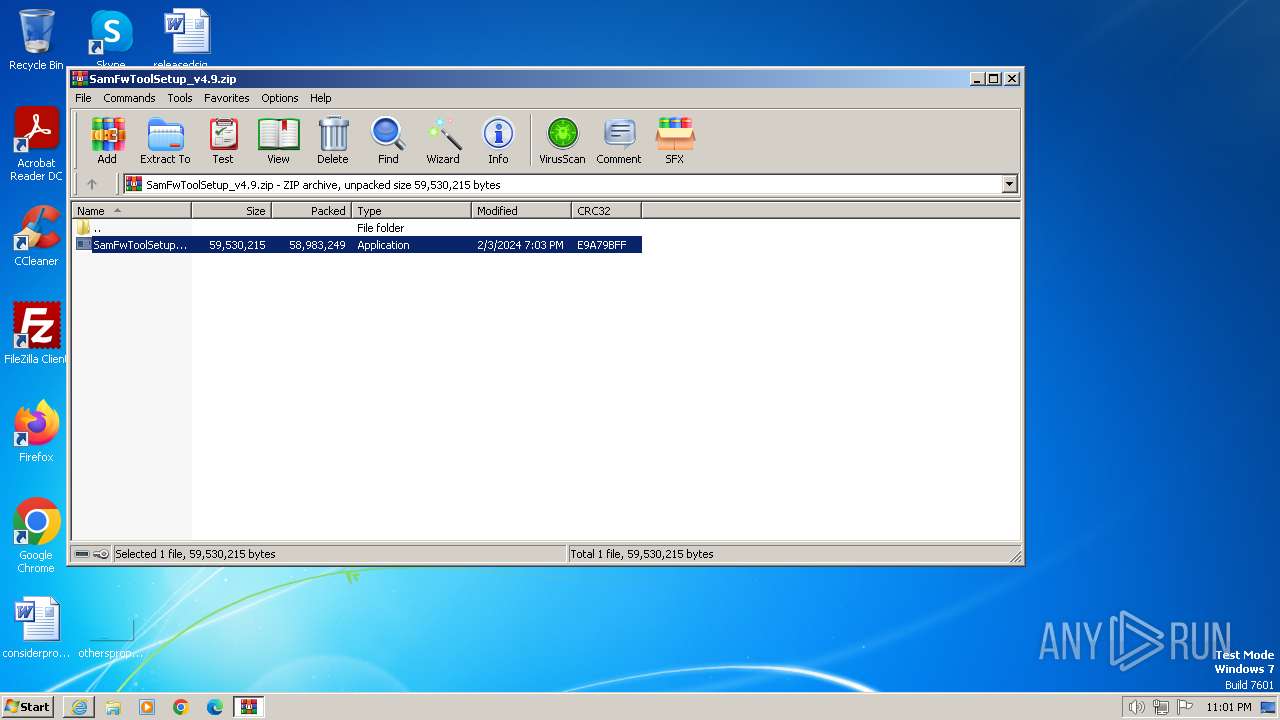
Drops the executable file immediately after the start
- SamFwToolSetup.exe (PID: 2832)
- SamFwToolSetup.exe (PID: 980)
- 7za.exe (PID: 2780)
- SamFwToolSetup.tmp (PID: 2240)
Detects Cygwin installation
- 7za.exe (PID: 2780)
SUSPICIOUS
Reads the Windows owner or organization settings
- SamFwToolSetup.tmp (PID: 2240)
Drops 7-zip archiver for unpacking
- SamFwToolSetup.tmp (PID: 2240)
- 7za.exe (PID: 2780)
The process creates files with name similar to system file names
- 7za.exe (PID: 2780)
Process drops legitimate windows executable
- 7za.exe (PID: 2780)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1992)
Reads settings of System Certificates
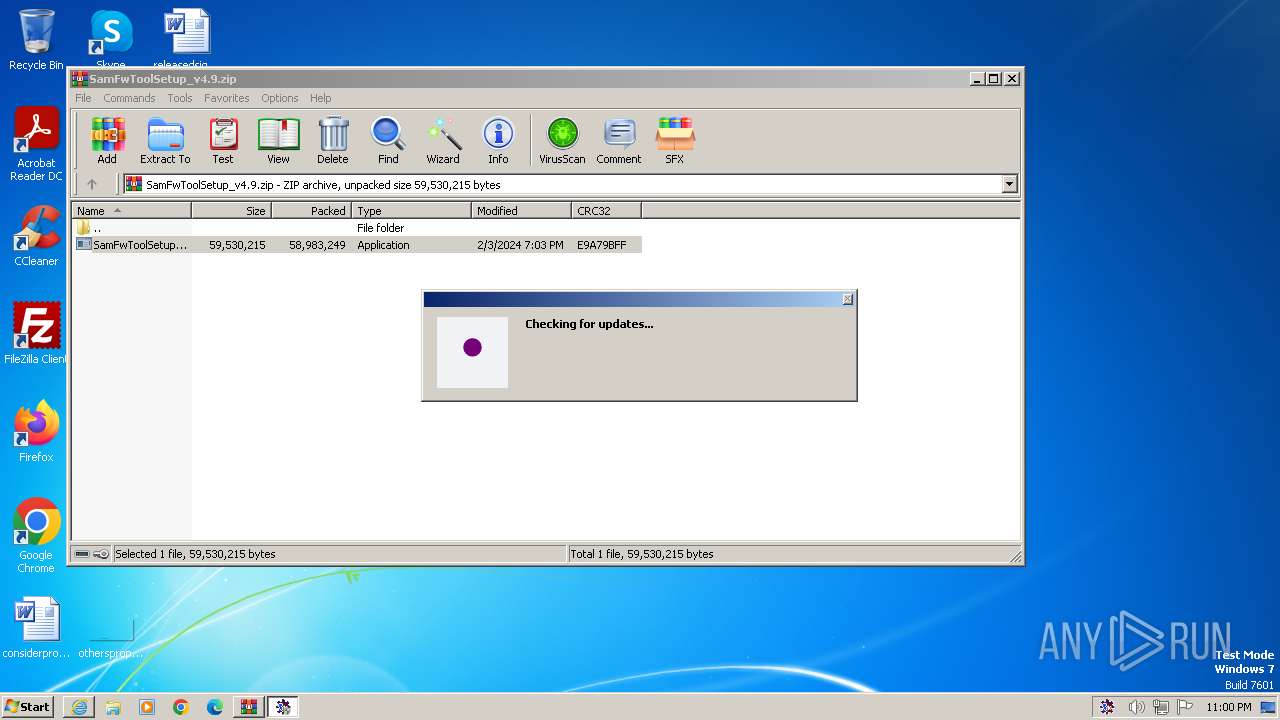
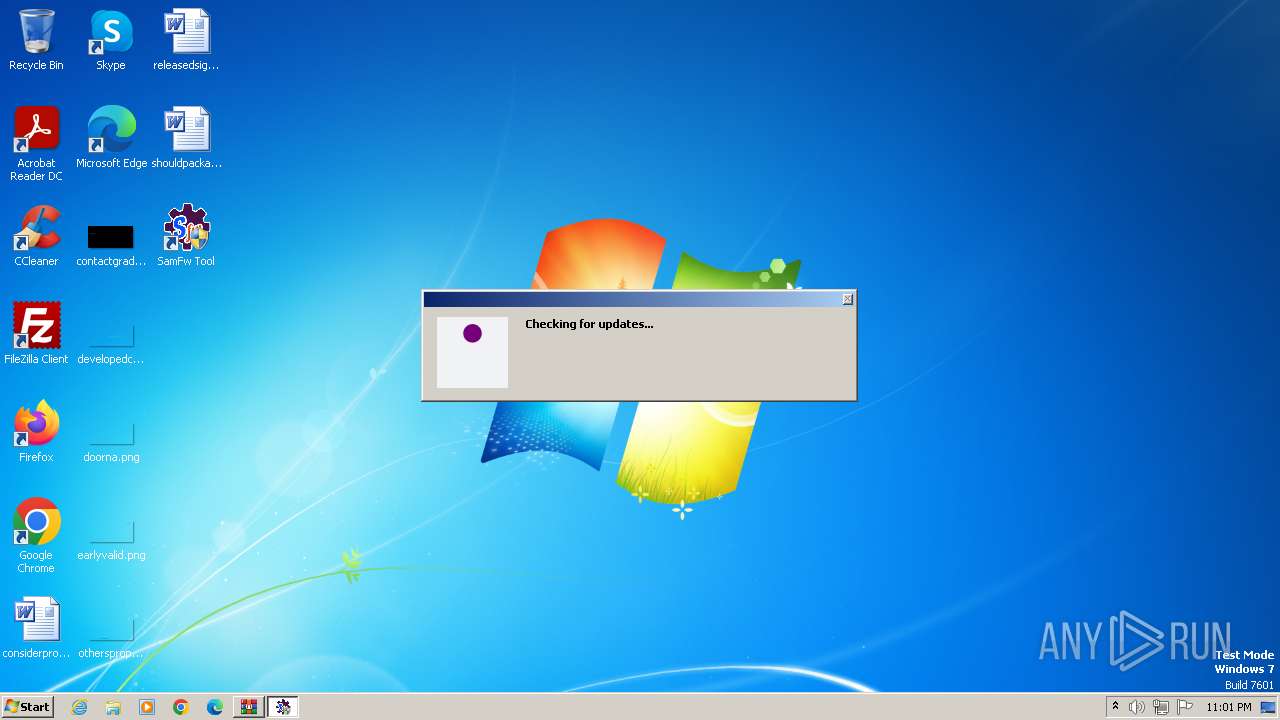
- SamFwTool.exe (PID: 3028)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3832)
Adds/modifies Windows certificates
- SamFwTool.exe (PID: 3028)
Non-standard symbols in registry
- SamFwToolSetup.tmp (PID: 2240)
Reads the Internet Settings
- SamFwTool.exe (PID: 3028)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3832)
INFO
Checks supported languages
- SamFwToolSetup.exe (PID: 2832)
- SamFwToolSetup.exe (PID: 980)
- SamFwToolSetup.tmp (PID: 2240)
- SamFwTool.exe (PID: 3028)
- 7za.exe (PID: 2780)
- SamFwToolSetup.tmp (PID: 1644)
- wmpnscfg.exe (PID: 316)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3832)
- SamFwTool.exe (PID: 1268)
Reads the computer name
- SamFwToolSetup.tmp (PID: 1644)
- 7za.exe (PID: 2780)
- SamFwToolSetup.tmp (PID: 2240)
- wmpnscfg.exe (PID: 316)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3028)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 3832)
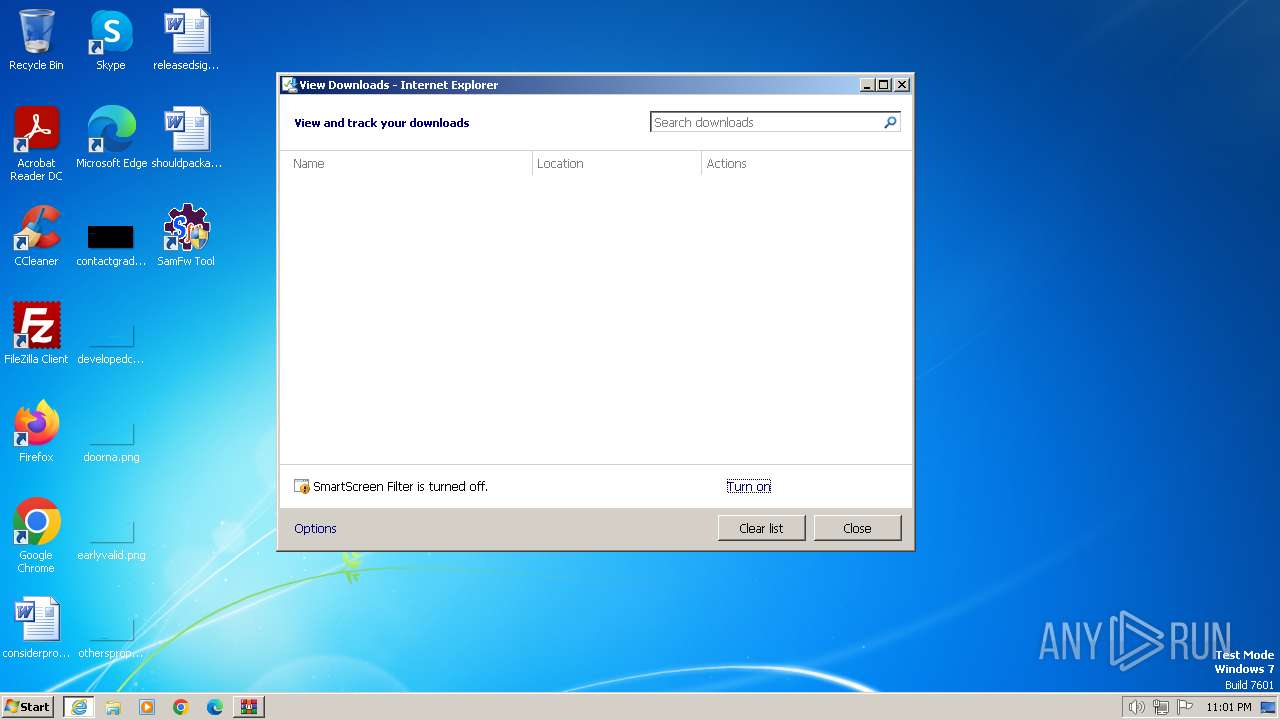
Application launched itself
- iexplore.exe (PID: 3500)
Create files in a temporary directory
- SamFwToolSetup.exe (PID: 2832)
- SamFwToolSetup.exe (PID: 980)
The process uses the downloaded file
- WinRAR.exe (PID: 1992)
- iexplore.exe (PID: 3500)
Creates files in the program directory
- SamFwToolSetup.tmp (PID: 2240)
- SamFwTool.exe (PID: 3028)
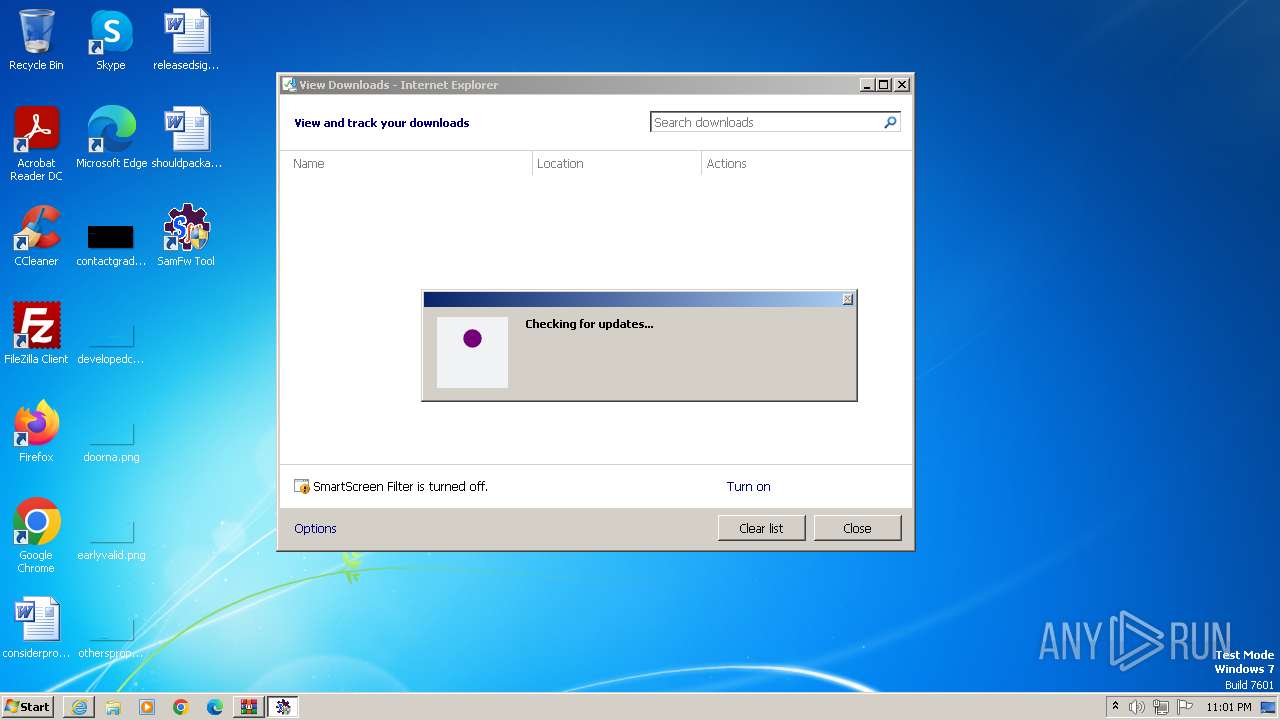
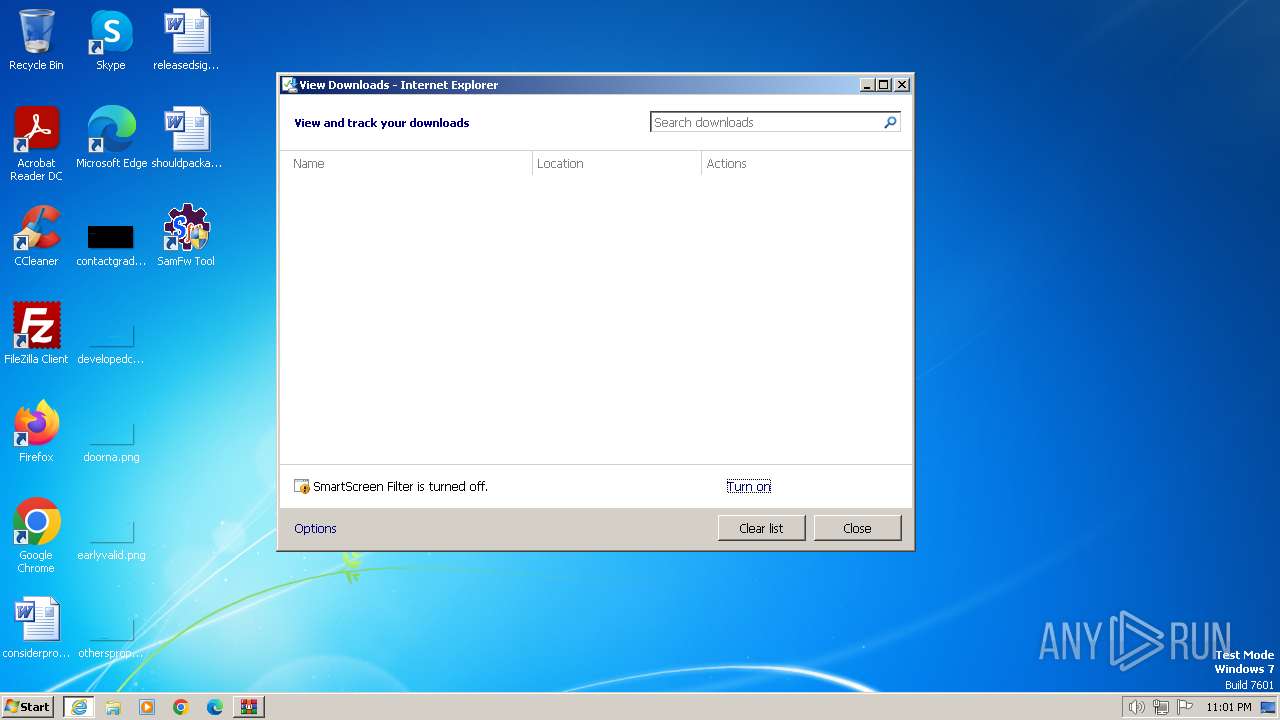
Modifies the phishing filter of IE
- iexplore.exe (PID: 3500)
Creates a software uninstall entry
- SamFwToolSetup.tmp (PID: 2240)
Reads Environment values
- SamFwTool.exe (PID: 3028)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3832)
Reads the software policy settings
- SamFwTool.exe (PID: 3028)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3832)
Manual execution by a user
- wmpnscfg.exe (PID: 316)
- SamFwTool.exe (PID: 2376)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 324)
- SamFwTool.exe (PID: 3564)
- SamFwTool.exe (PID: 3832)
Reads the machine GUID from the registry
- SamFwTool.exe (PID: 3028)
- SamFwTool.exe (PID: 1268)
- SamFwTool.exe (PID: 3232)
- SamFwTool.exe (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
16
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
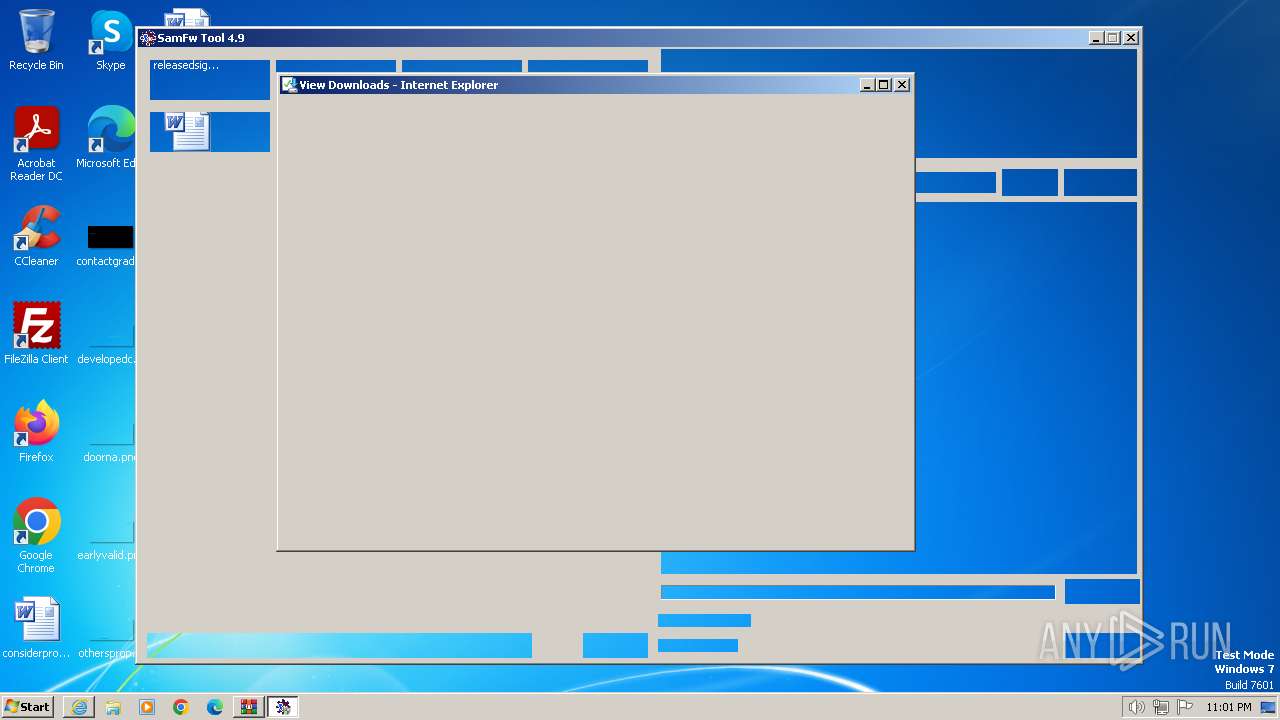
| 324 | "C:\SamFwTool\SamFwTool.exe" | C:\SamFwTool\SamFwTool.exe | — | explorer.exe | |||||||||||
User: admin Company: SamFw.com Integrity Level: MEDIUM Description: SamFwTool Exit code: 3221226540 Version: 4.9.0.0 Modules
| |||||||||||||||
| 980 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1992.28372\SamFwToolSetup.exe" /SPAWNWND=$130152 /NOTIFYWND=$120254 | C:\Users\admin\AppData\Local\Temp\Rar$EXa1992.28372\SamFwToolSetup.exe | SamFwToolSetup.tmp | ||||||||||||
User: admin Company: SamFw.com Integrity Level: HIGH Description: SamFw Tool Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1268 | "C:\SamFwTool\SamFwTool.exe" | C:\SamFwTool\SamFwTool.exe | explorer.exe | ||||||||||||
User: admin Company: SamFw.com Integrity Level: HIGH Description: SamFwTool Exit code: 0 Version: 4.9.0.0 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\AppData\Local\Temp\is-SJF7Q.tmp\SamFwToolSetup.tmp" /SL5="$120254,58690757,832512,C:\Users\admin\AppData\Local\Temp\Rar$EXa1992.28372\SamFwToolSetup.exe" | C:\Users\admin\AppData\Local\Temp\is-SJF7Q.tmp\SamFwToolSetup.tmp | — | SamFwToolSetup.exe | |||||||||||
User: admin Company: SamFw.com Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\SamFwToolSetup_v4.9.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3500 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\is-1496M.tmp\SamFwToolSetup.tmp" /SL5="$B0206,58690757,832512,C:\Users\admin\AppData\Local\Temp\Rar$EXa1992.28372\SamFwToolSetup.exe" /SPAWNWND=$130152 /NOTIFYWND=$120254 | C:\Users\admin\AppData\Local\Temp\is-1496M.tmp\SamFwToolSetup.tmp | — | SamFwToolSetup.exe | |||||||||||
User: admin Company: SamFw.com Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2376 | "C:\SamFwTool\SamFwTool.exe" | C:\SamFwTool\SamFwTool.exe | — | explorer.exe | |||||||||||
User: admin Company: SamFw.com Integrity Level: MEDIUM Description: SamFwTool Exit code: 3221226540 Version: 4.9.0.0 Modules
| |||||||||||||||
| 2780 | "C:\SamFwTool\data\7za.exe" x "C:\SamFwTool\data.7z" -o"C:\SamFwTool\" * -r -aoa | C:\SamFwTool\data\7za.exe | — | SamFwToolSetup.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 2 Version: 18.01 Modules
| |||||||||||||||
Total events
62 580
Read events
62 325
Write events
209
Delete events
46
Modification events
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31097983 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31097983 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
44
Suspicious files
20
Text files
16
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab213F.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2141.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2142.tmp | binary | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2140.tmp | binary | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
29
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | iexplore.exe | GET | 304 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?36ca310eb28aaa33 | unknown | — | — | unknown |
2232 | iexplore.exe | GET | 304 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?92967c53a8c0ec29 | unknown | — | — | unknown |
2232 | iexplore.exe | GET | — | 69.192.161.44:80 | http://x2.c.lencr.org/ | unknown | — | — | unknown |
2232 | iexplore.exe | GET | 200 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9df0723acf4b4299 | unknown | — | — | unknown |
2232 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
3500 | iexplore.exe | GET | 304 | 23.216.77.55:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e55f0cb727843010 | unknown | — | — | unknown |
2232 | iexplore.exe | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b150b552b216e1f4 | unknown | — | — | unknown |
3500 | iexplore.exe | GET | 304 | 23.216.77.55:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?aeb32cb922858c96 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 304 | 23.216.77.55:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e2ddf83a2417bb20 | unknown | — | — | unknown |
3500 | iexplore.exe | GET | 304 | 23.216.77.55:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f42b4d0af9d9768e | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2232 | iexplore.exe | 188.114.96.3:443 | samfw.com | CLOUDFLARENET | NL | unknown |
2232 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2232 | iexplore.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2232 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
3500 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3500 | iexplore.exe | 23.216.77.55:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 23.216.77.55:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
samfw.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |