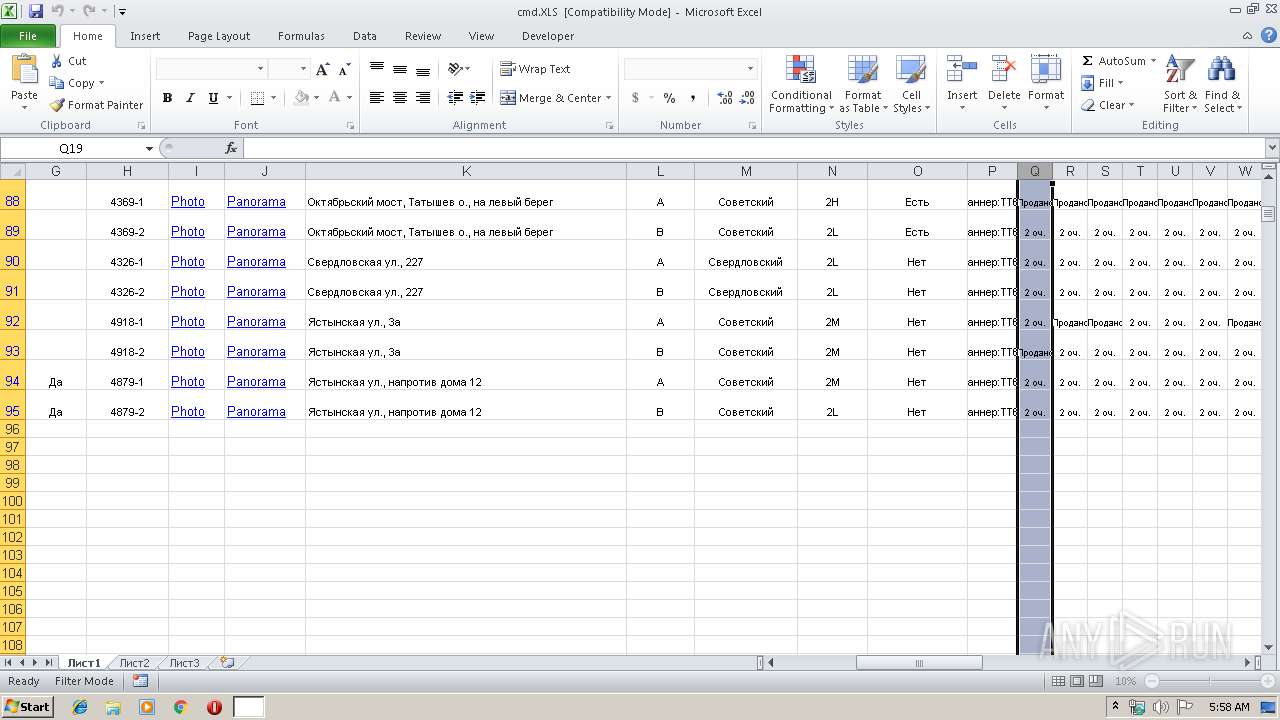
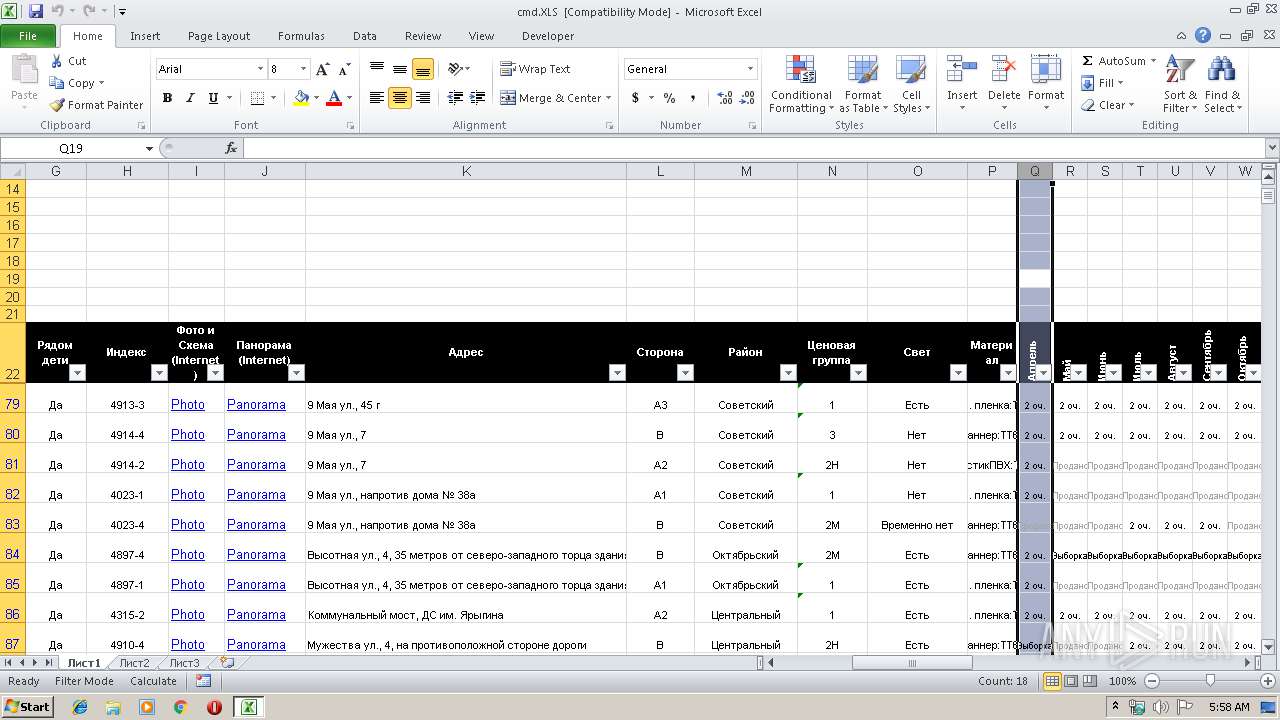
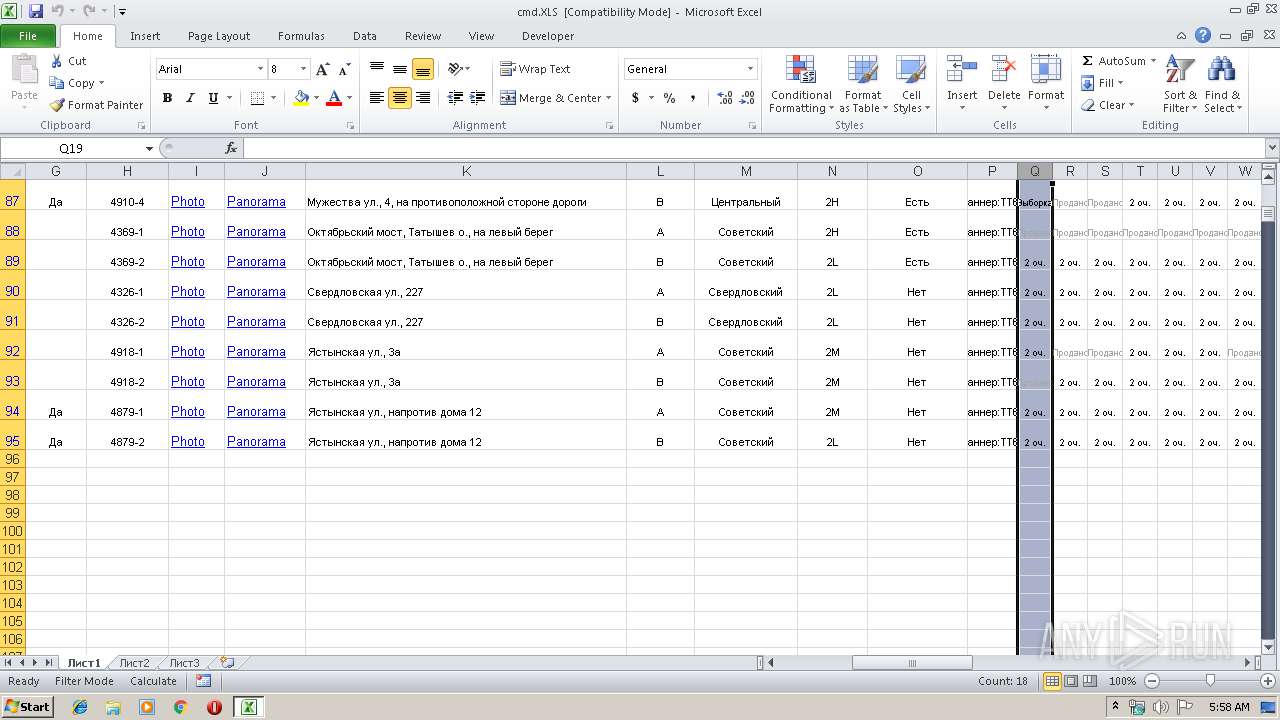
| File name: | cmd.XLS |
| Full analysis: | https://app.any.run/tasks/123c5db0-4b46-4219-9867-b0ece79b5776 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 05:58:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
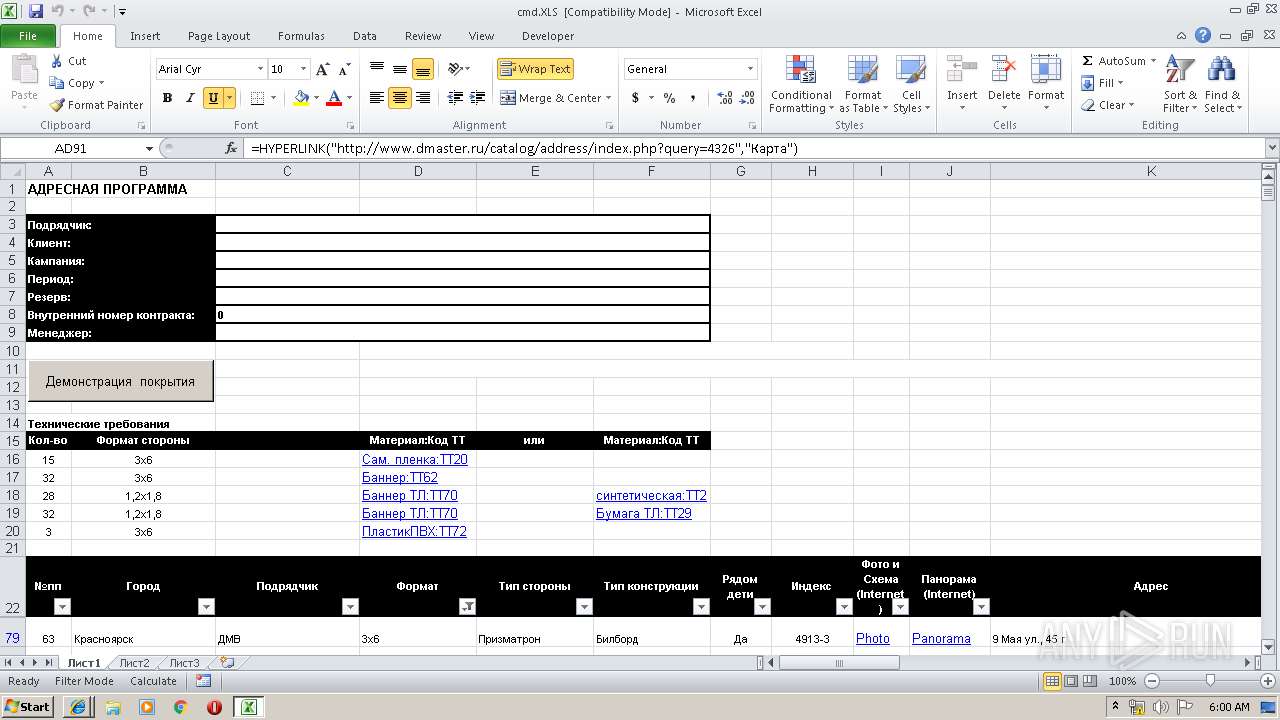
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: tmamonova, Last Saved By: RePack by Diakov, Name of Creating Application: Microsoft Excel, Last Printed: Mon Jun 28 06:14:04 2010, Create Time/Date: Mon Aug 14 07:31:30 2006, Last Saved Time/Date: Thu Mar 21 08:05:17 2019, Security: 0 |
| MD5: | 8BED224496AC5341117E065B50EA5F81 |
| SHA1: | D071EE54165CEE5ACF5142CF4D147CFC1233740D |
| SHA256: | AEF98D76AA60E4F47D067670172DAEB4F368EDBE04BB3842CEB432297D2E4BDF |
| SSDEEP: | 6144:FcTGrBZAPUGvtZkiWnkHLty/xLZwA9CK6QZjKR1OXa:ddcIq |
MALICIOUS
No malicious indicators.SUSPICIOUS
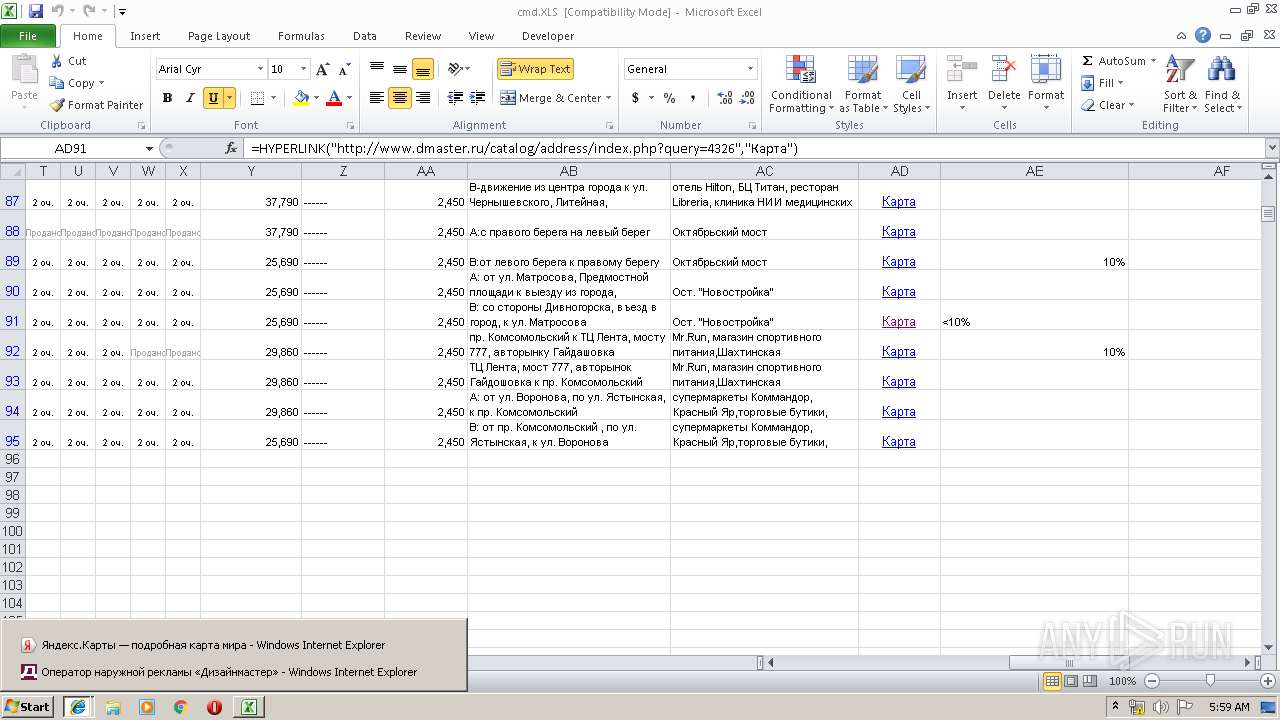
Reads internet explorer settings
- EXCEL.EXE (PID: 2940)
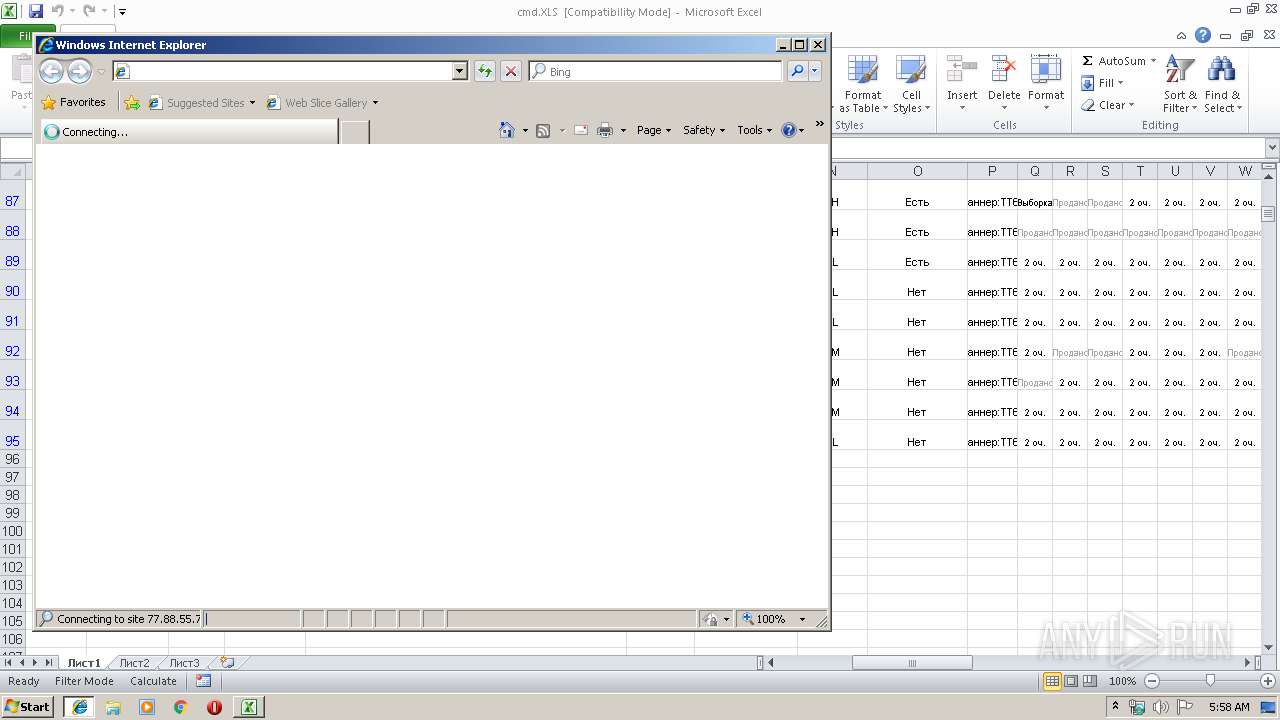
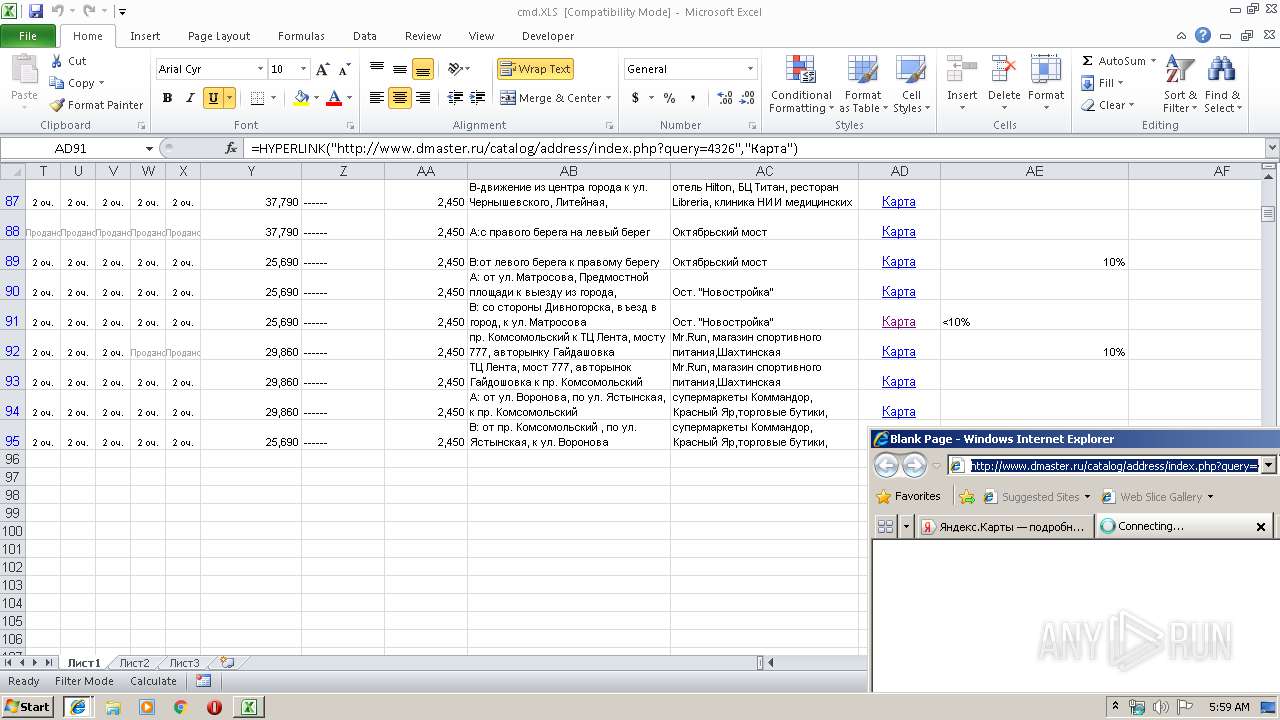
Unusual connect from Microsoft Office
- EXCEL.EXE (PID: 2940)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2940)
Creates files in the user directory
- EXCEL.EXE (PID: 2940)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2976)
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 2724)
Reads settings of System Certificates
- iexplore.exe (PID: 2288)
Changes internet zones settings
- iexplore.exe (PID: 2288)
Changes settings of System certificates
- iexplore.exe (PID: 2288)
Reads internet explorer settings
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 2724)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2288)
Dropped object may contain Bitcoin addresses
- EXCEL.EXE (PID: 2940)
- iexplore.exe (PID: 2724)
Reads Internet Cache Settings
- iexplore.exe (PID: 2548)
- iexplore.exe (PID: 2724)
- iexplore.exe (PID: 2288)
Application launched itself
- iexplore.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | tmamonova |
|---|---|
| LastModifiedBy: | RePack by Diakov |
| Software: | Microsoft Excel |
| LastPrinted: | 2010:06:28 05:14:04 |
| CreateDate: | 2006:08:14 06:31:30 |
| ModifyDate: | 2019:03:21 08:05:17 |
| Security: | None |
| CodePage: | Windows Cyrillic |
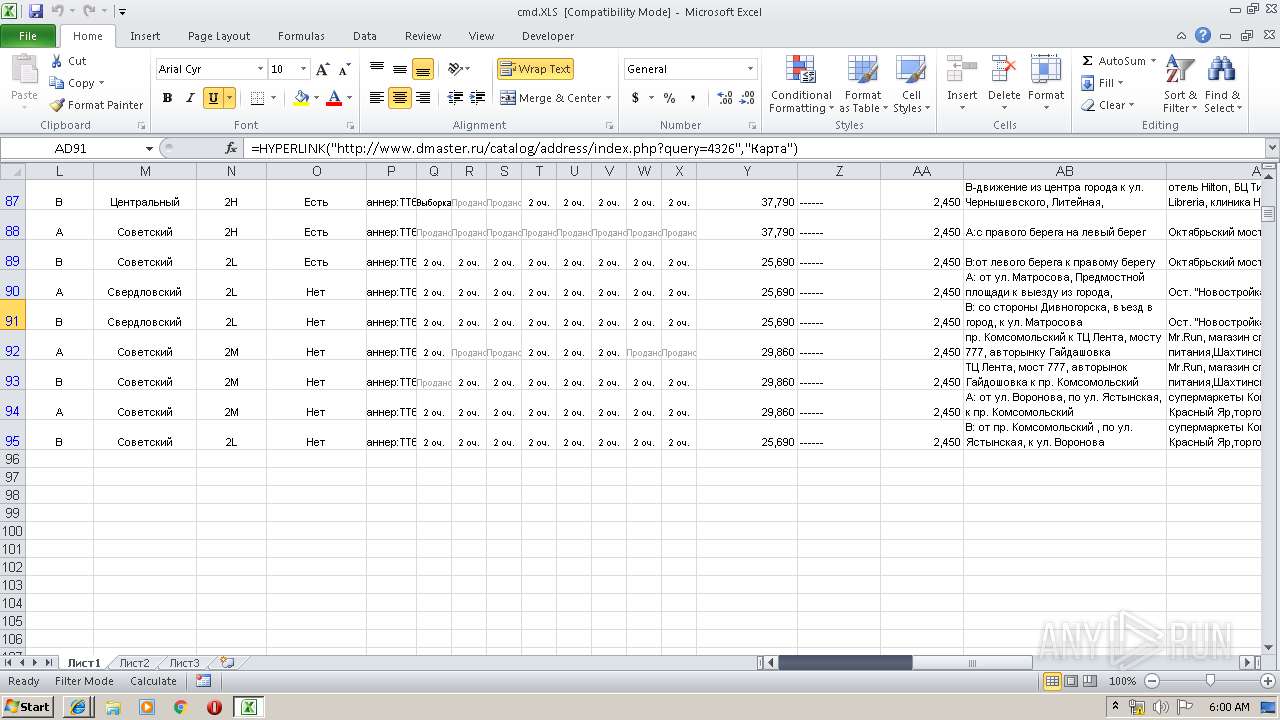
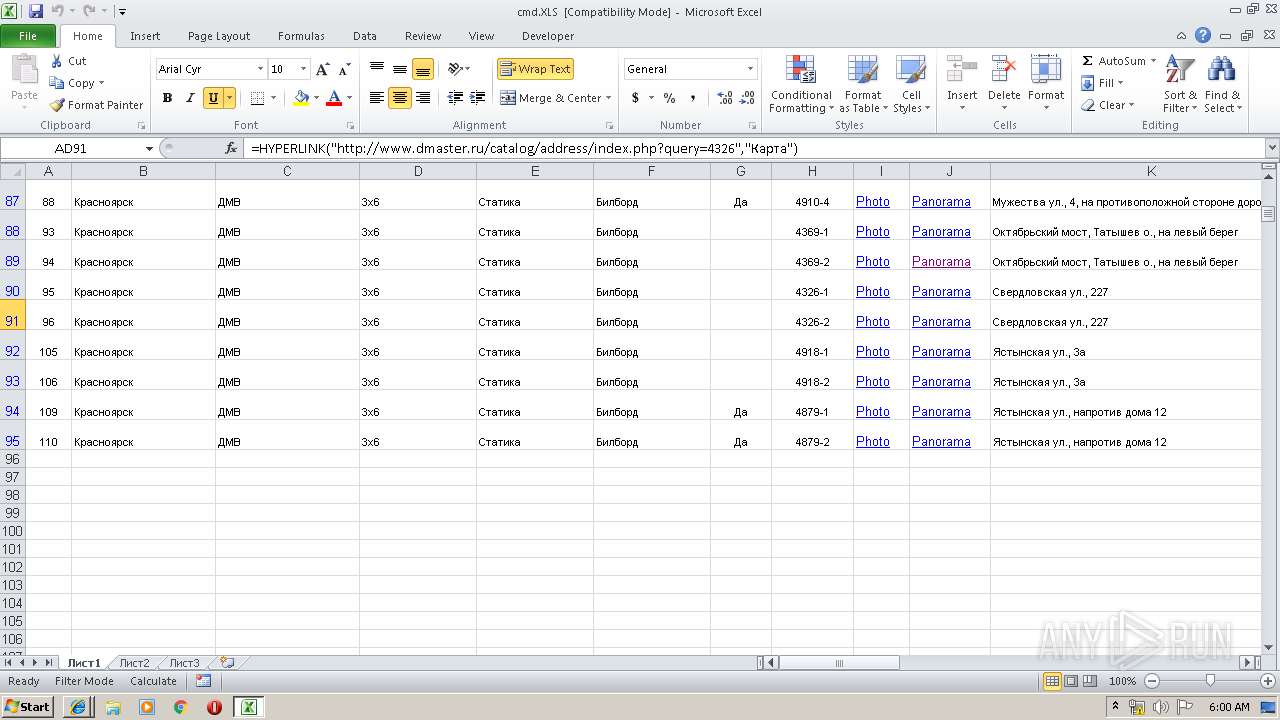
| Company: | Дизайнмастер |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 26 |
| CompObjUserType: | ???? Microsoft Excel 2003 |
Total processes
37
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2288 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2288 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2288 CREDAT:6402 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2976 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
1 378
Read events
1 195
Write events
173
Delete events
10
Modification events
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 5'; |
Value: 35273B007C0B0000010000000000000000000000 | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 7C0B00005608F34B74E0D40100000000 | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 5'; |
Value: 35273B007C0B0000010000000000000000000000 | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2940) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\100CB5 |
| Operation: | write | Name: | 100CB5 |
Value: 040000007C0B00002900000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0063006D0064002E0058004C005300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000000BC024D74E0D401B50C1000B50C100000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
106
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR726.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2940 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@yandex[1].txt | — | |
MD5:— | SHA256:— | |||
| 2940 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFEF8EF97D5528E7A4.TMP | — | |
MD5:— | SHA256:— | |||
| 2288 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@yandex[1].txt | — | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O0ROZ6X6\CFX-MQNt[1].txt | — | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\2XROVPU6\json[1].txt | — | |
MD5:— | SHA256:— | |||
| 2940 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@yandex[2].txt | text | |
MD5:— | SHA256:— | |||
| 2548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
42
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
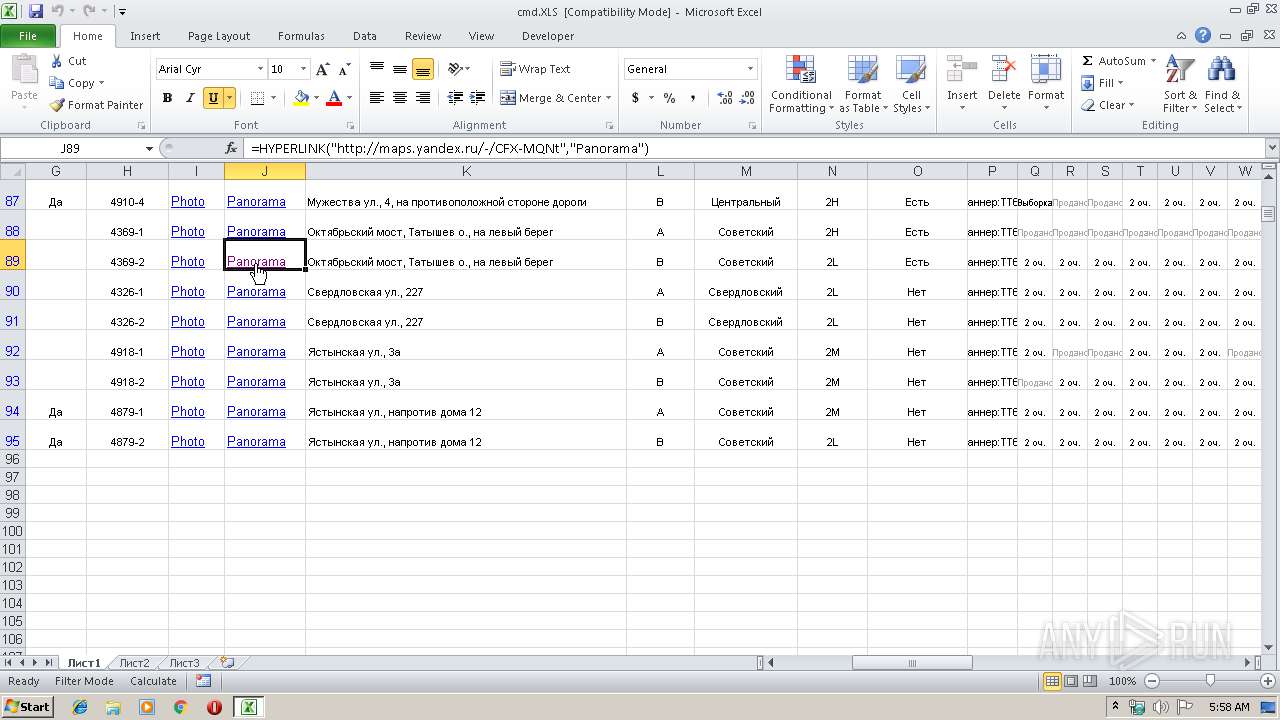
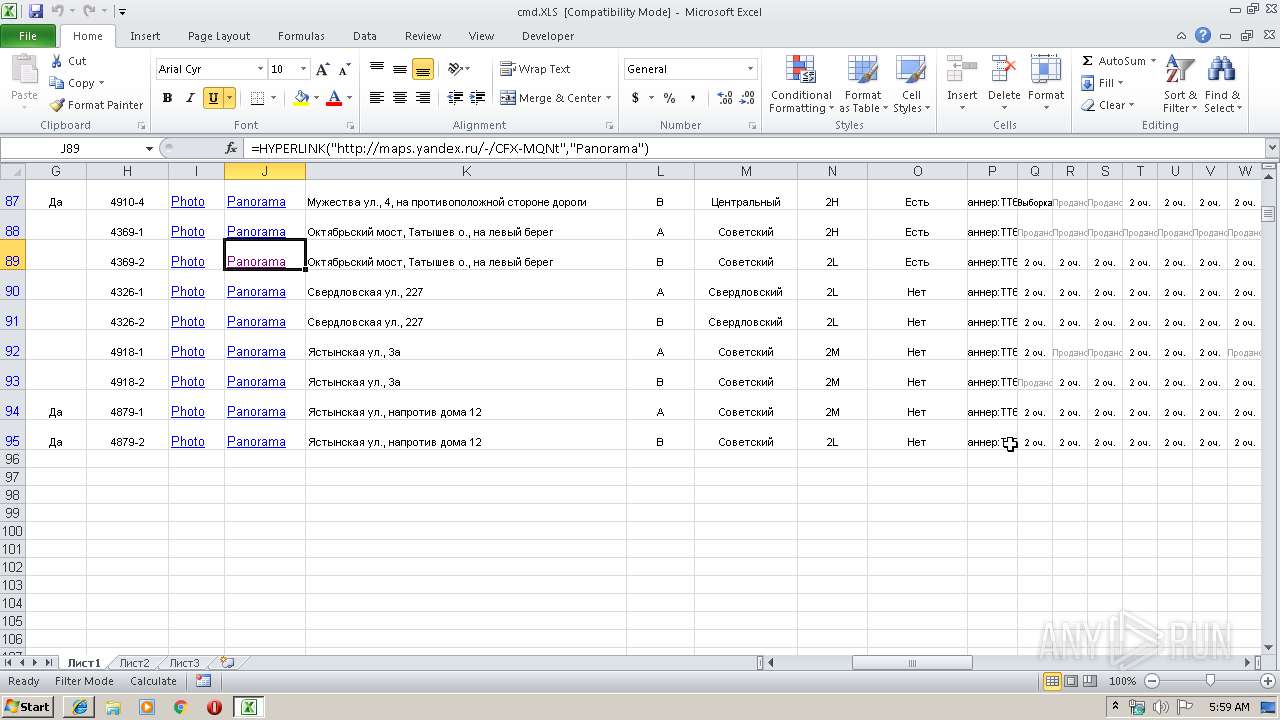
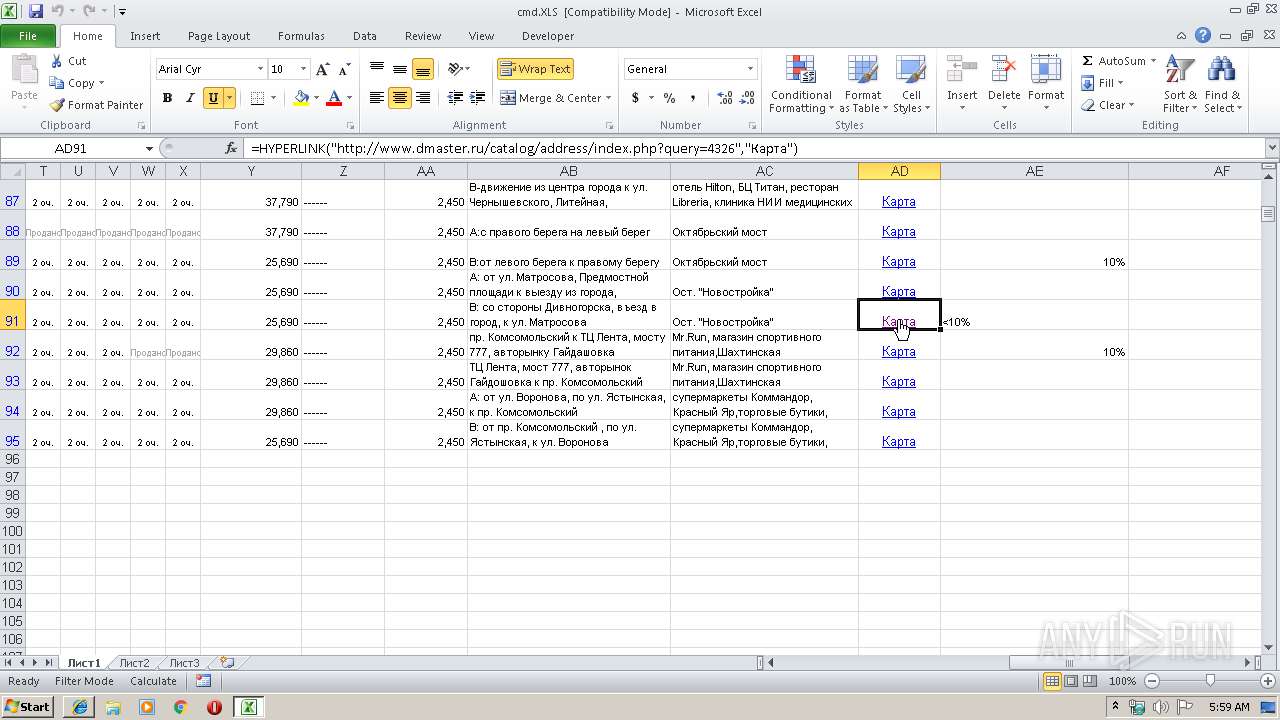
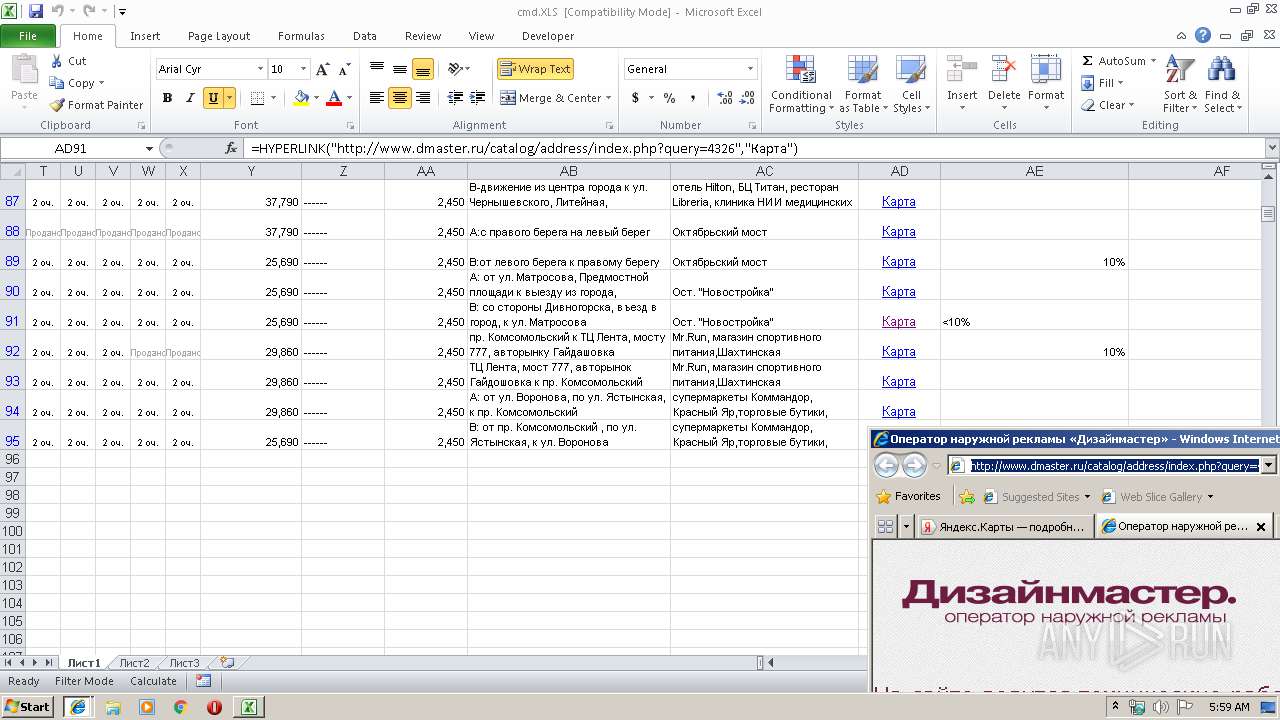
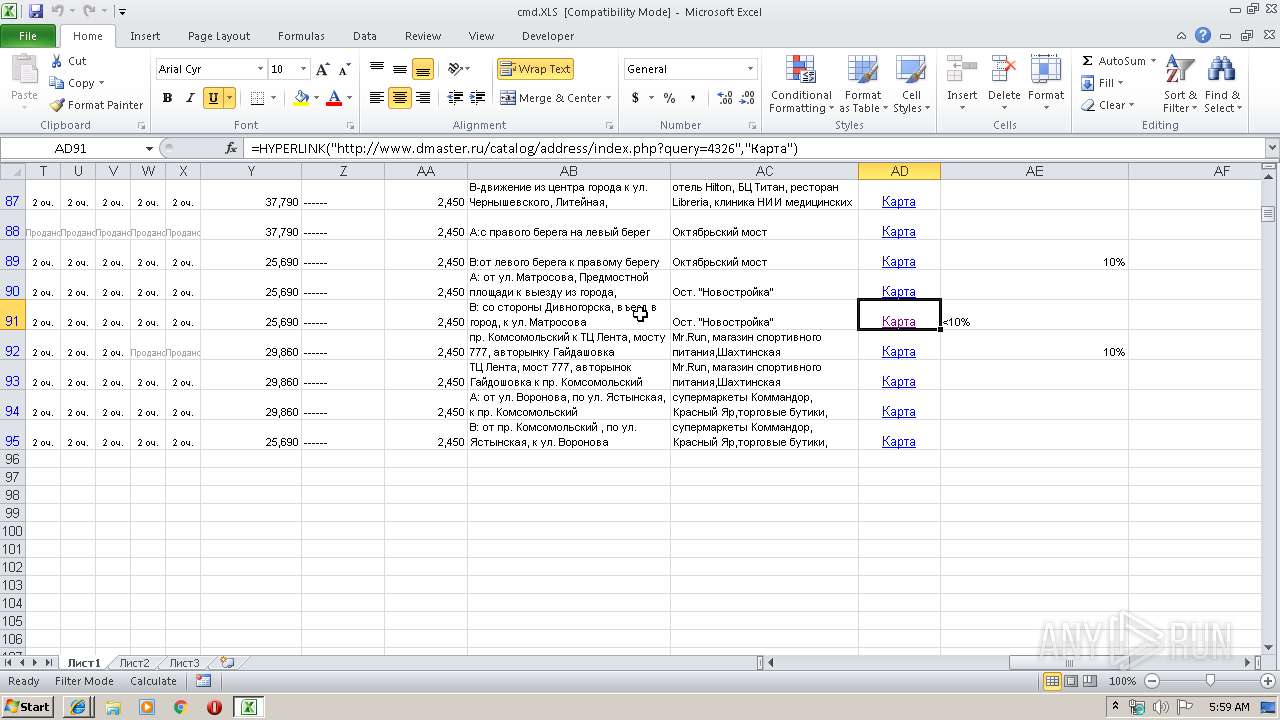
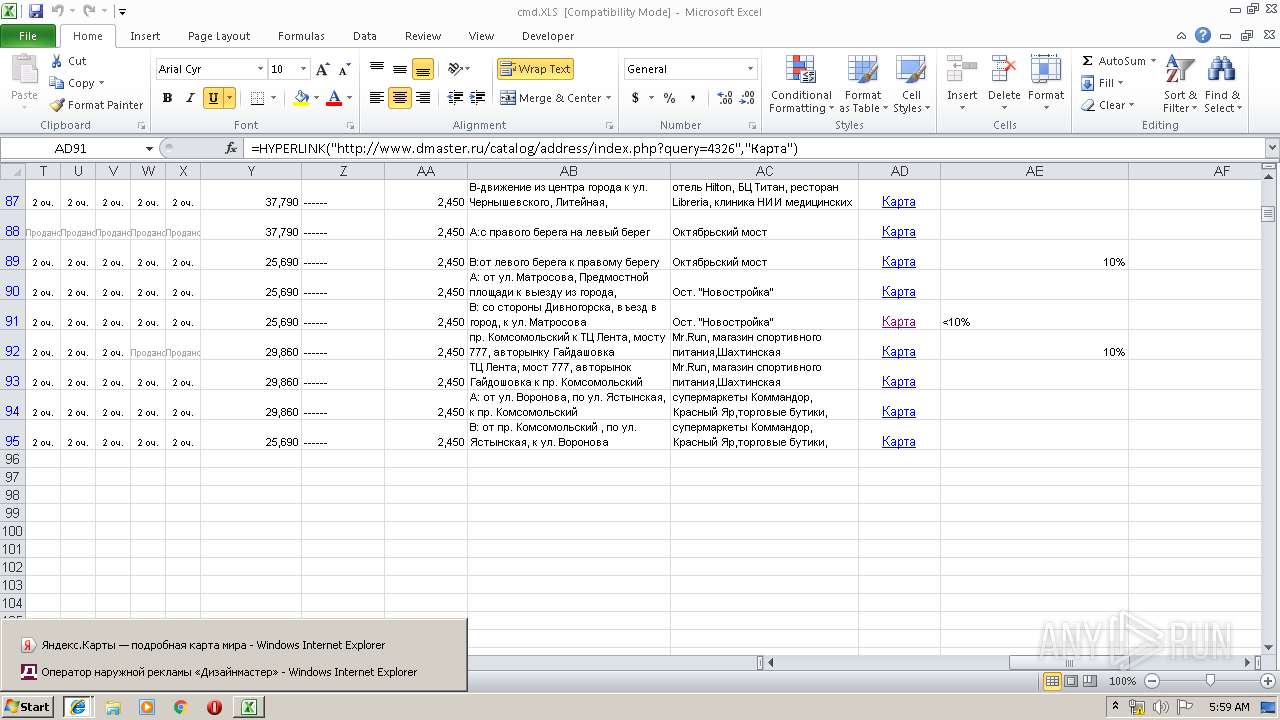
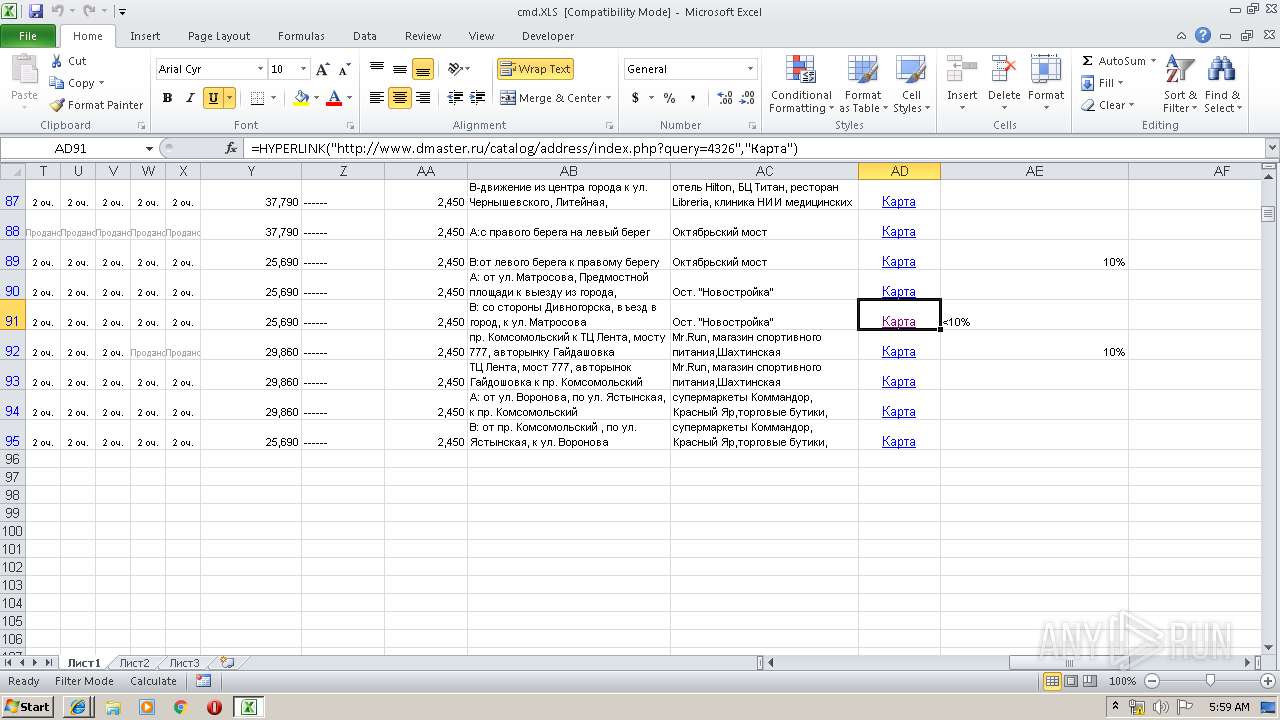
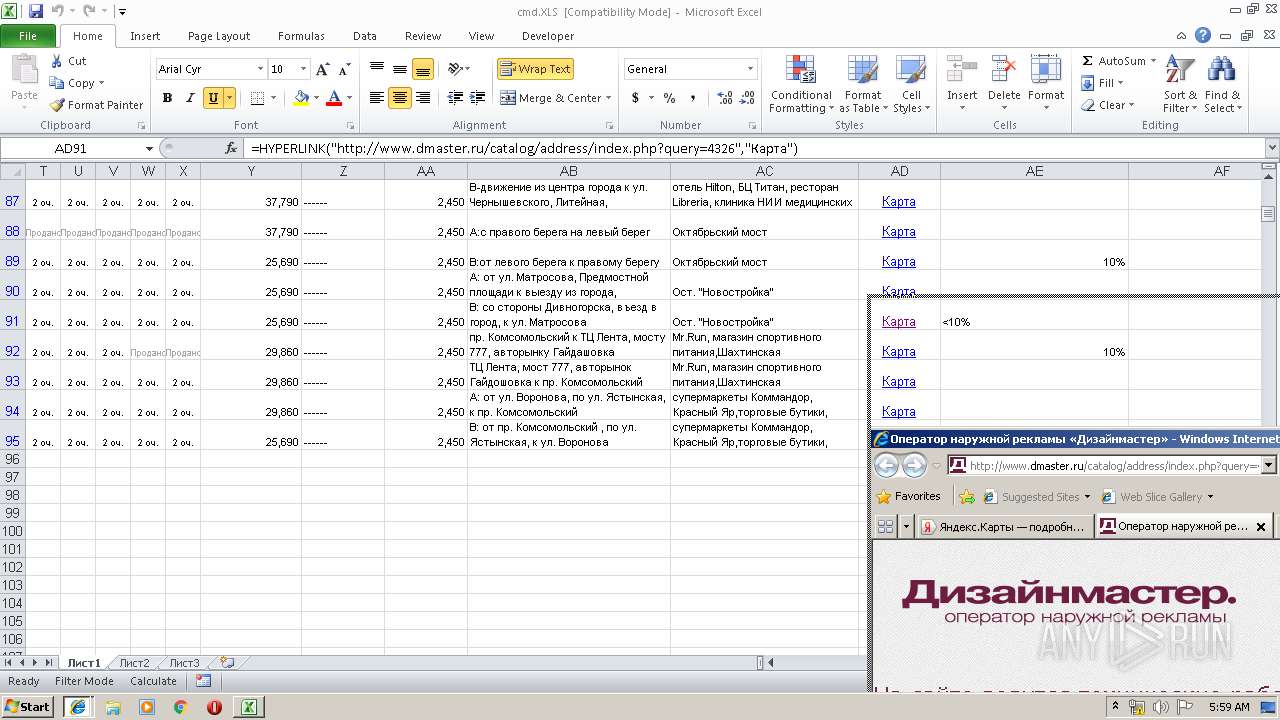
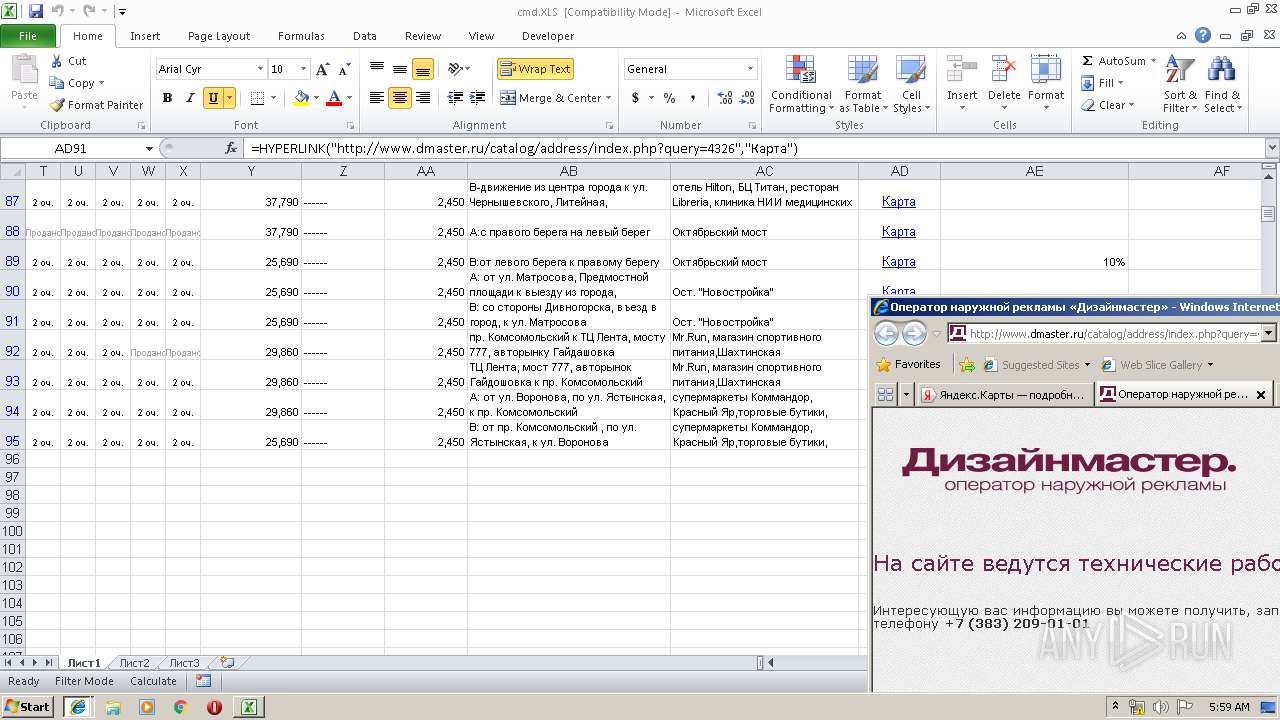
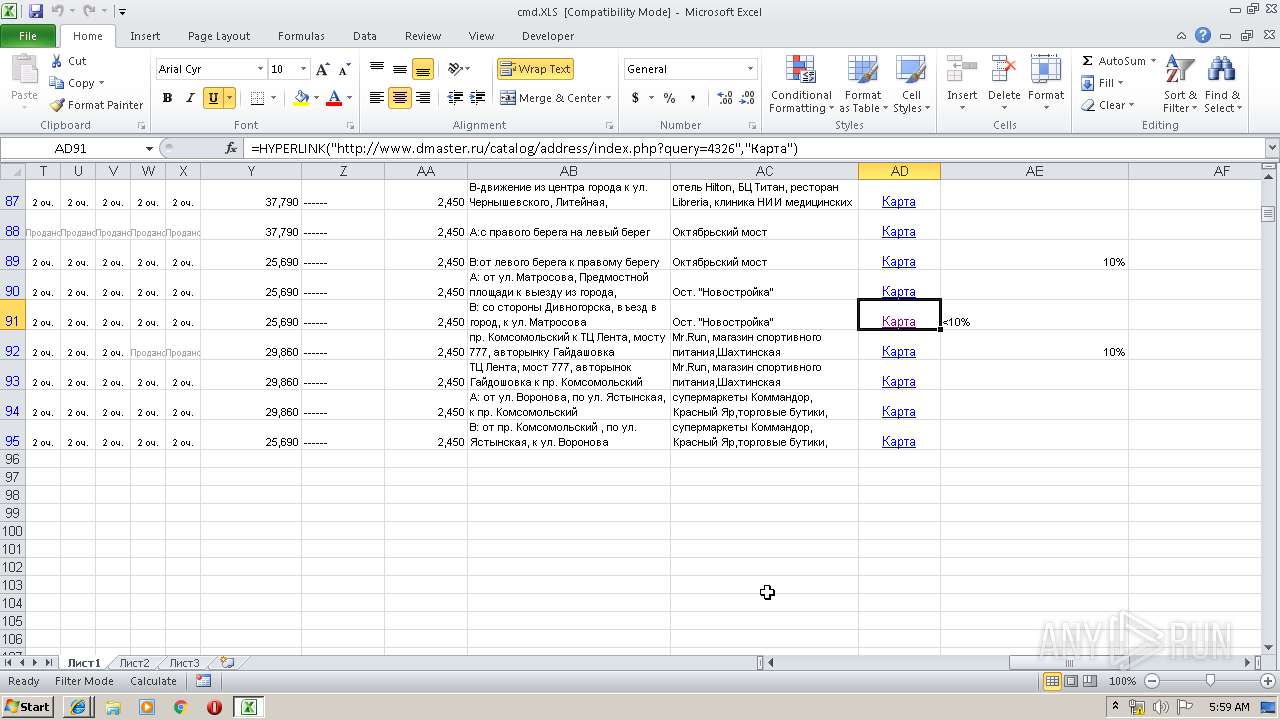
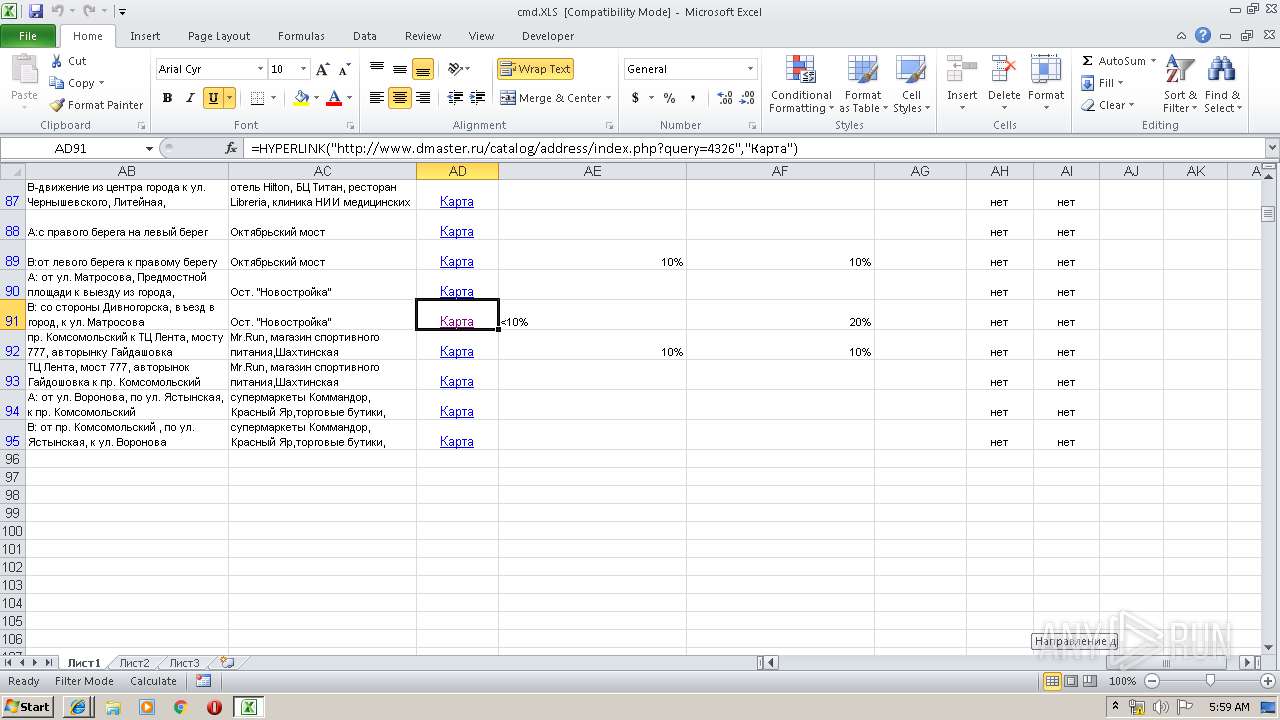
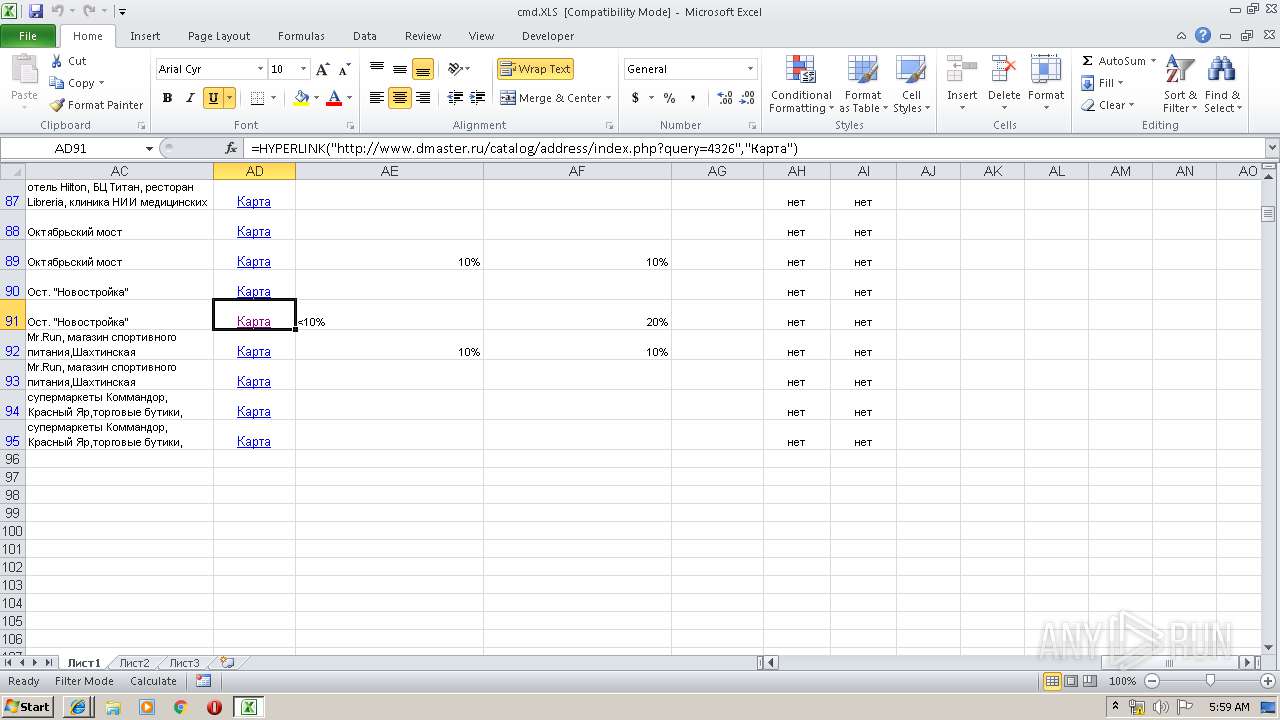
2940 | EXCEL.EXE | GET | — | 195.128.126.59:80 | http://www.dmaster.ru/js/scripts.js?153242909362815 | RU | — | — | unknown |
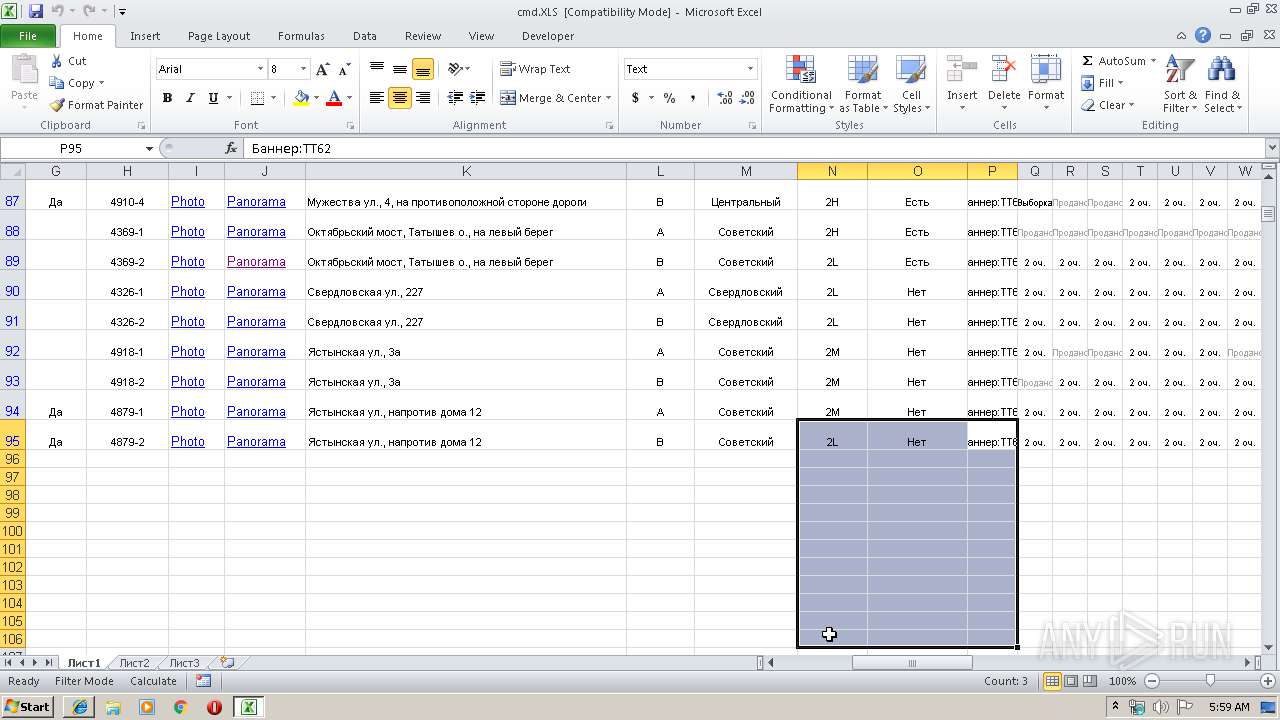
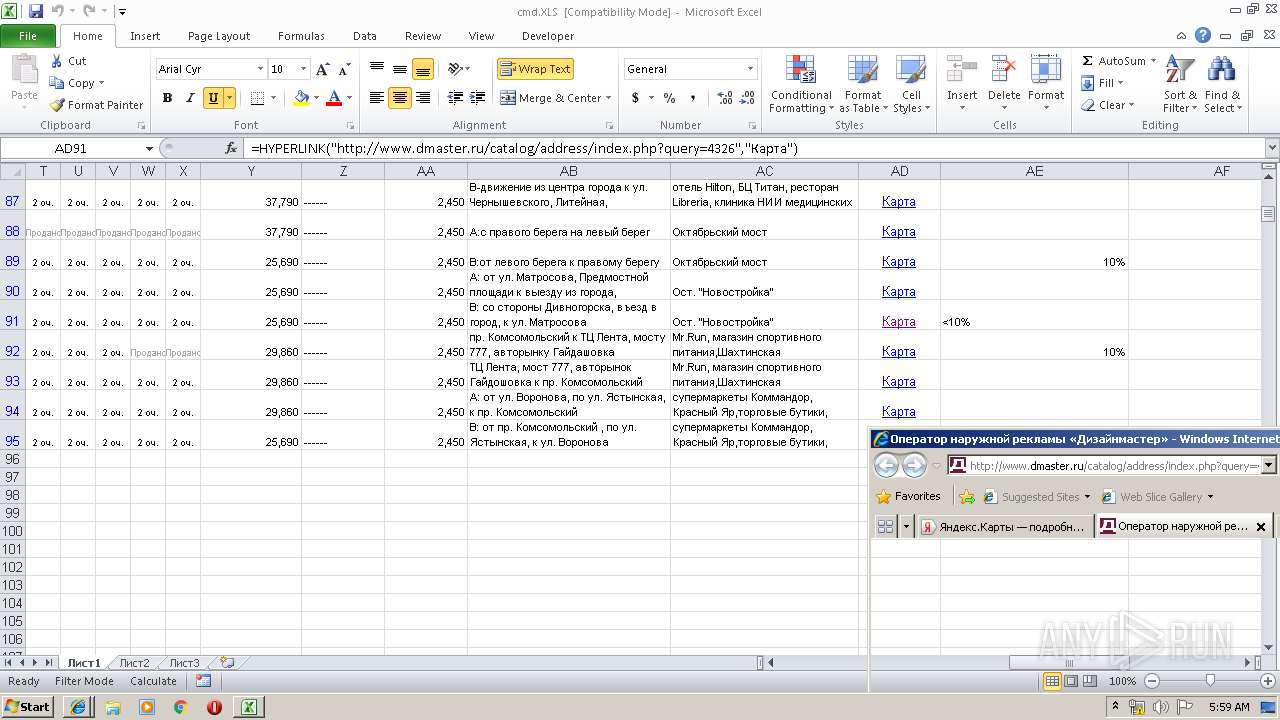
2940 | EXCEL.EXE | GET | 200 | 195.128.126.59:80 | http://www.dmaster.ru/catalog/address/index.php?query=4326 | RU | html | 1.58 Kb | unknown |
2940 | EXCEL.EXE | GET | 200 | 195.128.126.59:80 | http://www.dmaster.ru/css/style.css?1529564084124212 | RU | text | 23.7 Kb | unknown |
2940 | EXCEL.EXE | GET | 200 | 216.58.205.234:80 | http://fonts.googleapis.com/css?family=PT+Sans+Caption&subset=latin,cyrillic-ext | US | text | 180 b | whitelisted |
2940 | EXCEL.EXE | GET | 200 | 216.58.205.234:80 | http://fonts.googleapis.com/css?family=PT+Sans:400,700,400italic,700italic&subset=latin,cyrillic-ext | US | text | 162 b | whitelisted |
2940 | EXCEL.EXE | GET | 200 | 195.128.126.59:80 | http://www.dmaster.ru/css/colorbox.css?14568199964587 | RU | text | 1.50 Kb | unknown |
2940 | EXCEL.EXE | GET | 200 | 50.7.91.70:80 | http://www.dmaster.ru.opt-css.1c-bitrix-cdn.ru/bitrix/templates/dmaster_inner/template_styles.css?1553073474110 | DE | text | 105 b | suspicious |
2724 | iexplore.exe | GET | 200 | 195.128.126.59:80 | http://www.dmaster.ru/css/colorbox.css?14568199964587 | RU | text | 1.50 Kb | unknown |
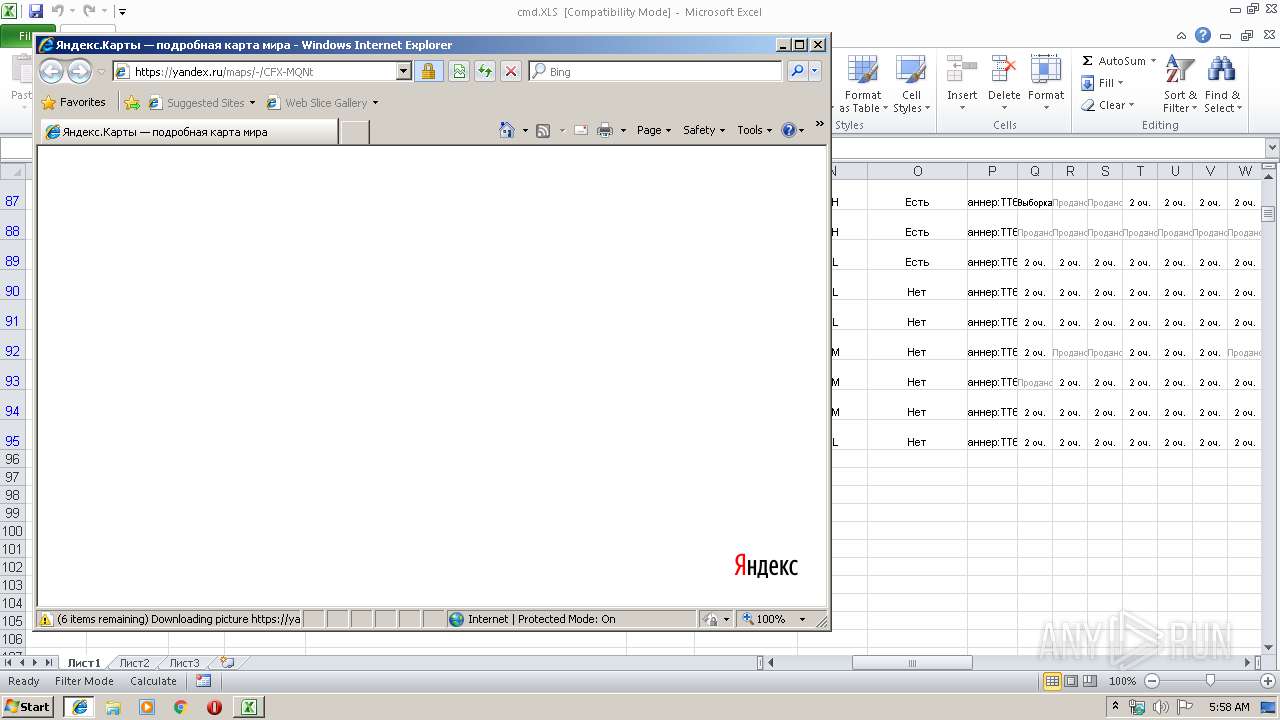
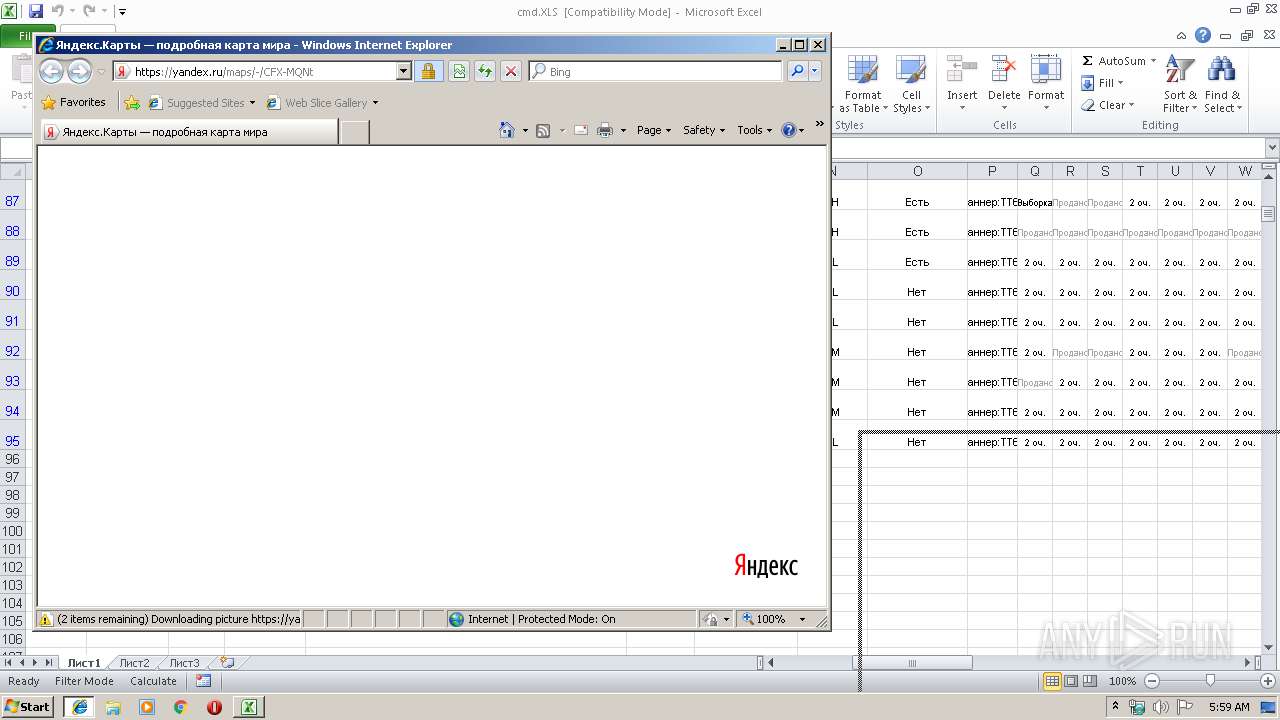
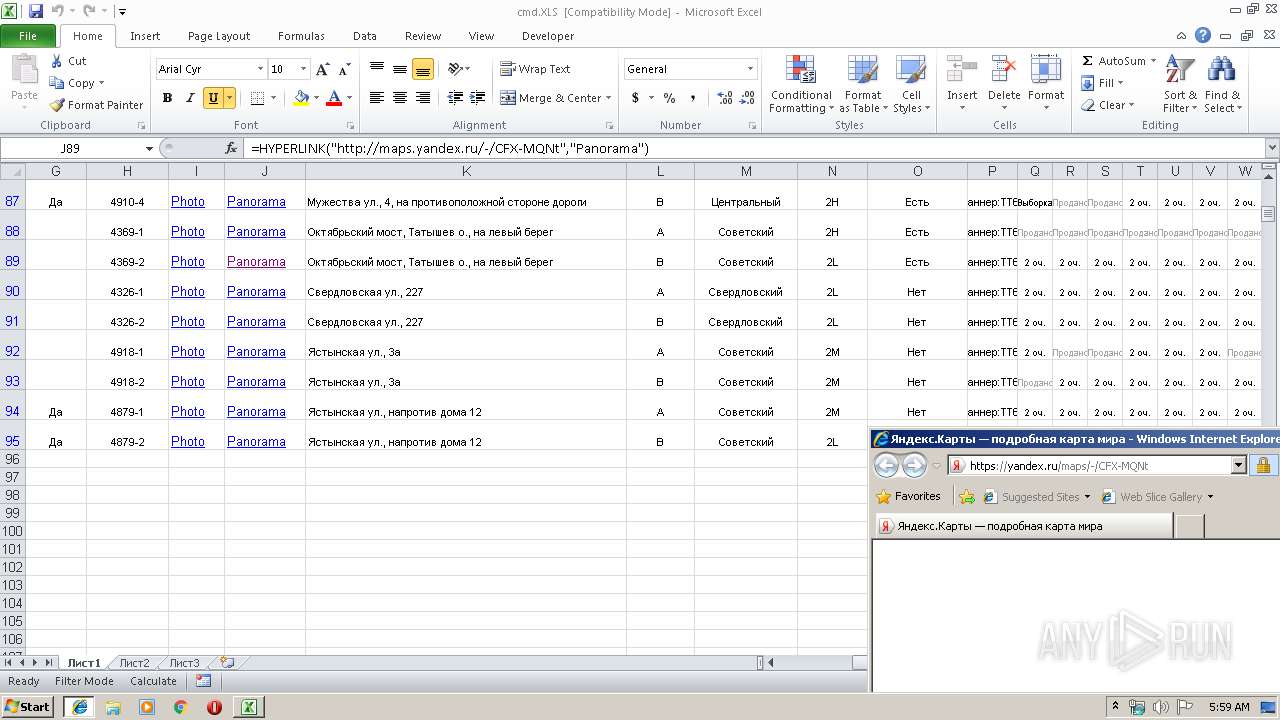
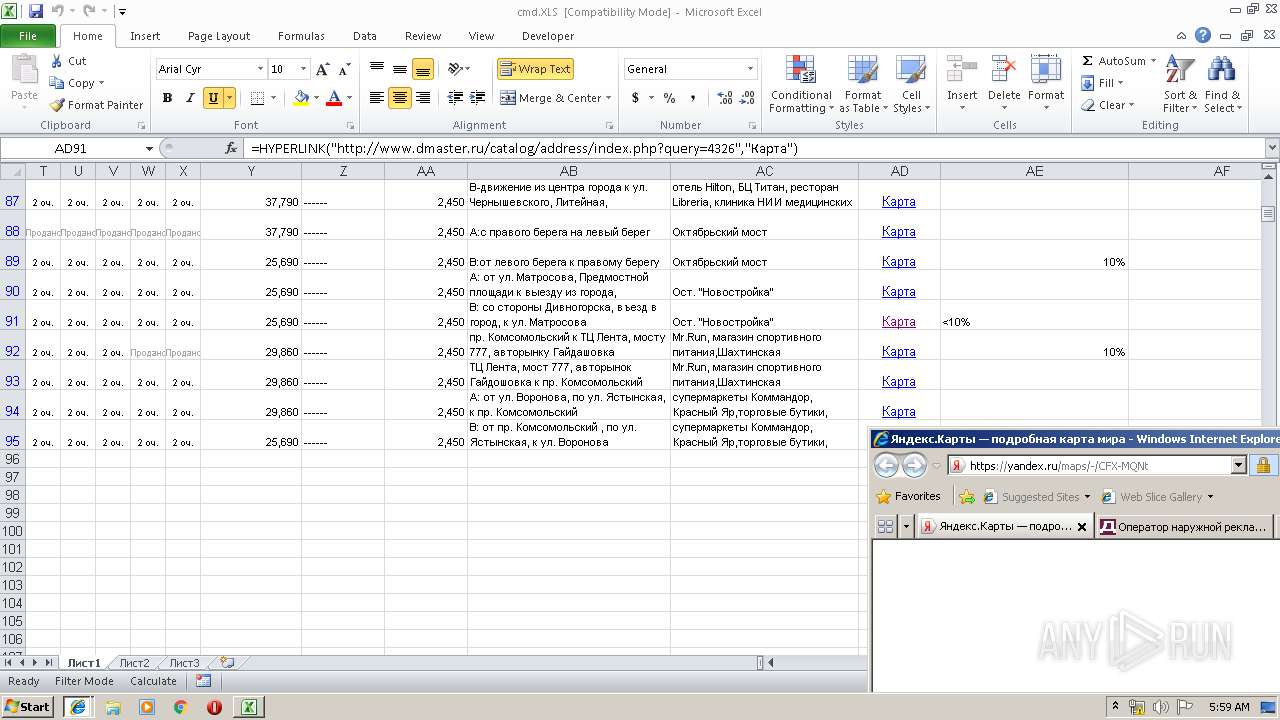
2940 | EXCEL.EXE | GET | 301 | 87.250.251.71:80 | http://maps.yandex.ru/-/CFX-MQNt | RU | html | 184 b | whitelisted |
2724 | iexplore.exe | GET | 200 | 216.58.205.234:80 | http://fonts.googleapis.com/css?family=PT+Sans+Caption&subset=latin,cyrillic-ext | US | text | 180 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | EXCEL.EXE | 77.88.55.70:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
2940 | EXCEL.EXE | 87.250.251.71:80 | maps.yandex.ru | YANDEX LLC | RU | whitelisted |
2288 | iexplore.exe | 77.88.55.70:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
2548 | iexplore.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2940 | EXCEL.EXE | 195.128.126.59:80 | www.dmaster.ru | Garant-Park-Internet Ltd | RU | unknown |
2548 | iexplore.exe | 87.250.250.254:443 | mc.admetrica.ru | YANDEX LLC | RU | whitelisted |
2940 | EXCEL.EXE | 50.7.91.70:80 | www.dmaster.ru.opt-css.1c-bitrix-cdn.ru | Cogent Communications | DE | unknown |
2940 | EXCEL.EXE | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2724 | iexplore.exe | 50.7.91.70:80 | www.dmaster.ru.opt-css.1c-bitrix-cdn.ru | Cogent Communications | DE | unknown |
2724 | iexplore.exe | 195.128.126.59:80 | www.dmaster.ru | Garant-Park-Internet Ltd | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
maps.yandex.ru |
| whitelisted |
yandex.ru |
| whitelisted |
www.bing.com |
| whitelisted |
api-maps.yandex.ru |
| whitelisted |
yastatic.net |
| whitelisted |
mc.yandex.ru |
| whitelisted |
yandex.st |
| whitelisted |
mc.admetrica.ru |
| unknown |
www.dmaster.ru |
| unknown |
fonts.googleapis.com |
| whitelisted |