| File name: | DiscordTokenNuker.exe |
| Full analysis: | https://app.any.run/tasks/13c05389-982b-4af5-920f-d6f7077364f7 |
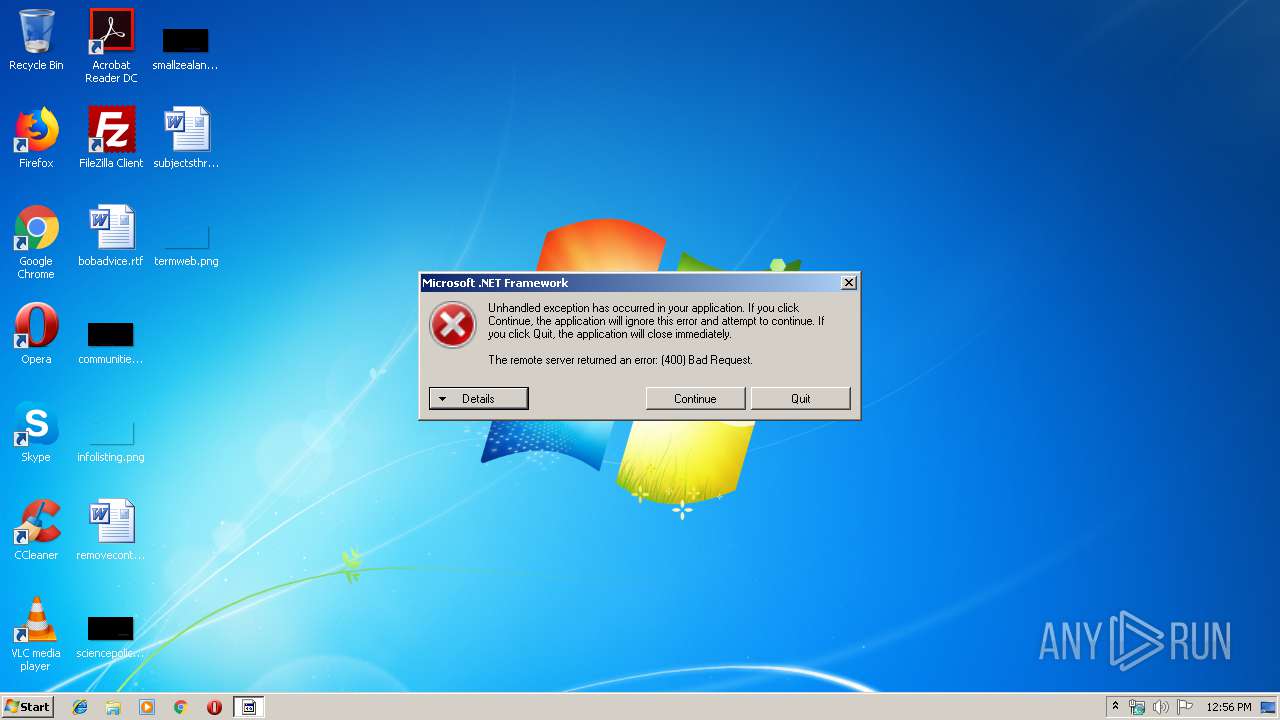
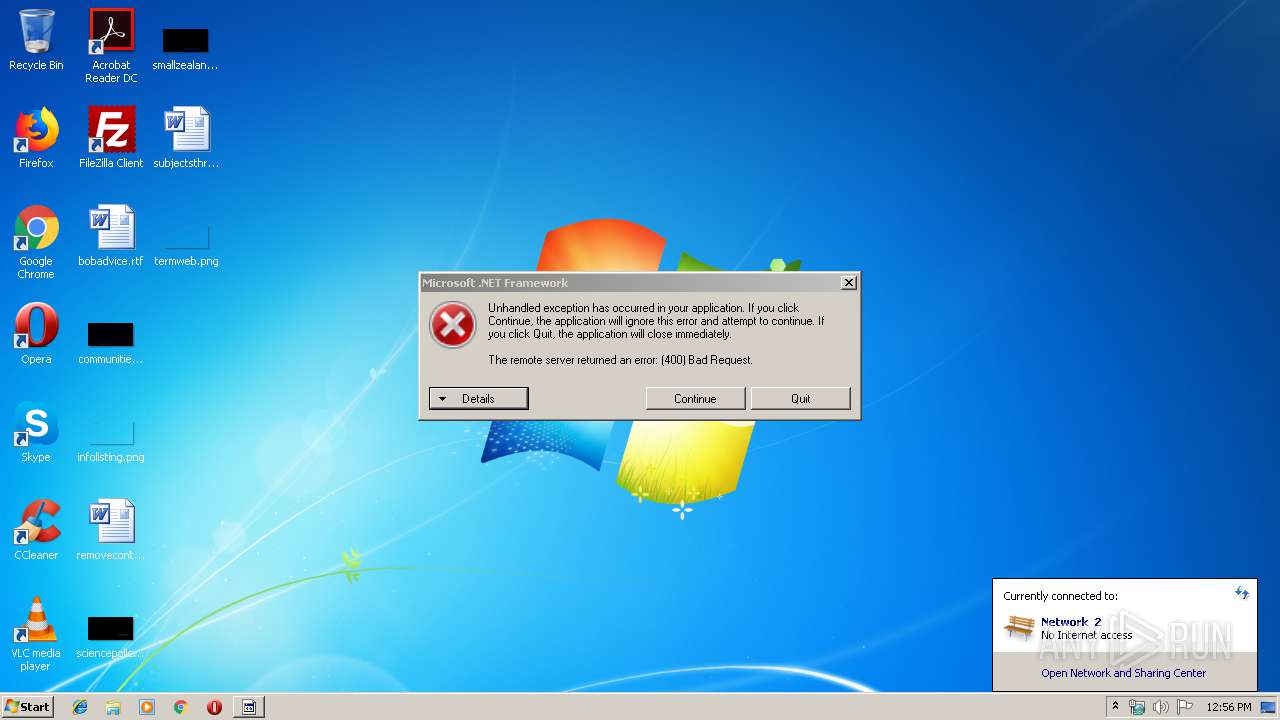
| Verdict: | Malicious activity |
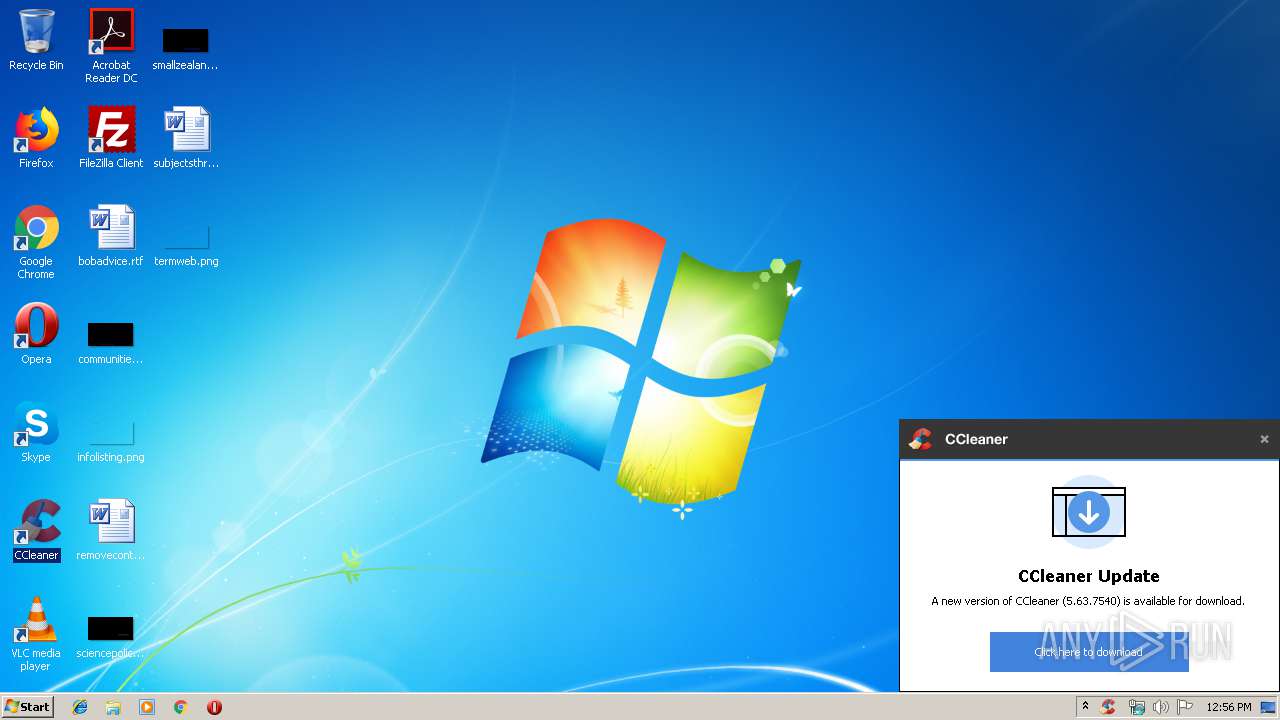
| Analysis date: | November 16, 2019, 12:56:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A0E733A848F1262CF197F85EB372FCD0 |
| SHA1: | C6A4BA7497001CD17AE51D808440FA18F8AC40EF |
| SHA256: | AEF600EFA72693E8060FCD86E97BABDAF9CAAAC80FC2AFC7A887A5D29B8E5CA0 |
| SSDEEP: | 192:i/EI4Emn3PkYzbxaFNQqp5XI5ZTkYauL+fstsxGwNtIW1YlH/+2UGTbvzrSMTftn:L4mTxGNQCuauLjtsxfNQH/+aTP+qftbL |
MALICIOUS
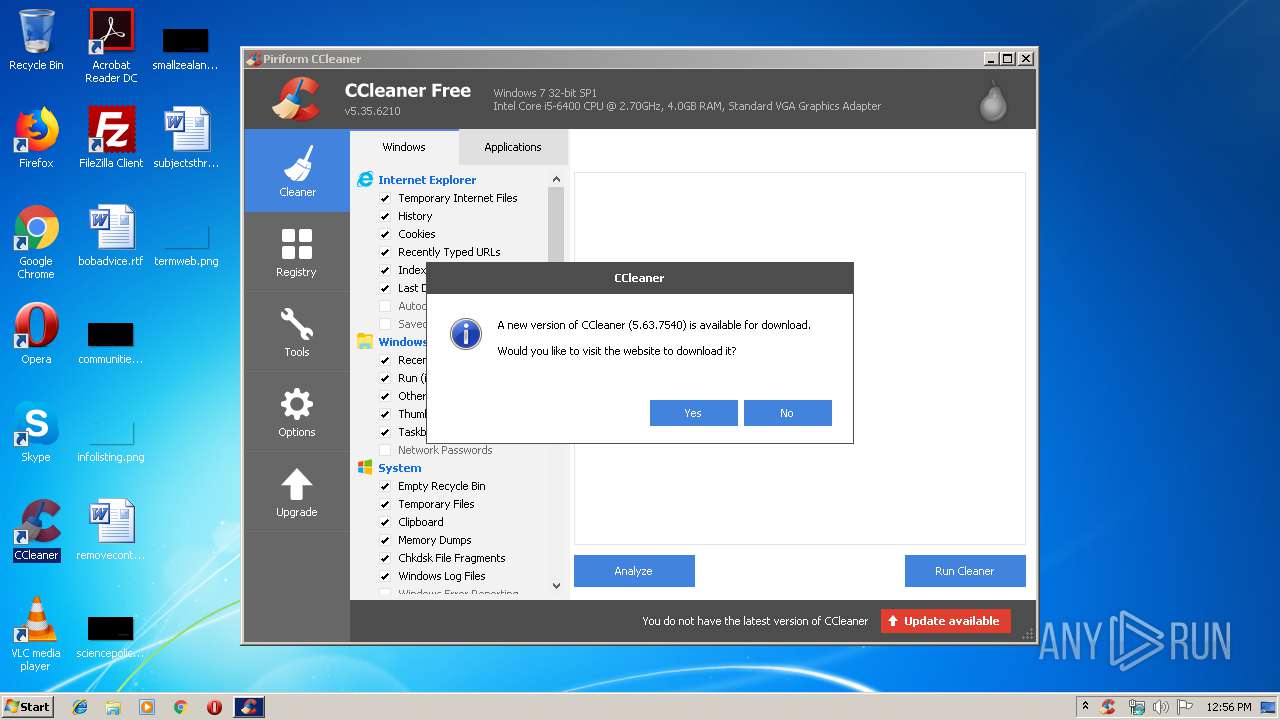
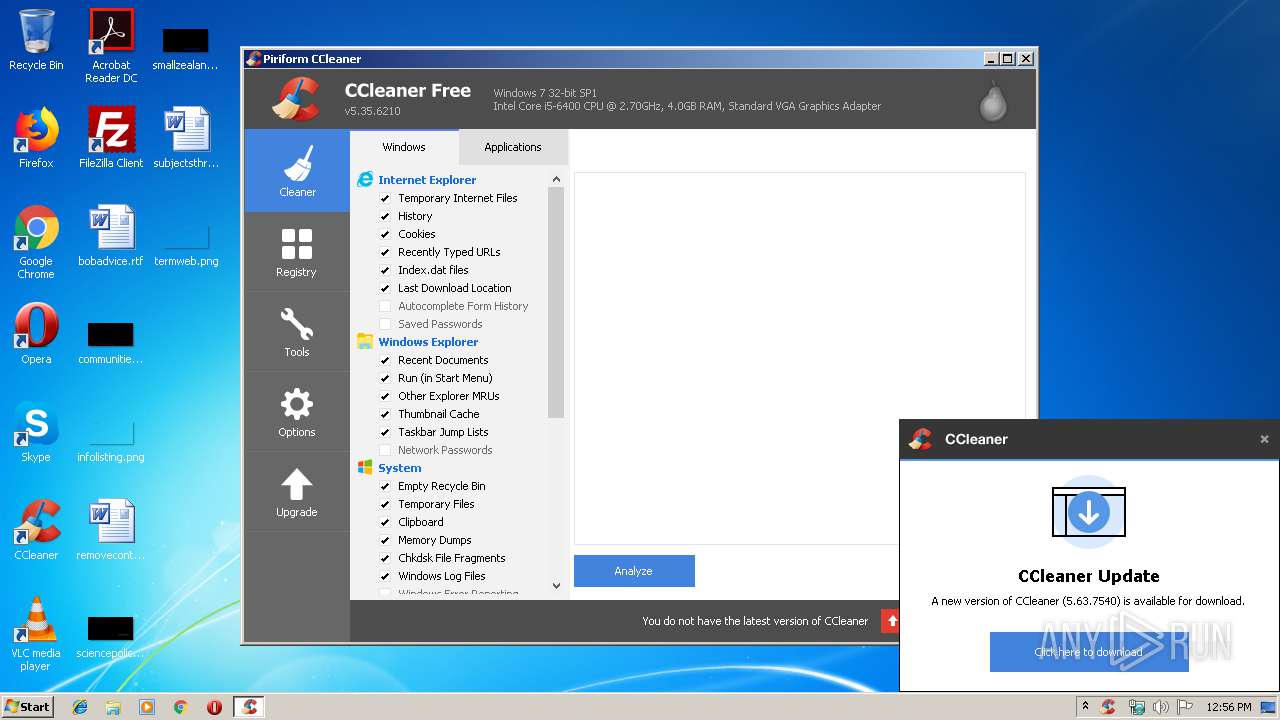
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 3820)
- CCleaner.exe (PID: 1764)
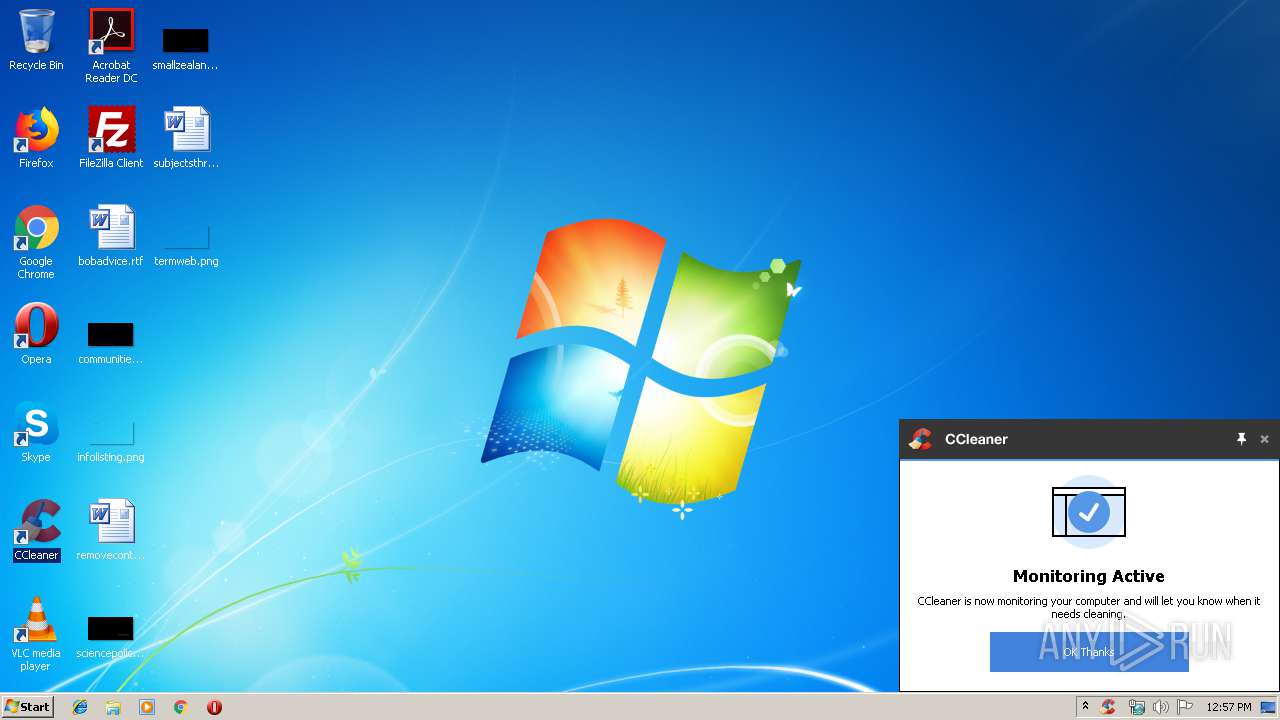
Actions looks like stealing of personal data
- CCleaner.exe (PID: 4080)
- CCleaner.exe (PID: 1764)
Changes the autorun value in the registry
- CCleaner.exe (PID: 1764)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 4080)
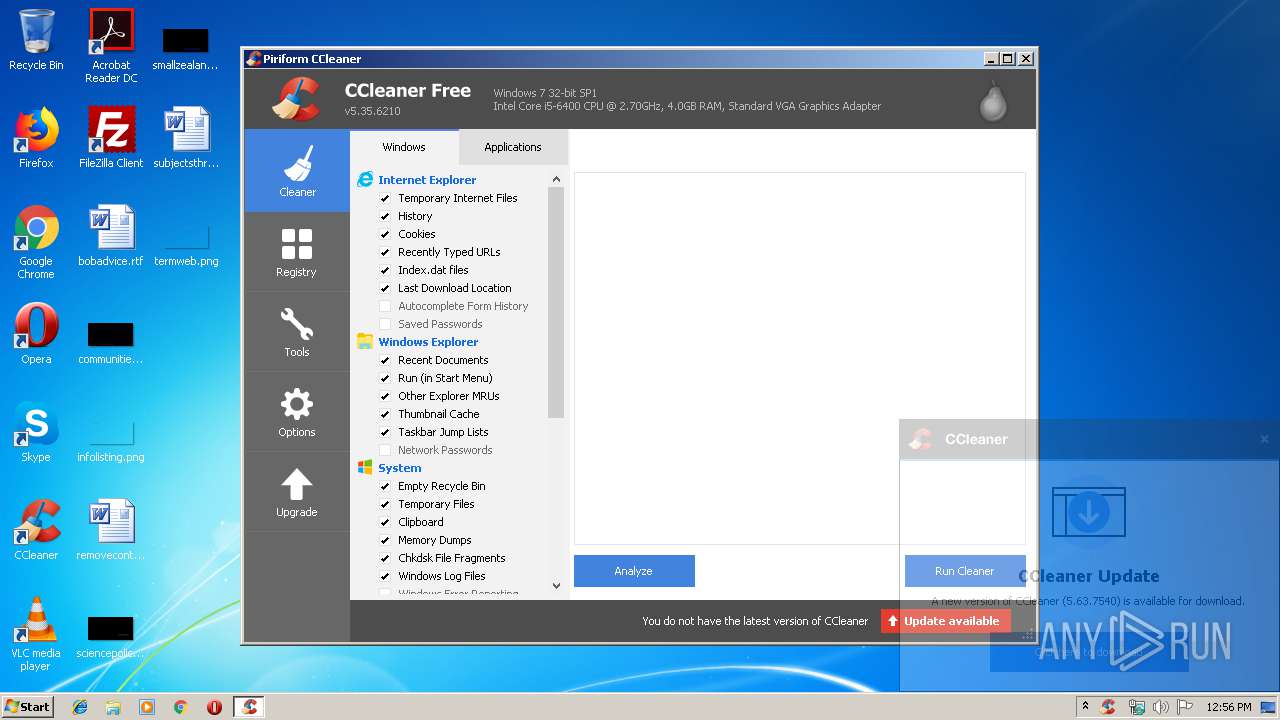
Executed via Task Scheduler
- CCleaner.exe (PID: 4080)
Reads internet explorer settings
- CCleaner.exe (PID: 4080)
- CCleaner.exe (PID: 1764)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 4080)
Creates files in the user directory
- CCleaner.exe (PID: 4080)
Application launched itself
- CCleaner.exe (PID: 4080)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 4080)
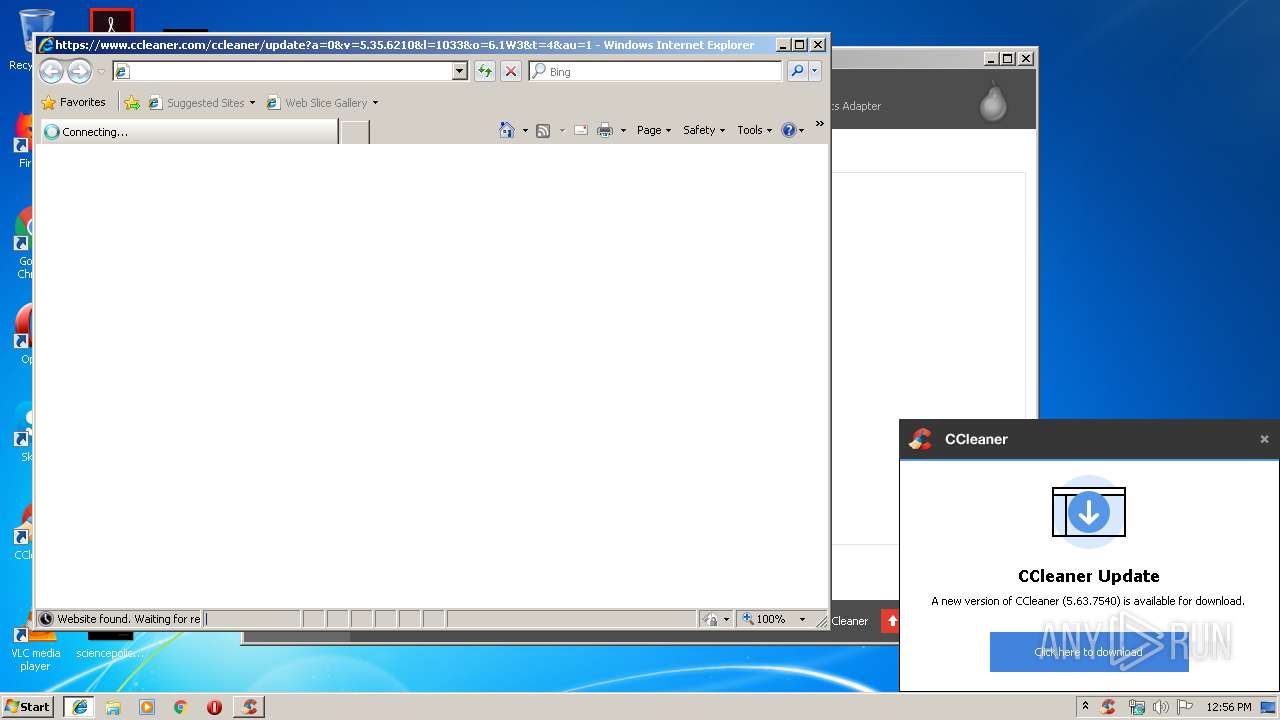
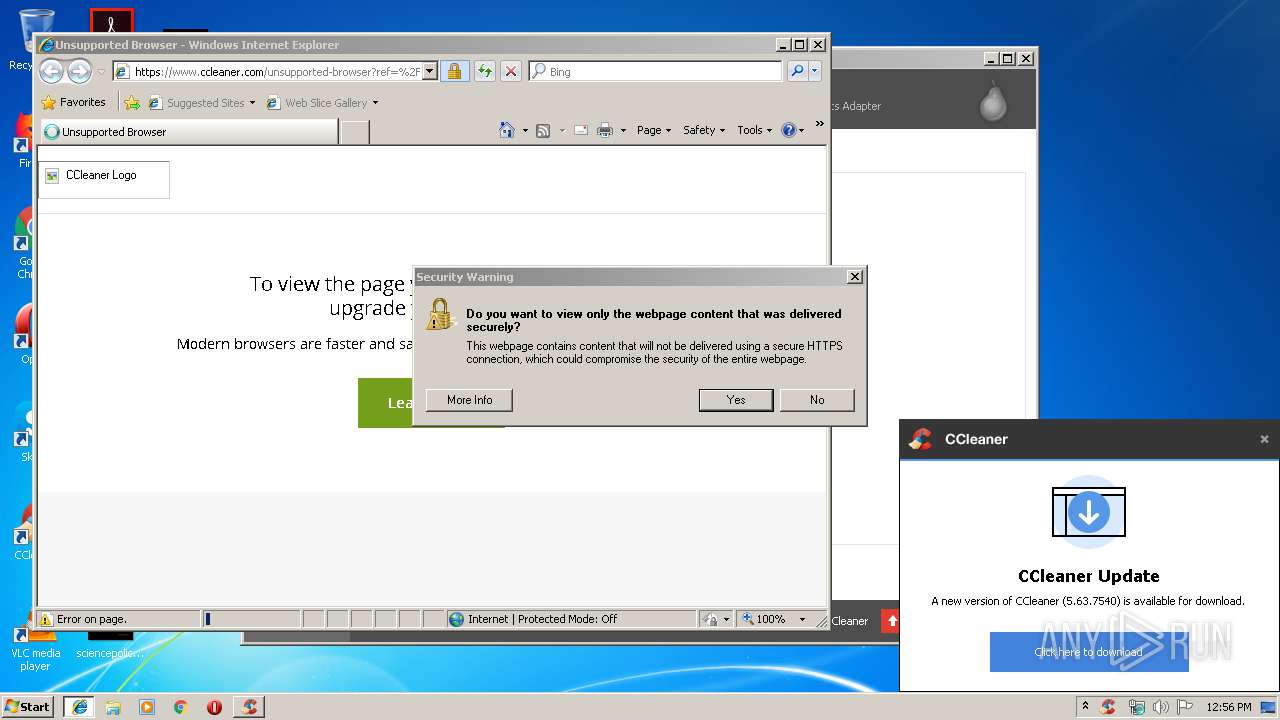
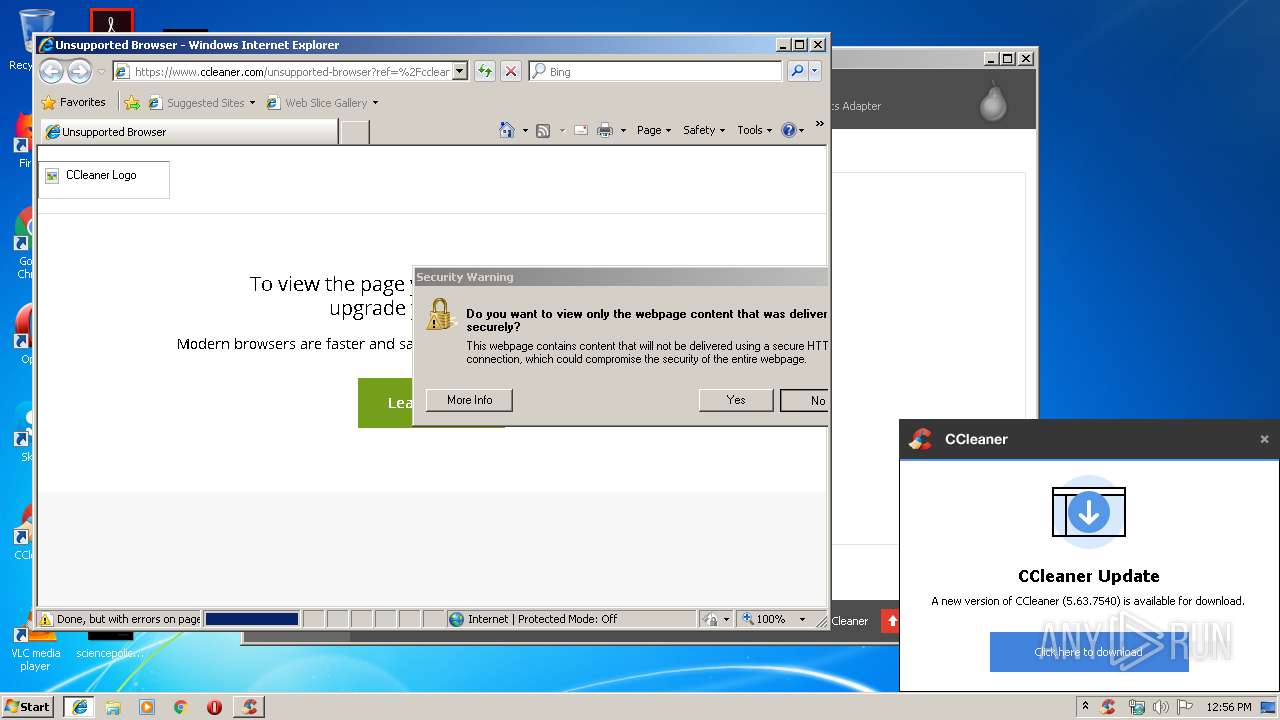
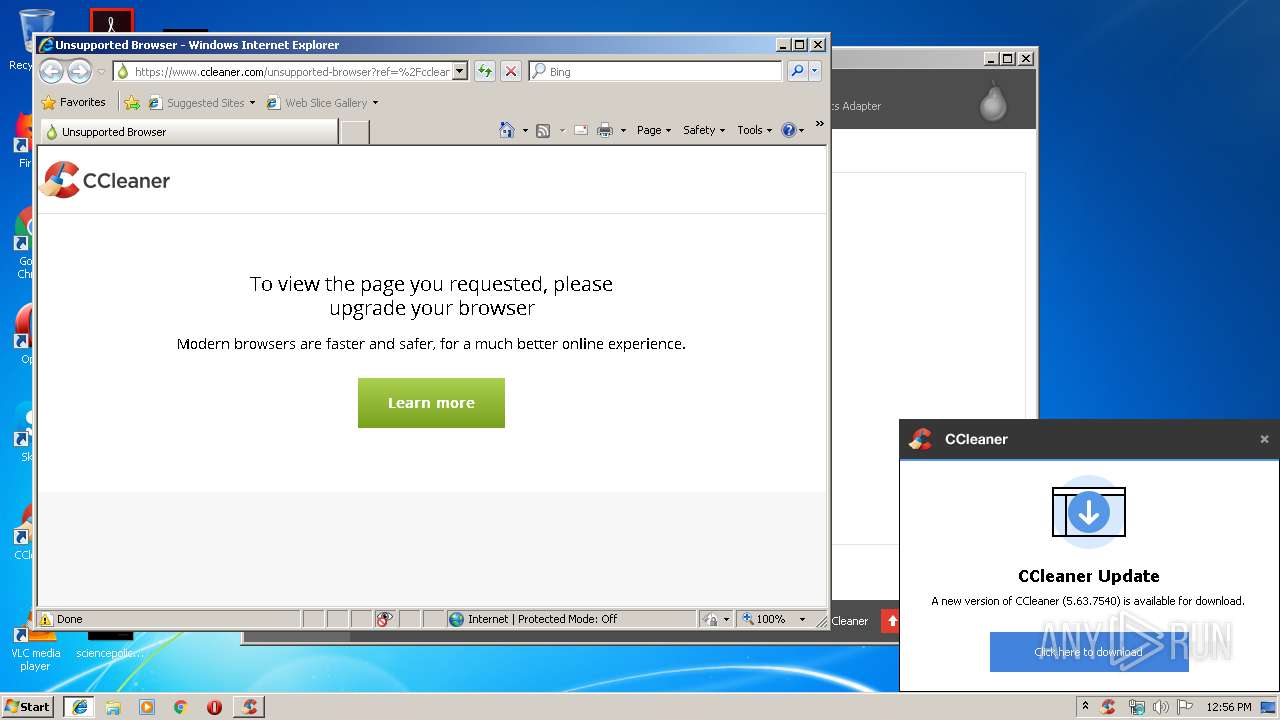
Starts Internet Explorer
- CCleaner.exe (PID: 4080)
INFO
Manual execution by user
- CCleaner.exe (PID: 3820)
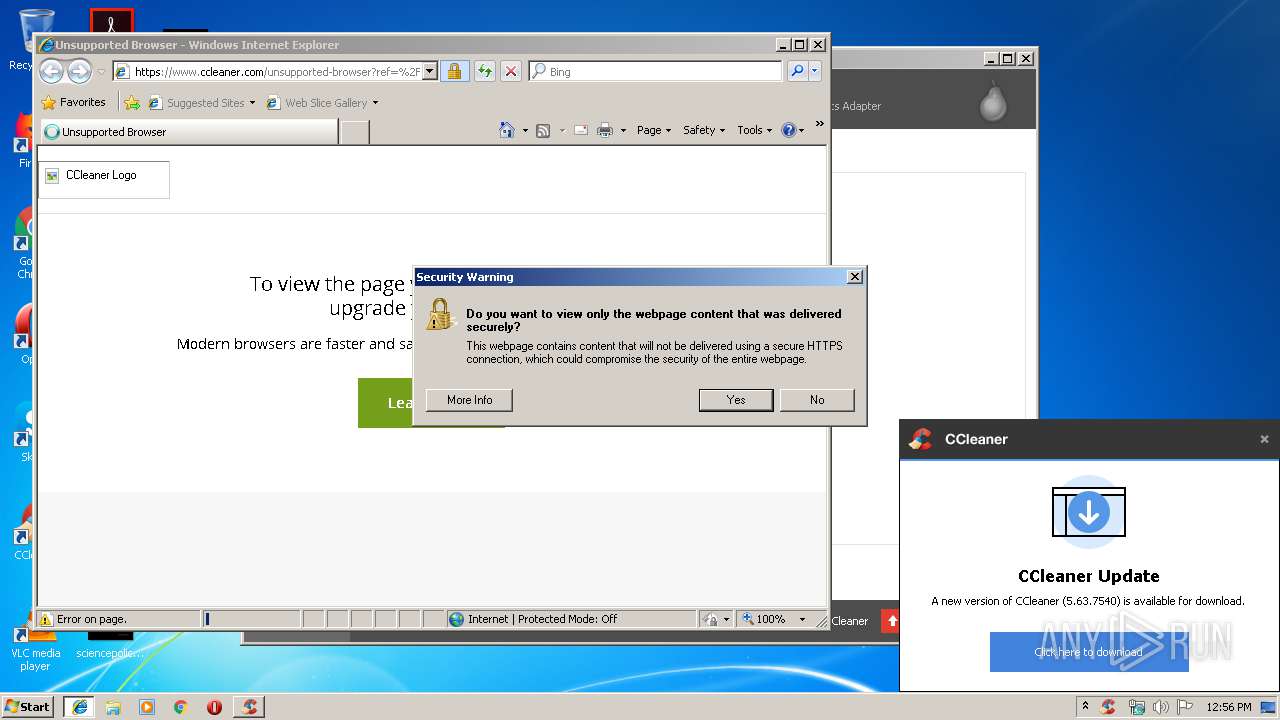
Reads Internet Cache Settings
- iexplore.exe (PID: 3028)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3028)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3028)
Changes settings of System certificates
- iexplore.exe (PID: 3028)
Reads settings of System Certificates
- iexplore.exe (PID: 3028)
- CCleaner.exe (PID: 4080)
Changes internet zones settings
- iexplore.exe (PID: 1600)
Creates files in the user directory
- iexplore.exe (PID: 3028)
Reads internet explorer settings
- iexplore.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2084:08:07 15:41:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 12288 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4e92 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | MVSV |
| FileVersion: | 1.0.0.0 |
| InternalName: | MVSV.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | MVSV.exe |
| ProductName: | MVSV |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Jul-1948 07:13:22 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | MVSV |
| FileVersion: | 1.0.0.0 |
| InternalName: | MVSV.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | MVSV.exe |
| ProductName: | MVSV |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Jul-1948 07:13:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00002E98 | 0x00003000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.68316 |
.rsrc | 0x00006000 | 0x0000058C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.02343 |
.reloc | 0x00008000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Users\admin\AppData\Local\Temp\DiscordTokenNuker.exe" | C:\Users\admin\AppData\Local\Temp\DiscordTokenNuker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MVSV Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | CCleaner.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
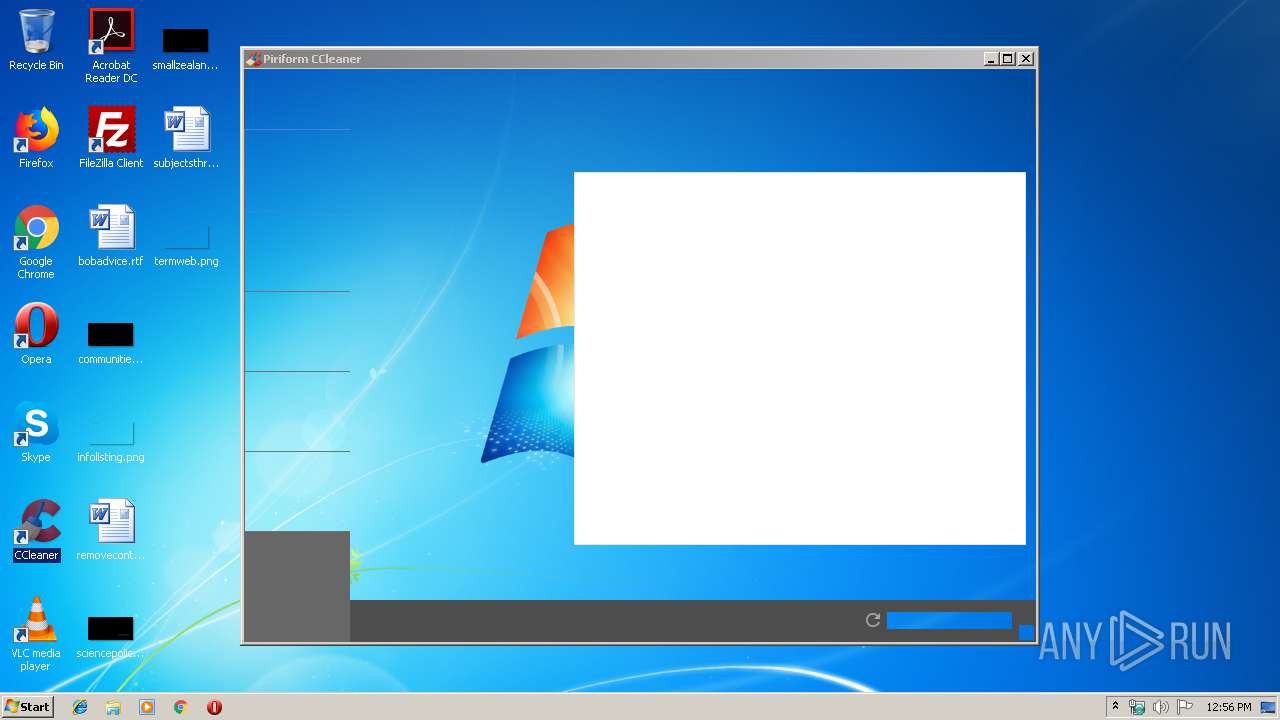
| 1764 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1600 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 3221225547 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3820 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 4080 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
Total events
1 065
Read events
751
Write events
311
Delete events
3
Modification events
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (960) DiscordTokenNuker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DiscordTokenNuker_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
10
Text files
28
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4080 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 4080 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LJPXWGAOPPPKYFS0LX91.temp | — | |
MD5:— | SHA256:— | |||
| 4080 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1QBSSZX3B15BTIIZQ9D8.temp | — | |
MD5:— | SHA256:— | |||
| 4080 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\02UTYJX8ODMIZTXZ9MRN.temp | — | |
MD5:— | SHA256:— | |||
| 1600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\standard[1].txt | — | |
MD5:— | SHA256:— | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab3752.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar3753.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | iexplore.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/ccleaner/update?a=0&v=5.35.6210&l=1033&o=6.1W3&t=4&au=1 | US | — | — | whitelisted |
4080 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
3028 | iexplore.exe | GET | 200 | 151.139.237.73:80 | http://s1.pir.fm/pf/logos--DA8LAgMPCAQ/ccleaner-logo--small.jpg | US | image | 6.34 Kb | suspicious |
1600 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3028 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
4080 | CCleaner.exe | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
4080 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
3028 | iexplore.exe | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
3028 | iexplore.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
1600 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3028 | iexplore.exe | 172.217.22.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3028 | iexplore.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3028 | iexplore.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3028 | iexplore.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
discordapp.com |
| whitelisted |
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
dev.visualwebsiteoptimizer.com |
| whitelisted |
s1.pir.fm |
| suspicious |