| File name: | Iostream.exe |
| Full analysis: | https://app.any.run/tasks/c18f8762-91df-45c9-b238-60319e0898aa |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 13:43:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8A23F732481FA4D1AB3322B0AB6D1CD3 |
| SHA1: | 57431747E37DA8EB687F82B0FC32511FB83220AB |
| SHA256: | AEED751E77E3A58D908638BBAF2DF2E2D39F05103DA12F982D9400C67BD78583 |
| SSDEEP: | 24576:U+gLjOb5a6y887m6opvv/qOj4L741psF36yg8xYZ:vUyPy88mfP7j0zZ |
MALICIOUS
Uses Task Scheduler to run other applications
- Iostream.exe (PID: 1080)
- Iostream.exe (PID: 3520)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2456)
- schtasks.exe (PID: 2268)
Runs app for hidden code execution
- Iostream.exe (PID: 1080)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- Iostream.exe (PID: 1080)
Executable content was dropped or overwritten
- Iostream.exe (PID: 1080)
- Iostream.exe (PID: 3520)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3388)
Creates files in the user directory
- WINWORD.EXE (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:06 14:21:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 160768 |
| InitializedDataSize: | 678912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x286000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2018 12:21:50 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 06-Apr-2018 12:21:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x000CC000 | 0x0005B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98822 | |
.rsrc | 0x000CD000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.49012 |
.idata | 0x000CE000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.30872 |
0x000CF000 | 0x00103000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.260771 | |
vpxwflbh | 0x001D2000 | 0x000B4000 | 0x000B3C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9233 |
dqbhgykr | 0x00286000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.52206 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
comctl32.dll |
kernel32.dll |
Total processes
43
Monitored processes
7
Malicious processes
0
Suspicious processes
1
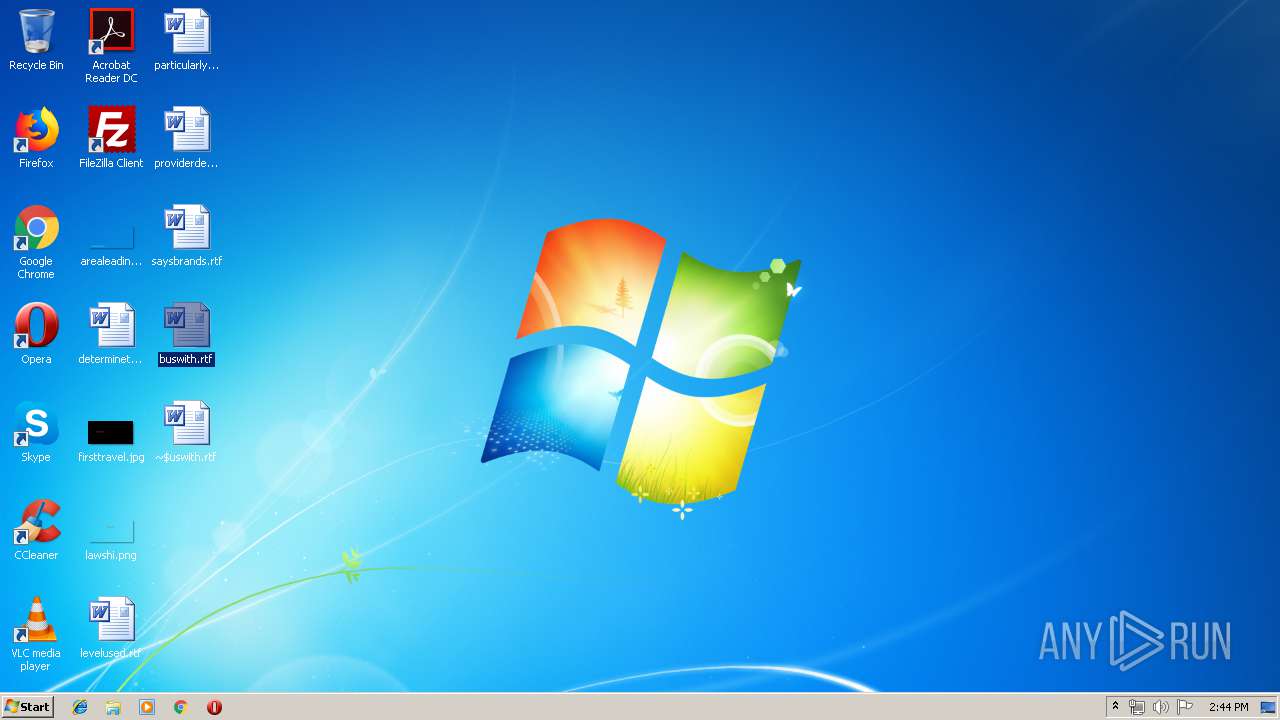
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\AppData\Local\Temp\Iostream.exe" | C:\Users\admin\AppData\Local\Temp\Iostream.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2268 | schtasks /create /tn WindowsRecoveryCleaner /tr "C:\ProgramData\Iostream.exe" /st 00:00 /sc daily /du 9999:59 /ri 1 /f | C:\Windows\system32\schtasks.exe | — | Iostream.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | schtasks /create /tn WindowsRecoveryCleaner /tr "C:\ProgramData\Iostream.exe" /st 00:00 /sc daily /du 9999:59 /ri 1 /f | C:\Windows\system32\schtasks.exe | — | Iostream.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
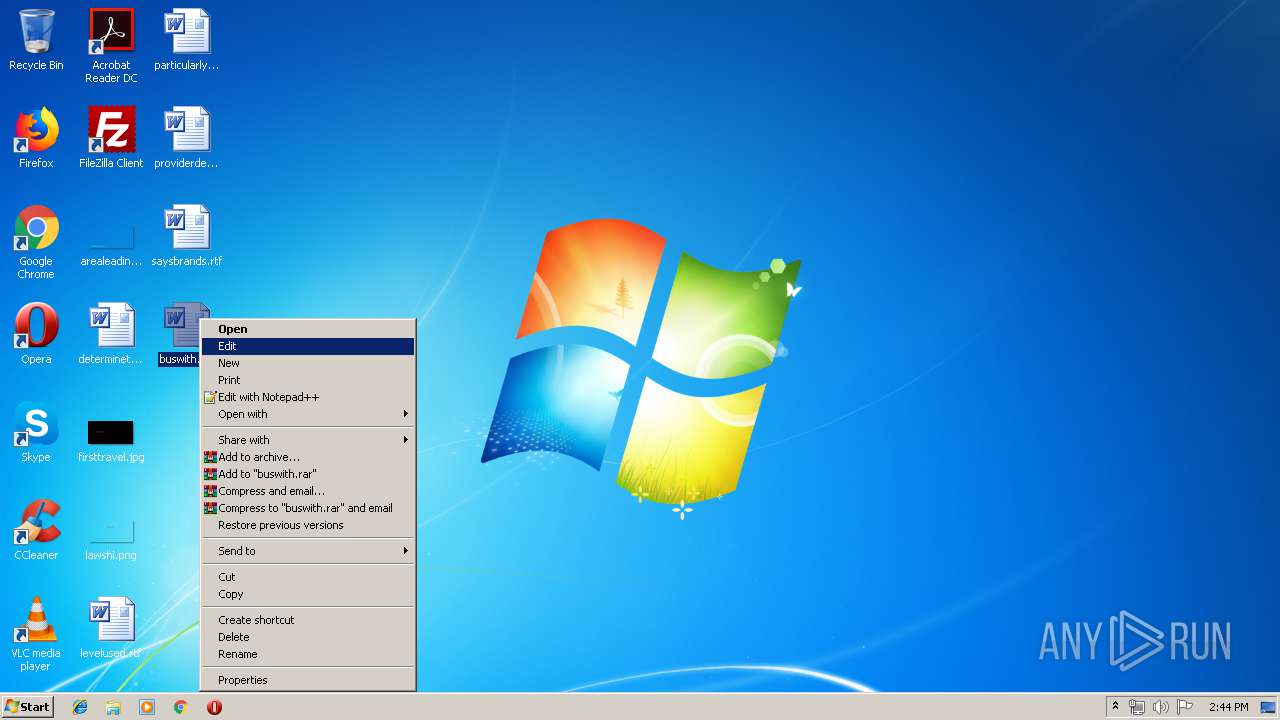
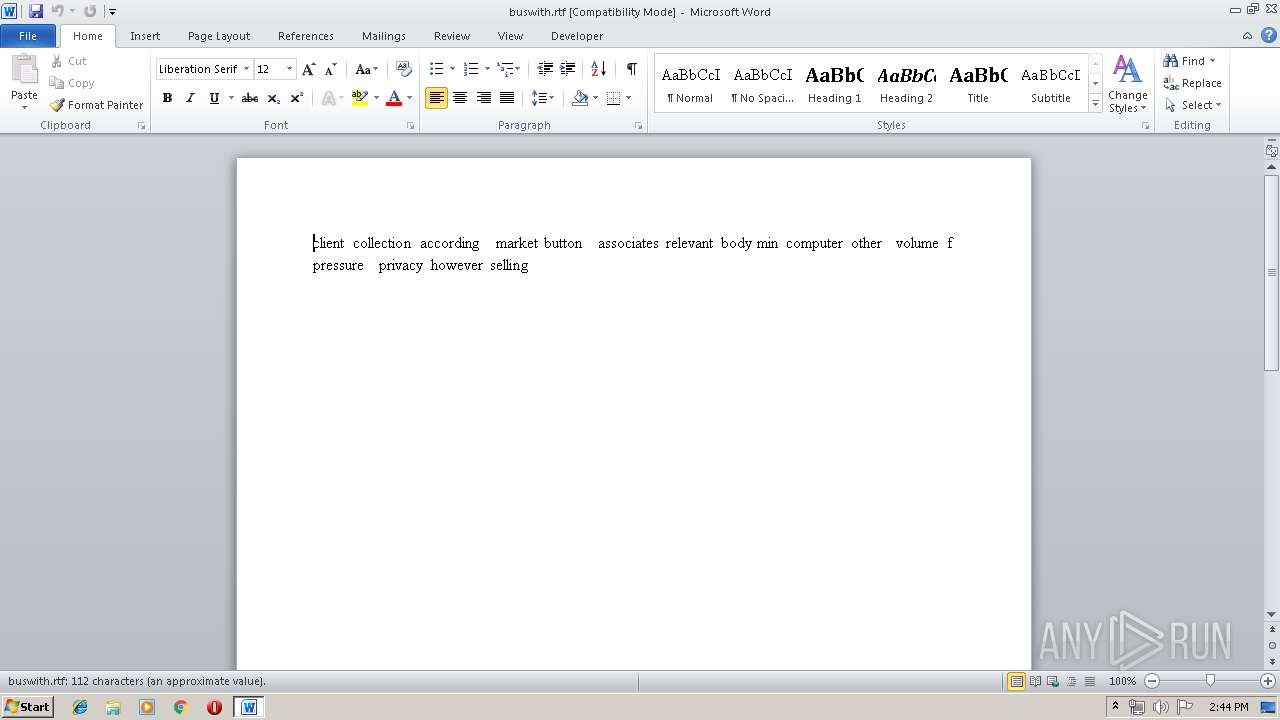
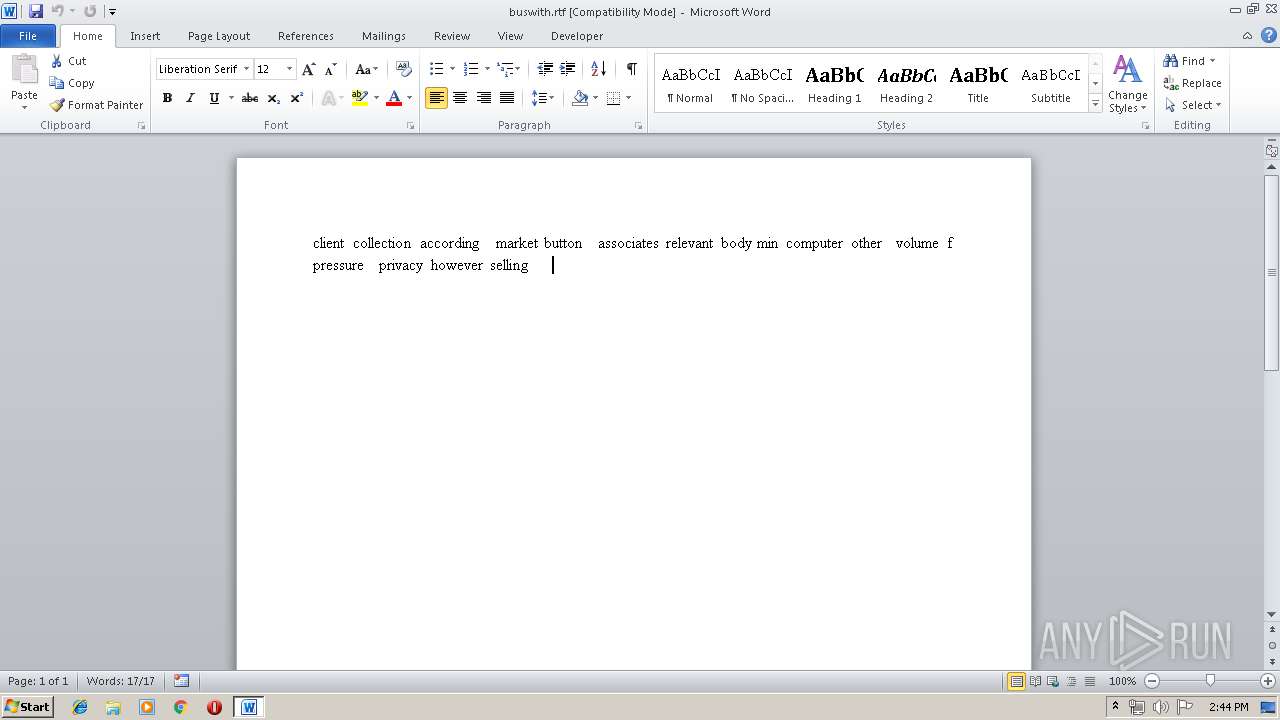
| 3388 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\buswith.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3520 | C:\ProgramData\Iostream.exe | C:\ProgramData\Iostream.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 9 Modules
| |||||||||||||||
| 3668 | "C:\Windows\System32\attrib.exe" | C:\Windows\System32\attrib.exe | Iostream.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
738
Read events
680
Write events
47
Delete events
11
Modification events
| (PID) Process: | (912) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (912) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {%5 |
Value: 7B2535003C0D0000010000000000000000000000 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318649887 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650000 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650001 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 3C0D0000AE5193006DFBD40100000000 | |||
| (PID) Process: | (3388) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >'5 |
Value: 3E2735003C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR116C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{485E50D0-BA79-4B03-B8BA-082F010035BB}.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{32EB6166-9CDE-4BA0-9BD4-3224EB5FDF22}.tmp | — | |
MD5:— | SHA256:— | |||
| 1080 | Iostream.exe | C:\ProgramData\Iostream.exe | executable | |
MD5:— | SHA256:— | |||
| 3520 | Iostream.exe | C:\ProgramData\Iostream.exe | executable | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\Desktop\~$uswith.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\buswith.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3388 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3668 | attrib.exe | 78.155.199.111:3333 | — | HLL LLC | RU | unknown |
DNS requests
Threats
Process | Message |
|---|---|
Iostream.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
Iostream.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|