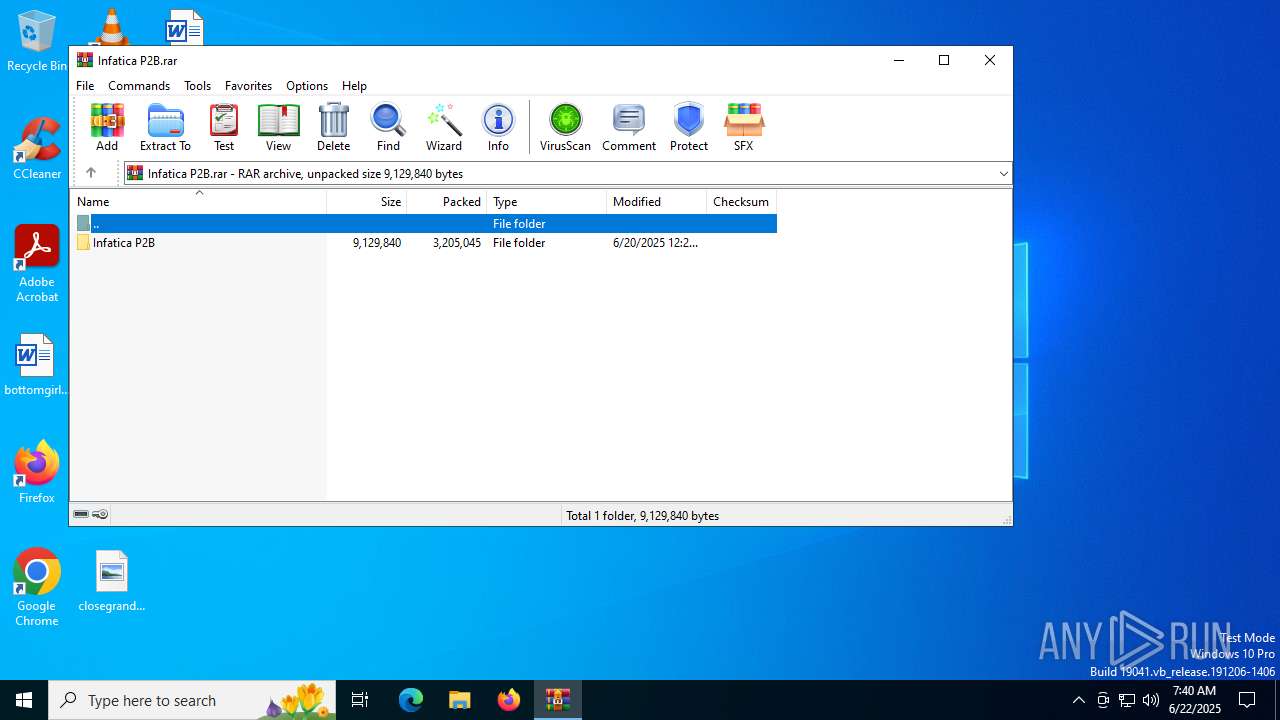
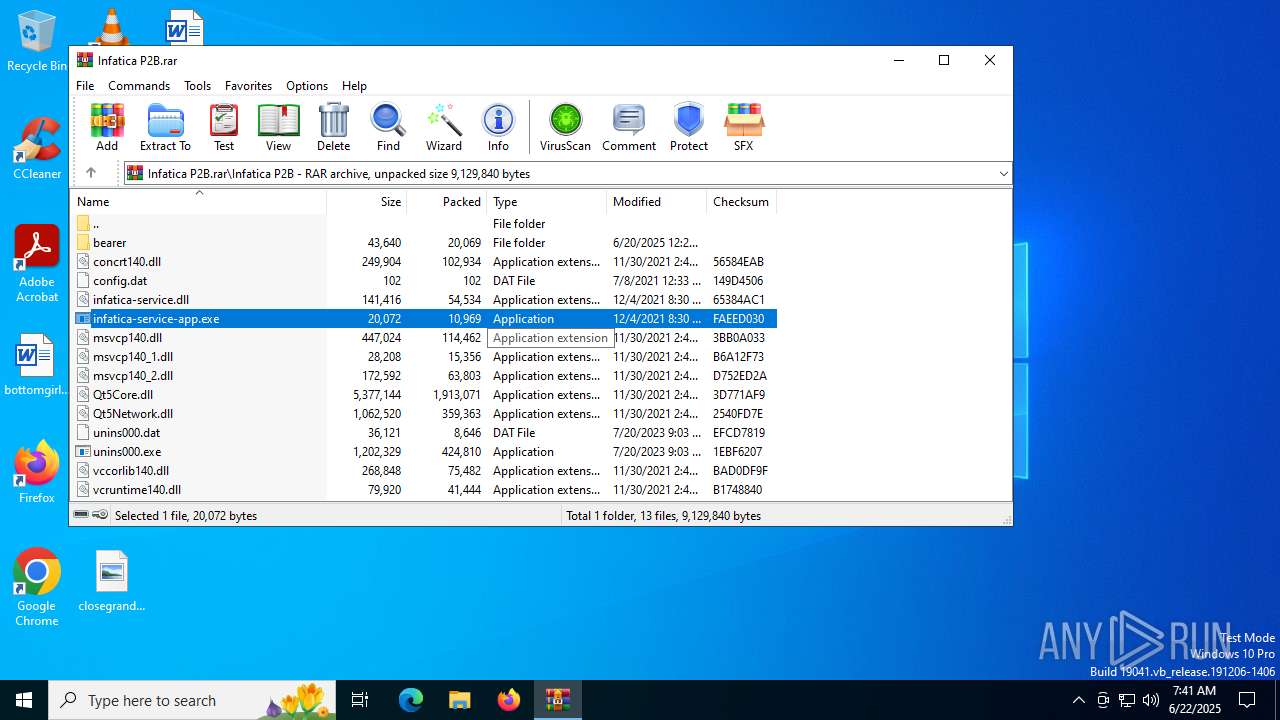
| File name: | Infatica P2B.rar |
| Full analysis: | https://app.any.run/tasks/8d179f7c-e9ee-4ad7-ad14-b9e92c329fc9 |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2025, 07:40:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A9D74A0ED6D46E5531DC980091140BDB |
| SHA1: | FABA366E008EAE07B21314A57B24C3B431097D37 |
| SHA256: | AEE70E50638B79F410BDCA412763F51AEE6AB78F5EA77D47329B93D61705A7DC |
| SSDEEP: | 98304:bBGGe/sXU1Yvjuo9AwRLGEF9syaesa6HPUNrRNYlIzyClAEjBn91AvLss6V6PDKB:4GvtT |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6508)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6508)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6508)
Connects to unusual port
- infatica-service-app.exe (PID: 304)
INFO
Checks supported languages
- infatica-service-app.exe (PID: 304)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6508)
Reads the computer name
- infatica-service-app.exe (PID: 304)
Checks proxy server information
- infatica-service-app.exe (PID: 304)
The sample compiled with english language support
- WinRAR.exe (PID: 6508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 20069 |
| UncompressedSize: | 43640 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Infatica P2B/bearer/qgenericbearer.dll |
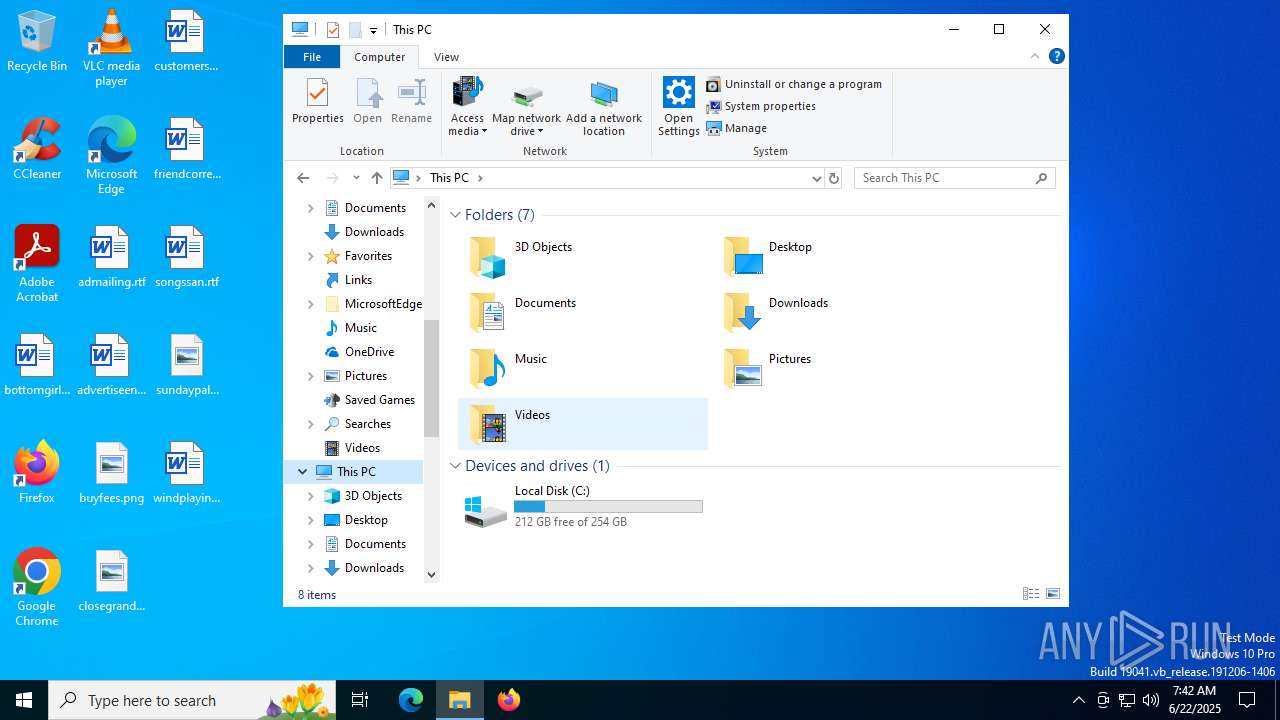
Total processes
140
Monitored processes
4
Malicious processes
0
Suspicious processes
1
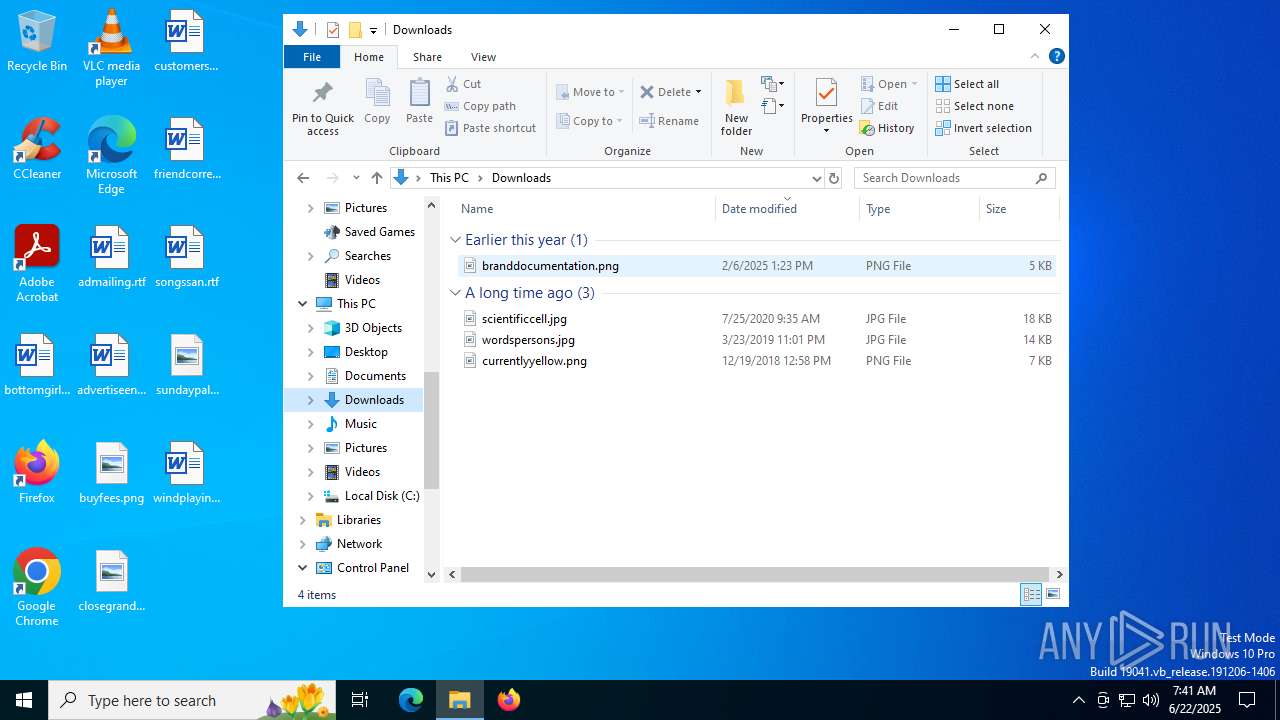
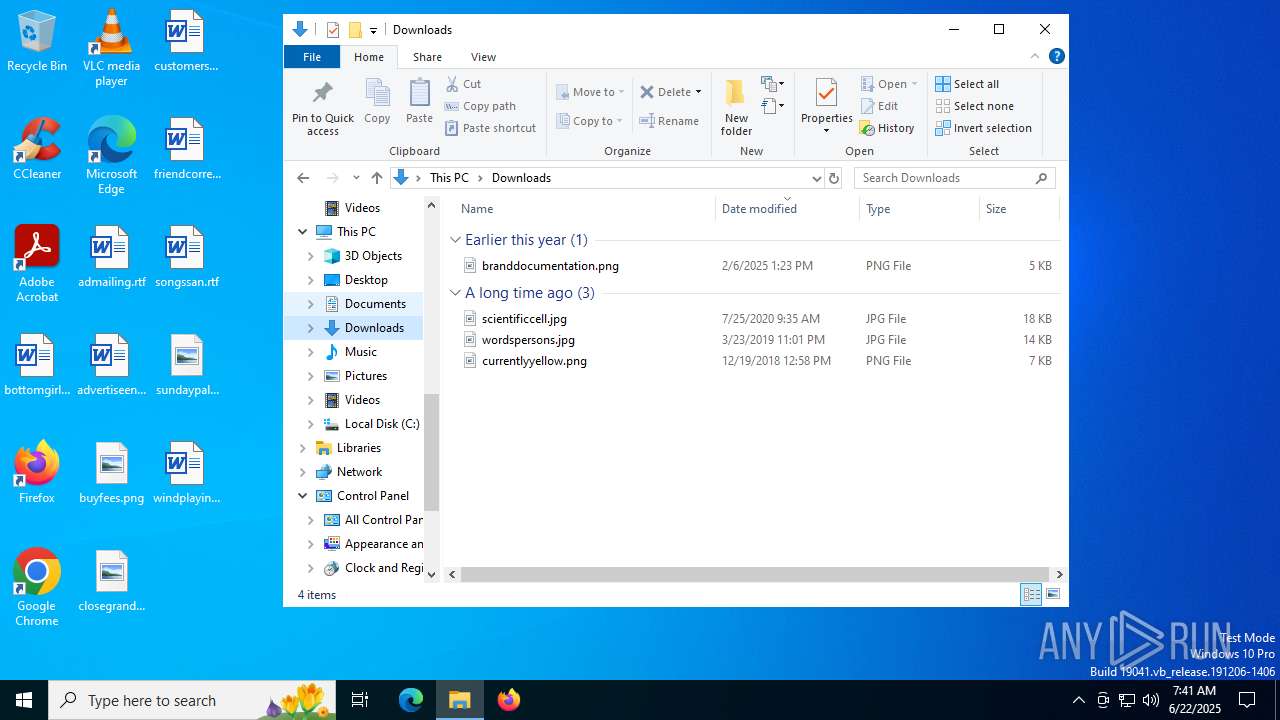
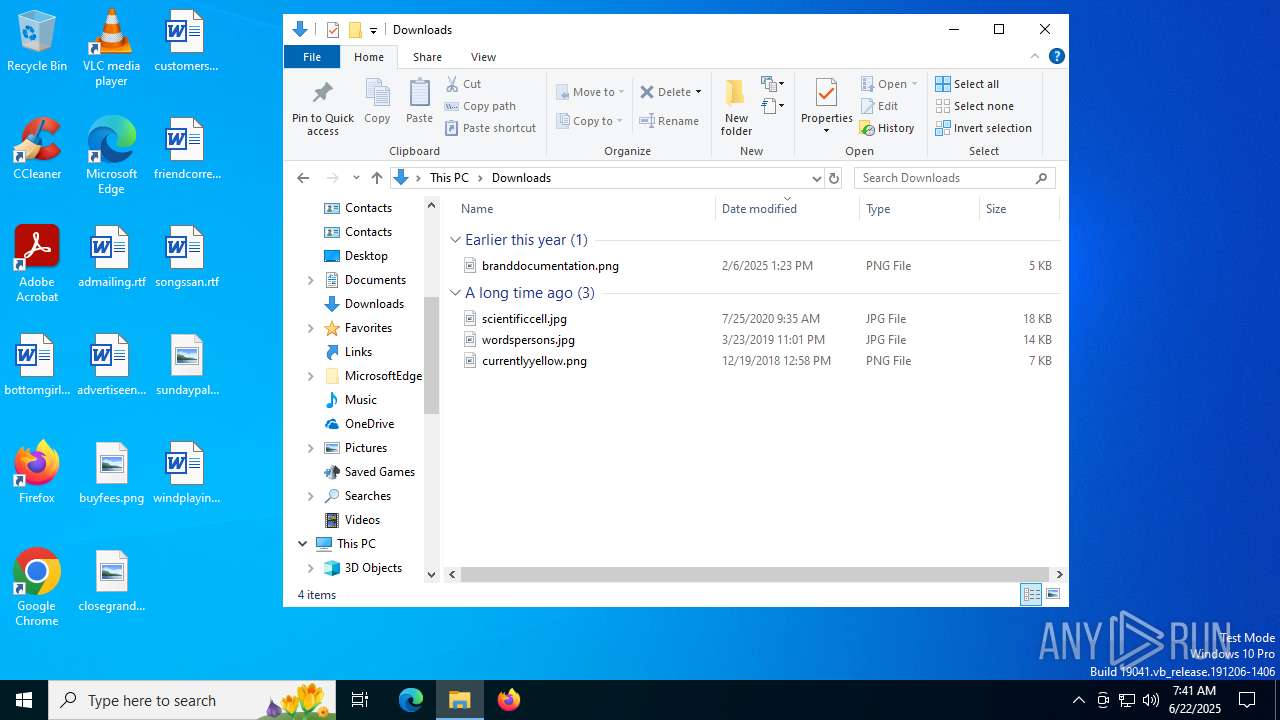
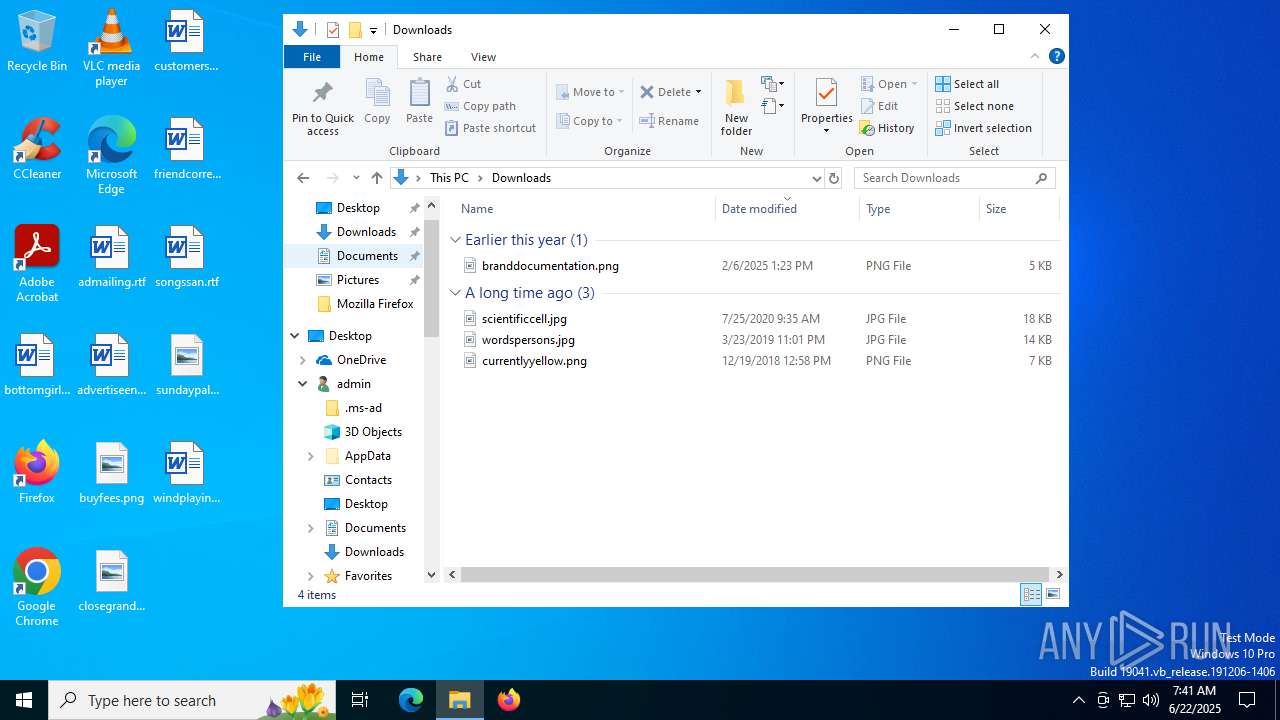
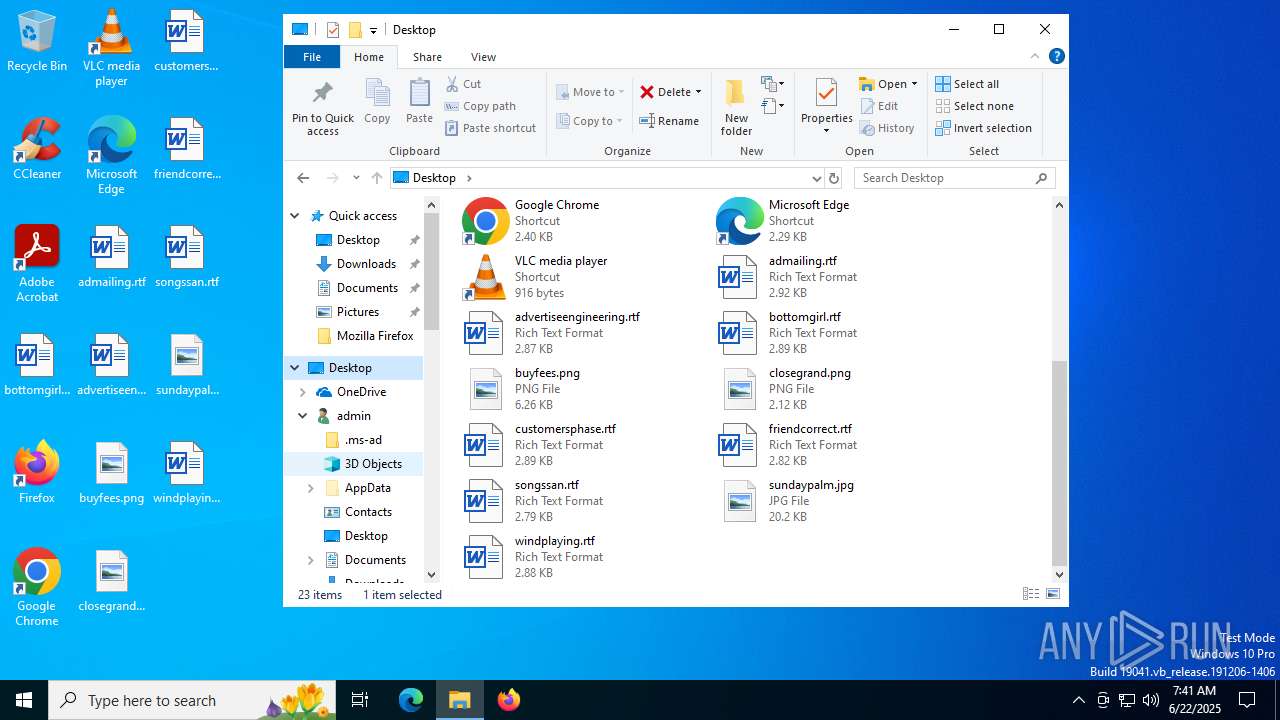
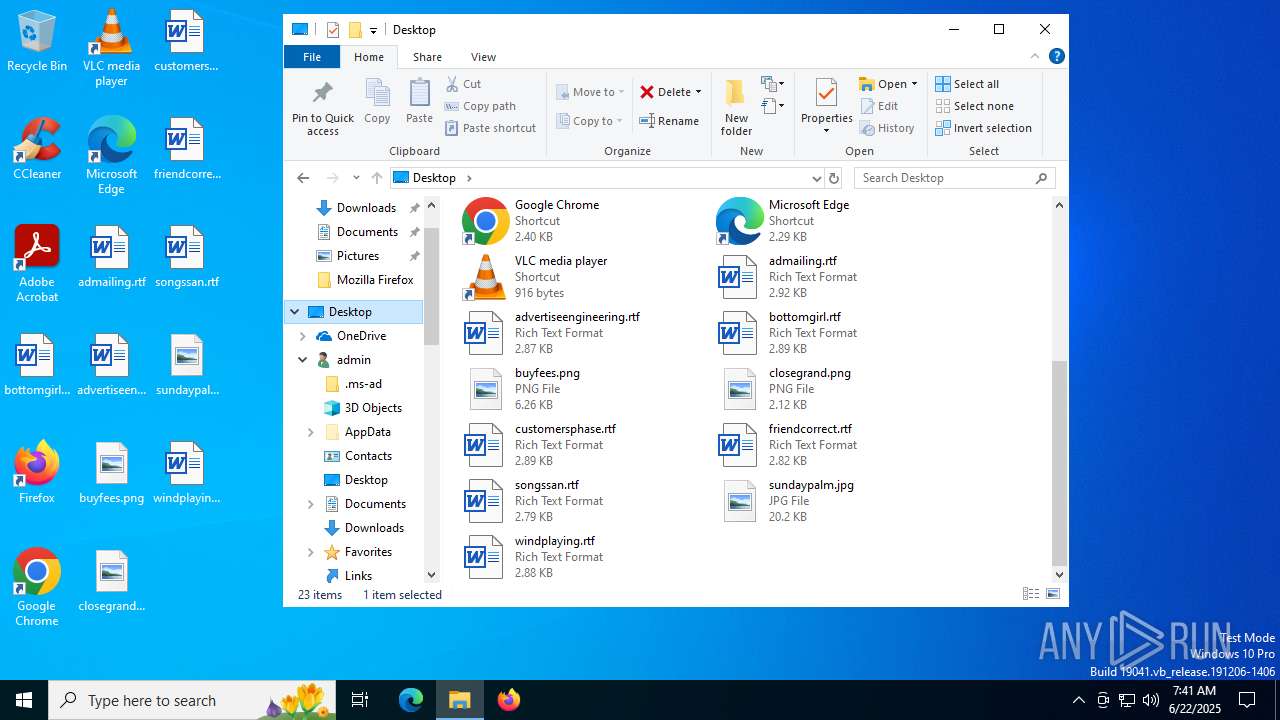
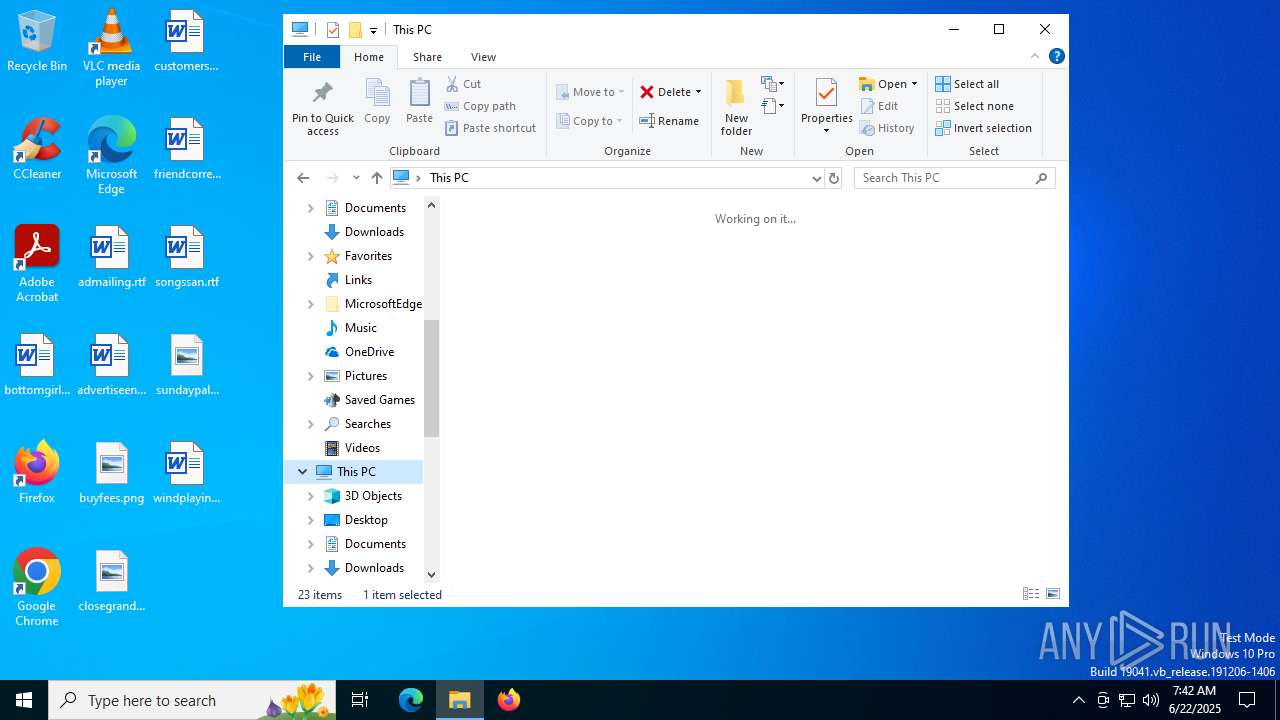
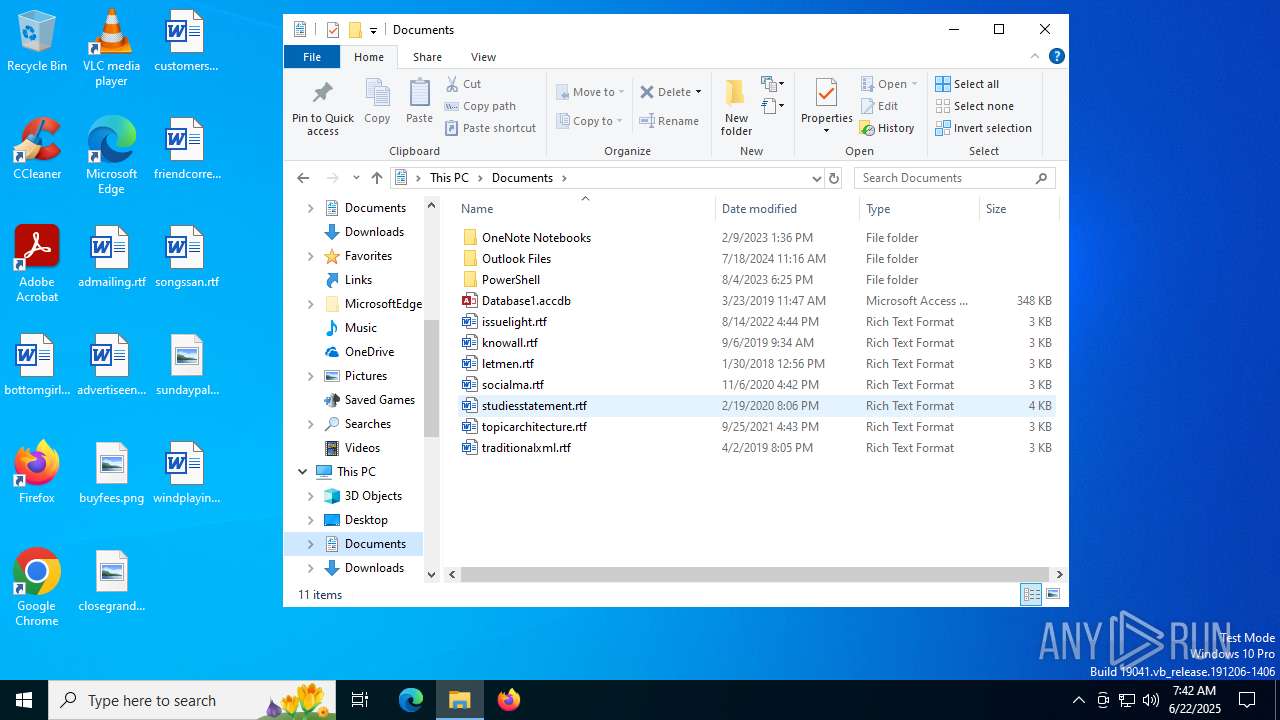
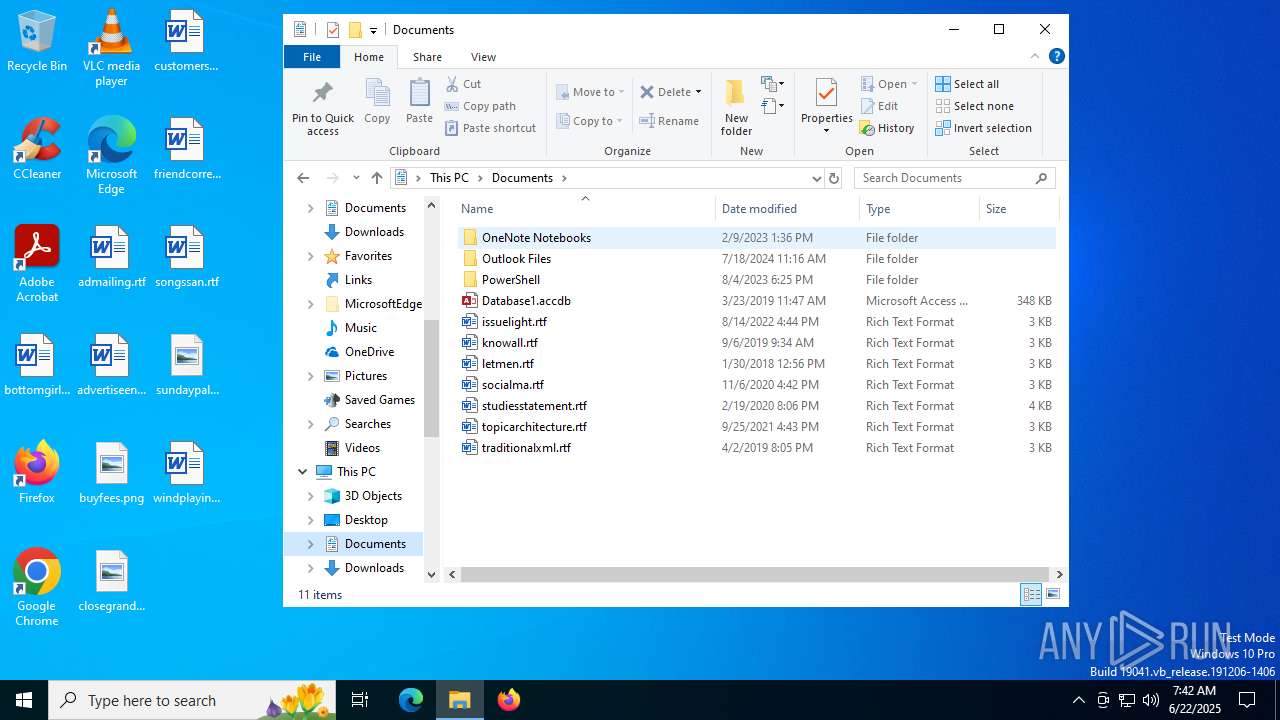
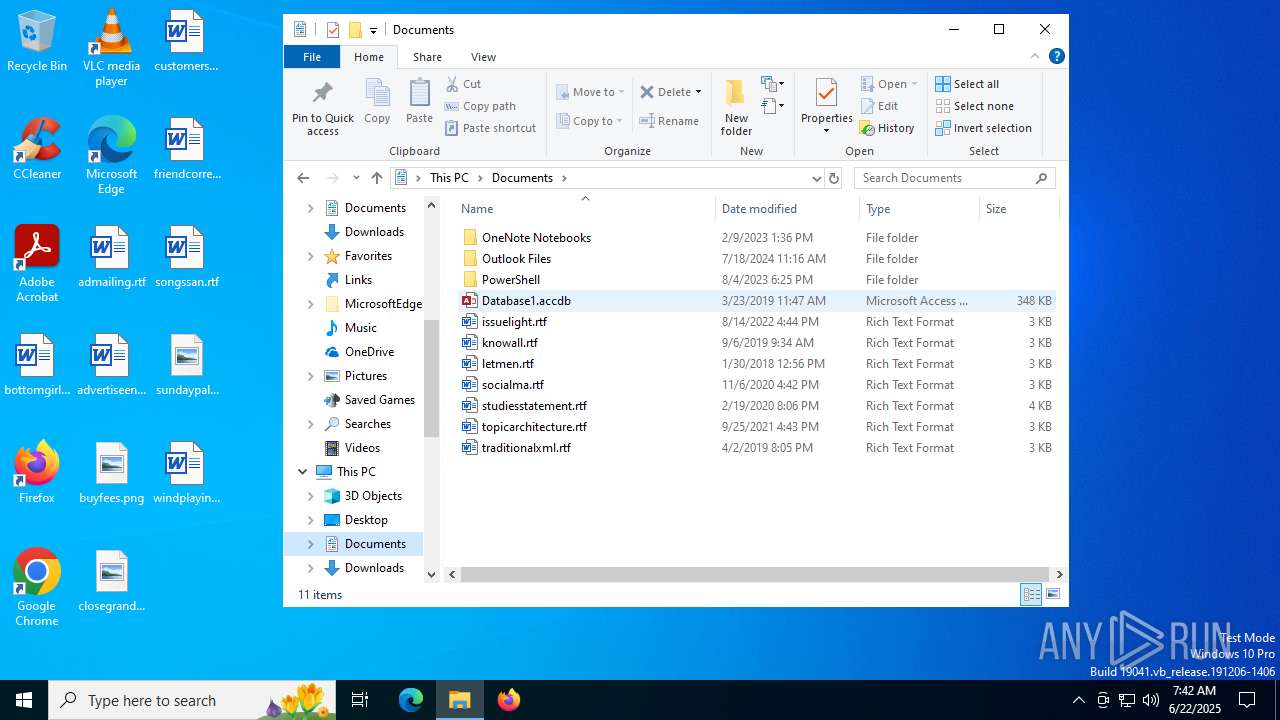
Behavior graph
Click at the process to see the details
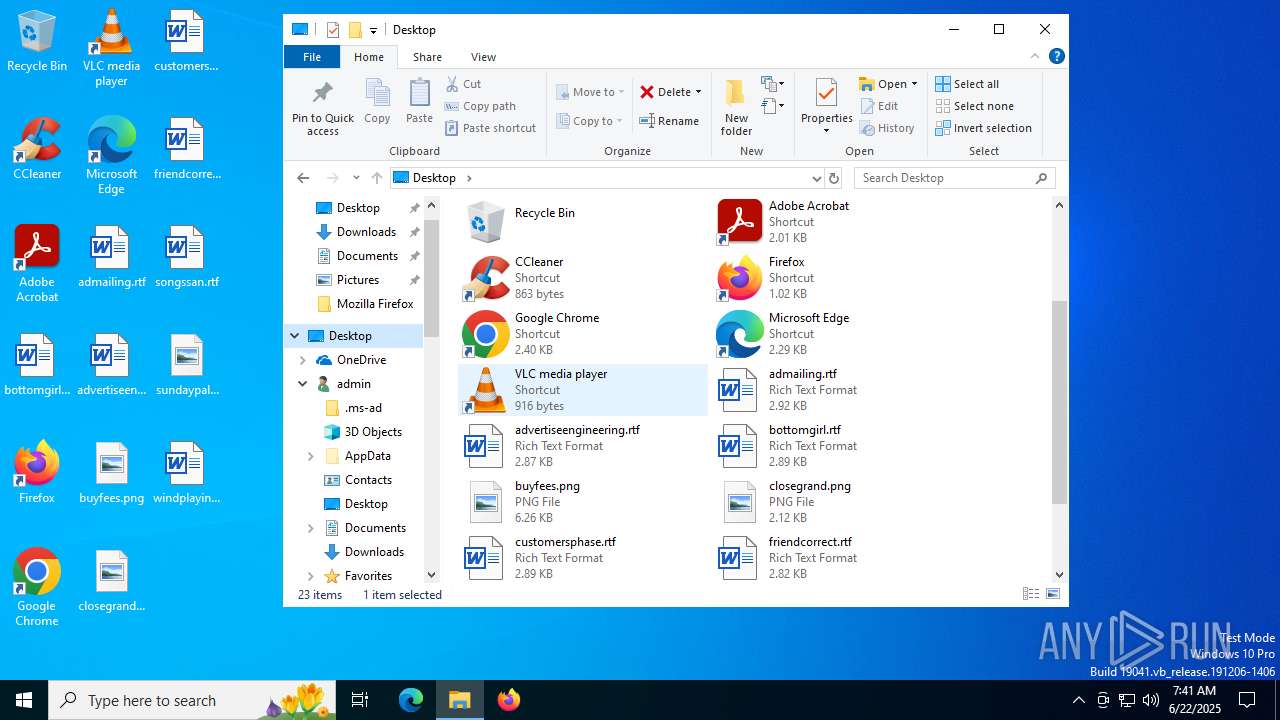
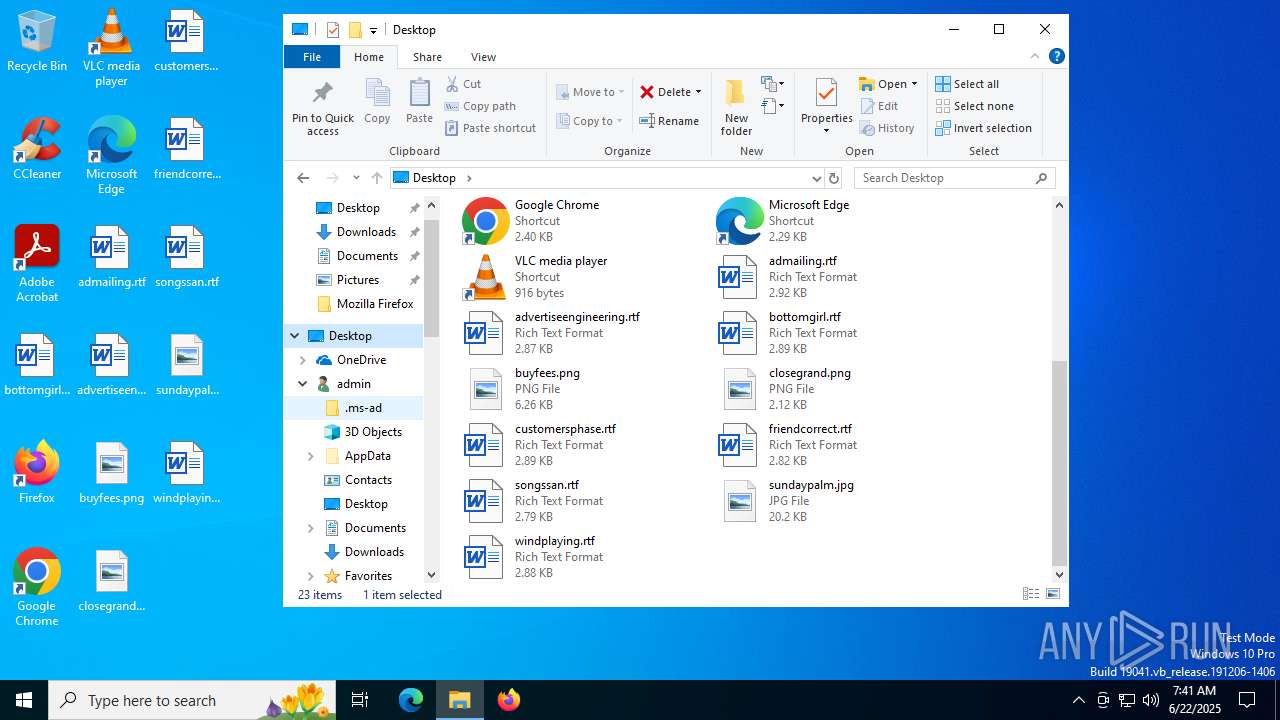
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\infatica-service-app.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\infatica-service-app.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Infatica SDK Modules
| |||||||||||||||
| 4544 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4576 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6508 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Infatica P2B.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 721
Read events
2 702
Write events
19
Delete events
0
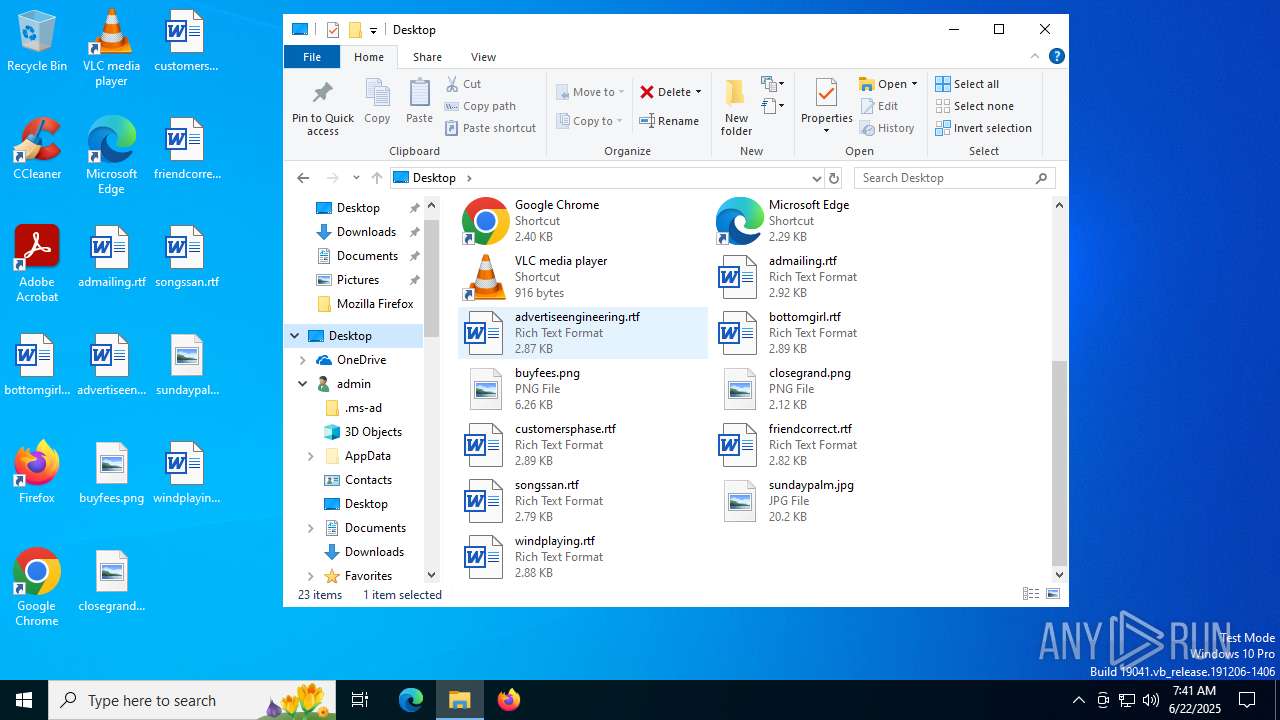
Modification events
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Infatica P2B.rar | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (304) infatica-service-app.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\sdk2107\proxy-service |
| Operation: | write | Name: | serviceId |
Value: 4000560061007200690061006E00740028000000000000007F000000000000000600510055007500690064000000C800F2004500F2009D00AE004D009C009B009B000B0014009F001F0059008F002900 | |||
| (PID) Process: | (6508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
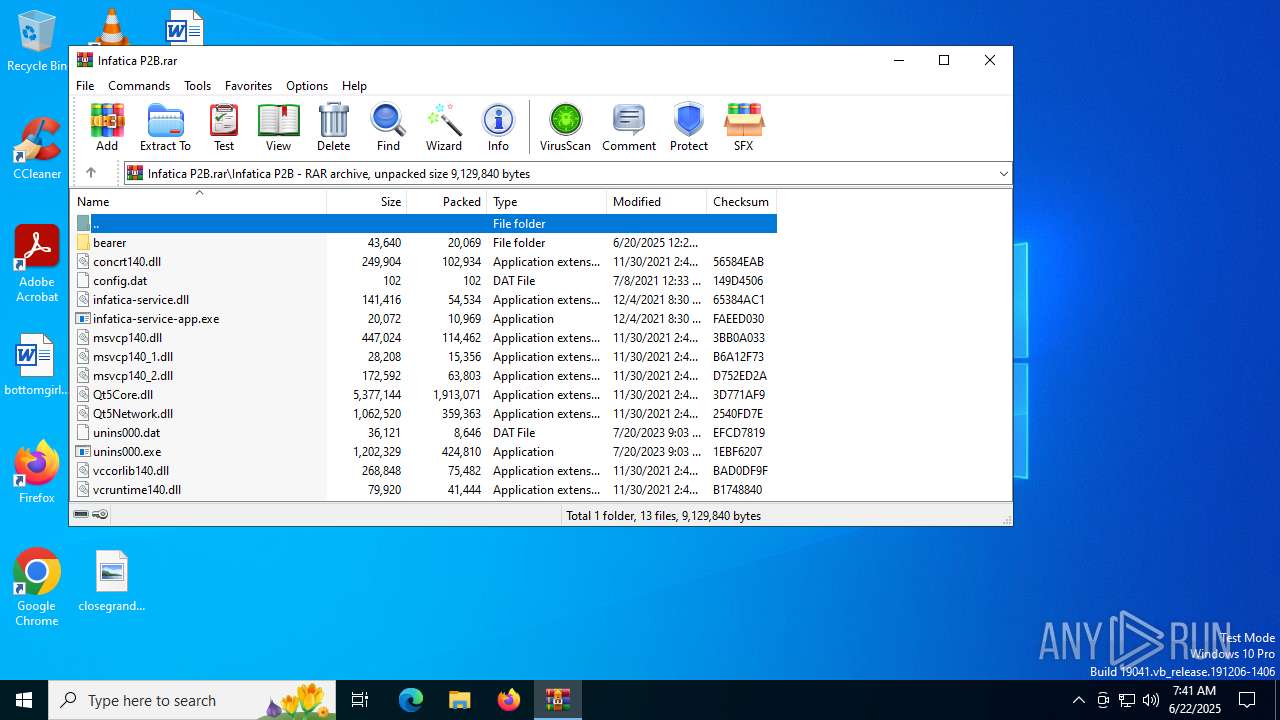
Executable files
12
Suspicious files
2
Text files
0
Unknown types
0
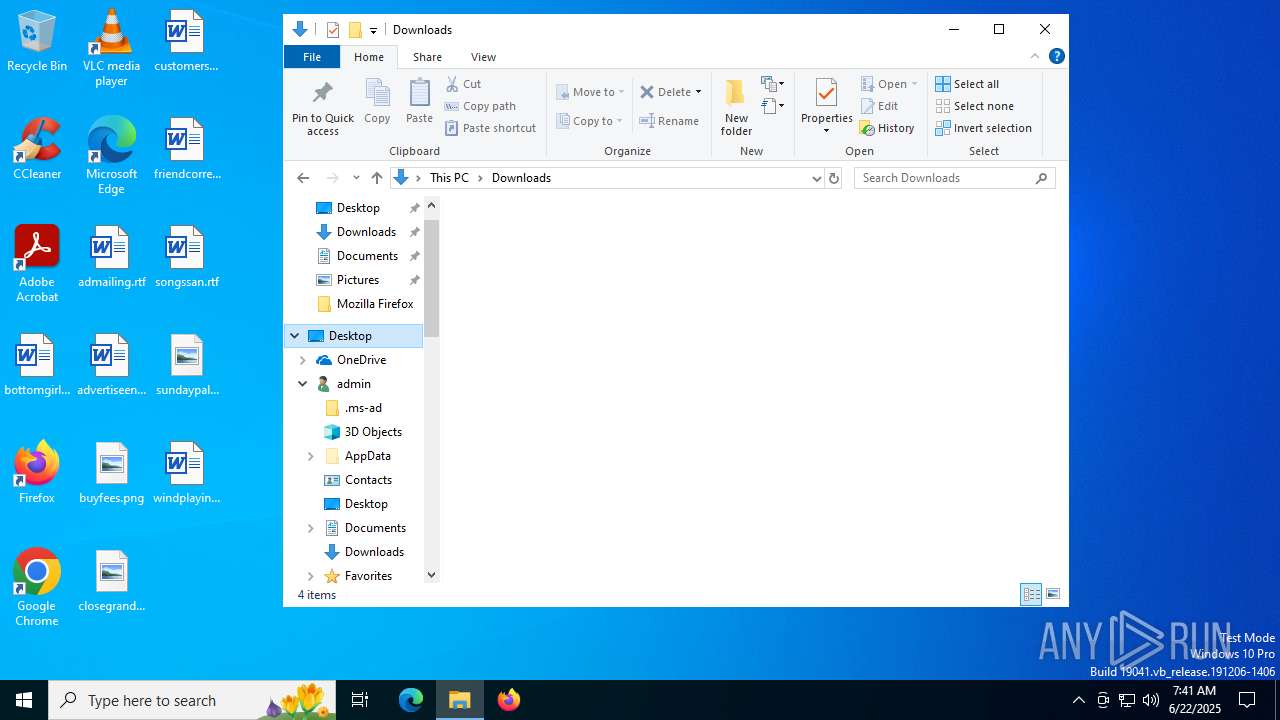
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\msvcp140_2.dll | executable | |
MD5:7E4E01078E60DE297CA889C28C439C39 | SHA256:57FAAA8F557168A3DDC4436BAFFA4D8BB9291863B31347CC9881139BA2773EF8 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\concrt140.dll | executable | |
MD5:DA3CD6C55230AD89B80144FFBD784B4E | SHA256:7EF49B9C11BA55490B304DDC8DA8B258AF6C53B10E27436876C6FDDC4FCFA9A1 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\infatica-service-app.exe | executable | |
MD5:551EDAB83D7C85F7CEBAA8AAE5EED5DE | SHA256:0C71619BF4D9B2EDEAF07936800C51735E49C7BAF3D7BA2E3A5583BB7AA20607 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\msvcp140.dll | executable | |
MD5:142BB4067CA3A325F02361DB404E945F | SHA256:46C00F2CC559E3B948325F5A38B09C2A13DE0F6175BEAF19742FC21A46F25164 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\msvcp140_1.dll | executable | |
MD5:AAEF16E870AC37D72A1BA1A3EFB975FC | SHA256:234EA3B79A79D46AA9A8EB5818903F9EC8915D806415BB6164463DA685945162 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\infatica-service.dll | executable | |
MD5:F2C2D424467B42BE77F58DC9027A476C | SHA256:7C551877CC4E8C2E09FBE59C4D9AD1ED6926133B4749782C00E09014E45AAE3D | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\Qt5Network.dll | executable | |
MD5:0FD8AD9B5FE25811E9FA9125E791E083 | SHA256:C9A7571426BB7D0F0939DC4D39D22329373FBD0320708EC6B99C0F516FF77D78 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\bearer\qgenericbearer.dll | executable | |
MD5:7CA70AC2C236F97E759756521D31D321 | SHA256:4EAA35944170C1C4B4F881079F29E326425C067328458632C836B0E207AC5ACF | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\config.dat | binary | |
MD5:A667EA15A1ADAB514921C0BF24650EC4 | SHA256:82E594916609F446D666C6F5B8798DB14D805337FE825B2DD277B1FF80BA9831 | |||
| 6508 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6508.40037\Infatica P2B\vcruntime140.dll | executable | |
MD5:0A79B529EB9012F65AC4500A7A915CA9 | SHA256:E985D4D2DA1711289B0A67A2DAB4002EF2CDA5EC7E27F576B0E026FA6EF224A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3768 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6292 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6292 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3876 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3768 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3768 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |