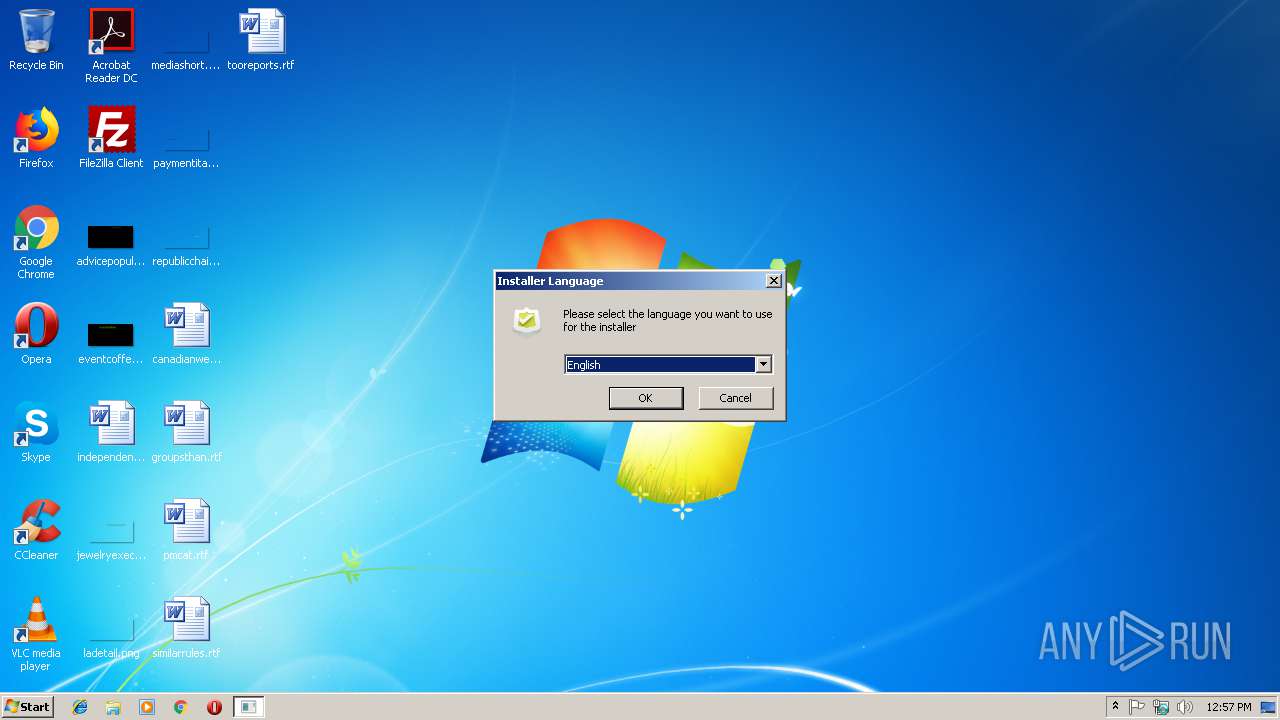
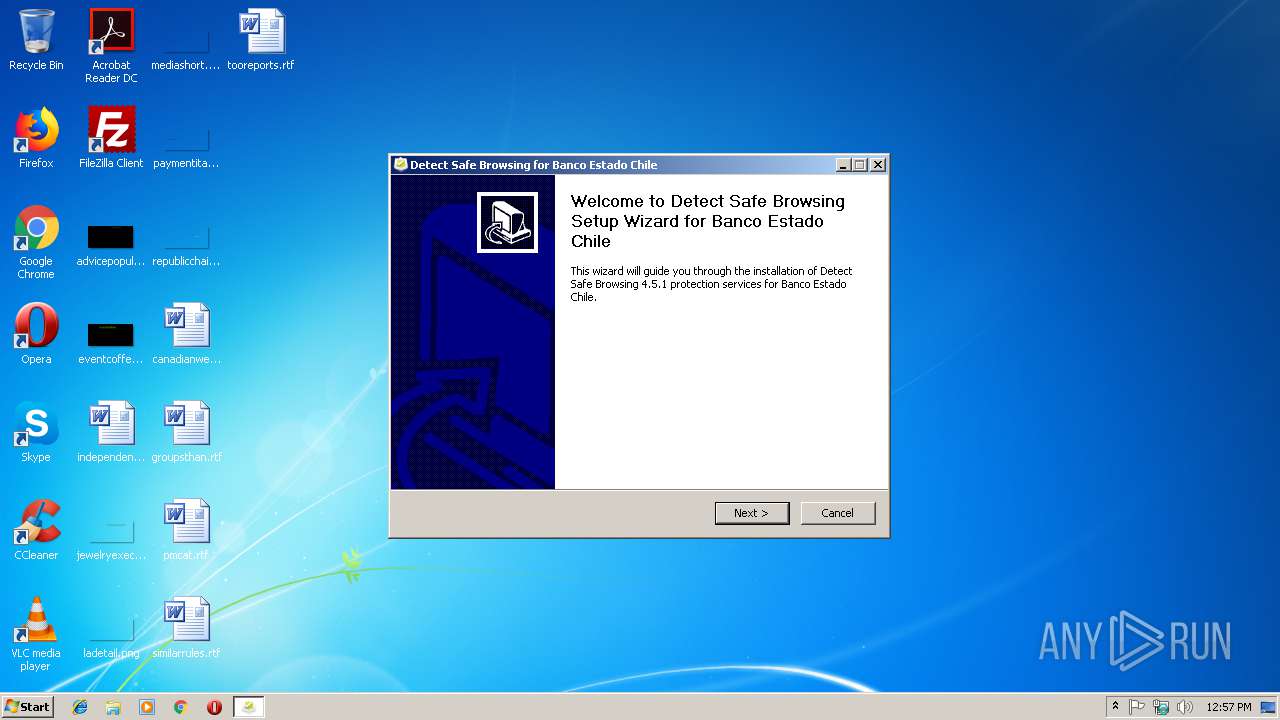
| File name: | Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe |
| Full analysis: | https://app.any.run/tasks/32938f08-a724-4f18-b391-ea5a8c1afc6c |
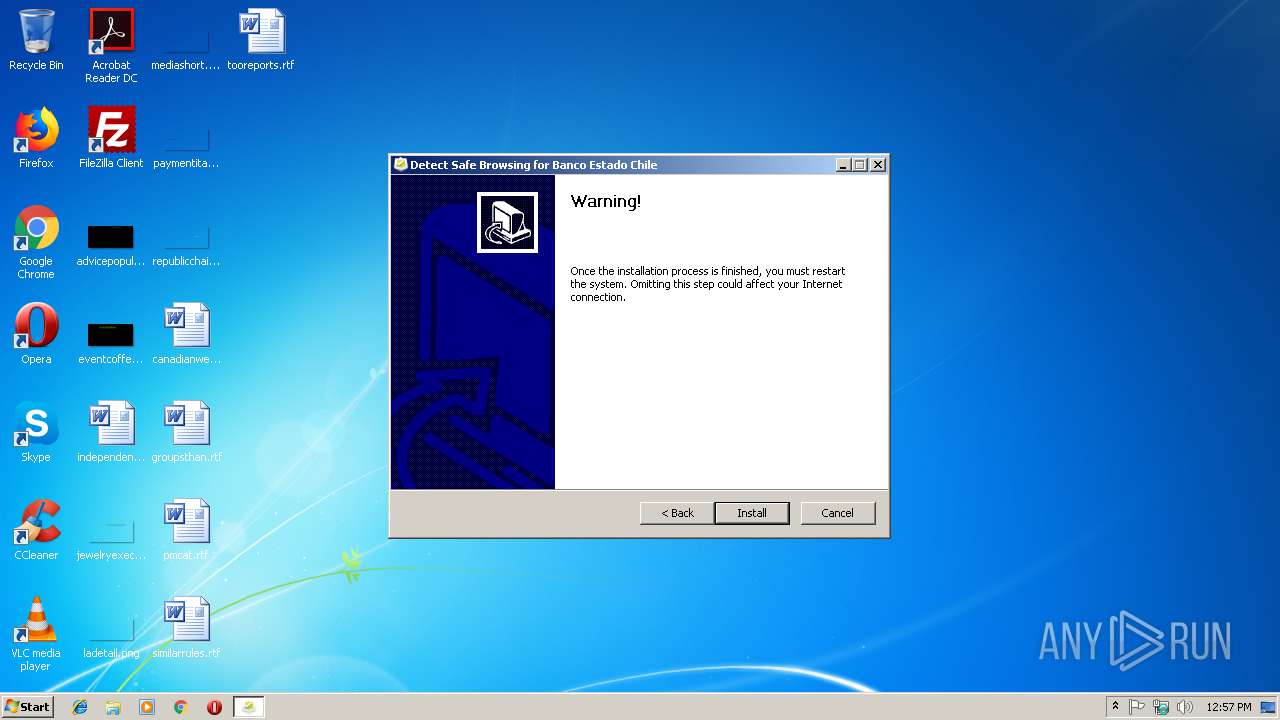
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 12:56:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 38C7B31306FB586032A73F57EBC5B3C0 |
| SHA1: | C875313478C661B2423D6A8A3C6D34421713280E |
| SHA256: | AEDEDF149EE82DE7D1263E80EEAC1D623132DF522C85B04902169D28D538EB21 |
| SSDEEP: | 6144:ZQqc0OEQeWaYirgiJ2H4mqBBE5G/cAjtC4X7Mh0sljElHpEwih8lgTxL3YYEnkm:XDZWaVr/4HzqB6EE07C0OElJqYg1I5 |
MALICIOUS
Application was dropped or rewritten from another process
- ns937E.tmp (PID: 2812)
- DetectUpdate.exe (PID: 2152)
- DetectUpdate.exe (PID: 3352)
- ns9544.tmp (PID: 2348)
- ProgressDialog.exe (PID: 2896)
- update4.5.1.exe (PID: 3536)
- DetectUpdate.exe (PID: 792)
- ProgressDialog.exe (PID: 1824)
- ns969D.tmp (PID: 3660)
- nsF9AA.tmp (PID: 2172)
- ns1439.tmp (PID: 3744)
- RegisterLSP.exe (PID: 2216)
- ns46D3.tmp (PID: 2456)
- RegisterLSP.exe (PID: 2804)
- ns49C2.tmp (PID: 2160)
- nsD62.tmp (PID: 2260)
- ns4B4B.tmp (PID: 2904)
- ns4ACD.tmp (PID: 2408)
- ns4C46.tmp (PID: 2352)
- vcredist_x8608.exe (PID: 3072)
- ns6ACB.tmp (PID: 3464)
- vcredist_x86.exe (PID: 2400)
- Setup.exe (PID: 3284)
- install.exe (PID: 3616)
Loads dropped or rewritten executable
- Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe (PID: 3676)
- update4.5.1.exe (PID: 3536)
- install.exe (PID: 3616)
- Setup.exe (PID: 3284)
SUSPICIOUS
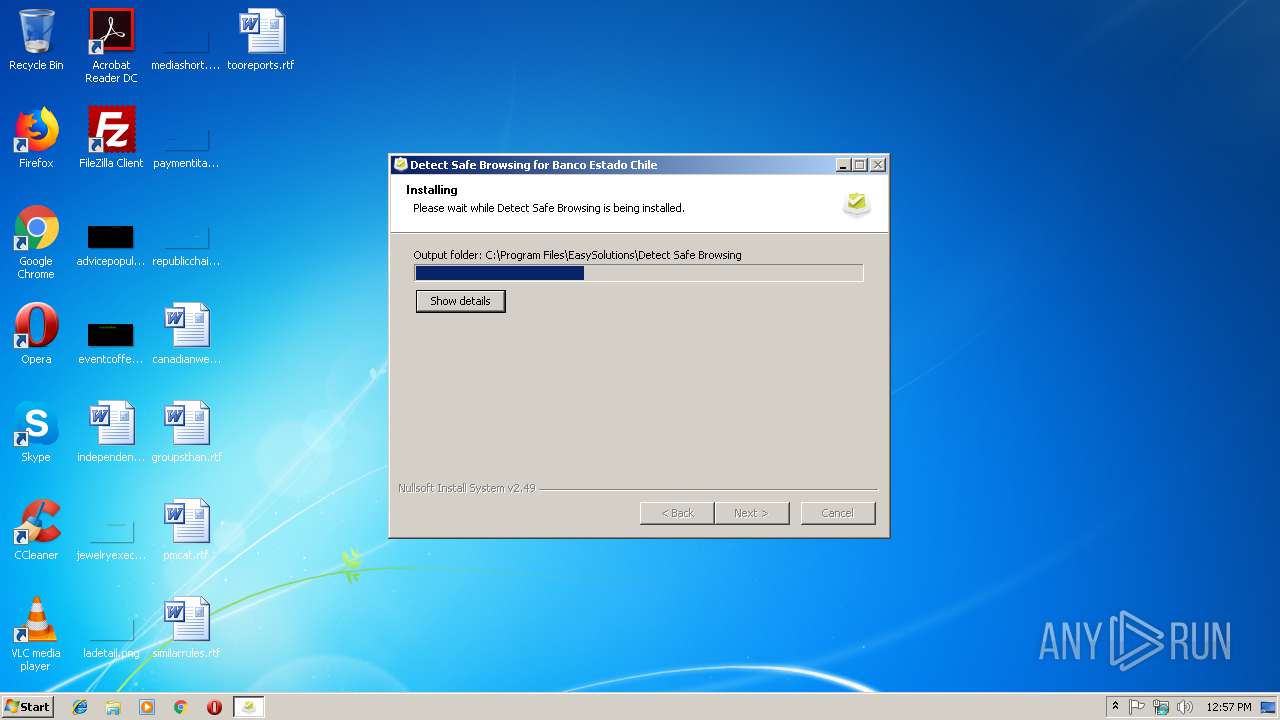
Creates files in the program directory
- Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe (PID: 3676)
- DetectUpdate.exe (PID: 792)
- update4.5.1.exe (PID: 3536)
Executable content was dropped or overwritten
- Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe (PID: 3676)
- DetectUpdate.exe (PID: 792)
- update4.5.1.exe (PID: 3536)
- msiexec.exe (PID: 2656)
- vcredist_x8608.exe (PID: 3072)
- vcredist_x86.exe (PID: 2400)
Creates a software uninstall entry
- Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe (PID: 3676)
Starts application with an unusual extension
- Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe (PID: 3676)
- update4.5.1.exe (PID: 3536)
Removes files from Windows directory
- update4.5.1.exe (PID: 3536)
- DetectUpdate.exe (PID: 792)
- msiexec.exe (PID: 2656)
- install.exe (PID: 3616)
- Setup.exe (PID: 3284)
Creates files in the Windows directory
- DetectUpdate.exe (PID: 792)
- update4.5.1.exe (PID: 3536)
- install.exe (PID: 3616)
- msiexec.exe (PID: 2656)
- RegisterLSP.exe (PID: 2804)
- Setup.exe (PID: 3284)
Starts CMD.EXE for commands execution
- nsF9AA.tmp (PID: 2172)
- cmd.exe (PID: 2868)
Starts SC.EXE for service management
- ns46D3.tmp (PID: 2456)
- ns49C2.tmp (PID: 2160)
- ns4B4B.tmp (PID: 2904)
- ns4ACD.tmp (PID: 2408)
Creates files in the driver directory
- update4.5.1.exe (PID: 3536)
INFO
Creates a software uninstall entry
- msiexec.exe (PID: 2656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.4.0 |
| ProductVersionNumber: | 1.0.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
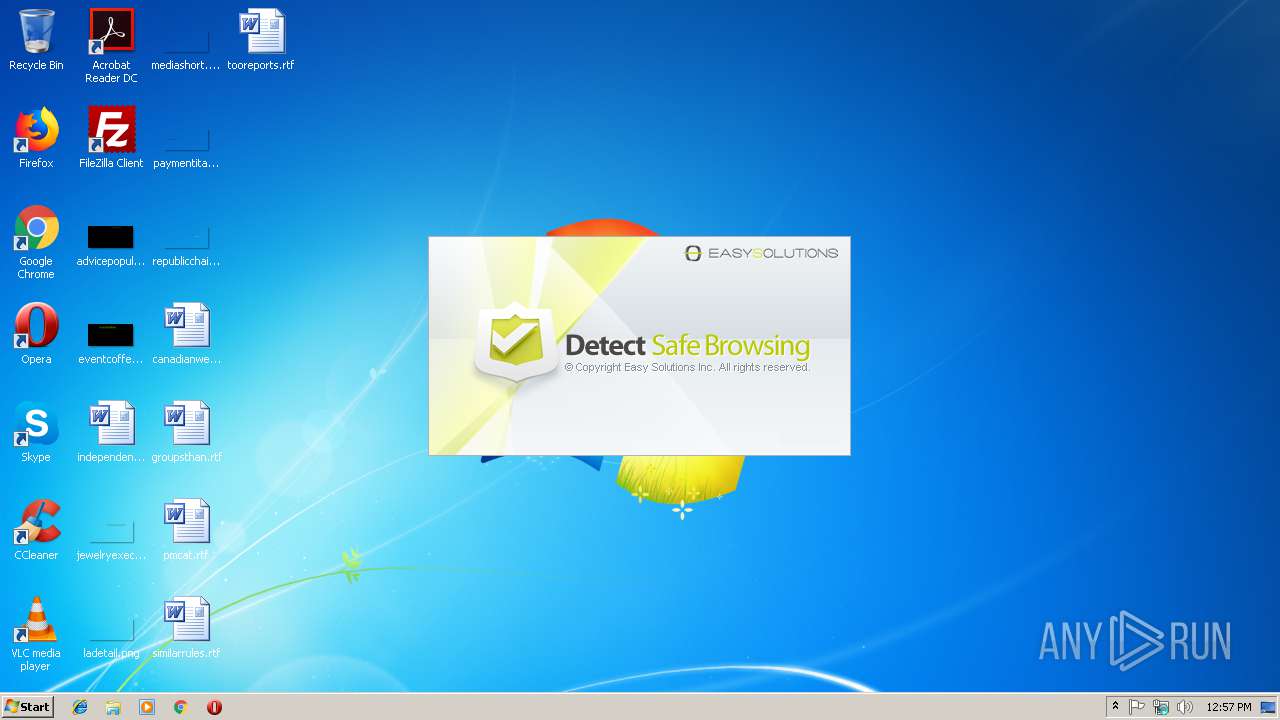
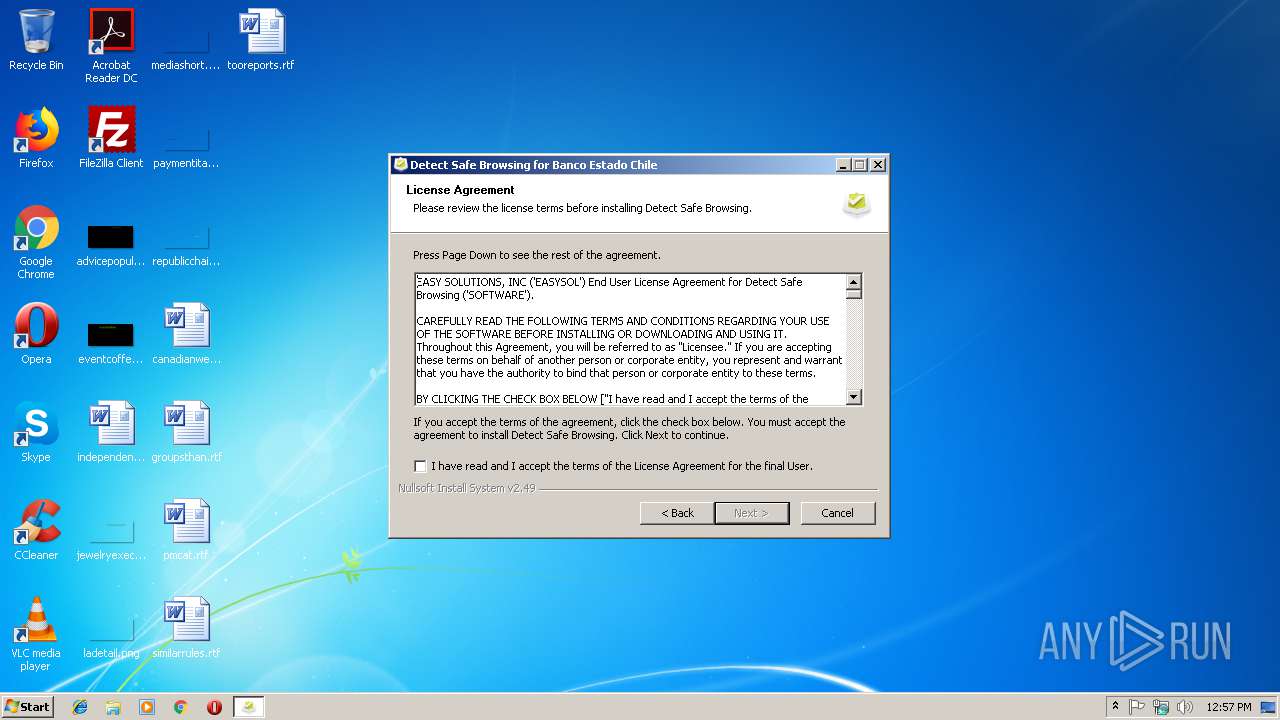
| Comments: | Detect Safe Browsing Setup. |
| CompanyName: | Easy Solutions Inc. |
| FileDescription: | Detect Safe Browsing |
| FileVersion: | 1.0.4 |
| InternalName: | DetectUpdate |
| LegalCopyright: | Copyright 2010-2013 Easy Solutions Inc. |
| LegalTrademarks: | DetectUpdate is a Trademark of Easy Solutions Inc. |
| OriginalFileName: | Detect Safe Browsing_Installer_x1.0.4.141.0.exe |
| ProductName: | Detect Safe Browsing |
| ProductVersion: | 1.0.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:41 |
| Detected languages: |
|
| Comments: | Detect Safe Browsing Setup. |
| CompanyName: | Easy Solutions Inc. |
| FileDescription: | Detect Safe Browsing |
| FileVersion: | 1.0.4 |
| InternalName: | DetectUpdate |
| LegalCopyright: | Copyright 2010-2013 Easy Solutions Inc. |
| LegalTrademarks: | DetectUpdate is a Trademark of Easy Solutions Inc. |
| OriginalFilename: | Detect Safe Browsing_Installer_x1.0.4.141.0.exe |
| ProductName: | Detect Safe Browsing |
| ProductVersion: | 1.0.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000058D2 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4331 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17976 |
.data | 0x00009000 | 0x0001AF78 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6178 |
.ndata | 0x00024000 | 0x0000D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00031000 | 0x00012E90 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.5417 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.51164 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 5.58672 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.58915 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.61363 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 5.74687 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.70099 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
78
Monitored processes
33
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | "C:\ProgramData\EasySolutions\DetectUpdate\DetectUpdate.exe" | C:\ProgramData\EasySolutions\DetectUpdate\DetectUpdate.exe | services.exe | ||||||||||||
User: SYSTEM Company: Easy Solutions Integrity Level: SYSTEM Description: Detect Automatic Update System Exit code: 0 Version: 1.0.4.0 Modules
| |||||||||||||||
| 1824 | C:\ProgramData\EasySolutions\DetectUpdate\ProgressDialog.exe | C:\ProgramData\EasySolutions\DetectUpdate\ProgressDialog.exe | — | DetectUpdate.exe | |||||||||||
User: admin Company: Easy Solutions Integrity Level: MEDIUM Description: Dialog Component Exit code: 0 Version: 1.0.4.0 Modules
| |||||||||||||||
| 2152 | "C:\ProgramData\EasySolutions\DetectUpdate\DetectUpdate.exe" /Start | C:\ProgramData\EasySolutions\DetectUpdate\DetectUpdate.exe | — | ns969D.tmp | |||||||||||
User: admin Company: Easy Solutions Integrity Level: HIGH Description: Detect Automatic Update System Exit code: 0 Version: 1.0.4.0 Modules
| |||||||||||||||
| 2160 | "C:\Windows\TEMP\nsyF999.tmp\ns49C2.tmp" sc query dsbwncf | C:\Windows\TEMP\nsyF999.tmp\ns49C2.tmp | — | update4.5.1.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2172 | "C:\Windows\TEMP\nsyF999.tmp\nsF9AA.tmp" cmd /Q /C For /f "tokens=2 delims=[]" %G in ( 'ver' ) Do For /f "tokens=2,3 delims=. " %H in ( "%G" ) Do Echo %H.%I | C:\Windows\TEMP\nsyF999.tmp\nsF9AA.tmp | — | update4.5.1.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\EasySolutions\Detect Safe Browsing\RegisterLSP.exe" -tc | C:\Program Files\EasySolutions\Detect Safe Browsing\RegisterLSP.exe | — | ns1439.tmp | |||||||||||
User: SYSTEM Company: EasySol Integrity Level: SYSTEM Description: RegisterLSP Exit code: 0 Version: 2.2.8.23 Modules
| |||||||||||||||
| 2260 | "C:\Windows\TEMP\nsyF999.tmp\nsD62.tmp" "C:\Program Files\EasySolutions\Detect Safe Browsing\RegisterLSP.exe" -tw | C:\Windows\TEMP\nsyF999.tmp\nsD62.tmp | — | update4.5.1.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\AppData\Local\Temp\nso932F.tmp\ns9544.tmp" "C:\ProgramData\EasySolutions\DetectUpdate\ProgressDialog.exe" /RegServer | C:\Users\admin\AppData\Local\Temp\nso932F.tmp\ns9544.tmp | — | Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2352 | "C:\Windows\TEMP\nsyF999.tmp\ns4C46.tmp" "C:\Program Files\EasySolutions\Detect Safe Browsing\vcredist_x8608.exe" /q /c:"msiexec /i vcredist.msi /qn /l*v %temp%\vcredist_x86.log" | C:\Windows\TEMP\nsyF999.tmp\ns4C46.tmp | — | update4.5.1.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\EasySolutions\Detect Safe Browsing\vcredist_x86.exe" /q /norestart | C:\Program Files\EasySolutions\Detect Safe Browsing\vcredist_x86.exe | ns6ACB.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2010 x86 Redistributable Setup Exit code: 5100 Version: 10.0.30319.415 Modules
| |||||||||||||||
Total events
1 160
Read events
564
Write events
584
Delete events
12
Modification events
| (PID) Process: | (3676) Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EasySolutions\Update\Conf |
| Operation: | write | Name: | clines |
Value: | |||
| (PID) Process: | (3352) DetectUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{FB0E8264-9BA8-4DE9-99F3-C0B875B03F12} |
| Operation: | write | Name: | LocalService |
Value: DetectUpdate | |||
| (PID) Process: | (3352) DetectUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{08E9AD83-ED7A-472D-8D58-DEB07E648B84}\1.0 |
| Operation: | write | Name: | |
Value: DetectUpdateLib | |||
| (PID) Process: | (3352) DetectUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{08E9AD83-ED7A-472D-8D58-DEB07E648B84}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 0 | |||
| (PID) Process: | (3352) DetectUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{08E9AD83-ED7A-472D-8D58-DEB07E648B84}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\ProgramData\EasySolutions\DetectUpdate\DetectUpdate.exe | |||
| (PID) Process: | (3352) DetectUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{08E9AD83-ED7A-472D-8D58-DEB07E648B84}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: C:\ProgramData\EasySolutions\DetectUpdate | |||
| (PID) Process: | (2896) ProgressDialog.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB26D1A6-2948-4536-9C97-5198CD869619} |
| Operation: | write | Name: | |
Value: DialogHandler Class | |||
| (PID) Process: | (2896) ProgressDialog.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB26D1A6-2948-4536-9C97-5198CD869619}\LocalServer32 |
| Operation: | write | Name: | |
Value: "C:\ProgramData\EasySolutions\DetectUpdate\ProgressDialog.exe" | |||
| (PID) Process: | (2896) ProgressDialog.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB26D1A6-2948-4536-9C97-5198CD869619}\LocalServer32 |
| Operation: | write | Name: | ServerExecutable |
Value: C:\ProgramData\EasySolutions\DetectUpdate\ProgressDialog.exe | |||
| (PID) Process: | (2896) ProgressDialog.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{FB26D1A6-2948-4536-9C97-5198CD869619}\TypeLib |
| Operation: | write | Name: | |
Value: {1CFBF7B3-F0F2-4760-B21B-3038A75C372D} | |||
Executable files
73
Suspicious files
7
Text files
148
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe | C:\Users\admin\AppData\Local\Temp\nso932F.tmp\ns9544.tmp | — | |
MD5:— | SHA256:— | |||
| 792 | DetectUpdate.exe | C:\Windows\TEMP\CabF802.tmp | — | |
MD5:— | SHA256:— | |||
| 792 | DetectUpdate.exe | C:\Windows\TEMP\TarF803.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe | C:\ProgramData\EasySolutions\DetectUpdate\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 792 | DetectUpdate.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9A19ADAD9D098E039450ABBEDD5616EB_E34CDEC989D450DEFFB9F6382363E0DD | der | |
MD5:— | SHA256:— | |||
| 792 | DetectUpdate.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7D266D9E1E69FA1EEFB9699B009B34C8_0A9BFDD75B598C2110CBF610C078E6E6 | binary | |
MD5:— | SHA256:— | |||
| 3676 | Detect_Safe_Browsing_Installer_x1.0.3.116.0.exe | C:\Users\admin\AppData\Local\Temp\nso932F.tmp\ns969D.tmp | executable | |
MD5:— | SHA256:— | |||
| 792 | DetectUpdate.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9A19ADAD9D098E039450ABBEDD5616EB_E34CDEC989D450DEFFB9F6382363E0DD | binary | |
MD5:— | SHA256:— | |||
| 792 | DetectUpdate.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7D266D9E1E69FA1EEFB9699B009B34C8_0A9BFDD75B598C2110CBF610C078E6E6 | der | |
MD5:— | SHA256:— | |||
| 3536 | update4.5.1.exe | C:\Windows\TEMP\nsyF999.tmp\searchKey.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
792 | DetectUpdate.exe | GET | 200 | 23.37.43.27:80 | http://sf.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CEAdTHZQ92xFMnNuAOVEIKD4%3D | NL | der | 1.62 Kb | whitelisted |
792 | DetectUpdate.exe | GET | 200 | 23.37.43.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
792 | DetectUpdate.exe | 66.45.226.210:443 | detectupdate.easysol.net | NEW JERSEY INTERNATIONAL INTERNET EXCHANGE LLC | US | unknown |
792 | DetectUpdate.exe | 23.37.43.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectupdate.easysol.net |
| unknown |
ocsp.verisign.com |
| whitelisted |
sf.symcd.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | A StopBlock was hit or a System Requirement was not met. |