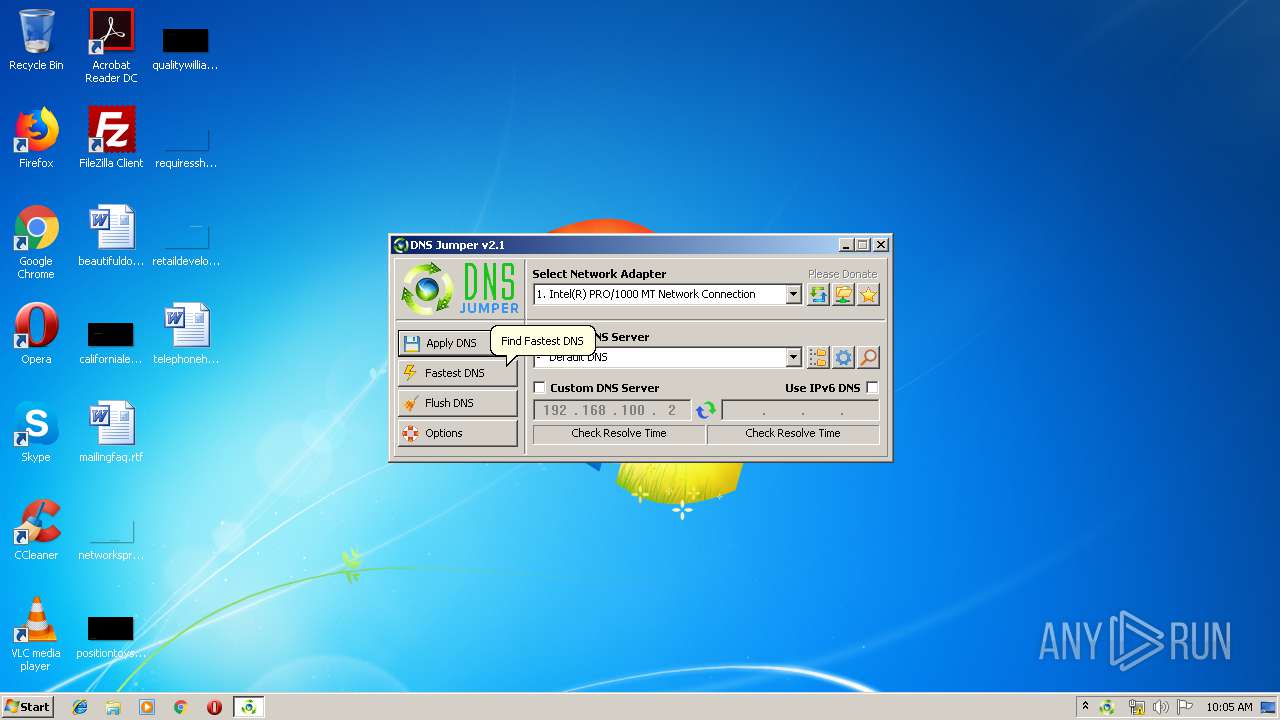
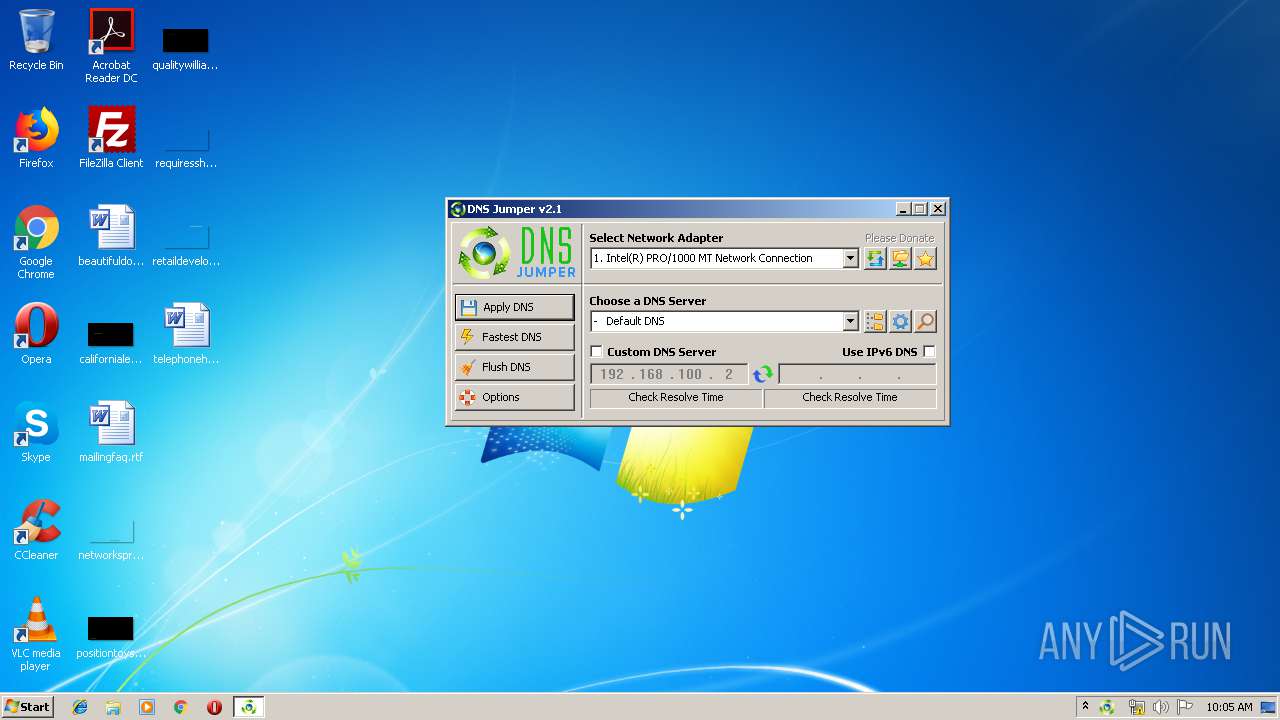
| File name: | DnsJumper.exe |
| Full analysis: | https://app.any.run/tasks/30e97ba1-e819-48e4-8c36-1617d19ad5aa |
| Verdict: | No threats detected |
| Analysis date: | June 27, 2019, 09:04:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 44A2470E6D3891C295422344B153CA85 |
| SHA1: | 9E8966130FD59743D97EFFC7DCF05FB648710339 |
| SHA256: | AEDBAA8D63EFC4C6B5F6662EBE366FEABA12640150EA2D0346F99D8693DBE2D5 |
| SSDEEP: | 24576:/aHMv6CFrjenyJQ6i2WoDqqOyLcUhDI6nEU4:/1v3jxJQ6iJnqOyFZi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses IPCONFIG.EXE to discover IP address
- DnsJumper.exe (PID: 3072)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:16 09:47:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 188416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 2.1.0.0 |
| Comments: | This application is designed to simplify the DNS changing process. |
| FileDescription: | DNS Jumper v2.1 |
| LegalCopyright: | Copyright © 2009 - 2017 www.sordum.org All Rights Reserved. |
| Coder: | By BlueLife |
| CompanyName: | www.sordum.org |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Apr-2010 07:47:33 |
| Detected languages: |
|
| FileVersion: | 2.1.0.0 |
| Comments: | This application is designed to simplify the DNS changing process. |
| FileDescription: | DNS Jumper v2.1 |
| LegalCopyright: | Copyright © 2009 - 2017 www.sordum.org All Rights Reserved. |
| Coder: | By BlueLife |
| CompanyName: | www.sordum.org |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Apr-2010 07:47:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00080017 | 0x00080200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6349 |
.rdata | 0x00082000 | 0x0000D95C | 0x0000DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.86691 |
.data | 0x00090000 | 0x0001A518 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.20173 |
.rsrc | 0x000AB000 | 0x00019D48 | 0x00019E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.77554 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25292 | 1182 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.44108 | 1046 | Latin 1 / Western European | English - United States | RT_STRING |
3 | 3.44665 | 978 | Latin 1 / Western European | English - United States | RT_STRING |
4 | 3.4107 | 1002 | Latin 1 / Western European | English - United States | RT_STRING |
5 | 3.42062 | 956 | Latin 1 / Western European | English - United States | RT_STRING |
6 | 2.98655 | 224 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 0.916632 | 176 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
14 | 5.15409 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
15 | 5.93038 | 16936 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
50 | 4.57188 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 828 | ipconfig.exe /flushdns | C:\Windows\system32\ipconfig.exe | — | DnsJumper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\DnsJumper.exe" | C:\Users\admin\AppData\Local\Temp\DnsJumper.exe | explorer.exe | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: DNS Jumper v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 3136 | "C:\Users\admin\AppData\Local\Temp\DnsJumper.exe" | C:\Users\admin\AppData\Local\Temp\DnsJumper.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: DNS Jumper v2.1 Exit code: 0 Version: 2.1.0.0 | |||||||||||||||
Total events
103
Read events
76
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | fdwSupport |
Value: 1 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | cFormatTags |
Value: 2 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | aFormatTagCache |
Value: 01000000100000001100000014000000 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | cFilterTags |
Value: 0 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | fdwSupport |
Value: 1 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | cFormatTags |
Value: 3 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | aFormatTagCache |
Value: 010000001000000006000000120000000700000012000000 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | cFilterTags |
Value: 0 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msgsm610 |
| Operation: | write | Name: | fdwSupport |
Value: 1 | |||
| (PID) Process: | (3072) DnsJumper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msgsm610 |
| Operation: | write | Name: | cFormatTags |
Value: 2 | |||
Executable files
0
Suspicious files
0
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | DnsJumper.exe | C:\Users\admin\AppData\Local\Temp\autFA7A.tmp | — | |
MD5:— | SHA256:— | |||
| 3072 | DnsJumper.exe | C:\Users\admin\AppData\Local\Temp\rhtkfdx | — | |
MD5:— | SHA256:— | |||
| 3072 | DnsJumper.exe | C:\Users\admin\AppData\Local\Temp\DnsJumper.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
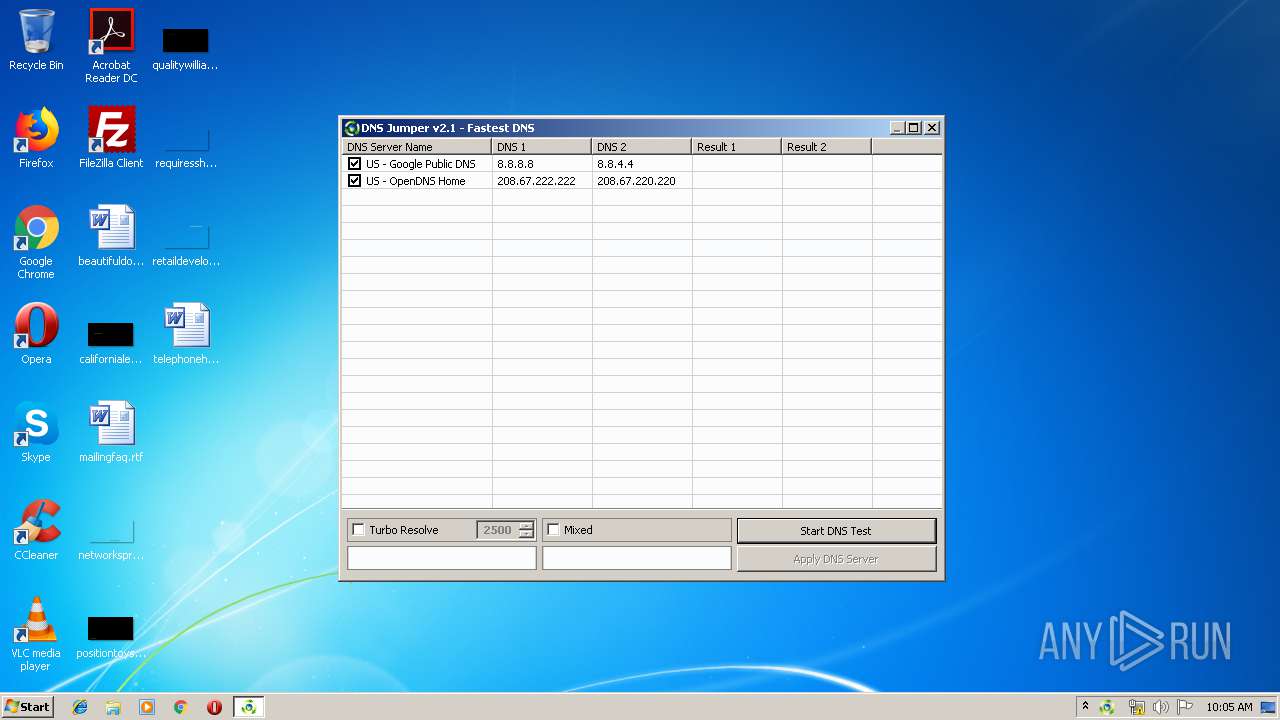
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
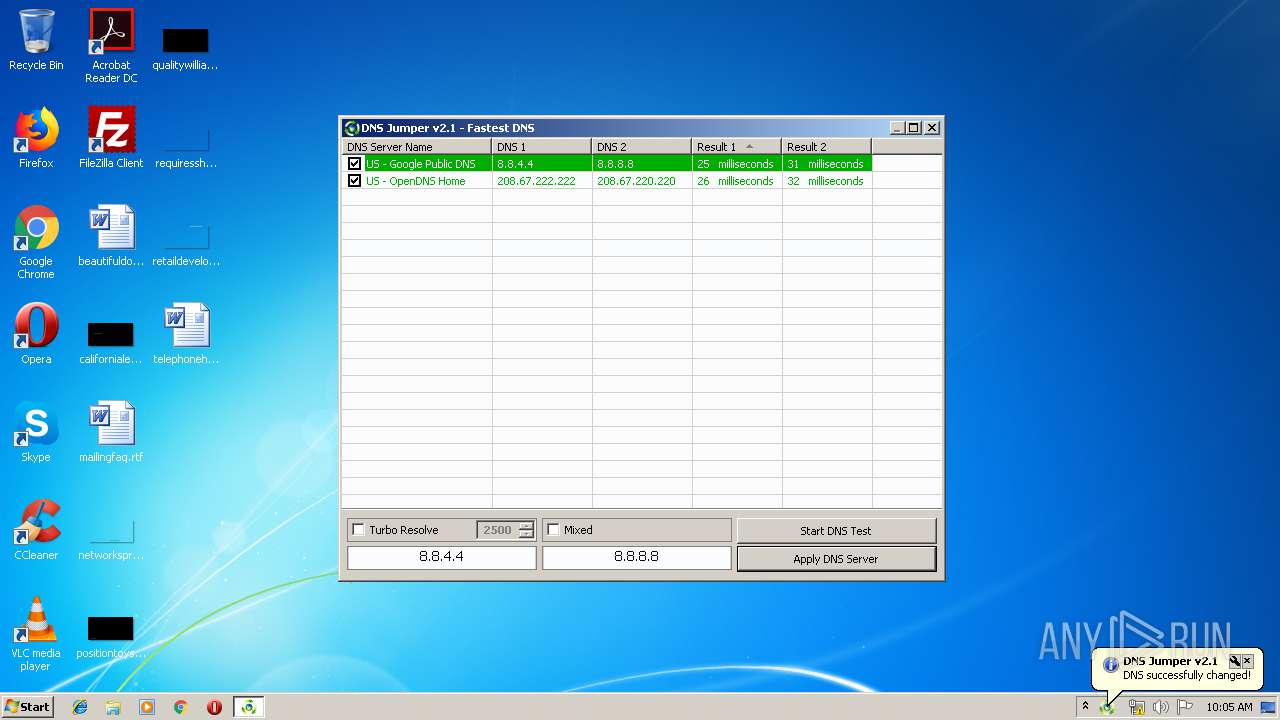
3072 | DnsJumper.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
— | — | 8.8.4.4:53 | — | Google Inc. | US | whitelisted |
3072 | DnsJumper.exe | 208.67.220.220:53 | — | OpenDNS, LLC | US | suspicious |
3072 | DnsJumper.exe | 208.67.222.222:53 | — | OpenDNS, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |