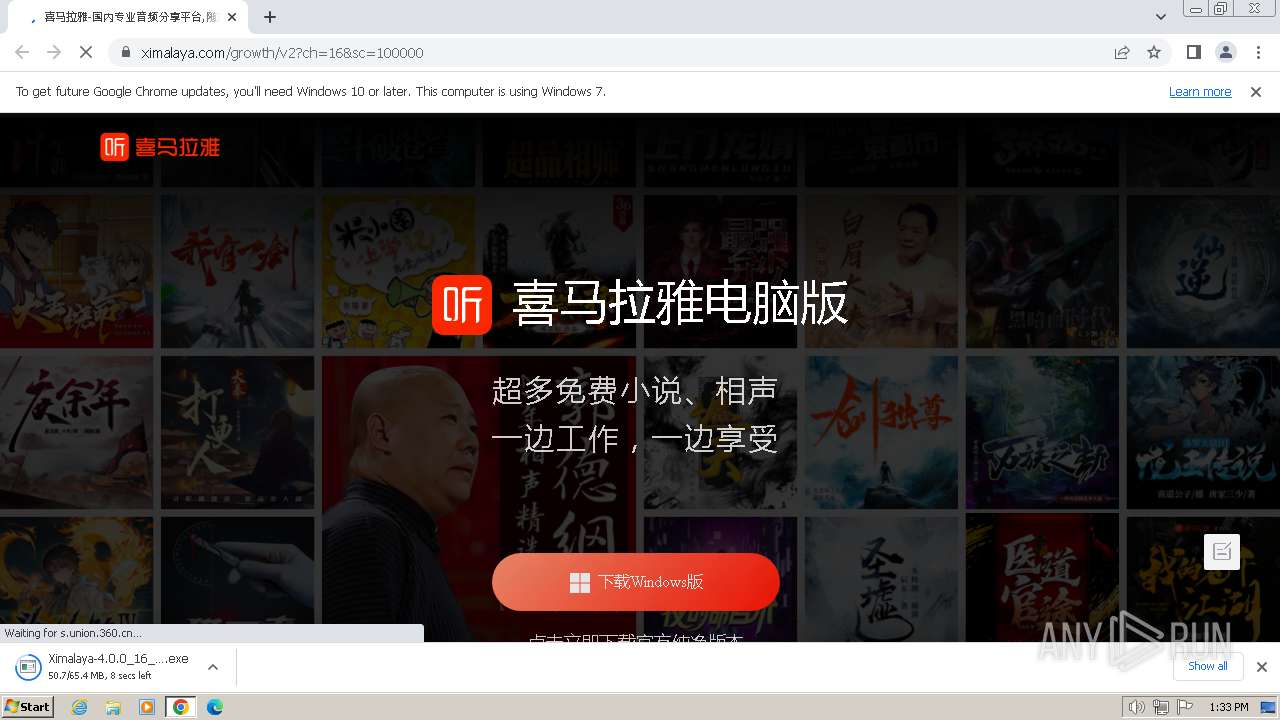
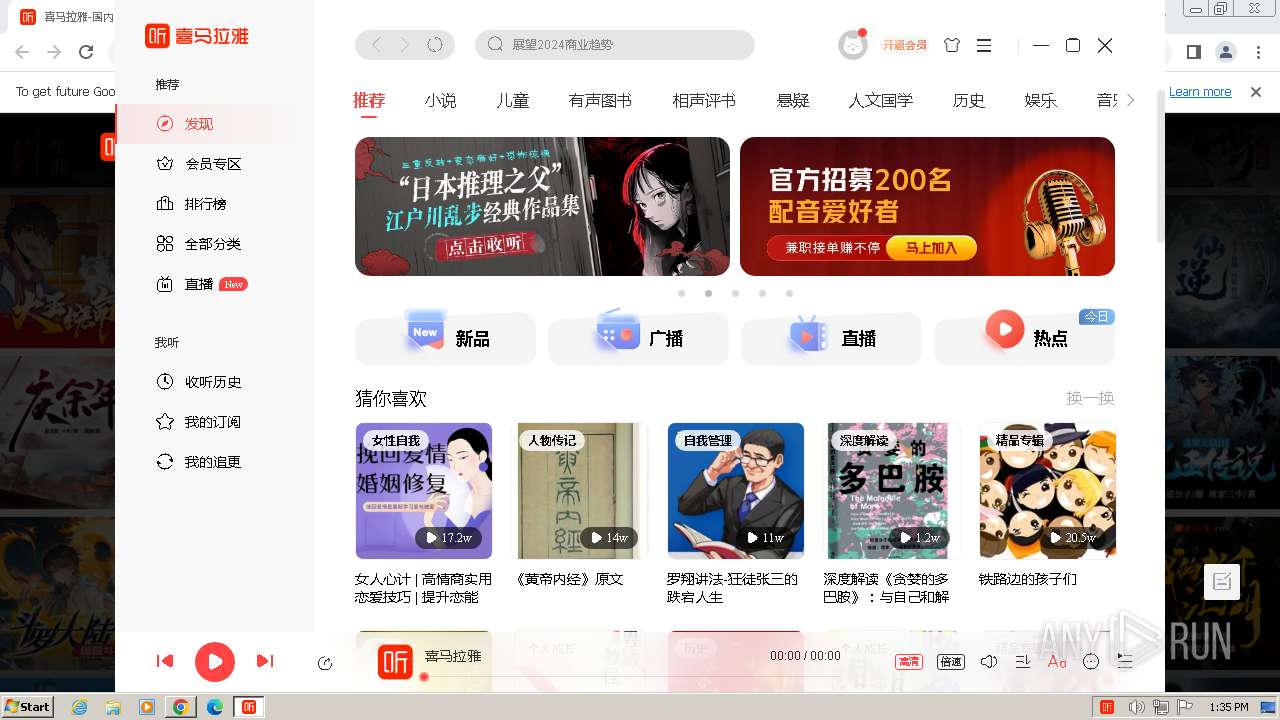
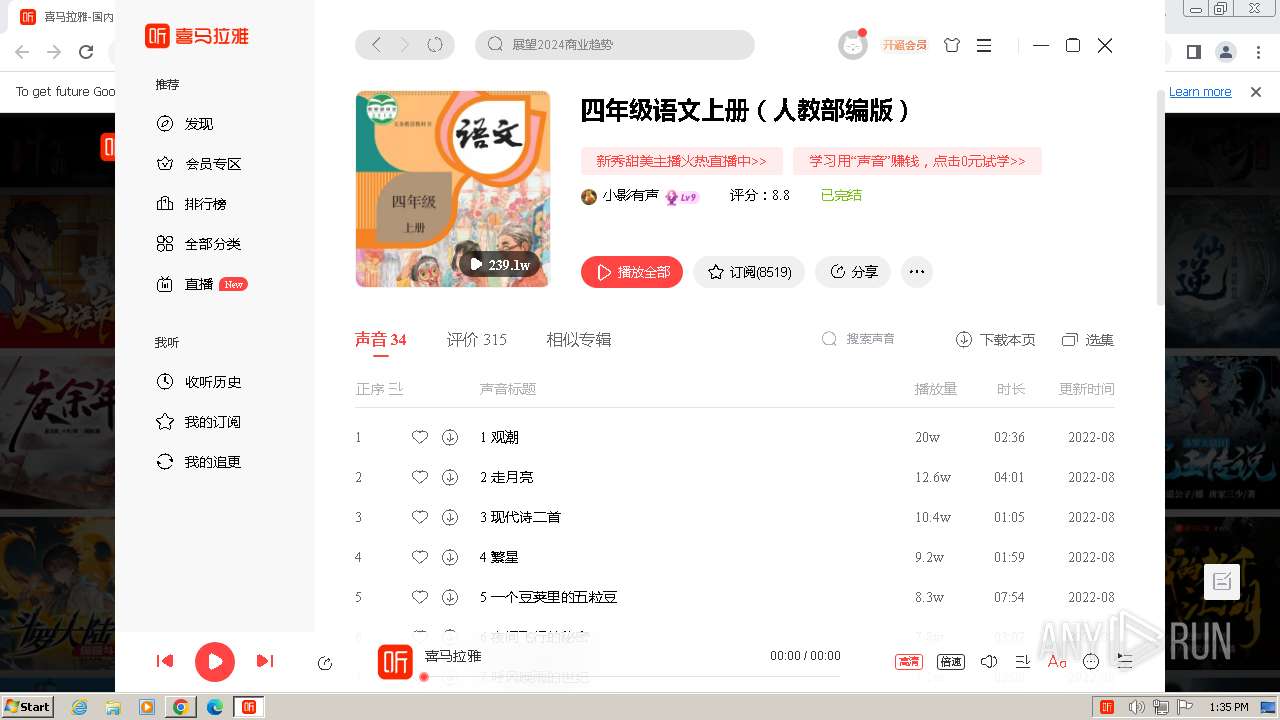
| URL: | pc.ximalaya.com |
| Full analysis: | https://app.any.run/tasks/2e223793-6c6e-4996-8666-50168def7664 |
| Verdict: | Malicious activity |
| Analysis date: | January 04, 2024, 13:31:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D4C271CA25D0A373982F8357C7ECD1E8 |
| SHA1: | C8A72DB40A0EACD2B516E60640DA39C3B190C88A |
| SHA256: | AED089D1D80F16E8EB037A16DB30AC51FA0637E027A680454DF79BA3963E6612 |
| SSDEEP: | 3:F9:F9 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2920)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 2920)
Changes powershell execution policy (Unrestricted)
- 喜马拉雅.exe (PID: 2428)
Changes the autorun value in the registry
- 喜马拉雅.exe (PID: 2428)
SUSPICIOUS
Starts CMD.EXE for commands execution
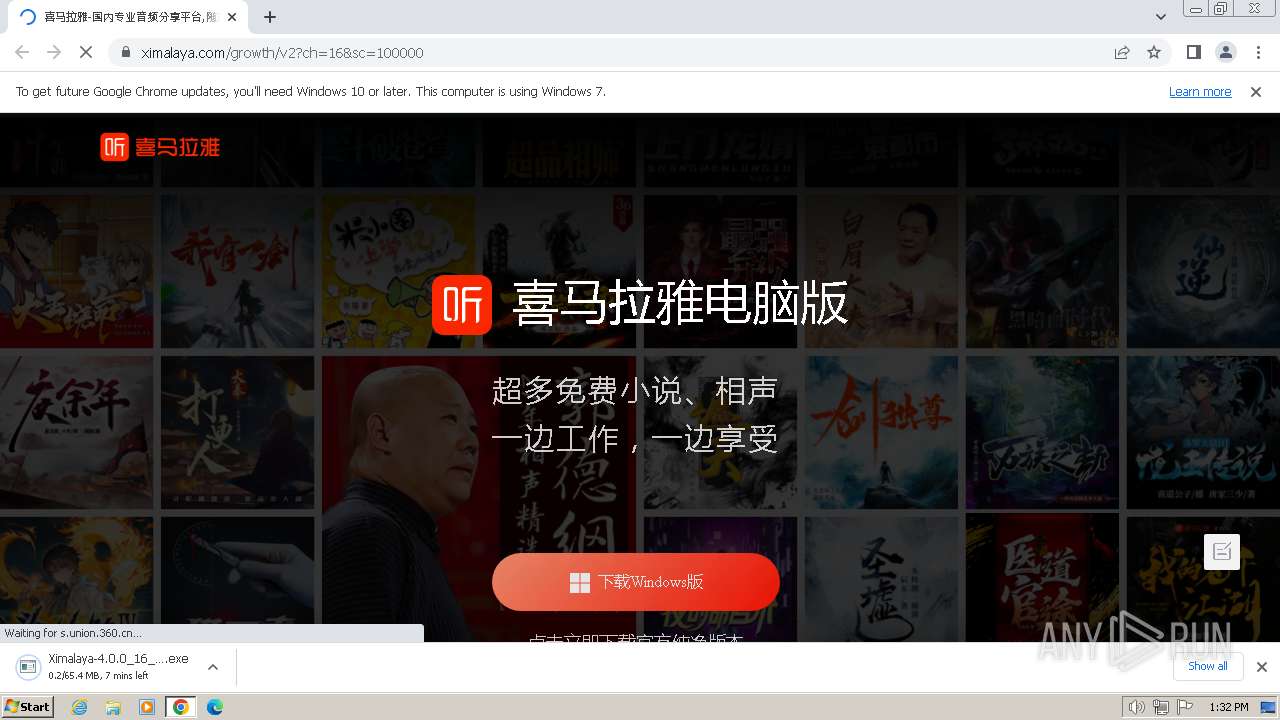
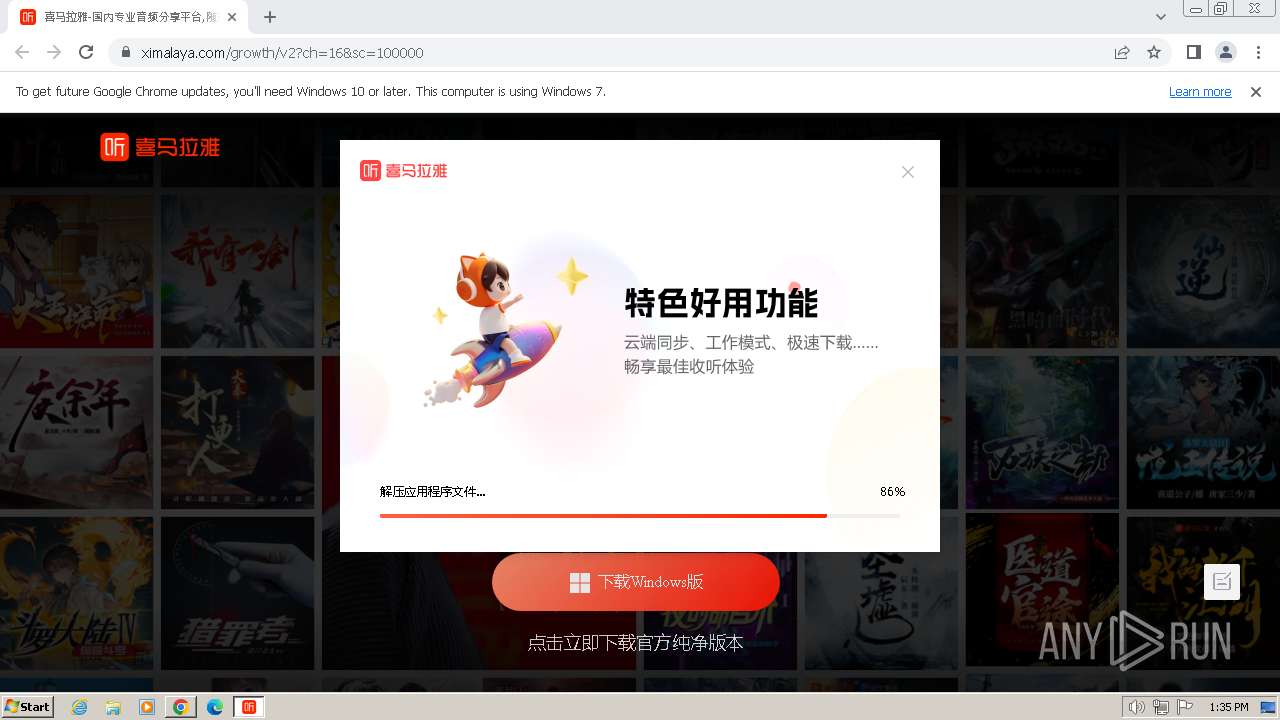
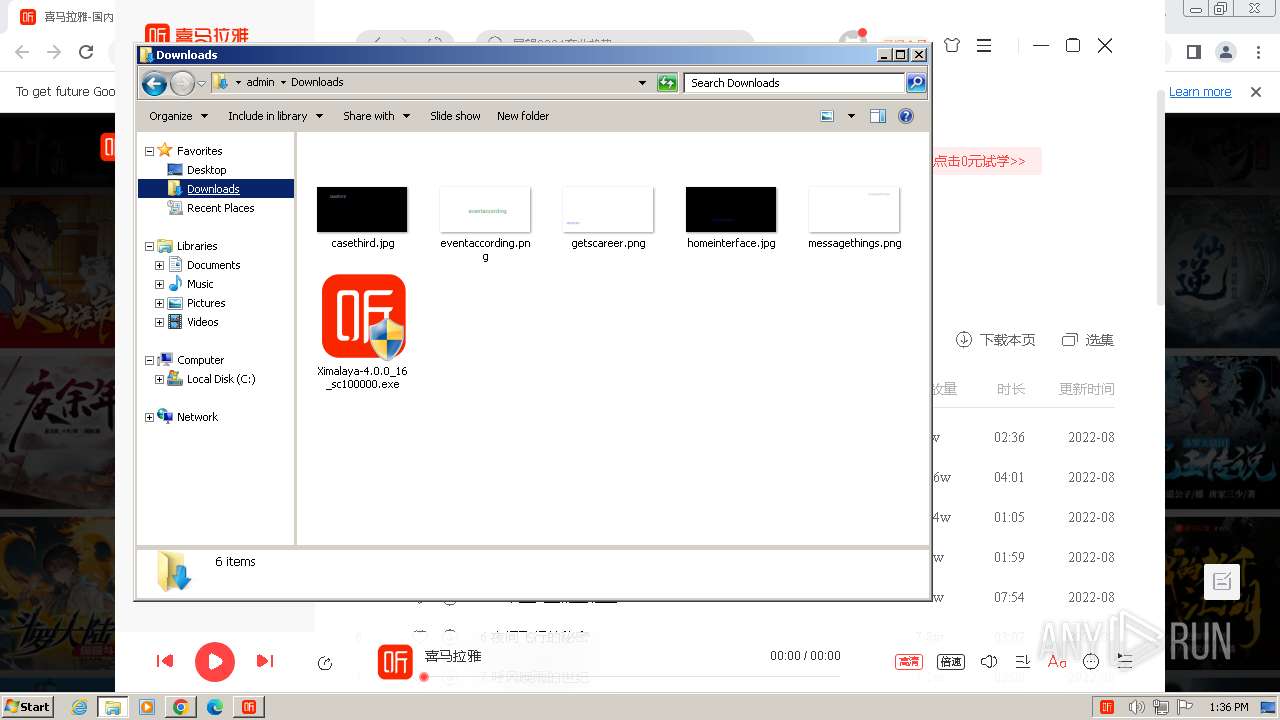
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 1428)
- 喜马拉雅.exe (PID: 3868)
Reads the Internet Settings
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
Executing commands from a ".bat" file
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
The process creates files with name similar to system file names
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
Starts application with an unusual extension
- cmd.exe (PID: 2172)
The process hides Powershell's copyright startup banner
- 喜马拉雅.exe (PID: 2428)
Starts POWERSHELL.EXE for commands execution
- 喜马拉雅.exe (PID: 2428)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 3620)
Reads settings of System Certificates
- 喜马拉雅.exe (PID: 2428)
INFO
Checks supported languages
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 1812)
- chcp.com (PID: 2476)
- 喜马拉雅.exe (PID: 2896)
- 喜马拉雅.exe (PID: 2908)
- 喜马拉雅.exe (PID: 1428)
- 喜马拉雅.exe (PID: 2104)
- 喜马拉雅.exe (PID: 3868)
Checks proxy server information
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
Reads the computer name
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 2908)
- 喜马拉雅.exe (PID: 2896)
- 喜马拉雅.exe (PID: 1428)
- 喜马拉雅.exe (PID: 2104)
- 喜马拉雅.exe (PID: 3868)
Reads the machine GUID from the registry
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
The process uses the downloaded file
- chrome.exe (PID: 120)
- chrome.exe (PID: 3452)
Creates files or folders in the user directory
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 1812)
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 2908)
- 喜马拉雅.exe (PID: 1428)
Drops the executable file immediately after the start
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- chrome.exe (PID: 120)
- chrome.exe (PID: 1792)
Creates files in the program directory
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
Malware-specific behavior (creating "System.dll" in Temp)
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
Create files in a temporary directory
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
Reads Environment values
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 1428)
- 喜马拉雅.exe (PID: 3868)
Drops 7-zip archiver for unpacking
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
Process drops legitimate windows executable
- Ximalaya-4.0.0_16_sc100000.exe (PID: 2444)
Application launched itself
- chrome.exe (PID: 120)
- 喜马拉雅.exe (PID: 2428)
Reads product name
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 1428)
- 喜马拉雅.exe (PID: 3868)
Reads CPU info
- 喜马拉雅.exe (PID: 2428)
Process checks computer location settings
- 喜马拉雅.exe (PID: 2428)
- 喜马拉雅.exe (PID: 1428)
- 喜马拉雅.exe (PID: 3868)
Reads the Internet Settings
- explorer.exe (PID: 3468)
Manual execution by a user
- explorer.exe (PID: 3628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
59
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e558b38,0x6e558b48,0x6e558b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "pc.ximalaya.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 292 | REG QUERY HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v electron.app.喜马拉雅 /t REG_SZ | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1260 --field-trial-handle=1084,i,13745021023643614765,13531103863842641785,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1492 --field-trial-handle=1084,i,13745021023643614765,13531103863842641785,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | powershell.exe -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | 喜马拉雅.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=1976 --field-trial-handle=1084,i,13745021023643614765,13531103863842641785,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 876 | C:\Windows\system32\cmd.exe /d /s /c "REG QUERY HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v electron.app.喜马拉雅 /t REG_SZ" | C:\Windows\System32\cmd.exe | — | 喜马拉雅.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 968 | REG QUERY HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme /t REG_DWORD | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1168 | C:\Windows\system32\cmd.exe /d /s /c "REG QUERY HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme /t REG_DWORD" | C:\Windows\System32\cmd.exe | — | 喜马拉雅.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
19 133
Read events
18 955
Write events
177
Delete events
1
Modification events
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
31
Suspicious files
496
Text files
73
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe127a.TMP | — | |
MD5:— | SHA256:— | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe126a.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe126a.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe1b15.TMP | — | |
MD5:— | SHA256:— | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RFe1558.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
133
DNS requests
115
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWM3QUFZQV9zN2JXZFNHTWhCbGtIMVUwdw/1.0.0.14_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 2.83 Kb | unknown |
492 | chrome.exe | GET | 200 | 43.152.26.110:80 | http://pc.ximalaya.com/ | DE | html | 2.11 Kb | unknown |
2444 | Ximalaya-4.0.0_16_sc100000.exe | GET | 200 | 101.33.11.106:80 | http://m.ximalaya.com/web-config/api/jc/queryAllData?app=web&group=xmly-pc&key=nsis-config | DE | binary | 617 b | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 7.29 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 9.99 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 361 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 10.1 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 12.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | US | binary | 5.51 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
492 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
120 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
492 | chrome.exe | 43.152.26.110:80 | pc.ximalaya.com | ACE | DE | unknown |
492 | chrome.exe | 90.84.250.19:443 | s1.xmcdn.com | Orange | FR | unknown |
492 | chrome.exe | 43.152.26.110:443 | pc.ximalaya.com | ACE | DE | unknown |
492 | chrome.exe | 216.58.212.132:443 | www.google.com | GOOGLE | US | whitelisted |
492 | chrome.exe | 90.84.250.28:443 | s1.xmcdn.com | Orange | FR | unknown |
492 | chrome.exe | 104.192.110.245:443 | jspassport.ssl.qhimg.com | Beijing Qihu Technology Company Limited | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
pc.ximalaya.com |
| unknown |
s1.xmcdn.com |
| unknown |
www.ximalaya.com |
| unknown |
imagev2.xmcdn.com |
| unknown |
mermaid.ximalaya.com |
| unknown |
www.google.com |
| whitelisted |
fdfs.xmcdn.com |
| unknown |
jspassport.ssl.qhimg.com |
| whitelisted |
m.ximalaya.com |
| unknown |
Threats
Process | Message |
|---|---|
Ximalaya-4.0.0_16_sc100000.exe | LabelUI, font, 0
|
Ximalaya-4.0.0_16_sc100000.exe | HorizontalLayoutUI, borderround, 4,4,4,4
|
Ximalaya-4.0.0_16_sc100000.exe | RichEdit, textcolor, #FF000000
|
Ximalaya-4.0.0_16_sc100000.exe | HorizontalLayoutUI, height, 40
|
Ximalaya-4.0.0_16_sc100000.exe | RichEdit, height, 24
|
Ximalaya-4.0.0_16_sc100000.exe | RichEdit, wantreturn, false
|
Ximalaya-4.0.0_16_sc100000.exe | HorizontalLayoutUI, bkcolor, #FFFFFFFF
|
Ximalaya-4.0.0_16_sc100000.exe | ButtonUI, name, btnSelectDir
|
Ximalaya-4.0.0_16_sc100000.exe | RichEdit, bkcolor, #FFFFFFFF
|
Ximalaya-4.0.0_16_sc100000.exe | HorizontalLayoutUI, inset, 8,8,8,8
|