| File name: | bsod.exe |
| Full analysis: | https://app.any.run/tasks/bd727b1c-e8a7-444f-8692-1bf958aae54a |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2024, 03:48:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 5BF557EC1E159AD37AE2D3C48CA1691B |
| SHA1: | 995A3B9C3C1E1ED69E8EA7271EF8AC9AA9622722 |
| SHA256: | AEC1E1115BE6507E190AFC0504DC19ED1EB4FC26B115C987C2CB4D9311BA9421 |
| SSDEEP: | 1536:55zACEc7lu/pTUfzM74mVvtfsa7Rn/aHwWLcWgIxnC+C:5WHc7lu/pT+M7VVvtEkRS8WgIxnC+C |
MALICIOUS
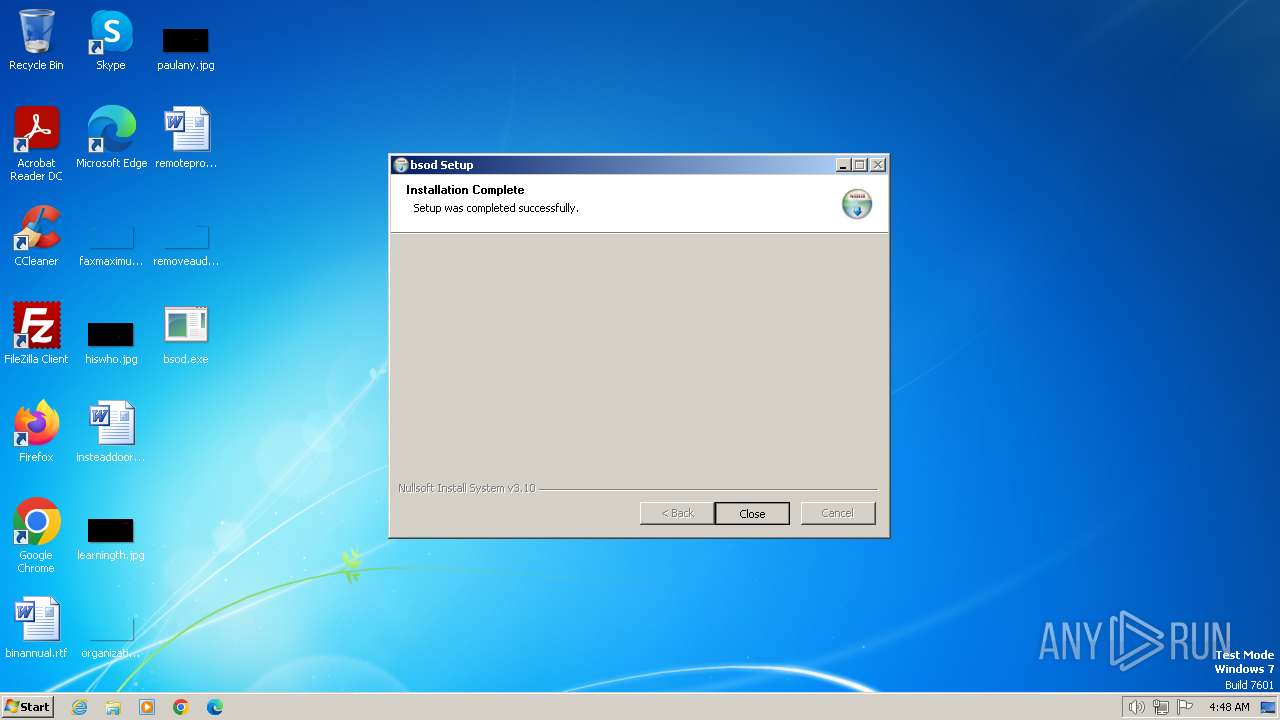
Drops the executable file immediately after the start
- bsod.exe (PID: 3996)
SUSPICIOUS
Executable content was dropped or overwritten
- bsod.exe (PID: 3996)
Reads security settings of Internet Explorer
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
Executing commands from a ".bat" file
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
Reads the Internet Settings
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
Starts CMD.EXE for commands execution
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
INFO
Reads the computer name
- bsod.exe (PID: 2688)
- bsod.exe (PID: 3996)
- bsod.exe (PID: 748)
Create files in a temporary directory
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
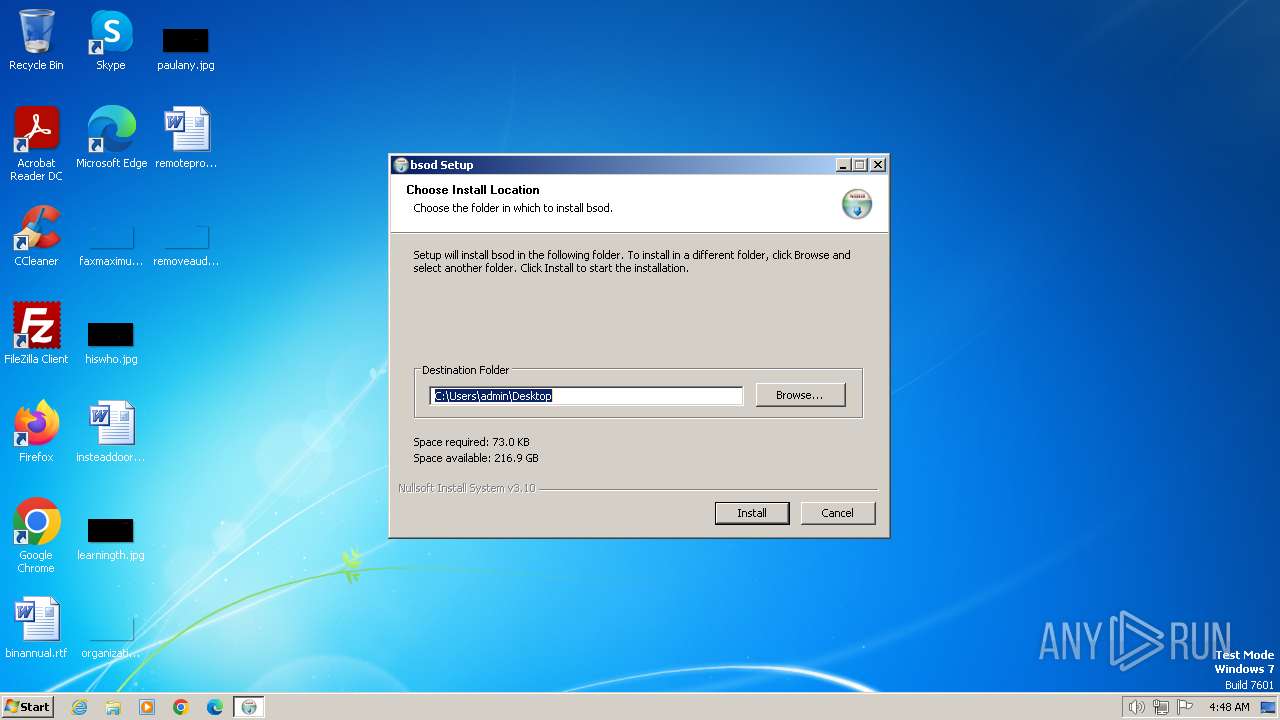
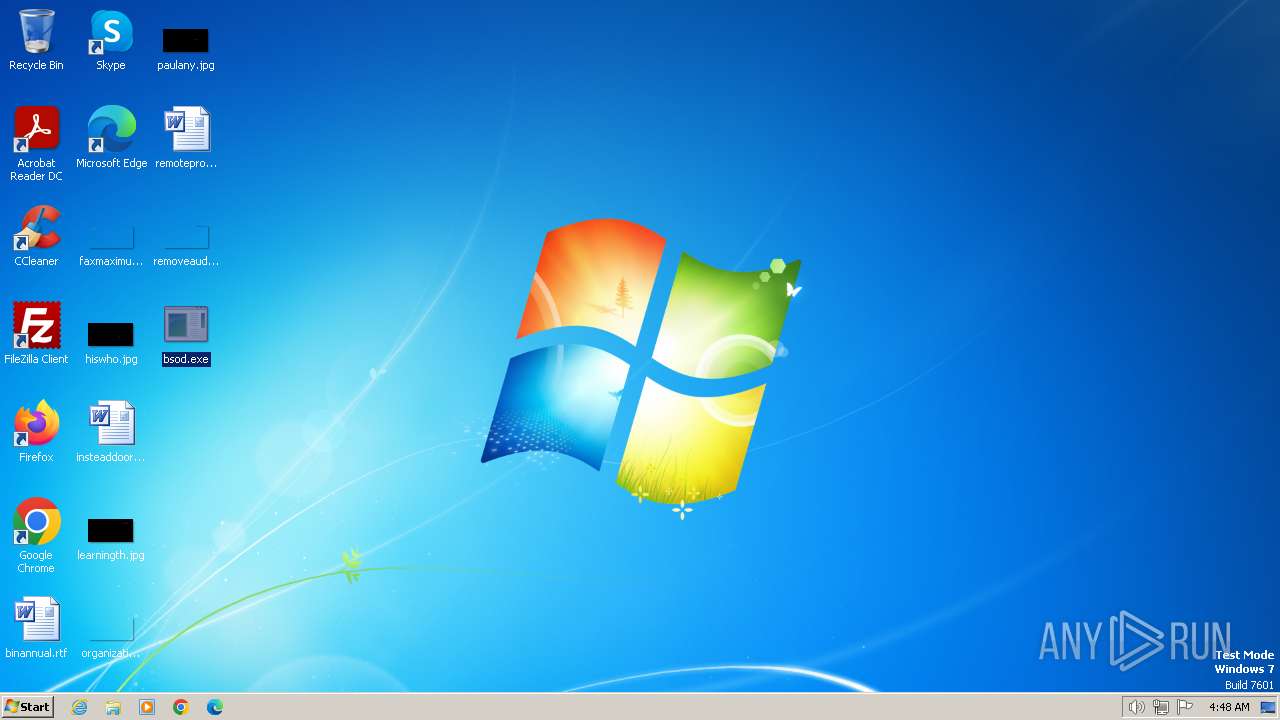
Manual execution by a user
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
Checks supported languages
- bsod.exe (PID: 3996)
- bsod.exe (PID: 2688)
- bsod.exe (PID: 748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:30 16:55:15+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x351c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
47
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Users\admin\Desktop\bsod.exe" | C:\Users\admin\Desktop\bsod.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 848 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\i6.bat" " | C:\Windows\System32\cmd.exe | — | bsod.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\bsod.exe" | C:\Users\admin\AppData\Local\Temp\bsod.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\Desktop\bsod.exe" | C:\Users\admin\Desktop\bsod.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3068 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\i6.bat" " | C:\Windows\System32\cmd.exe | — | bsod.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\AppData\Local\Temp\bsod.exe" | C:\Users\admin\AppData\Local\Temp\bsod.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
7 207
Read events
7 191
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2688) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2688) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2688) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2688) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (748) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (748) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (748) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (748) bsod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | bsod.exe | C:\Users\admin\Desktop\bsod.exe | executable | |
MD5:— | SHA256:— | |||
| 2688 | bsod.exe | C:\Users\admin\AppData\Local\Temp\i6.t | binary | |
MD5:— | SHA256:— | |||
| 2688 | bsod.exe | C:\Users\admin\AppData\Local\Temp\i6.bat | text | |
MD5:— | SHA256:— | |||
| 848 | cmd.exe | C:\Users\admin\AppData\Local\Temp\i6.f | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |