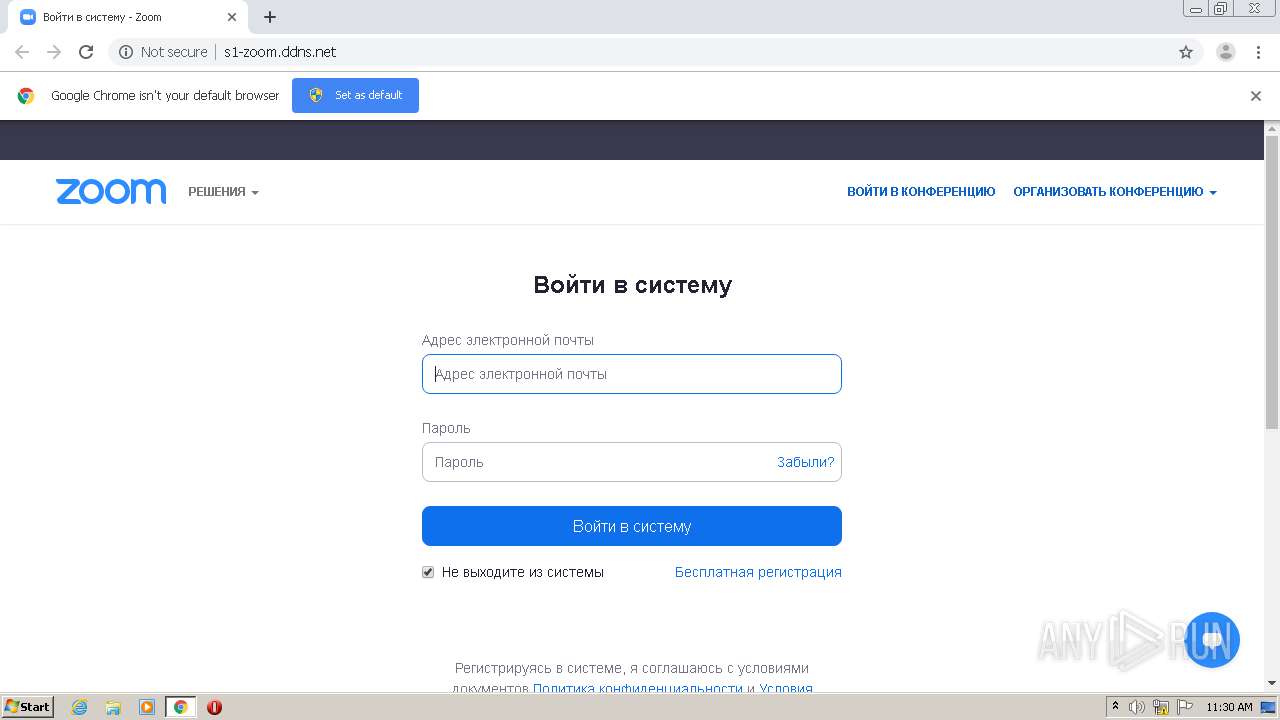
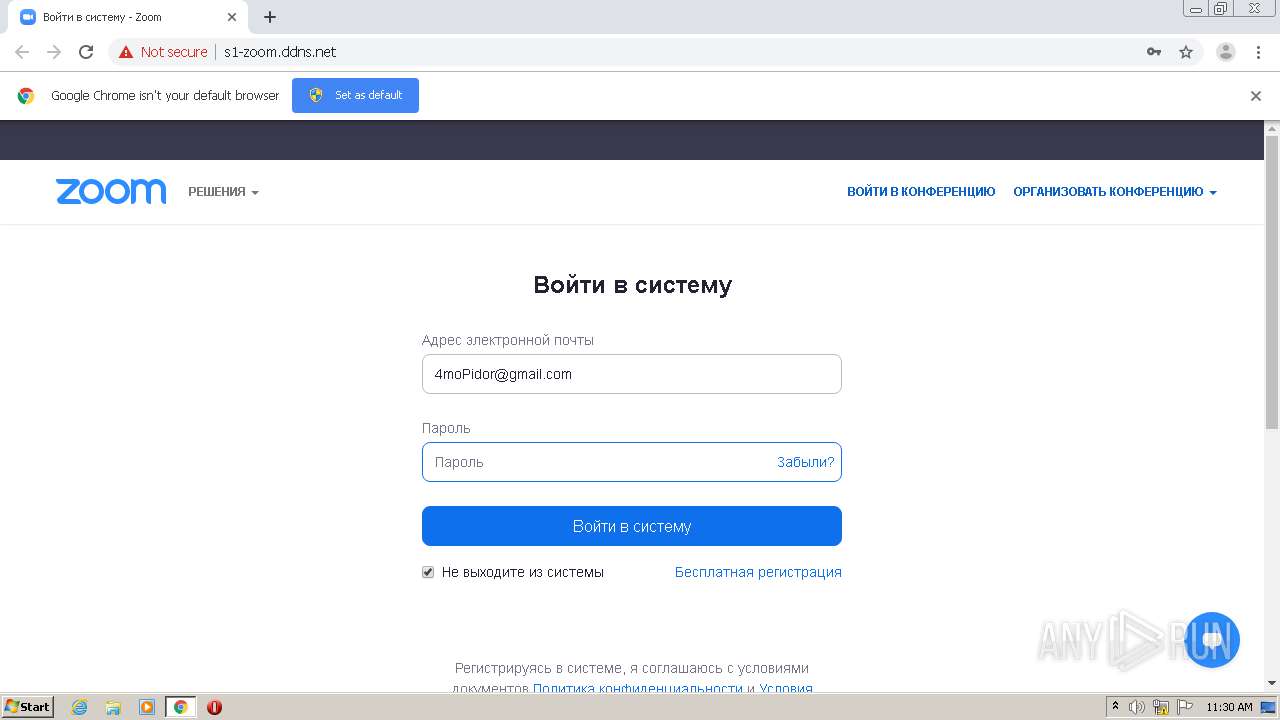
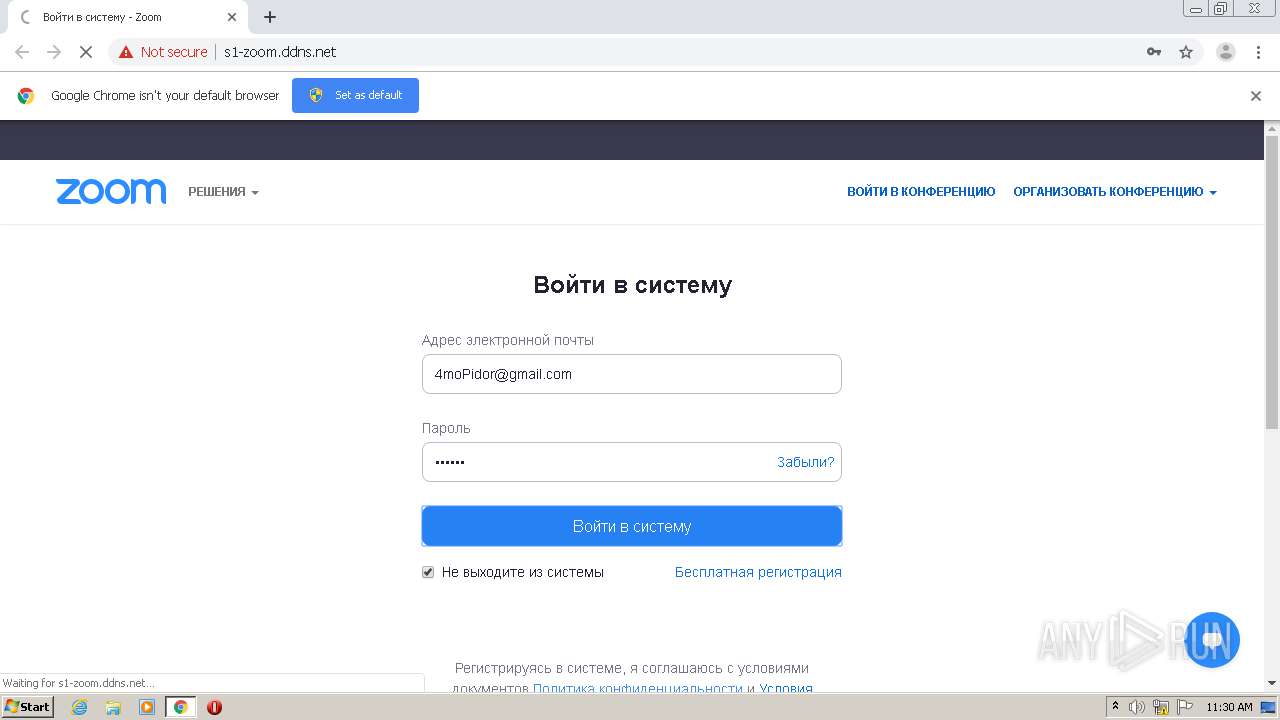
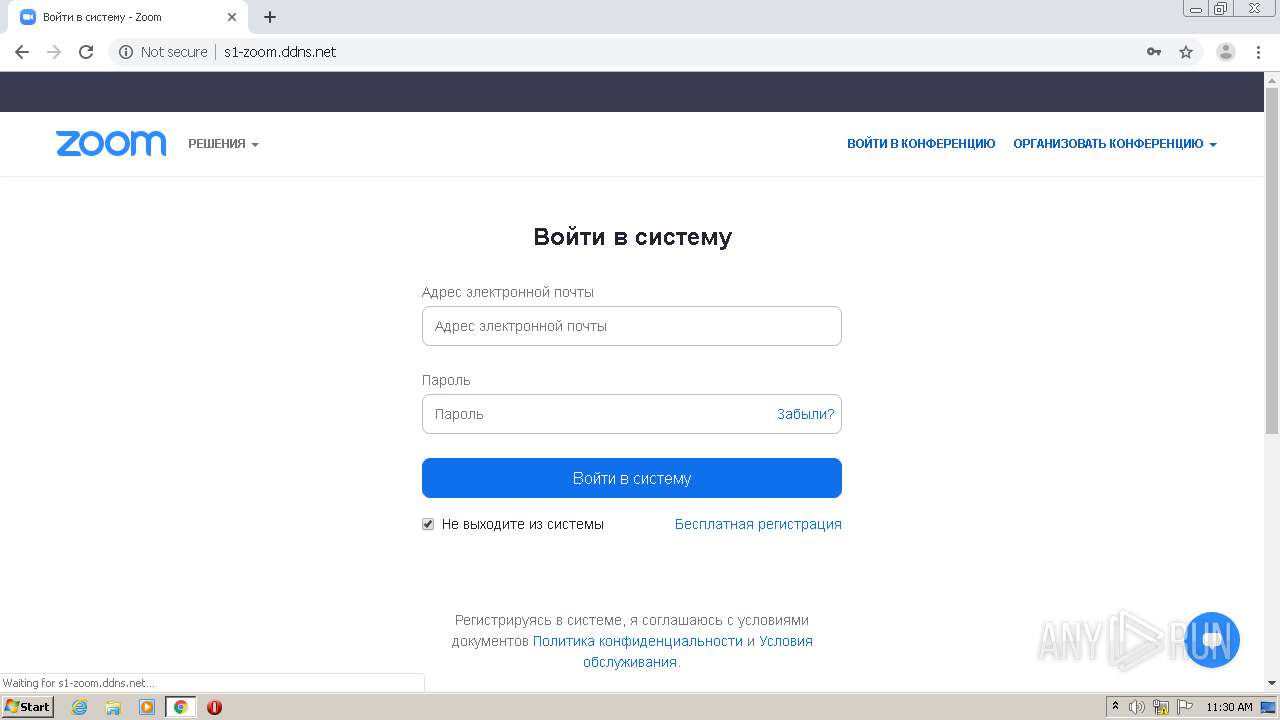
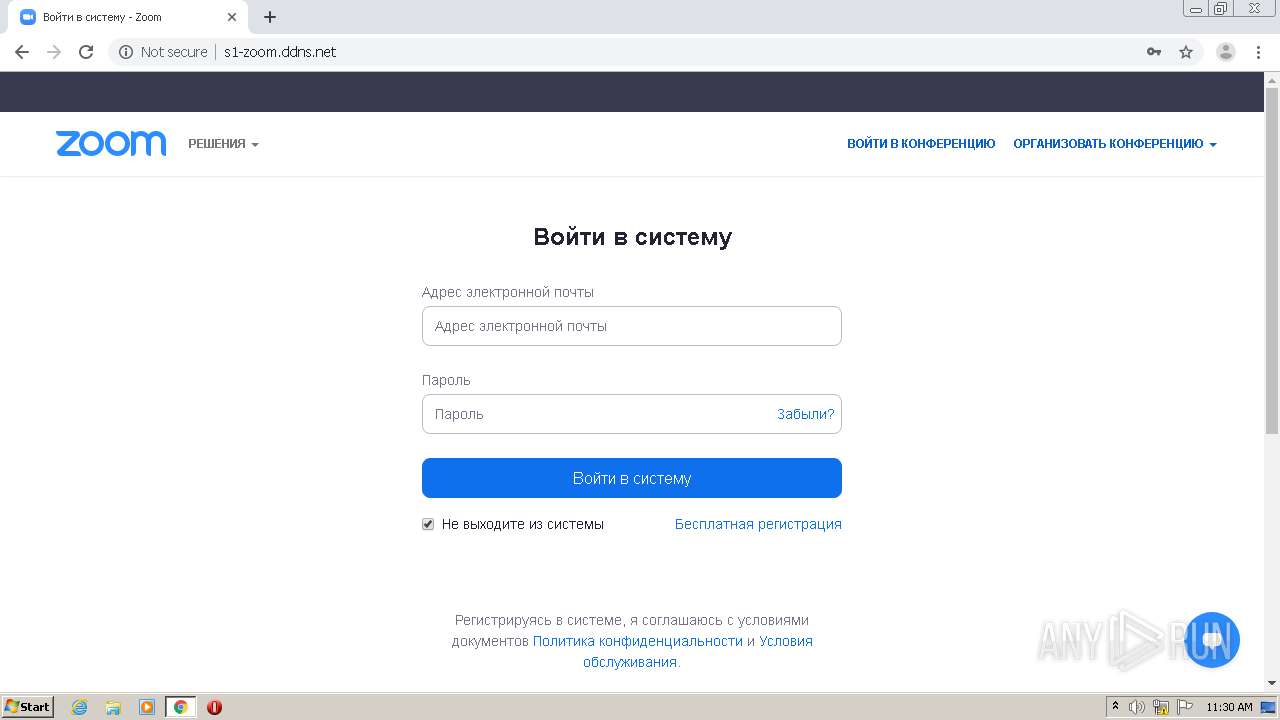
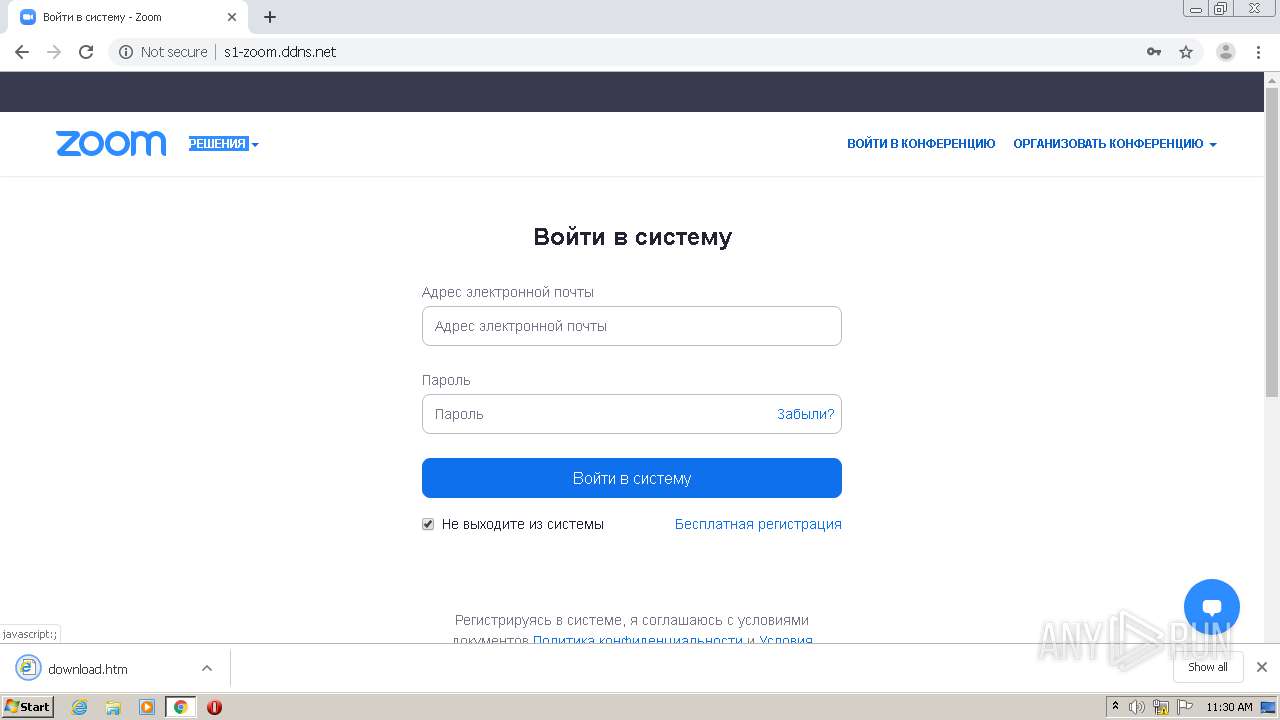
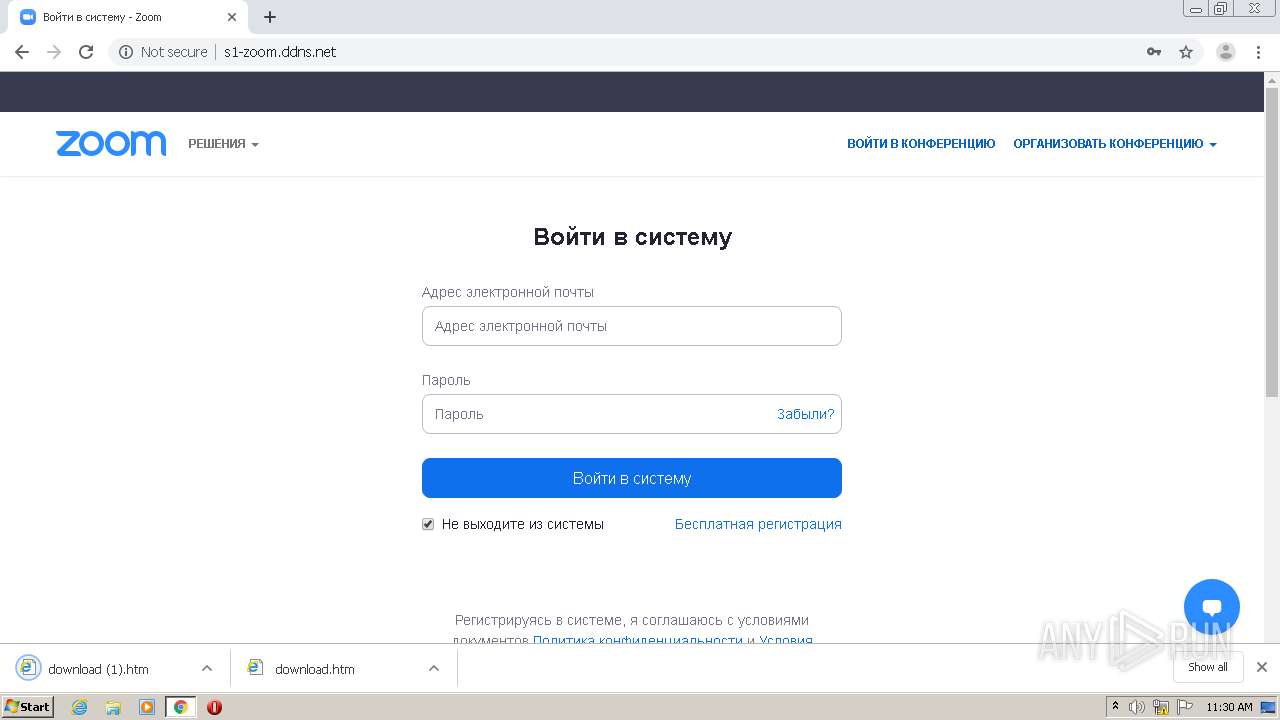
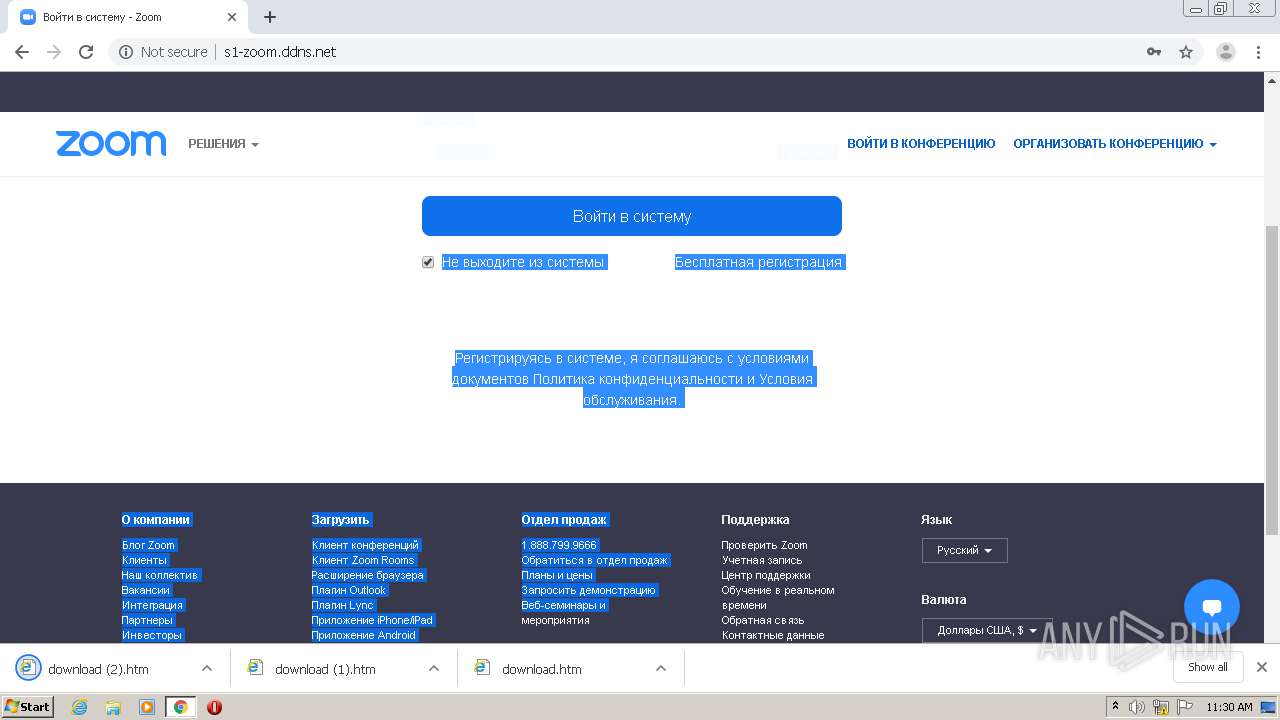
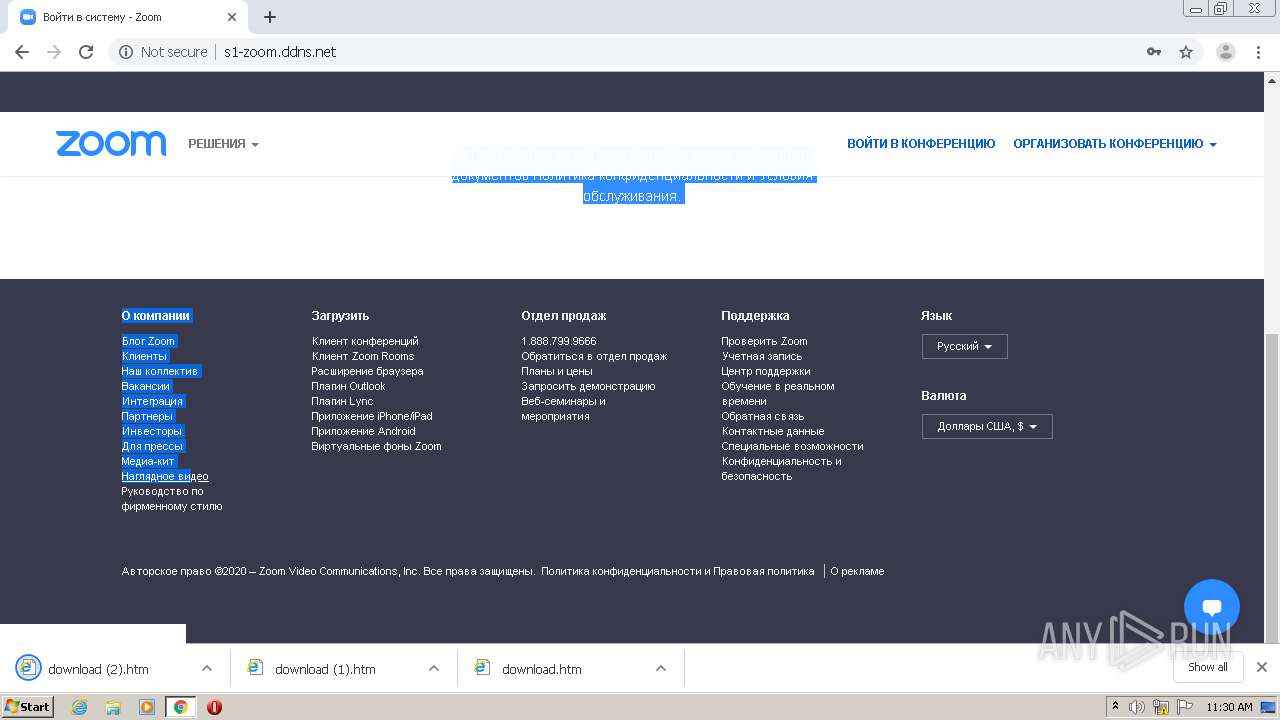
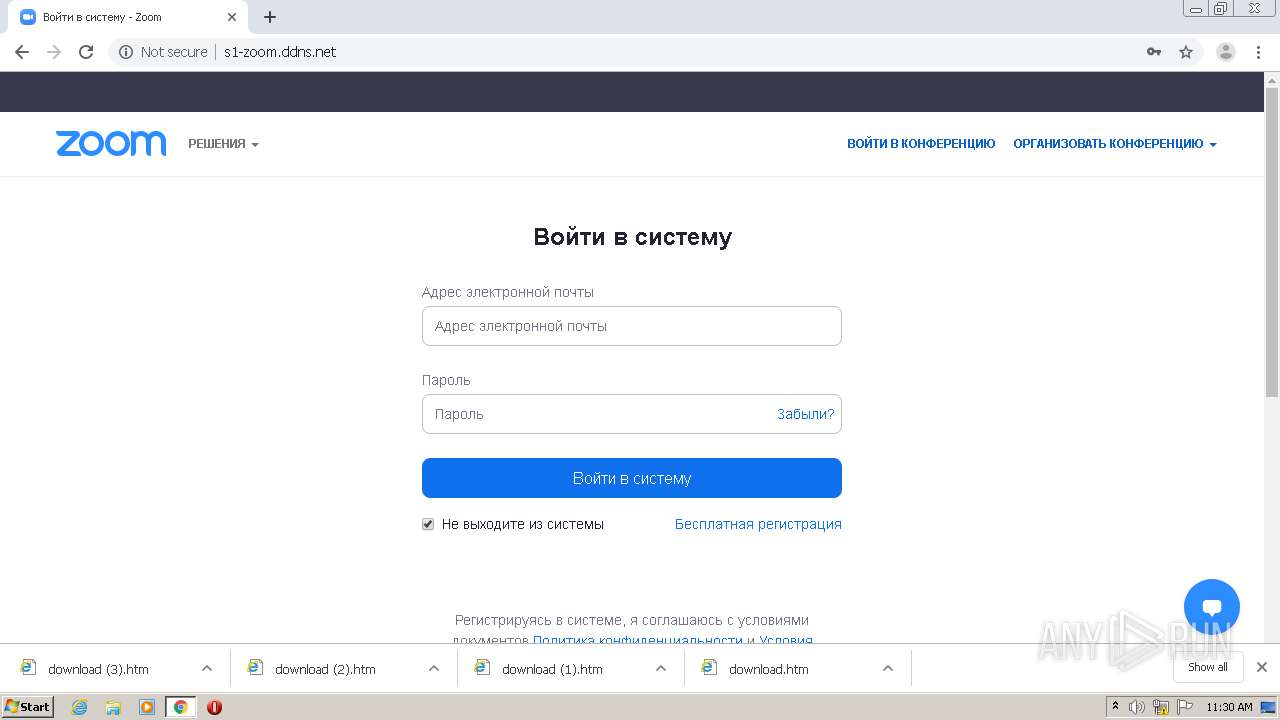
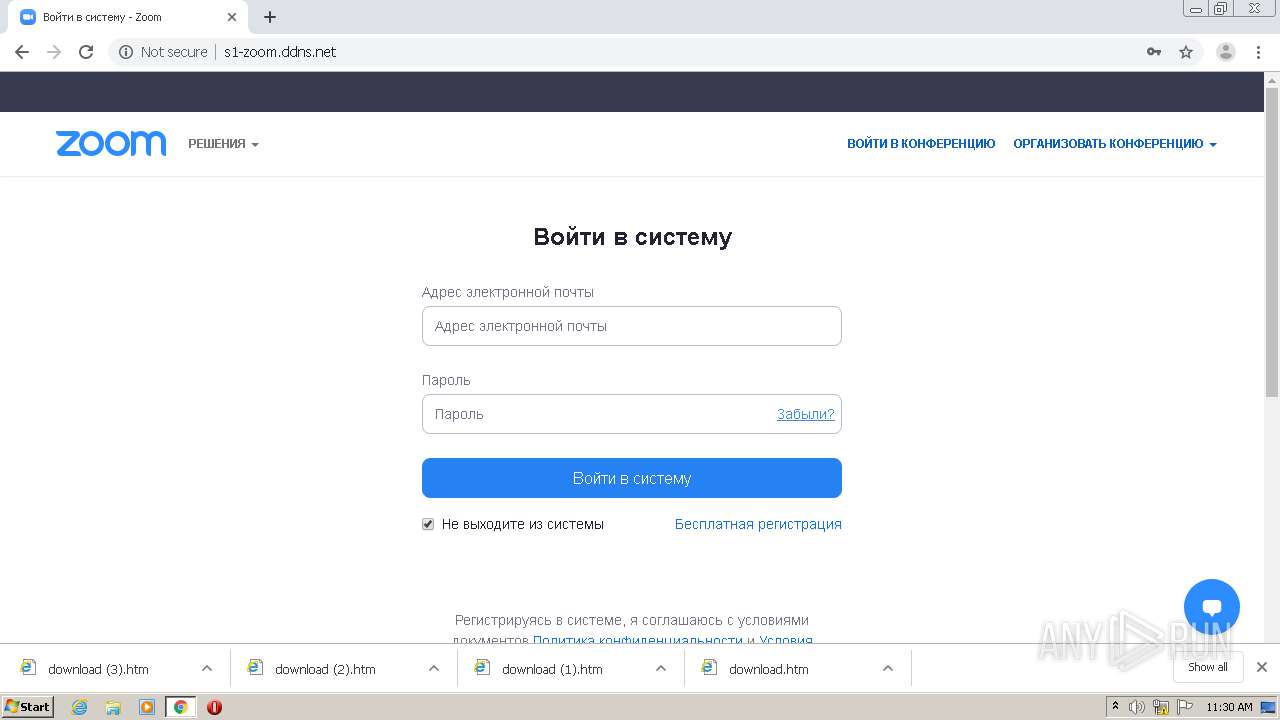
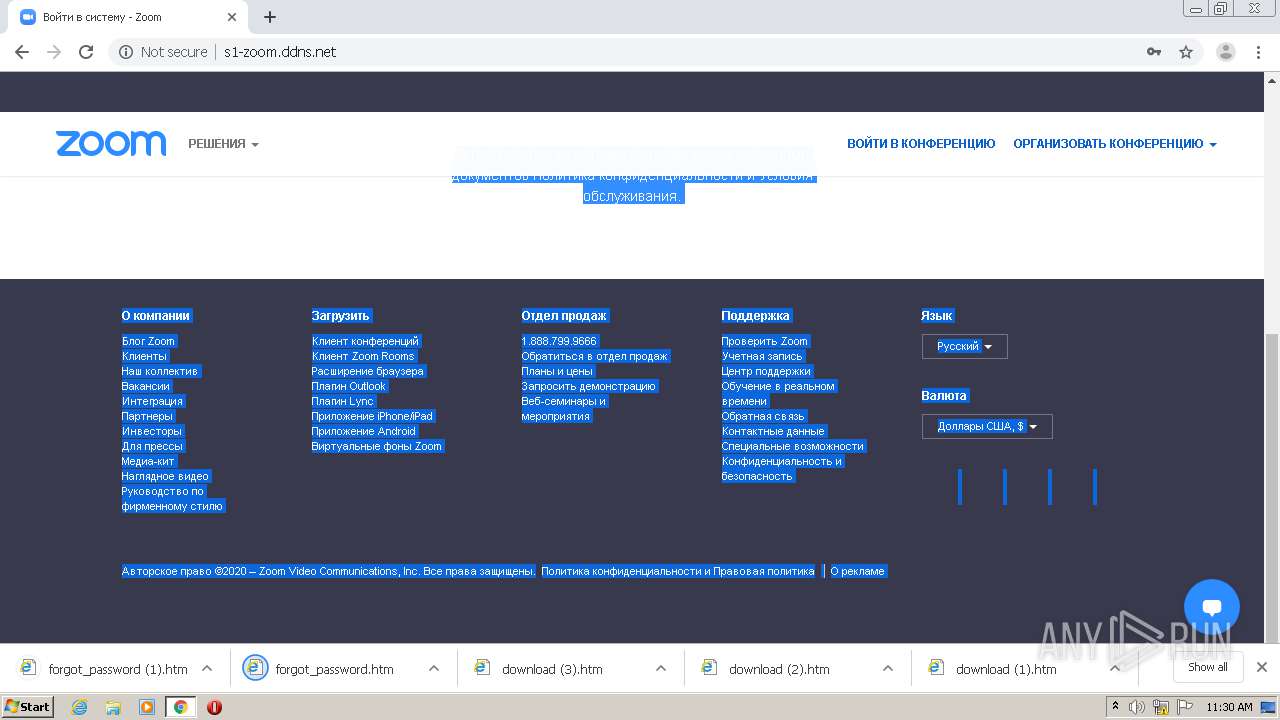
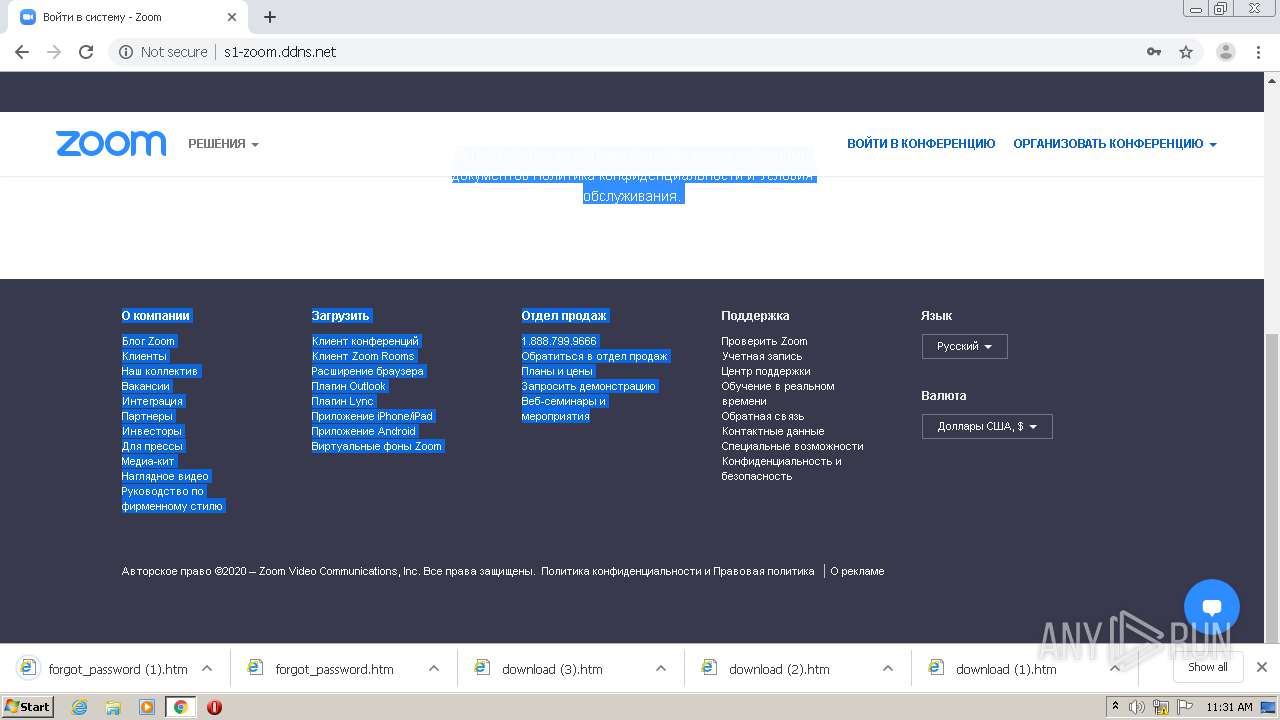
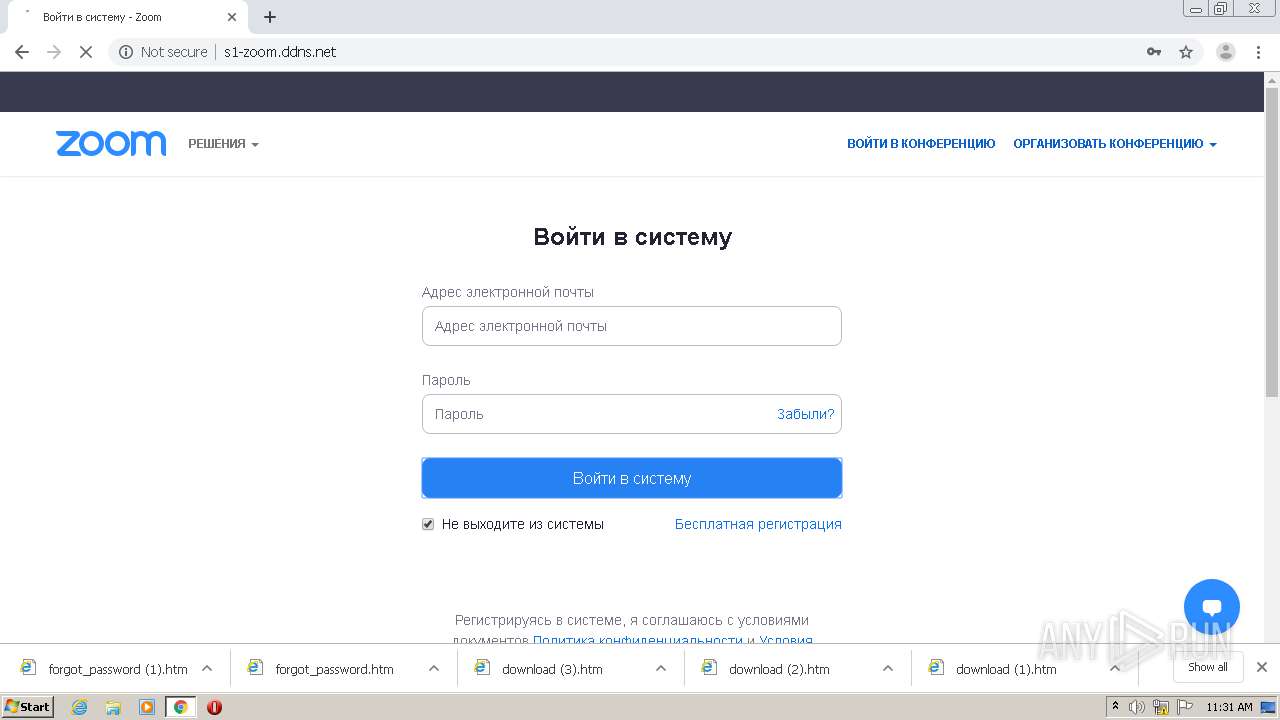
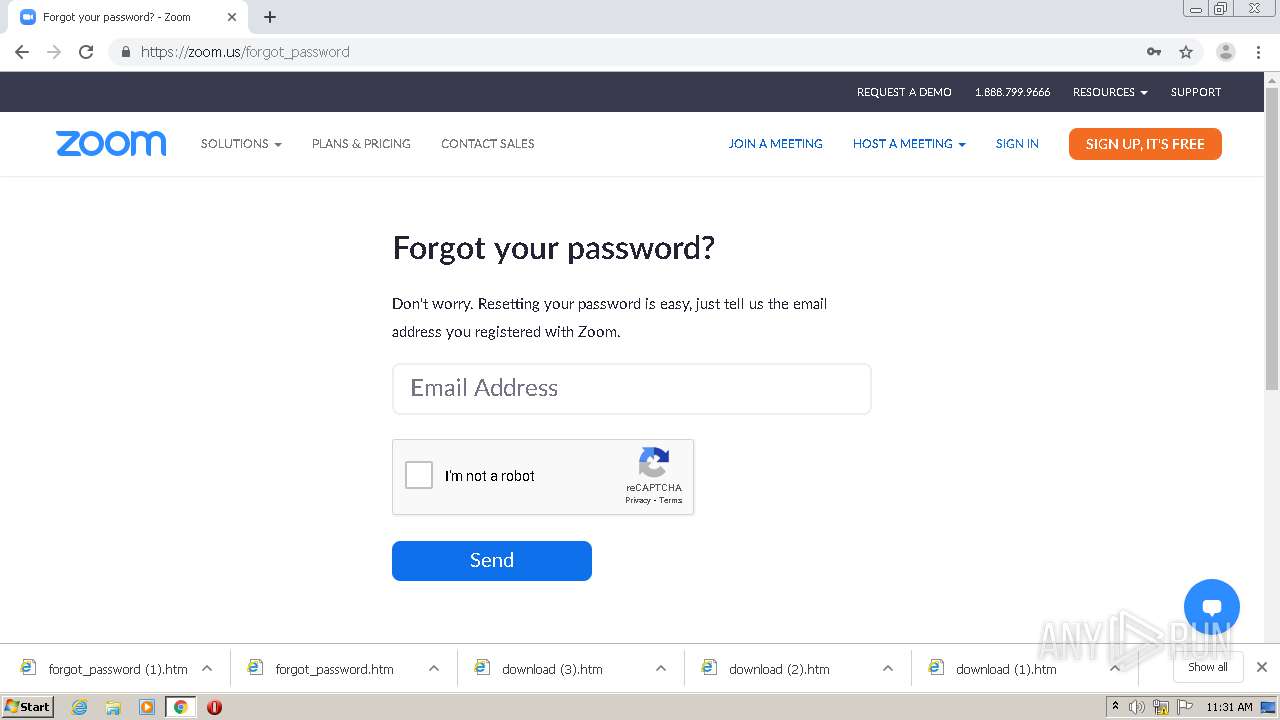
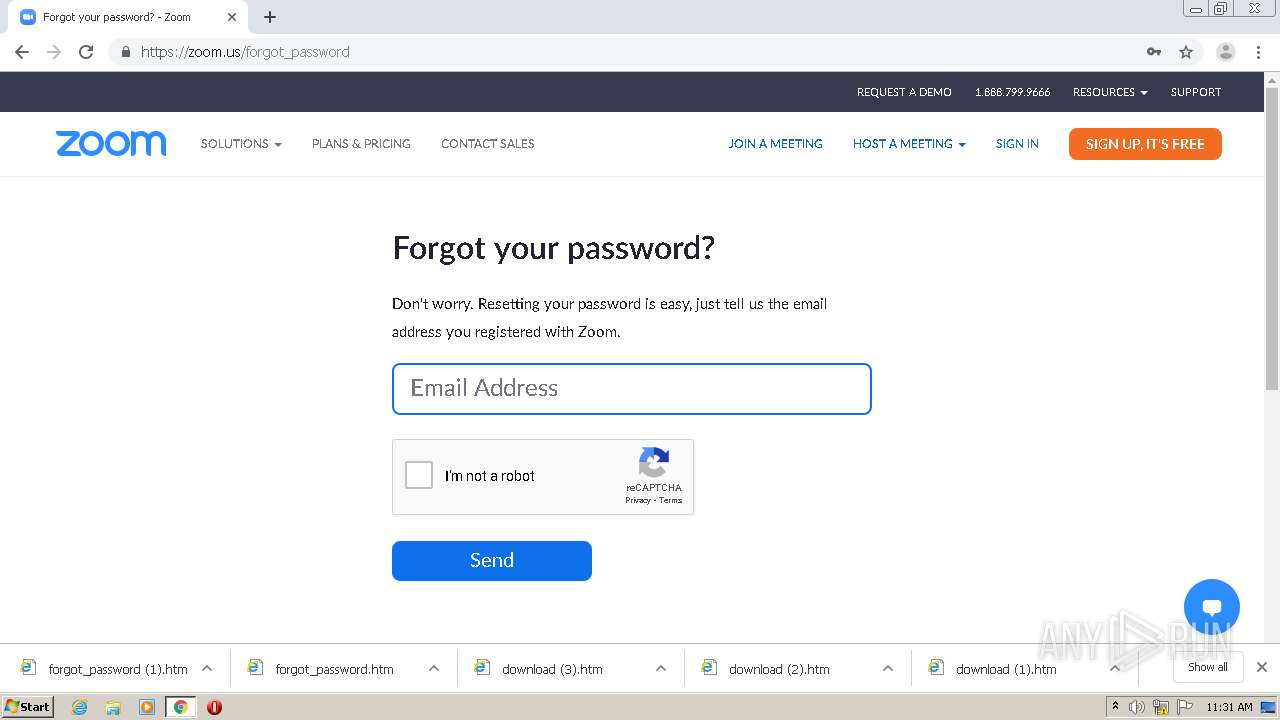
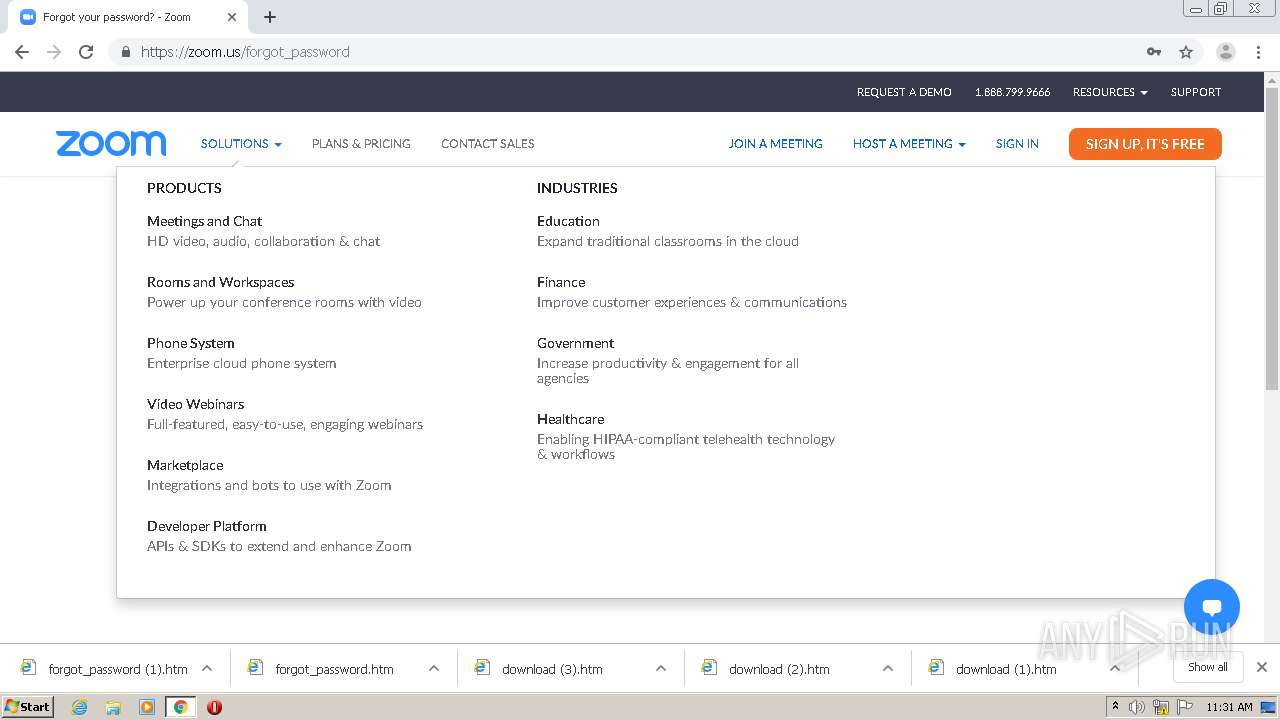
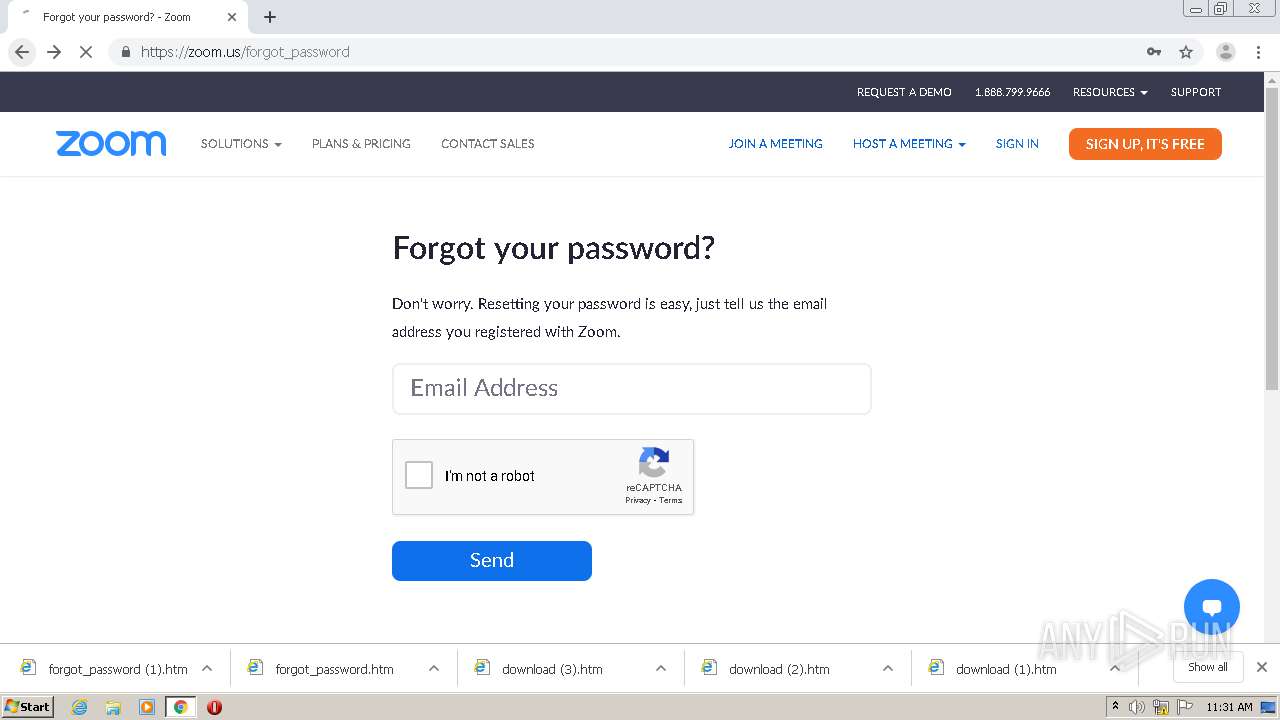
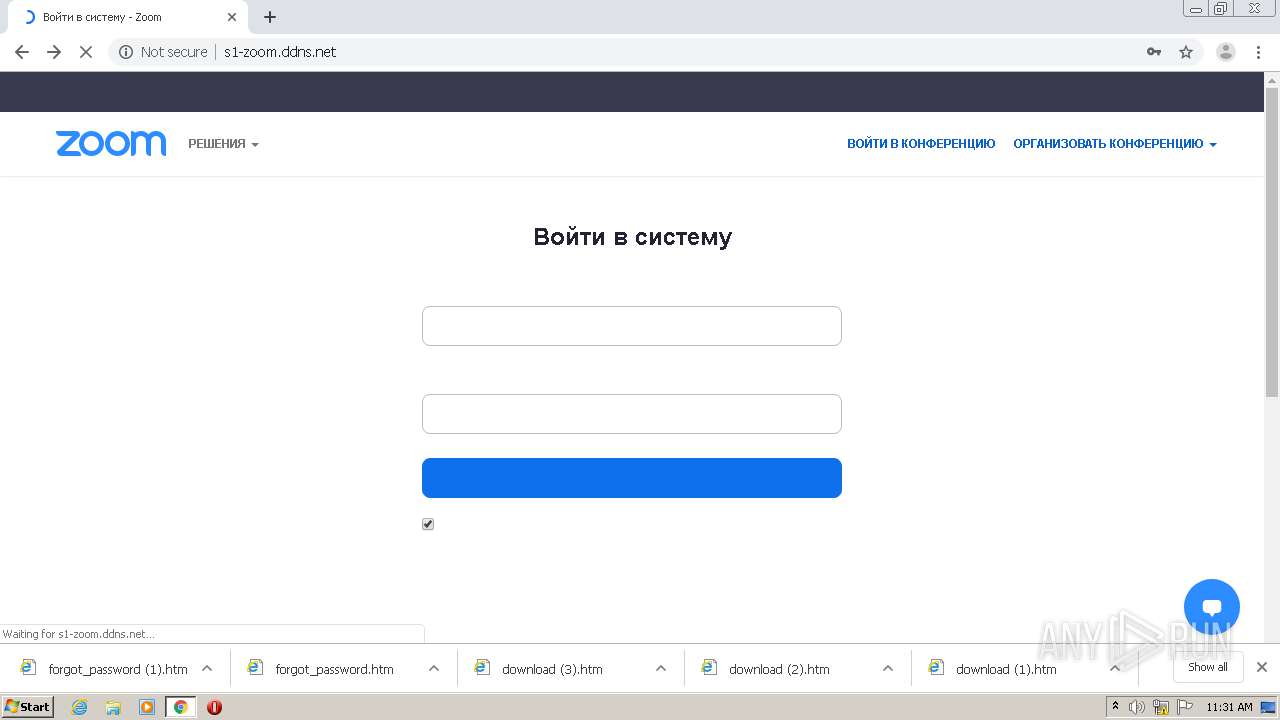
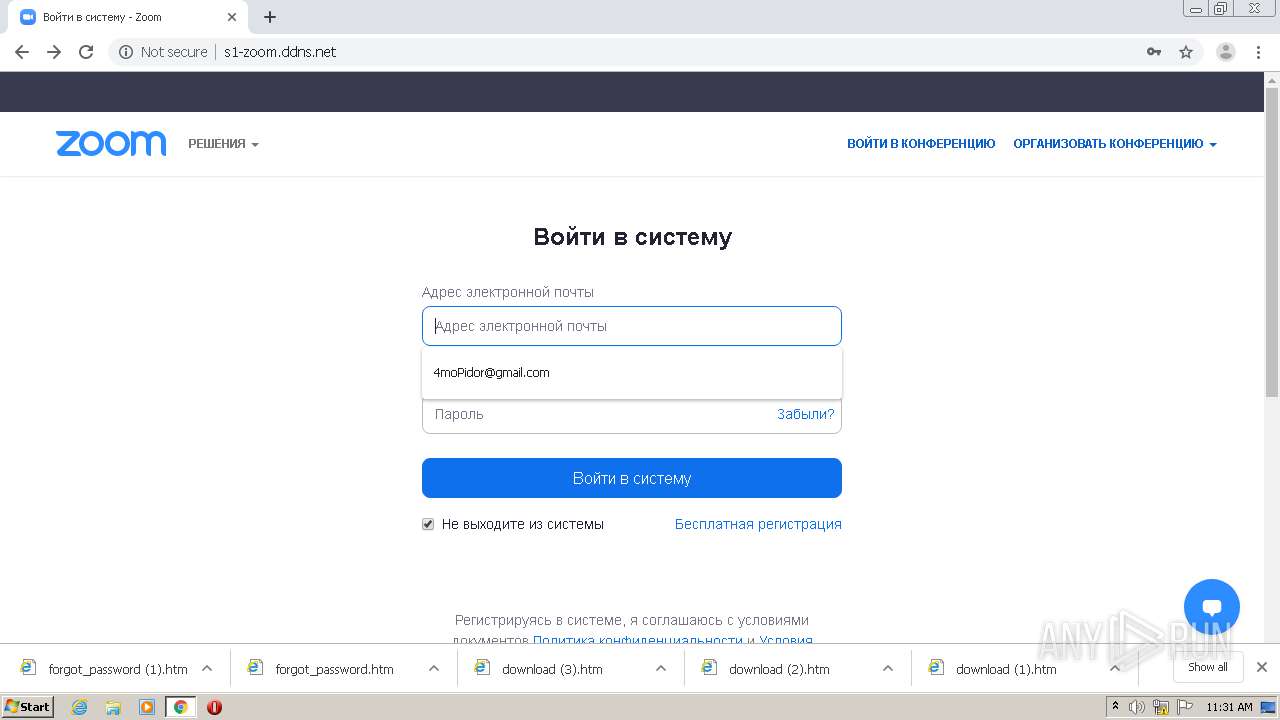
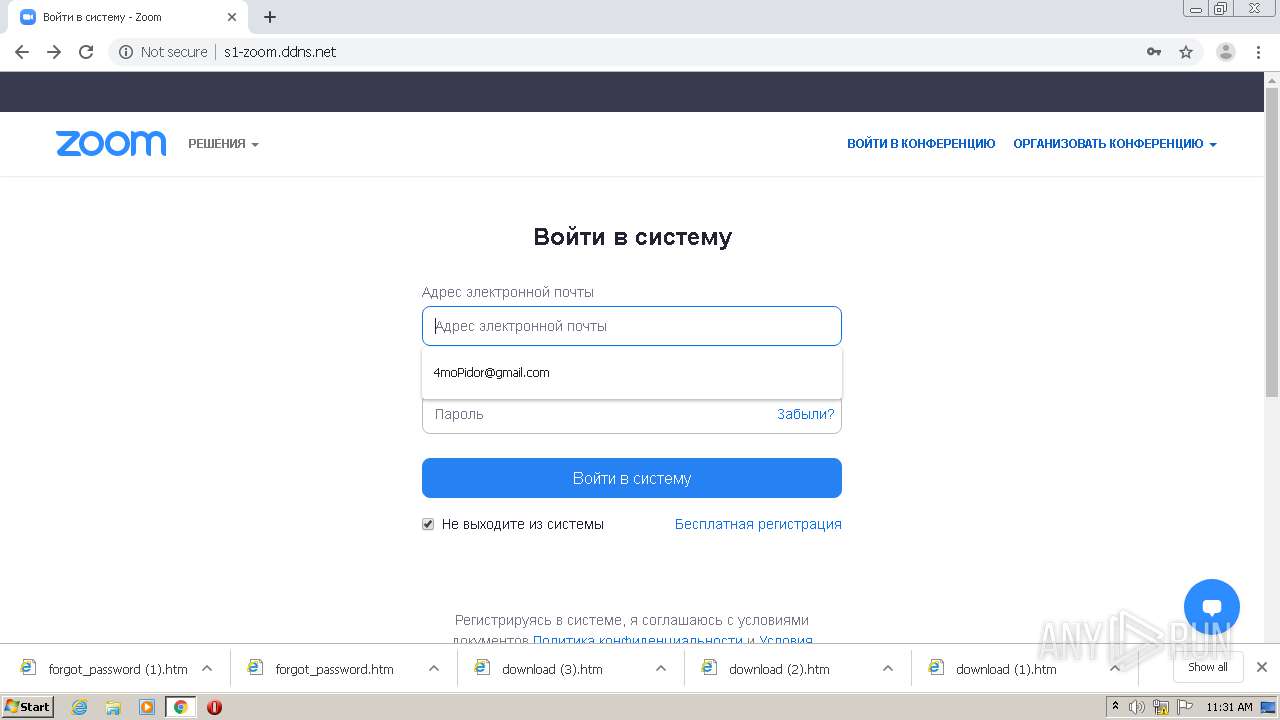
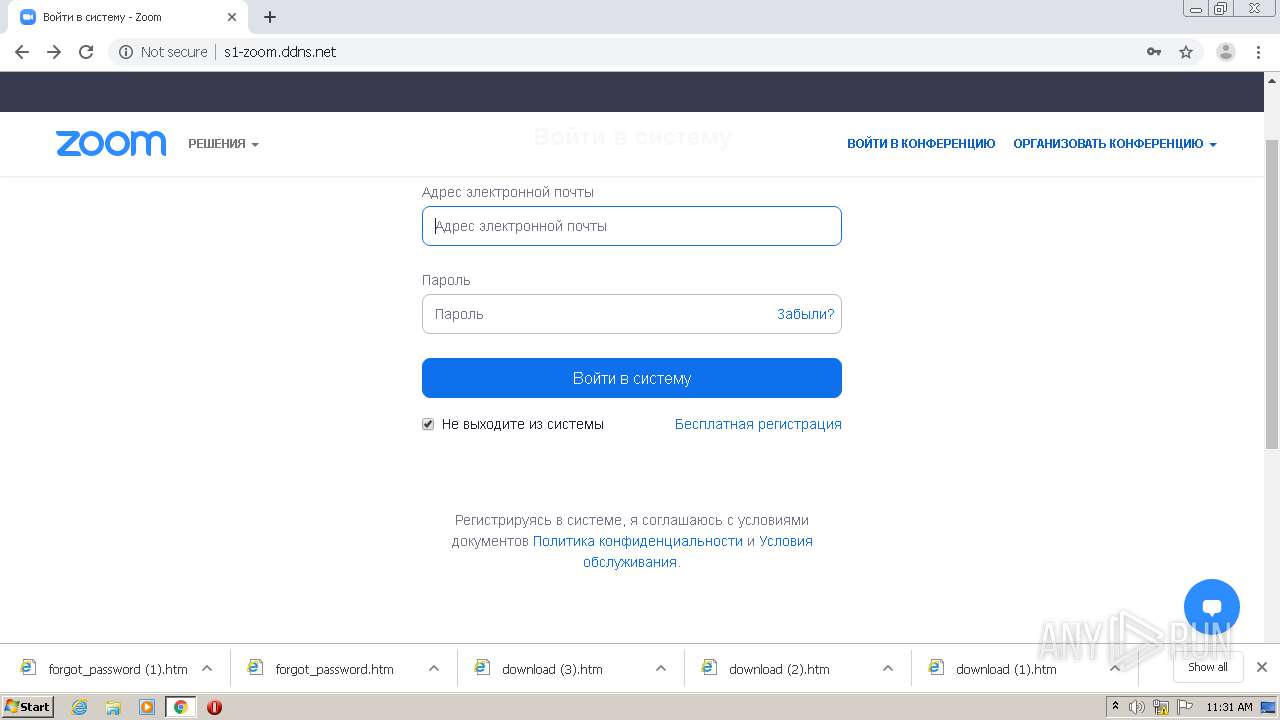
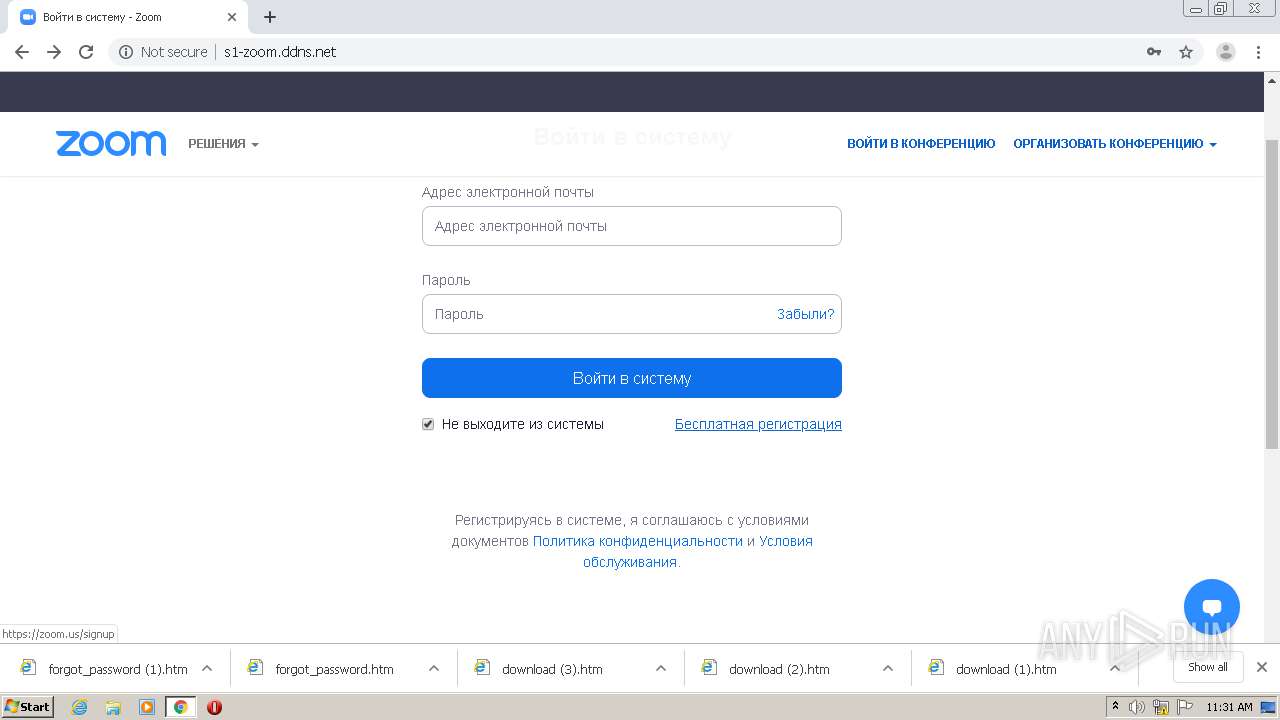
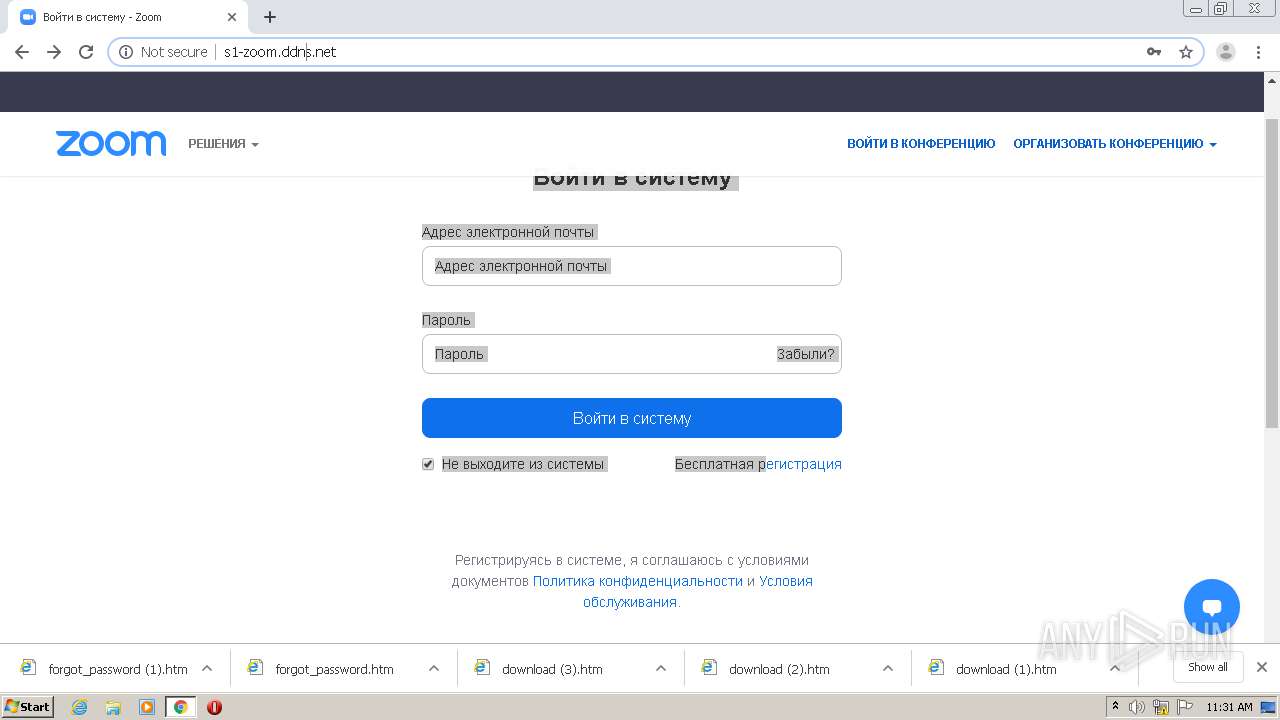
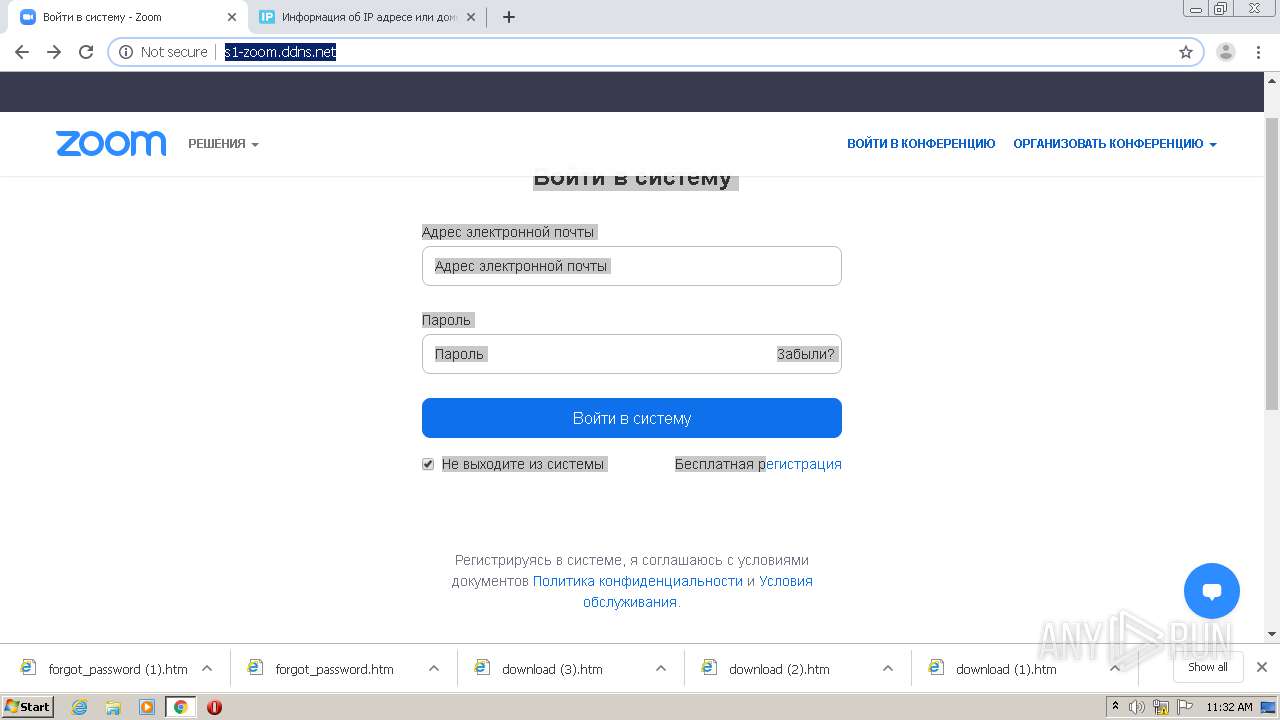
| URL: | http://s1-zoom.ddns.net/ |
| Full analysis: | https://app.any.run/tasks/f2111853-d293-457d-a069-5ce224045d31 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 11:29:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C3874DF91F2E7460CACE2826C40CF20A |
| SHA1: | DD4F786F5FB37C15DCF8B166E9511818FA6A669F |
| SHA256: | AEB542417B6CDED9CAD878163BAB4A90398B1A07AAC1D61A518C56FCD1B0B4B5 |
| SSDEEP: | 3:N1KNUKIL3iIs:C6TL8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 1896)
Reads the hosts file
- chrome.exe (PID: 2580)
- chrome.exe (PID: 1896)
Application launched itself
- chrome.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
27
Malicious processes
0
Suspicious processes
0
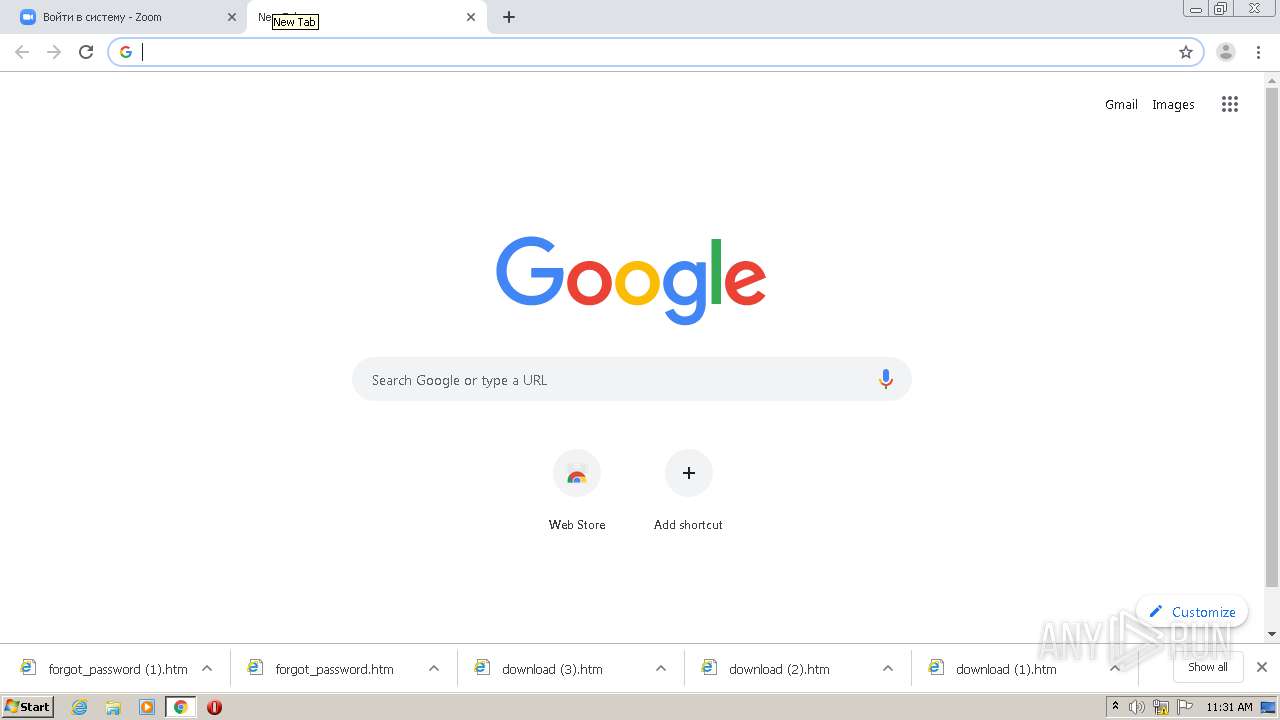
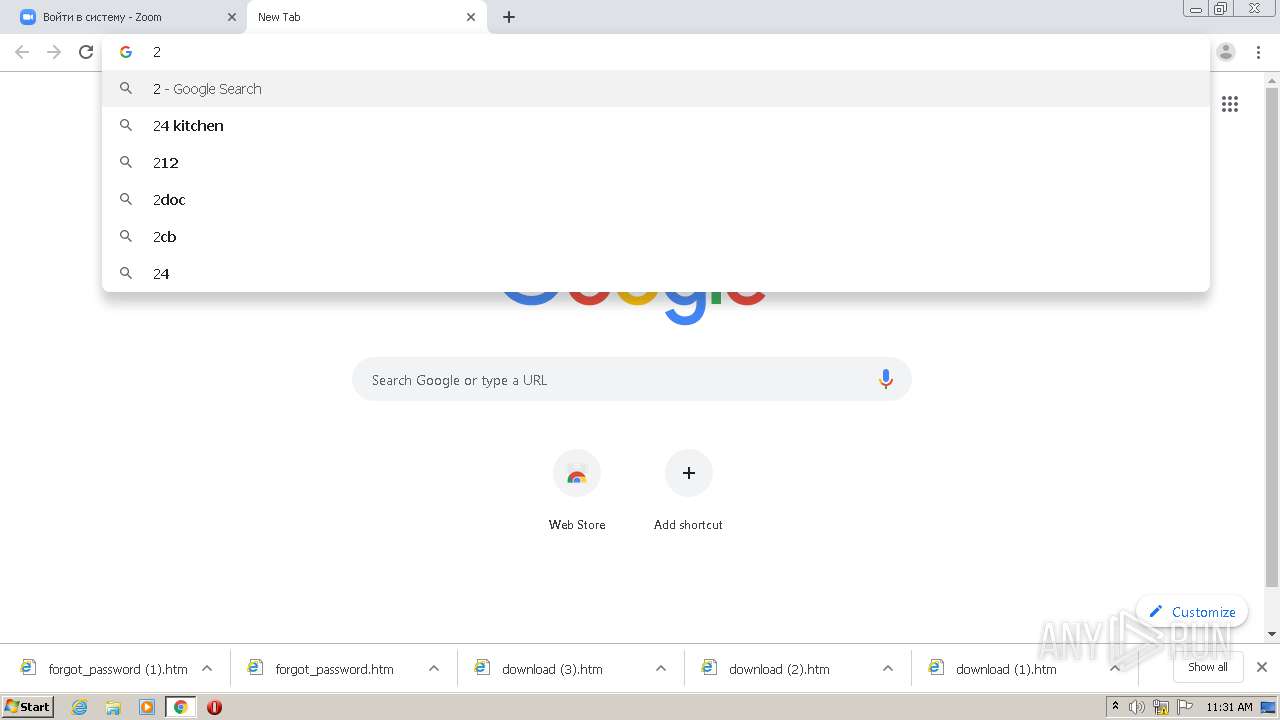
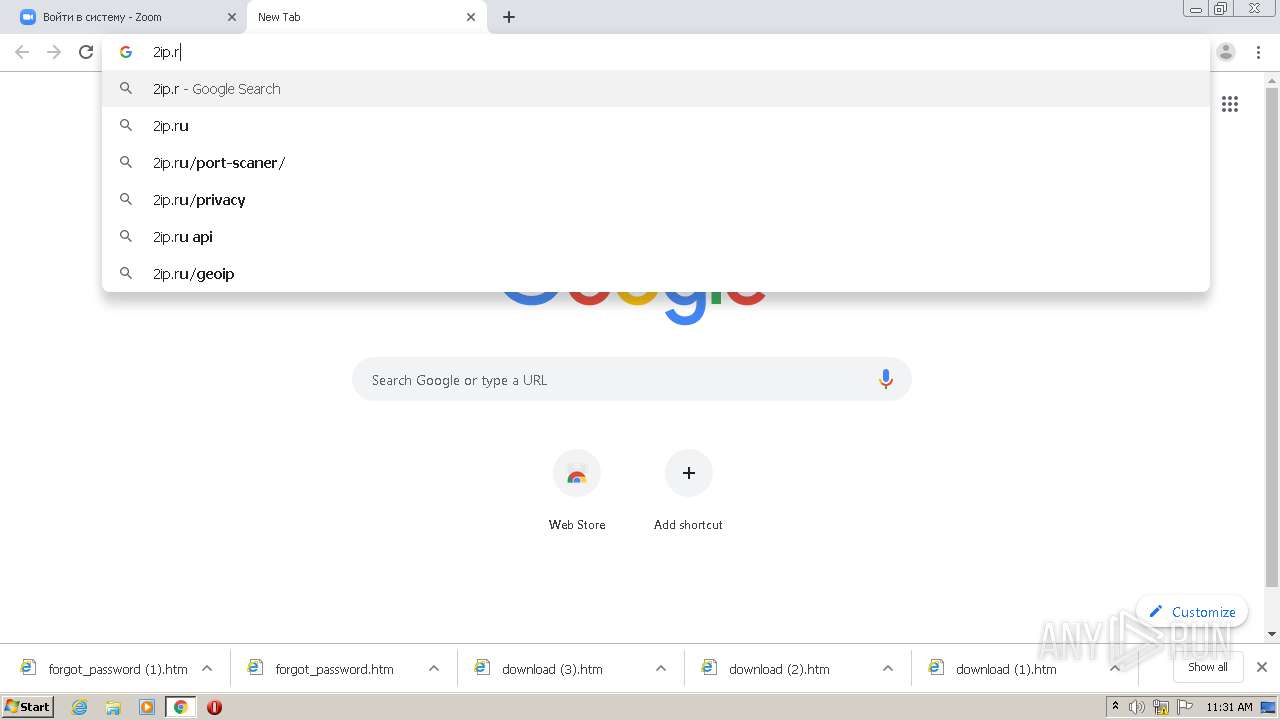
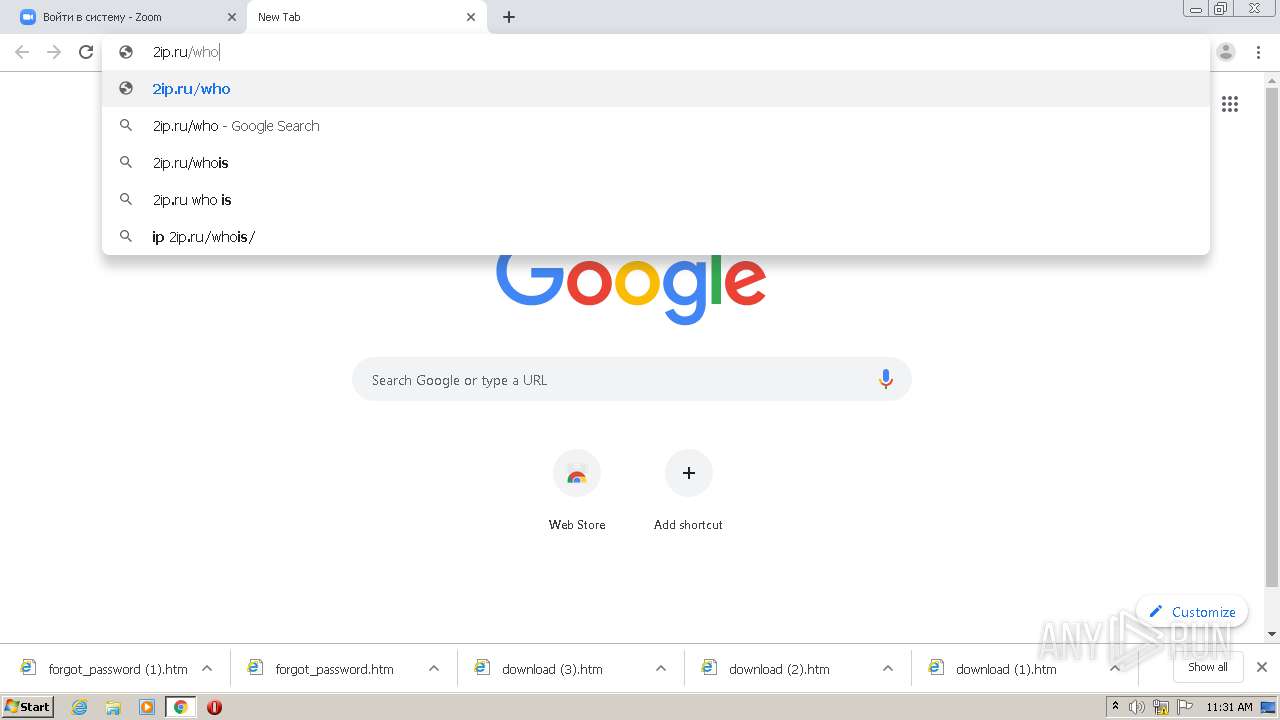
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1451198852802267396 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6722228794440740213 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=68328118568157229 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2000929790833541195 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12571867176149389452 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15523897188760633764 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6651835212875297614 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=959195516882592536 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14293826626719427061 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,8509335175868708310,11941062736166425287,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12930171309872166494 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 003
Read events
928
Write events
72
Delete events
3
Modification events
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2580-13251123007009375 |
Value: 259 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
114
Text files
136
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3863F-A14.pma | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFfcb26.TMP | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\87bbbc1f-309f-4dd2-8691-647b1e0d07ab.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFfcae8.TMP | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFfccad.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
92
DNS requests
61
Threats
8
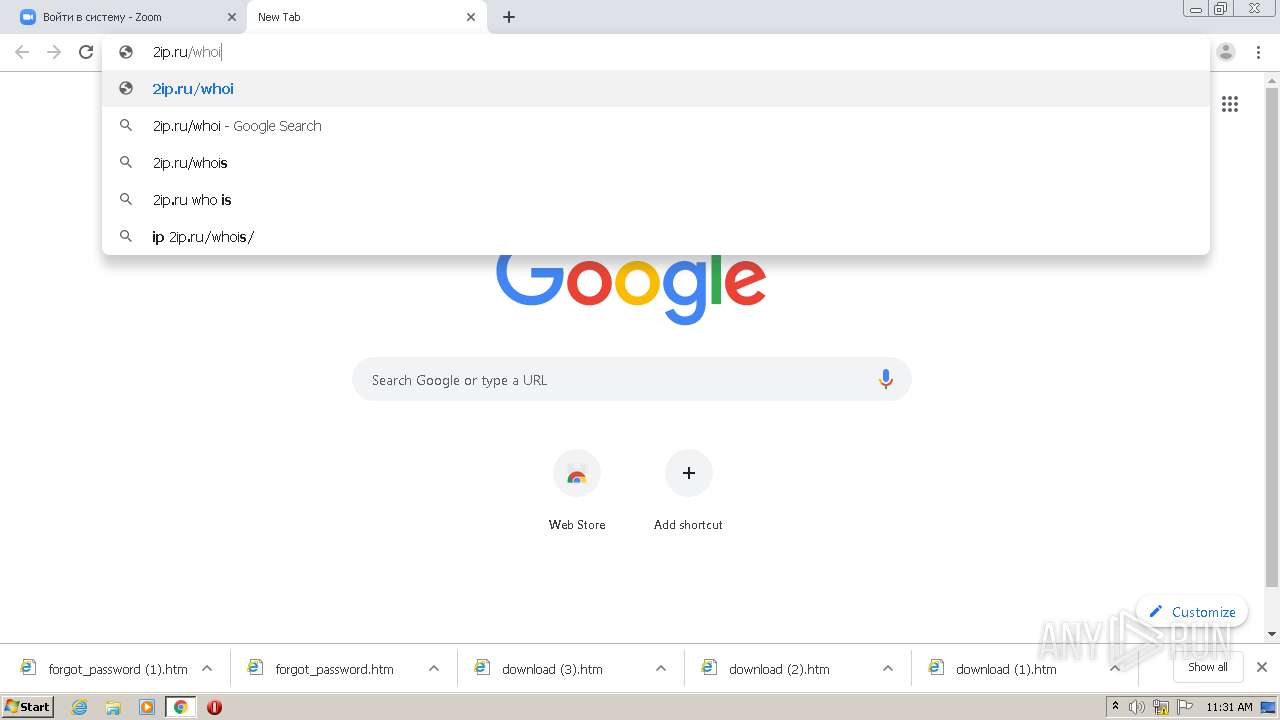
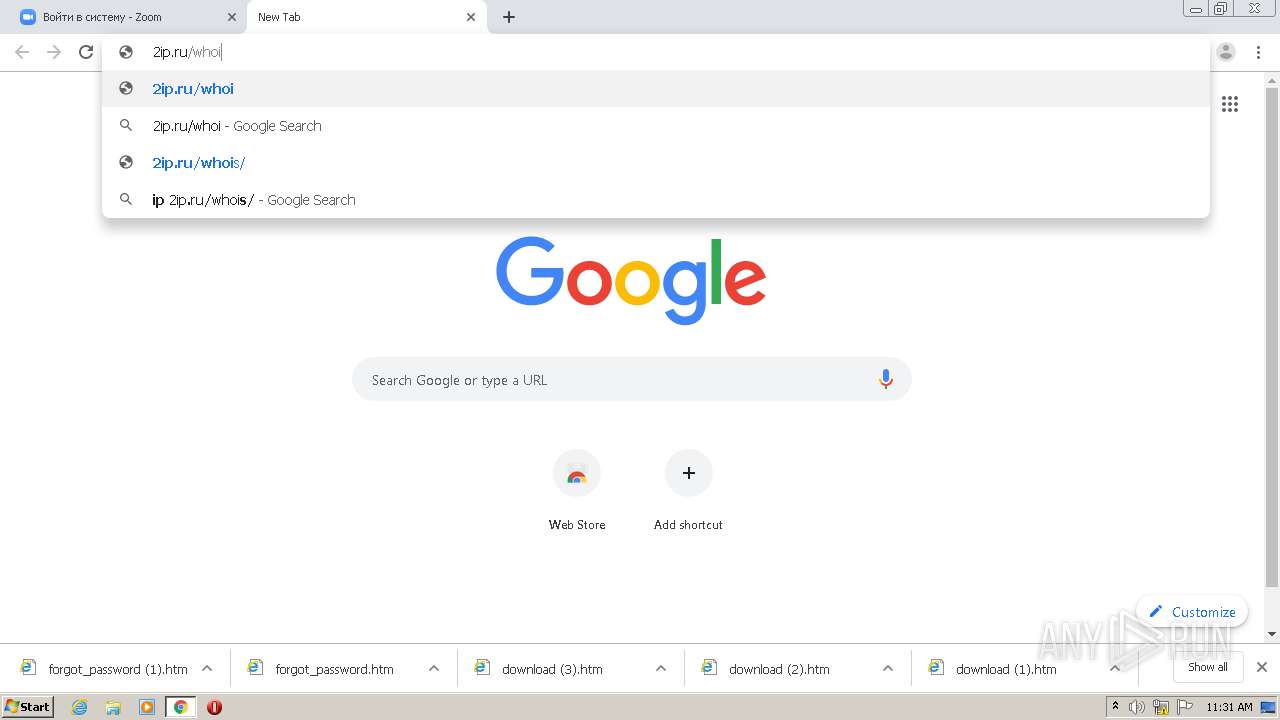
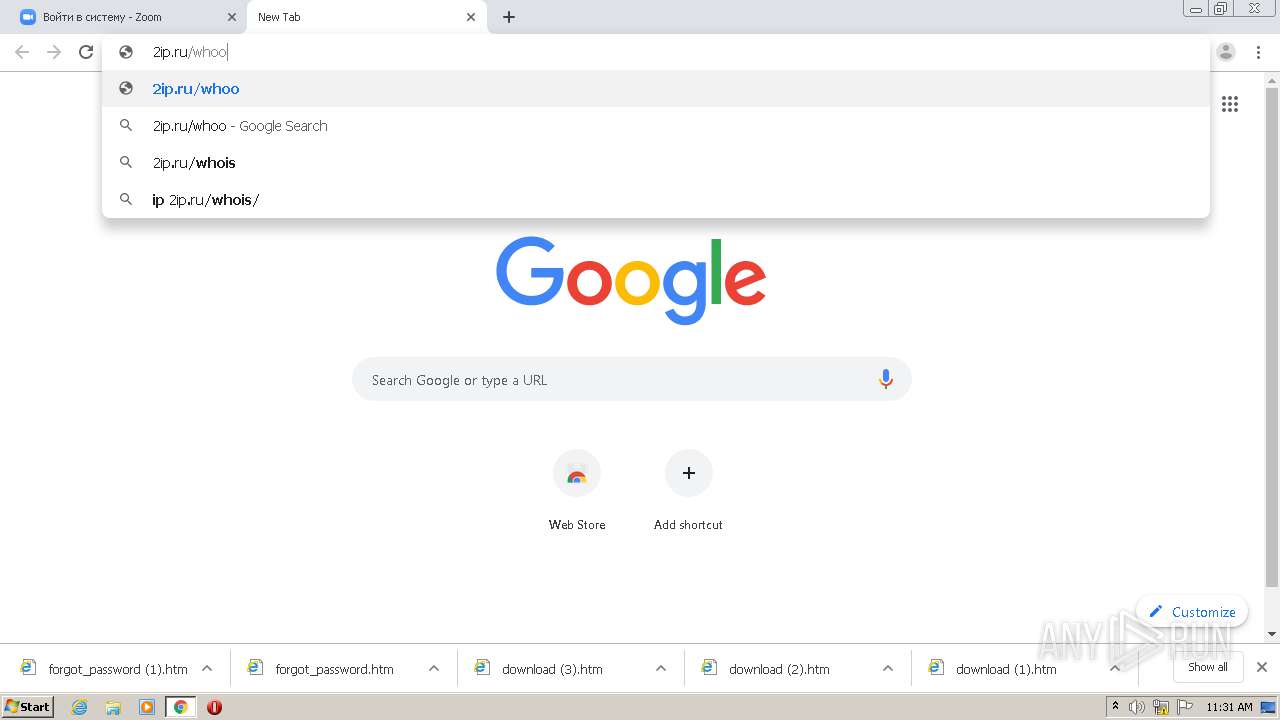
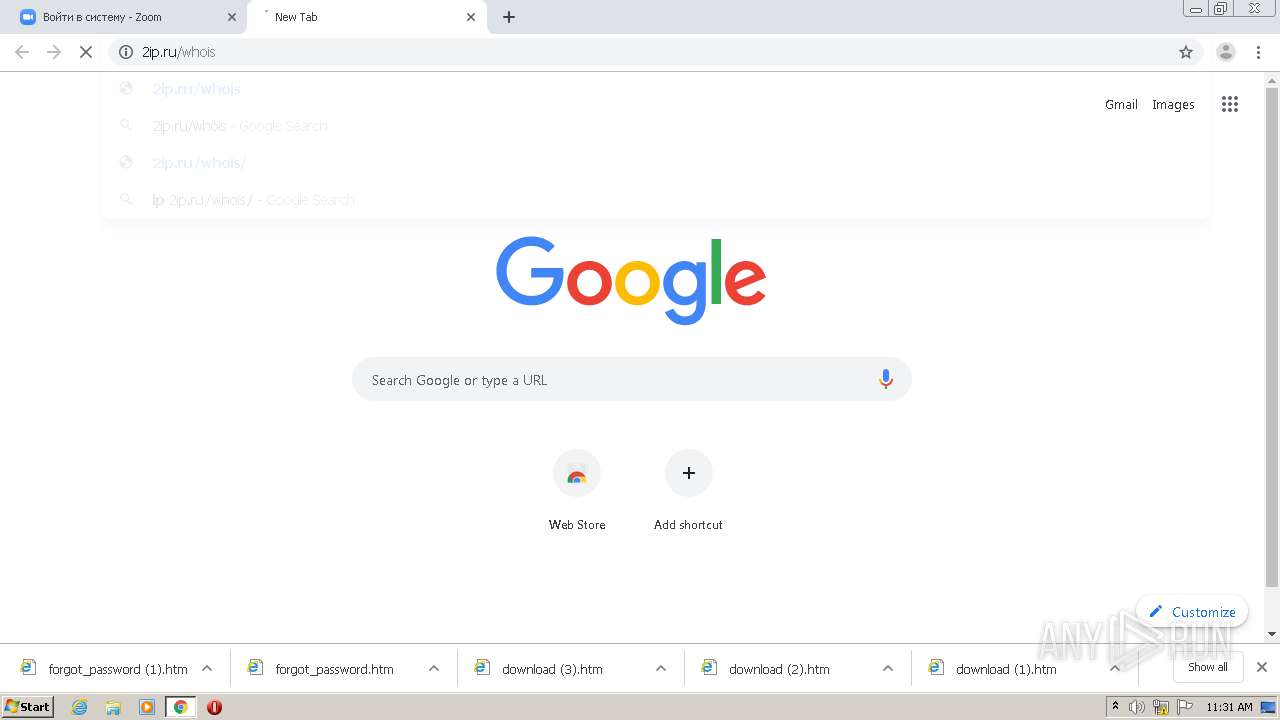
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
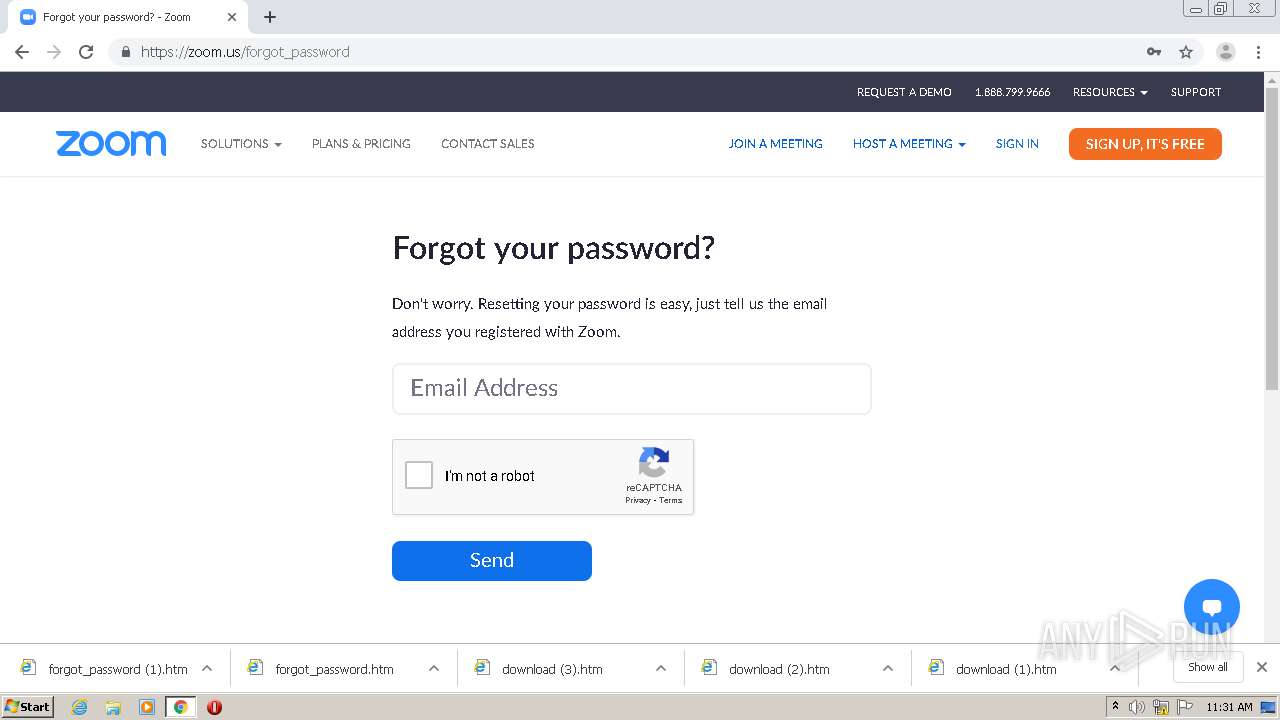
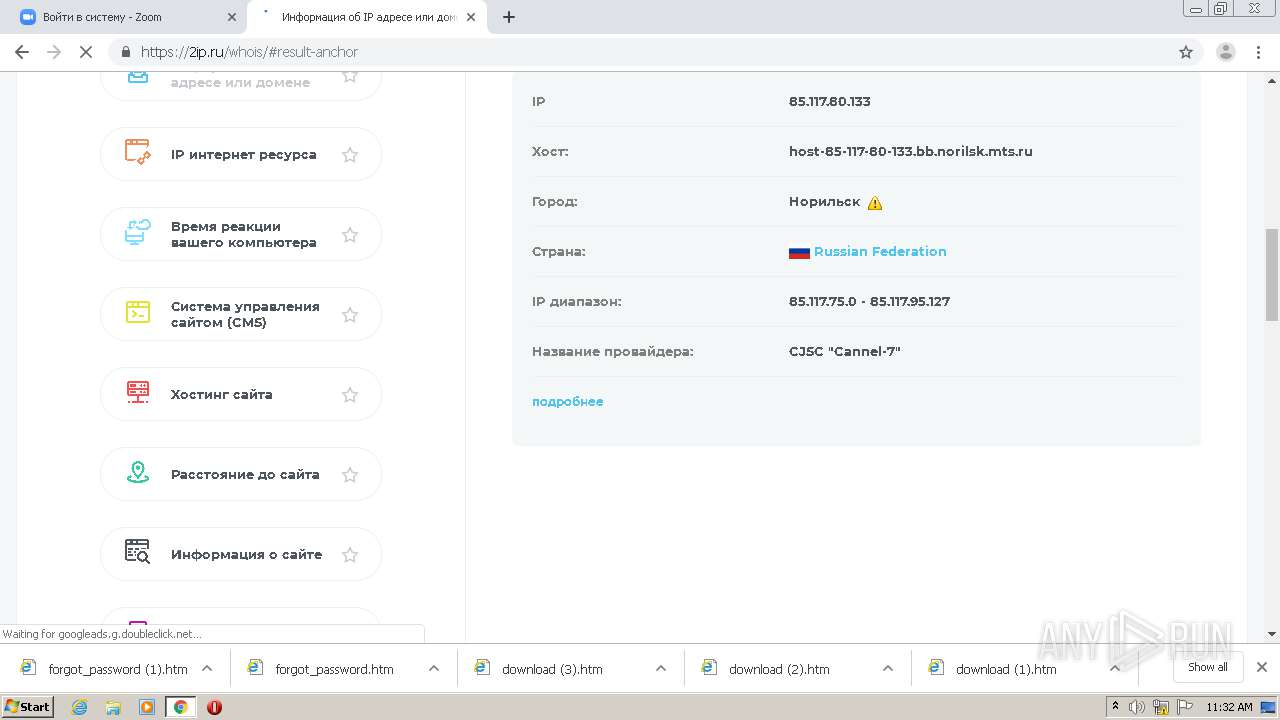
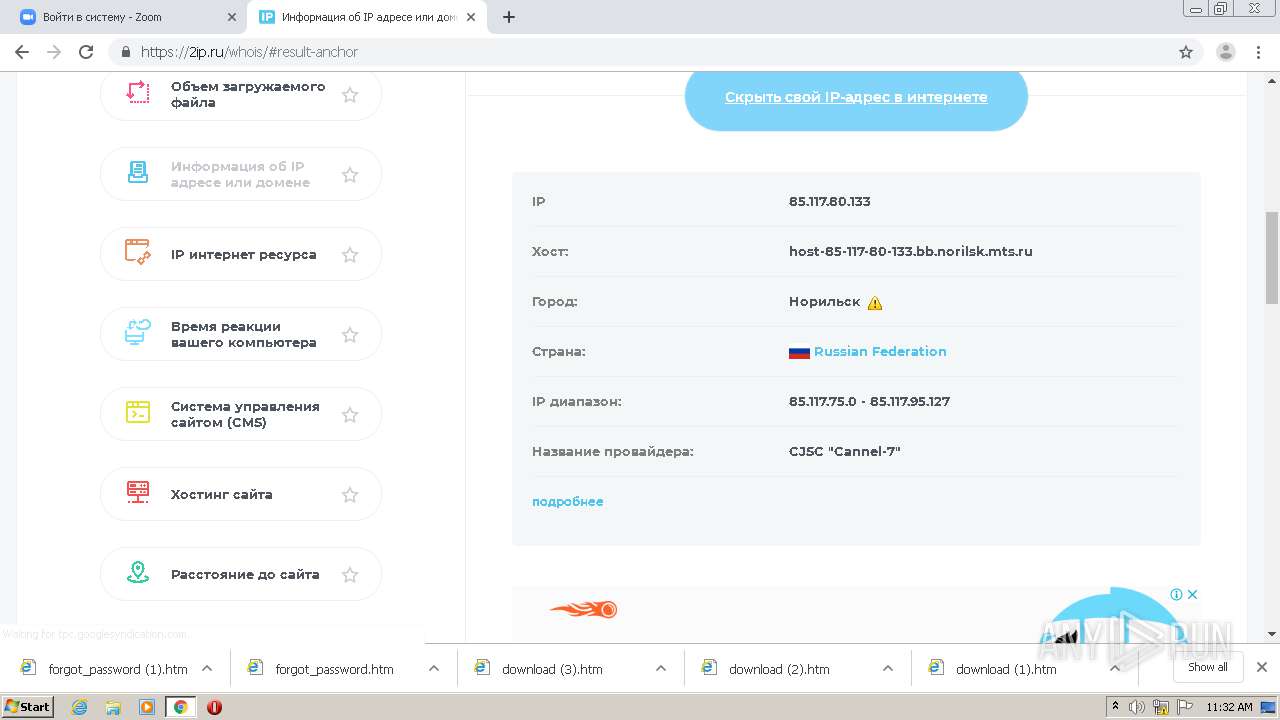
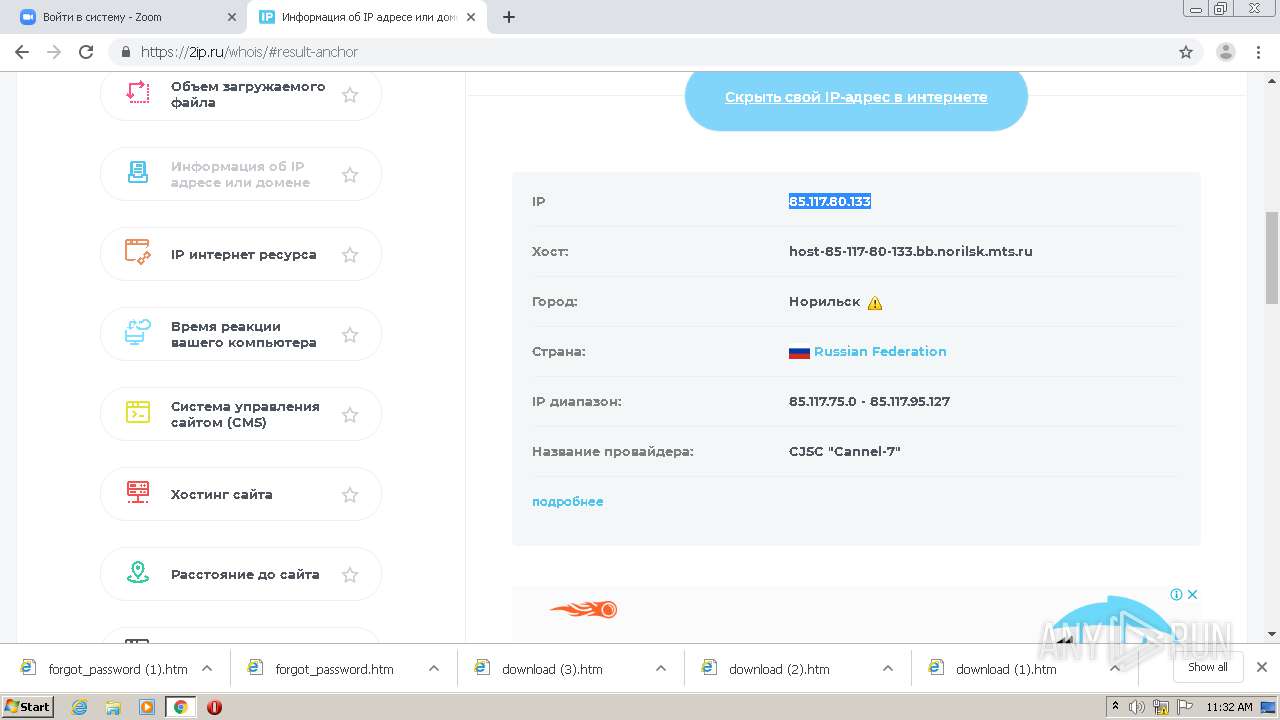
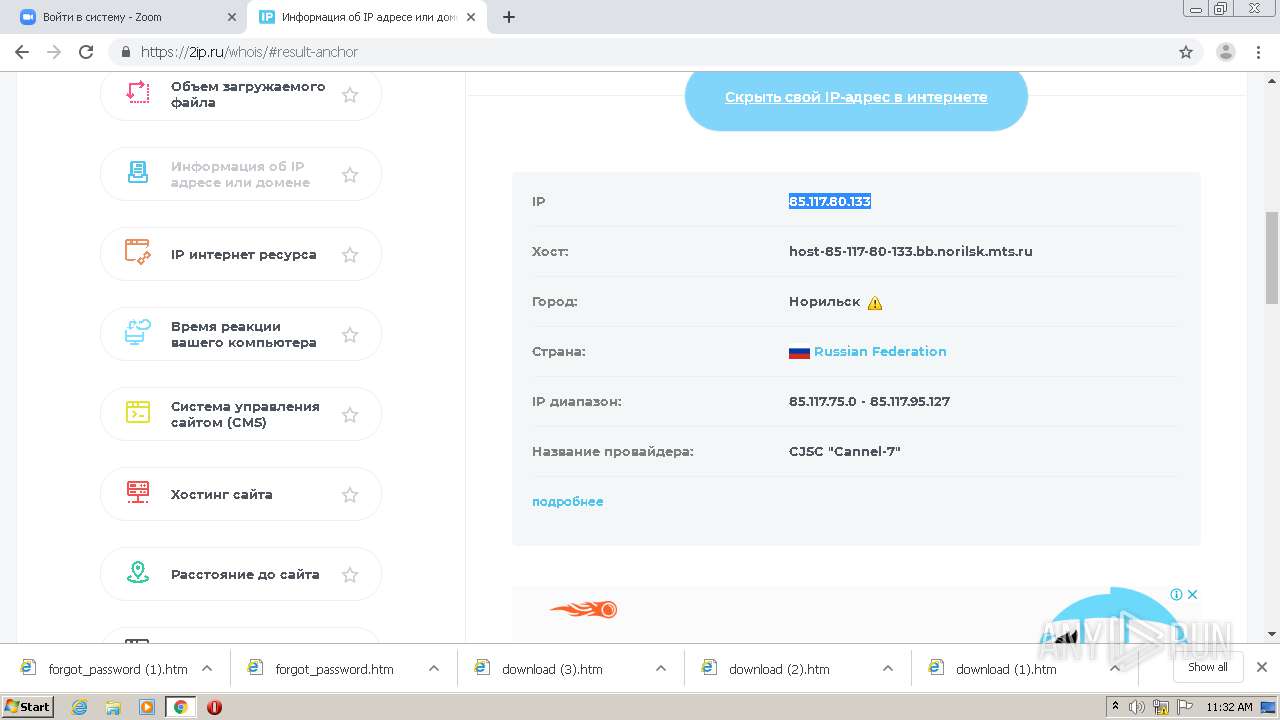
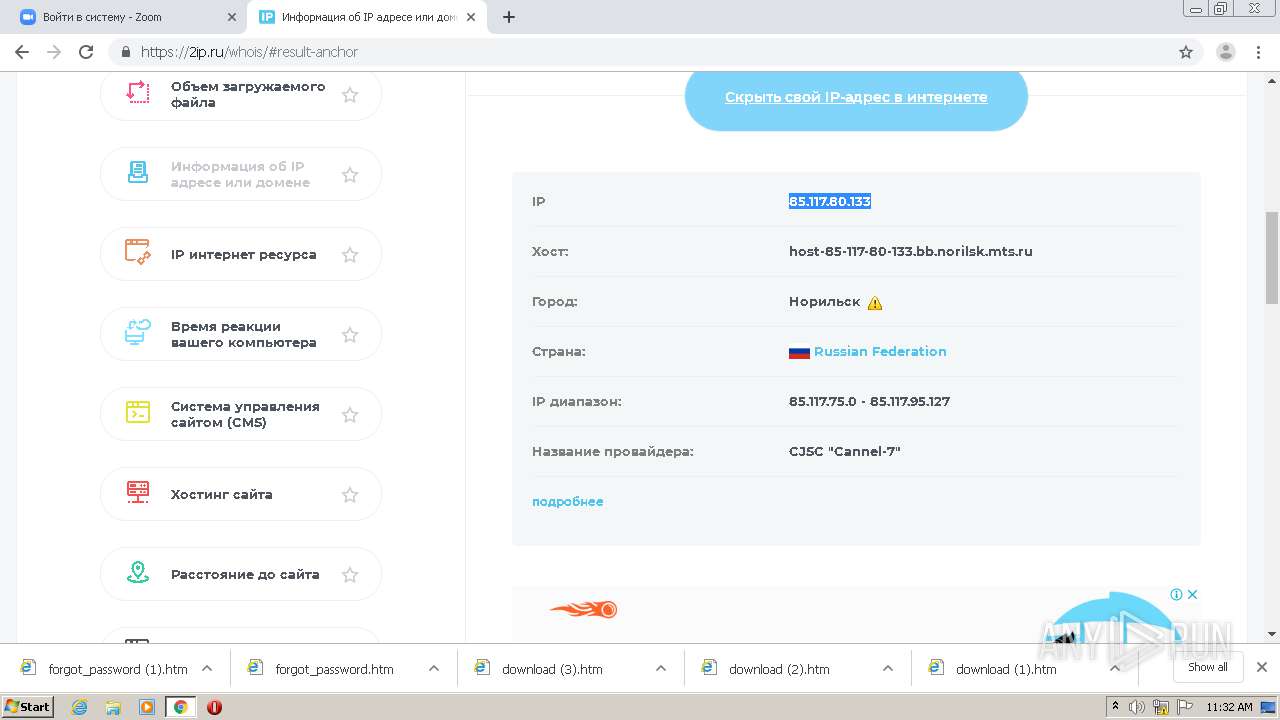
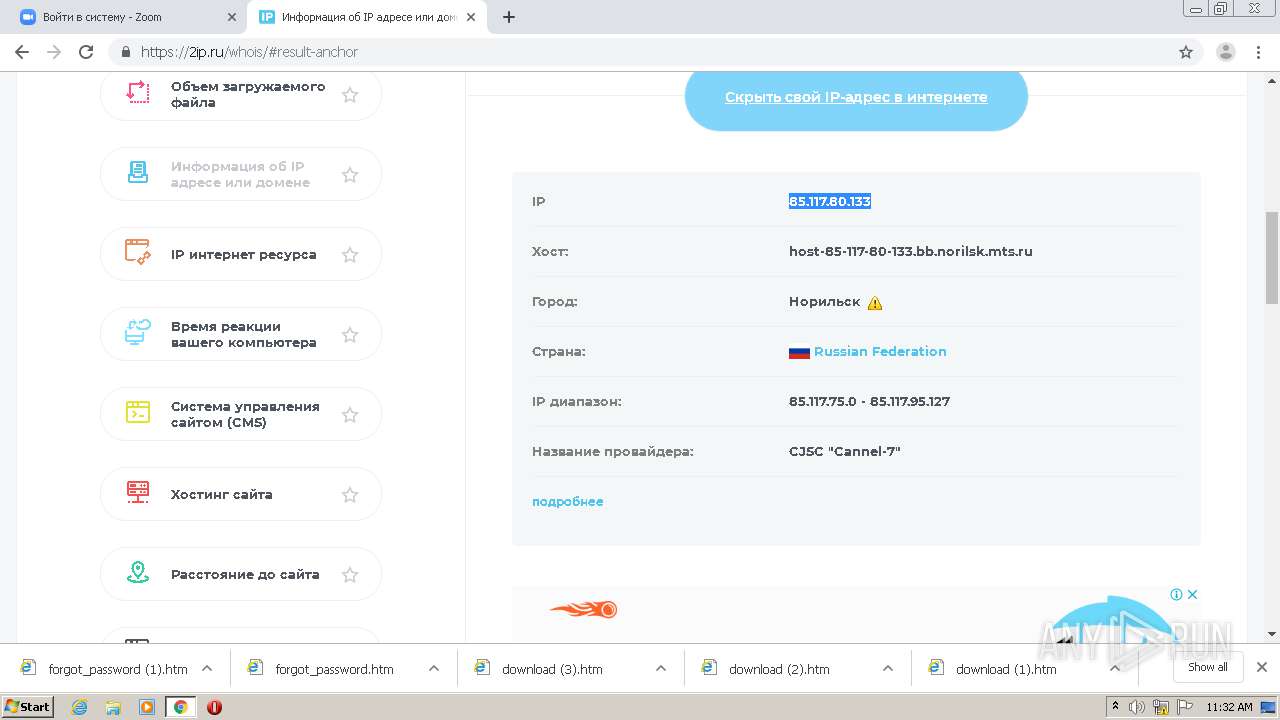
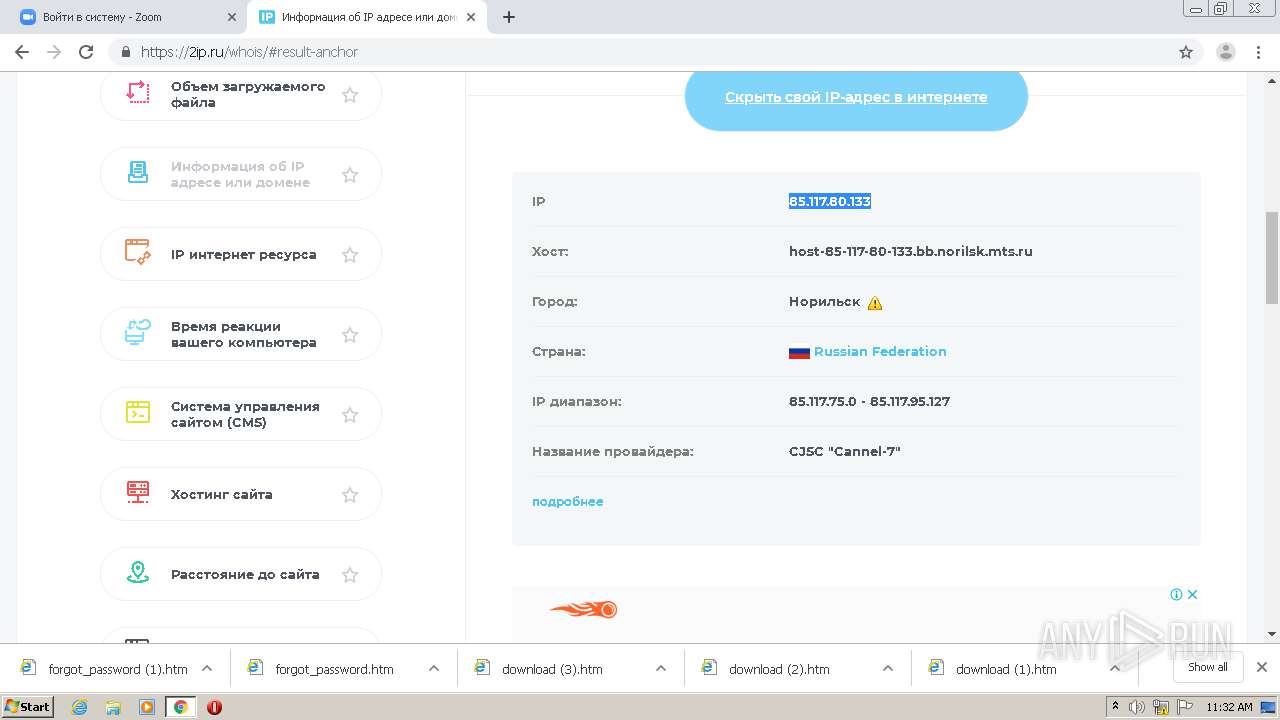
1896 | chrome.exe | GET | 200 | 85.117.80.133:80 | http://s1-zoom.ddns.net/index_files/all.min.css | RU | text | 193 Kb | malicious |
1896 | chrome.exe | GET | 200 | 85.117.80.133:80 | http://s1-zoom.ddns.net/ | RU | html | 65.5 Kb | malicious |
1896 | chrome.exe | GET | 404 | 85.117.80.133:80 | http://s1-zoom.ddns.net/image/new/home/social_icon.png | RU | xml | 1.22 Kb | malicious |
1896 | chrome.exe | GET | 200 | 85.117.80.133:80 | http://s1-zoom.ddns.net/index_files/signin.min.css | RU | text | 10.7 Kb | malicious |
1896 | chrome.exe | GET | 404 | 85.117.80.133:80 | http://s1-zoom.ddns.net/fonts/lato/Lato-Semibold.woff2 | RU | xml | 1.22 Kb | malicious |
1896 | chrome.exe | GET | 200 | 85.117.80.133:80 | http://s1-zoom.ddns.net/ | RU | html | 65.5 Kb | malicious |
1896 | chrome.exe | GET | 404 | 85.117.80.133:80 | http://s1-zoom.ddns.net/fonts/lato/Lato-Regular.woff | RU | xml | 1.22 Kb | malicious |
1896 | chrome.exe | GET | 200 | 85.117.80.133:80 | http://s1-zoom.ddns.net/index_files/saved_resource.html | RU | html | 705 b | malicious |
1896 | chrome.exe | POST | 200 | 85.117.80.133:80 | http://s1-zoom.ddns.net/log.php | RU | html | 137 b | malicious |
1896 | chrome.exe | GET | — | 85.117.80.133:80 | http://s1-zoom.ddns.net/favicon.ico | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1896 | chrome.exe | 85.117.80.133:80 | s1-zoom.ddns.net | MTS PJSC | RU | malicious |
1896 | chrome.exe | 13.35.253.153:443 | d24cgw3uvb9a9h.cloudfront.net | — | US | unknown |
— | — | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 142.250.80.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 172.217.6.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
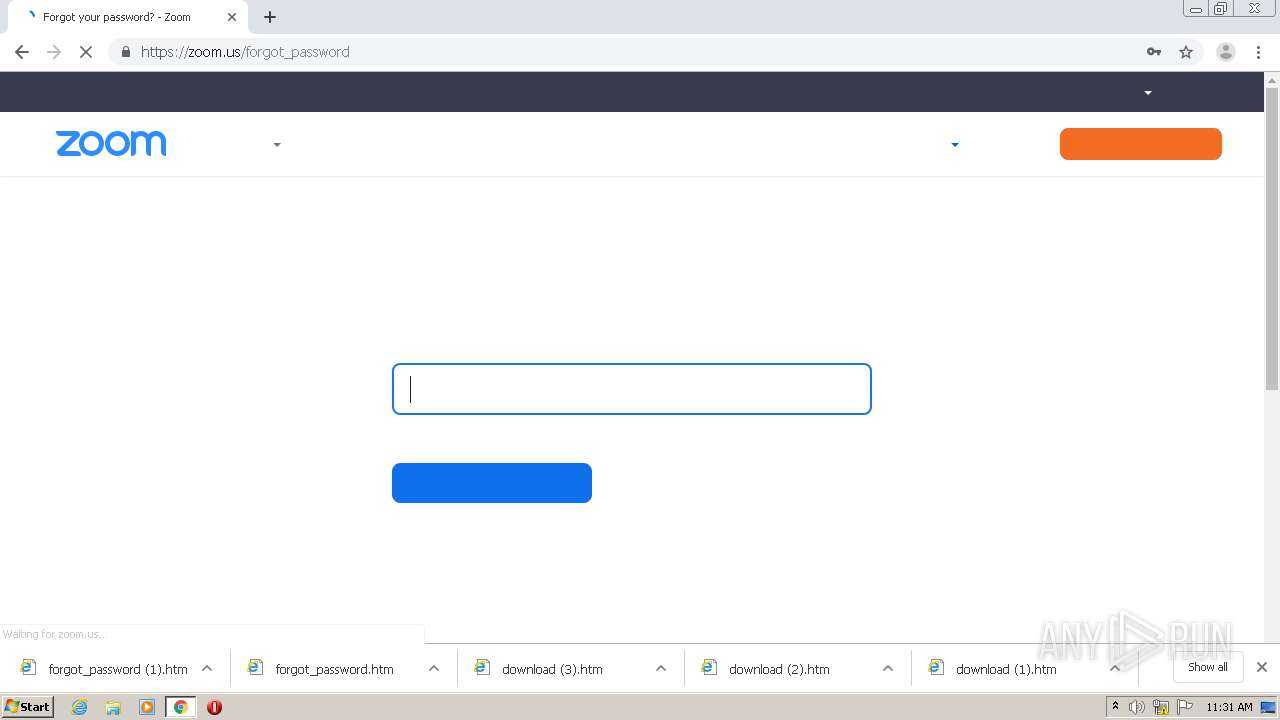
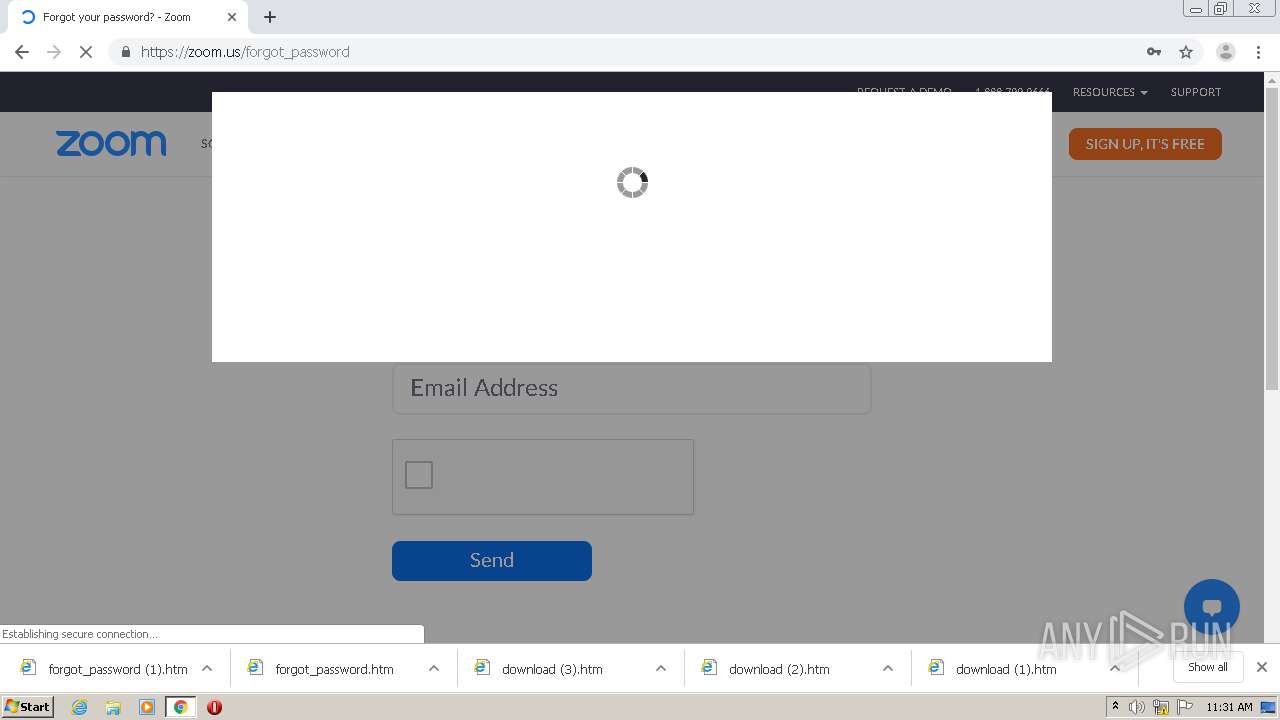
1896 | chrome.exe | 52.202.62.206:443 | zoom.us | Amazon.com, Inc. | US | suspicious |
1896 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 34.198.105.228:443 | prefmgr-cookie.truste-svc.net | Amazon.com, Inc. | US | unknown |
1896 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1896 | chrome.exe | 143.204.90.28:443 | consent-pref.trustarc.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s1-zoom.ddns.net |
| malicious |
accounts.google.com |
| shared |
d24cgw3uvb9a9h.cloudfront.net |
| shared |
clients1.google.com |
| whitelisted |
blog.zoom.us |
| whitelisted |
investors.zoom.us |
| suspicious |
marketplace.zoom.us |
| whitelisted |
support.zoom.us |
| whitelisted |
www.facebook.com |
| whitelisted |
www.linkedin.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
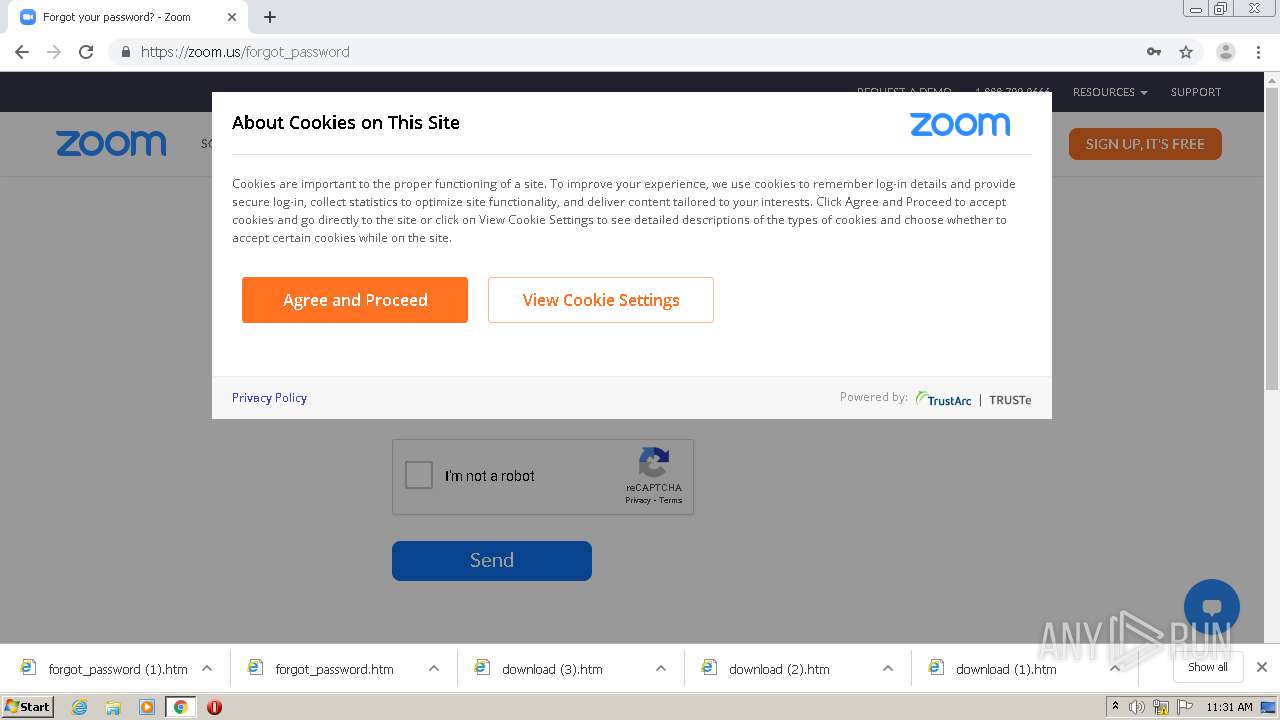
1896 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
1896 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
1056 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1896 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
3 ETPRO signatures available at the full report