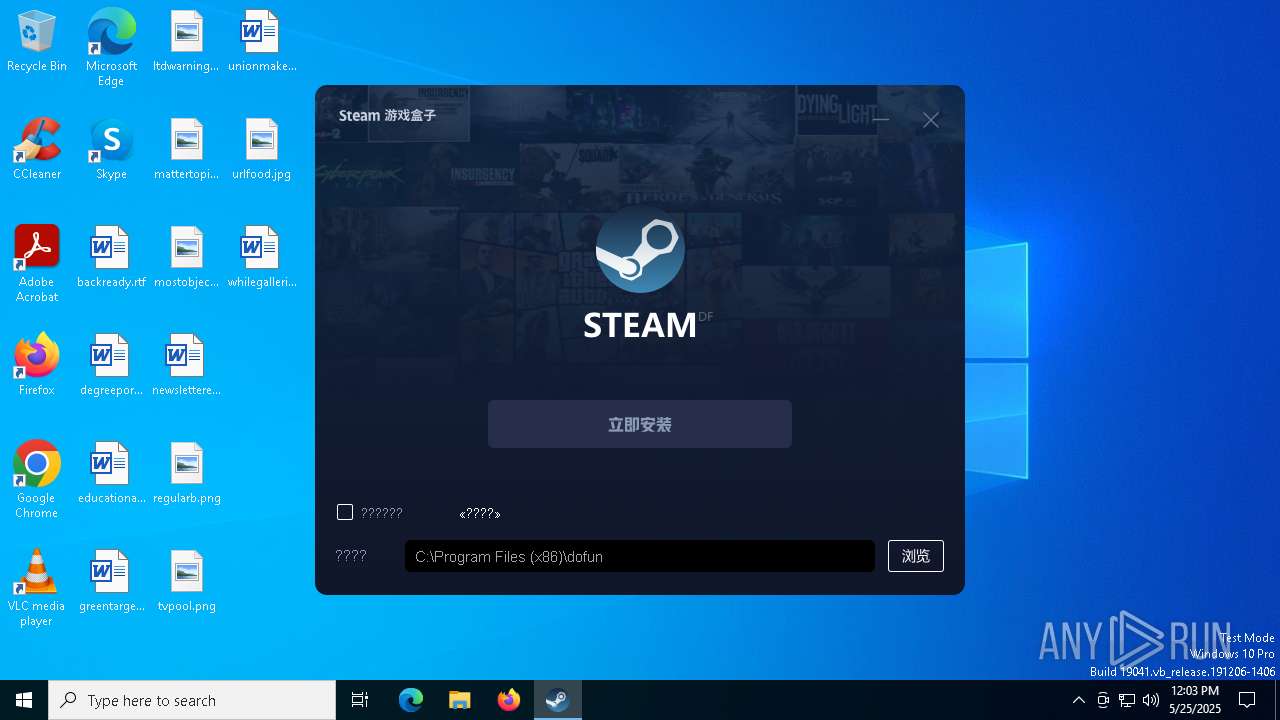
| download: | /package/dfbox_yx03_24.06.26.exe |
| Full analysis: | https://app.any.run/tasks/0c1a47a0-f324-4a3e-a29c-6df538bbef03 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 12:03:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 5D44913A4E27B440D4CD867713D2CBF6 |
| SHA1: | 80BDD11F20F304B2017F65D486911DFC6CCB963C |
| SHA256: | AEA6391AD35D83D7871B82EA10D59CC470CD79DC44143D7D8172C183C4BD22E0 |
| SSDEEP: | 98304:pD19DlBMq71K4KrWNhQlWo6OU+IZUxYNF2lqd00CNDRwQXmtOI41xnv+rapDFAN7:C02CEs |
MALICIOUS
Changes Windows Defender settings
- dfbox_yx03_24.06.26.exe (PID: 4844)
Adds path to the Windows Defender exclusion list
- dfbox_yx03_24.06.26.exe (PID: 4844)
SUSPICIOUS
Mutex name with non-standard characters
- dfbox_yx03_24.06.26.exe (PID: 4844)
The process hide an interactive prompt from the user
- dfbox_yx03_24.06.26.exe (PID: 4844)
Starts POWERSHELL.EXE for commands execution
- dfbox_yx03_24.06.26.exe (PID: 4844)
Script adds exclusion path to Windows Defender
- dfbox_yx03_24.06.26.exe (PID: 4844)
Executable content was dropped or overwritten
- dfbox_yx03_24.06.26.exe (PID: 4844)
Process drops legitimate windows executable
- dfbox_yx03_24.06.26.exe (PID: 4844)
The process drops C-runtime libraries
- dfbox_yx03_24.06.26.exe (PID: 4844)
INFO
Creates files in the program directory
- dfbox_yx03_24.06.26.exe (PID: 4844)
Checks supported languages
- dfbox_yx03_24.06.26.exe (PID: 4844)
Create files in a temporary directory
- dfbox_yx03_24.06.26.exe (PID: 4844)
Reads the computer name
- dfbox_yx03_24.06.26.exe (PID: 4844)
The sample compiled with chinese language support
- dfbox_yx03_24.06.26.exe (PID: 4844)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6392)
The sample compiled with english language support
- dfbox_yx03_24.06.26.exe (PID: 4844)
Reads the software policy settings
- slui.exe (PID: 4284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:27 09:11:45+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.28 |
| CodeSize: | 3772416 |
| InitializedDataSize: | 1099776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x342aa0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
136
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 536 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | ||||
| 4180 | "C:\Users\admin\AppData\Local\Temp\dfbox_yx03_24.06.26.exe" | C:\Users\admin\AppData\Local\Temp\dfbox_yx03_24.06.26.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | ||||
| 4212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 4284 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 4844 | "C:\Users\admin\AppData\Local\Temp\dfbox_yx03_24.06.26.exe" | C:\Users\admin\AppData\Local\Temp\dfbox_yx03_24.06.26.exe | explorer.exe | |
User: admin Integrity Level: HIGH | ||||
| 6392 | powershell -inputformat none -outputformat none -NonInteractive -Command "Add-MpPreference -ExclusionPath 'C:\Program Files (x86)\dofun\yx03'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | dfbox_yx03_24.06.26.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 6824 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
107
Suspicious files
94
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4844 | dfbox_yx03_24.06.26.exe | C:\Users\admin\AppData\Local\Temp\df\zstart.dll | — | |
MD5:— | SHA256:— | |||
| 6392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xfknvmdu.g12.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4844 | dfbox_yx03_24.06.26.exe | C:\Users\admin\AppData\Local\Temp\skin.zip | compressed | |
MD5:20DEC096986FAA3E97266D6C5D60E17A | SHA256:2B7ADCDD03167FBDE58EE2E9C8CF171120B80E1E09D063865184BCF2625813F0 | |||
| 4844 | dfbox_yx03_24.06.26.exe | C:\Users\admin\AppData\Local\Temp\df\zlibwapi.dll.tmp | executable | |
MD5:99DDBAE512435B8DE08B2461FEB5BBEA | SHA256:0DC334E37C8DB0BEE2382AAEAF43C1210D576EDF2AA6B1E534DF5253D8E317A2 | |||
| 4844 | dfbox_yx03_24.06.26.exe | C:\Users\admin\AppData\Local\Temp\df\steamlauncher.exe | executable | |
MD5:B1ADAF244333AC4B0E942F542D04425A | SHA256:61FD3C5AC38430DF80827606C2382139B54784F7DDA1796166D12D27021AE669 | |||
| 4844 | dfbox_yx03_24.06.26.exe | C:\Users\admin\AppData\Local\Temp\df\temp\zstart.dll.tmp | executable | |
MD5:8FA2A1D77FB24232CA397A32954D9CAD | SHA256:04AA94E5F725776C641EAEF8F4794AA48BD10354CA156D7E4EE856F84F8B83D9 | |||
| 6392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ge5v3eh3.s1k.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4844 | dfbox_yx03_24.06.26.exe | C:\Users\admin\AppData\Local\Temp\df\zstart.dll.tmp | executable | |
MD5:8FA2A1D77FB24232CA397A32954D9CAD | SHA256:04AA94E5F725776C641EAEF8F4794AA48BD10354CA156D7E4EE856F84F8B83D9 | |||
| 6392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4nham11j.m51.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6392 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xkv44pdl.oa3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
4212 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
4844 | dfbox_yx03_24.06.26.exe | POST | 200 | 39.105.192.231:80 | http://client.88gog.com/api/user/public/client/channel/resource | CN | binary | 378 b | unknown |
4212 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5796 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1328 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4844 | dfbox_yx03_24.06.26.exe | 118.178.60.245:443 | download.88gog.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4844 | dfbox_yx03_24.06.26.exe | 39.105.192.231:80 | client.88gog.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
4844 | dfbox_yx03_24.06.26.exe | 39.105.138.72:443 | www.zuhaowan.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
download.88gog.com |
| unknown |
client.88gog.com |
| unknown |
dfbox-88gog-oss-client.oss-cn-hangzhou.aliyuncs.com |
| unknown |
www.zuhaowan.com |
| unknown |
download-pkg.didikaihei.cn |
| unknown |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
4844 | dfbox_yx03_24.06.26.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |