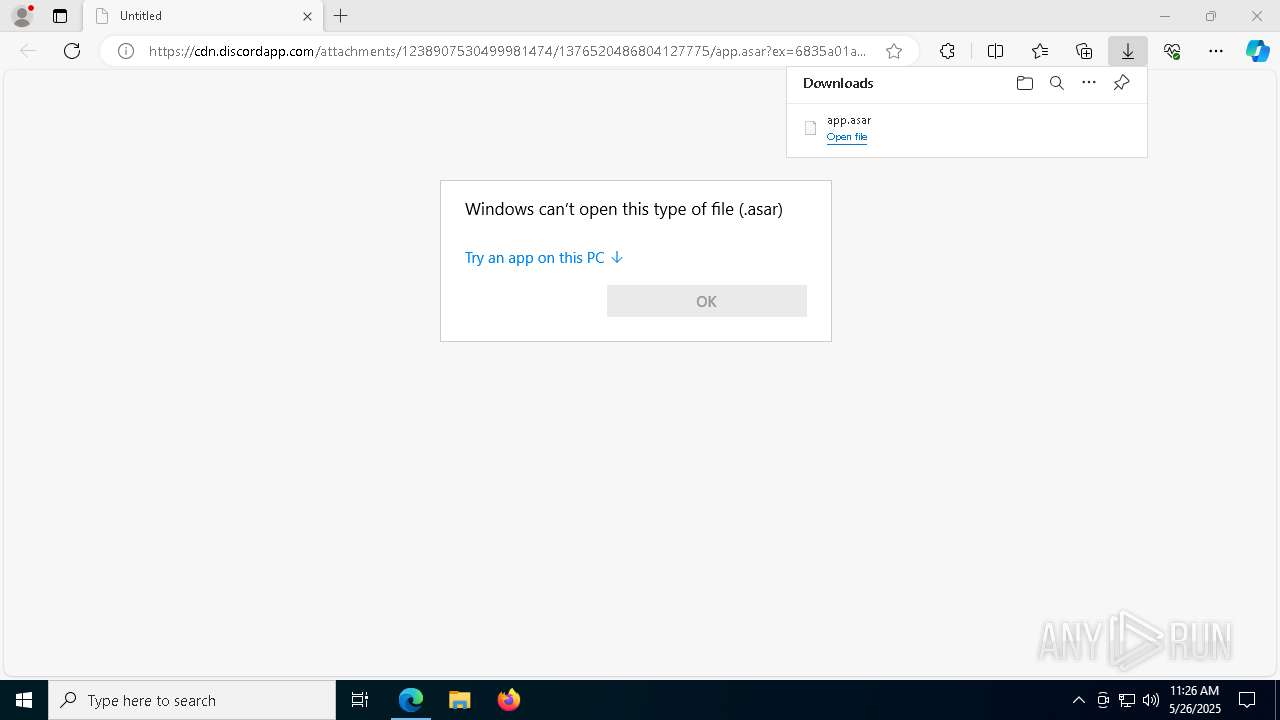
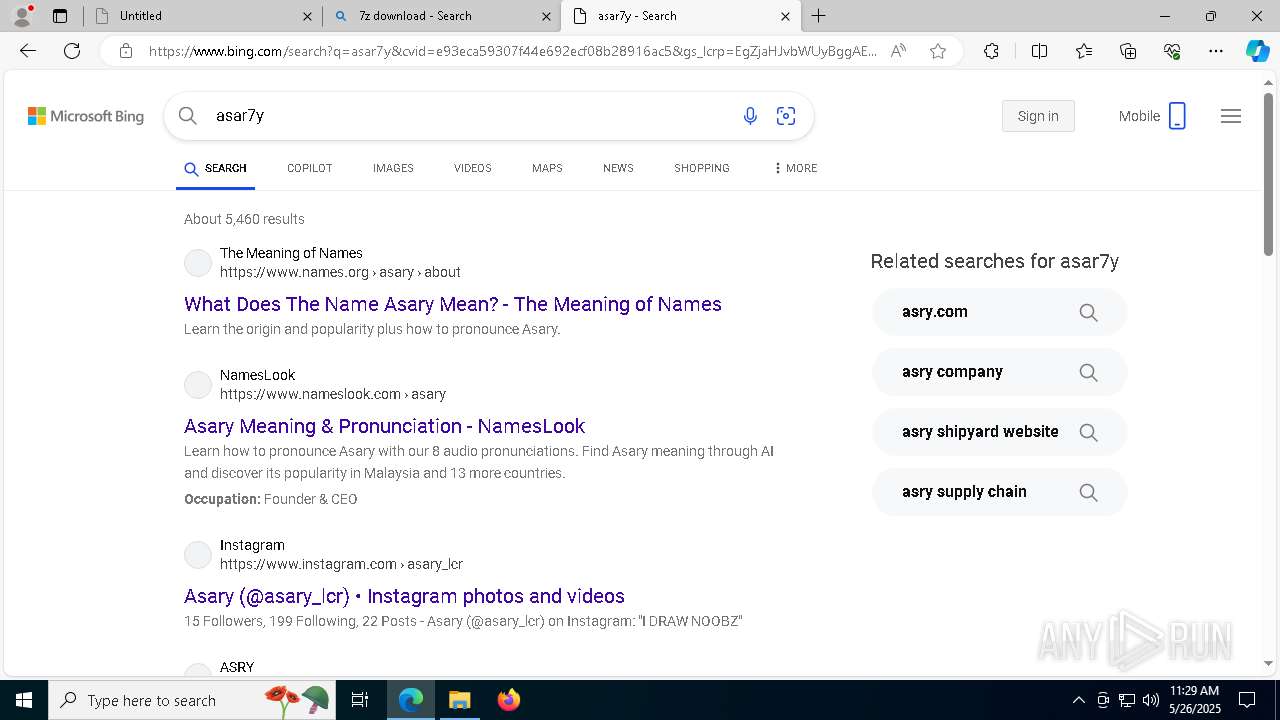
| URL: | https://cdn.discordapp.com/attachments/1238907530499981474/1376520486804127775/app.asar?ex=6835a01a&is=68344e9a&hm=0b4ff8f67f4ac814f692e8f3a86f36bbcdcaec5b5346e4ab1586c0759fcb85a4& |
| Full analysis: | https://app.any.run/tasks/234d04a1-15fd-42a4-9343-fb3f029189b5 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 11:25:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 29A5834804CC366B3D7403E29A54C425 |
| SHA1: | 0E286941D159BDE5EF554EC8D931EF8F965FADF8 |
| SHA256: | AEA3E2D6B4B16CCC784939631876ADBAE7CEA06239059756F763C30BA36244B5 |
| SSDEEP: | 3:N8cCWdy6//OaN6vIiU3UXEQ7Wa4vuhcERLqDiPlT3BdcGwojWR0I7Izn:2cry6XDN6QiXXJfRuDeDHw6zI7Izn |
MALICIOUS
No malicious indicators.SUSPICIOUS
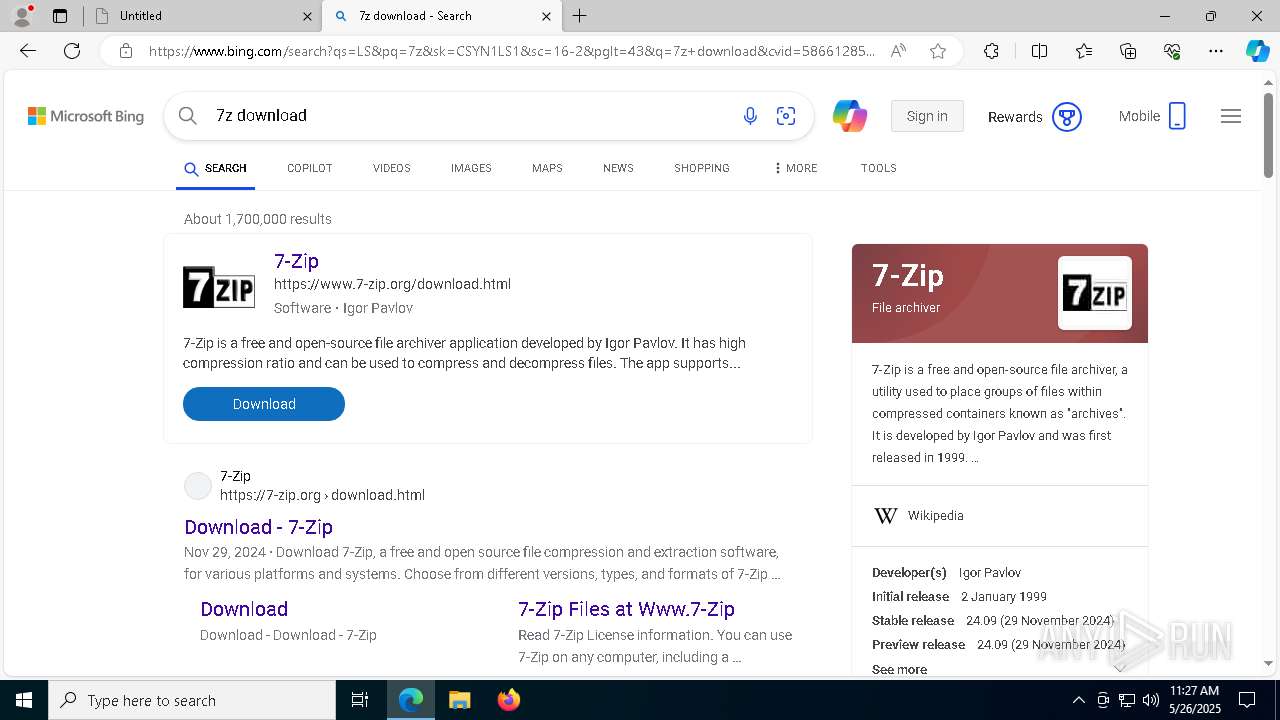
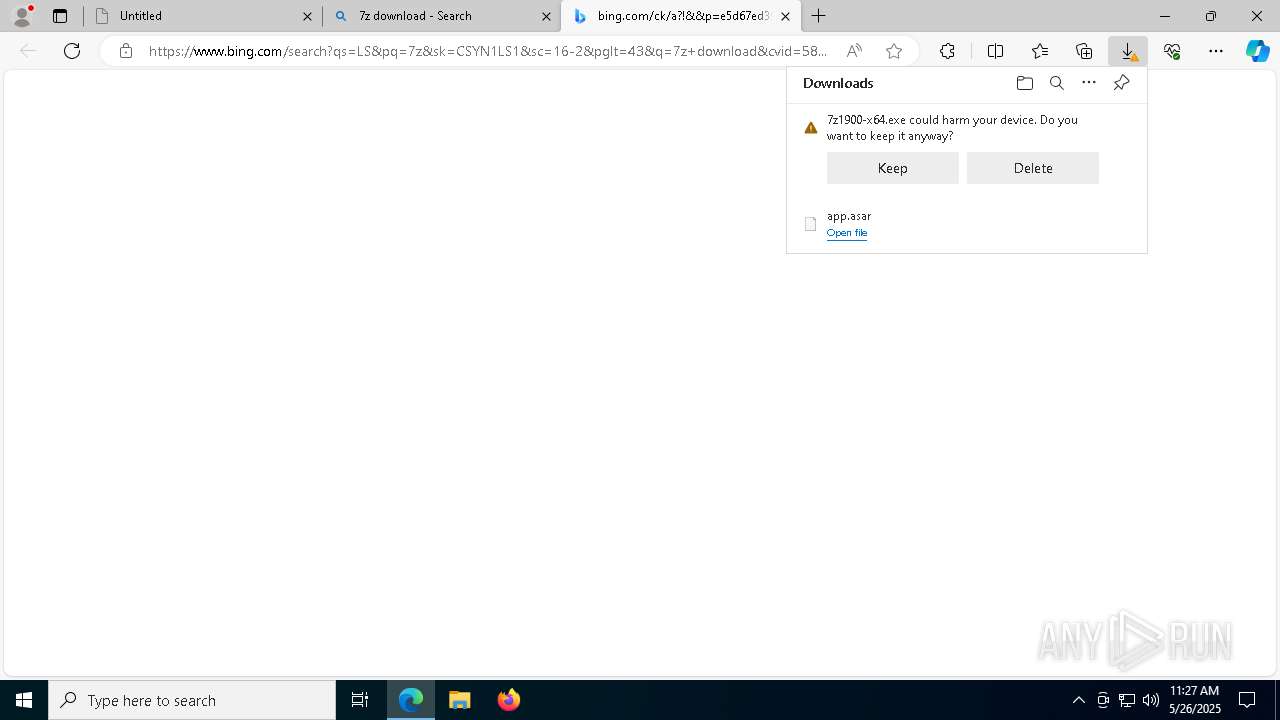
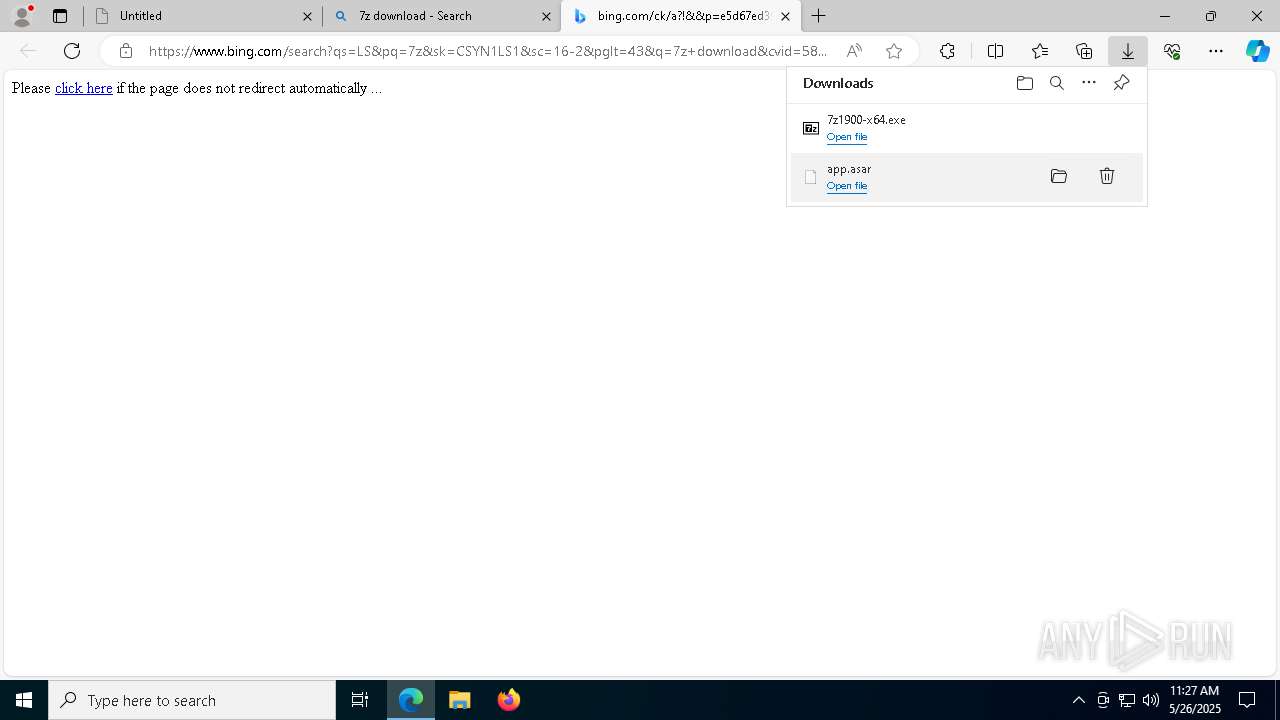
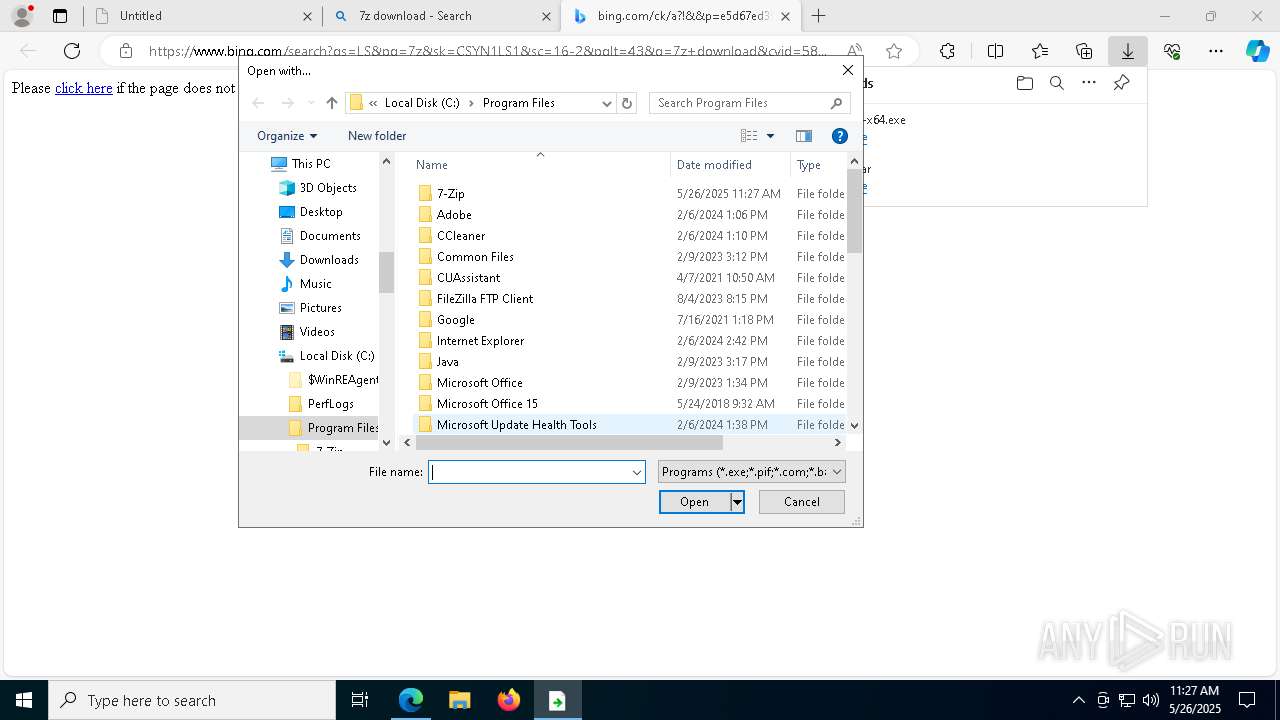
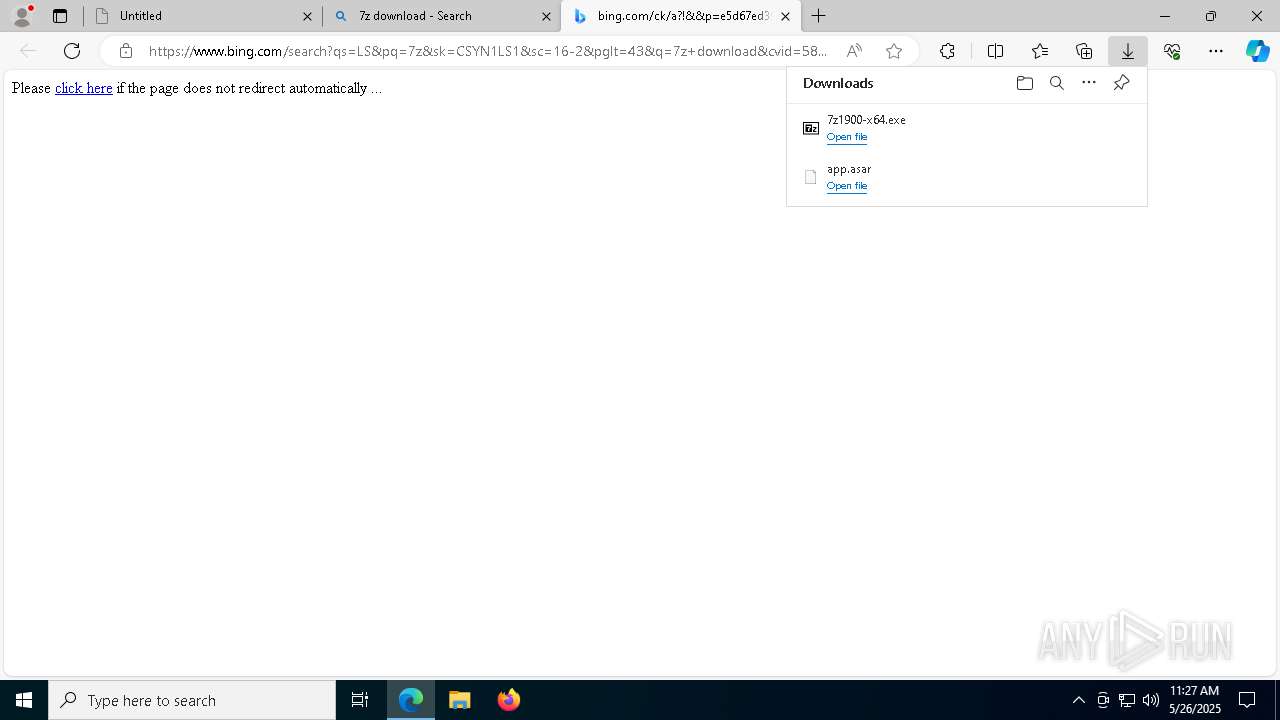
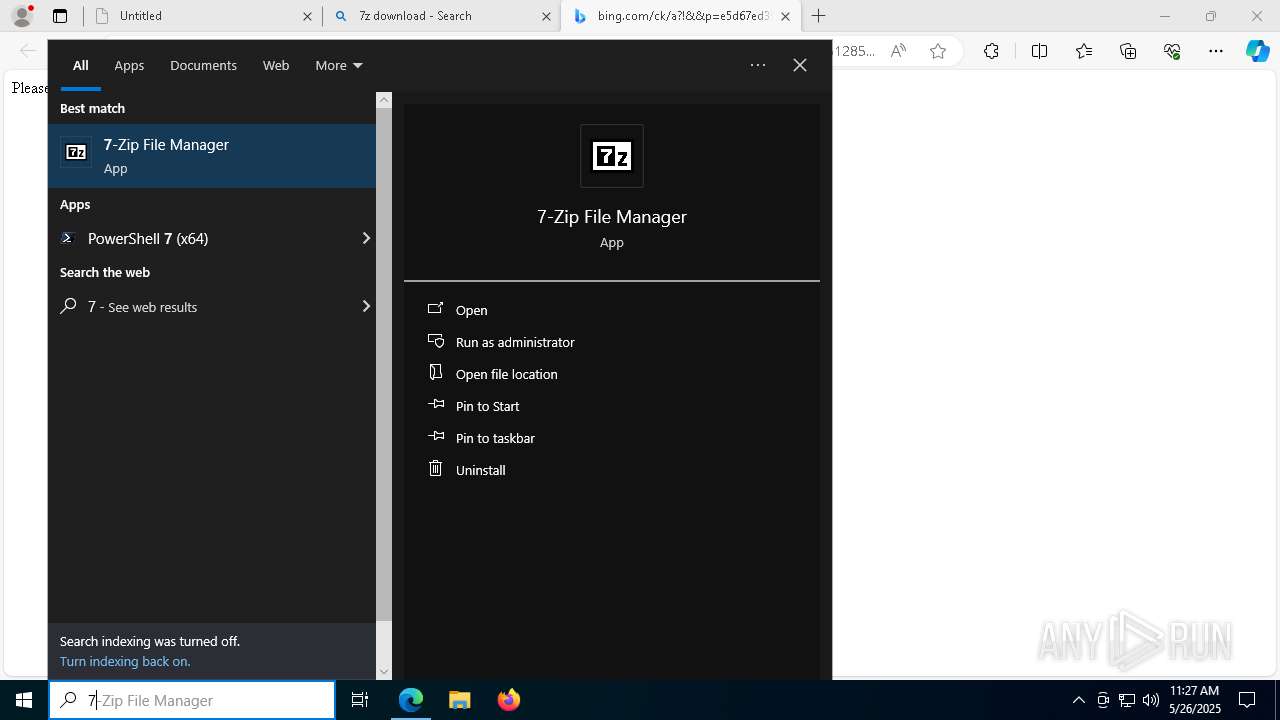
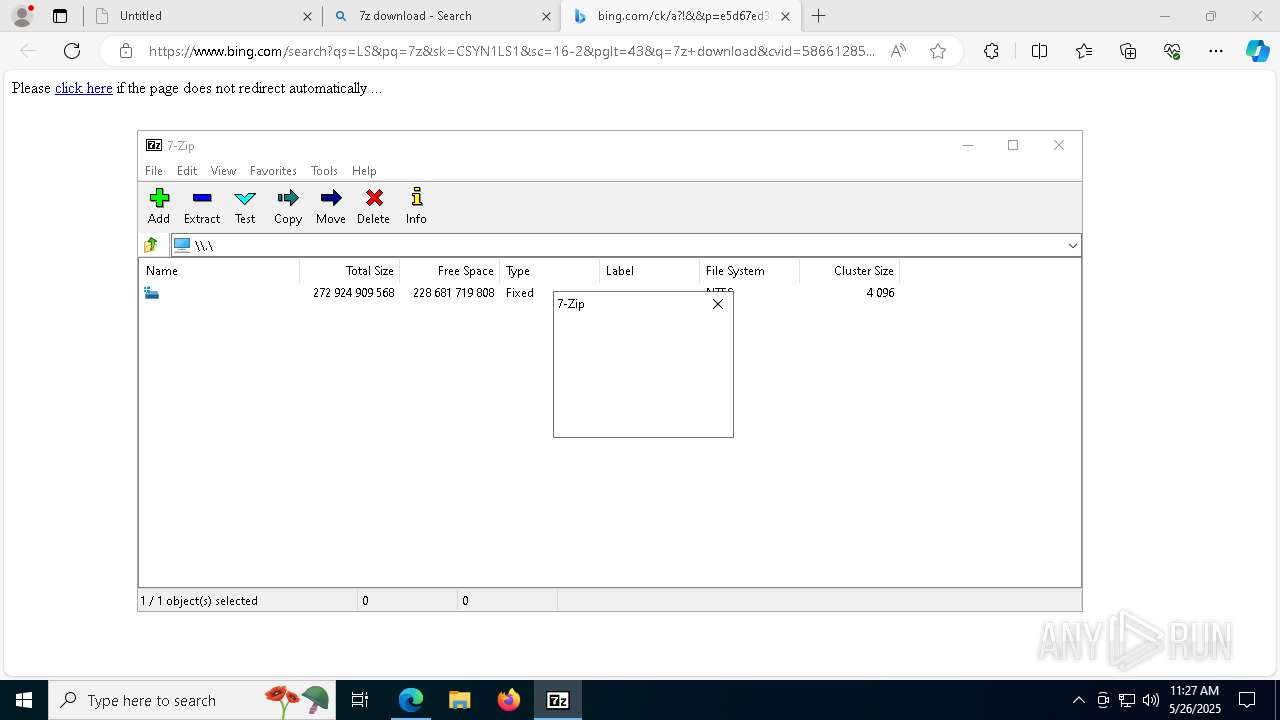
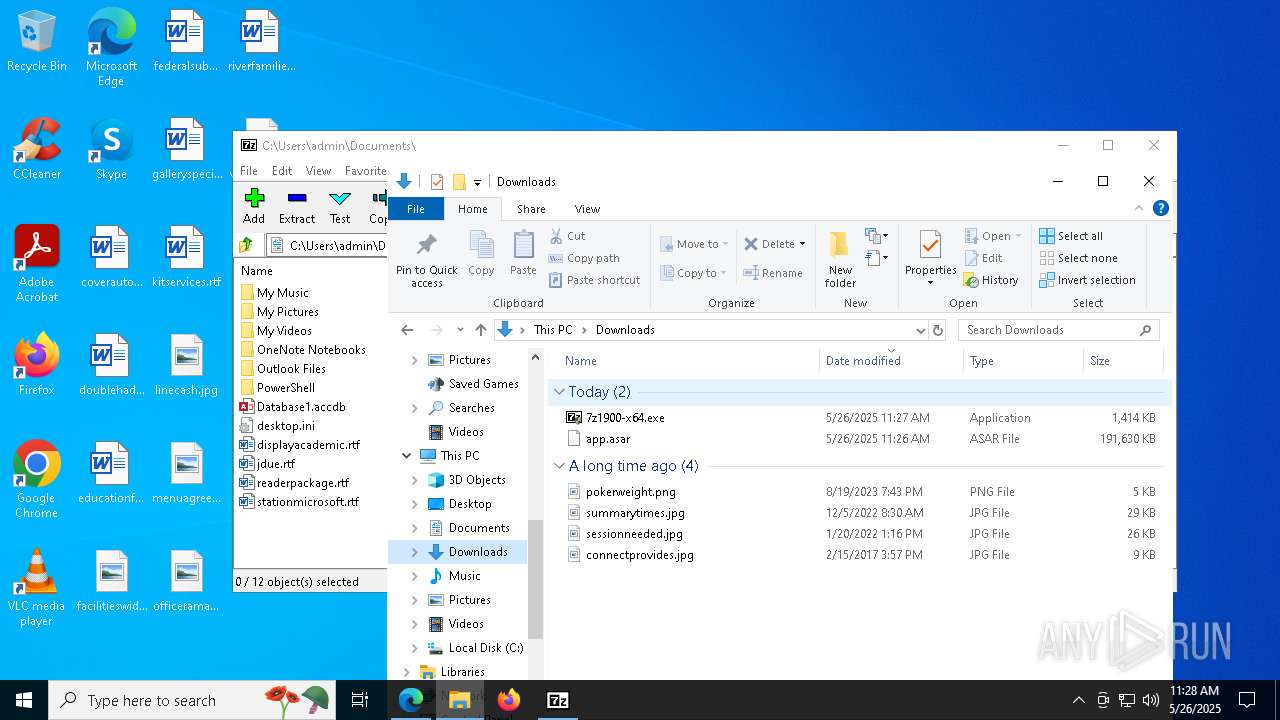
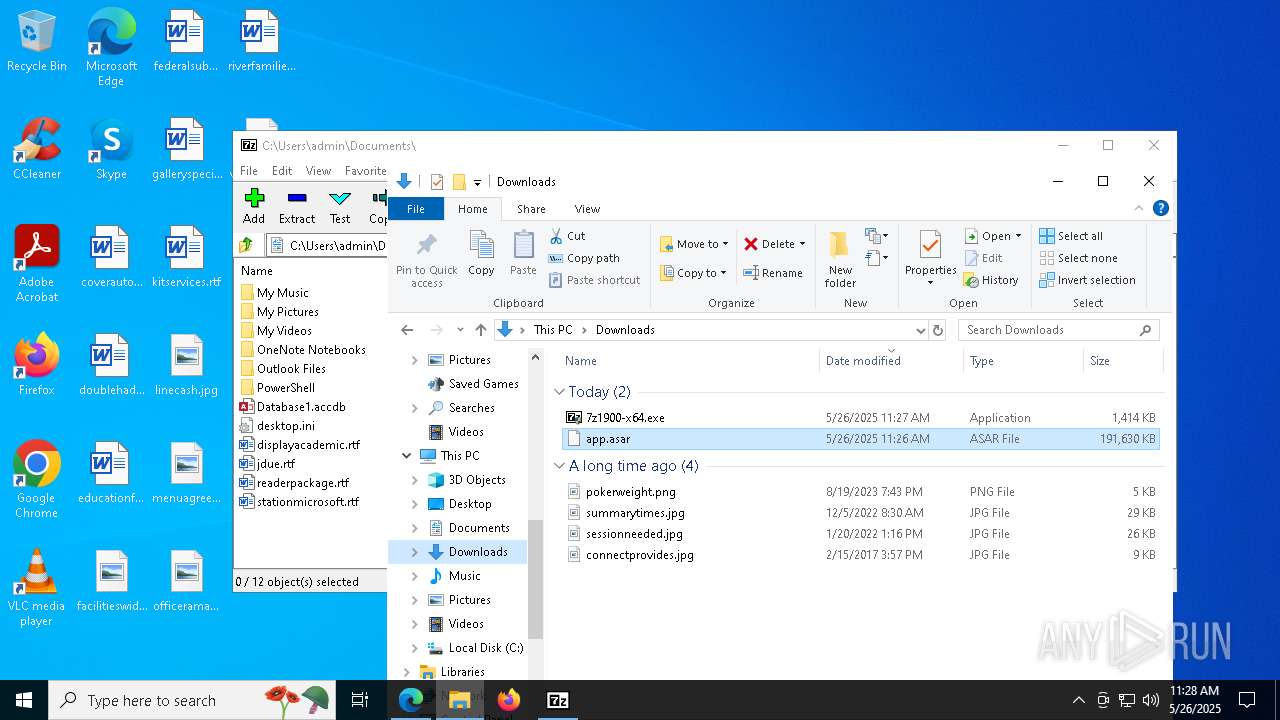
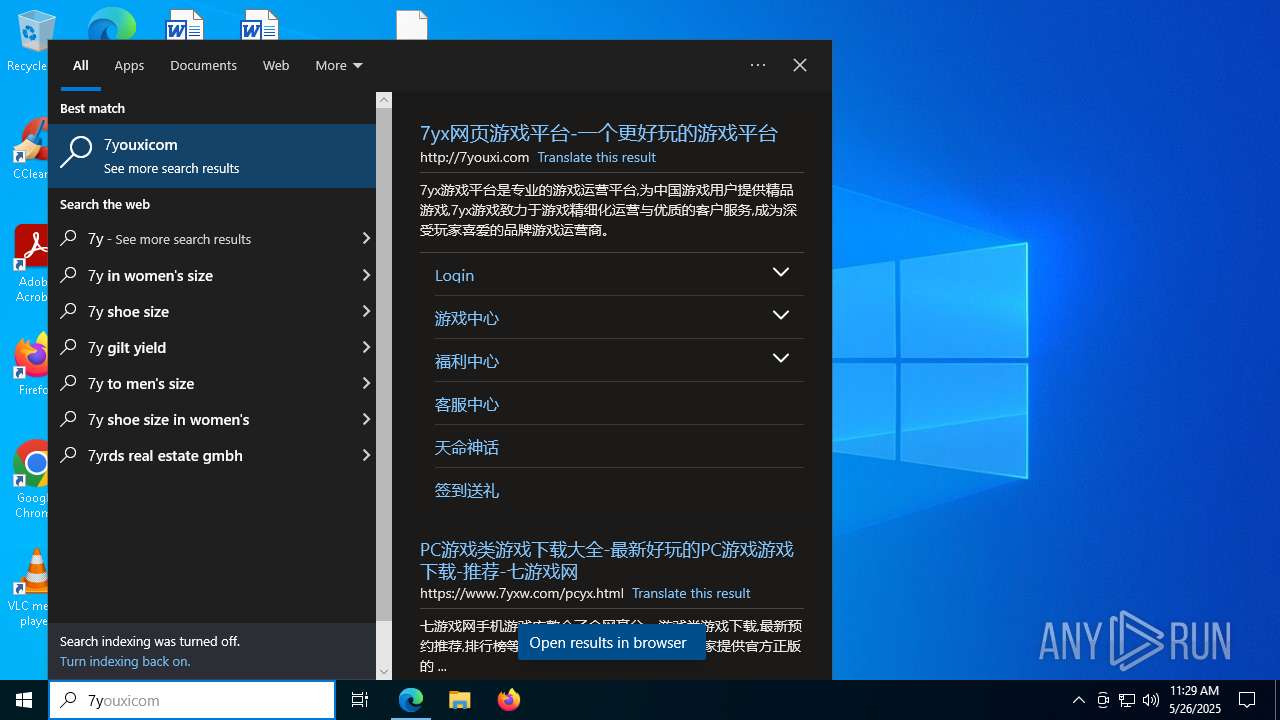
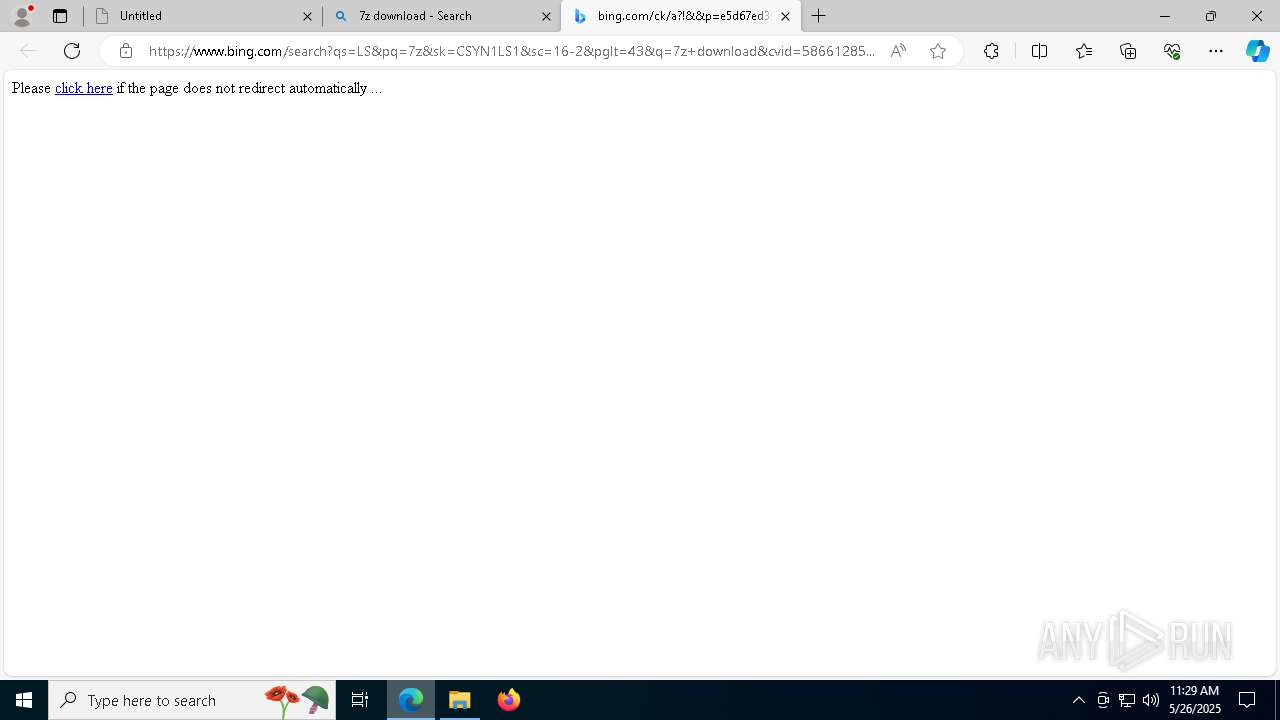
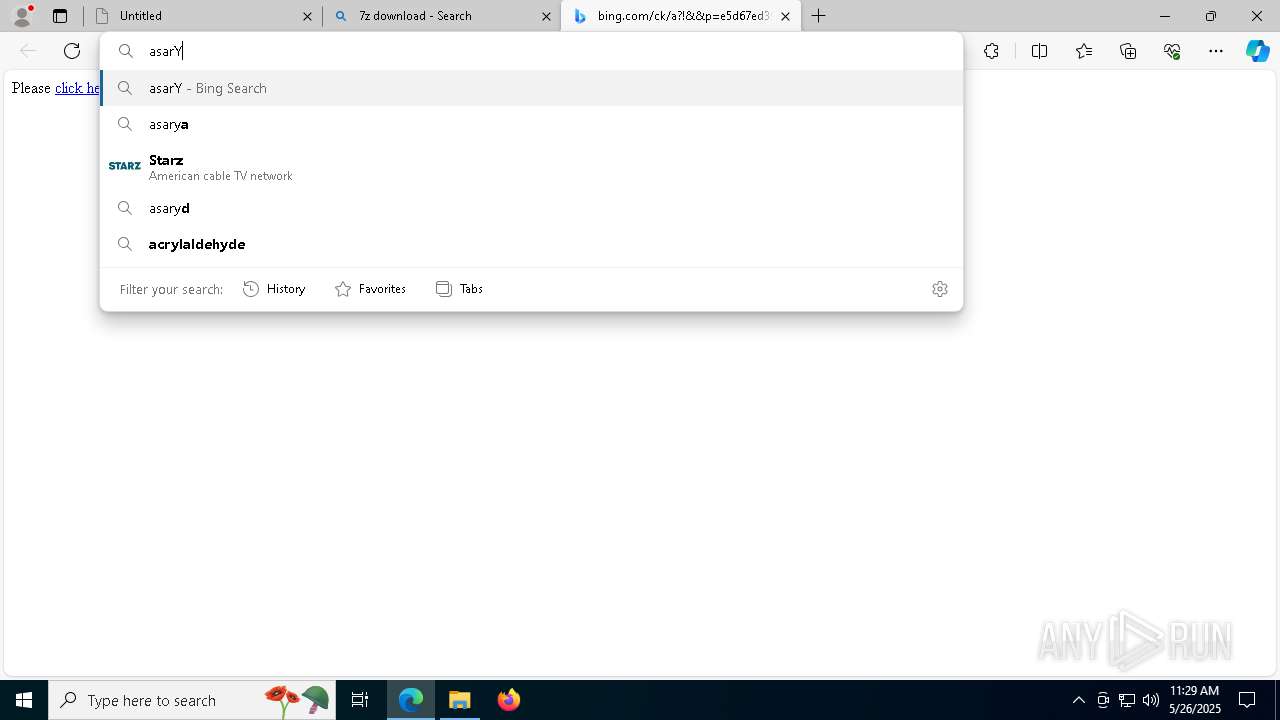
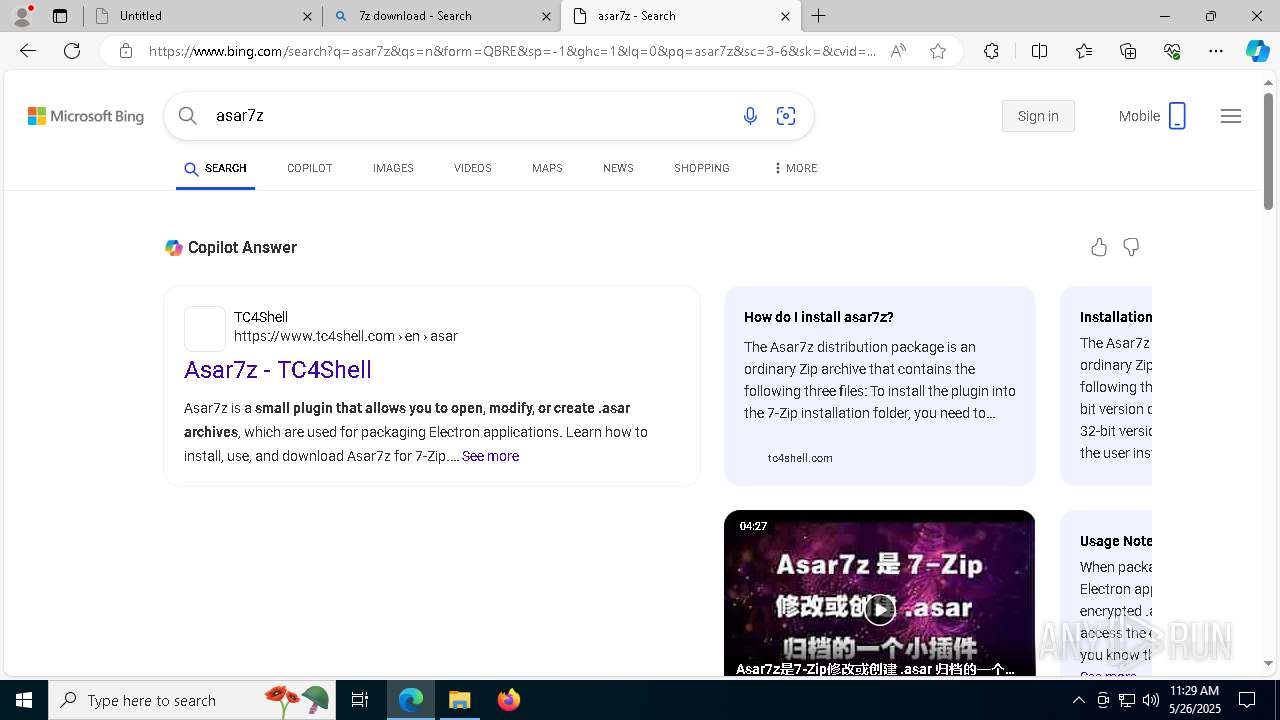
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 7188)
- iexplore.exe (PID: 3332)
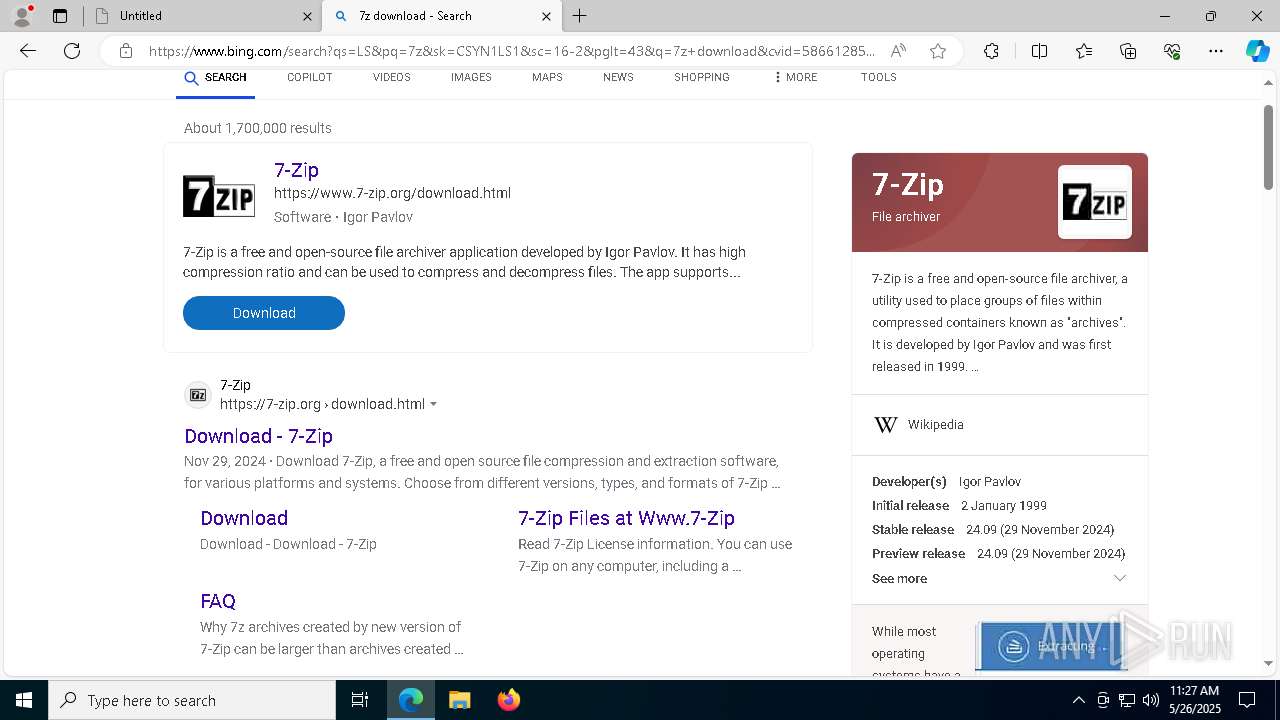
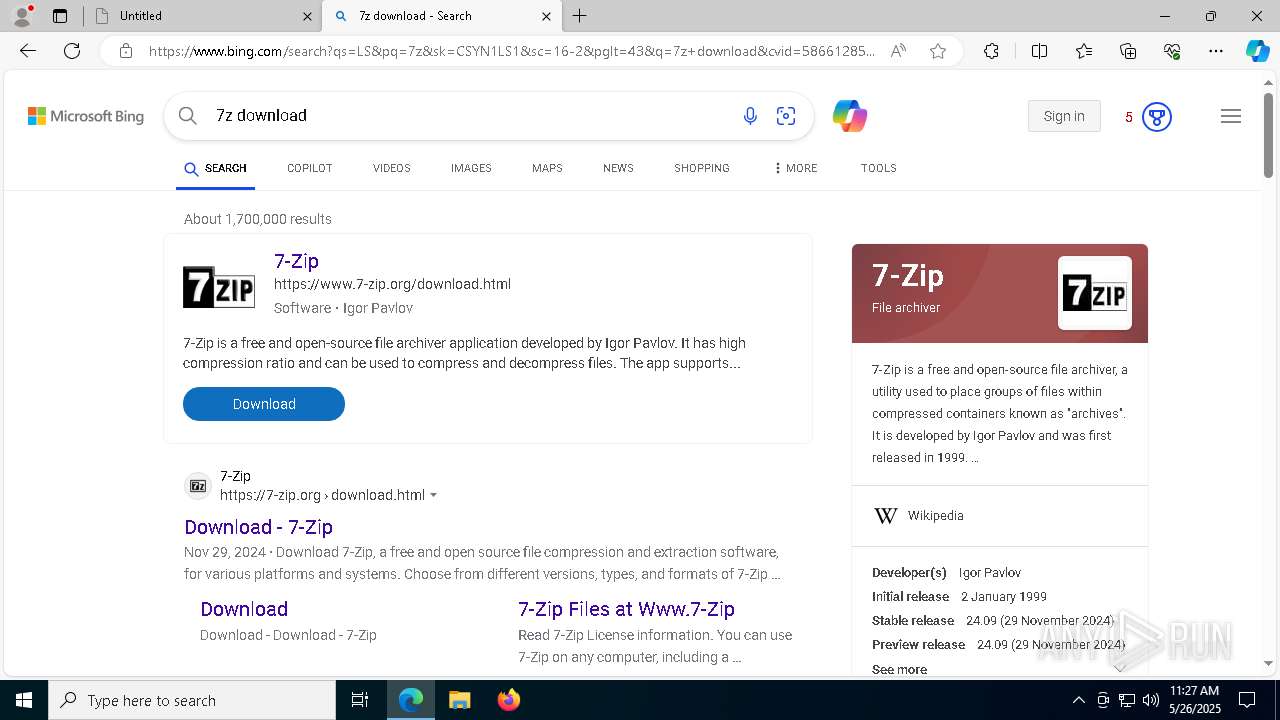
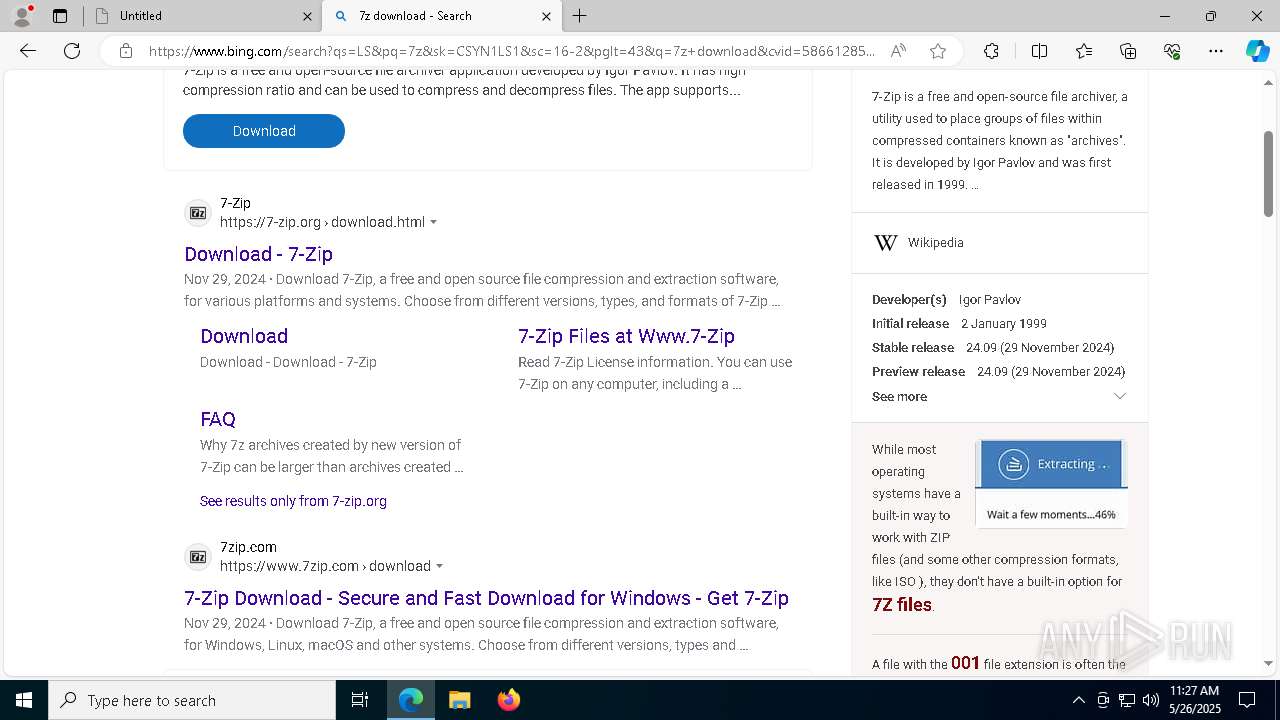
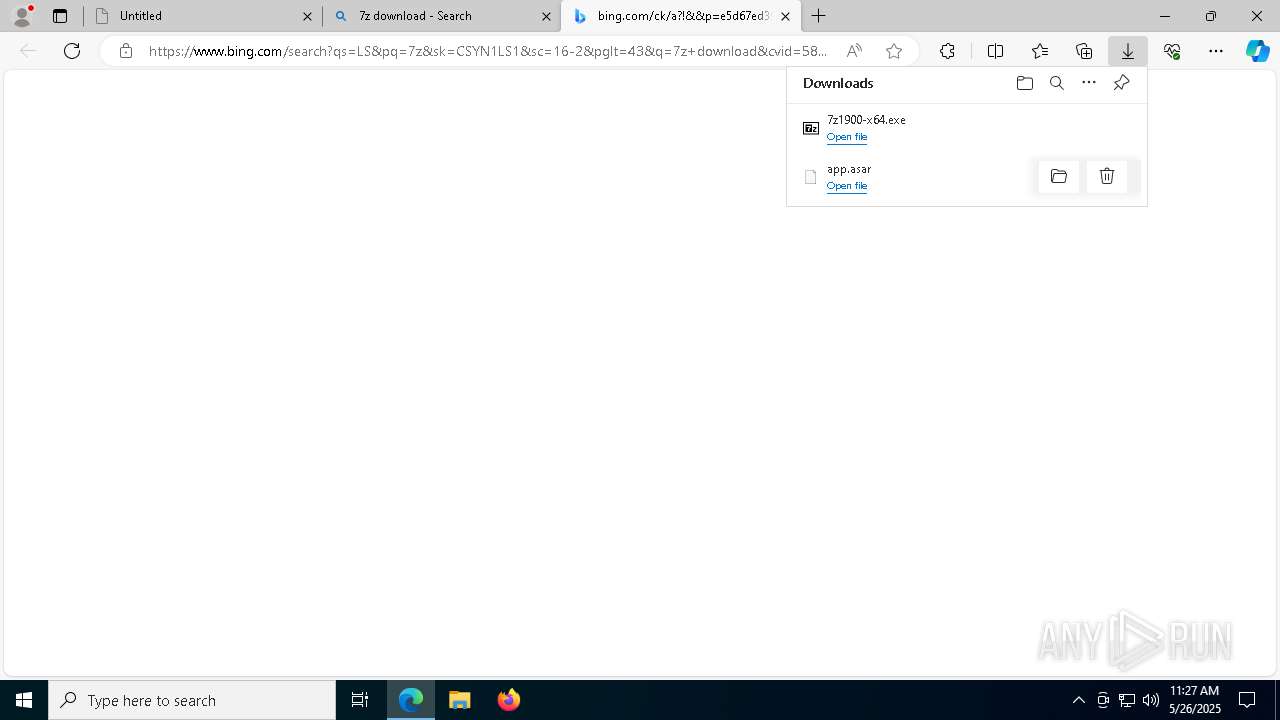
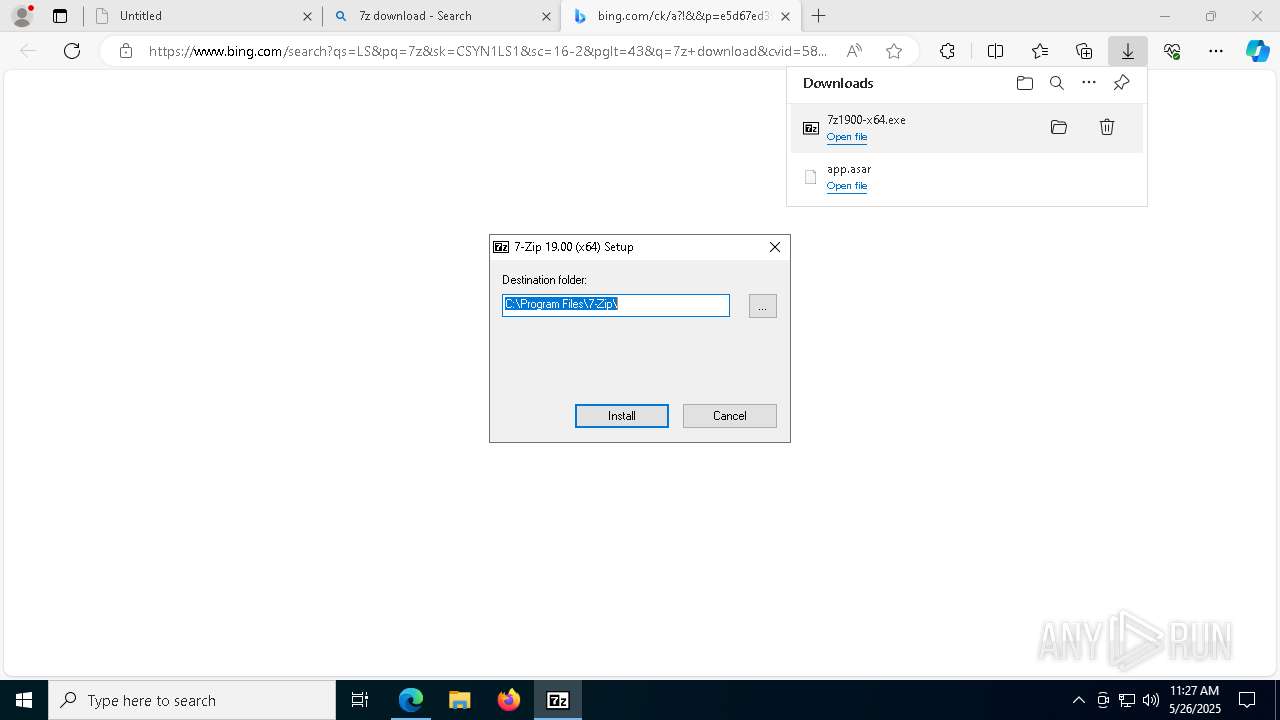
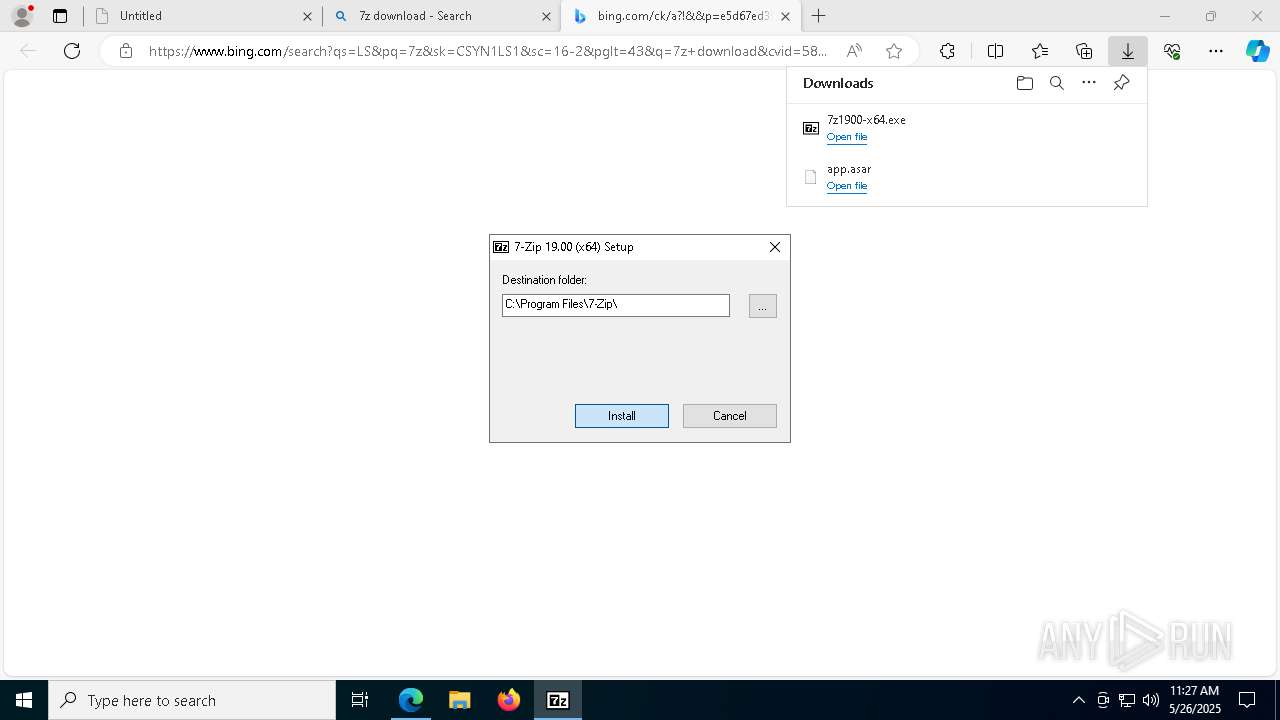
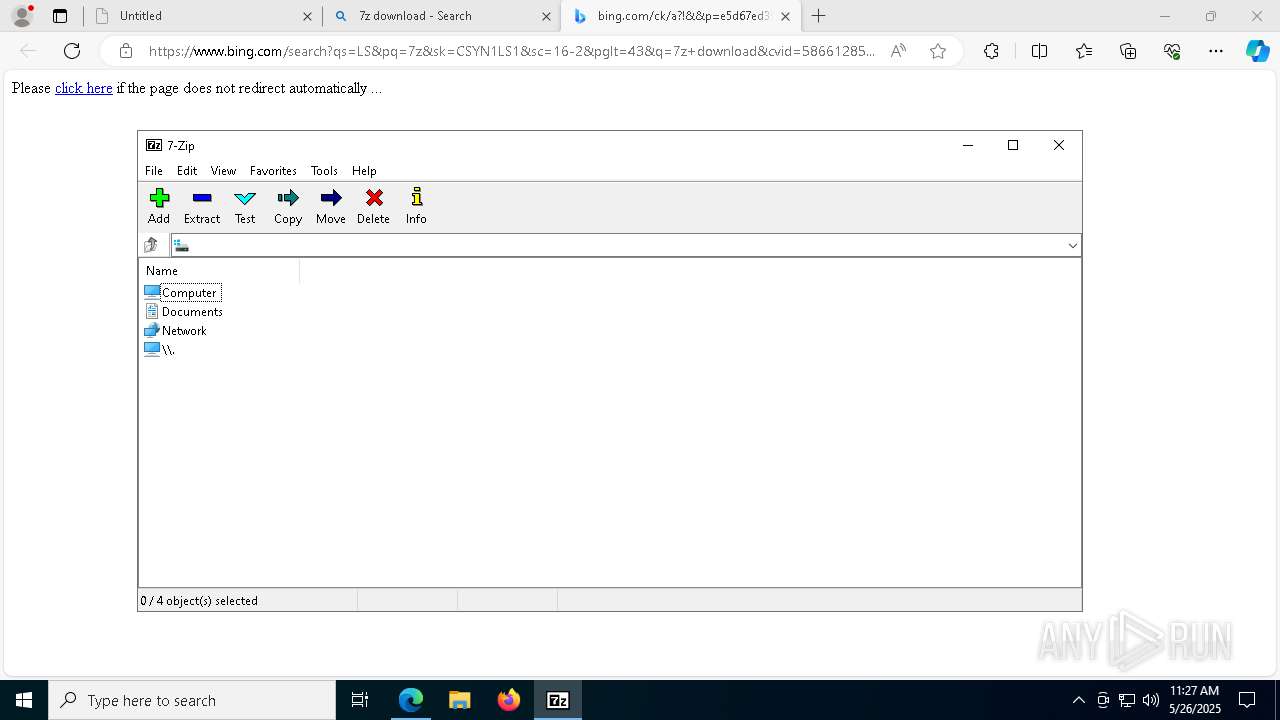
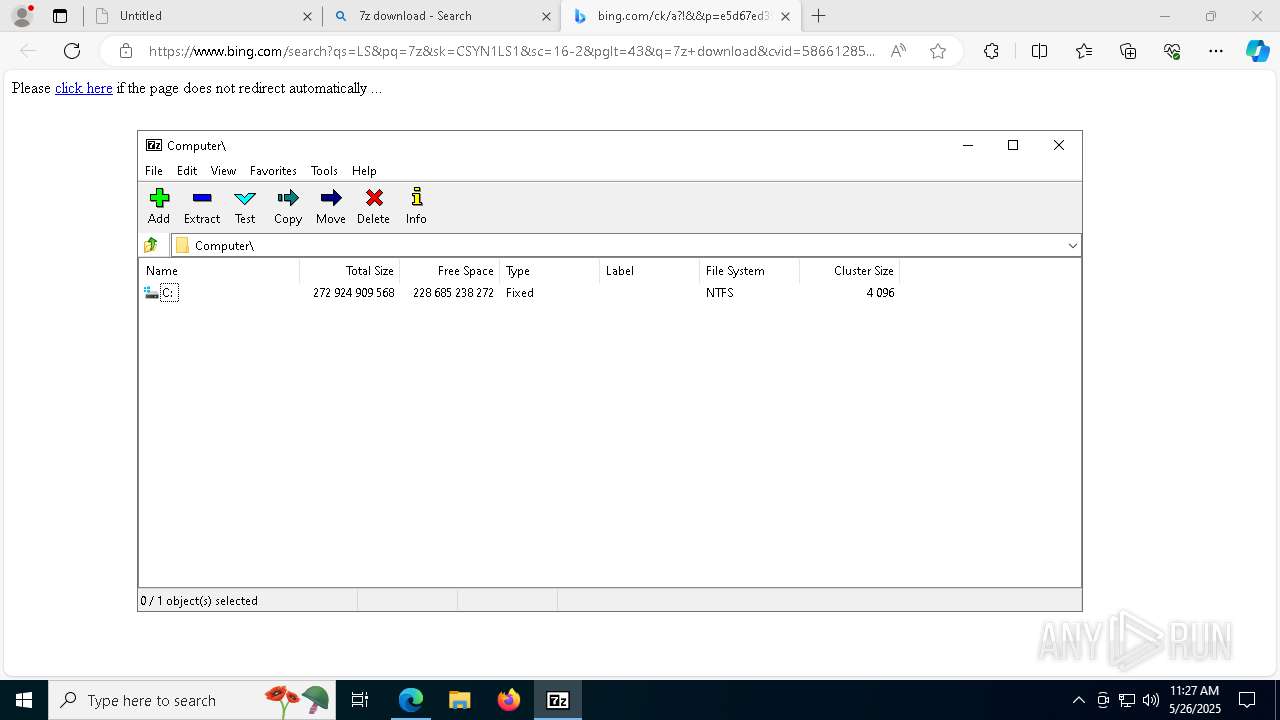
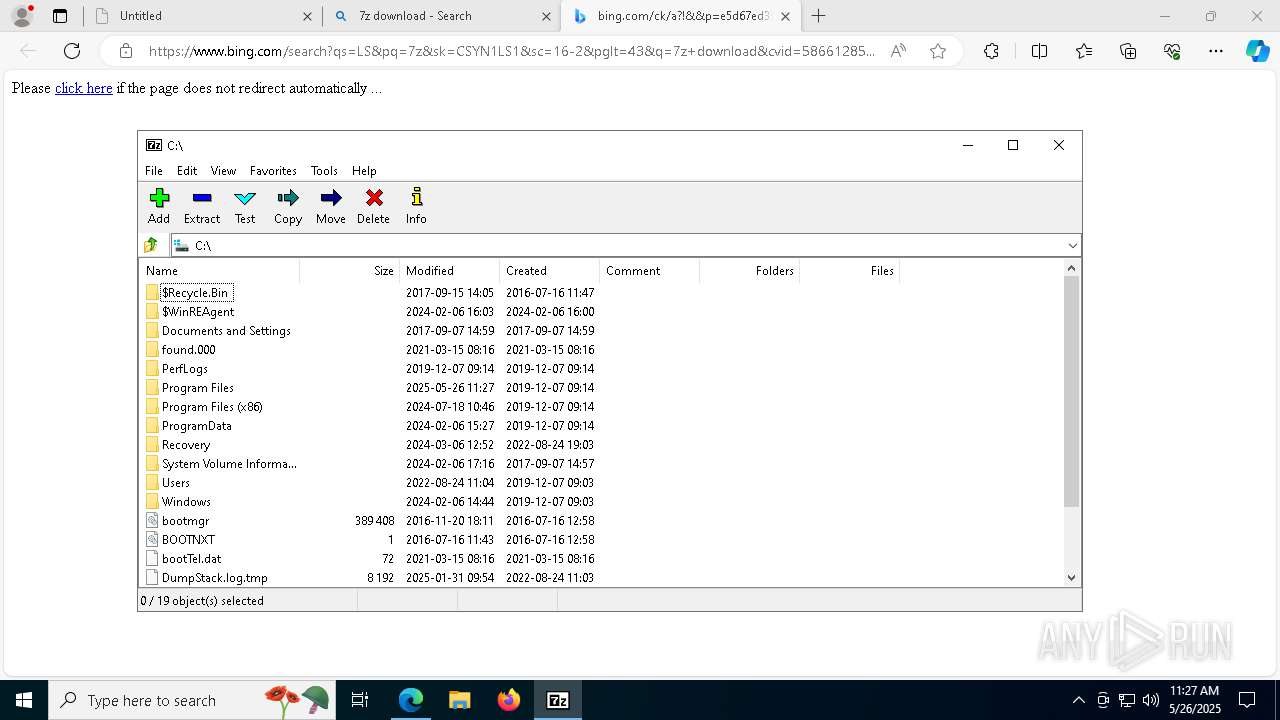
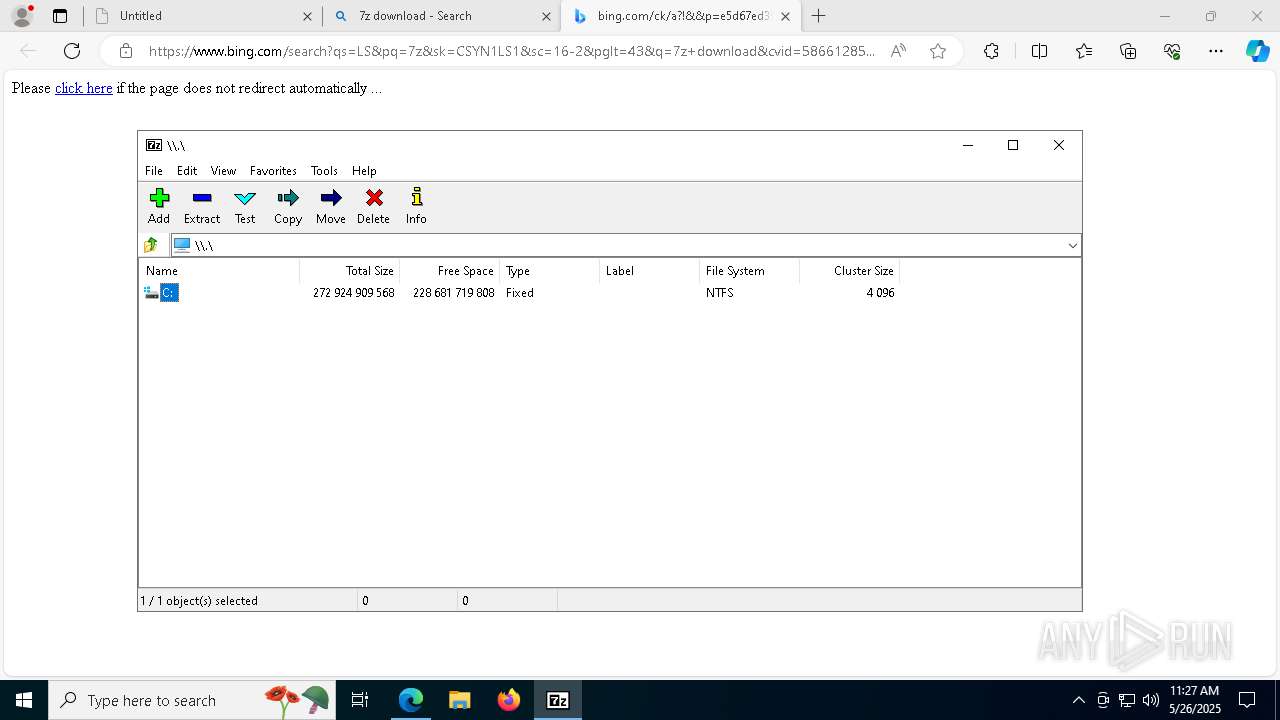
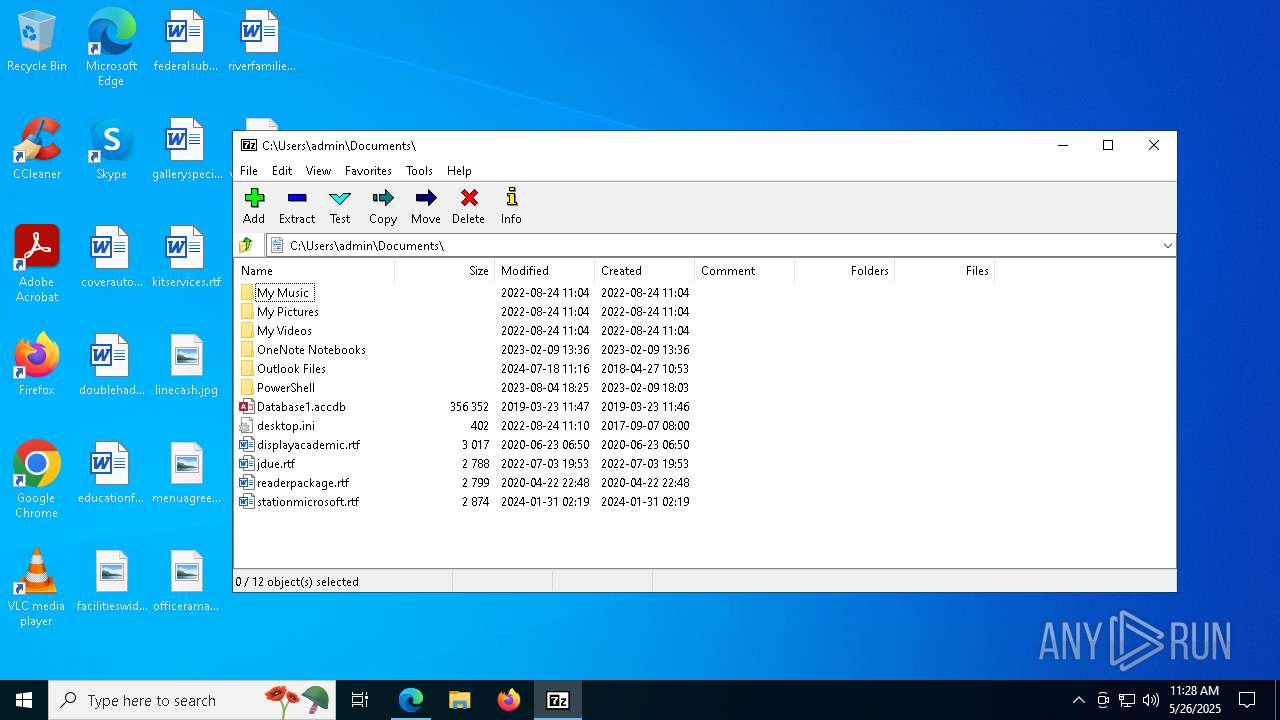
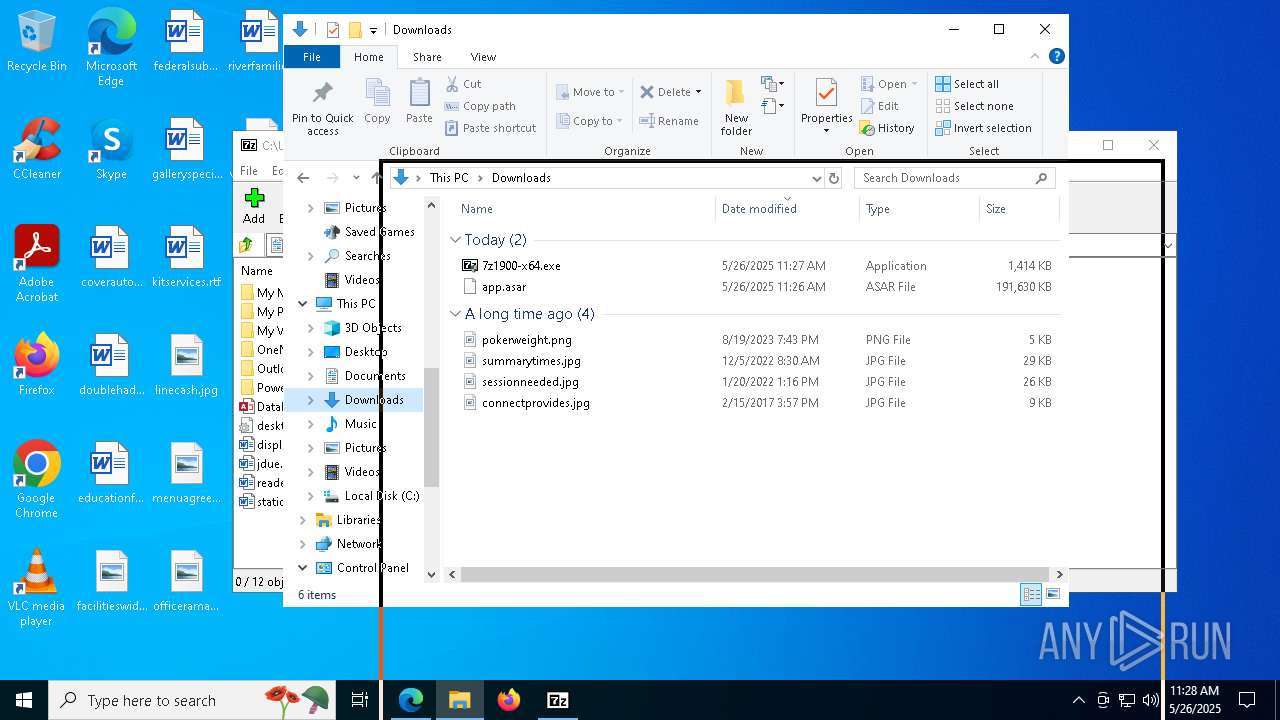
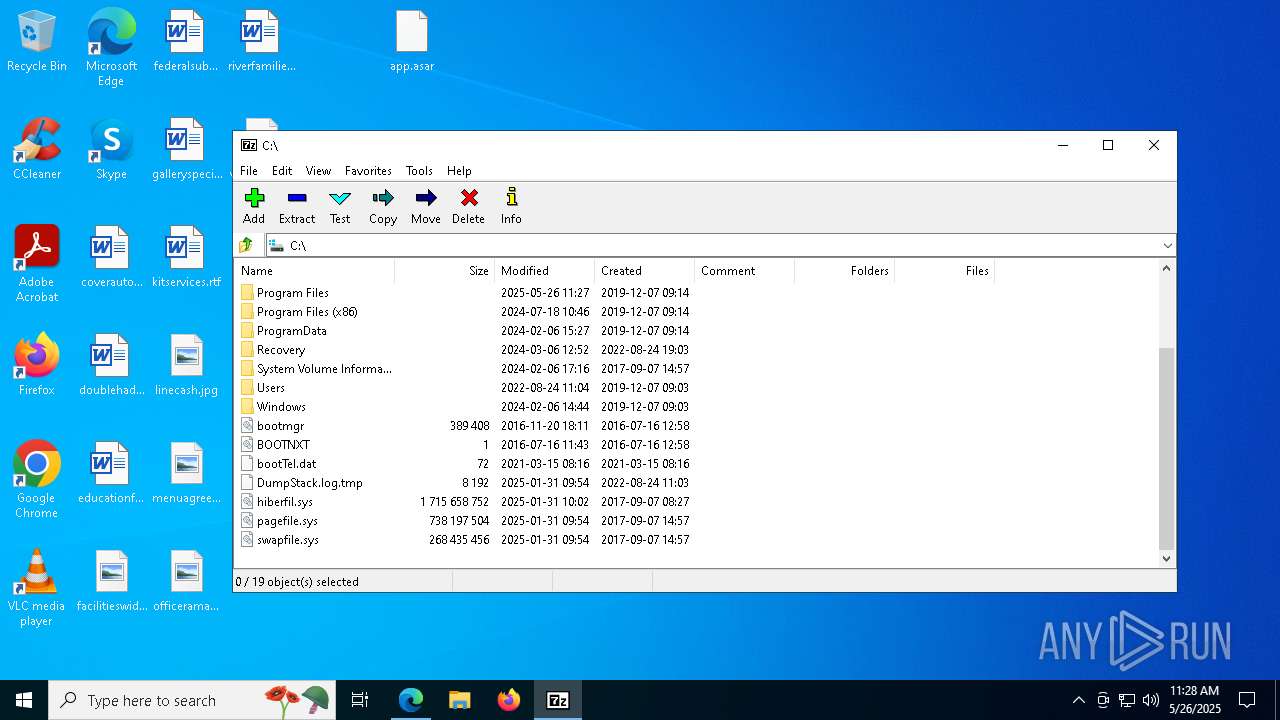
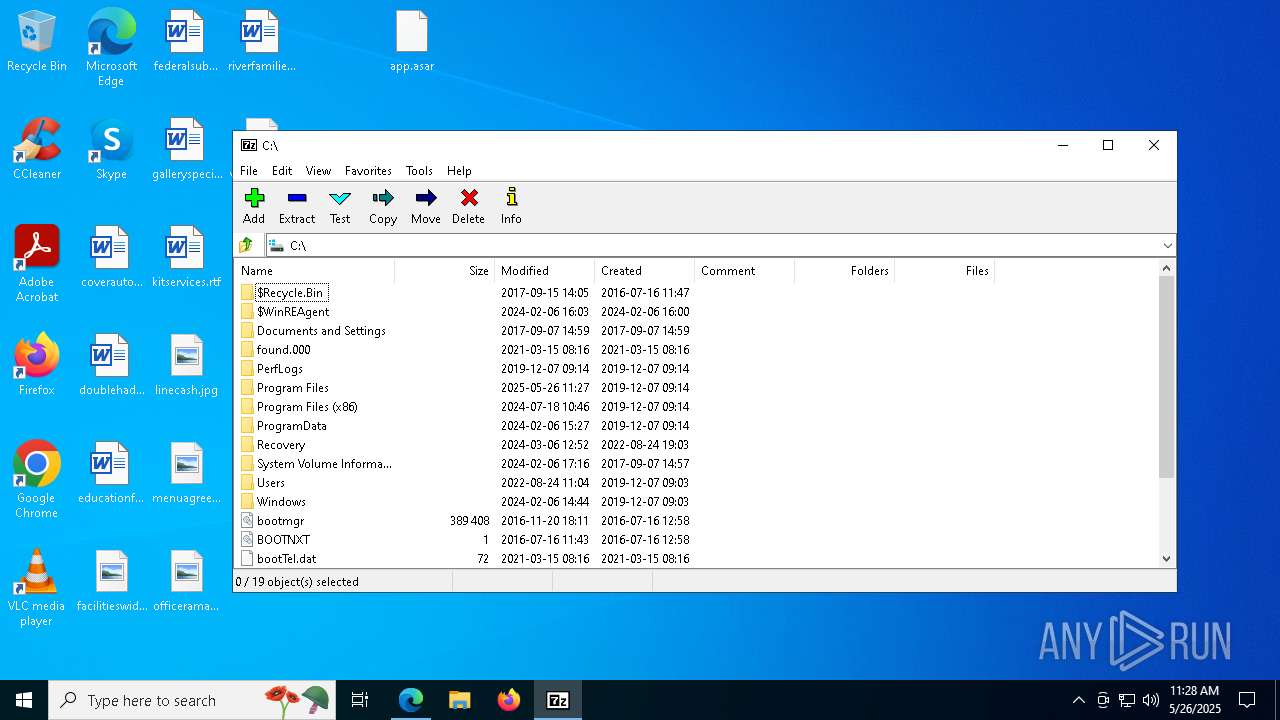
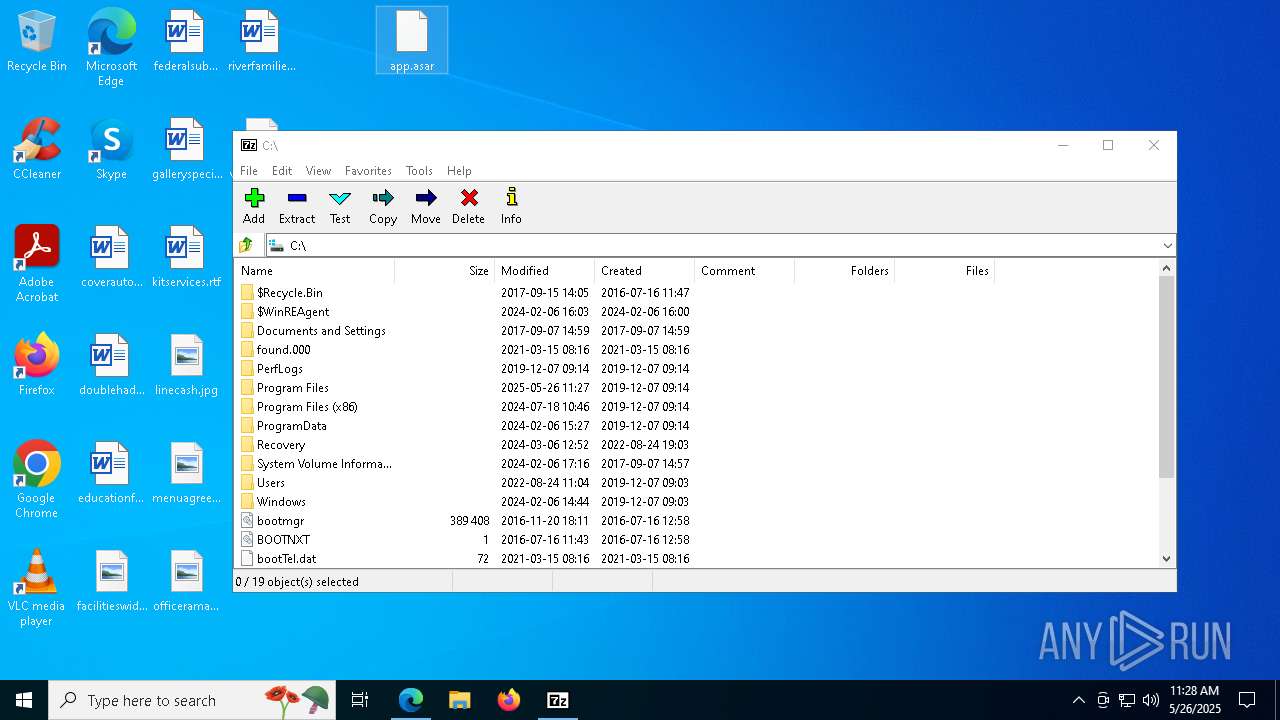
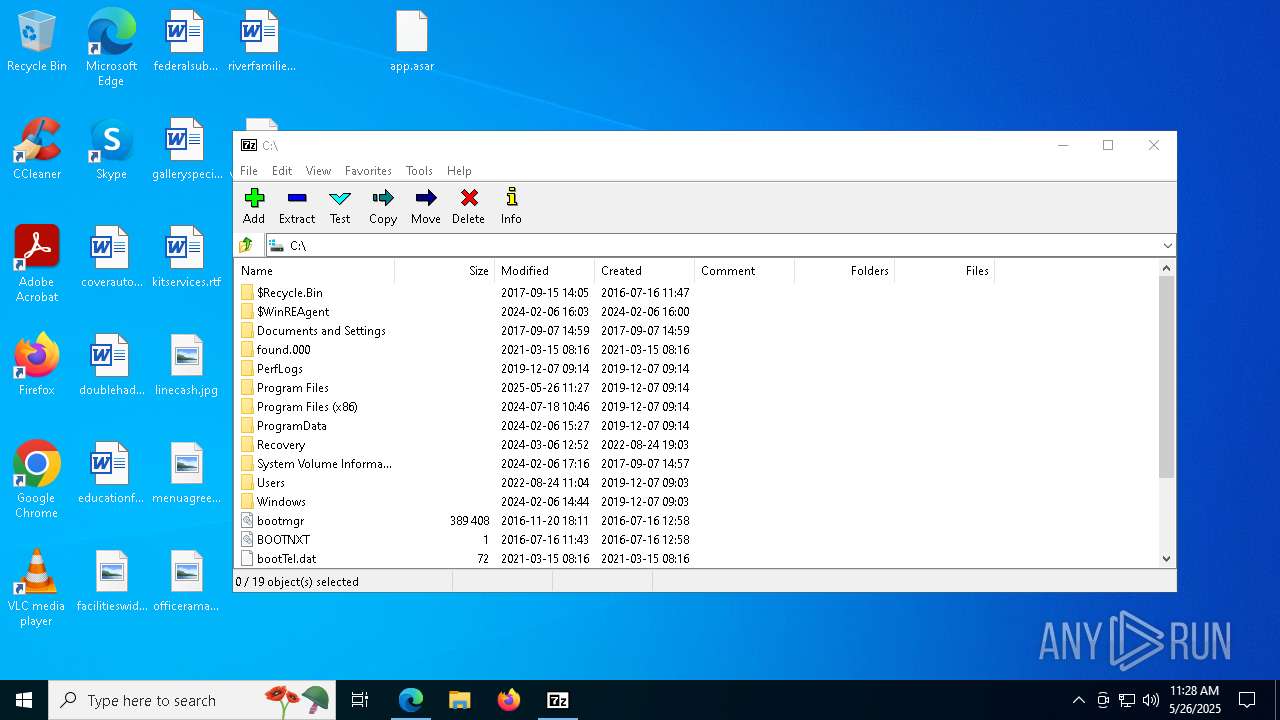
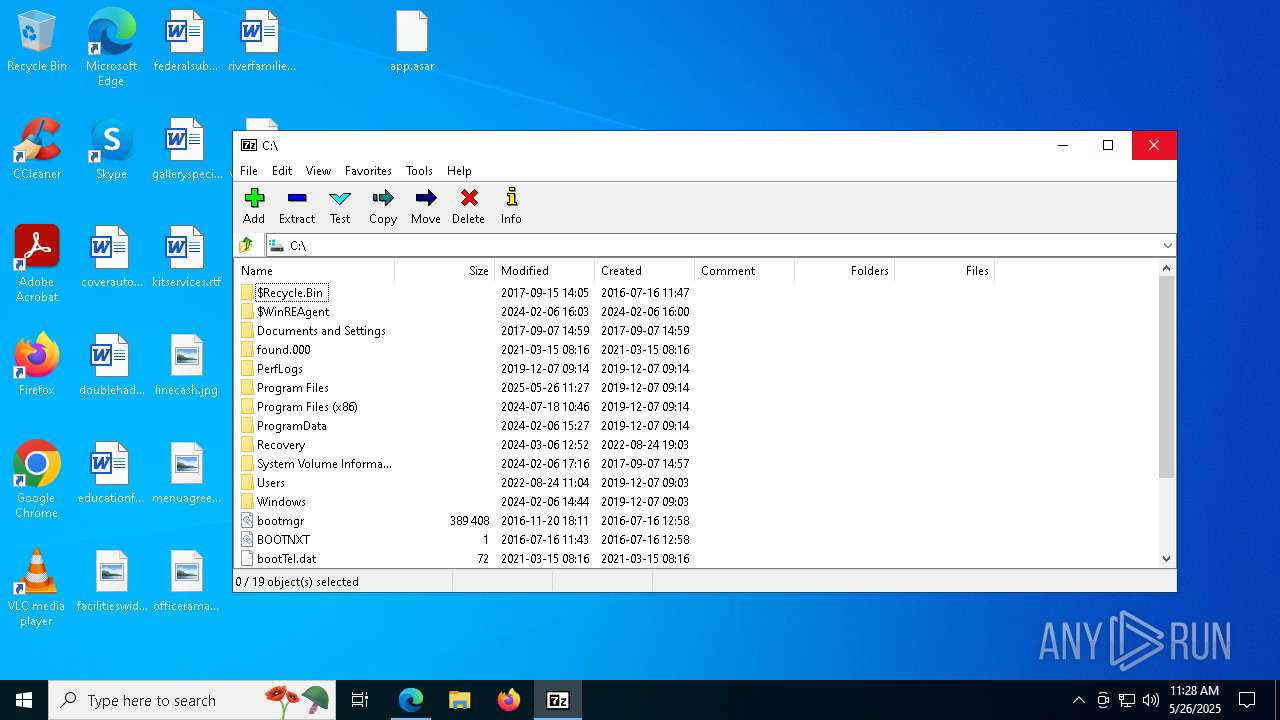
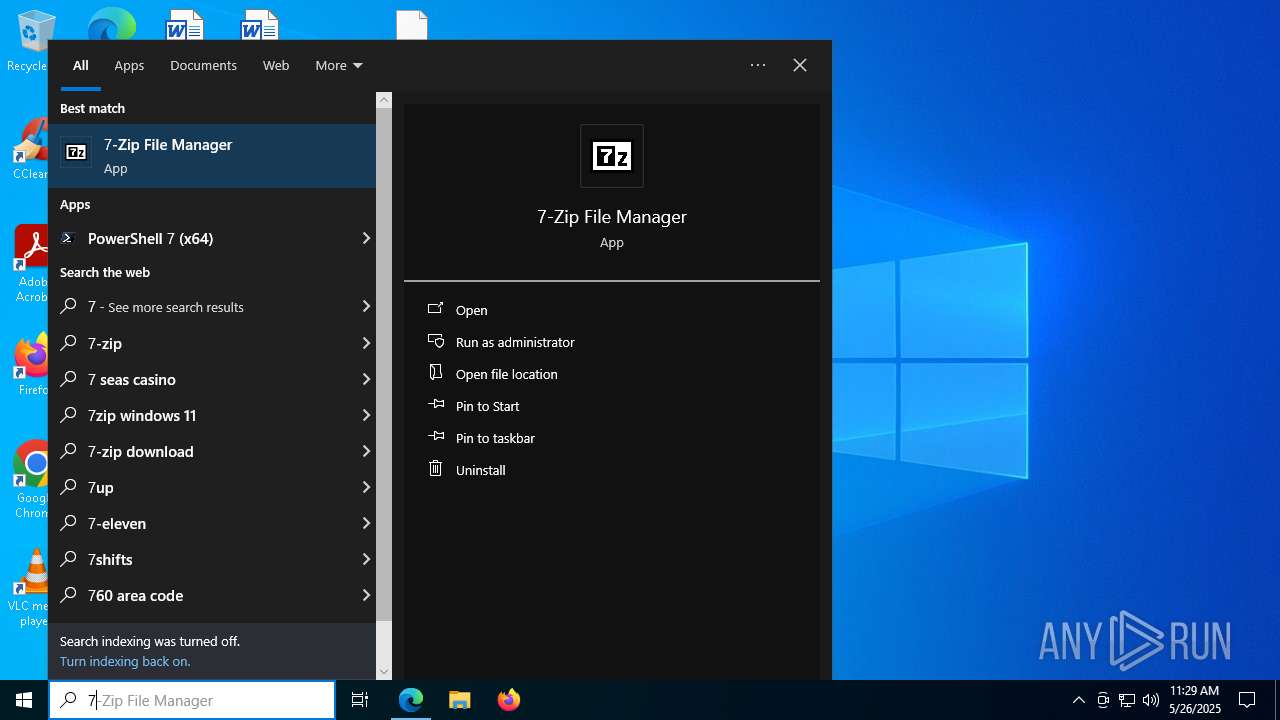
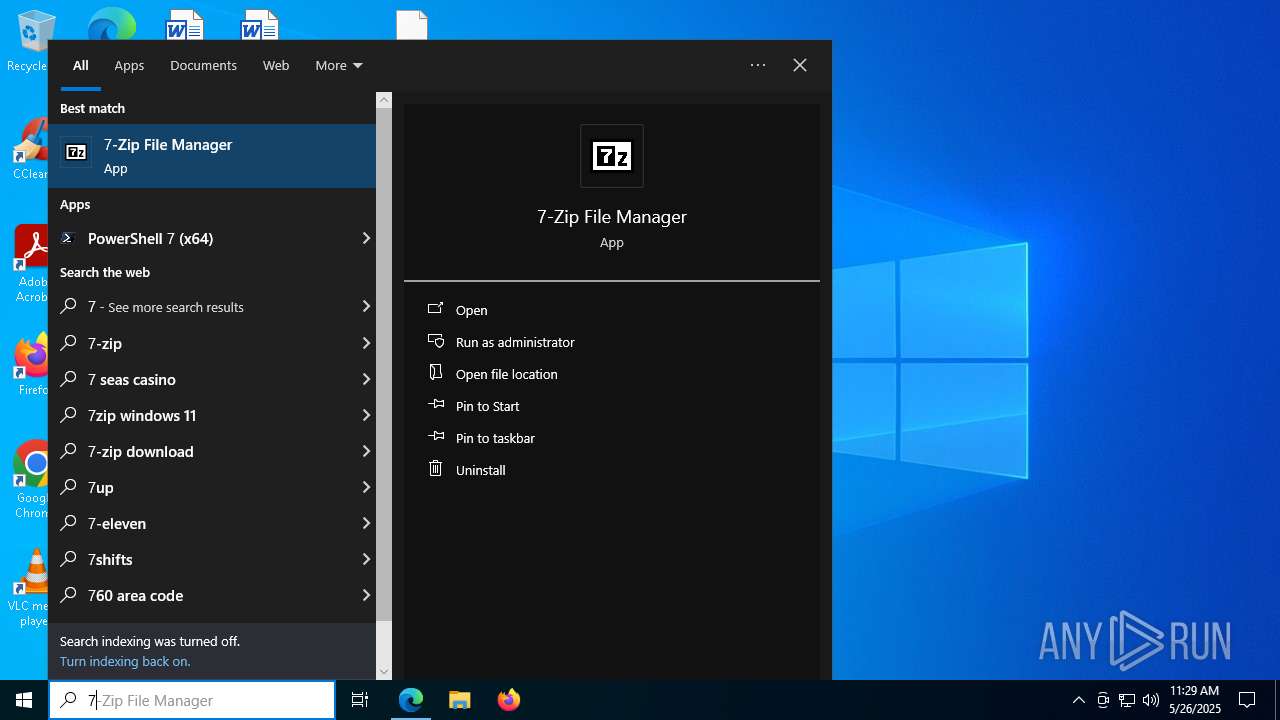
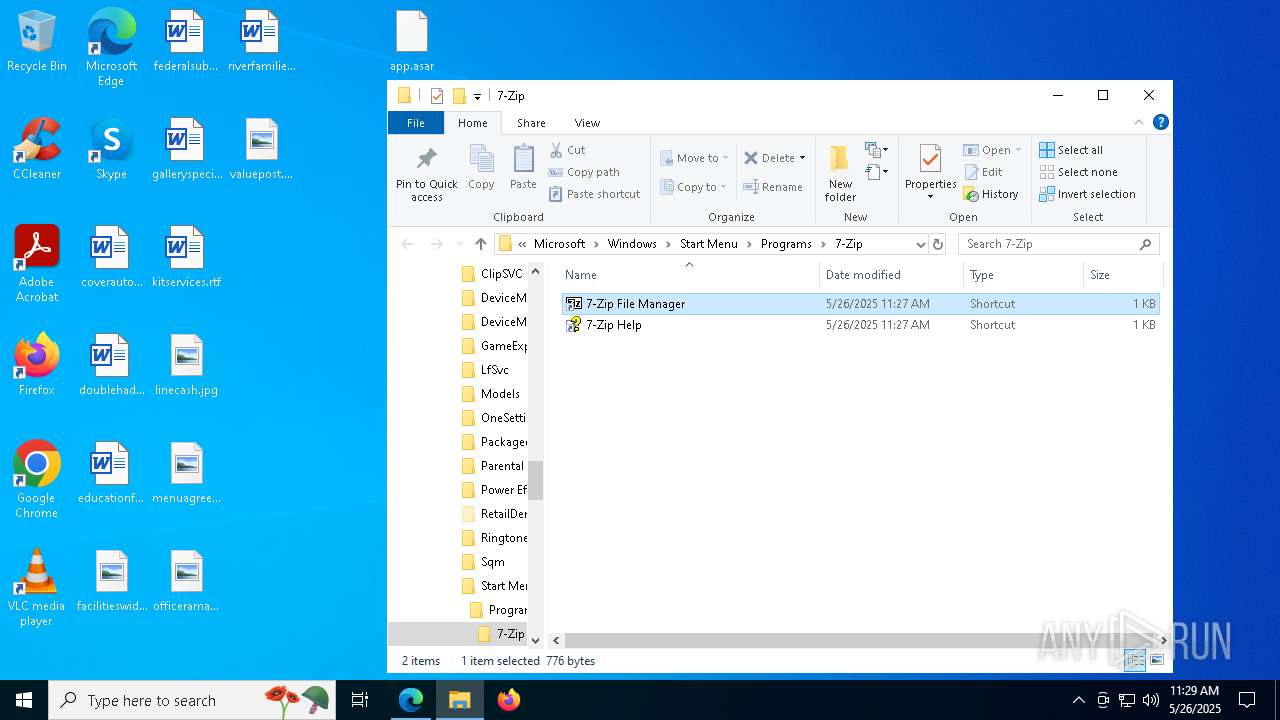
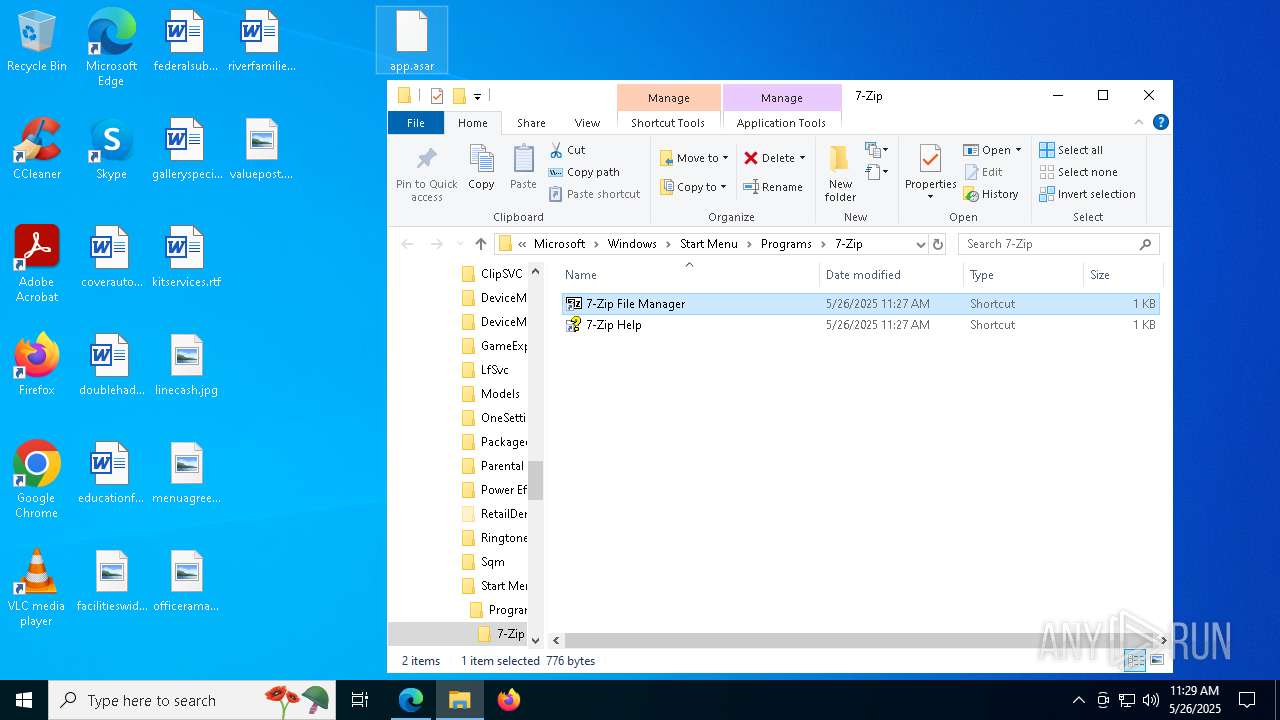
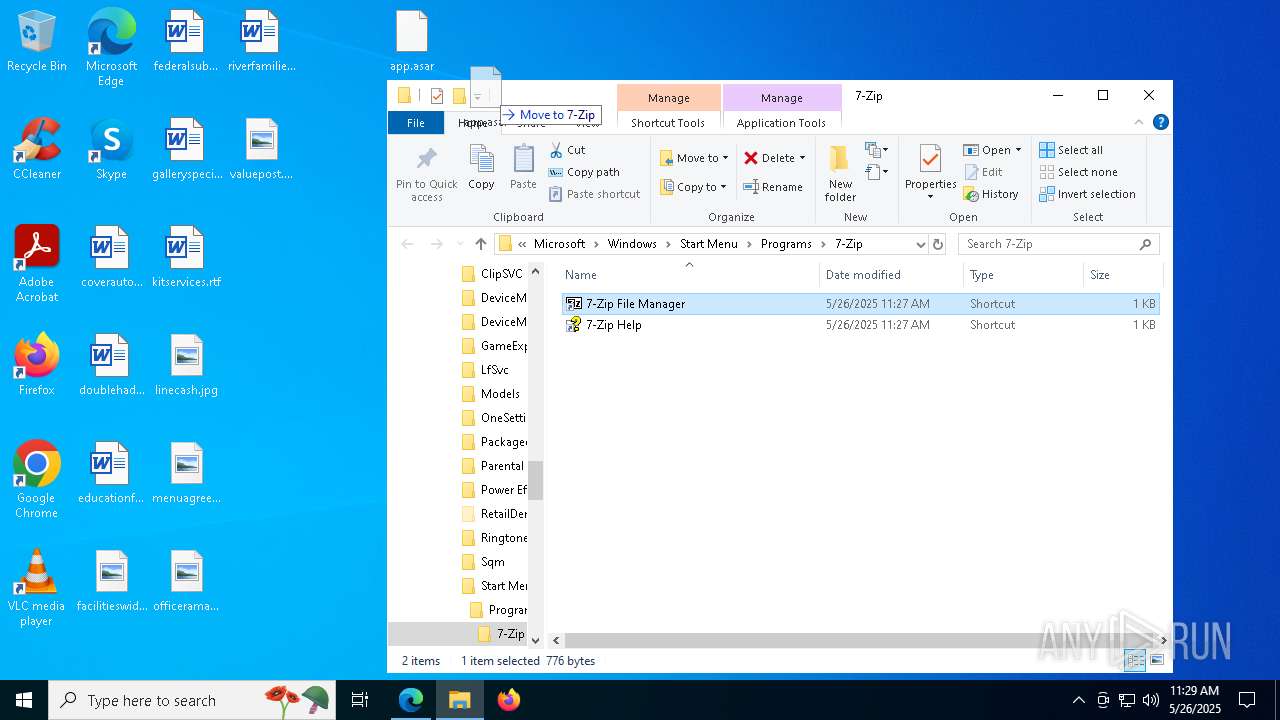
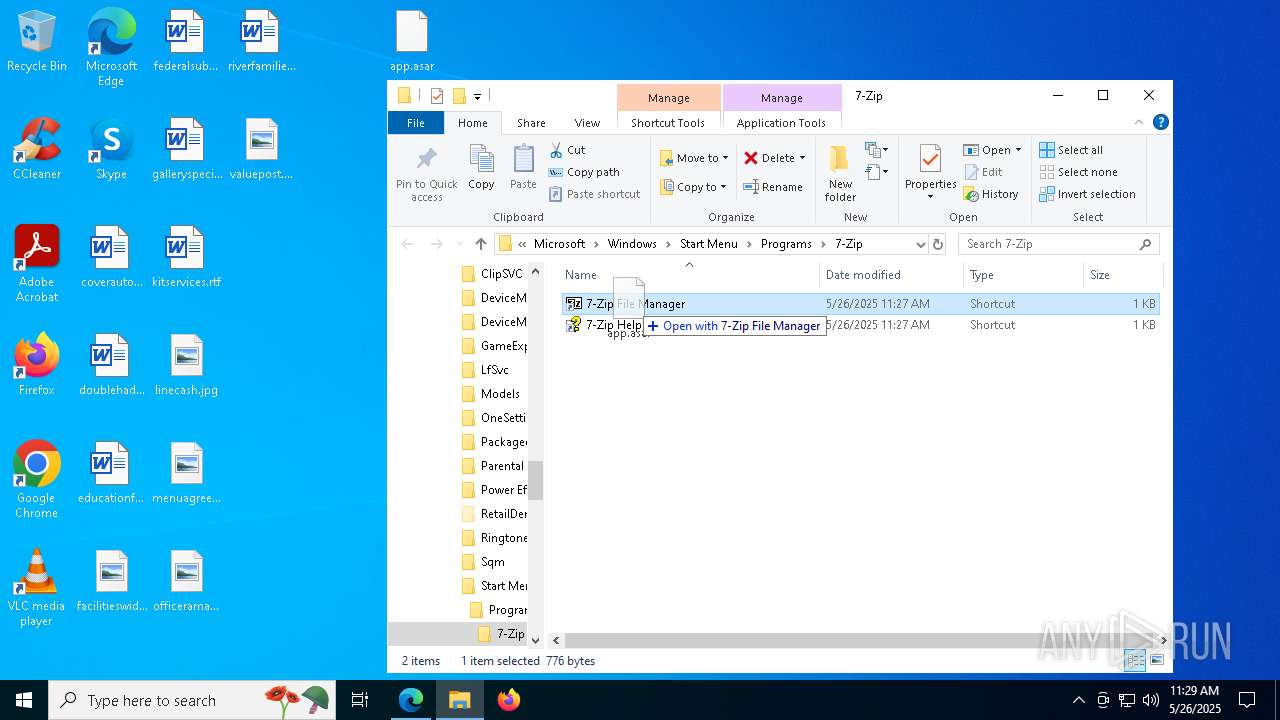
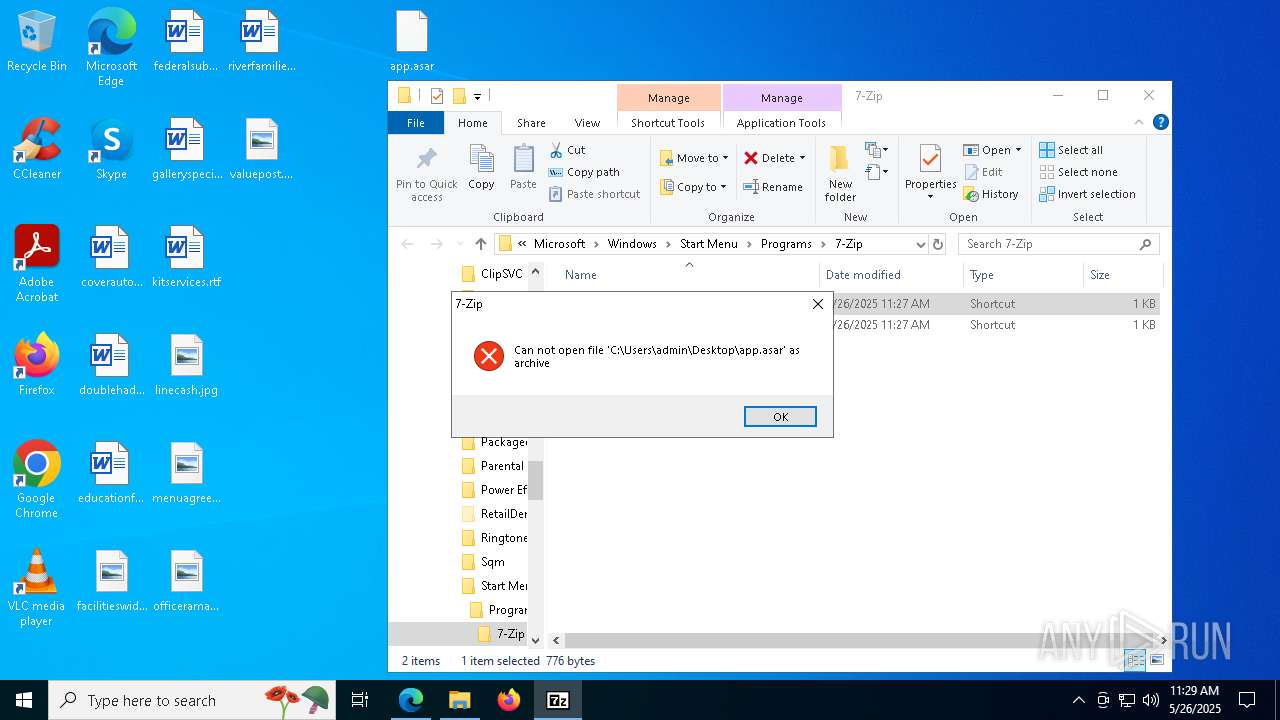
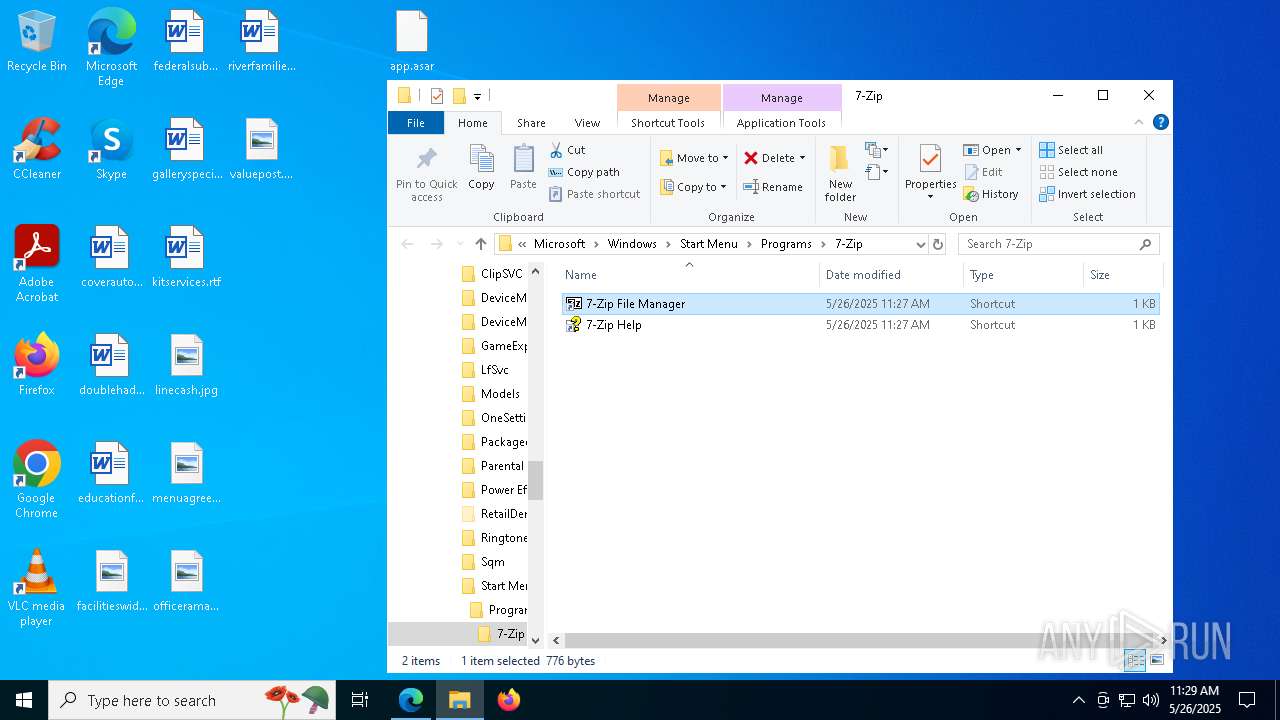
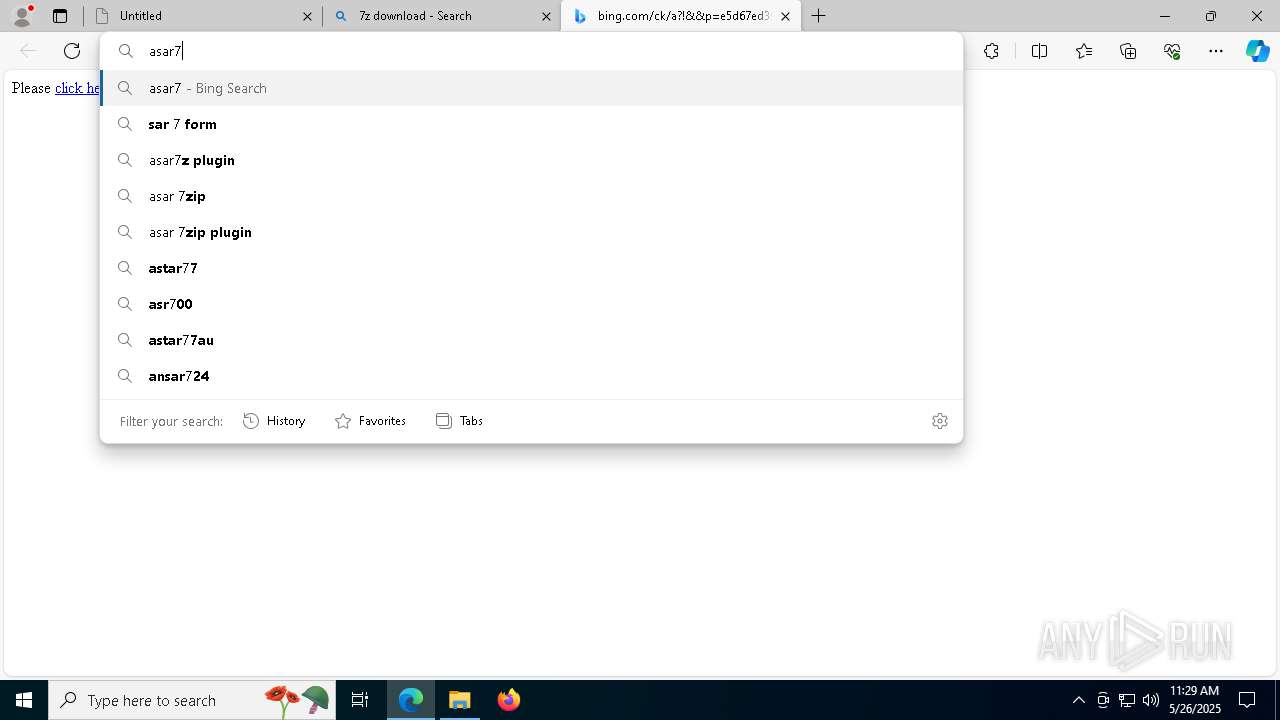
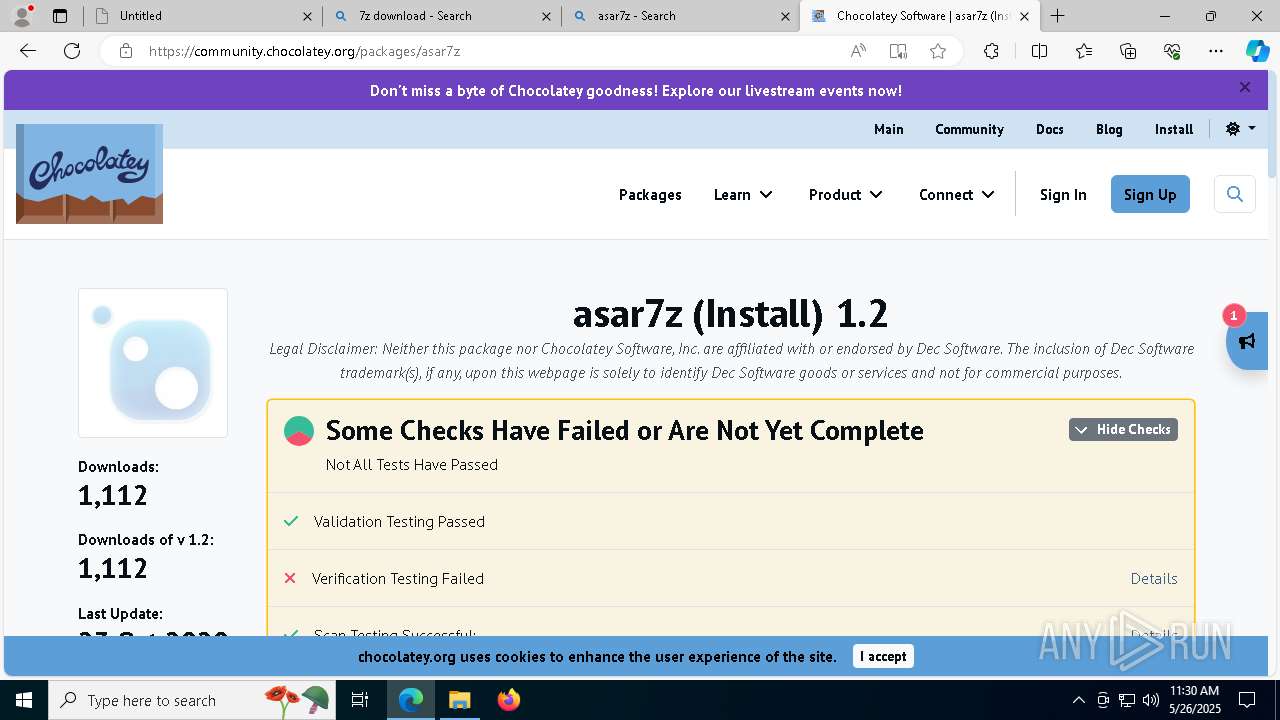
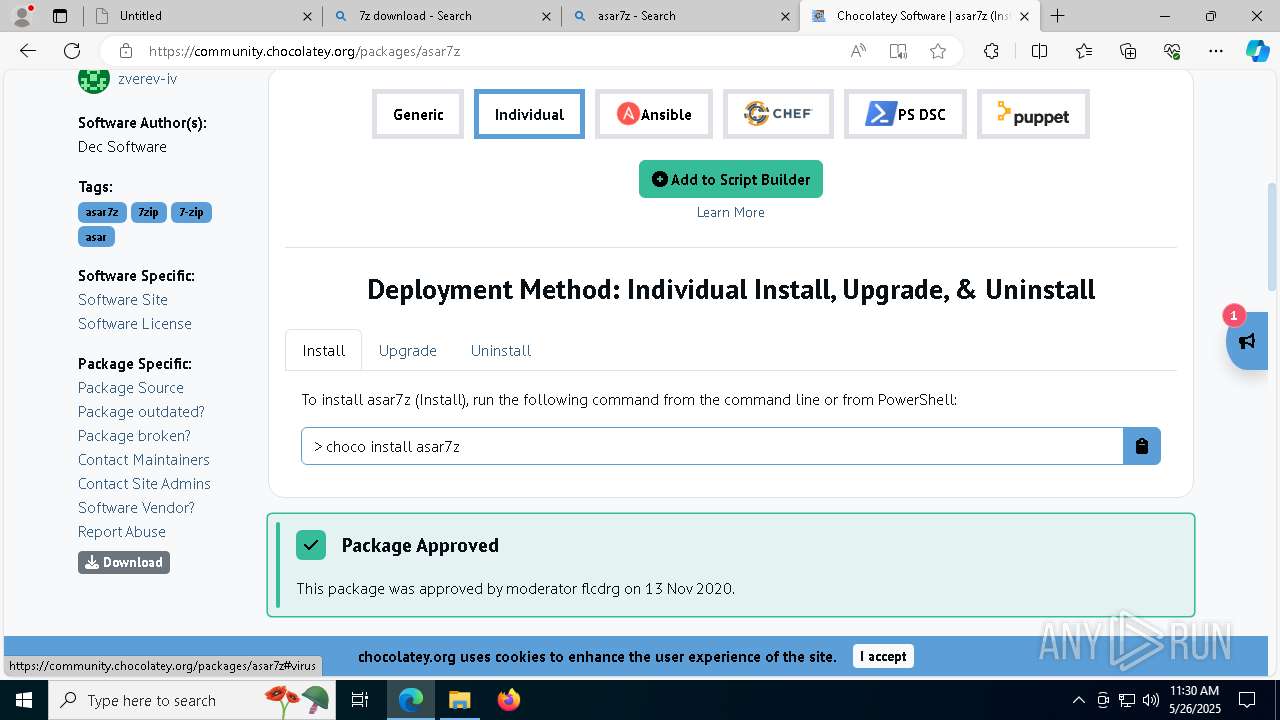
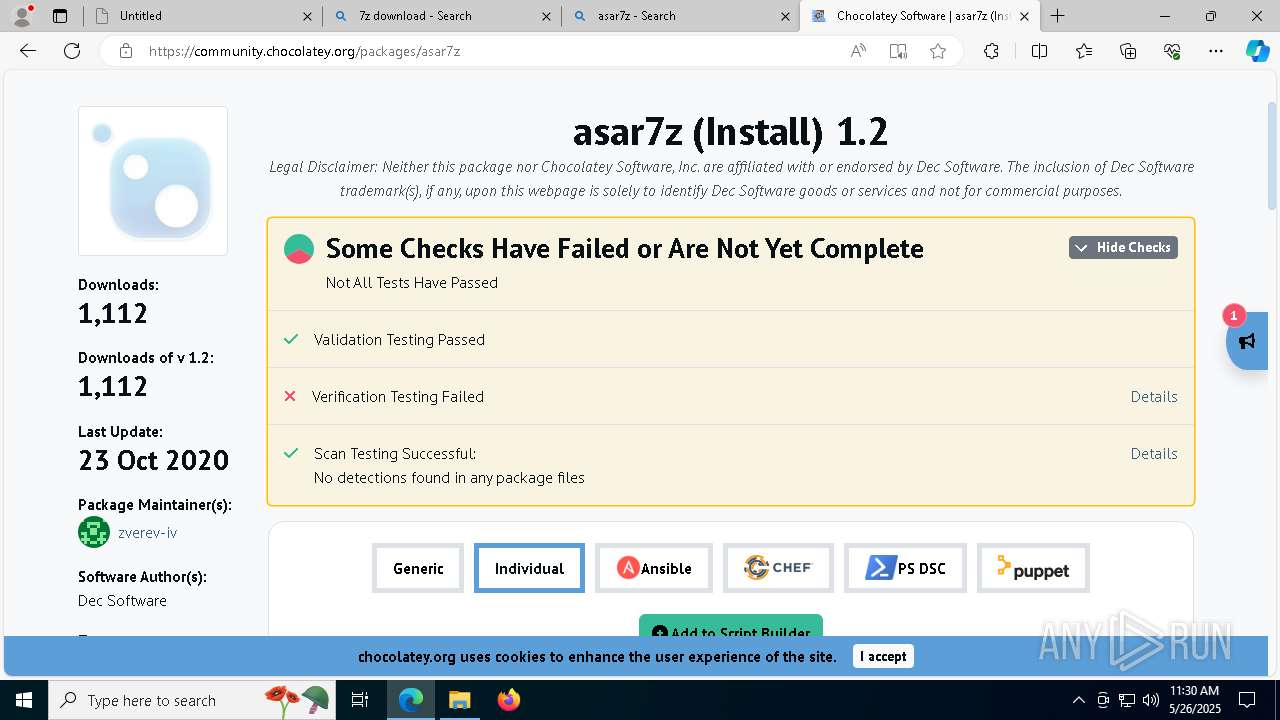
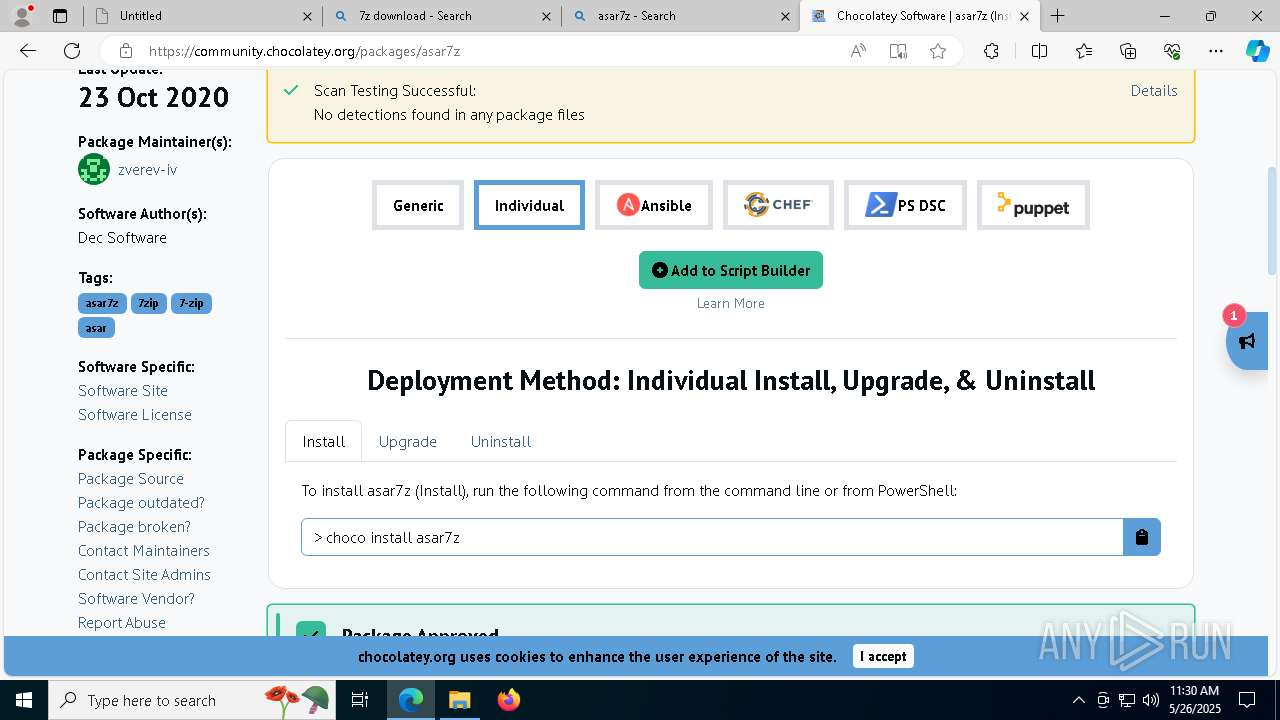
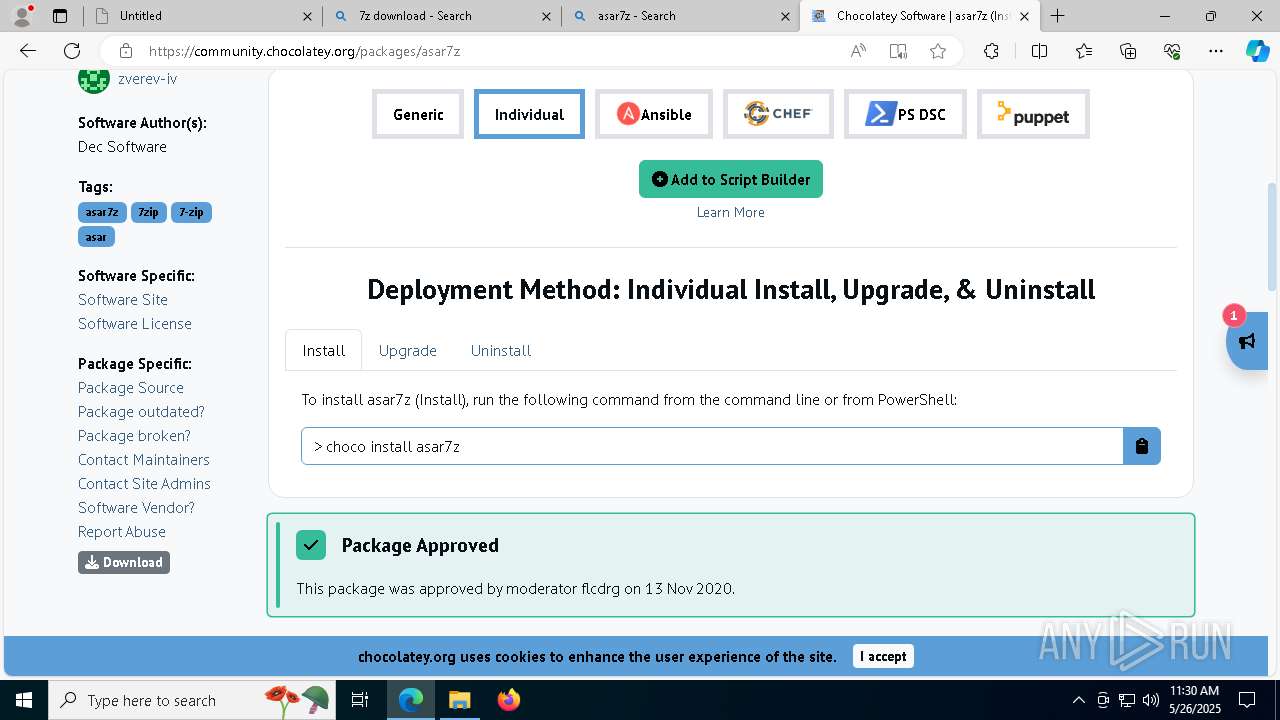
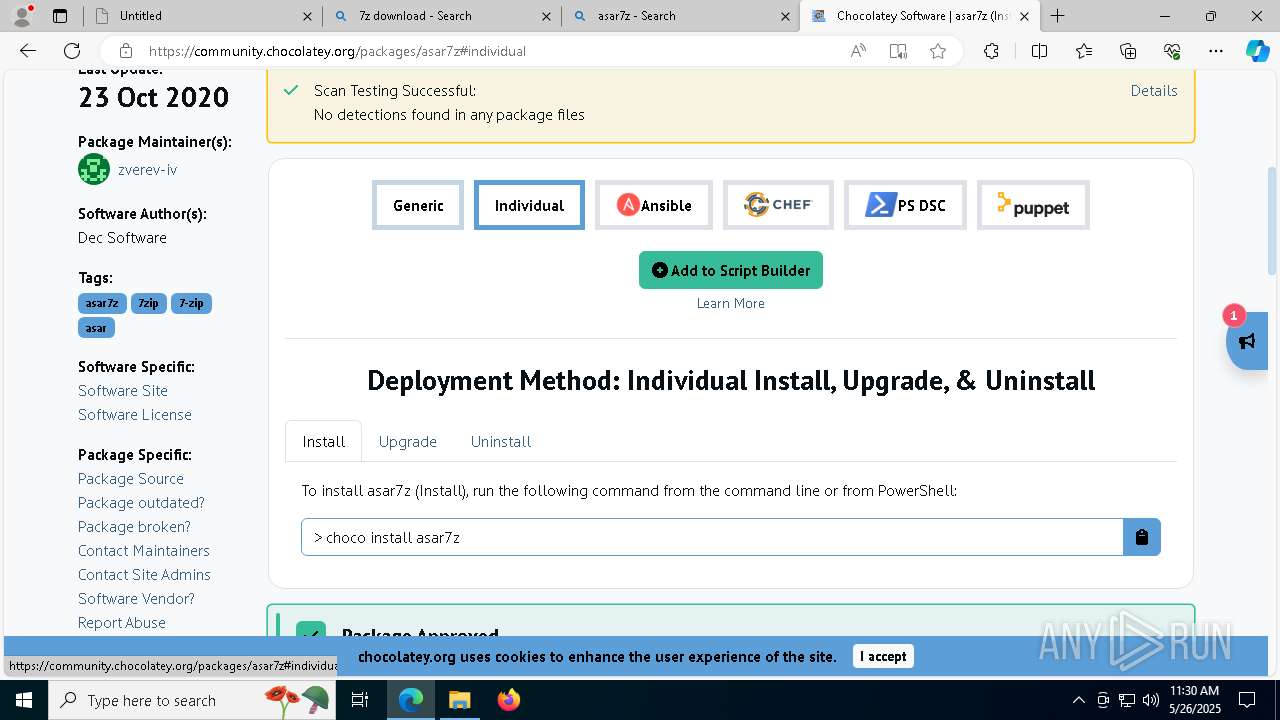
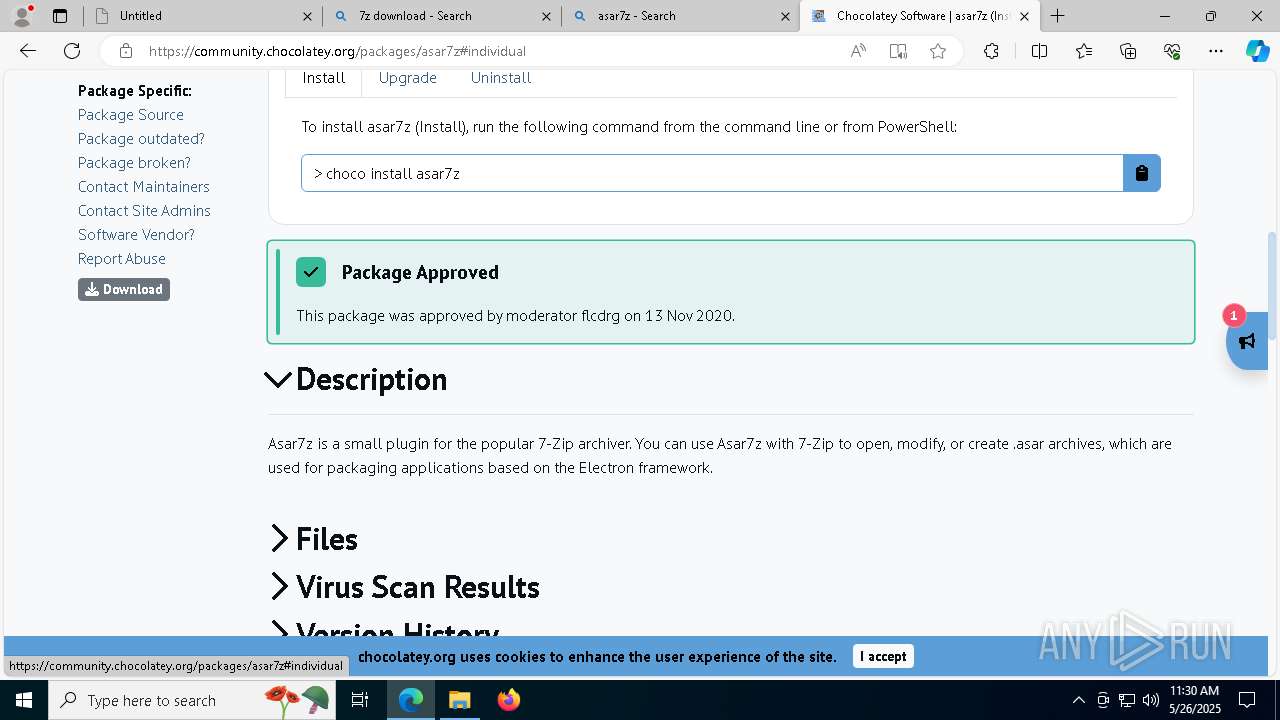
Drops 7-zip archiver for unpacking
- msedge.exe (PID: 7440)
- msedge.exe (PID: 7188)
- 7z1900-x64.exe (PID: 8288)
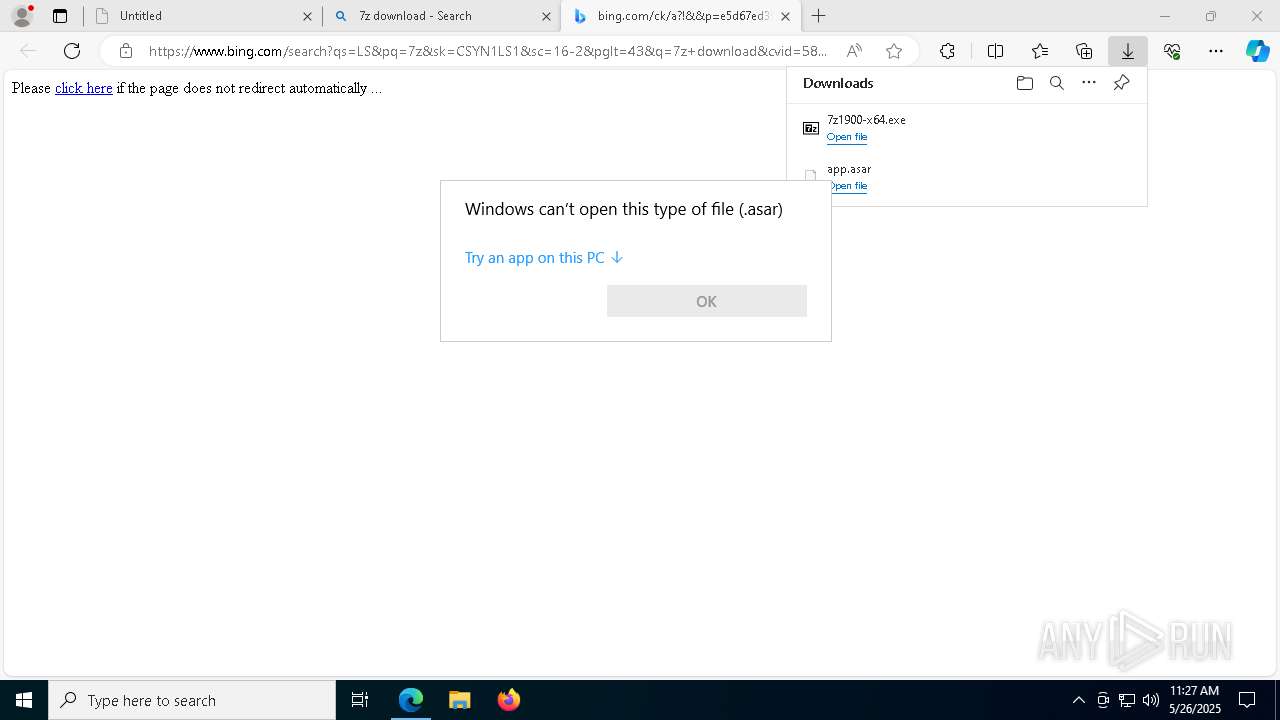
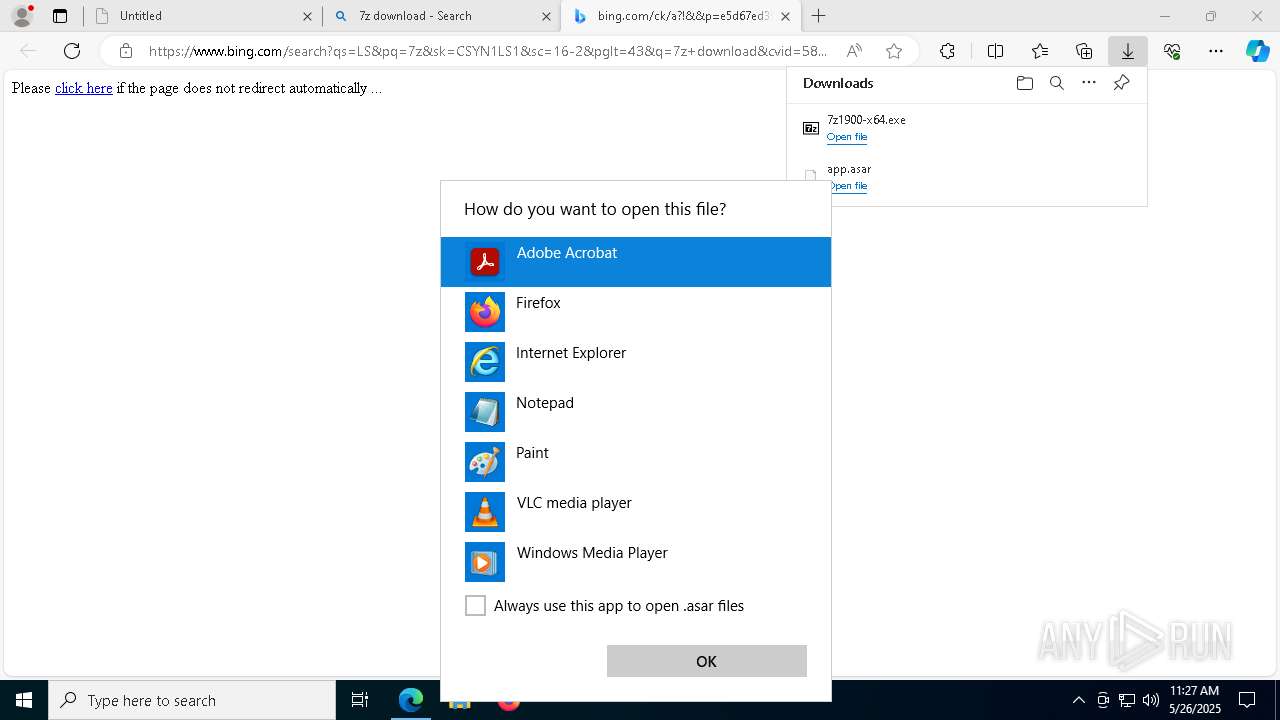
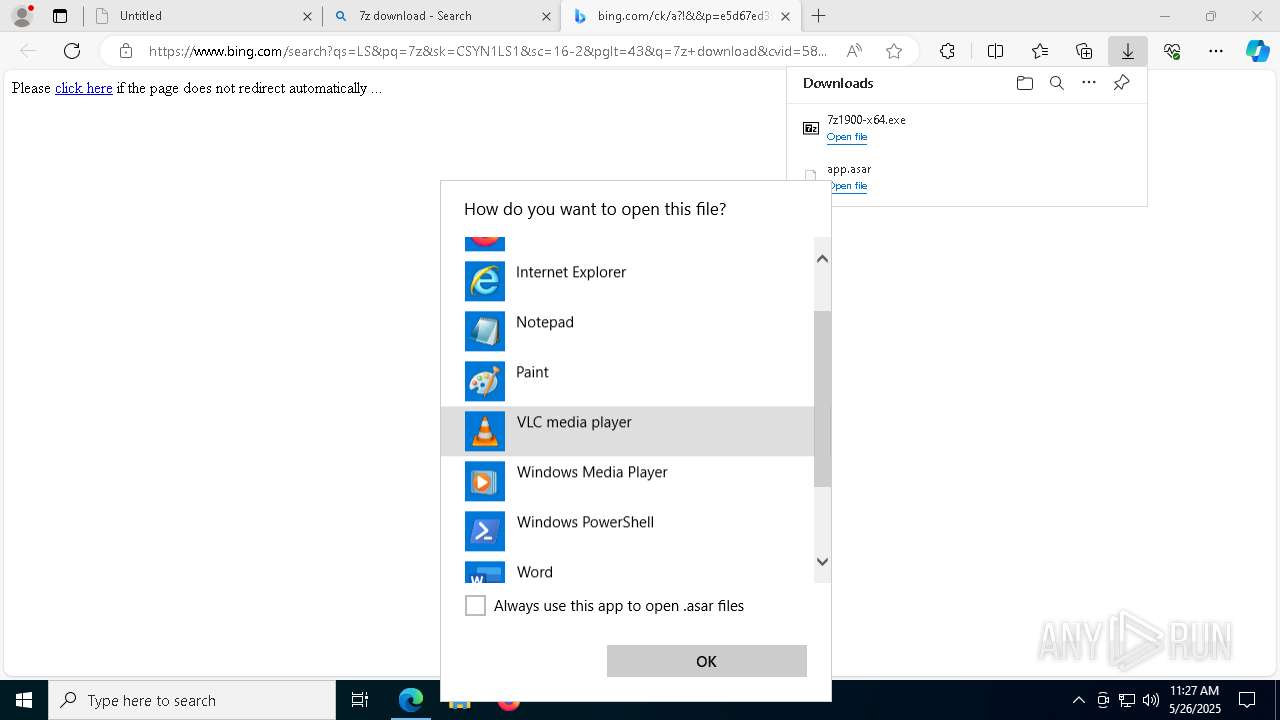
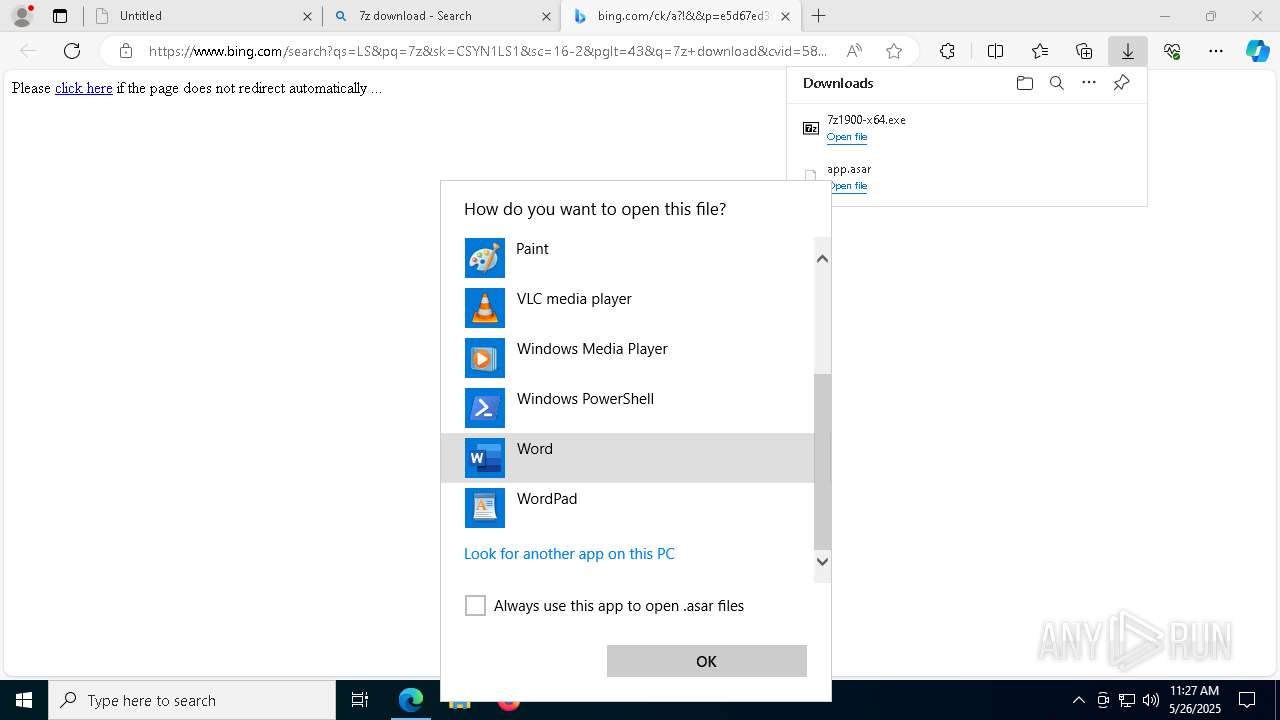
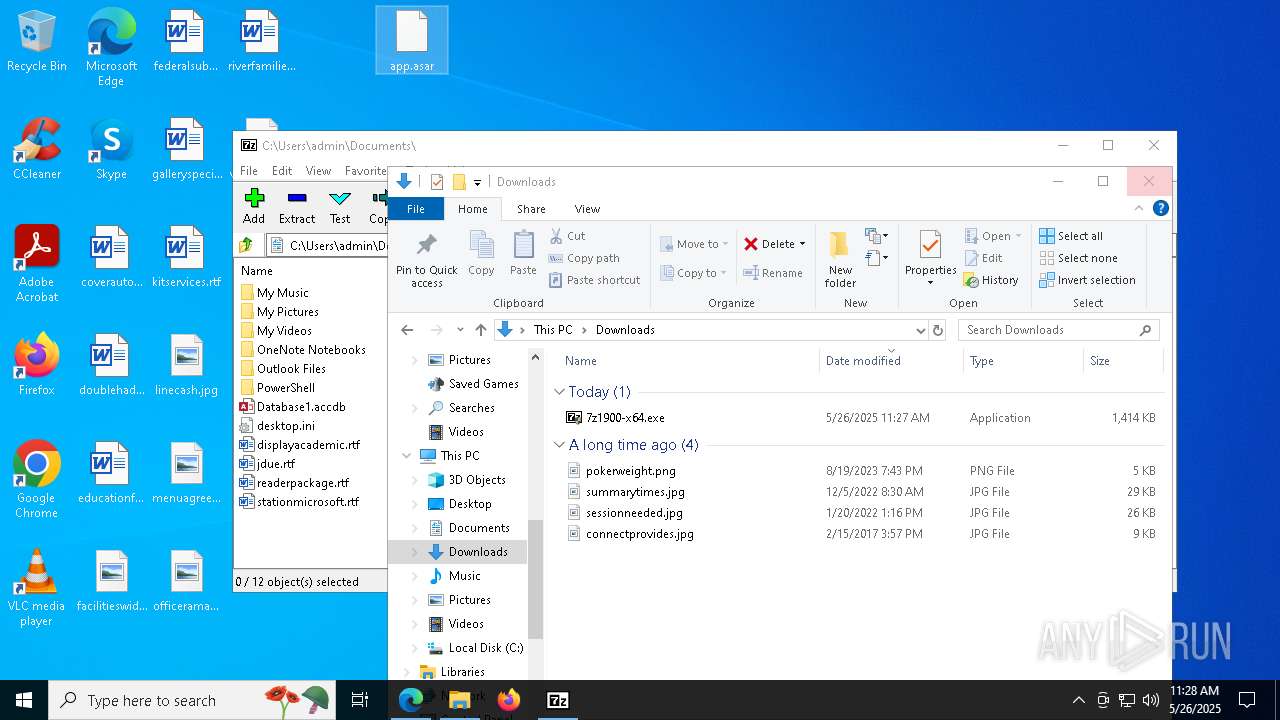
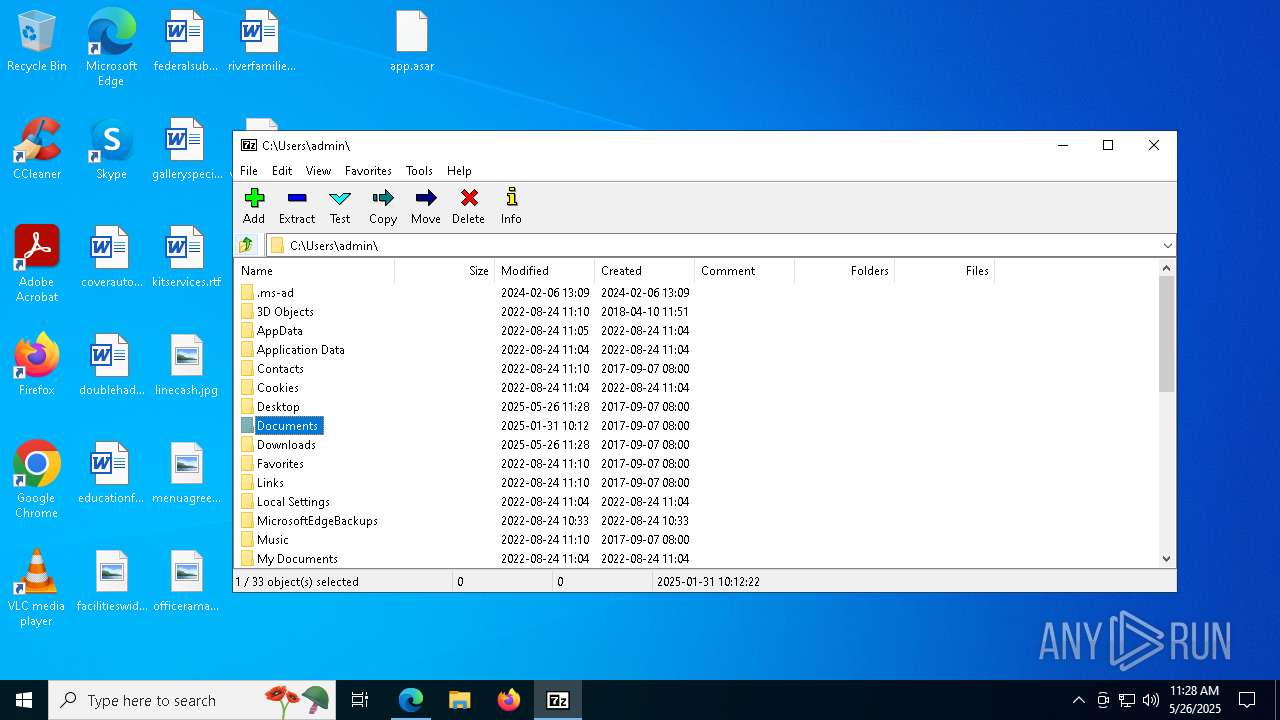
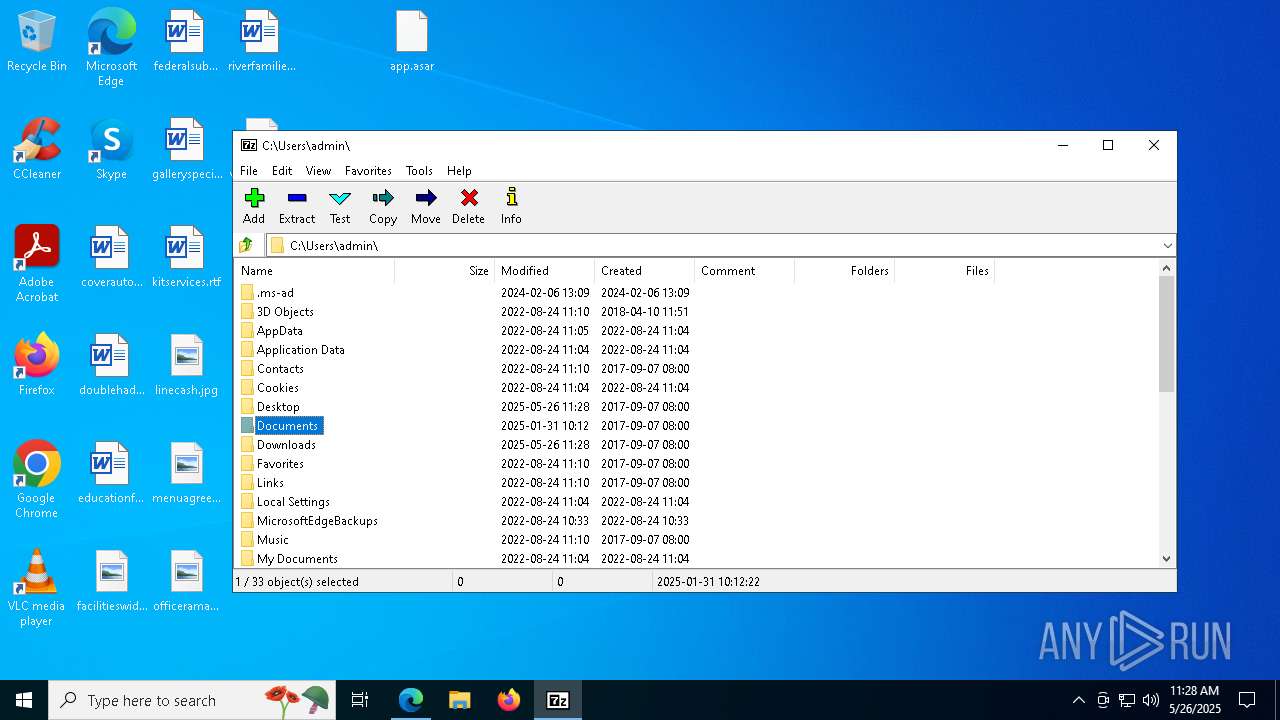
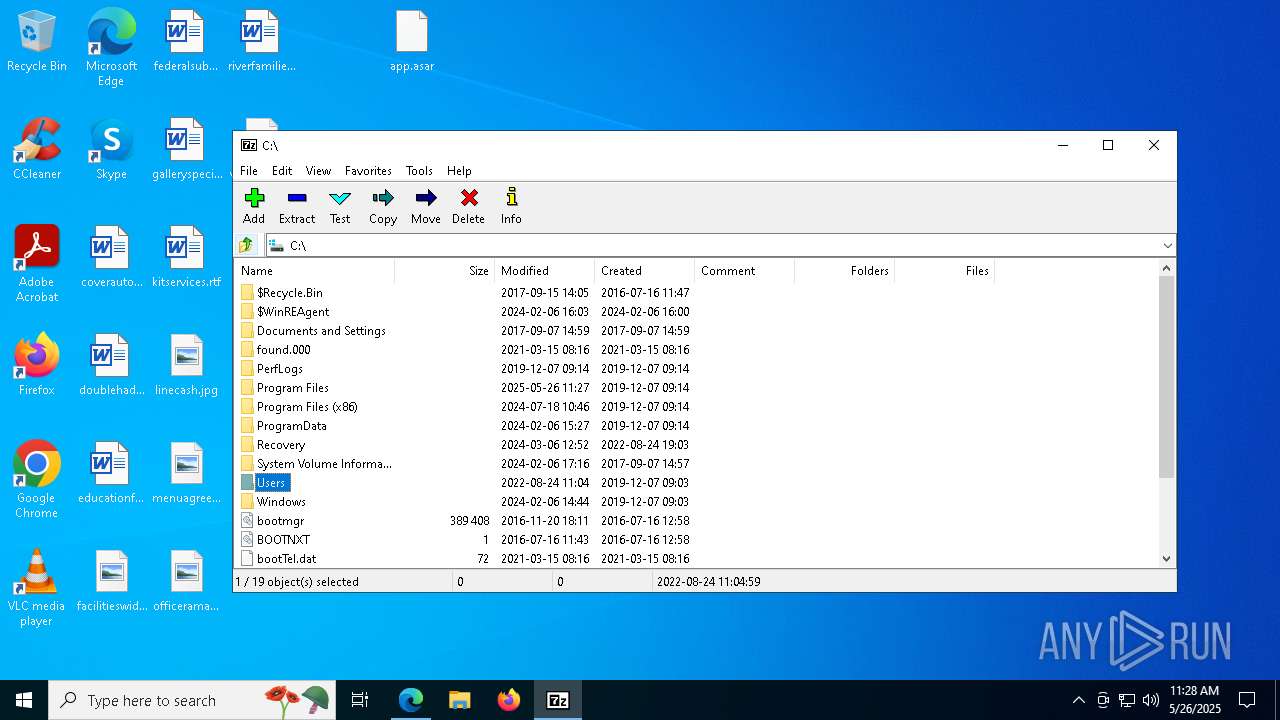
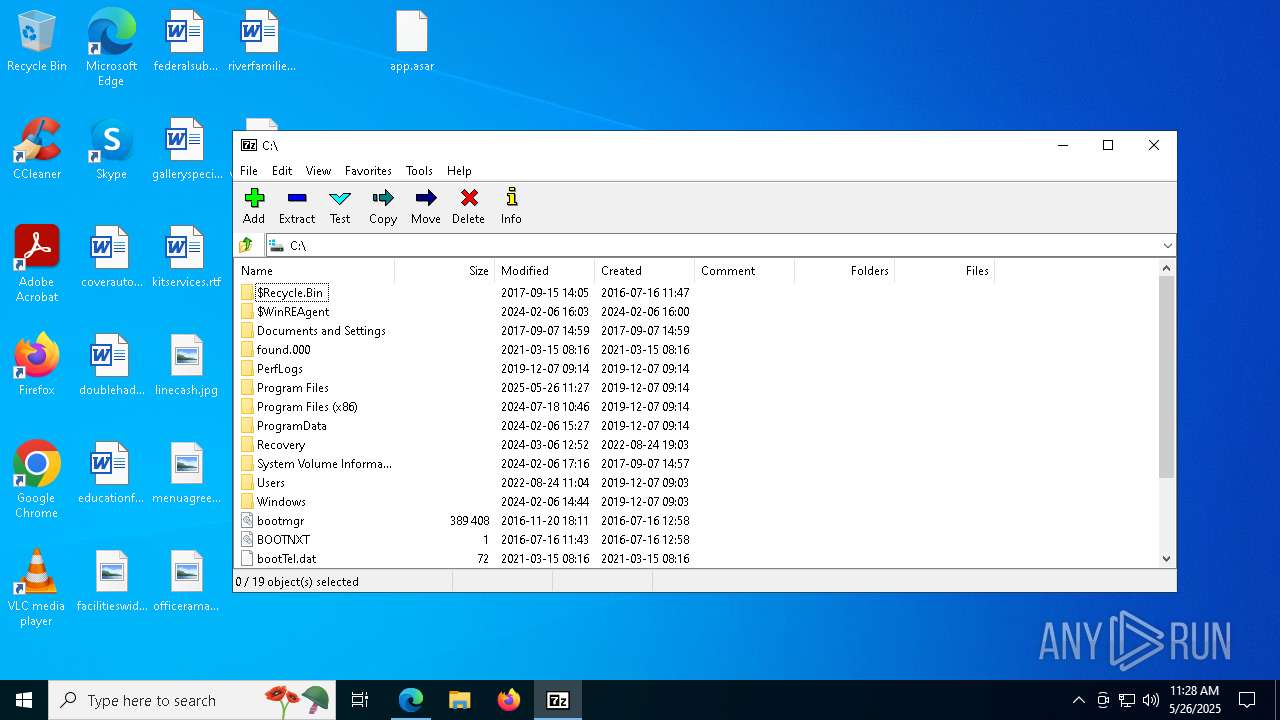
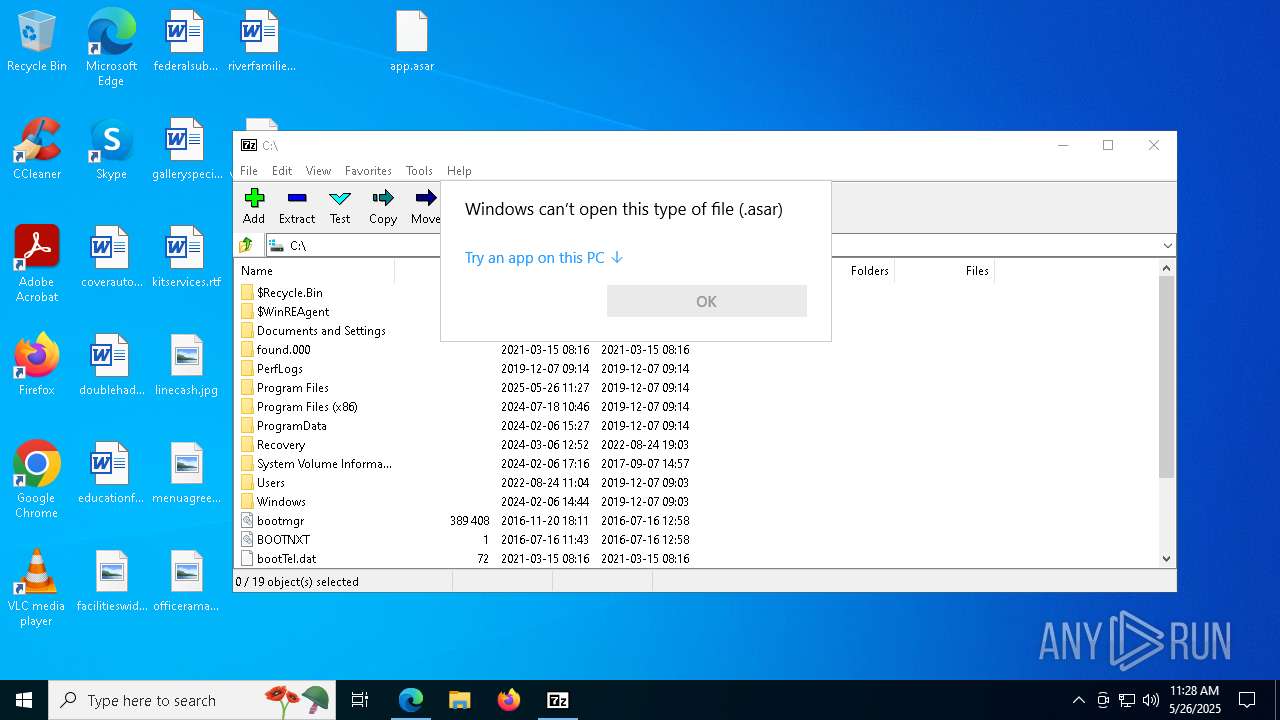
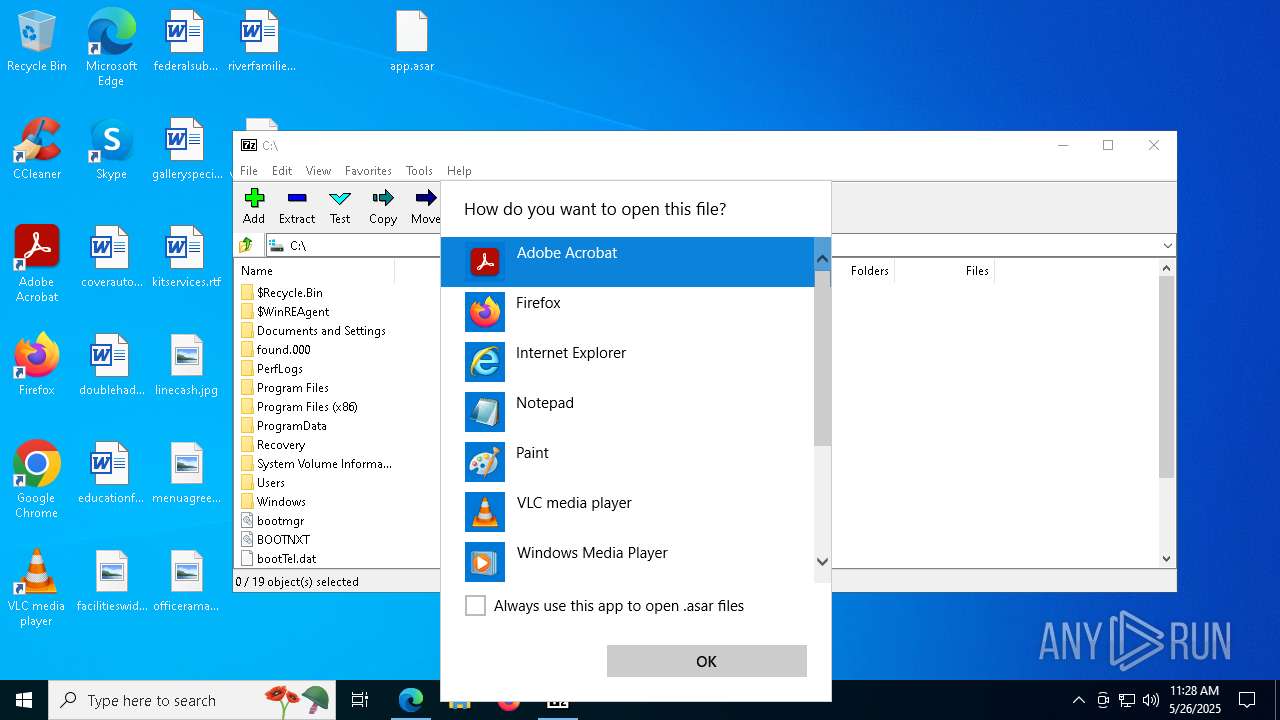
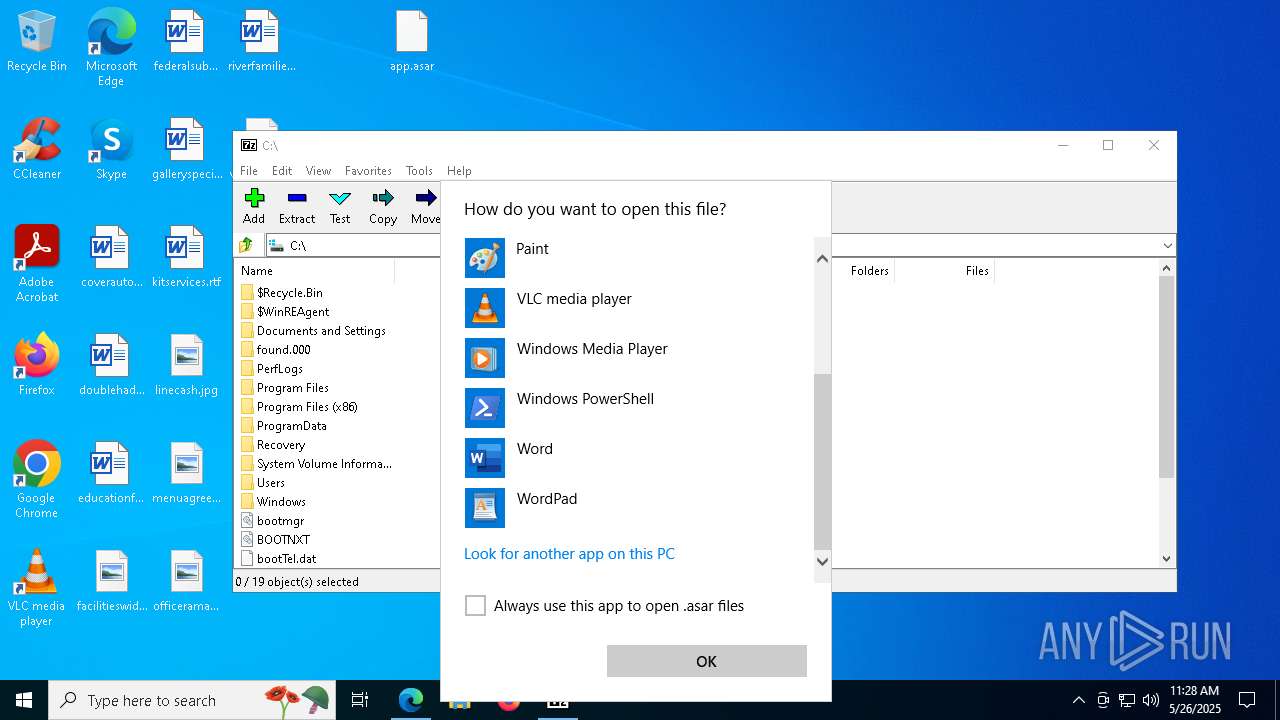
Creates file in the systems drive root
- OpenWith.exe (PID: 3032)
Creates a software uninstall entry
- 7z1900-x64.exe (PID: 8288)
Executable content was dropped or overwritten
- 7z1900-x64.exe (PID: 8288)
Creates/Modifies COM task schedule object
- 7z1900-x64.exe (PID: 8288)
INFO
Application launched itself
- msedge.exe (PID: 7188)
Reads the computer name
- identity_helper.exe (PID: 8484)
- 7z1900-x64.exe (PID: 8288)
Reads Environment values
- identity_helper.exe (PID: 8484)
Attempting to use instant messaging service
- msedge.exe (PID: 7440)
Reads Microsoft Office registry keys
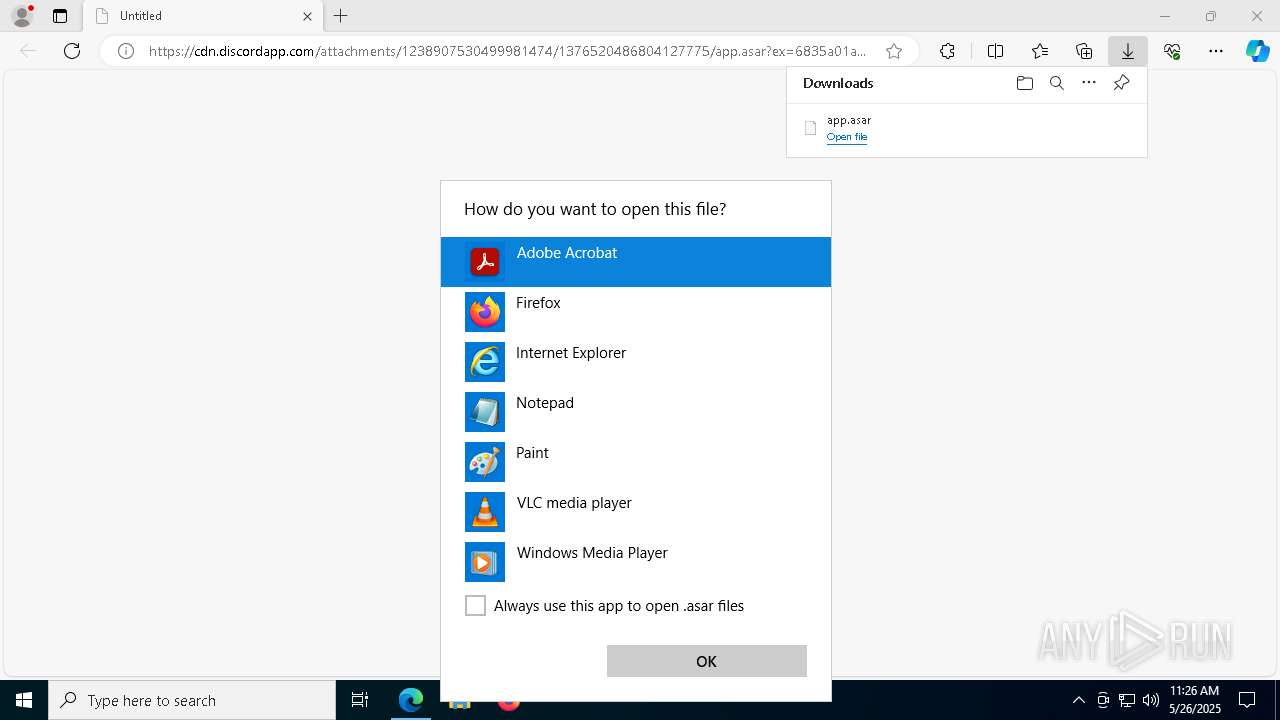
- OpenWith.exe (PID: 7944)
- OpenWith.exe (PID: 3032)
Reads the software policy settings
- slui.exe (PID: 8272)
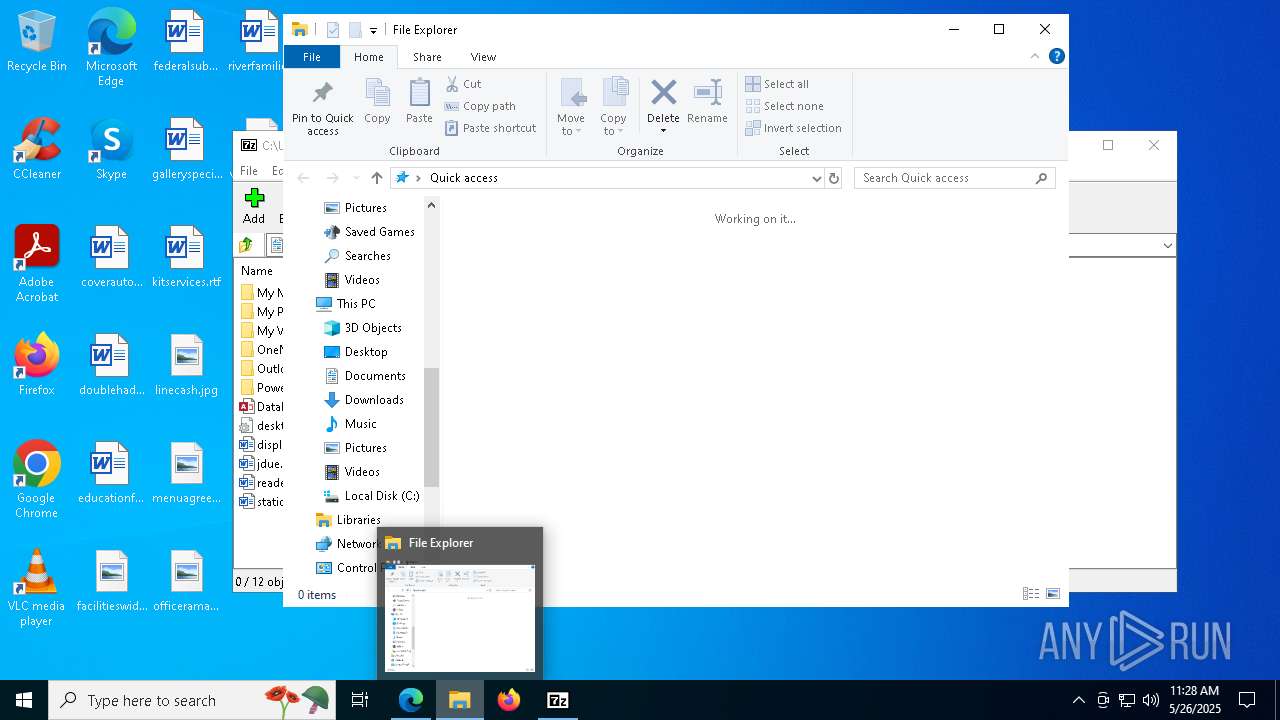
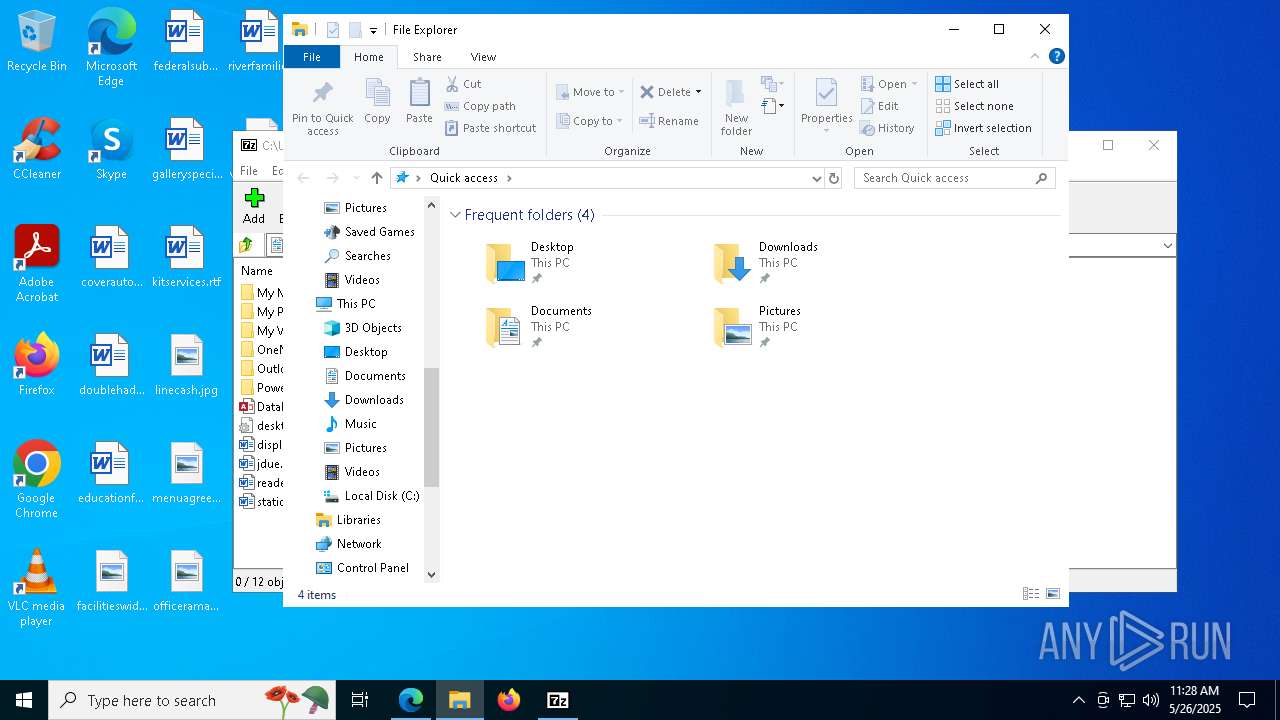
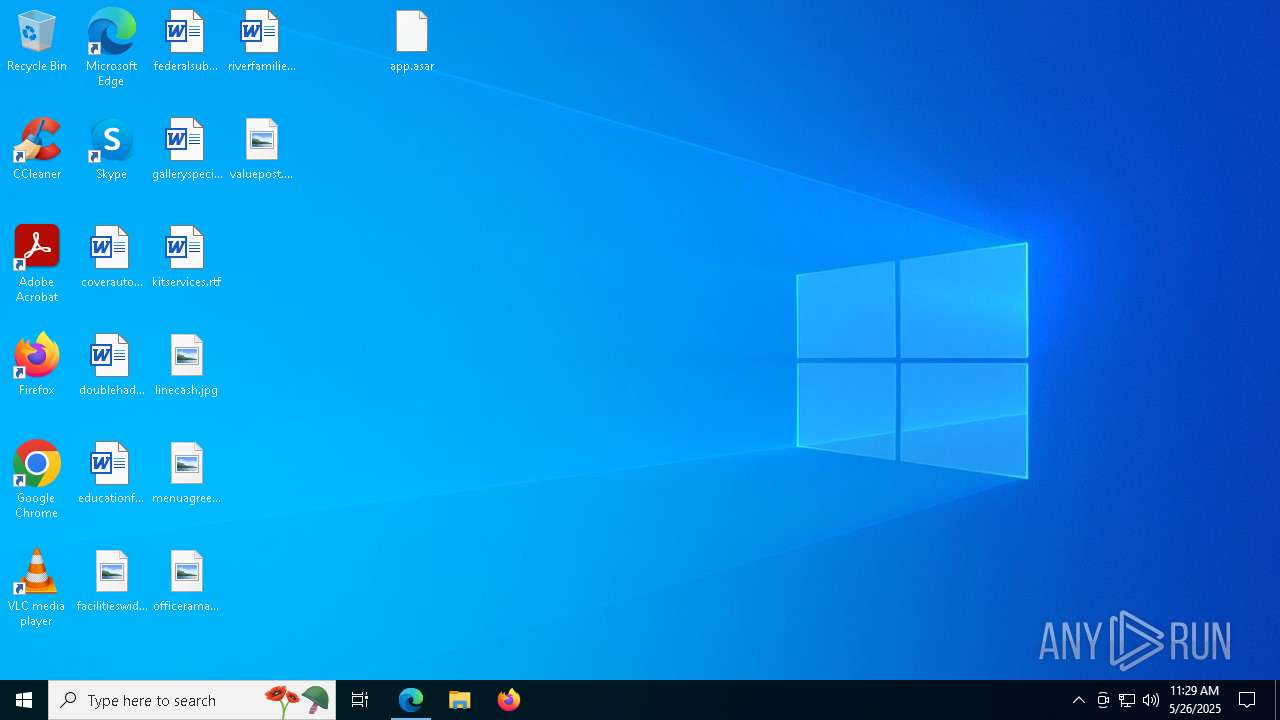
Launch of the file from Downloads directory
- msedge.exe (PID: 7188)
- msedge.exe (PID: 920)
- msedge.exe (PID: 6372)
Executable content was dropped or overwritten
- msedge.exe (PID: 7188)
- msedge.exe (PID: 7440)
The sample compiled with english language support
- msedge.exe (PID: 7440)
- msedge.exe (PID: 7188)
- 7z1900-x64.exe (PID: 8288)
Checks supported languages
- 7z1900-x64.exe (PID: 8288)
- identity_helper.exe (PID: 8484)
Creates files in the program directory
- 7z1900-x64.exe (PID: 8288)
The sample compiled with russian language support
- 7z1900-x64.exe (PID: 8288)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 3032)
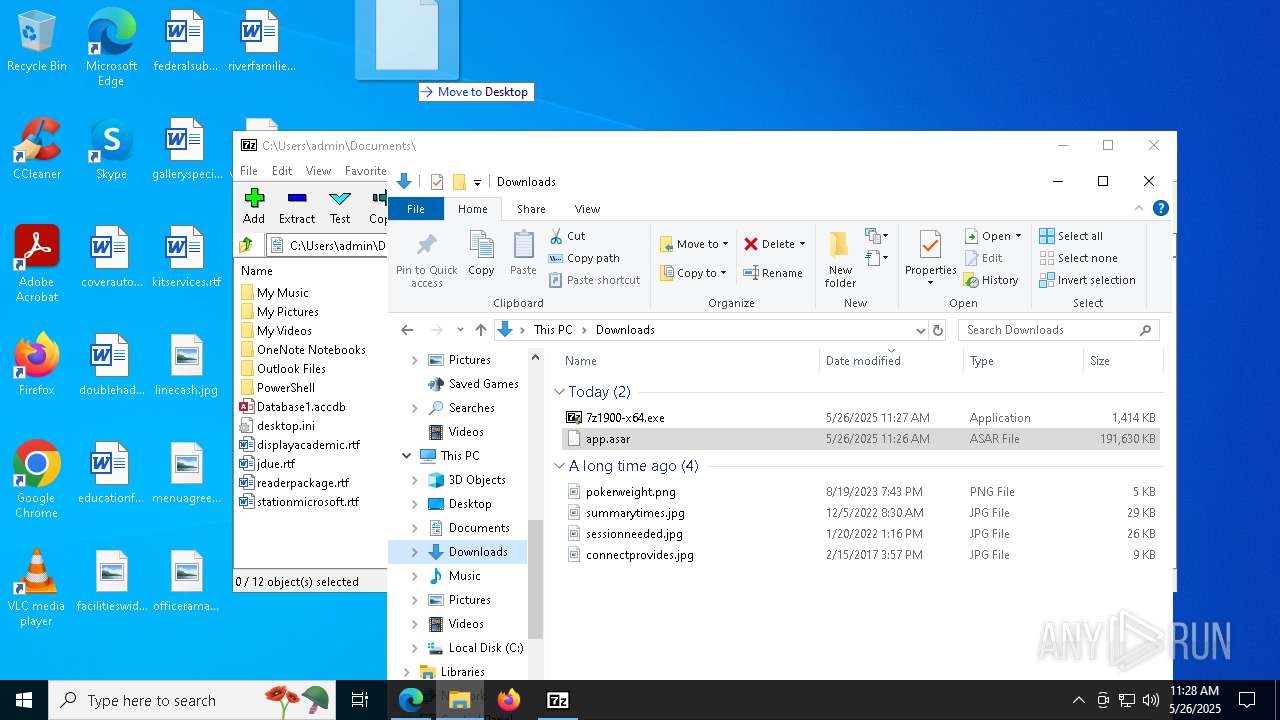
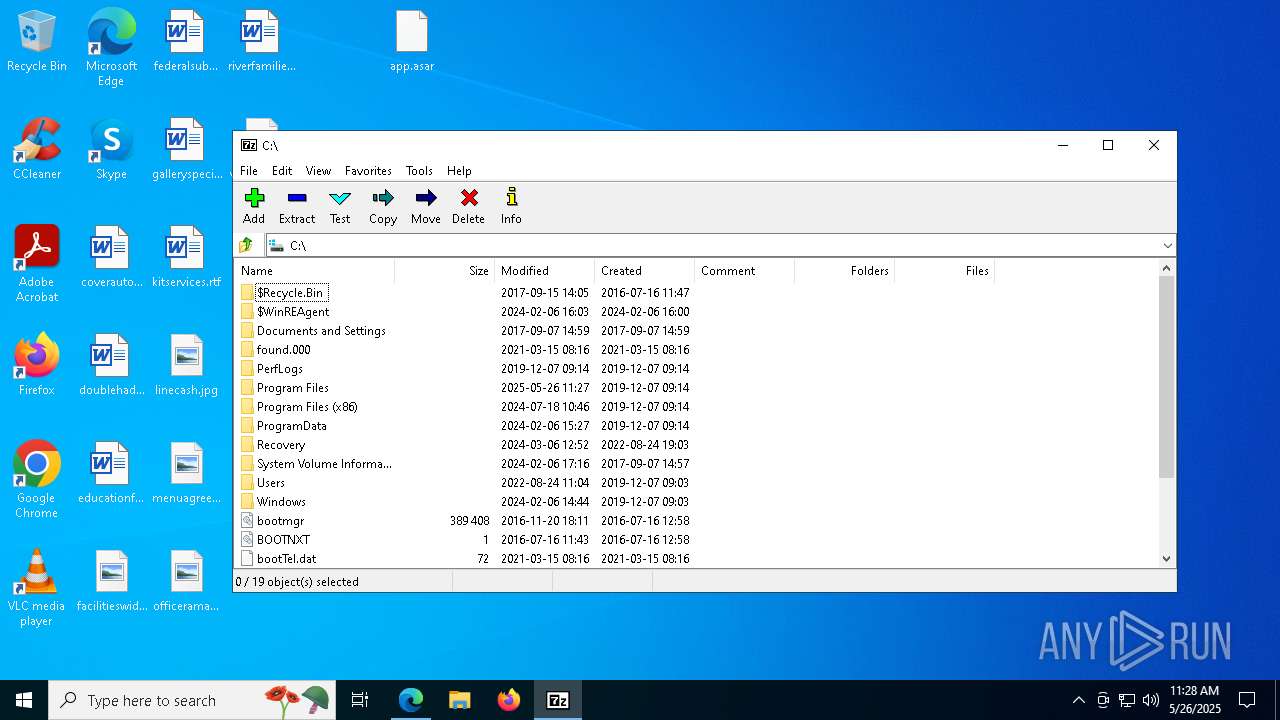
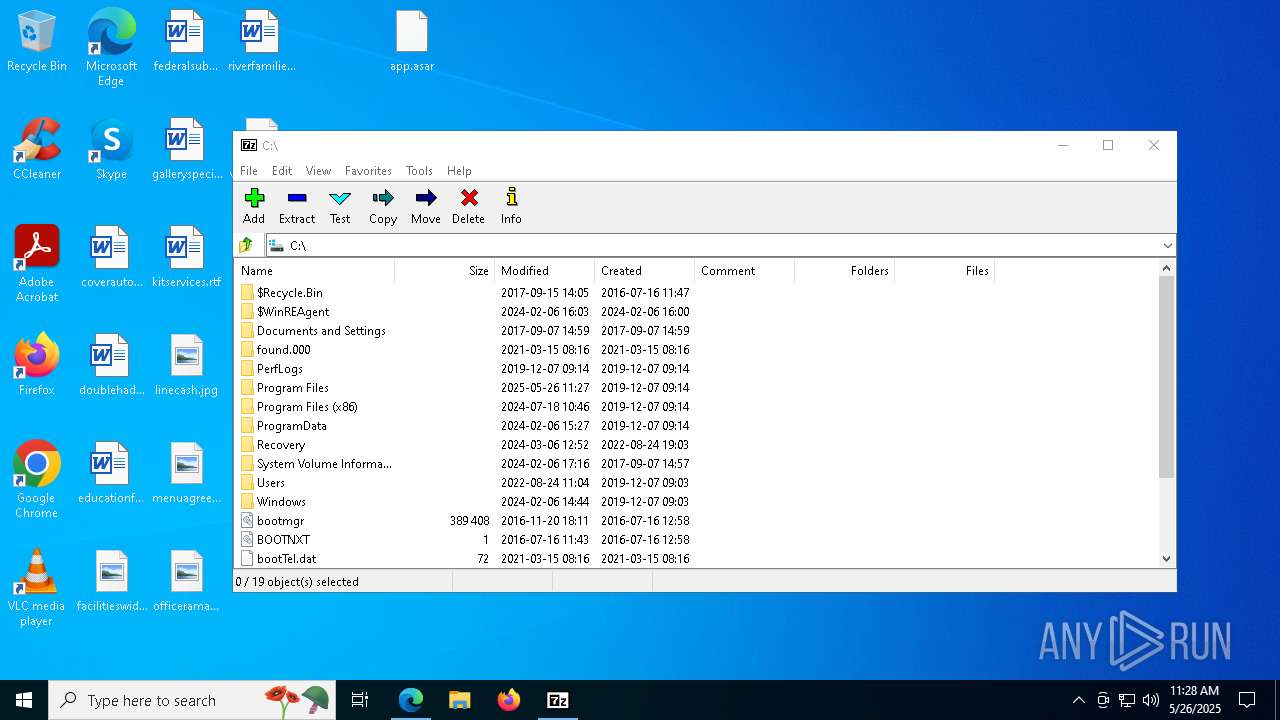
Manual execution by a user
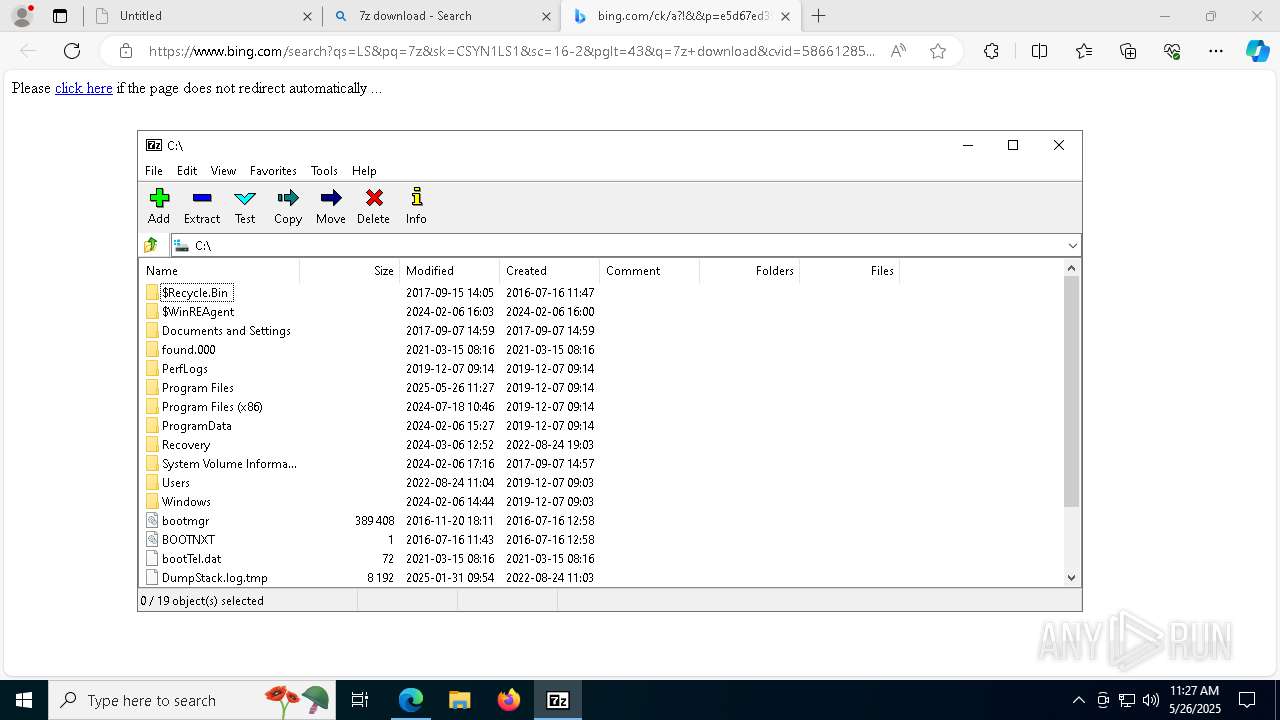
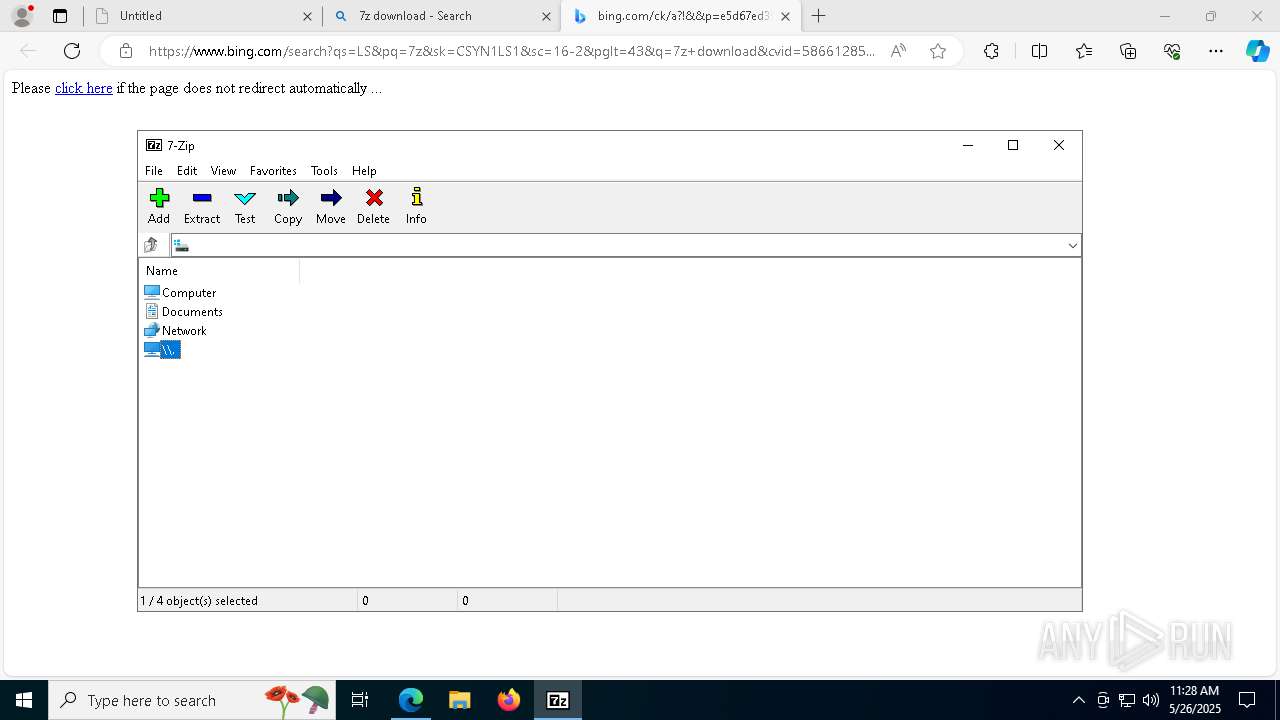
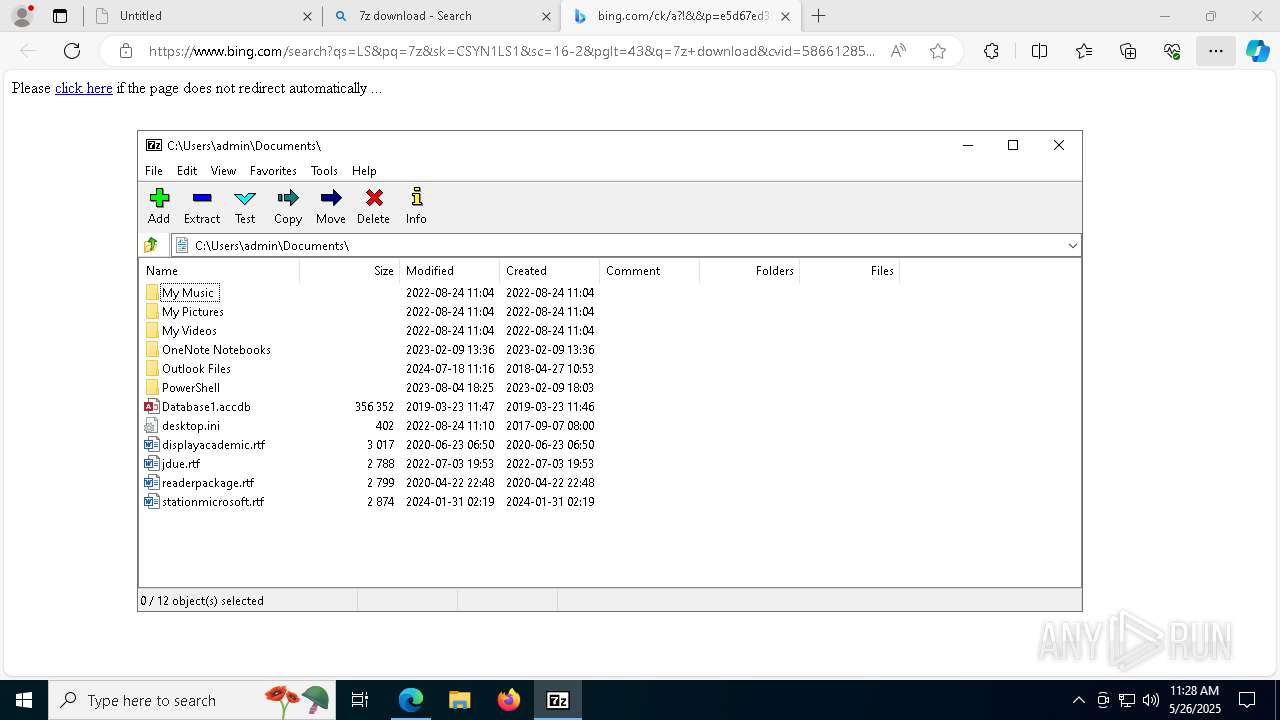
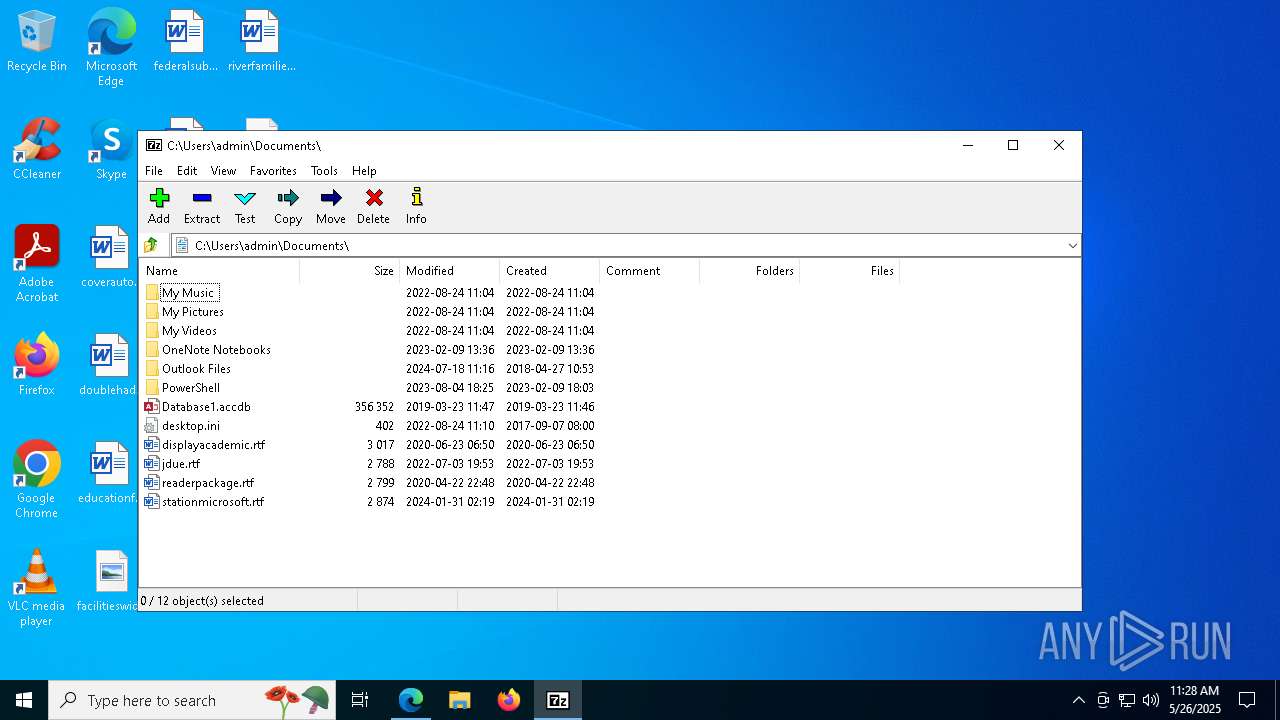
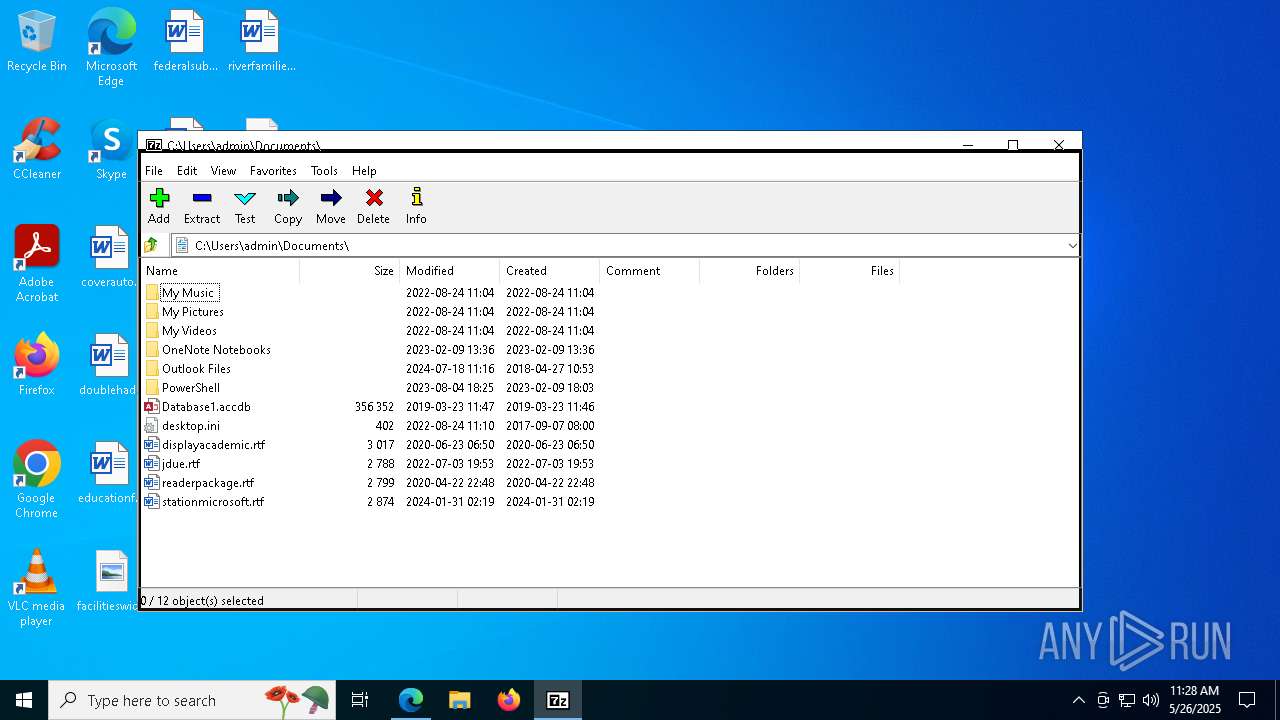
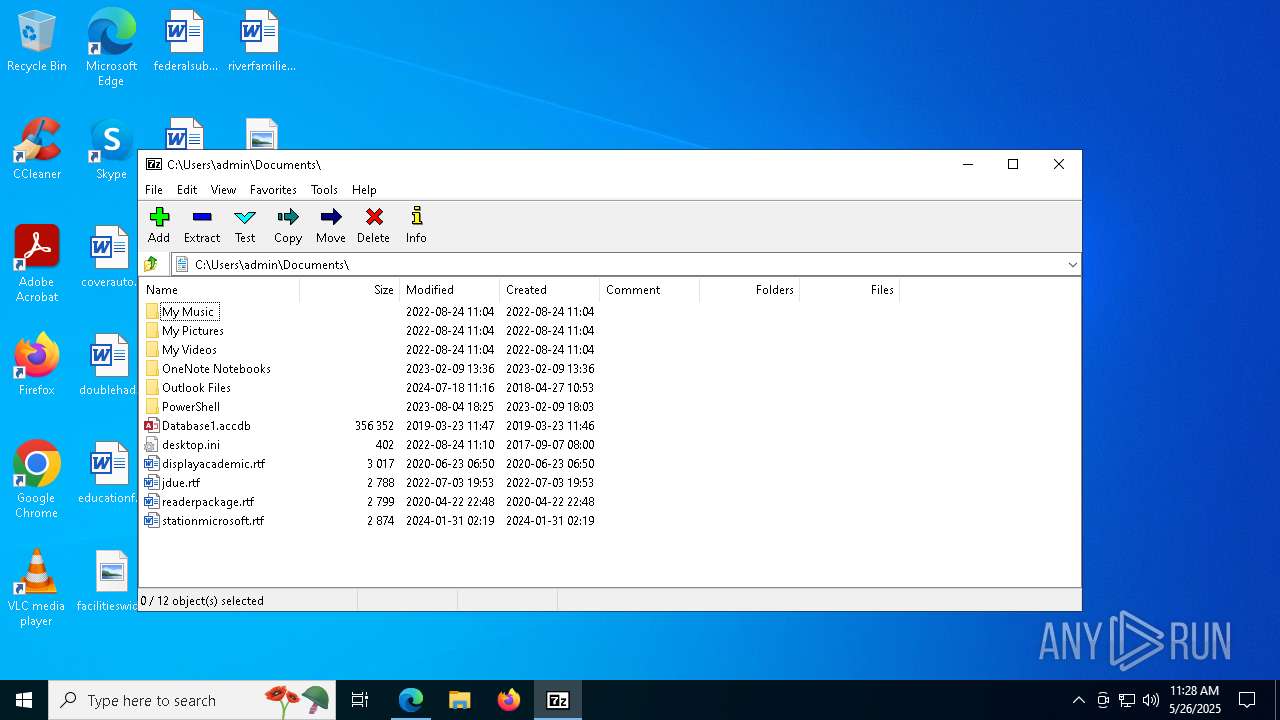
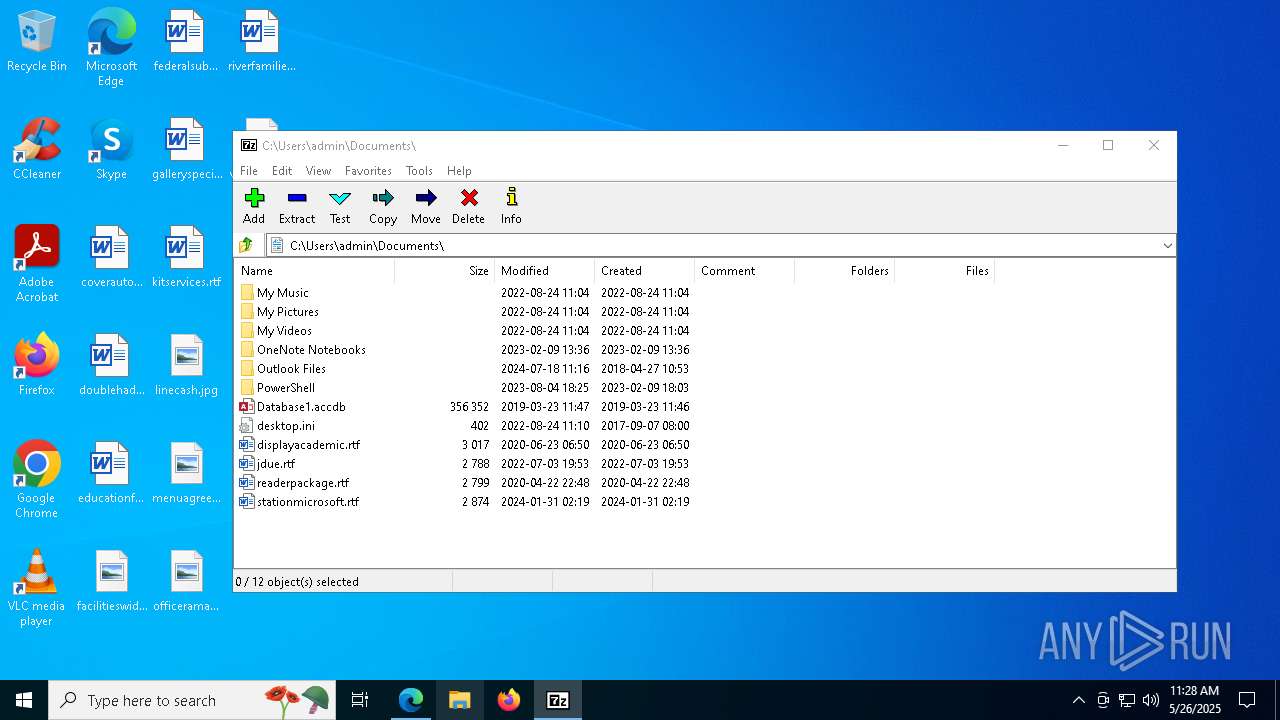
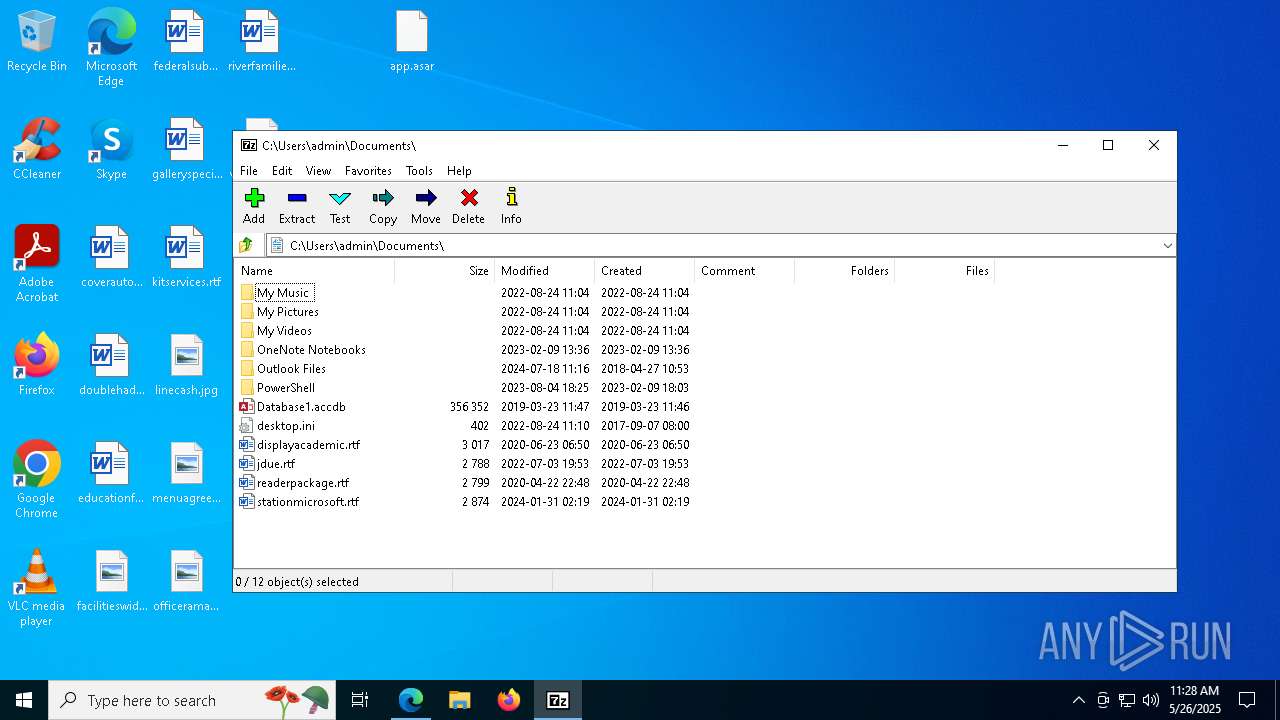
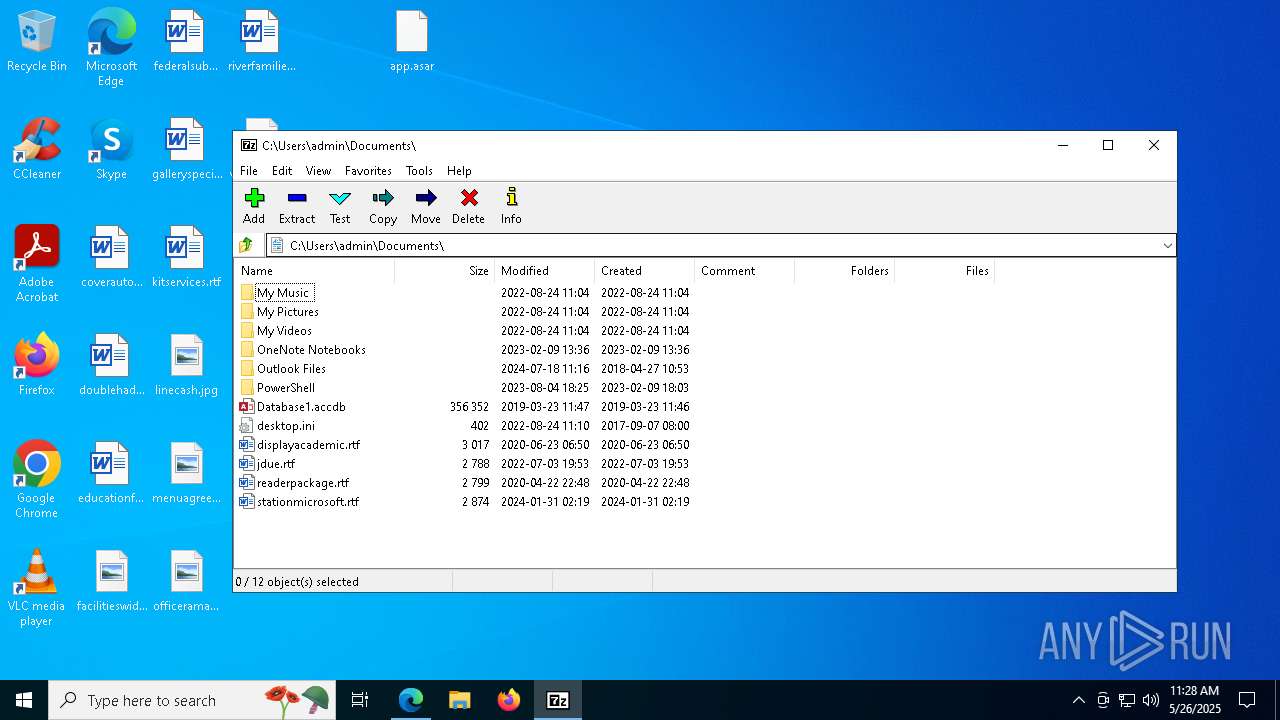
- 7zFM.exe (PID: 2084)
- 7zFM.exe (PID: 5608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
217
Monitored processes
73
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5392 --field-trial-handle=2368,i,14888433741903452362,9332379303552344365,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5800 --field-trial-handle=2368,i,14888433741903452362,9332379303552344365,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3664 --field-trial-handle=2368,i,14888433741903452362,9332379303552344365,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7828 --field-trial-handle=2368,i,14888433741903452362,9332379303552344365,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=5456 --field-trial-handle=2368,i,14888433741903452362,9332379303552344365,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6944 --field-trial-handle=2368,i,14888433741903452362,9332379303552344365,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\7-Zip\7zFM.exe" C:\Users\admin\Desktop\app.asar | C:\Program Files\7-Zip\7zFM.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 2908 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cdn.discordapp.com/attachments/1238907530499981474/1376520486804127775/app.asar?ex=6835a01a&is=68344e9a&hm=0b4ff8f67f4ac814f692e8f3a86f36bbcdcaec5b5346e4ab1586c0759fcb85a4&" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 080
Read events
14 962
Write events
117
Delete events
1
Modification events
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
51
Suspicious files
733
Text files
246
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b8c3.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b8c3.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b8c3.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b8d2.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b8d2.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
171
DNS requests
184
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8800 | svchost.exe | GET | 206 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305172&P2=404&P3=2&P4=Aii3Ru%2fTGJOjvipyv08yFbv3EsZUIW%2fc1KqSPloHfisKEzC0fKaUmrN%2bexI8ZS26%2bA64ASYsGt%2bxjf%2bj9xN41g%3d%3d | unknown | — | — | whitelisted |
8800 | svchost.exe | HEAD | 200 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305172&P2=404&P3=2&P4=Aii3Ru%2fTGJOjvipyv08yFbv3EsZUIW%2fc1KqSPloHfisKEzC0fKaUmrN%2bexI8ZS26%2bA64ASYsGt%2bxjf%2bj9xN41g%3d%3d | unknown | — | — | whitelisted |
8800 | svchost.exe | GET | 206 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305172&P2=404&P3=2&P4=Aii3Ru%2fTGJOjvipyv08yFbv3EsZUIW%2fc1KqSPloHfisKEzC0fKaUmrN%2bexI8ZS26%2bA64ASYsGt%2bxjf%2bj9xN41g%3d%3d | unknown | — | — | whitelisted |
5776 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5776 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8800 | svchost.exe | GET | 206 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305172&P2=404&P3=2&P4=Aii3Ru%2fTGJOjvipyv08yFbv3EsZUIW%2fc1KqSPloHfisKEzC0fKaUmrN%2bexI8ZS26%2bA64ASYsGt%2bxjf%2bj9xN41g%3d%3d | unknown | — | — | whitelisted |
8800 | svchost.exe | GET | 206 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305172&P2=404&P3=2&P4=Aii3Ru%2fTGJOjvipyv08yFbv3EsZUIW%2fc1KqSPloHfisKEzC0fKaUmrN%2bexI8ZS26%2bA64ASYsGt%2bxjf%2bj9xN41g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7440 | msedge.exe | 162.159.133.233:443 | cdn.discordapp.com | — | — | whitelisted |
7440 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7188 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7440 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
cdn.discordapp.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7440 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7440 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7440 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |