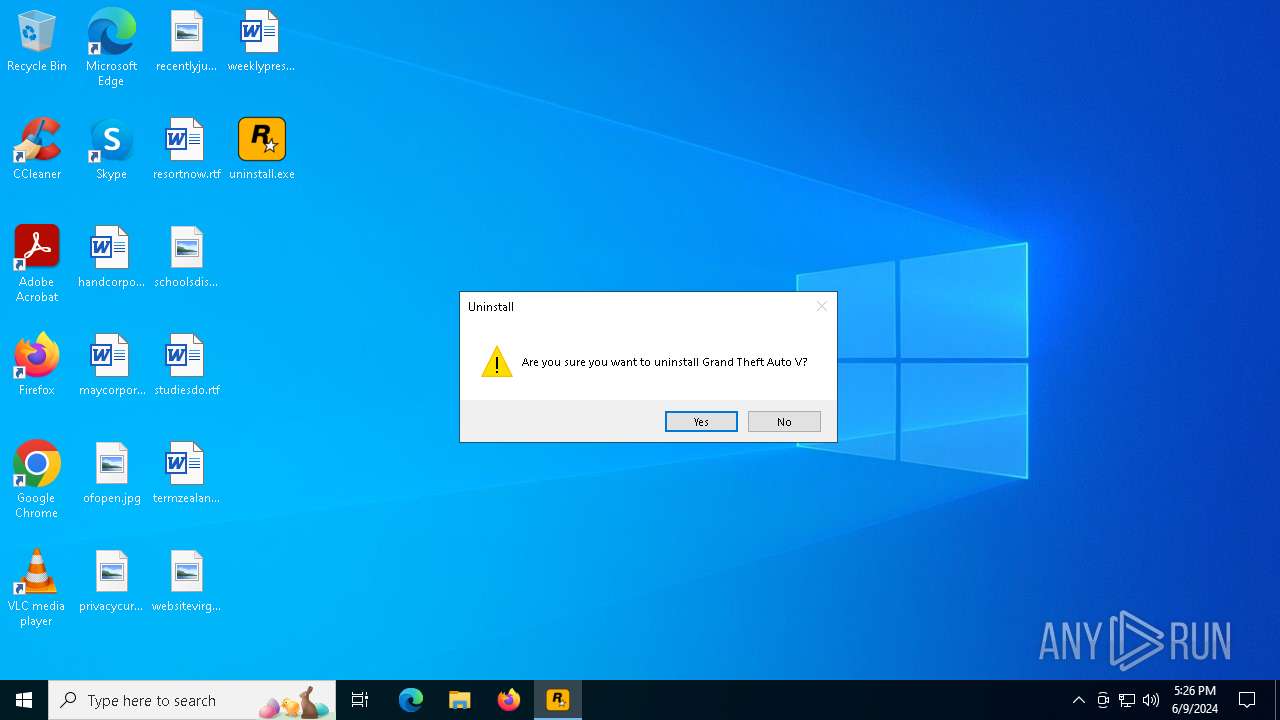
| File name: | uninstall.exe |
| Full analysis: | https://app.any.run/tasks/db59ef7f-0791-47cd-a476-cd27c341ca2e |
| Verdict: | Malicious activity |
| Analysis date: | June 09, 2024, 17:25:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | FF20D634CC7479FD5B2CD00D1CBFB02D |
| SHA1: | 900AF90BE9D6814A4645886A92E13CF7E1338809 |
| SHA256: | AE9DC0082544860CA710944CC82A95871B56B7D81FE3AEDB968EB2B9B69CF680 |
| SSDEEP: | 6144:naqoXHvQHHE7/h9oMqQPwr/2Zv4NnMKY2ptD:naqofQHIHoMqQPdZQNnxtD |
MALICIOUS
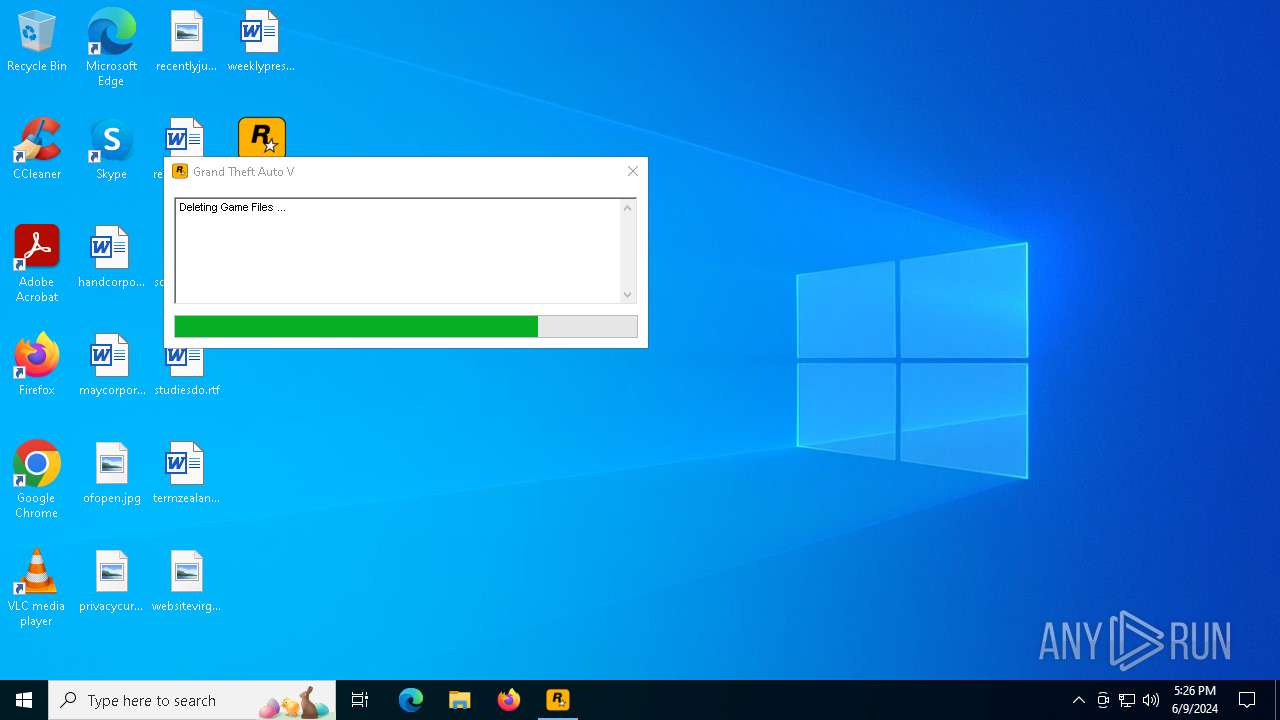
Drops the executable file immediately after the start
- uninstall.exe (PID: 6284)
Starts CMD.EXE for self-deleting
- uninstall.exe (PID: 6372)
SUSPICIOUS
Reads security settings of Internet Explorer
- uninstall.exe (PID: 6284)
Reads the date of Windows installation
- uninstall.exe (PID: 6284)
Application launched itself
- uninstall.exe (PID: 6284)
Starts CMD.EXE for commands execution
- uninstall.exe (PID: 6372)
The process deletes folder without confirmation
- uninstall.exe (PID: 6372)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6564)
Hides command output
- cmd.exe (PID: 6564)
INFO
Checks supported languages
- uninstall.exe (PID: 6284)
- uninstall.exe (PID: 6372)
Process checks whether UAC notifications are on
- uninstall.exe (PID: 6284)
Reads the computer name
- uninstall.exe (PID: 6284)
- uninstall.exe (PID: 6372)
Process checks computer location settings
- uninstall.exe (PID: 6284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:01:08 12:53:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.34 |
| CodeSize: | 104960 |
| InitializedDataSize: | 524800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x190fc |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Rockstar Games |
| FileDescription: | Rockstar Games Launcher Redirector |
| FileVersion: | 1.0.0.0 |
| InternalName: | RockstarRedirector.exe |
| LegalCopyright: | Rockstar Games Inc. (C) 2005-2019 Take Two Interactive. All rights reserved. |
| OriginalFileName: | RockstarRedirector.exe |
| ProductName: | Rockstar Games Launcher Redirector |
| ProductVersion: | 1.0.0.0 |
Total processes
121
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6284 | "C:\Users\admin\Desktop\uninstall.exe" | C:\Users\admin\Desktop\uninstall.exe | — | explorer.exe | |||||||||||
User: admin Company: Rockstar Games Integrity Level: MEDIUM Description: Rockstar Games Launcher Redirector Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6372 | "C:\Users\admin\Desktop\uninstall.exe" | C:\Users\admin\Desktop\uninstall.exe | uninstall.exe | ||||||||||||
User: admin Company: Rockstar Games Integrity Level: HIGH Description: Rockstar Games Launcher Redirector Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6564 | cmd.exe /C ping 127.0.0.1 -n 5 -w 1000 > Nul & Del /f /q "C:\Users\admin\Desktop\uninstall.exe" & cd .. & rmdir /q "C:\Users\admin\Desktop" | C:\Windows\System32\cmd.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6624 | ping 127.0.0.1 -n 5 -w 1000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
891
Read events
882
Write events
9
Delete events
0
Modification events
| (PID) Process: | (6284) uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6284) uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6284) uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6284) uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6372) uninstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\Desktop\uninstall.exe | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5608 | RUXIMICS.exe | GET | 200 | 2.19.122.202:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.19.122.202:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5608 | RUXIMICS.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | POST | 200 | 51.11.192.48:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5380 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5608 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5608 | RUXIMICS.exe | 2.19.122.202:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 2.19.122.202:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5608 | RUXIMICS.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
5140 | MoUsoCoreWorker.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5456 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |