| File name: | CompatTelRunner.exe |
| Full analysis: | https://app.any.run/tasks/5473351f-85ce-4ccf-b656-505d4ec97901 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2025, 20:31:13 |
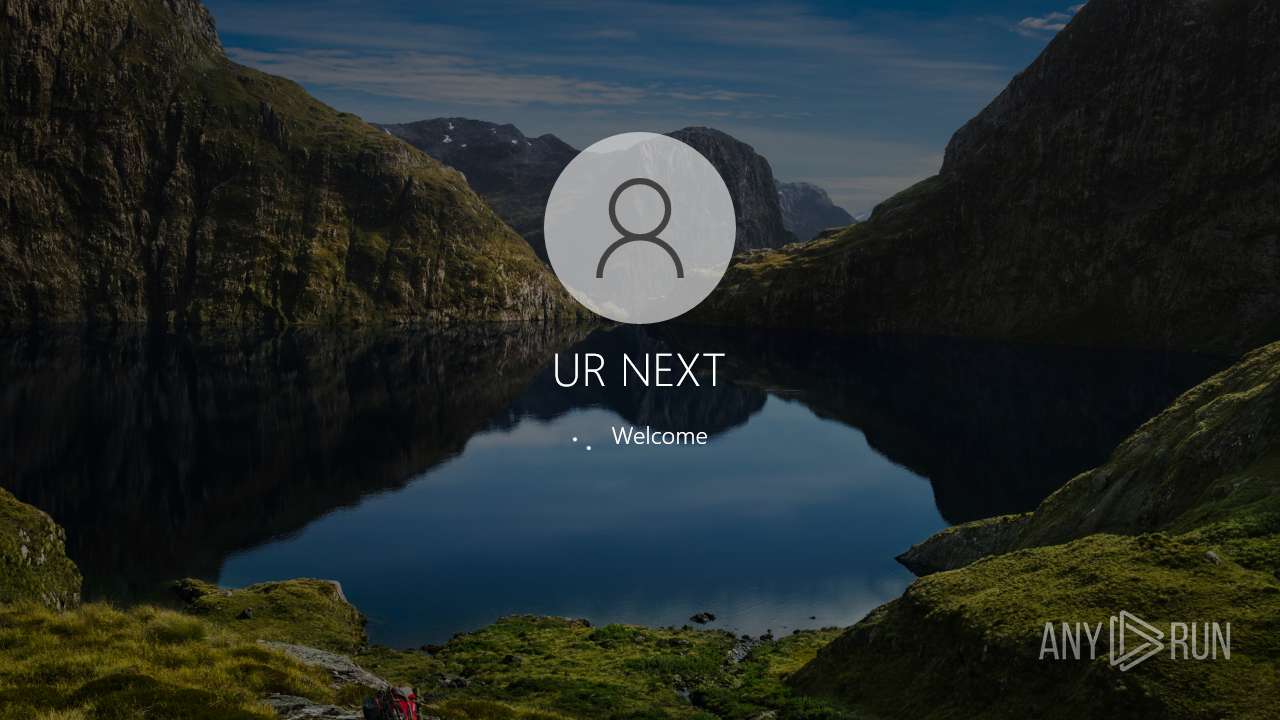
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | FD6FEAEE9FCE7FB12B47EC0578F20570 |
| SHA1: | E268F2A2C61EDDDC0C3B549953DF47E199AD301B |
| SHA256: | AE872001B1389392EB4758832D95FA9707018A26FFEF6F8685B180049AA20106 |
| SSDEEP: | 6144:ffEmsOnkCnaTgKdJXWCDQRBlYUpfDGWMaYzkSboPGalPC:ffEmsOnkBgKdJXWCDQRBlY6MaYgGahC |
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 7548)
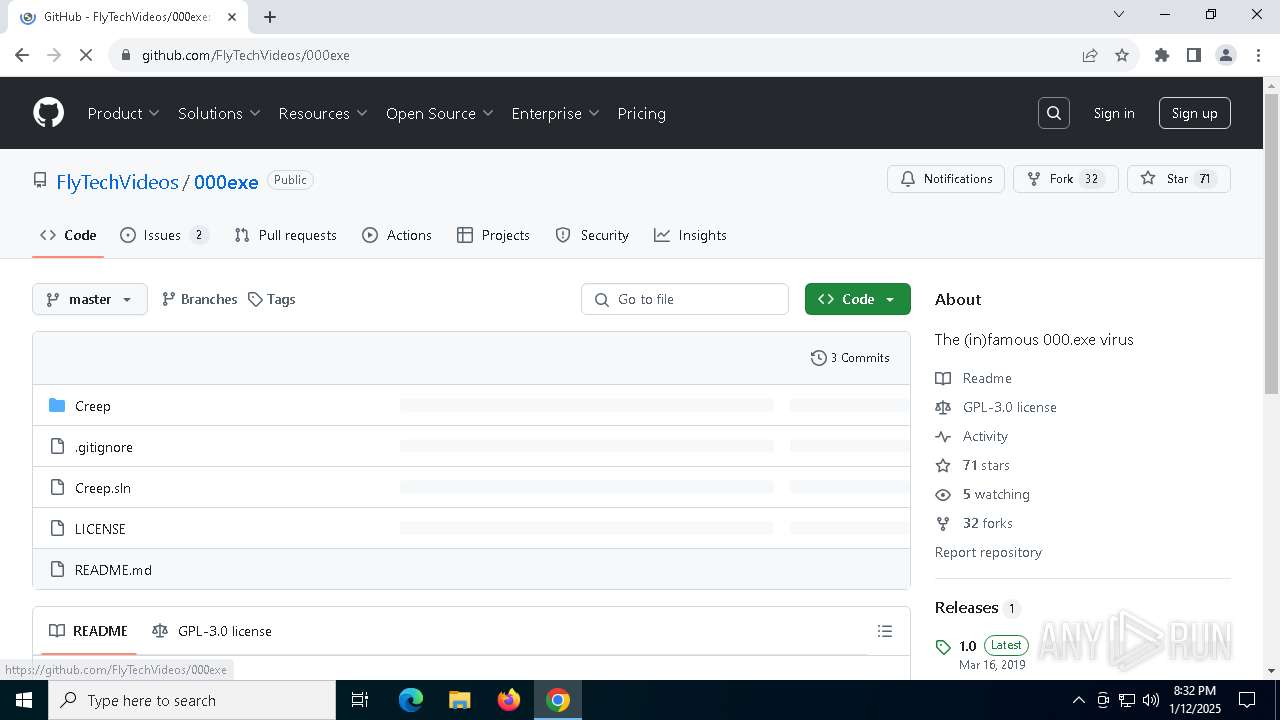
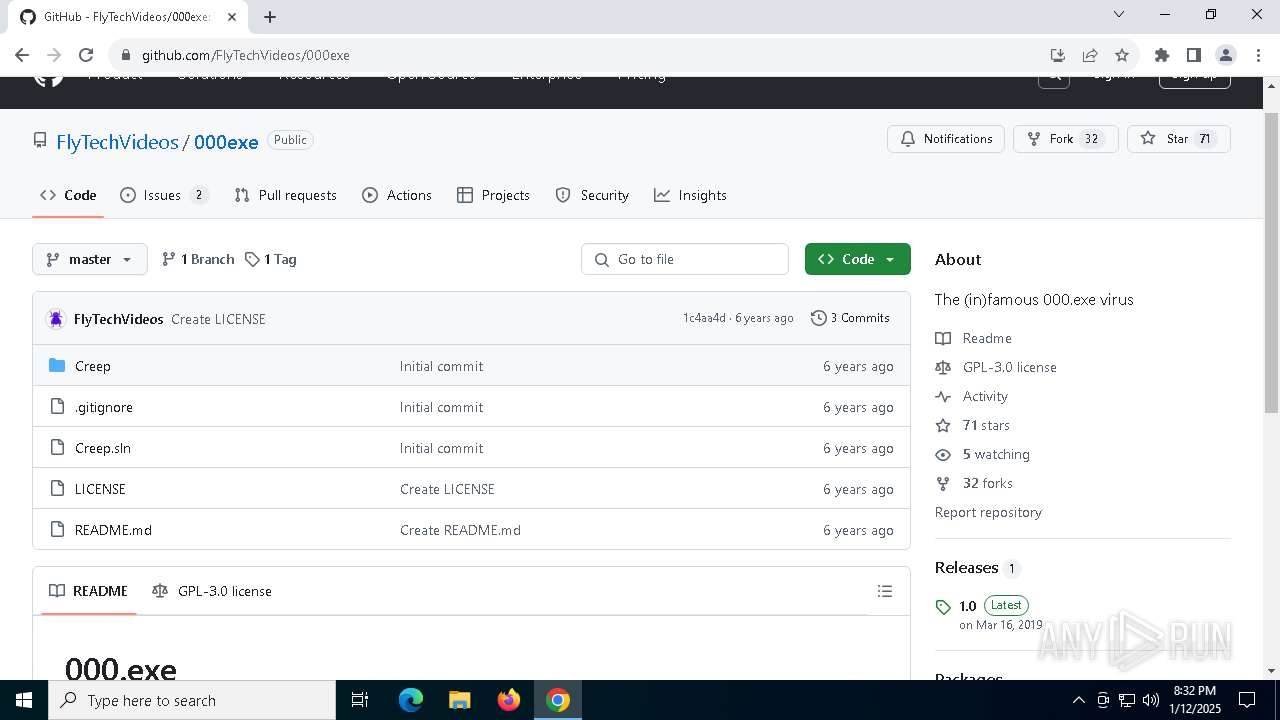
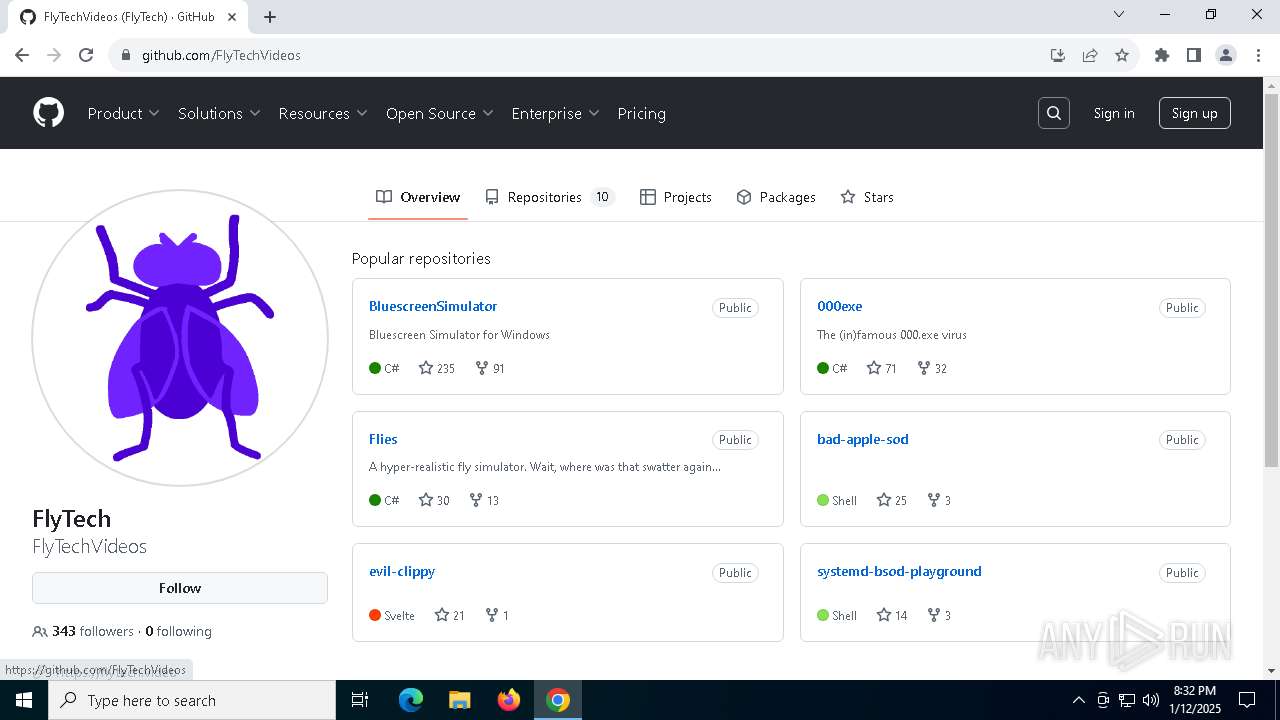
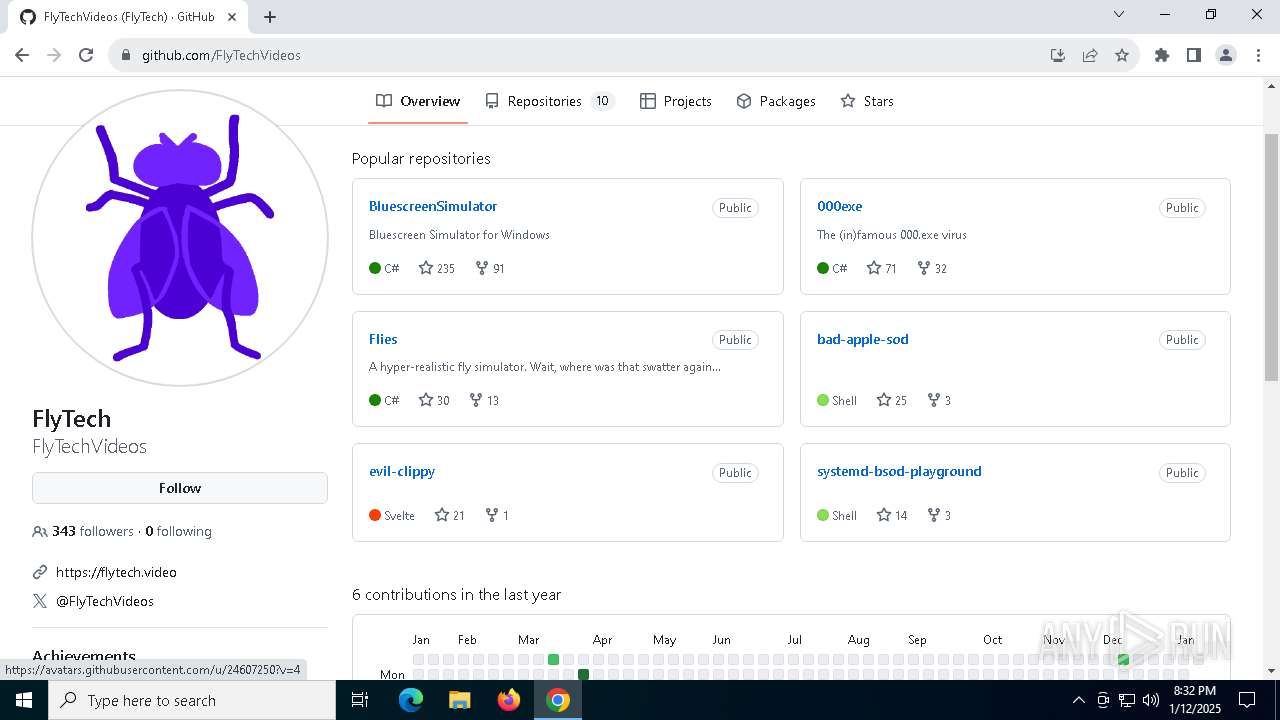
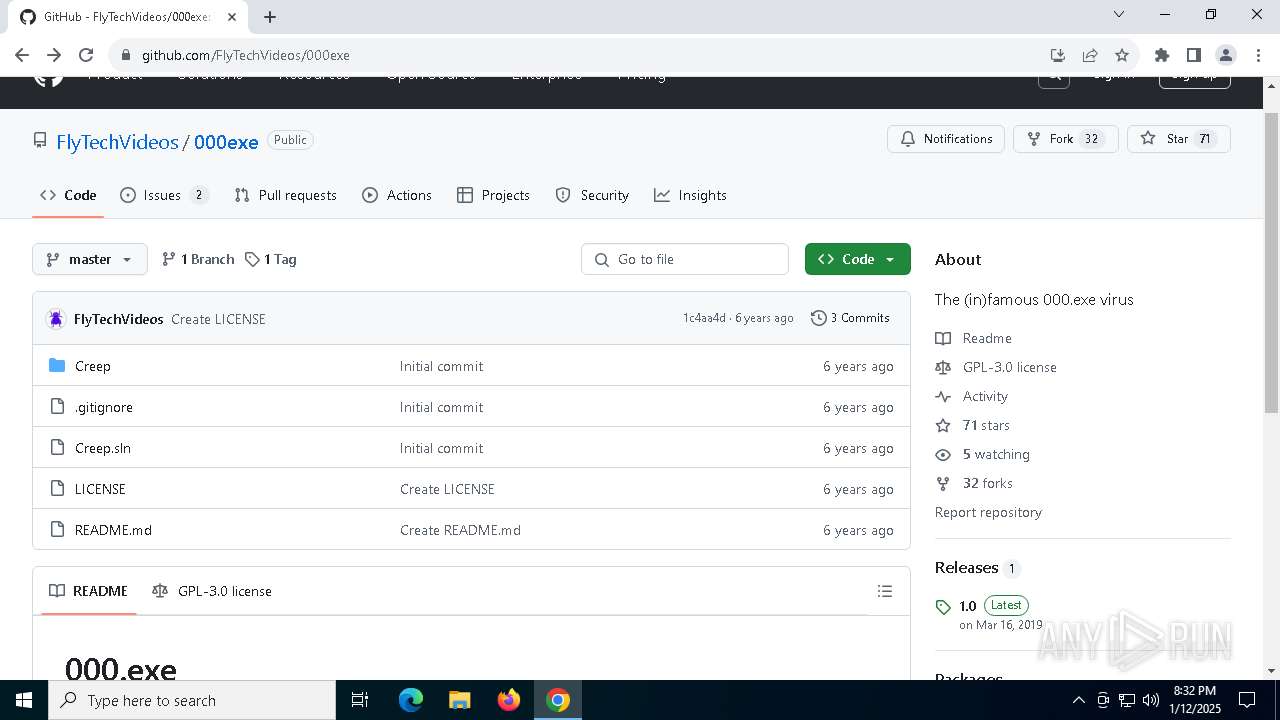
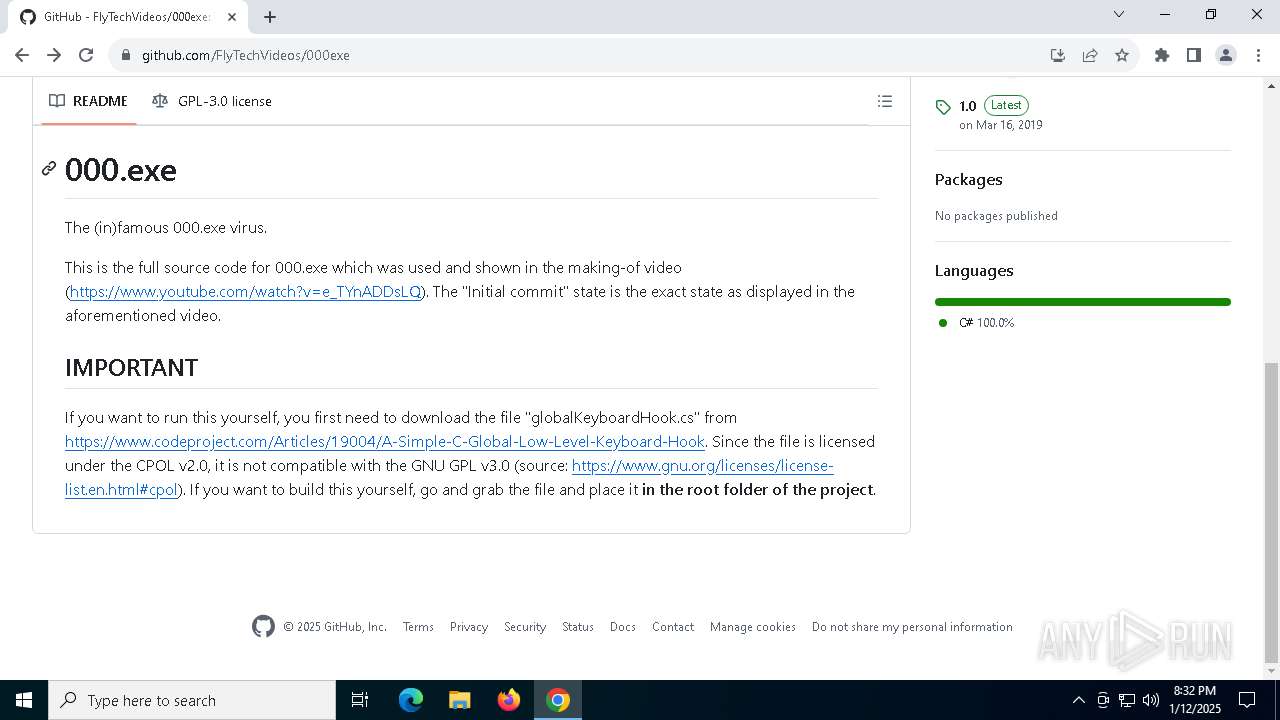
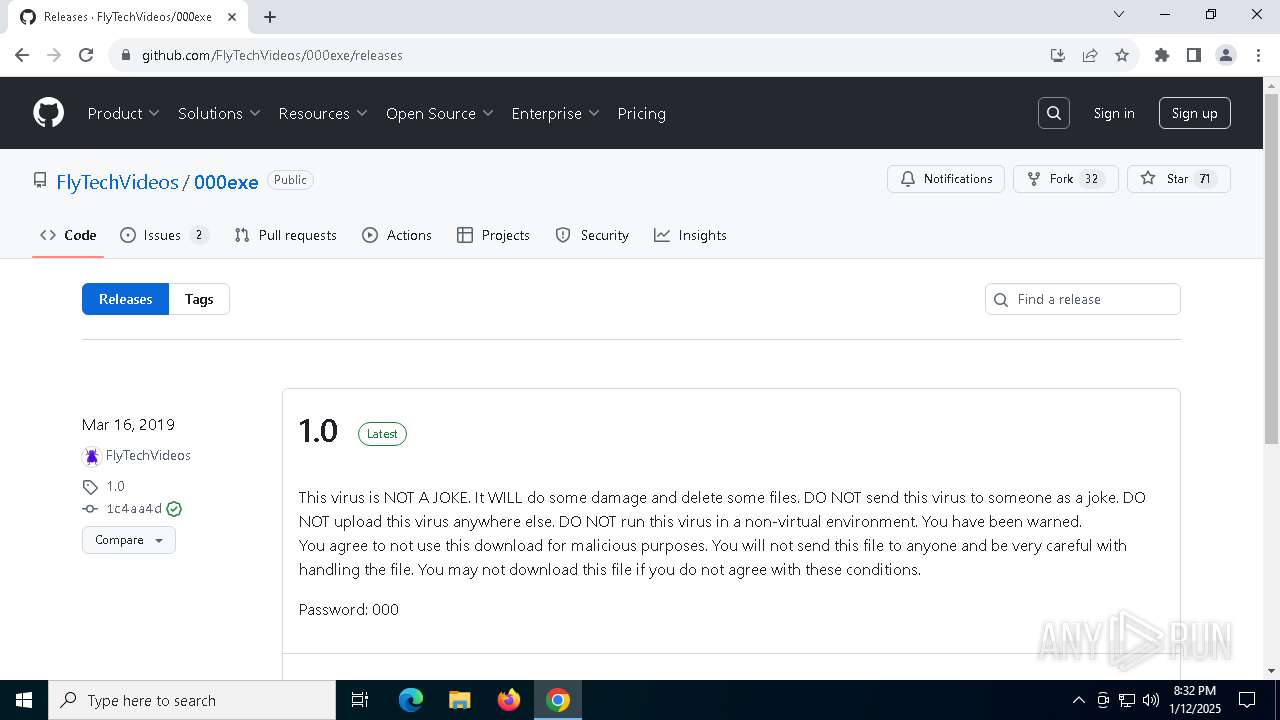
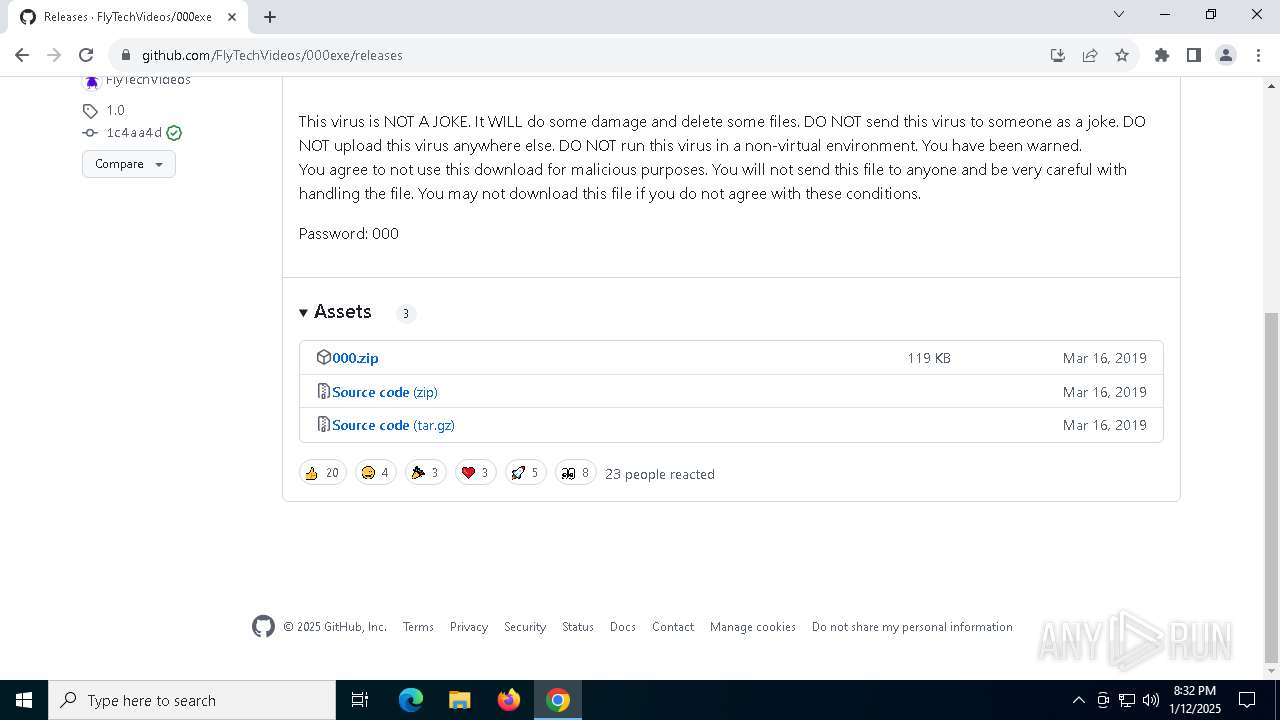
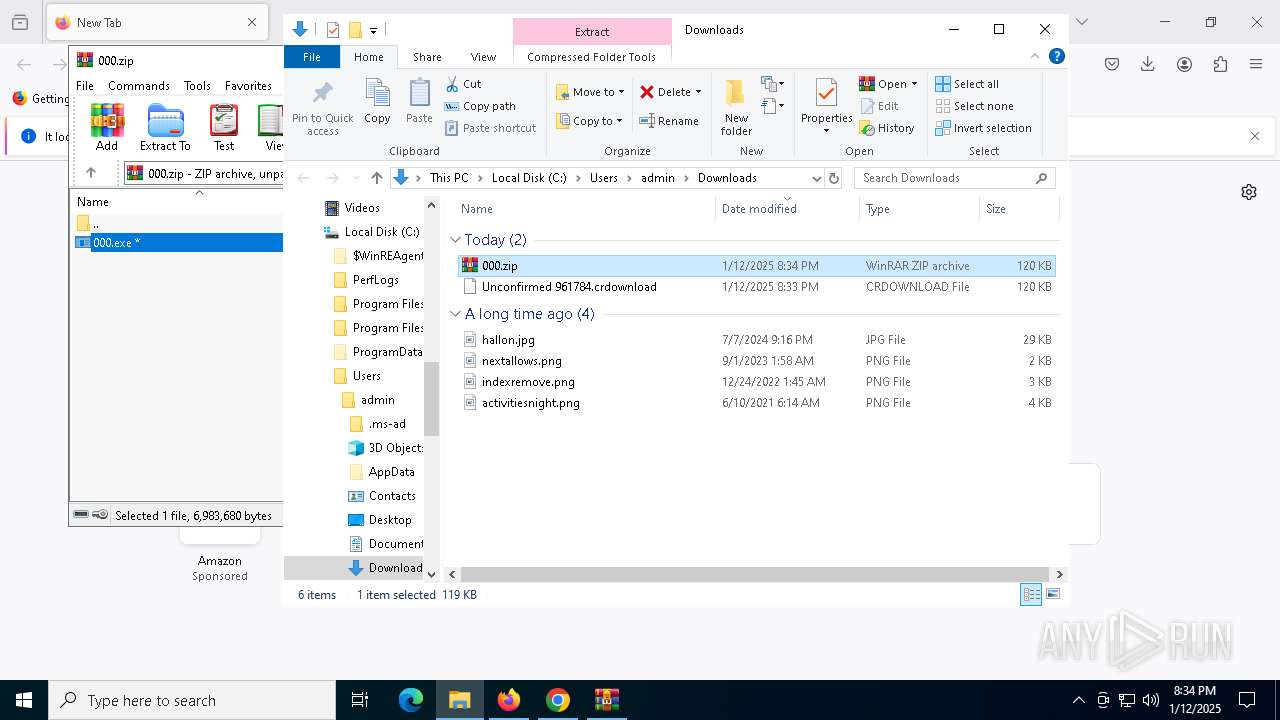
DARKROAD has been detected (YARA)
- 000.exe (PID: 7500)
SUSPICIOUS
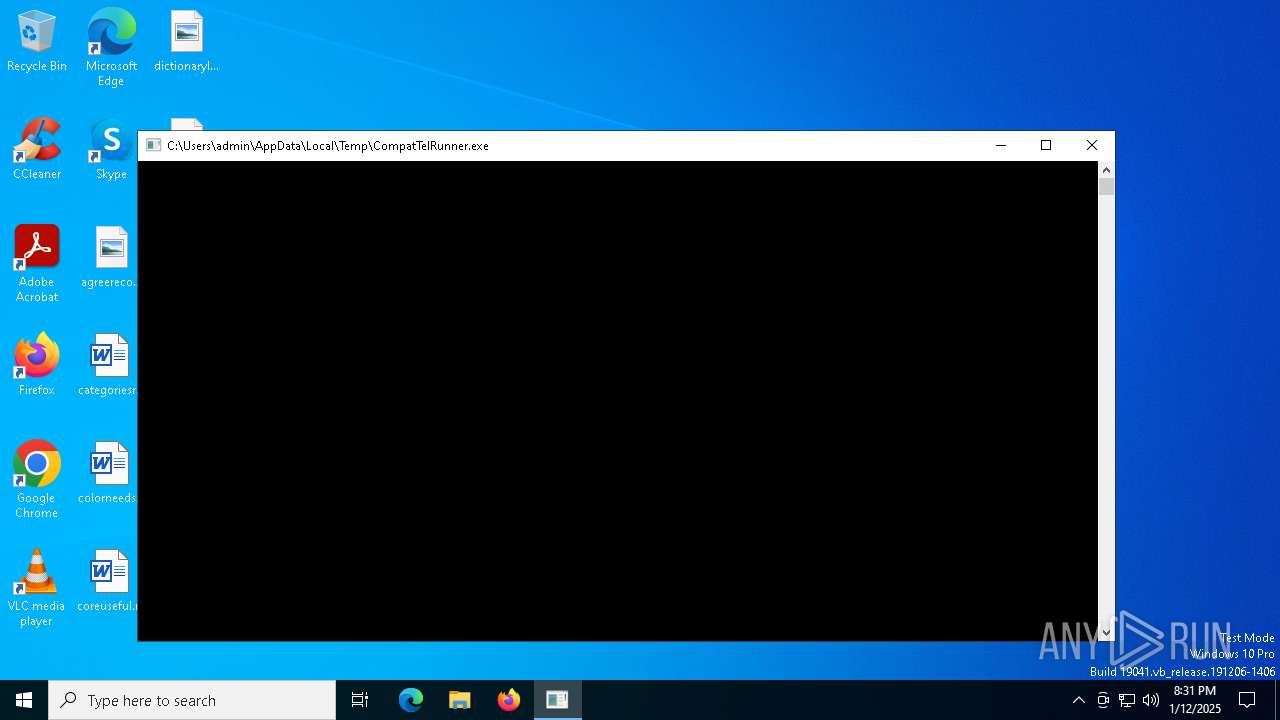
Starts a Microsoft application from unusual location
- CompatTelRunner.exe (PID: 6316)
Process drops legitimate windows executable
- CompatTelRunner.exe (PID: 6316)
Executable content was dropped or overwritten
- 000.exe (PID: 7500)
- cmd.exe (PID: 7548)
- rniw.exe (PID: 5700)
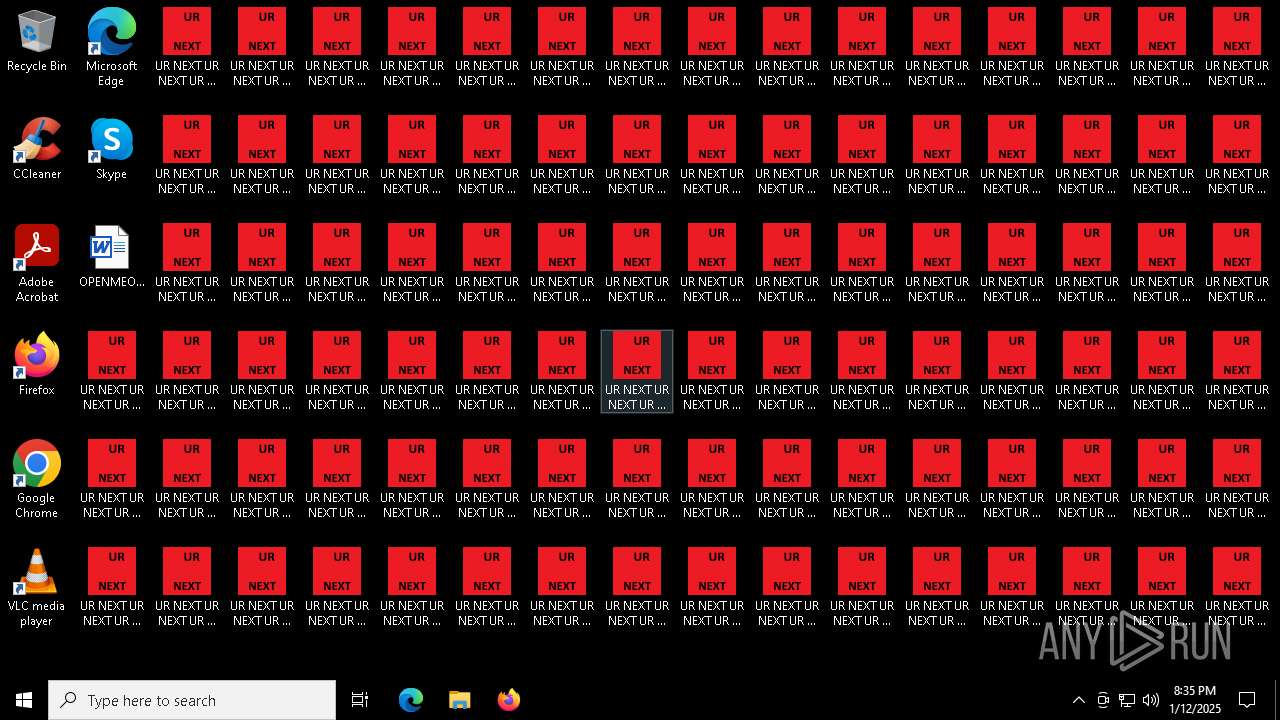
Changes the desktop background image
- 000.exe (PID: 7500)
Executing commands from a ".bat" file
- 000.exe (PID: 7500)
- rniw.exe (PID: 5700)
Starts CMD.EXE for commands execution
- 000.exe (PID: 7500)
- rniw.exe (PID: 5700)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7548)
Reads security settings of Internet Explorer
- 000.exe (PID: 7500)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 7548)
The system shut down or reboot
- cmd.exe (PID: 7548)
SQL CE related mutex has been found
- 000.exe (PID: 7500)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5900)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3328)
INFO
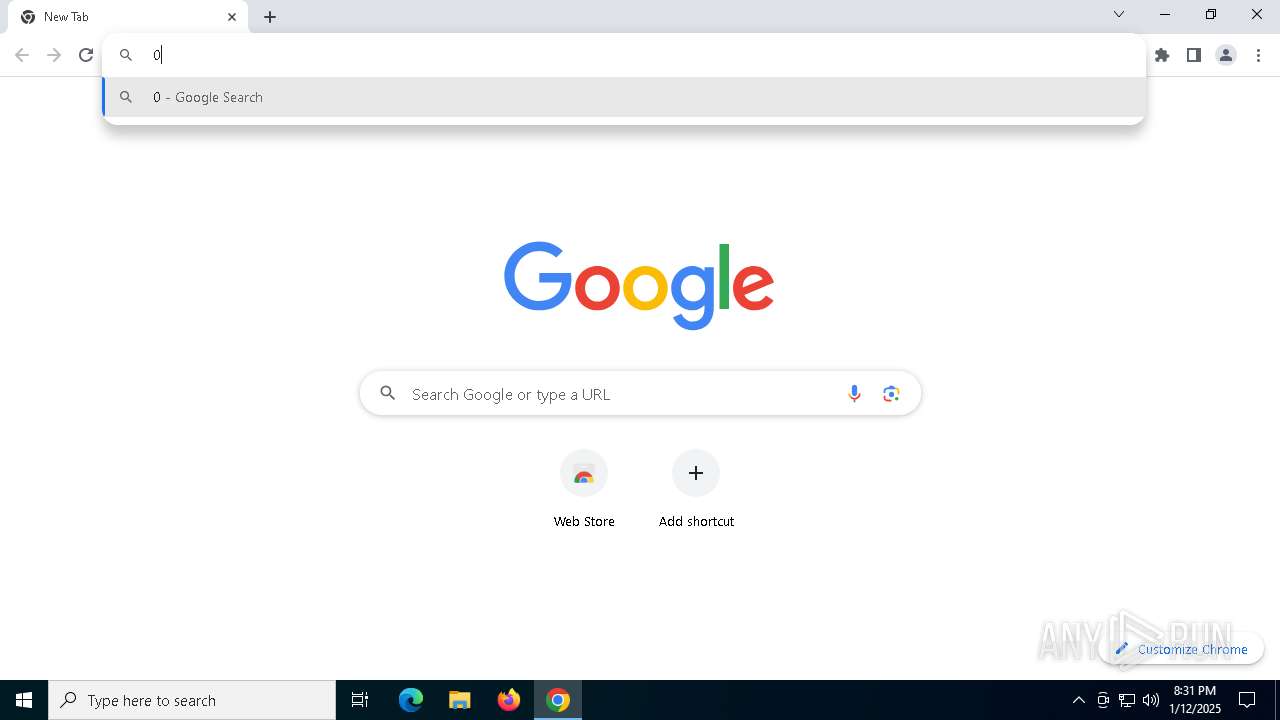
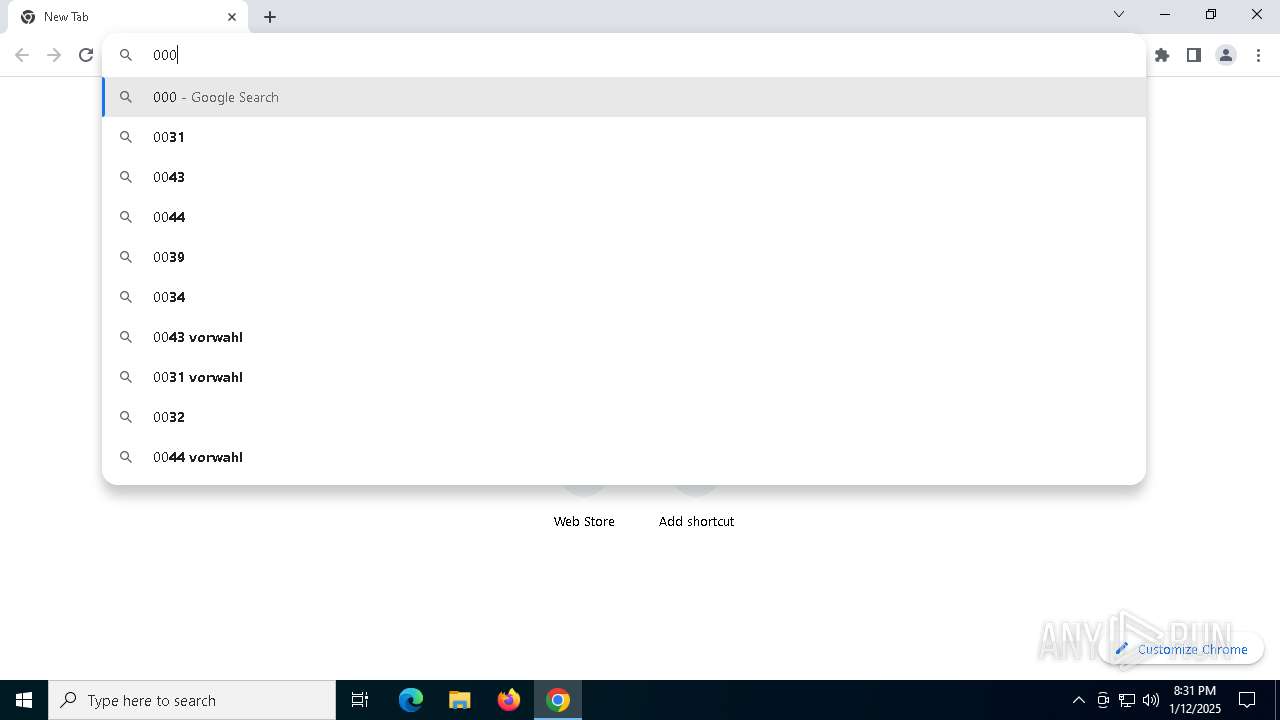
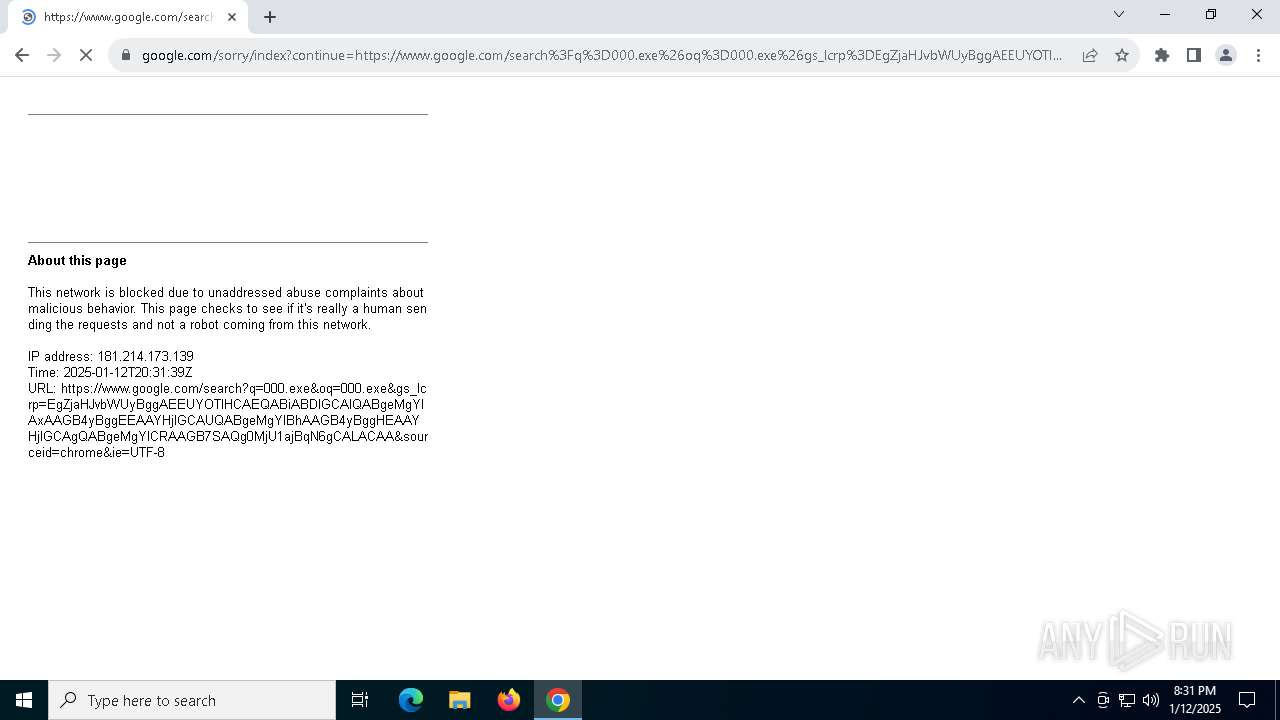
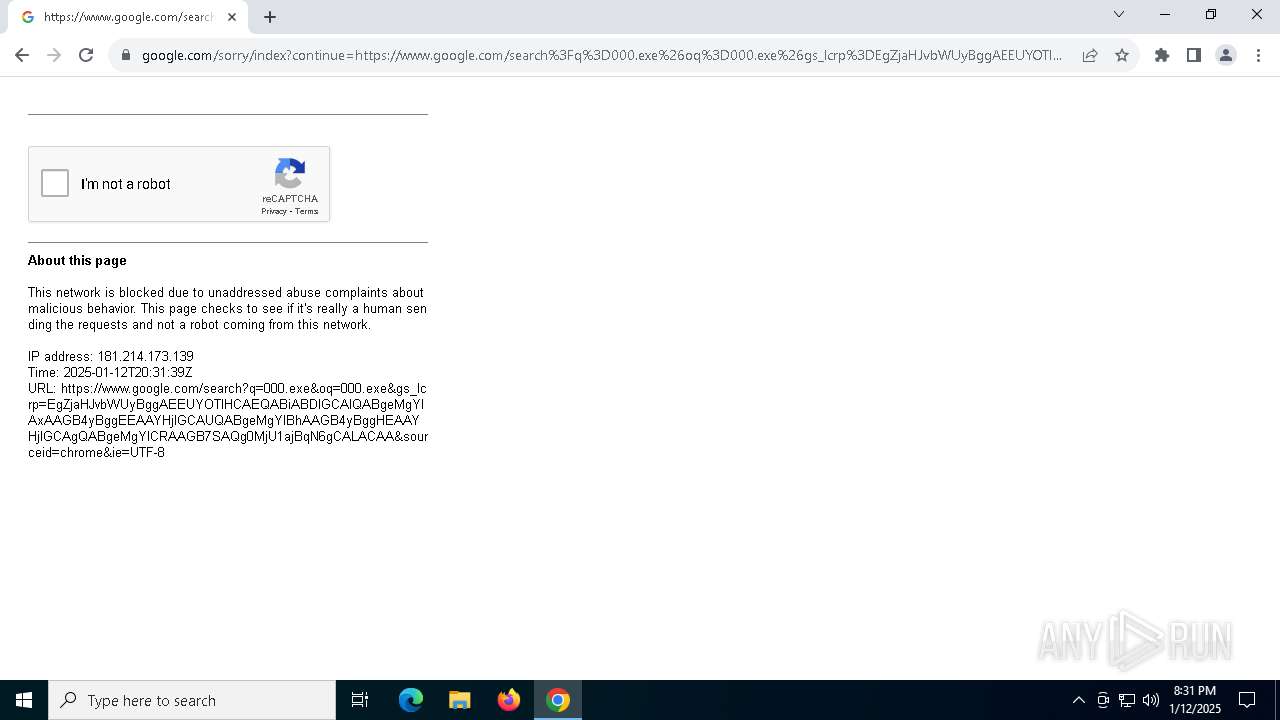
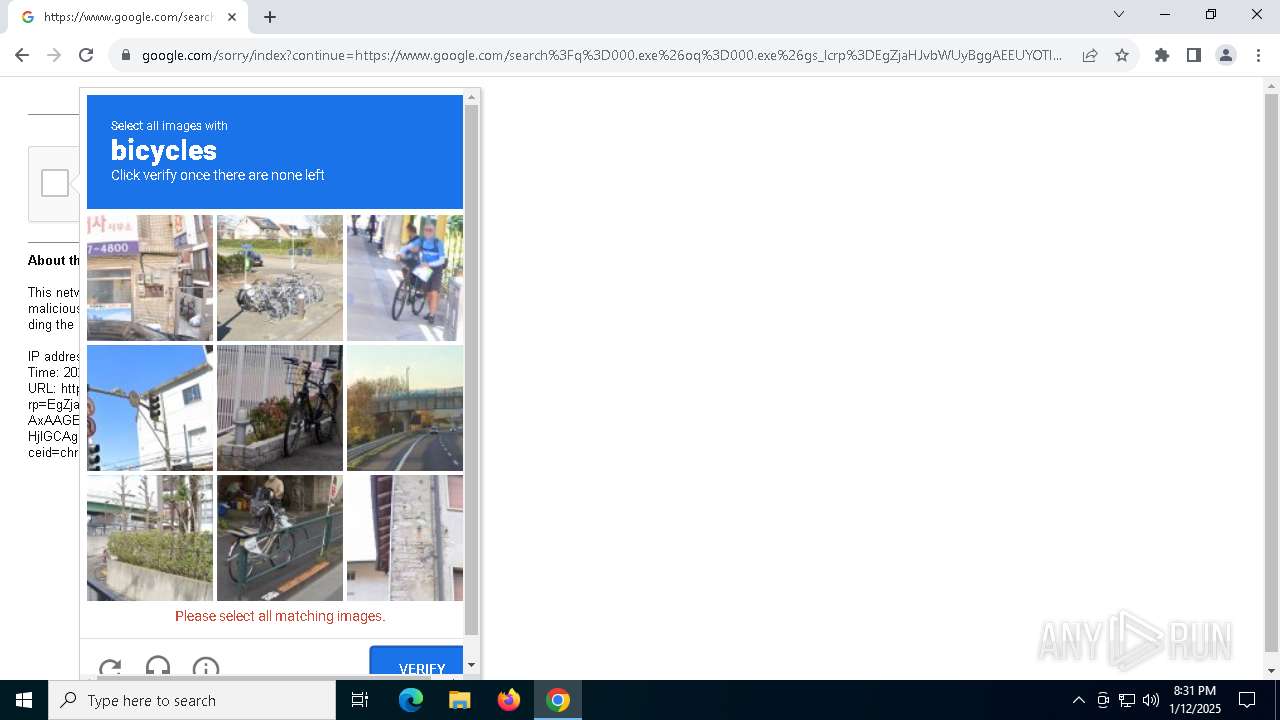
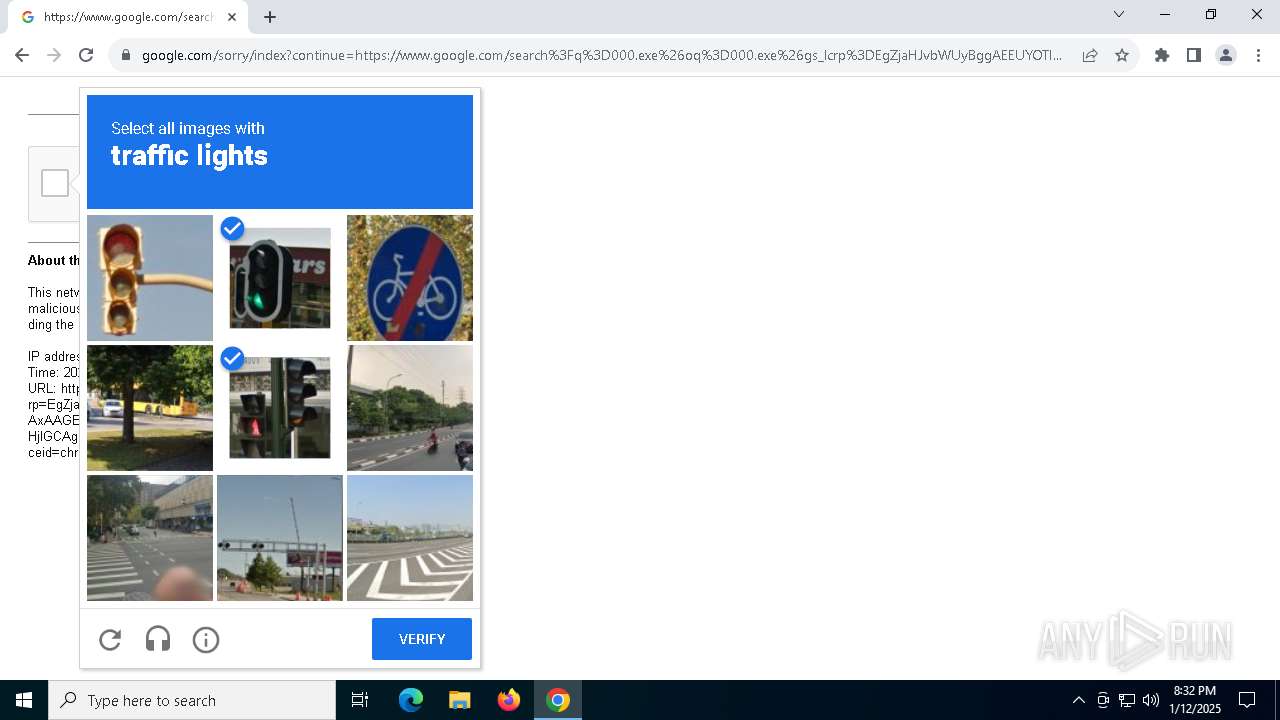
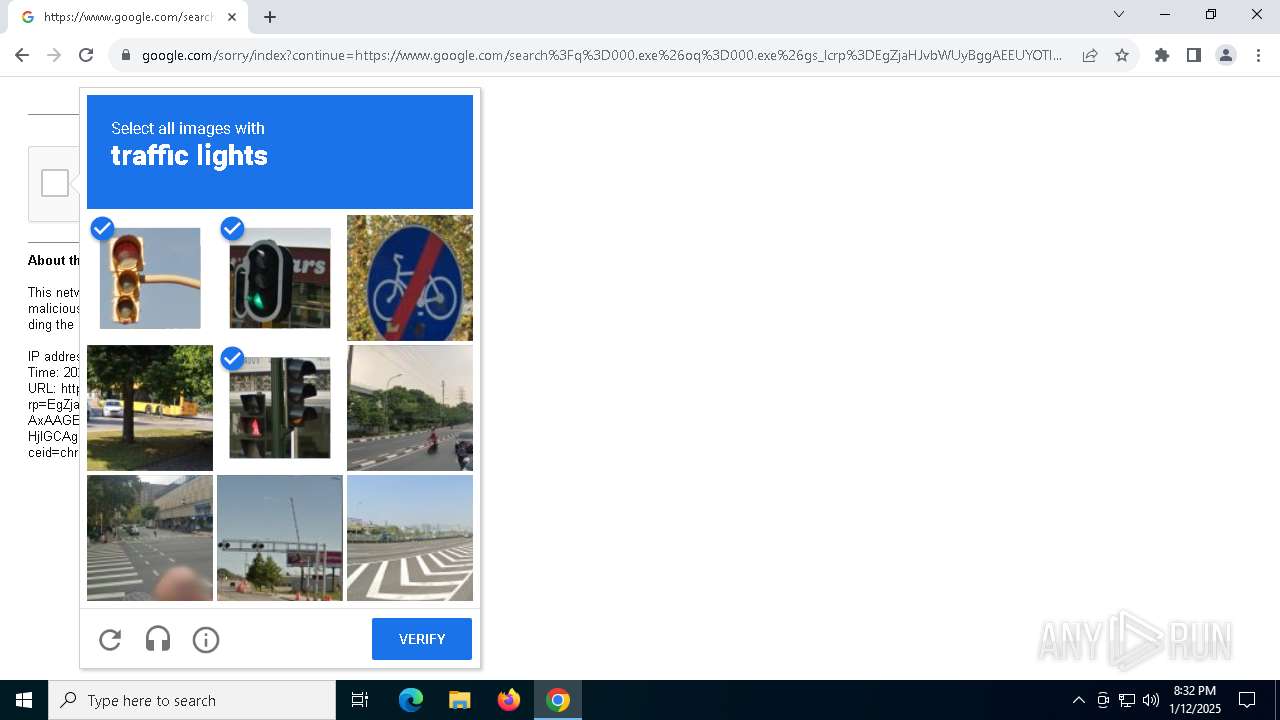
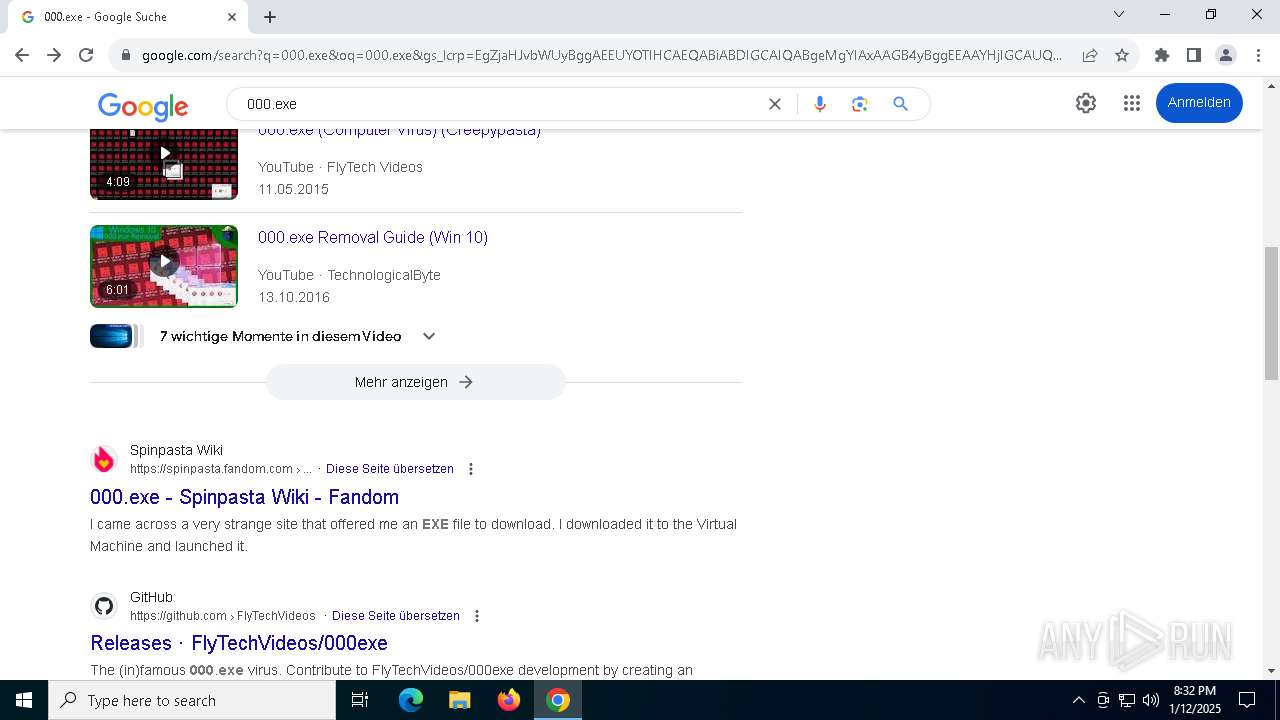
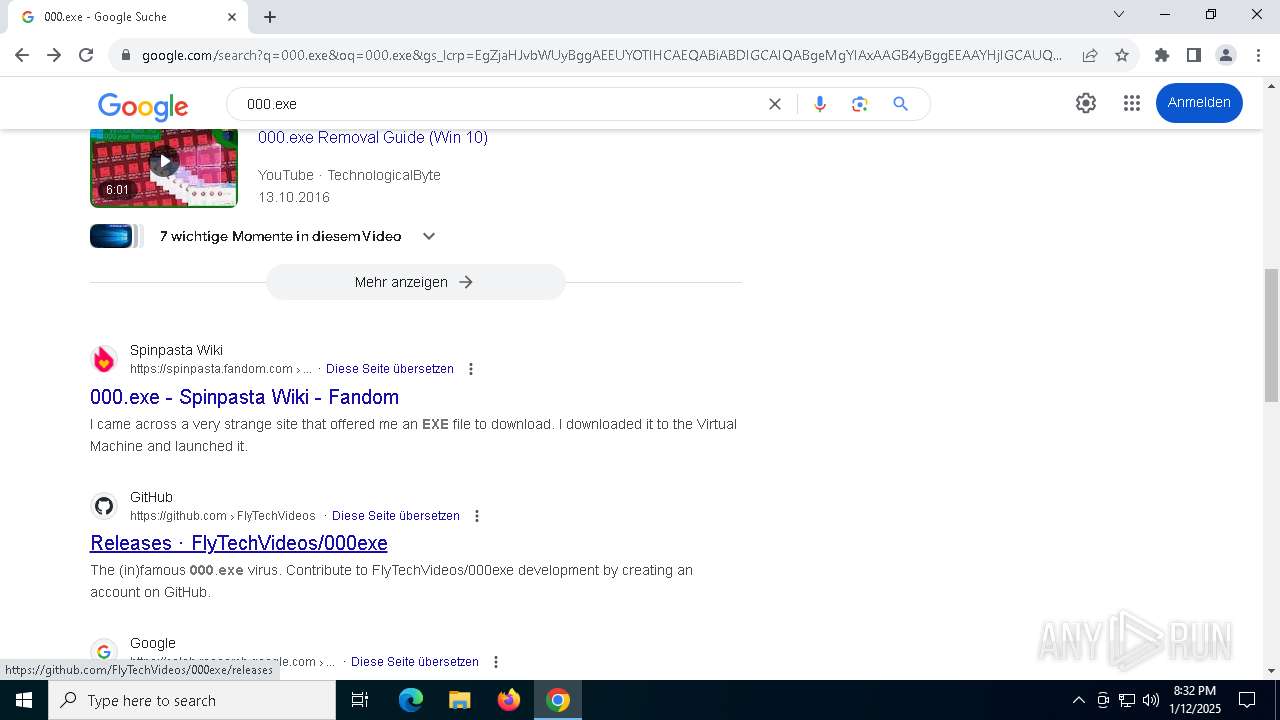
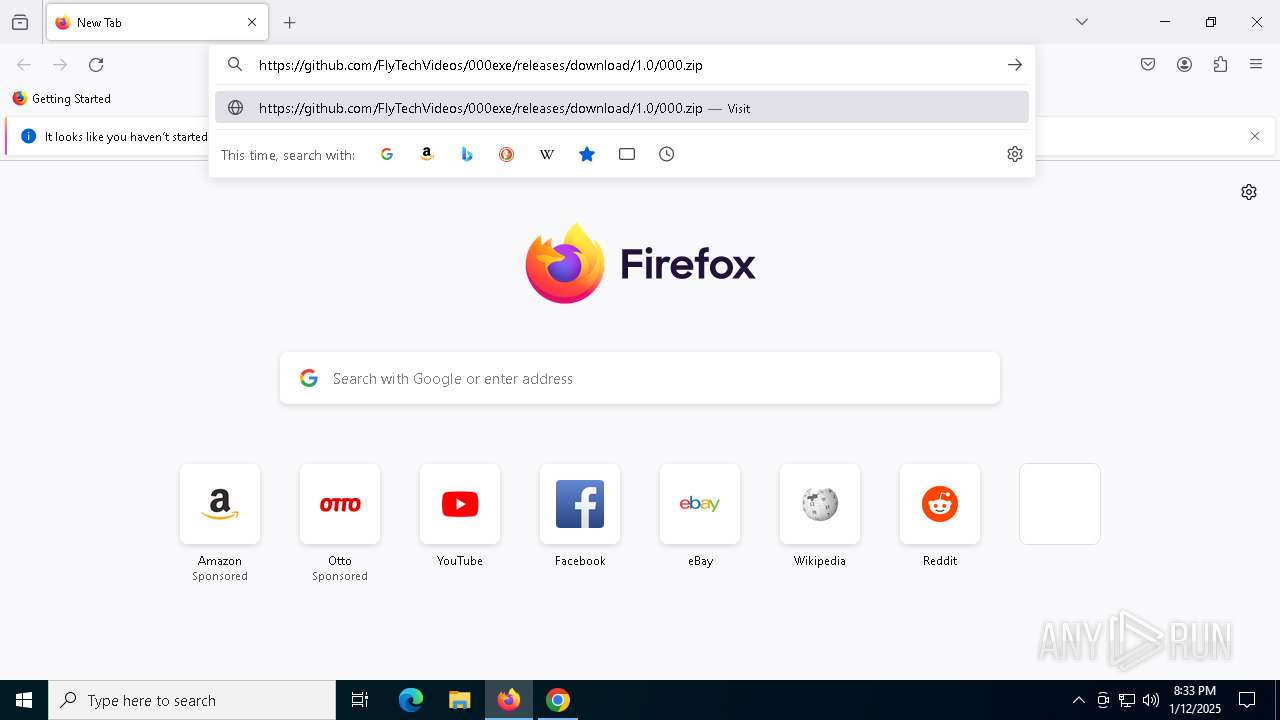
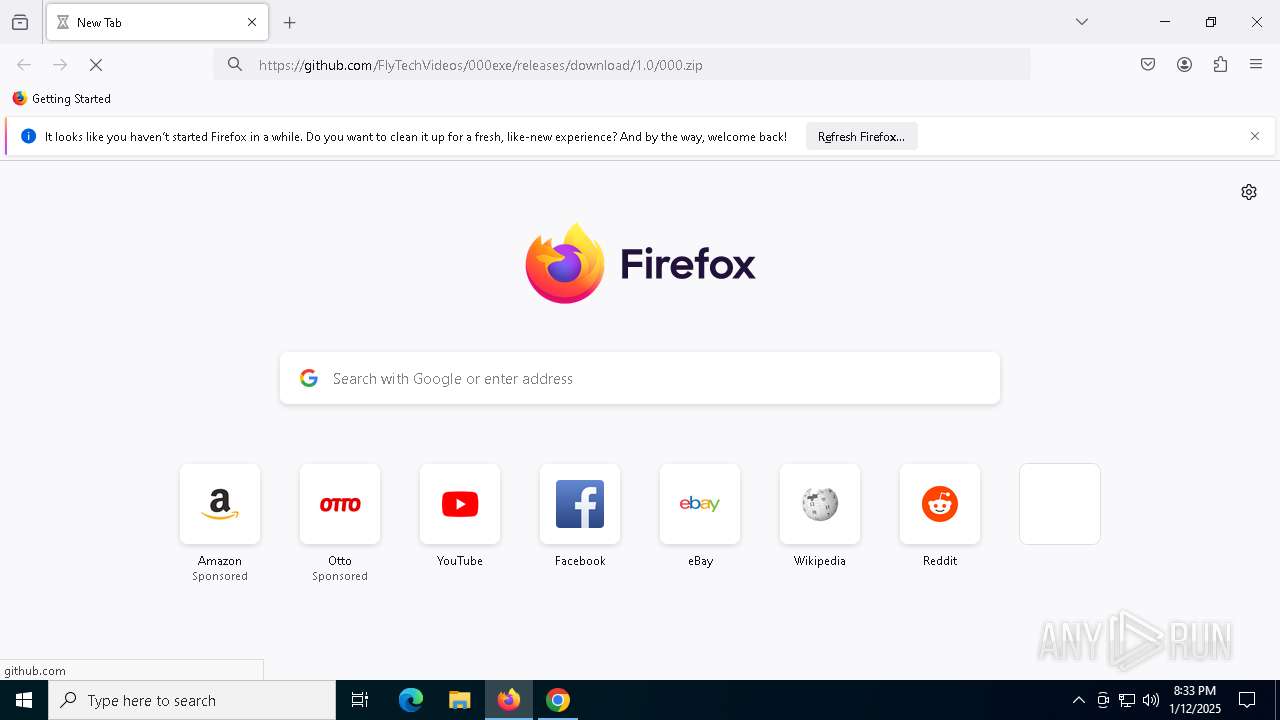
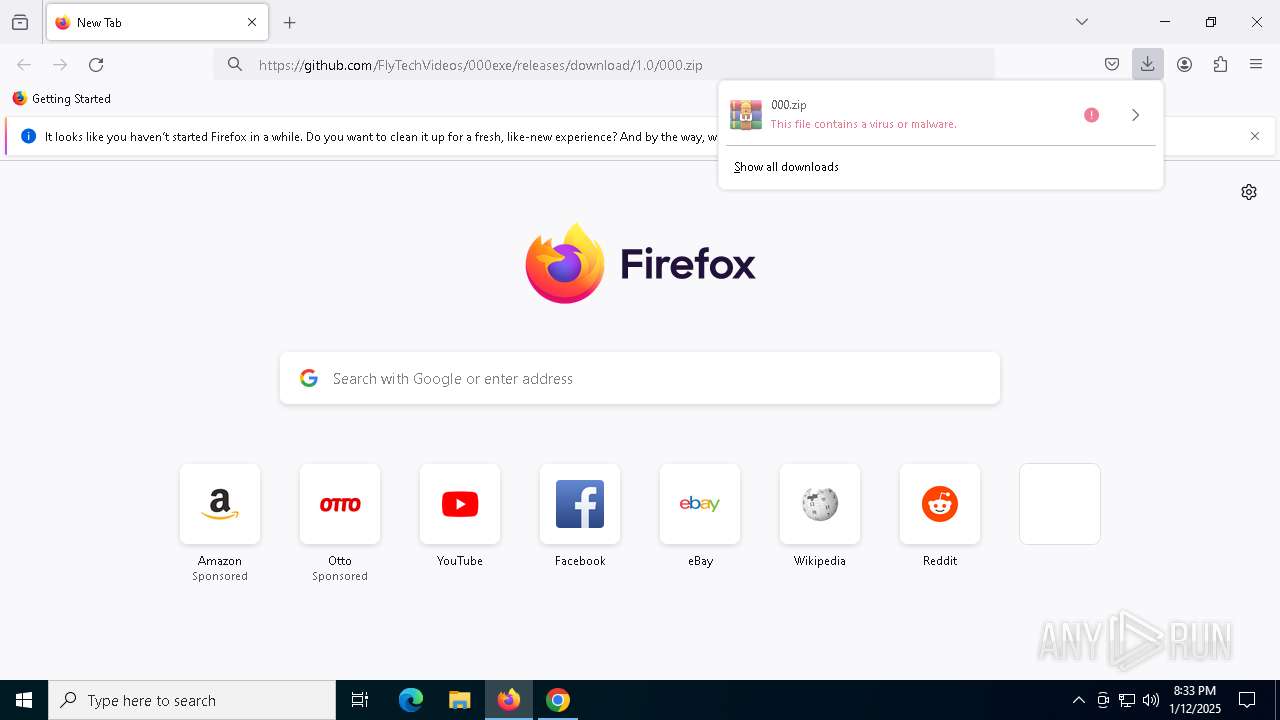
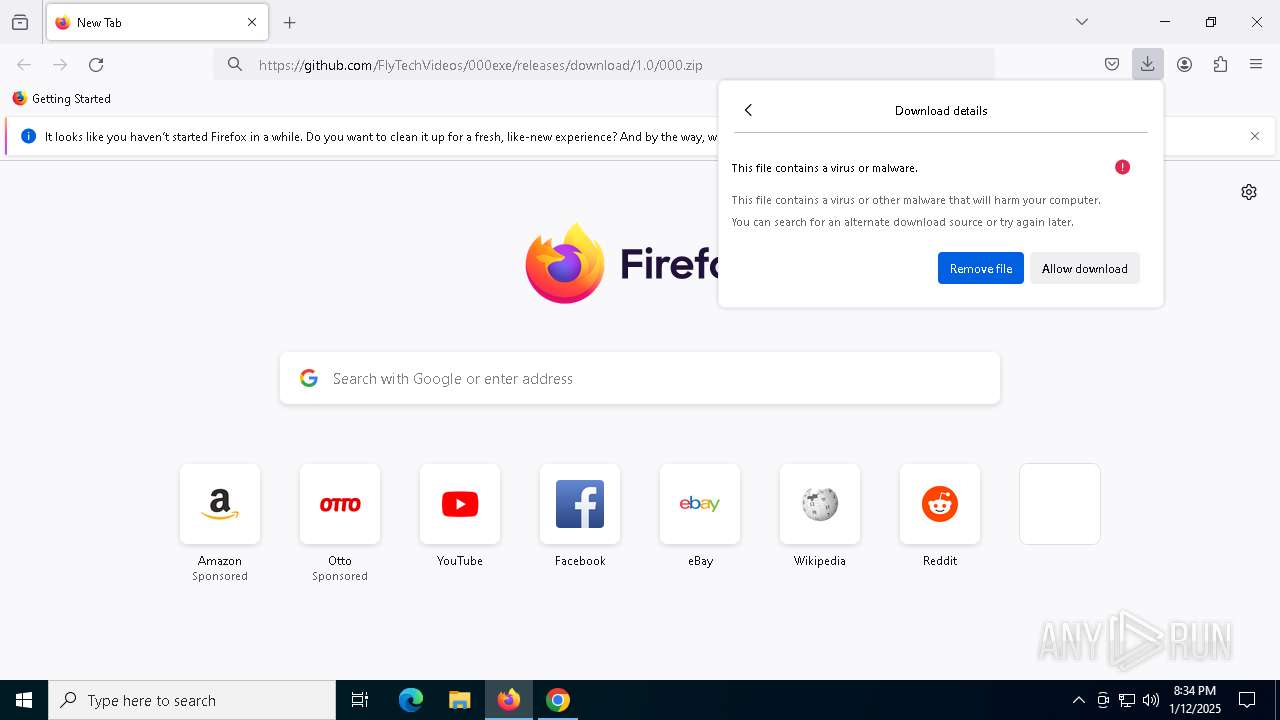
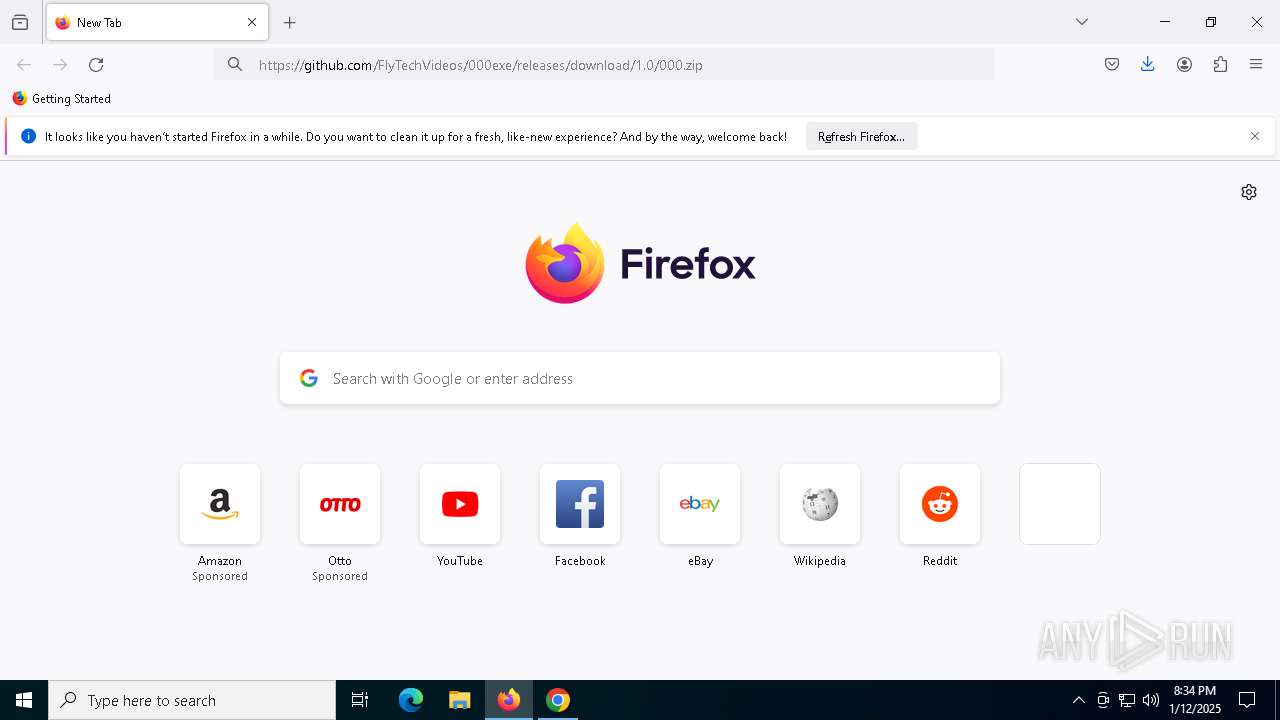
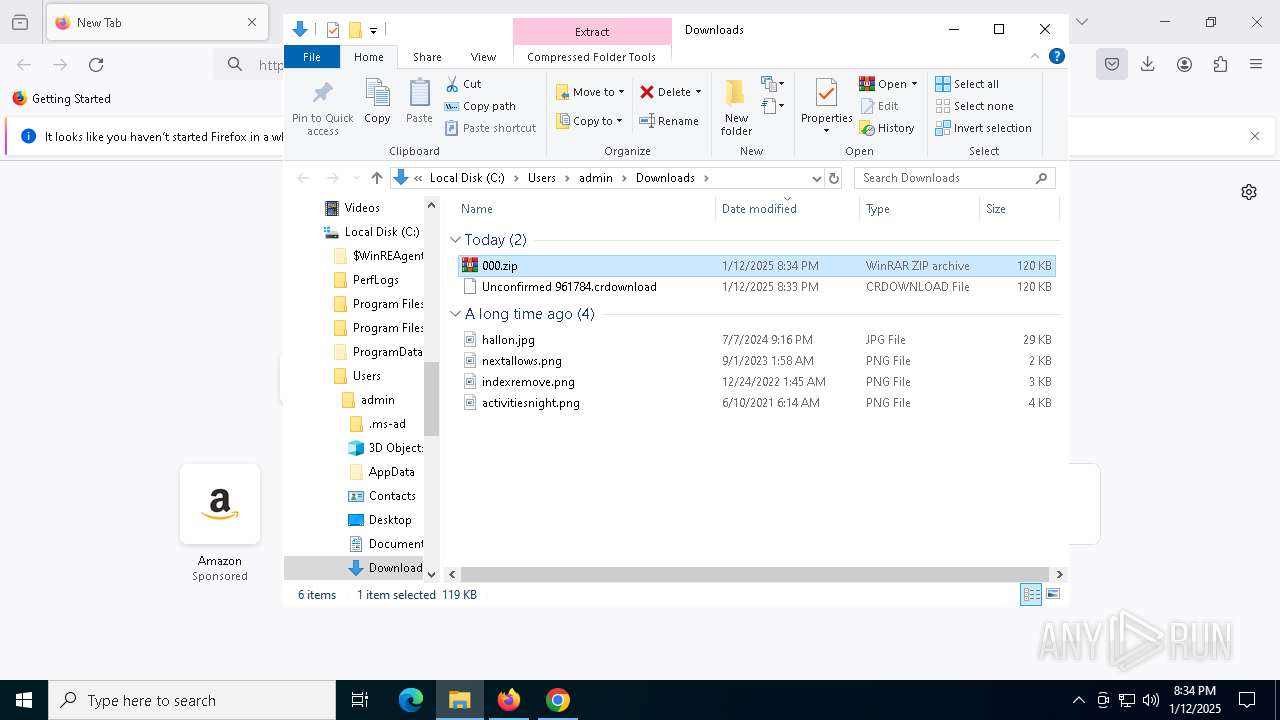
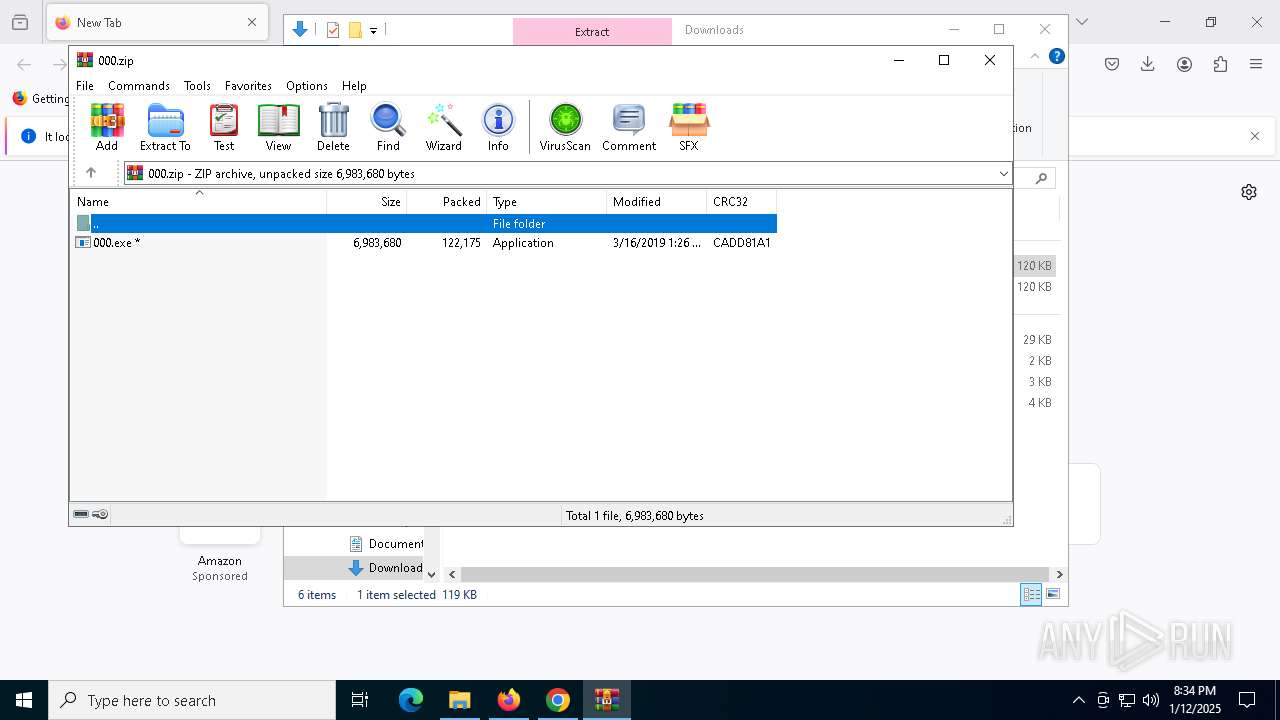
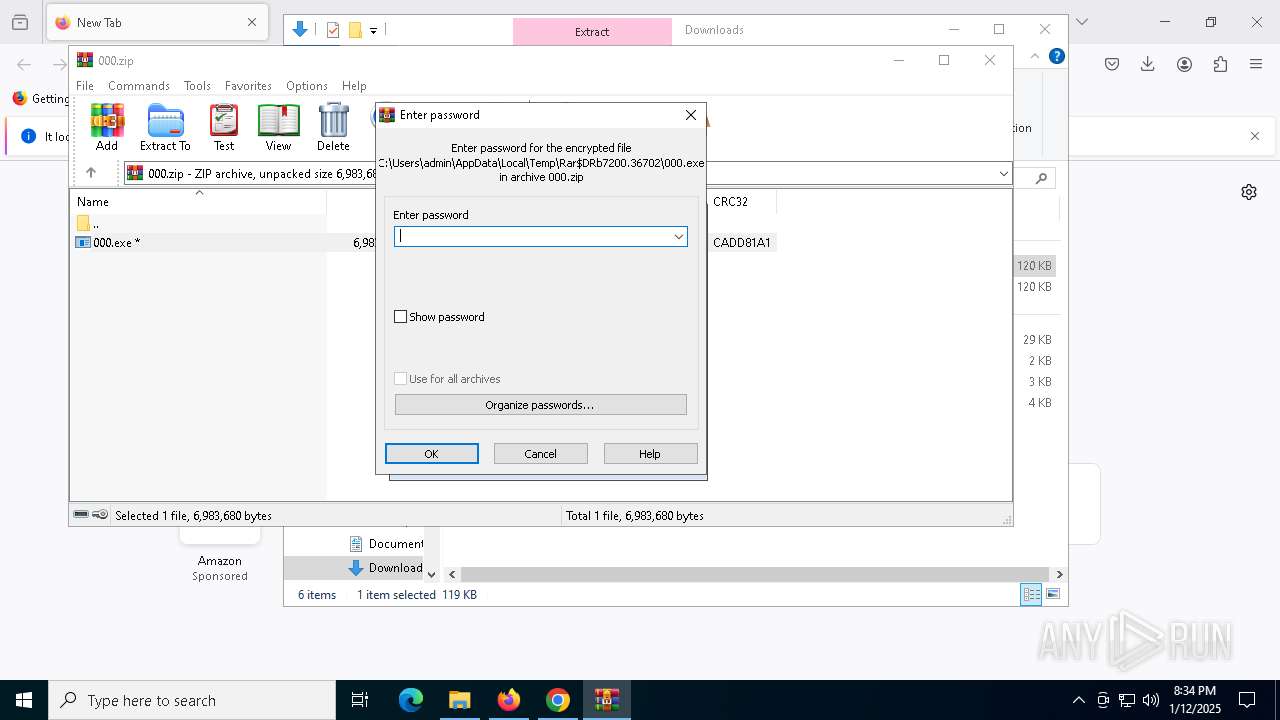
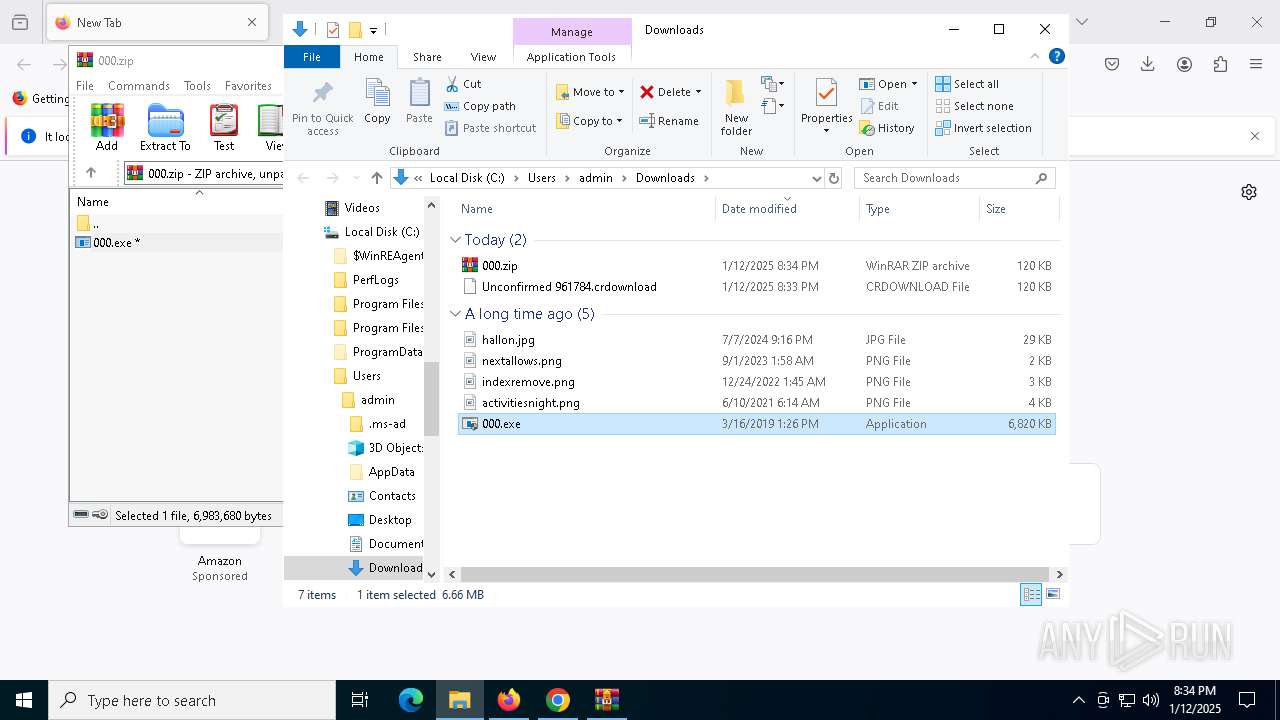
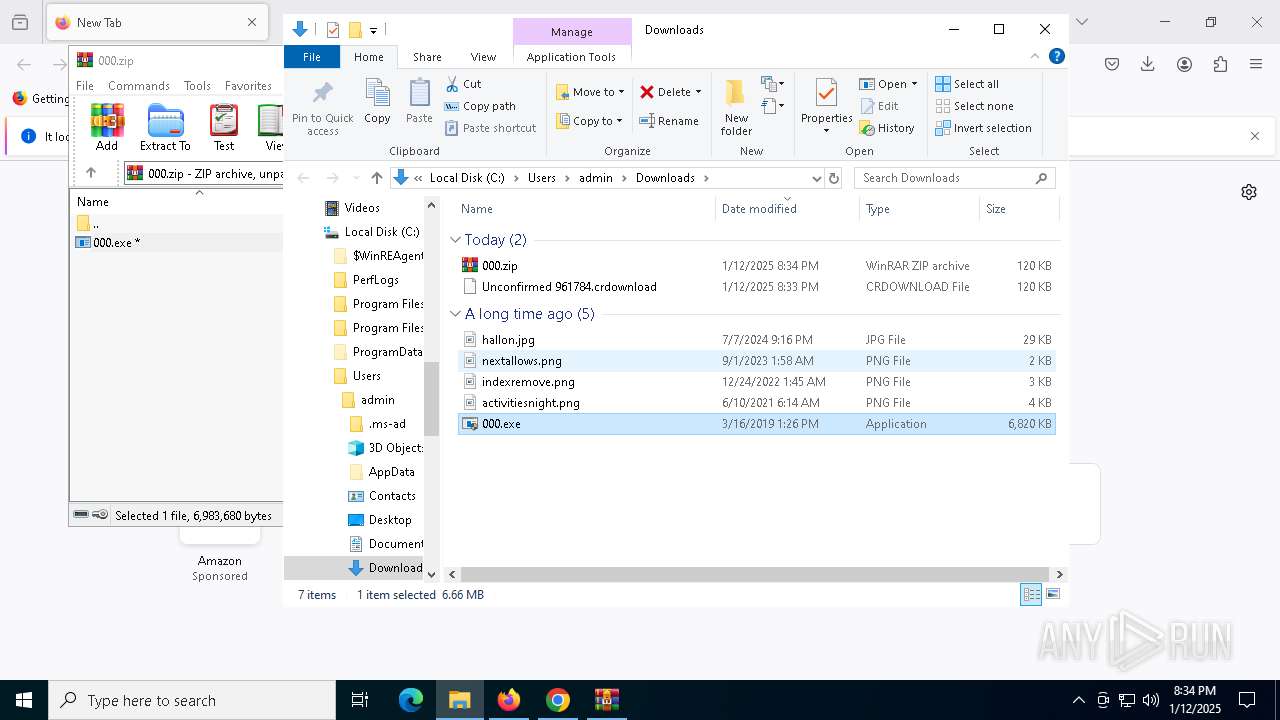
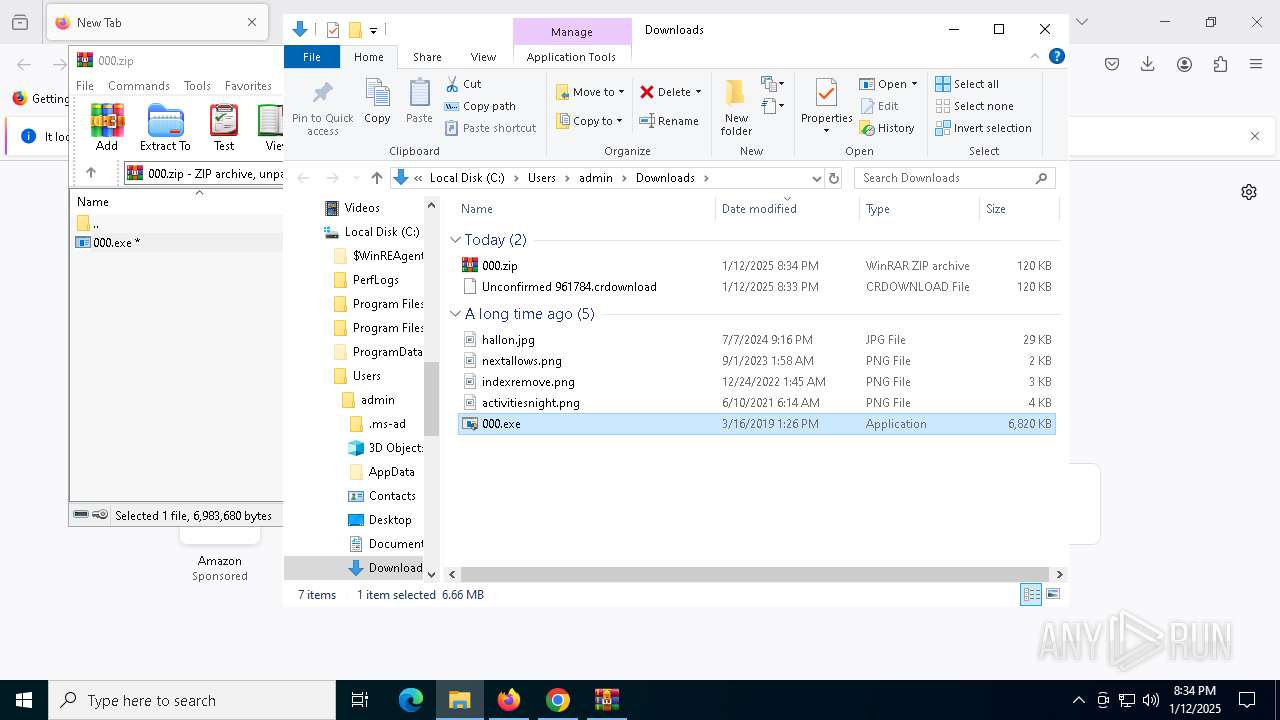
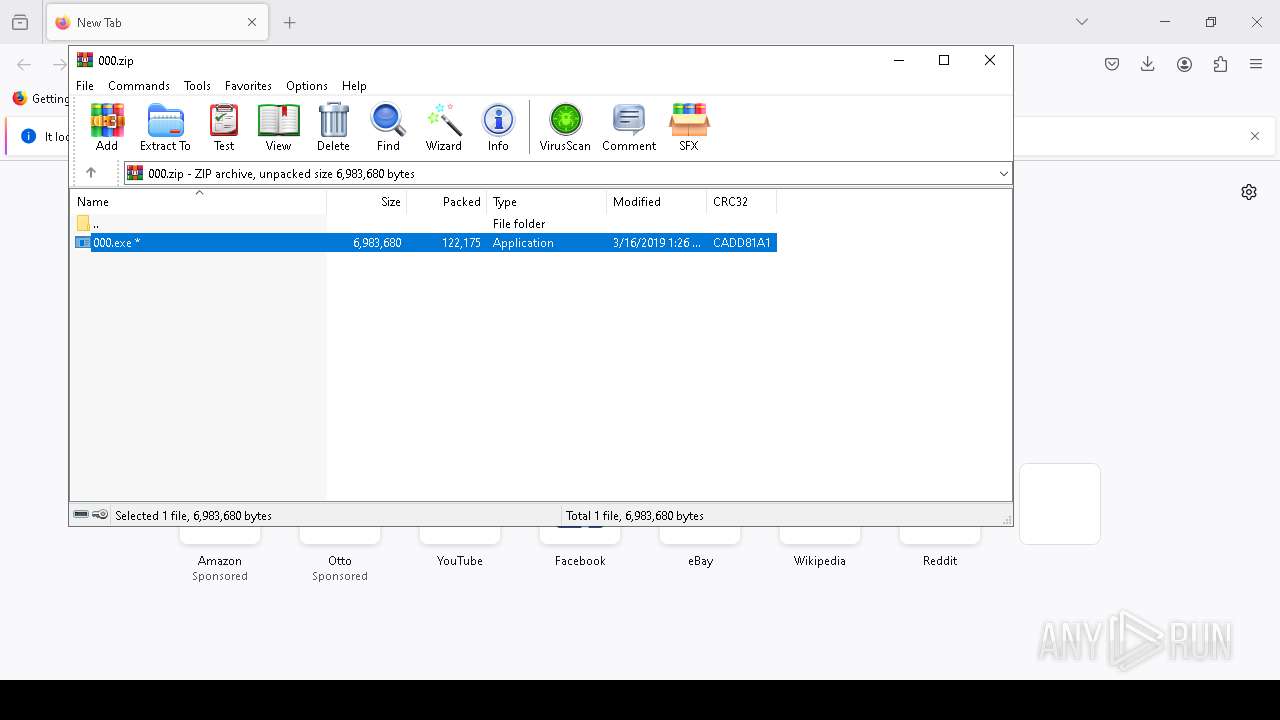
Manual execution by a user
- chrome.exe (PID: 7124)
- firefox.exe (PID: 6724)
- WinRAR.exe (PID: 7200)
- 000.exe (PID: 7448)
- 000.exe (PID: 7500)
- rniw.exe (PID: 5700)
The sample compiled with english language support
- CompatTelRunner.exe (PID: 6316)
- chrome.exe (PID: 4136)
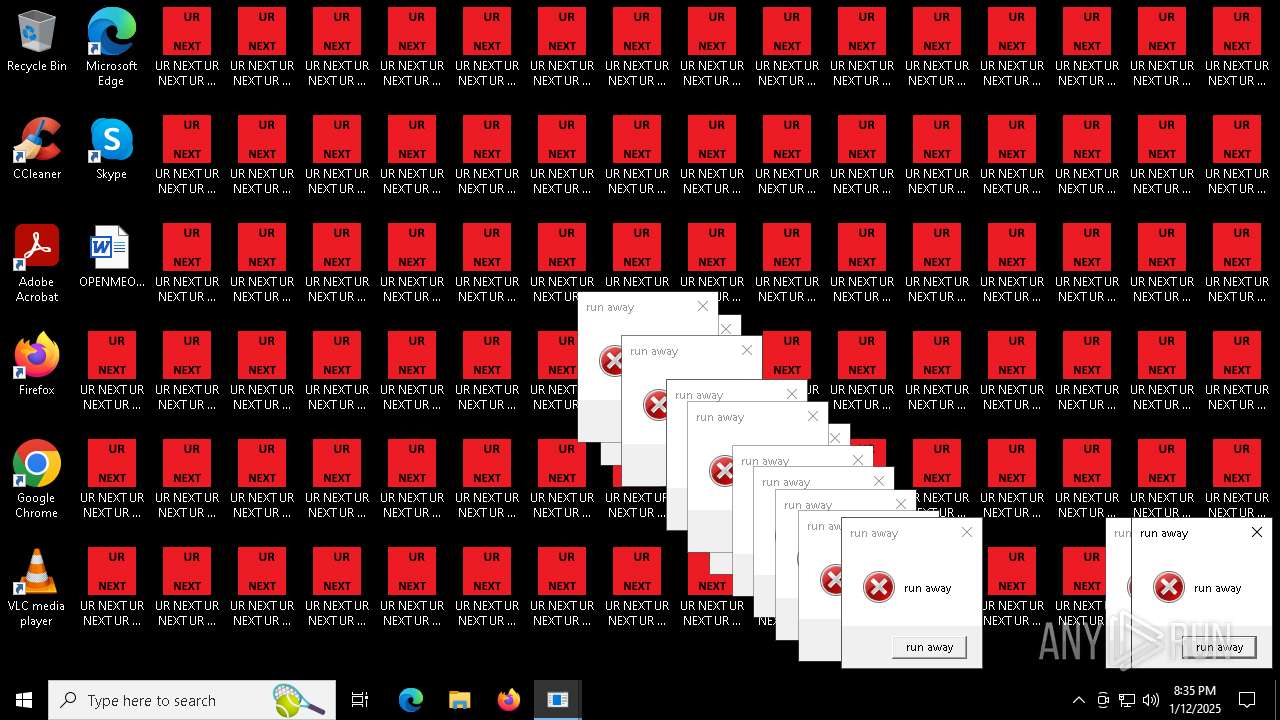
Reads the computer name
- CompatTelRunner.exe (PID: 6316)
- 000.exe (PID: 7500)
- runaway.exe (PID: 4272)
- PLUGScheduler.exe (PID: 3328)
- runaway.exe (PID: 5720)
- runaway.exe (PID: 5796)
- runaway.exe (PID: 6424)
- runaway.exe (PID: 6484)
- runaway.exe (PID: 6540)
- runaway.exe (PID: 6648)
- runaway.exe (PID: 6700)
- runaway.exe (PID: 6864)
- runaway.exe (PID: 6916)
- runaway.exe (PID: 6516)
- runaway.exe (PID: 6232)
- runaway.exe (PID: 6848)
- runaway.exe (PID: 7064)
- runaway.exe (PID: 5744)
- runaway.exe (PID: 6968)
- runaway.exe (PID: 7136)
- runaway.exe (PID: 7052)
- runaway.exe (PID: 6320)
- runaway.exe (PID: 6456)
- runaway.exe (PID: 6064)
- runaway.exe (PID: 6728)
- runaway.exe (PID: 7368)
- runaway.exe (PID: 7424)
- runaway.exe (PID: 7768)
- runaway.exe (PID: 7824)
- runaway.exe (PID: 7944)
- runaway.exe (PID: 8056)
- runaway.exe (PID: 7544)
- runaway.exe (PID: 7656)
- runaway.exe (PID: 7352)
- runaway.exe (PID: 8100)
- runaway.exe (PID: 7652)
- runaway.exe (PID: 7860)
- runaway.exe (PID: 7580)
- runaway.exe (PID: 7232)
- runaway.exe (PID: 8032)
- runaway.exe (PID: 8200)
- runaway.exe (PID: 7748)
- runaway.exe (PID: 8260)
- runaway.exe (PID: 8428)
- runaway.exe (PID: 8540)
- runaway.exe (PID: 7684)
Checks supported languages
- CompatTelRunner.exe (PID: 6316)
- 000.exe (PID: 7500)
- PLUGScheduler.exe (PID: 3328)
- rniw.exe (PID: 5700)
- runaway.exe (PID: 6208)
- runaway.exe (PID: 6156)
- runaway.exe (PID: 6308)
- runaway.exe (PID: 4840)
- runaway.exe (PID: 5720)
- runaway.exe (PID: 5796)
- runaway.exe (PID: 6364)
- runaway.exe (PID: 6484)
- runaway.exe (PID: 6424)
- runaway.exe (PID: 6540)
- runaway.exe (PID: 6648)
- runaway.exe (PID: 6700)
- runaway.exe (PID: 6864)
- runaway.exe (PID: 6808)
- runaway.exe (PID: 6968)
- runaway.exe (PID: 6916)
- runaway.exe (PID: 4272)
- runaway.exe (PID: 7136)
- runaway.exe (PID: 2132)
- runaway.exe (PID: 6232)
- runaway.exe (PID: 6848)
- runaway.exe (PID: 7064)
- runaway.exe (PID: 6712)
- runaway.exe (PID: 6924)
- runaway.exe (PID: 6548)
- runaway.exe (PID: 7160)
- runaway.exe (PID: 5744)
- runaway.exe (PID: 6768)
- runaway.exe (PID: 7052)
- runaway.exe (PID: 7084)
- runaway.exe (PID: 6320)
- runaway.exe (PID: 6880)
- runaway.exe (PID: 6064)
- runaway.exe (PID: 6456)
- runaway.exe (PID: 7192)
- runaway.exe (PID: 7244)
- runaway.exe (PID: 7312)
- runaway.exe (PID: 7368)
- runaway.exe (PID: 7424)
- runaway.exe (PID: 7484)
- runaway.exe (PID: 7768)
- runaway.exe (PID: 7824)
- runaway.exe (PID: 7944)
- runaway.exe (PID: 8000)
- runaway.exe (PID: 8056)
- runaway.exe (PID: 7544)
- runaway.exe (PID: 7600)
- runaway.exe (PID: 7656)
- runaway.exe (PID: 7712)
- runaway.exe (PID: 7448)
- runaway.exe (PID: 7652)
- runaway.exe (PID: 7732)
- runaway.exe (PID: 7860)
- runaway.exe (PID: 8100)
- runaway.exe (PID: 7580)
- runaway.exe (PID: 5804)
- runaway.exe (PID: 7332)
- runaway.exe (PID: 8032)
- runaway.exe (PID: 8168)
- runaway.exe (PID: 7232)
- runaway.exe (PID: 7352)
- runaway.exe (PID: 8112)
- runaway.exe (PID: 7508)
- runaway.exe (PID: 7288)
- runaway.exe (PID: 7684)
- runaway.exe (PID: 7180)
- runaway.exe (PID: 8428)
- runaway.exe (PID: 7748)
- runaway.exe (PID: 8200)
- runaway.exe (PID: 8260)
- runaway.exe (PID: 8316)
- runaway.exe (PID: 8372)
- runaway.exe (PID: 8540)
- runaway.exe (PID: 8480)
- runaway.exe (PID: 8600)
- runaway.exe (PID: 8656)
Executable content was dropped or overwritten
- chrome.exe (PID: 4136)
- WinRAR.exe (PID: 7200)
Application launched itself
- firefox.exe (PID: 6724)
- firefox.exe (PID: 4360)
- chrome.exe (PID: 7124)
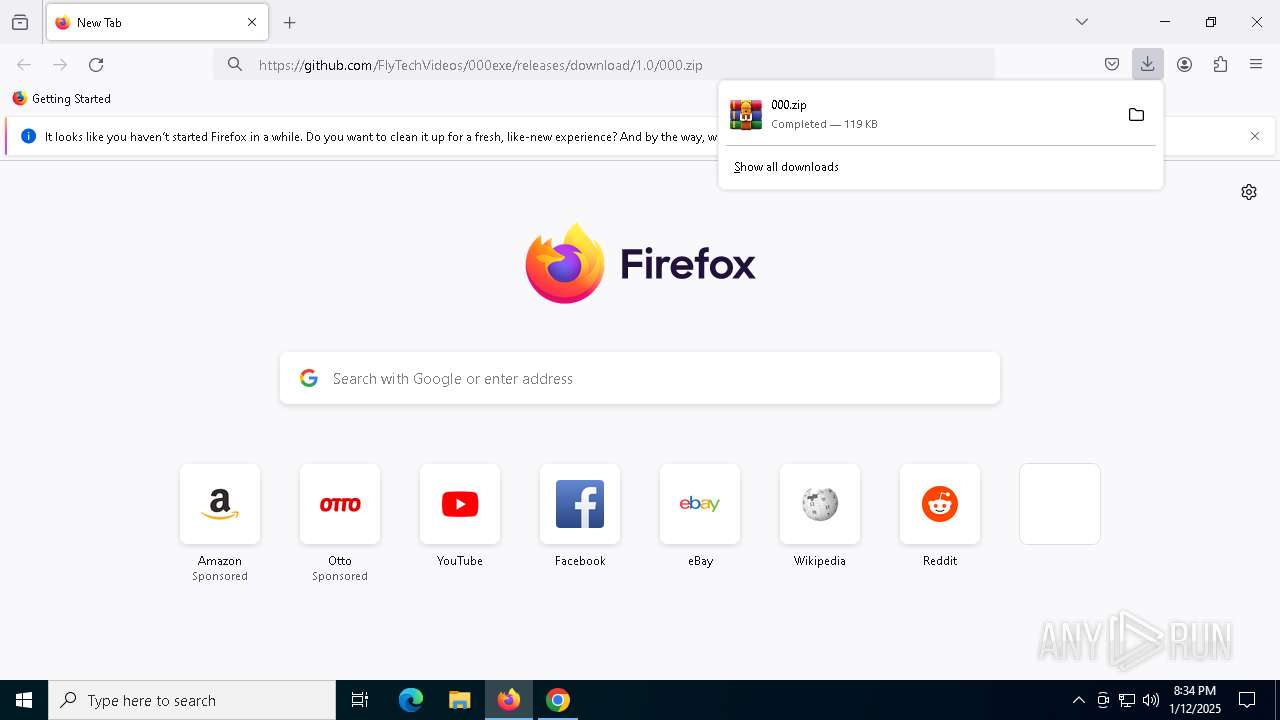
The process uses the downloaded file
- firefox.exe (PID: 4360)
- WinRAR.exe (PID: 7200)
- rniw.exe (PID: 5700)
Creates files or folders in the user directory
- 000.exe (PID: 7500)
Create files in a temporary directory
- 000.exe (PID: 7500)
Creates files in the program directory
- cmd.exe (PID: 7548)
- 000.exe (PID: 7500)
- PLUGScheduler.exe (PID: 3328)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7736)
- WMIC.exe (PID: 7872)
Checks proxy server information
- 000.exe (PID: 7500)
Reads the machine GUID from the registry
- 000.exe (PID: 7500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 1992:03:30 12:08:32+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.2 |
| CodeSize: | 172544 |
| InitializedDataSize: | 76288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29fb0 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.19041.5198 |
| ProductVersionNumber: | 10.0.19041.5198 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Compatibility Telemetry |
| FileVersion: | 10.0.19041.5198 (WinBuild.160101.0800) |
| InternalName: | CompatTelRunner.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | CompatTelRunner.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.19041.5198 |
Total processes
471
Monitored processes
229
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=6104 --field-trial-handle=1940,i,17253656414649306909,5963544174233148142,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5920 --field-trial-handle=1940,i,17253656414649306909,5963544174233148142,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5360 --field-trial-handle=1940,i,17253656414649306909,5963544174233148142,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2672 -childID 4 -isForBrowser -prefsHandle 5224 -prefMapHandle 5228 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1536 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c5ed16a5-4adc-4c98-a053-6860bd59ed9b} 4360 "\\.\pipe\gecko-crash-server-pipe.4360" 179b261fd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3256 --field-trial-handle=1940,i,17253656414649306909,5963544174233148142,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4804 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4872 -prefMapHandle 4244 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b036ef16-16e6-40fc-9c8c-48b4d012f931} 4360 "\\.\pipe\gecko-crash-server-pipe.4360" 179b14b7d10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3176 --field-trial-handle=1940,i,17253656414649306909,5963544174233148142,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2132 | ping 1.1.1.1 -n 1 -w 1000 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: UR NEXT Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | runaway.exe | C:\Users\admin\AppData\Local\Temp\86E3.tmp\runaway.exe | — | cmd.exe | |||||||||||
User: UR NEXT Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=3708 --field-trial-handle=1940,i,17253656414649306909,5963544174233148142,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
38 756
Read events
38 618
Write events
129
Delete events
9
Modification events
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | bjbddleefiddlmdfdfbgodgacjjldihj |
Value: 5CFE6AD362B9AABBD07085580BC6C063CF1C79A0B22ECB6BCBA21EECA68BA07F | |||
| (PID) Process: | (7124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | mhjfbmdgcfjbbpaeojofohoefgiehjai |
Value: F6EE482B70E472BD0FE04C8E130D7E2A0D87334BDC8F199AD874C100863BC5BE | |||
Executable files
13
Suspicious files
598
Text files
487
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13812a.TMP | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF138139.TMP | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF138139.TMP | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF138139.TMP | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF138139.TMP | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
151
DNS requests
202
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6800 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6800 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6588 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6588 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6588 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6588 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 92.123.104.34:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
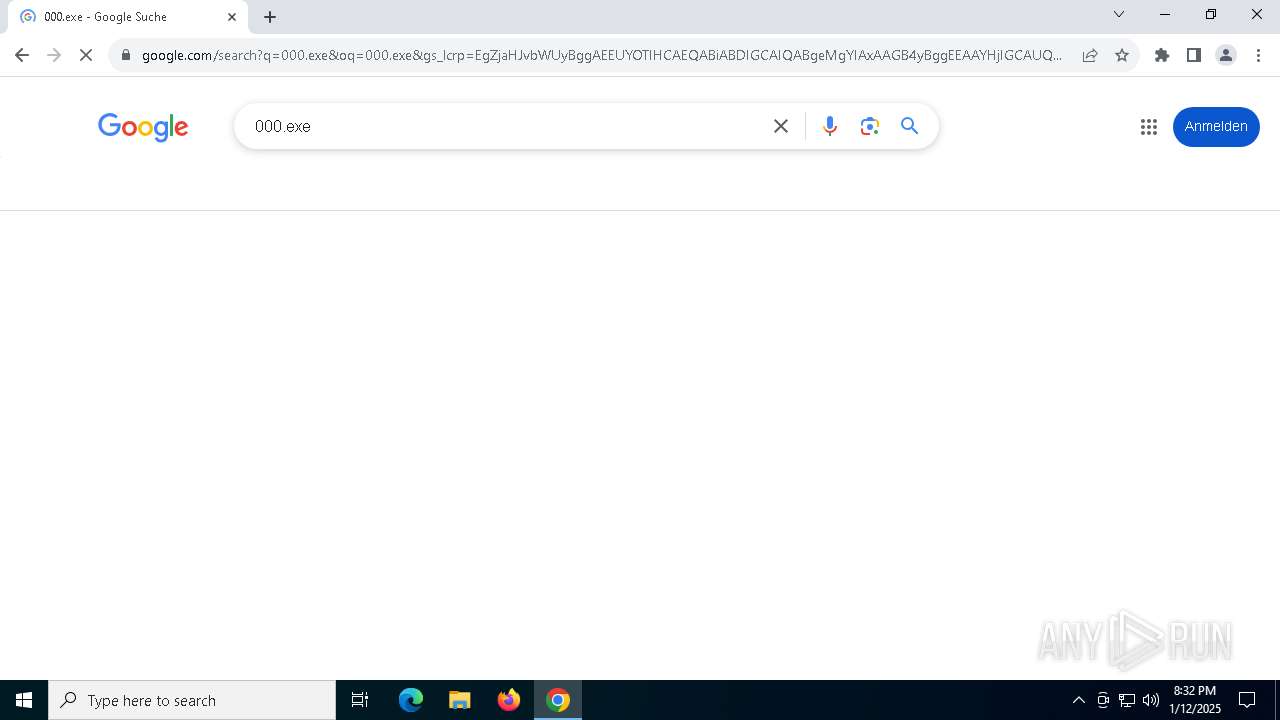
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |