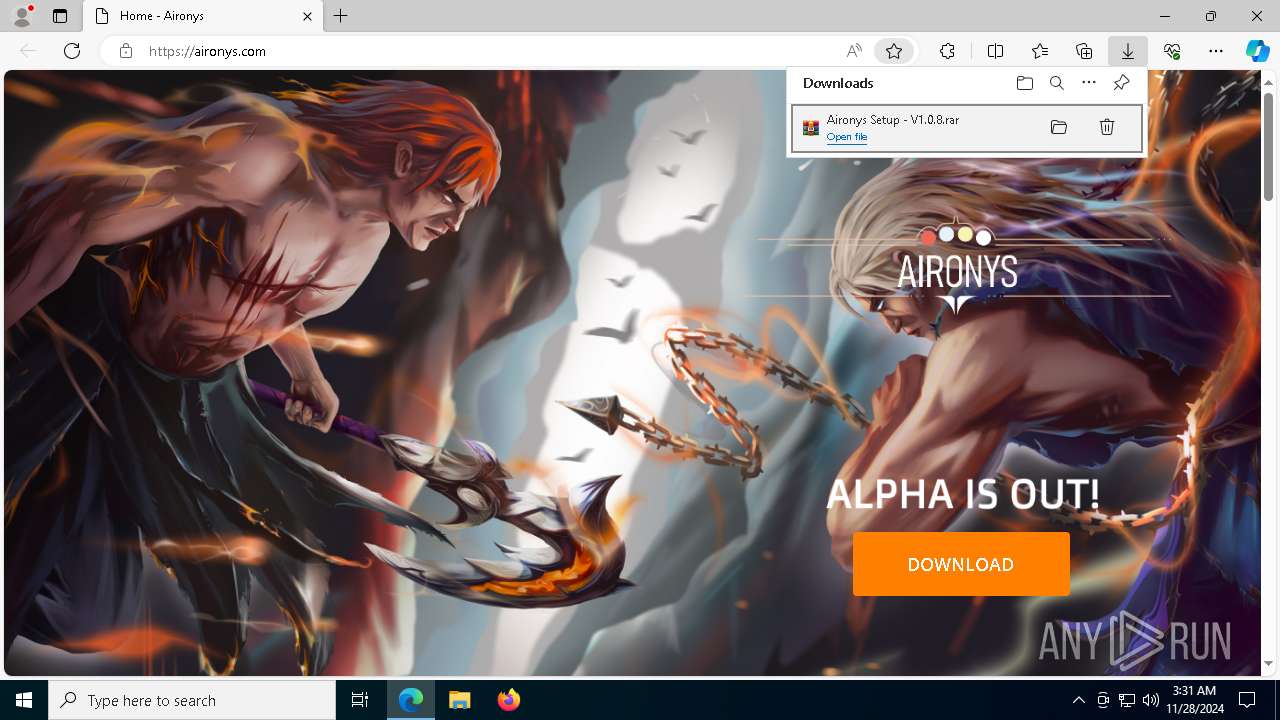
| URL: | https://aironys.com/ |
| Full analysis: | https://app.any.run/tasks/1c2388ca-1279-40e1-9917-18fd7ac79c36 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
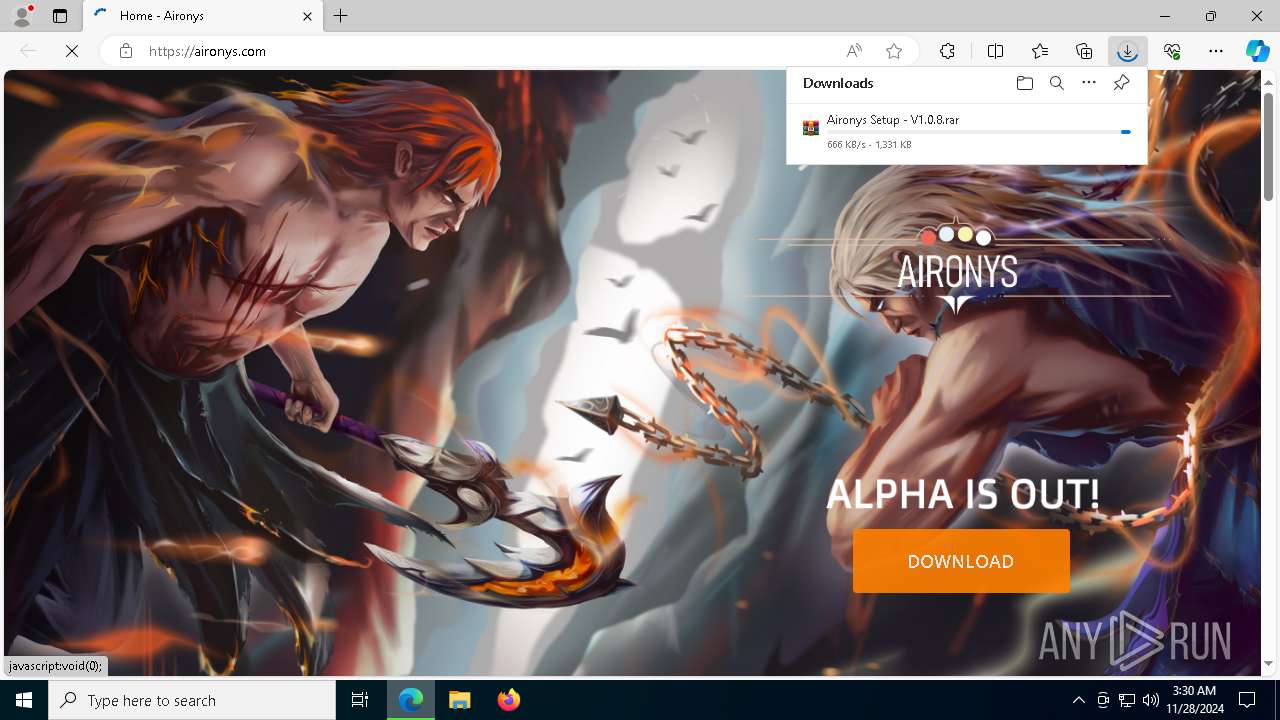
| Analysis date: | November 28, 2024, 03:30:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7C208814701CE8E9D0A09232CFFC4B43 |
| SHA1: | F48D29740238C0434E8E2BC99EA08E112A960128 |
| SHA256: | AE70817265FEB6673E888B2CC943146502F5D74E9427CB1001806A135A325100 |
| SSDEEP: | 3:N8JWZIKn:2MIK |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 6932)
- cmd.exe (PID: 6904)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 1416)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 6912)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 1192)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 8064)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 1200)
- cmd.exe (PID: 7252)
- cmd.exe (PID: 6660)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 6420)
- cmd.exe (PID: 6492)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 4512)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 3936)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 3060)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 236)
- cmd.exe (PID: 5000)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8812)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 6860)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 8928)
- cmd.exe (PID: 8792)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8804)
- cmd.exe (PID: 8324)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 8880)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 8816)
- cmd.exe (PID: 8640)
- cmd.exe (PID: 6920)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 9048)
- cmd.exe (PID: 8324)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 8664)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 9024)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 8732)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 4388)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 9076)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 6812)
- cmd.exe (PID: 3128)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 8272)
- cmd.exe (PID: 8332)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 848)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 8224)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 8436)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 8496)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 6624)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 4388)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 8352)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 628)
- cmd.exe (PID: 8224)
- cmd.exe (PID: 8436)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 9048)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 6920)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 8784)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 8492)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 8652)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8704)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 8732)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 4504)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 6784)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 8308)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 4504)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 3920)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 6704)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 8284)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 8492)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 8732)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 5876)
- cmd.exe (PID: 8)
- cmd.exe (PID: 876)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 4388)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 524)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 8704)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 8876)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 9172)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 8428)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 524)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 8204)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 6424)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 8180)
- cmd.exe (PID: 8264)
- cmd.exe (PID: 396)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 640)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 9088)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 8648)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 372)
- cmd.exe (PID: 6920)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 6864)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 8876)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 644)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 8624)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 640)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 848)
- cmd.exe (PID: 8388)
- cmd.exe (PID: 8816)
- cmd.exe (PID: 6544)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 8740)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 9200)
- cmd.exe (PID: 8340)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 8612)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 9028)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 8204)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 8388)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 5456)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 5876)
- cmd.exe (PID: 9200)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 5268)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 5320)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 6424)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 8704)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 8880)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 1468)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 6524)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 9100)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 6200)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 7960)
- cmd.exe (PID: 644)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 5564)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8844)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 7044)
- cmd.exe (PID: 8496)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 9100)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 644)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 6200)
- cmd.exe (PID: 5792)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 8376)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 6200)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 8572)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 6888)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 5792)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 8904)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 8940)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 7200)
- cmd.exe (PID: 8496)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 8352)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 8376)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 8880)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 628)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 876)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 9116)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 8204)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 8648)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 8308)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 8740)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 9140)
- cmd.exe (PID: 6864)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 876)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 8264)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 3772)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 5872)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 628)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 8904)
- cmd.exe (PID: 4952)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 6692)
- cmd.exe (PID: 9104)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 1596)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 4500)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 6932)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 6624)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 8940)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 876)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 4204)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 8296)
- cmd.exe (PID: 876)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 9140)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 6624)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 9048)
- cmd.exe (PID: 4136)
- cmd.exe (PID: 3128)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 6348)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 8388)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 8632)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 3816)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 8)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 8704)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 9036)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 9140)
- cmd.exe (PID: 7412)
- cmd.exe (PID: 5308)
- cmd.exe (PID: 8196)
- cmd.exe (PID: 9200)
- cmd.exe (PID: 6324)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 8740)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 6076)
- cmd.exe (PID: 4228)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 880)
- cmd.exe (PID: 8252)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 848)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 5812)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 5792)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 9104)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 5308)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 768)
- cmd.exe (PID: 8960)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 5792)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 8224)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 5088)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 2412)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 6864)
- cmd.exe (PID: 8)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 6604)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 5860)
- cmd.exe (PID: 848)
- cmd.exe (PID: 6624)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 876)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5088)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 6528)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 8252)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 8904)
- cmd.exe (PID: 8972)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 4228)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 8272)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 8348)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 876)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 6880)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 4952)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 6076)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 5208)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 5192)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 4544)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 2388)
- cmd.exe (PID: 5692)
- cmd.exe (PID: 8824)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 5088)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 876)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 8492)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 7252)
- cmd.exe (PID: 5192)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 6324)
- cmd.exe (PID: 5432)
- cmd.exe (PID: 9172)
- cmd.exe (PID: 424)
- cmd.exe (PID: 8464)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 5816)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 9312)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 9024)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 5268)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 8604)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 10372)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 9932)
- cmd.exe (PID: 4056)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 9732)
- cmd.exe (PID: 11192)
- cmd.exe (PID: 10564)
- cmd.exe (PID: 9880)
- cmd.exe (PID: 9336)
- cmd.exe (PID: 9664)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 9860)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10508)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 11144)
- cmd.exe (PID: 9988)
- cmd.exe (PID: 10400)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 11248)
- cmd.exe (PID: 10356)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 880)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 9244)
- cmd.exe (PID: 9768)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 9616)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 9588)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 9652)
- cmd.exe (PID: 10532)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 10328)
- cmd.exe (PID: 9900)
- cmd.exe (PID: 6880)
- cmd.exe (PID: 9928)
- cmd.exe (PID: 1156)
- cmd.exe (PID: 8592)
- cmd.exe (PID: 10156)
- cmd.exe (PID: 10956)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 5268)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 9304)
- cmd.exe (PID: 10840)
- cmd.exe (PID: 6616)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 900)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 9880)
- cmd.exe (PID: 10196)
- cmd.exe (PID: 9320)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 10260)
- cmd.exe (PID: 10648)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 10544)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 9888)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 10552)
- cmd.exe (PID: 8972)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 10348)
- cmd.exe (PID: 10904)
- cmd.exe (PID: 10400)
- cmd.exe (PID: 10192)
- cmd.exe (PID: 10500)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 10272)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 10892)
- cmd.exe (PID: 10028)
- cmd.exe (PID: 10944)
- cmd.exe (PID: 11168)
- cmd.exe (PID: 10324)
- cmd.exe (PID: 10936)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 10064)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 10092)
- cmd.exe (PID: 10140)
- cmd.exe (PID: 10316)
- cmd.exe (PID: 9172)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 10988)
- cmd.exe (PID: 10108)
- cmd.exe (PID: 9828)
- cmd.exe (PID: 9844)
- cmd.exe (PID: 9864)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 9440)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 10032)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 10868)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 9340)
- cmd.exe (PID: 9476)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 10412)
- cmd.exe (PID: 9584)
- cmd.exe (PID: 10740)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 9492)
- cmd.exe (PID: 8632)
- cmd.exe (PID: 11216)
- cmd.exe (PID: 11196)
- cmd.exe (PID: 9452)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 11028)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 9836)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 9580)
- cmd.exe (PID: 10876)
- cmd.exe (PID: 11096)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 10516)
- cmd.exe (PID: 9980)
- cmd.exe (PID: 10148)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 5872)
- cmd.exe (PID: 9416)
- cmd.exe (PID: 2672)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10564)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 9608)
- cmd.exe (PID: 11164)
- cmd.exe (PID: 7412)
- cmd.exe (PID: 10232)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 10244)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 8144)
- cmd.exe (PID: 10820)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 6076)
- cmd.exe (PID: 10400)
- cmd.exe (PID: 9264)
- cmd.exe (PID: 9960)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 628)
- cmd.exe (PID: 9400)
- cmd.exe (PID: 11180)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 10924)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 5140)
- cmd.exe (PID: 10672)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 1468)
- cmd.exe (PID: 10548)
- cmd.exe (PID: 9536)
- cmd.exe (PID: 10376)
- cmd.exe (PID: 4388)
- cmd.exe (PID: 10048)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 10844)
- cmd.exe (PID: 9852)
- cmd.exe (PID: 10740)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 9344)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10232)
- cmd.exe (PID: 9512)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 10088)
- cmd.exe (PID: 9252)
- cmd.exe (PID: 10332)
- cmd.exe (PID: 9904)
- cmd.exe (PID: 10032)
- cmd.exe (PID: 10804)
- cmd.exe (PID: 9992)
DISCORDGRABBER has been detected (YARA)
- uJIZ7lYrzb.exe (PID: 1512)
GROWTOPIA has been detected (YARA)
- uJIZ7lYrzb.exe (PID: 1512)
Adds extension to the Windows Defender exclusion list
- uJIZ7lYrzb.exe (PID: 1512)
- cmd.exe (PID: 6136)
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 8744)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 848)
SUSPICIOUS
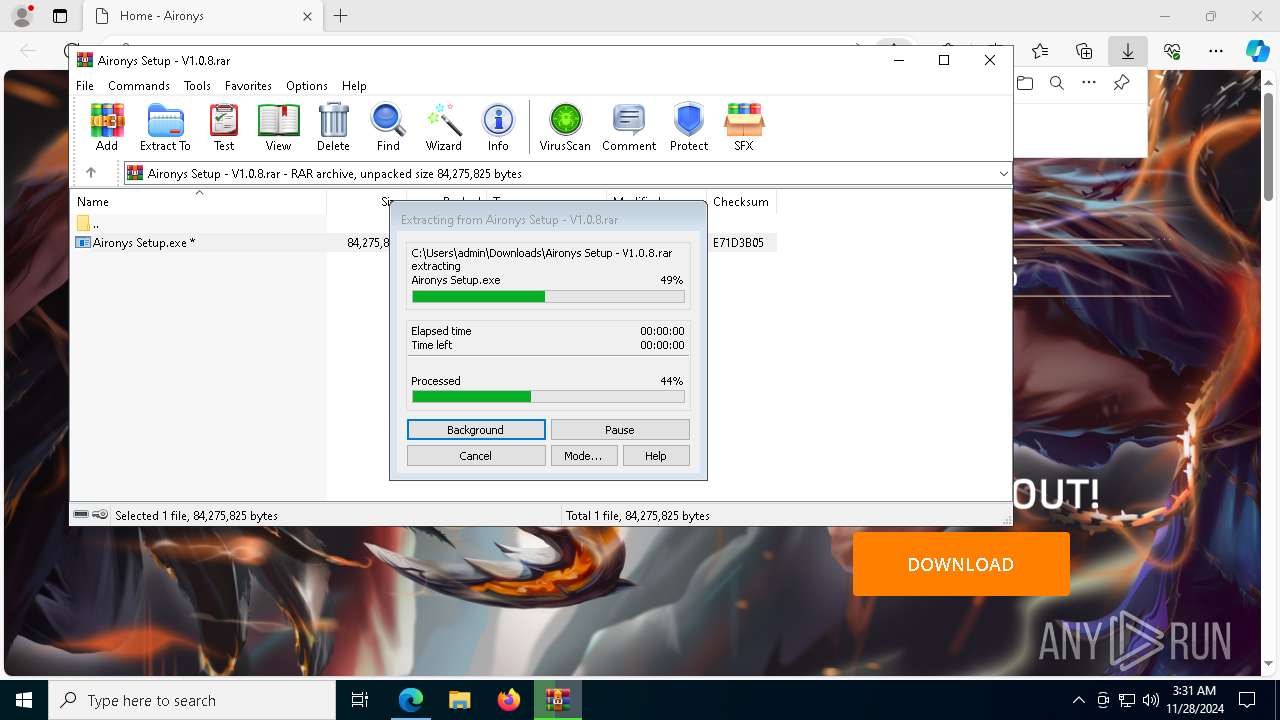
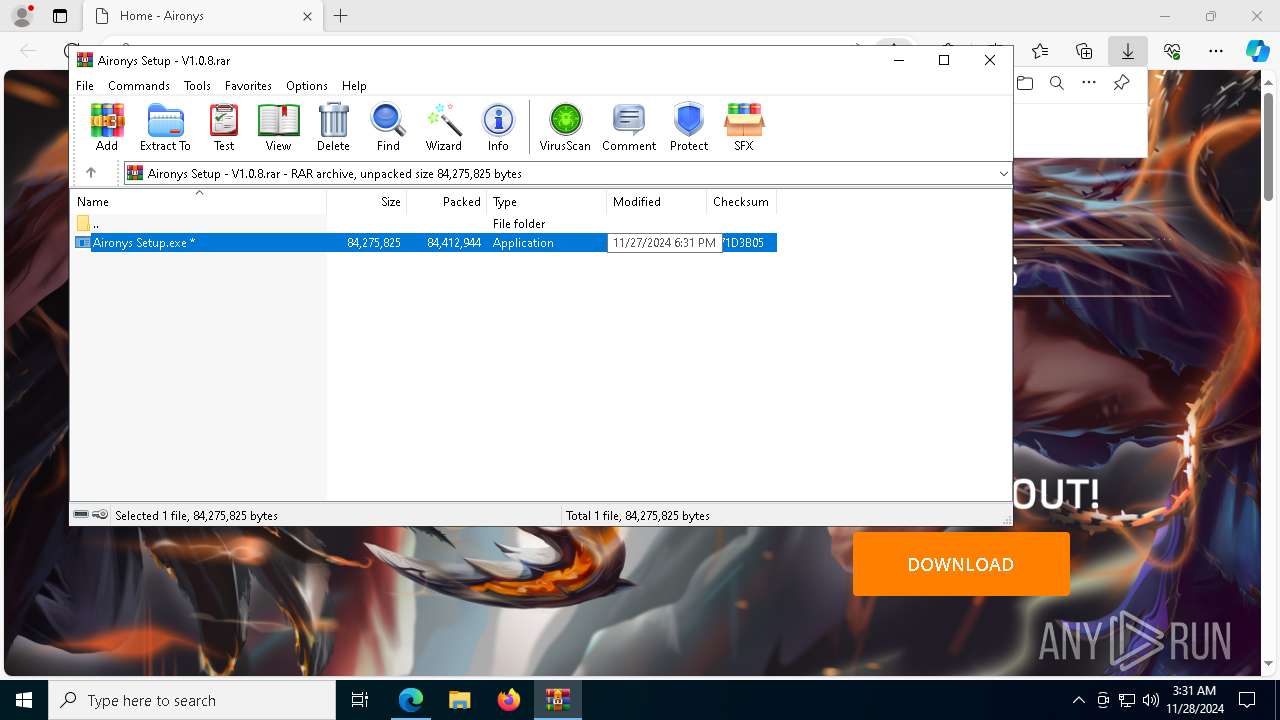
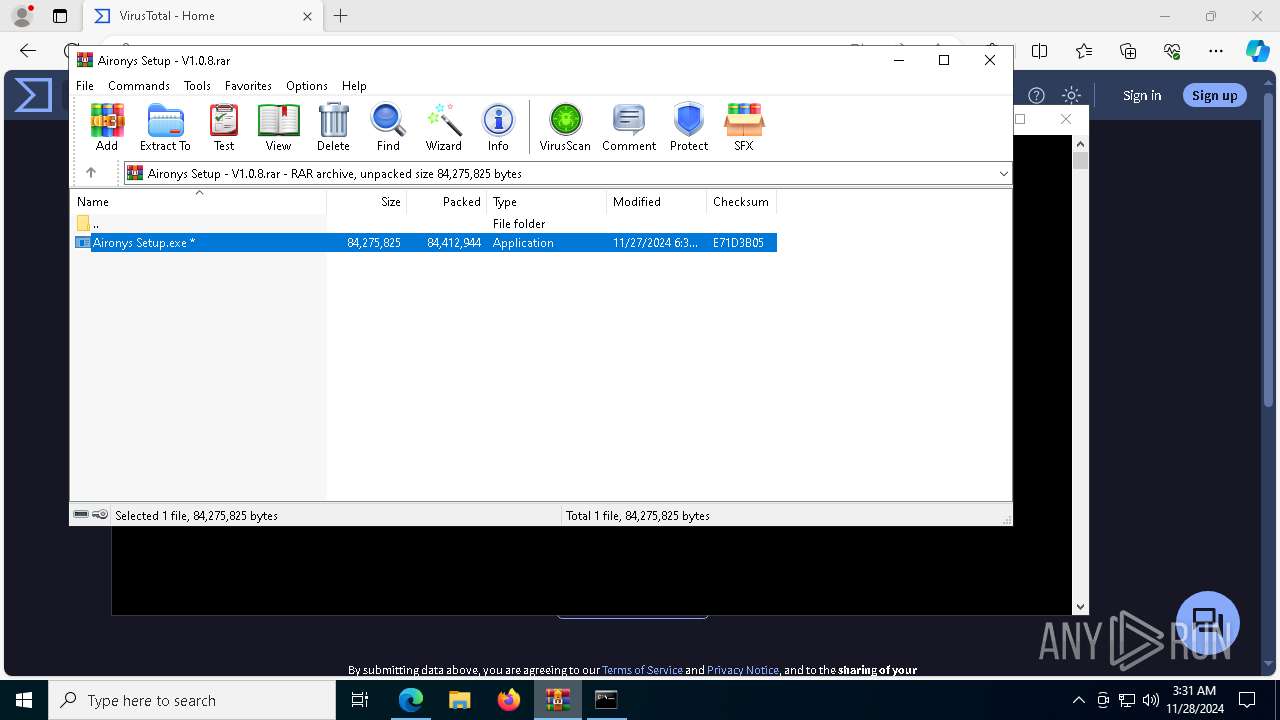
Malware-specific behavior (creating "System.dll" in Temp)
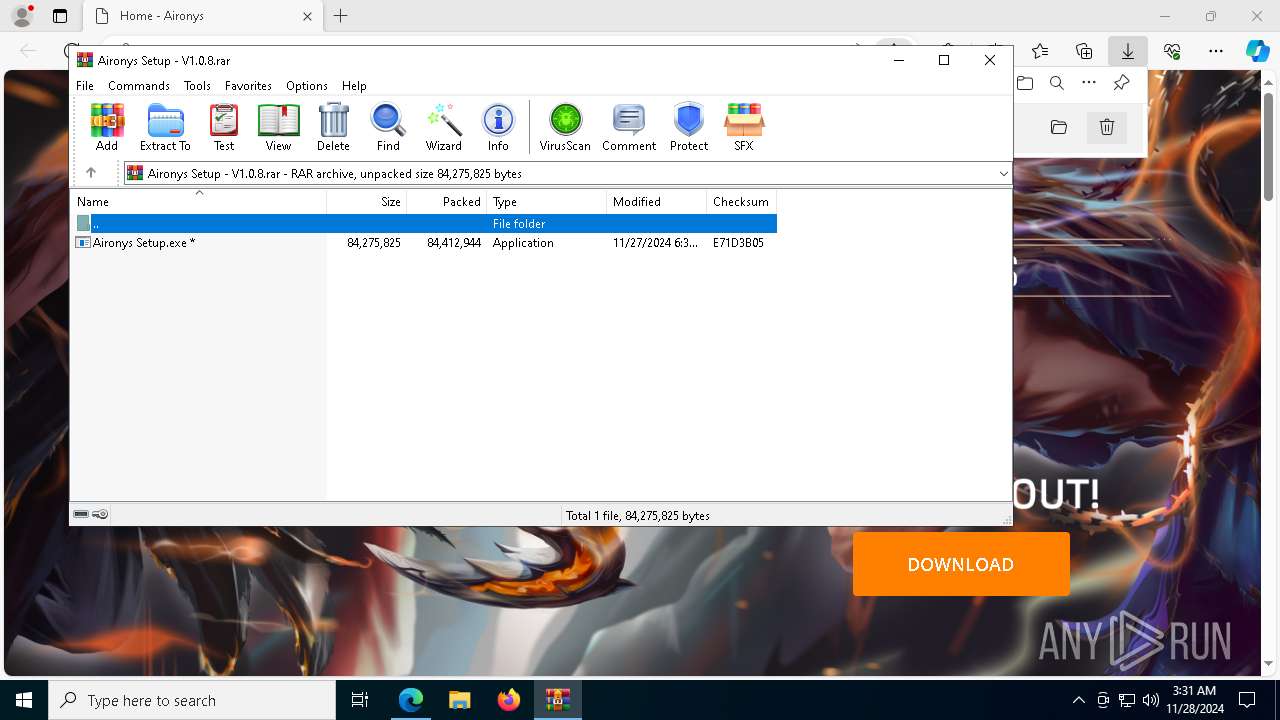
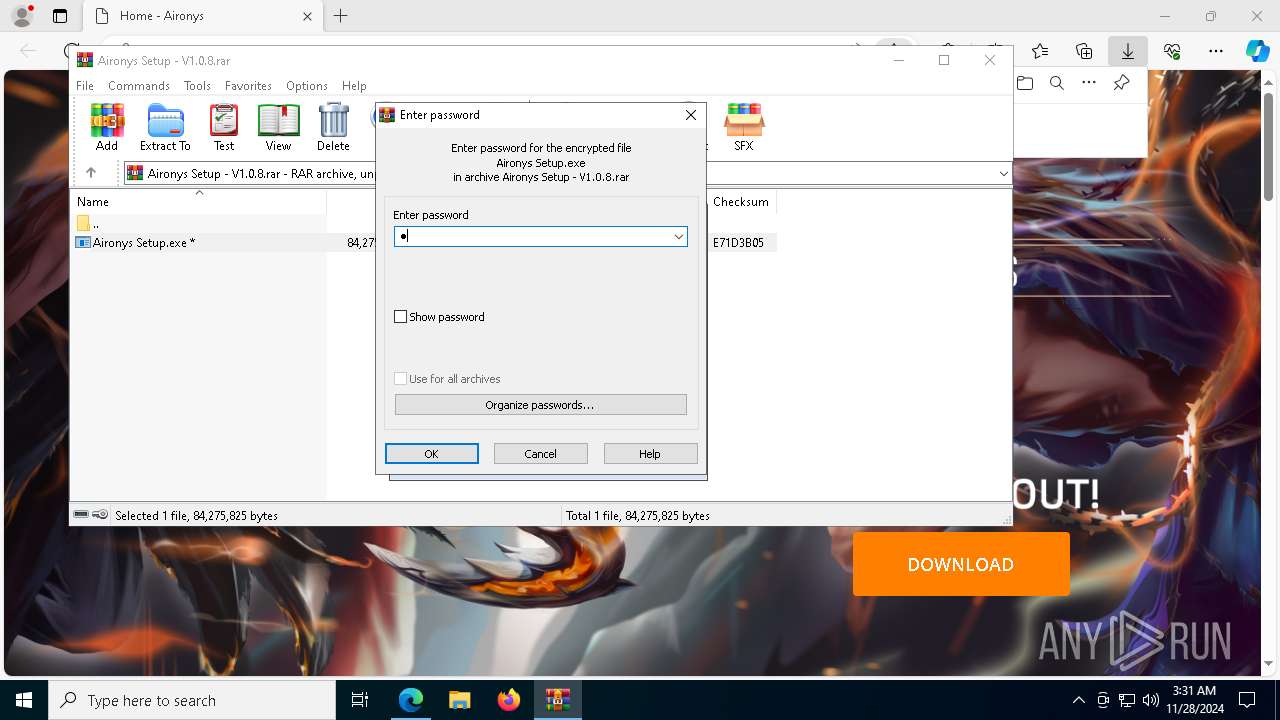
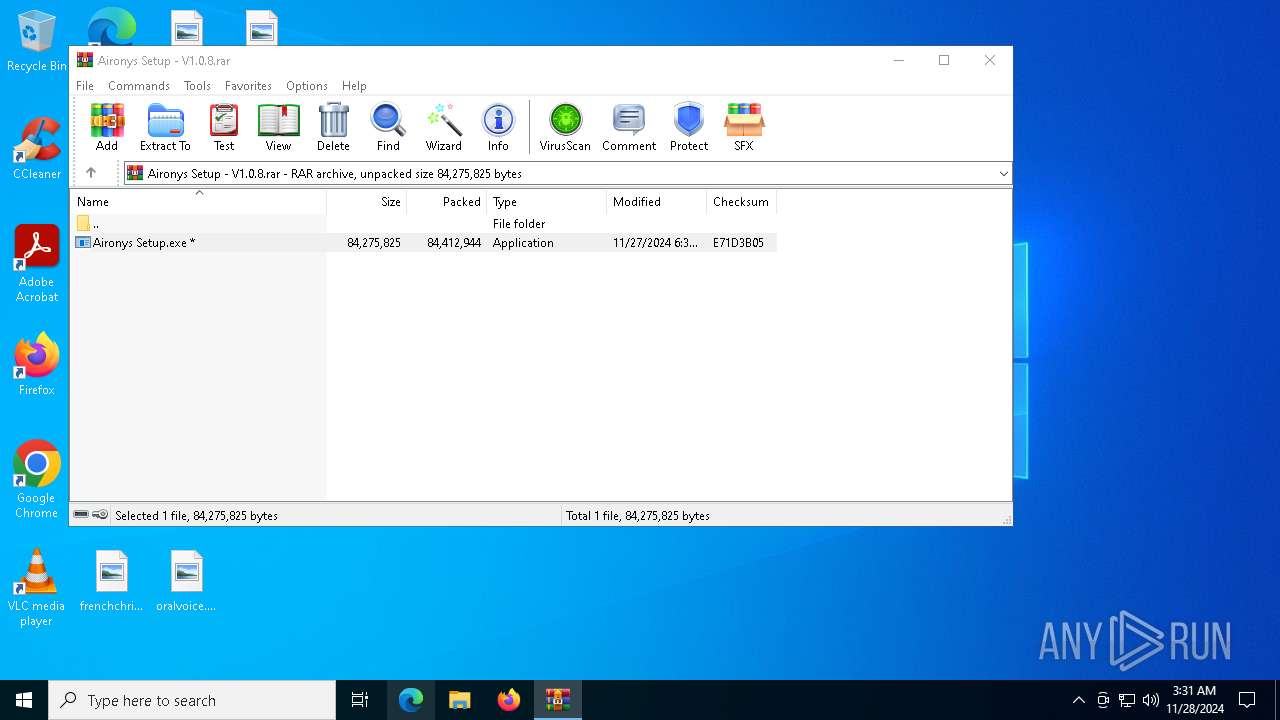
- Aironys Setup.exe (PID: 2124)
Executable content was dropped or overwritten
- Aironys Setup.exe (PID: 2124)
- uJIZ7lYrzb.exe (PID: 1512)
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Drops 7-zip archiver for unpacking
- Aironys Setup.exe (PID: 2124)
Process drops legitimate windows executable
- Aironys Setup.exe (PID: 2124)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 6360)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 7264)
Application launched itself
- uJIZ7lYrzb.exe (PID: 1512)
Starts process via Powershell
- powershell.exe (PID: 4512)
- powershell.exe (PID: 8628)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 1616)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3680)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 6136)
- downloaded.exe (PID: 1864)
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Get information on the list of running processes
- uJIZ7lYrzb.exe (PID: 1512)
- cmd.exe (PID: 7116)
- cmd.exe (PID: 6440)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4536)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 6764)
- cmd.exe (PID: 7156)
- cmd.exe (PID: 6648)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 5076)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 9048)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 396)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 8812)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 8996)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 8532)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 6596)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 8296)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 8892)
- cmd.exe (PID: 8928)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 6404)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 7064)
- cmd.exe (PID: 4132)
- cmd.exe (PID: 4668)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 8428)
- cmd.exe (PID: 6544)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 9008)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 8552)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 5876)
- cmd.exe (PID: 6172)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 396)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 9088)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 9076)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 628)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 8700)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6784)
- cmd.exe (PID: 8264)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 8604)
- cmd.exe (PID: 396)
- cmd.exe (PID: 8732)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 6168)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 1864)
- cmd.exe (PID: 8972)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 876)
- cmd.exe (PID: 6784)
- cmd.exe (PID: 6552)
- cmd.exe (PID: 8704)
- cmd.exe (PID: 7624)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 8856)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 244)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 8336)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 8336)
- cmd.exe (PID: 8632)
- cmd.exe (PID: 6364)
- cmd.exe (PID: 6756)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 556)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 8652)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 8284)
- cmd.exe (PID: 5732)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8856)
- cmd.exe (PID: 644)
- cmd.exe (PID: 6348)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 9036)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 244)
- cmd.exe (PID: 8920)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 8624)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 6784)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 6524)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 6696)
- cmd.exe (PID: 8612)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 4576)
- cmd.exe (PID: 8360)
- cmd.exe (PID: 5080)
- cmd.exe (PID: 8856)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 9116)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 6524)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 8360)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 6828)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 8632)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 8204)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 8456)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 8376)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 9048)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 880)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 8844)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8592)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 9048)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 8632)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 9028)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 628)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 5864)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 6864)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 5140)
- cmd.exe (PID: 5688)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 1888)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 8616)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 6440)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 8852)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 6748)
- cmd.exe (PID: 244)
- cmd.exe (PID: 6452)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 5692)
- cmd.exe (PID: 4576)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 4388)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 8300)
- cmd.exe (PID: 8216)
- cmd.exe (PID: 8716)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 8240)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 6552)
- cmd.exe (PID: 9024)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 3052)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 4872)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 5816)
- cmd.exe (PID: 8332)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 7220)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8628)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 556)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 8476)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 6888)
- cmd.exe (PID: 5688)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 8964)
- cmd.exe (PID: 10112)
- cmd.exe (PID: 10724)
- cmd.exe (PID: 10892)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 10012)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 10500)
- cmd.exe (PID: 10316)
- cmd.exe (PID: 9896)
- cmd.exe (PID: 9344)
- cmd.exe (PID: 11116)
- cmd.exe (PID: 9172)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 8492)
- cmd.exe (PID: 2164)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 9484)
- cmd.exe (PID: 9648)
- cmd.exe (PID: 10208)
- cmd.exe (PID: 9424)
- cmd.exe (PID: 9636)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9588)
- cmd.exe (PID: 10484)
- cmd.exe (PID: 10152)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 10308)
- cmd.exe (PID: 644)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 2112)
- cmd.exe (PID: 9280)
- cmd.exe (PID: 9920)
- cmd.exe (PID: 10116)
- cmd.exe (PID: 8784)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 8816)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 9352)
- cmd.exe (PID: 9256)
- cmd.exe (PID: 10156)
- cmd.exe (PID: 10704)
- cmd.exe (PID: 10556)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 628)
- cmd.exe (PID: 10188)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 3144)
- cmd.exe (PID: 5240)
- cmd.exe (PID: 10376)
- cmd.exe (PID: 11228)
- cmd.exe (PID: 9056)
- cmd.exe (PID: 9588)
- cmd.exe (PID: 5268)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 10824)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 9872)
- cmd.exe (PID: 6788)
- cmd.exe (PID: 10204)
- cmd.exe (PID: 10832)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 9380)
- cmd.exe (PID: 10404)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 9716)
- cmd.exe (PID: 11108)
- cmd.exe (PID: 5692)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 9516)
- cmd.exe (PID: 6932)
- cmd.exe (PID: 10872)
- cmd.exe (PID: 9496)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 8564)
Cryptography encrypted command line is found
- cmd.exe (PID: 8188)
- powershell.exe (PID: 8060)
- powershell.exe (PID: 7360)
- cmd.exe (PID: 3540)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 7512)
Starts CMD.EXE for commands execution
- uJIZ7lYrzb.exe (PID: 1512)
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
MS Edge headless start
- msedge.exe (PID: 8436)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8356)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8208)
Script adds exclusion extension to Windows Defender
- cmd.exe (PID: 6136)
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5320)
The executable file from the user directory is run by the CMD process
- downloaded.exe (PID: 1864)
Manipulates environment variables
- powershell.exe (PID: 6664)
- powershell.exe (PID: 7644)
Script adds exclusion path to Windows Defender
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Process uninstalls Windows update
- wusa.exe (PID: 4520)
- wusa.exe (PID: 7828)
The process executes via Task Scheduler
- powershell.exe (PID: 8492)
- powershell.exe (PID: 4036)
Uses powercfg.exe to modify the power settings
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Executes as Windows Service
- updater.exe (PID: 4132)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 8492)
- powershell.exe (PID: 4036)
Starts SC.EXE for service management
- downloaded.exe (PID: 6632)
- updater.exe (PID: 4132)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 4132)
Executes application which crashes
- cmd.exe (PID: 8944)
- cmd.exe (PID: 6544)
INFO
Application launched itself
- msedge.exe (PID: 6208)
- msedge.exe (PID: 6028)
- chrome.exe (PID: 7080)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 8176)
Manual execution by a user
- msedge.exe (PID: 6028)
The executable file from the user directory is run by the Powershell process
- downloaded.exe (PID: 6632)
Executable content was dropped or overwritten
- chrome.exe (PID: 5812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
5 709
Monitored processes
5 566
Malicious processes
5
Suspicious processes
1 277
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | taskkill /F /IM processhacker.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | taskkill /F /IM processhacker.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /F /IM immunitydebugger.exe" | C:\Windows\System32\cmd.exe | — | uJIZ7lYrzb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | taskkill /F /IM processhacker.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | taskkill /F /IM processhacker.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /F /IM immunitydebugger.exe" | C:\Windows\System32\cmd.exe | — | uJIZ7lYrzb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /F /IM wireshark.exe" | C:\Windows\System32\cmd.exe | — | uJIZ7lYrzb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
44 519
Read events
44 458
Write events
61
Delete events
0
Modification events
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C70AEEFC86862F00 | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 70D301FD86862F00 | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {818FBEBD-DD7D-48E2-9F80-ED1BE8A896DD} | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B1444FBE-8675-418B-8AC5-03E249BC01F7} | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F905695-0964-410F-9A99-7F50BBAC3693} | |||
| (PID) Process: | (6208) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2F3735E4-1F1A-4A48-8F5A-B2F450CB99B0} | |||
Executable files
53
Suspicious files
1 008
Text files
260
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1357e7.TMP | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1357e7.TMP | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1357f7.TMP | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1357e7.TMP | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135806.TMP | — | |
MD5:— | SHA256:— | |||
| 6208 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
197
DNS requests
226
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3628 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059272&P2=404&P3=2&P4=dtz5lV7aR5qWUol3OSNOiZA5QC58J8WSQbZn9h78AE%2fvmjbqu4gMhBZVp9mrvzxHTjWlWjByJviY06bPnM9cEA%3d%3d | unknown | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7568 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059272&P2=404&P3=2&P4=dtz5lV7aR5qWUol3OSNOiZA5QC58J8WSQbZn9h78AE%2fvmjbqu4gMhBZVp9mrvzxHTjWlWjByJviY06bPnM9cEA%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059272&P2=404&P3=2&P4=dtz5lV7aR5qWUol3OSNOiZA5QC58J8WSQbZn9h78AE%2fvmjbqu4gMhBZVp9mrvzxHTjWlWjByJviY06bPnM9cEA%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059272&P2=404&P3=2&P4=dtz5lV7aR5qWUol3OSNOiZA5QC58J8WSQbZn9h78AE%2fvmjbqu4gMhBZVp9mrvzxHTjWlWjByJviY06bPnM9cEA%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059272&P2=404&P3=2&P4=dtz5lV7aR5qWUol3OSNOiZA5QC58J8WSQbZn9h78AE%2fvmjbqu4gMhBZVp9mrvzxHTjWlWjByJviY06bPnM9cEA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5004 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6208 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
aironys.com |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
6552 | msedge.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
6552 | msedge.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|