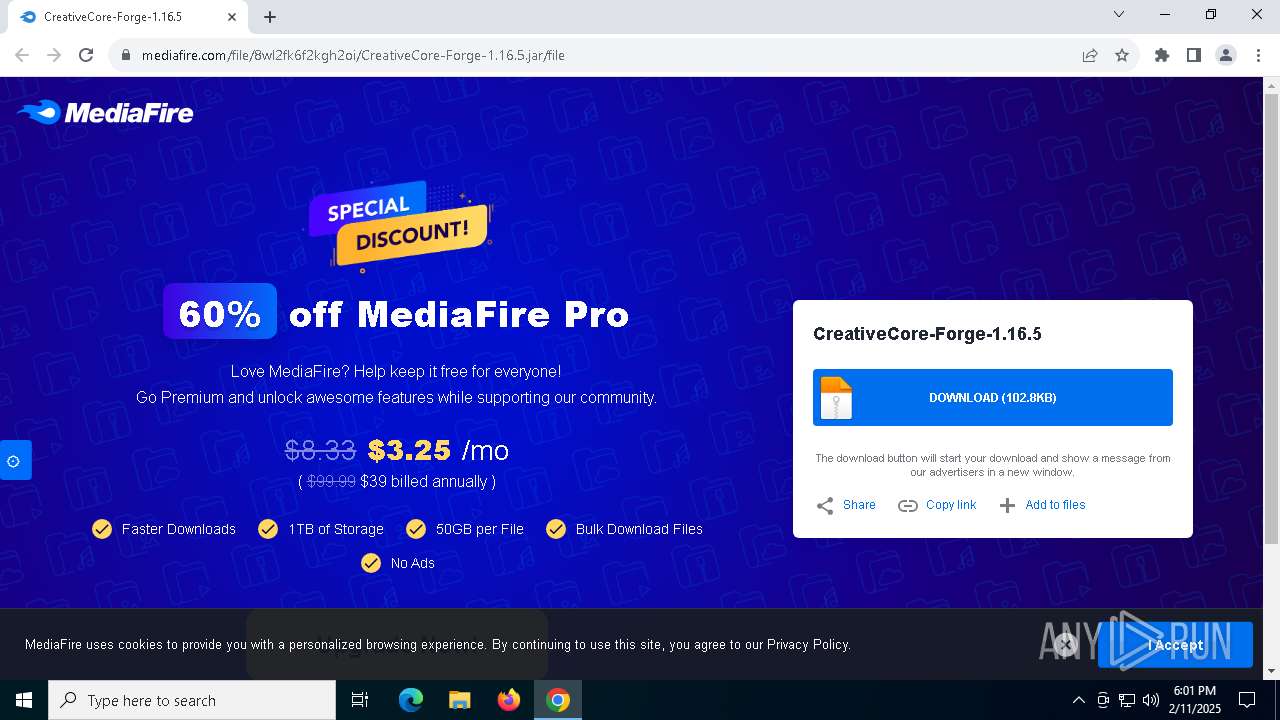
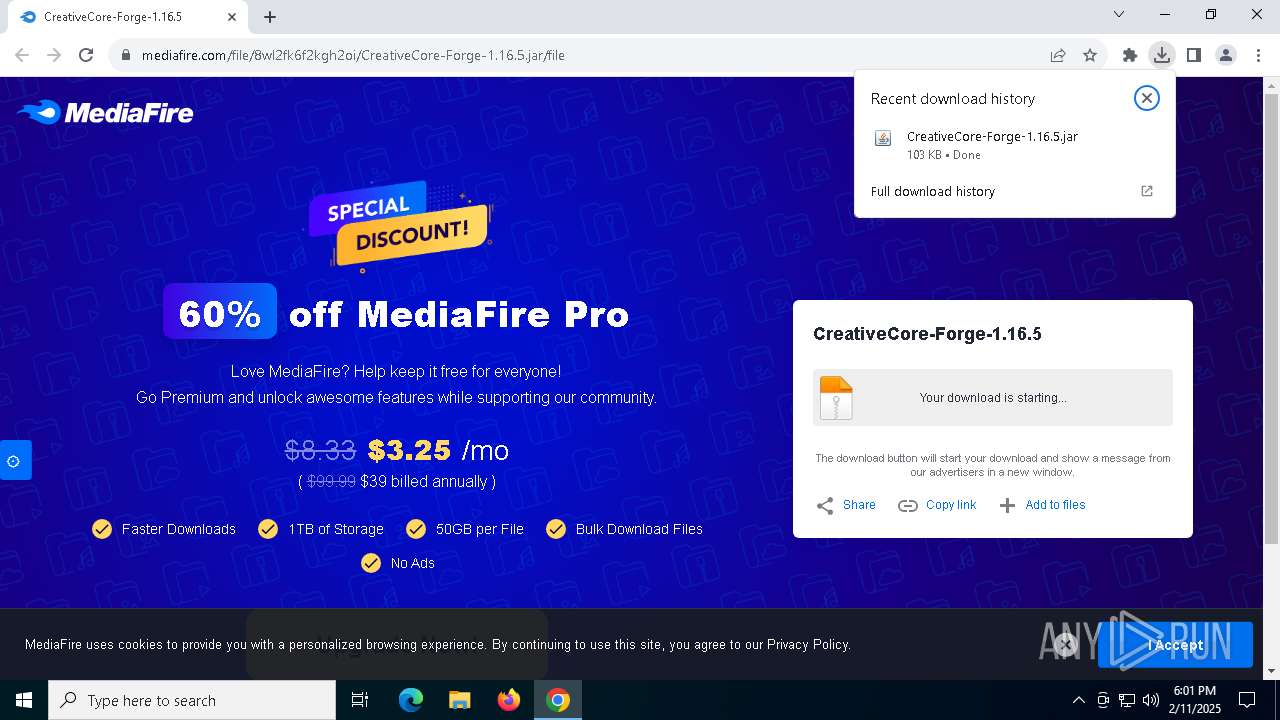
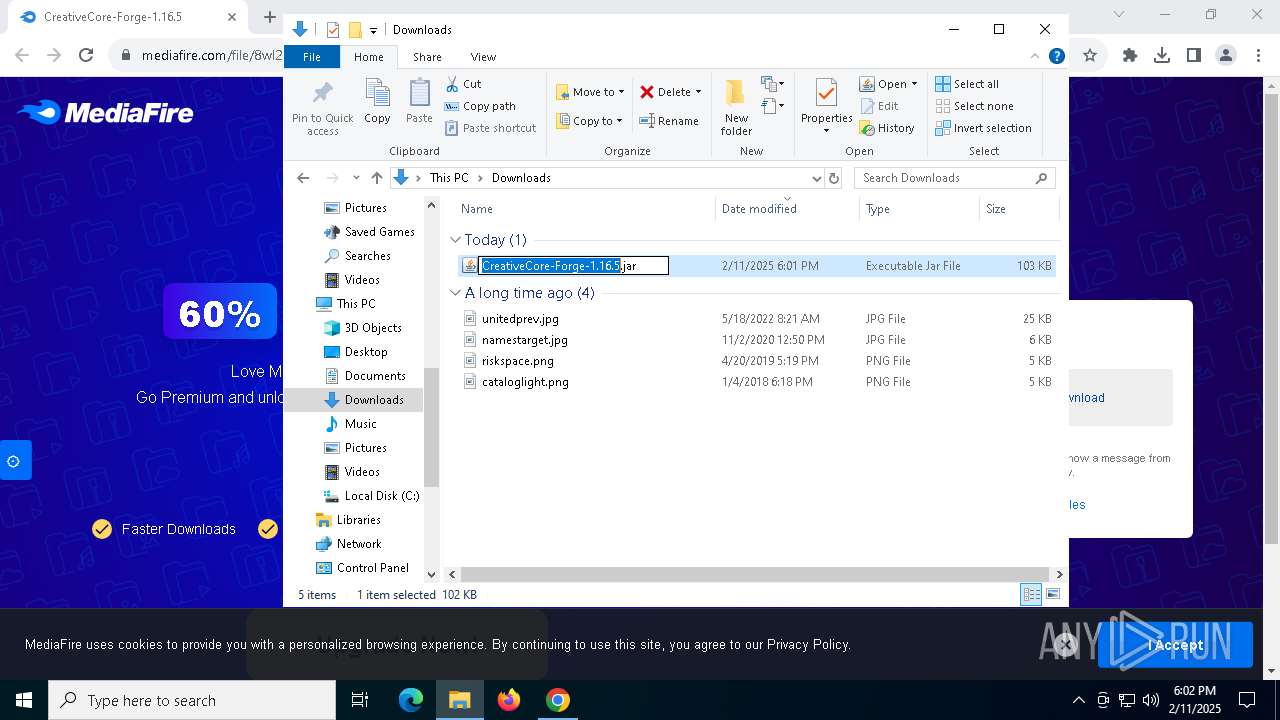
| URL: | https://www.mediafire.com/file/8wl2fk6f2kgh2oi/CreativeCore-Forge-1.16.5.jar/file |
| Full analysis: | https://app.any.run/tasks/795cfc69-0155-4f53-97aa-4ea9640d5326 |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2025, 18:01:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 404EA112E96FFD497FD8EA7F9B779883 |
| SHA1: | 24E2A516B9658606C2C2EE11D63C32E4DE5868FA |
| SHA256: | AE6AECB1BC9F48D60CD15C46981781C0B9DB489236E4C2117D4EC7F710448035 |
| SSDEEP: | 3:N8DSLw3eGUodBH9QaKe5UMQA4:2OLw3eG5BH9QoQX |
MALICIOUS
No malicious indicators.SUSPICIOUS
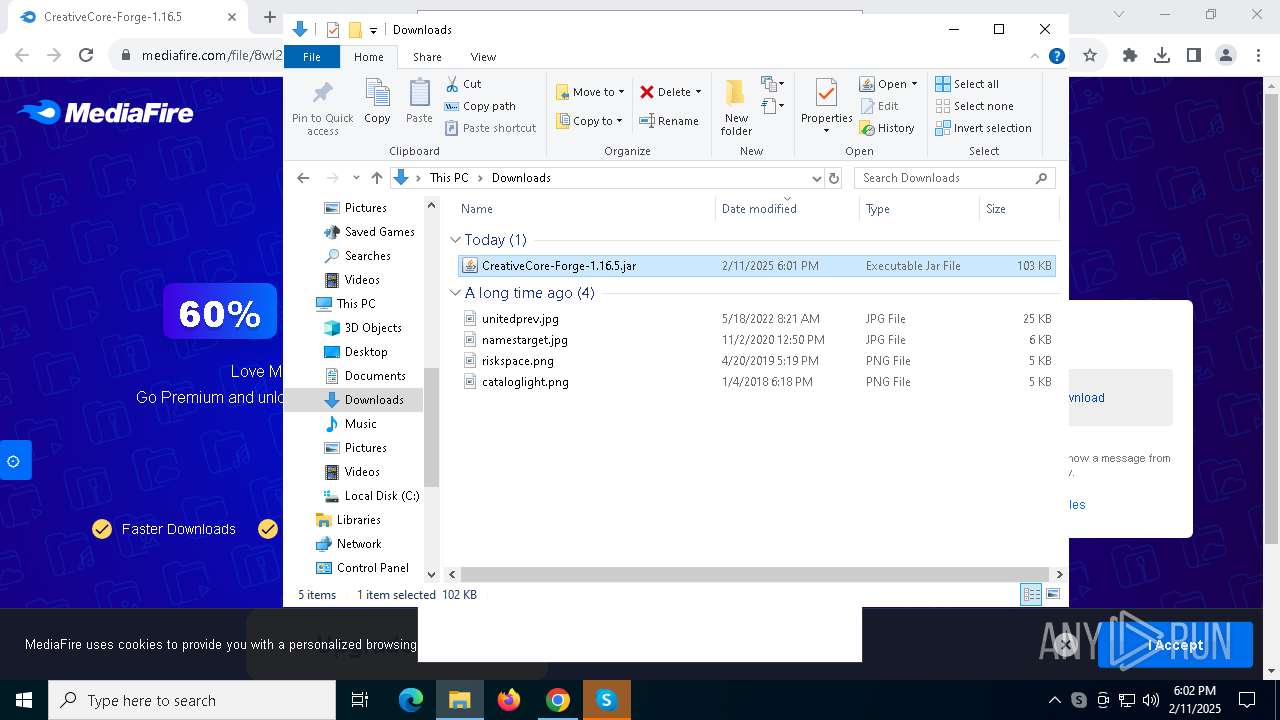
Application launched itself
- Skype.exe (PID: 5564)
Uses REG/REGEDIT.EXE to modify registry
- Skype.exe (PID: 5564)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6500)
- OpenWith.exe (PID: 4624)
Manual execution by a user
- Skype.exe (PID: 5564)
- javaw.exe (PID: 6452)
- javaw.exe (PID: 1804)
Application launched itself
- chrome.exe (PID: 6500)
Checks supported languages
- Skype.exe (PID: 5564)
- Skype.exe (PID: 2164)
- Skype.exe (PID: 7152)
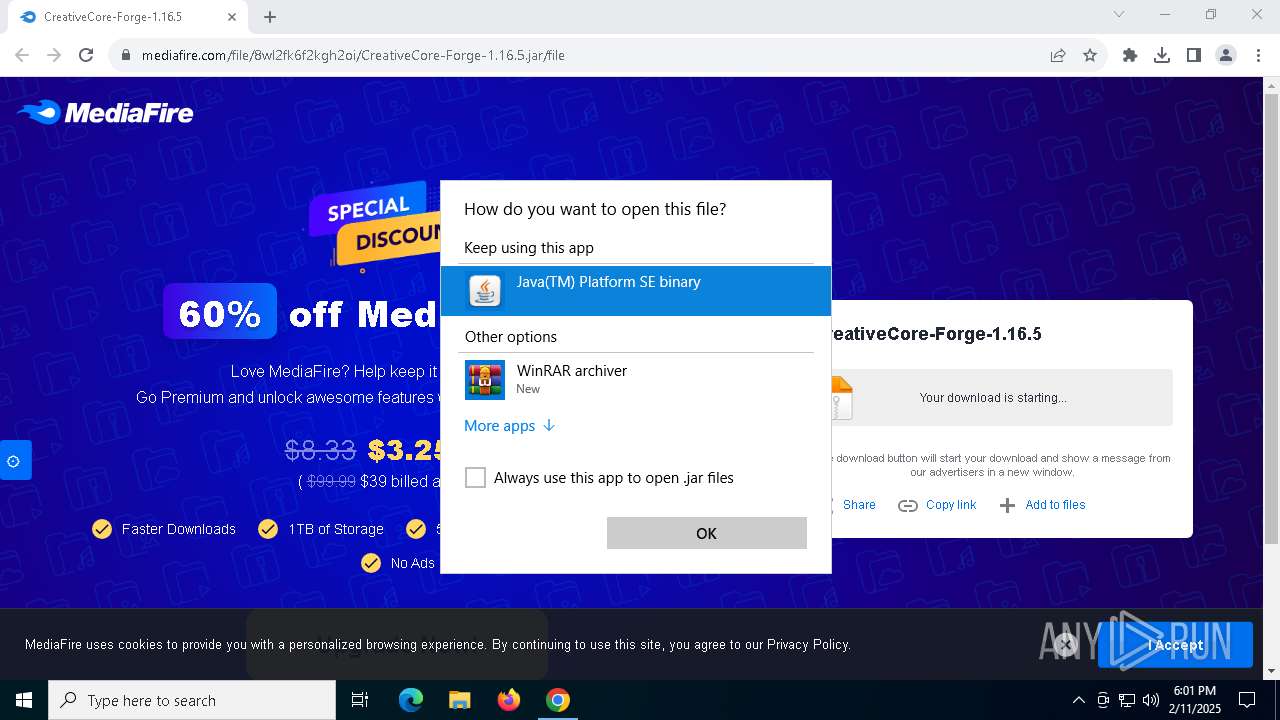
Application based on Java
- javaw.exe (PID: 4548)
- javaw.exe (PID: 6452)
- javaw.exe (PID: 1804)
Checks proxy server information
- Skype.exe (PID: 5564)
Process checks computer location settings
- Skype.exe (PID: 5564)
- Skype.exe (PID: 7152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
170
Monitored processes
38
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 520 | "C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=2080 --field-trial-handle=2156,i,12178089493177637064,16207908962562725168,131072 --enable-features=WinUseBrowserSpellChecker,WinUseHybridSpellChecker,WinrtGeolocationImplementation --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: LOW Description: Skype Version: 8.104.0.207 Modules
| |||||||||||||||
| 1572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
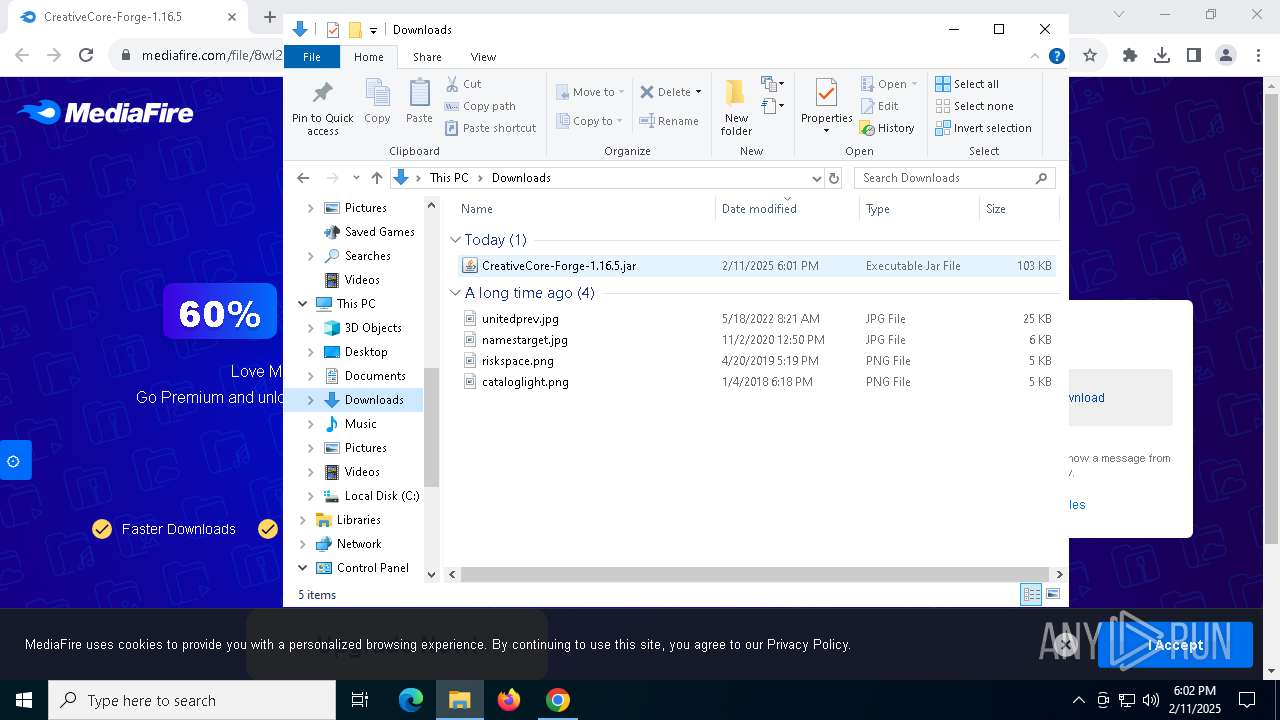
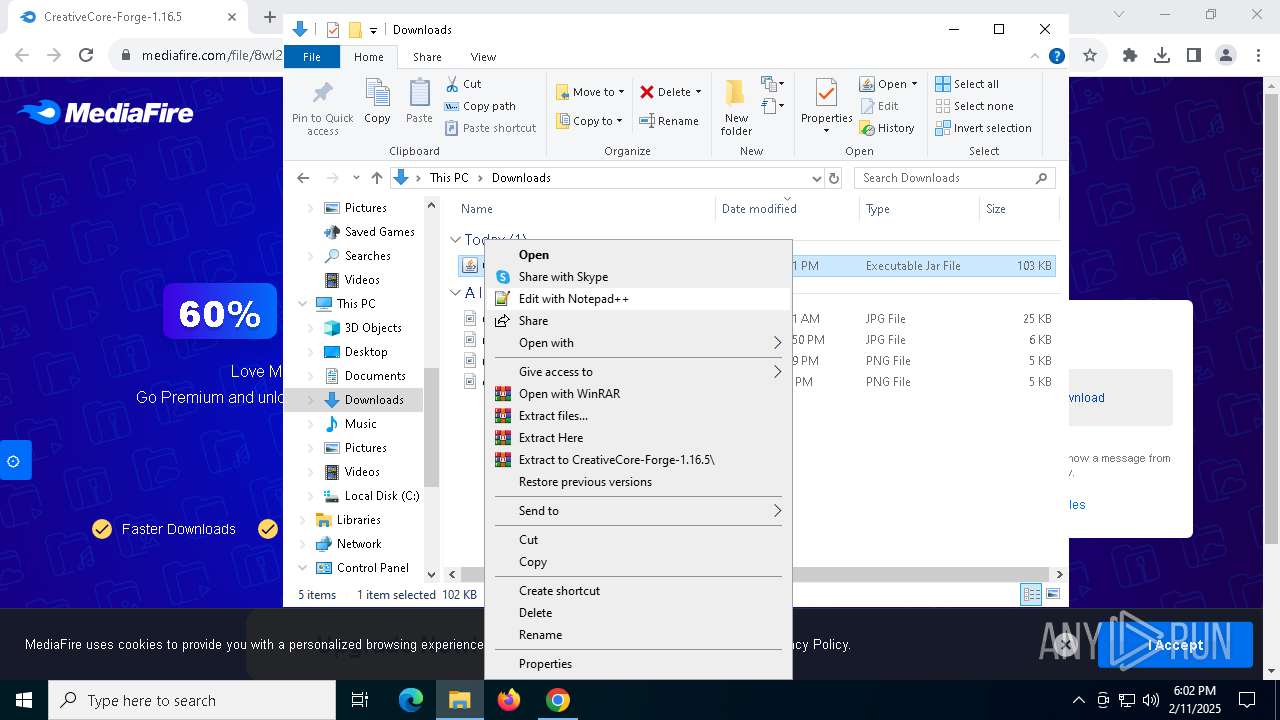
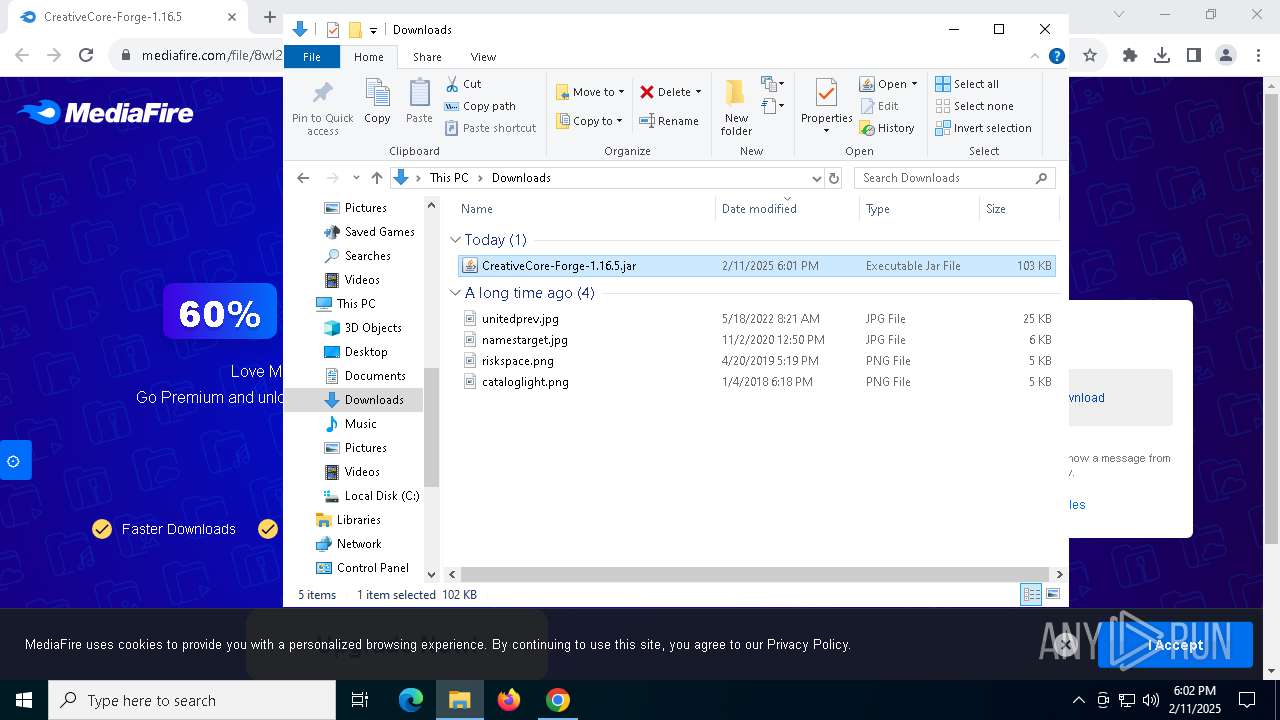
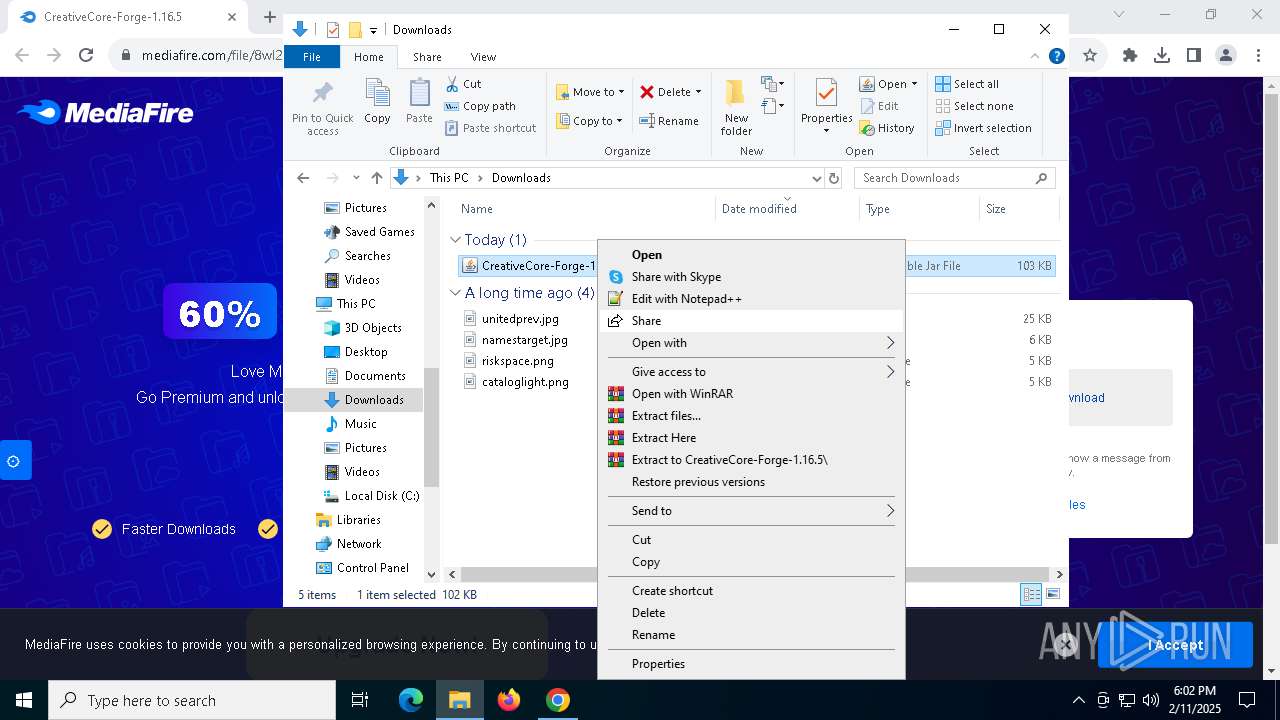
| 1804 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\Downloads\CreativeCore-Forge-1.16.5.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2164 | "C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop" --mojo-platform-channel-handle=2464 --field-trial-handle=2156,i,12178089493177637064,16207908962562725168,131072 --enable-features=WinUseBrowserSpellChecker,WinUseHybridSpellChecker,WinrtGeolocationImplementation --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Program Files (x86)\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Version: 8.104.0.207 Modules
| |||||||||||||||
| 2804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3172 | C:\WINDOWS\system32\reg.exe QUERY HKCU\Software\Microsoft\Skype /v RestartForUpdate | C:\Windows\SysWOW64\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3488 | C:\WINDOWS\system32\reg.exe QUERY HKCU\Software\Microsoft\Edge\BLBeacon /v version | C:\Windows\SysWOW64\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3732 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 058
Read events
11 028
Write events
12
Delete events
18
Modification events
| (PID) Process: | (6500) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6500) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6500) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6500) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6500) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000065E2BC02AF7CDB01 | |||
| (PID) Process: | (6500) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
| (PID) Process: | (4624) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
| (PID) Process: | (5564) Skype.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (5564) Skype.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
Executable files
0
Suspicious files
73
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF137d22.TMP | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF137d22.TMP | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF137d32.TMP | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF137d32.TMP | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF137d32.TMP | — | |
MD5:— | SHA256:— | |||
| 6500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
77
DNS requests
97
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2380 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2380 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6360 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 2.19.246.123:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6500 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6844 | chrome.exe | 104.17.151.117:443 | www.mediafire.com | CLOUDFLARENET | — | whitelisted |
6844 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
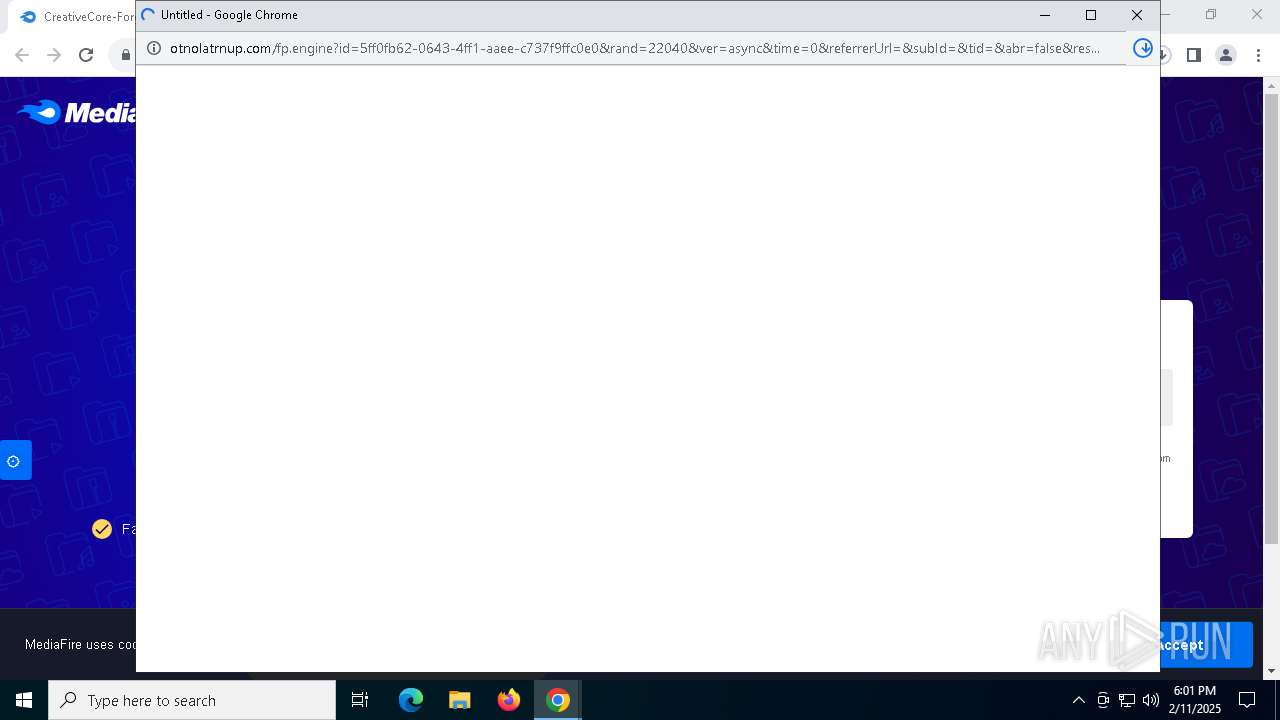
6844 | chrome.exe | 172.67.199.186:443 | the.gatekeeperconsent.com | CLOUDFLARENET | US | unknown |
6844 | chrome.exe | 104.19.208.227:443 | cdn.otnolatrnup.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
accounts.google.com |
| whitelisted |
the.gatekeeperconsent.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
static.mediafire.com |
| whitelisted |
privacy.gatekeeperconsent.com |
| unknown |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6844 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6844 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6844 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6844 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6844 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |