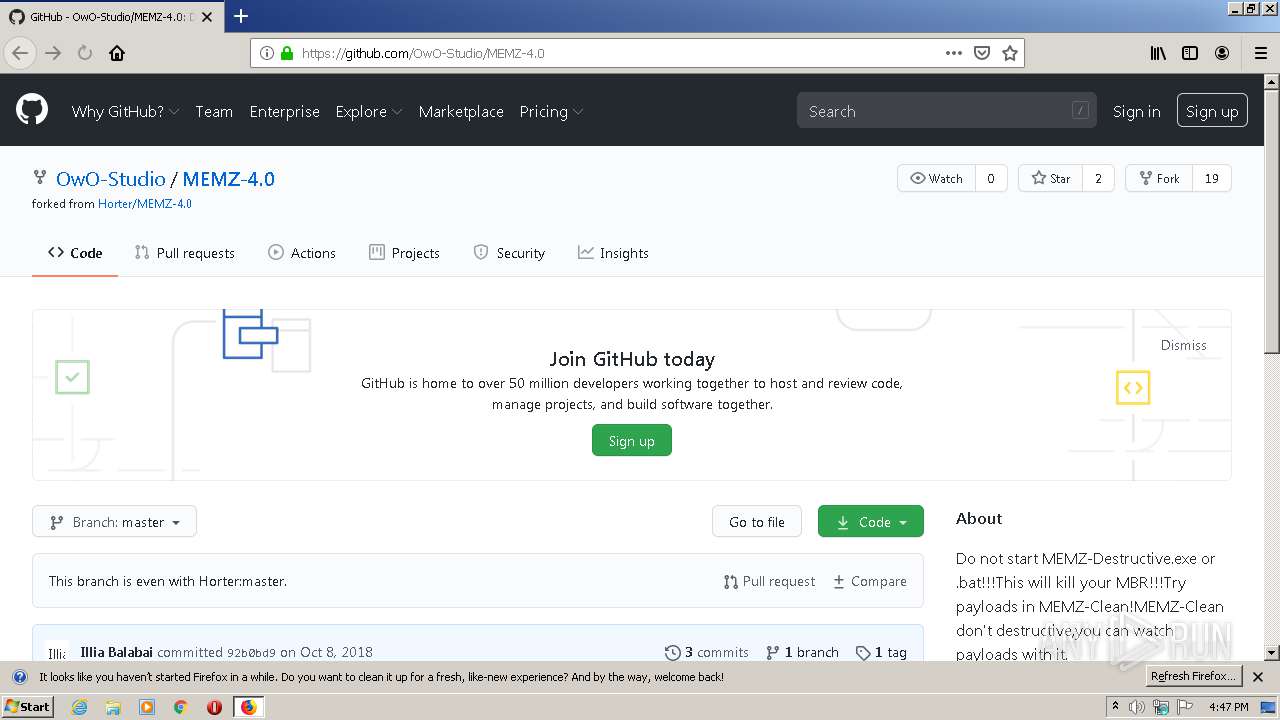
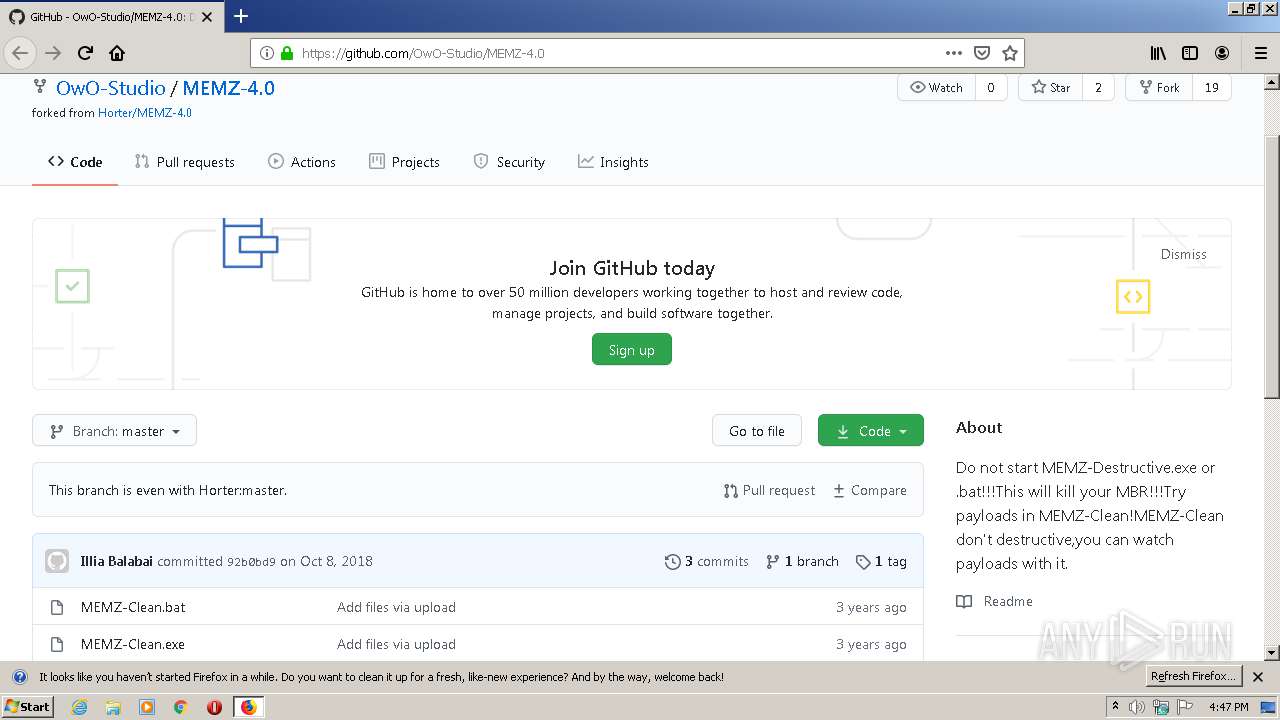
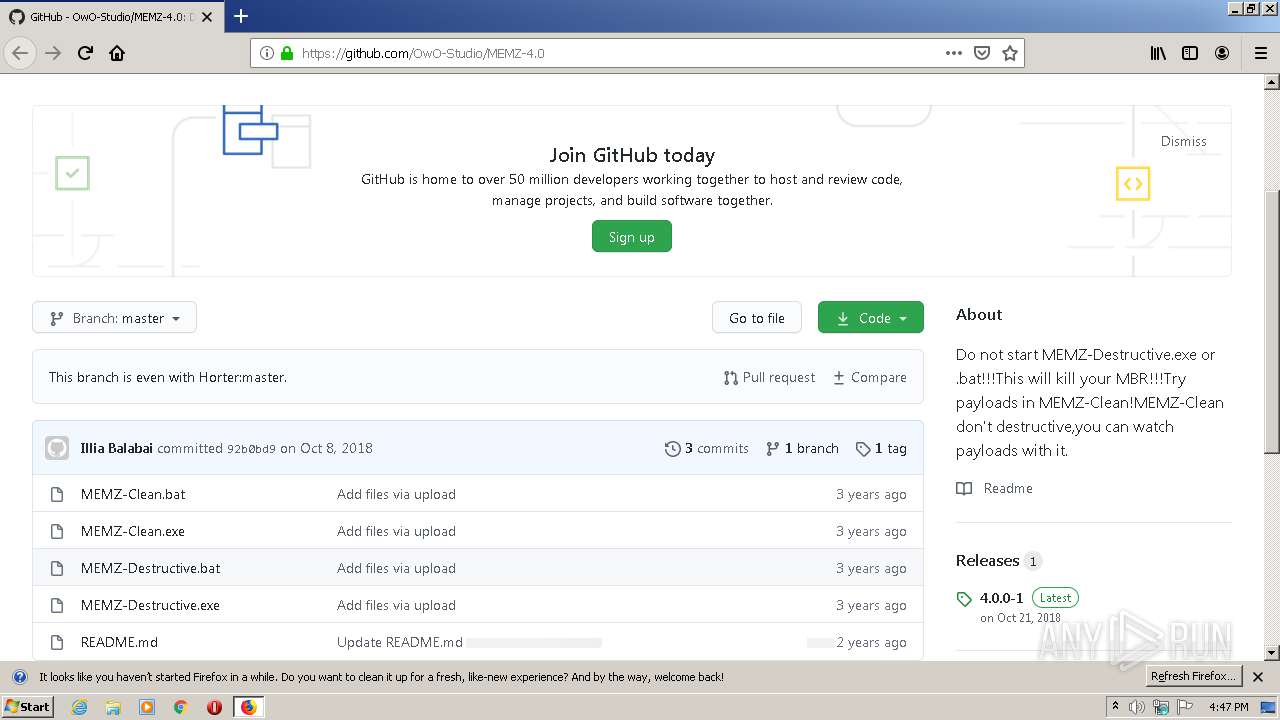
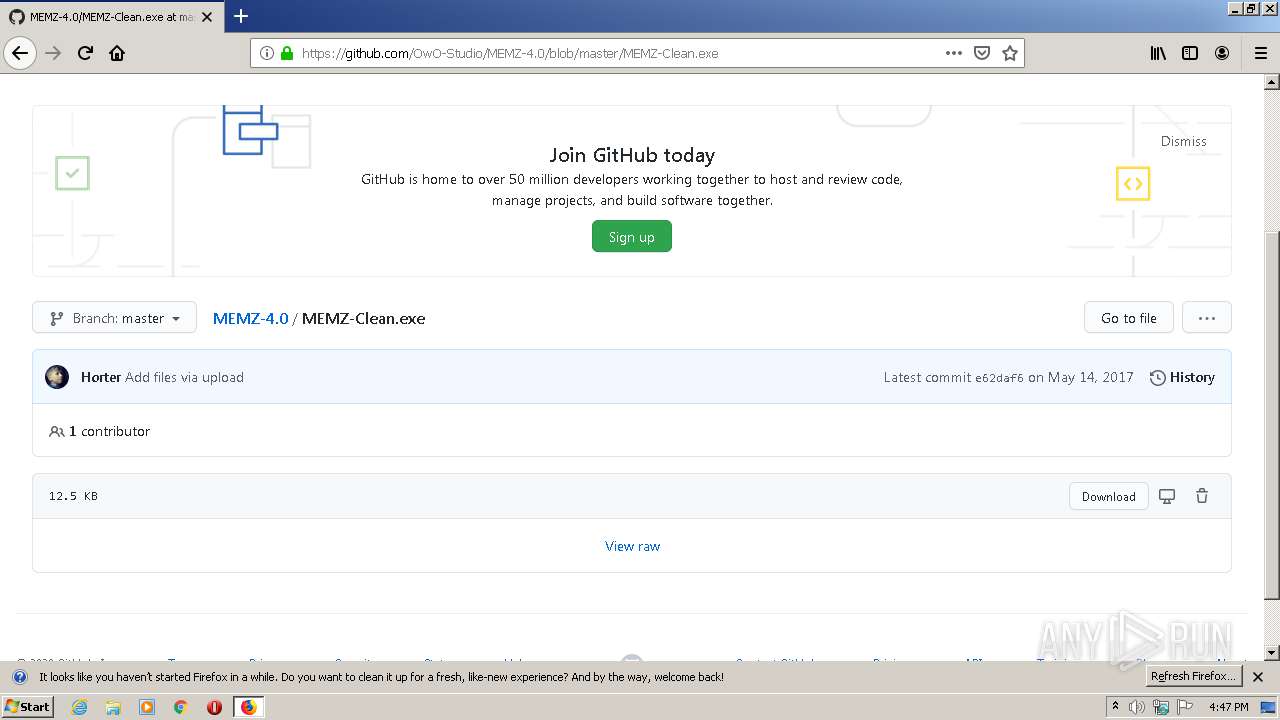
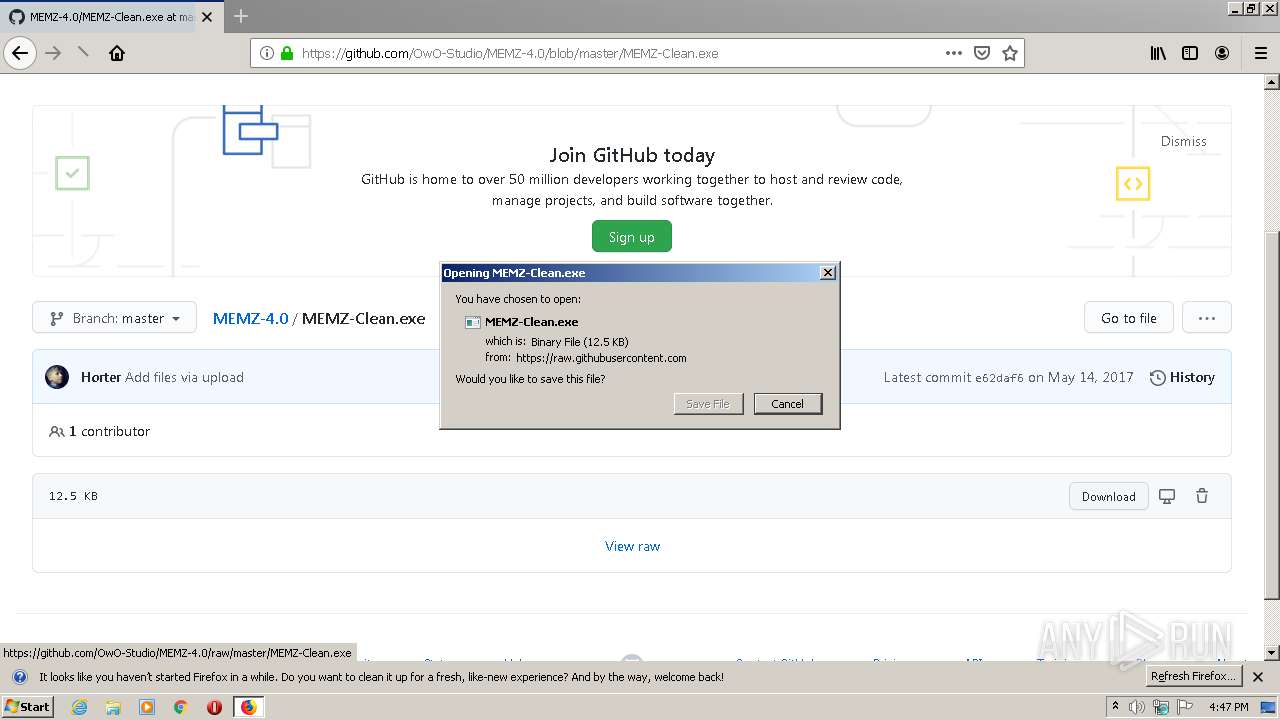
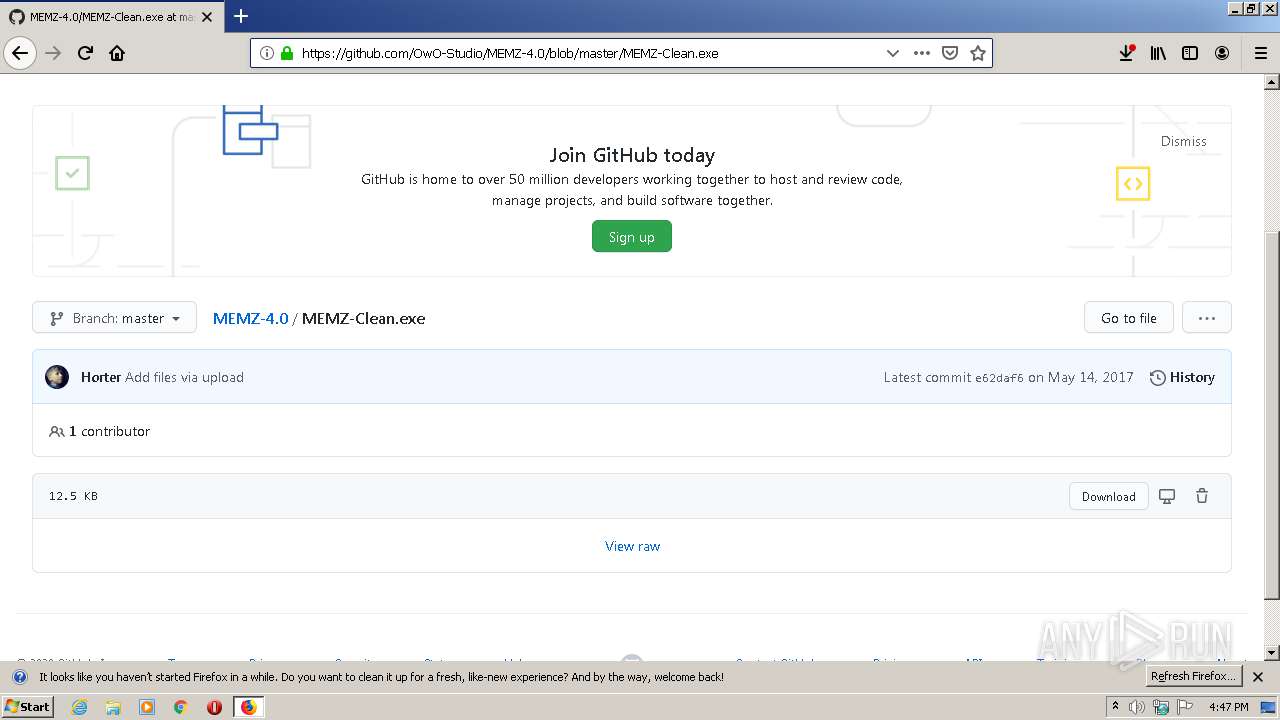
| URL: | https://github.com/OwO-Studio/MEMZ-4.0 |
| Full analysis: | https://app.any.run/tasks/fb3b01df-da1b-42b5-9a5e-96cb6de43ddd |
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2020, 15:47:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 410BC430431BB12DCA1CC78F3A89FADE |
| SHA1: | 57DC410832C5BE8DDD4730EF5065FCE109834DA4 |
| SHA256: | AE6539839A542FC267FC770695333224F8D8B2ED926B154269887C5850E3B683 |
| SSDEEP: | 3:N8tEdUI2gMFhn:2uu1Fh |
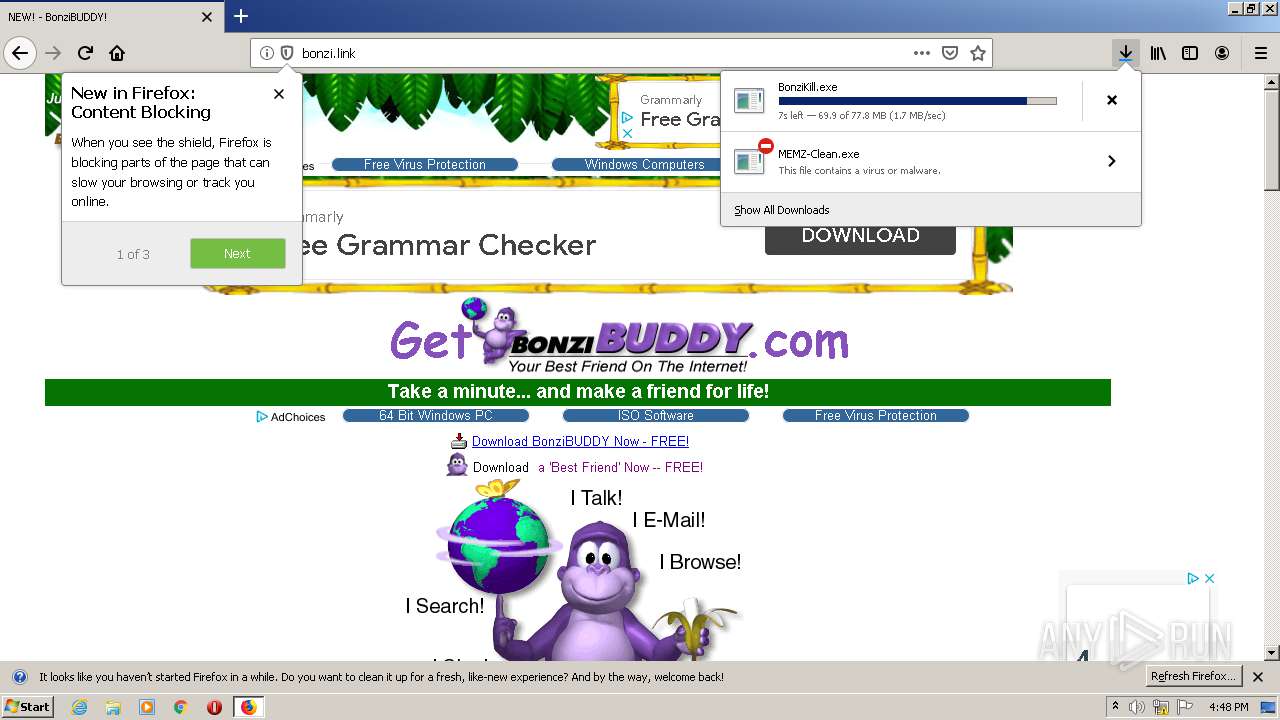
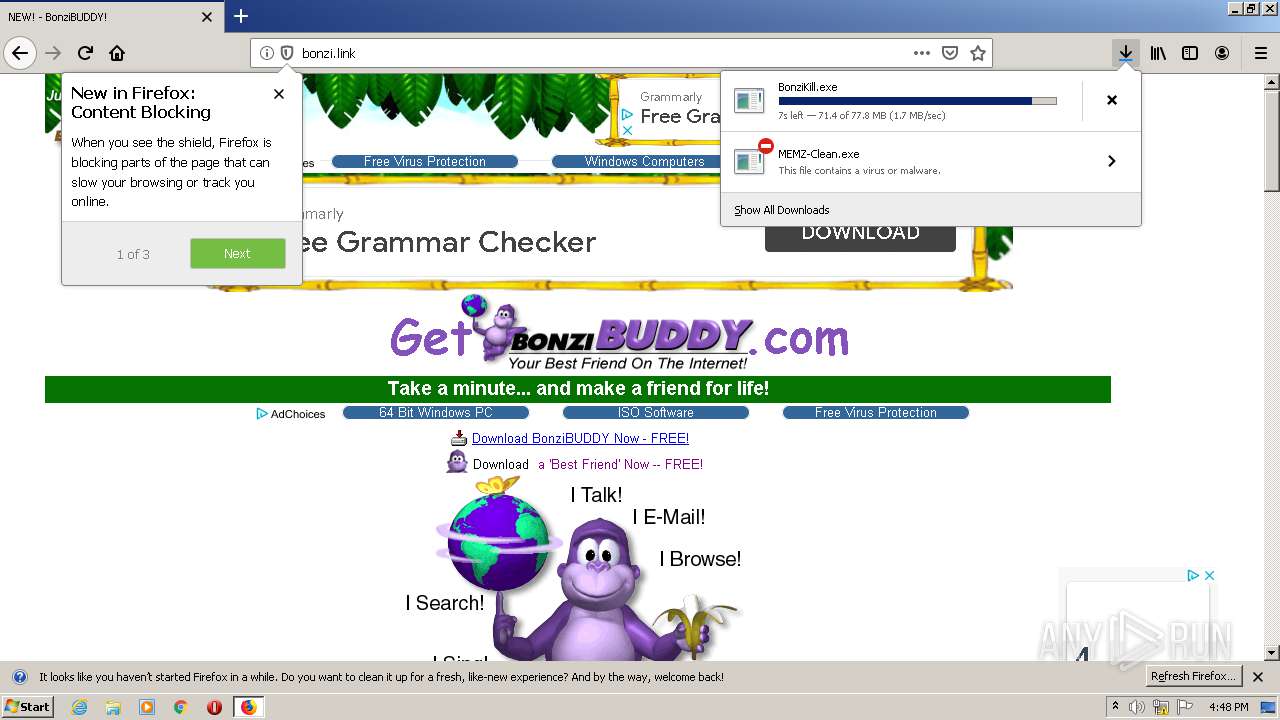
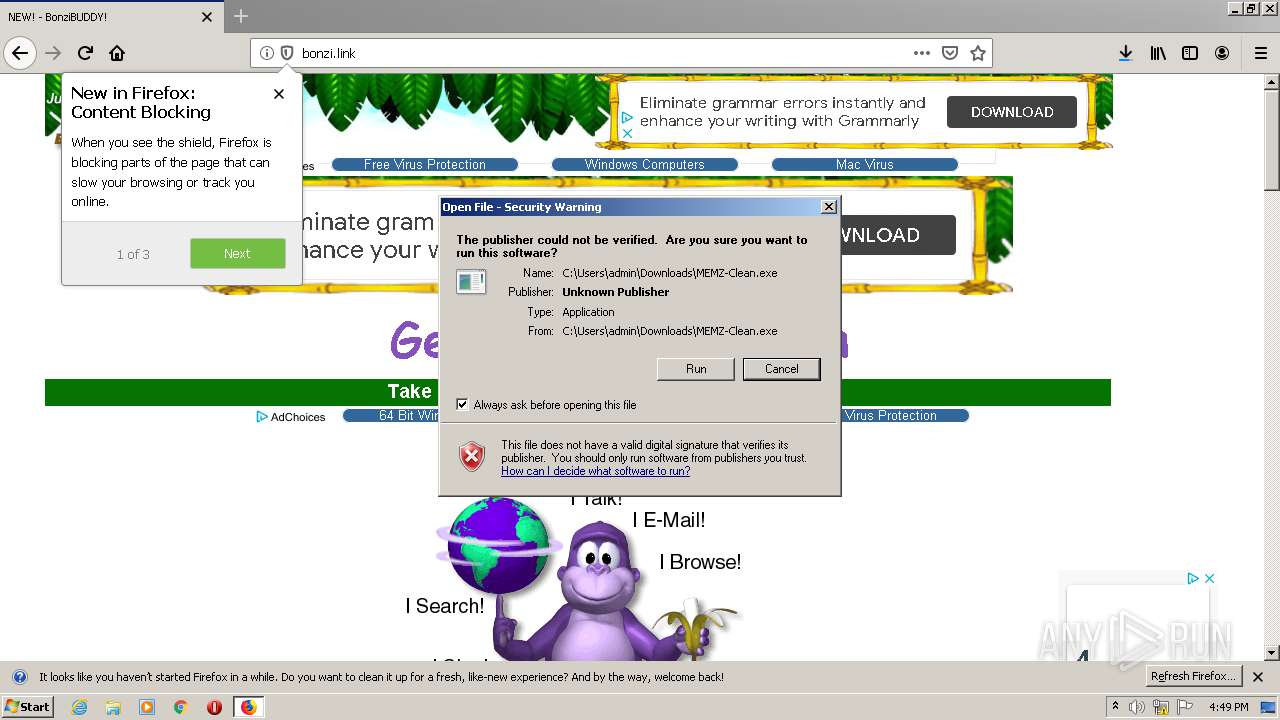
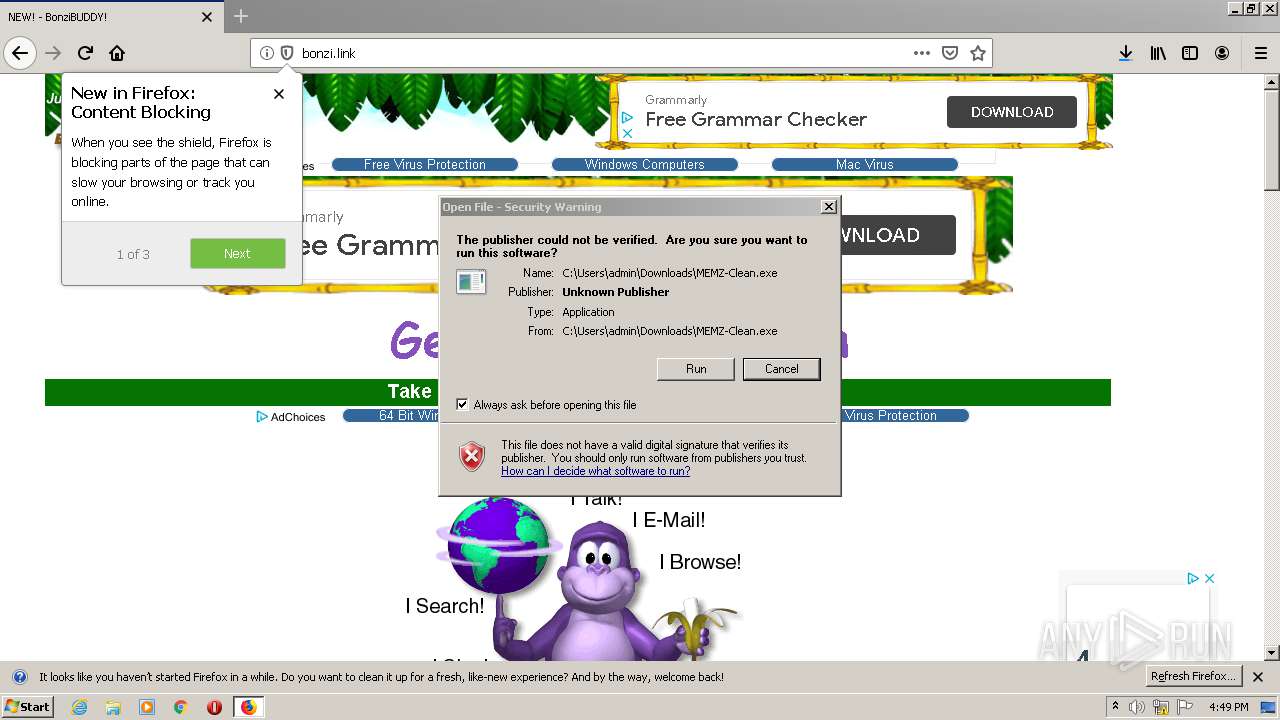
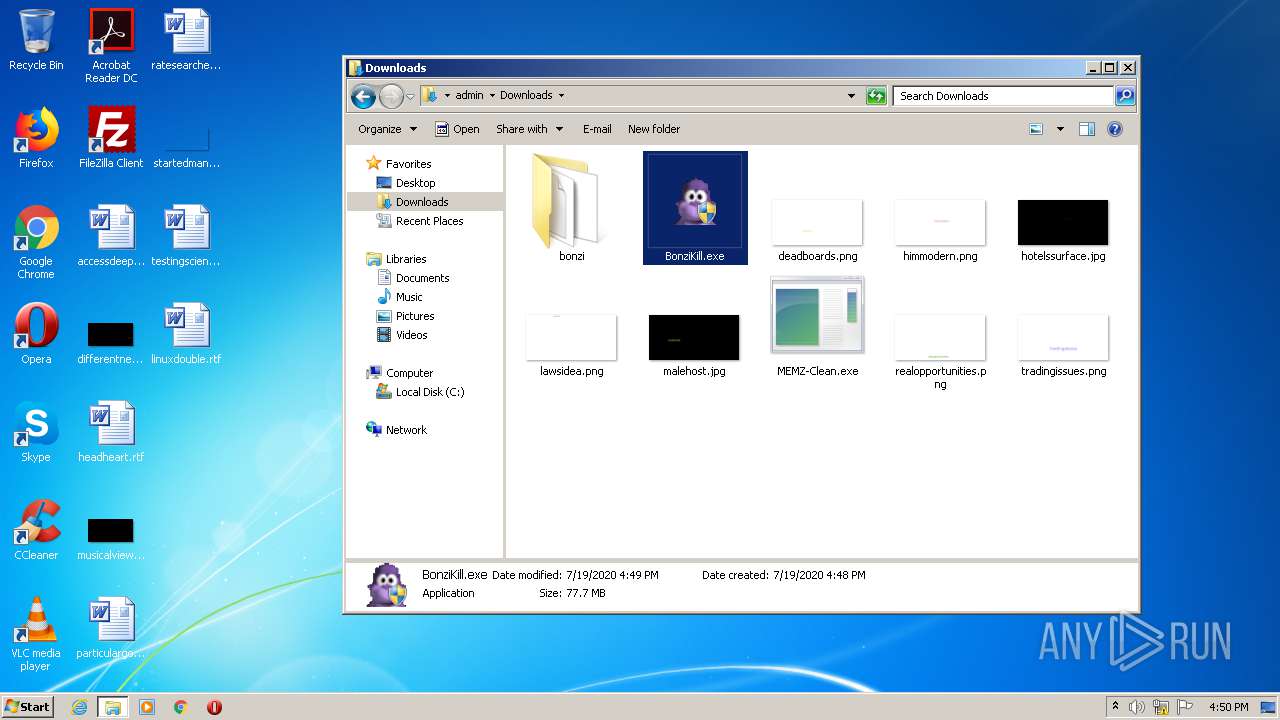
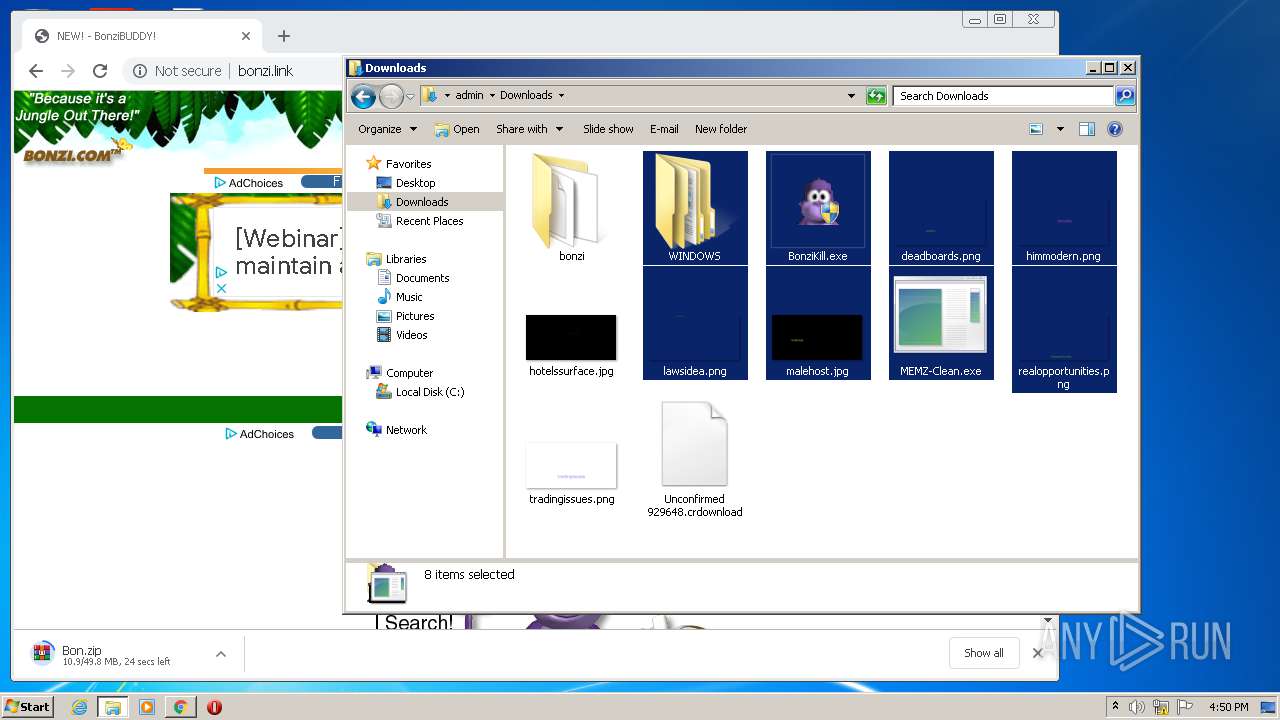
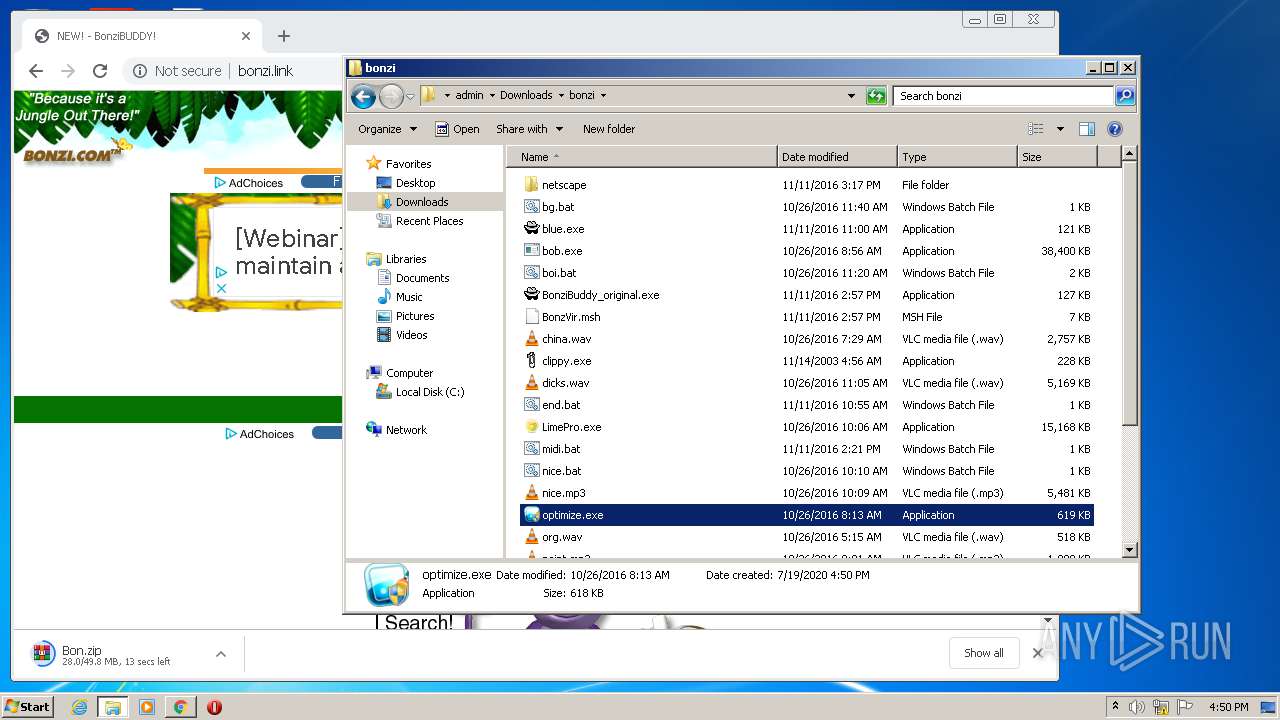
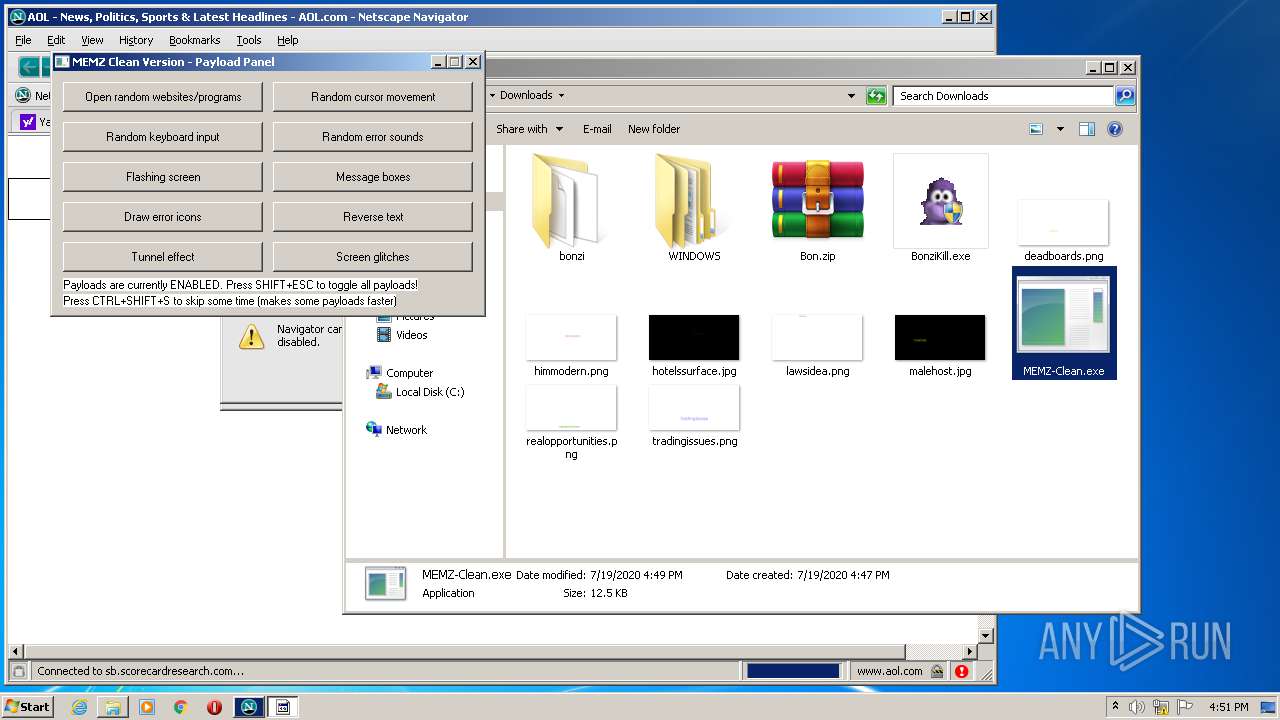
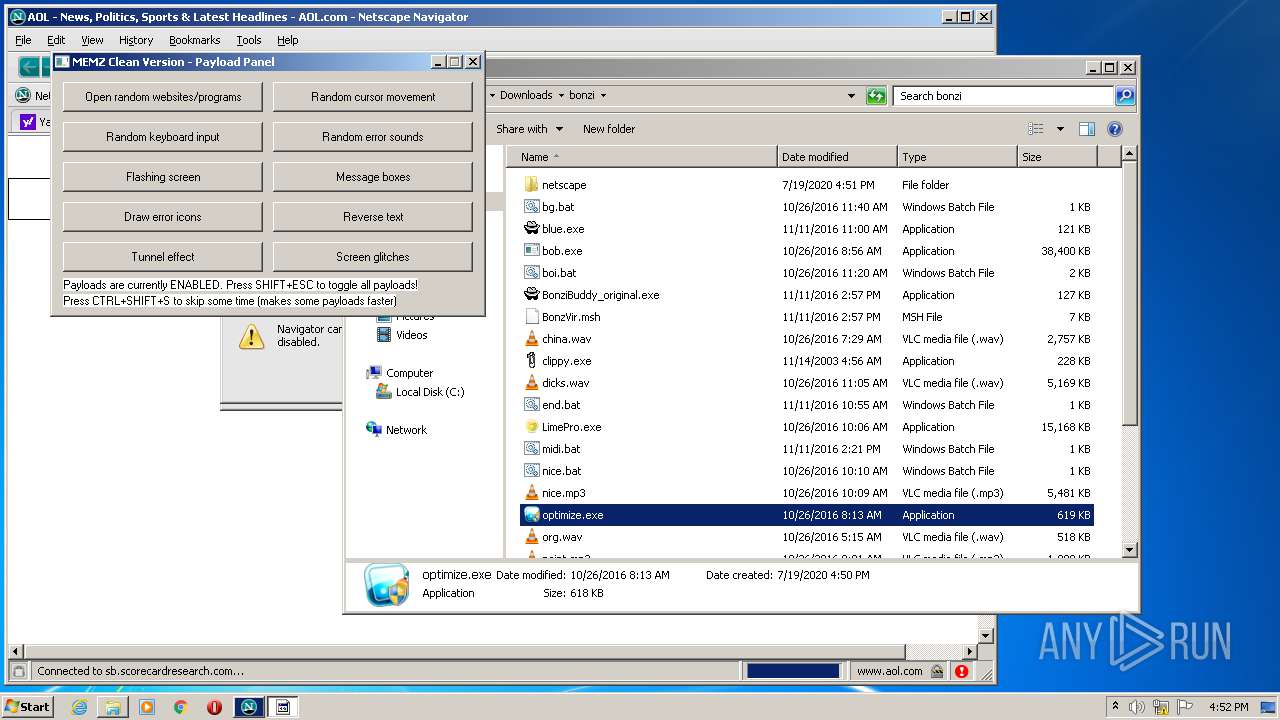
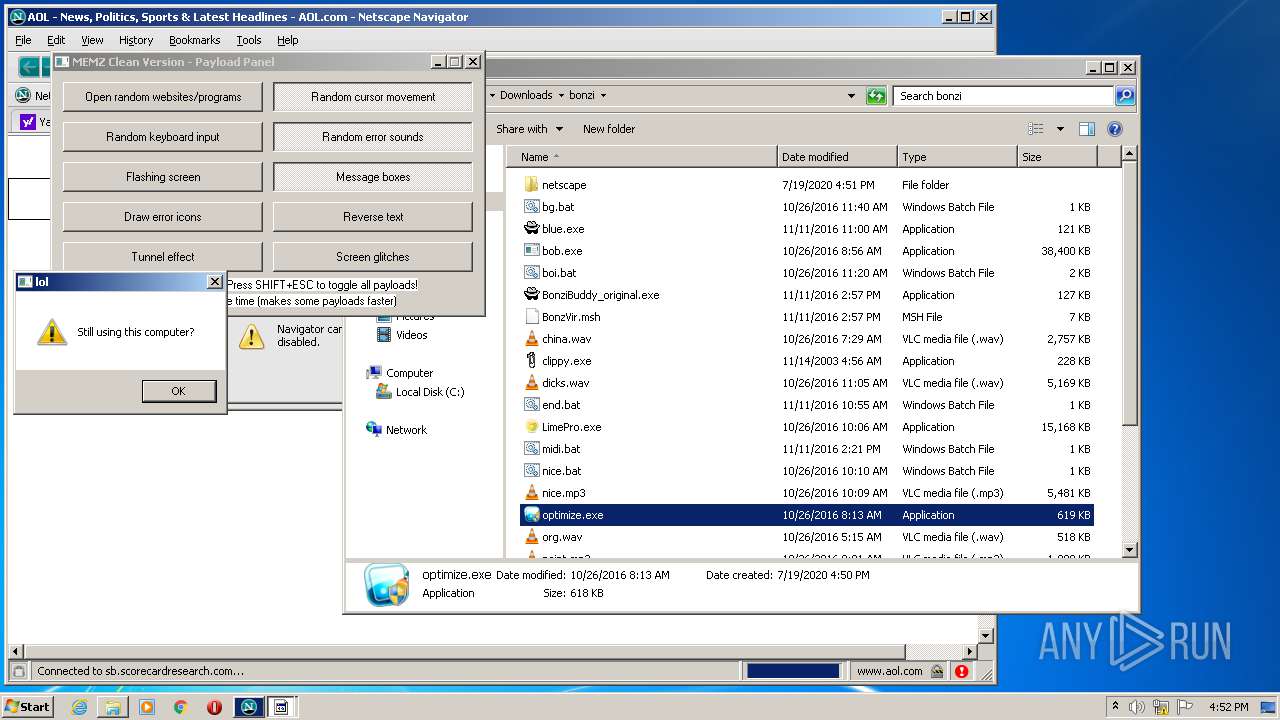
MALICIOUS
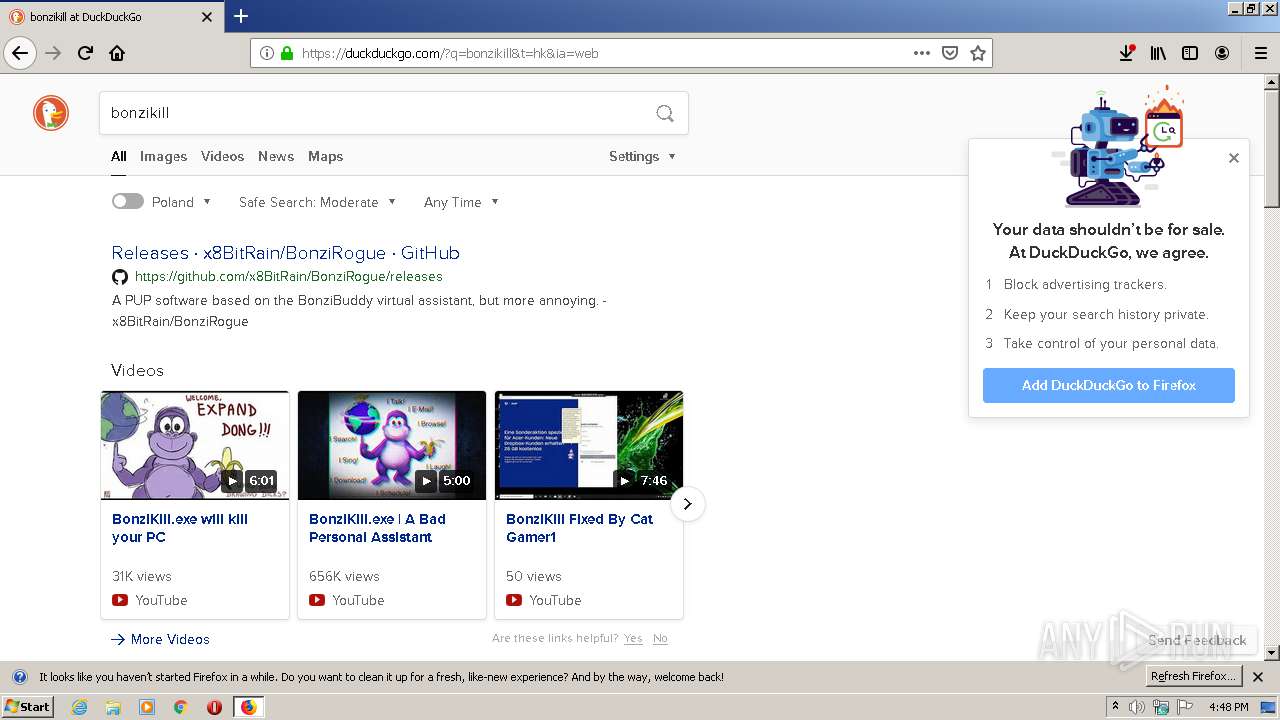
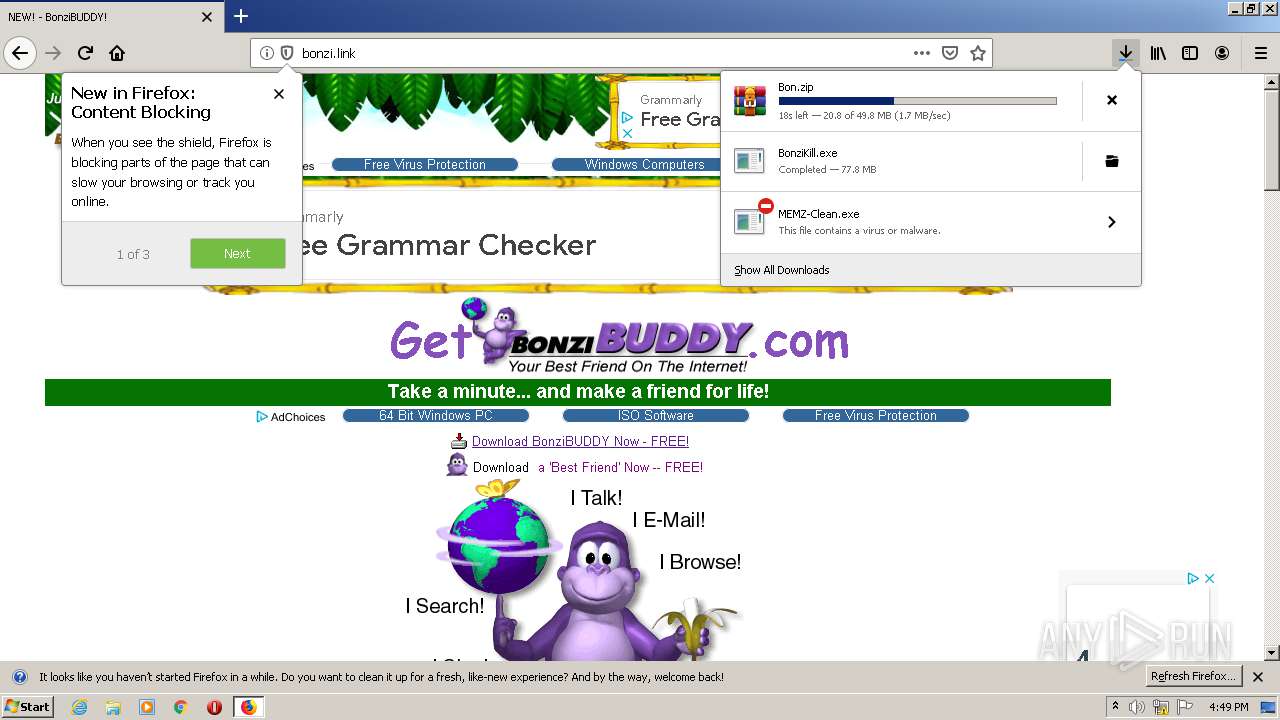
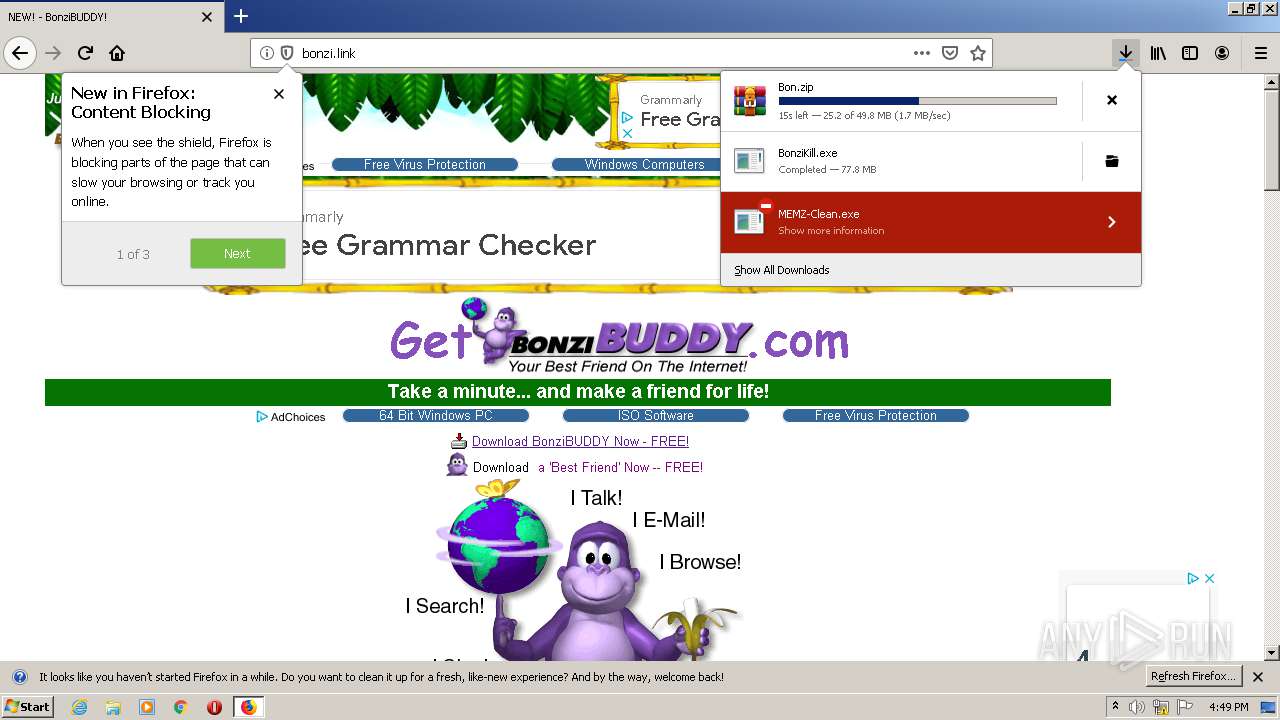
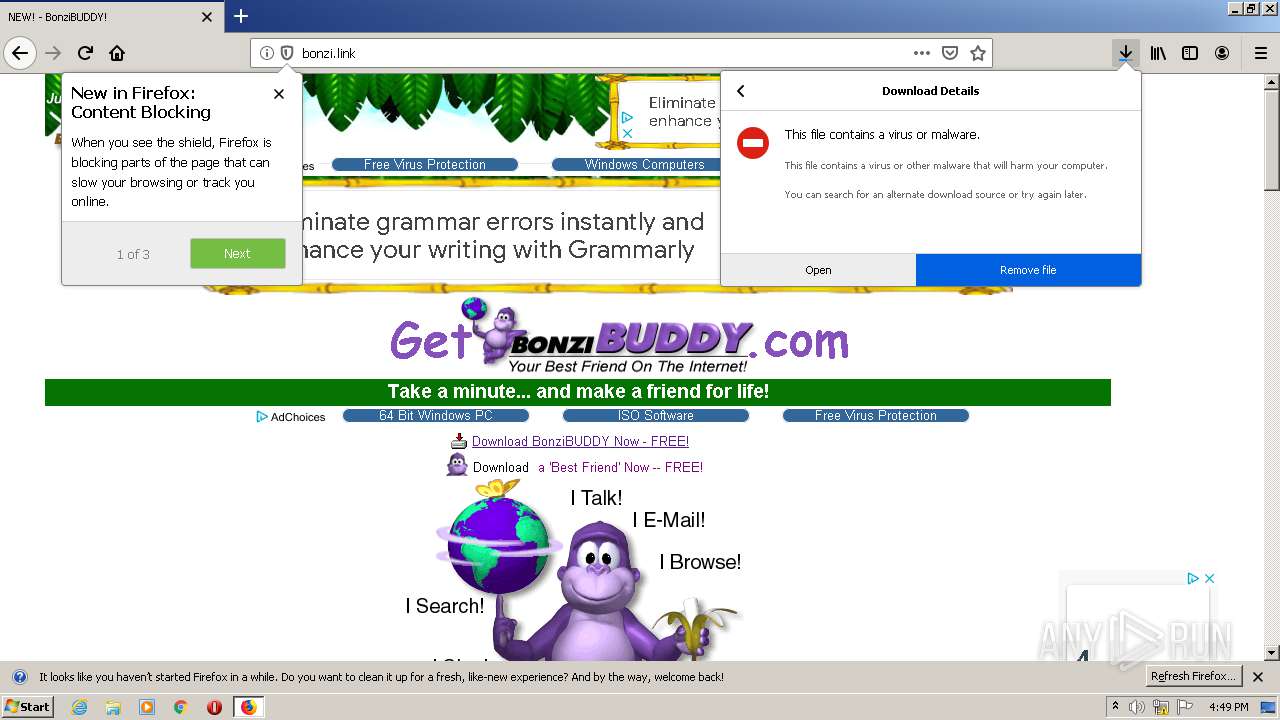
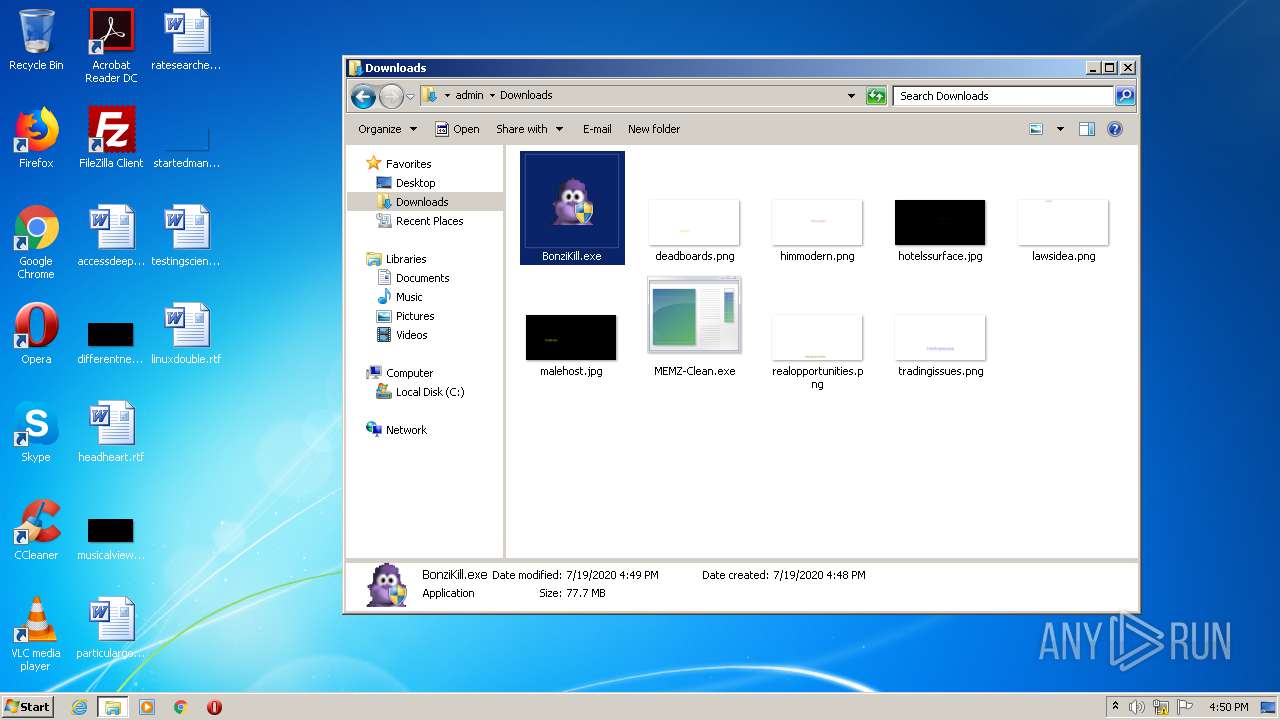
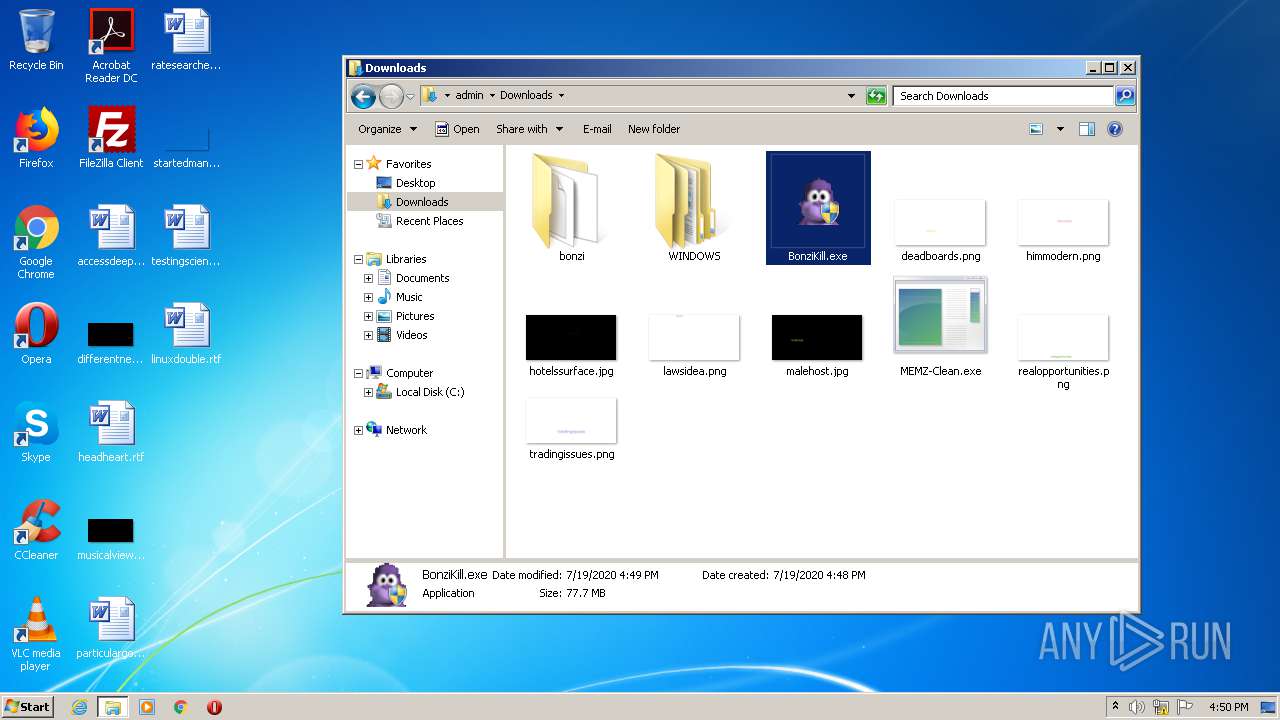
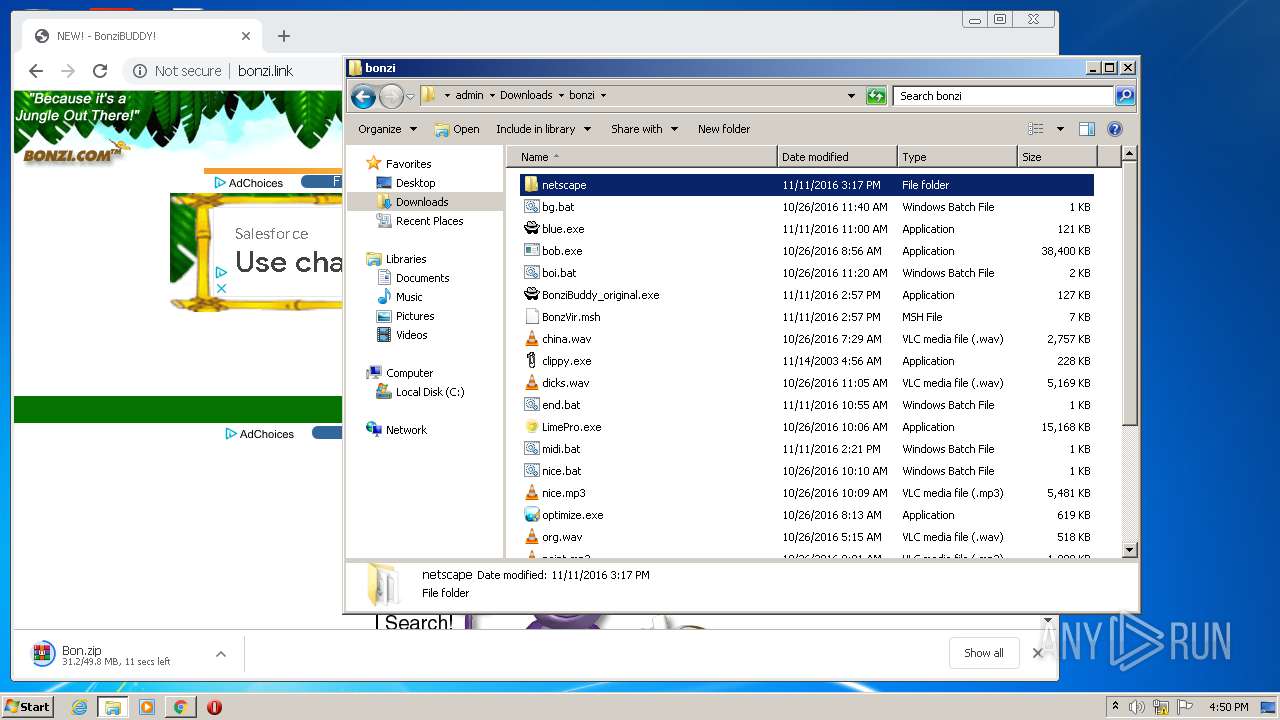
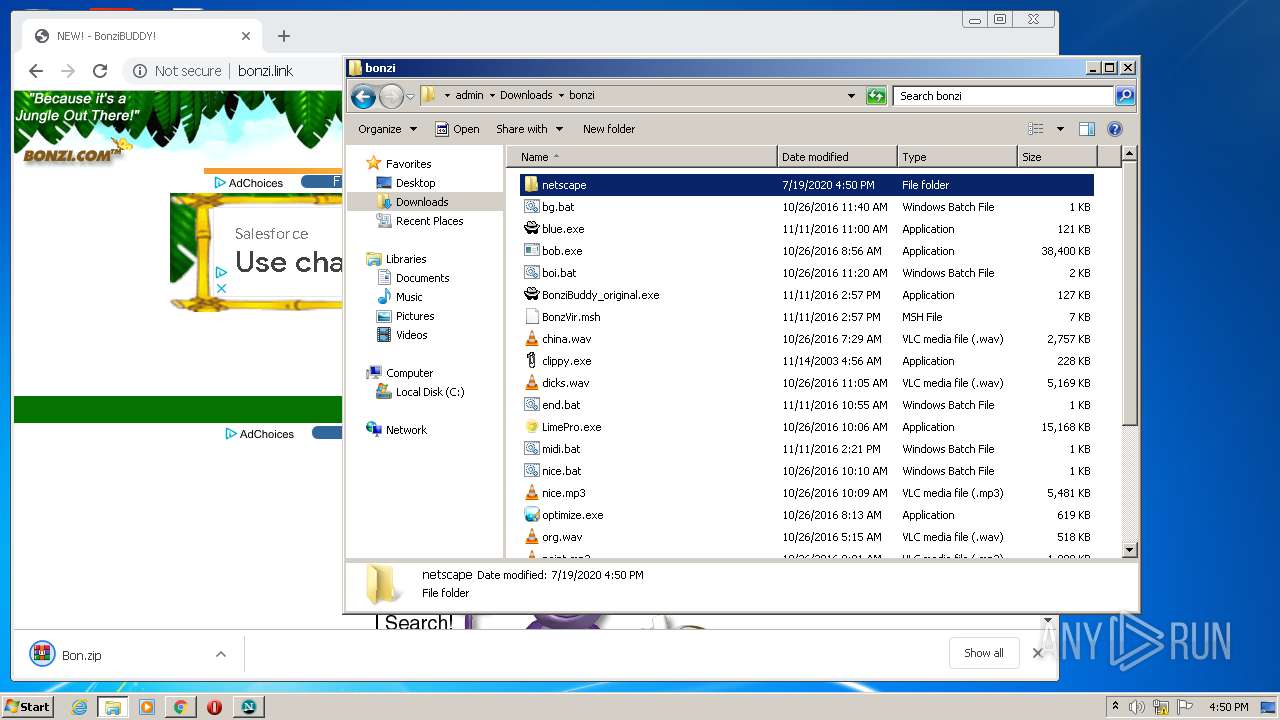
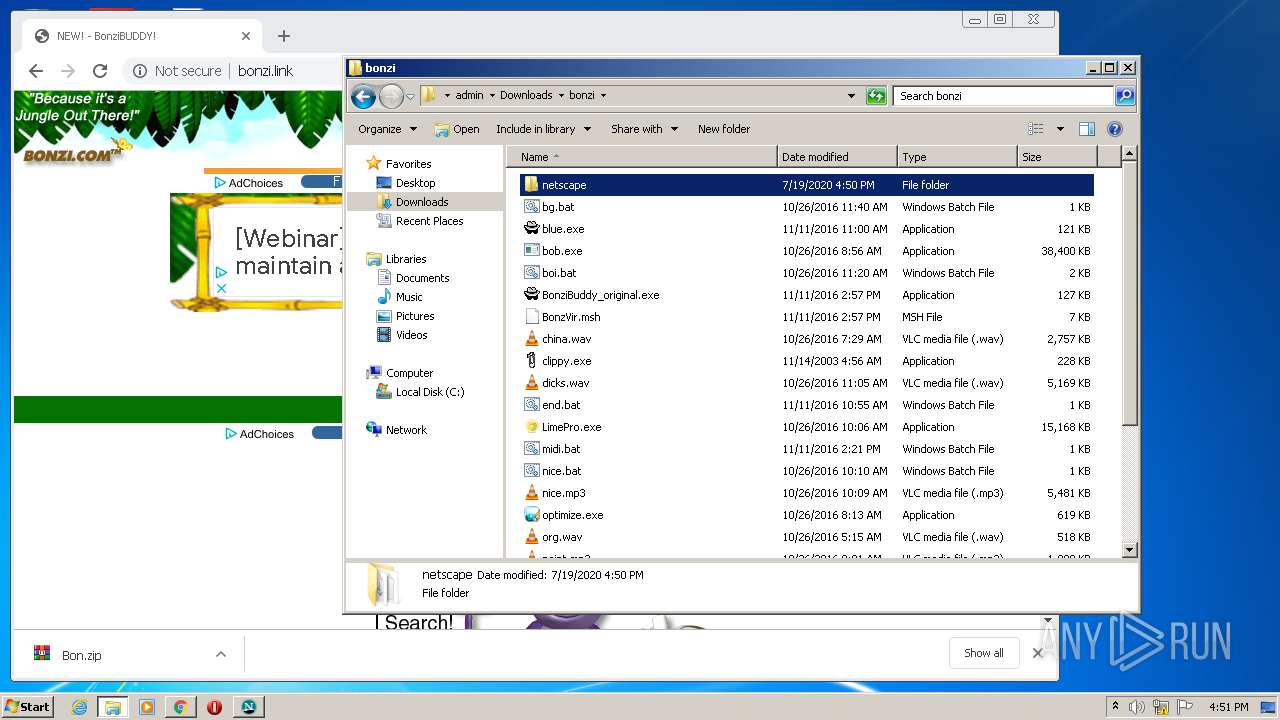
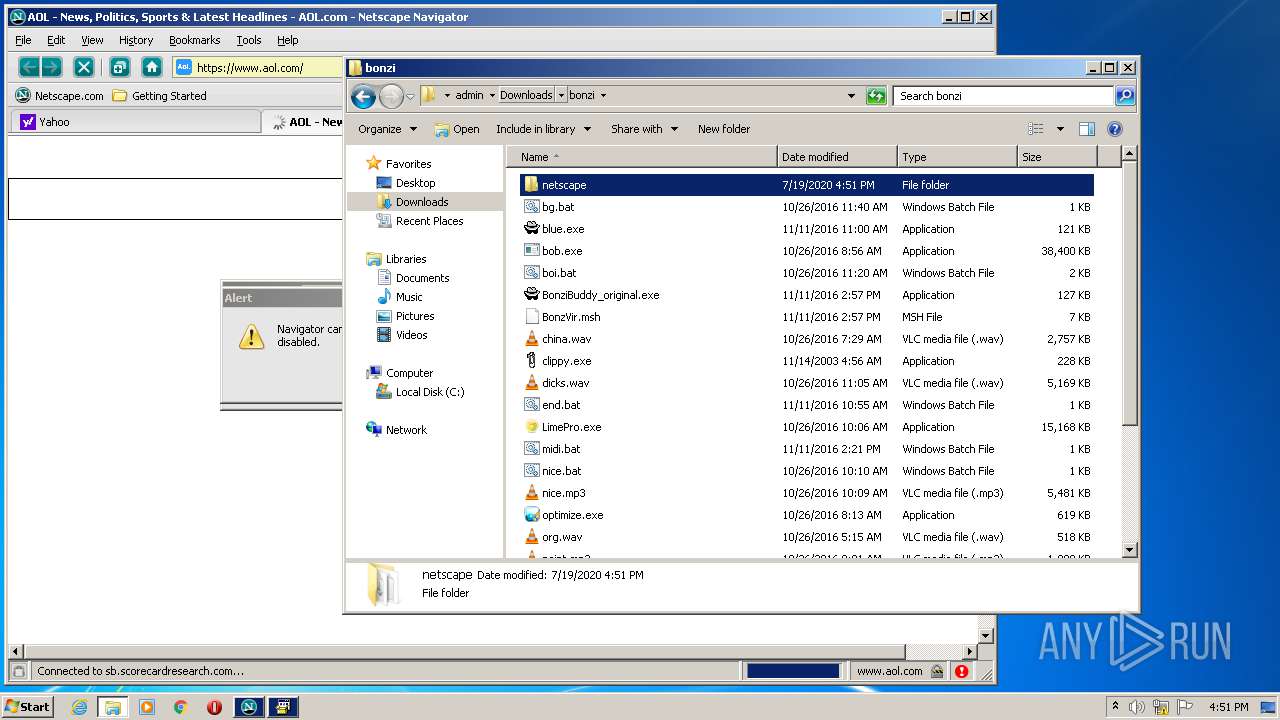
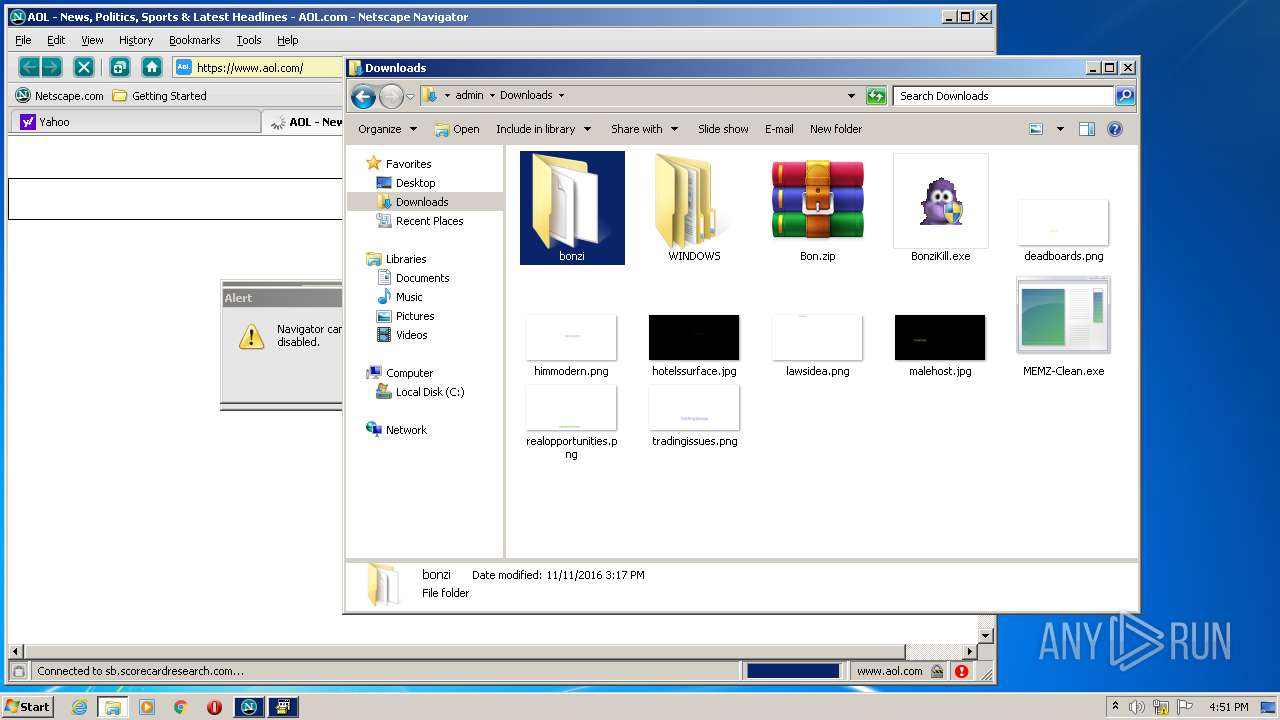
Application was dropped or rewritten from another process
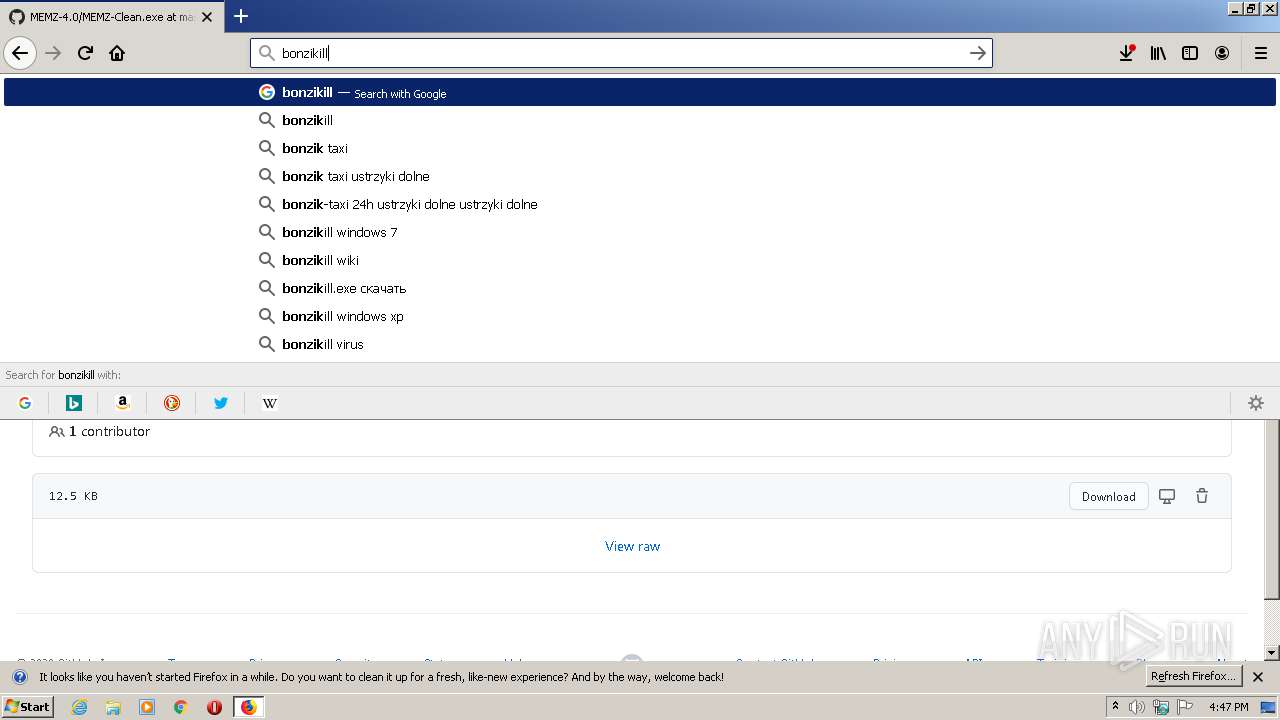
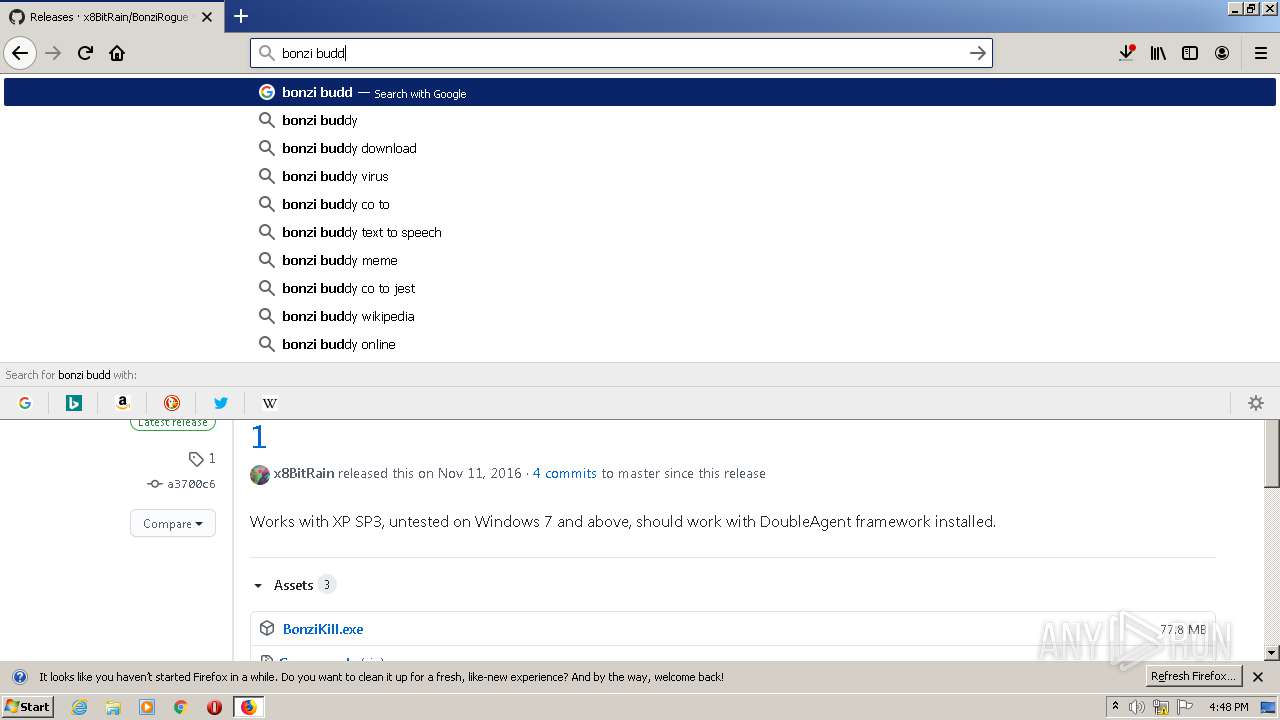
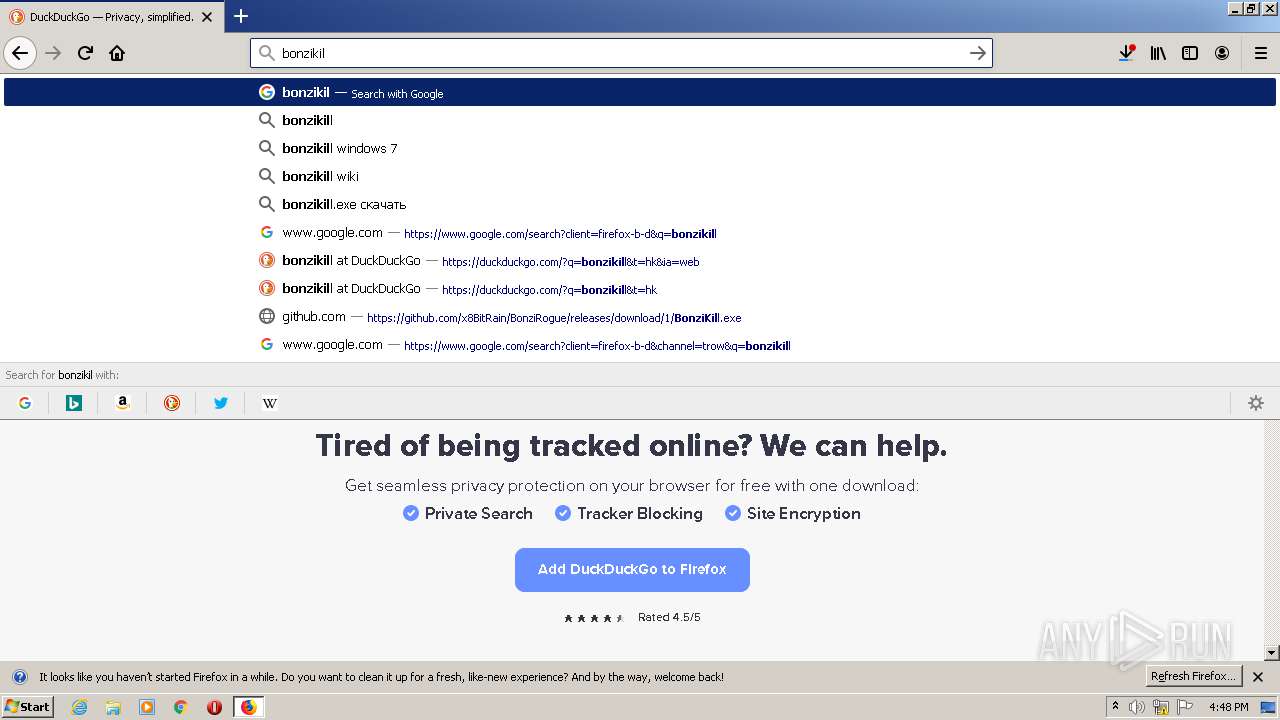
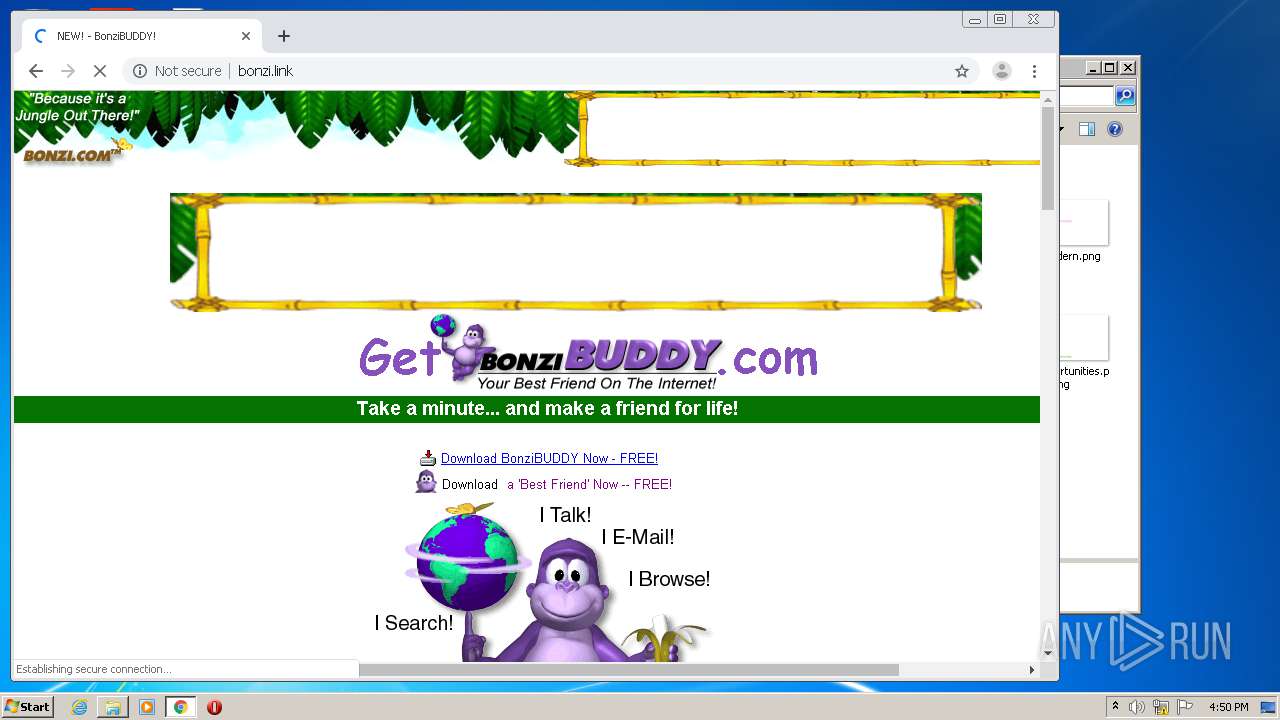
- BonziKill.exe (PID: 2636)
- BonziBuddy_original.exe (PID: 3984)
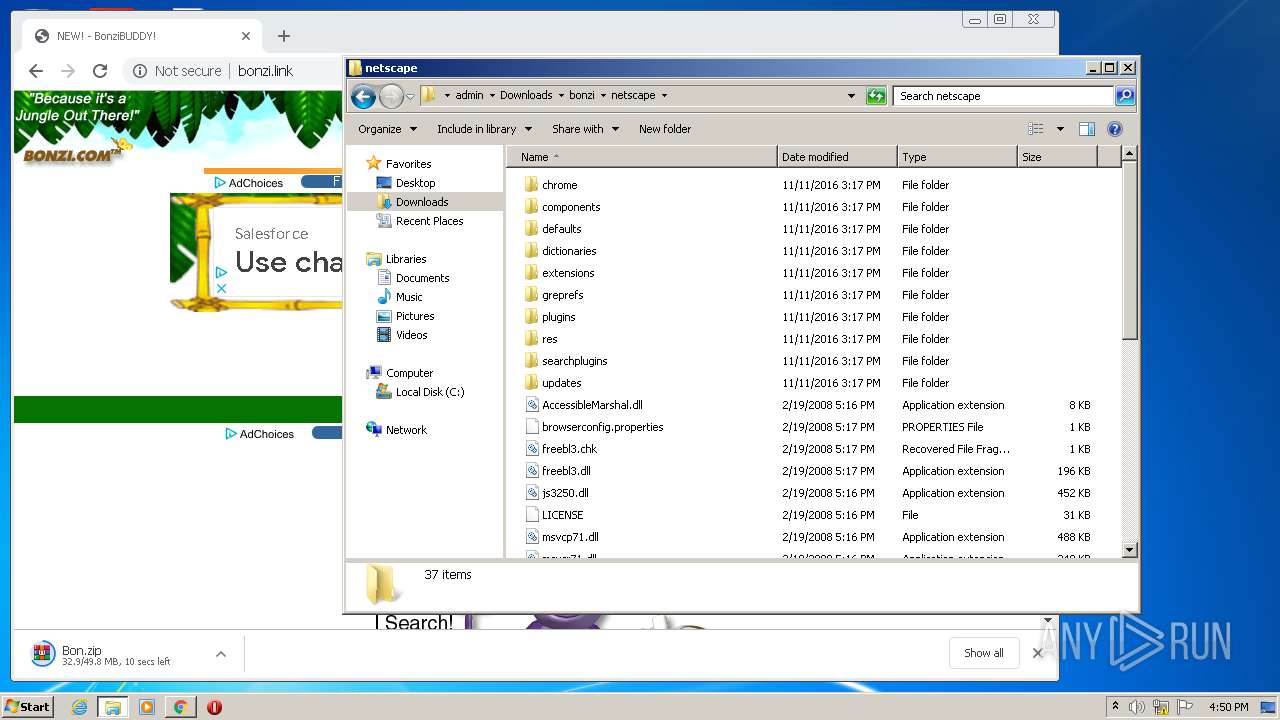
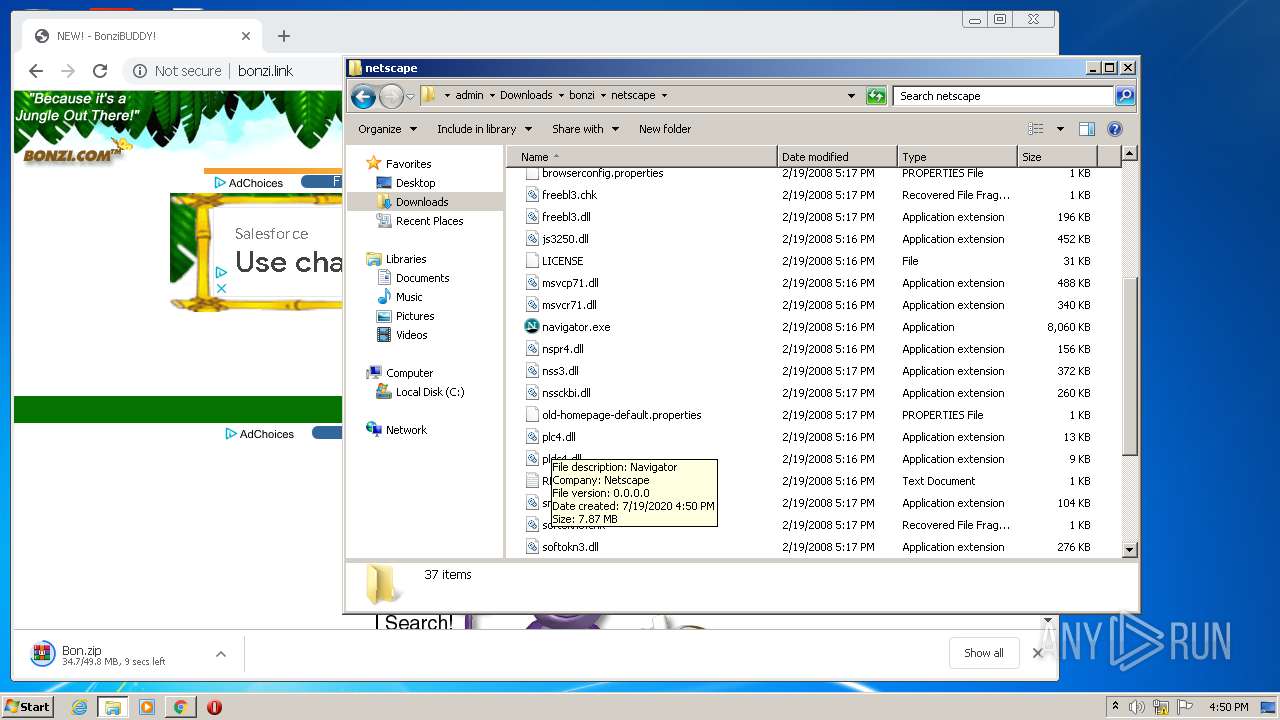
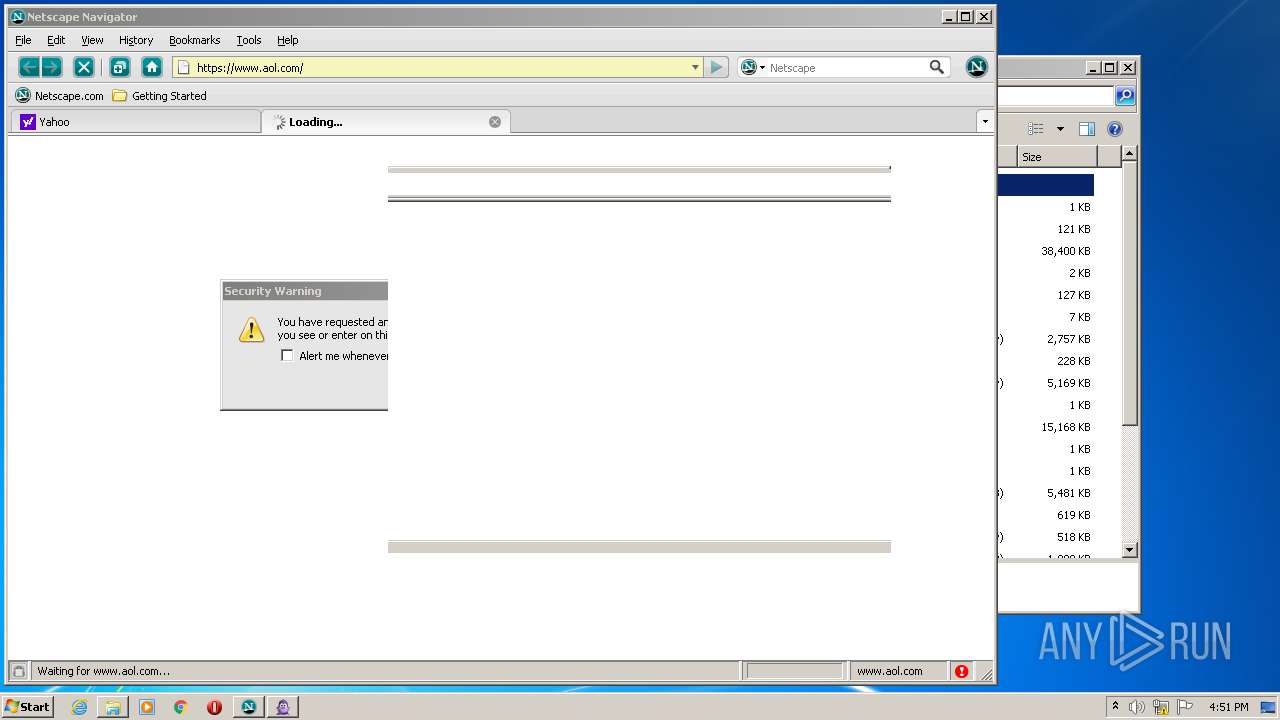
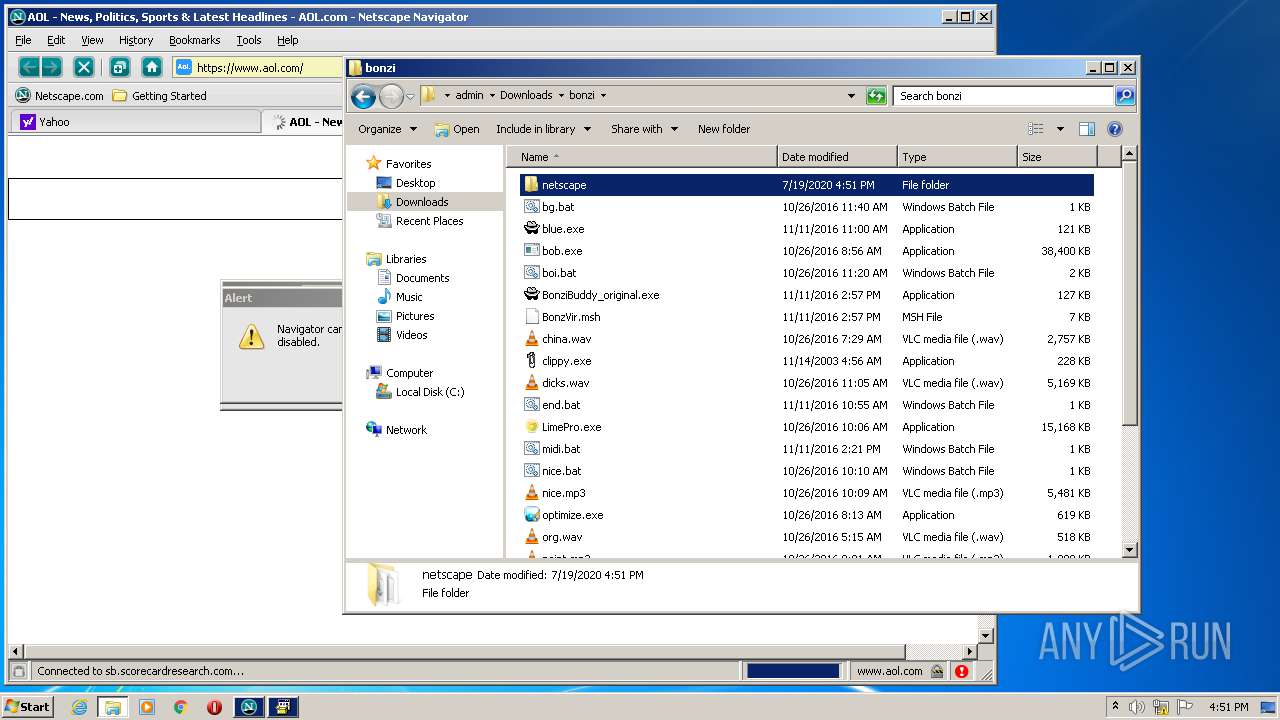
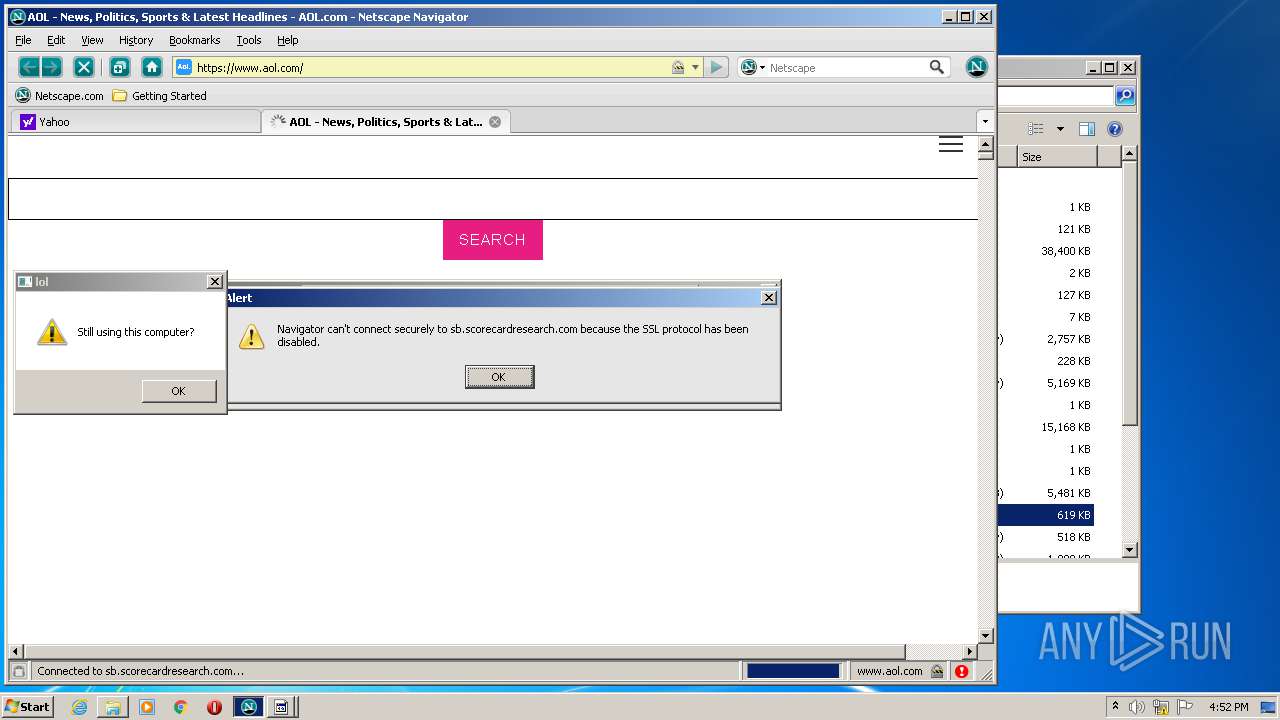
- navigator.exe (PID: 1116)
- navigator.exe (PID: 1588)
- navigator.exe (PID: 1264)
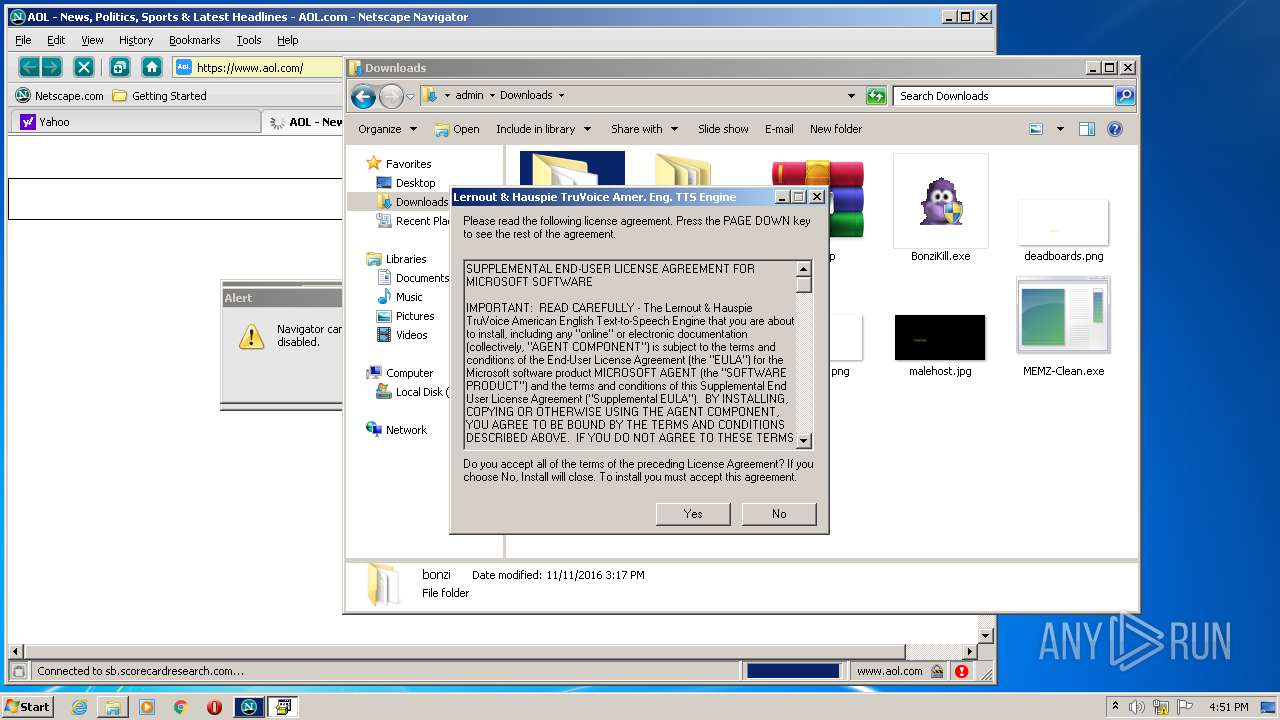
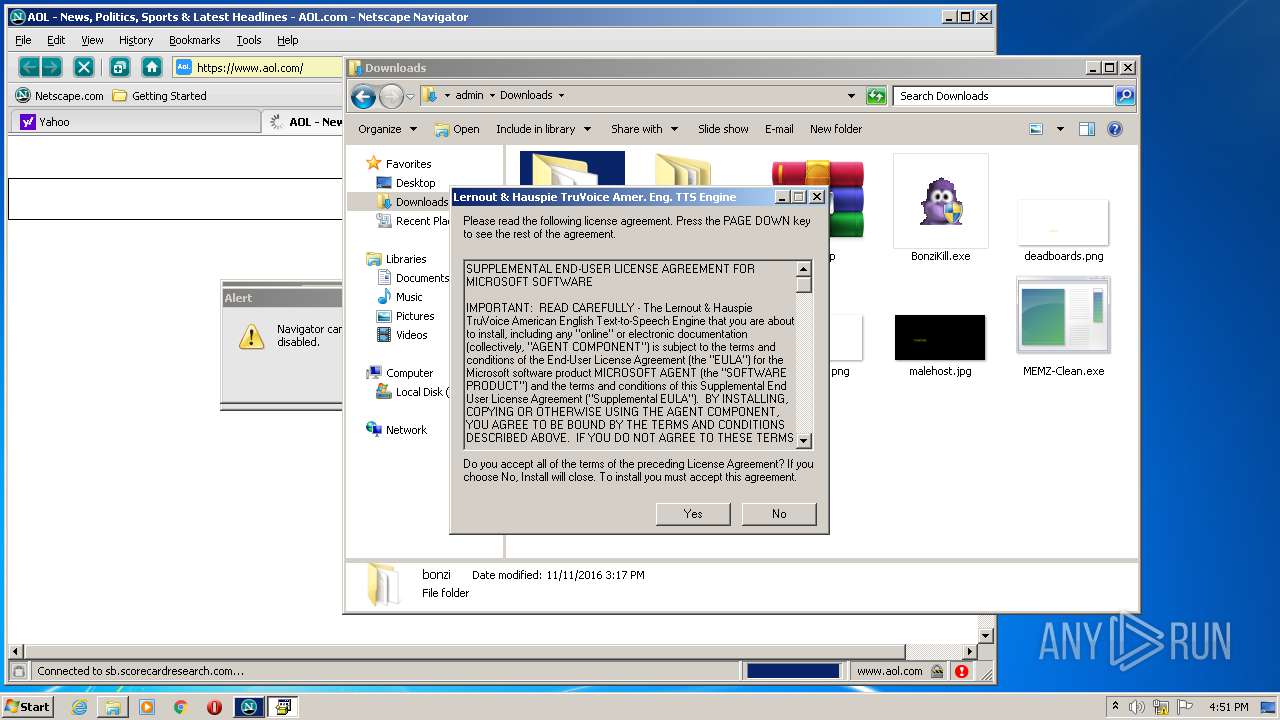
- tv_enua.exe (PID: 3628)
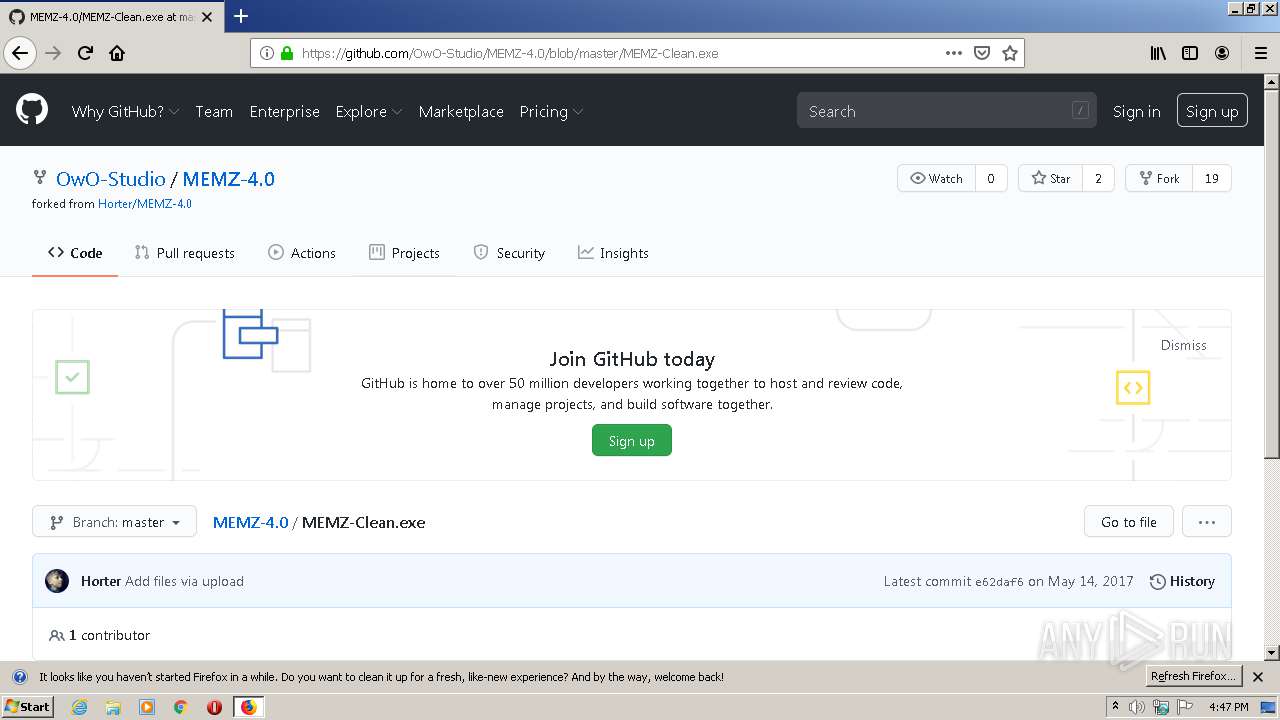
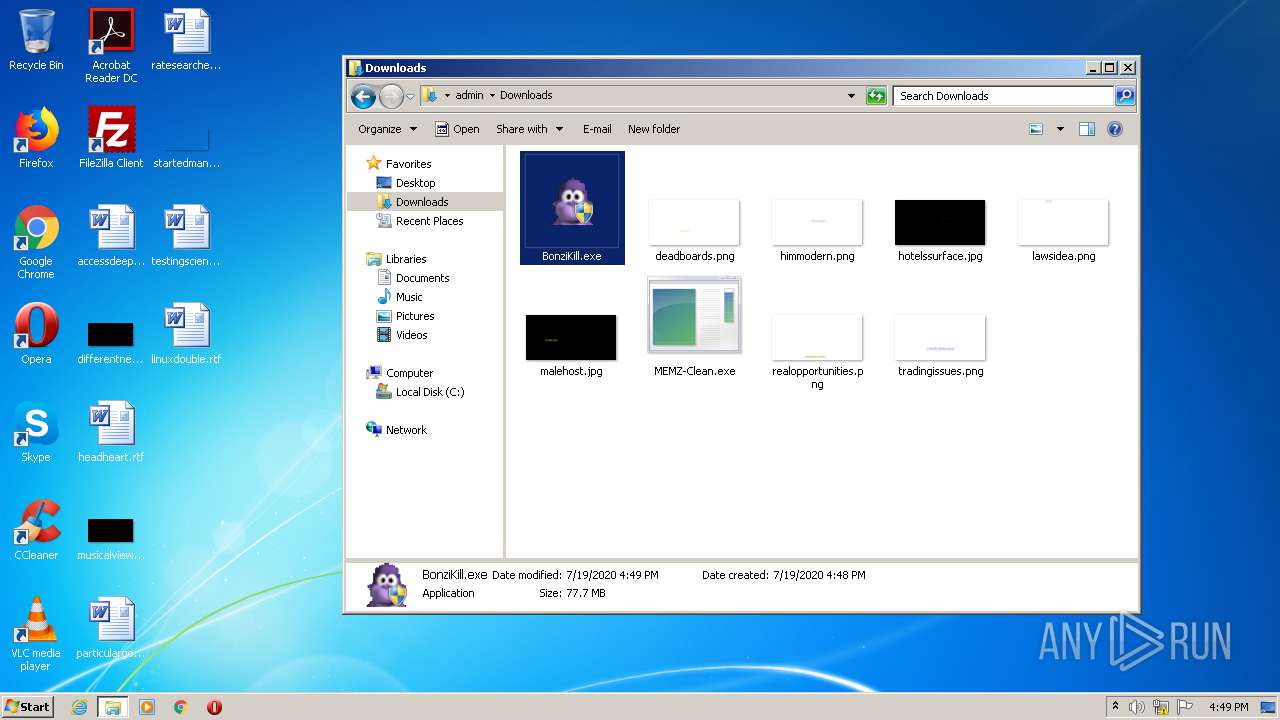
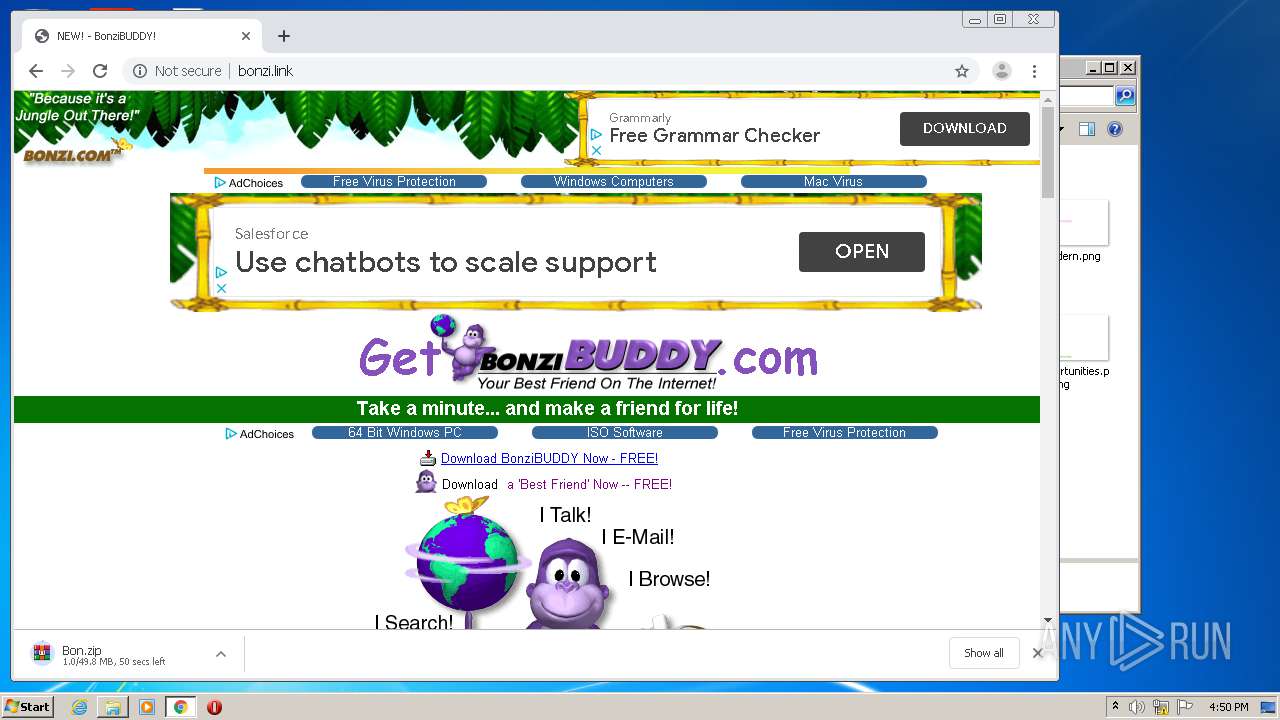
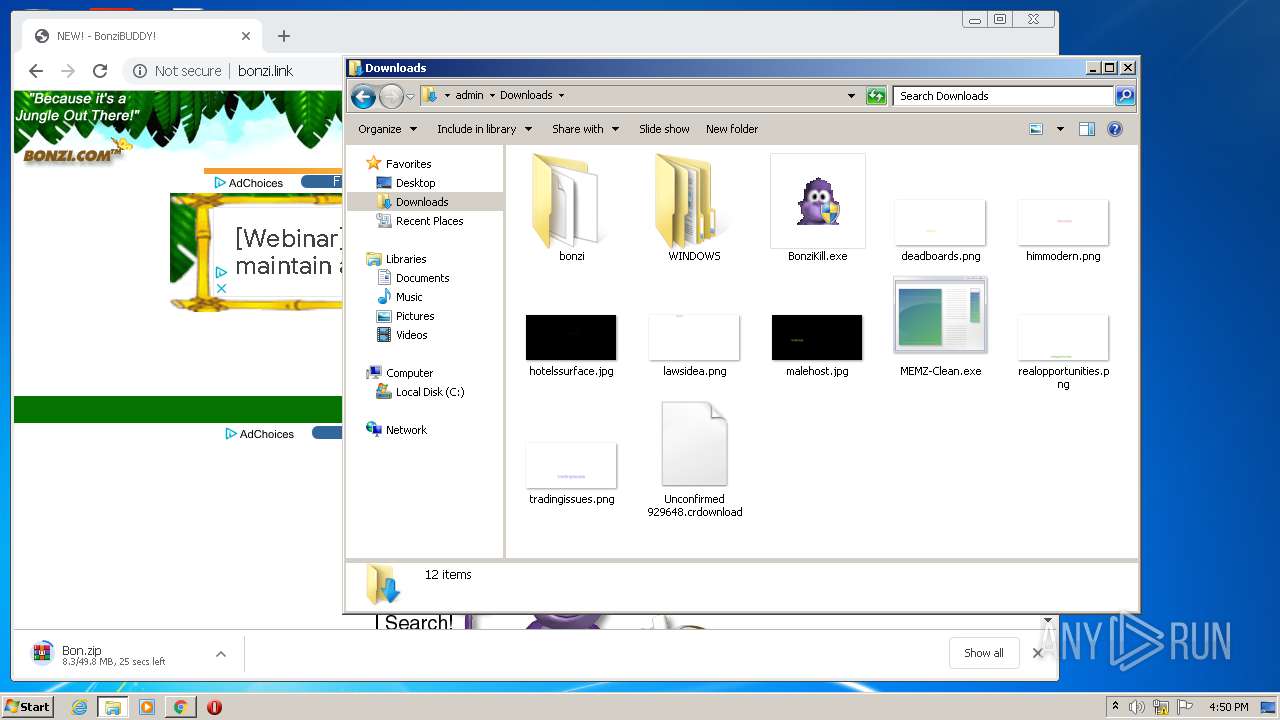
- MEMZ-Clean.exe (PID: 2872)
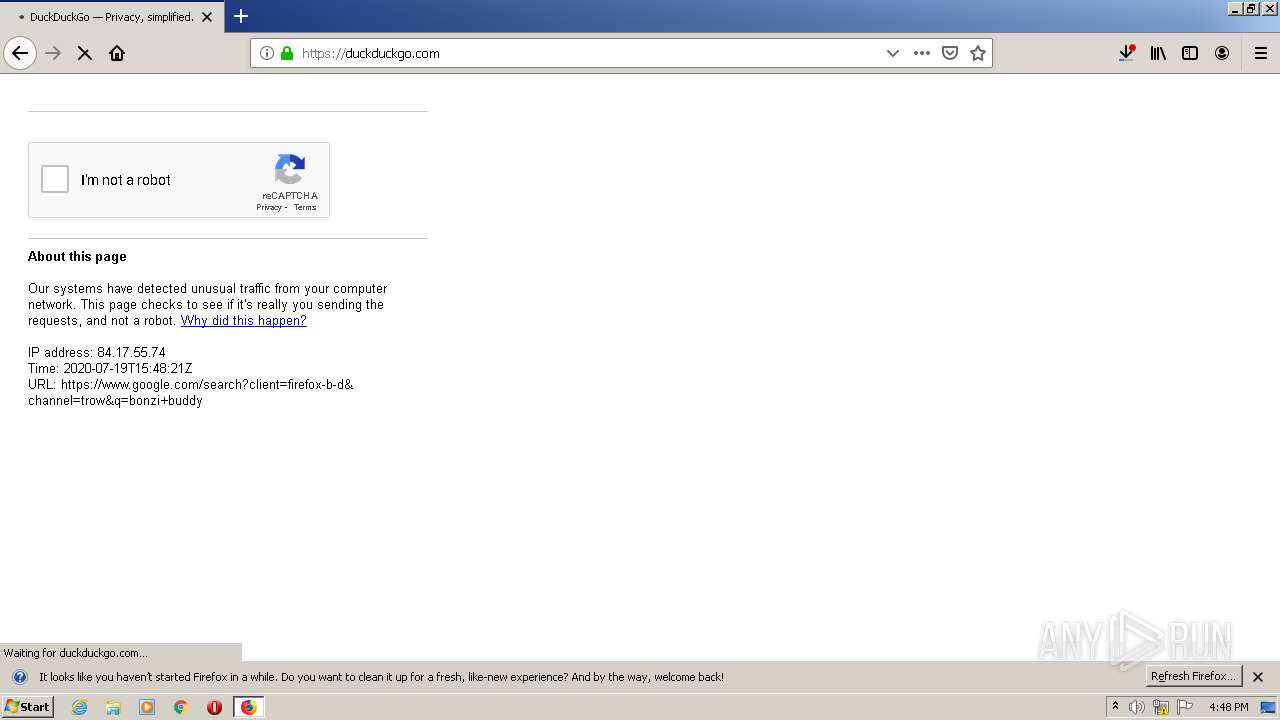
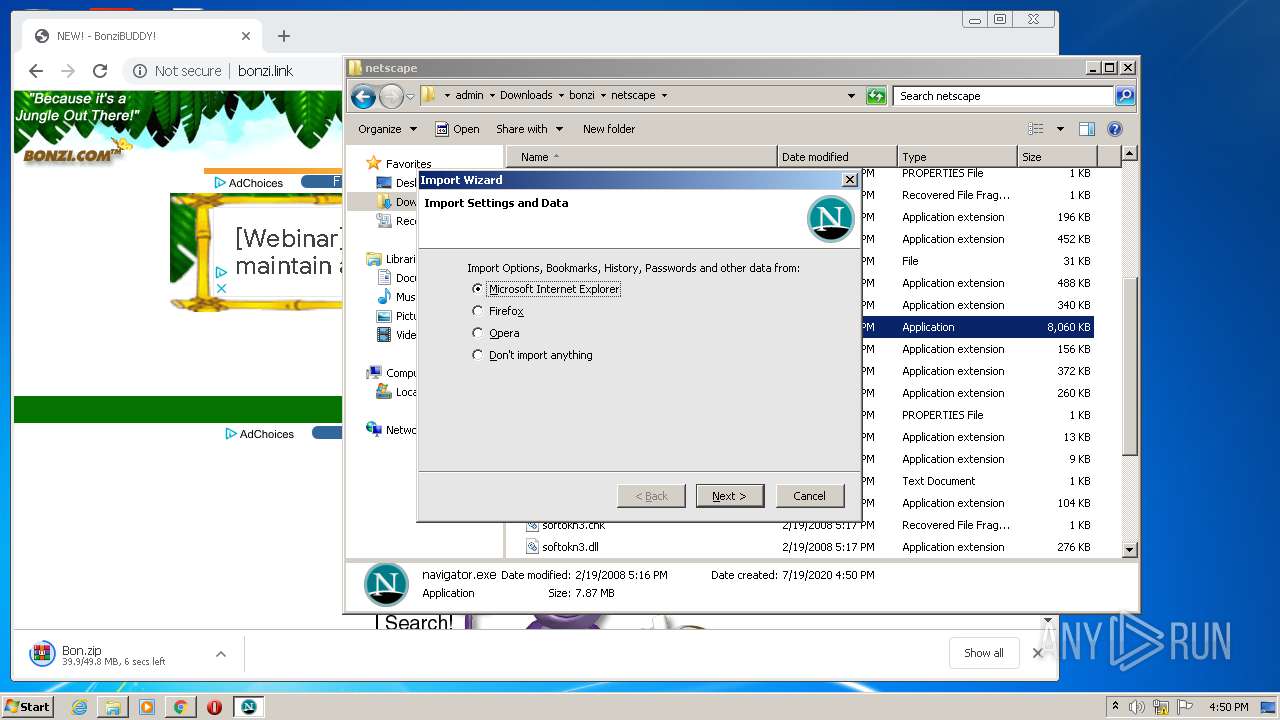
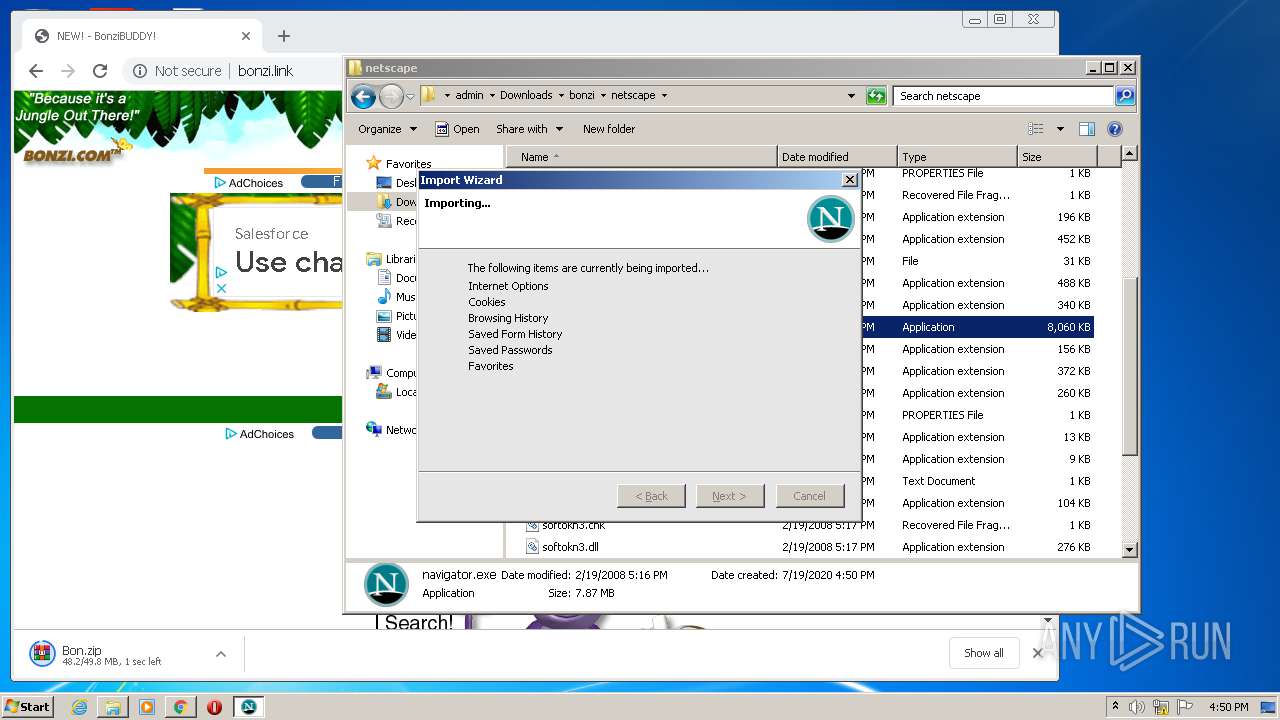
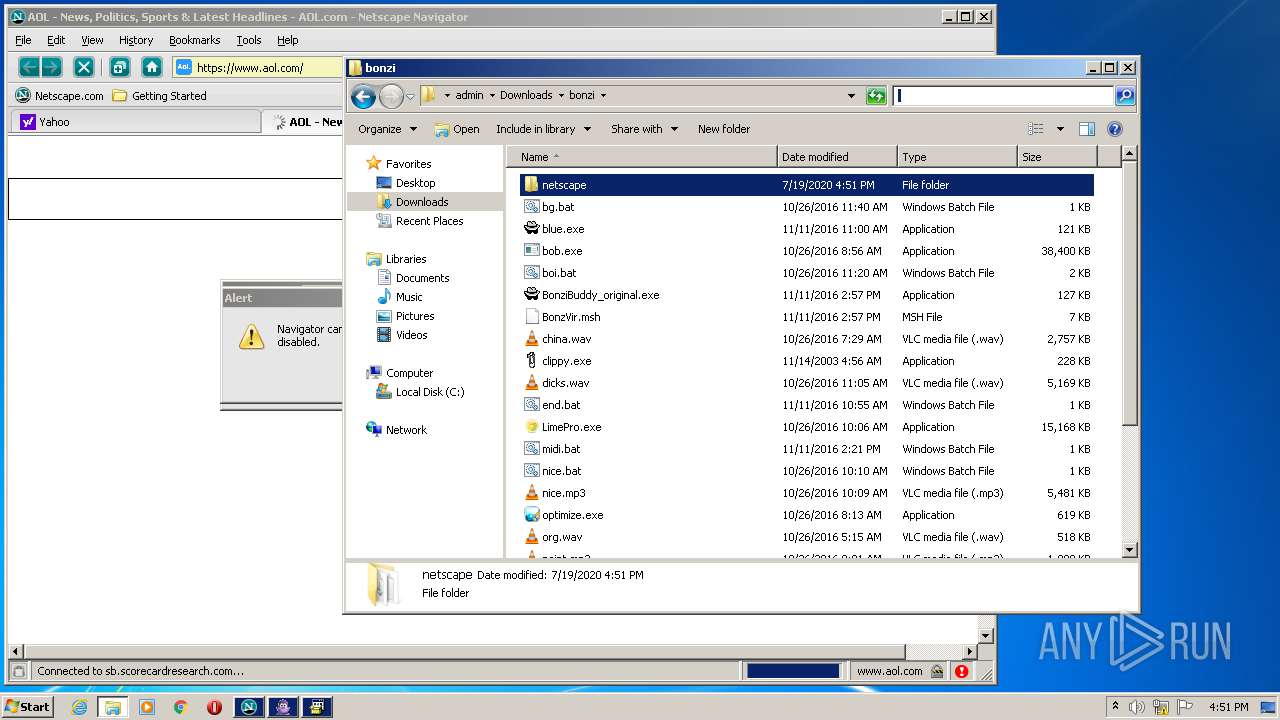
Actions looks like stealing of personal data
- navigator.exe (PID: 1588)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3480)
- navigator.exe (PID: 1588)
- navigator.exe (PID: 1116)
- navigator.exe (PID: 1264)
- BonziBuddy_original.exe (PID: 3984)
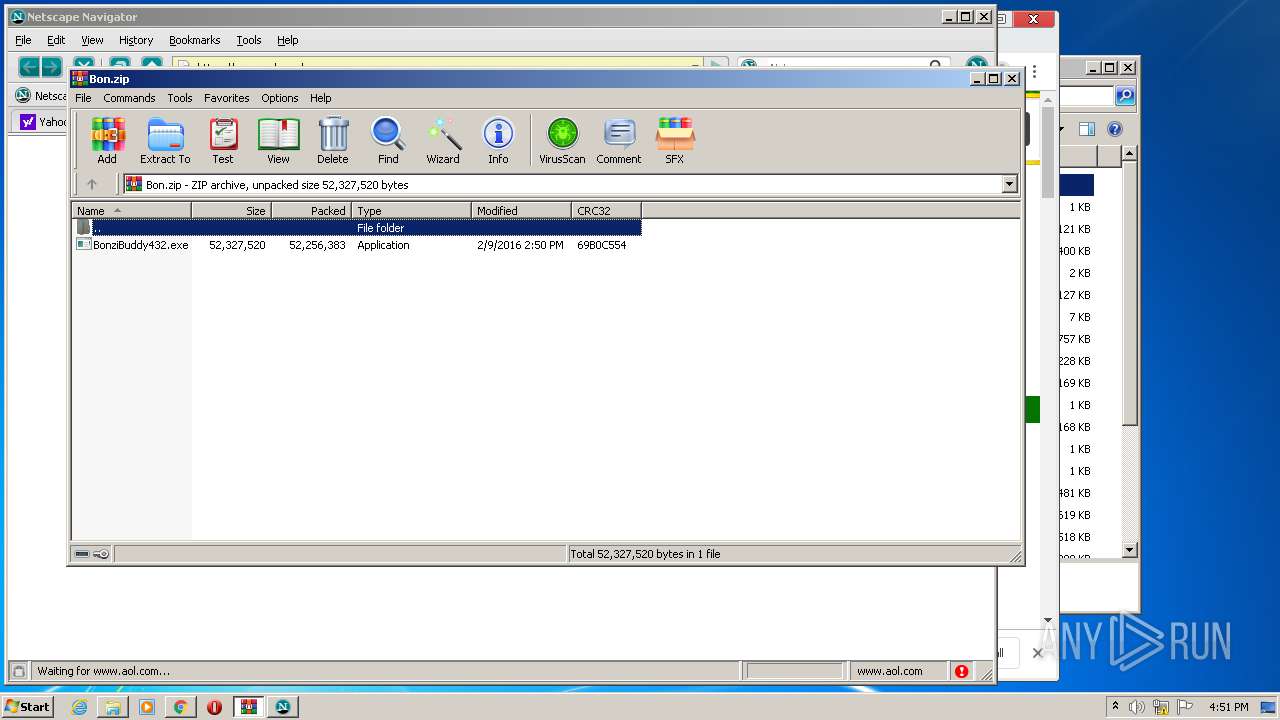
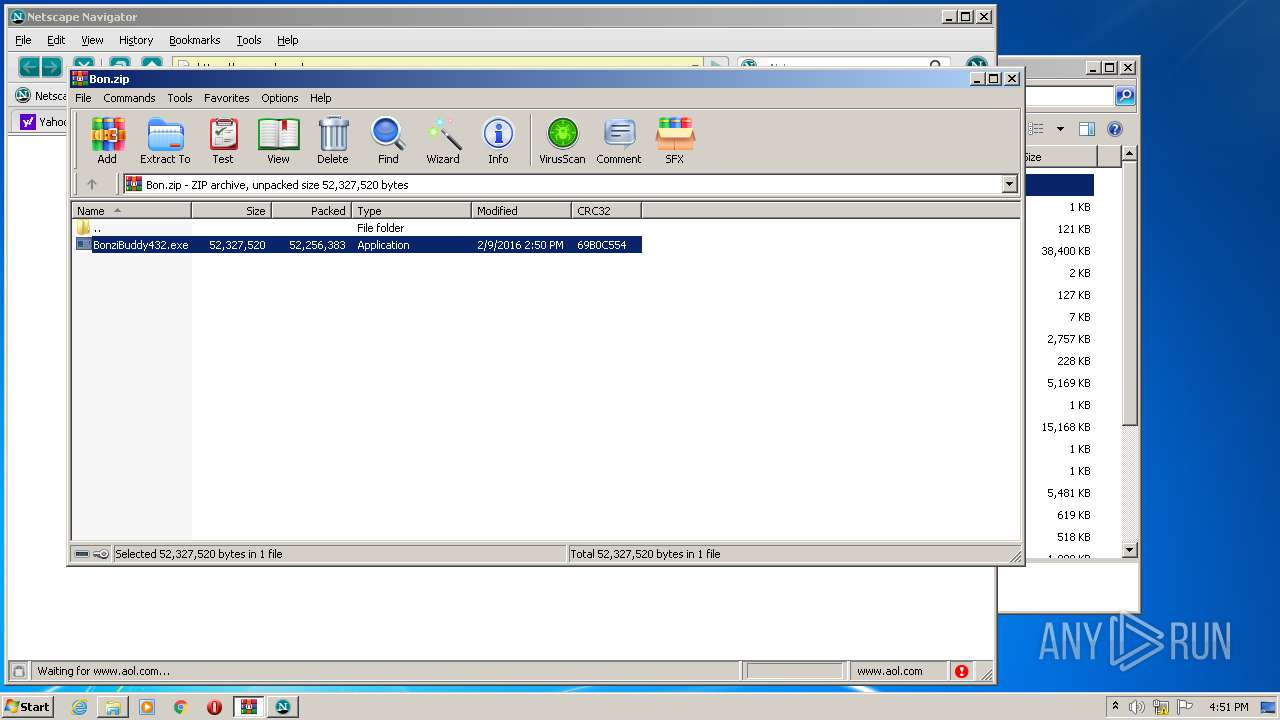
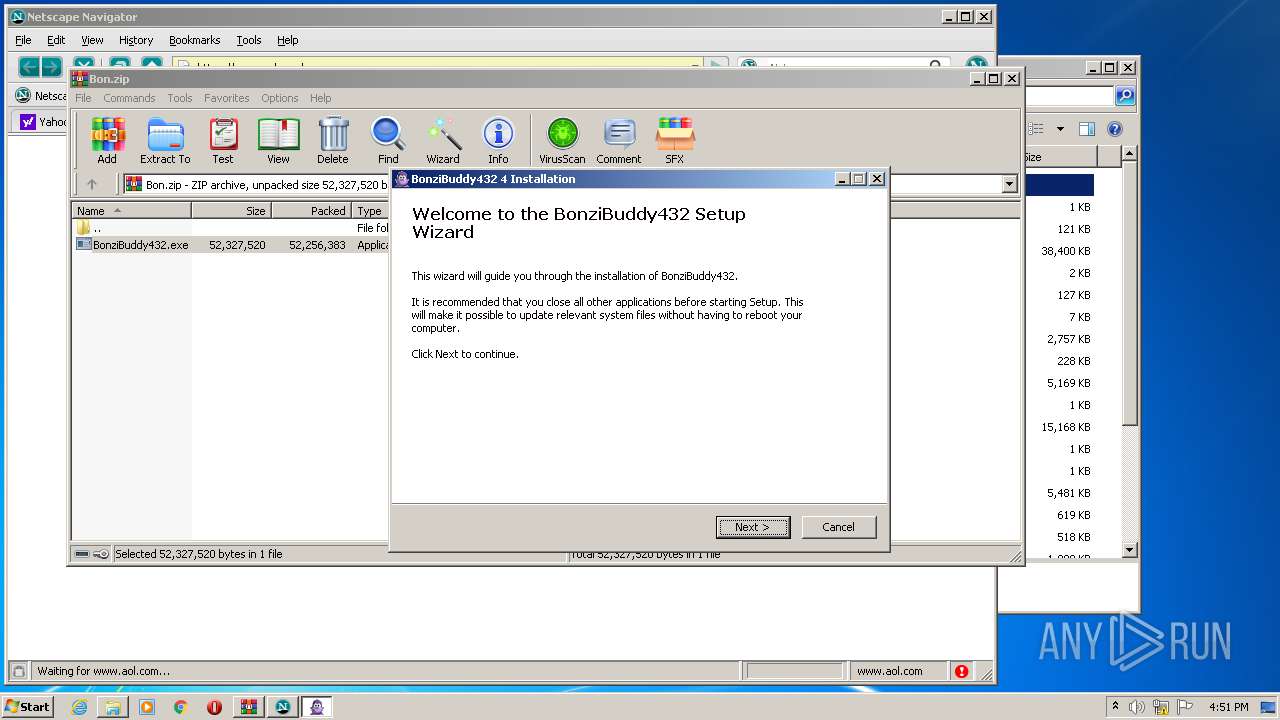
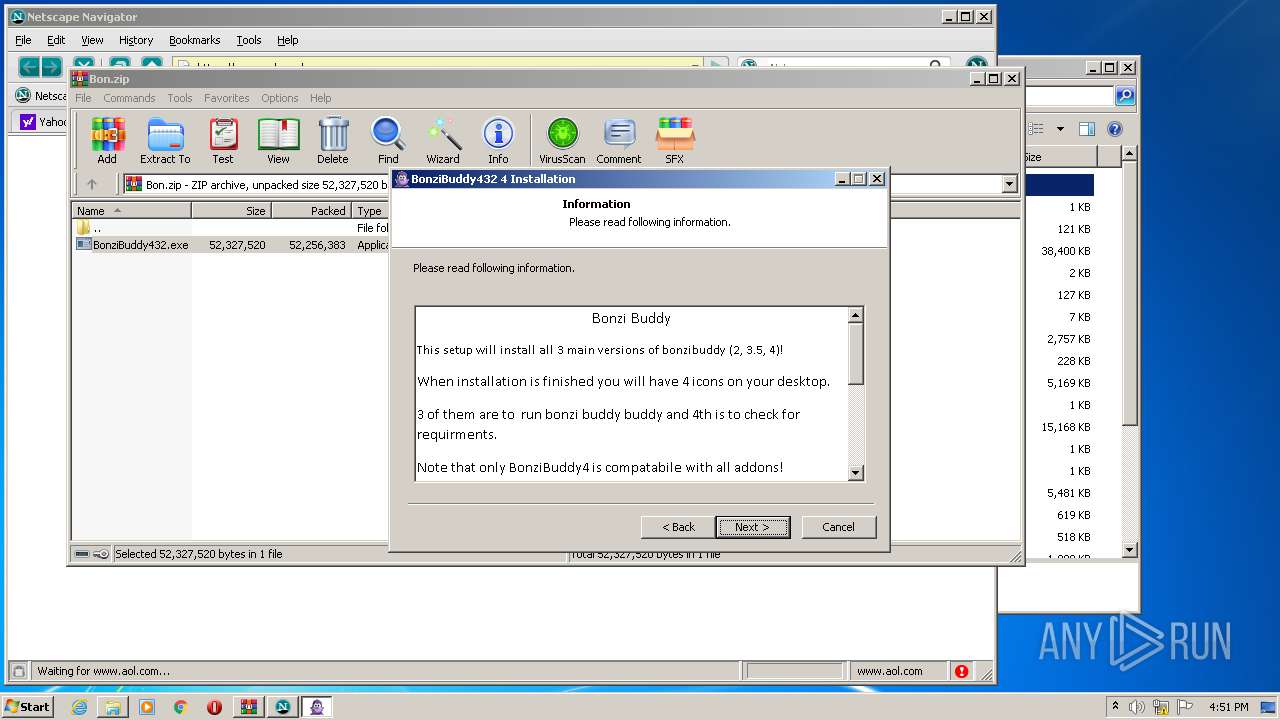
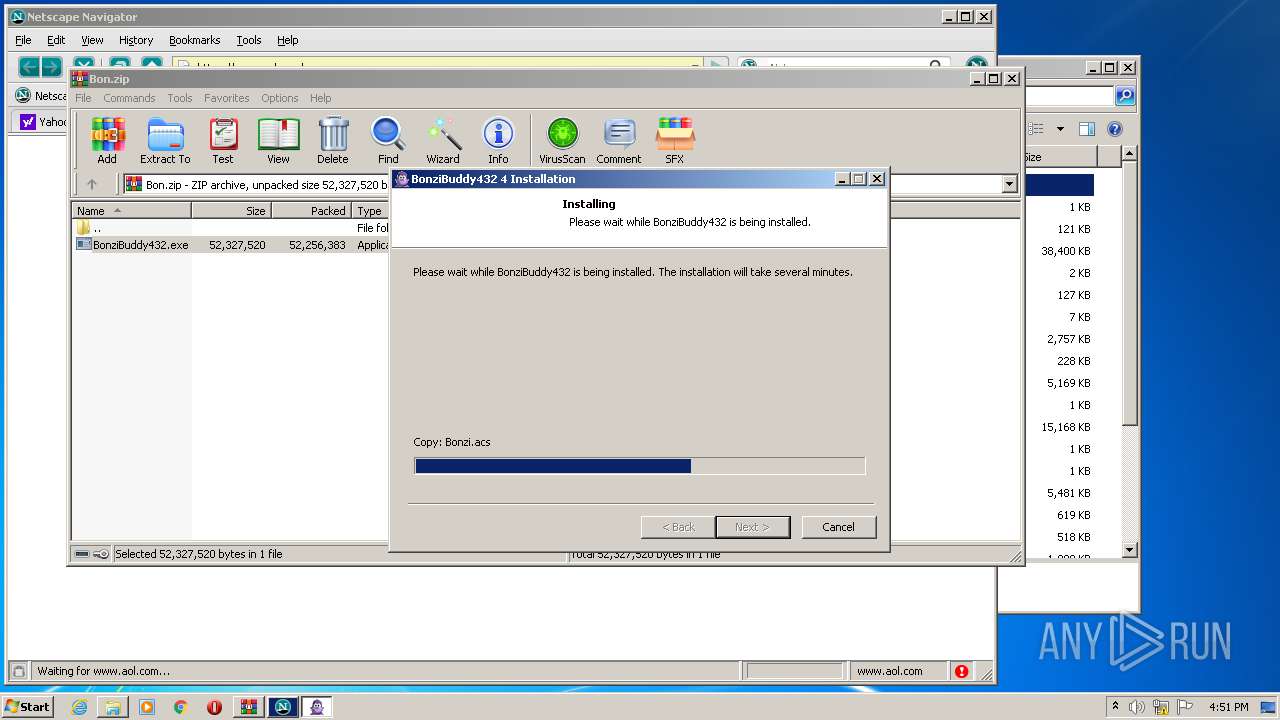
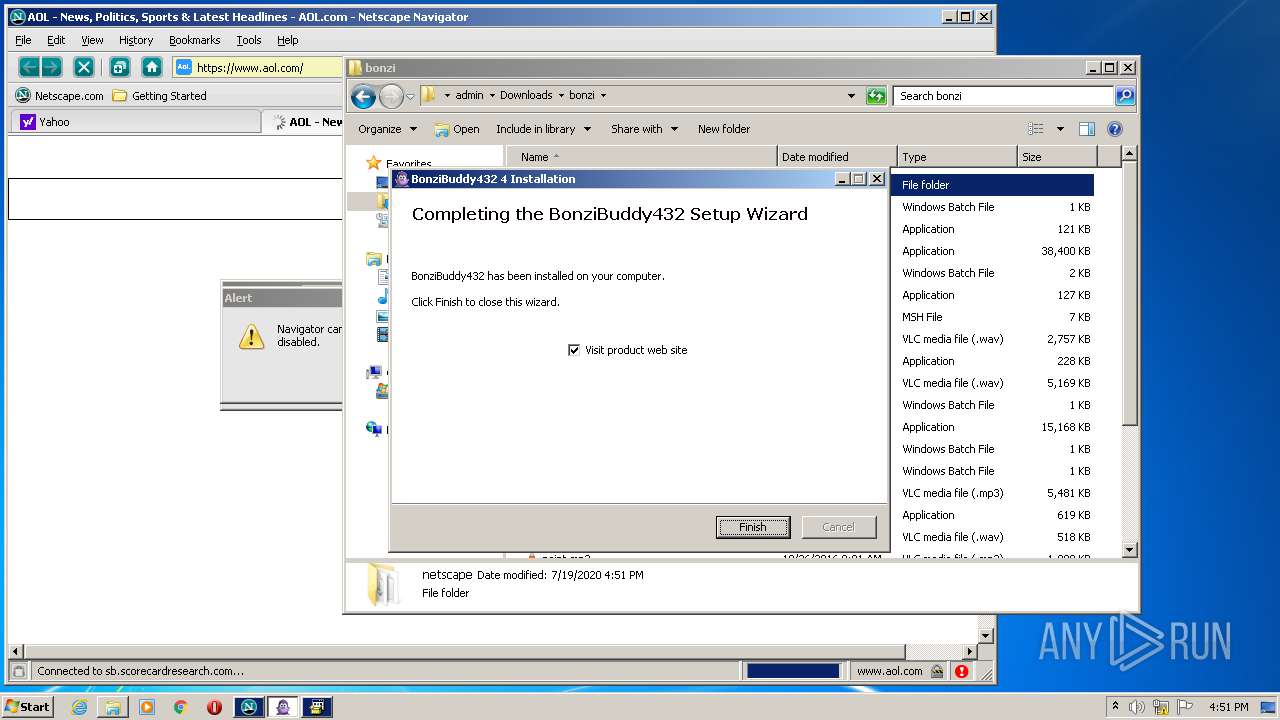
- BonziBuddy432.exe (PID: 2852)
- regsvr32.exe (PID: 2424)
- tv_enua.exe (PID: 3628)
- regsvr32.exe (PID: 2144)
Registers / Runs the DLL via REGSVR32.EXE
- tv_enua.exe (PID: 3628)
Changes the autorun value in the registry
- tv_enua.exe (PID: 3628)
SUSPICIOUS
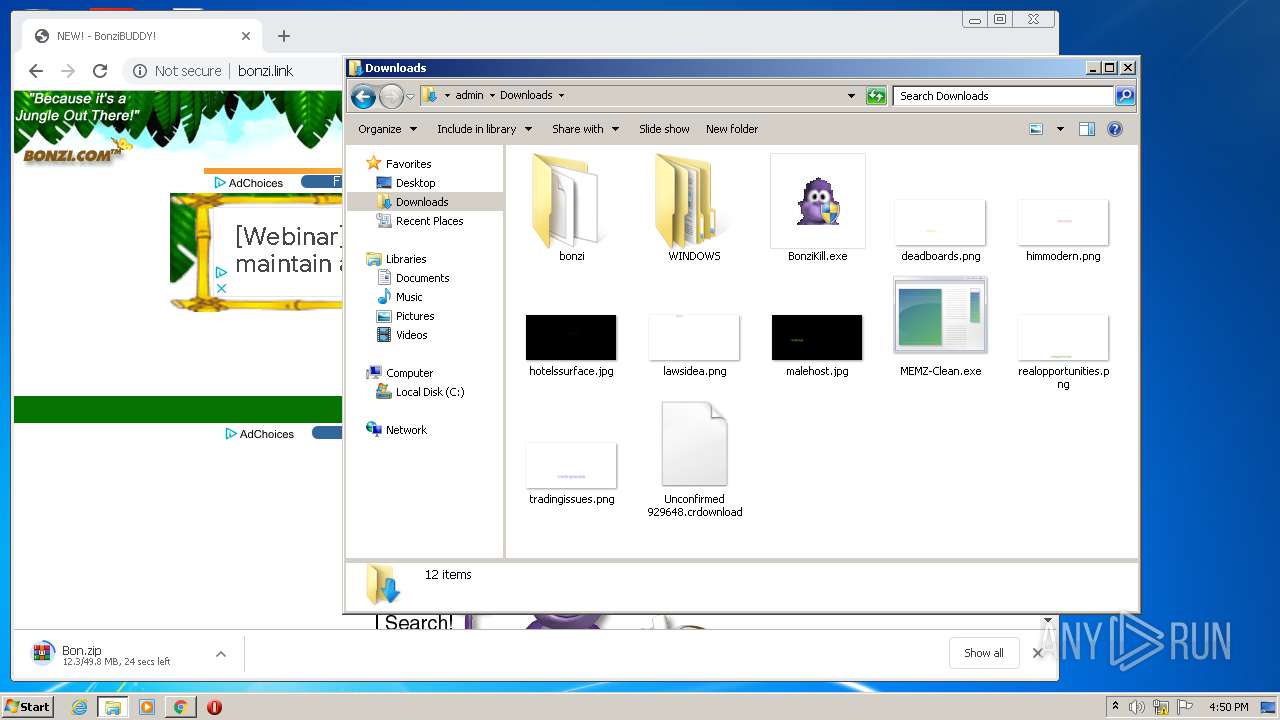
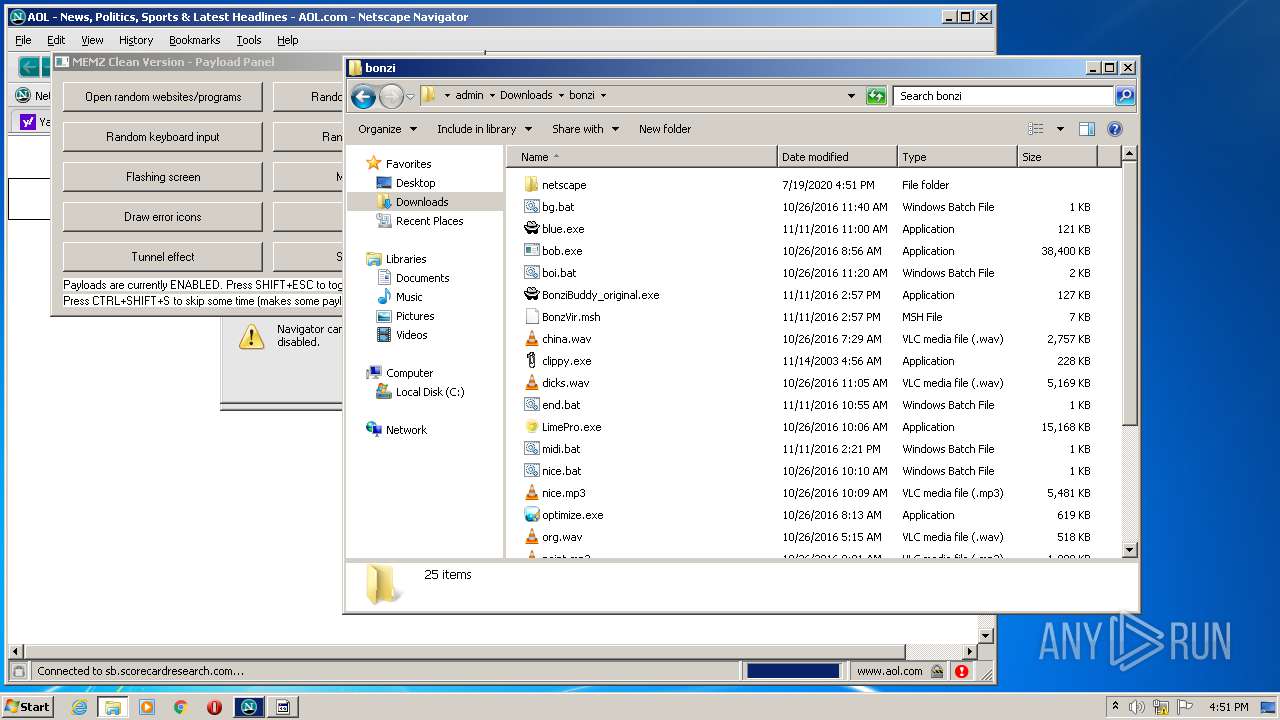
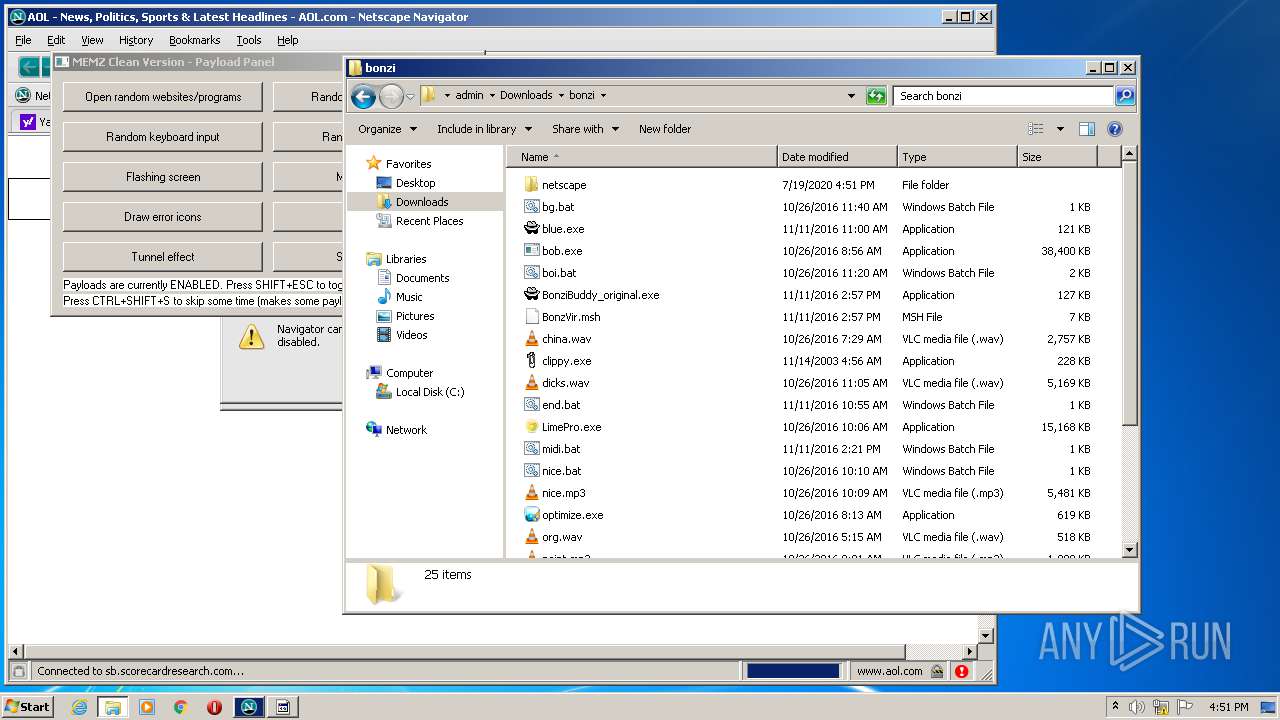
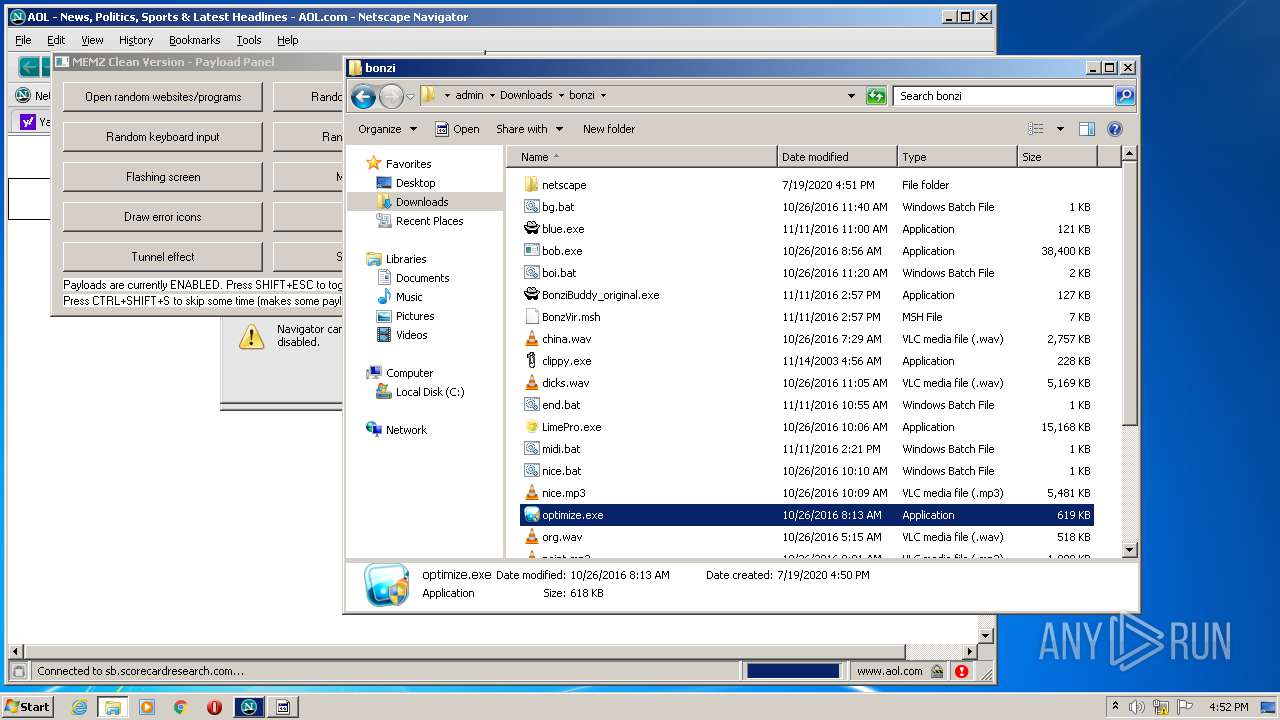
Creates files in the program directory
- firefox.exe (PID: 2864)
- BonziBuddy432.exe (PID: 2852)
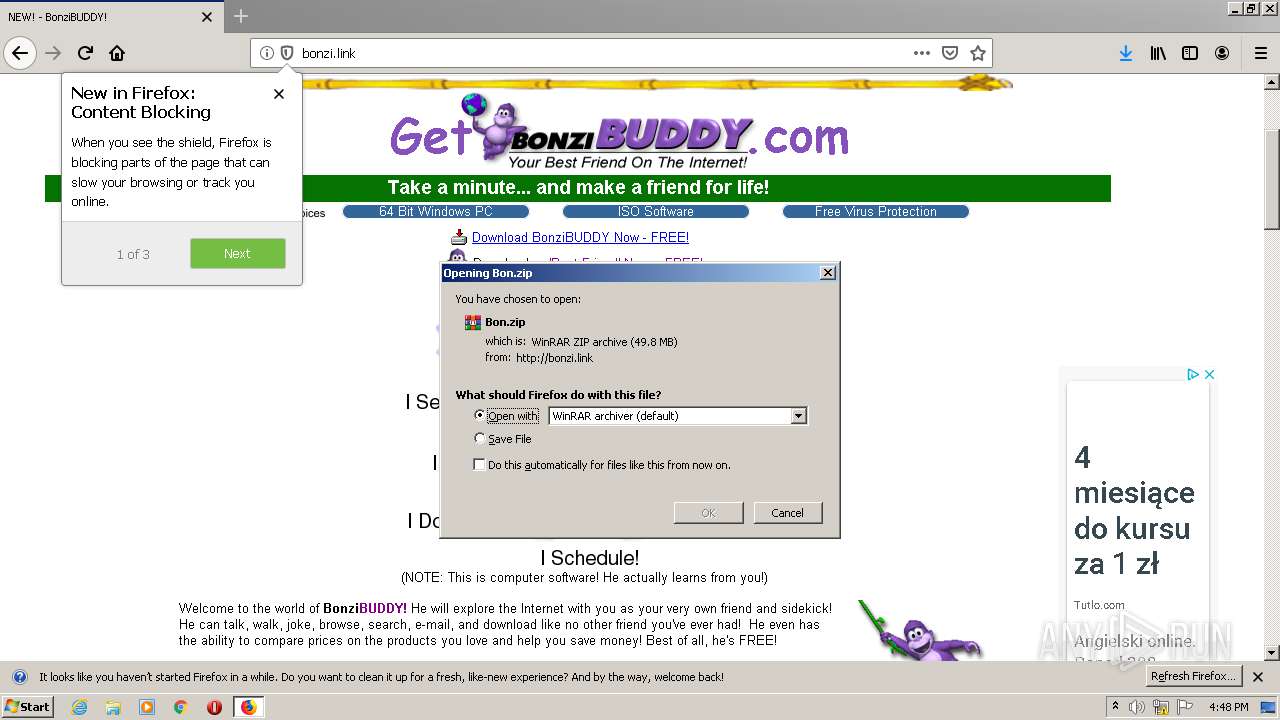
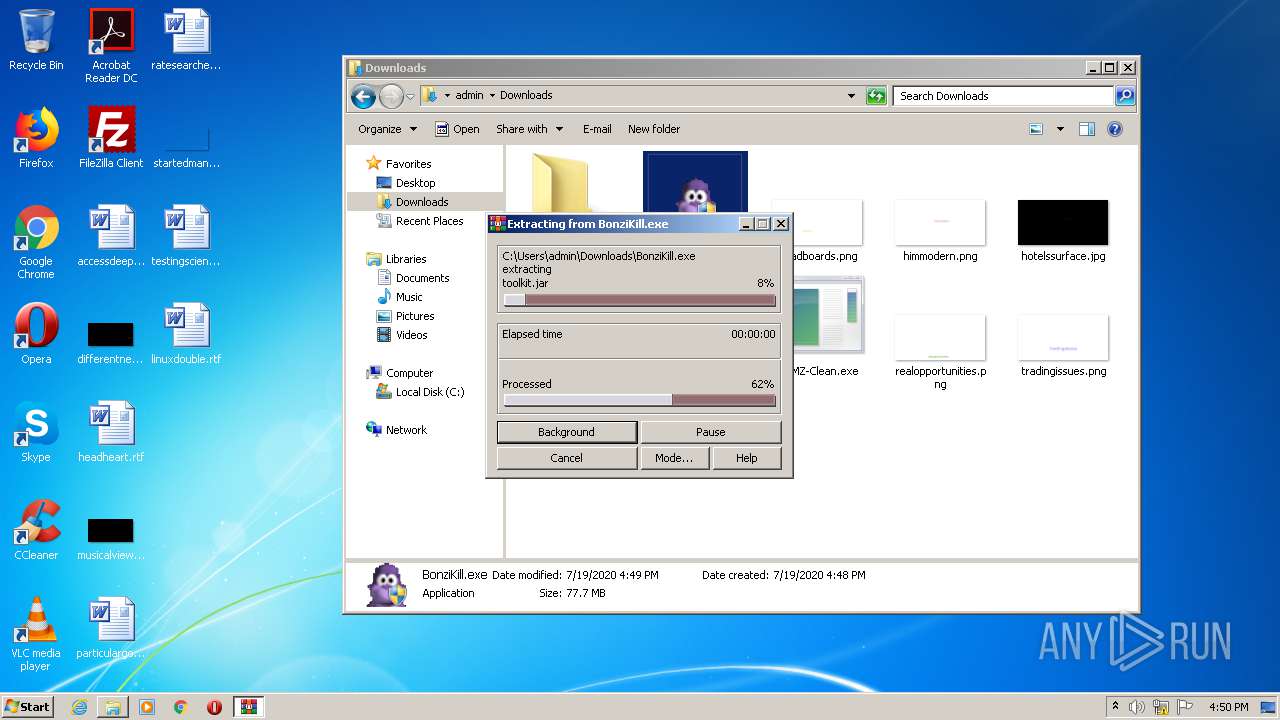
Executable content was dropped or overwritten
- firefox.exe (PID: 2864)
- BonziKill.exe (PID: 2636)
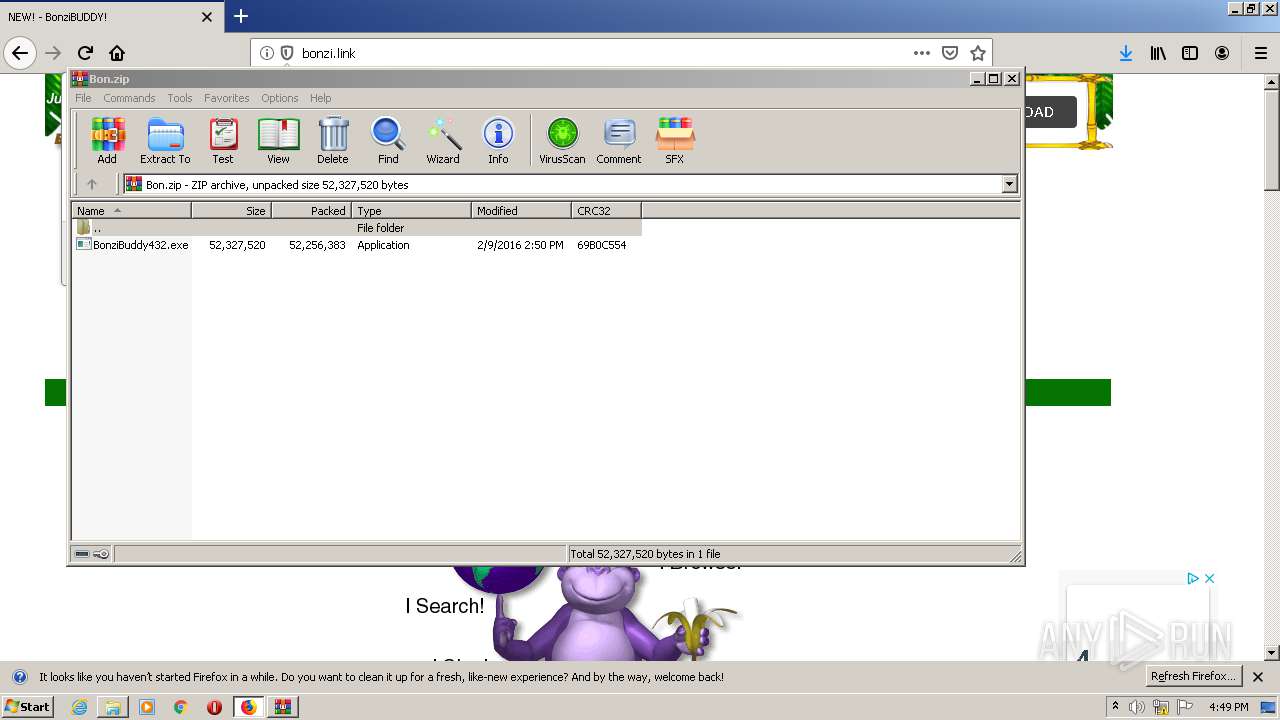
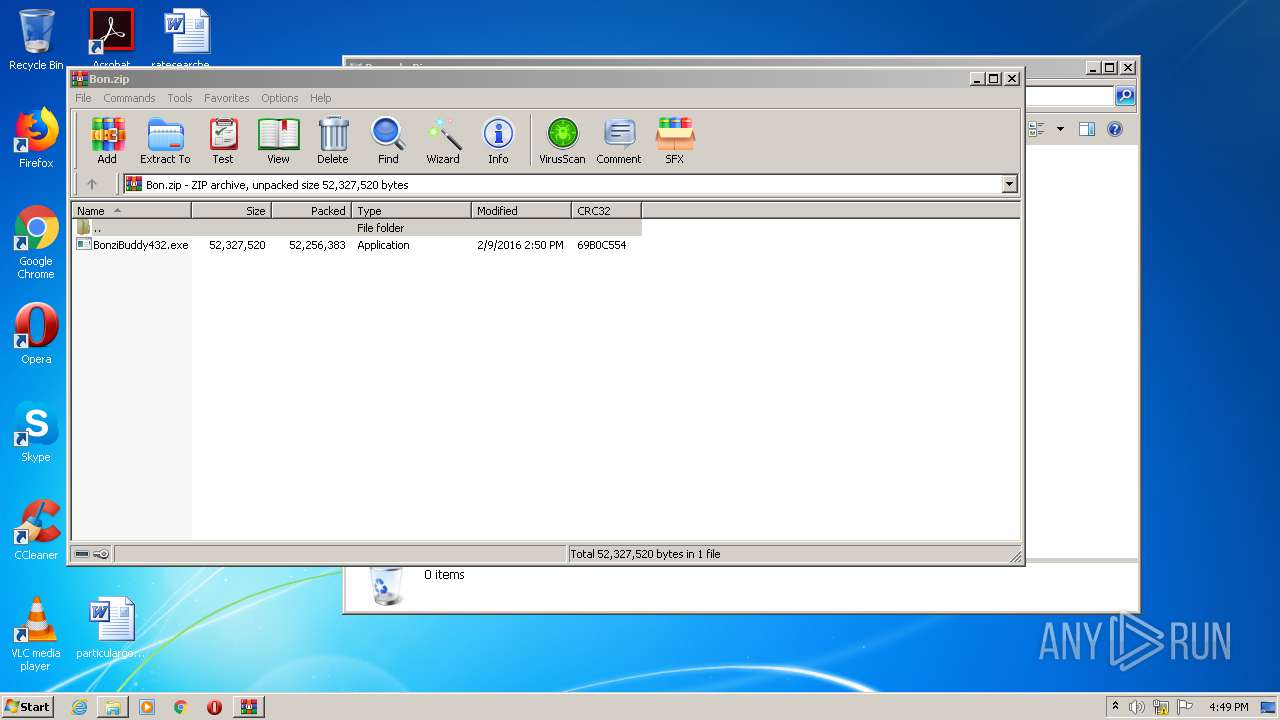
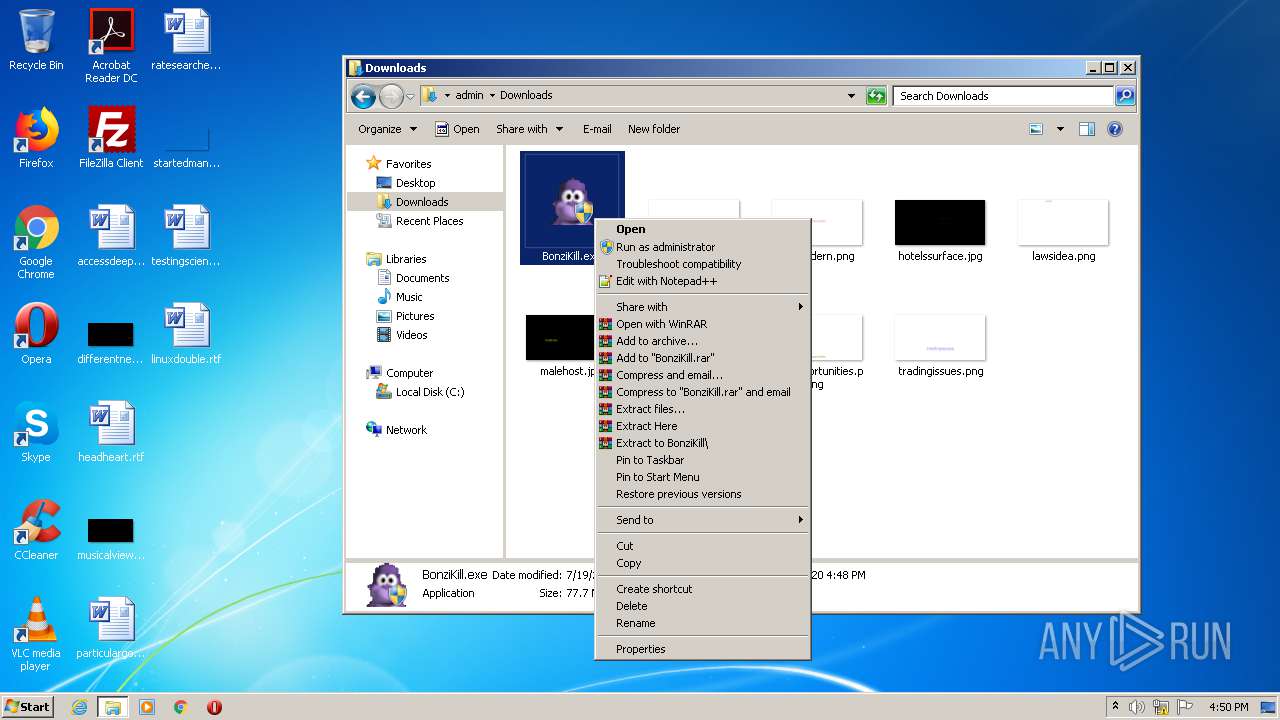
- WinRAR.exe (PID: 3956)
- tv_enua.exe (PID: 3628)
- BonziBuddy432.exe (PID: 2852)
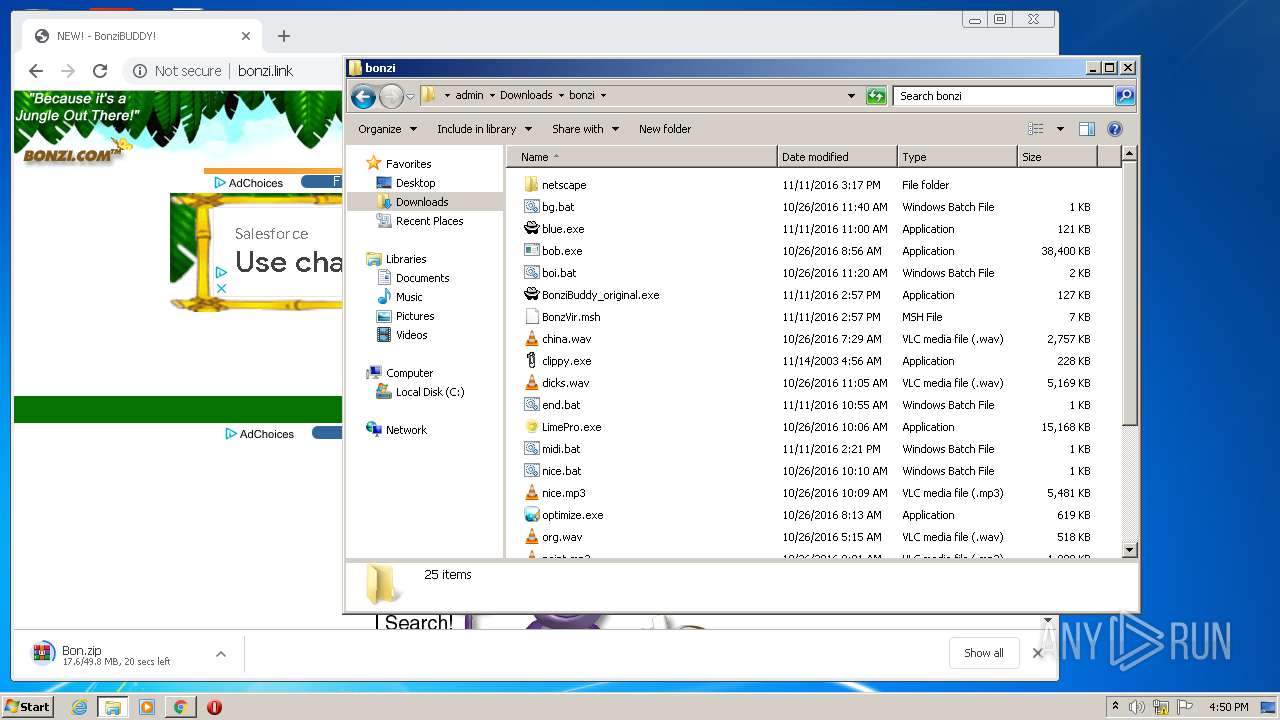
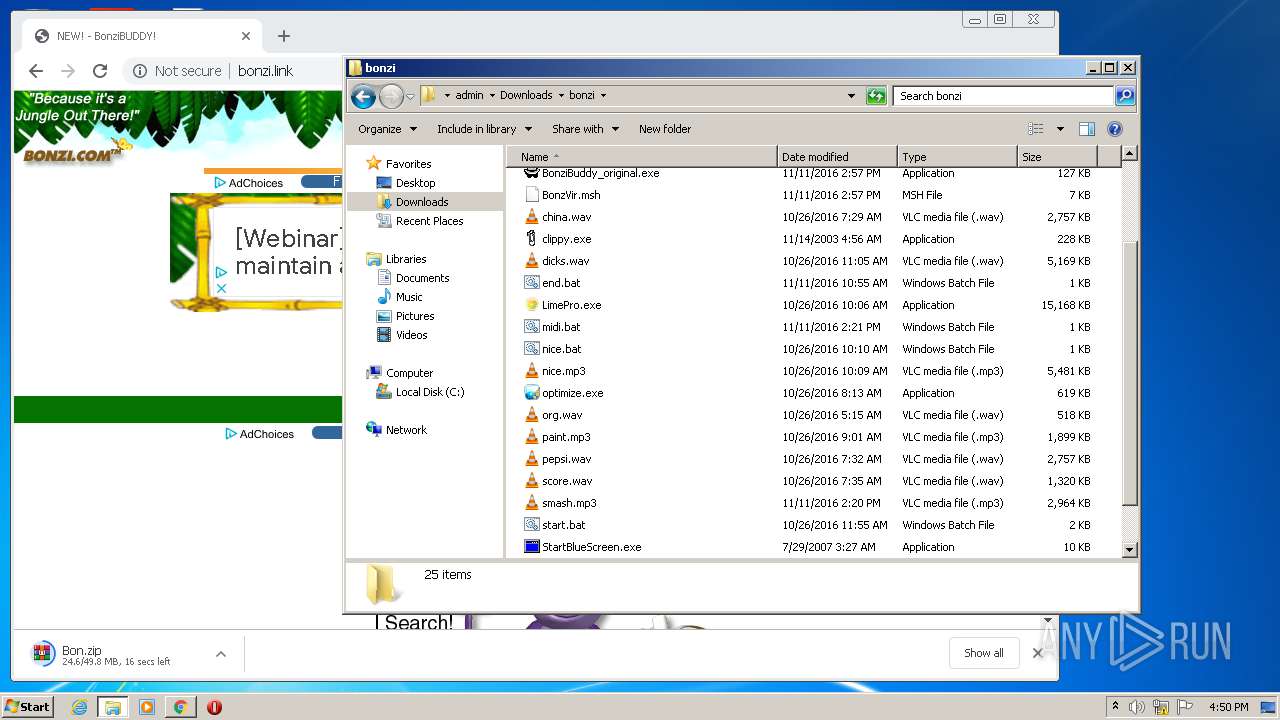
Creates files in the Windows directory
- BonziKill.exe (PID: 2636)
- BonziBuddy432.exe (PID: 2852)
- tv_enua.exe (PID: 3628)
Application launched itself
- navigator.exe (PID: 1116)
- navigator.exe (PID: 1588)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3160)
Creates files in the user directory
- navigator.exe (PID: 1116)
- navigator.exe (PID: 1588)
- navigator.exe (PID: 1264)
- BonziBuddy432.exe (PID: 2852)
Removes files from Windows directory
- BonziBuddy432.exe (PID: 2852)
- tv_enua.exe (PID: 3628)
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 2852)
- tv_enua.exe (PID: 3628)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 2852)
Creates COM task schedule object
- regsvr32.exe (PID: 2144)
- regsvr32.exe (PID: 2424)
INFO
Application launched itself
- firefox.exe (PID: 2864)
- firefox.exe (PID: 1428)
- chrome.exe (PID: 3160)
Reads CPU info
- firefox.exe (PID: 2864)
Reads Internet Cache Settings
- firefox.exe (PID: 2864)
- chrome.exe (PID: 3160)
Adds / modifies Windows certificates
- pingsender.exe (PID: 676)
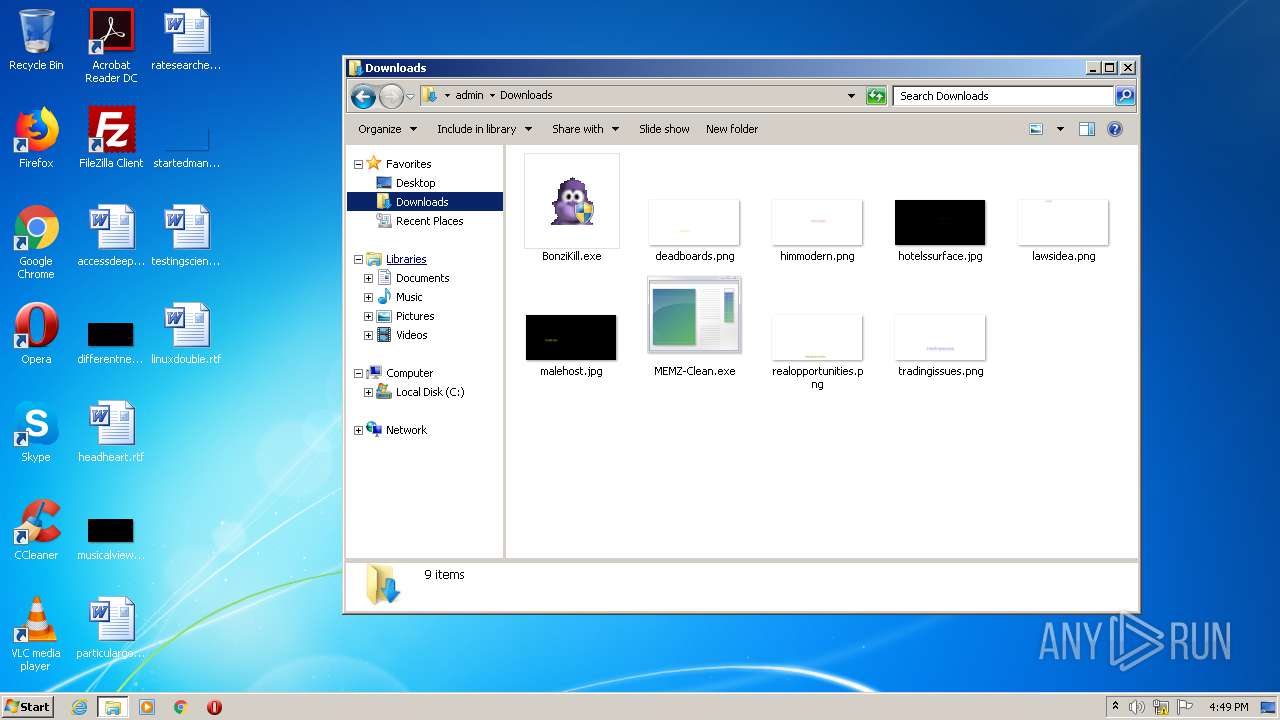
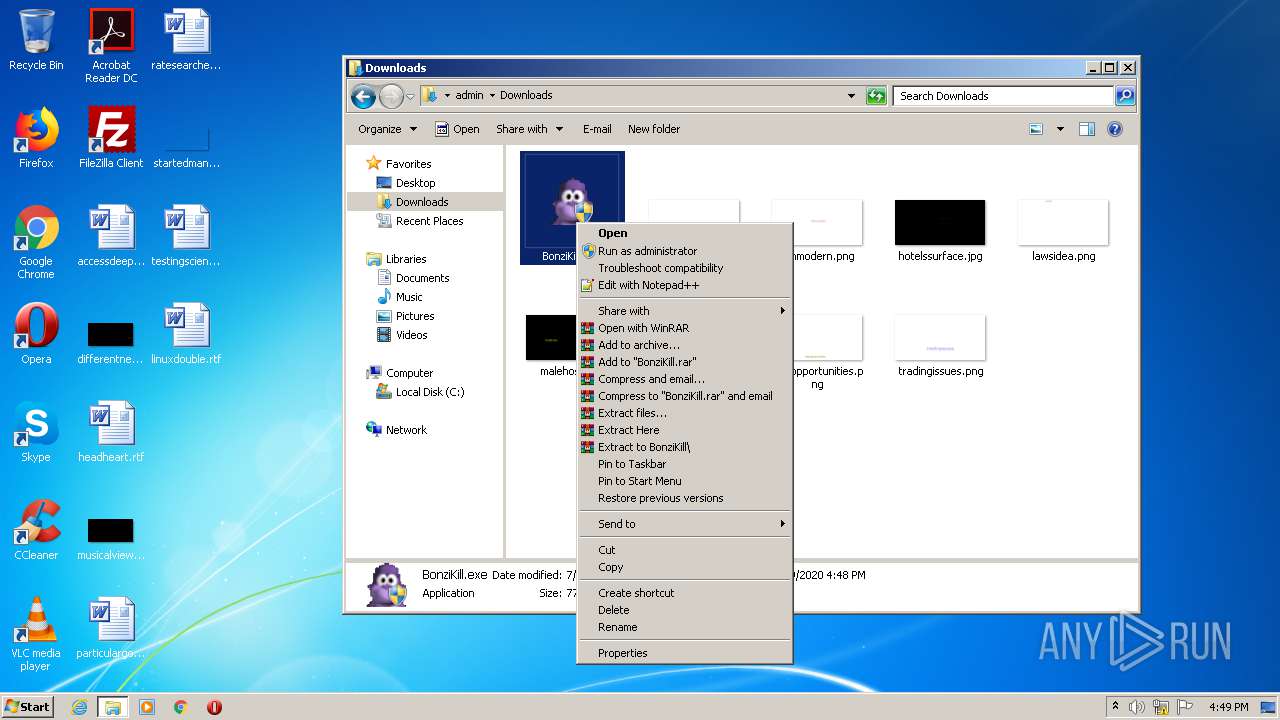
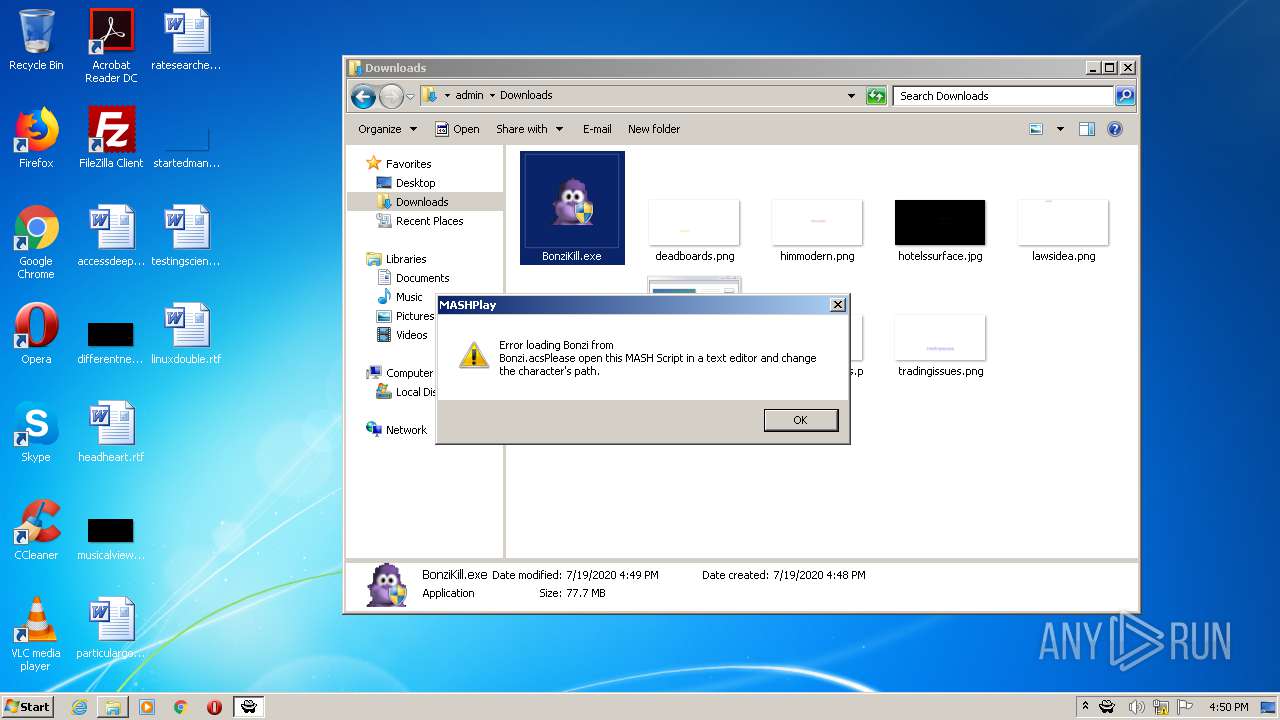
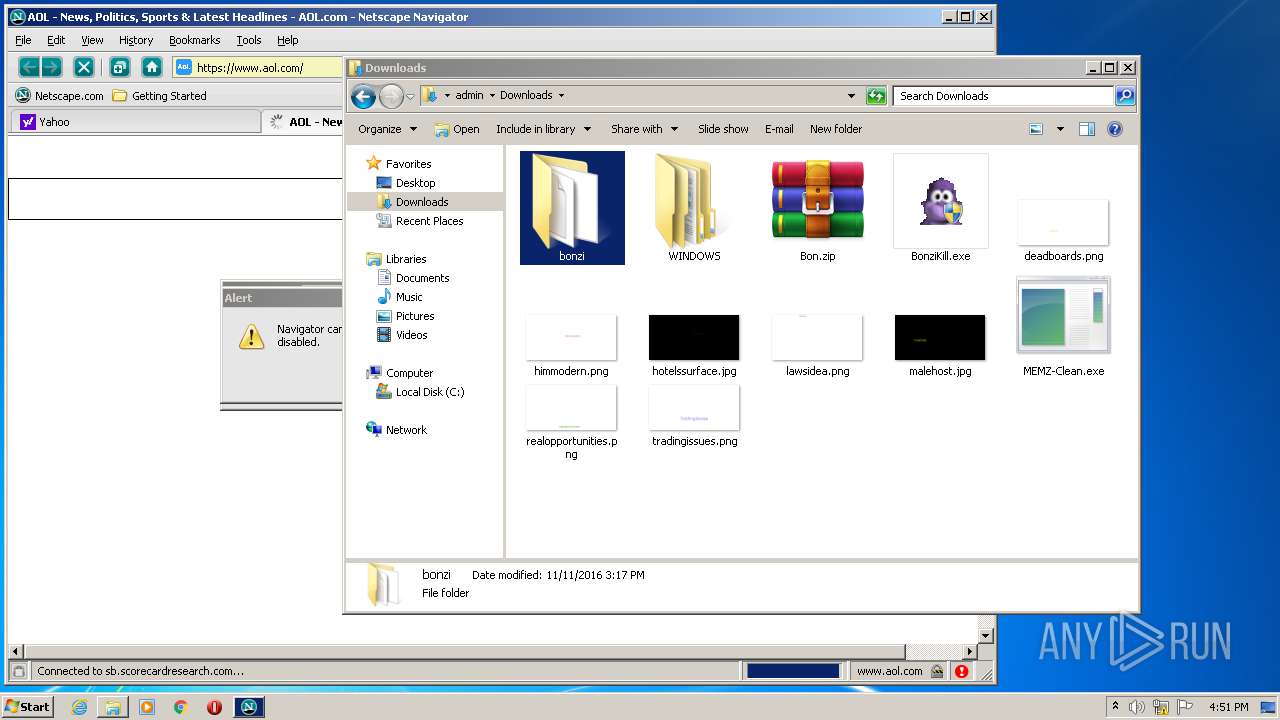
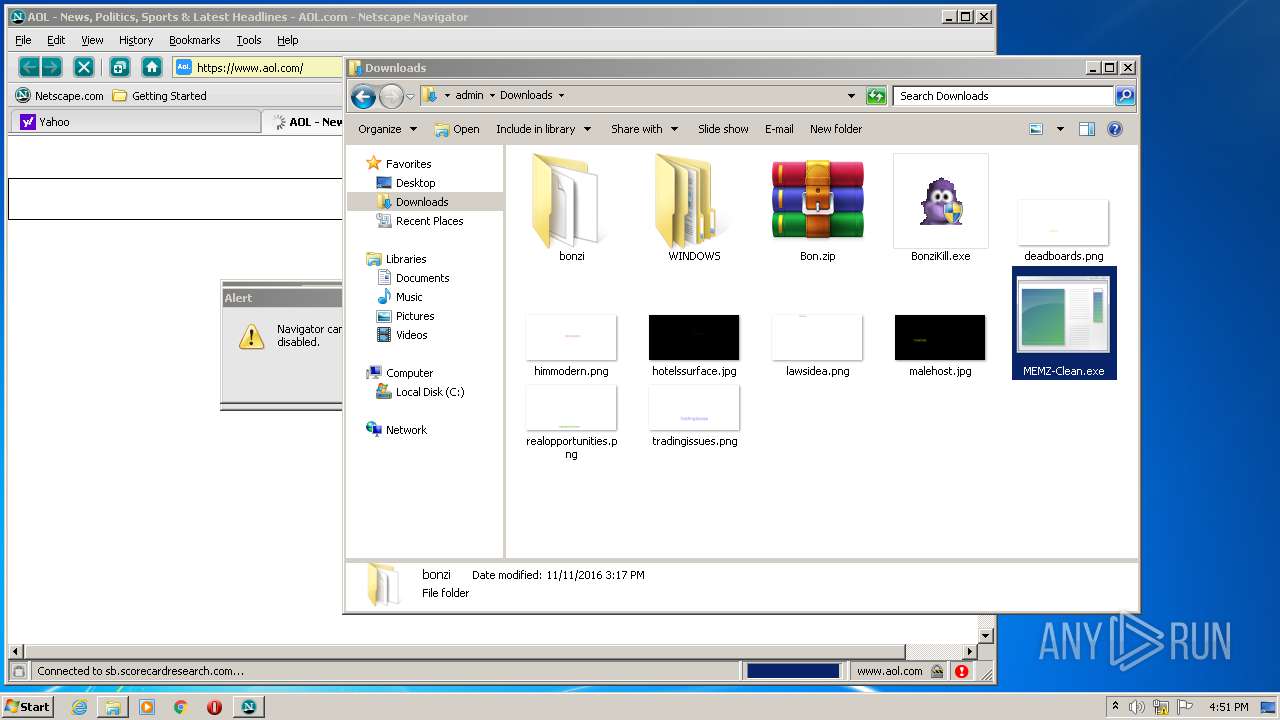
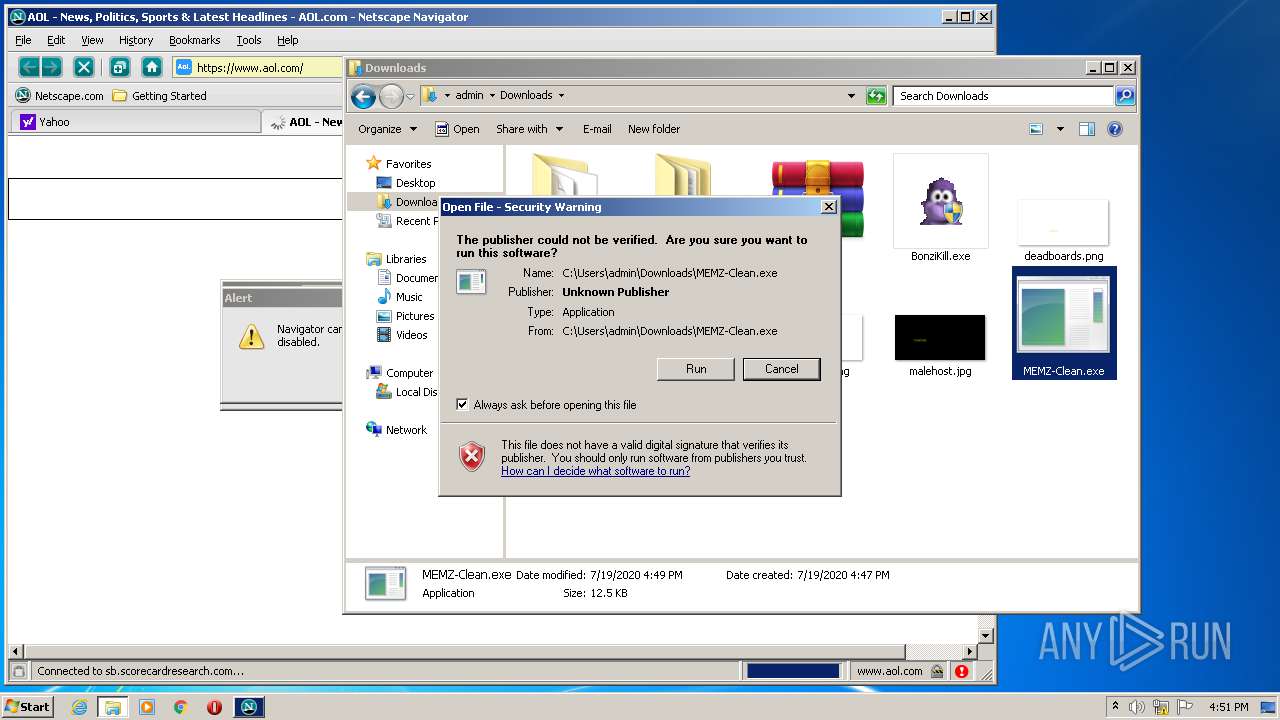
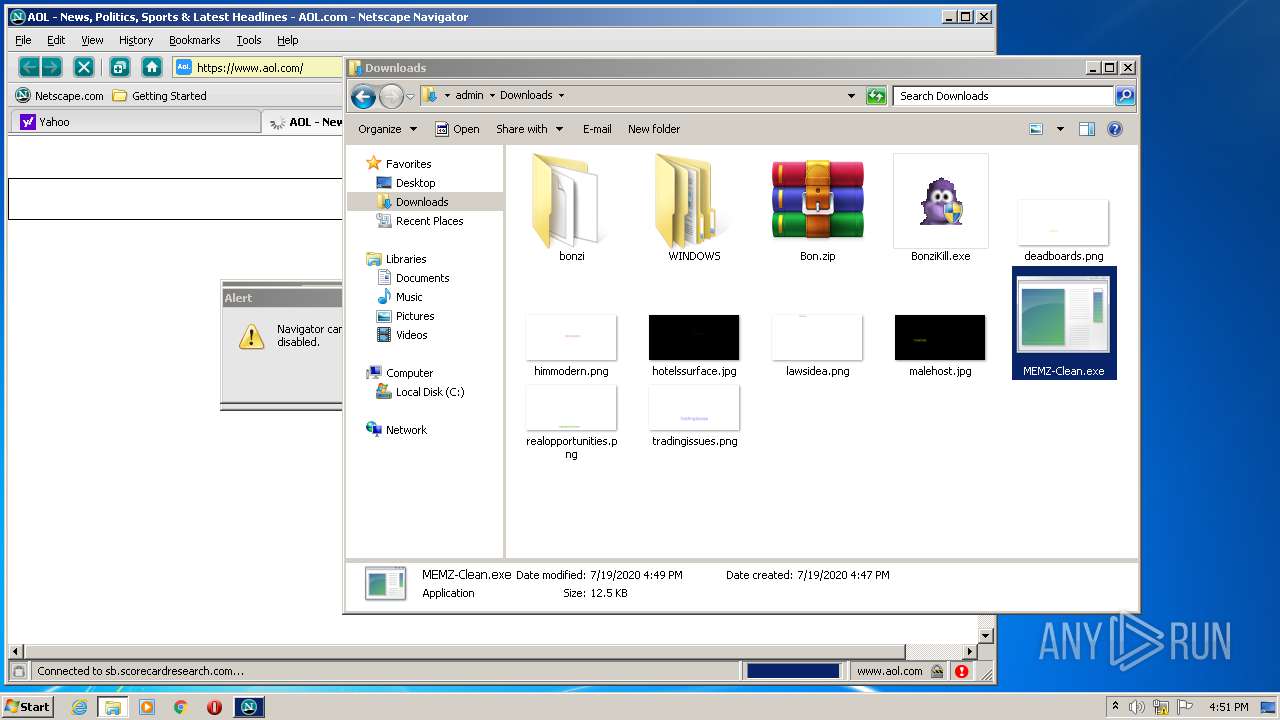
Manual execution by user
- BonziKill.exe (PID: 2636)
- WinRAR.exe (PID: 3956)
- chrome.exe (PID: 3160)
- navigator.exe (PID: 1116)
- MEMZ-Clean.exe (PID: 2872)
Changes settings of System certificates
- pingsender.exe (PID: 676)
Reads the hosts file
- chrome.exe (PID: 2524)
- chrome.exe (PID: 3160)
Reads settings of System Certificates
- chrome.exe (PID: 2524)
Creates files in the user directory
- firefox.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
115
Monitored processes
59
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | cmd /c ""C:\Program Files\BonziBuddy432\Runtimes\CheckRuntimes.bat" " | C:\Windows\system32\cmd.exe | — | BonziBuddy432.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3734970168024588066,2331383203264636795,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9911574678557001545 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3734970168024588066,2331383203264636795,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1475371652400209926 --mojo-platform-channel-handle=3628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/72453d19-b727-44a5-be64-462520c4f960/main/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\72453d19-b727-44a5-be64-462520c4f960 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
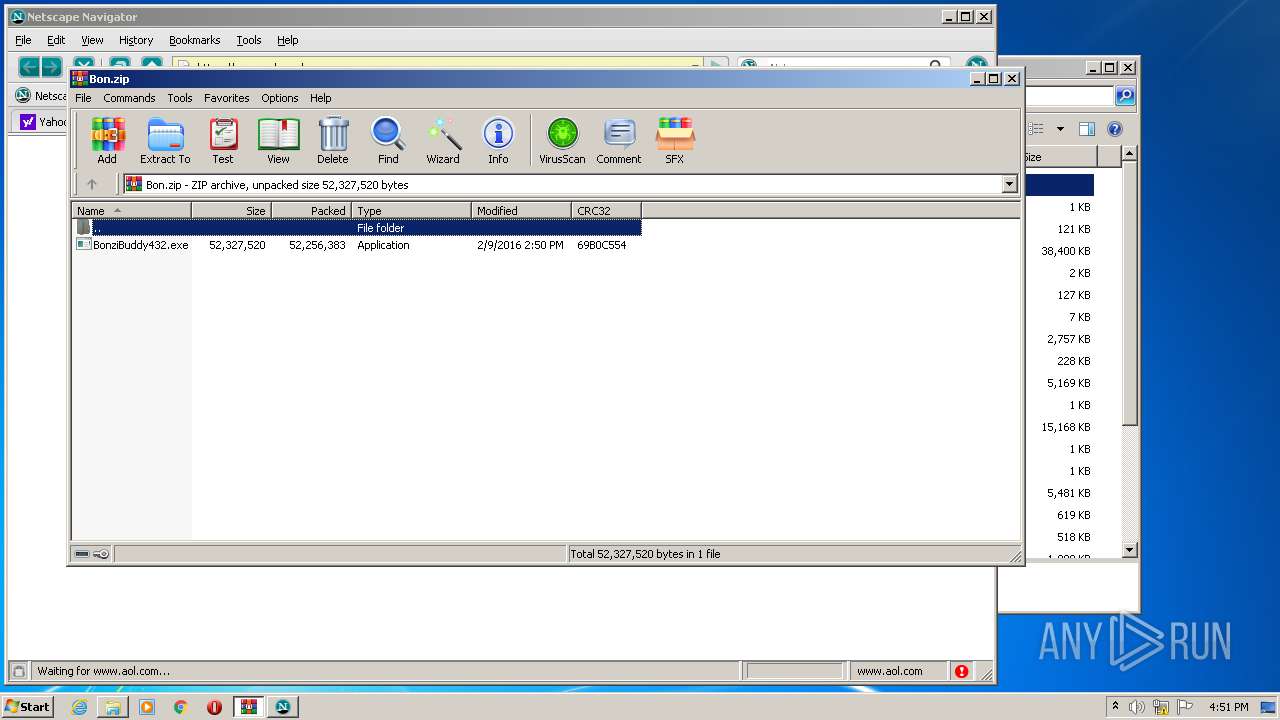
| 796 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Bon.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | firefox.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,3734970168024588066,2331383203264636795,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7089461034333354809 --mojo-platform-channel-handle=4900 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | grpconv.exe -o | C:\Windows\system32\grpconv.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
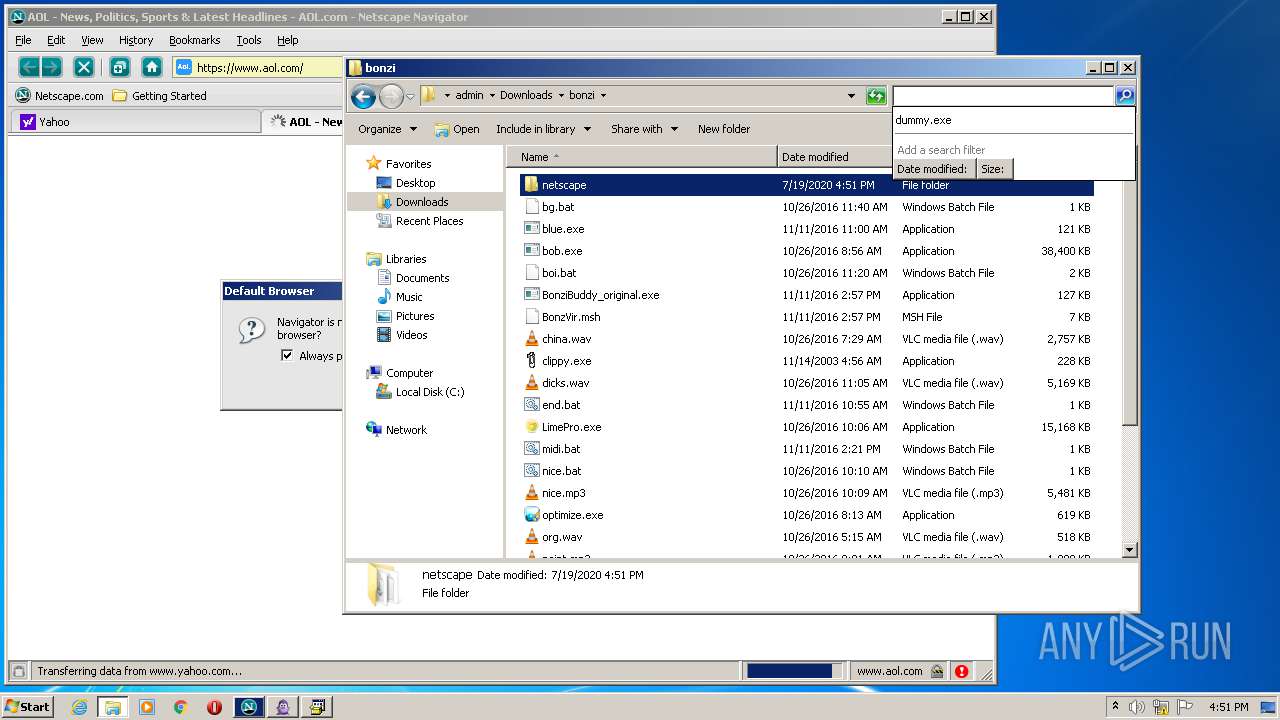
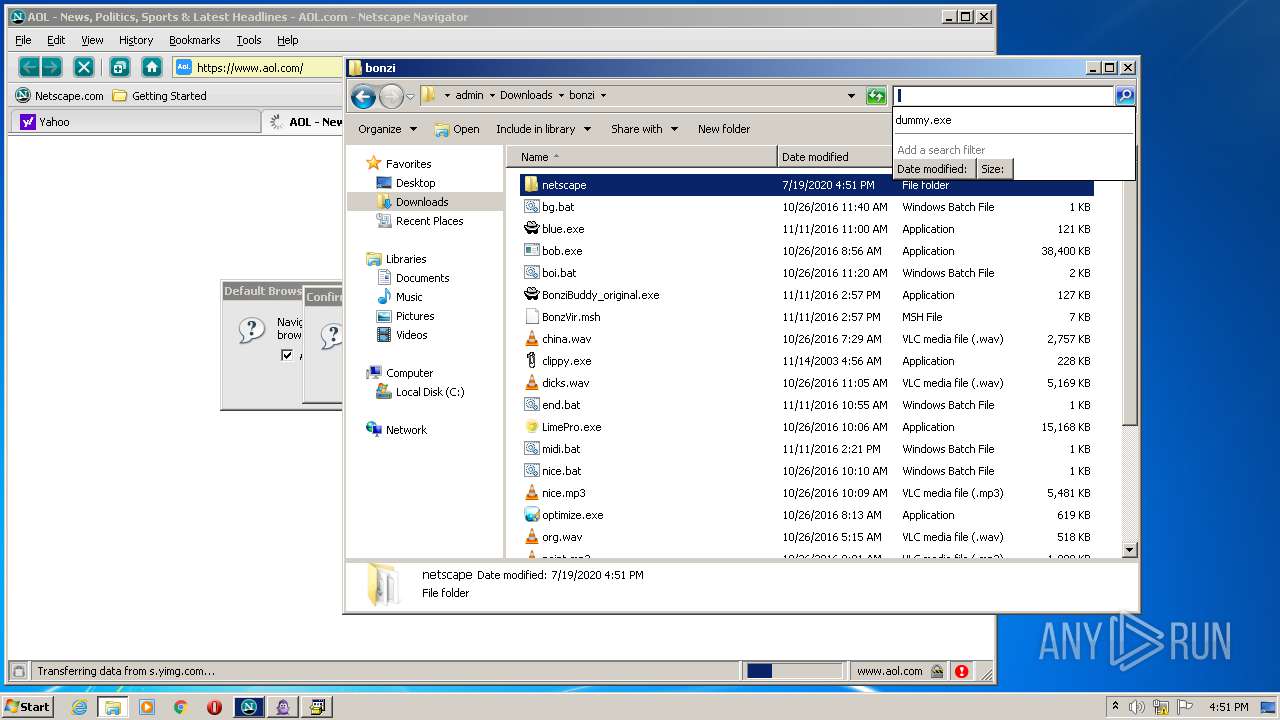
| 1116 | "C:\Users\admin\Downloads\bonzi\netscape\navigator.exe" | C:\Users\admin\Downloads\bonzi\netscape\navigator.exe | — | explorer.exe | |||||||||||
User: admin Company: Netscape Integrity Level: MEDIUM Description: Navigator Exit code: 0 Version: Personal Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3734970168024588066,2331383203264636795,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6701417164964928678 --mojo-platform-channel-handle=2264 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1264 | "C:\Users\admin\Downloads\bonzi\netscape\navigator.exe" | C:\Users\admin\Downloads\bonzi\netscape\navigator.exe | navigator.exe | ||||||||||||
User: admin Company: Netscape Integrity Level: MEDIUM Description: Navigator Exit code: 0 Version: Personal Modules
| |||||||||||||||
Total events
6 033
Read events
4 501
Write events
1 478
Delete events
54
Modification events
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 6402960500000000 | |||
| (PID) Process: | (1428) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 6302960500000000 | |||
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2864) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
171
Suspicious files
404
Text files
884
Unknown types
176
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\CF34632806DC502706207394B3DF787834FD3D16 | der | |
MD5:— | SHA256:— | |||
| 2864 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\3398711F4F6ADDB84139AD7F73C74168F4D30336 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
161
DNS requests
198
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2864 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
2864 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2864 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2864 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2864 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
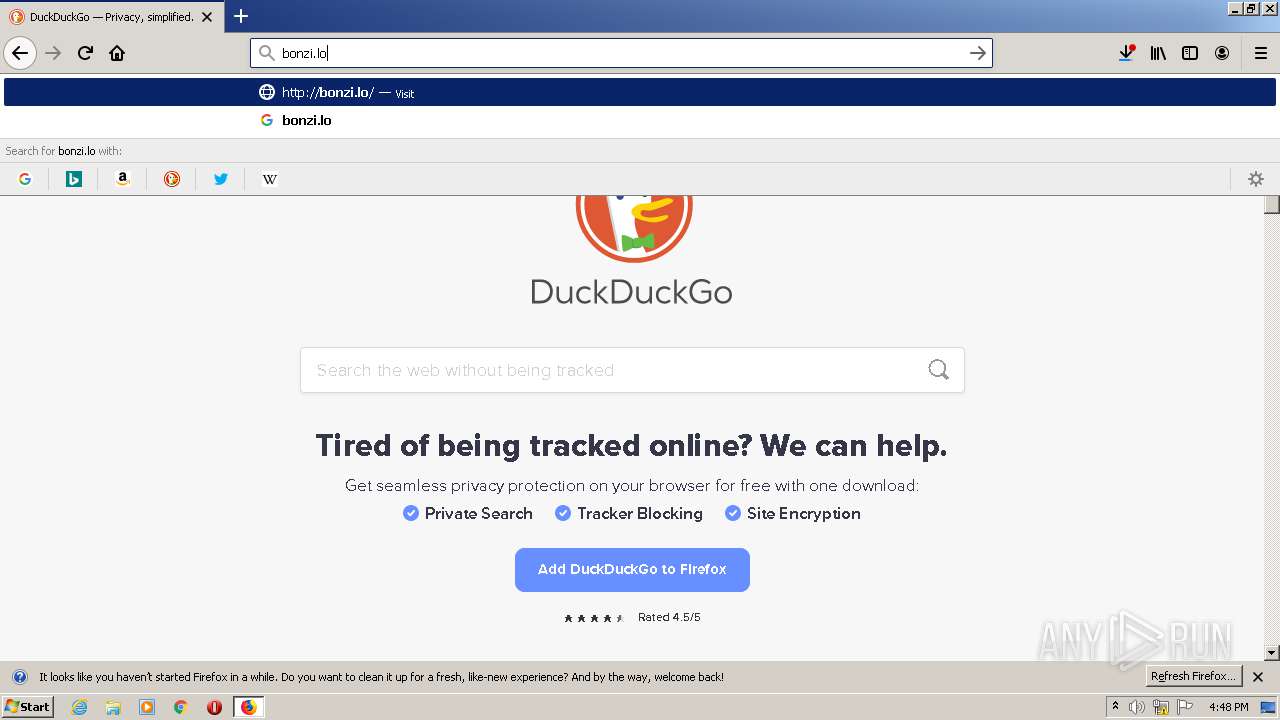
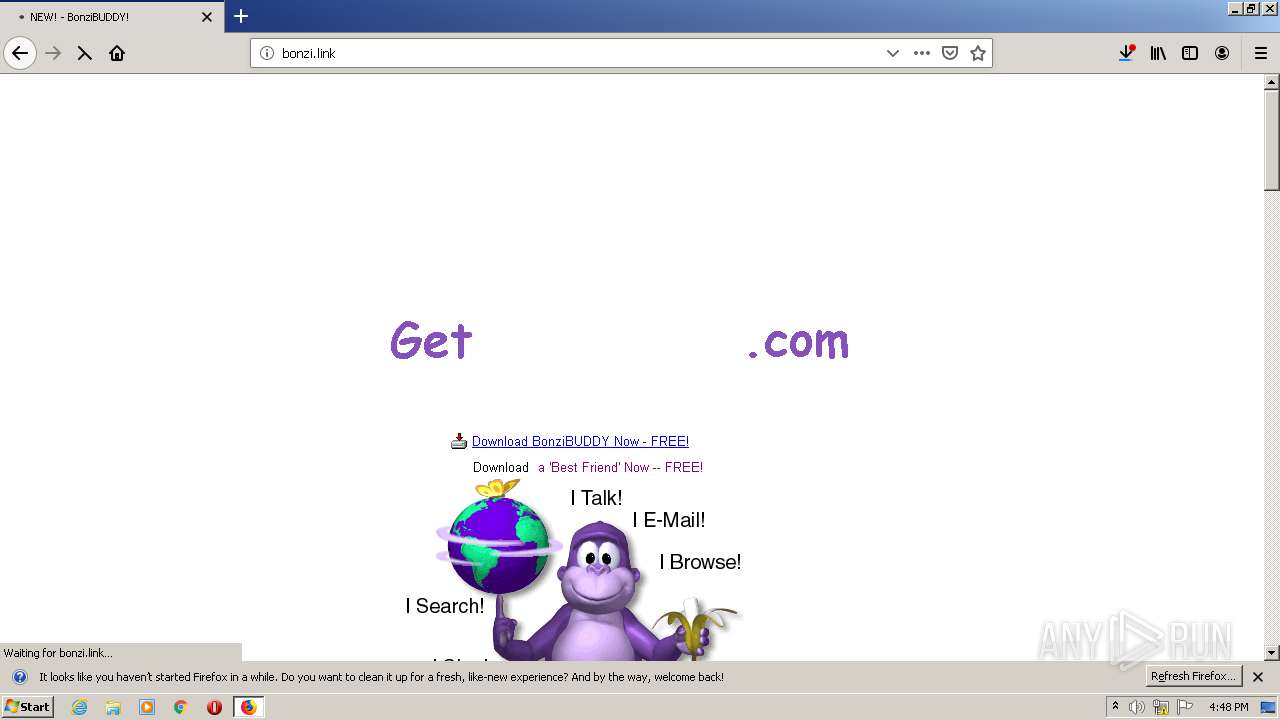
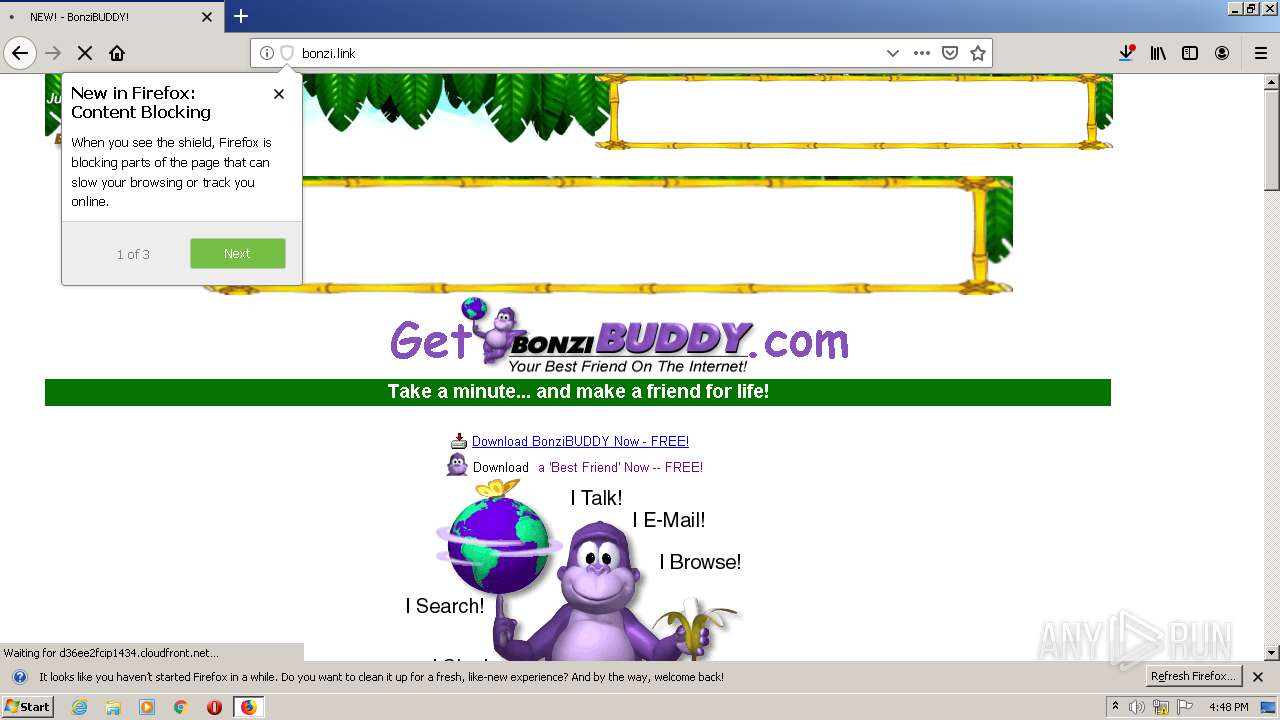
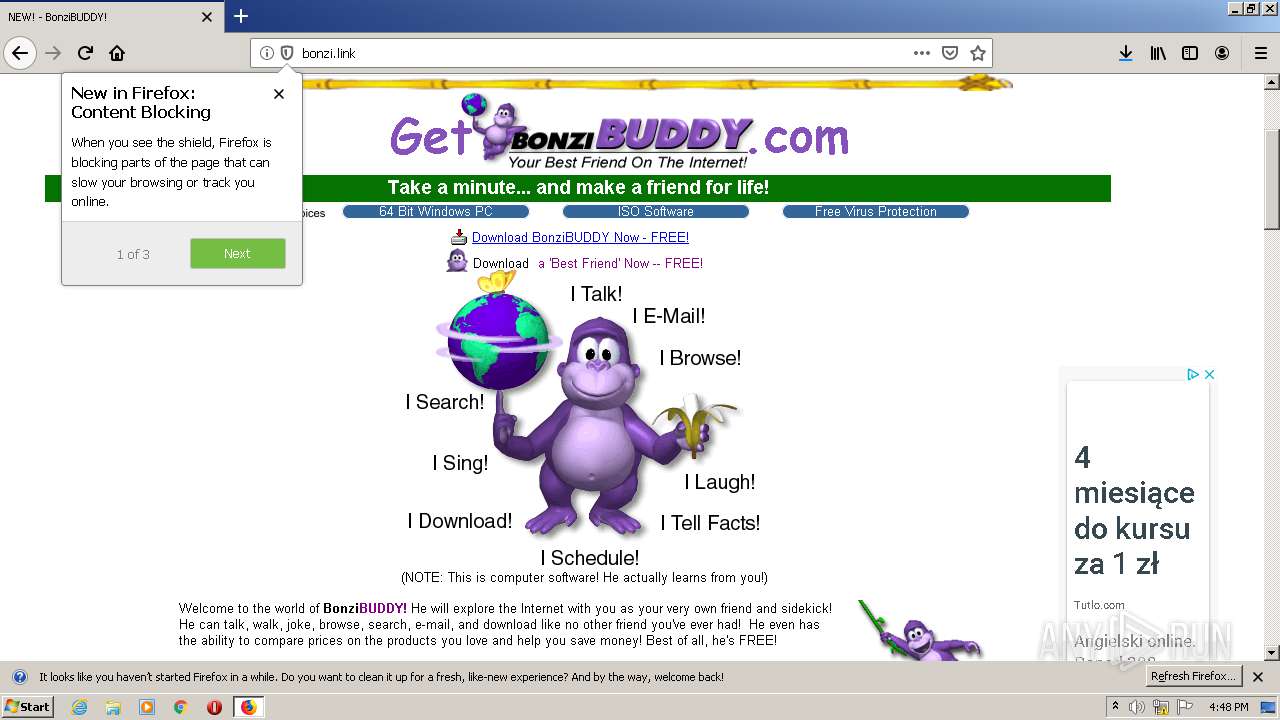
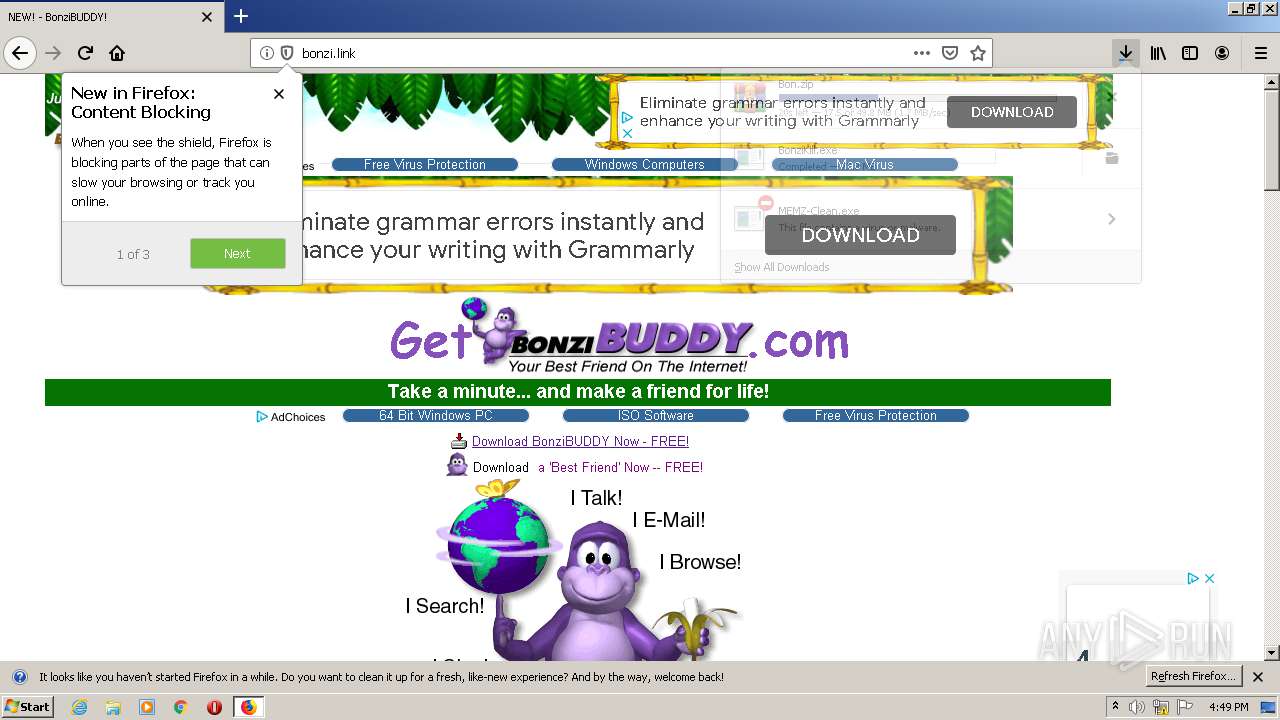
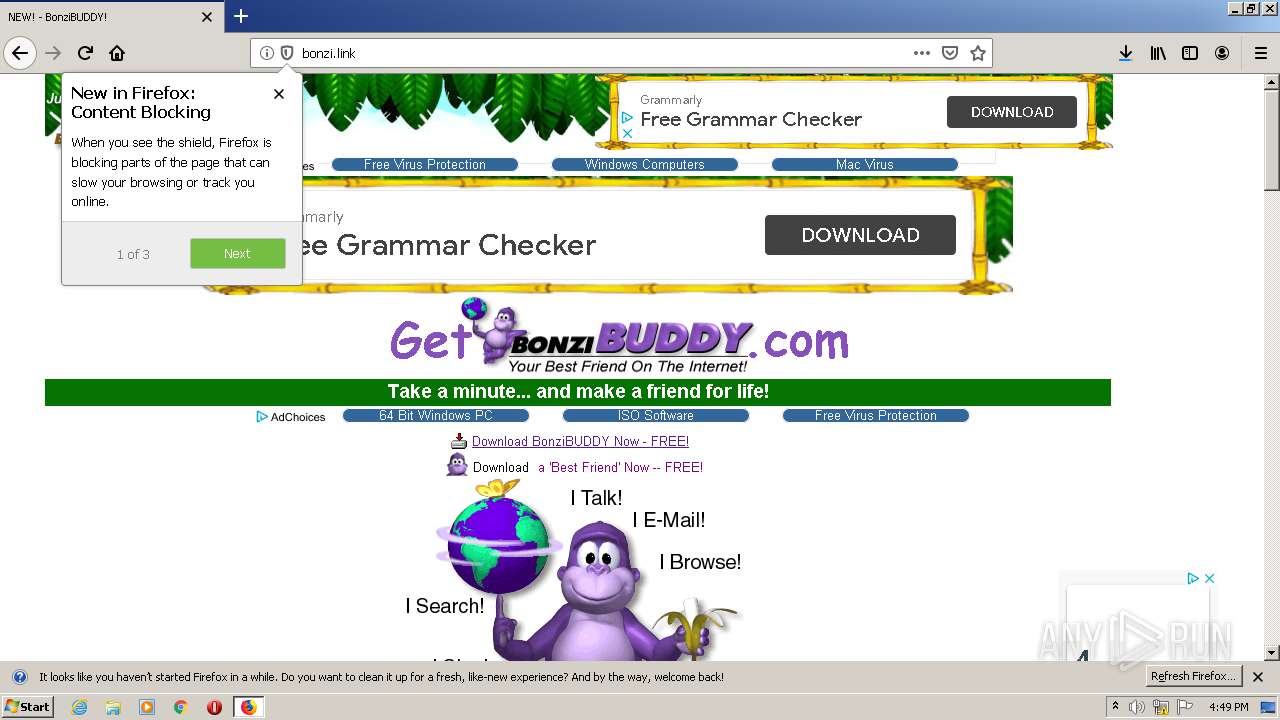
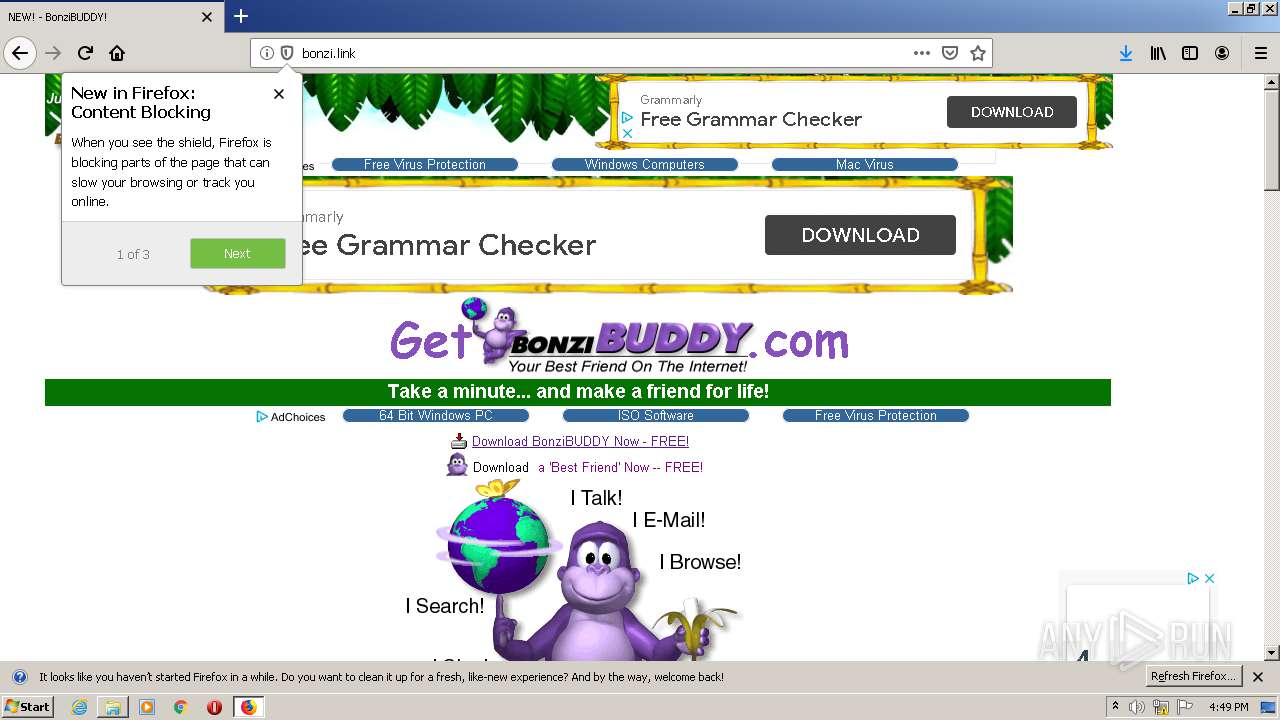
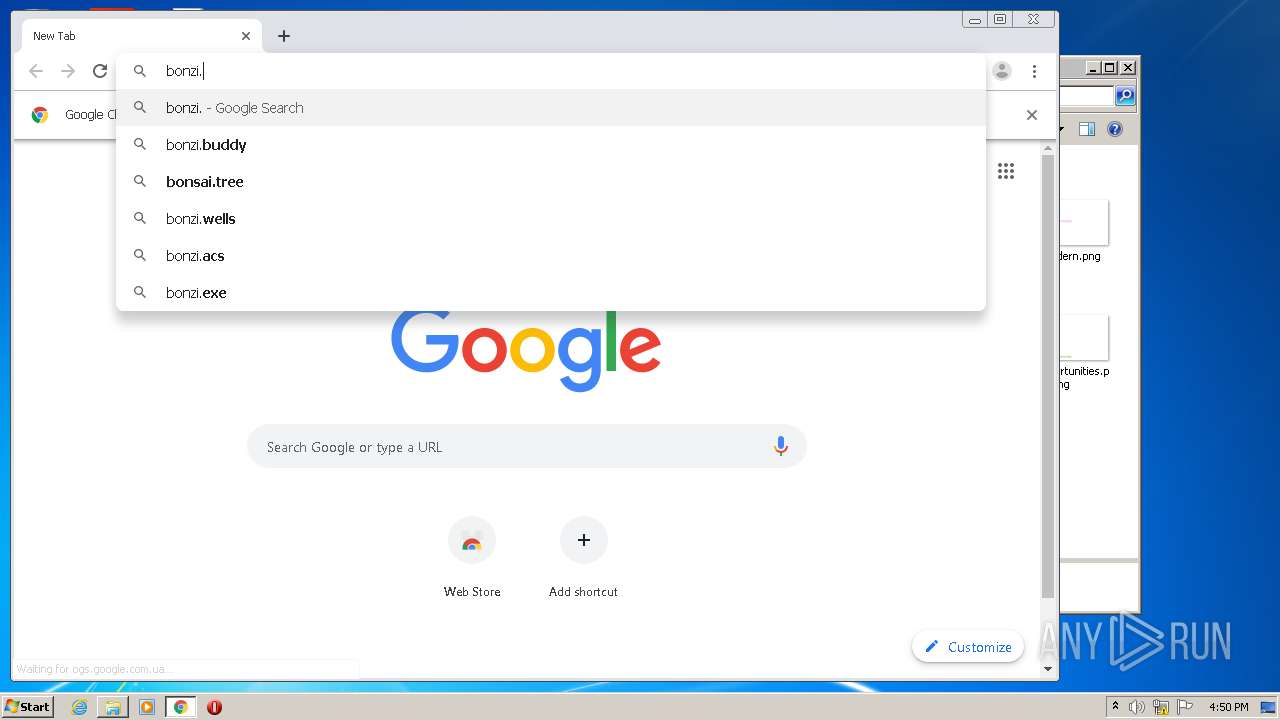
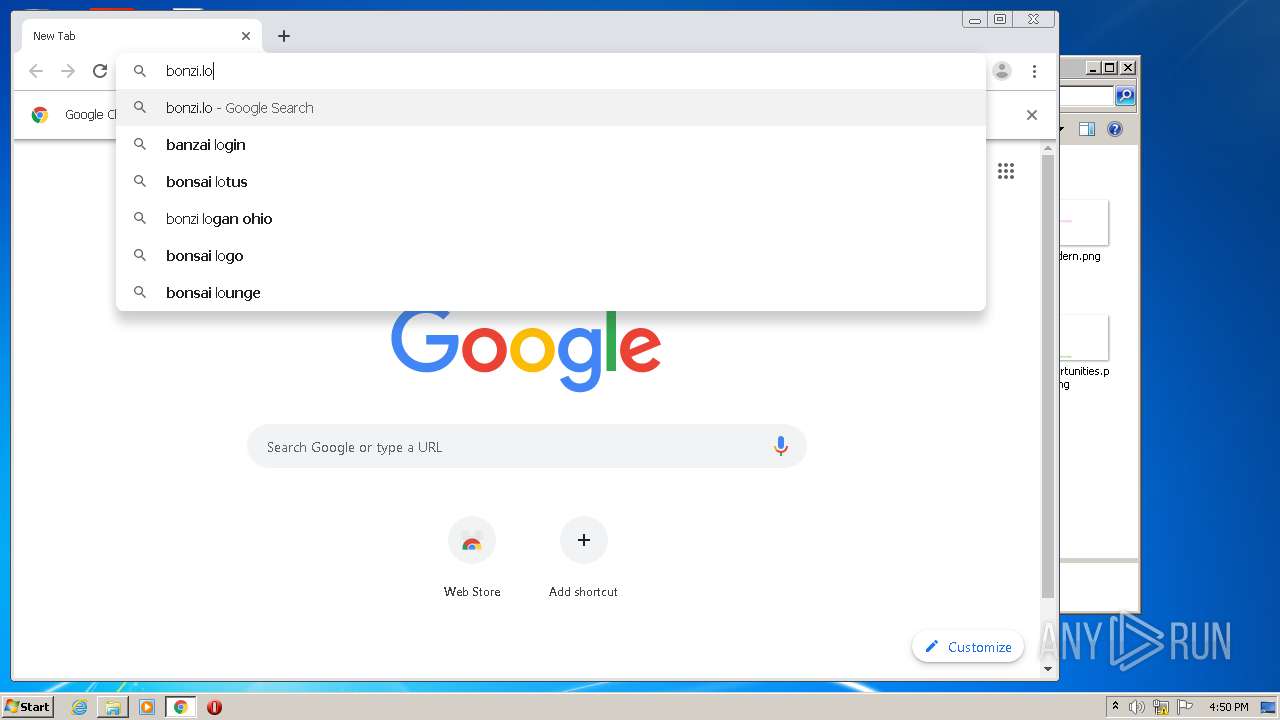
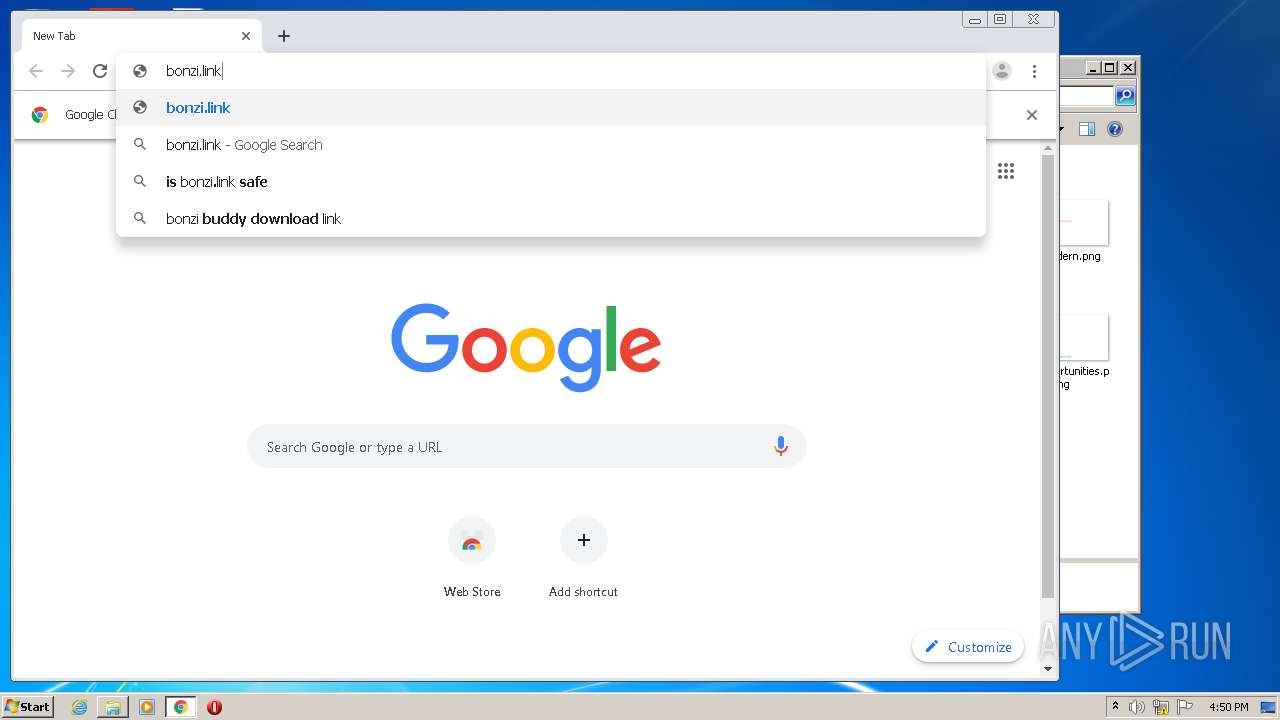
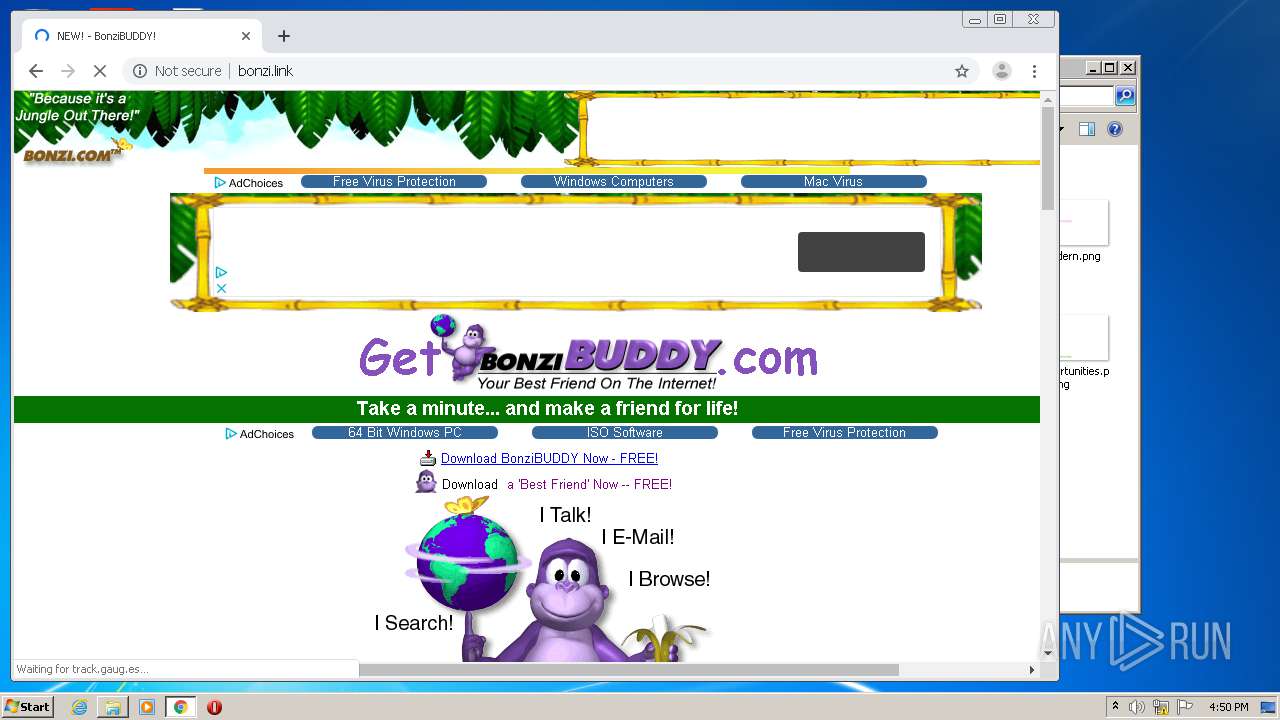
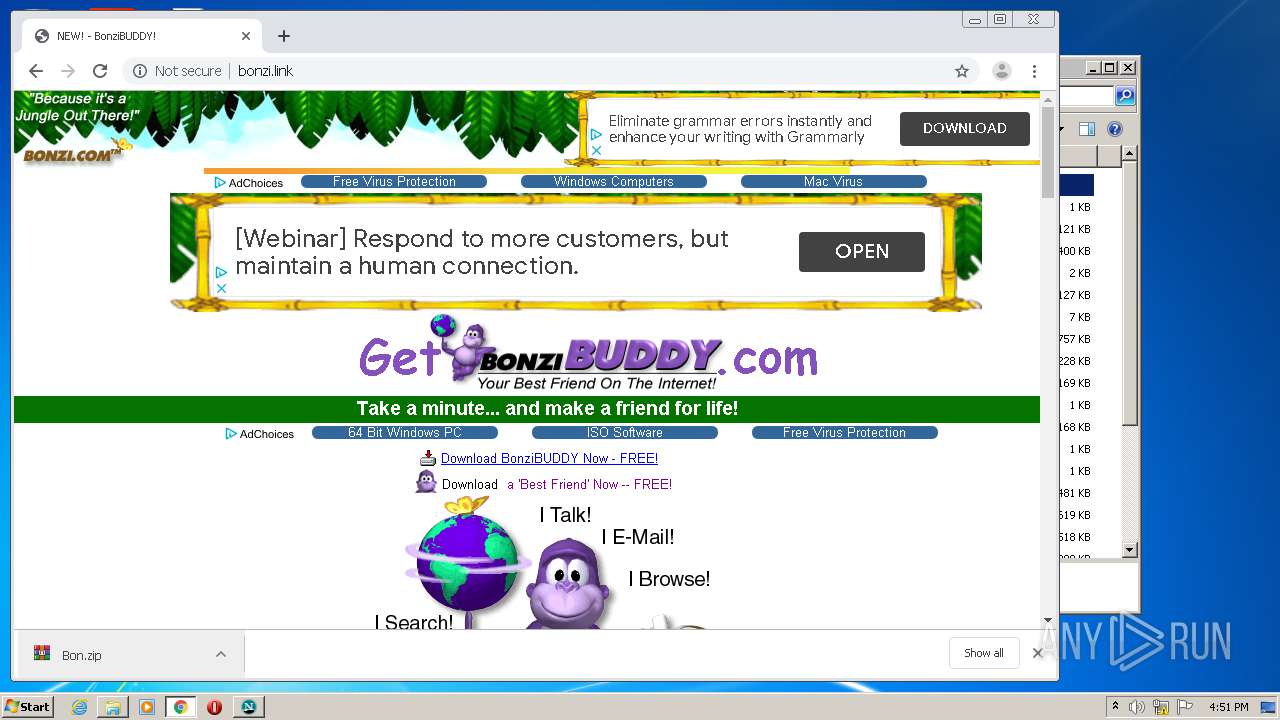
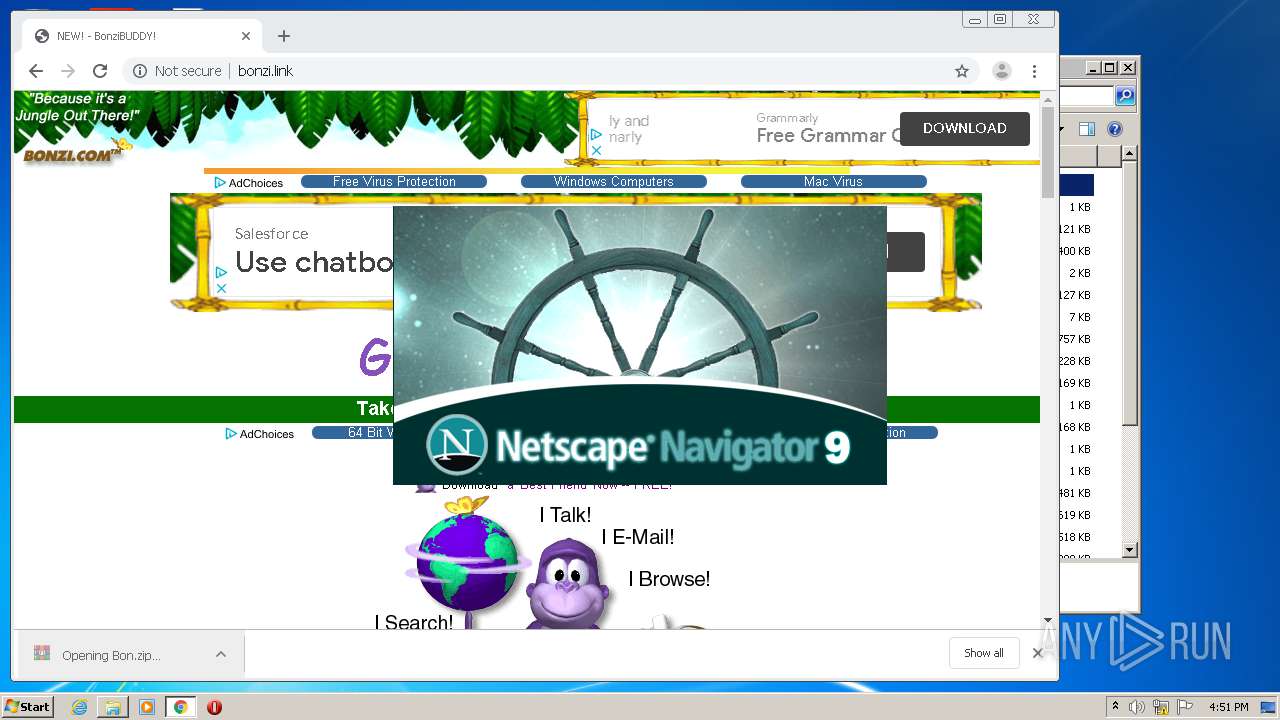
2864 | firefox.exe | GET | 200 | 145.239.5.59:80 | http://bonzi.link/ | GB | html | 4.04 Kb | suspicious |
2864 | firefox.exe | GET | 200 | 2.16.107.58:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2864 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
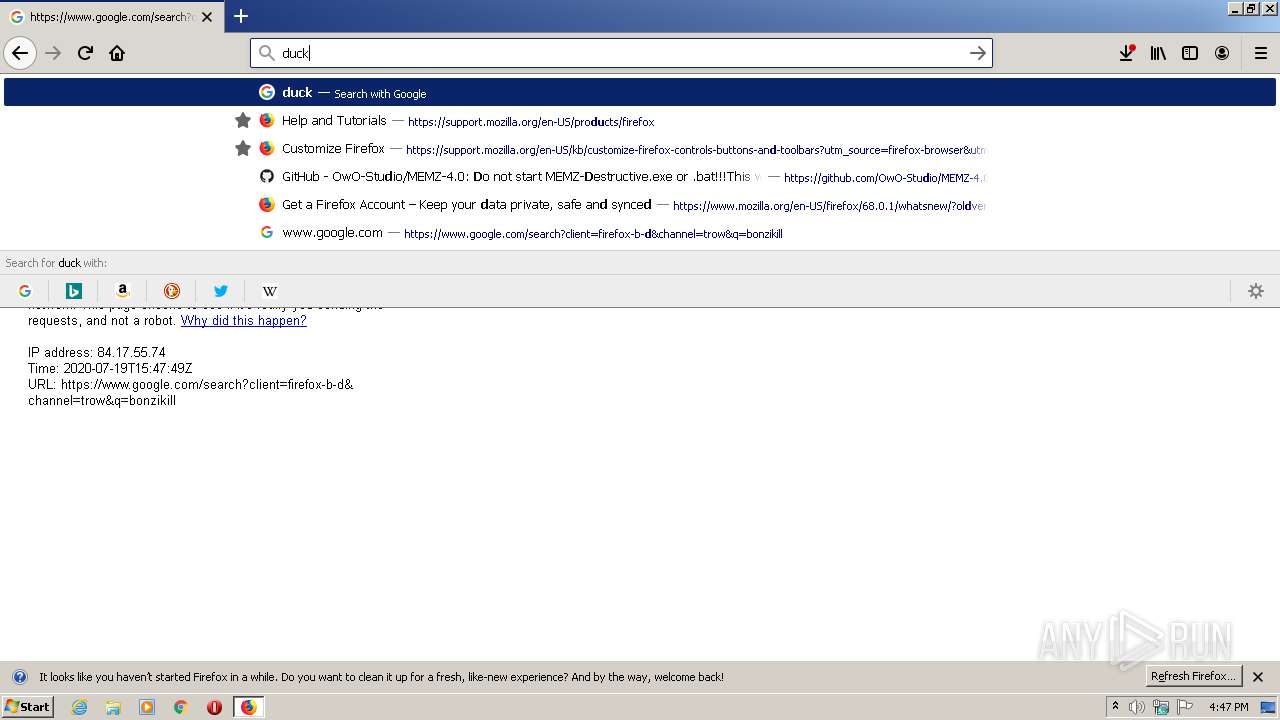
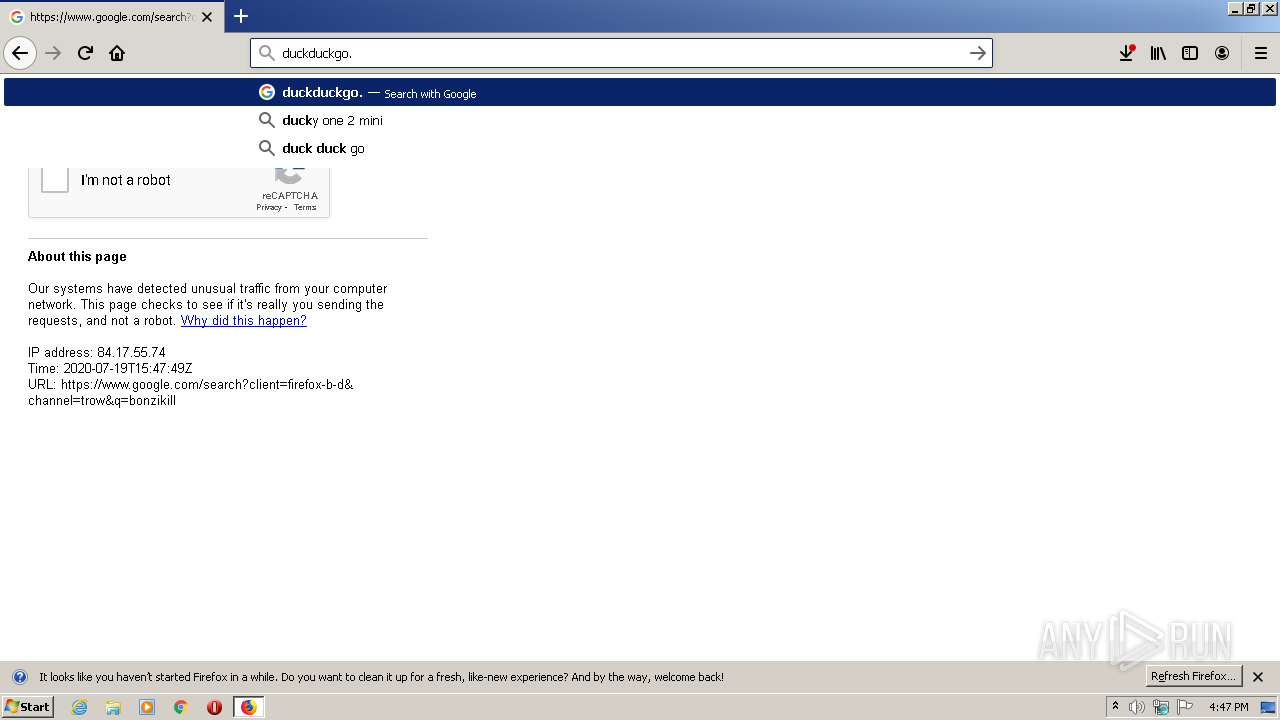
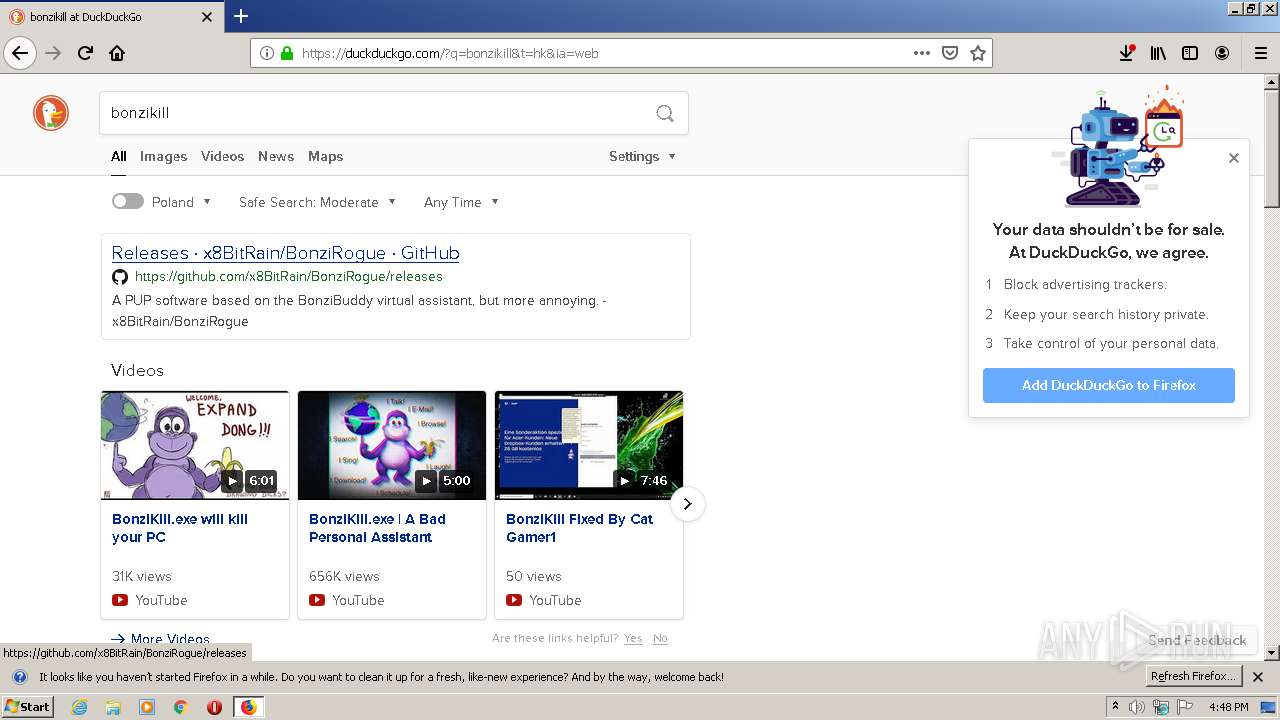
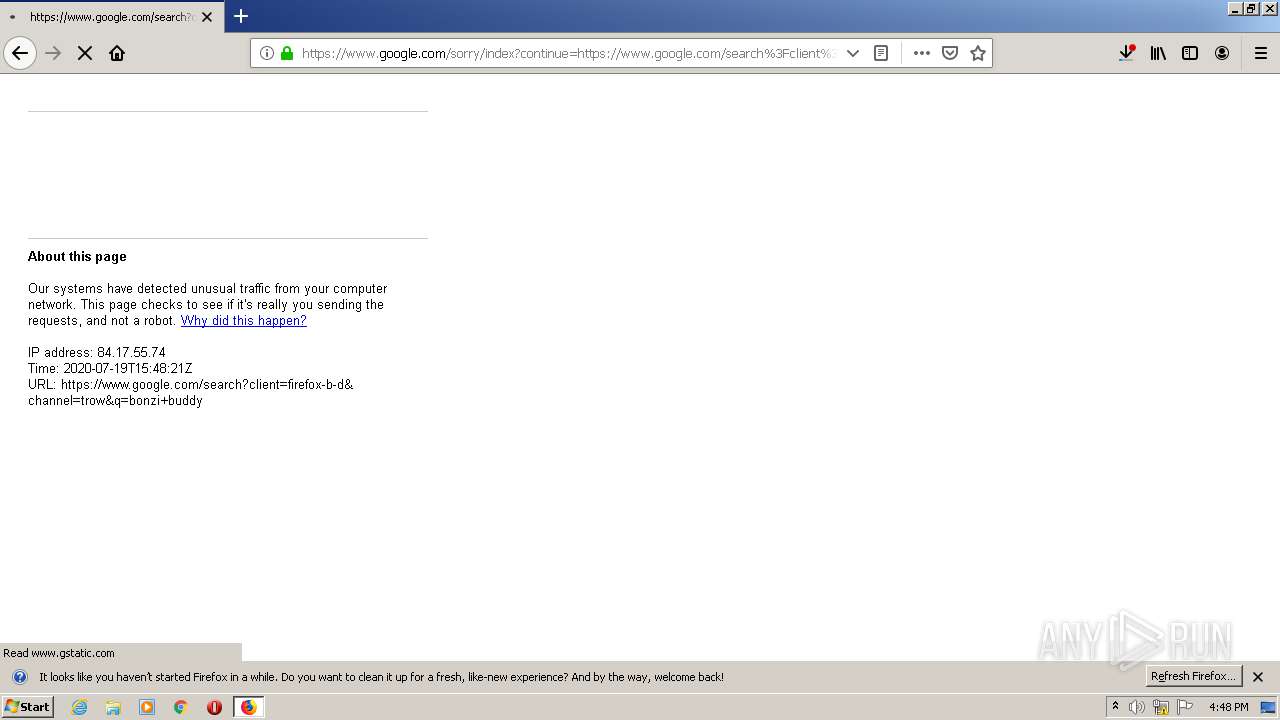
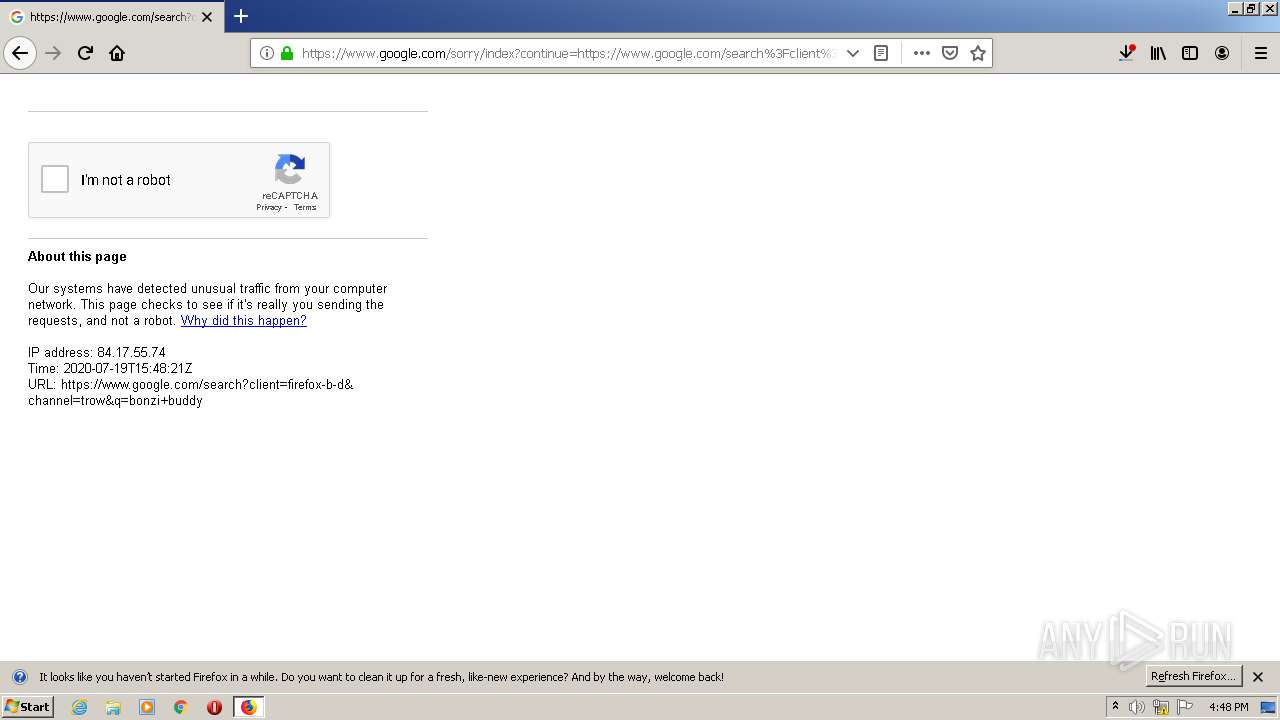
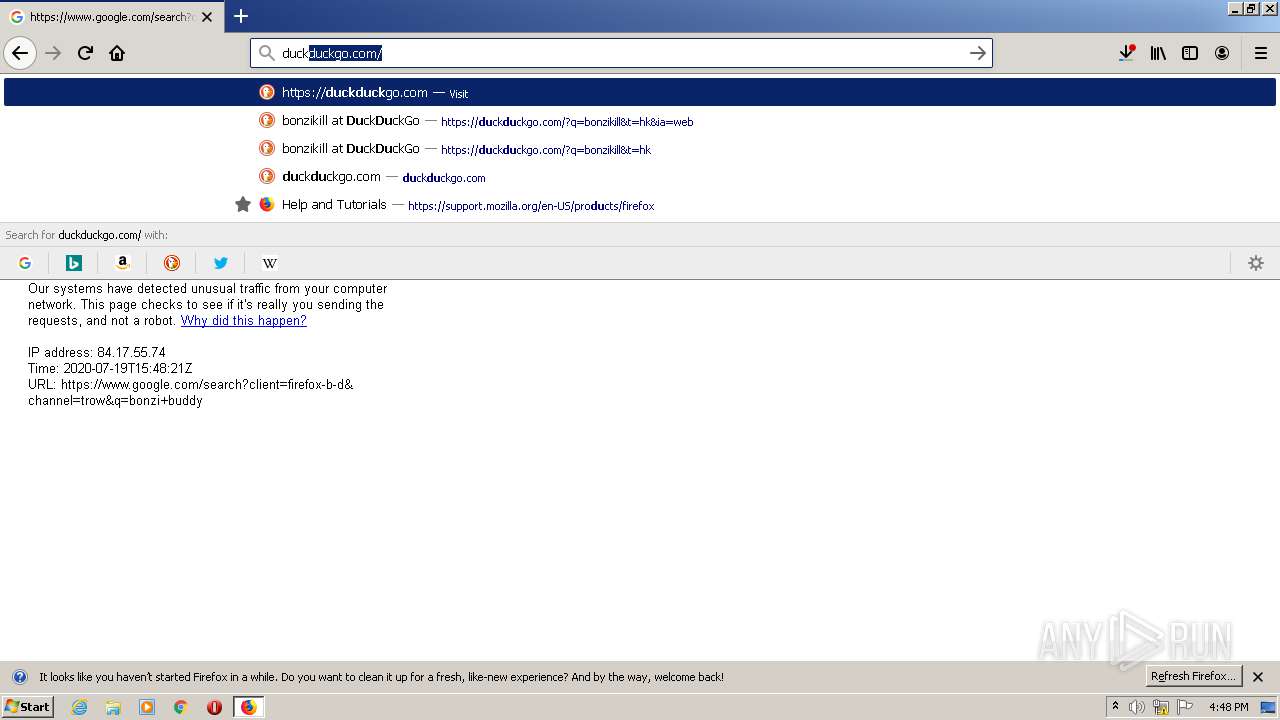
2864 | firefox.exe | GET | 301 | 40.114.177.156:80 | http://duckduckgo.com/ | NL | html | 162 b | whitelisted |
2864 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
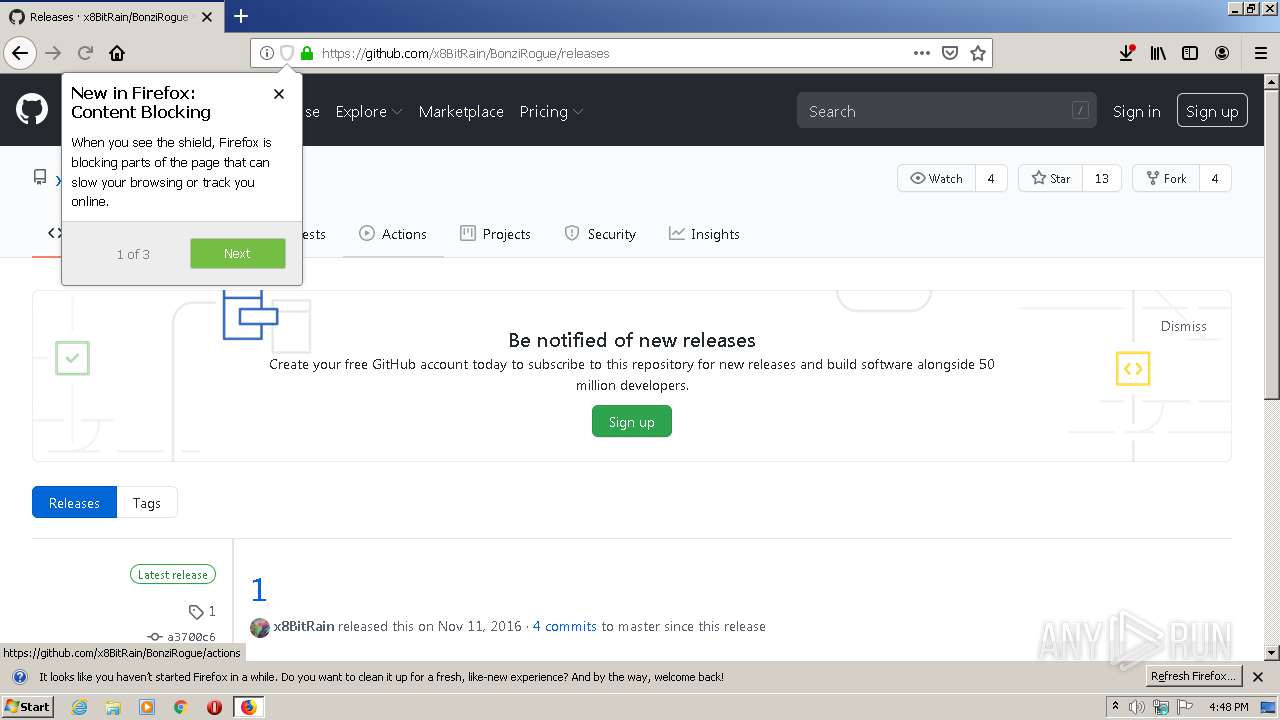
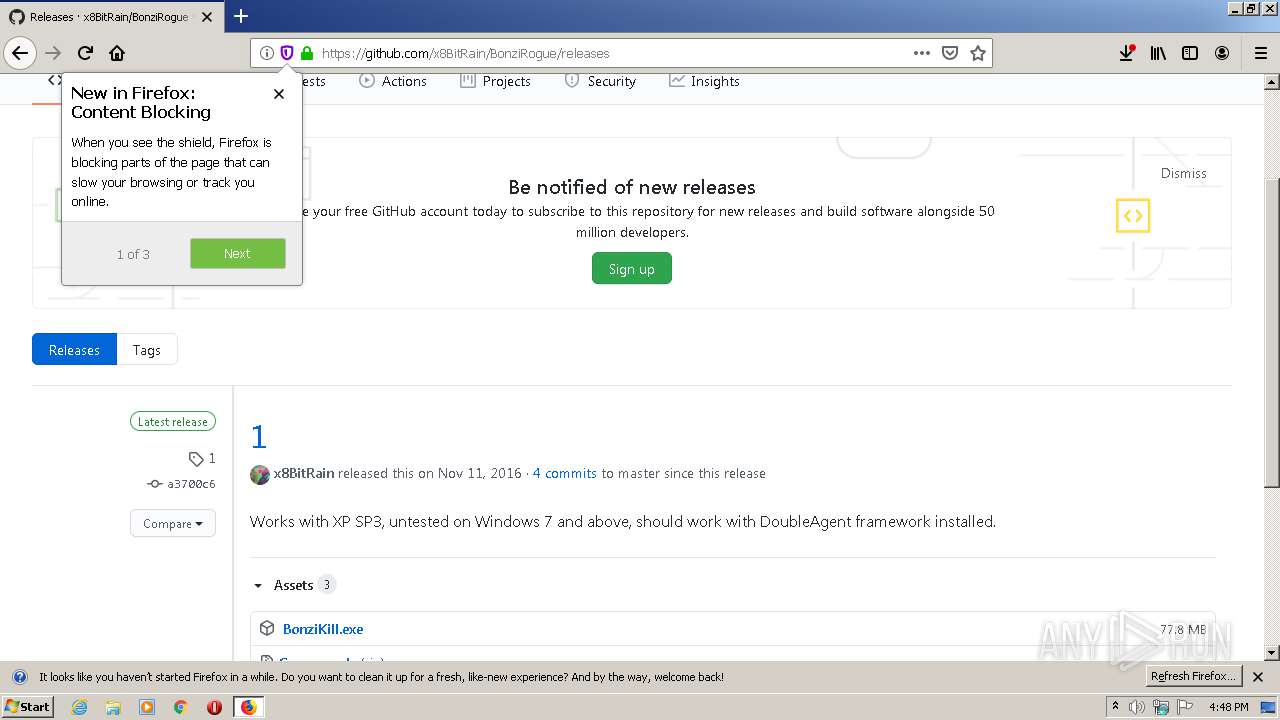
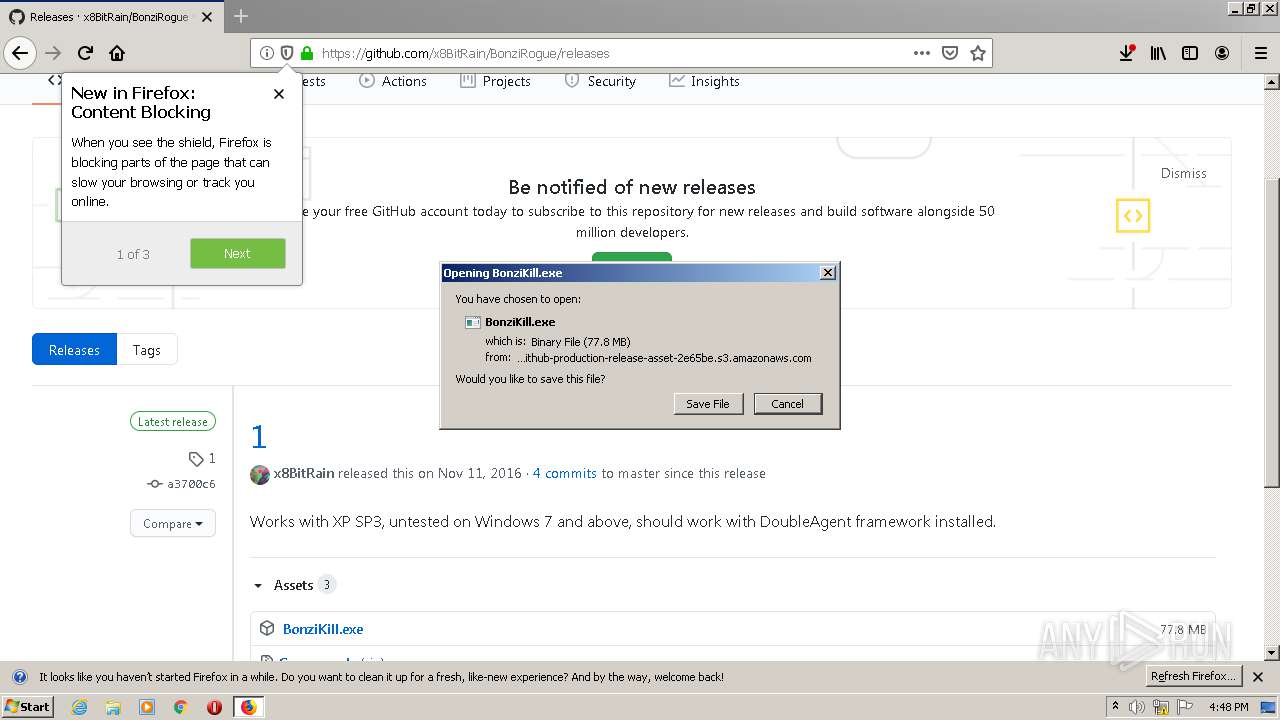
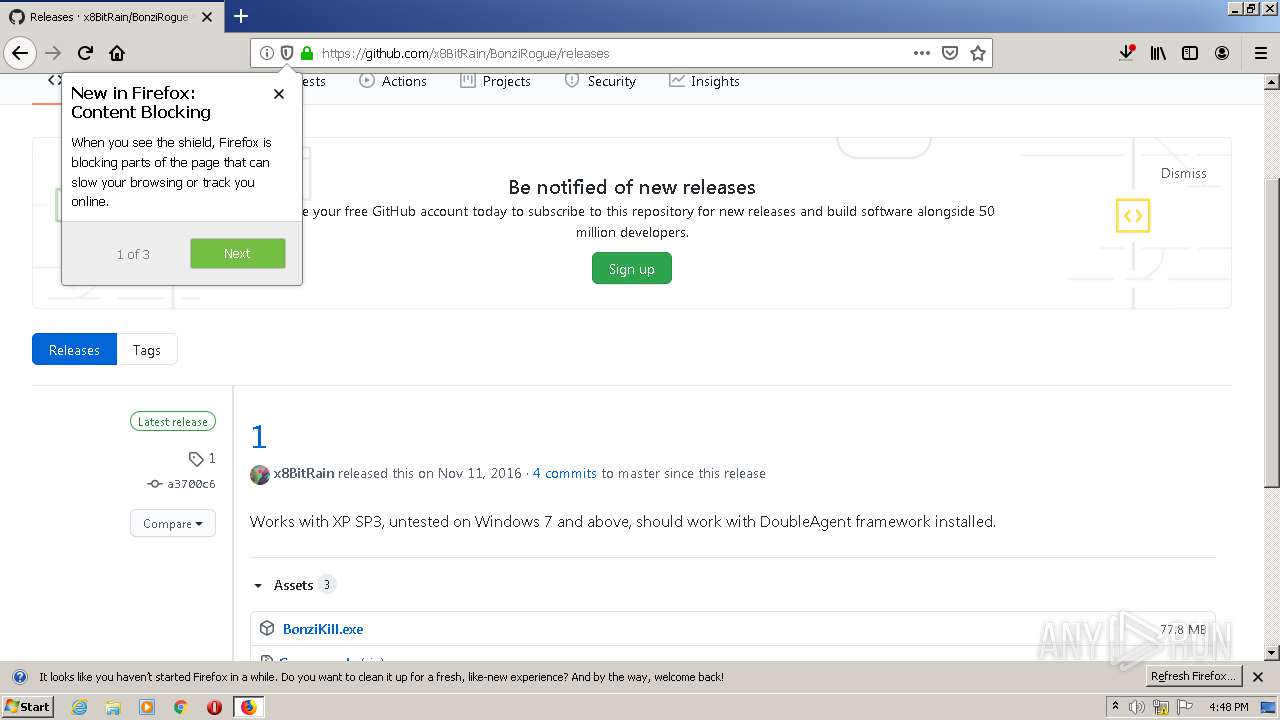
2864 | firefox.exe | 140.82.118.4:443 | github.com | — | US | malicious |
2864 | firefox.exe | 2.16.107.58:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
2864 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2864 | firefox.exe | 52.222.149.57:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2864 | firefox.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2864 | firefox.exe | 52.26.190.215:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2864 | firefox.exe | 52.222.149.54:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | whitelisted |
2864 | firefox.exe | 52.206.227.240:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
2864 | firefox.exe | 151.101.0.133:443 | camo.githubusercontent.com | Fastly | US | malicious |
2864 | firefox.exe | 172.217.21.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
github.com |
| malicious |
a1089.dscd.akamai.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
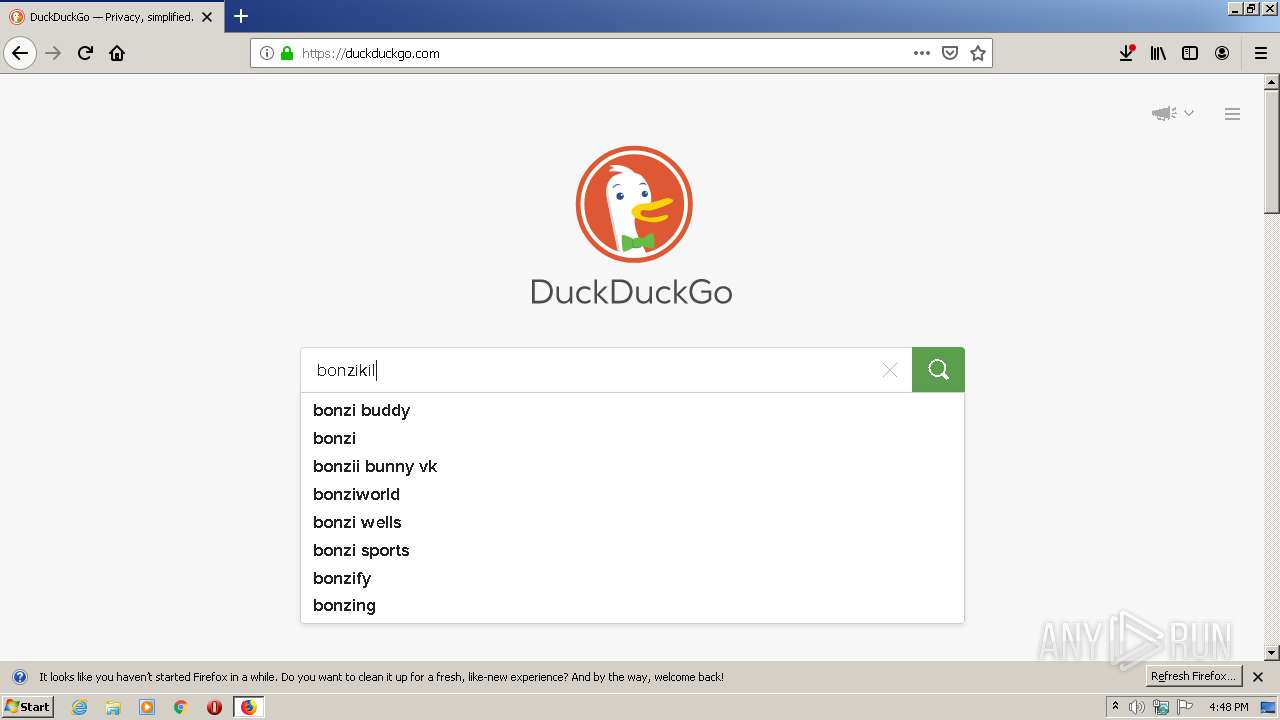
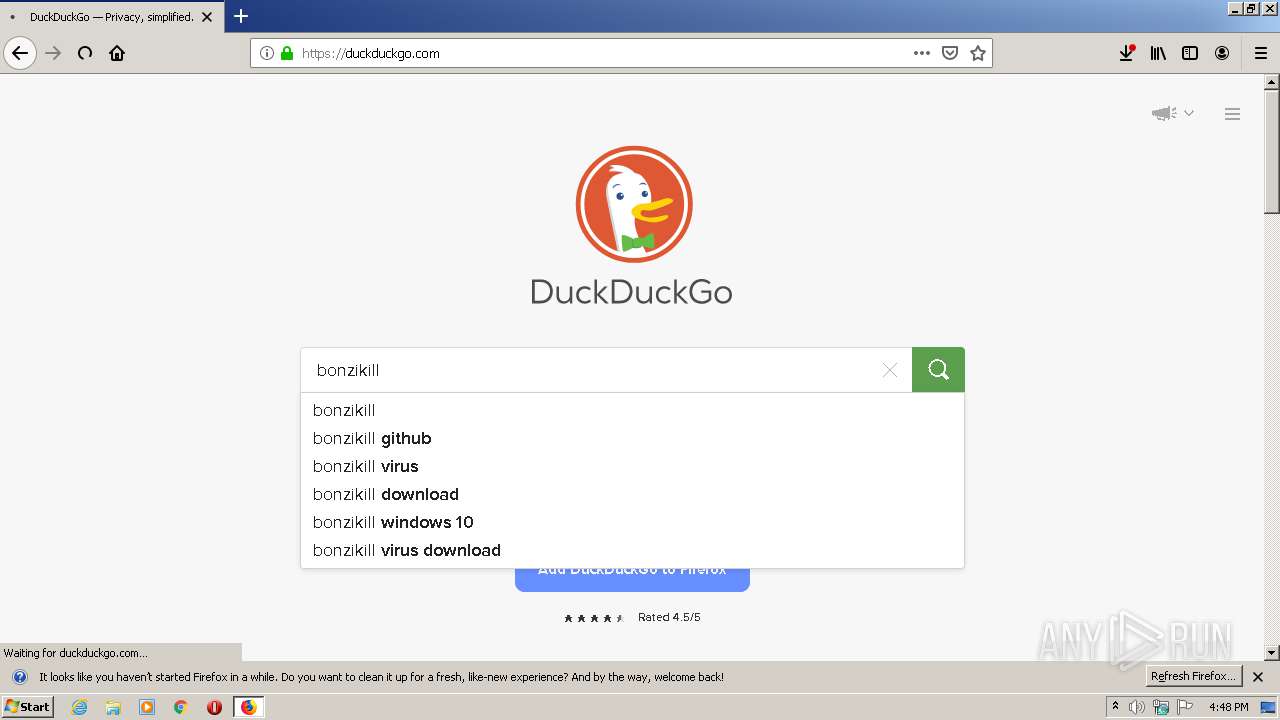
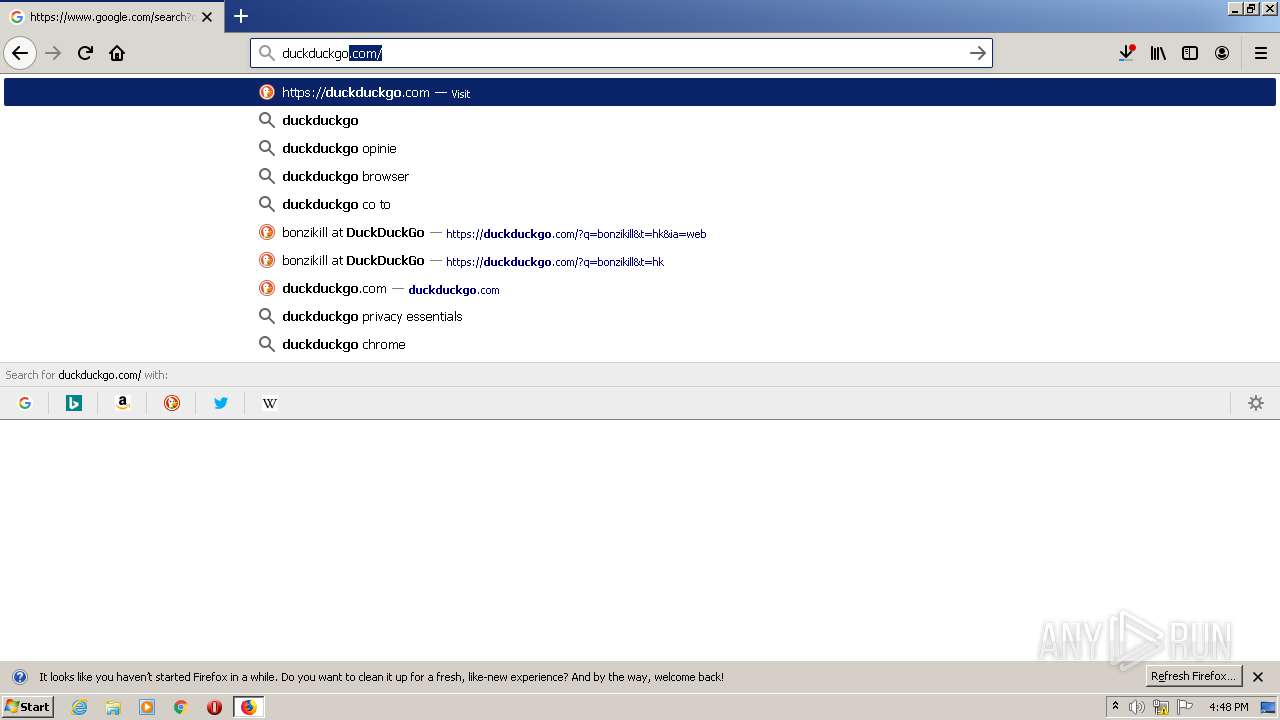
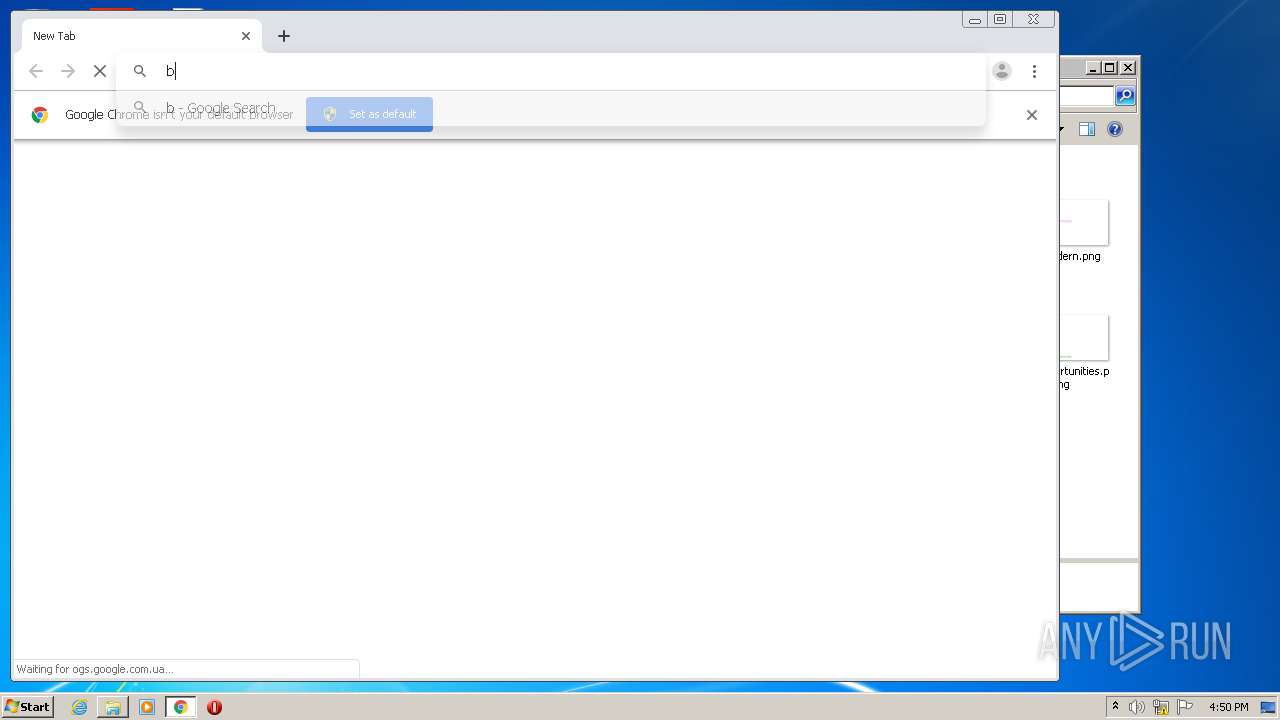
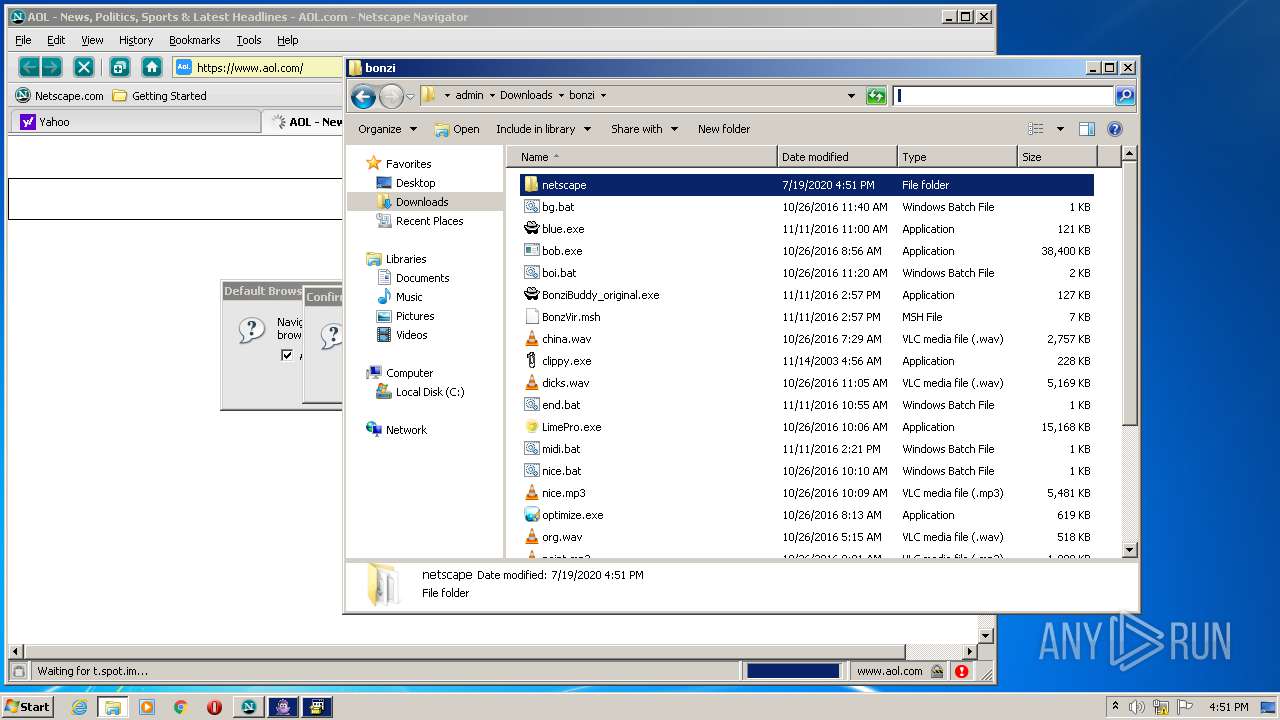
1264 | navigator.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake FireFox Version 2. |
1264 | navigator.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake FireFox Version 2. |
1264 | navigator.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake FireFox Version 2. |