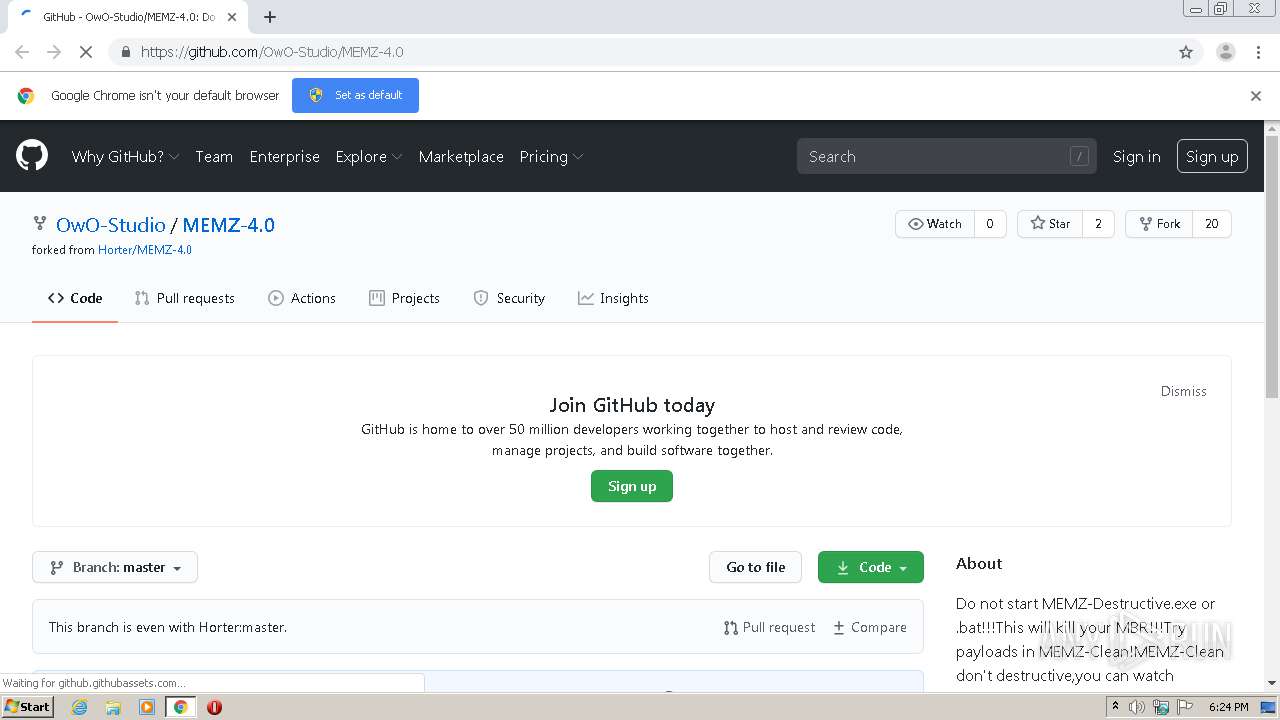
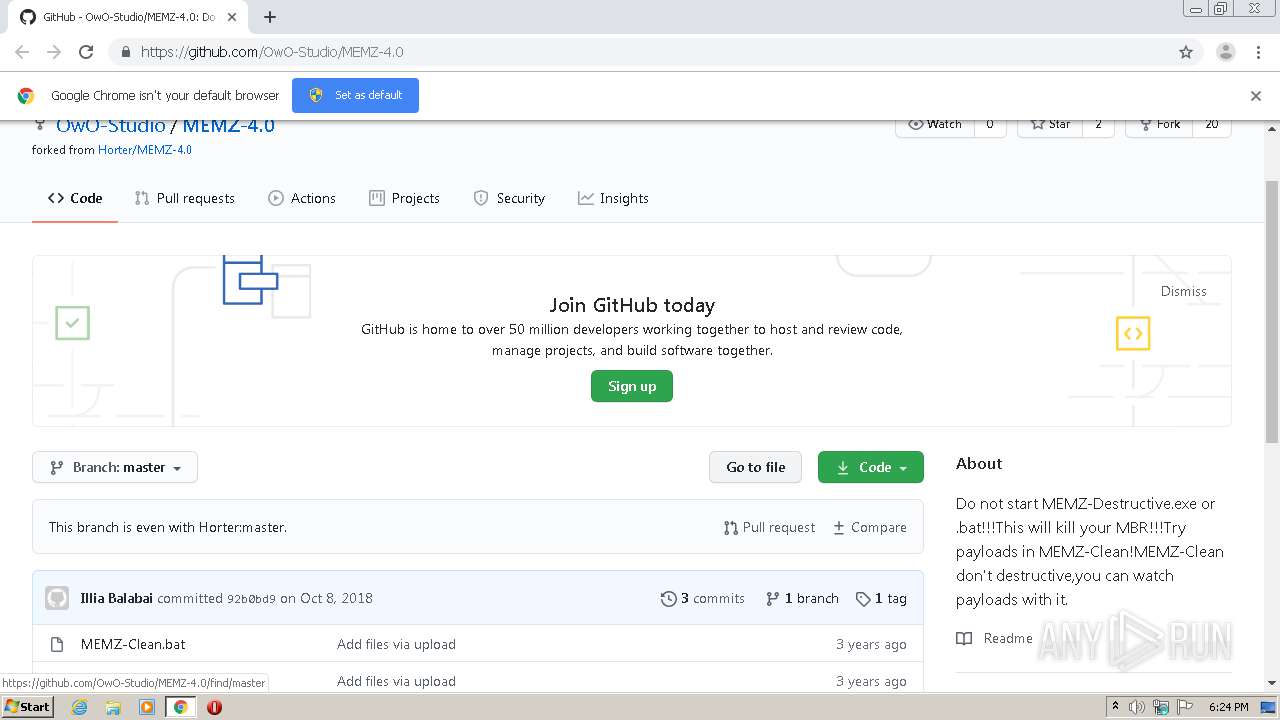
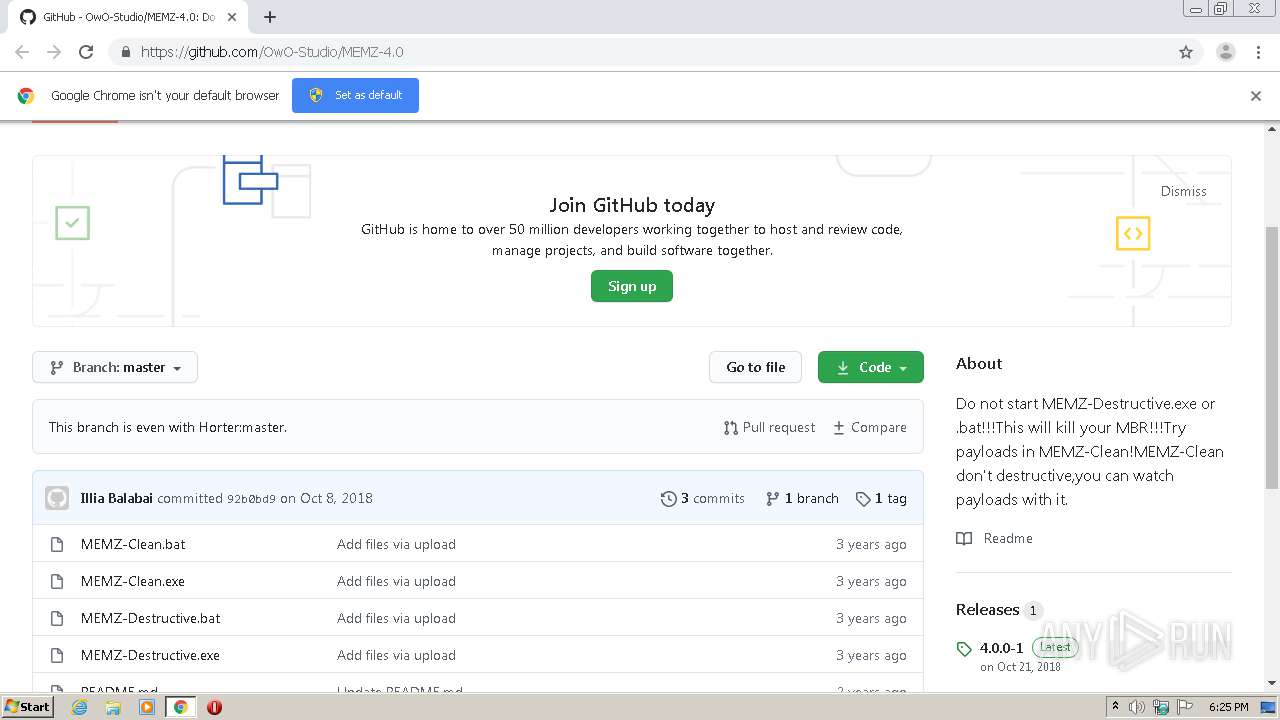
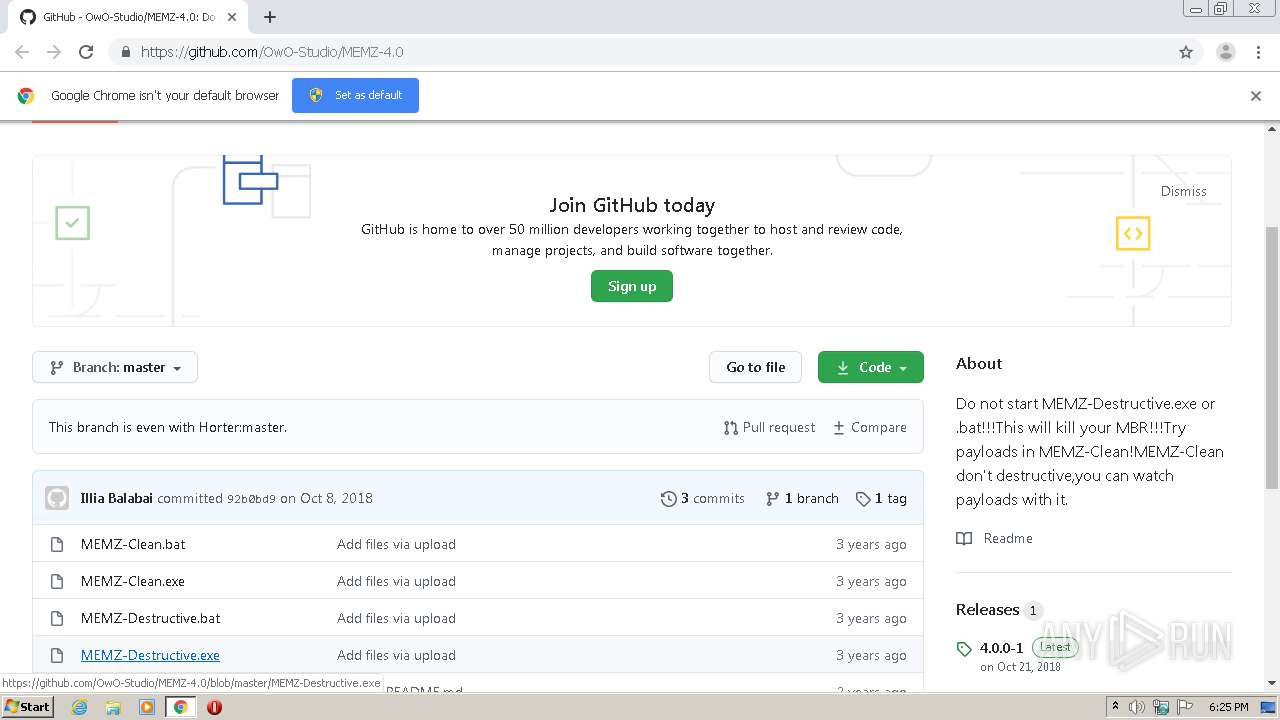
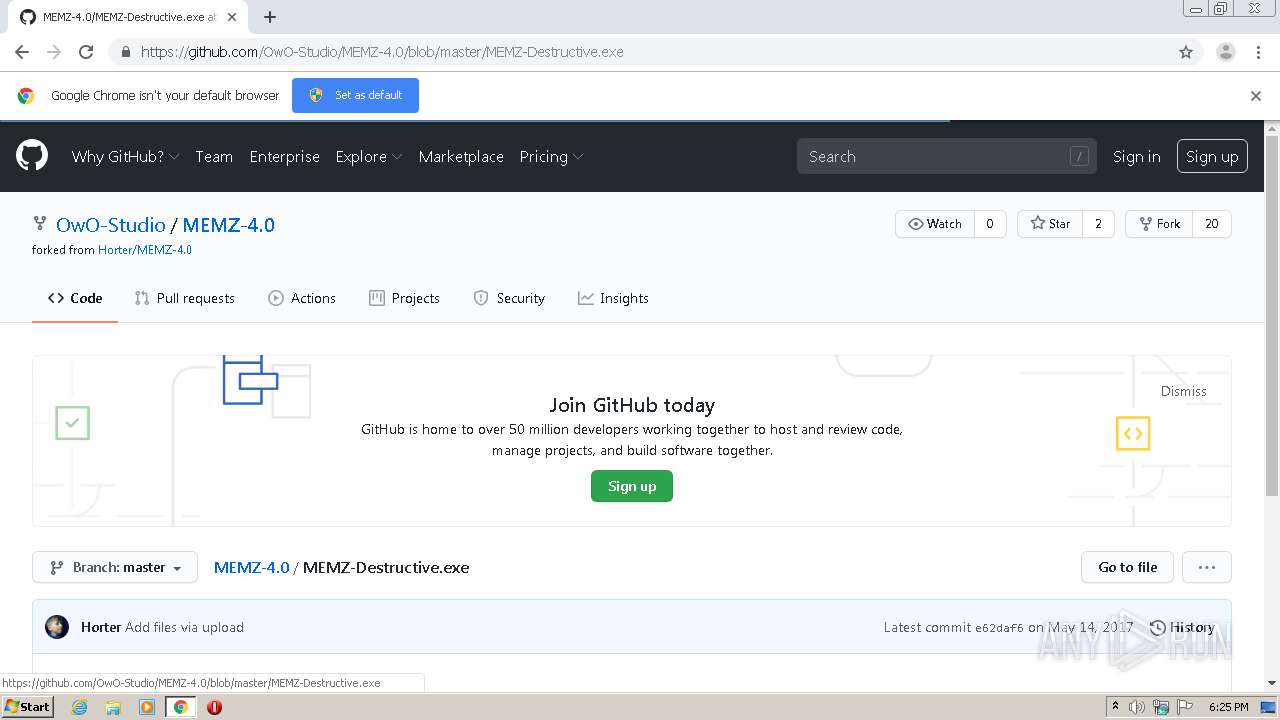
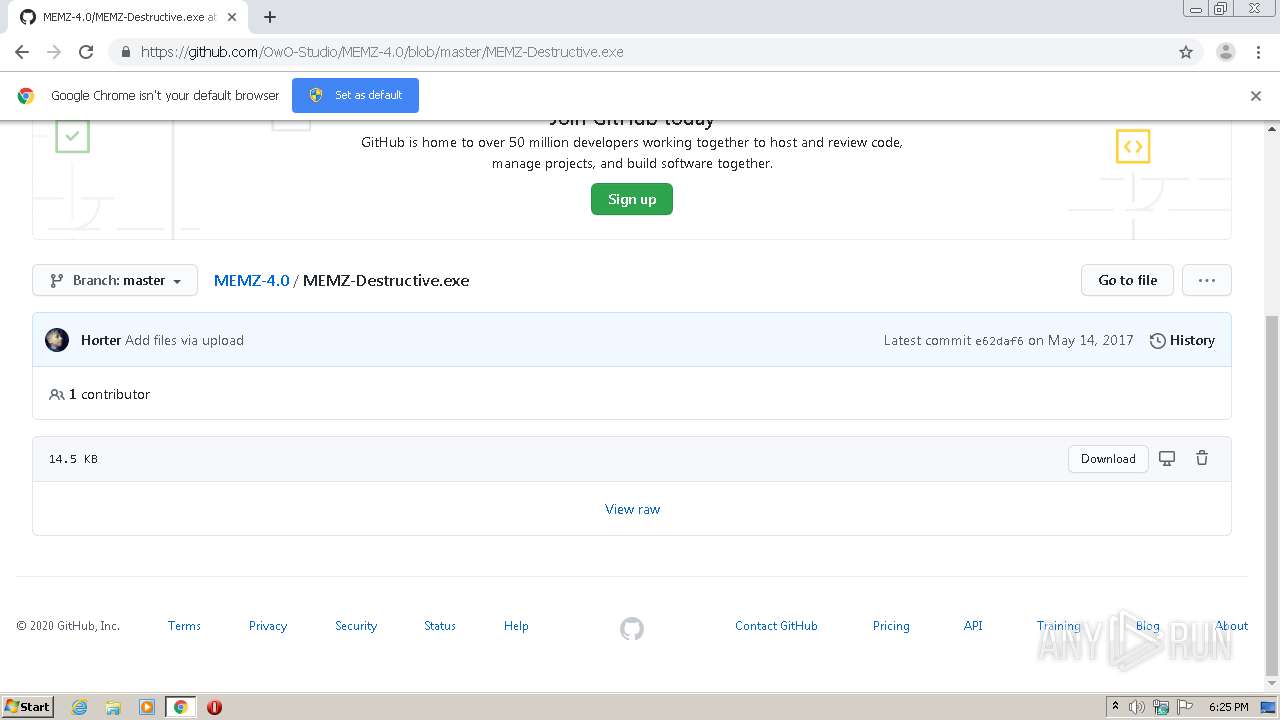
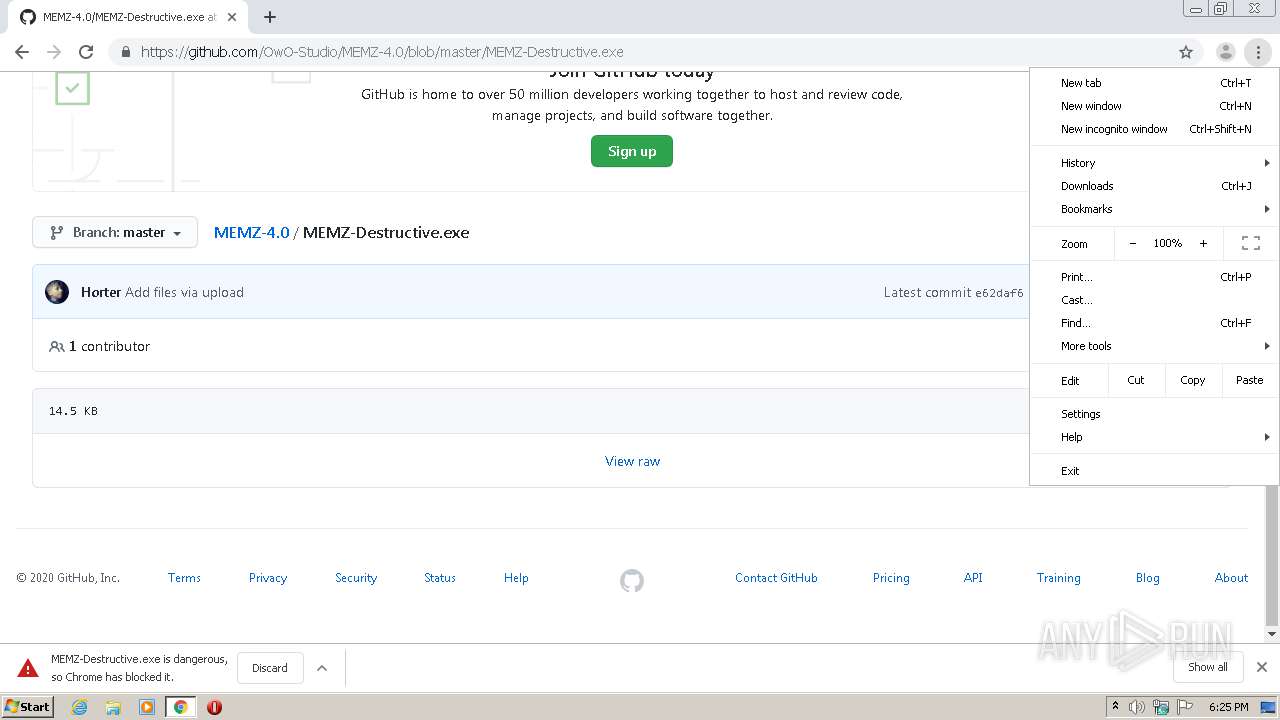
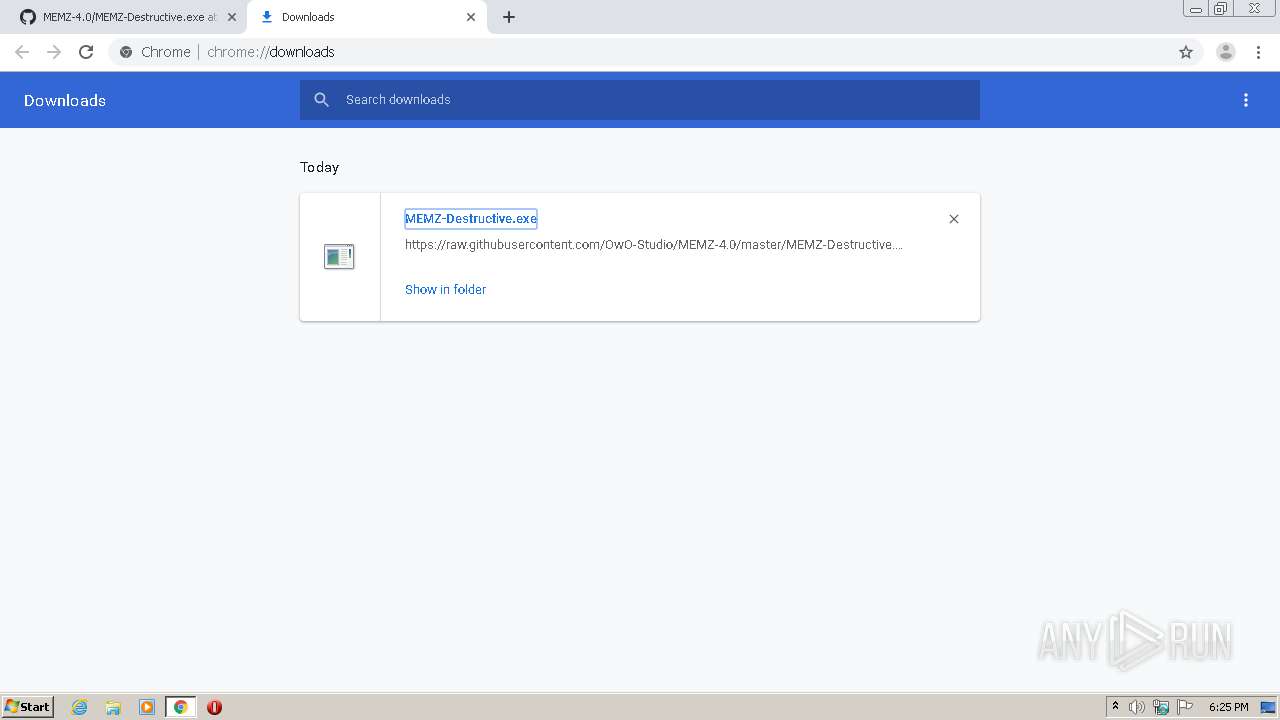
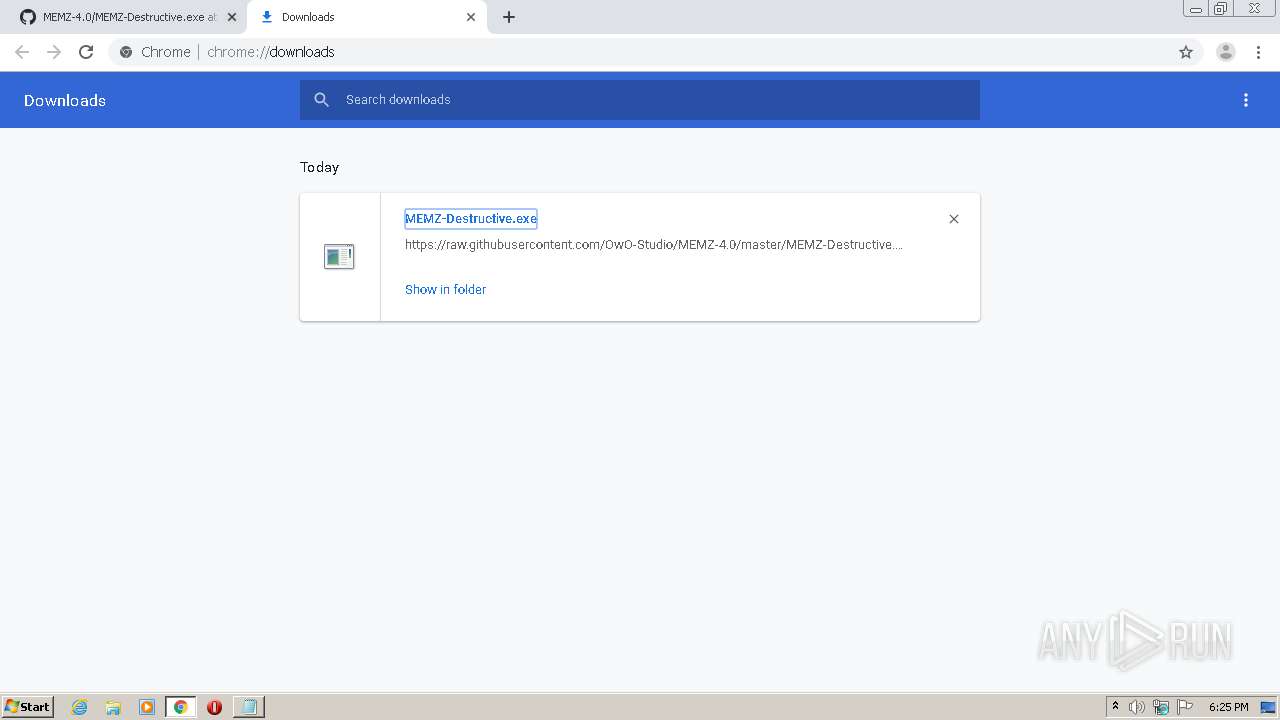
| URL: | https://github.com/OwO-Studio/MEMZ-4.0 |
| Full analysis: | https://app.any.run/tasks/2be911ff-0f2e-4545-8cf3-397a8818517c |
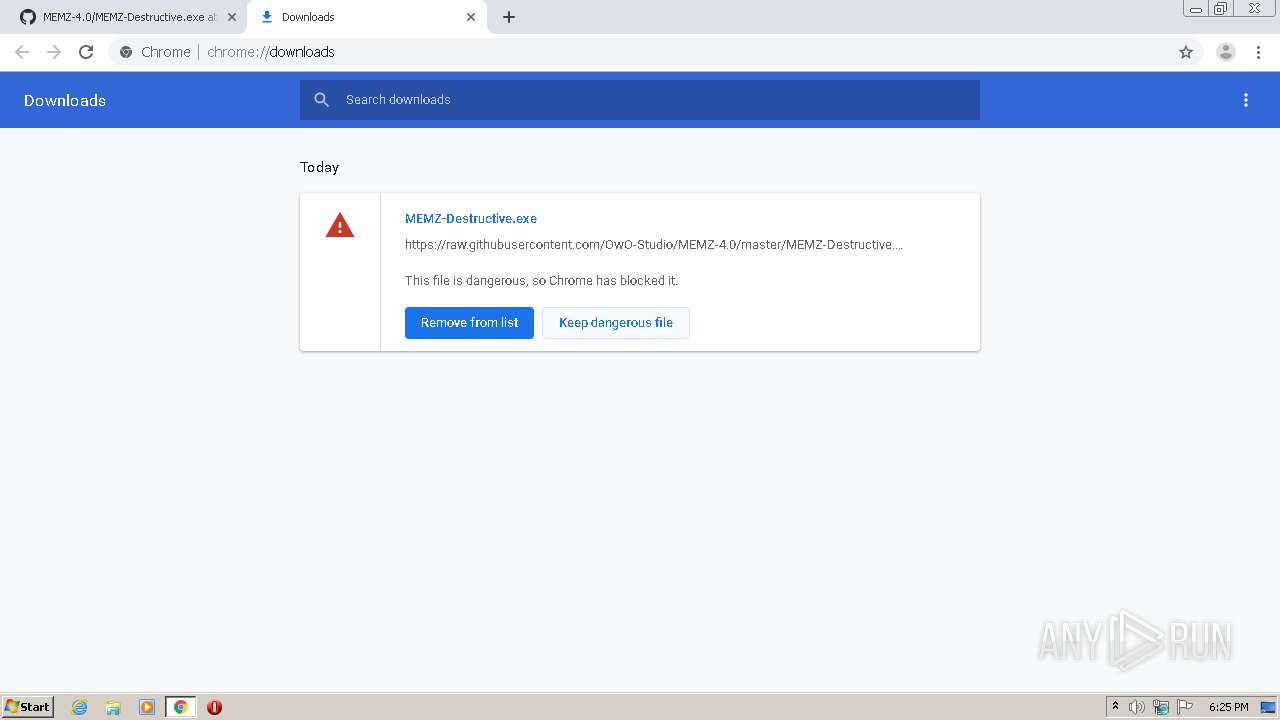
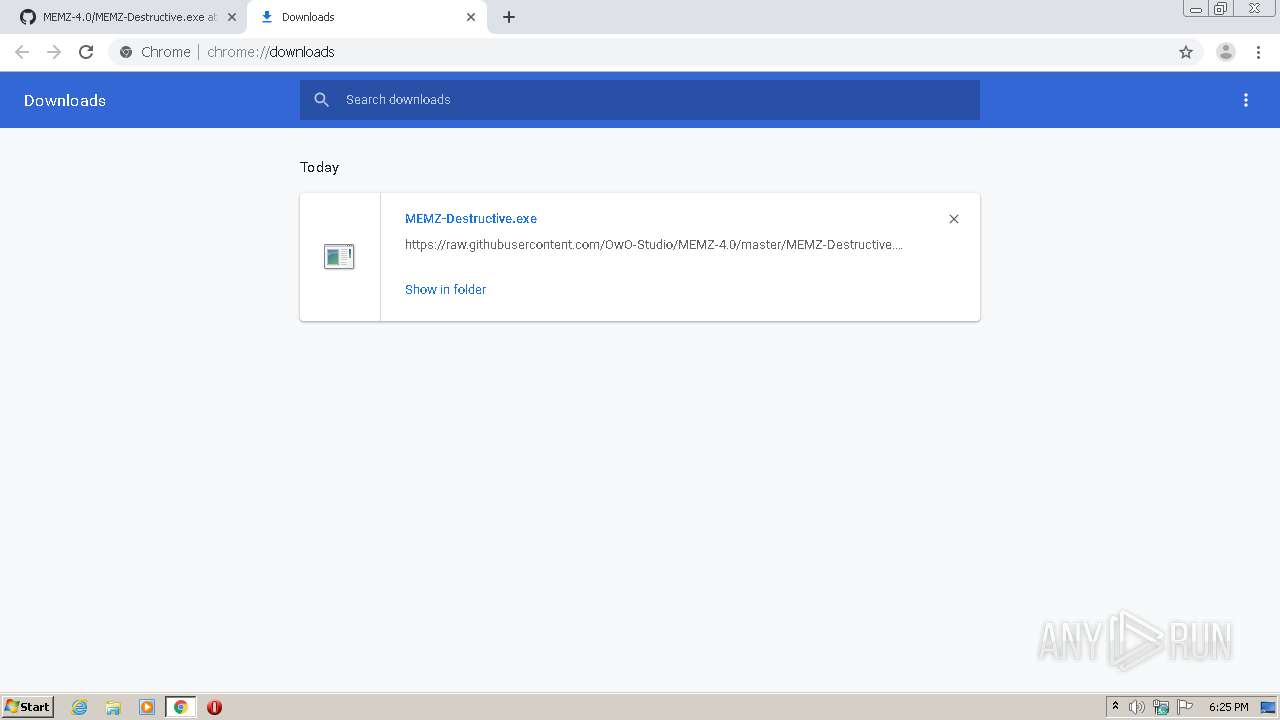
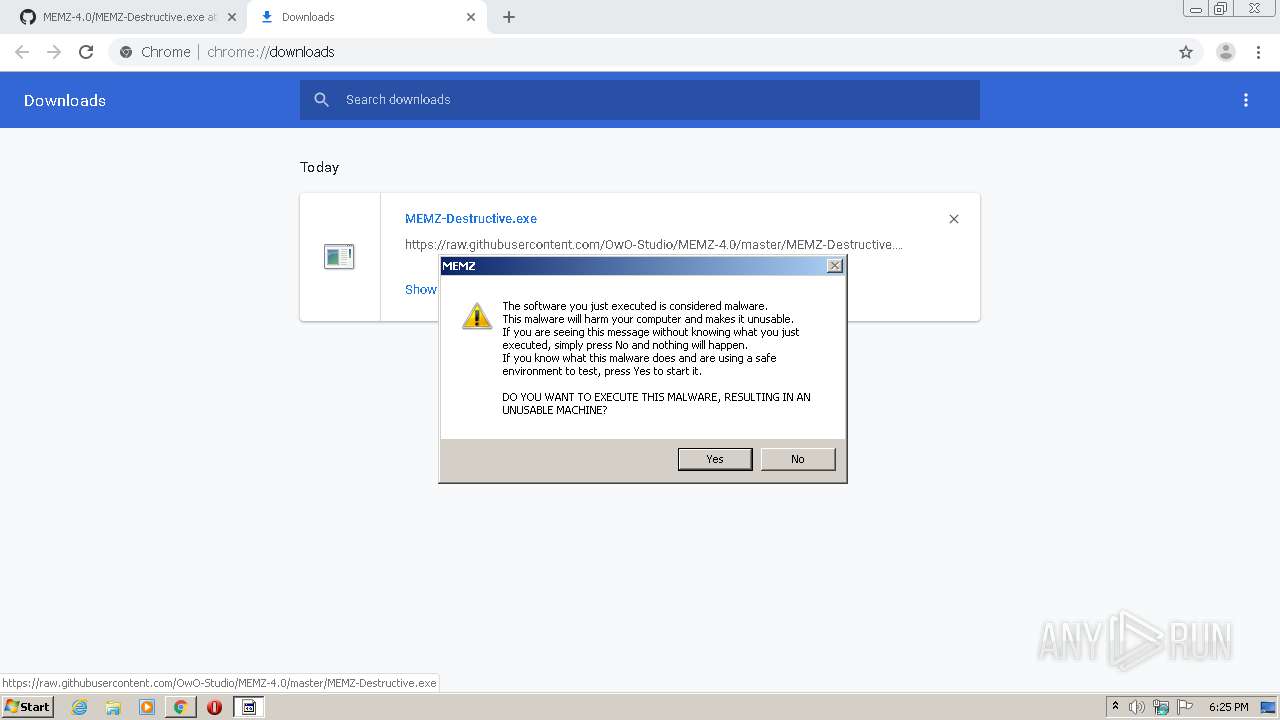
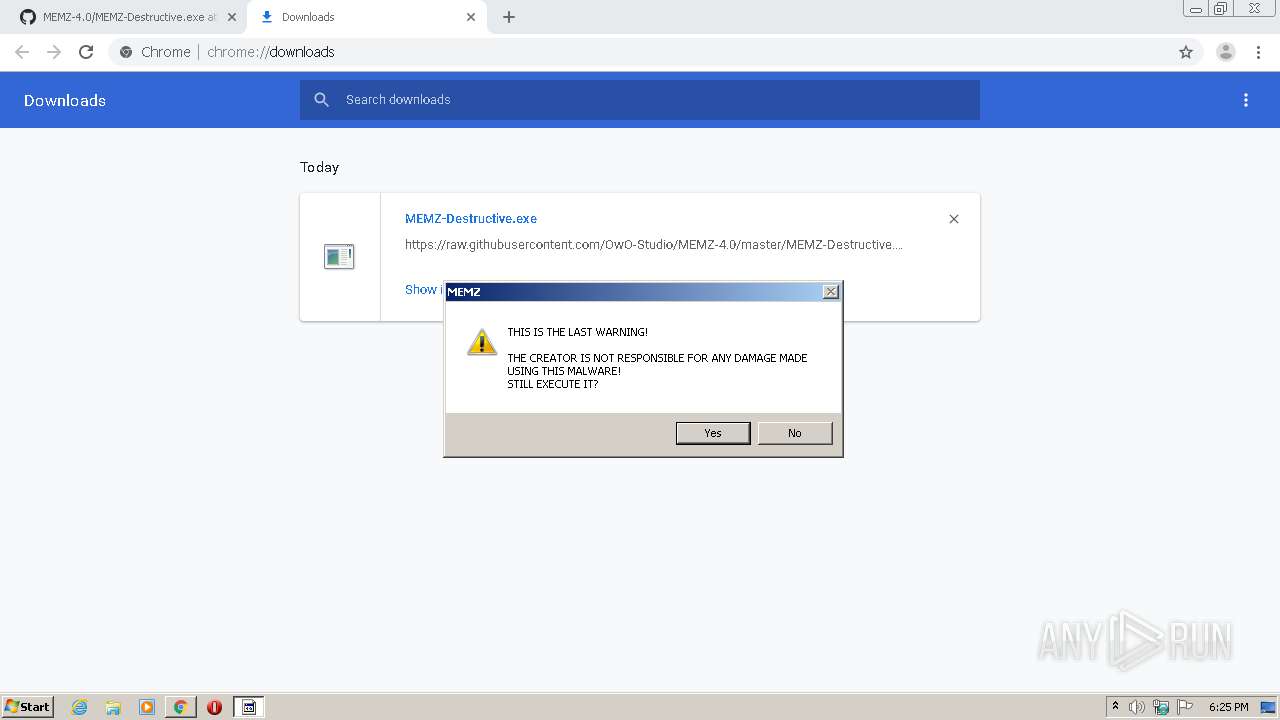
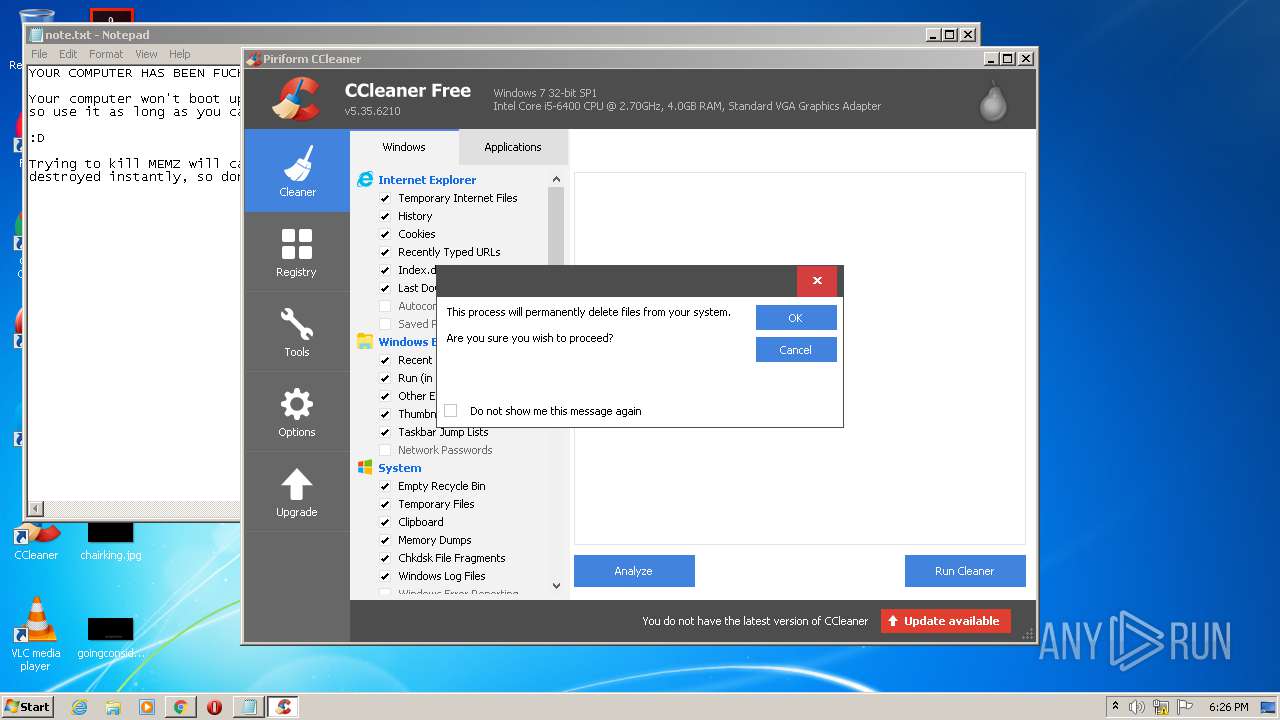
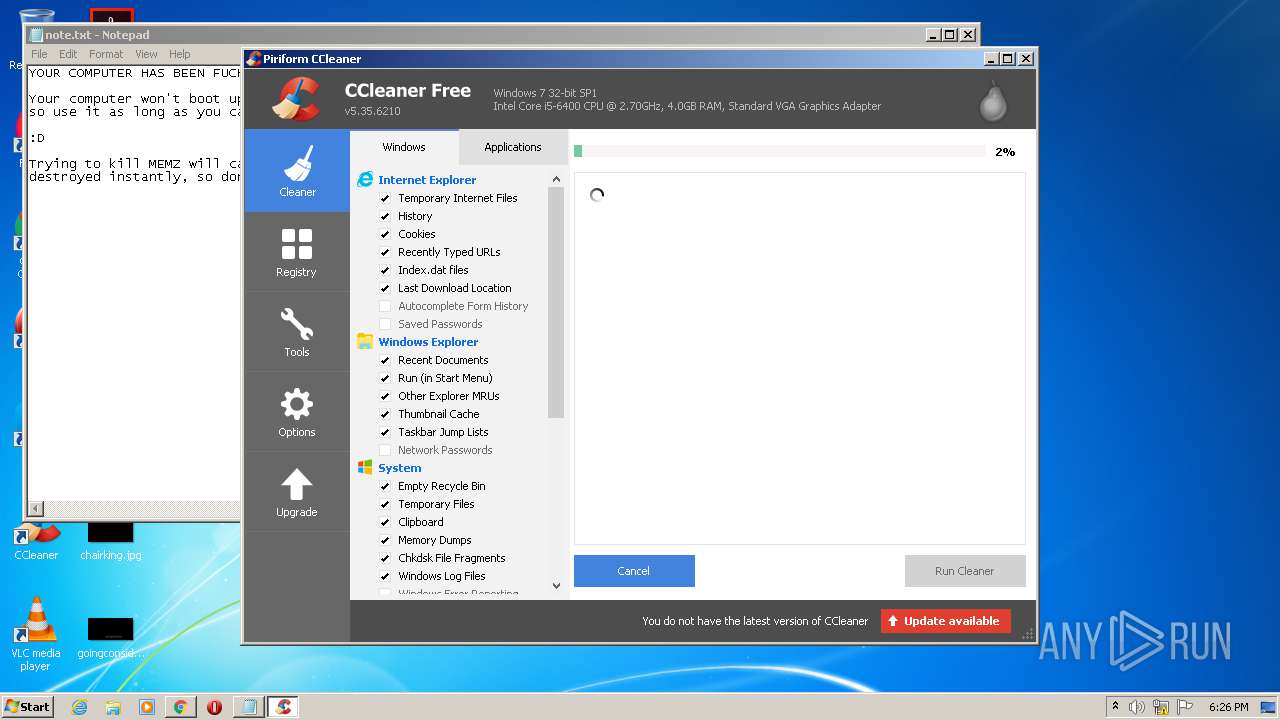
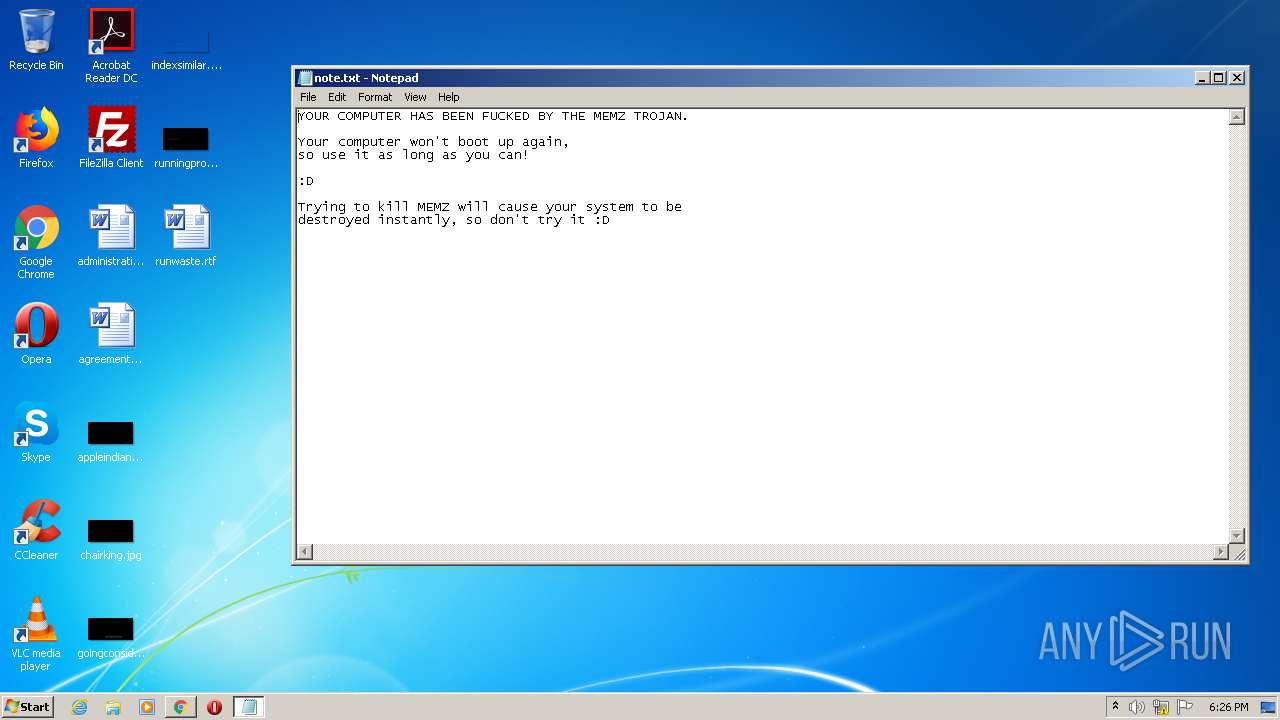
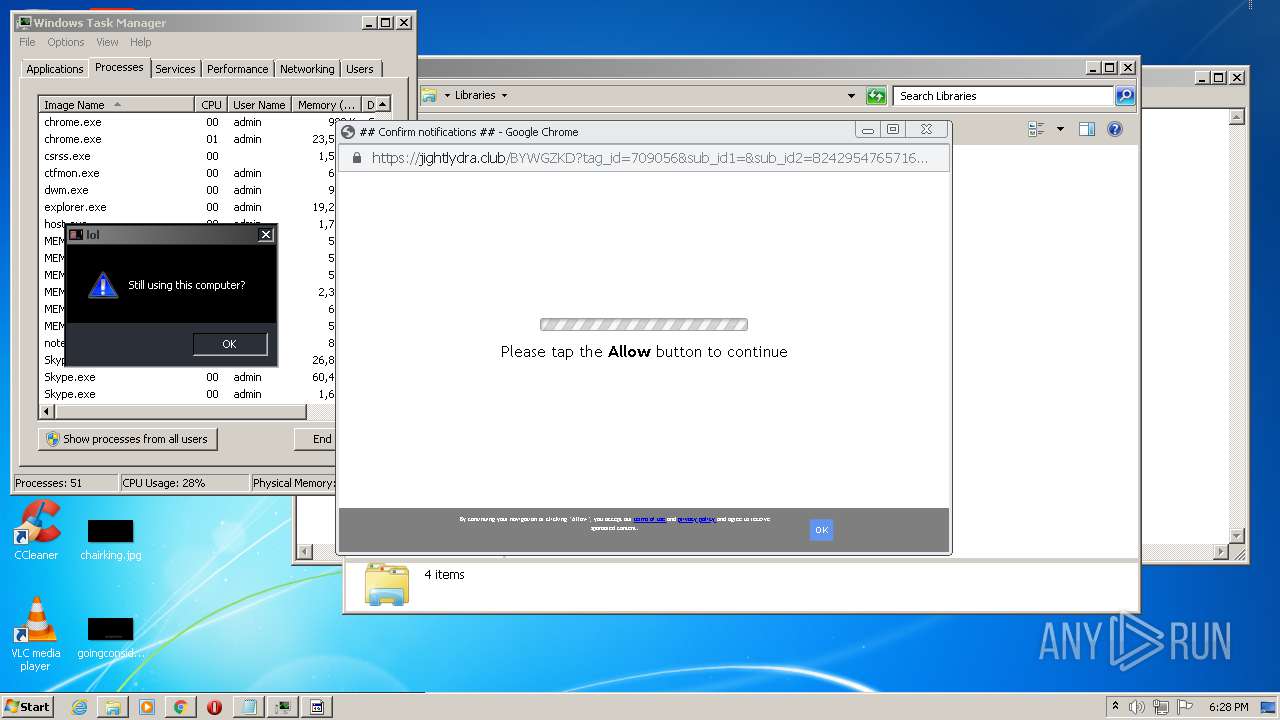
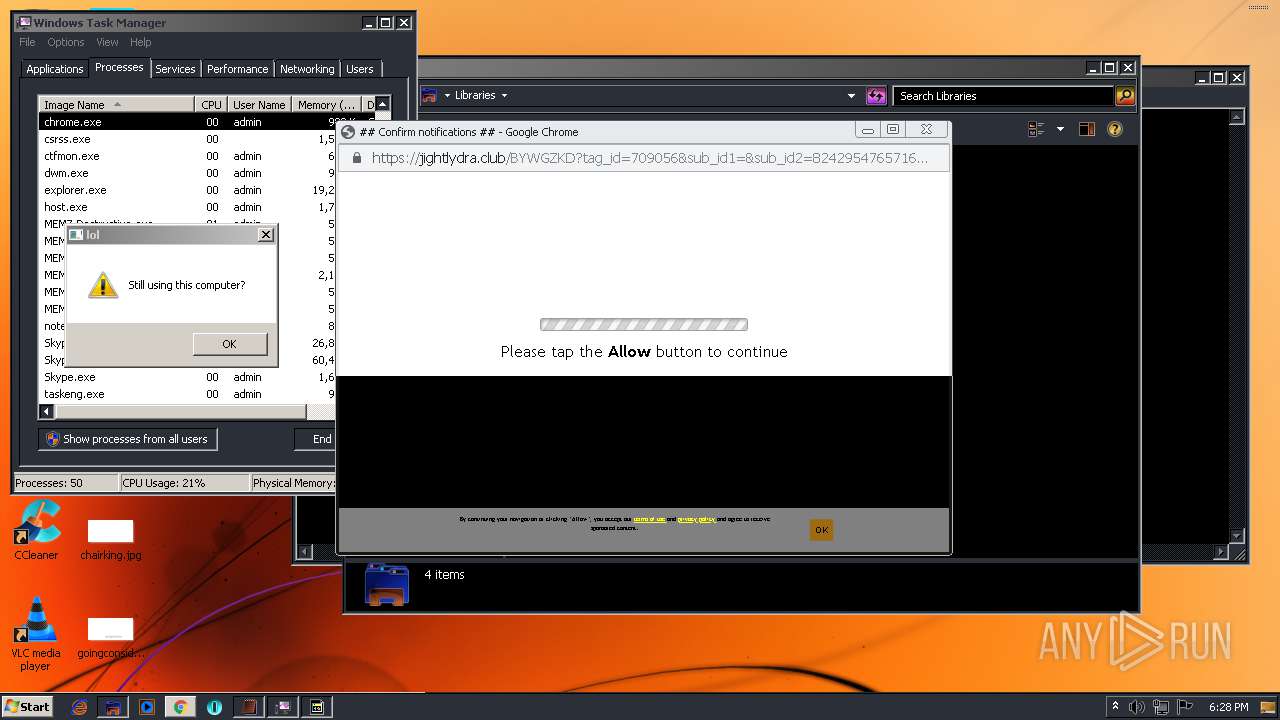
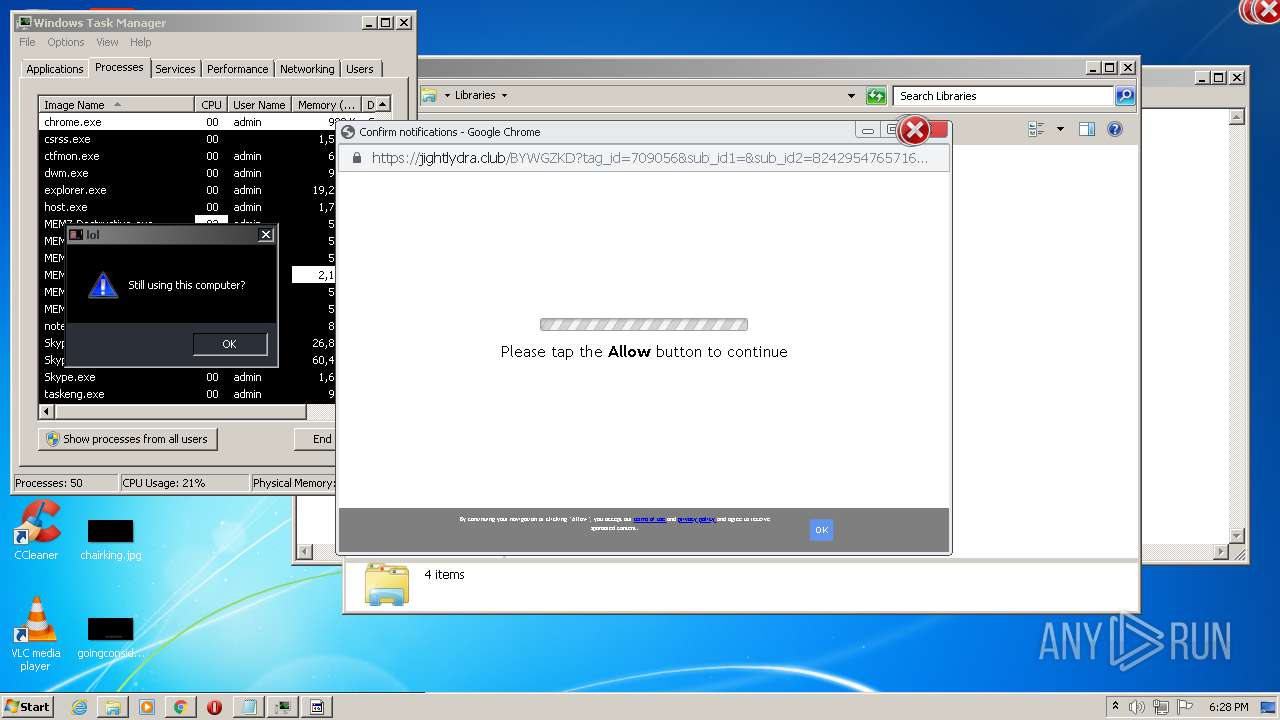
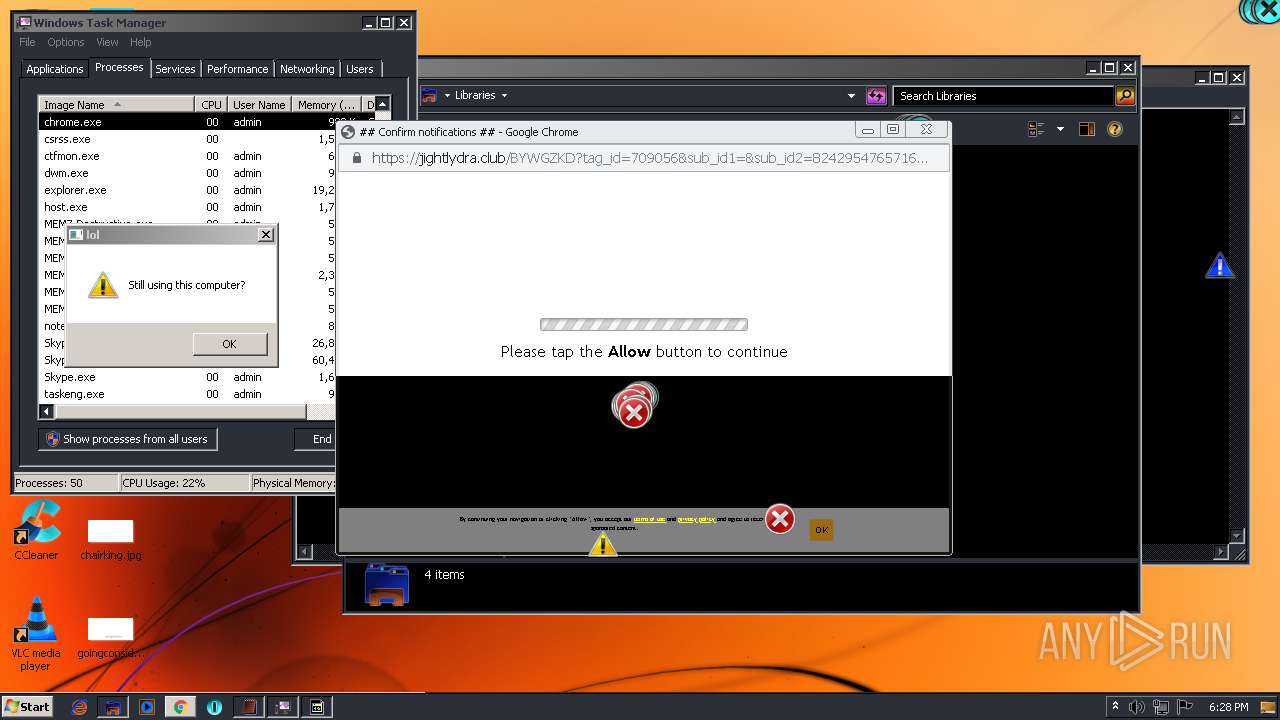
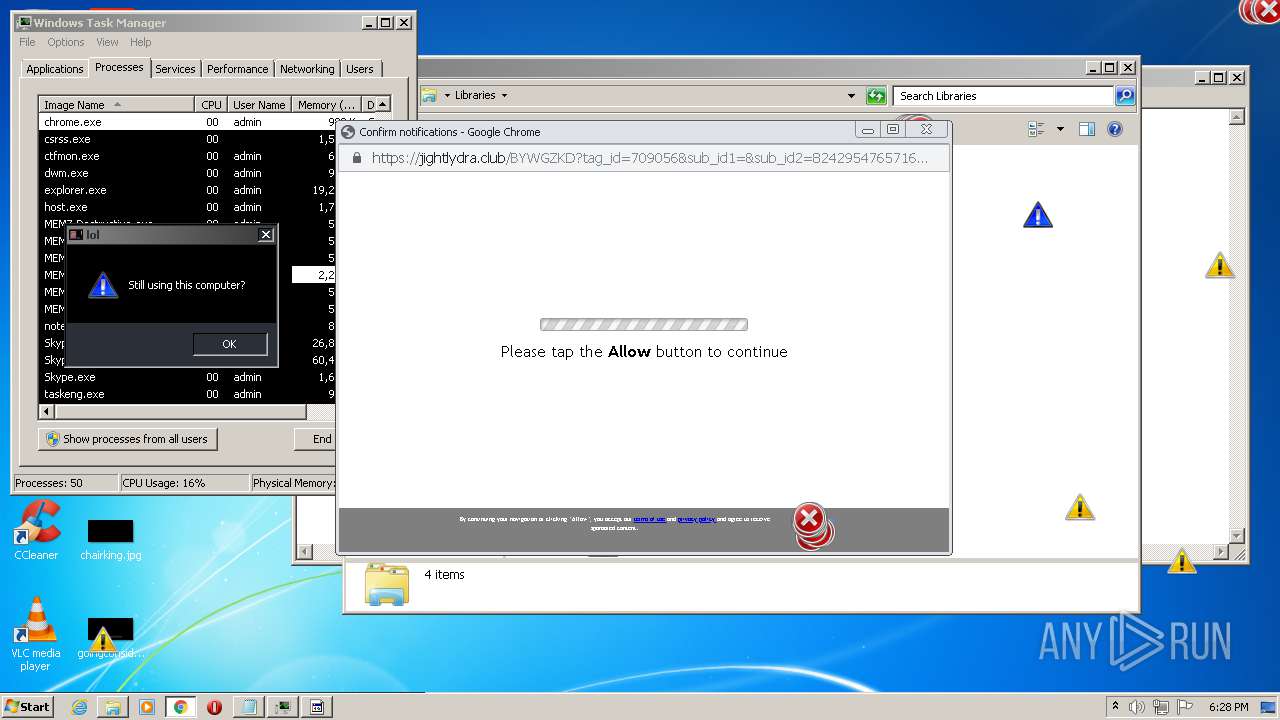
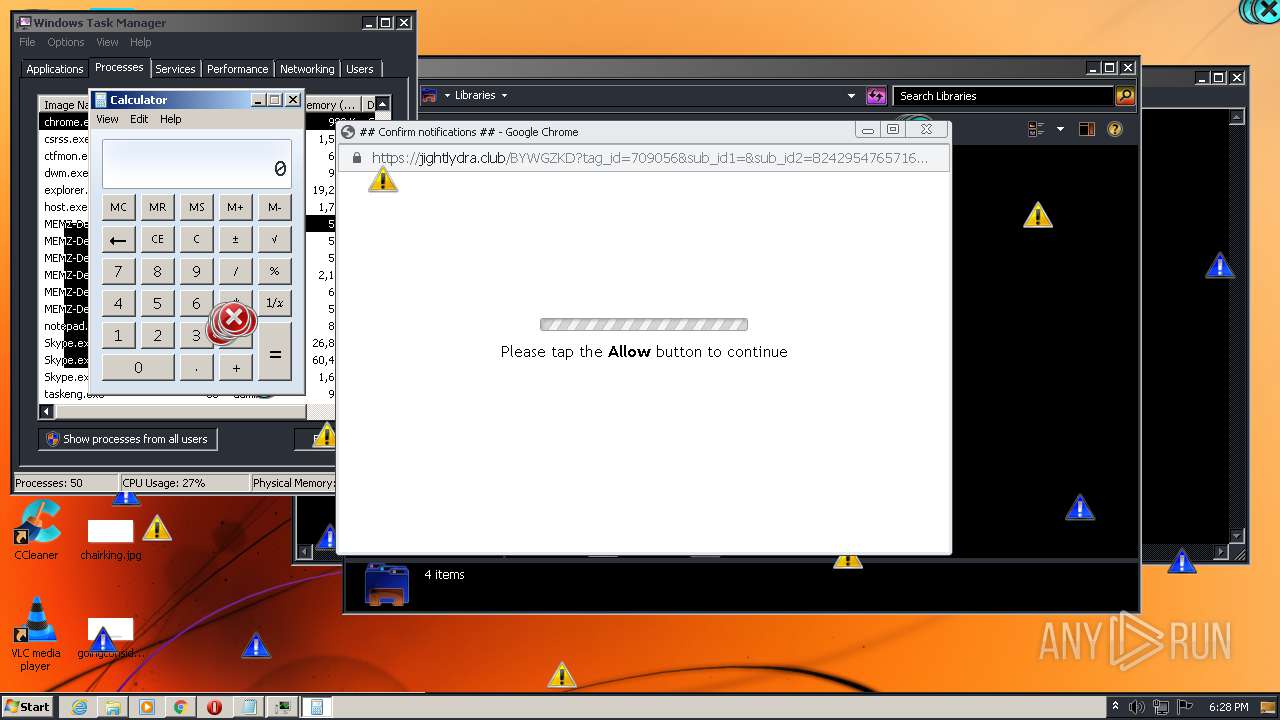
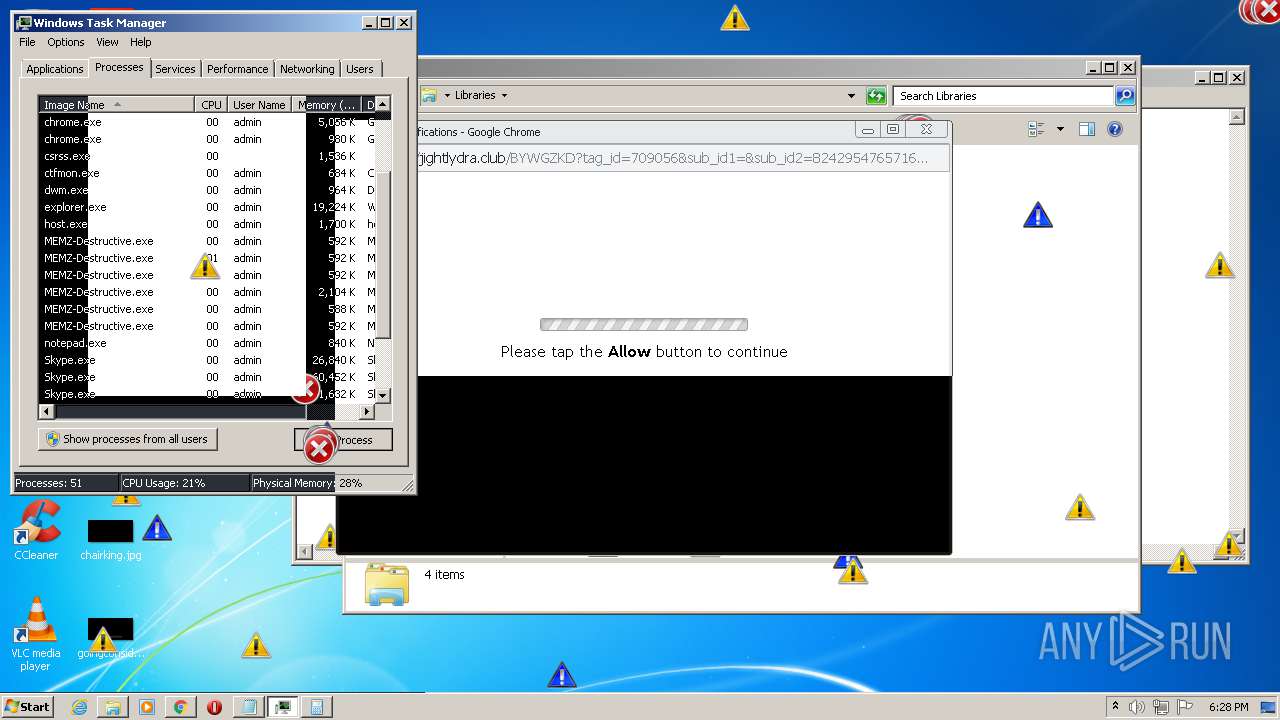
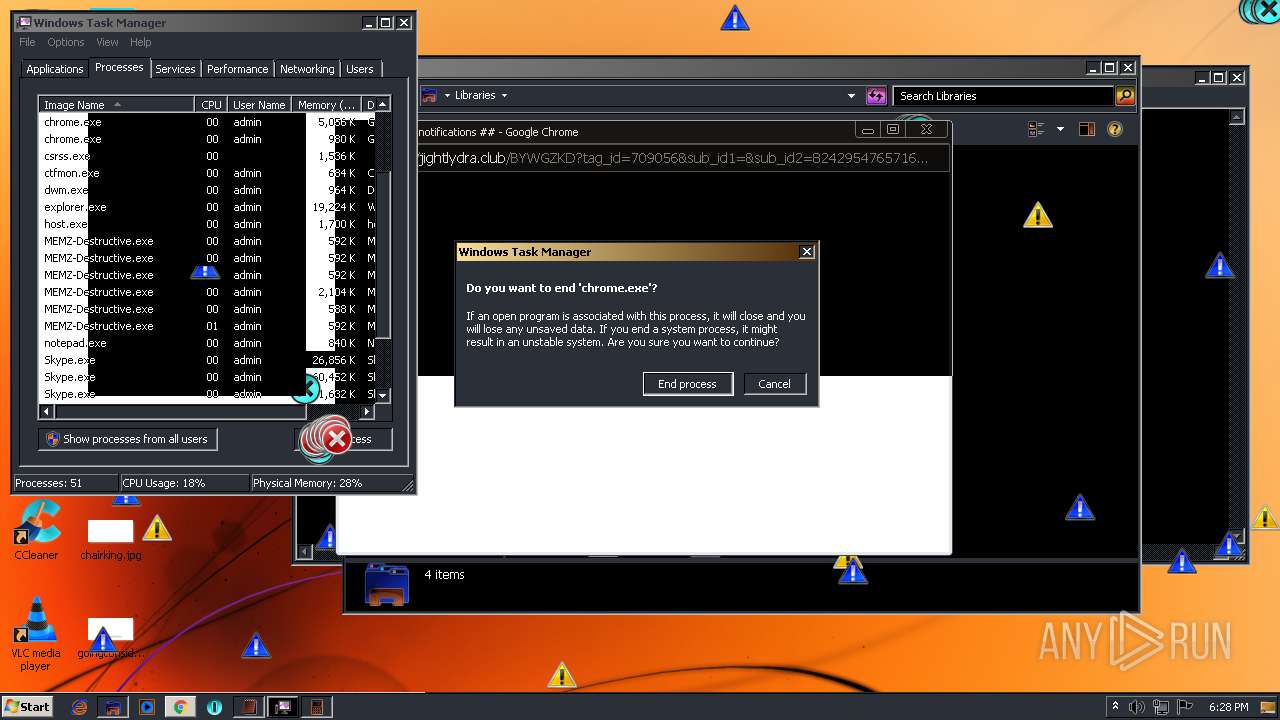
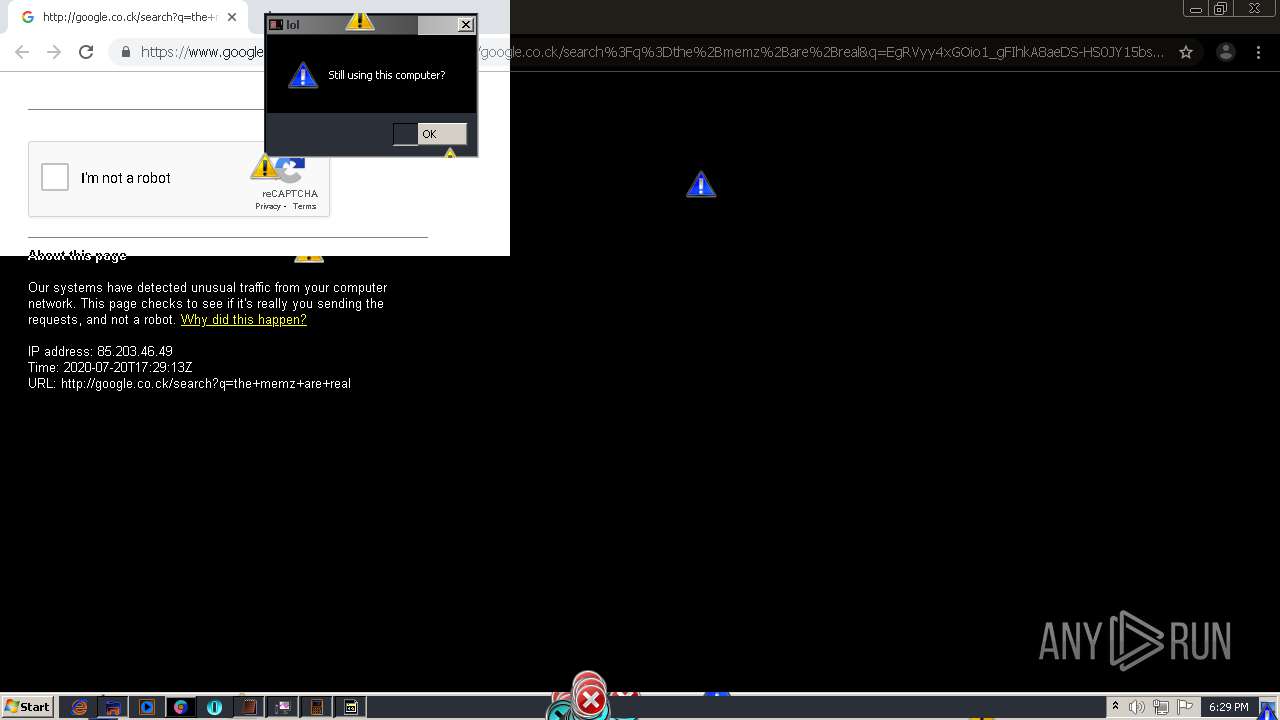
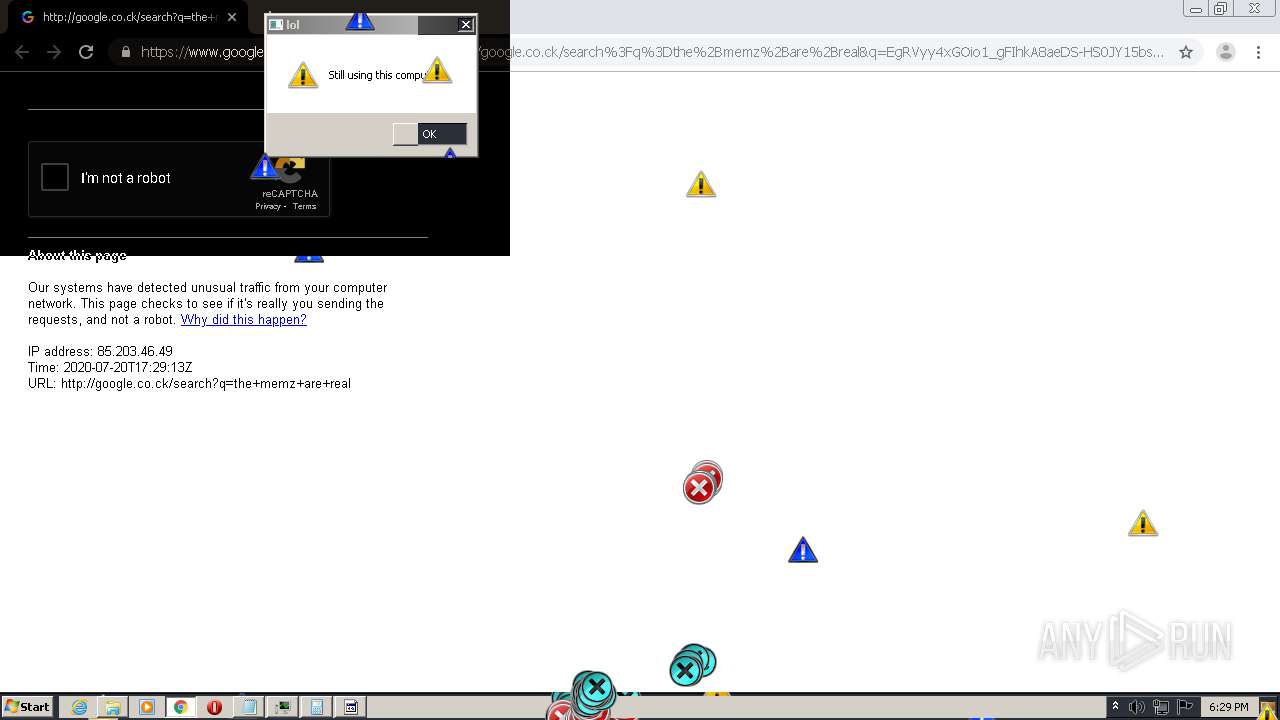
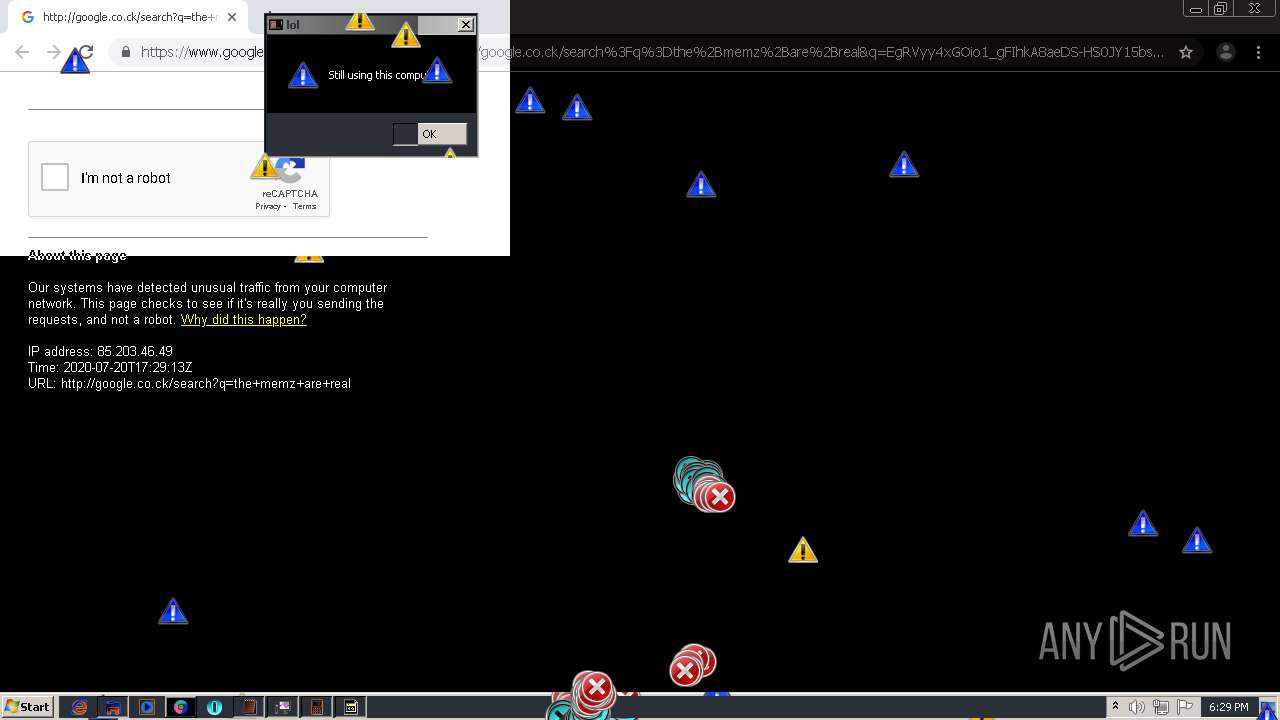
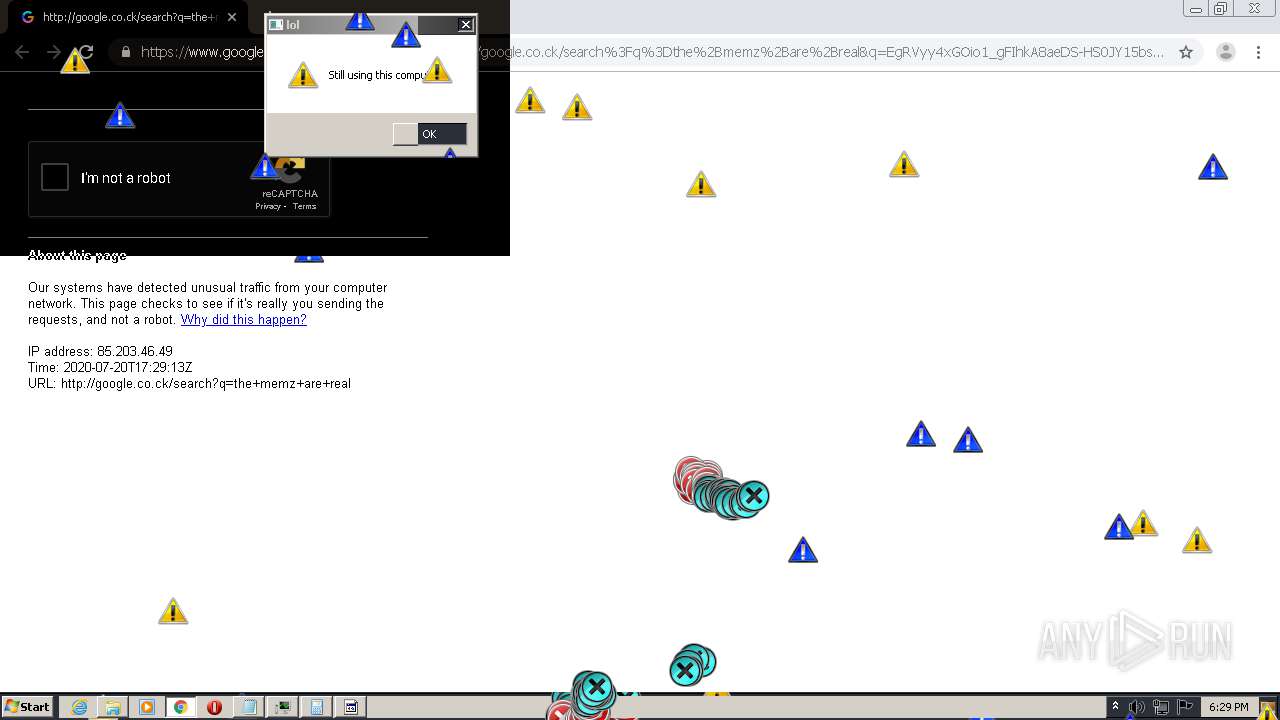
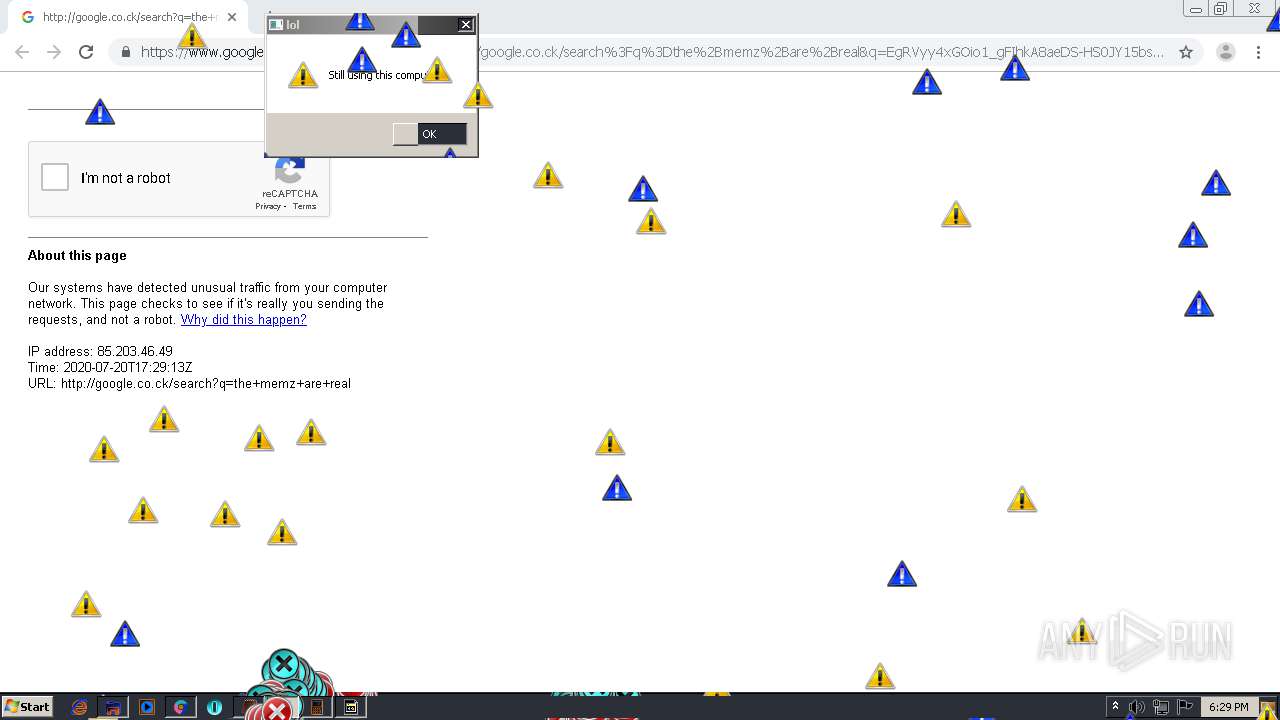
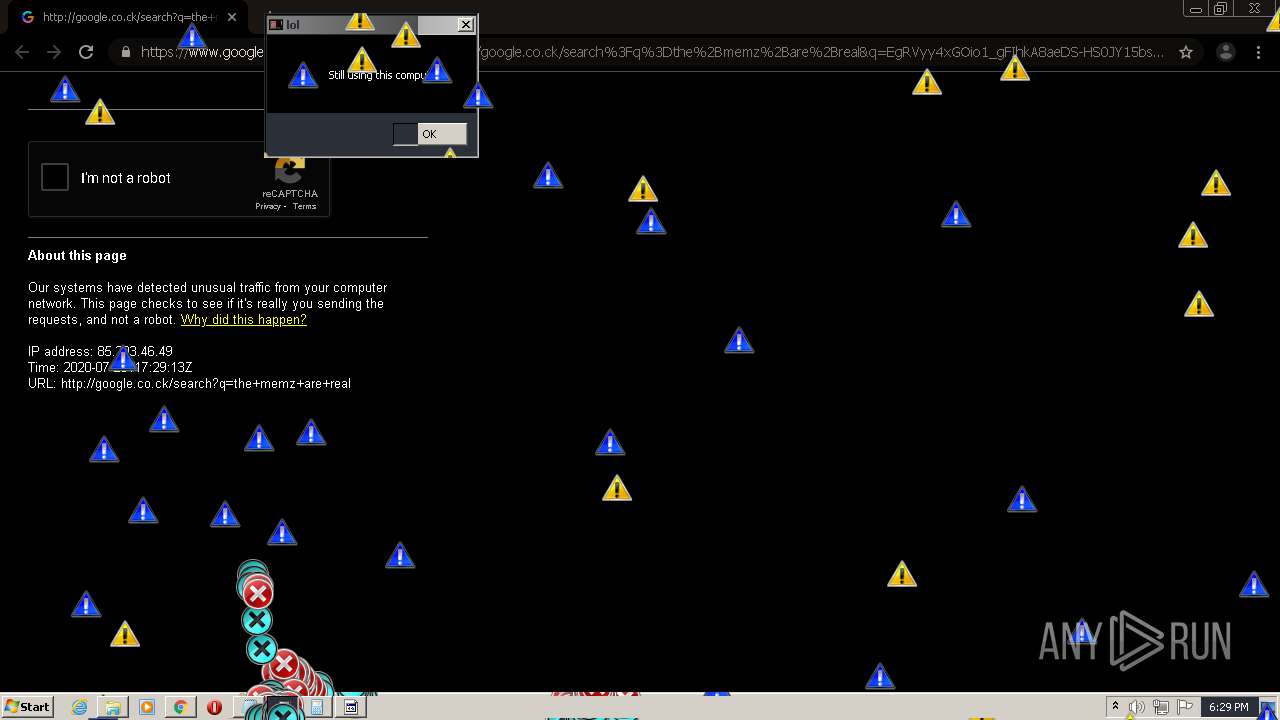
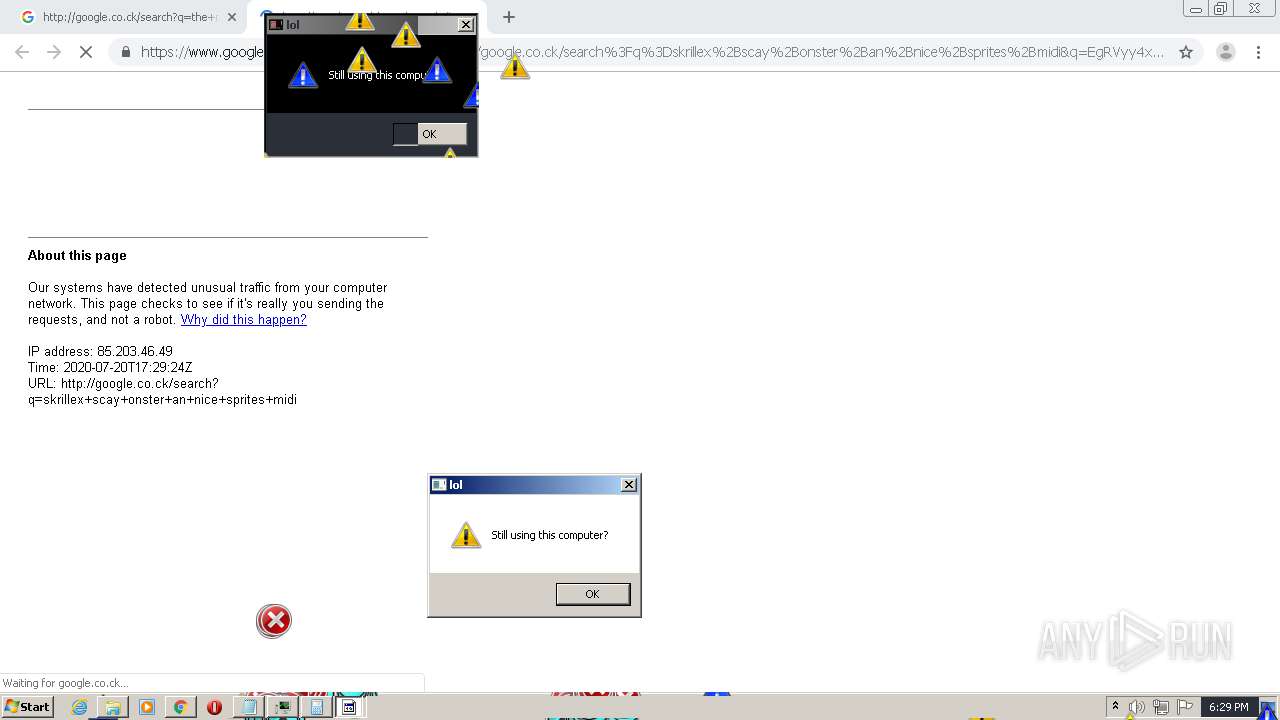
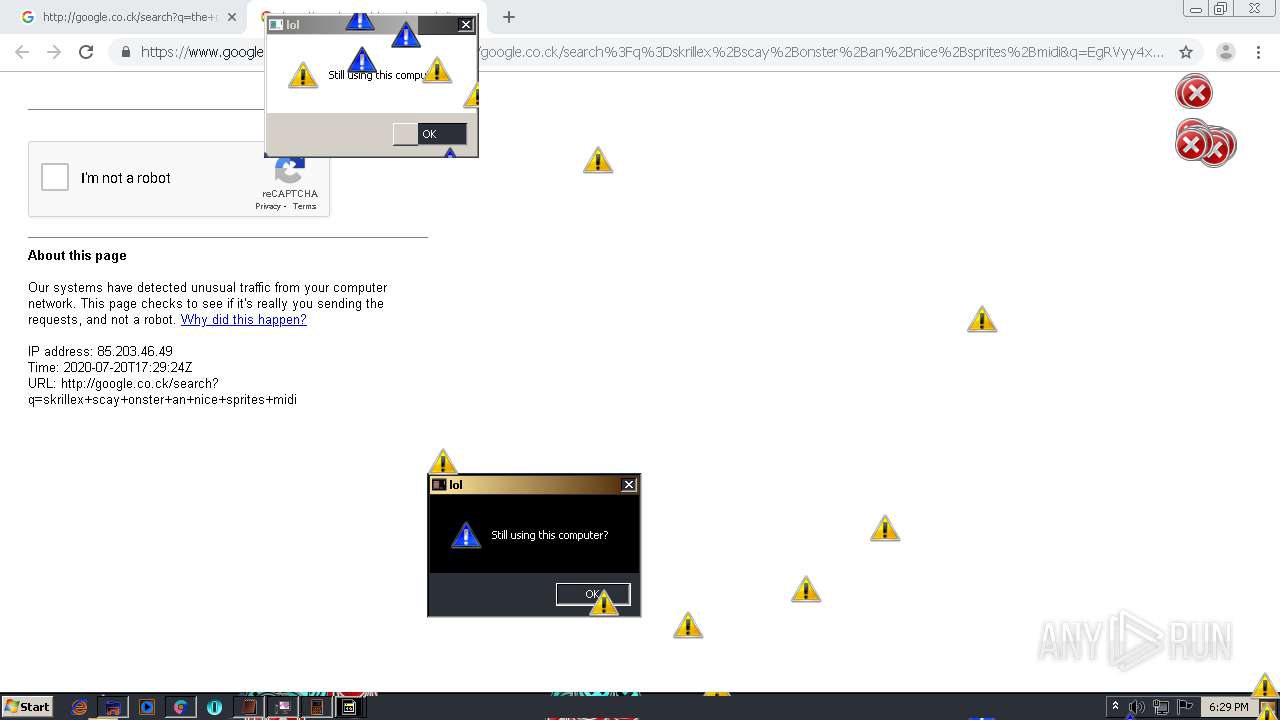
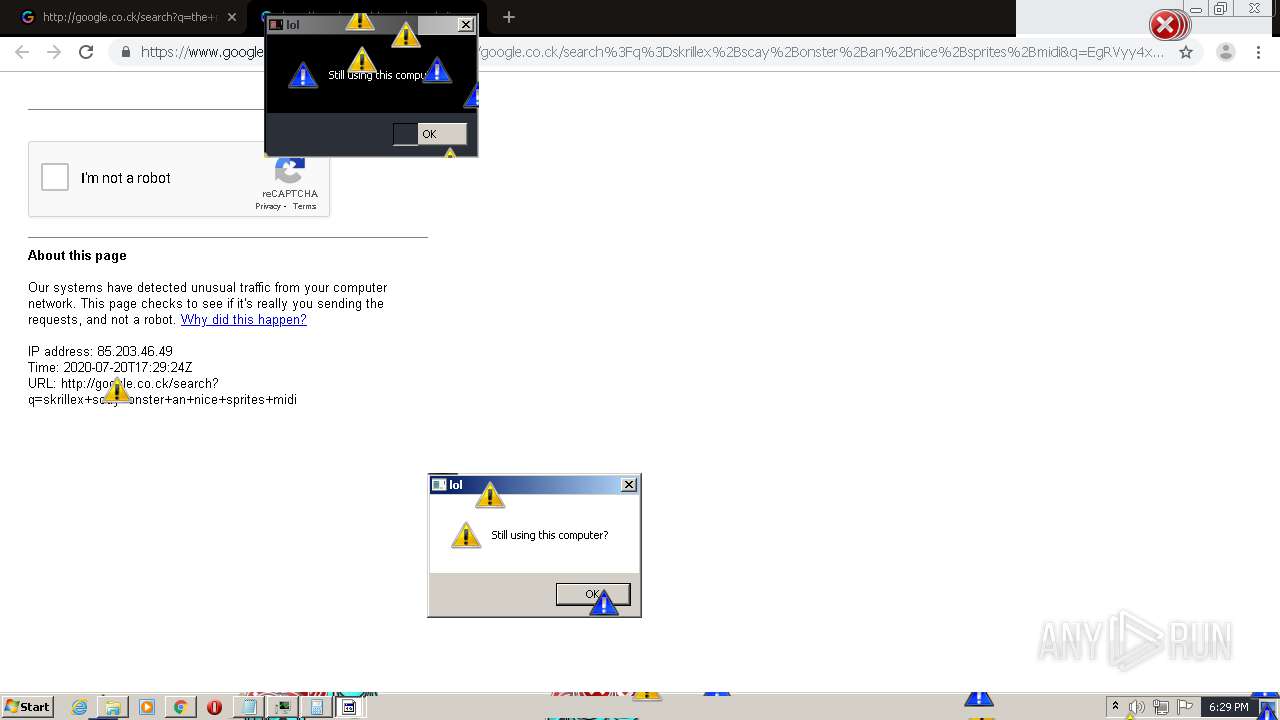
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2020, 17:24:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 410BC430431BB12DCA1CC78F3A89FADE |
| SHA1: | 57DC410832C5BE8DDD4730EF5065FCE109834DA4 |
| SHA256: | AE6539839A542FC267FC770695333224F8D8B2ED926B154269887C5850E3B683 |
| SSDEEP: | 3:N8tEdUI2gMFhn:2uu1Fh |
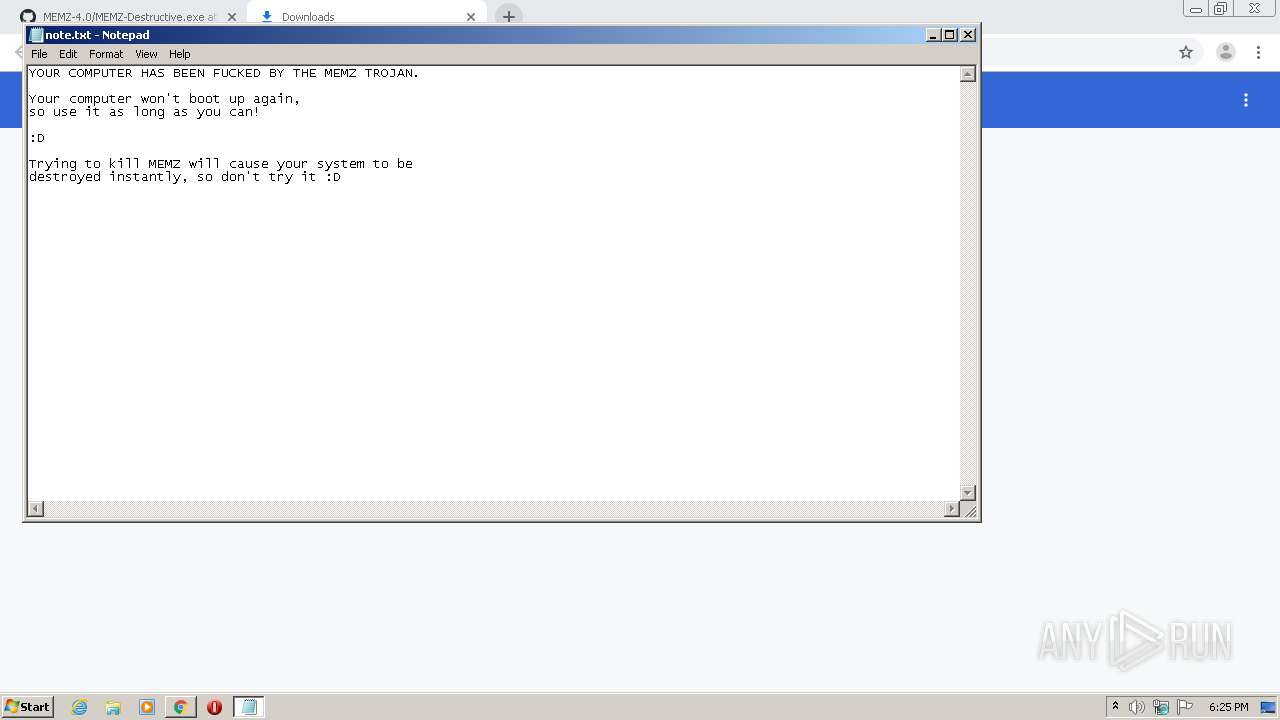
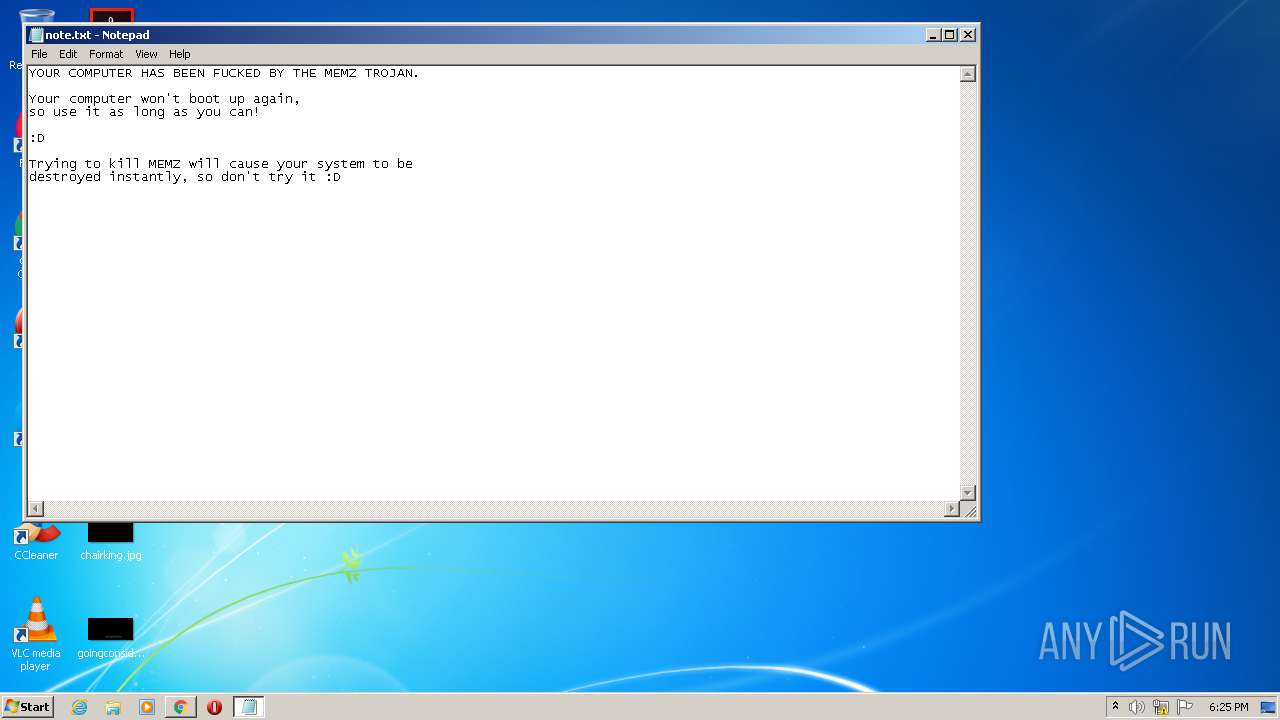
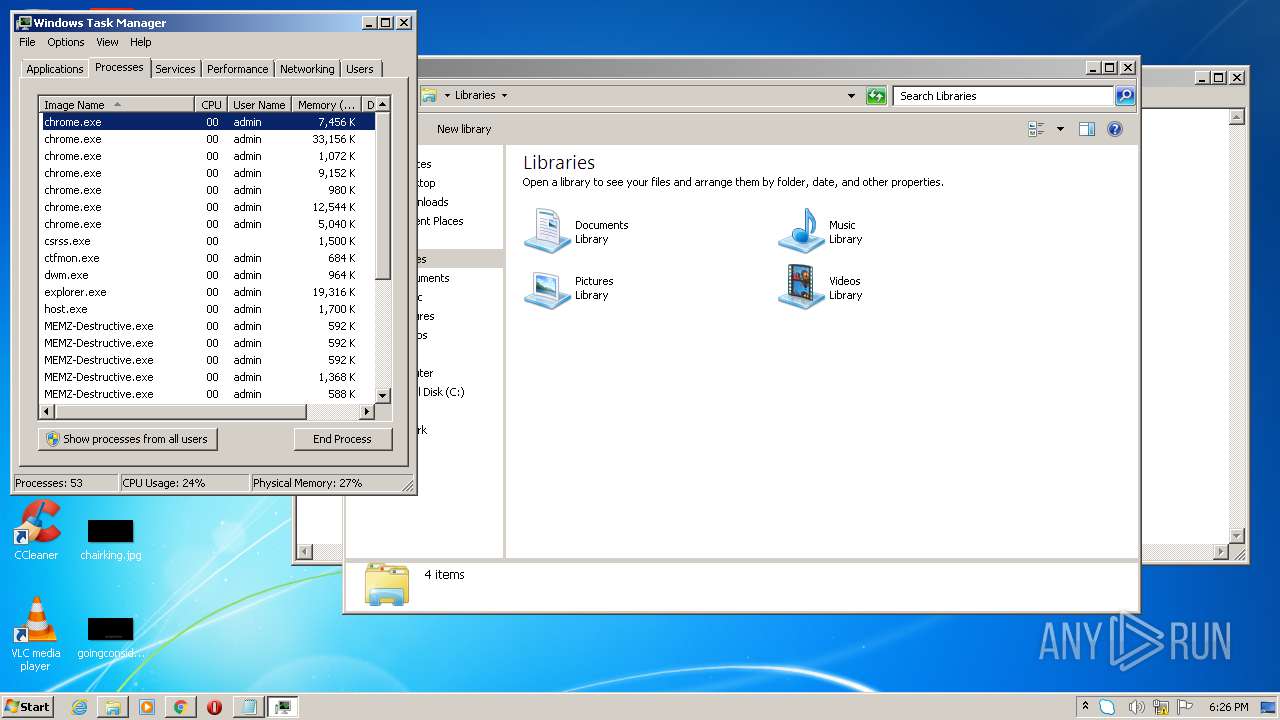
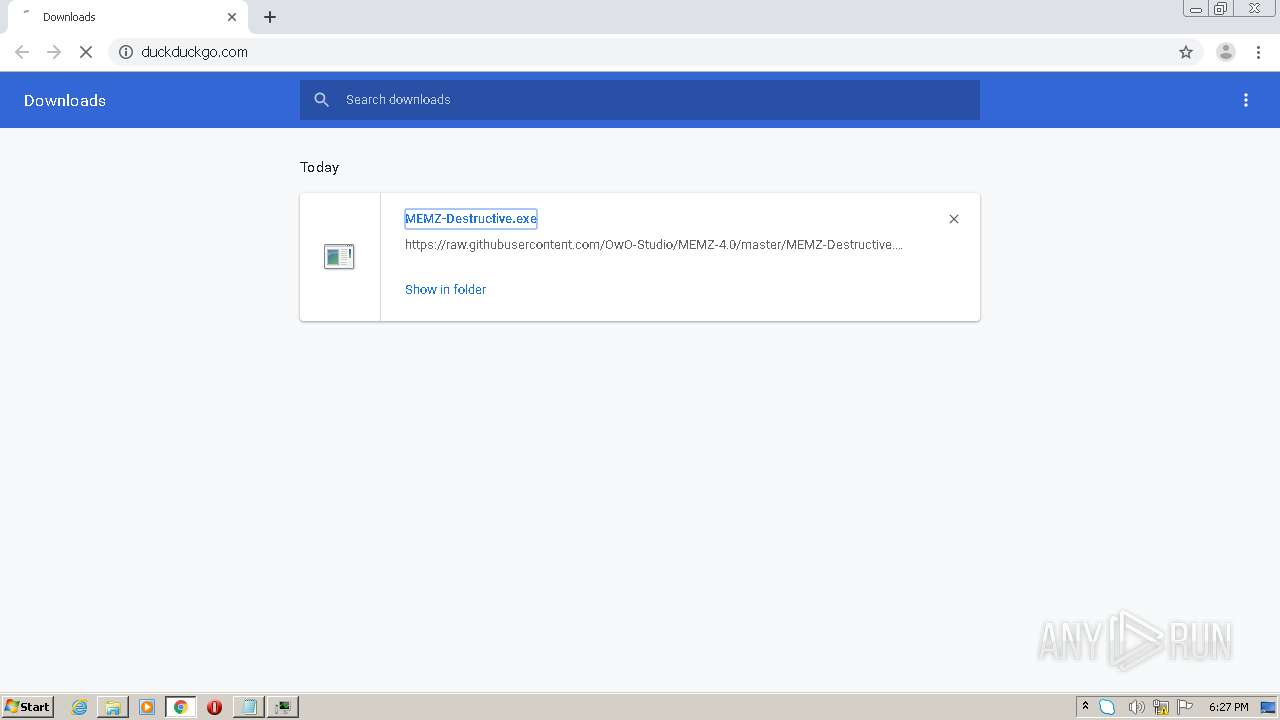
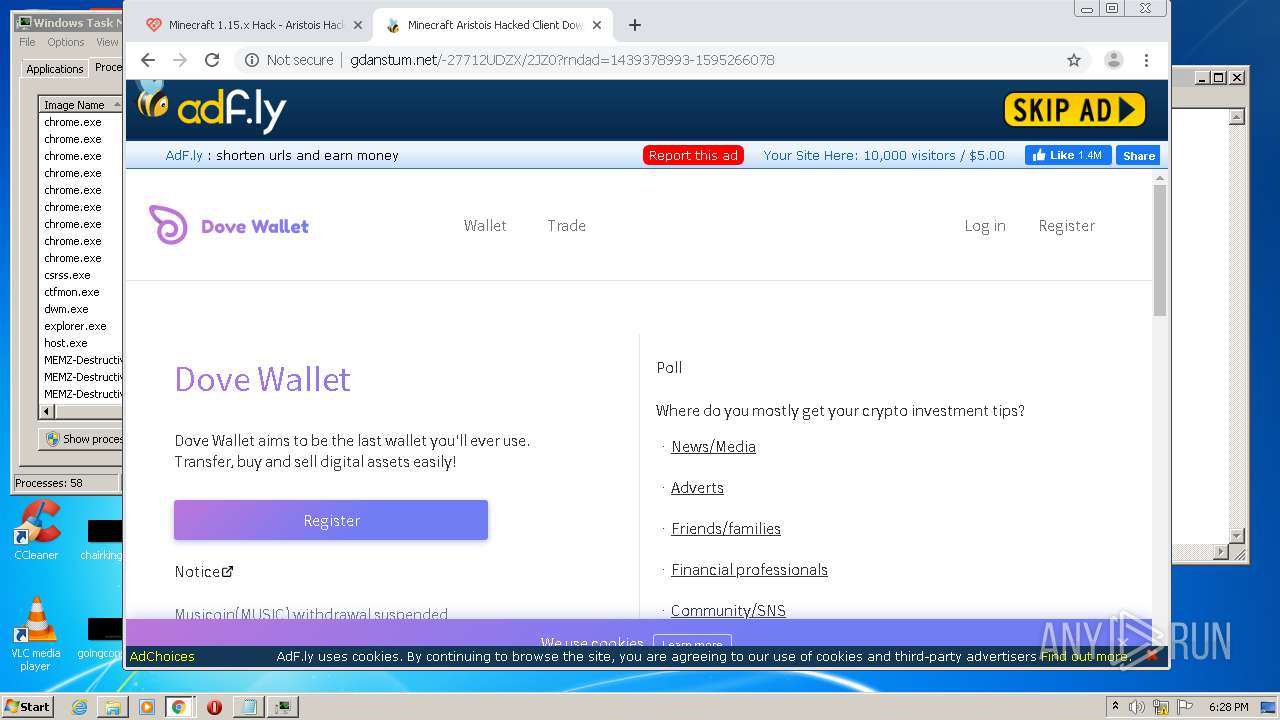
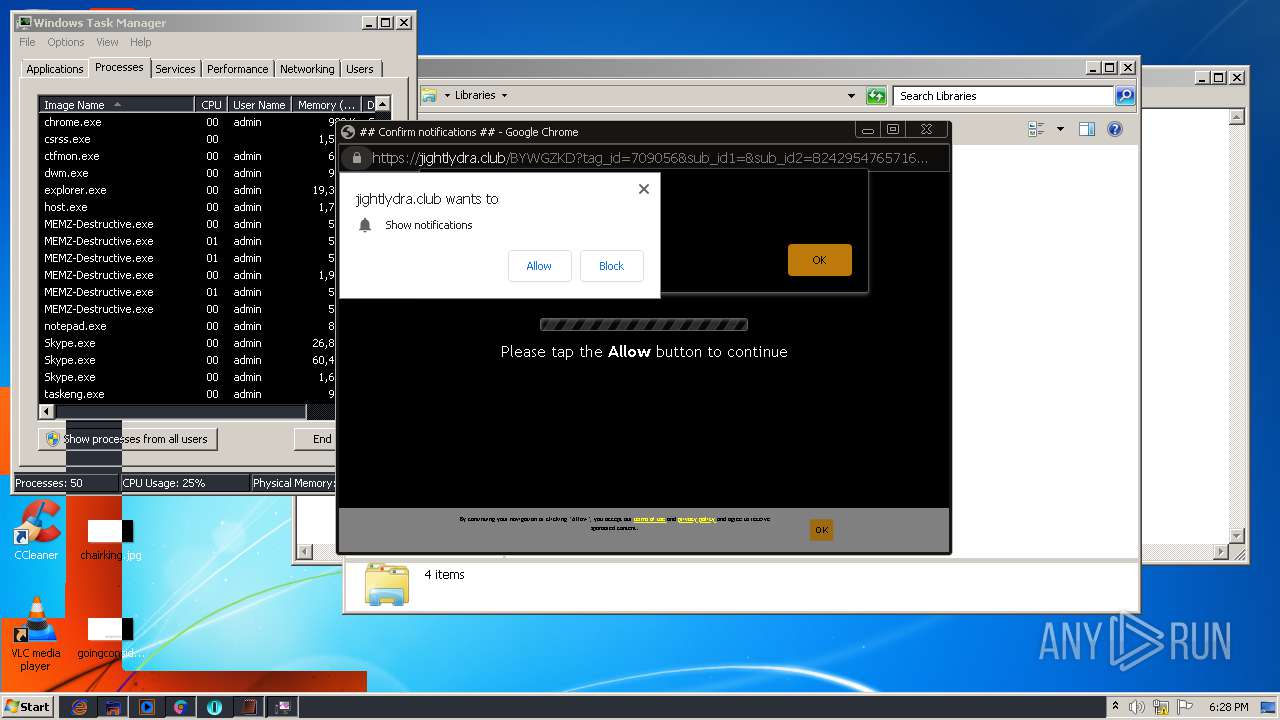
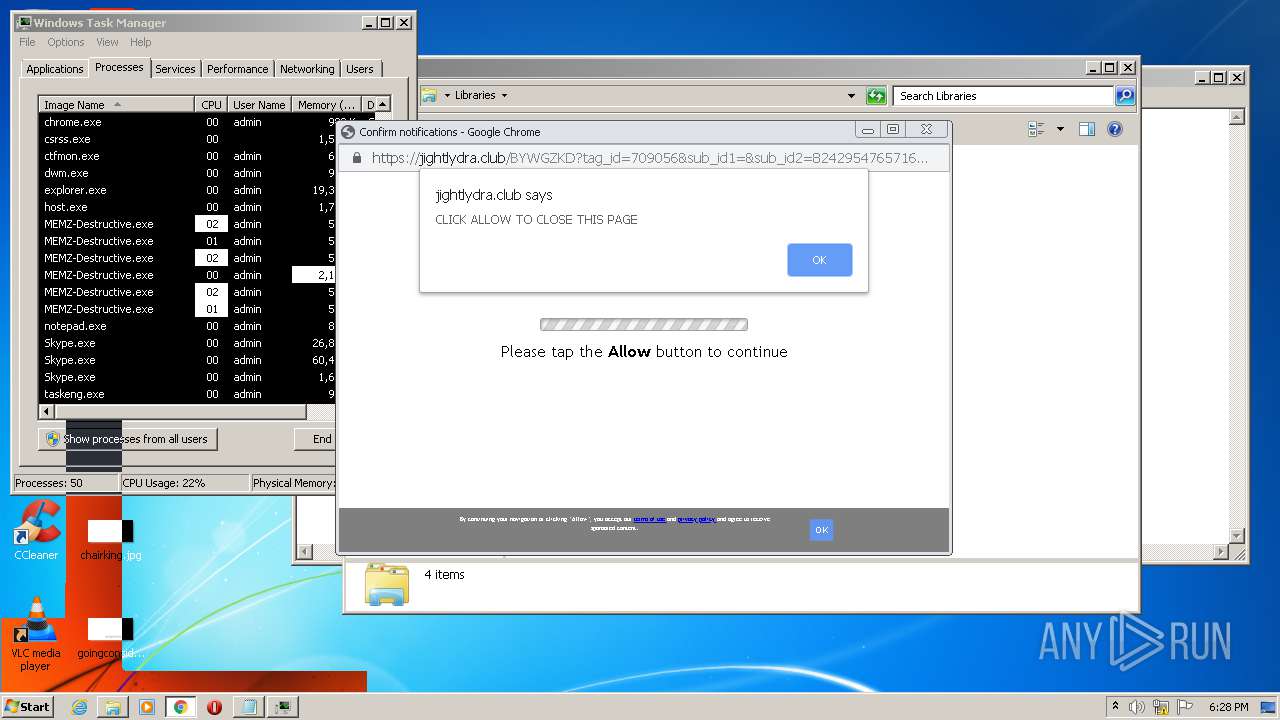
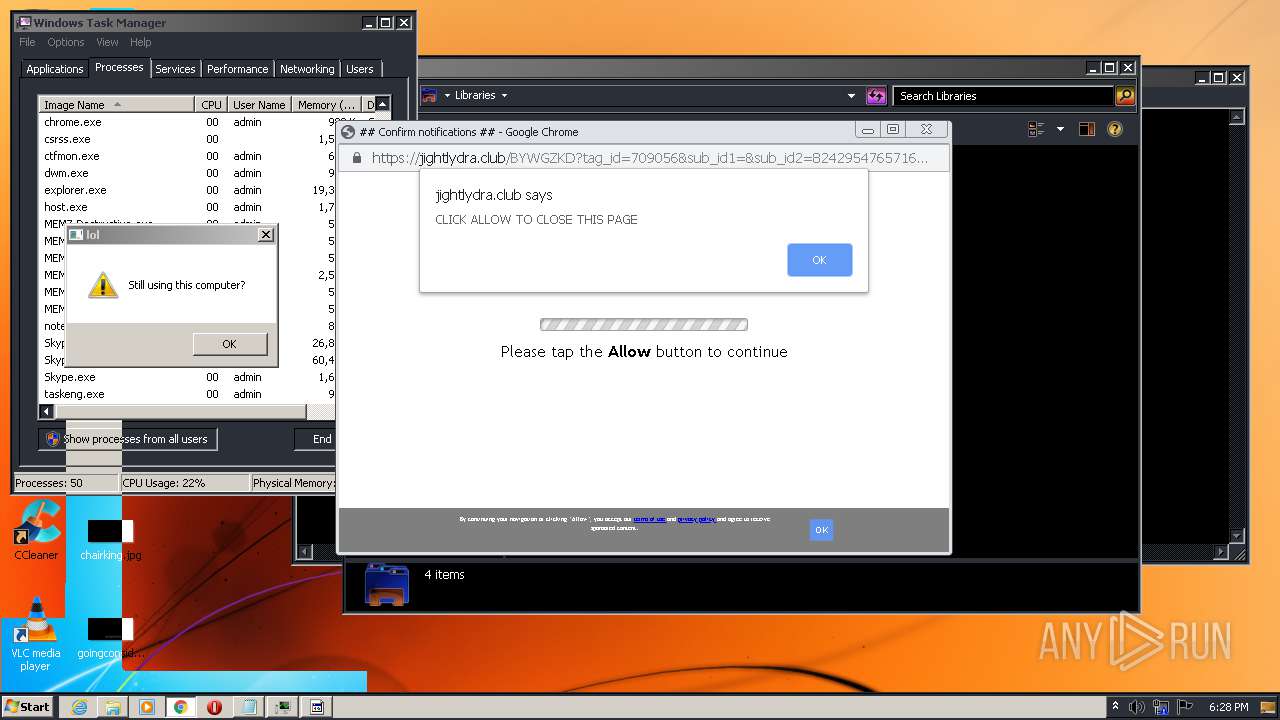
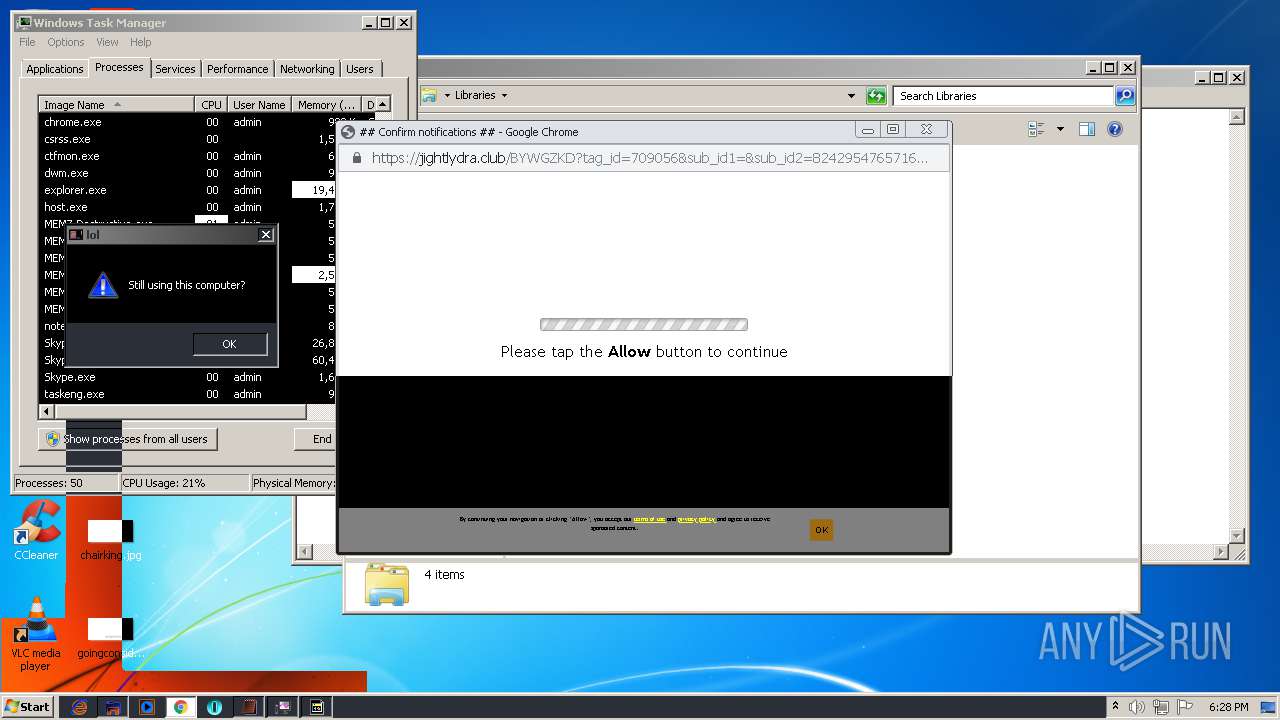
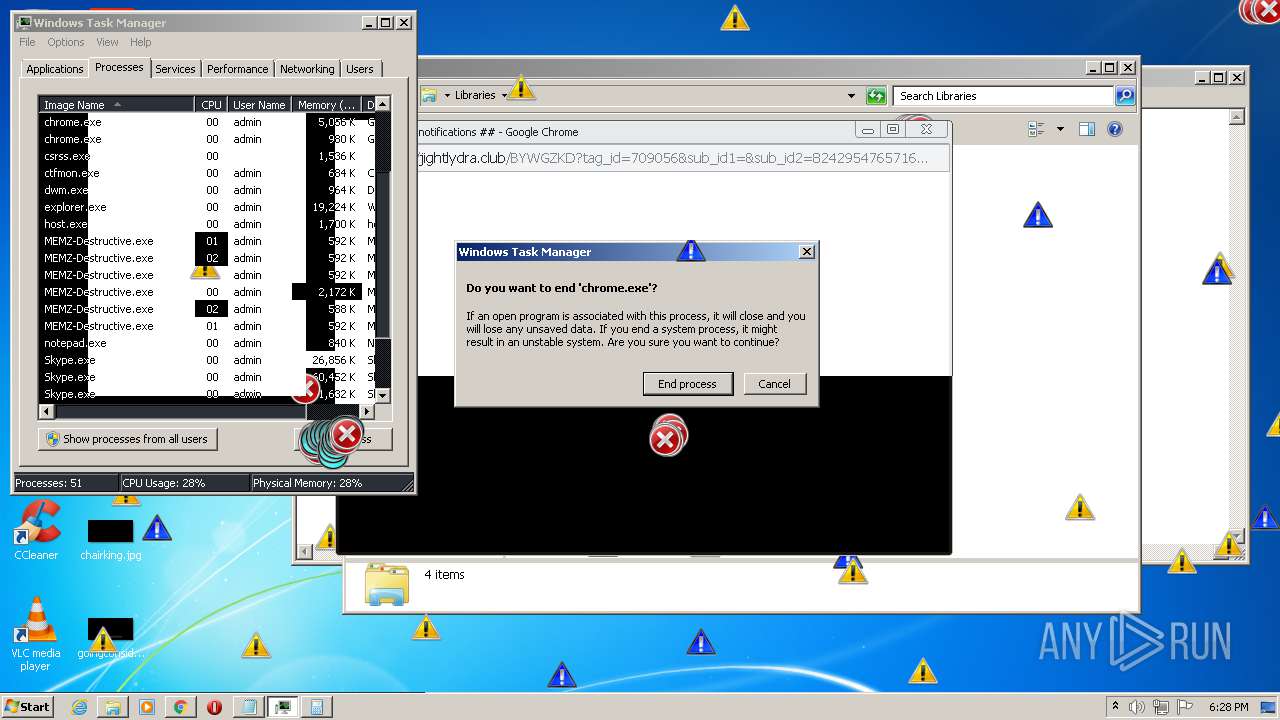
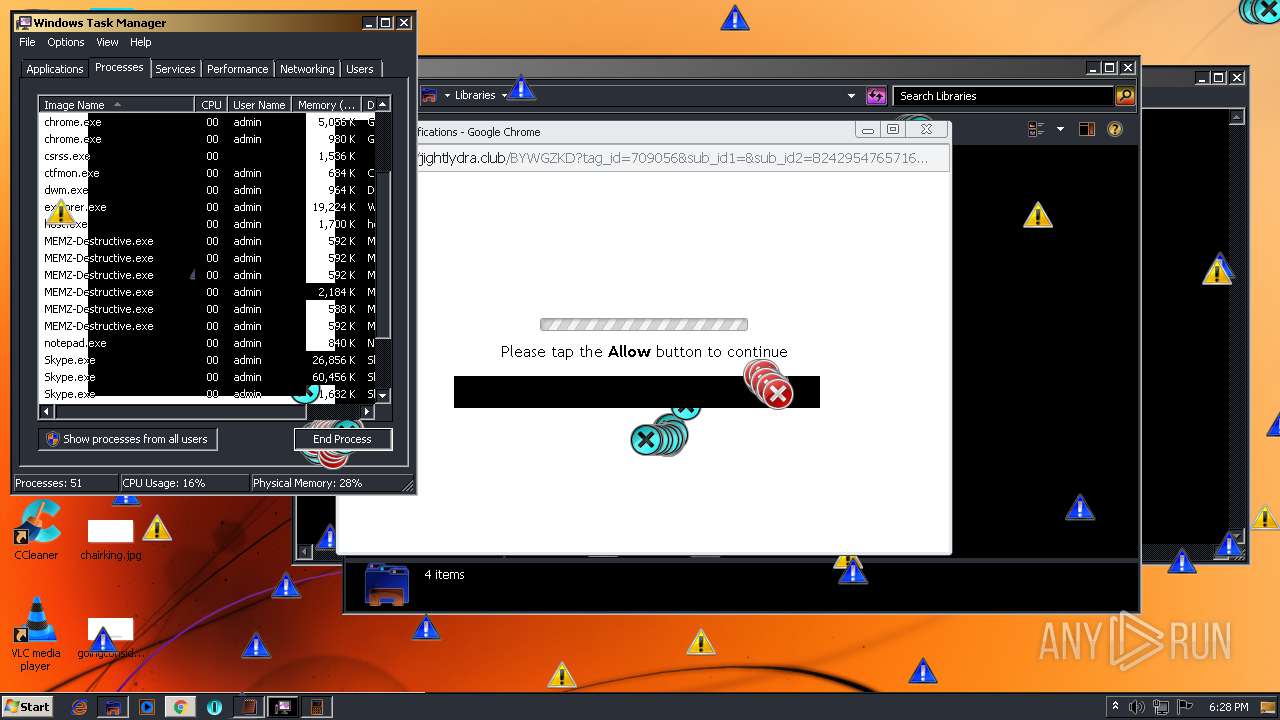
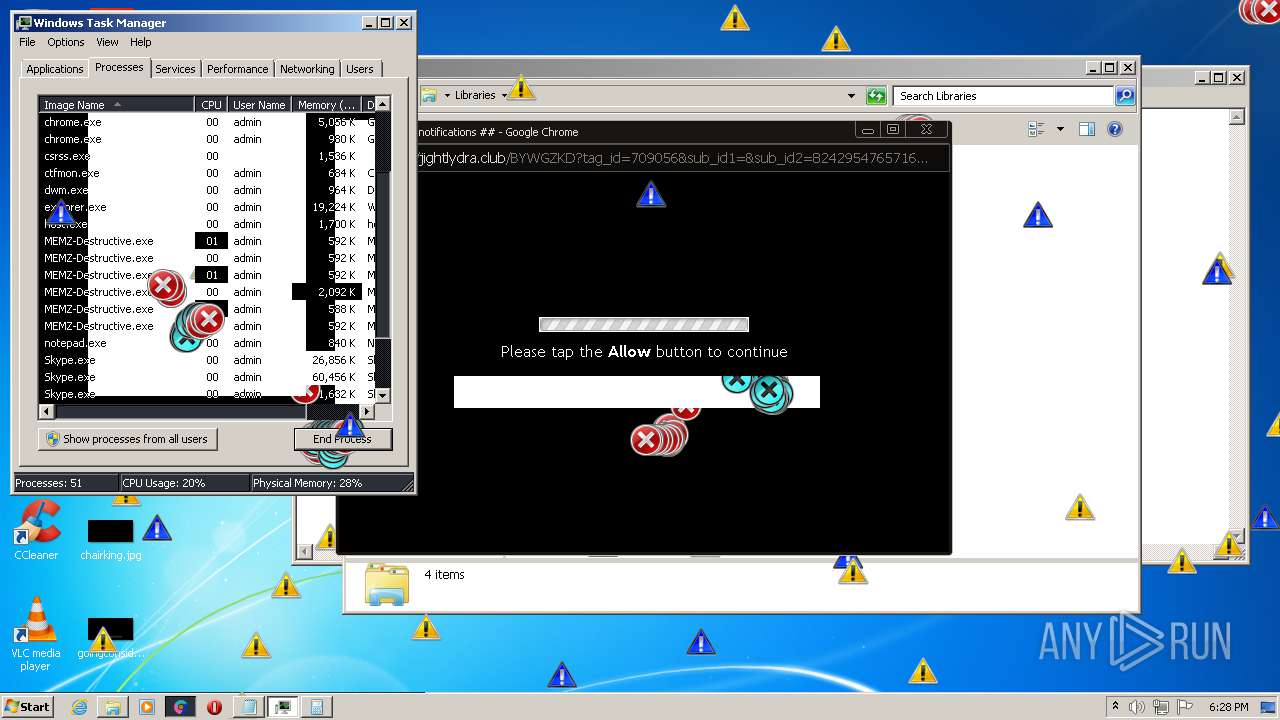
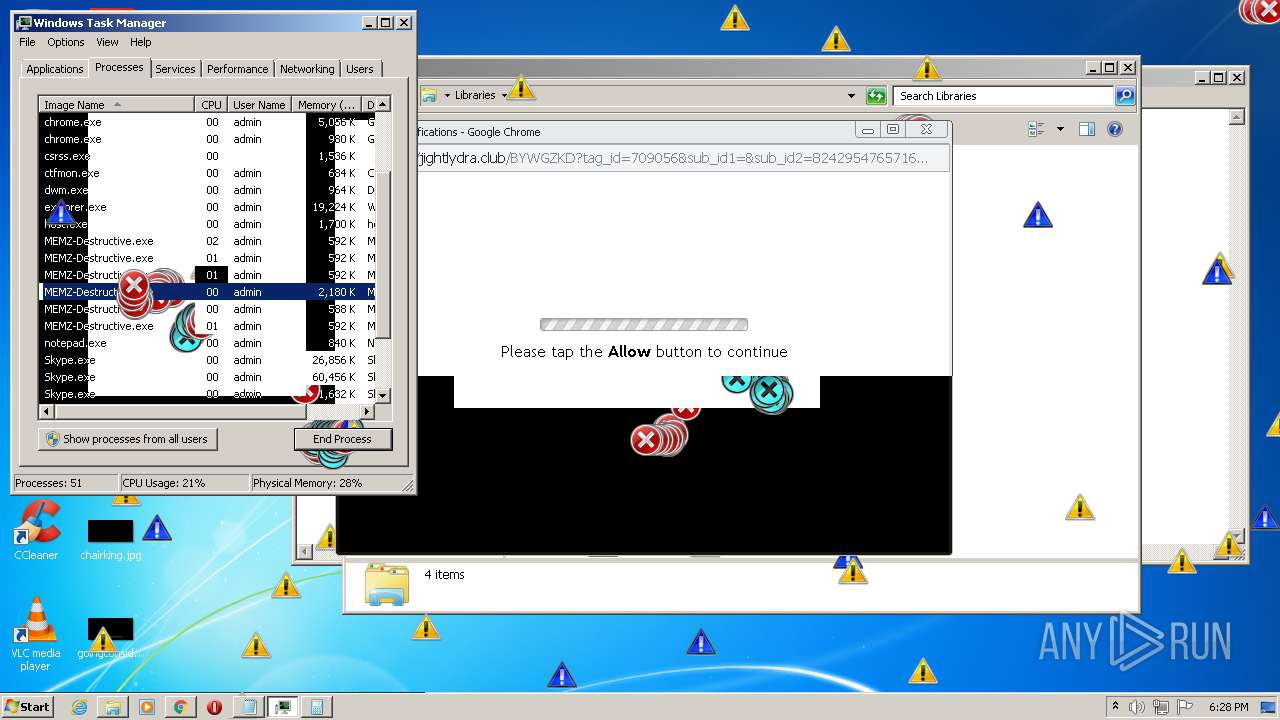
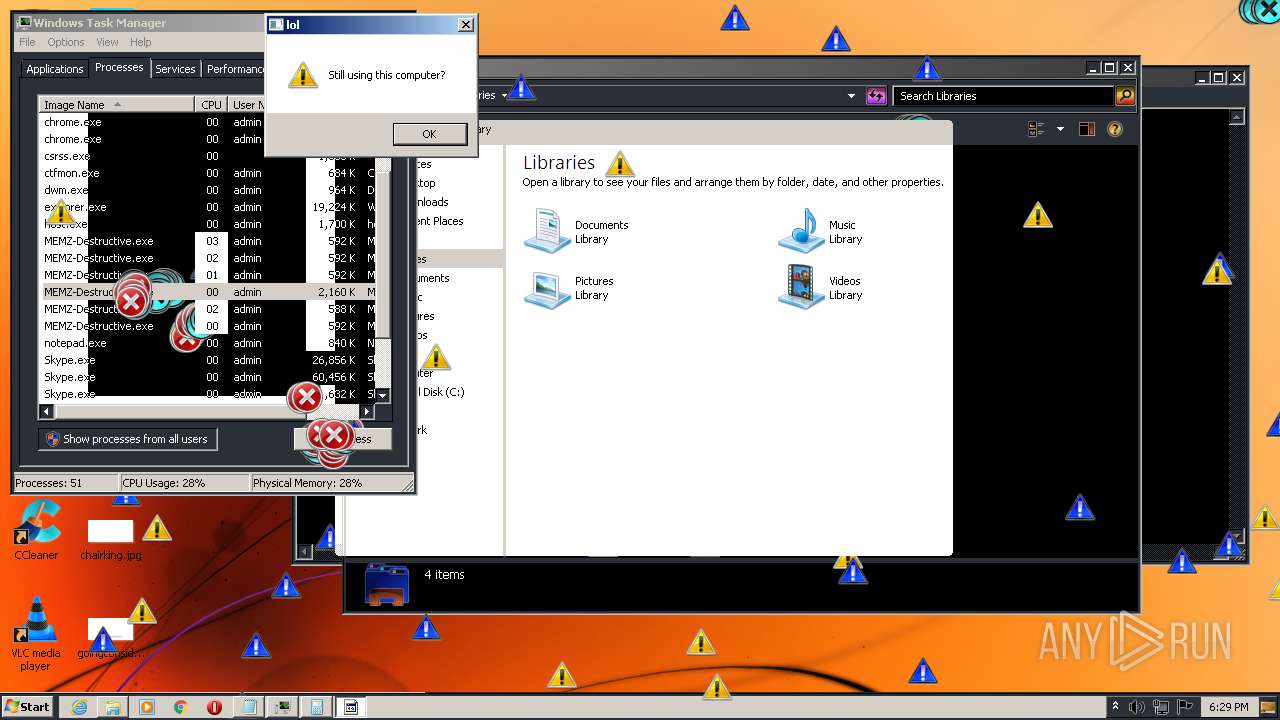
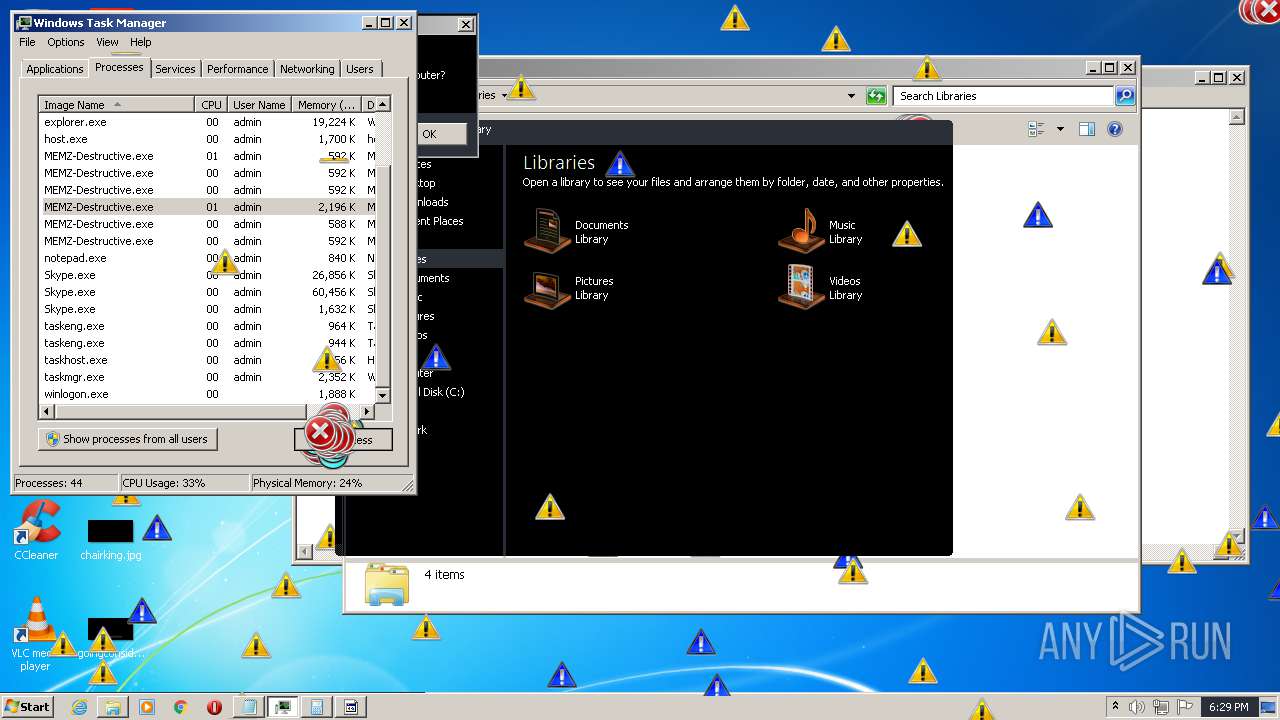
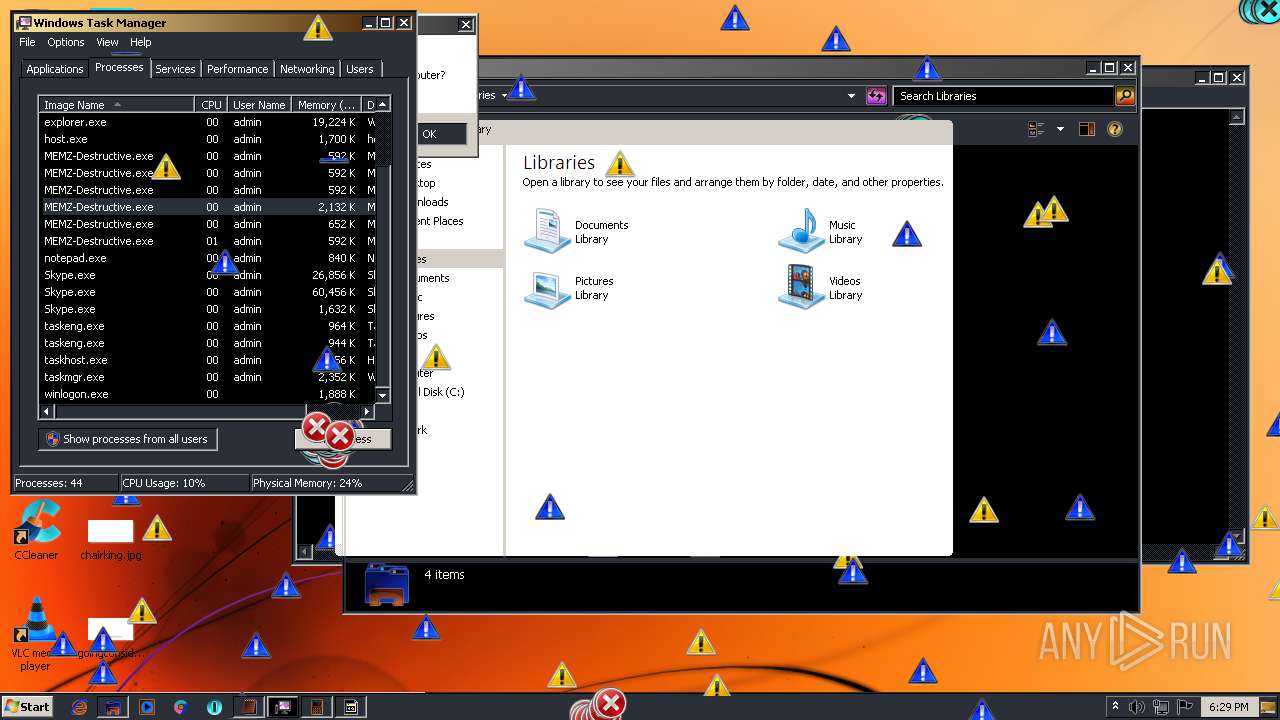
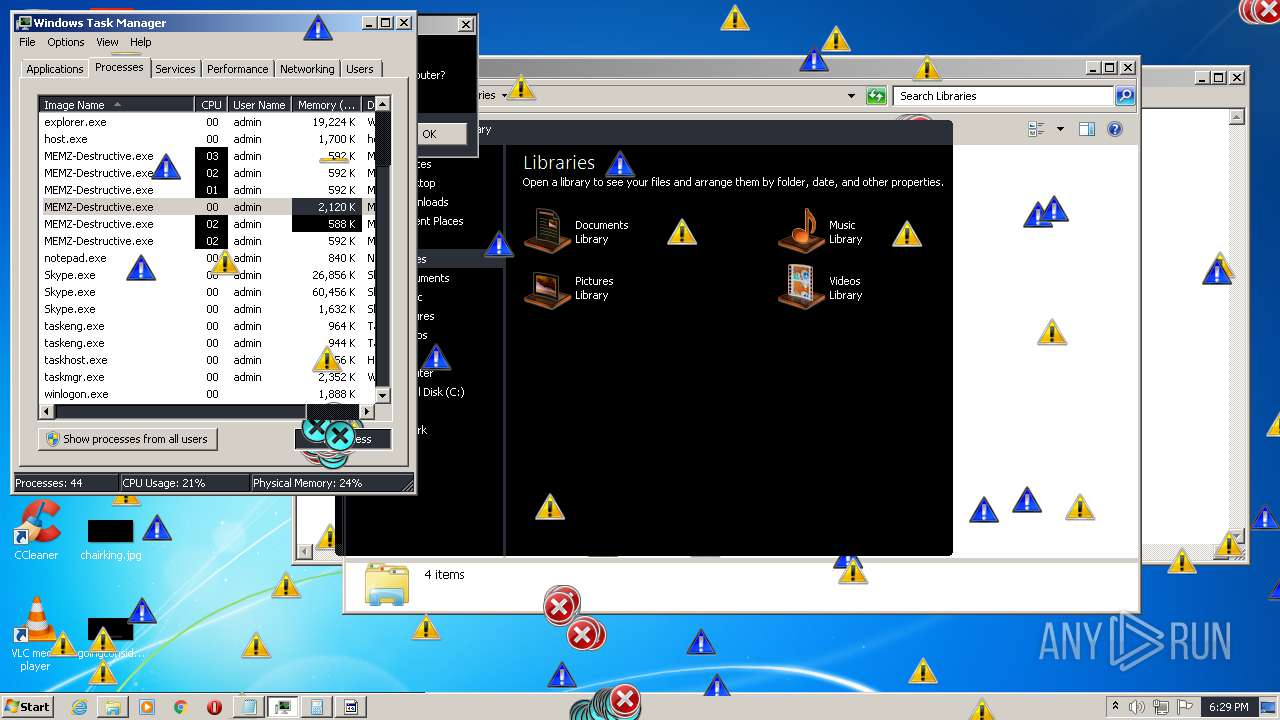
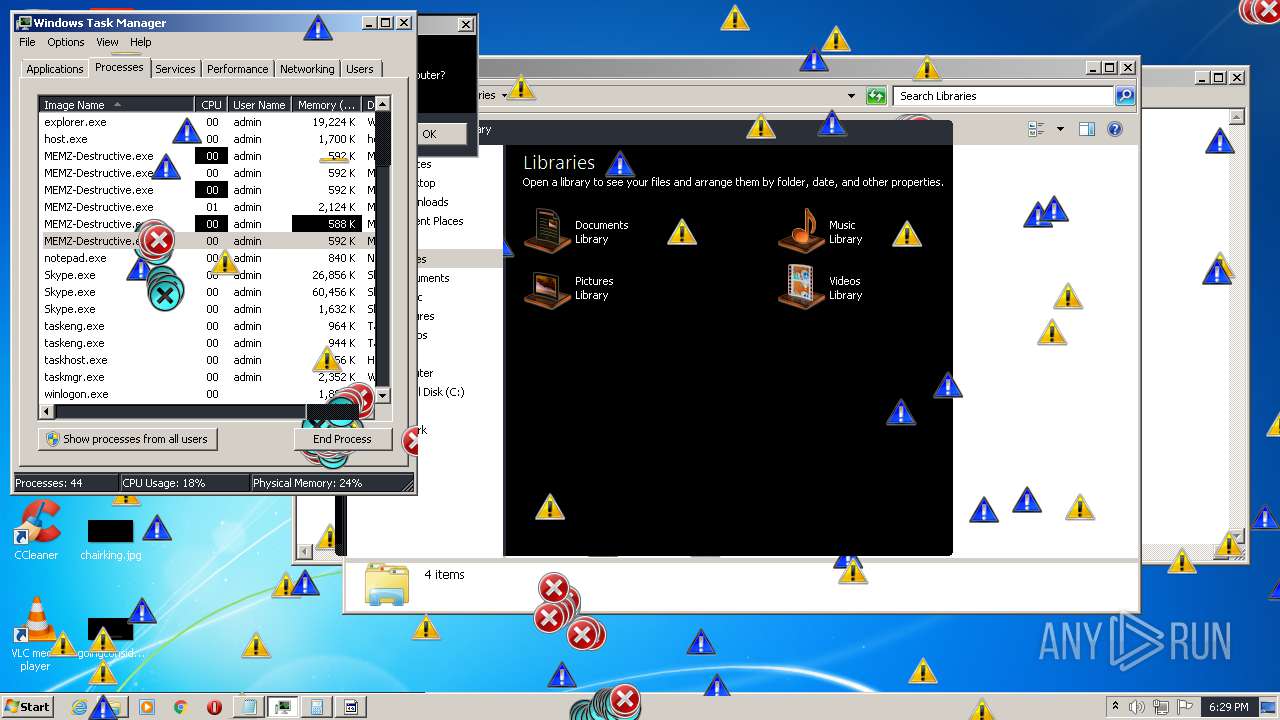
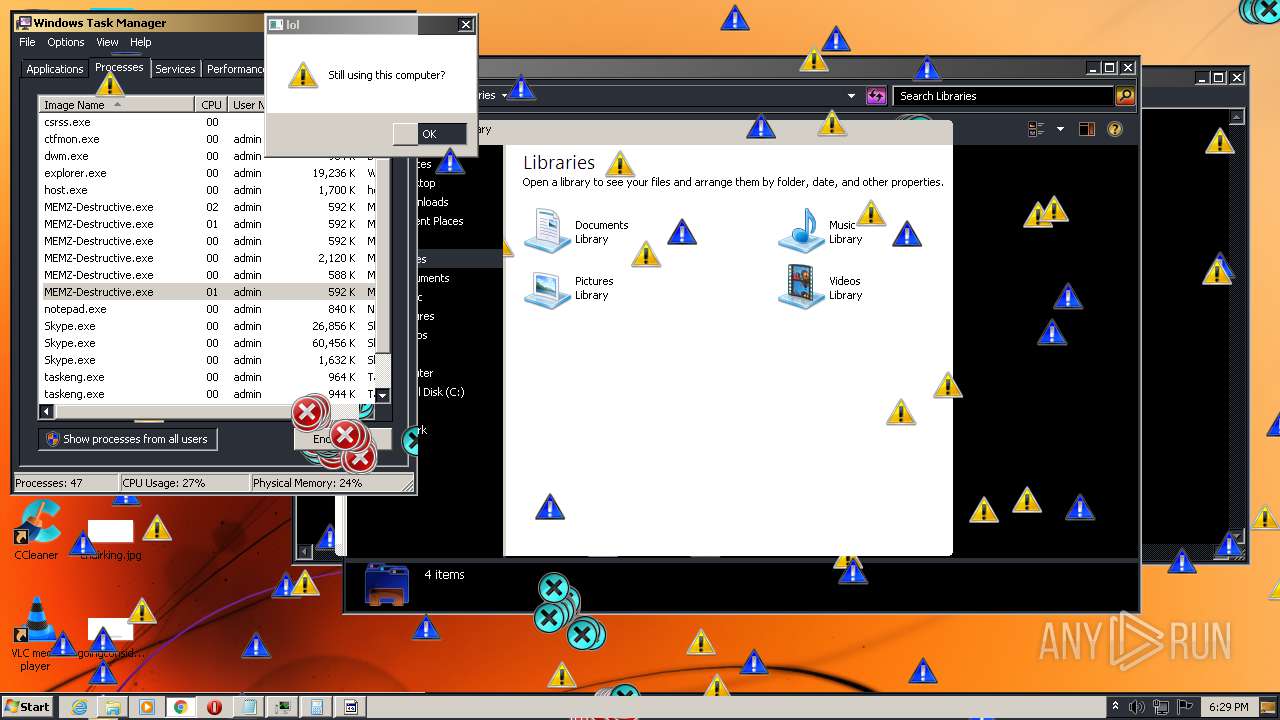
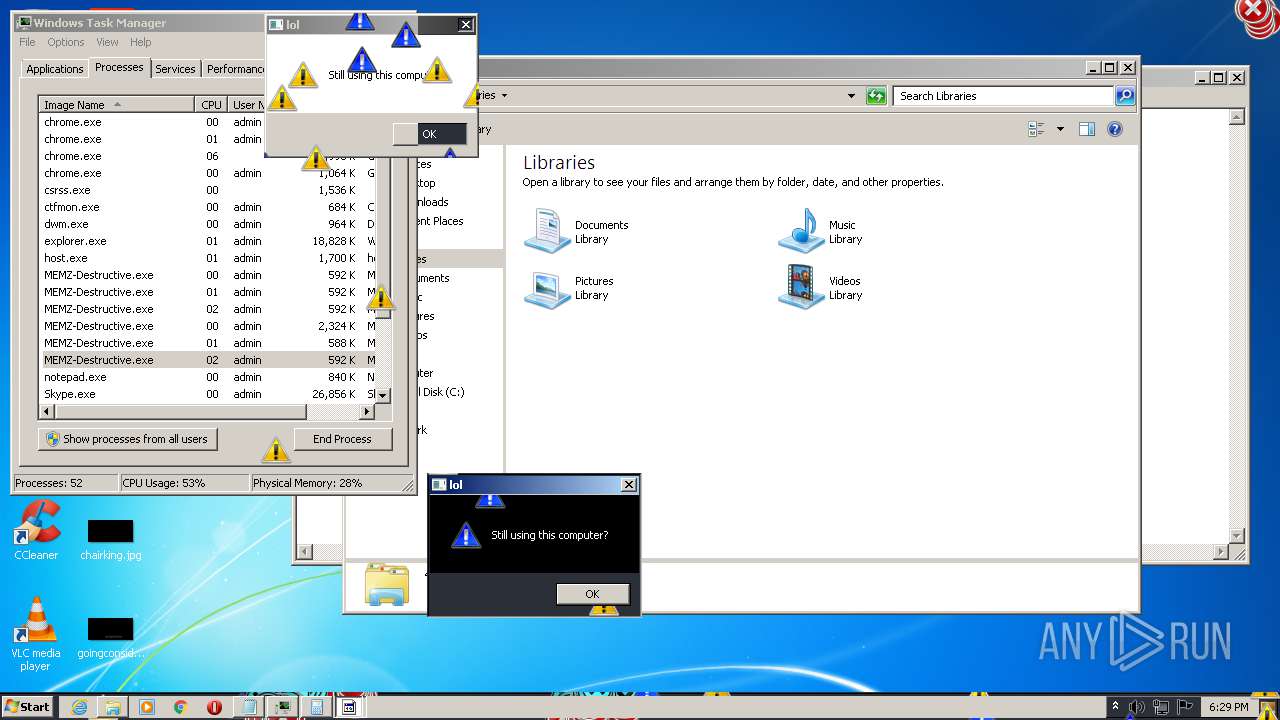
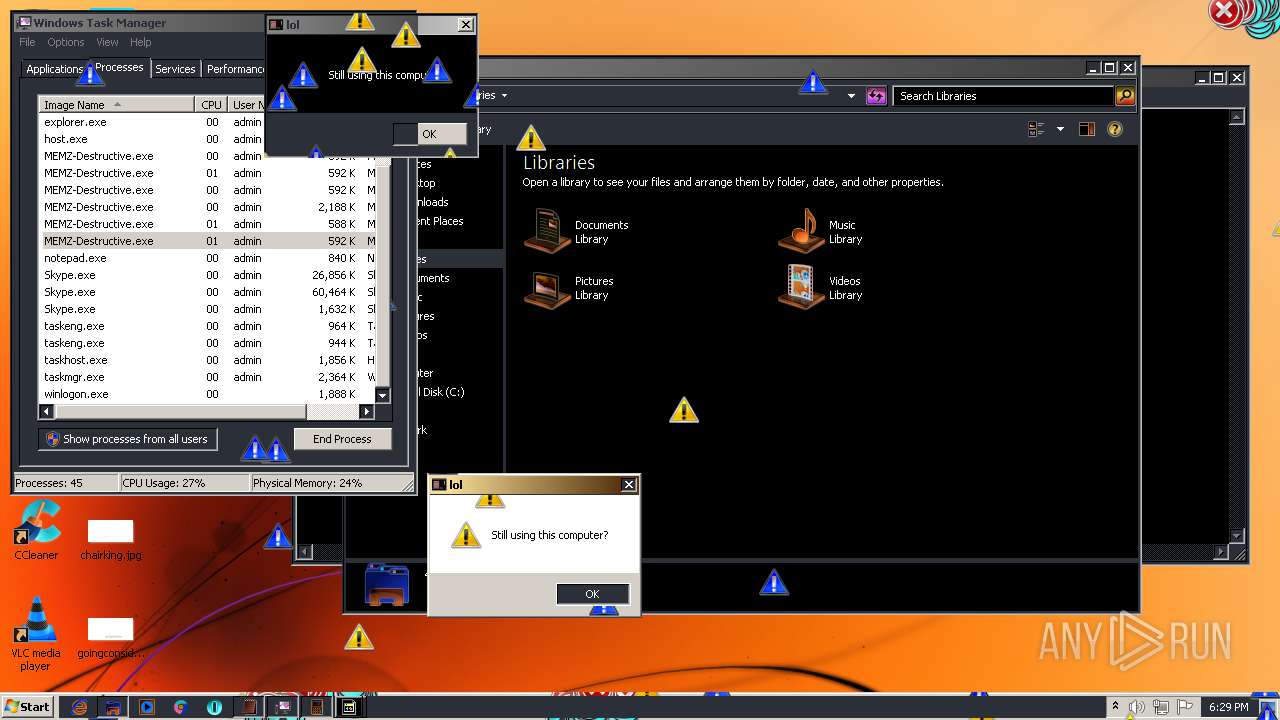
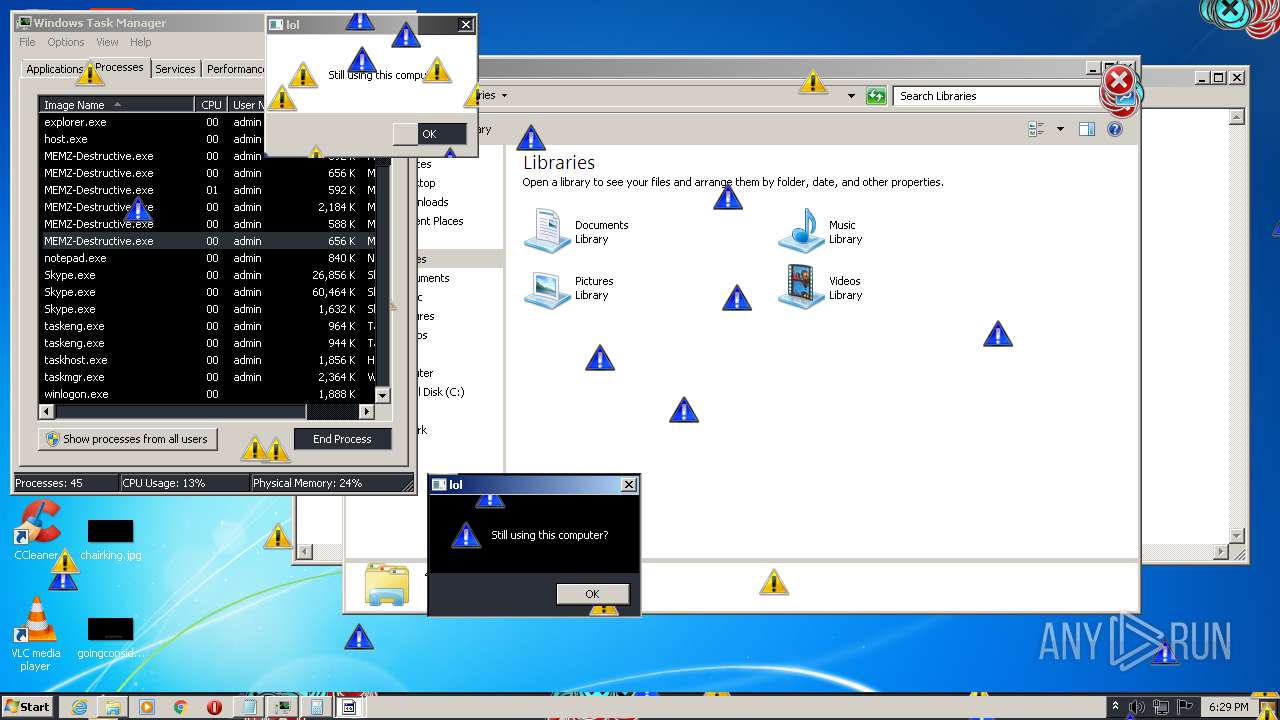
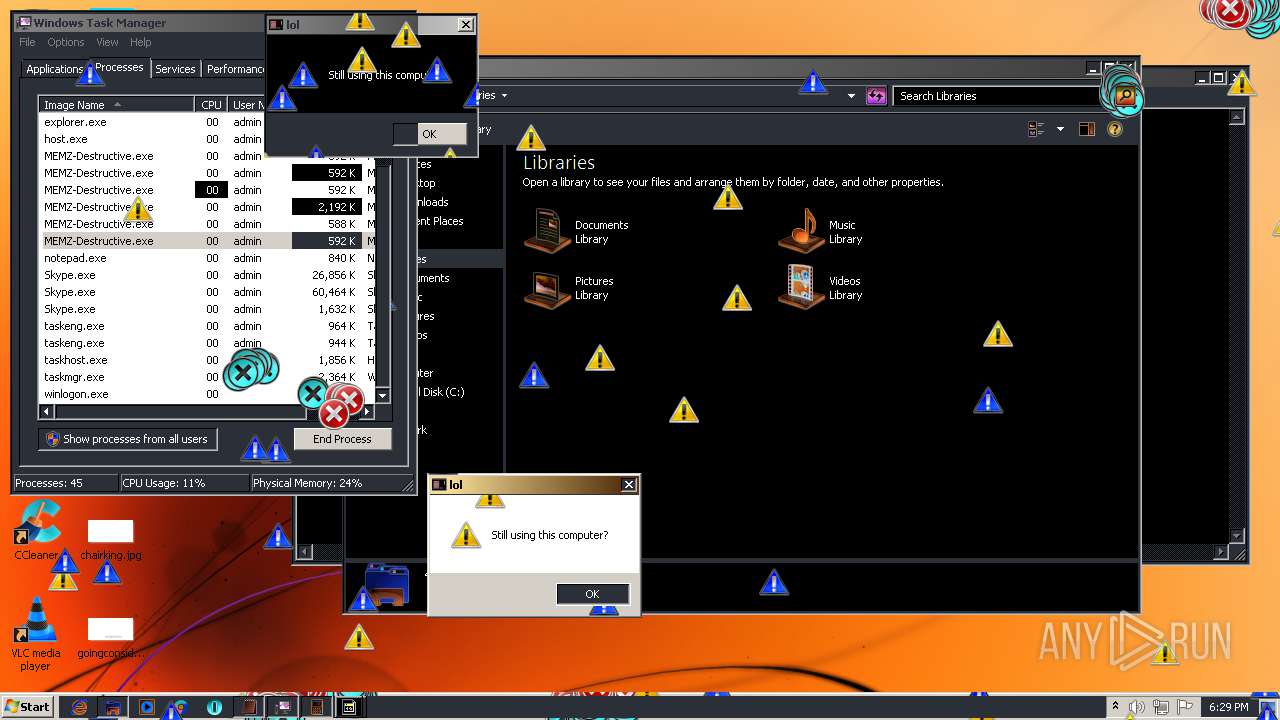
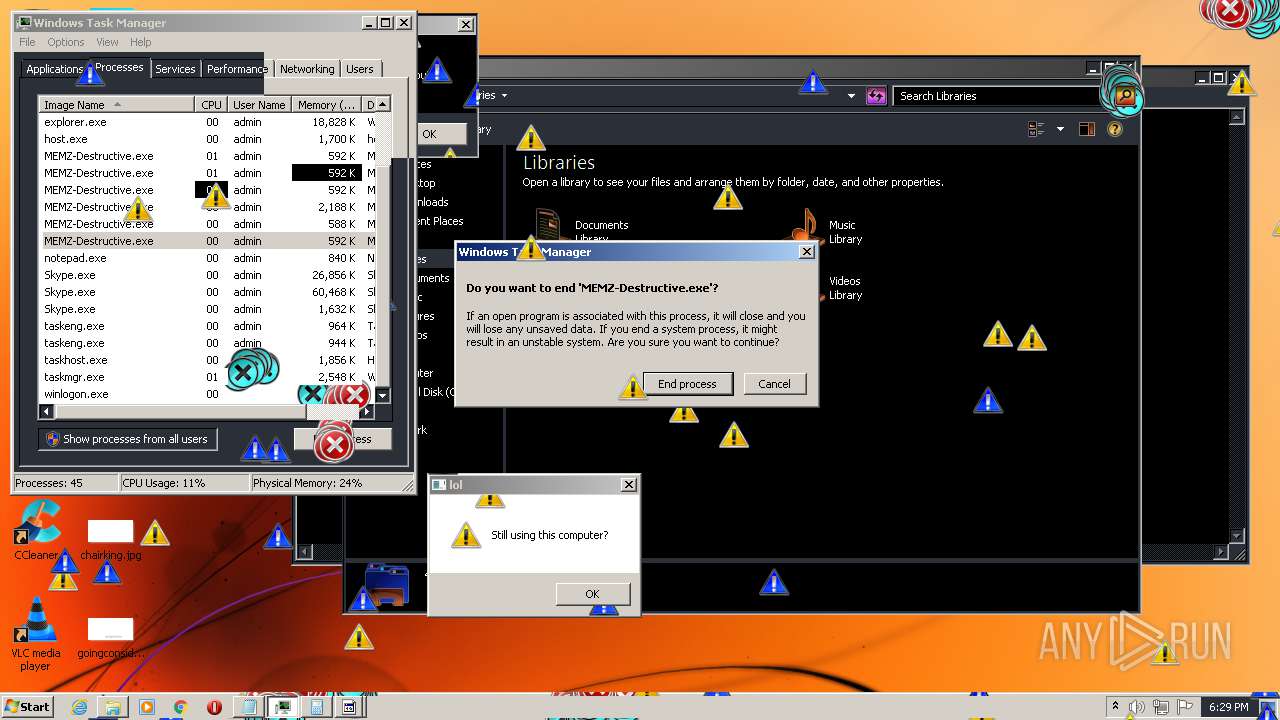
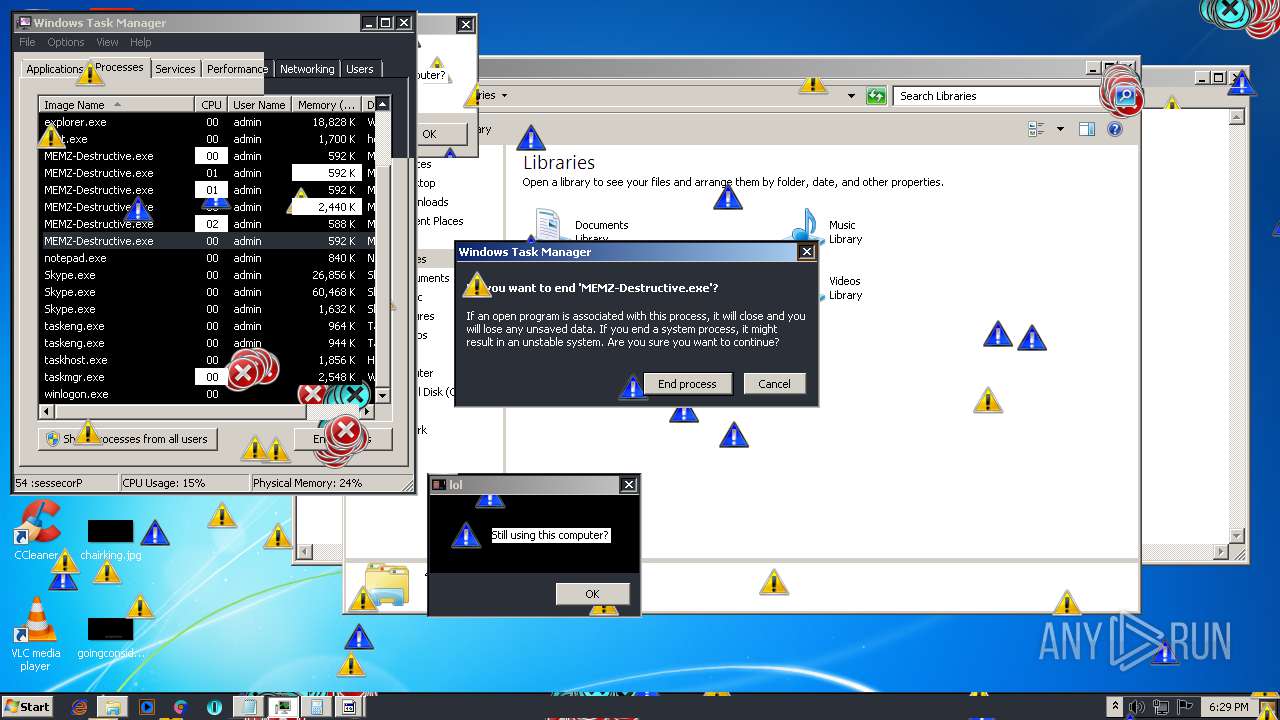
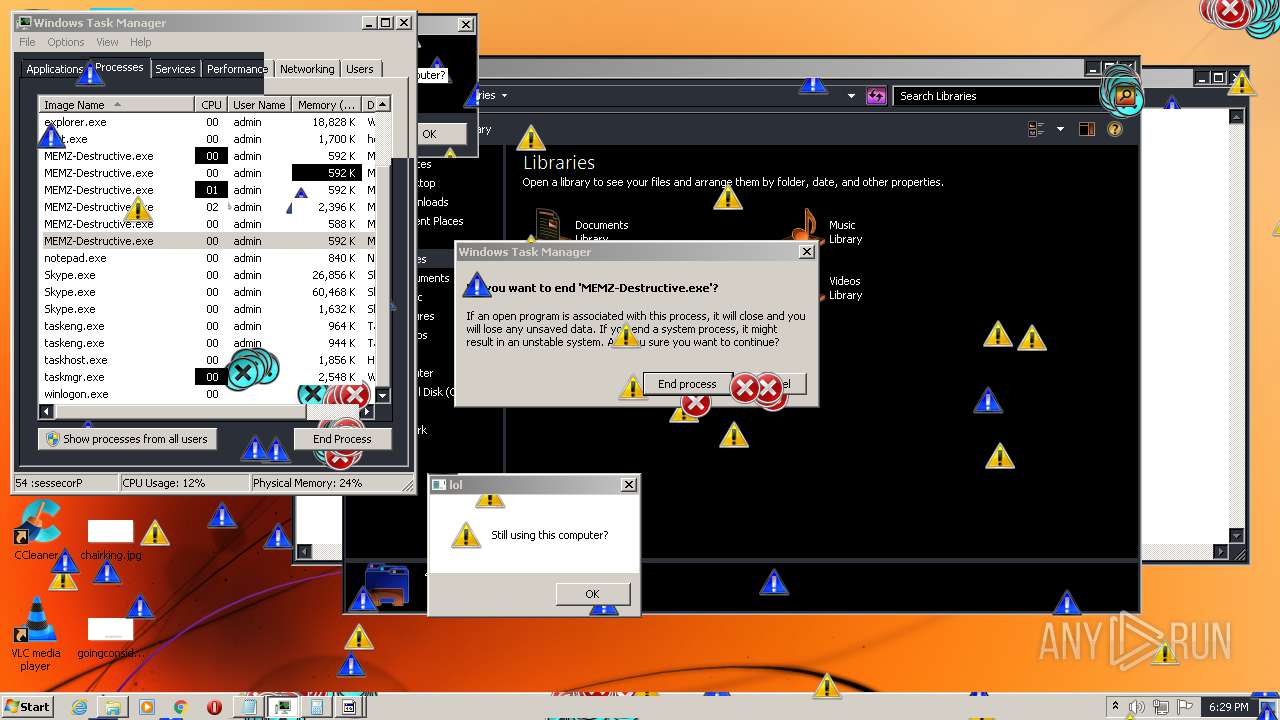
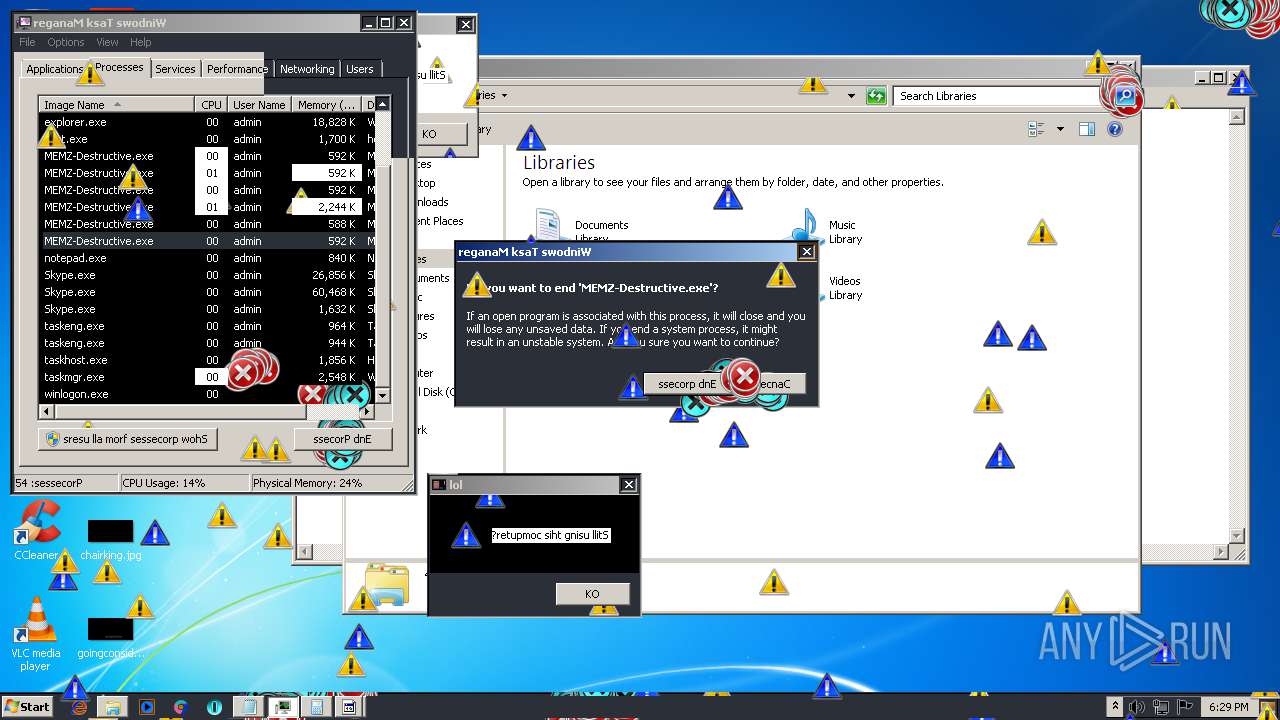
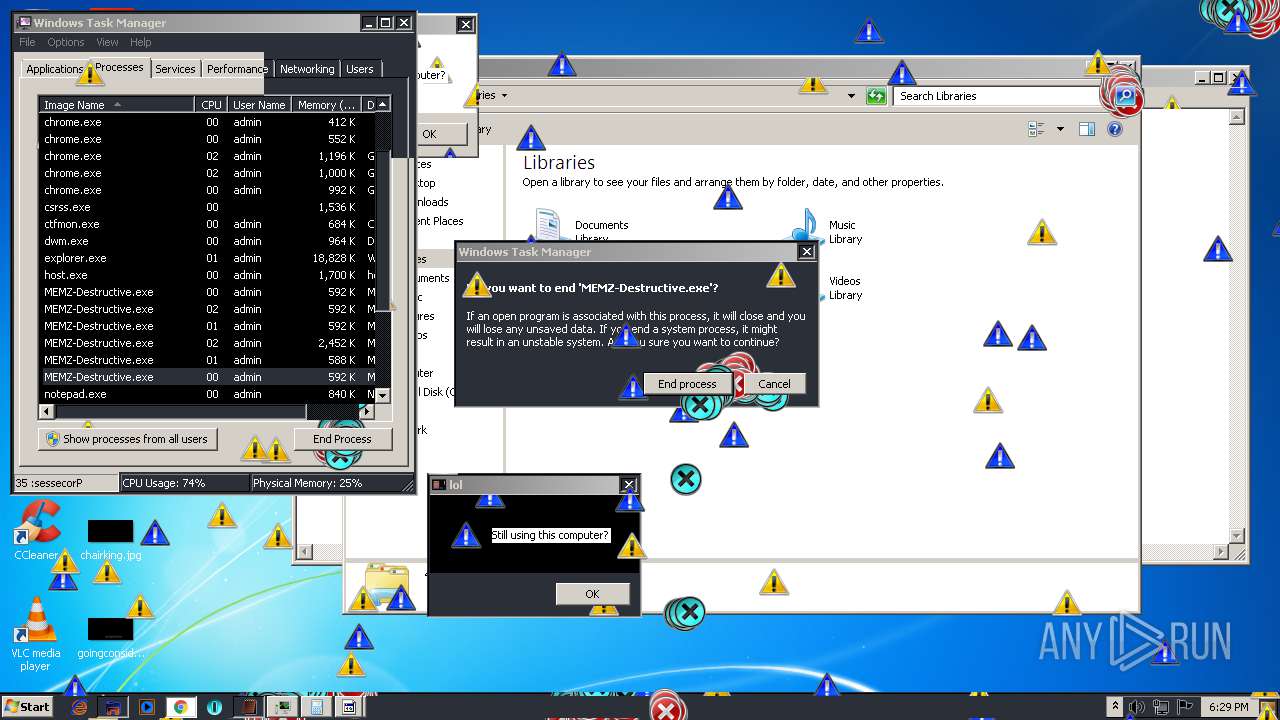
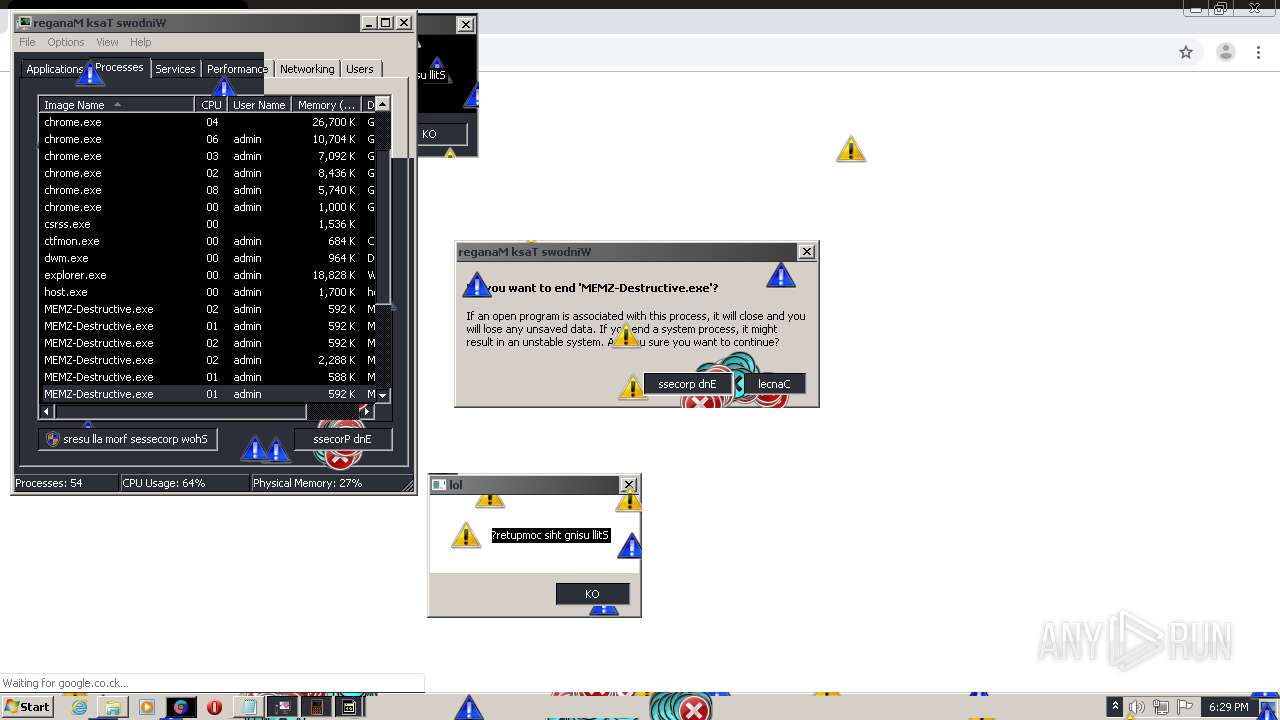
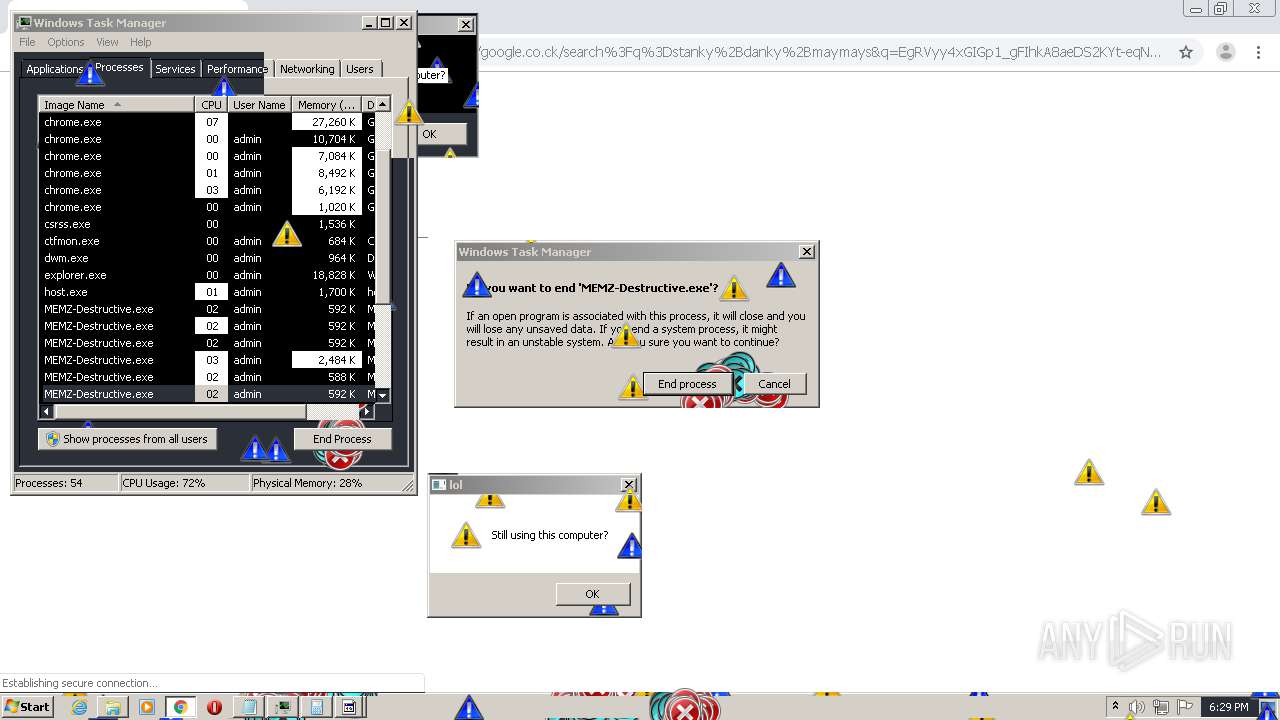
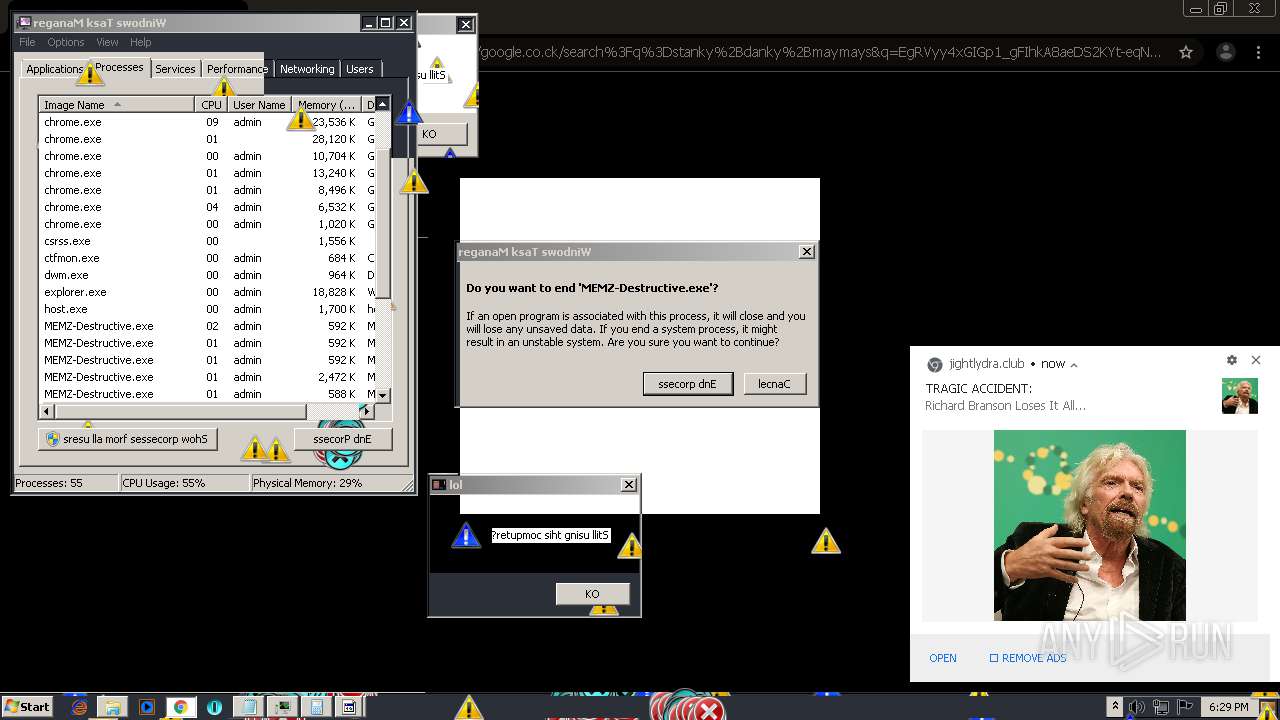
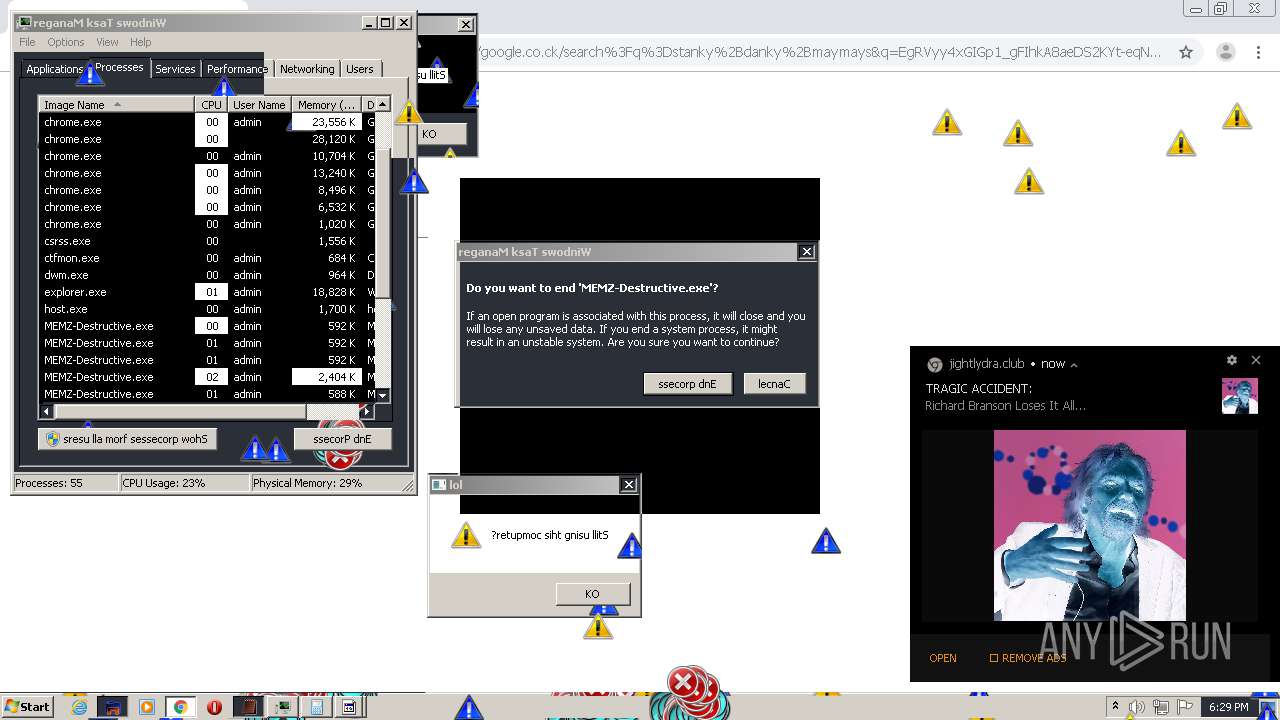
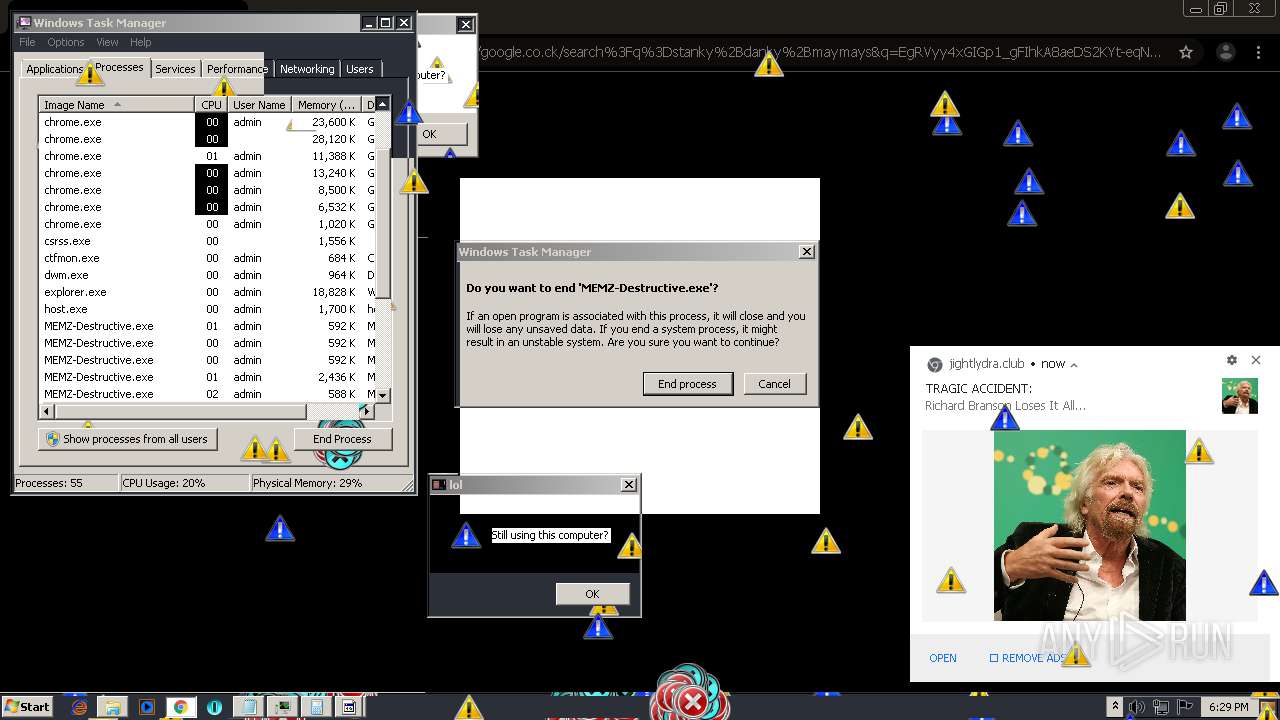
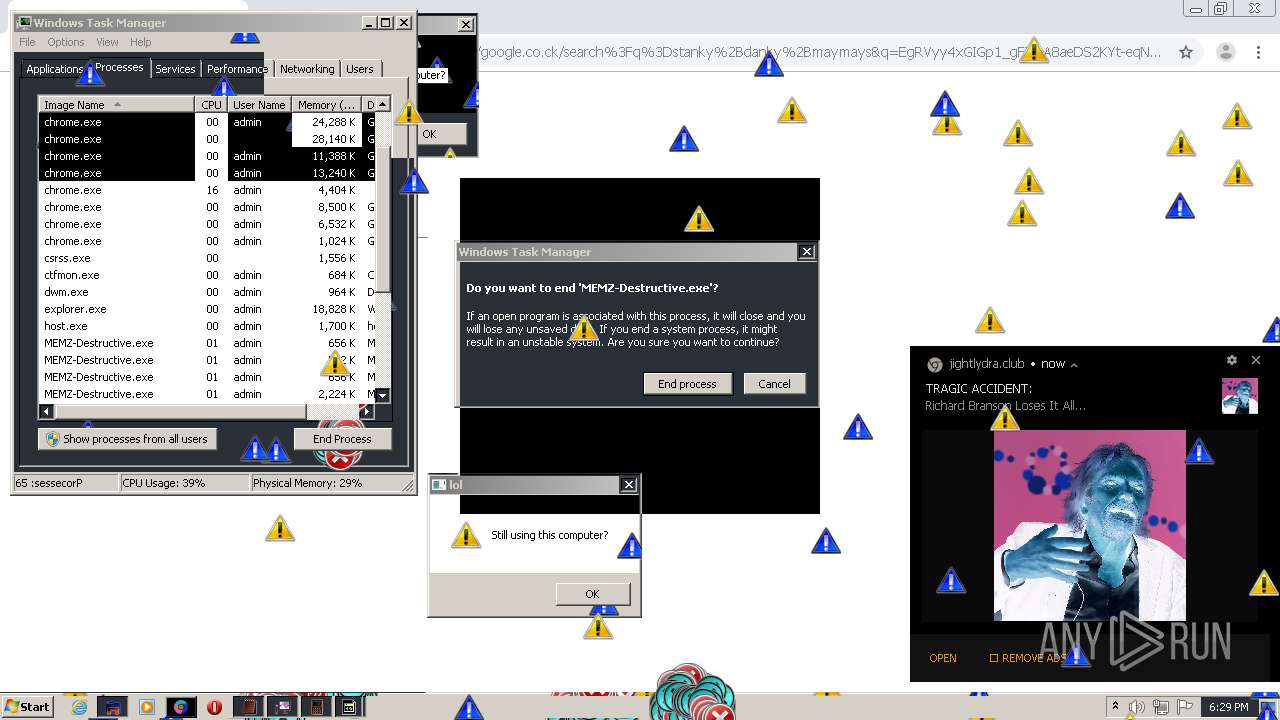
MALICIOUS
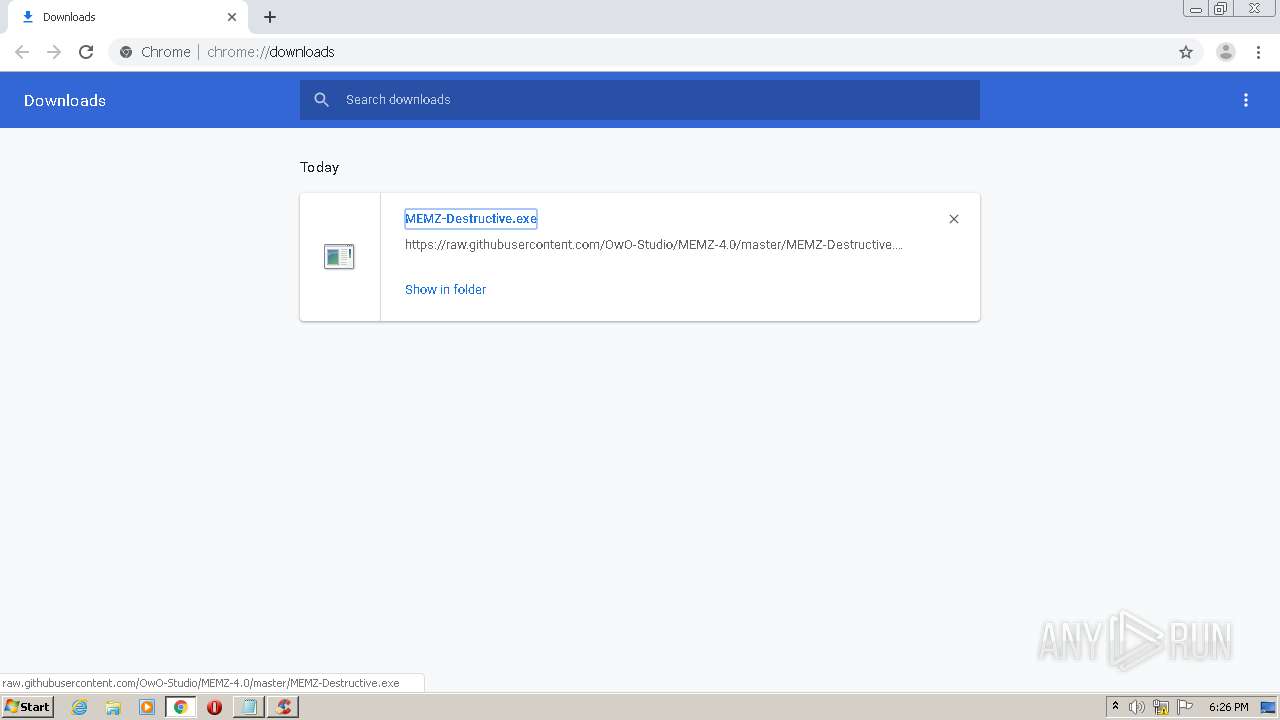
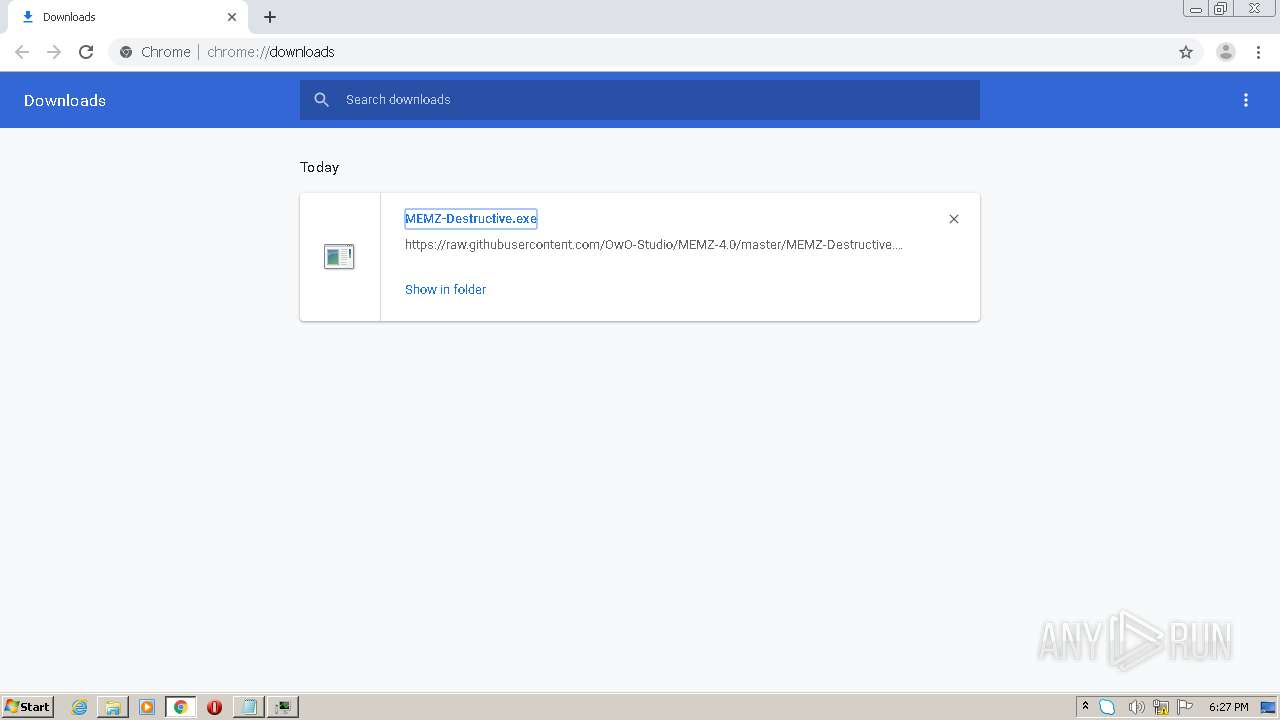
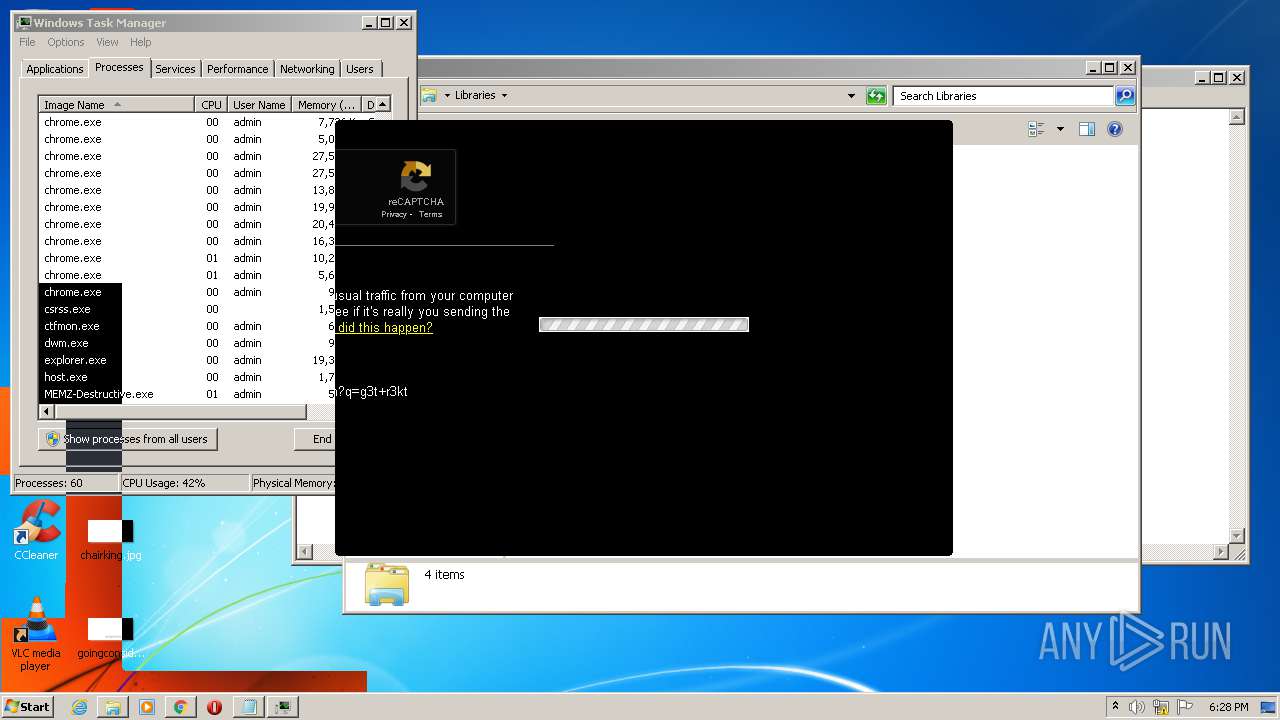
Application was dropped or rewritten from another process
- MEMZ-Destructive.exe (PID: 3224)
- MEMZ-Destructive.exe (PID: 2944)
- MEMZ-Destructive.exe (PID: 1528)
- MEMZ-Destructive.exe (PID: 568)
- MEMZ-Destructive.exe (PID: 2852)
- MEMZ-Destructive.exe (PID: 2832)
- MEMZ-Destructive.exe (PID: 3936)
- MEMZ-Destructive.exe (PID: 2144)
Low-level write access rights to disk partition
- MEMZ-Destructive.exe (PID: 2852)
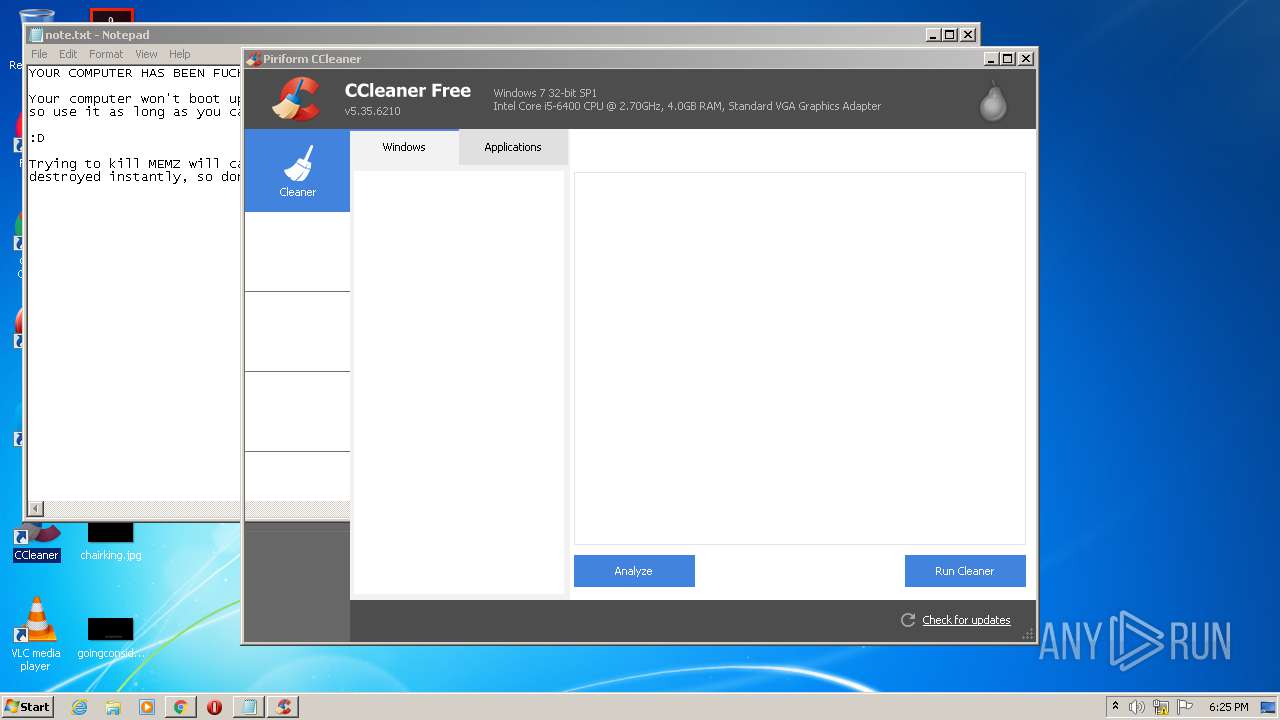
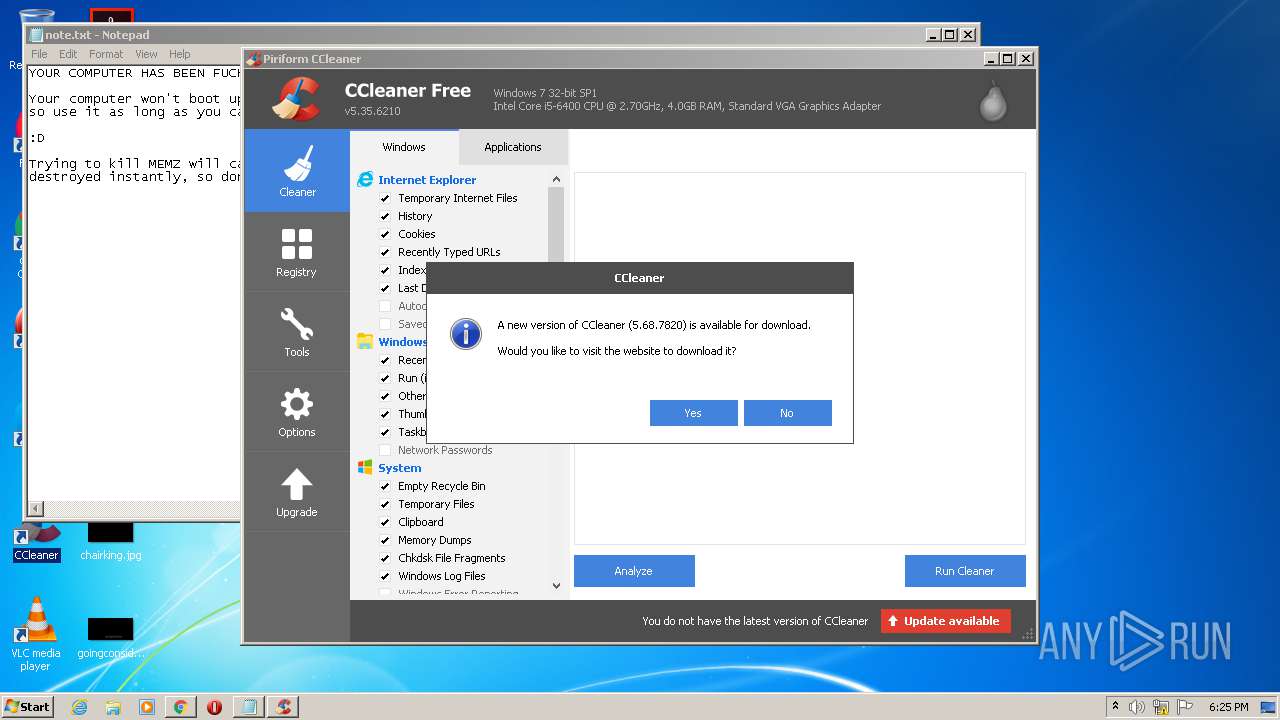
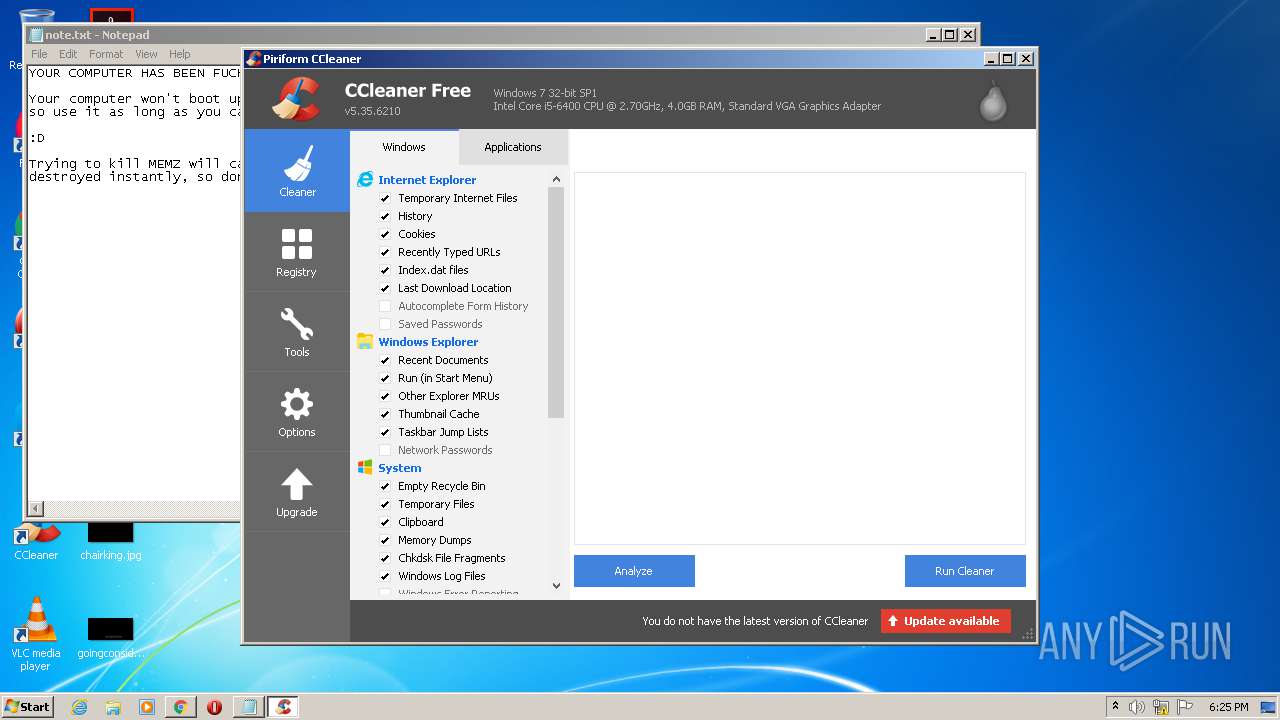
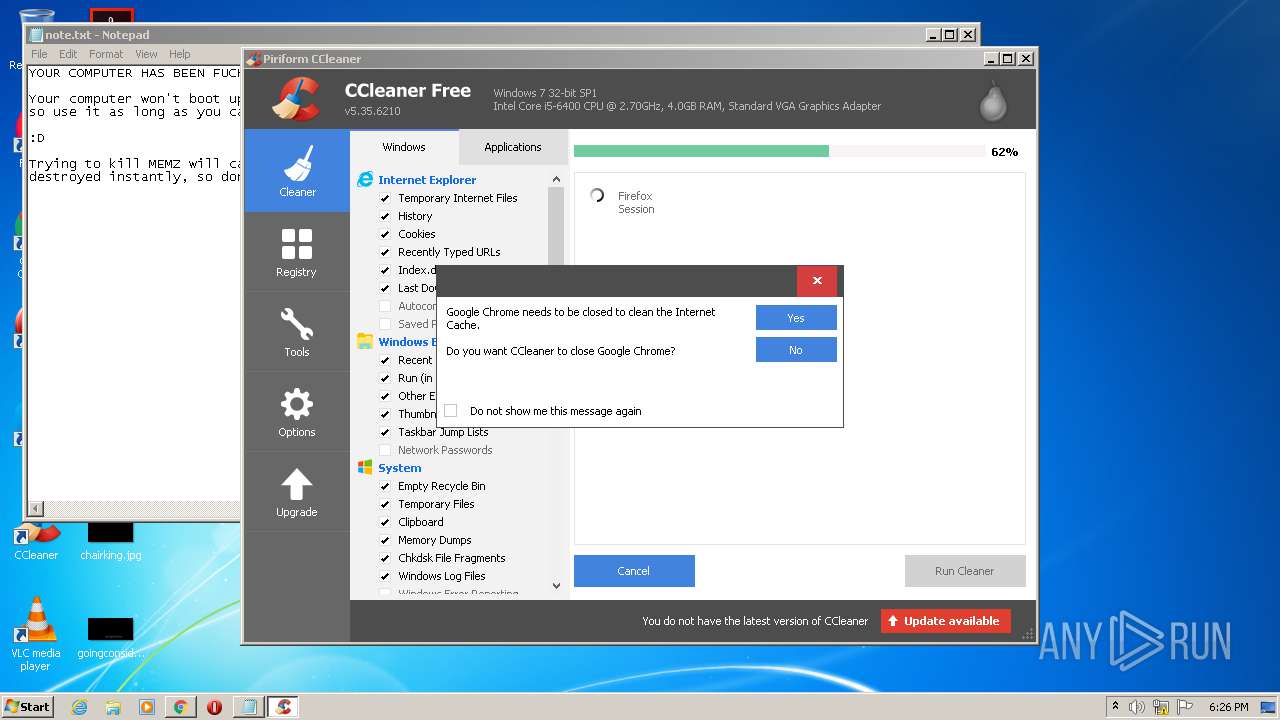
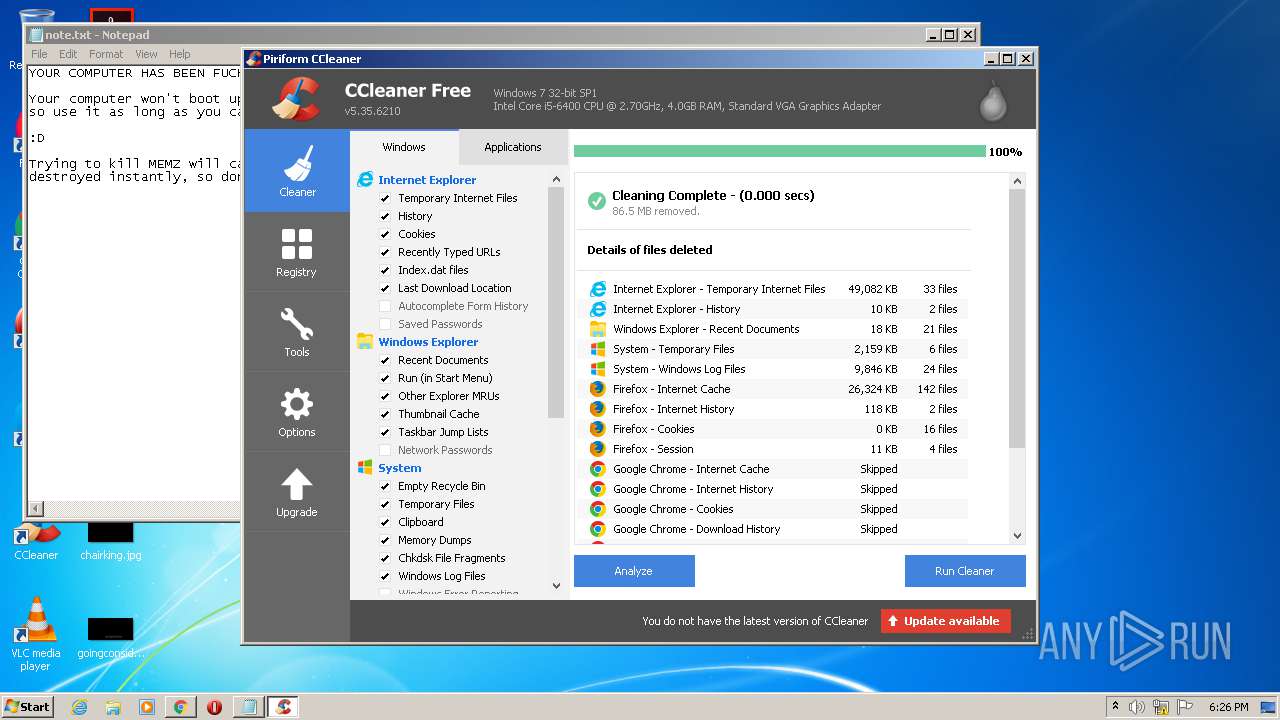
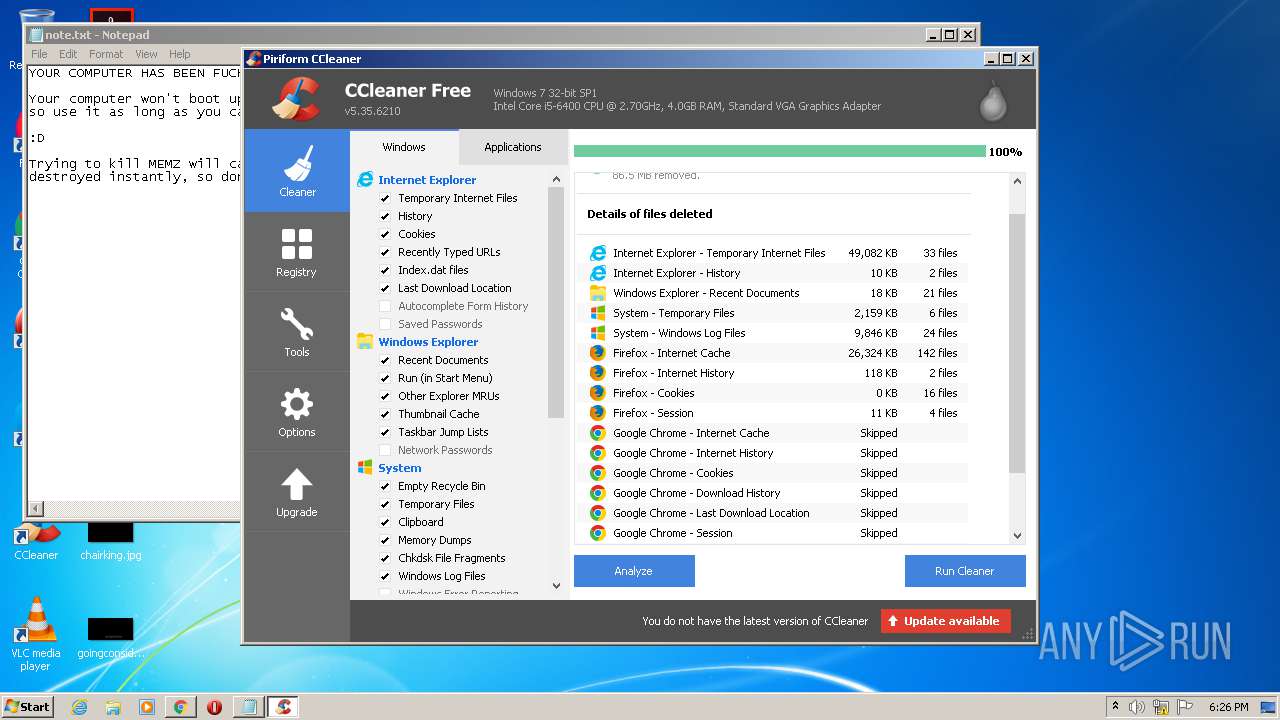
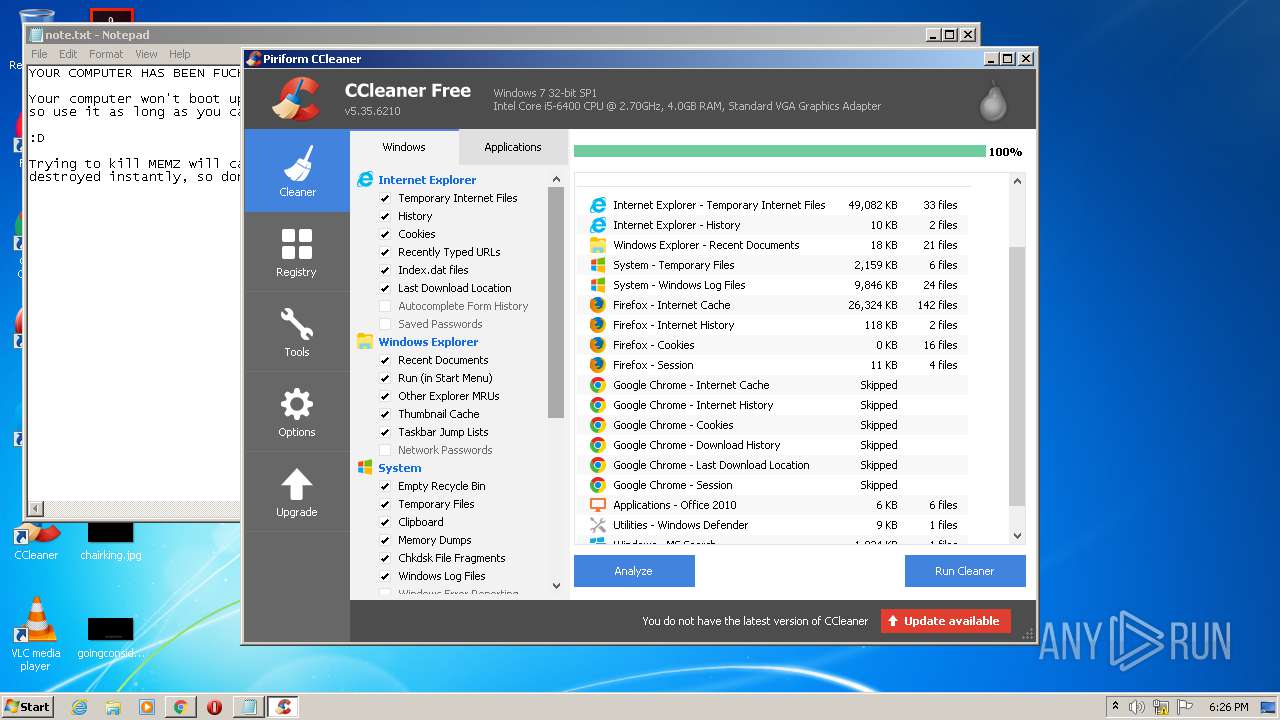
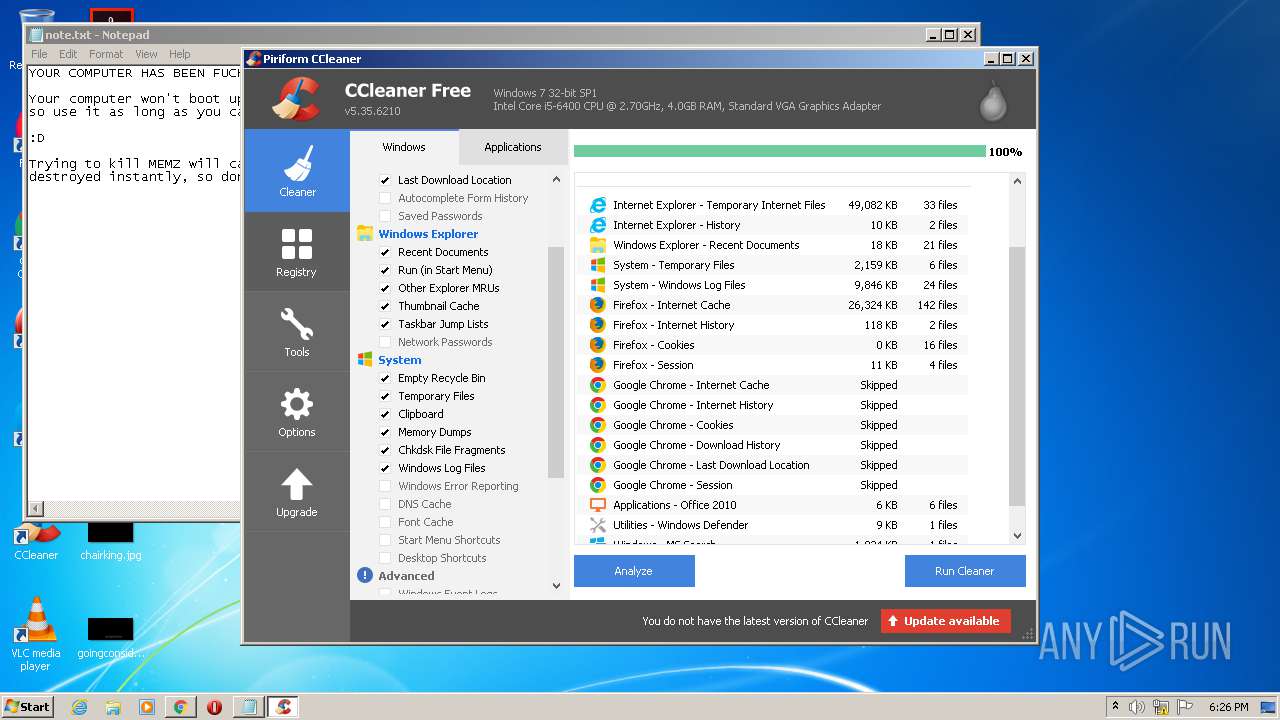
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2868)
- CCleaner.exe (PID: 2300)
Changes the autorun value in the registry
- reg.exe (PID: 3912)
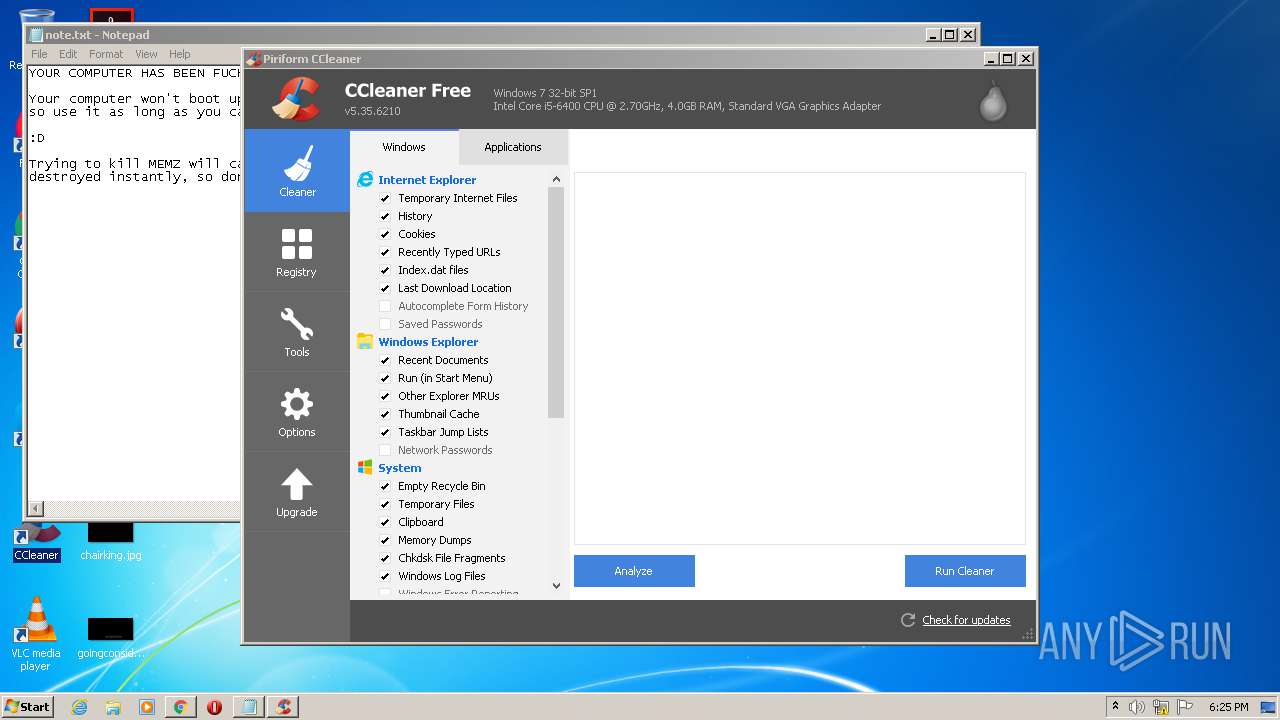
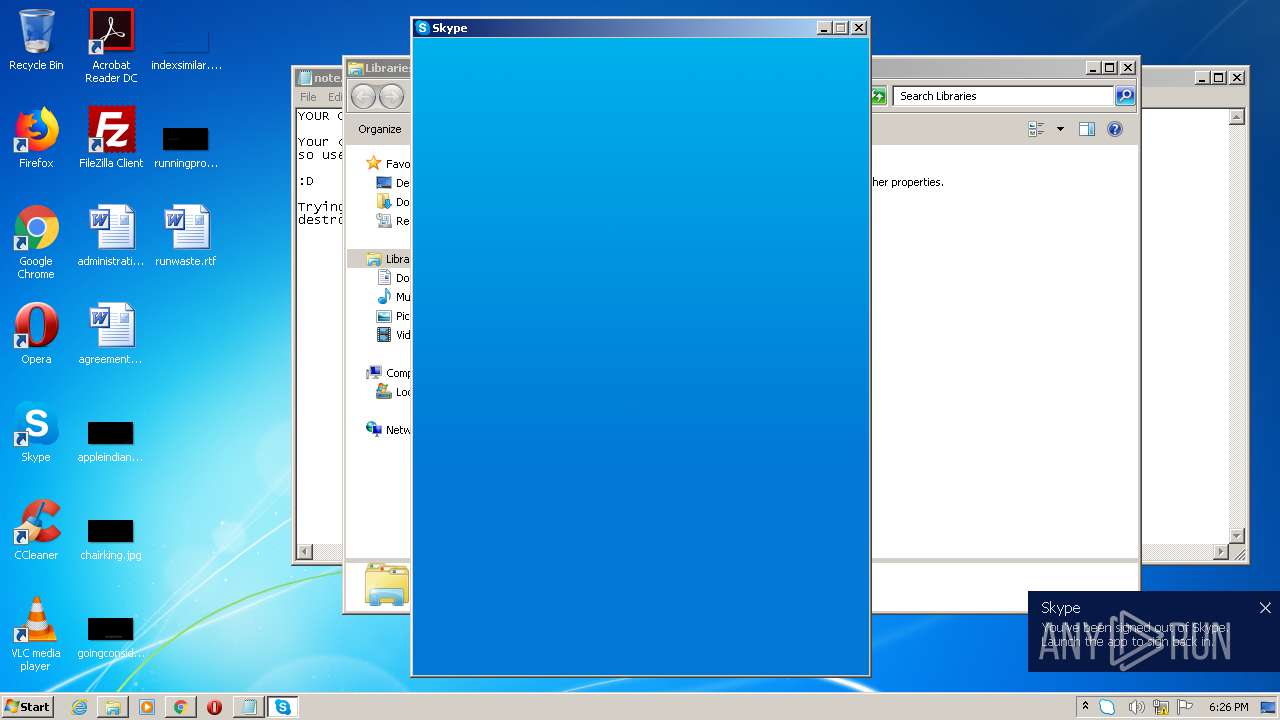
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2300)
SUSPICIOUS
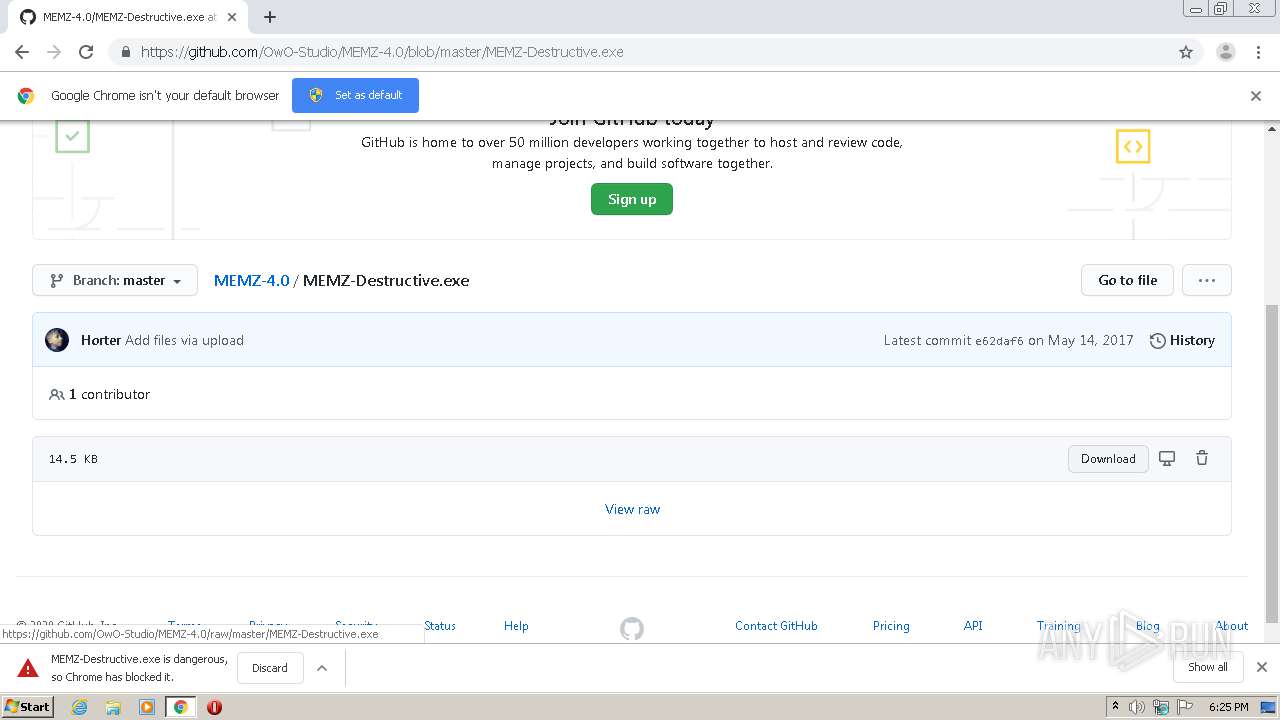
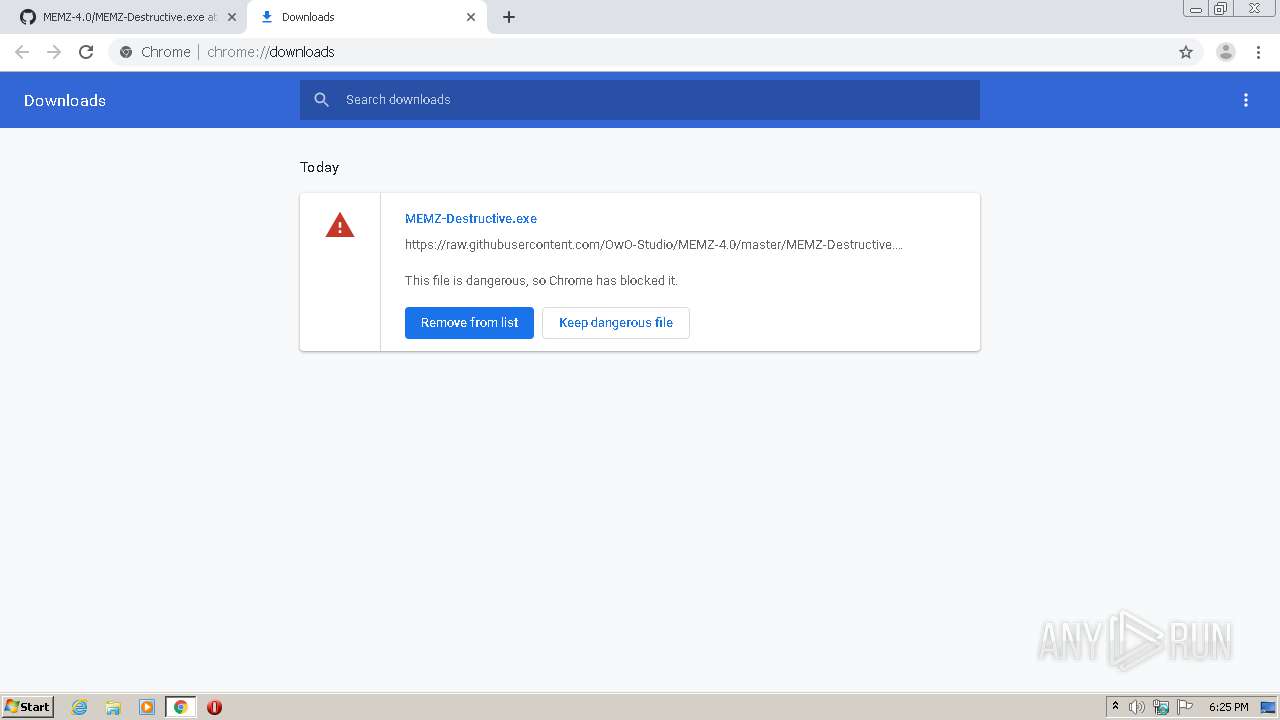
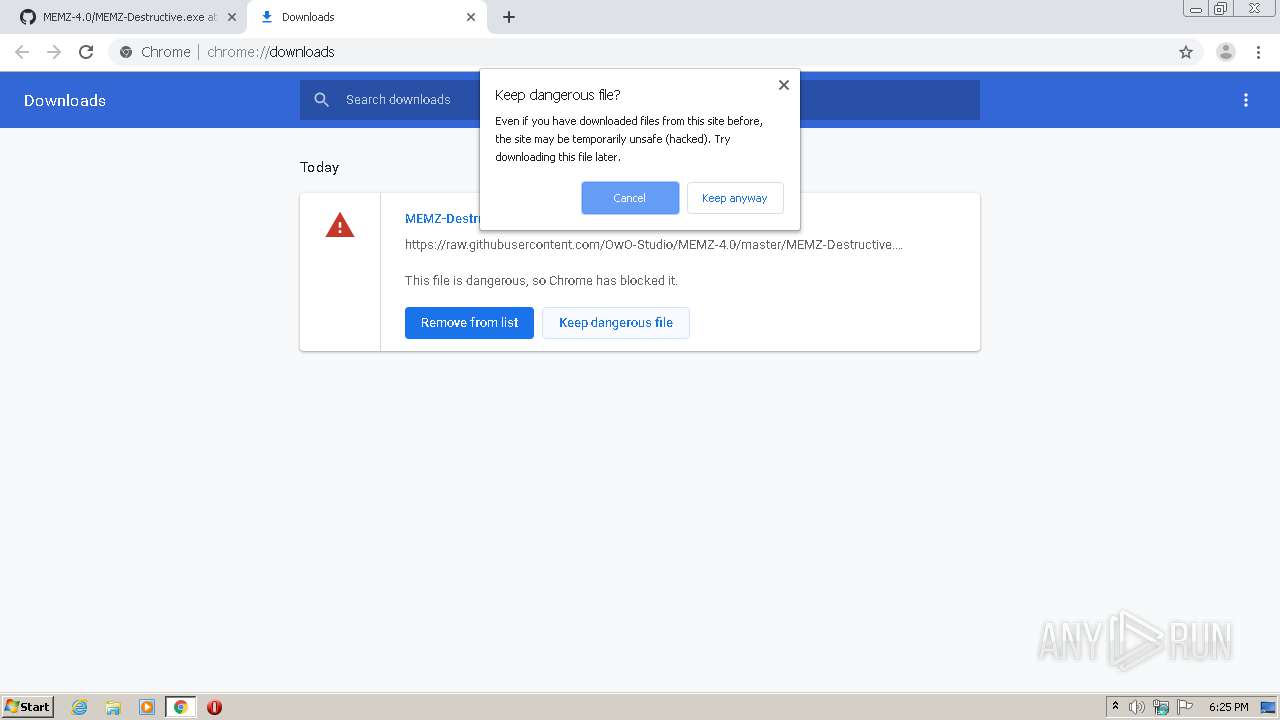
Modifies files in Chrome extension folder
- chrome.exe (PID: 1916)
Executable content was dropped or overwritten
- chrome.exe (PID: 1916)
Cleans NTFS data-stream (Zone Identifier)
- MEMZ-Destructive.exe (PID: 3224)
Application launched itself
- MEMZ-Destructive.exe (PID: 3224)
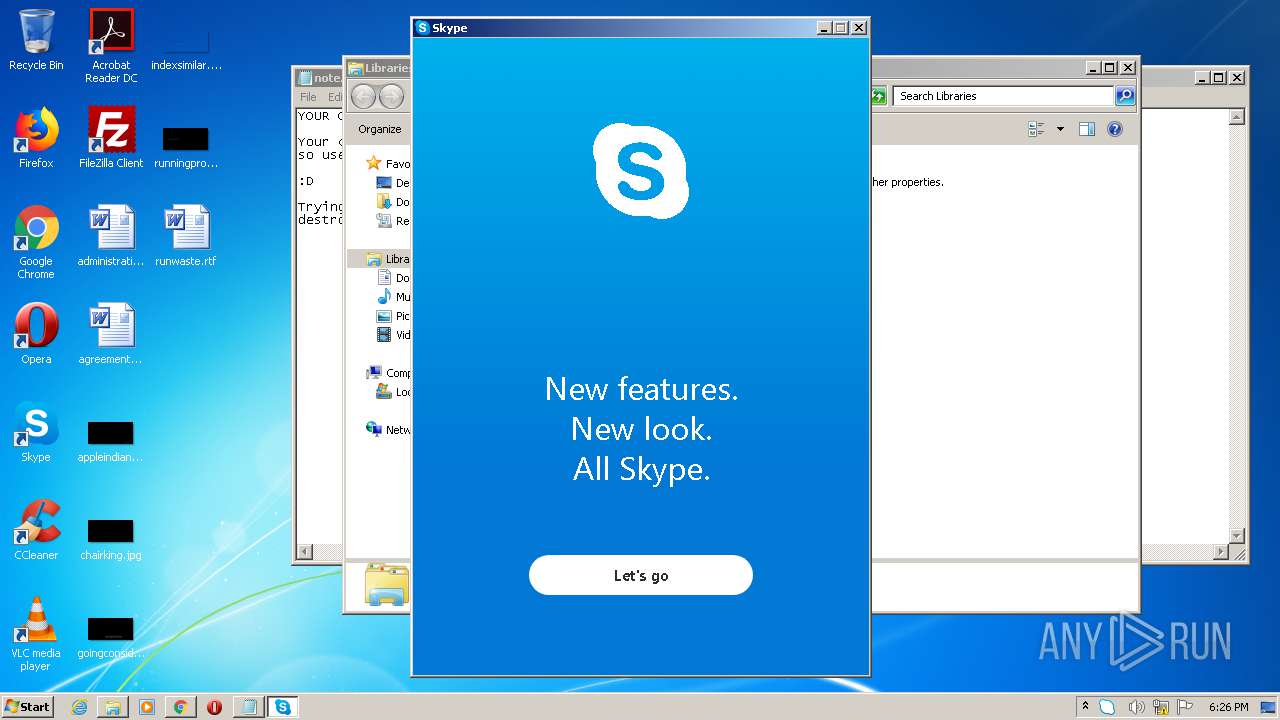
- Skype.exe (PID: 1032)
- Skype.exe (PID: 2456)
- Skype.exe (PID: 2584)
- Skype.exe (PID: 1828)
Low-level read access rights to disk partition
- MEMZ-Destructive.exe (PID: 2852)
- CCleaner.exe (PID: 2300)
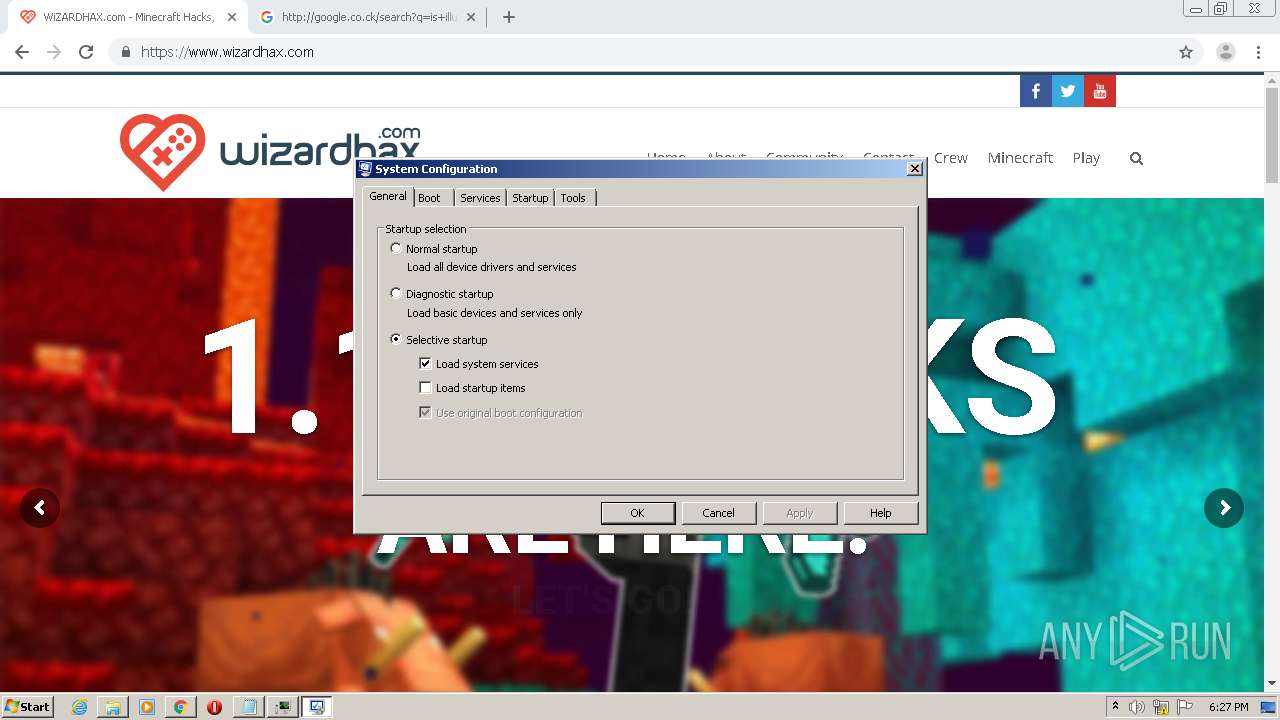
- msconfig.exe (PID: 2684)
Executed via Task Scheduler
- CCleaner.exe (PID: 2300)
Reads internet explorer settings
- CCleaner.exe (PID: 2300)
Creates files in the user directory
- CCleaner.exe (PID: 2300)
- Skype.exe (PID: 2456)
- Skype.exe (PID: 1032)
- Skype.exe (PID: 2584)
Reads Internet Cache Settings
- CCleaner.exe (PID: 2300)
- taskhost.exe (PID: 2560)
- taskhost.exe (PID: 1928)
Executed as Windows Service
- taskhost.exe (PID: 1928)
- taskhost.exe (PID: 2560)
- taskhost.exe (PID: 3900)
Removes files from Windows directory
- CCleaner.exe (PID: 2300)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 1032)
Reads CPU info
- Skype.exe (PID: 1032)
- Skype.exe (PID: 1828)
Modifies the open verb of a shell class
- Skype.exe (PID: 1032)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2300)
INFO
Reads the hosts file
- chrome.exe (PID: 184)
- chrome.exe (PID: 1916)
- Skype.exe (PID: 1032)
- Skype.exe (PID: 1828)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3976)
Reads settings of System Certificates
- chrome.exe (PID: 184)
- CCleaner.exe (PID: 2300)
- Skype.exe (PID: 1032)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3976)
Application launched itself
- chrome.exe (PID: 1916)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2664)
Reads Internet Cache Settings
- chrome.exe (PID: 1916)
Modifies the open verb of a shell class
- chrome.exe (PID: 1916)
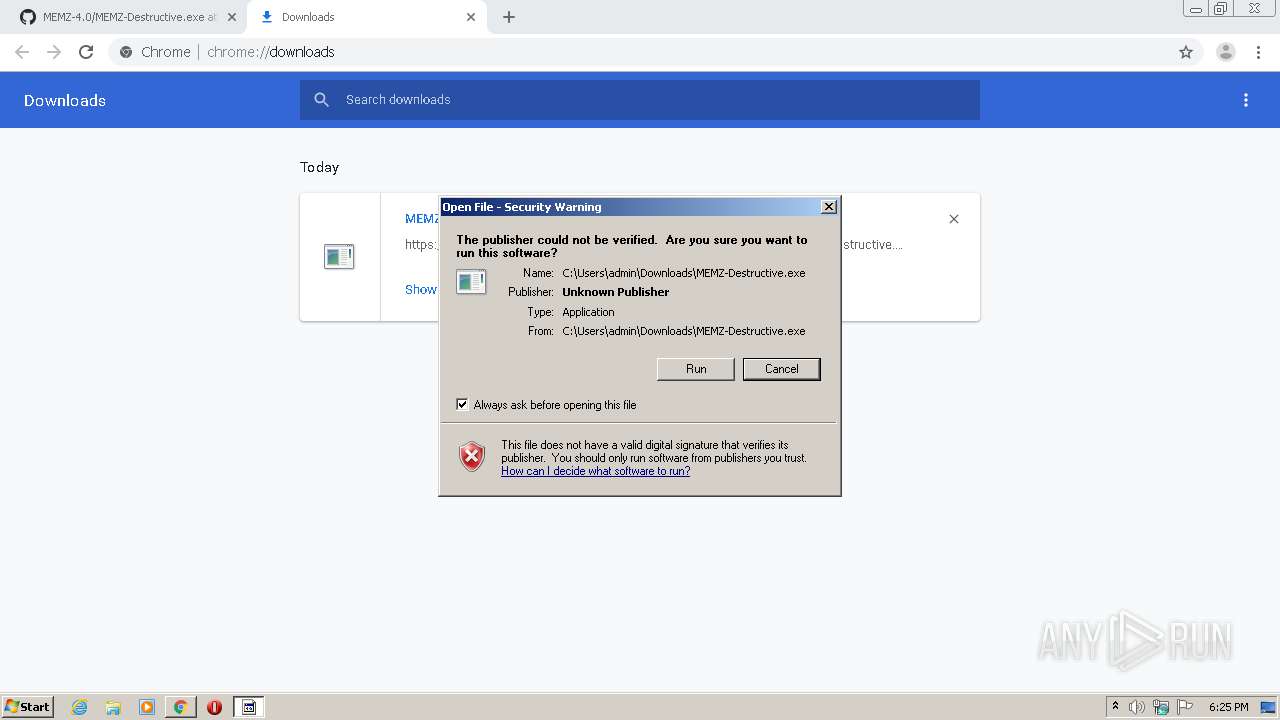
Manual execution by user
- CCleaner.exe (PID: 2868)
- Skype.exe (PID: 1032)
- Skype.exe (PID: 1828)
- taskmgr.exe (PID: 1148)
Creates files in the user directory
- chrome.exe (PID: 1916)
Dropped object may contain Bitcoin addresses
- Skype.exe (PID: 1032)
- chrome.exe (PID: 184)
- chrome.exe (PID: 1916)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2096)
Dropped object may contain TOR URL's
- chrome.exe (PID: 1916)
Adds / modifies Windows certificates
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3976)
Changes settings of System certificates
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3976)
Reads Microsoft Office registry keys
- CCleaner.exe (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
178
Monitored processes
133
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,13056010891811041691,11128551961201961311,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18054525783533077653 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,13056010891811041691,11128551961201961311,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11430540108130232029 --mojo-platform-channel-handle=1652 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,17063974207760591581,9289888920229165960,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2502221875243196795 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1724 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,13056010891811041691,11128551961201961311,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7442670026659832696 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Users\admin\Downloads\MEMZ-Destructive.exe" /watchdog | C:\Users\admin\Downloads\MEMZ-Destructive.exe | — | MEMZ-Destructive.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,13056010891811041691,11128551961201961311,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16585013714125902763 --mojo-platform-channel-handle=4236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,13056010891811041691,11128551961201961311,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5842196333293845048 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e5ca9d0,0x6e5ca9e0,0x6e5ca9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
Total events
4 335
Read events
3 654
Write events
594
Delete events
87
Modification events
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1916-13239739486114625 |
Value: 259 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1916-13239739486114625 |
Value: 259 | |||
Executable files
3
Suspicious files
394
Text files
553
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F15D35E-77C.pma | — | |
MD5:— | SHA256:— | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\744ce80d-2a9c-4345-8c9e-a4ed19bd17b5.tmp | — | |
MD5:— | SHA256:— | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1109b1.TMP | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:A9C81BA506E2A0D898698EAF075EBE5C | SHA256:92FB2125FB5A0B877B76C4E3409B250EFF394804C7F24E236FBE162E1054AF90 | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF110b86.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
167
DNS requests
135
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
184 | chrome.exe | GET | 200 | 173.194.129.201:80 | http://r4---sn-aigzrn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.46.49&mm=28&mn=sn-aigzrn7s&ms=nvh&mt=1595265800&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
184 | chrome.exe | GET | 200 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=8p&mip=85.203.46.49&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1595265800&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 824 Kb | whitelisted |
2300 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
184 | chrome.exe | GET | 301 | 40.114.177.156:80 | http://duckduckgo.com/ | NL | html | 162 b | whitelisted |
2300 | CCleaner.exe | GET | 200 | 151.101.2.109:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.35.6210&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | text | 17 b | whitelisted |
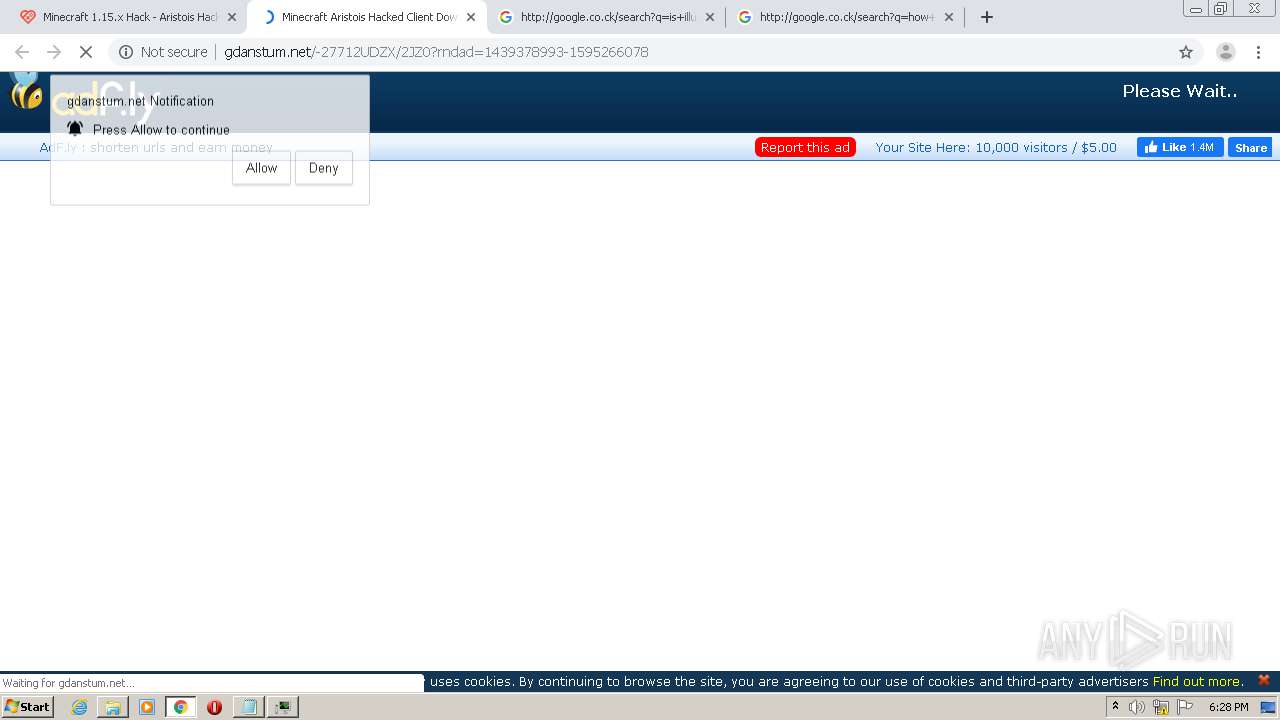
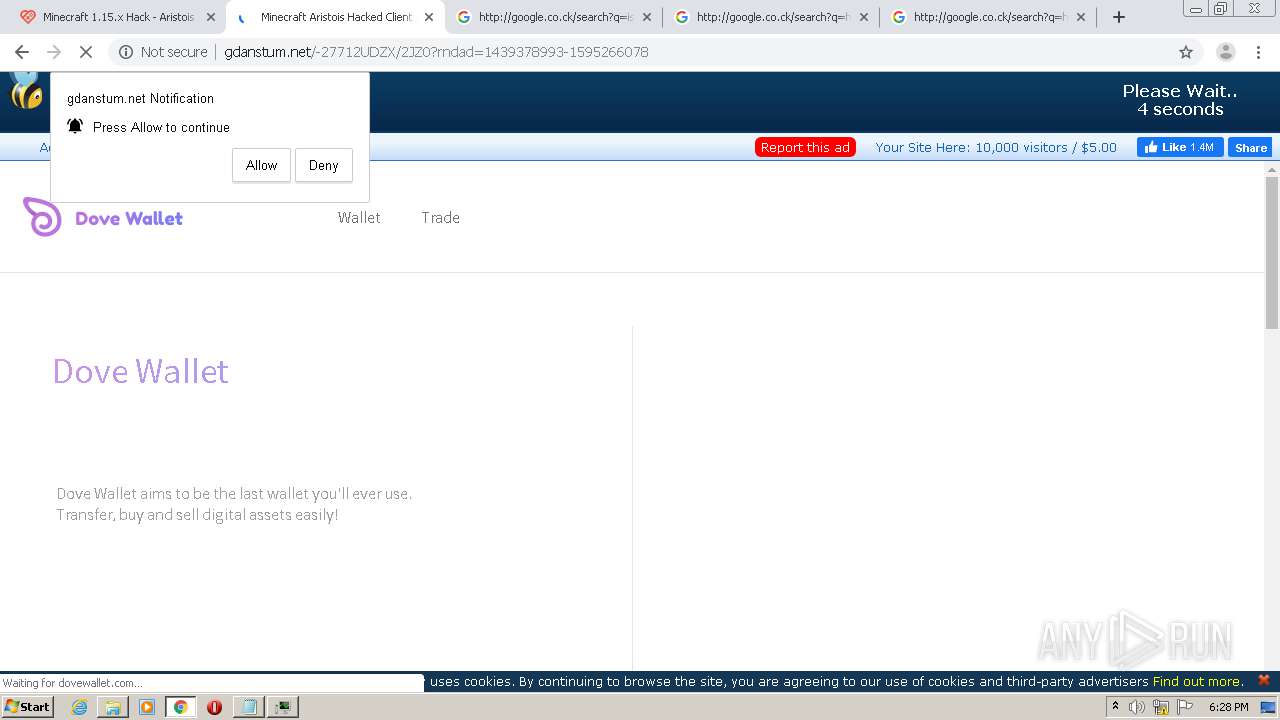
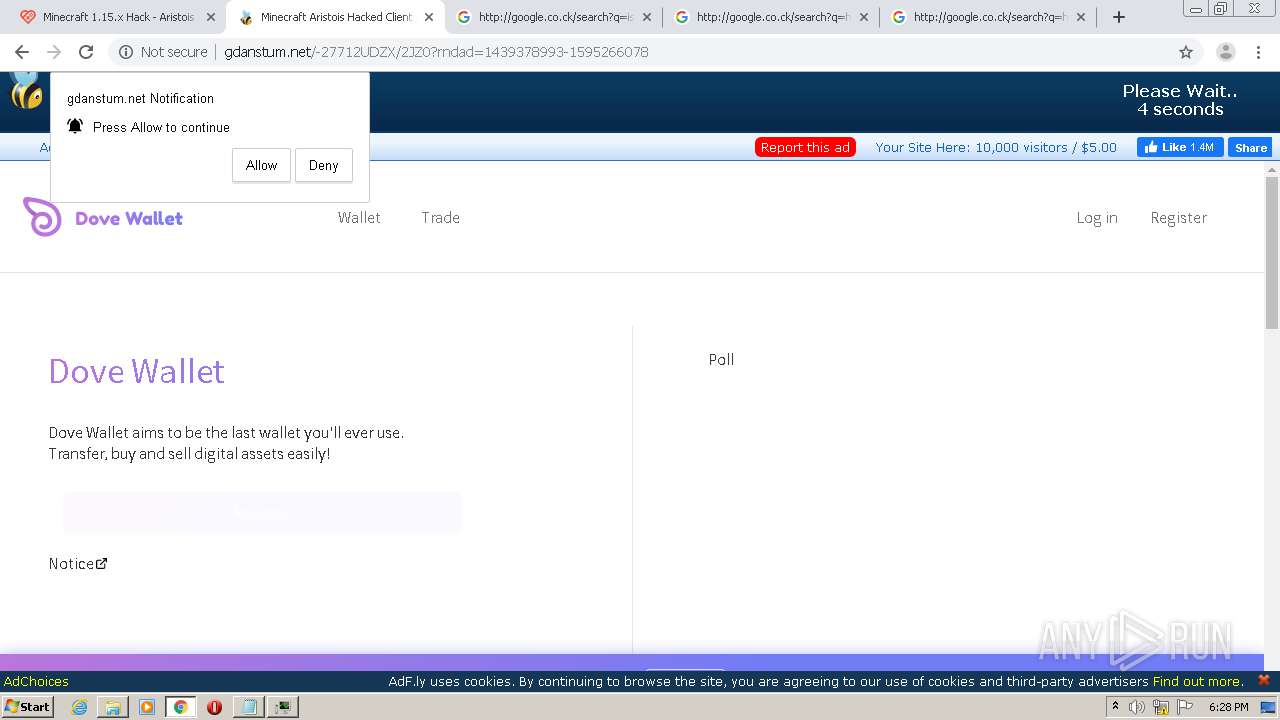
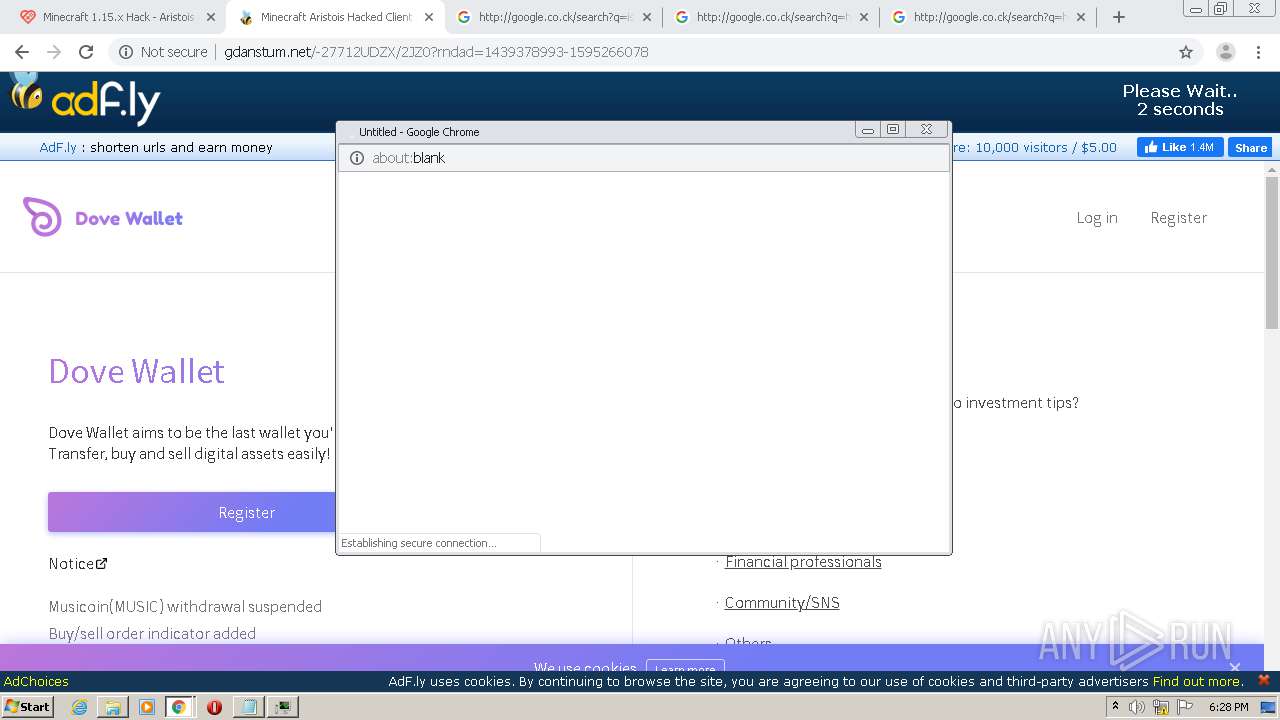
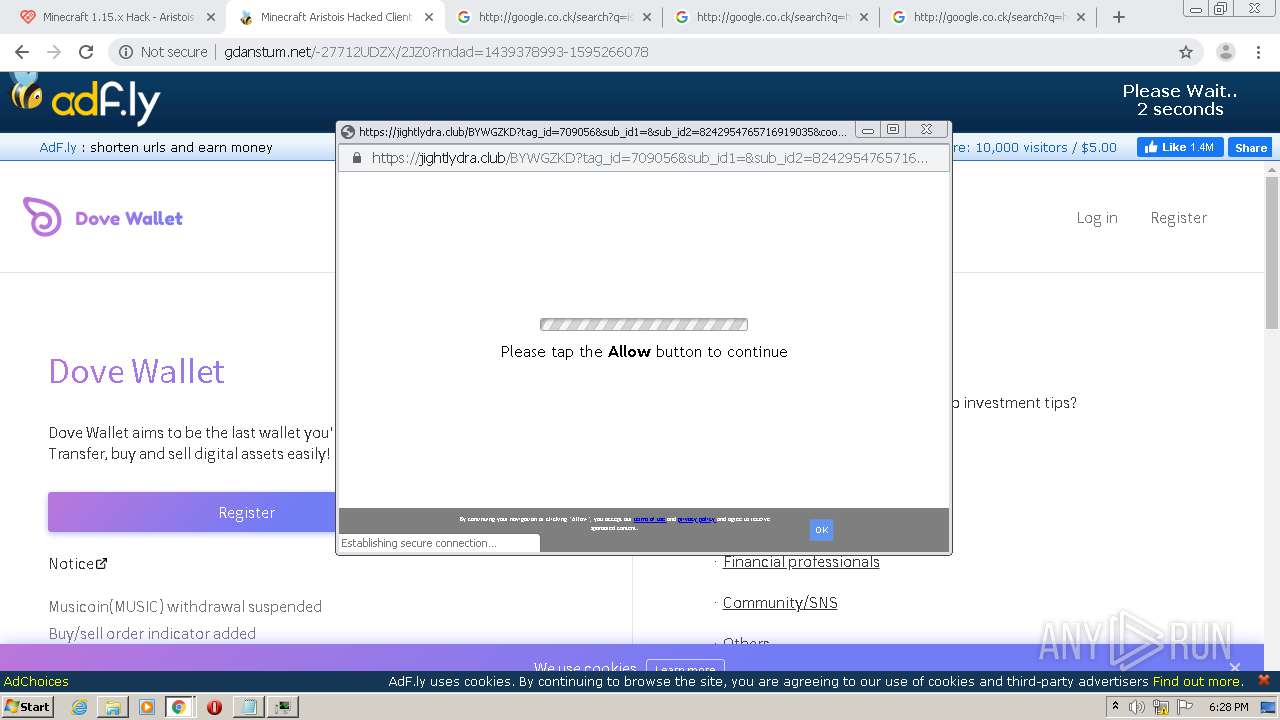
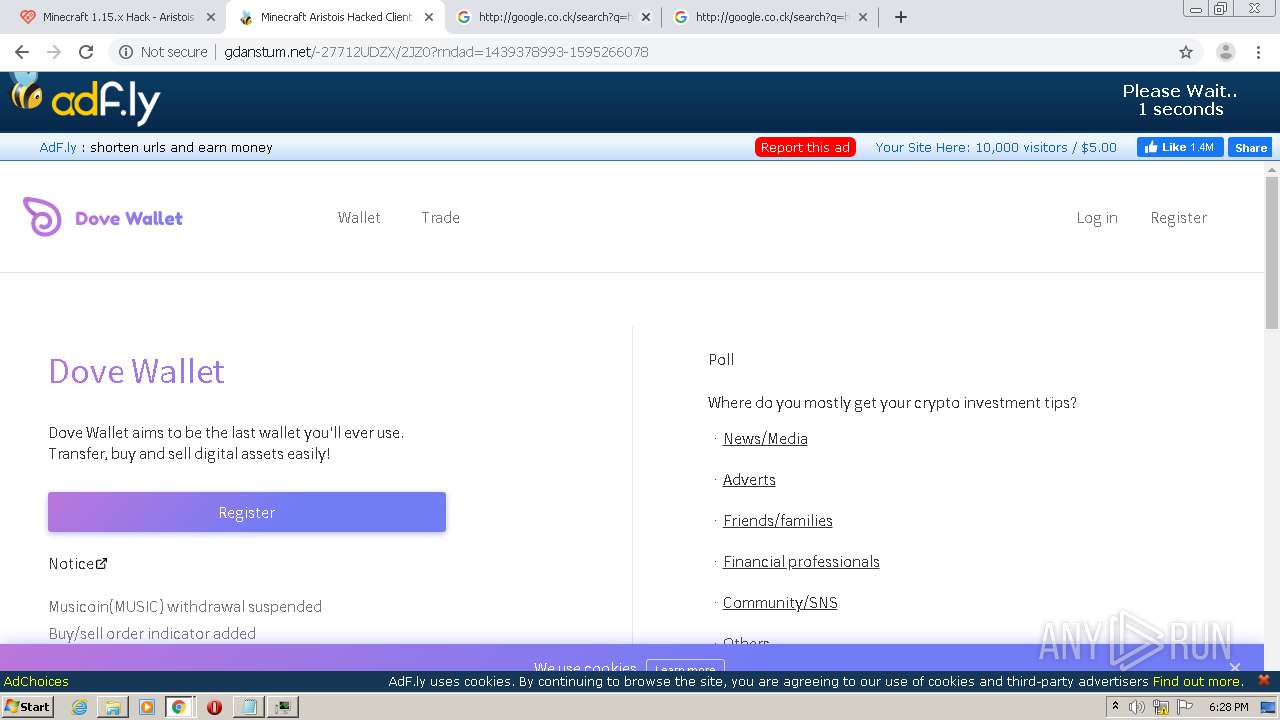
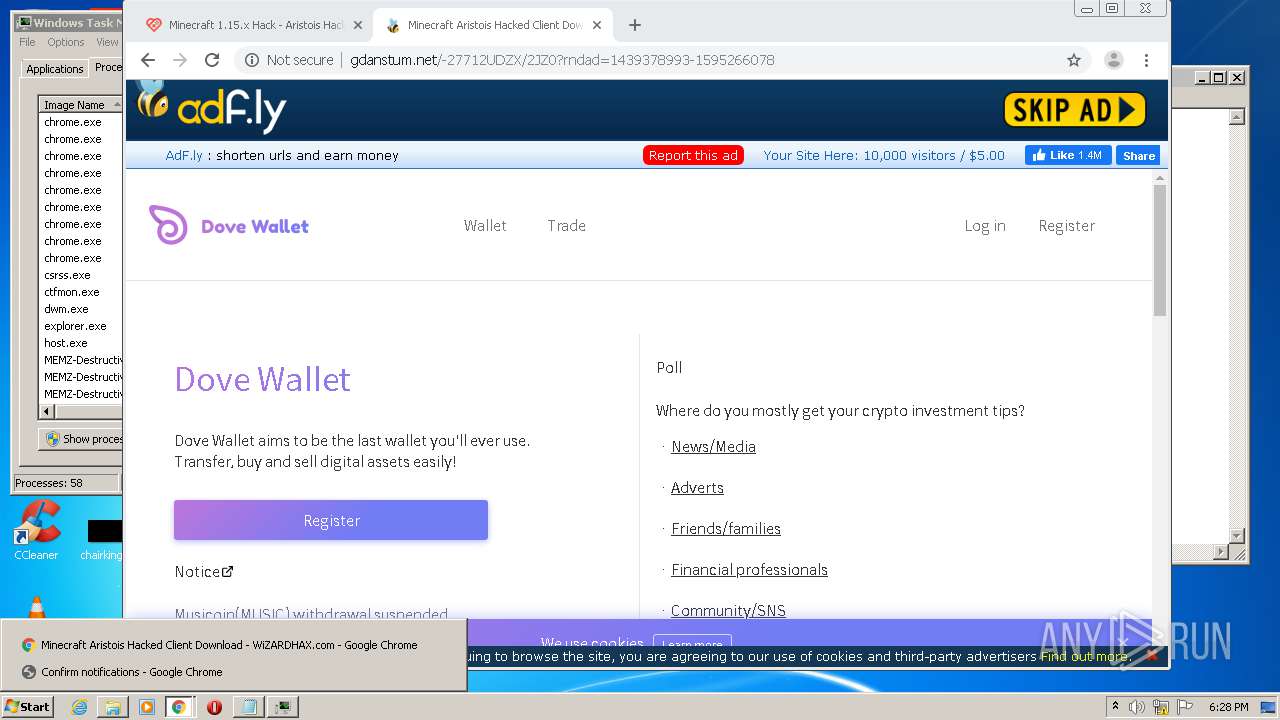
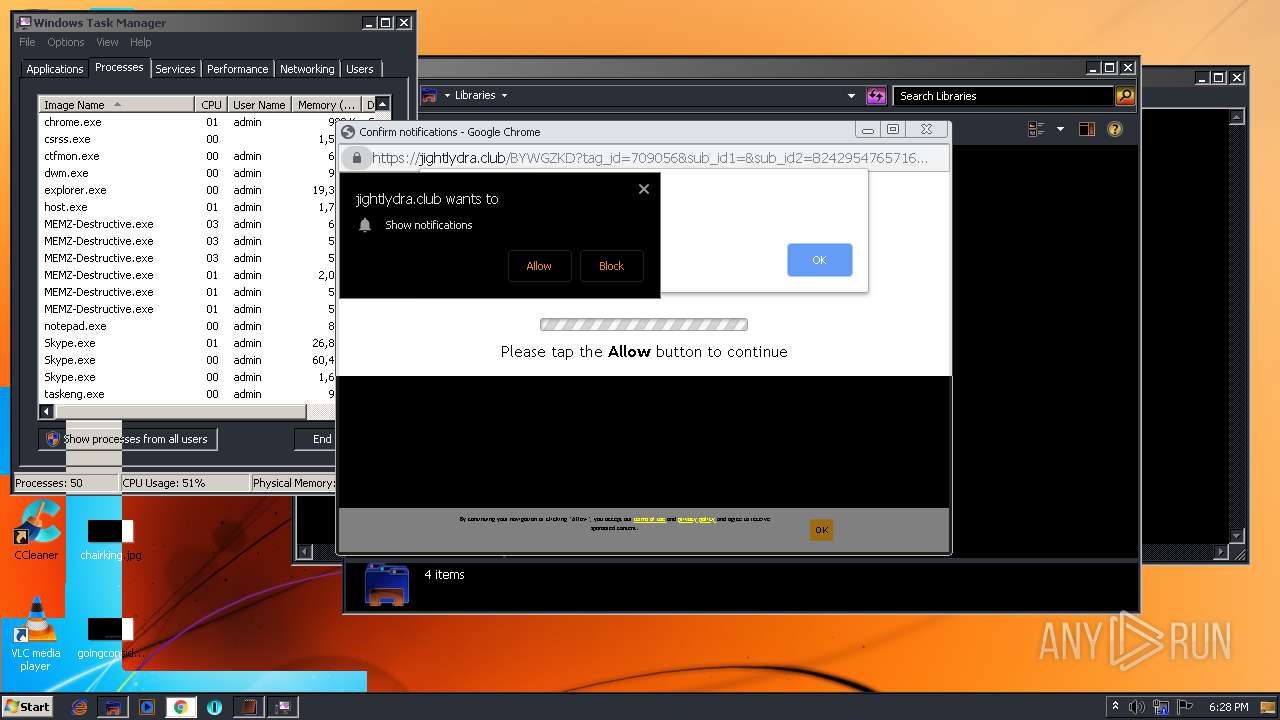
184 | chrome.exe | GET | 200 | 172.64.170.11:80 | http://gdanstum.net/-27712UDZX/2JZ0?rndad=1439378993-1595266078 | US | html | 5.69 Kb | suspicious |
184 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
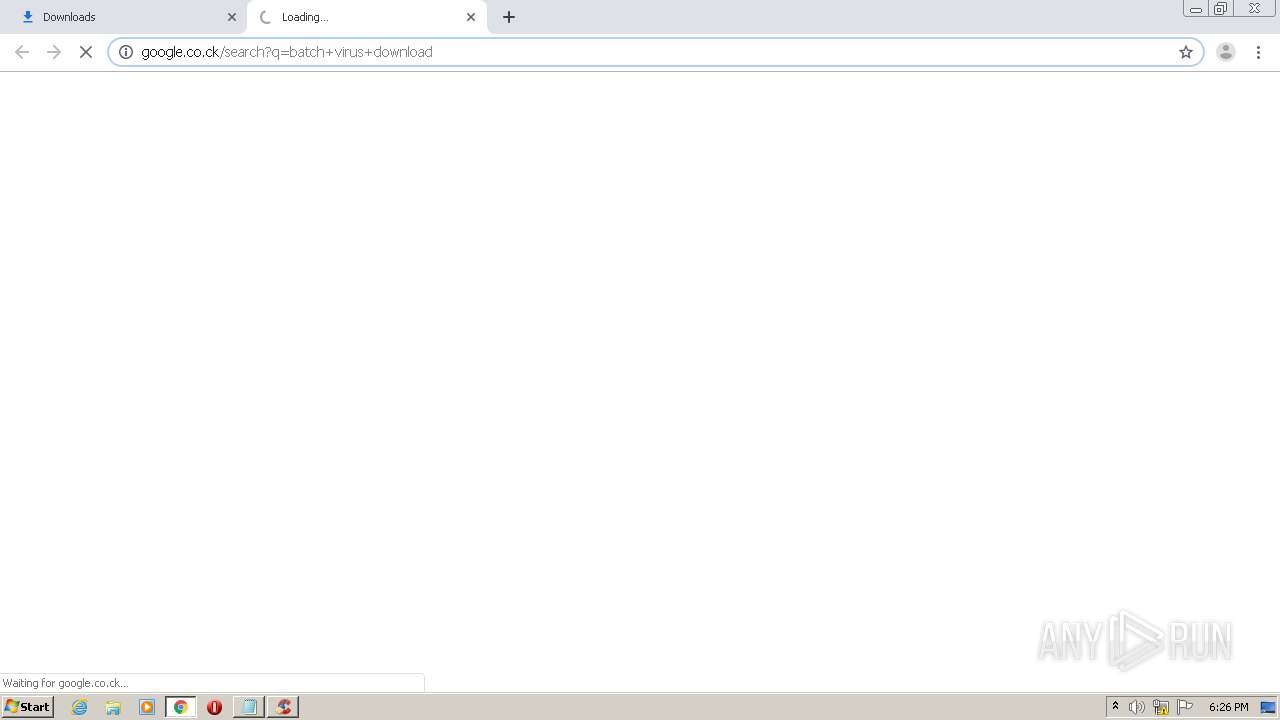
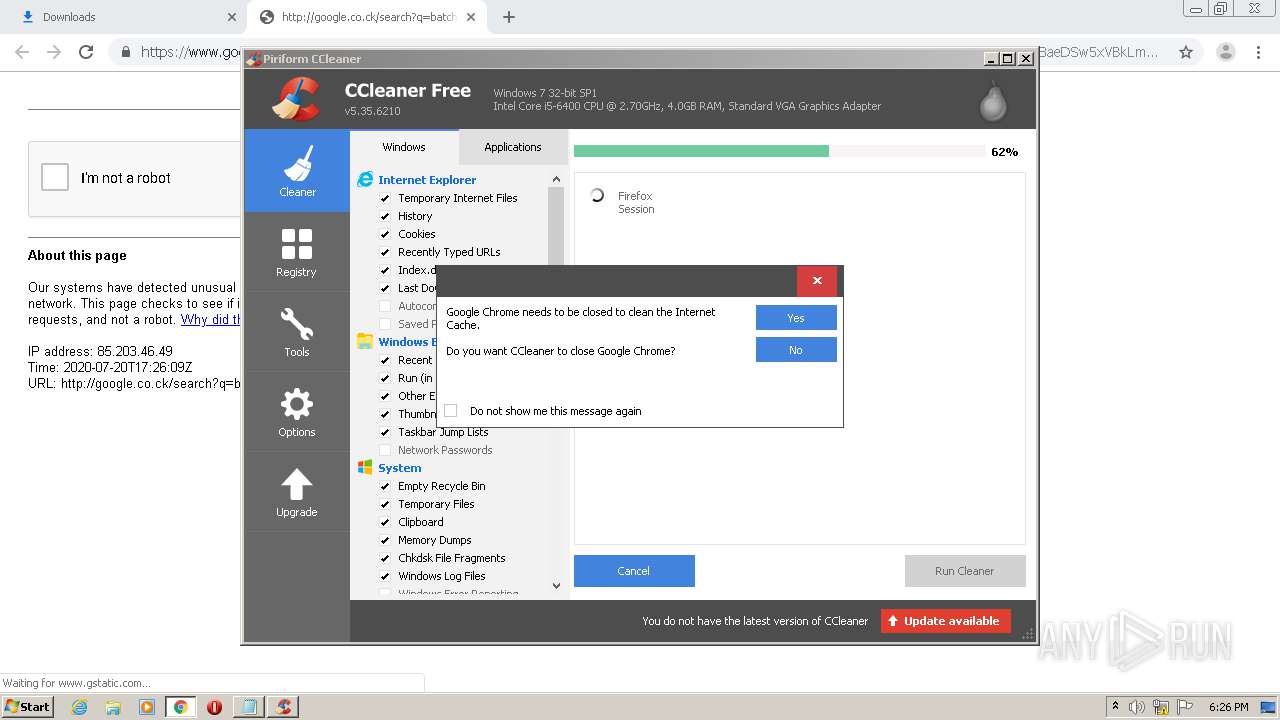
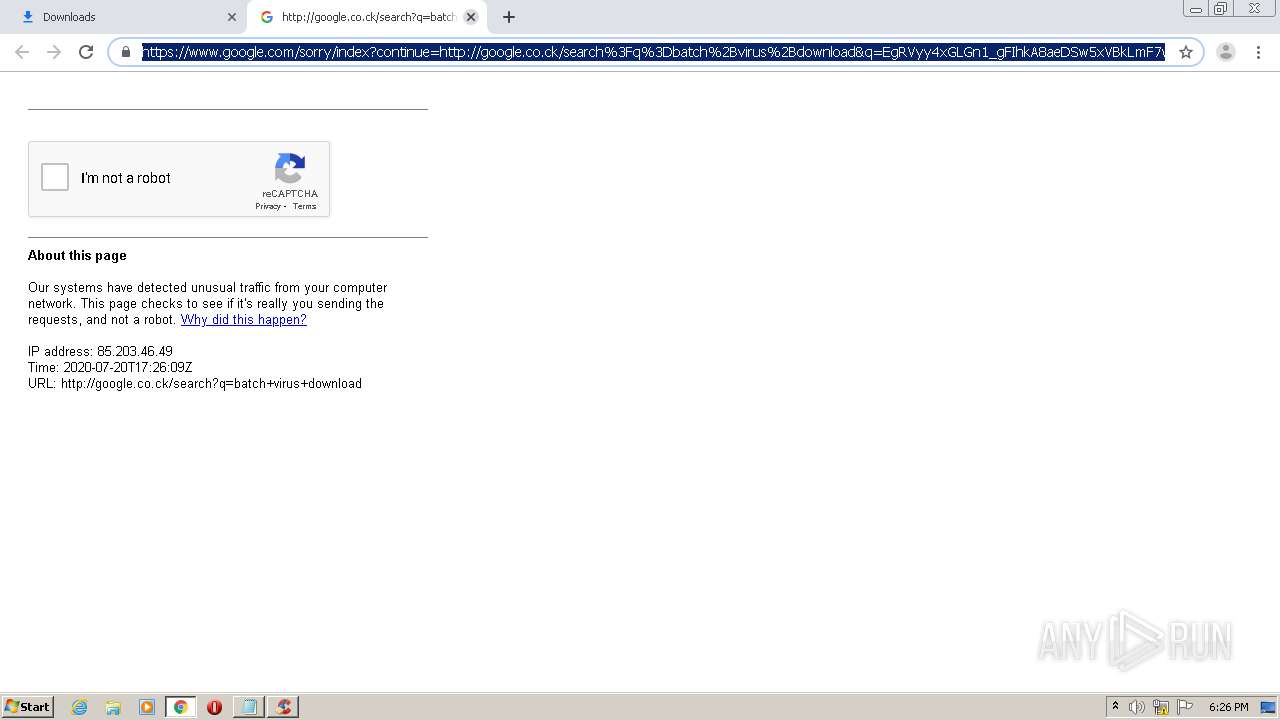
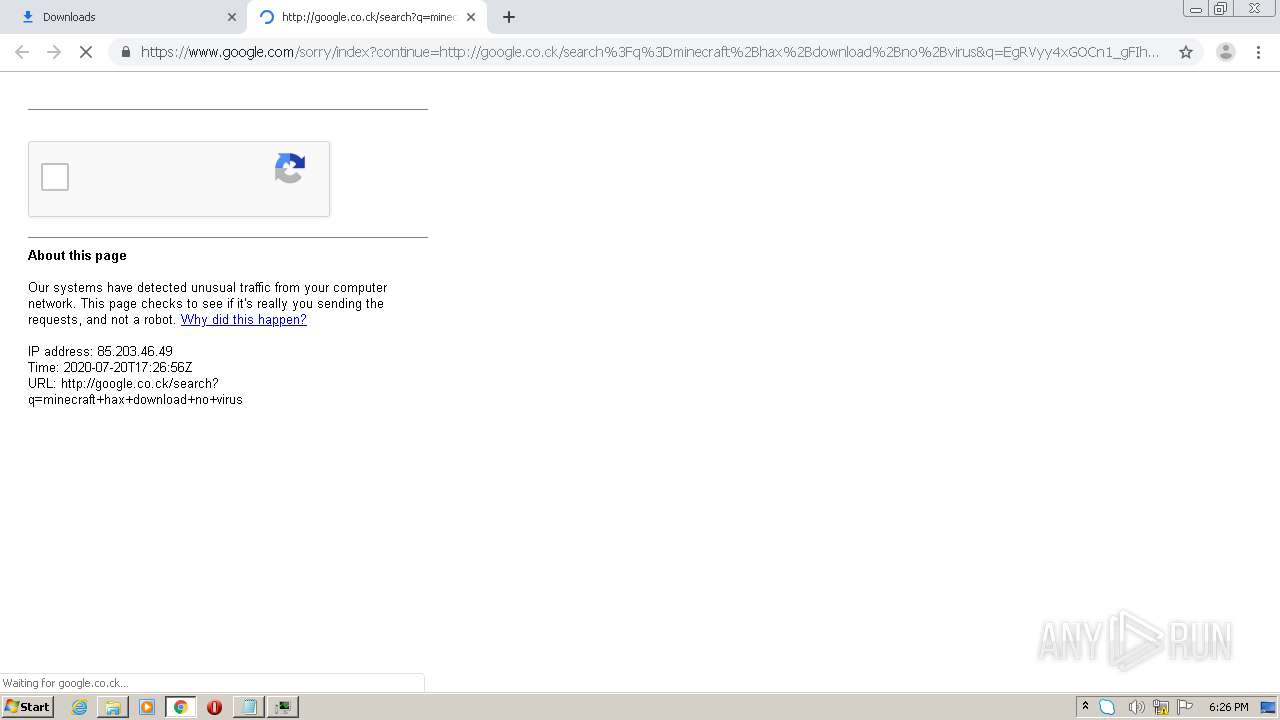
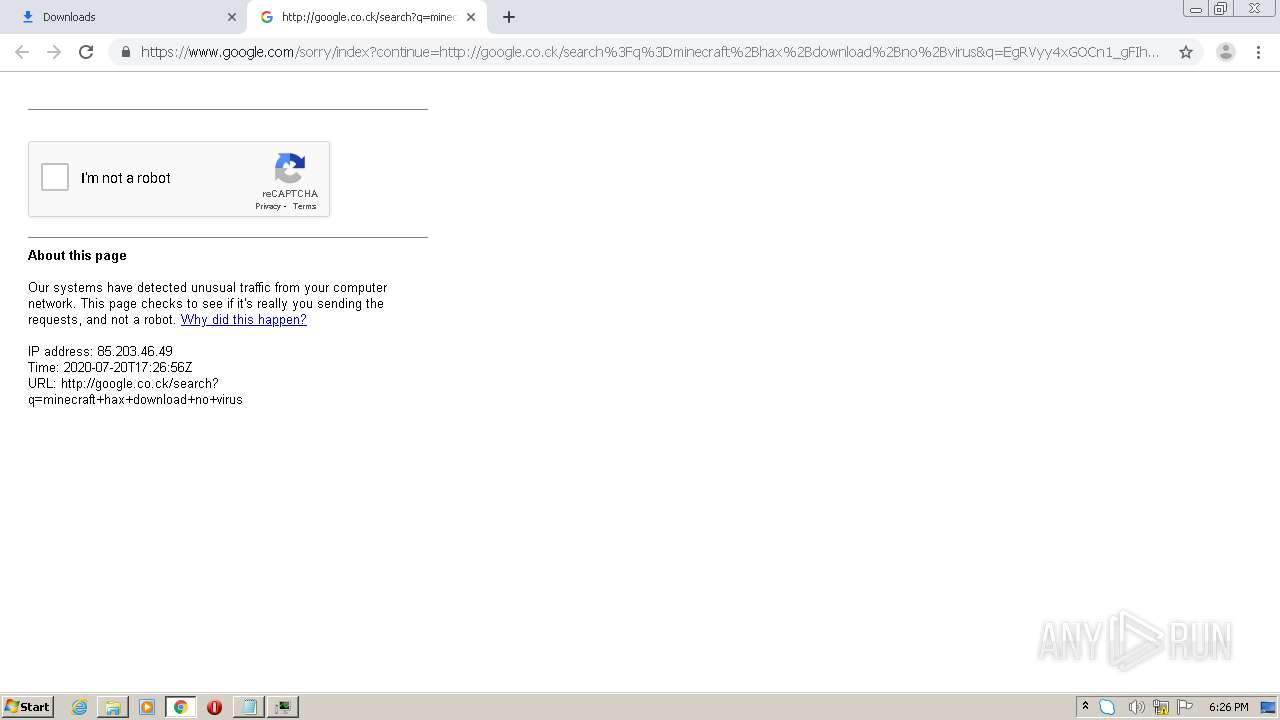
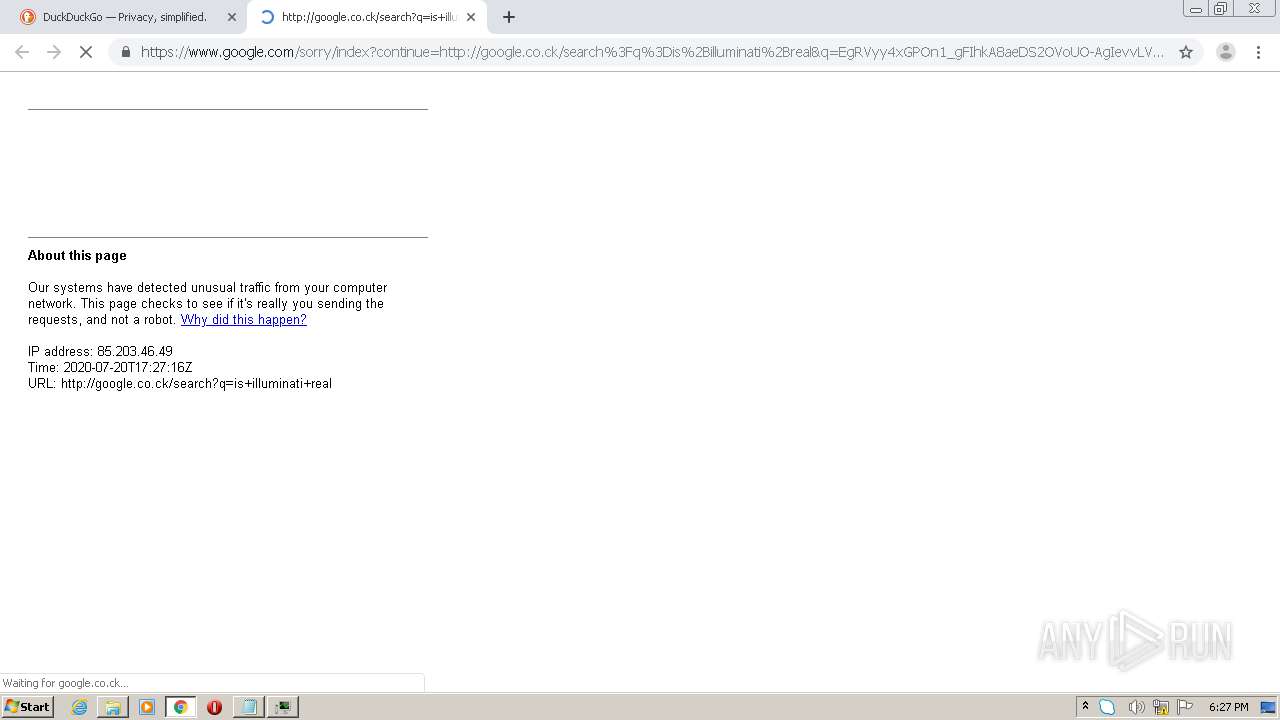
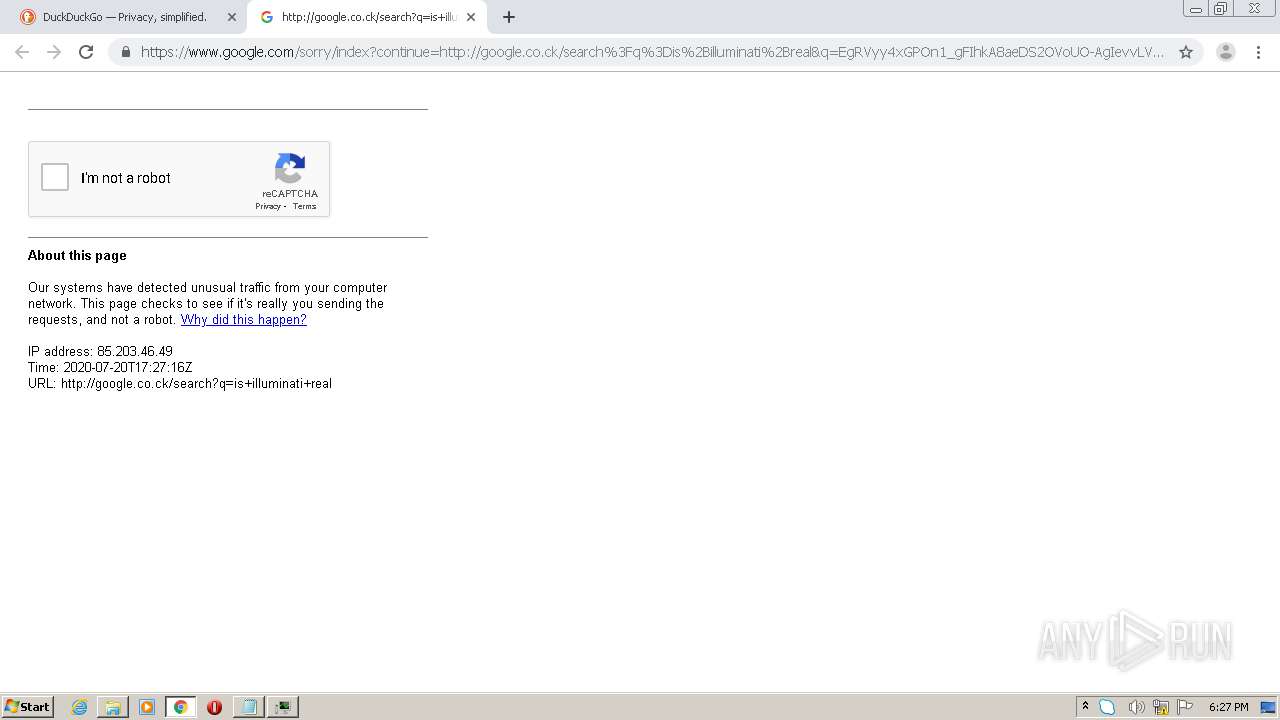
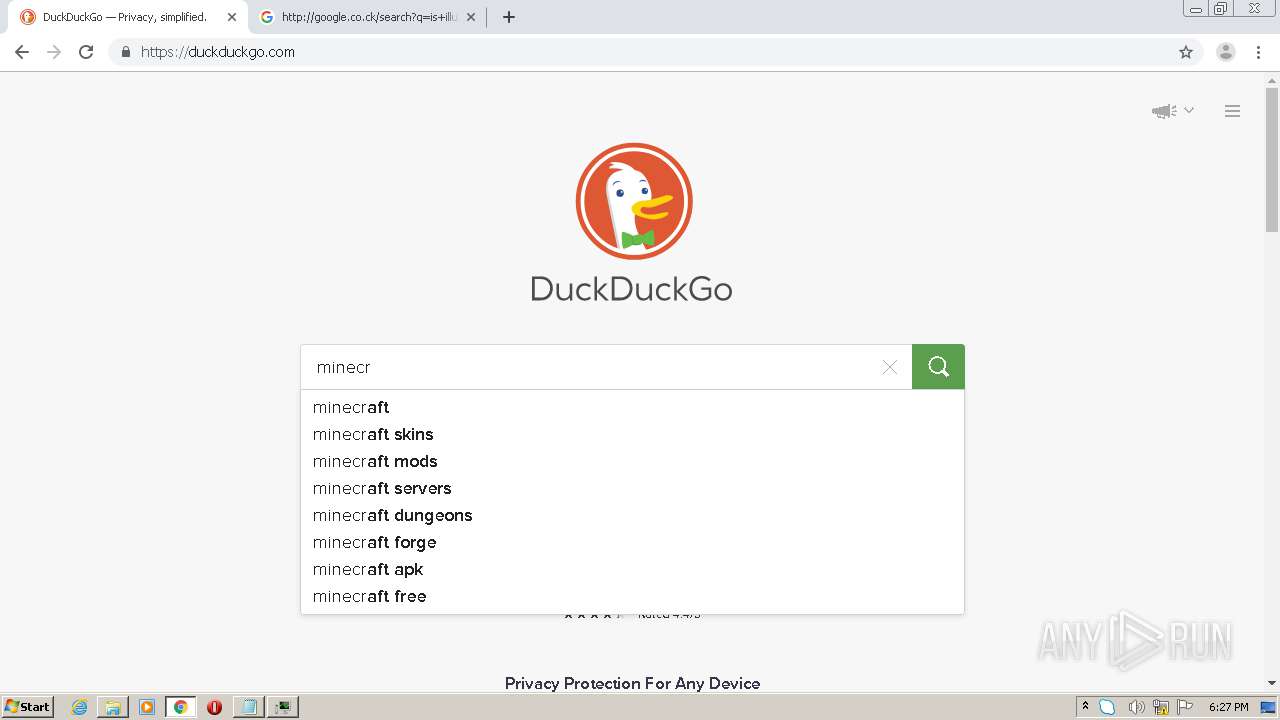
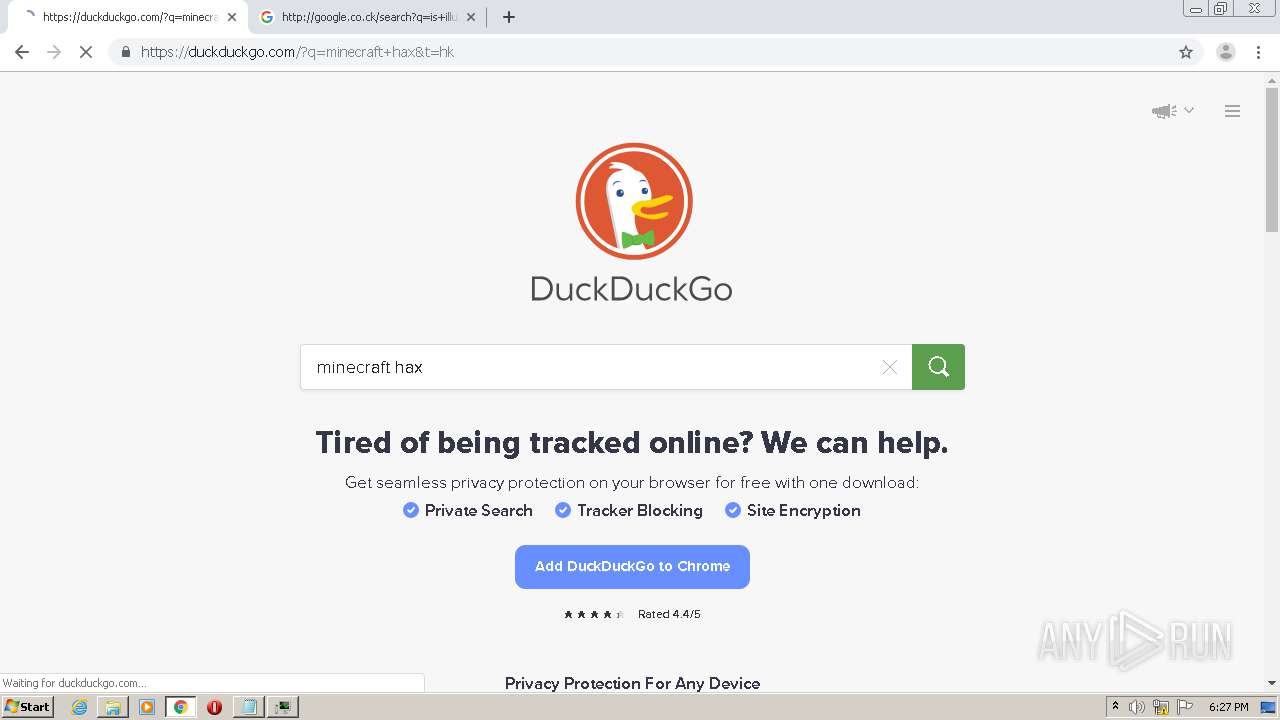
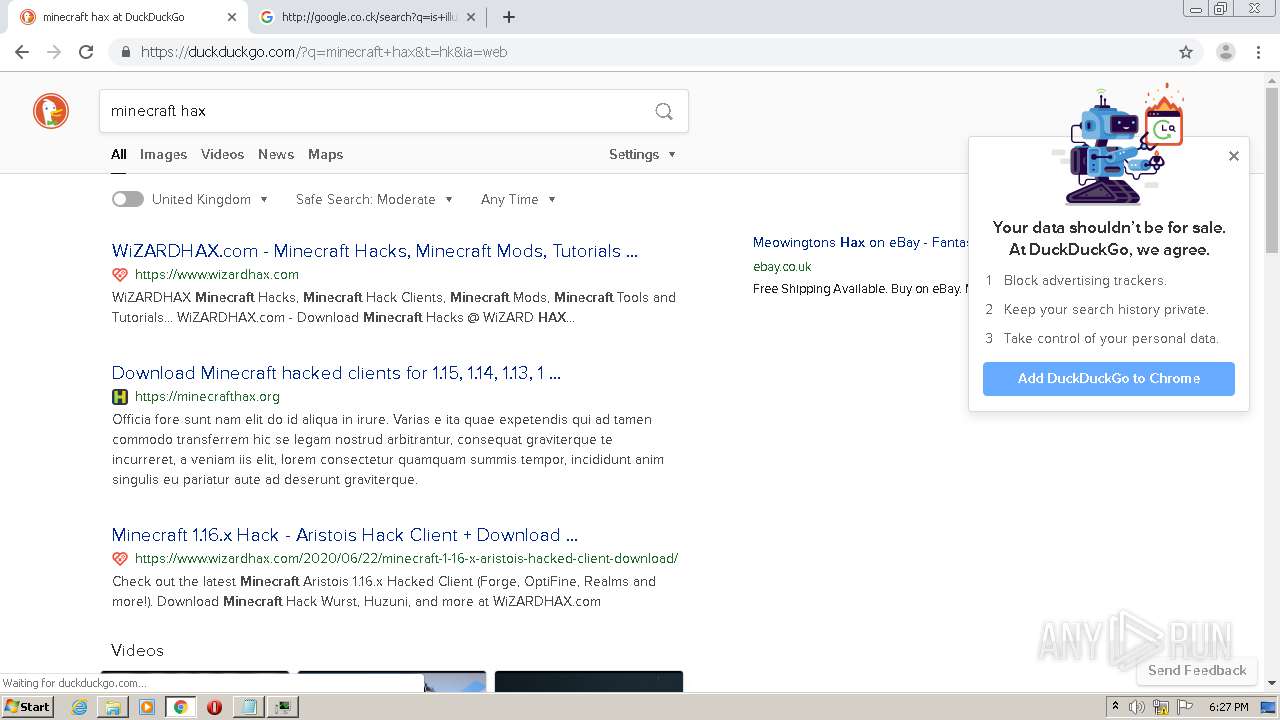
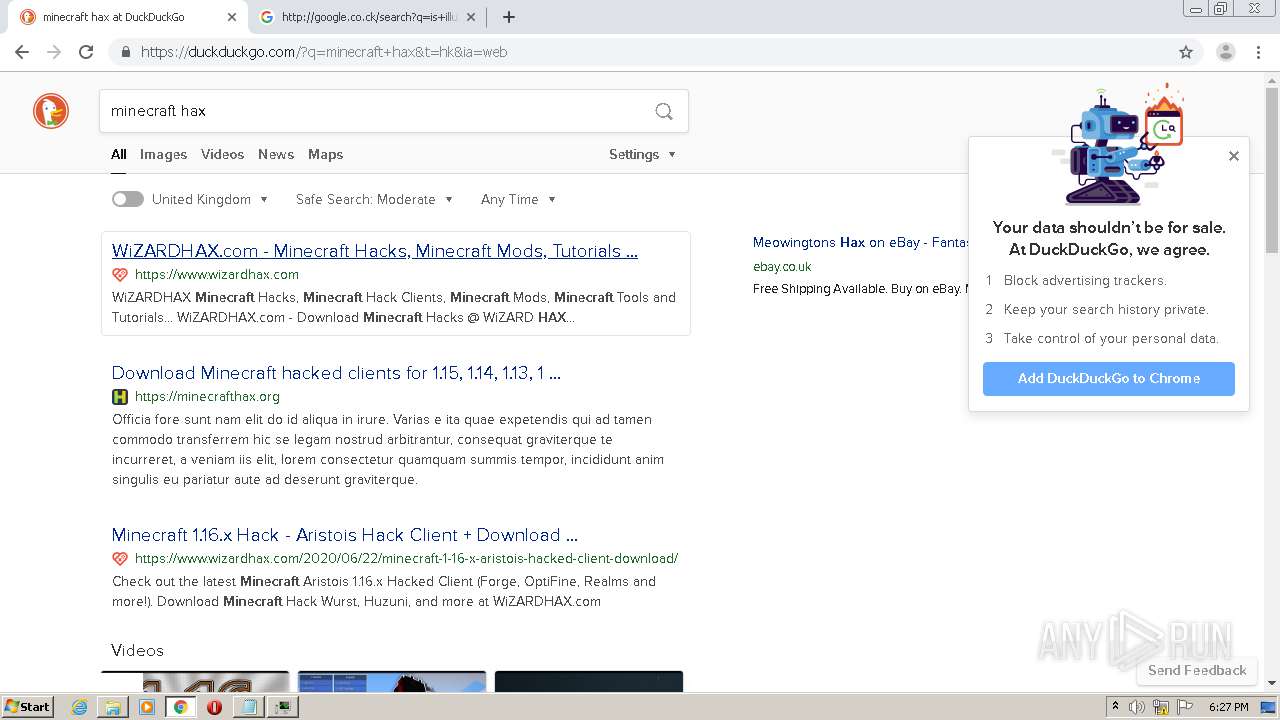
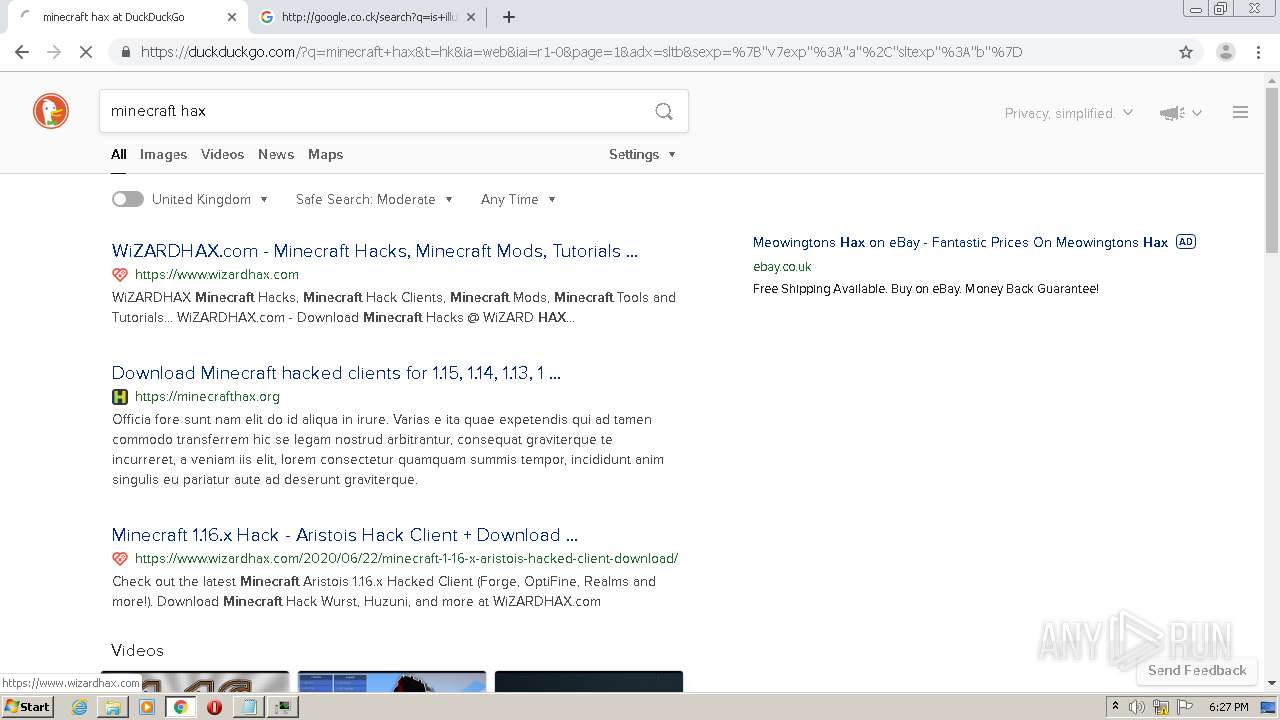
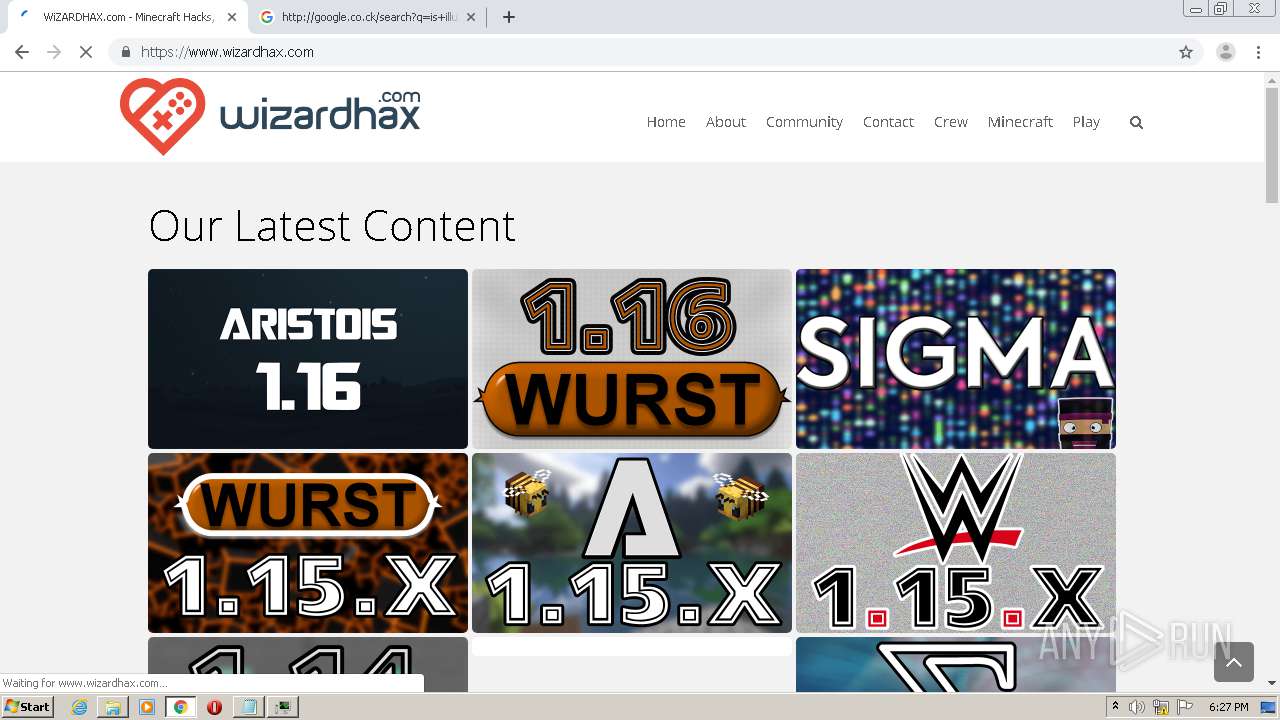
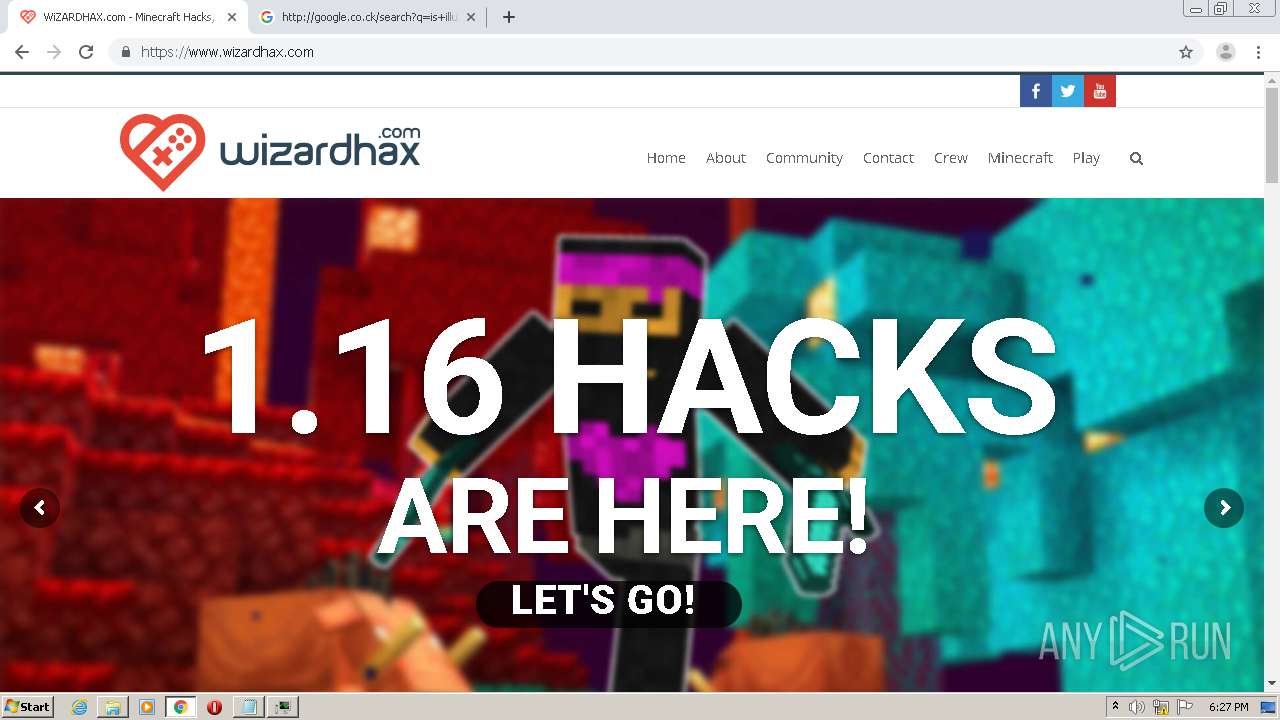
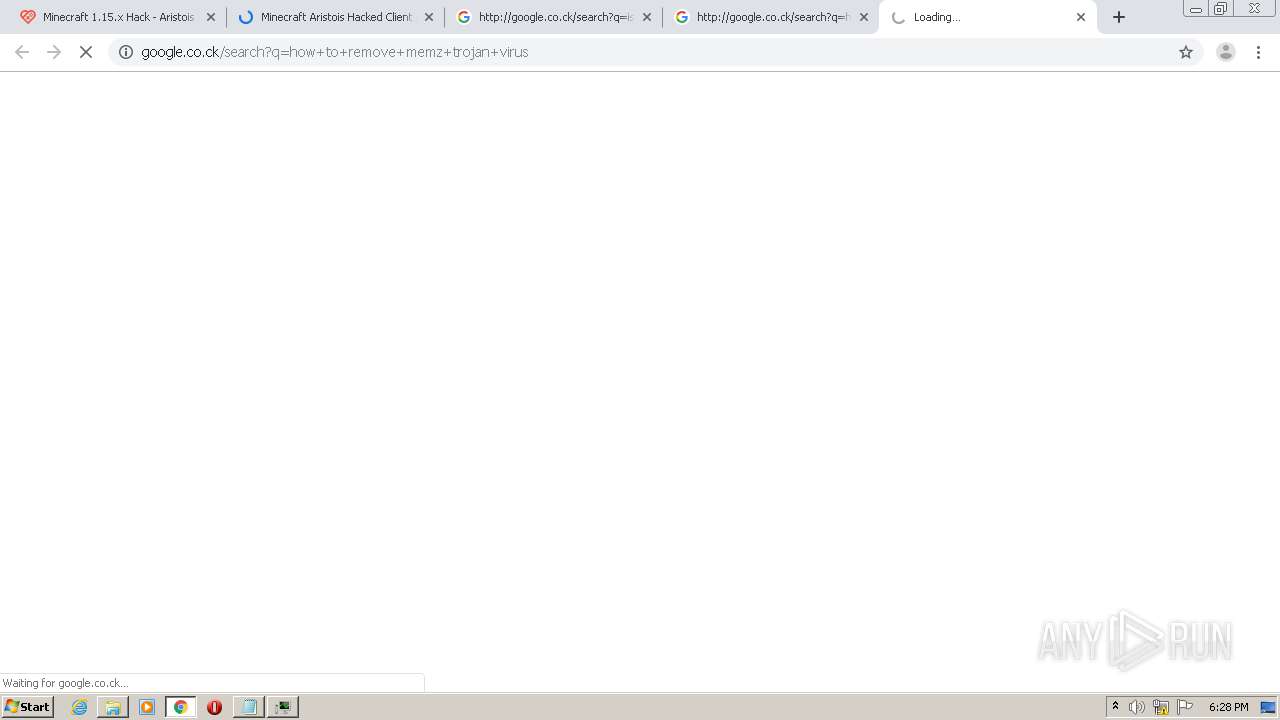
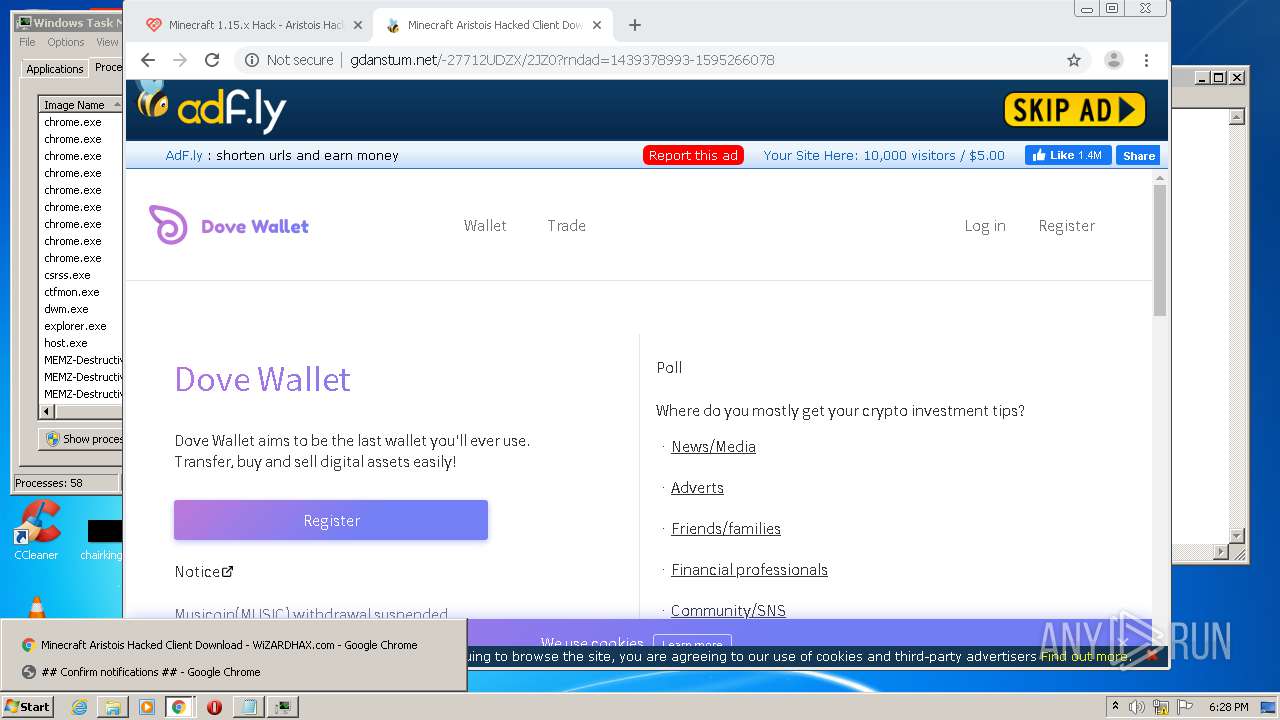
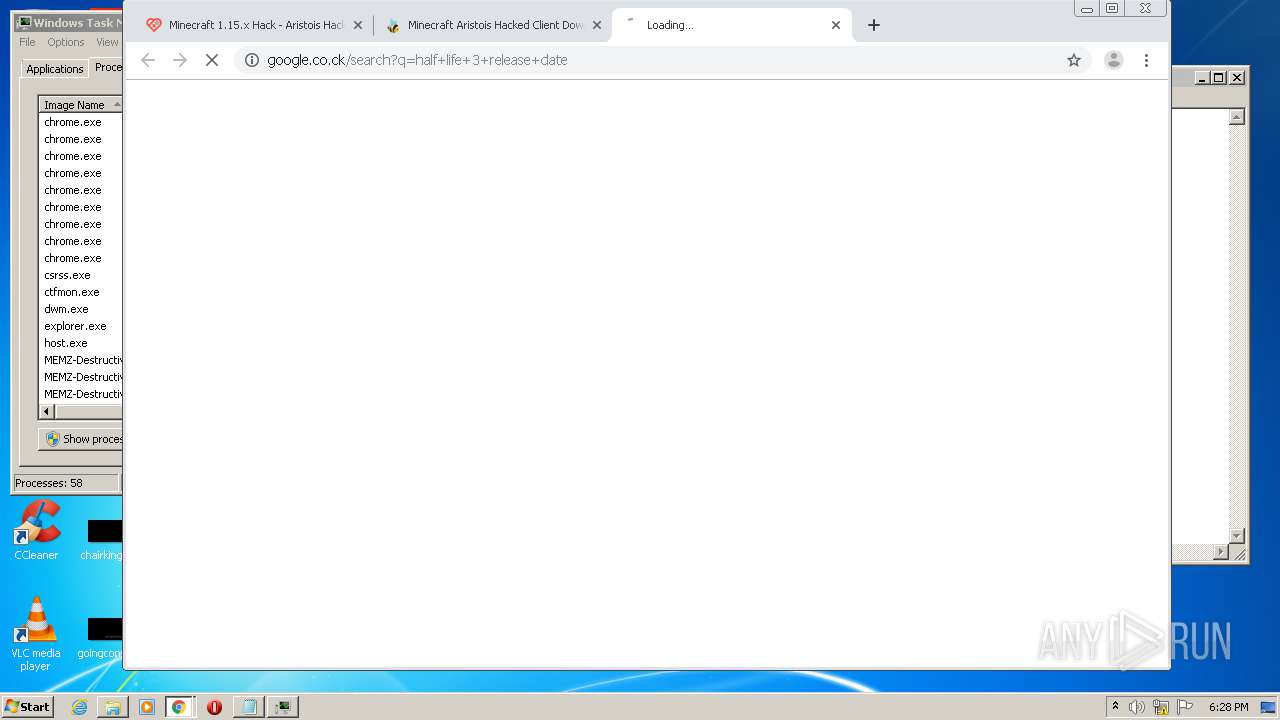
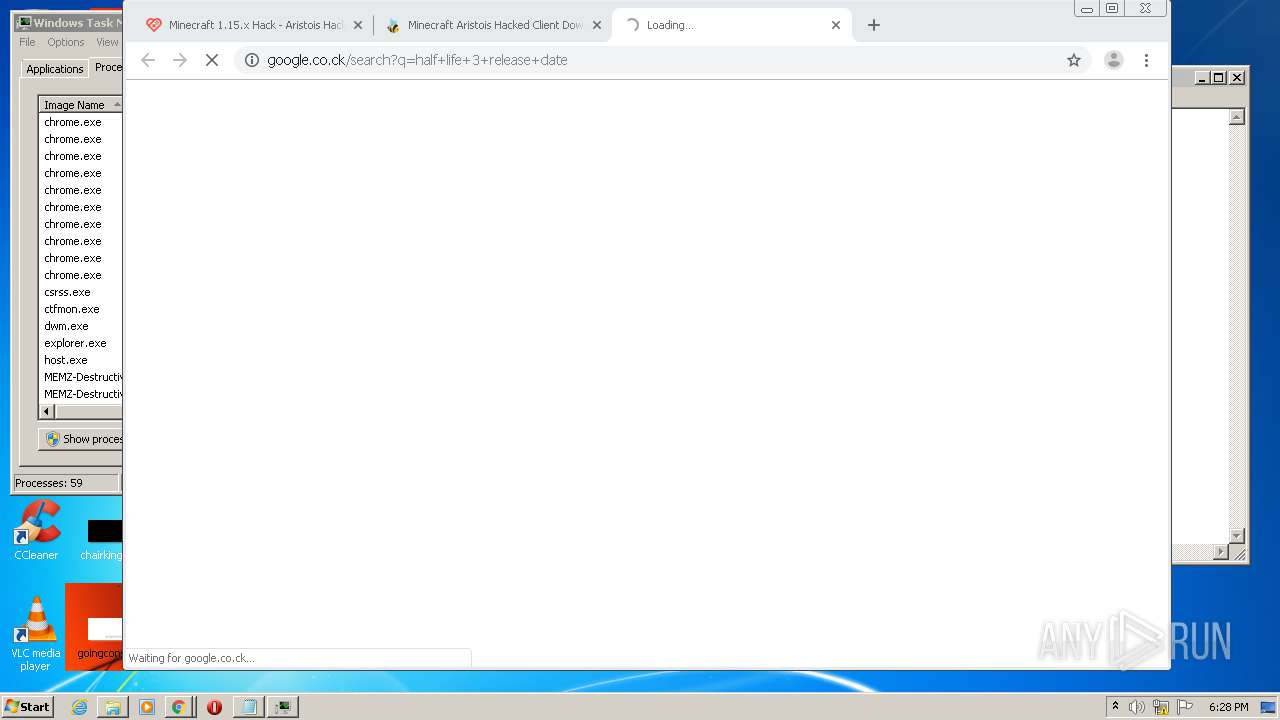
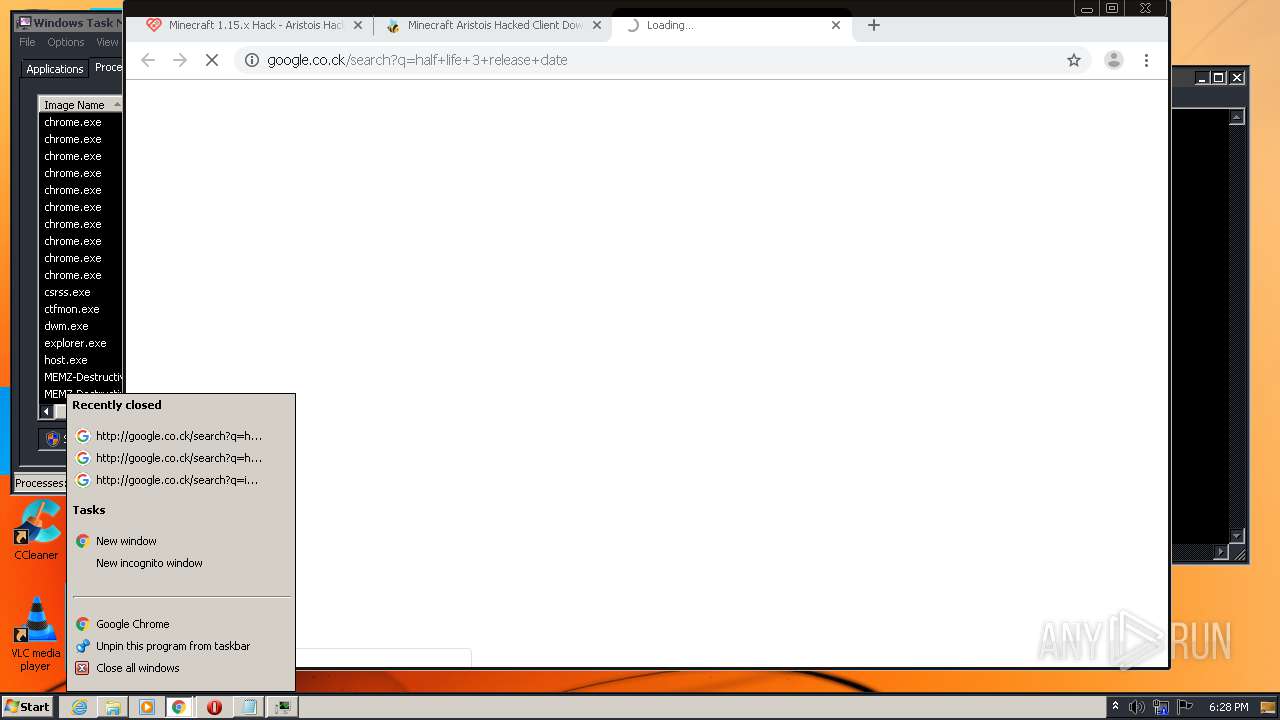
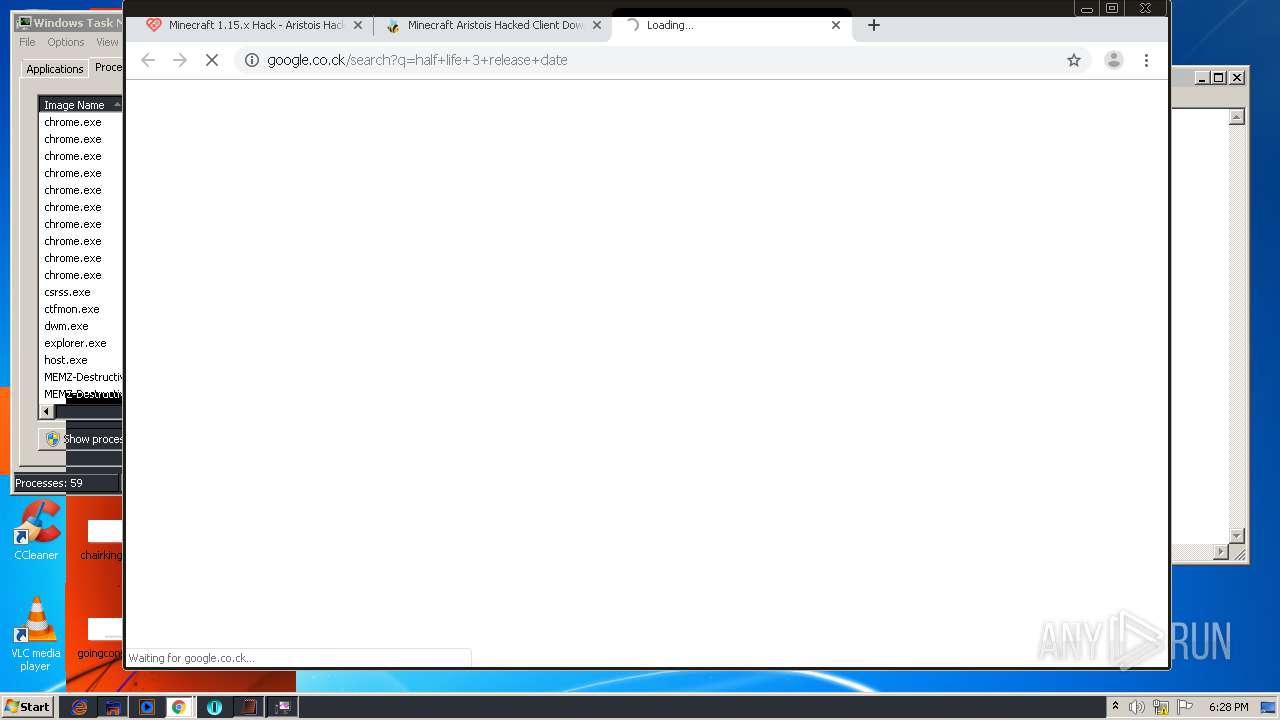
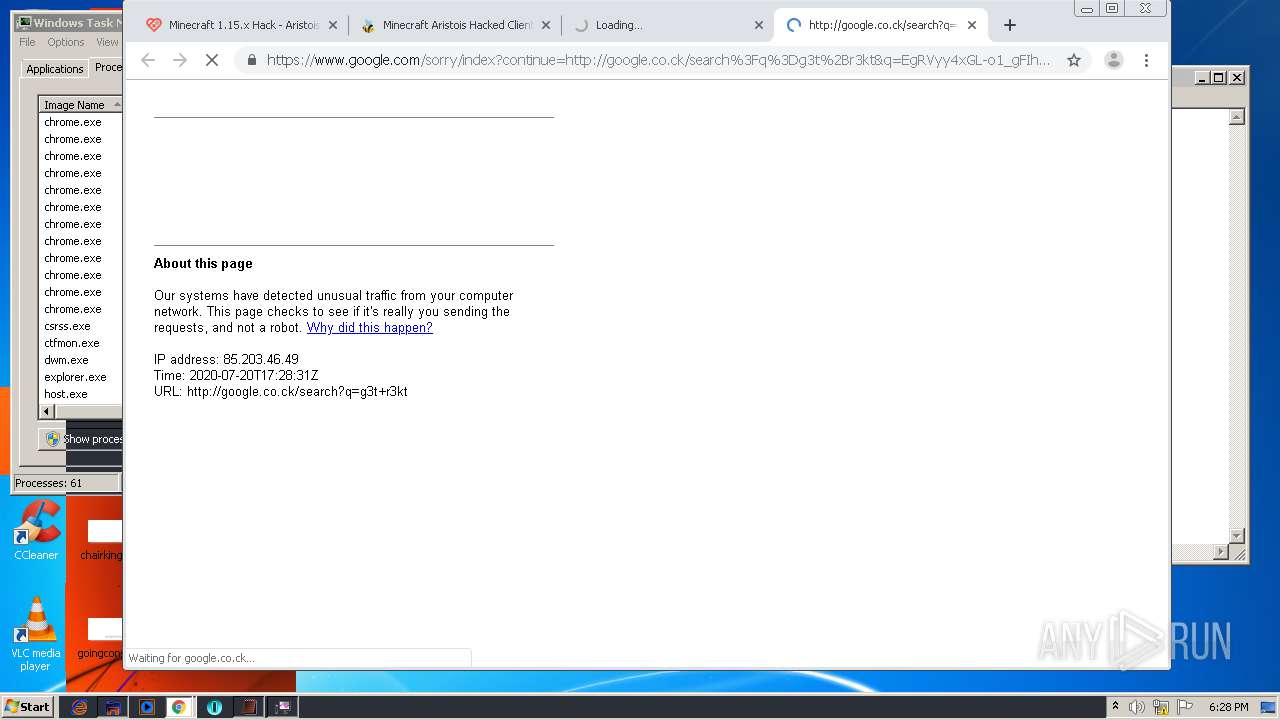
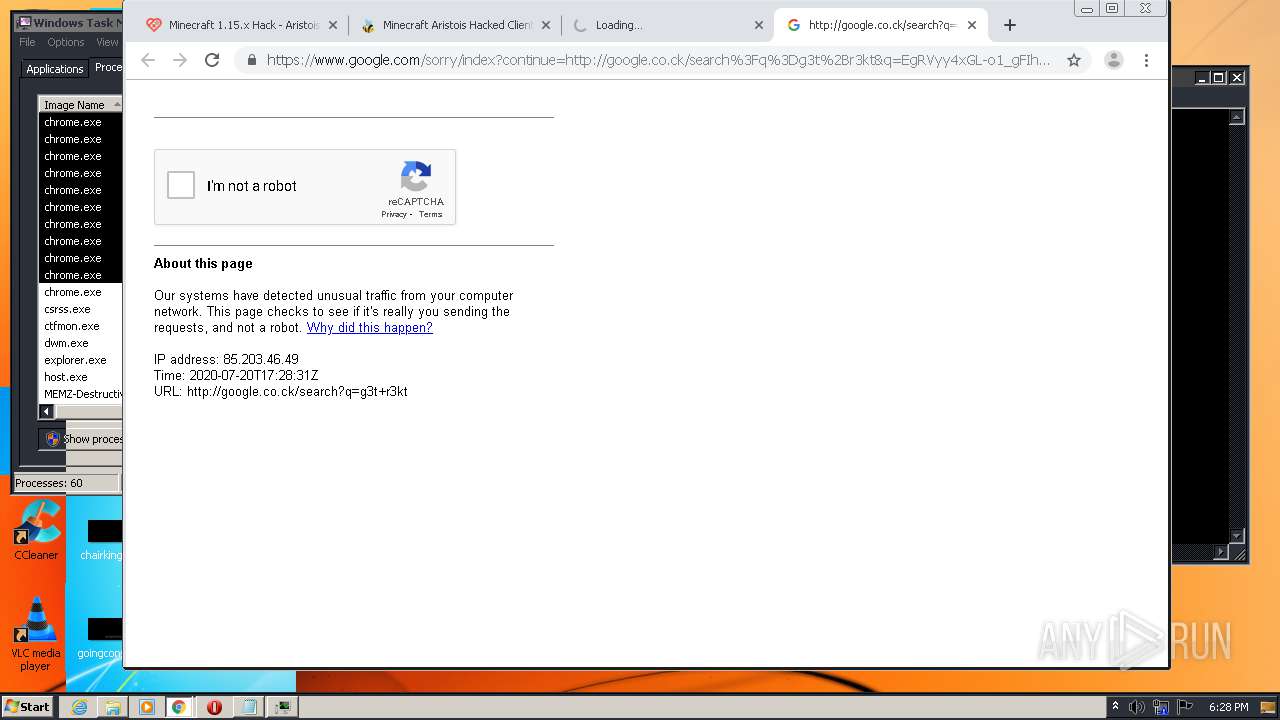
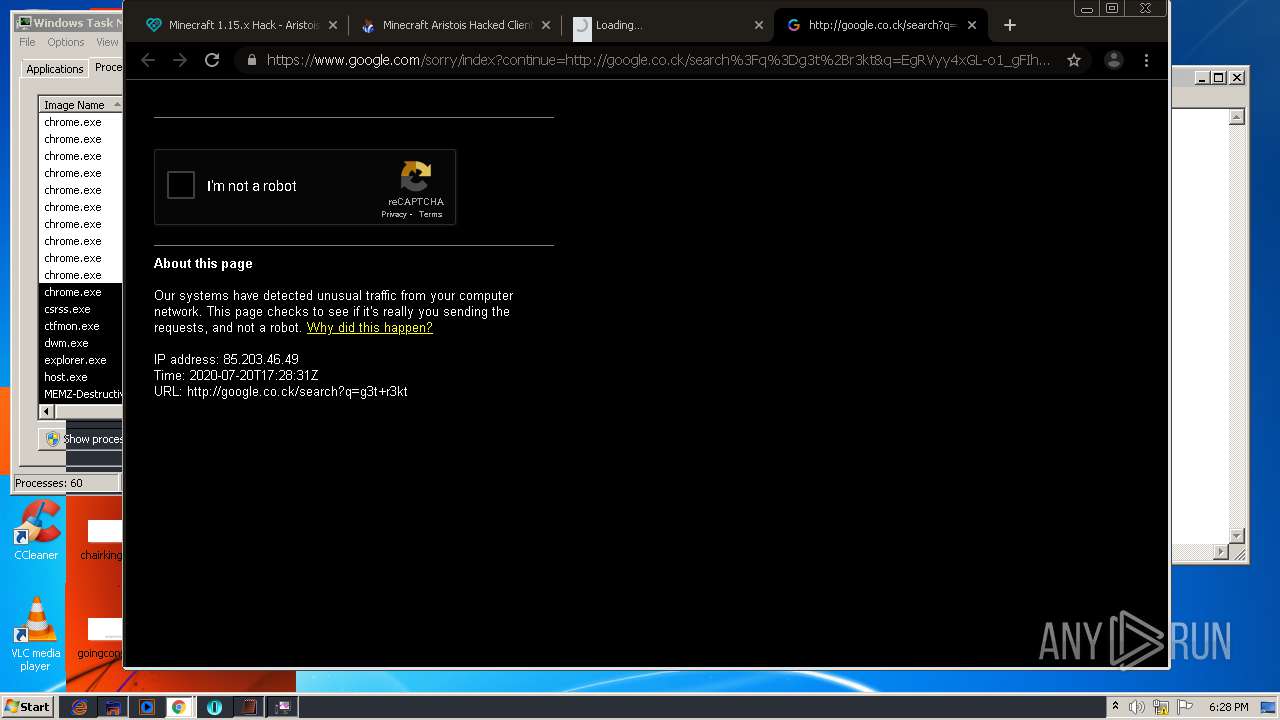
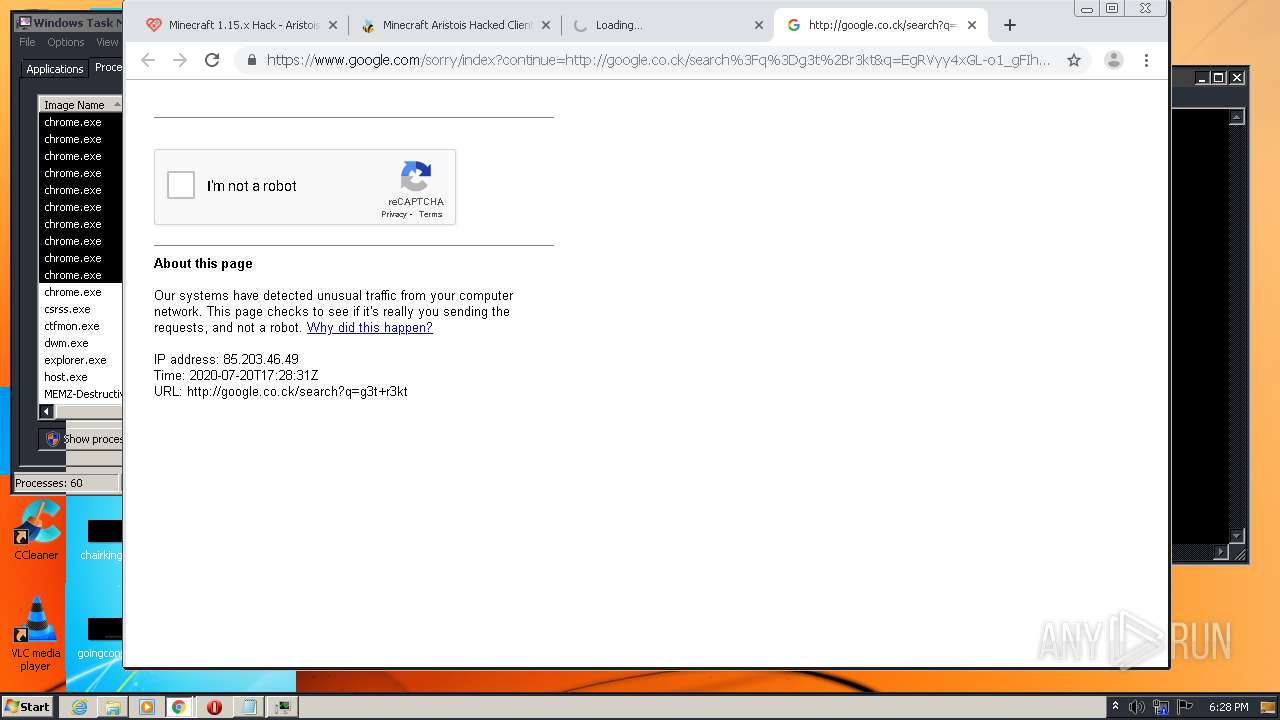
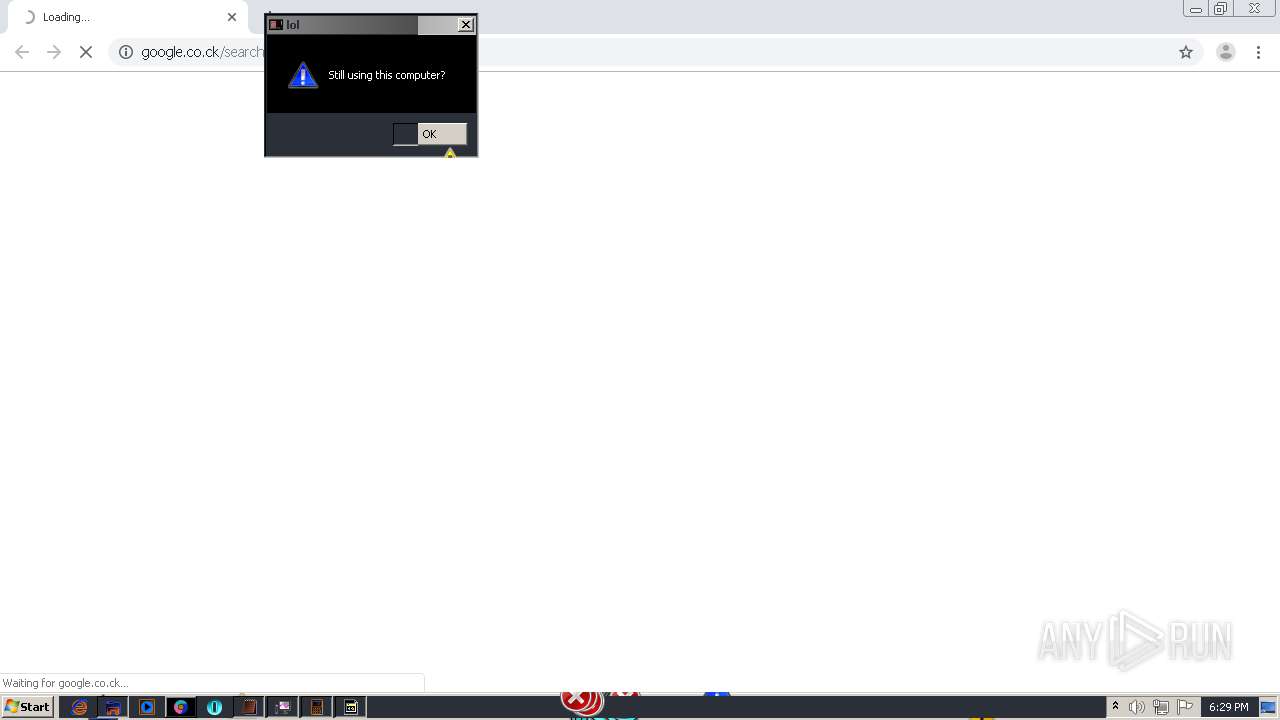
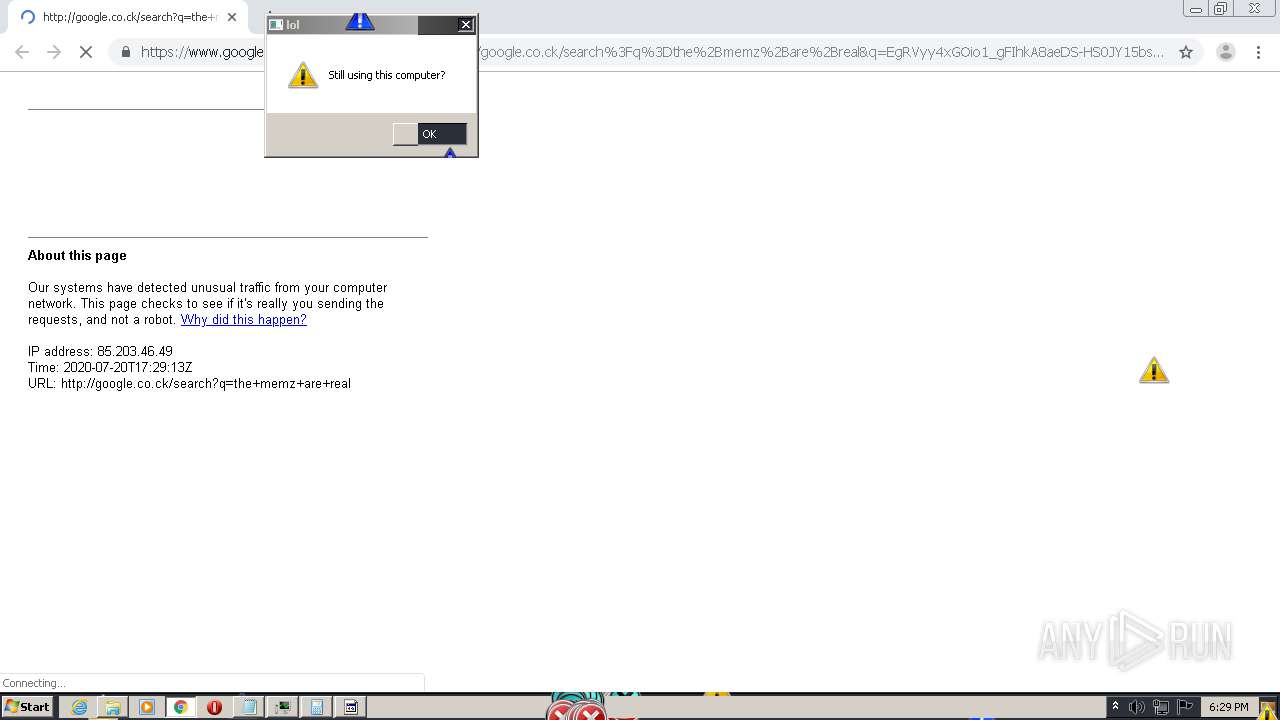
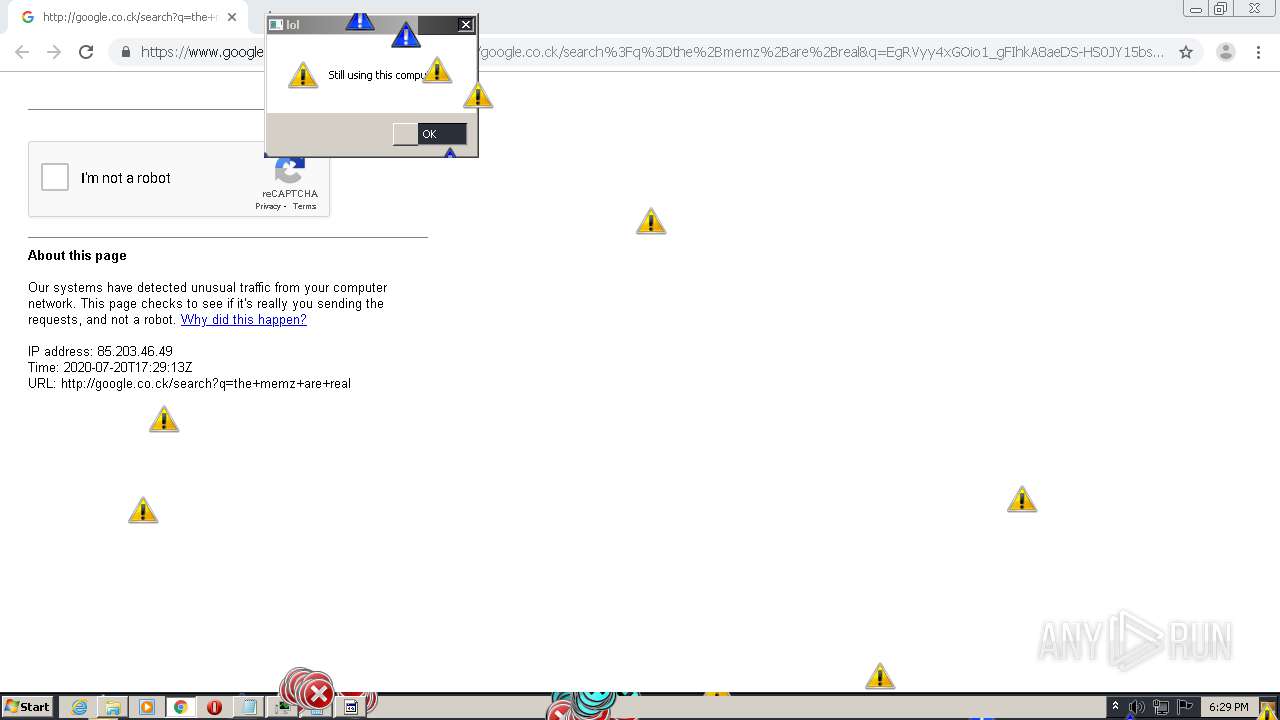
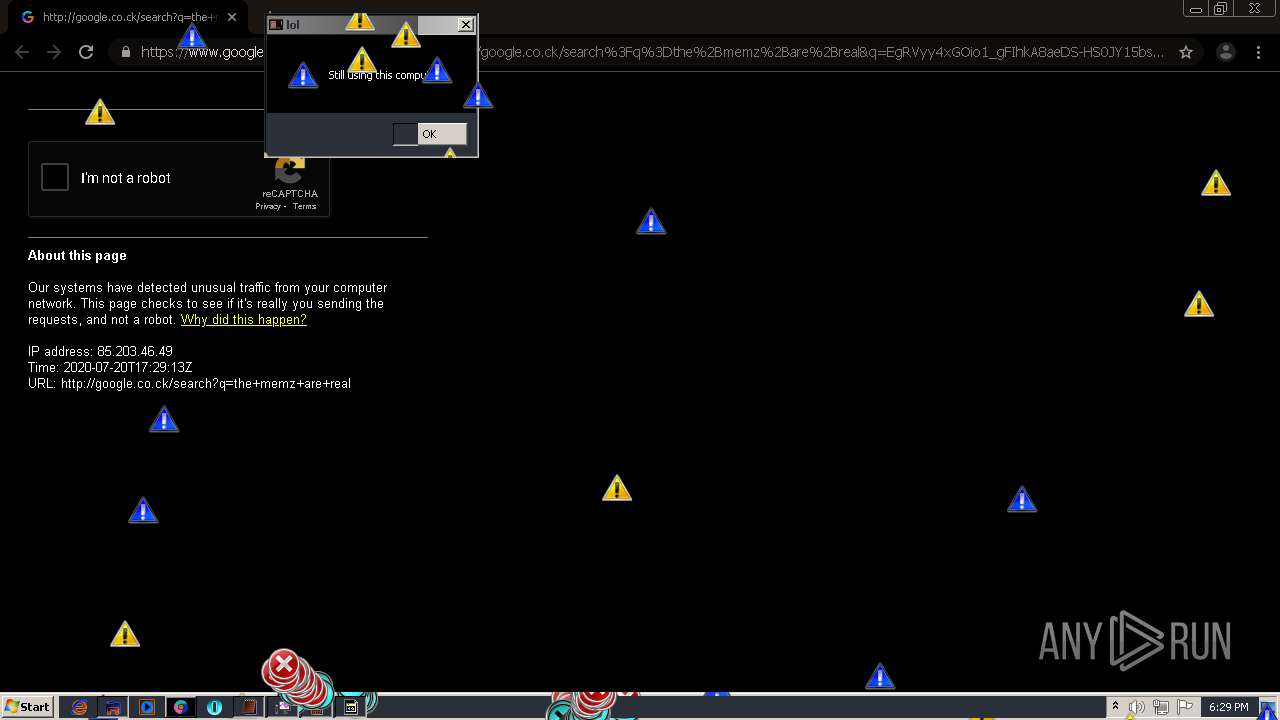
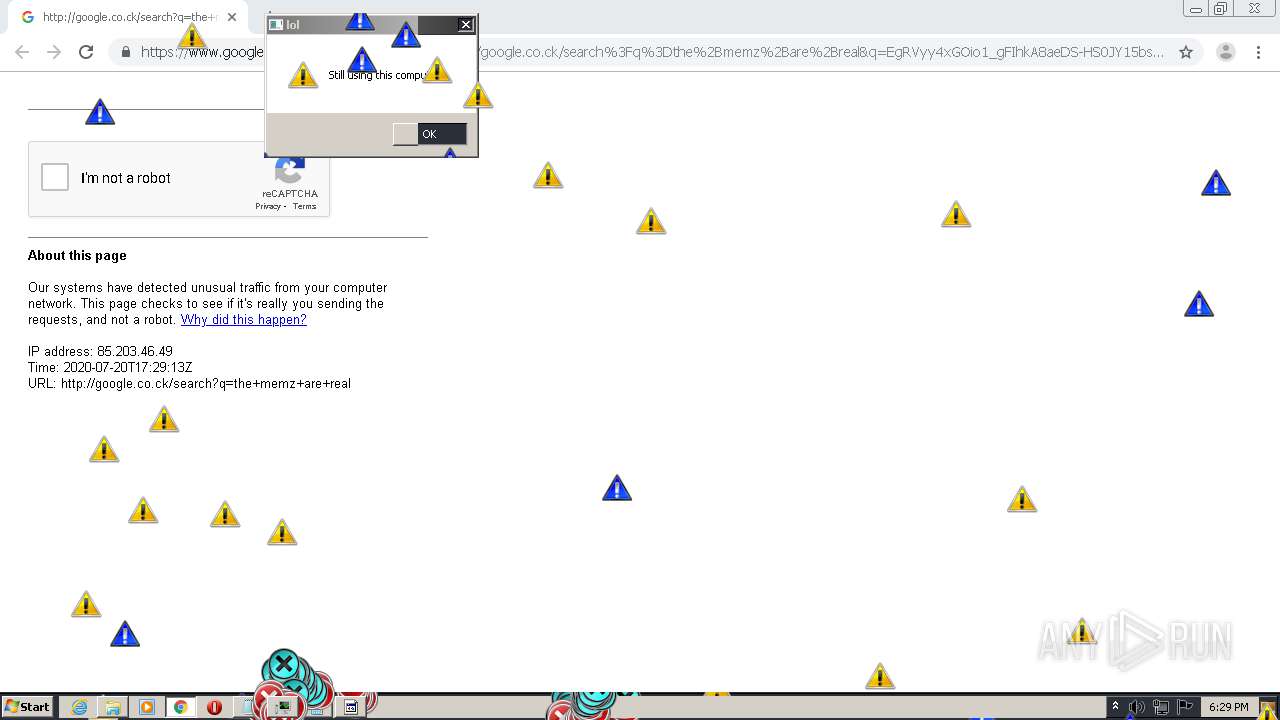
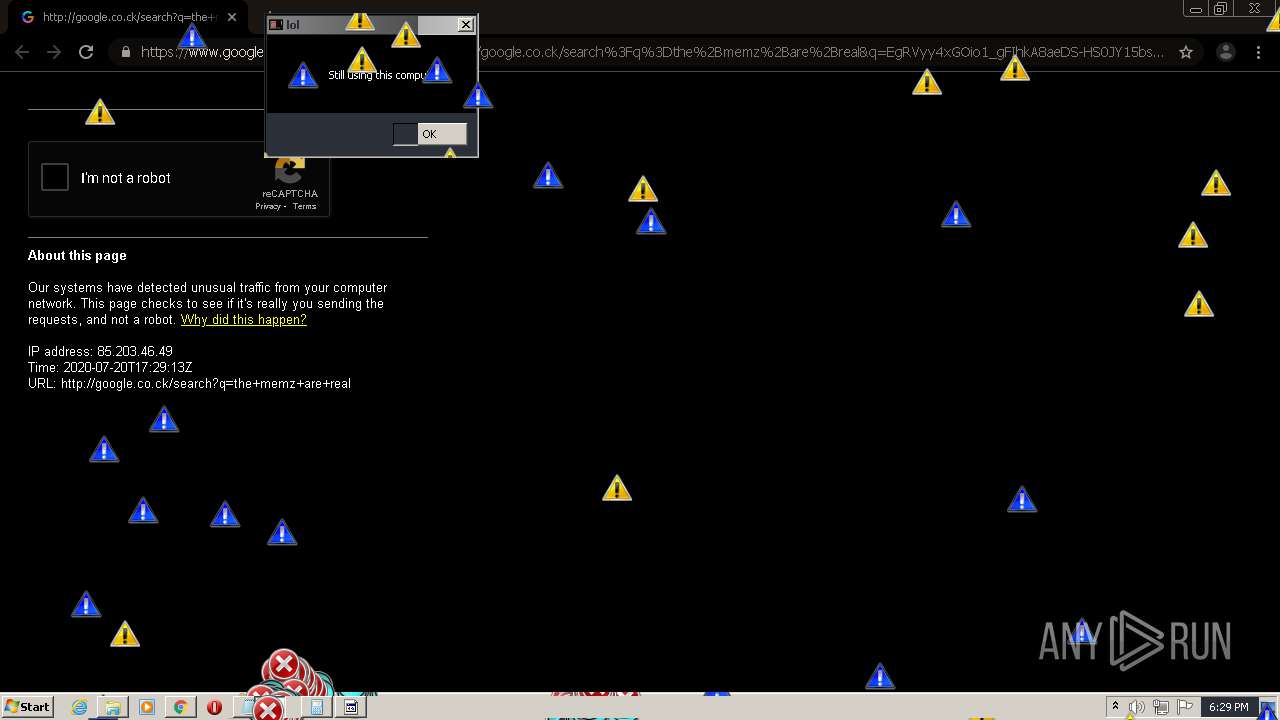
184 | chrome.exe | GET | 302 | 172.217.21.196:80 | http://google.co.ck/search?q=minecraft+hax+download+no+virus | US | html | 375 b | whitelisted |
184 | chrome.exe | GET | 302 | 172.217.21.196:80 | http://google.co.ck/search?q=how+to+remove+memz+trojan+virus | US | html | 377 b | whitelisted |
184 | chrome.exe | GET | 301 | 104.31.64.175:80 | http://tinyical.com/2JZ0 | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
184 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 140.82.118.4:443 | github.com | — | US | malicious |
184 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 185.199.110.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
— | — | 185.199.110.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
184 | chrome.exe | 216.58.212.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 151.101.0.133:443 | avatars0.githubusercontent.com | Fastly | US | malicious |
184 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
Threats
Process | Message |
|---|---|
Skype.exe | [2712:3996:0720/182634.812:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [2712:1708:0720/182634.812:VERBOSE1:crash_service.cc(333)] client start. pid = 1032
|
Skype.exe | [2712:3996:0720/182634.812:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2712:3996:0720/182634.812:VERBOSE1:crash_service.cc(145)] window handle is 000101FE
|
Skype.exe | [2712:3996:0720/182634.812:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2712:3996:0720/182634.812:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2712:1708:0720/182637.032:VERBOSE1:crash_service.cc(333)] client start. pid = 2456
|
Skype.exe | [3656:3348:0720/182637.234:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [3656:3348:0720/182637.235:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [3656:3348:0720/182637.235:VERBOSE1:crash_service.cc(145)] window handle is 0001021E
|