| File name: | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe |
| Full analysis: | https://app.any.run/tasks/6dc08d7d-189c-48b2-9527-deecd8f7edc0 |
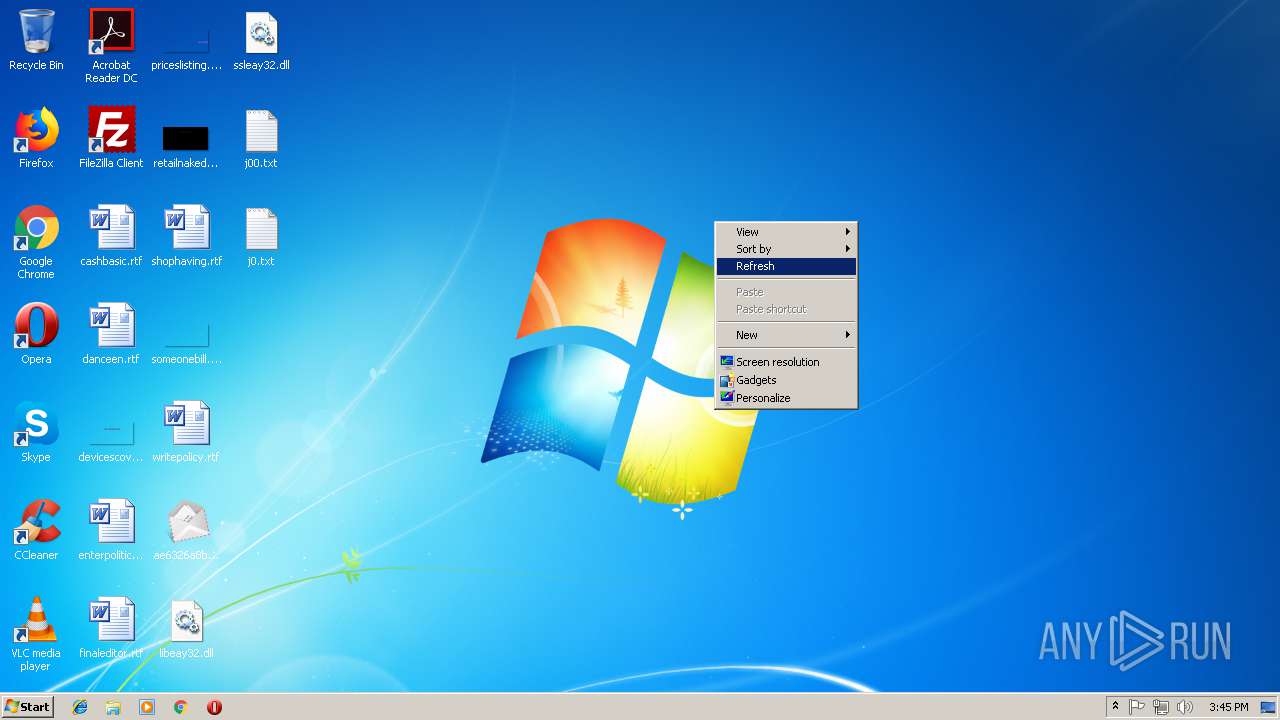
| Verdict: | Malicious activity |
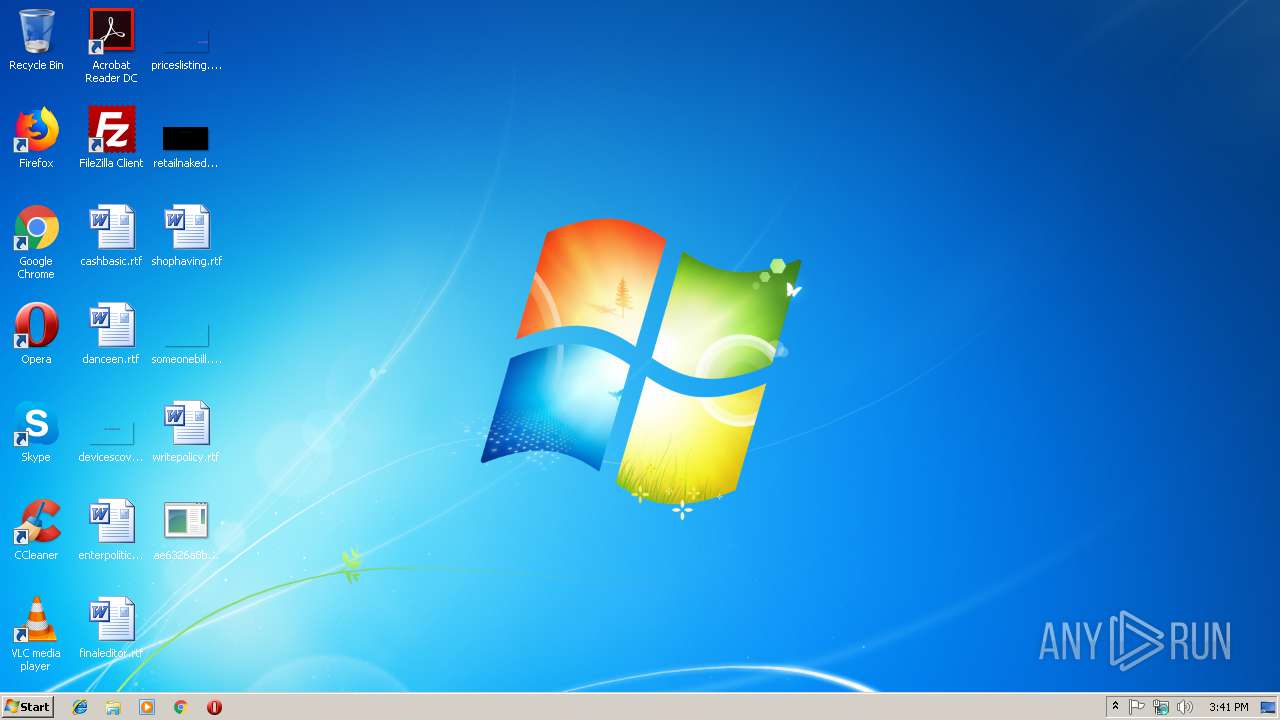
| Analysis date: | December 14, 2018, 15:41:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 47A026D93AE8E0CC292E8D7A71DDC89E |
| SHA1: | 3DC2E43549705DB2795DFC969100DC480272C66F |
| SHA256: | AE6326A8B0297DC6EFF583F2305ABAEAB0347A3AEF95FC51C5D76708CF32B73F |
| SSDEEP: | 49152:/WmzvvmoVQXuSaD6U1JTU/HH2DCWijV+wpNX2+PmLRL7tP6LCXCWh:/WwvjtJo/s7UV+ezPmyL87h |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1904)
- ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe (PID: 3816)
Changes the autorun value in the registry
- reg.exe (PID: 3468)
SUSPICIOUS
Executable content was dropped or overwritten
- ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe (PID: 3816)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2872)
Starts CMD.EXE for commands execution
- ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe (PID: 3816)
Connects to unusual port
- ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe (PID: 3816)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (62.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (23.7) |
| .scr | | | Windows screen saver (7.4) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:05 00:45:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2522112 |
| InitializedDataSize: | 2321920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2690b8 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.19.9593.18224 |
| ProductVersionNumber: | 6.19.9593.18224 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | © Microsoft Corporation |
| FileDescription: | Mail SSL Connection Serv |
| FileVersion: | 6.19.9593.18224 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved |
| OriginalFileName: | wmssl.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.19.9593.18224 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-May-2018 22:45:19 |
| Detected languages: |
|
| CompanyName: | © Microsoft Corporation |
| FileDescription: | Mail SSL Connection Serv |
| FileVersion: | 6.19.9593.18224 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved |
| OriginalFilename: | wmssl.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.19.9593.18224 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 04-May-2018 22:45:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x002658A4 | 0x00265A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45005 |
.itext | 0x00267000 | 0x00002118 | 0x00002200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.1776 |
.data | 0x0026A000 | 0x00009838 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.35983 |
.bss | 0x00274000 | 0x000057B4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0027A000 | 0x00003AC4 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.51381 |
.didata | 0x0027E000 | 0x000009A6 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.12822 |
.edata | 0x0027F000 | 0x0000005E | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.09973 |
.tls | 0x00280000 | 0x00000040 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00281000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.170146 |
.reloc | 0x00282000 | 0x000372BC | 0x00037400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86531 | 714 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.79233 | 304 | UNKNOWN | English - United States | RT_ICON |
3 | 2.67122 | 176 | UNKNOWN | English - United States | RT_ICON |
4 | 2.53632 | 1640 | UNKNOWN | English - United States | RT_ICON |
5 | 2.74735 | 744 | UNKNOWN | English - United States | RT_ICON |
6 | 2.80662 | 488 | UNKNOWN | English - United States | RT_ICON |
7 | 2.70561 | 296 | UNKNOWN | English - United States | RT_ICON |
8 | 3.93372 | 3752 | UNKNOWN | English - United States | RT_ICON |
9 | 3.49872 | 2216 | UNKNOWN | English - United States | RT_ICON |
10 | 2.88117 | 1736 | UNKNOWN | English - United States | RT_ICON |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x00062430 |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1904 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | cmd /c ""C:\Users\admin\Desktop\registr.bat" " | C:\Windows\system32\cmd.exe | — | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | reg add HKCU\Environment /v "UserInitMprLogonScript" /t REG_EXPAND_SZ /d "C:\Users\admin\Desktop\ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | "C:\Users\admin\Desktop\ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe" | C:\Users\admin\Desktop\ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | explorer.exe | ||||||||||||
User: admin Company: © Microsoft Corporation Integrity Level: MEDIUM Description: Mail SSL Connection Serv Exit code: 0 Version: 6.19.9593.18224 Modules
| |||||||||||||||
Total events
46
Read events
39
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3816) ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3816) ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1904) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1904) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (3468) reg.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | UserInitMprLogonScript |
Value: C:\Users\admin\Desktop\ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | |||
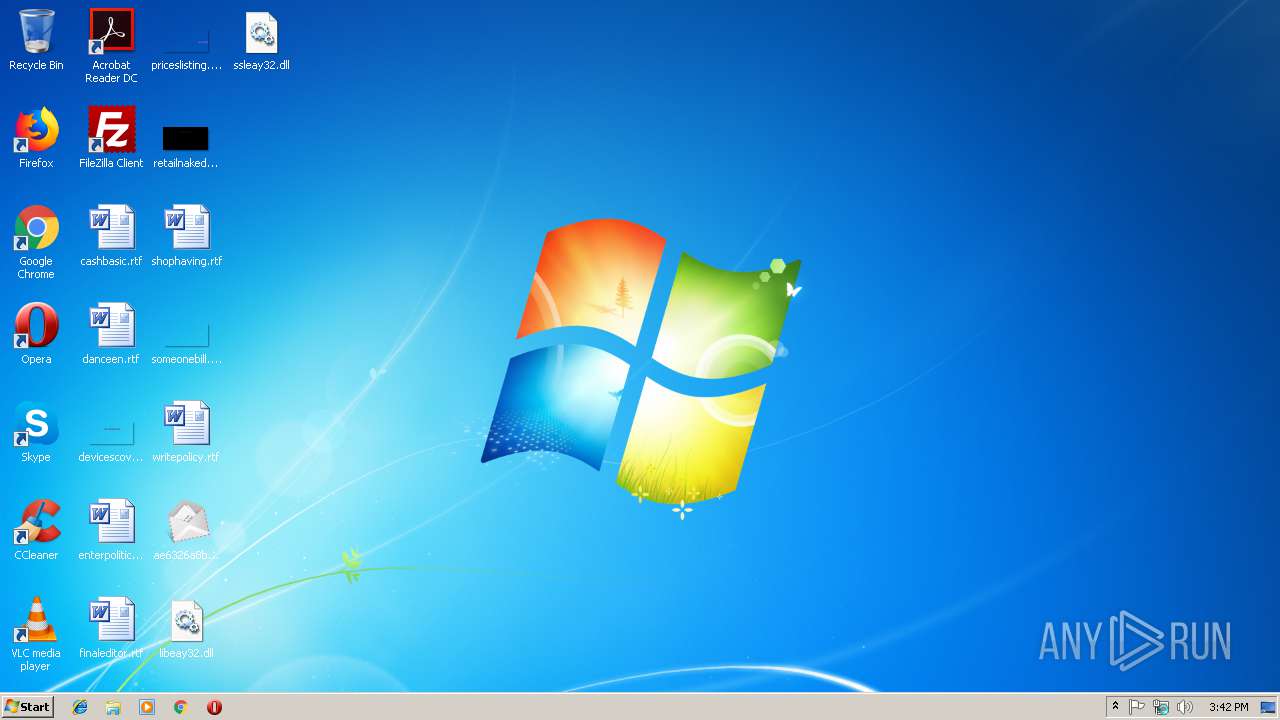
Executable files
2
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | C:\Users\admin\Desktop\registr.bat | text | |
MD5:— | SHA256:— | |||
| 3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | C:\Users\admin\Desktop\l30.dat | text | |
MD5:— | SHA256:— | |||
| 3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | C:\Users\admin\Desktop\j00.txt | text | |
MD5:— | SHA256:— | |||
| 3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | C:\Users\admin\Desktop\j0.txt | text | |
MD5:21438EF4B9AD4FC266B6129A2F60DE29 | SHA256:13BF7B3039C63BF5A50491FA3CFD8EB4E699D1BA1436315AEF9CBE5711530354 | |||
| 3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | C:\Users\admin\Desktop\ssleay32.dll | executable | |
MD5:30D2D646266BA7EE64689F263B9C297D | SHA256:494E06380DC07ACFCC7F8B80C49DFA0D5F5C1B391742D3A4C4DBBE42F2845AD7 | |||
| 3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | C:\Users\admin\Desktop\libeay32.dll | executable | |
MD5:CC655EB0F4916668820269271CE09DBE | SHA256:56F69B6D7FAE68E7C6AAC88AE68D8A9DCE0C4299CFE8635B2138E45433C75D53 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | 185.25.51.38:465 | ambcomission.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
3816 | ae6326a8b0297dc6eff583f2305abaeab0347a3aef95fc51c5d76708cf32b73f.exe | 185.25.51.38:995 | ambcomission.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ambcomission.com |
| unknown |