| File name: | ae5fa327c0dcd0c7c8bc3674c2d72416a8c487e34e27552f4b9ca393d32ecaff |
| Full analysis: | https://app.any.run/tasks/7c1360bd-e3fa-43c5-8baa-da2260f9cc3e |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 24, 2019, 06:35:01 |
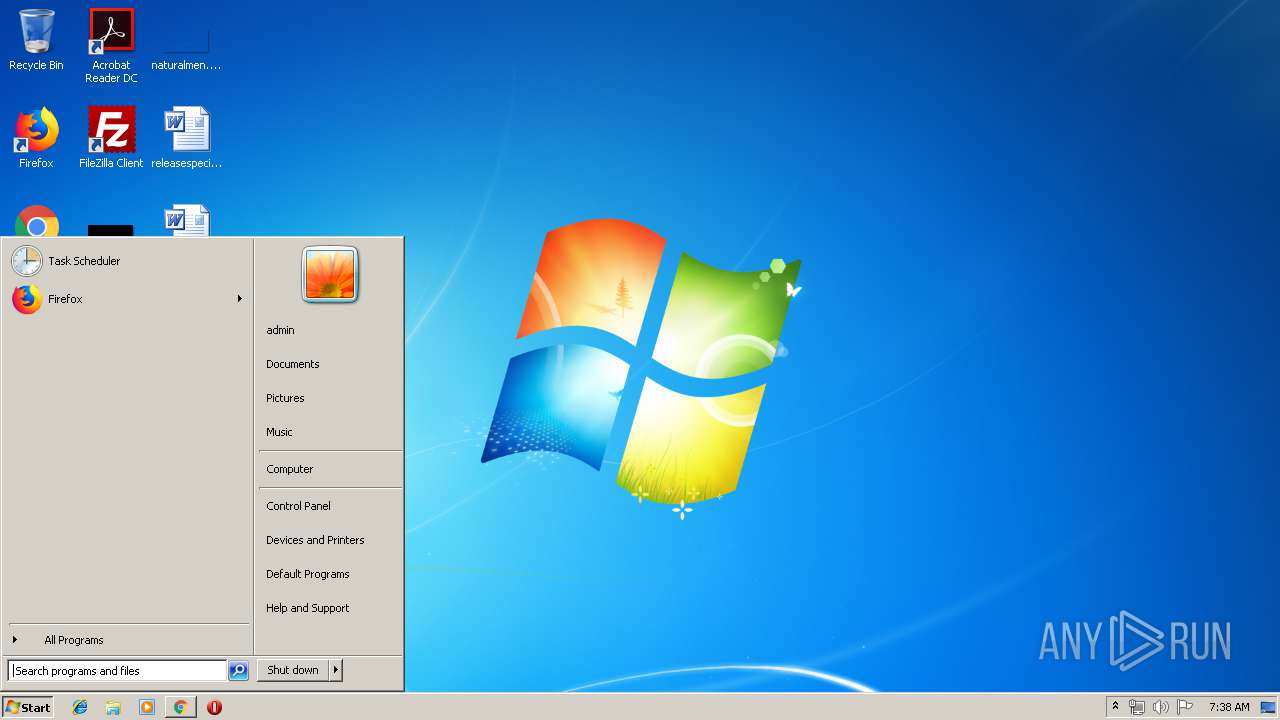
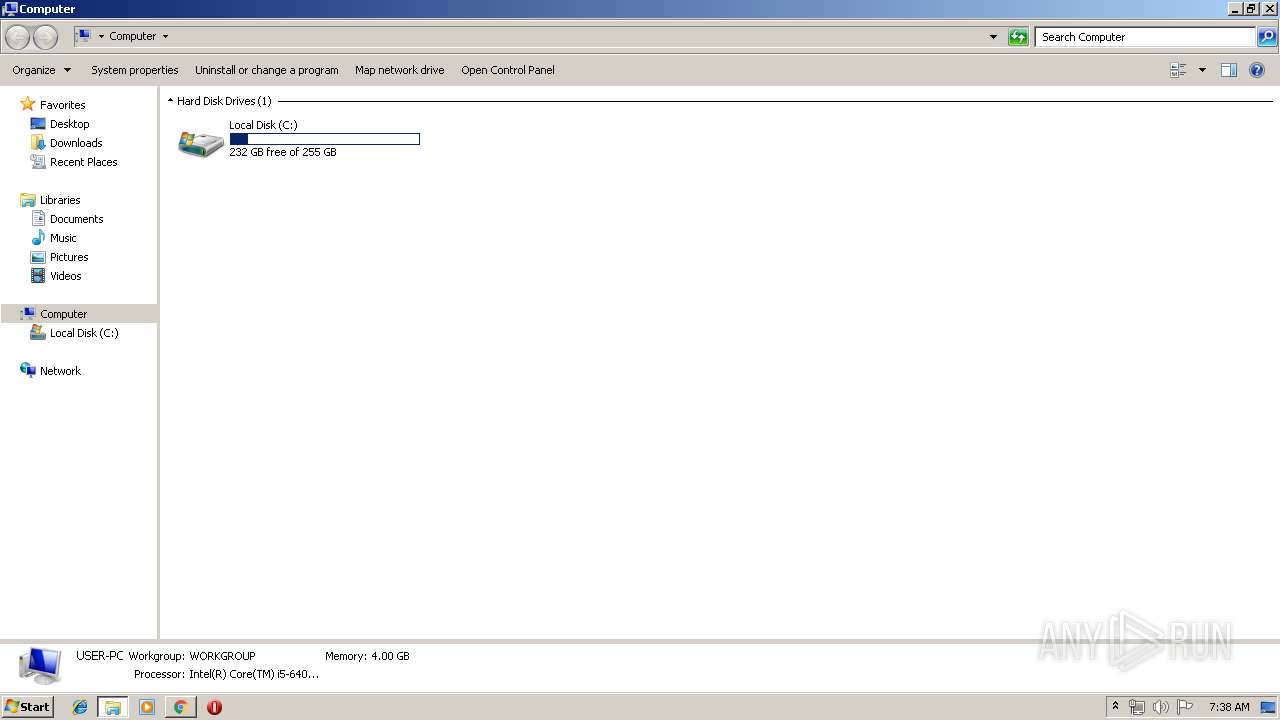
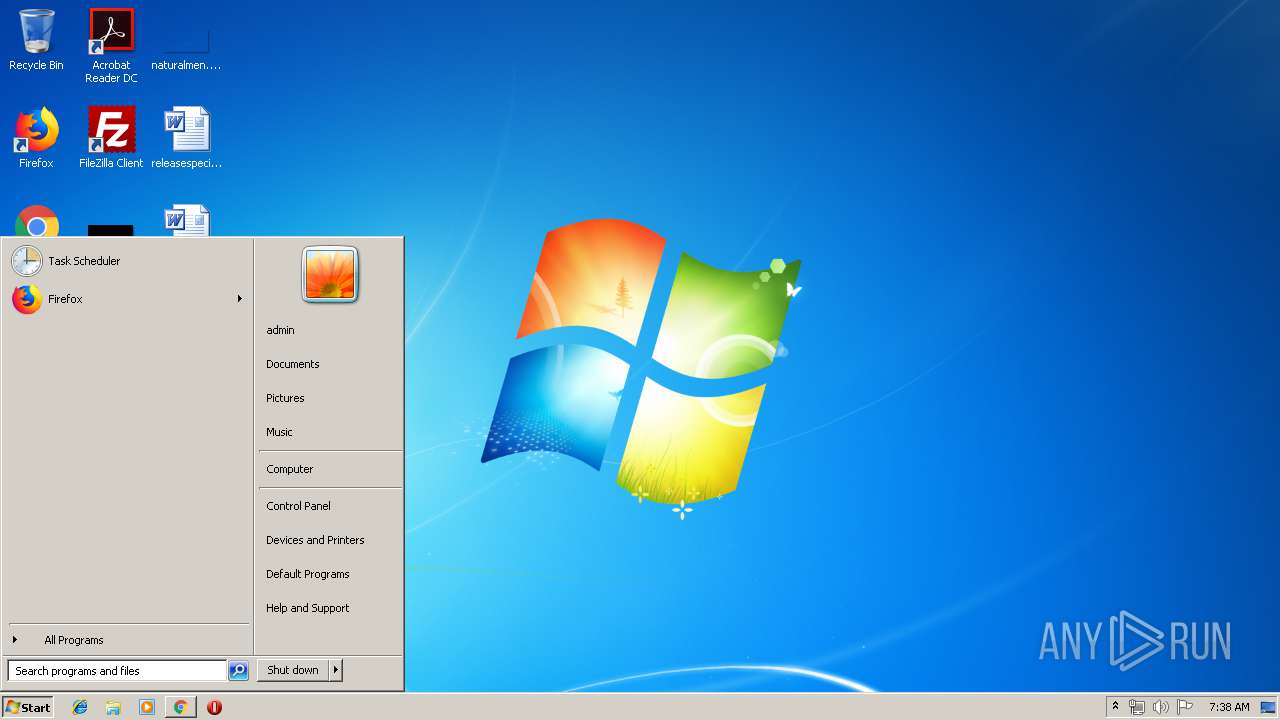
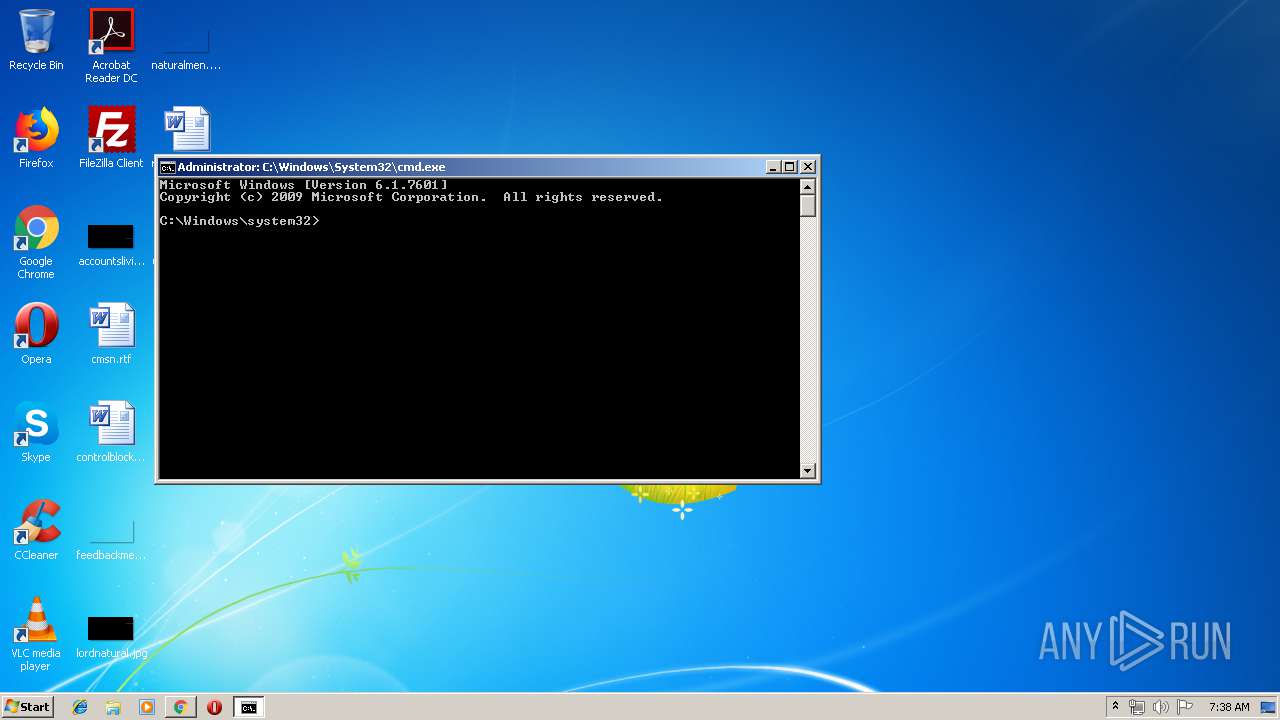
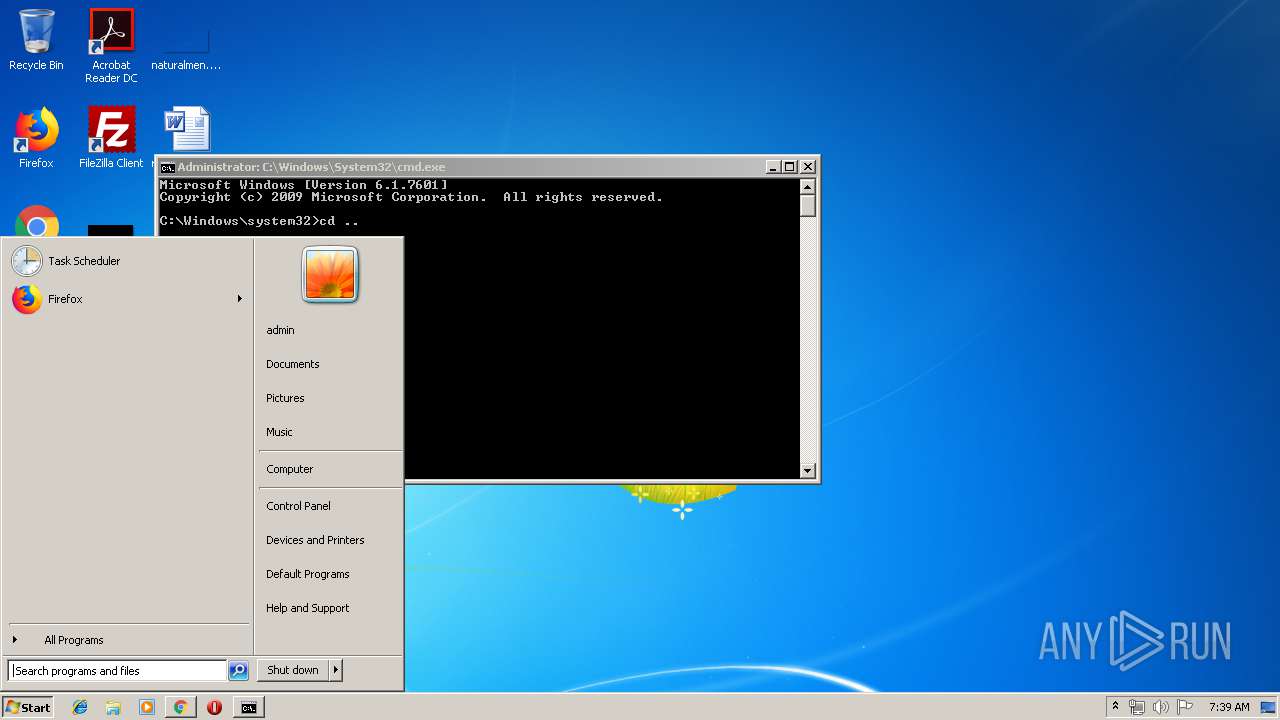
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0B14D98C827EA8E2256DC7BE46BF1712 |
| SHA1: | 8EC615A36BD11984346C1D90724C82C16EC20735 |
| SHA256: | AE5FA327C0DCD0C7C8BC3674C2D72416A8C487E34E27552F4B9CA393D32ECAFF |
| SSDEEP: | 3072:mqJobgNTvIixmFCpbjxfOugLE4Ze/FO+VQDUcUNWs+jm6ts:NLv5IodfVgLQ/FfMBghAml |
MALICIOUS
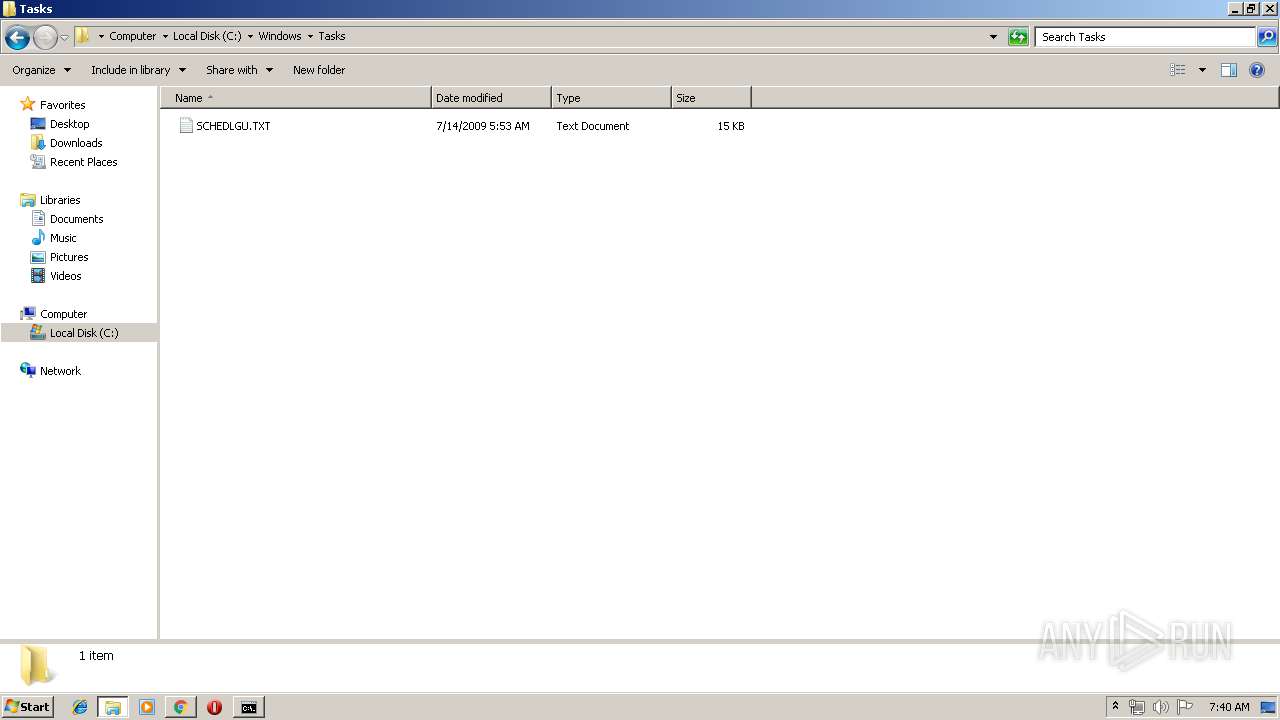
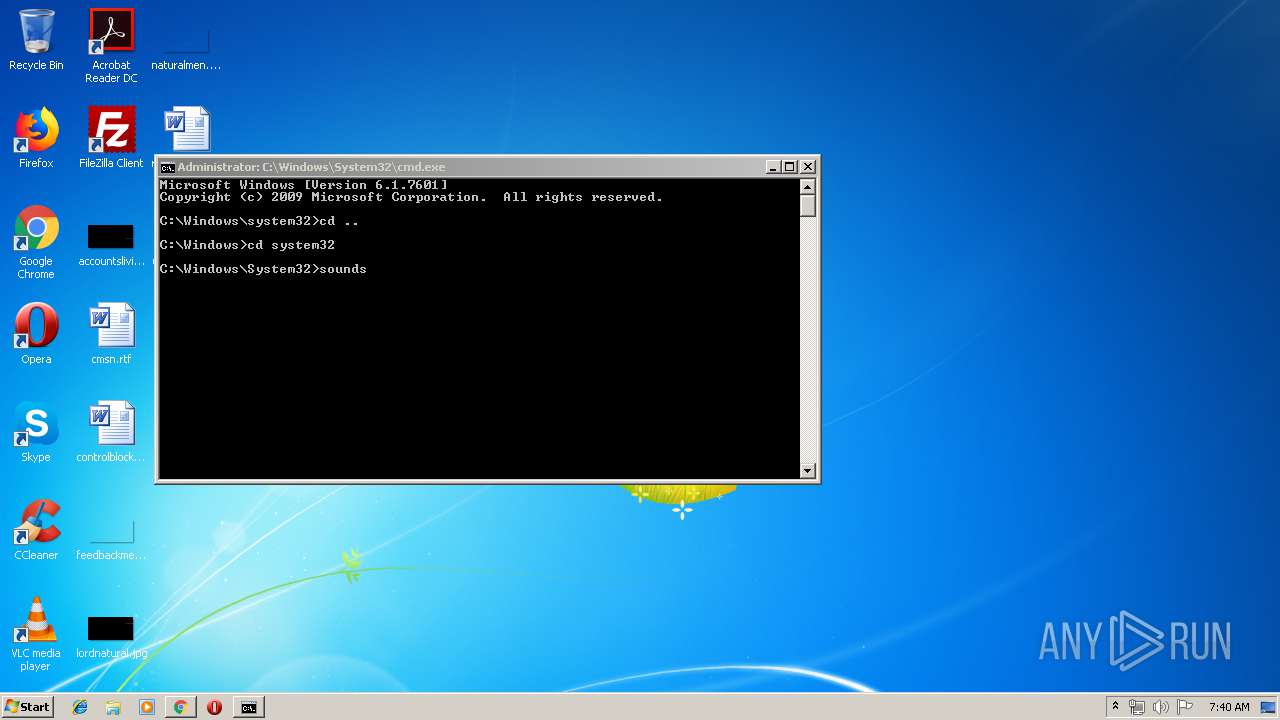
EMOTET was detected
- soundser.exe (PID: 3756)
Emotet process was detected
- soundser.exe (PID: 2796)
Changes the autorun value in the registry
- soundser.exe (PID: 3756)
Connects to CnC server
- soundser.exe (PID: 3756)
SUSPICIOUS
Application launched itself
- ae5fa327c0dcd0c7c8bc3674c2d72416a8c487e34e27552f4b9ca393d32ecaff.exe (PID: 1084)
- soundser.exe (PID: 2796)
Starts itself from another location
- ae5fa327c0dcd0c7c8bc3674c2d72416a8c487e34e27552f4b9ca393d32ecaff.exe (PID: 3728)
Connects to server without host name
- soundser.exe (PID: 3756)
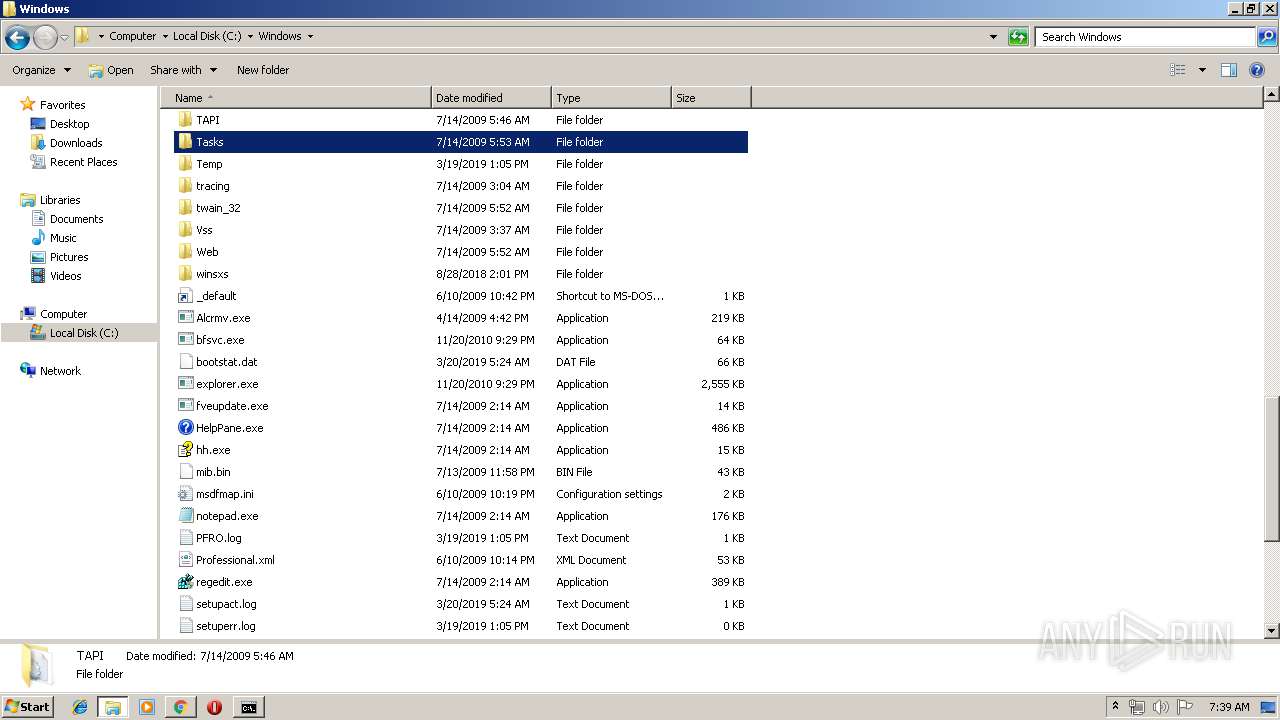
Executable content was dropped or overwritten
- ae5fa327c0dcd0c7c8bc3674c2d72416a8c487e34e27552f4b9ca393d32ecaff.exe (PID: 3728)
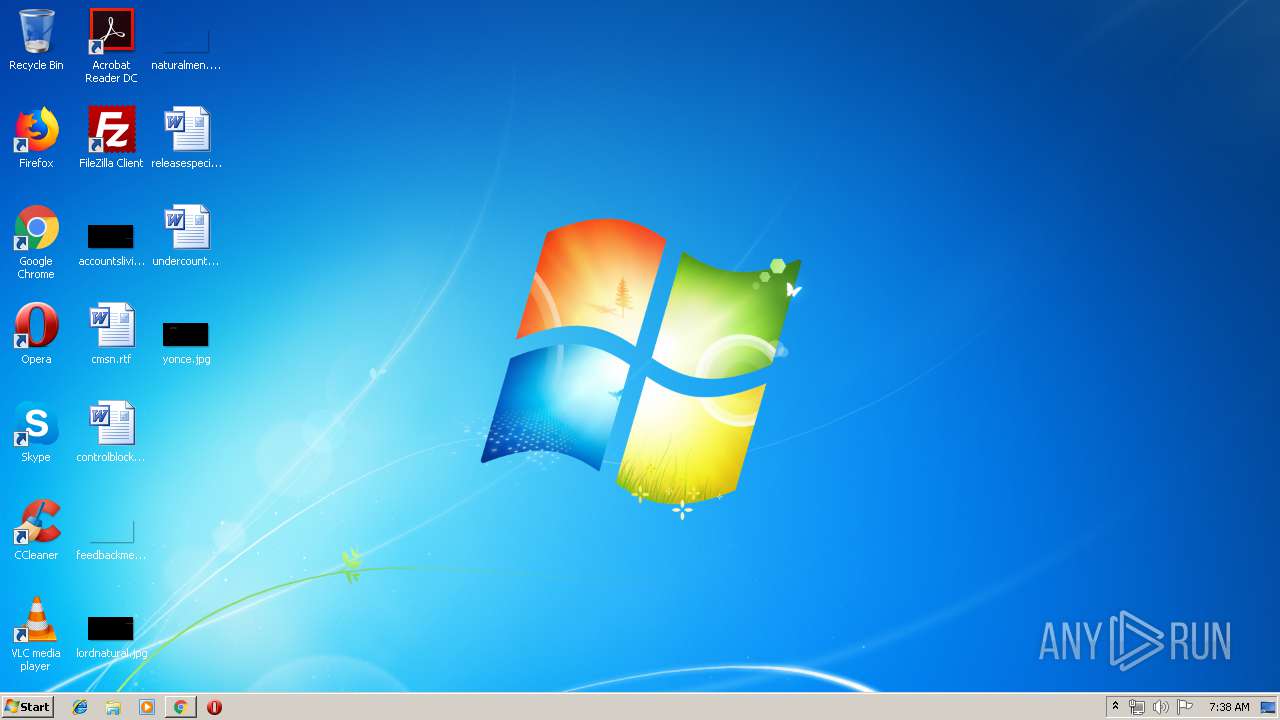
Modifies files in Chrome extension folder
- chrome.exe (PID: 3180)
INFO
Application launched itself
- chrome.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (50.4) |
|---|---|---|
| .exe | | | InstallShield setup (16.1) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (11.6) |
| .exe | | | Win64 Executable (generic) (10.3) |
| .scr | | | Windows screen saver (4.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:24 07:23:21+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 6144 |
| InitializedDataSize: | 184832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2530 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.7600.16385 |
| ProductVersionNumber: | 6.1.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Memory Diagnostic |
| FileVersion: | 6.1.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | MdRes.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | MdRes.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7600.16385 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Apr-2018 05:23:21 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Memory Diagnostic |
| FileVersion: | 6.1.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | MdRes.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | MdRes.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7600.16385 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 24-Apr-2018 05:23:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000016EE | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73408 |
.rdata | 0x00003000 | 0x000000AC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.68869 |
.data | 0x00004000 | 0x0001B698 | 0x0001B600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.00746 |
.rsrc | 0x00020000 | 0x00011748 | 0x00011800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.07954 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.57424 | 912 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.58831 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.46778 | 488 | UNKNOWN | English - United States | RT_ICON |
4 | 2.28325 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 5.36778 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 5.89219 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 5.00505 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 2.49618 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 7.9776 | 38200 | UNKNOWN | English - United States | RT_ICON |
10 | 4.94612 | 9640 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
Total processes
61
Monitored processes
24
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --service-pipe-token=7969862703127450368 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7969862703127450368 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5663029019333388896 --mojo-platform-channel-handle=4348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3312702929826115961 --mojo-platform-channel-handle=2876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1084 | "C:\Users\admin\AppData\Local\Temp\ae5fa327c0dcd0c7c8bc3674c2d72416a8c487e34e27552f4b9ca393d32ecaff.exe" --46234477 | C:\Users\admin\AppData\Local\Temp\ae5fa327c0dcd0c7c8bc3674c2d72416a8c487e34e27552f4b9ca393d32ecaff.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa60f18,0x6fa60f28,0x6fa60f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3184 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5799134866275758962 --mojo-platform-channel-handle=2336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13429359172945981158 --mojo-platform-channel-handle=3104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=120780683977713065 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,9590772959286727987,1416632359325823009,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1685366317759669918 --mojo-platform-channel-handle=2348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
629
Read events
521
Write events
103
Delete events
5
Modification events
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
57
Text files
101
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c9d6b2af-67d7-4130-af50-d32d99a915e5.tmp | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
16
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3180 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 510 b | whitelisted |
3756 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/symbols/vermont/ | US | — | — | malicious |
3756 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/xian/site/ringin/ | US | — | — | malicious |
3180 | chrome.exe | GET | 200 | 87.245.198.13:80 | http://r2---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=91.221.66.140&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1556087249&mv=u&pl=23&shardbypass=yes | RU | crx | 842 Kb | whitelisted |
3756 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/results/bml/ringin/ | CW | binary | 148 b | malicious |
3756 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/prov/usbccid/ringin/merge/ | CW | binary | 66.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3180 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 87.245.198.13:80 | r2---sn-gxuog0-axqe.gvt1.com | RETN Limited | RU | whitelisted |
3180 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 216.58.206.3:443 | www.google.de | Google Inc. | US | whitelisted |
3756 | soundser.exe | 68.229.130.39:80 | — | Cox Communications Inc. | US | malicious |
3180 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 172.217.22.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3180 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3756 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 11 |
3756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3756 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3756 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3756 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
12 ETPRO signatures available at the full report