| File name: | parsec-windows.exe |
| Full analysis: | https://app.any.run/tasks/057d373e-5975-422b-8a10-4c0d1fee3699 |
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2024, 12:10:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 01EF58E7C144C701B2EA01CFC049DBE4 |
| SHA1: | 2F572ACCB519096C9EA805812BA53703C16CCEEA |
| SHA256: | AE5B66322E5A7C26AD21CCC556BDC1618796166565D2939142C5AA3D76C38ACE |
| SSDEEP: | 98304:3PgwkW/21bBYyUc4DJj3iWLhOtvwWprCD7DpCQJzZFmRrQQSrLhdtjB2MzxuPhzC:3/c |
MALICIOUS
Drops the executable file immediately after the start
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- nefconw.exe (PID: 3624)
- drvinst.exe (PID: 5952)
- nefconw.exe (PID: 4216)
- parsec-vdd.exe (PID: 7164)
- drvinst.exe (PID: 6628)
- nefconw.exe (PID: 6468)
- parsecd.exe (PID: 7044)
- drvinst.exe (PID: 1856)
- parsecd.exe (PID: 4720)
Creates a writable file in the system directory
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 6628)
- pservice.exe (PID: 3976)
- drvinst.exe (PID: 1856)
Changes the autorun value in the registry
- nefconw.exe (PID: 4216)
- parsecd.exe (PID: 4720)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- parsec-vdd.exe (PID: 7164)
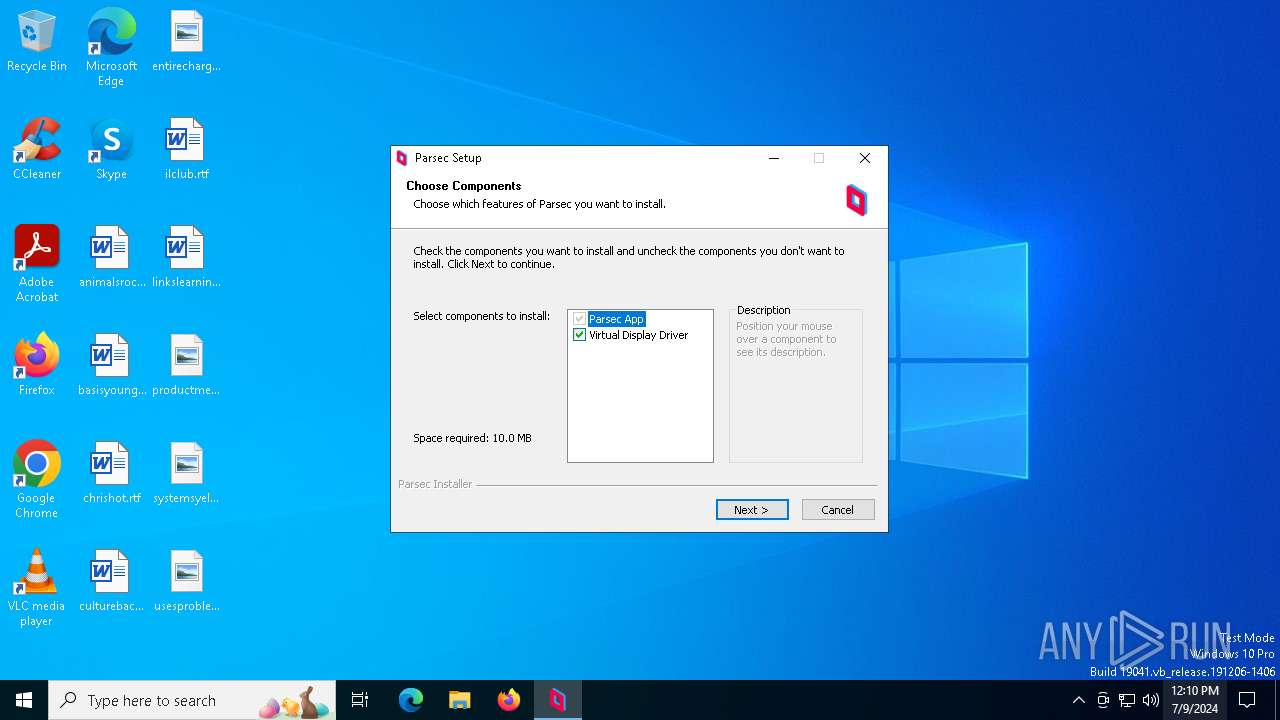
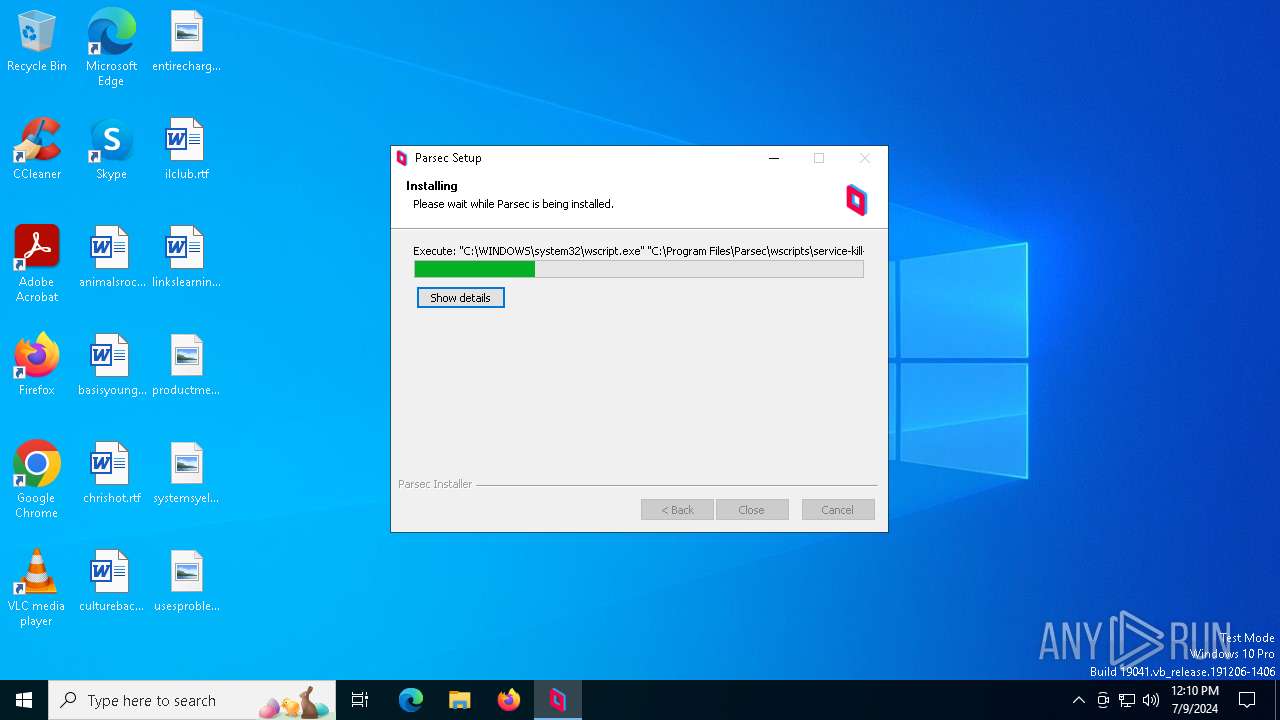
The process executes VB scripts
- parsec-windows.exe (PID: 5240)
Uses TASKKILL.EXE to kill process
- wscript.exe (PID: 5236)
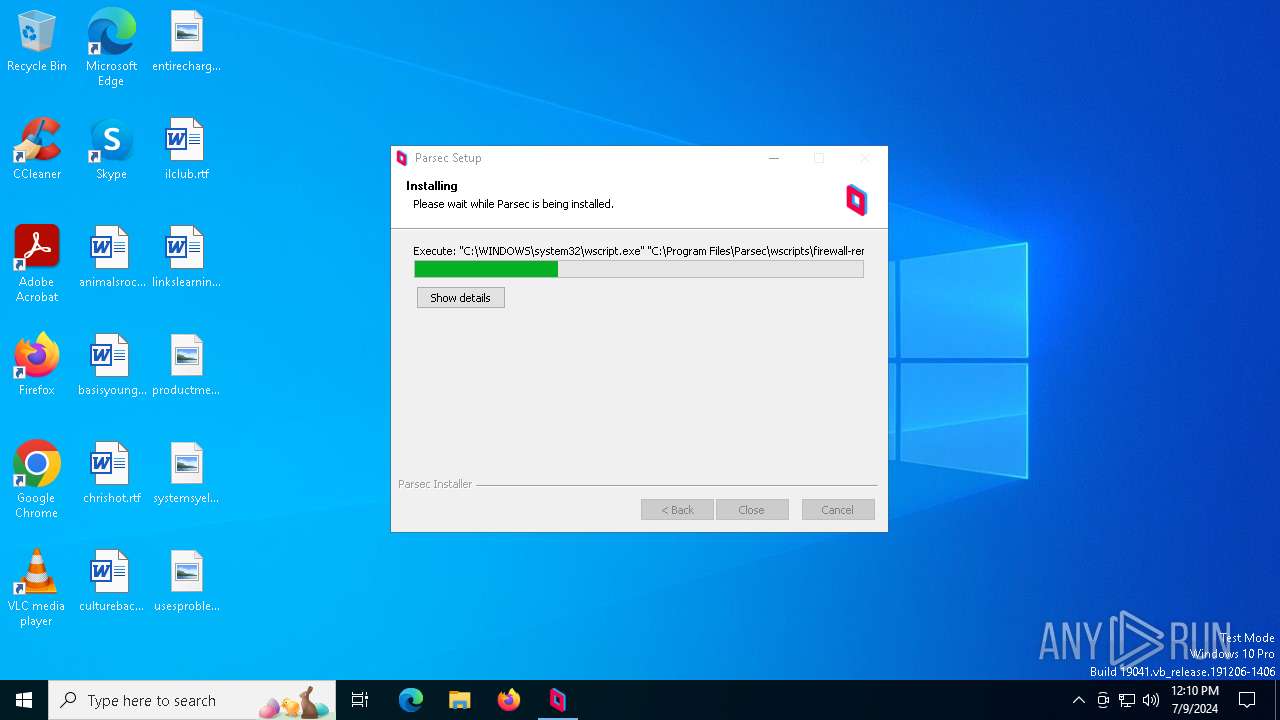
Uses NETSH.EXE to delete a firewall rule or allowed programs
- wscript.exe (PID: 4084)
Executable content was dropped or overwritten
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- nefconw.exe (PID: 3624)
- drvinst.exe (PID: 5952)
- nefconw.exe (PID: 4216)
- drvinst.exe (PID: 1856)
- parsec-vdd.exe (PID: 7164)
- nefconw.exe (PID: 6468)
- drvinst.exe (PID: 6628)
- parsecd.exe (PID: 7044)
- parsecd.exe (PID: 4720)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2632)
- wscript.exe (PID: 4084)
- wscript.exe (PID: 2364)
Runs shell command (SCRIPT)
- wscript.exe (PID: 476)
- wscript.exe (PID: 1832)
- wscript.exe (PID: 5236)
- wscript.exe (PID: 2632)
- wscript.exe (PID: 4084)
- wscript.exe (PID: 2364)
The process creates files with name similar to system file names
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- parsec-vdd.exe (PID: 7164)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5004)
Creates a software uninstall entry
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- parsec-vdd.exe (PID: 7164)
Uses NETSH.EXE to add a firewall rule or allowed programs
- wscript.exe (PID: 2364)
Starts CMD.EXE for commands execution
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- parsec-vdd.exe (PID: 7164)
Drops a system driver (possible attempt to evade defenses)
- parsec-vud.exe (PID: 992)
- nefconw.exe (PID: 3624)
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 1856)
- nefconw.exe (PID: 4216)
Executes as Windows Service
- pservice.exe (PID: 3976)
- WUDFHost.exe (PID: 5896)
Executing commands from a ".bat" file
- parsec-vud.exe (PID: 992)
- parsec-vdd.exe (PID: 7164)
Creates files in the driver directory
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 1856)
- drvinst.exe (PID: 6628)
Checks Windows Trust Settings
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 6628)
- drvinst.exe (PID: 1856)
- parsecd.exe (PID: 7044)
- parsecd.exe (PID: 4720)
- parsecd.exe (PID: 3232)
- pservice.exe (PID: 3976)
Creates or modifies Windows services
- drvinst.exe (PID: 1048)
- drvinst.exe (PID: 3944)
- drvinst.exe (PID: 6984)
- drvinst.exe (PID: 6604)
Uses WEVTUTIL.EXE to remove publishers and event logs from the manifest
- parsec-vdd.exe (PID: 7164)
- wevtutil.exe (PID: 4720)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- parsec-vdd.exe (PID: 7164)
- wevtutil.exe (PID: 420)
Reads security settings of Internet Explorer
- parsecd.exe (PID: 7044)
Uses RUNDLL32.EXE to load library
- parsecd.exe (PID: 3232)
INFO
Creates files in the program directory
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- parsec-vdd.exe (PID: 7164)
- parsecd.exe (PID: 3232)
Reads the computer name
- parsec-windows.exe (PID: 5240)
- pservice.exe (PID: 3976)
- nefconw.exe (PID: 4196)
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 1048)
- nefconw.exe (PID: 3624)
- nefconw.exe (PID: 4216)
- drvinst.exe (PID: 3944)
- drvinst.exe (PID: 1856)
- drvinst.exe (PID: 6984)
- nefconw.exe (PID: 2896)
- nefconw.exe (PID: 6704)
- nefconw.exe (PID: 6468)
- drvinst.exe (PID: 6628)
- drvinst.exe (PID: 6604)
- parsecd.exe (PID: 7044)
- parsecd.exe (PID: 4720)
- parsecd.exe (PID: 3232)
- identity_helper.exe (PID: 8180)
Checks supported languages
- parsec-windows.exe (PID: 5240)
- pservice.exe (PID: 3976)
- nefconc.exe (PID: 6036)
- parsec-vud.exe (PID: 992)
- nefconw.exe (PID: 4196)
- nefconw.exe (PID: 3624)
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 1048)
- nefconw.exe (PID: 4216)
- drvinst.exe (PID: 3944)
- drvinst.exe (PID: 1856)
- drvinst.exe (PID: 6984)
- parsec-vdd.exe (PID: 7164)
- nefconw.exe (PID: 2896)
- nefconw.exe (PID: 6704)
- drvinst.exe (PID: 6628)
- nefconw.exe (PID: 6468)
- drvinst.exe (PID: 6604)
- parsecd.exe (PID: 7044)
- parsecd.exe (PID: 4720)
- parsecd.exe (PID: 3232)
- identity_helper.exe (PID: 8180)
Create files in a temporary directory
- parsec-windows.exe (PID: 5240)
- parsec-vud.exe (PID: 992)
- nefconw.exe (PID: 3624)
- nefconw.exe (PID: 4216)
- parsec-vdd.exe (PID: 7164)
- nefconw.exe (PID: 6468)
Reads the software policy settings
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 1856)
- drvinst.exe (PID: 6628)
- pservice.exe (PID: 3976)
- parsecd.exe (PID: 7044)
- parsecd.exe (PID: 4720)
- parsecd.exe (PID: 3232)
Reads the machine GUID from the registry
- drvinst.exe (PID: 5952)
- drvinst.exe (PID: 1856)
- drvinst.exe (PID: 6628)
- parsecd.exe (PID: 7044)
- pservice.exe (PID: 3976)
- parsecd.exe (PID: 4720)
- parsecd.exe (PID: 3232)
Reads the time zone
- runonce.exe (PID: 6528)
Reads security settings of Internet Explorer
- runonce.exe (PID: 6528)
- rundll32.exe (PID: 5248)
Creates files or folders in the user directory
- parsecd.exe (PID: 7044)
- parsecd.exe (PID: 4720)
- parsecd.exe (PID: 3232)
Checks proxy server information
- parsecd.exe (PID: 7044)
Reads Microsoft Office registry keys
- rundll32.exe (PID: 5248)
- msedge.exe (PID: 7136)
Application launched itself
- msedge.exe (PID: 7136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 150.93.2.0 |
| ProductVersionNumber: | 150.93.2.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Parsec |
| FileVersion: | 150.93.2.0 |
| ProductName: | Parsec |
Total processes
242
Monitored processes
98
Malicious processes
15
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wevtutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | wevtutil im "C:\Program Files\Parsec Virtual Display Driver\mm.man" | C:\Windows\SysWOW64\wevtutil.exe | — | parsec-vdd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2616 --field-trial-handle=2432,i,18192458963900716163,13435066415303771696,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 476 | "C:\Users\admin\AppData\Local\Temp\parsec-windows.exe" | C:\Users\admin\AppData\Local\Temp\parsec-windows.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Parsec Exit code: 3221226540 Version: 150.93.2.0 Modules
| |||||||||||||||
| 476 | "C:\WINDOWS\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\service-remove.vbs" | C:\Windows\SysWOW64\wscript.exe | — | parsec-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Parsec\vusb\parsec-vud.exe" /S | C:\Program Files\Parsec\vusb\parsec-vud.exe | cmd.exe | ||||||||||||
User: admin Company: Parsec Cloud Inc. Integrity Level: HIGH Description: Parsec Virtual USB Adapter Driver Exit code: 0 Version: 0.2.8.0 Modules
| |||||||||||||||
| 1048 | DrvInst.exe "2" "201" "ROOT\USB\0000" "C:\WINDOWS\System32\DriverStore\FileRepository\parsecvusba.inf_amd64_dae154cc0d6f64e9\parsecvusba.inf" "oem1.inf:*:*:0.2.8.0:Root\Parsec\VUSBA," "464910f03" "00000000000001E0" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files\Parsec Virtual Display Driver\vddinstall.bat"" | C:\Windows\SysWOW64\cmd.exe | — | parsec-vdd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | "C:\Windows\System32\netsh.exe" advfirewall firewall delete rule name=parsec.exe | C:\Windows\SysWOW64\netsh.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 663
Read events
49 366
Write events
259
Delete events
38
Modification events
| (PID) Process: | (5236) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5236) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5236) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5236) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (476) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (476) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (476) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (476) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4084) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4084) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
40
Suspicious files
117
Text files
58
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\firewall-remove.vbs | text | |
MD5:5D4D70CDF36FCDAA292DA1DA9133320C | SHA256:75F1DECE4FDA689A907F6D74B513ADB0C1771C1B79EA71160179542C9C4AB2F0 | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\service-remove.vbs | text | |
MD5:B90E75DD7903CB2D6328BB3714865C7A | SHA256:970B3C2A9EA1906A177810990478932E3517F47ABA267CF2AB9E4BA65E7B475F | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\legacy-cleanup.vbs | text | |
MD5:C78520C3162C1962F3164714B37EB4D0 | SHA256:DEA38BD553ABE93C689DE42D0220ADD18F9BE3E3D2FA53F97EB8649F586DF4F3 | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\firewall-add.vbs | text | |
MD5:882374285898F16B5F9FF44AFC1AE701 | SHA256:0BE5AA5CC6395A86878F56B131E13DB4908E48F06E892FF8F8CF9E2D3B6C8ABB | |||
| 5240 | parsec-windows.exe | C:\Users\admin\AppData\Local\Temp\nsyAE1.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\service-install.vbs | text | |
MD5:971E2A344A6E17347A81EEB21ADA7BA7 | SHA256:01F62A12DE3307B375DFF3EBCD6961D76FFCBC24F70682C7875655A811CE76A1 | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\vusb\parsec-vud.exe | executable | |
MD5:2D009D446A0BA83EC2F12242F7ED126C | SHA256:436088A5EB416935D7BD452E4E53123C2E65B737EAB7D98EBE1913618F95E61B | |||
| 5240 | parsec-windows.exe | C:\Users\admin\AppData\Local\Temp\nsyAE1.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\wscripts\service-kill-parsec.vbs | text | |
MD5:F7B0C63E7AEA5CBD96F7BF1021B28B73 | SHA256:71F9CC28497B959377439F6611615EF582745DD5B9CCA02B5C4B24BB1FC3DFB8 | |||
| 5240 | parsec-windows.exe | C:\Program Files\Parsec\skel\appdata.json | binary | |
MD5:2C669AF7EE4ADEDDF72FA0102AA0378D | SHA256:CD5D52066766B7F0FD7222E551A96C539F17C72DEBD32F8DA9F76DF4627A6DD5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
119
DNS requests
88
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1888 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1888 | svchost.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6068 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
7044 | parsecd.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | unknown |
7044 | parsecd.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | unknown |
7044 | parsecd.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAloEugzUPGt9OnVZ%2FPPgls%3D | unknown | — | — | unknown |
3976 | pservice.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | unknown |
3976 | pservice.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | unknown |
3976 | pservice.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAloEugzUPGt9OnVZ%2FPPgls%3D | unknown | — | — | unknown |
4264 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1776 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1888 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1888 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1888 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1888 | svchost.exe | 104.119.109.218:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
builds.parsec.app |
| unknown |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |