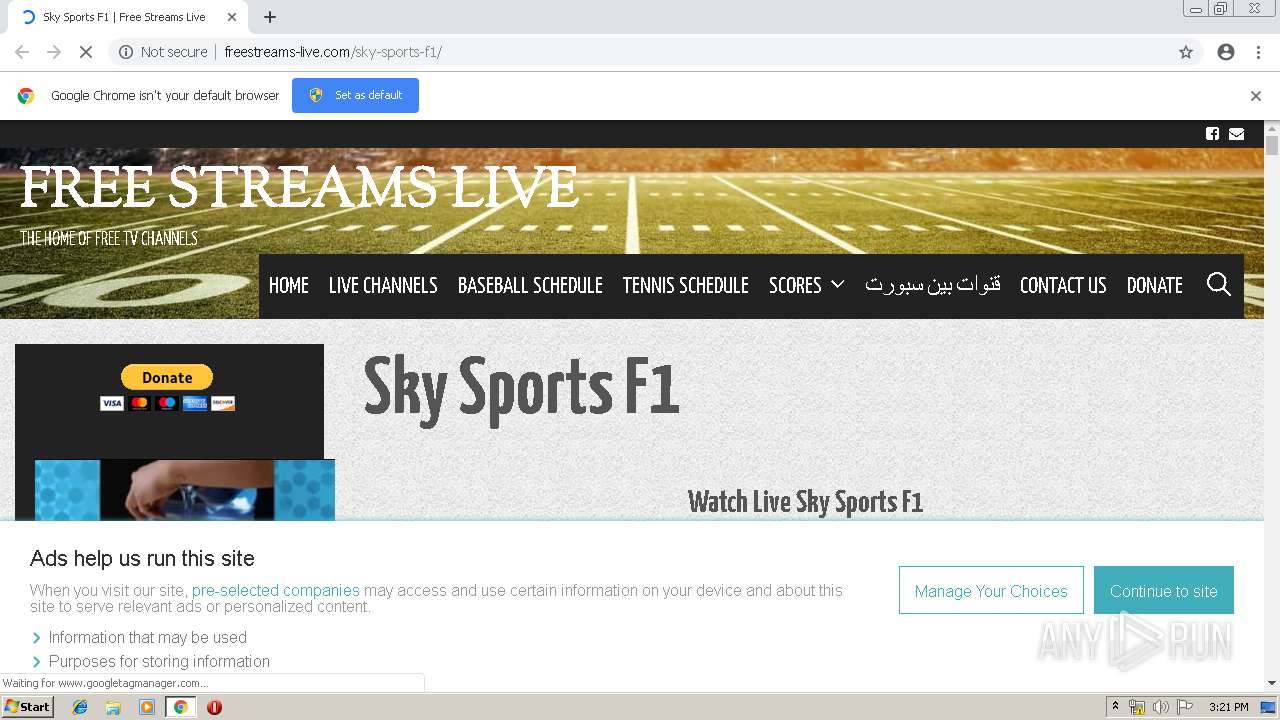
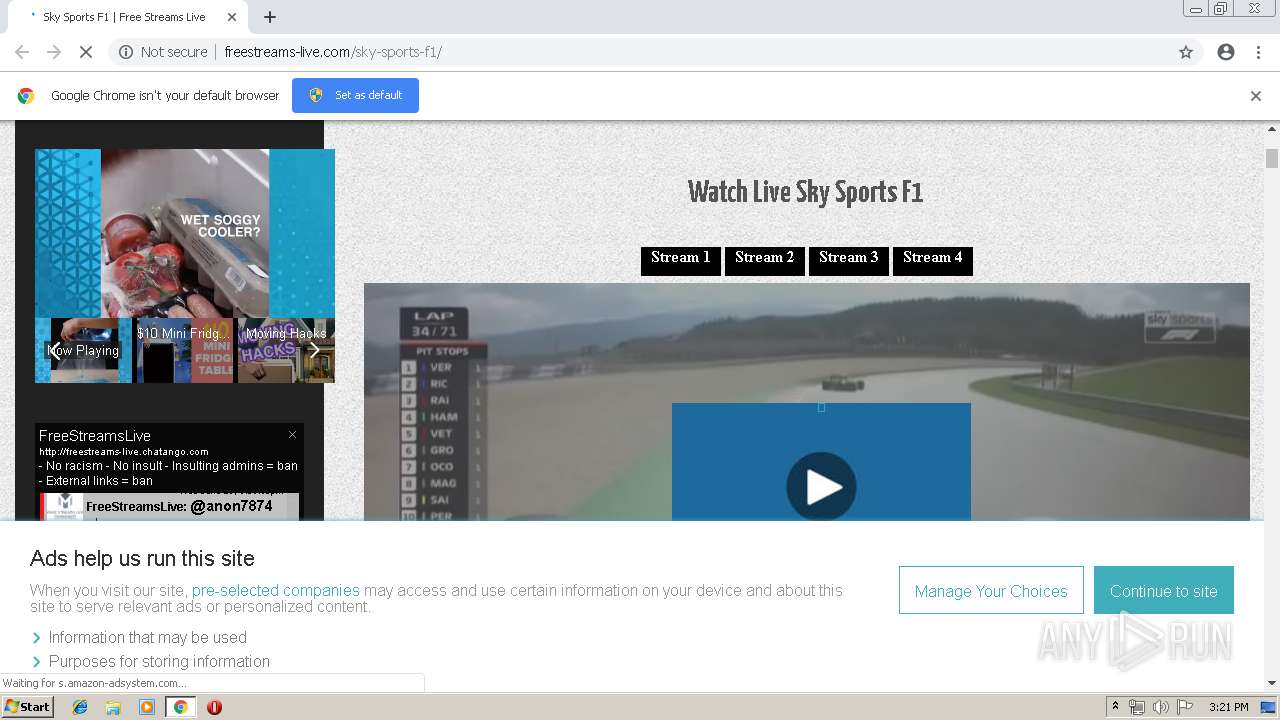
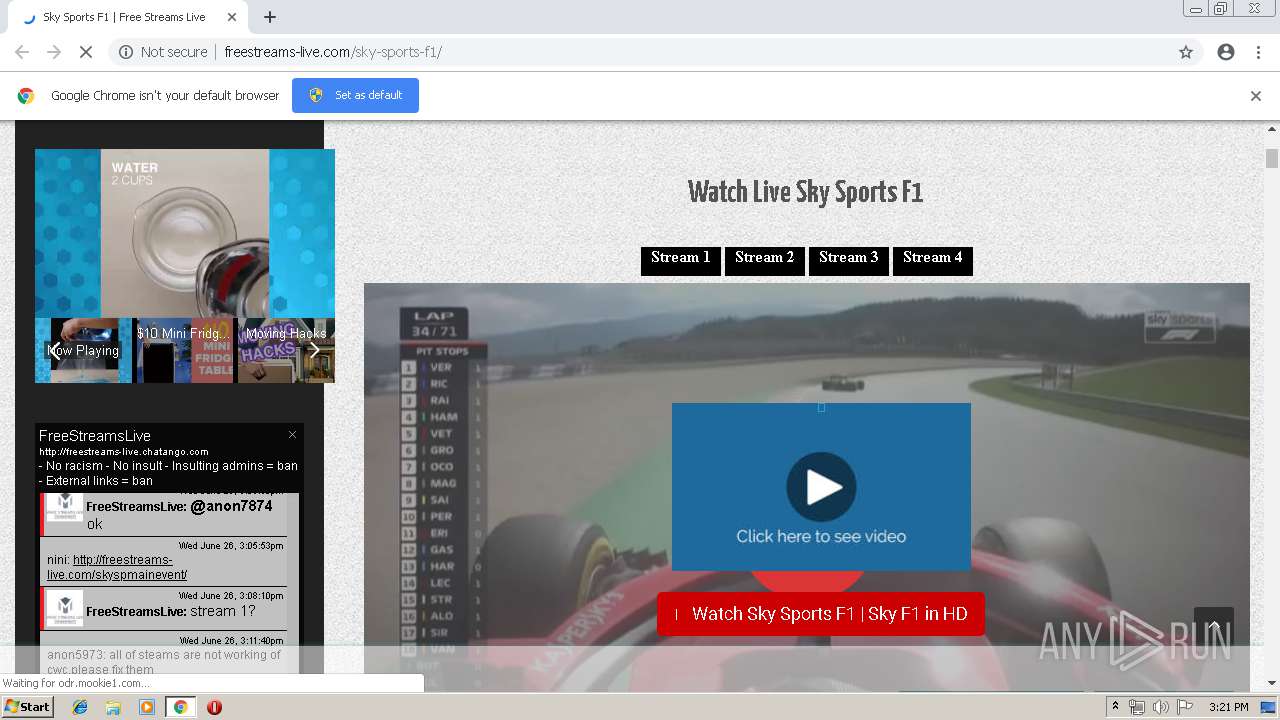
| URL: | http://freestreams-live.com/sky-sports-f1/ |
| Full analysis: | https://app.any.run/tasks/82e6bec3-cda5-4717-ac42-1e0158bd67e2 |
| Verdict: | Suspicious activity |
| Analysis date: | June 26, 2019, 14:20:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | AC75172A2DB68B8AA784E844F5083EE6 |
| SHA1: | 8F7B23932EFD9CCF46FBC351F83A33F6CCCC1082 |
| SHA256: | AE57C1164C156AF5F48224A8F9D061B0BF5B9105FDFFDF334086469E483A2BC3 |
| SSDEEP: | 3:N1KYQzRRcJMMkOoMwe:CY8TcJMz9Mwe |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3660)
INFO
Application launched itself
- chrome.exe (PID: 3660)
Reads settings of System Certificates
- chrome.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=490865088778904468 --mojo-platform-channel-handle=3572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2714492823795005121 --mojo-platform-channel-handle=2240 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16509160202921332292 --mojo-platform-channel-handle=7680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1456752846589109793 --mojo-platform-channel-handle=5252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17919435080159295048 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17919435080159295048 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10828921620051180586 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10828921620051180586 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3360 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13854938952786546588 --mojo-platform-channel-handle=5572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15403696630750045299 --mojo-platform-channel-handle=2664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2022990159826162492 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2022990159826162492 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
615
Read events
532
Write events
79
Delete events
4
Modification events
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3660-13206032475763250 |
Value: 259 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3660) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
120
Text files
169
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\91d1021d-9ba5-4544-aa91-71bd2682b8fd.tmp | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
236
TCP/UDP connections
198
DNS requests
114
Threats
91
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/sky-sports-f1/ | US | html | 53.8 Kb | malicious |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/wp-content/plugins/bradmax-player/assets/js/default_player.js?ver=2.7.0 | US | text | 507 Kb | malicious |
3660 | chrome.exe | GET | 200 | 172.217.22.10:80 | http://fonts.googleapis.com/css?family=Yanone+Kaffeesatz:200,300,regular,700|Sorts+Mill+Goudy:regular,italic | US | text | 749 b | whitelisted |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/wp-content/themes/durga/style.min.css?ver=1.0.0 | US | text | 8.27 Kb | malicious |
3660 | chrome.exe | GET | 200 | 104.25.68.115:80 | http://services.bilsyndication.com/adv1/?d=760 | US | text | 196 b | suspicious |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/wp-includes/css/dist/block-library/style.min.css?ver=5.2.2 | US | text | 5.75 Kb | malicious |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/cdn-cgi/scripts/5c5dd728/cloudflare-static/email-decode.min.js | US | html | 655 b | malicious |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/wp-content/themes/durga/css/unsemantic-grid.min.css?ver=1.0.0 | US | text | 2.91 Kb | malicious |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/wp-content/plugins/show-hidecollapse-expand/assets/css/bg-show-hide.css?ver=5.2.2 | US | text | 1.76 Kb | malicious |
3660 | chrome.exe | GET | 200 | 104.18.44.177:80 | http://freestreams-live.com/wp-content/plugins/jetpack/css/jetpack.css?ver=7.4.1 | US | text | 15.6 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | chrome.exe | 104.18.44.177:80 | freestreams-live.com | Cloudflare Inc | US | shared |
3660 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3660 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3660 | chrome.exe | 172.217.22.10:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3660 | chrome.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3660 | chrome.exe | 104.25.68.115:80 | services.bilsyndication.com | Cloudflare Inc | US | shared |
3660 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
3660 | chrome.exe | 104.25.67.115:80 | services.bilsyndication.com | Cloudflare Inc | US | shared |
3660 | chrome.exe | 92.122.255.130:443 | www.paypal.com | GTT Communications Inc. | — | unknown |
3660 | chrome.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
freestreams-live.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
services.bilsyndication.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s0.wp.com |
| whitelisted |
st.chatango.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3660 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3660 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3660 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |